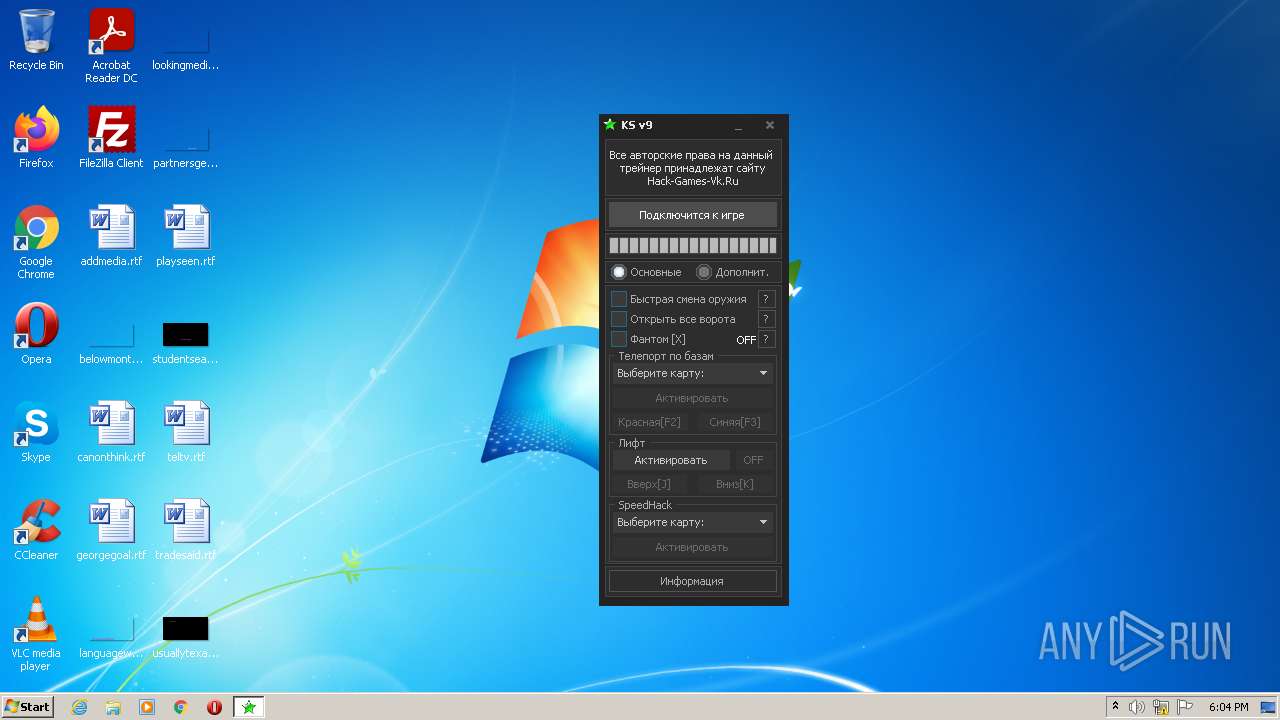
| File name: | Чит Контра Сити От SanCheDoz_а V9.exe |
| Full analysis: | https://app.any.run/tasks/521356d9-cc05-45f2-ad2b-7acdf7aad87a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 17:04:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B603049C25093C37CF19F216012C9F6D |
| SHA1: | 17B65F6F3A18E97E2F4A7568D96682786A6B3F0F |
| SHA256: | D5593AAB8FFEAE018AC0B3E0D518AB66FD7E742B080B146D5E95BD9B5AE793FE |
| SSDEEP: | 49152:SYkdJqPSvC9b7QS3WlK08JsZrH7agUW160+fDQgotIRCDboO9d3kTyTWk4wY/:SxdMPF4zusZvDg0+RoIgd30MY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Чит Контра Сити От SanCheDoz_а V9.exe (PID: 2952)
Reads the computer name
- Чит Контра Сити От SanCheDoz_а V9.exe (PID: 2952)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| Comments: | by VLAGISLAV |
|---|---|
| ProductVersion: | 9.0.0.0 |
| FileVersion: | 9.0.0.0 |
| CompanyName: | hack-games-vk.ru |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 9.0.0.0 |
| FileVersionNumber: | 9.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x3cd9bc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 612864 |
| CodeSize: | 3983360 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2016:04:25 11:46:31+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Apr-2016 09:46:31 |
| Detected languages: |
|
| CompanyName: | hack-games-vk.ru |
| FileVersion: | 9.0.0.0 |
| ProductVersion: | 9.0.0.0 |
| Comments: | by VLAGISLAV |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 25-Apr-2016 09:46:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003C8B54 | 0x003C8C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47211 |
.itext | 0x003CA000 | 0x00003A2C | 0x00003C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.12667 |
.data | 0x003CE000 | 0x000109B4 | 0x00010A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.25414 |
.bss | 0x003DF000 | 0x000066D0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x003E6000 | 0x0000411A | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.19269 |
.didata | 0x003EB000 | 0x000009A6 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11987 |
.edata | 0x003EC000 | 0x0000005E | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.10363 |
.tls | 0x003ED000 | 0x0000004C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x003EE000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.20692 |
.reloc | 0x003EF000 | 0x0004B08C | 0x0004B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71874 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86531 | 714 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.6633 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.92331 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
Kernel32.dll |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x00062904 |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Users\admin\AppData\Local\Temp\Чит Контра Сити От SanCheDoz_а V9.exe" | C:\Users\admin\AppData\Local\Temp\Чит Контра Сити От SanCheDoz_а V9.exe | Explorer.EXE | ||||||||||||
User: admin Company: hack-games-vk.ru Integrity Level: MEDIUM Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
Total events
850
Read events
850
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | Чит Контра Сити От SanCheDoz_а V9.exe | GET | 200 | 23.202.231.167:80 | http://kbzserves.tk/Cheat/KS/MainScript.php?s=1&v=9T&u=[C4BA-3647] | US | html | 391 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.202.231.167:80 | kbzserves.tk | Akamai Technologies, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kbzserves.tk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2952 | Чит Контра Сити От SanCheDoz_а V9.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |