| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/8d79349e-7a42-42e7-8f63-ef4b6f636299 |
| Verdict: | Malicious activity |
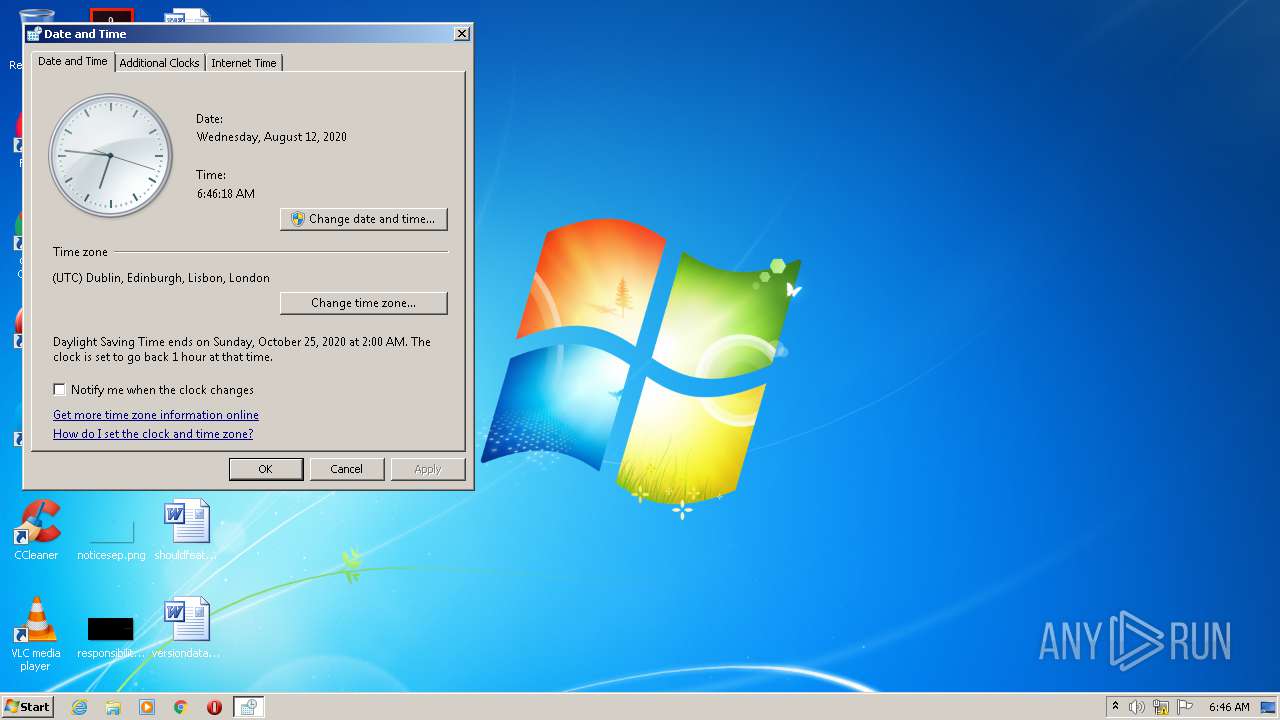
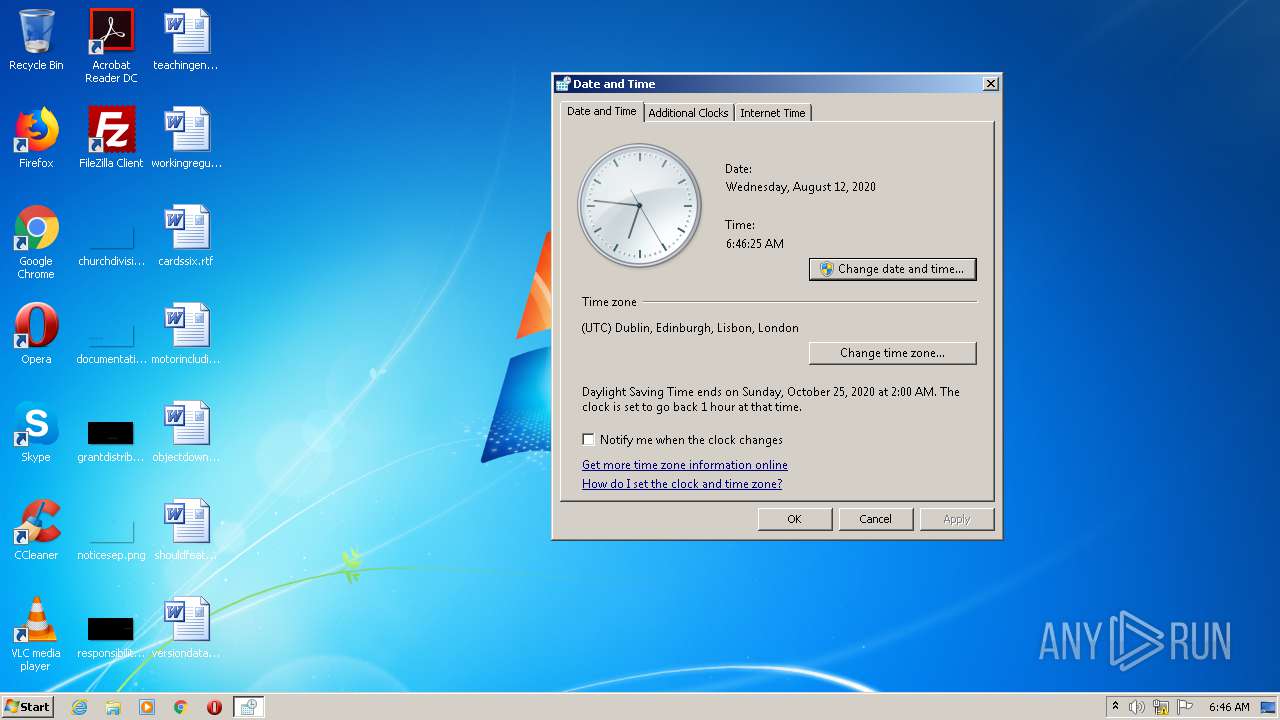
| Analysis date: | August 12, 2020, 05:43:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 645FC735A4A8C11F02F3C7C8B0E646E2 |
| SHA1: | 5A3BC3455ABB9C071E613A4ED458B7AE88D3C675 |
| SHA256: | D576B6171B62A5EF9CDDCD6CE8AC22407B91FB0A256EBDAAA97C9ED25C1D3B7B |
| SSDEEP: | 12288:Ttb20Qc3lT7af41ePBRYuQLKpqeUhbTv5OFgNuPPpHSgaON6vqV6A:Ttb20pkaCqT5TBWgNQ7ahqV6A |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2992)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2488)
- schtasks.exe (PID: 3132)
Uses Task Scheduler to run other applications
- MSShell32.exe (PID: 3656)
- 1.exe (PID: 2936)
SUSPICIOUS
Executable content was dropped or overwritten
- 1.exe (PID: 2936)
Uses NETSH.EXE for network configuration
- MSShell32.exe (PID: 3656)
Starts CMD.EXE for commands execution
- 1.exe (PID: 2936)
Creates files in the user directory
- 1.exe (PID: 2936)
Executed via Task Scheduler
- MSShell32.exe (PID: 2780)
- MSShell32.exe (PID: 1528)
- MSShell32.exe (PID: 2868)
- MSShell32.exe (PID: 3500)
- MSShell32.exe (PID: 3184)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 2716)
- control.exe (PID: 1896)
Executed via COM
- DllHost.exe (PID: 2908)
- DllHost.exe (PID: 1376)
INFO
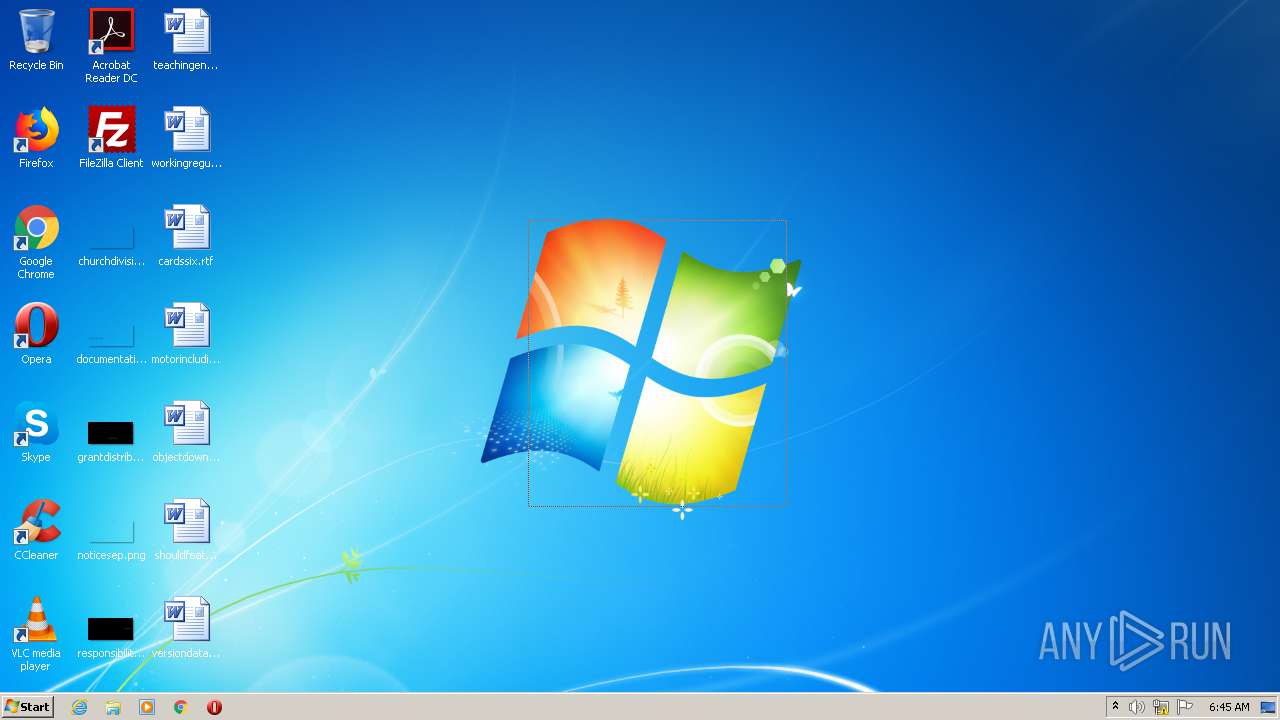
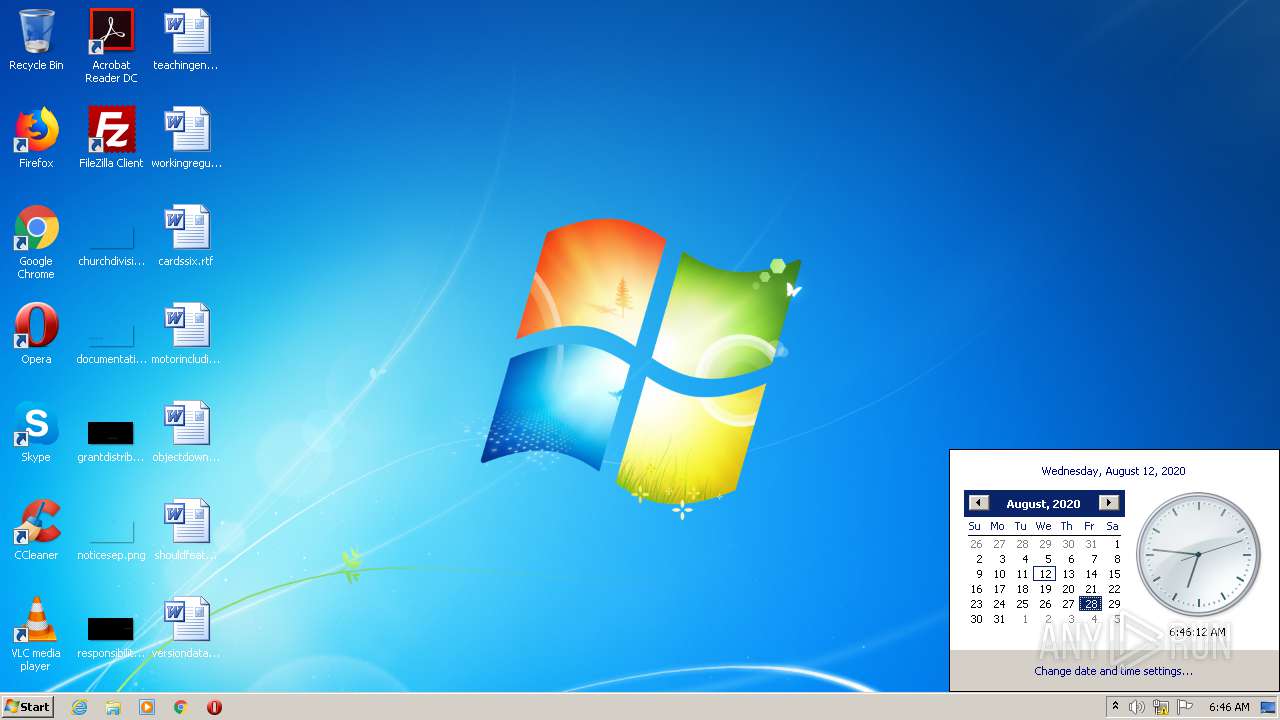
Manual execution by user
- control.exe (PID: 2716)
- WINWORD.EXE (PID: 2720)
