| download: | privazer.exe |
| Full analysis: | https://app.any.run/tasks/ffc299bf-94c8-4477-ac9a-bda10c9b56f7 |
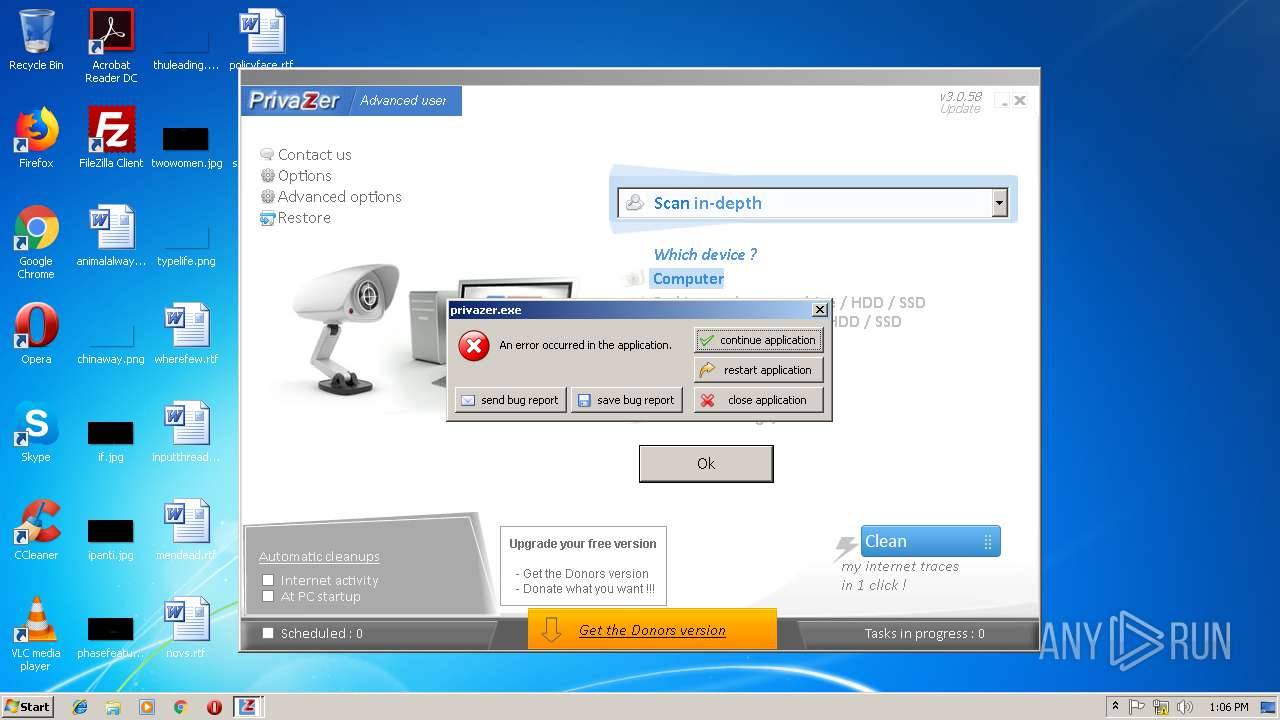
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 13:03:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6673E7865AD6FBA833FEFDFB97DB95F3 |
| SHA1: | 2FB530716DB4961034A6BF4F565069CD321343DE |
| SHA256: | D5612350DC3572A79598F91850F5E8DCC030BE7F74CAC444378C162DBF0F0462 |
| SSDEEP: | 393216:82gXj19KSr2KjVJHxSUQa4bISYxH6eEUxUsUDpcpl6RVK:W2DDpdRVK |
MALICIOUS
Loads the Task Scheduler COM API
- privazer.exe (PID: 3472)
- privazer.exe (PID: 2592)
Application was dropped or rewritten from another process
- leveldb-viewer.exe (PID: 2344)
- leveldb-viewer.exe (PID: 2976)
- leveldb-viewer.exe (PID: 3804)
- dismhost.exe (PID: 2132)
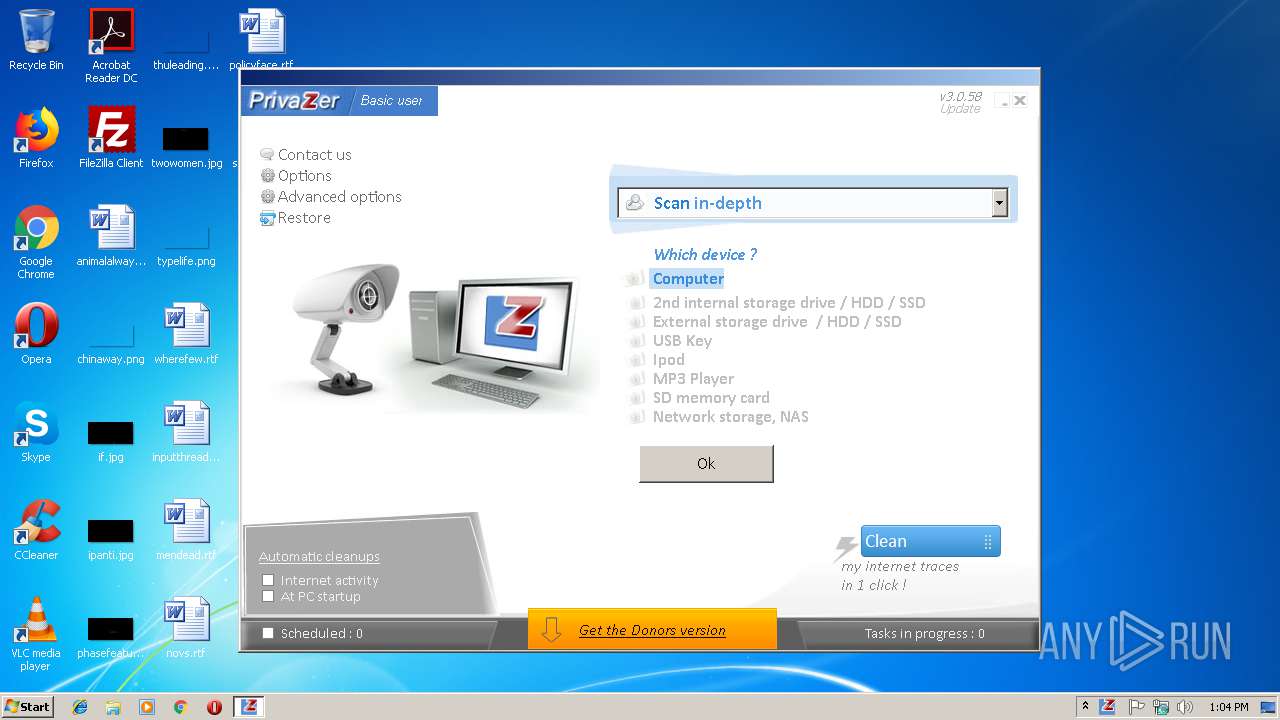
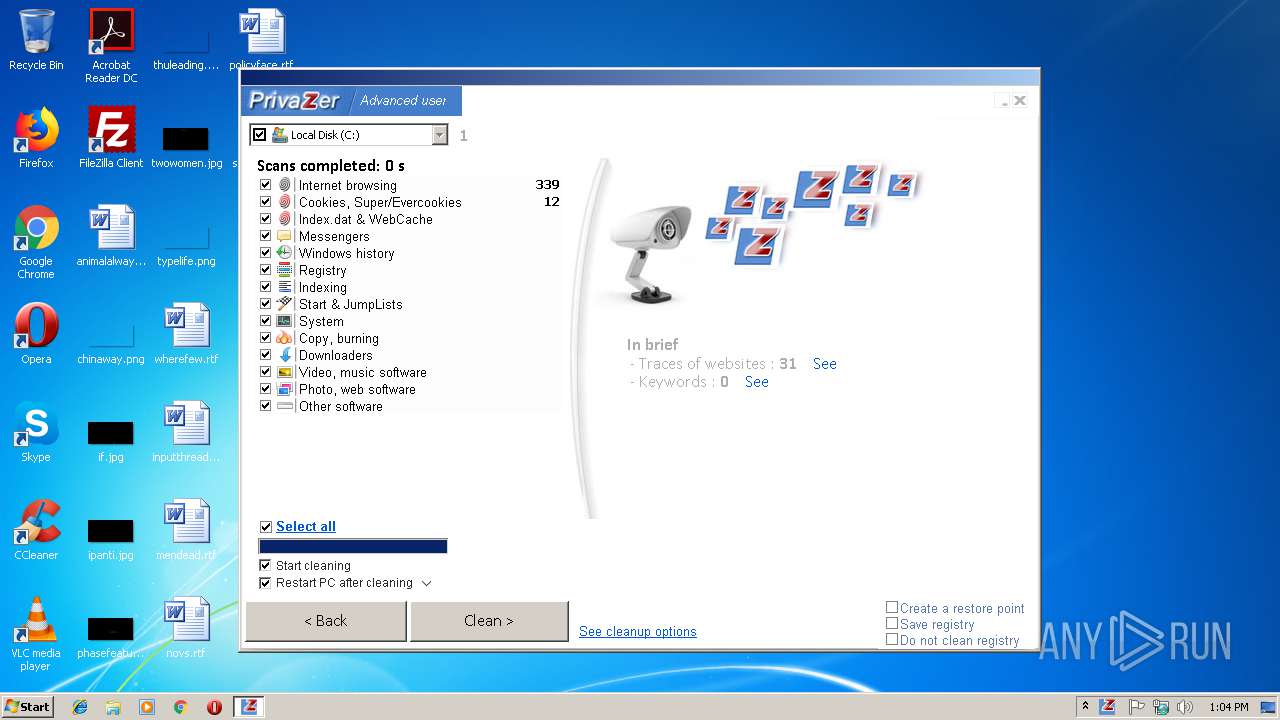
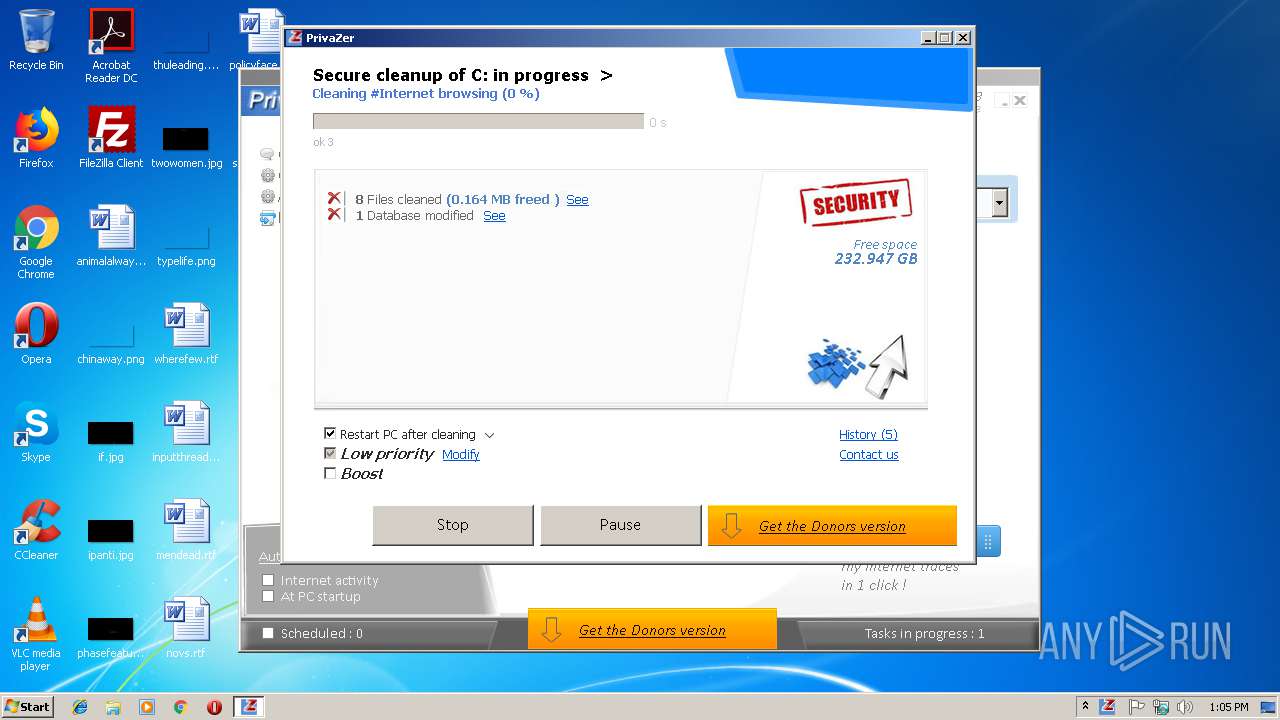
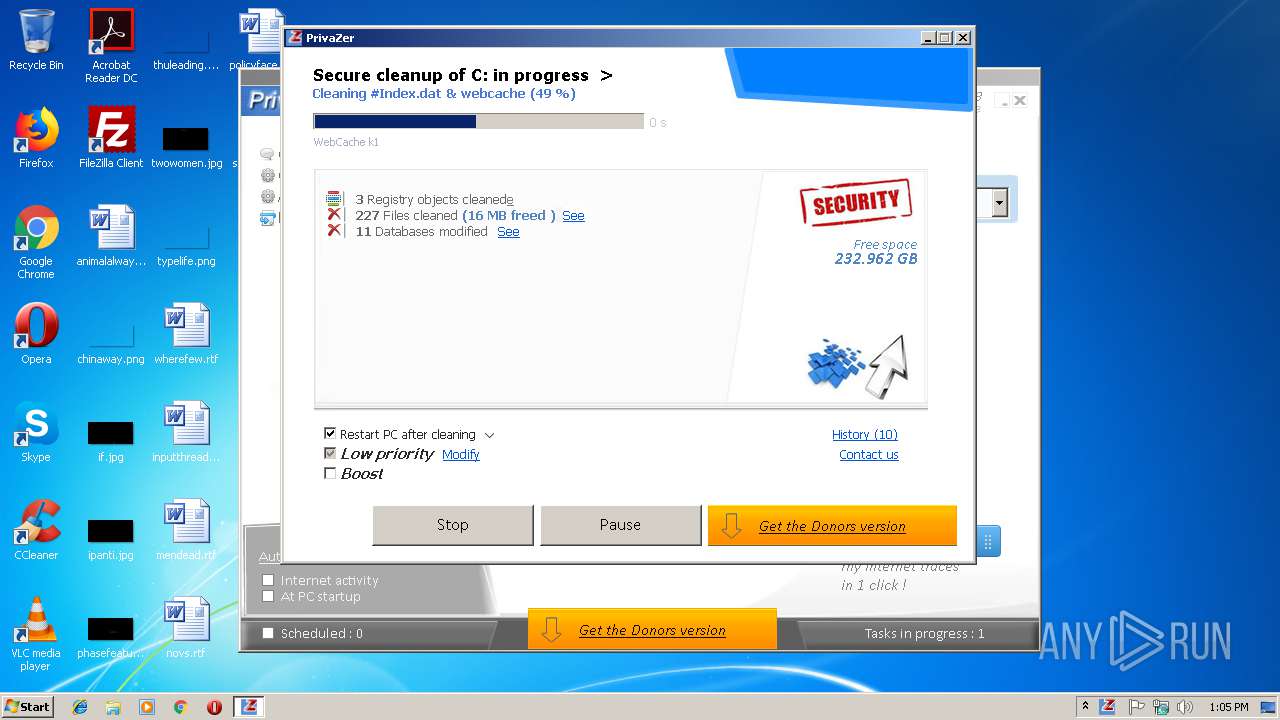
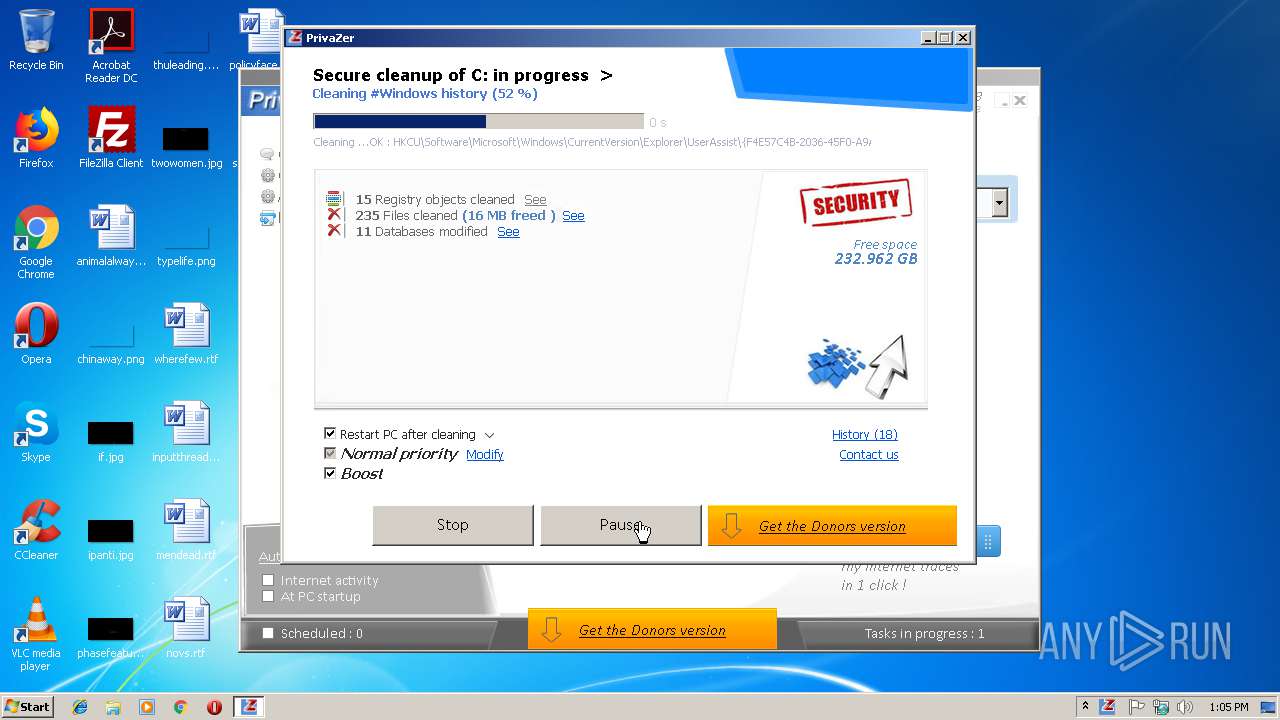
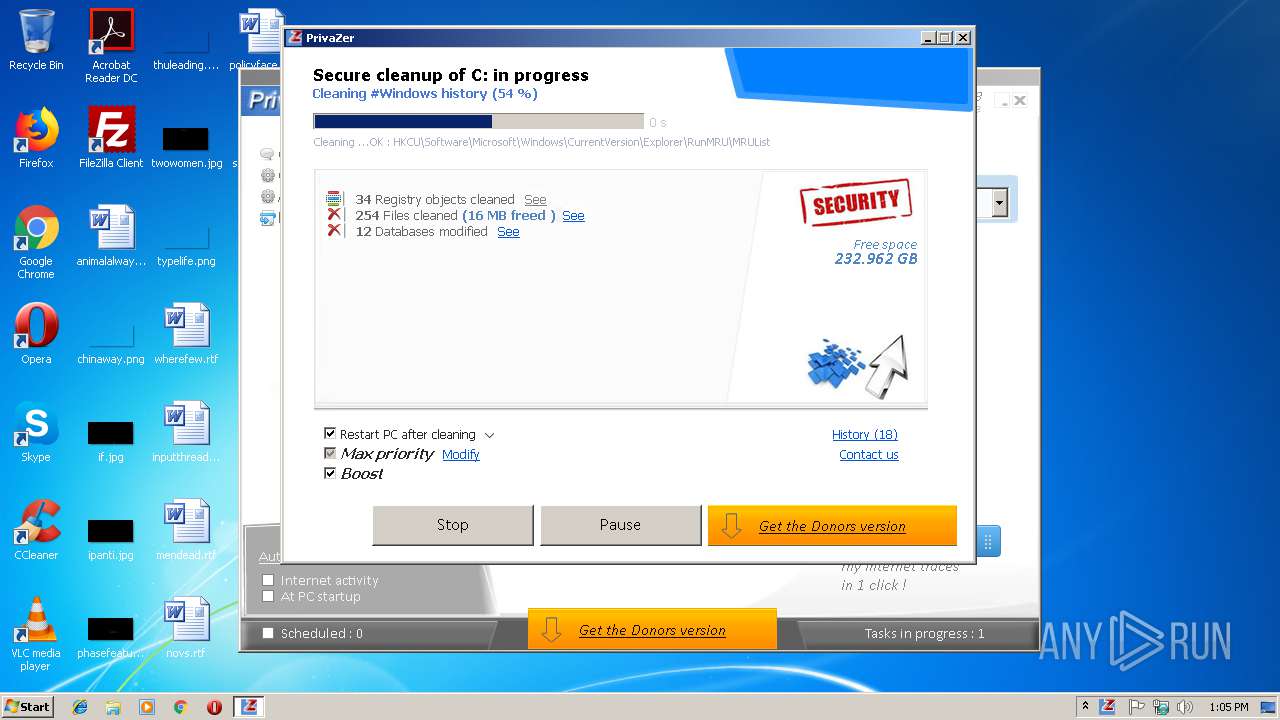
Actions looks like stealing of personal data
- privazer.exe (PID: 2592)
Loads dropped or rewritten executable
- privazer.exe (PID: 2592)
- cleanmgr.exe (PID: 3076)
- dismhost.exe (PID: 2132)
- TrustedInstaller.exe (PID: 3968)
SUSPICIOUS
Application launched itself
- privazer.exe (PID: 3472)
Executable content was dropped or overwritten
- privazer.exe (PID: 2592)
- cleanmgr.exe (PID: 3076)
Creates files in the program directory
- SearchIndexer.exe (PID: 2544)
- privazer.exe (PID: 2592)
- SearchIndexer.exe (PID: 3876)
Creates files in the user directory
- privazer.exe (PID: 2592)
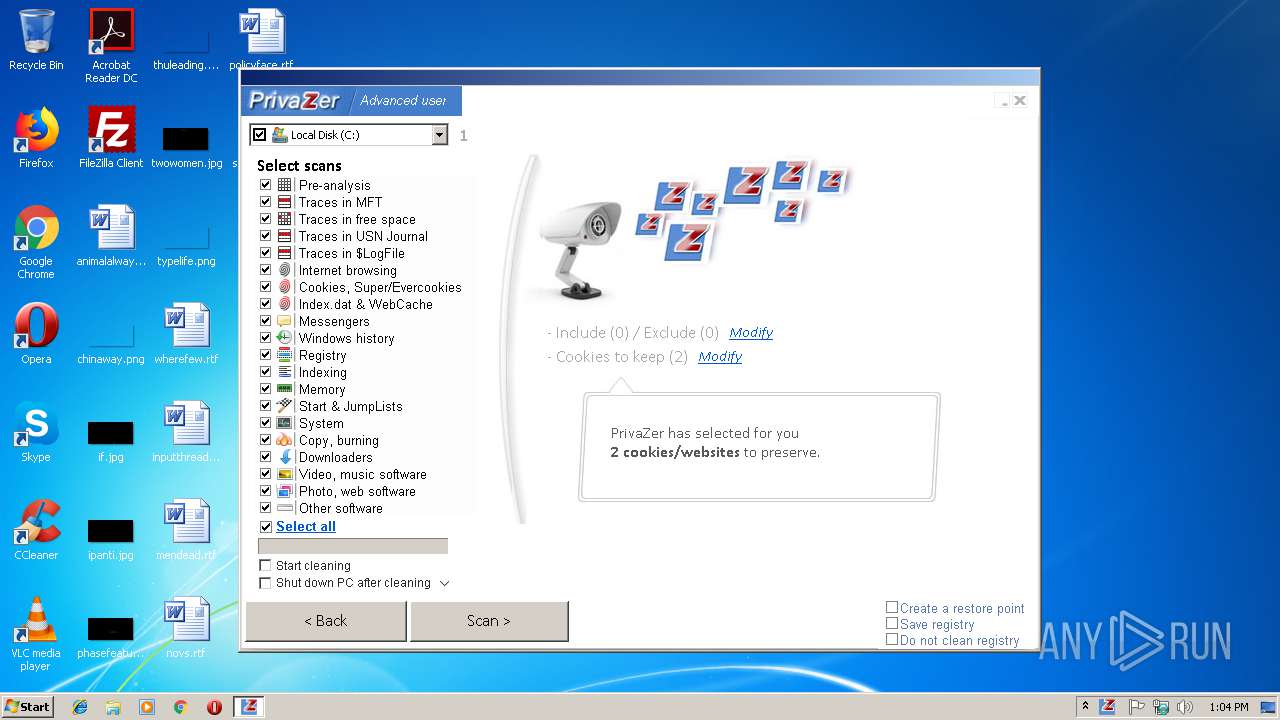
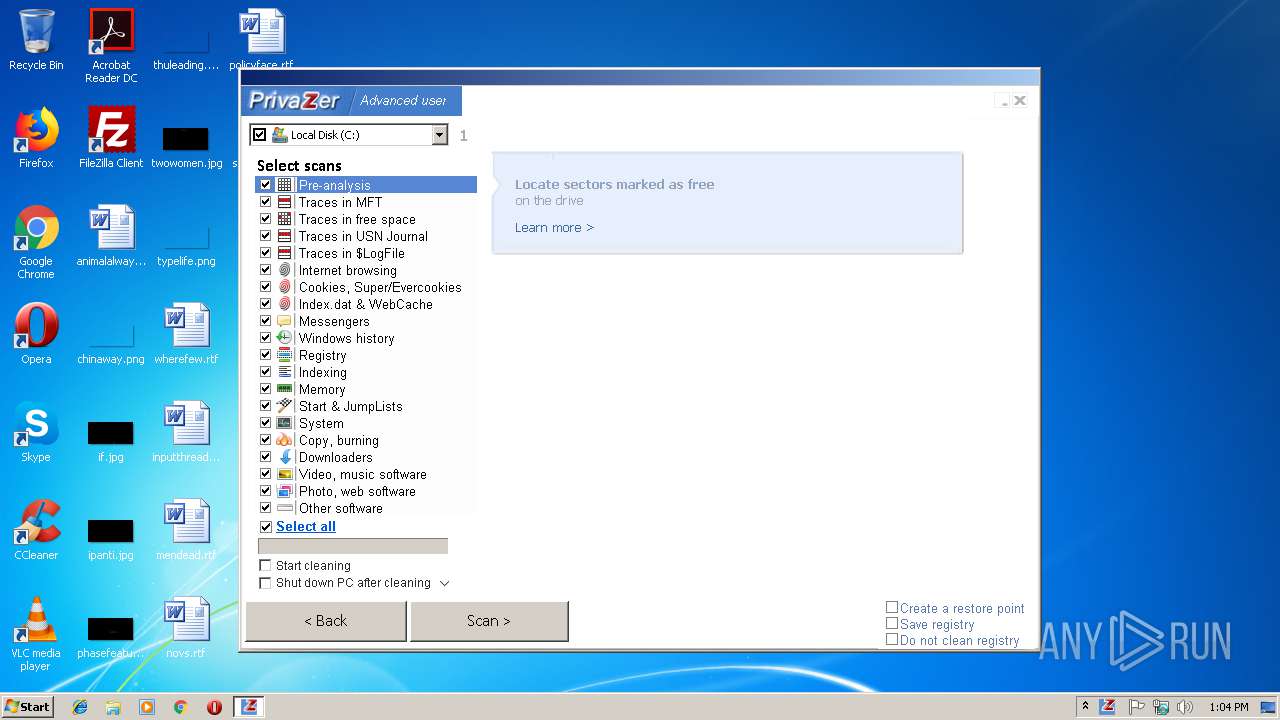
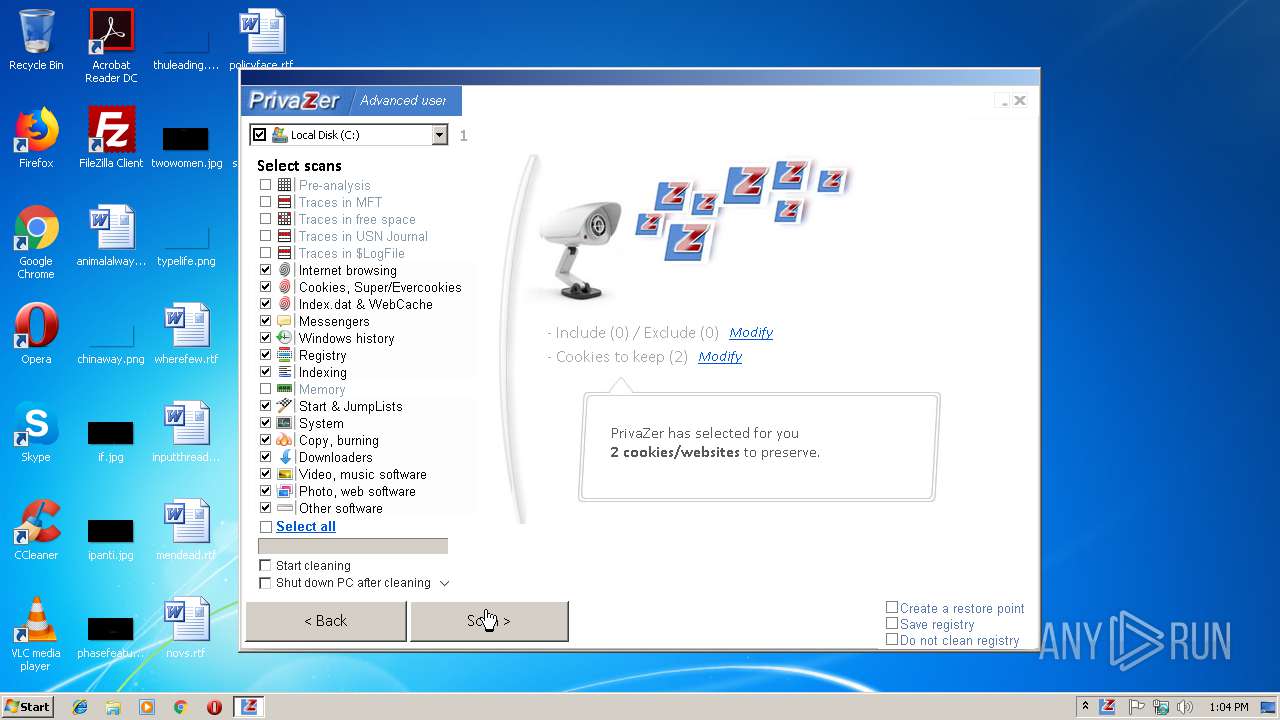
Reads the cookies of Mozilla Firefox
- privazer.exe (PID: 2592)
Reads the cookies of Google Chrome
- privazer.exe (PID: 2592)
Starts CMD.EXE for commands execution
- privazer.exe (PID: 2592)
Reads Internet Cache Settings
- privazer.exe (PID: 2592)
Writes to a desktop.ini file (may be used to cloak folders)
- privazer.exe (PID: 2592)
- cleanmgr.exe (PID: 3076)
Removes files from Windows directory
- privazer.exe (PID: 2592)
Creates files in the Windows directory
- privazer.exe (PID: 2592)
- SearchProtocolHost.exe (PID: 2284)
- TrustedInstaller.exe (PID: 3968)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3748)
Searches for installed software
- privazer.exe (PID: 2592)
INFO
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (80.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.4) |
| .exe | | | Win16/32 Executable Delphi generic (3.8) |
| .exe | | | Generic Win/DOS Executable (3.7) |
| .exe | | | DOS Executable Generic (3.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 6665216 |
| InitializedDataSize: | 11359744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x65945c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
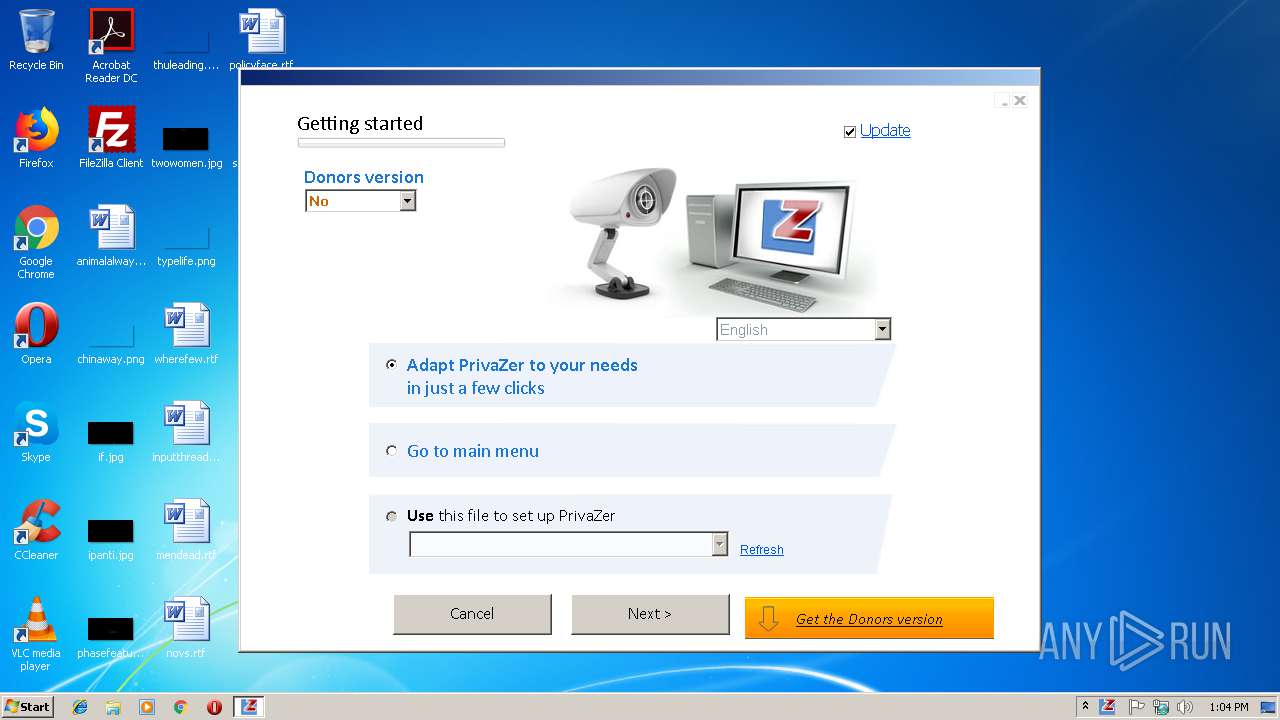
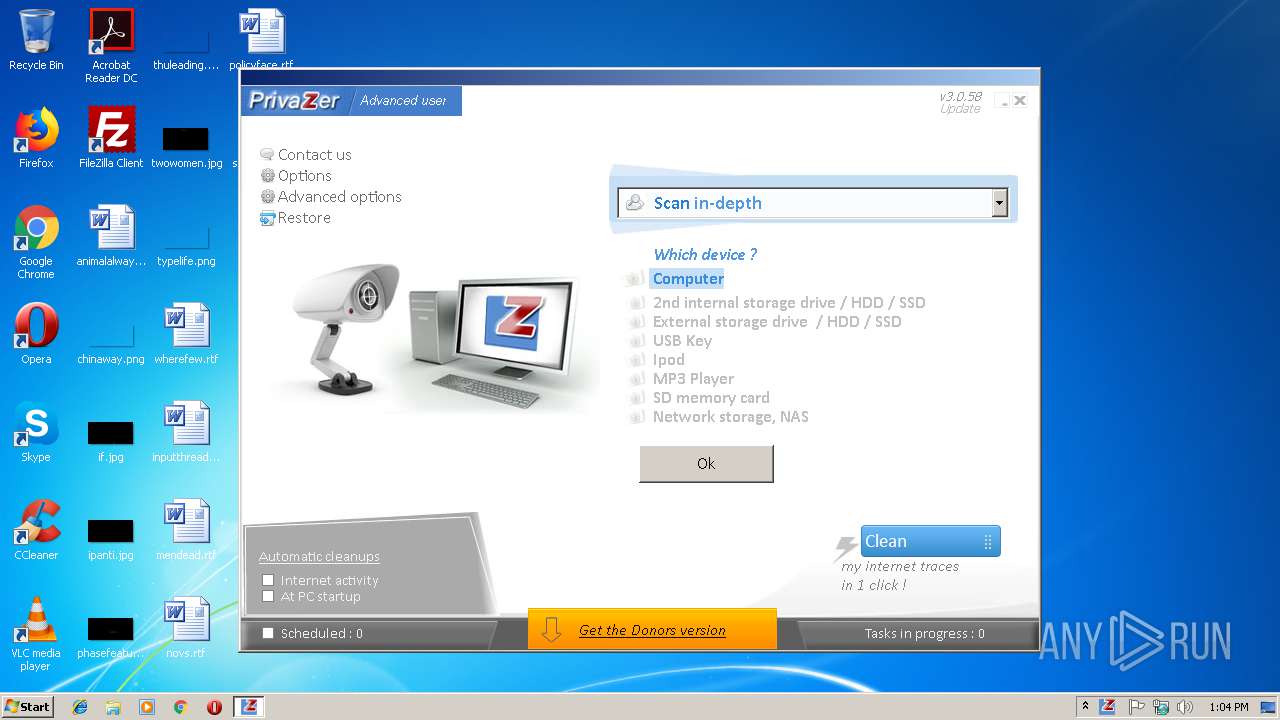
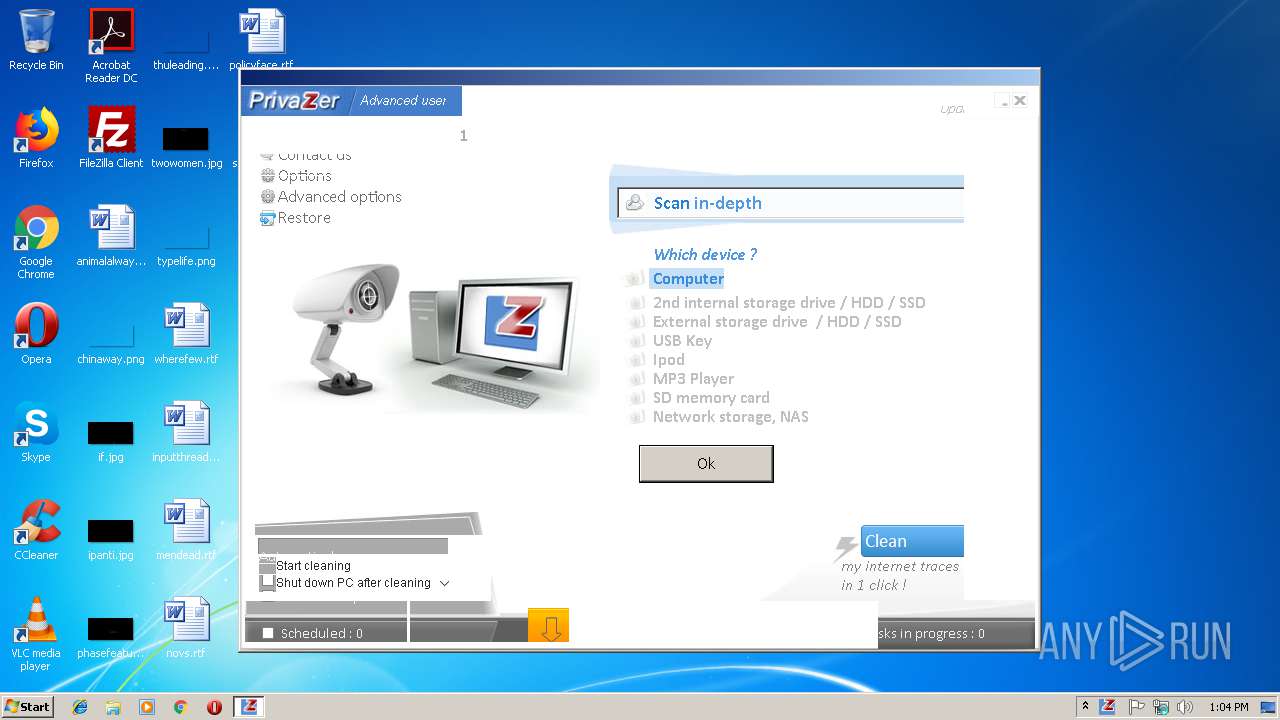
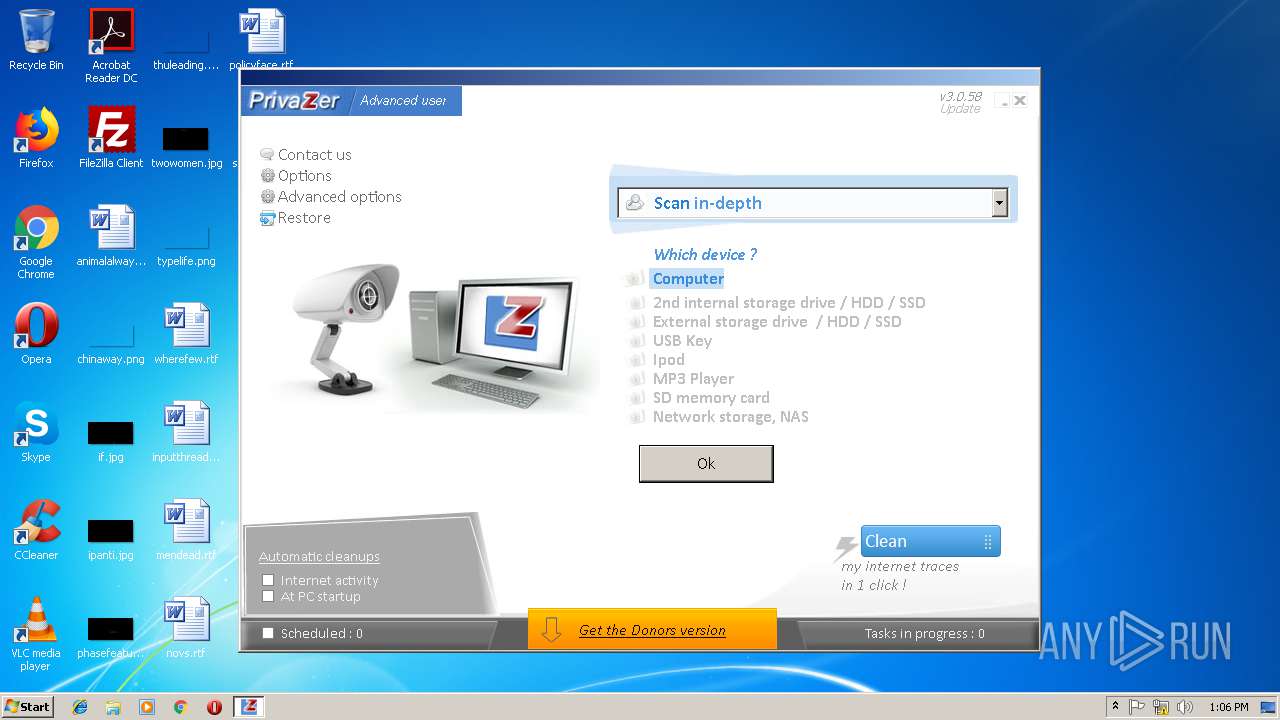
| FileVersionNumber: | 3.0.58.0 |
| ProductVersionNumber: | 3.0.58.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Goversoft LLC |
| FileDescription: | PrivaZer |
| FileVersion: | 3.0.58.0 |
| InternalName: | - |
| LegalCopyright: | Goversoft |
| LegalTrademarks: | PrivaZer |
| OriginalFileName: | privaZer |
| ProductName: | PrivaZer |
| ProductVersion: | 1.0.0.0 |
| Comments: | All rights reserved |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Goversoft LLC |
| FileDescription: | PrivaZer |
| FileVersion: | 3.0.58.0 |
| InternalName: | - |
| LegalCopyright: | Goversoft |
| LegalTrademarks: | PrivaZer |
| OriginalFilename: | privaZer |
| ProductName: | PrivaZer |
| ProductVersion: | 1.0.0.0 |
| Comments: | All rights reserved |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0065B2D4 | 0x0065B400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42451 |
DATA | 0x0065D000 | 0x0001780C | 0x00017A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.90296 |
BSS | 0x00675000 | 0x0000E68D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00684000 | 0x00004C82 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91054 |
.edata | 0x00689000 | 0x0000004F | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.858512 |
.tls | 0x0068A000 | 0x00000230 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0068B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.214733 |
.reloc | 0x0068C000 | 0x00056E7C | 0x00057000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.79521 |
.rsrc | 0x006E3000 | 0x00A61964 | 0x00A61A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.57137 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15146 | 1954 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.32366 | 1384 | UNKNOWN | French - France | RT_ICON |
3 | 3.91973 | 270376 | UNKNOWN | French - France | RT_ICON |
4 | 4.99287 | 9640 | UNKNOWN | French - France | RT_ICON |
5 | 5.32789 | 4264 | UNKNOWN | French - France | RT_ICON |
6 | 5.4762 | 1128 | UNKNOWN | French - France | RT_ICON |
7 | 3.08368 | 196 | UNKNOWN | English - United States | RT_STRING |
8 | 1.49923 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
9 | 1.45949 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
10 | 1.81975 | 748 | UNKNOWN | German - Germany | RT_CURSOR |
Imports
ADVAPI32.DLL |
SHFolder.dll |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
mpr.dll |
msi.dll |
ntdll.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
madTraceProcess | 1 | 0x0006264C |
Total processes
82
Monitored processes
32
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1516 | "C:\Windows\System32\cmd.exe" /A /C cacls "C:\System Volume Information\Chkdsk" /E /R admin | C:\Windows\System32\cmd.exe | — | privazer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2132 | C:\Users\admin\AppData\Local\Temp\63DB2E9F-A193-47F4-B319-E0E5EB597B5F\dismhost.exe {AB564220-060F-42B0-AED1-4C4B8FD8BAF6} | C:\Users\admin\AppData\Local\Temp\63DB2E9F-A193-47F4-B319-E0E5EB597B5F\dismhost.exe | cleanmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2252 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | "C:\Windows\System32\cmd.exe" /A /C wmic.exe process where caption="dllhost.exe" get Processid, commandline >"C:\Users\admin\AppData\Local\Temp\000\dllhost0_5383" | C:\Windows\System32\cmd.exe | — | privazer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe1_ Global\UsGthrCtrlFltPipeMssGthrPipe1 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\google\Chrome\User Data\Default\Local Storage\leveldb-viewer.exe" -r9 | C:\Users\admin\AppData\Local\google\Chrome\User Data\Default\Local Storage\leveldb-viewer.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2412 | cacls "C:\System Volume Information\Chkdsk" /E /R admin | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Windows\System32\cmd.exe" /A /C "C:\Users\admin\AppData\Local\google\Chrome\User Data\Default\Local Storage\leveldb-viewer.exe" -r9 | C:\Windows\System32\cmd.exe | — | privazer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\privazer.exe" C:\Users\admin\AppData\Local\Temp\privazer.exe | C:\Users\admin\AppData\Local\Temp\privazer.exe | privazer.exe | ||||||||||||
User: admin Company: Goversoft LLC Integrity Level: HIGH Description: PrivaZer Exit code: 0 Version: 3.0.58.0 Modules
| |||||||||||||||
Total events
9 578
Read events
6 611
Write events
2 217
Delete events
750
Modification events
| (PID) Process: | (3472) privazer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3472) privazer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2592) privazer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privazer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
36
Suspicious files
53
Text files
200
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2344 | leveldb-viewer.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\000002.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2344 | leveldb-viewer.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\priva_out_file.txt | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Local\google\Chrome\User Data\Default\Local Storage\priva_out_file.txt | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\favicons.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\default\about+home\idb\3312185054sbndi_pspte.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\default\about+newtab\idb\3312185054sbndi_pspte.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2592 | privazer.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1059394878bslnoicgkullipsFt2s%.sqlite-shm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2592 | privazer.exe | GET | 404 | 94.23.156.117:80 | http://privazer.com/new_version_3.0.058.txt | GB | html | 221 b | malicious |
2592 | privazer.exe | GET | 200 | 94.23.156.117:80 | http://privazer.com/hcheck_updates.php?country=DGIMDZEEBTCDCABGBOGOIWICEMDXFKACGNEMDTGHDIIWBP&discret=discret_1 | GB | text | 79 b | malicious |
2592 | privazer.exe | GET | 301 | 94.23.156.117:80 | http://www.privazer.com/hcheck_updates.php?country=DGIMDZEEBTCDCABGBOGOIWICEMDXFKACGNEMDTGHDIIWBP&discret=discret_1 | GB | html | 178 b | malicious |
2592 | privazer.exe | GET | 301 | 94.23.156.117:80 | http://www.privazer.com/new_version_3.0.058.txt | GB | html | 178 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | privazer.exe | 94.23.156.117:80 | www.privazer.com | OVH SAS | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.privazer.com |
| unknown |
privazer.com |
| unknown |
Threats
Process | Message |
|---|---|
cleanmgr.exe | PID=3076 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
cleanmgr.exe | PID=3076 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnecê |
cleanmgr.exe | PID=3076 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
cleanmgr.exe | PID=3076 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
cleanmgr.exe | PID=3076 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
cleanmgr.exe | PID=3076 Getting Provider OSServices - CDISMProviderStore::GetProvider |
cleanmgr.exe | PID=3076 Getting Provider OSServices - CDISMProviderStore::GetProvider |
cleanmgr.exe | PID=3076 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
cleanmgr.exe | PID=3076 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |
cleanmgr.exe | PID=3076 Failed to gain access to the log file (null). Logging has been disabled. (hr:0x80070003) - CDISMLogger::Initialize |