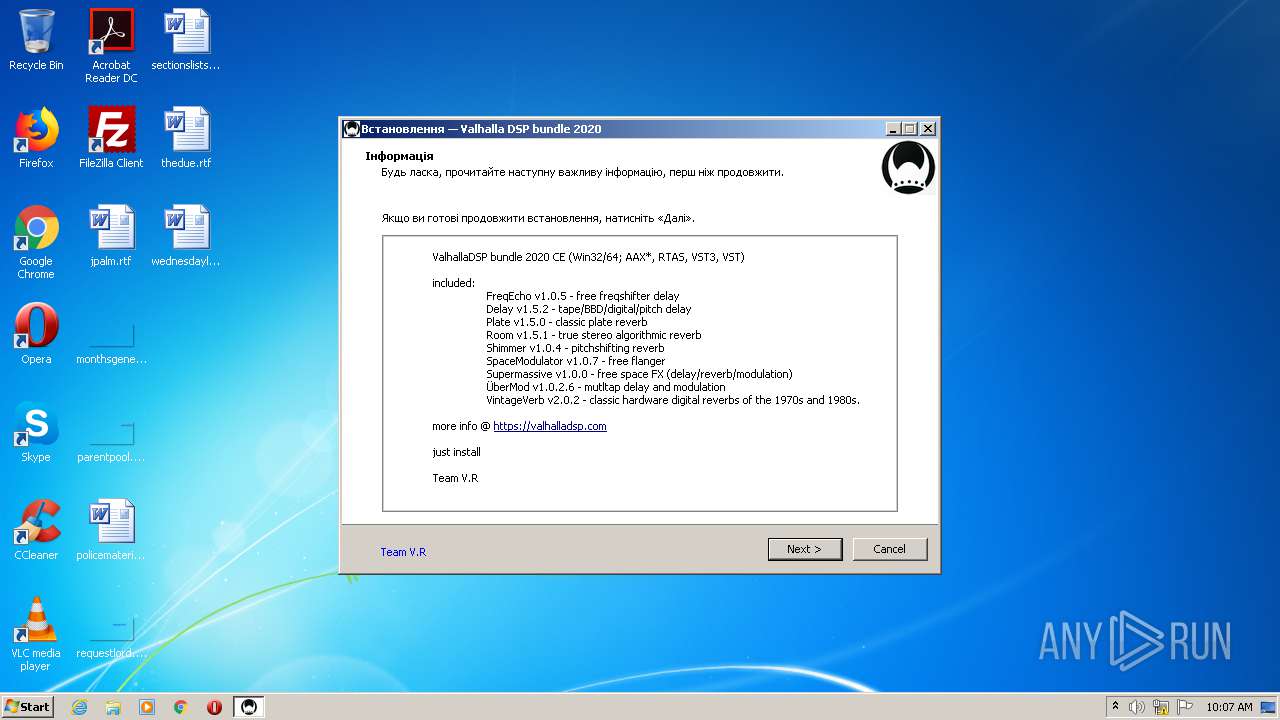
| File name: | ValhallaDSP bundle 2020 CE.exe |
| Full analysis: | https://app.any.run/tasks/3277d067-6621-48db-a952-8a7cb3bd3c13 |
| Verdict: | No threats detected |
| Analysis date: | October 22, 2020, 09:07:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8EEFB1D965A2F01F1F8F85543FDECCD6 |
| SHA1: | C389E03CFDC9F15B79ACAB6834E9F414A93BD9CF |
| SHA256: | D585CDB5C980C58EAECB91A456AB3D9FFA61CA96B8E6CD8794A2A1FBEA086AEE |
| SSDEEP: | 196608:e2SQzy6gi9cJPBRsXPedfkt73oAyagvrvEmZ9xAyz5/5Vcis1ZV40fO:WQzbcrRsXPedk3lHkw1n40m |
MALICIOUS
No malicious indicators.SUSPICIOUS
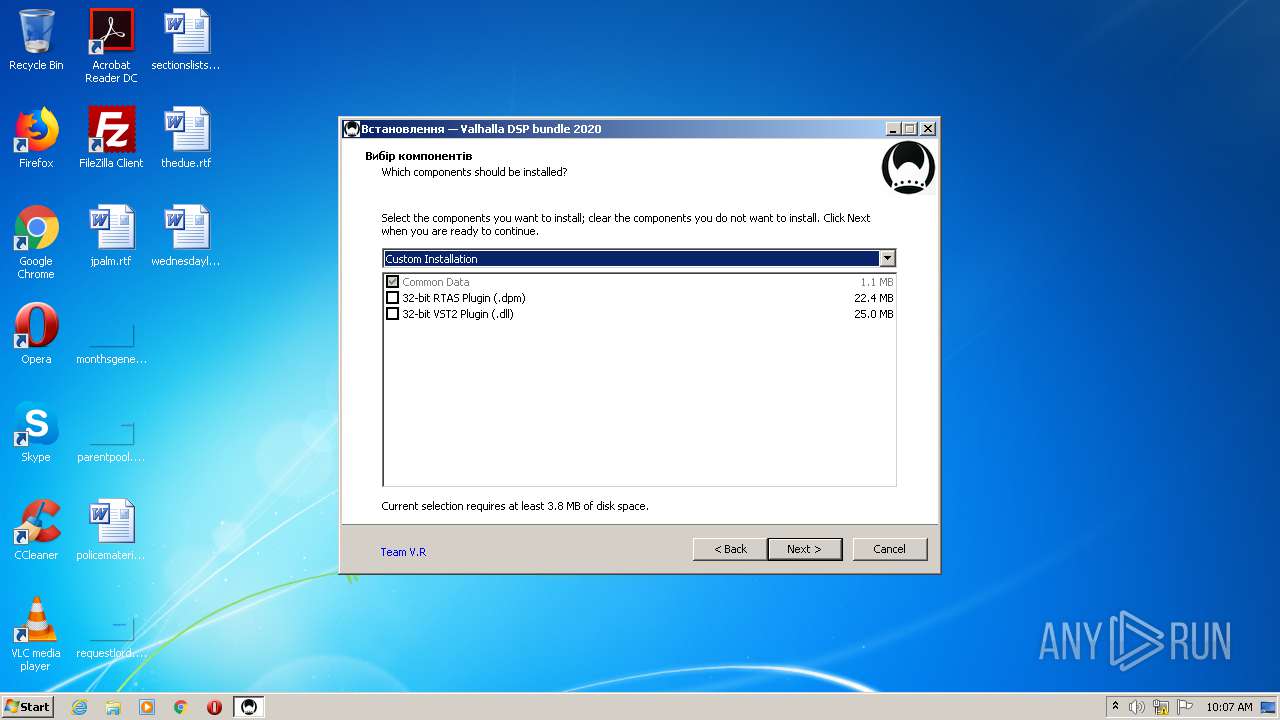
Executable content was dropped or overwritten
- ValhallaDSP bundle 2020 CE.exe (PID: 3692)
- ValhallaDSP bundle 2020 CE.exe (PID: 492)
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Reads the Windows organization settings
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Reads Windows owner or organization settings
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
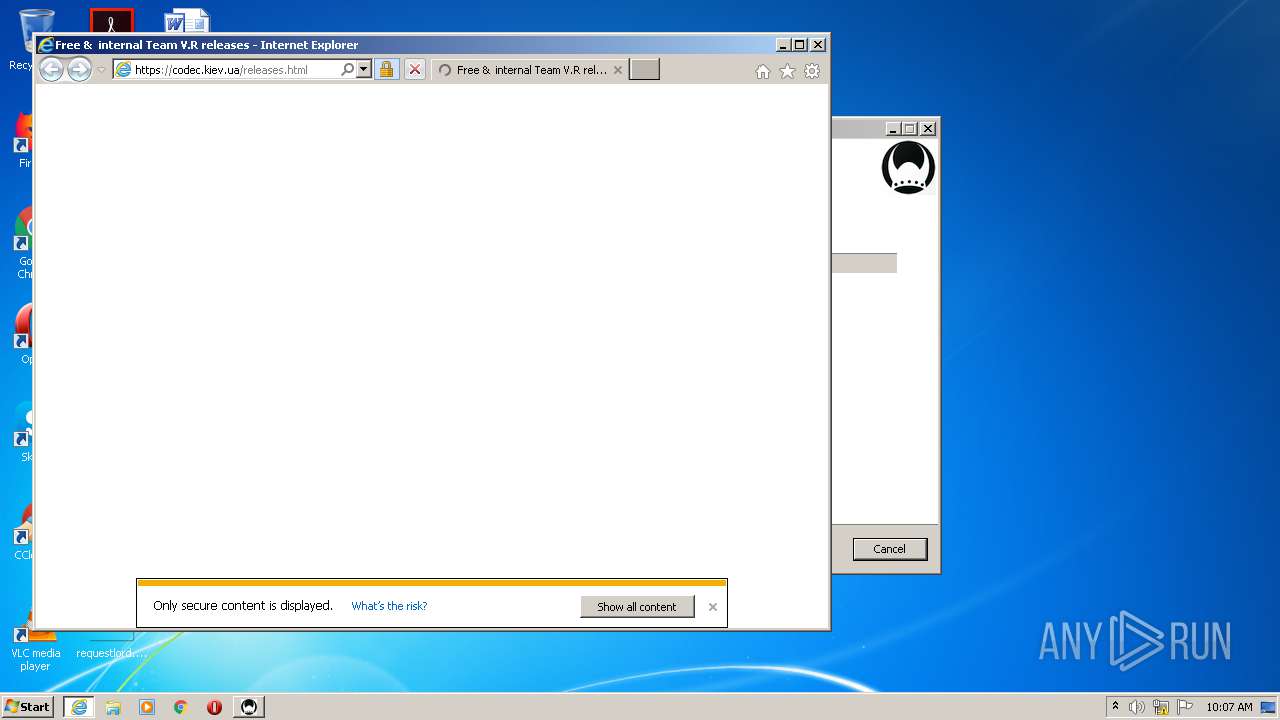
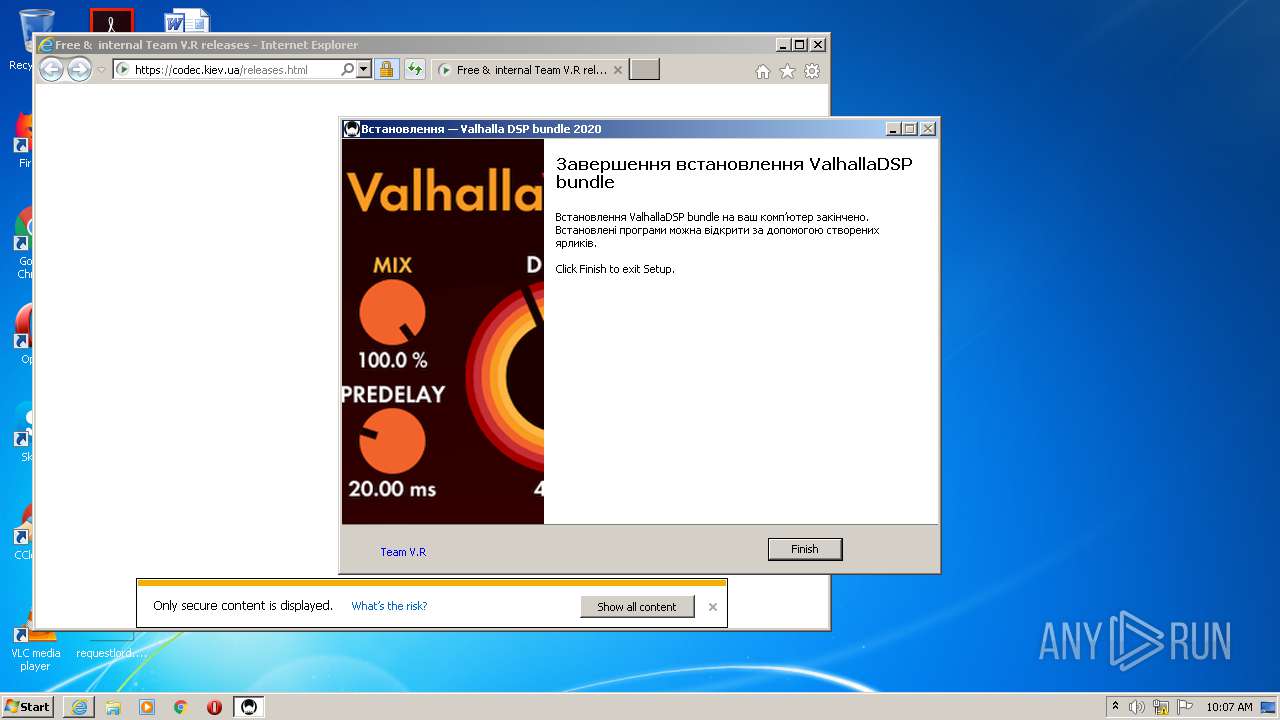
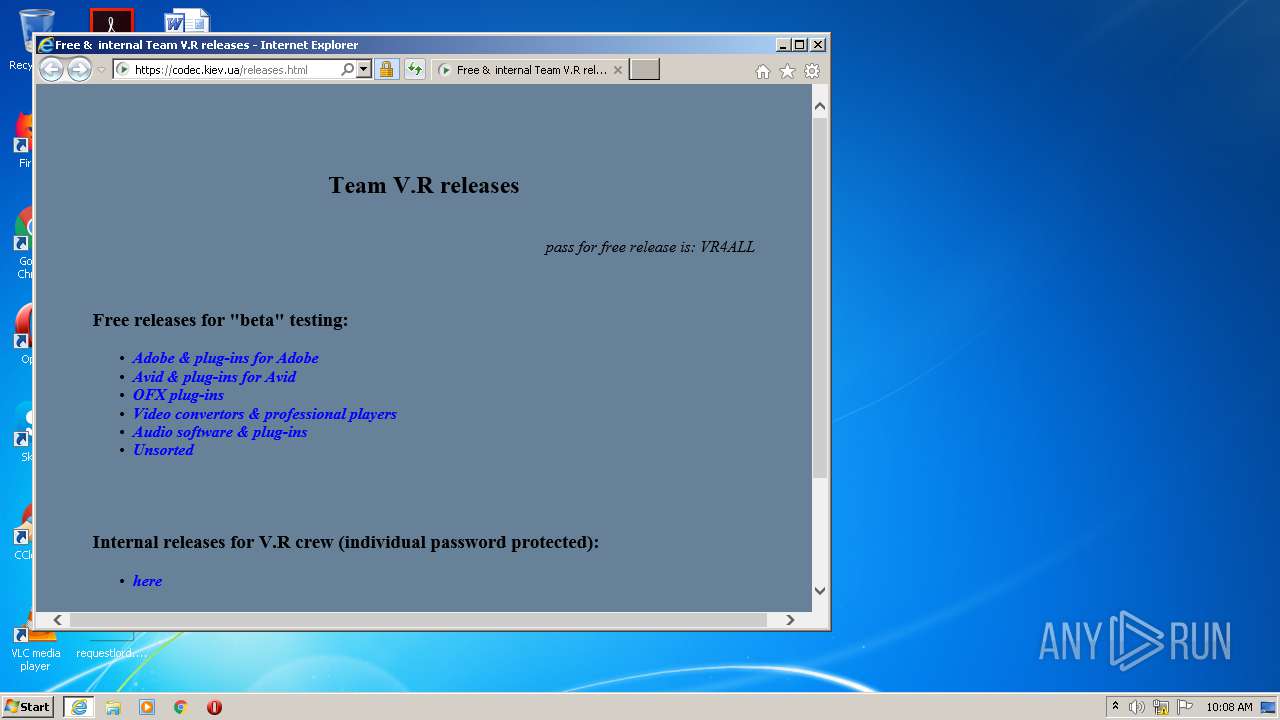
Starts Internet Explorer
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Creates files in the user directory
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
INFO
Application was dropped or rewritten from another process
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
- ValhallaDSP bundle 2020 CE.tmp (PID: 1580)
Changes internet zones settings
- iexplore.exe (PID: 2268)
Changes settings of System certificates
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 2268)
Loads dropped or rewritten executable
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Reads Internet Cache Settings
- iexplore.exe (PID: 2268)
- iexplore.exe (PID: 2524)
Application launched itself
- iexplore.exe (PID: 2268)
Reads internet explorer settings
- iexplore.exe (PID: 2524)
Creates a software uninstall entry
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2524)
- iexplore.exe (PID: 2268)
Creates files in the user directory
- iexplore.exe (PID: 2524)
Reads settings of System Certificates
- iexplore.exe (PID: 2268)
Creates files in the program directory
- ValhallaDSP bundle 2020 CE.tmp (PID: 1396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:12 17:48:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 216576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2020.0.0.0 |
| ProductVersionNumber: | 2020.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Released by Team V.R |
| CompanyName: | Valhalla DSP |
| FileDescription: | bundle |
| FileVersion: | bundle 2020 |
| LegalCopyright: | © Valhalla DSP |
| OriginalFileName: | |
| ProductName: | Valhalla DSP bundle |
| ProductVersion: | 2020 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Mar-2020 16:48:59 |
| Detected languages: |
|
| Comments: | Released by Team V.R |
| CompanyName: | Valhalla DSP |
| FileDescription: | bundle |
| FileVersion: | bundle 2020 |
| LegalCopyright: | © Valhalla DSP |
| OriginalFileName: | - |
| ProductName: | Valhalla DSP bundle |
| ProductVersion: | 2020 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 12-Mar-2020 16:48:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B3604 | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35433 |
.itext | 0x000B5000 | 0x00001684 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9709 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04216 |
.bss | 0x000BB000 | 0x00006DA0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0002FE28 | 0x00030000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04249 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.67947 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.6061 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.91248 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.955 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.22215 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.37106 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.49714 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054058 |
Total processes
46
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe" | C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe | explorer.exe | ||||||||||||
User: admin Company: Valhalla DSP Integrity Level: MEDIUM Description: bundle Exit code: 0 Version: bundle 2020 Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\AppData\Local\Temp\is-GTJK0.tmp\ValhallaDSP bundle 2020 CE.tmp" /SL5="$70184,13916924,958976,C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe" /SPAWNWND=$401C4 /NOTIFYWND=$A0164 | C:\Users\admin\AppData\Local\Temp\is-GTJK0.tmp\ValhallaDSP bundle 2020 CE.tmp | ValhallaDSP bundle 2020 CE.exe | ||||||||||||
User: admin Company: Valhalla DSP Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\AppData\Local\Temp\is-JLFSL.tmp\ValhallaDSP bundle 2020 CE.tmp" /SL5="$A0164,13916924,958976,C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe" | C:\Users\admin\AppData\Local\Temp\is-JLFSL.tmp\ValhallaDSP bundle 2020 CE.tmp | — | ValhallaDSP bundle 2020 CE.exe | |||||||||||
User: admin Company: Valhalla DSP Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Internet Explorer\iexplore.exe" https://codec.kiev.ua/releases.html | C:\Program Files\Internet Explorer\iexplore.exe | ValhallaDSP bundle 2020 CE.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2268 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe" /SPAWNWND=$401C4 /NOTIFYWND=$A0164 | C:\Users\admin\AppData\Local\Temp\ValhallaDSP bundle 2020 CE.exe | ValhallaDSP bundle 2020 CE.tmp | ||||||||||||
User: admin Company: Valhalla DSP Integrity Level: HIGH Description: bundle Exit code: 0 Version: bundle 2020 Modules
| |||||||||||||||
Total events
1 356
Read events
1 230
Write events
120
Delete events
6
Modification events
| (PID) Process: | (1396) ValhallaDSP bundle 2020 CE.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 74050000069B15CB52A8D601 | |||
| (PID) Process: | (1396) ValhallaDSP bundle 2020 CE.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: F1A99330DAE23F82E2FEBB65E40FC16EA162B663052CED87C41445BD27083C30 | |||
| (PID) Process: | (1396) ValhallaDSP bundle 2020 CE.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3781878290 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30845010 | |||
| (PID) Process: | (1396) ValhallaDSP bundle 2020 CE.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000E8C973CF52A8D601 | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
4
Suspicious files
27
Text files
1 491
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\is-7HCRM.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-GSVKB.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-MOUVT.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-T7BB1.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-VKUOQ.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-6JKD0.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-79EU7.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-UP3HG.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-PP247.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | ValhallaDSP bundle 2020 CE.tmp | C:\ProgramData\Valhalla DSP, LLC\ValhallaDelay\Presets\Designer\Richard Devine\is-ABOT0.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | iexplore.exe | GET | — | 172.217.21.194:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | — | — | whitelisted |
2524 | iexplore.exe | GET | — | 172.217.21.194:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | — | — | whitelisted |
2524 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCOUTy4wn8XWggAAAAAWy8I | US | der | 472 b | whitelisted |
2524 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTv61FVlC2Sp0PGS59EjMxVIQ%3D%3D | unknown | der | 527 b | whitelisted |
2524 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2268 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2524 | iexplore.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDs6m8Yj1axcgIAAAAAfDUL | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2524 | iexplore.exe | 185.13.5.43:443 | codec.kiev.ua | PE Freehost | UA | unknown |
2524 | iexplore.exe | 172.217.21.194:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2524 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2524 | iexplore.exe | 216.58.207.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2524 | iexplore.exe | 172.217.22.74:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2524 | iexplore.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2268 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2524 | iexplore.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2268 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2268 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
codec.kiev.ua |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cse.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
www.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
api.bing.com |
| whitelisted |