- control.exe (PID: 1896)
Creates files in the user directory
- WINWORD.EXE (PID: 2720)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:23 03:18:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 570880 |
| InitializedDataSize: | 313856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25f74 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-May-2017 01:18:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-May-2017 01:18:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008B54F | 0x0008B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68041 |
.rdata | 0x0008D000 | 0x0002CC42 | 0x0002CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.77019 |
.data | 0x000BA000 | 0x00009D54 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.00269 |
.rsrc | 0x000C4000 | 0x0000F3B0 | 0x0000F400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99487 |
.reloc | 0x000D4000 | 0x0000A474 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.24543 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38312 | 944 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
SCRIPT | 7.99745 | 61254 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
67
Monitored processes
19
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1376 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | C:\Users\admin\AppData\Roaming\MSShell32.exe | C:\Users\admin\AppData\Roaming\MSShell32.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1792 | ping 0.0.0.0 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
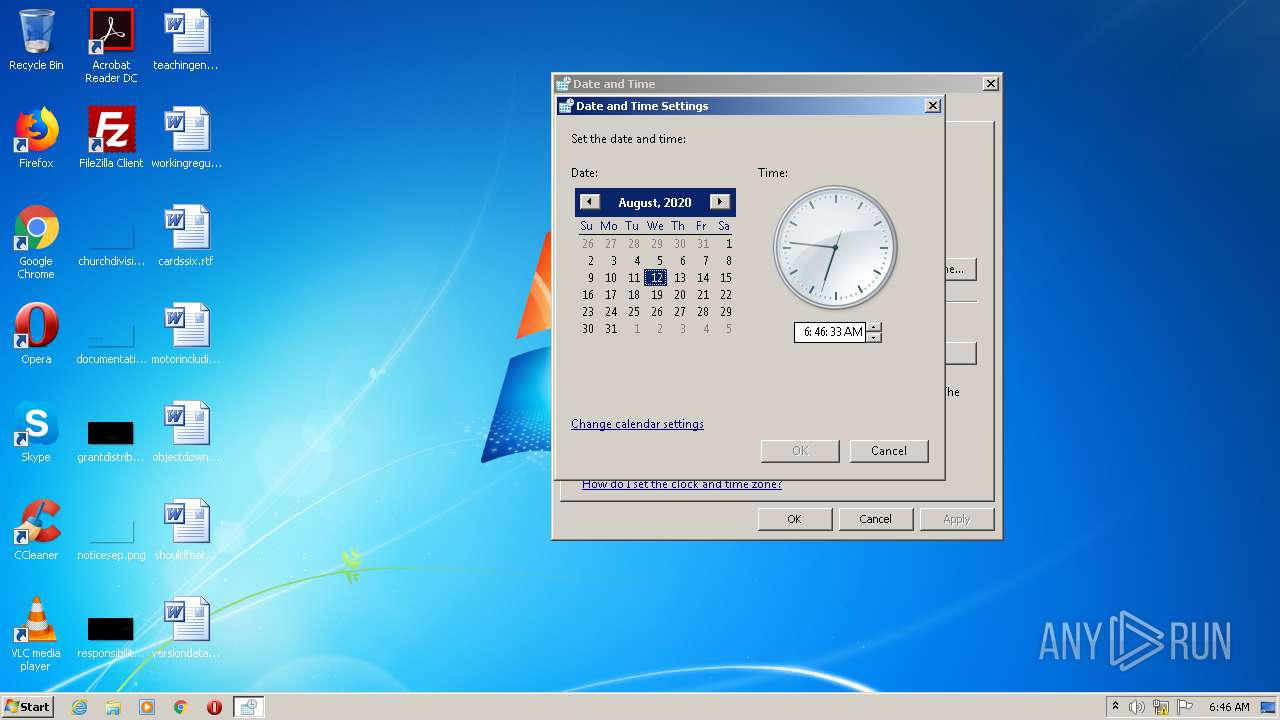
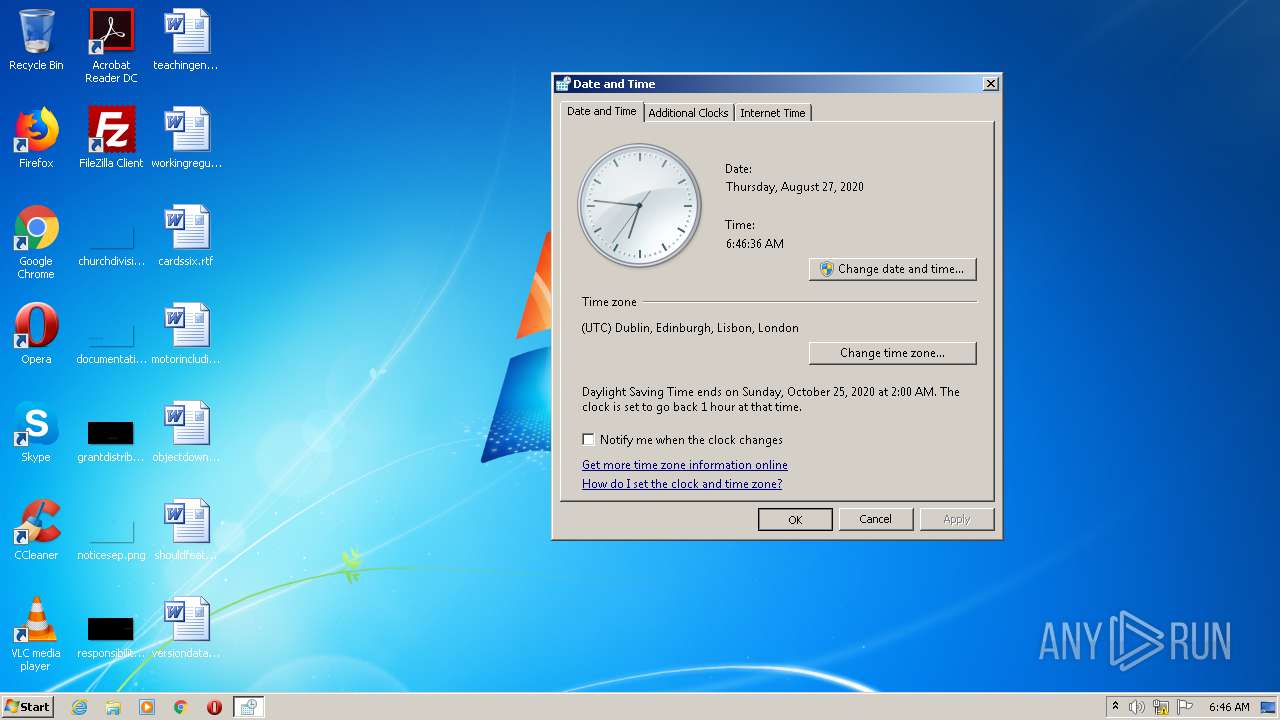
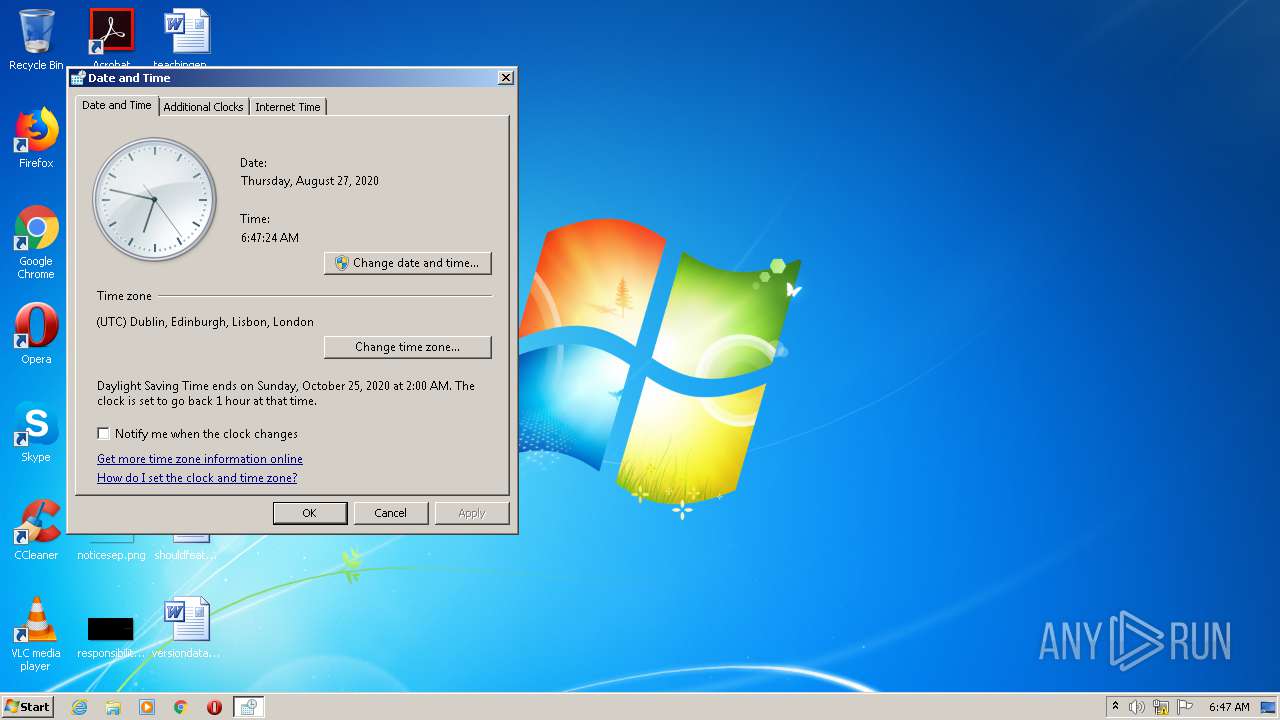
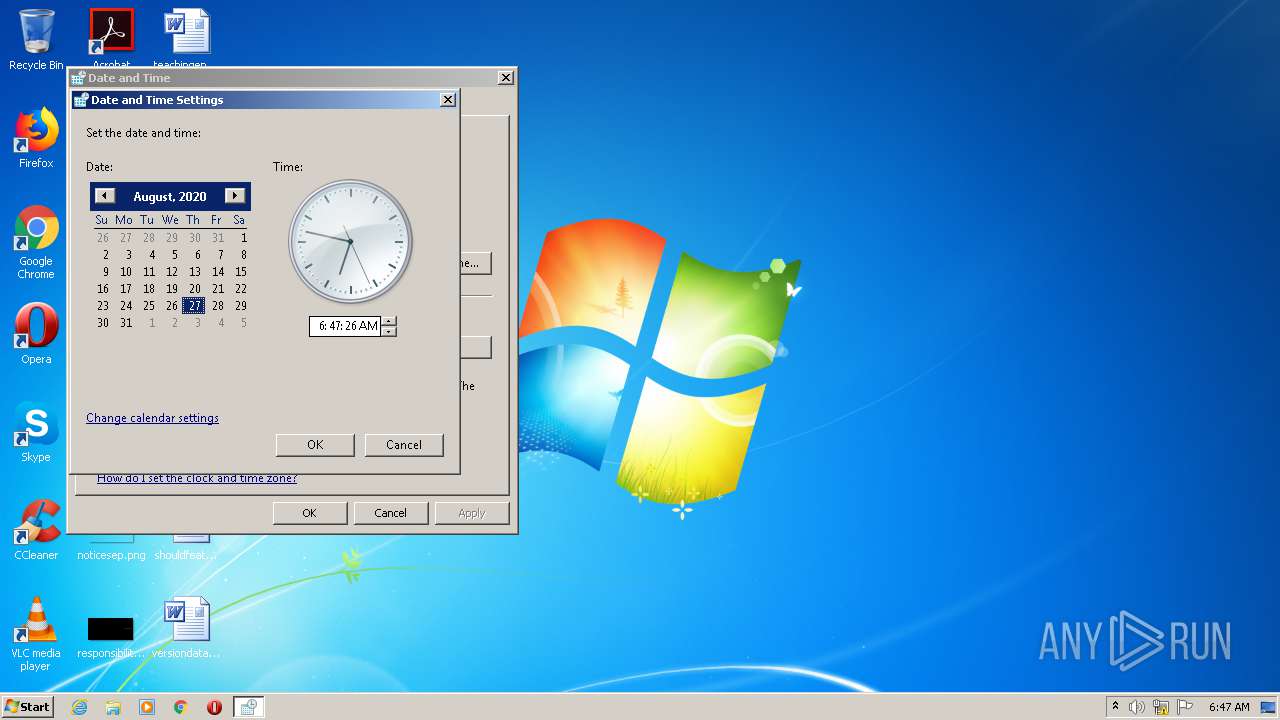
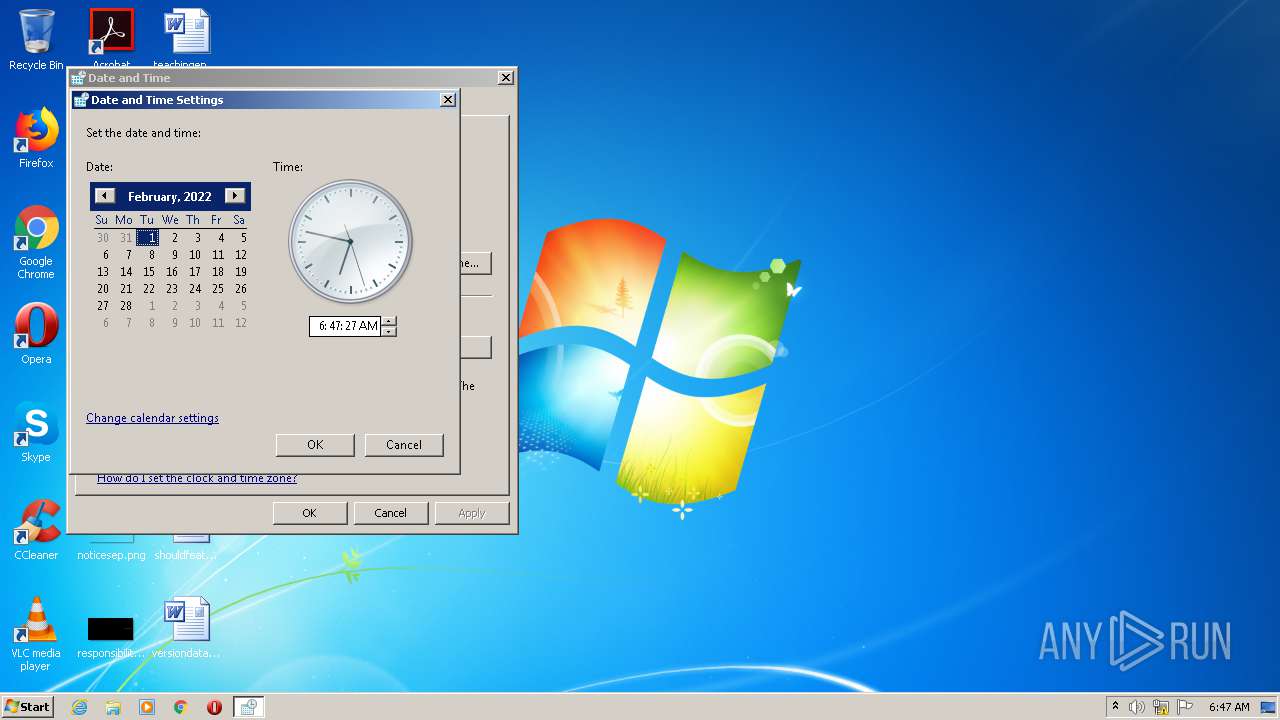
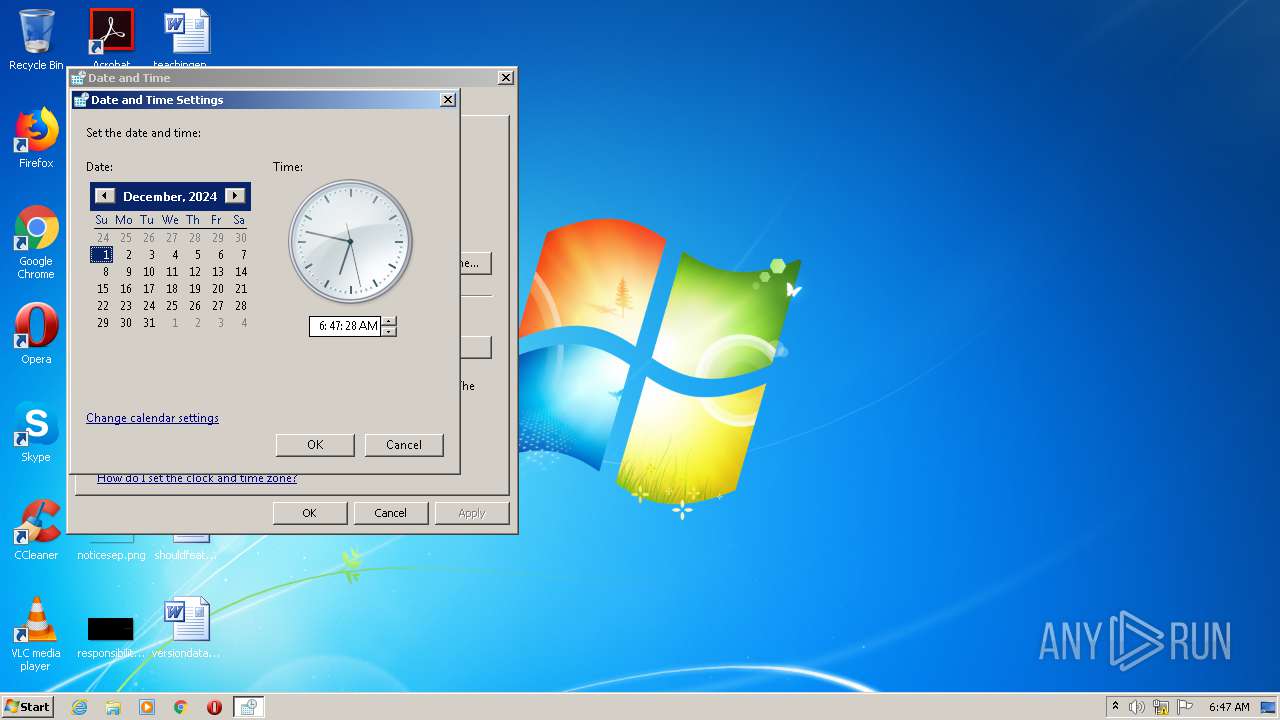
| 1896 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn MSShell32 /tr "C:\Users\admin\AppData\Roaming\MSShell32.exe" | C:\Windows\System32\schtasks.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\cardssix.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2780 | C:\Users\admin\AppData\Roaming\MSShell32.exe | C:\Users\admin\AppData\Roaming\MSShell32.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2868 | C:\Users\admin\AppData\Roaming\MSShell32.exe | C:\Users\admin\AppData\Roaming\MSShell32.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2908 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 968
Read events
1 573
Write events
244
Delete events
151
Modification events
| (PID) Process: | (3656) MSShell32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 2 | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3352) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
Executable files
1
Suspicious files
0
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5F68.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0B6BAA9E-8A2F-41C5-ACF3-B7010E0A338D}.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{69E4460D-0744-44B1-B476-ADA34012C69A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{81CA423A-C2CC-468D-B5C9-0C73B05CAA1B}.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | 1.exe | C:\Users\admin\AppData\Roaming\MSShell32.exe | executable | |
MD5:645FC735A4A8C11F02F3C7C8B0E646E2 | SHA256:D576B6171B62A5EF9CDDCD6CE8AC22407B91FB0A256EBDAAA97C9ED25C1D3B7B | |||
| 3656 | MSShell32.exe | C:\Users\admin\AppData\Roaming\MSShell32.ini | text | |
MD5:A5ECD644E2428C7C18B0B039C9C66889 | SHA256:9E81F05F62EB9EBA87520DDC0D42E1FB83CFD47D3918CB8C2372D04A39F27EC0 | |||
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:C0F682202040CD6299EA01172FCAEFBF | SHA256:5EC9A1F61604ACF4D8FF0592CBC12D4842CC46BDAEDC10EA50865FB6D00FBAB7 | |||
| 2720 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\cardssix.rtf.LNK | lnk | |
MD5:74C3DBE8CCEB24B96842C1D9C0E70F95 | SHA256:FF01D957D3E036EC7D17999CA0547A67E1CACD90D8383DB253AFEF2651D126CB | |||
| 2936 | 1.exe | C:\Users\admin\AppData\Roaming\MSShell32.ini | text | |
MD5:97A75A065383136B888DA2884B84CEBA | SHA256:46F6285AE622E0C180232E435CE0B43311C9F5B38CE43526160B993B734A3268 | |||
| 2720 | WINWORD.EXE | C:\Users\admin\Desktop\~$rdssix.rtf | pgc | |
MD5:02B734F74ED4CF0E3CB56E2C3B0E667B | SHA256:F240B81C3C5D4BFB12A3D0B6FA787F06F6D7E85607A41C3190A73FC308ACB418 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
8
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3656 | MSShell32.exe | 156.205.63.98:37556 | coordinates.ddns.net | TE-AS | EG | unknown |
3656 | MSShell32.exe | 156.205.186.12:37556 | egyth.dynu.net | TE-AS | EG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
coordinates.ddns.net |
| malicious |
egyth.dynu.net |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |