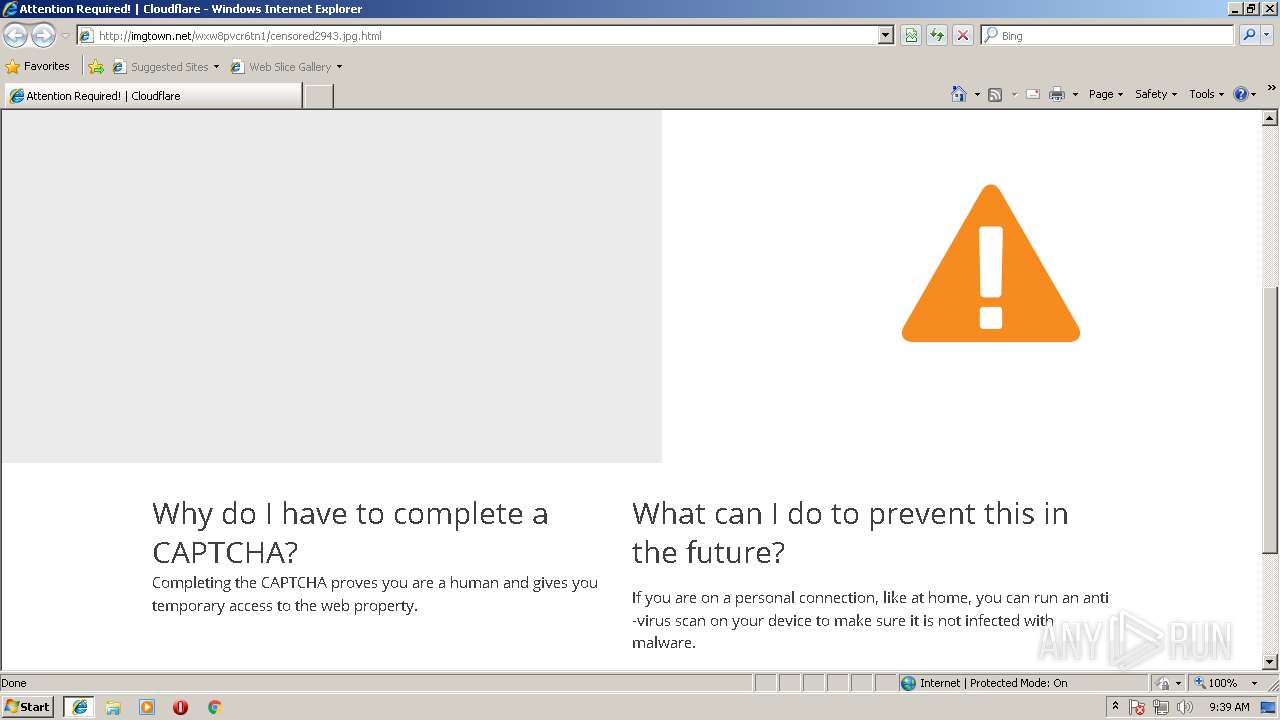
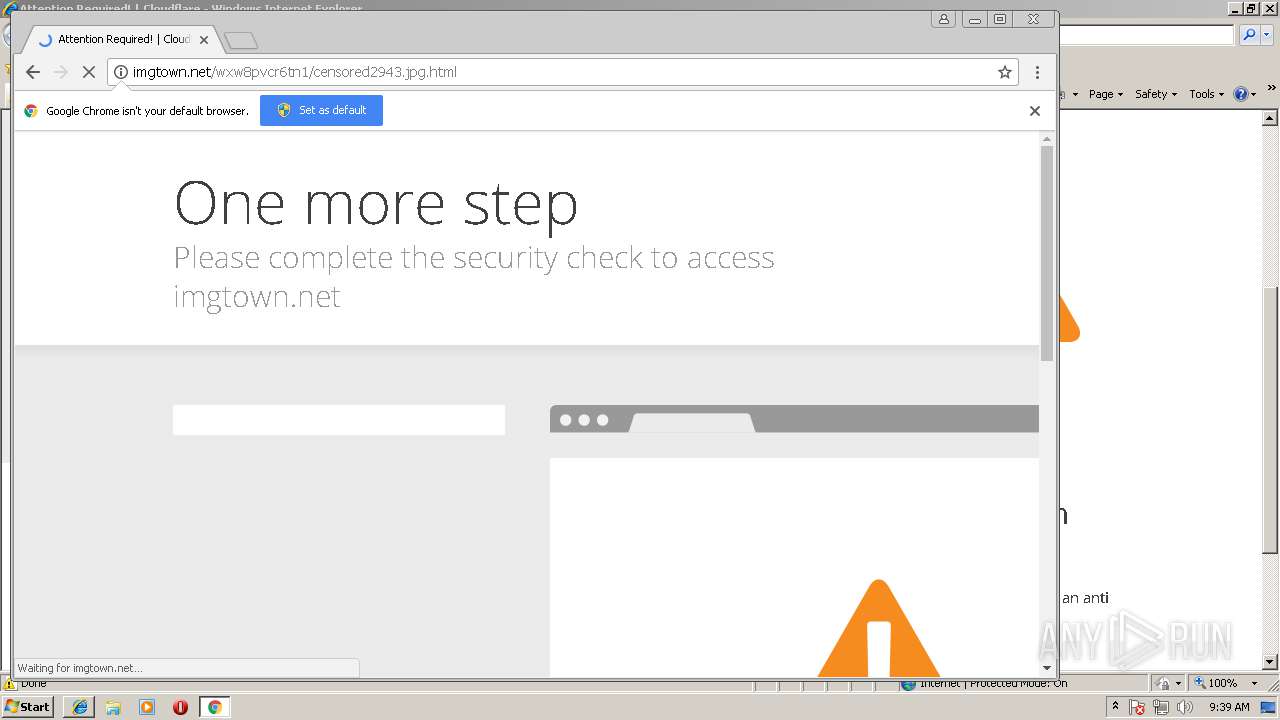
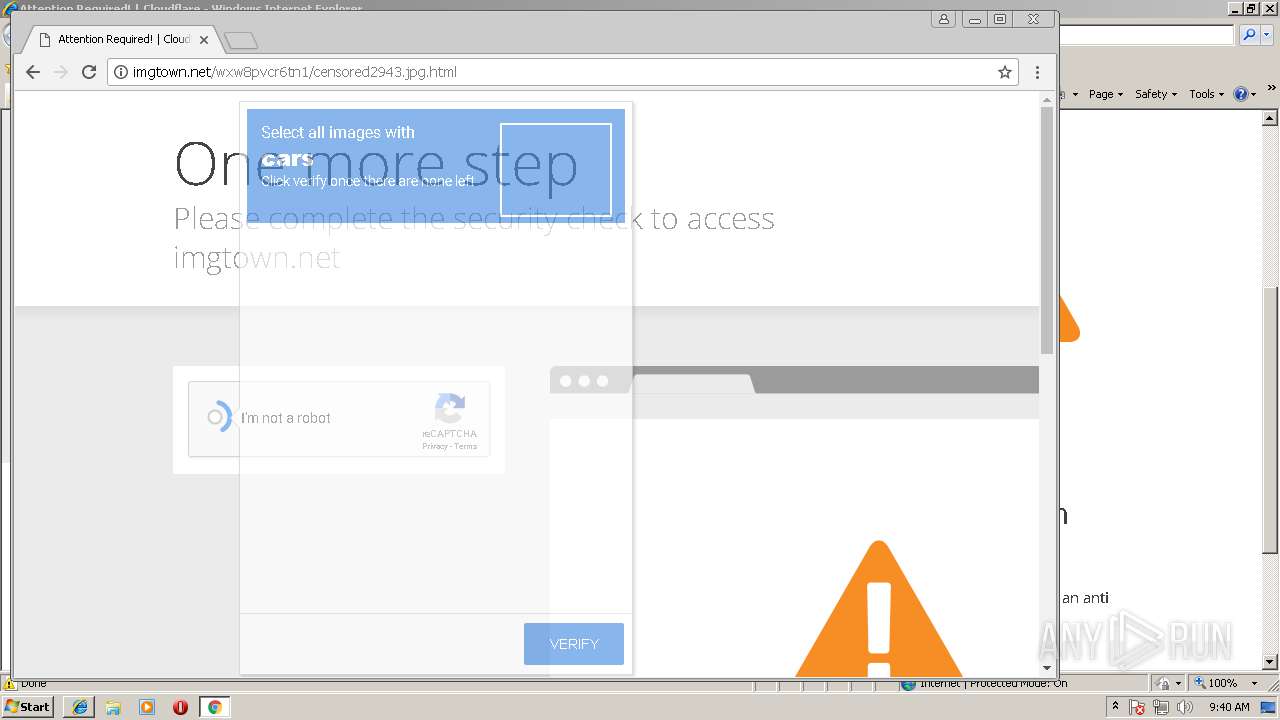
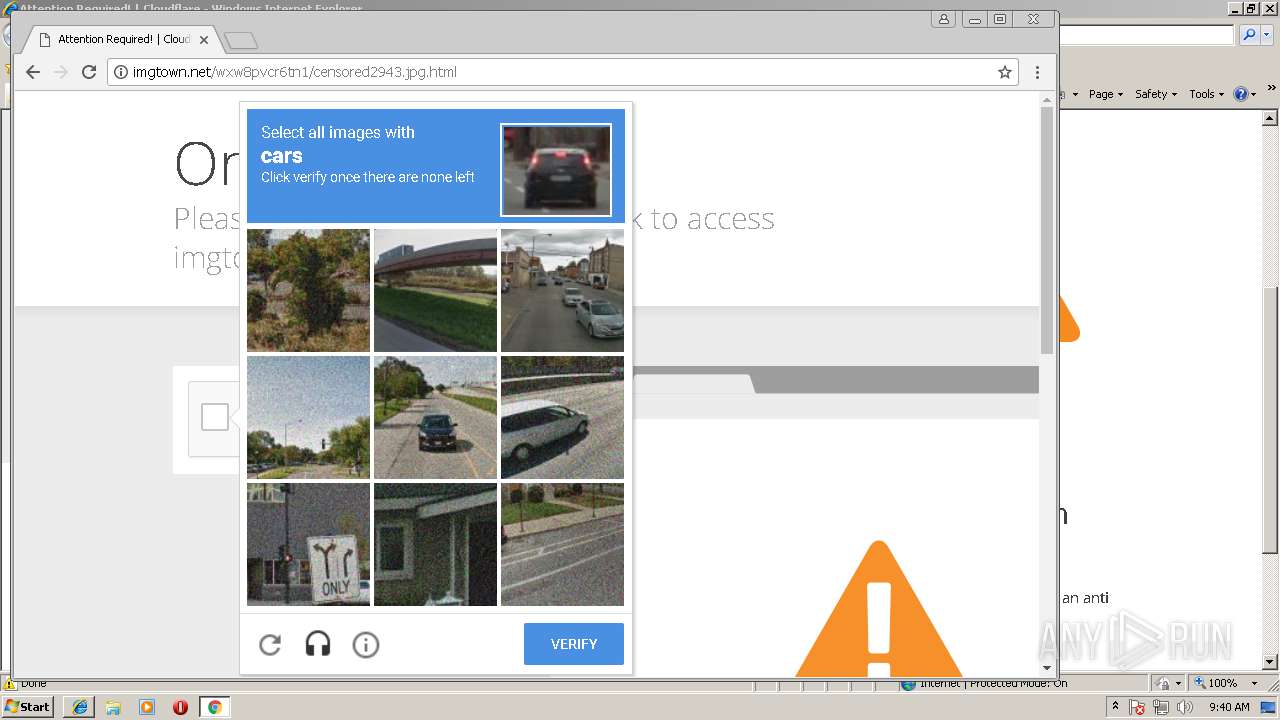
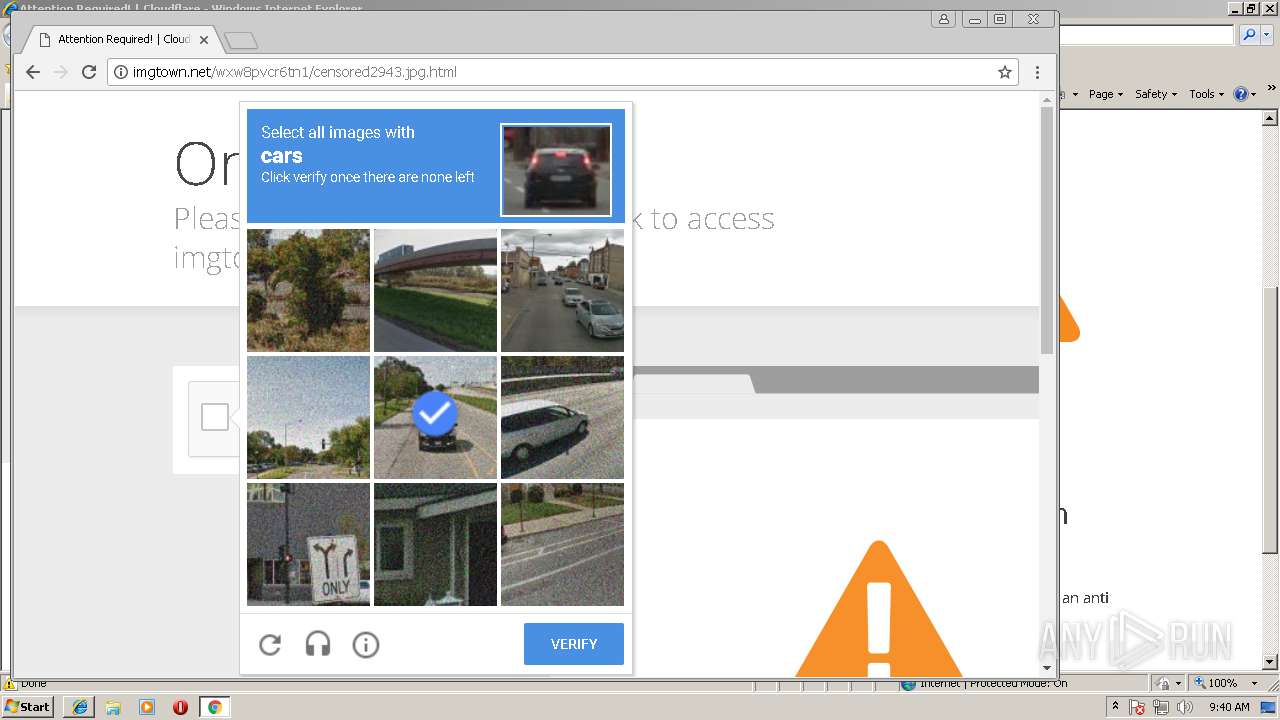
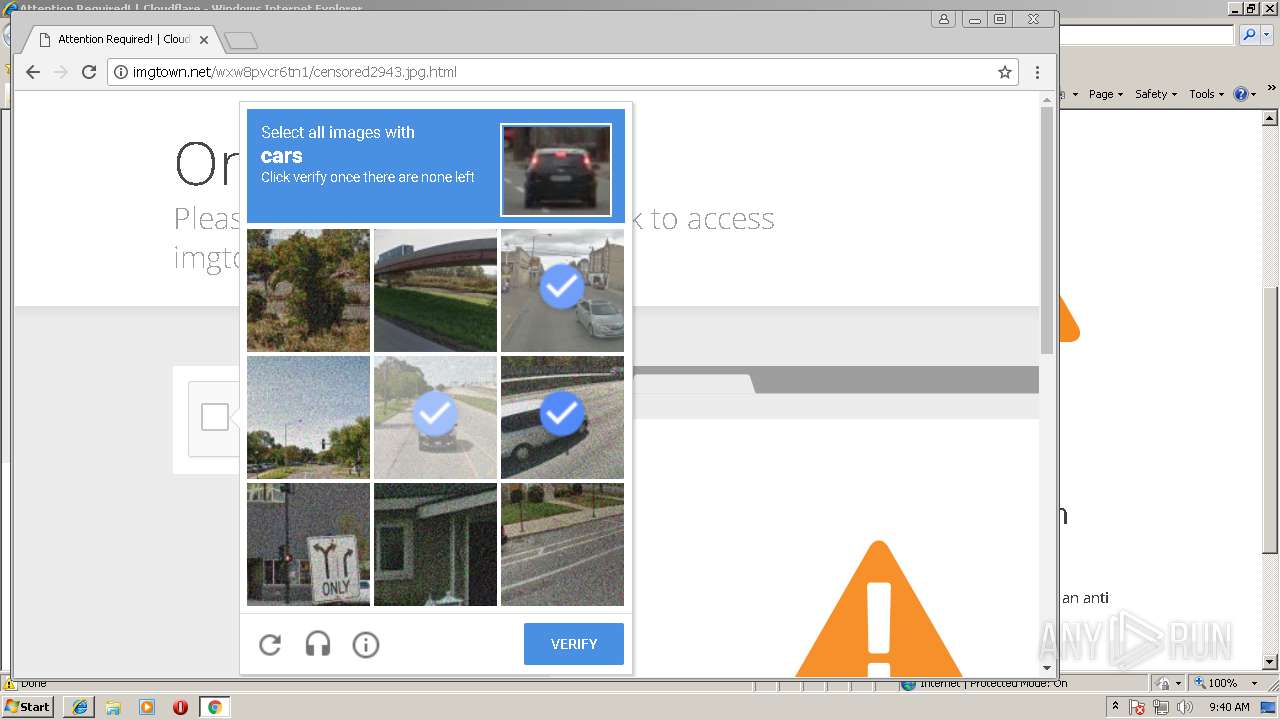
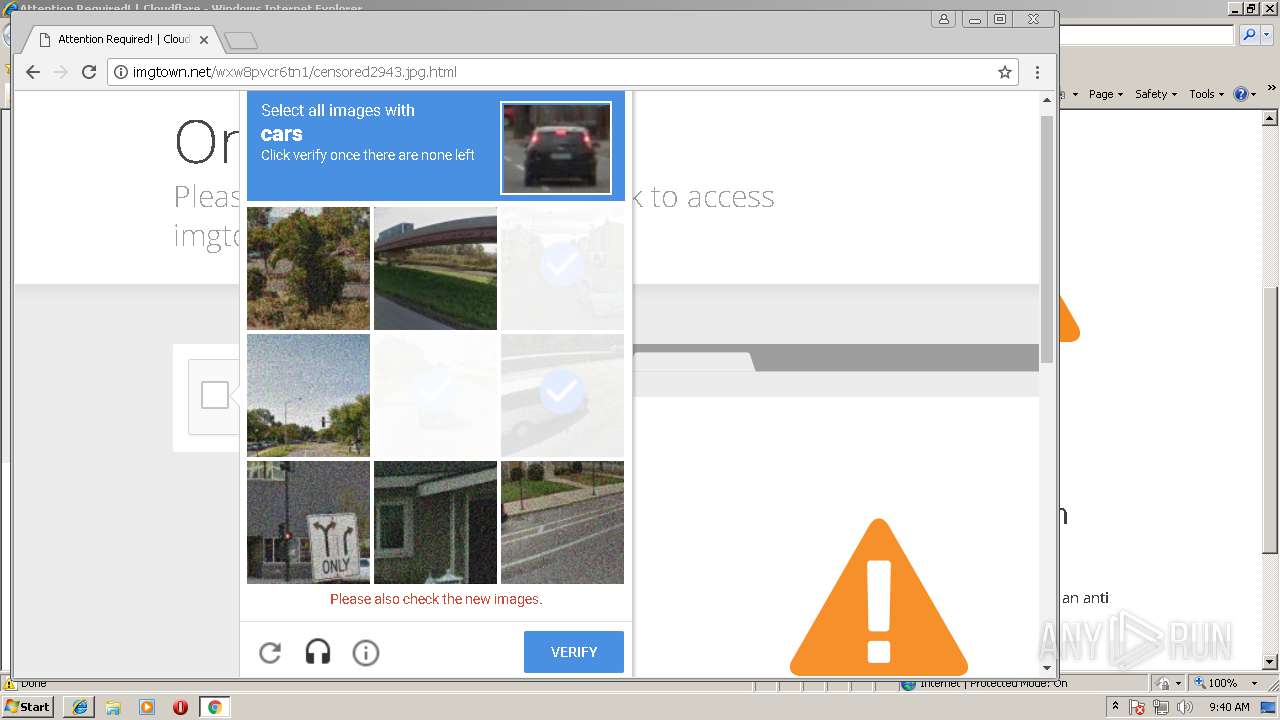
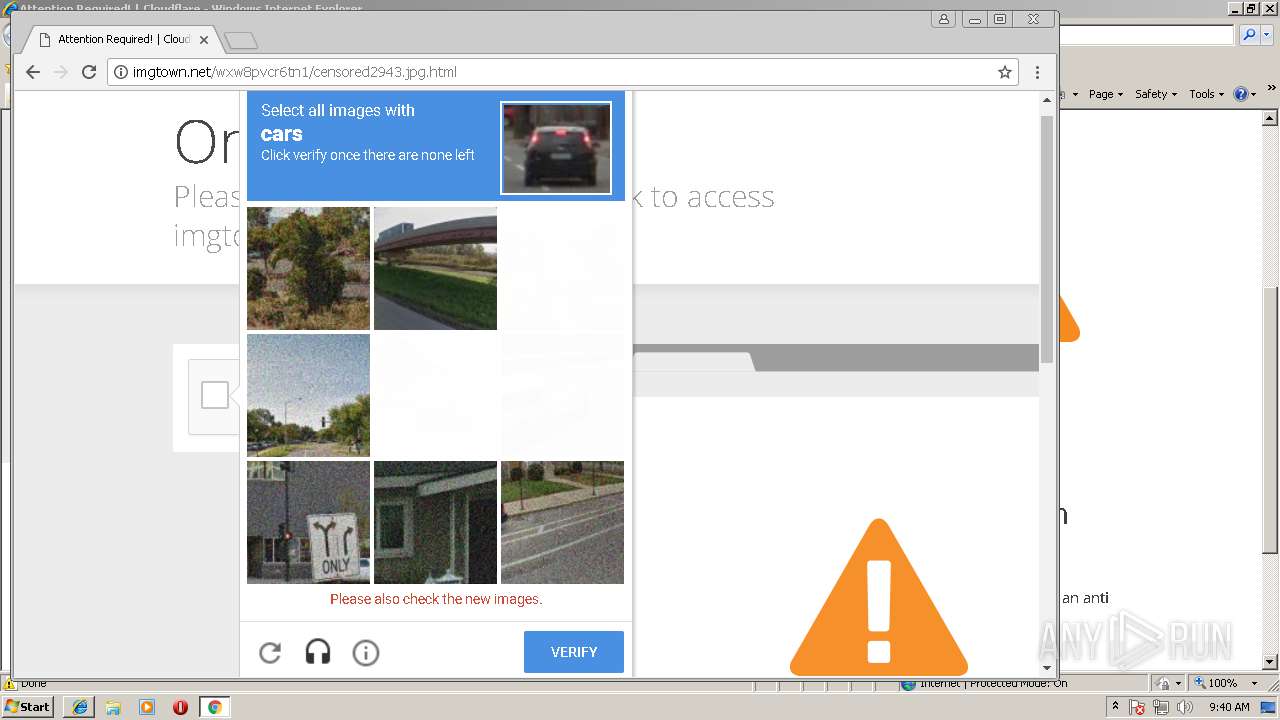
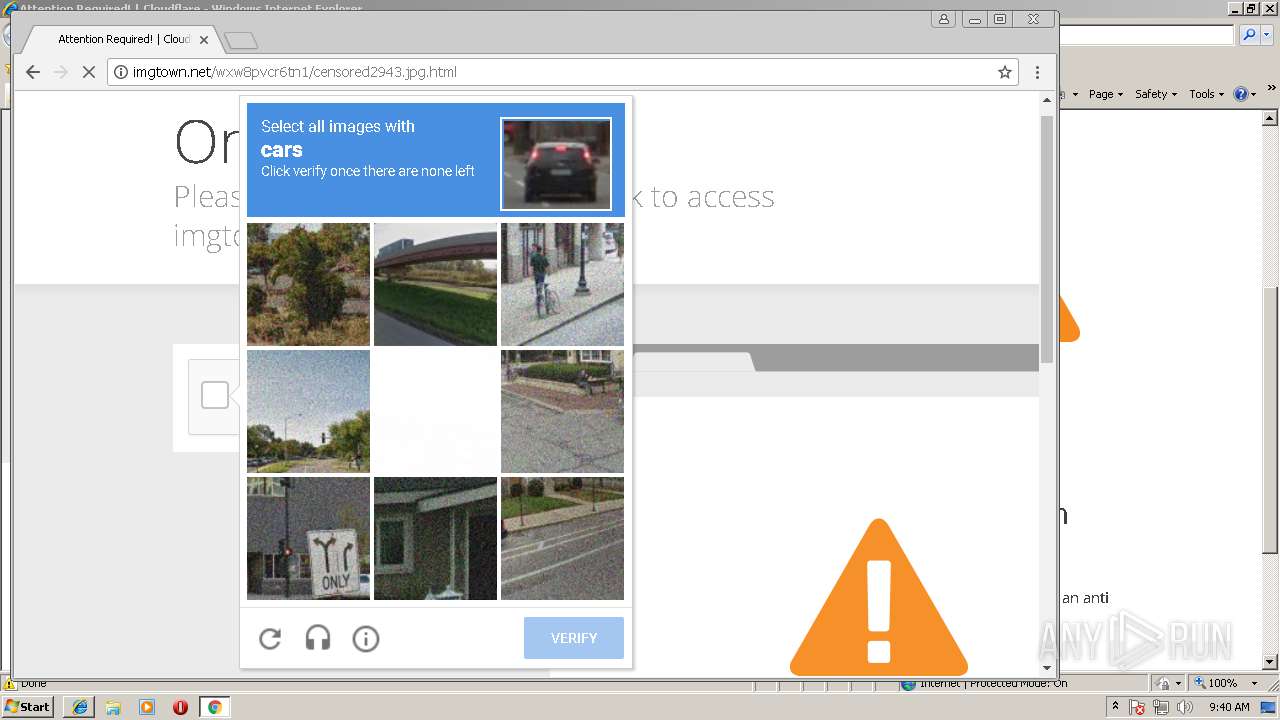
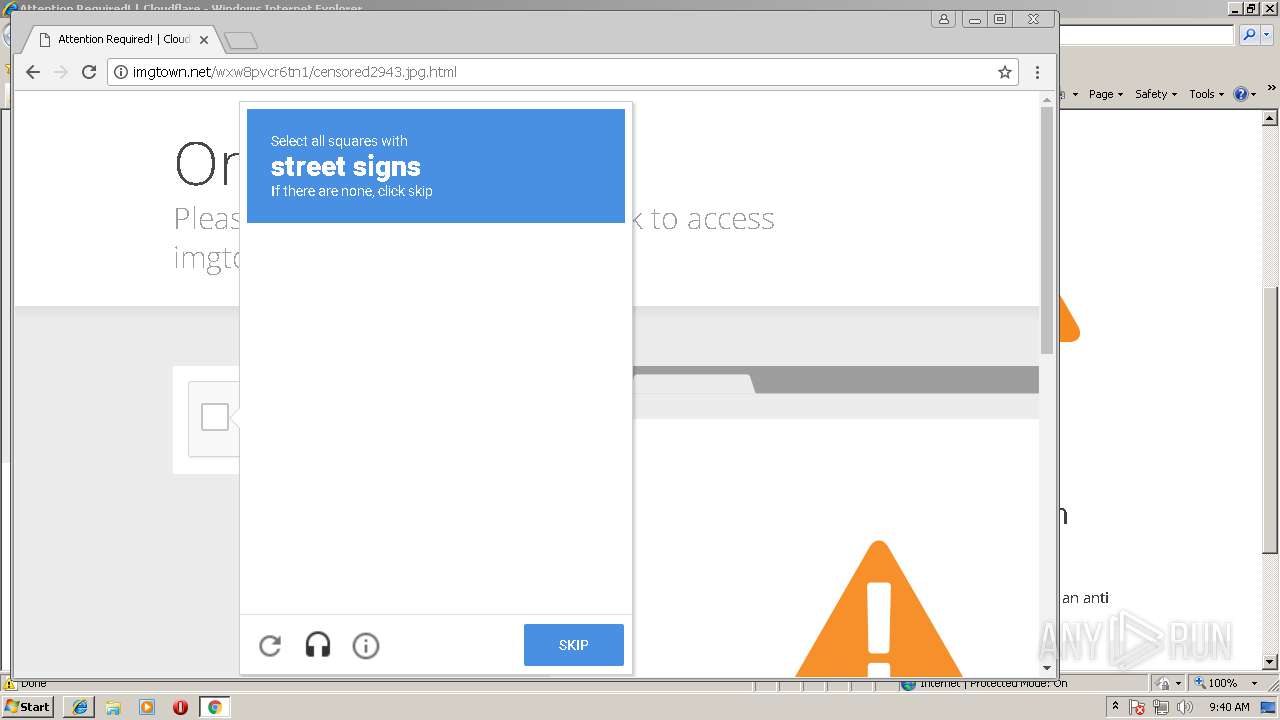
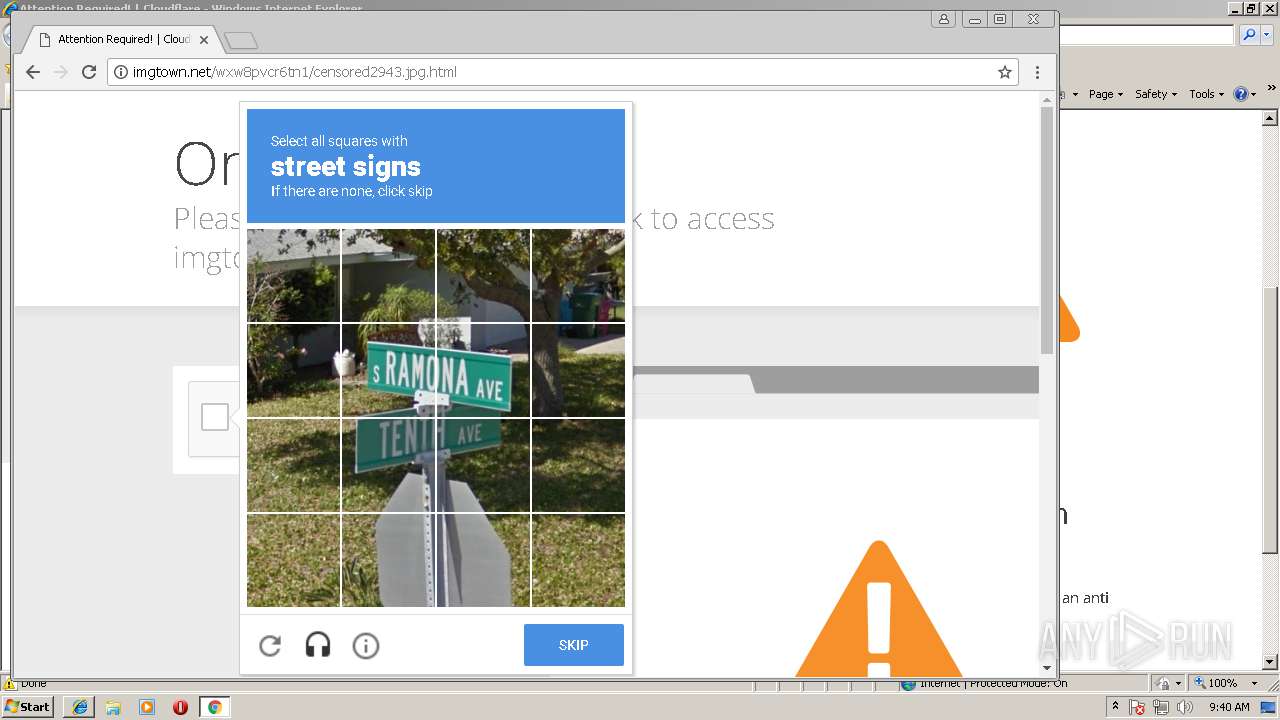
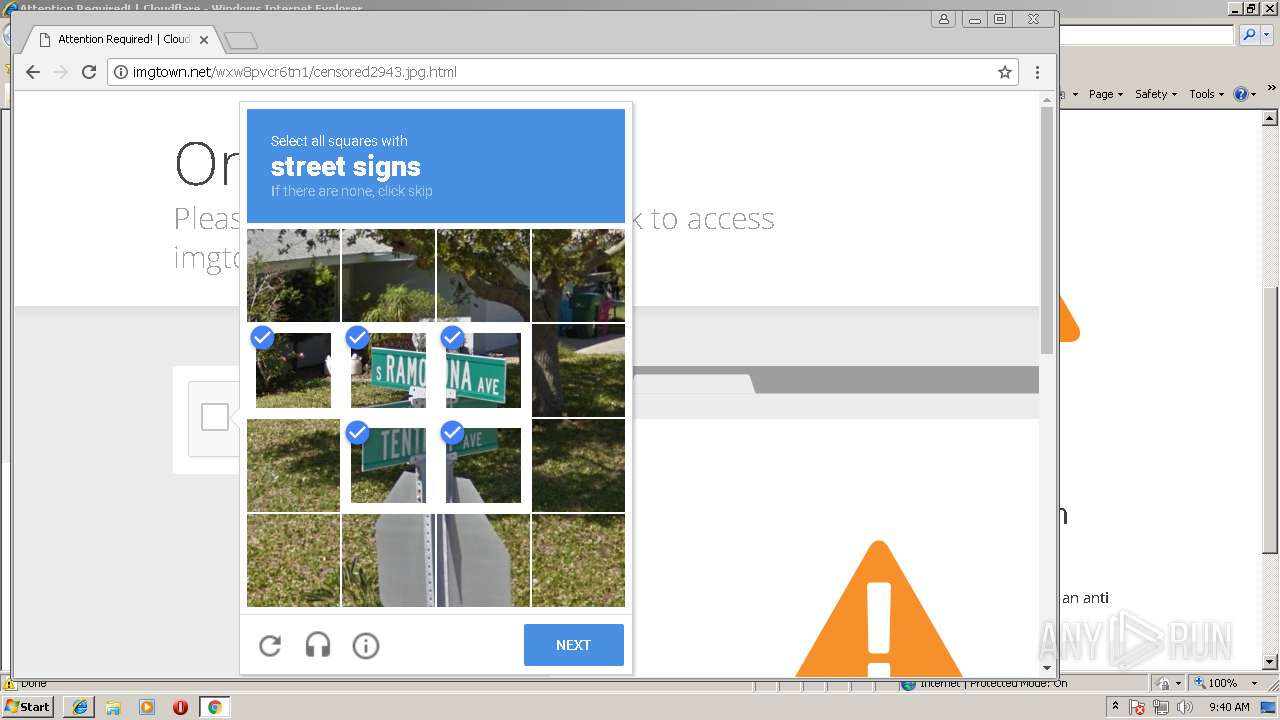
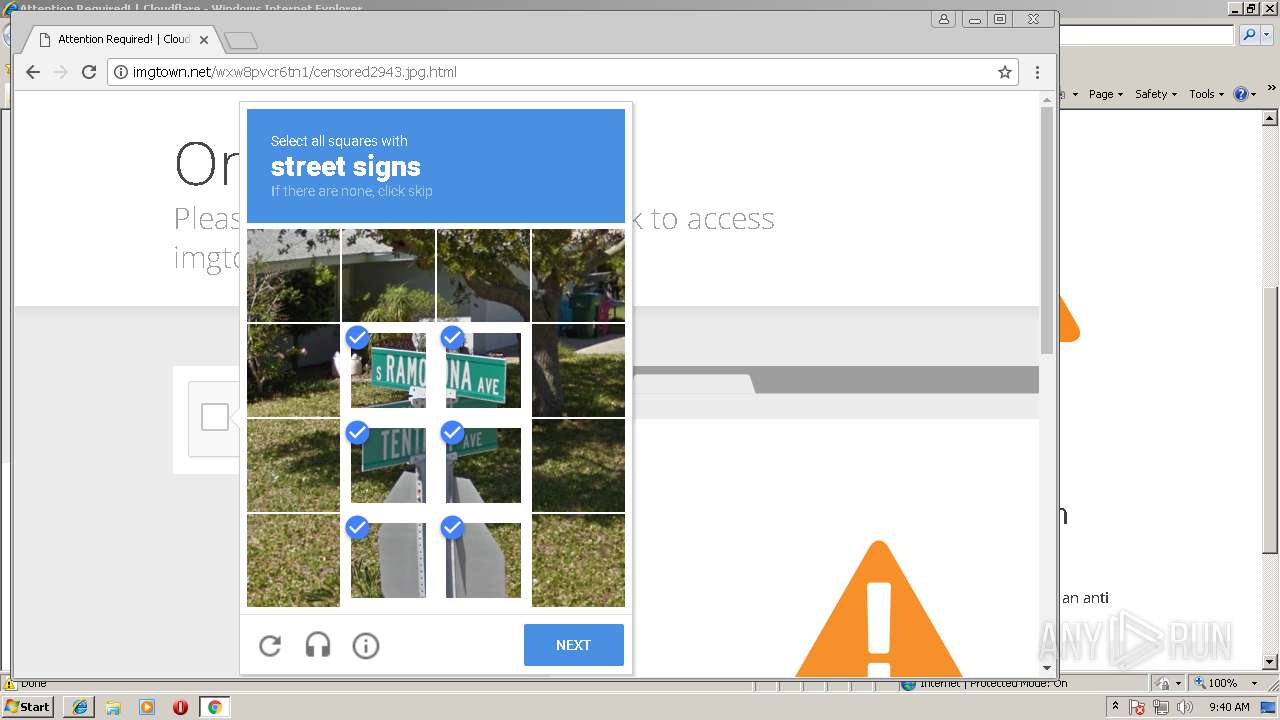
| URL: | http://imgtown.net/wxw8pvcr6tn1/censored2943.jpg.html |
| Full analysis: | https://app.any.run/tasks/5be43556-b016-4009-876f-6c8e413b2387 |
| Verdict: | No threats detected |
| Analysis date: | August 08, 2018, 08:39:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FDE4711F58DAFC864C16A467718D9273 |
| SHA1: | E35DA58281DB78172CB49710D3523AB5842D26E0 |
| SHA256: | D54B1896663F3D90550187E0B7C4BD6C2E2390E4A31A1591F1709C7F216151DE |
| SSDEEP: | 3:N1KX/scAxYAdPGAeBXgMC0:Cvscip/ehgB0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2192)
- chrome.exe (PID: 276)
Changes internet zones settings
- iexplore.exe (PID: 2192)
Creates files in the user directory
- iexplore.exe (PID: 3560)
Modifies the open verb of a shell class
- chrome.exe (PID: 276)
Dropped object may contain URL's
- iexplore.exe (PID: 3560)
- chrome.exe (PID: 276)
Reads Internet Cache Settings
- iexplore.exe (PID: 3560)
Reads internet explorer settings
- iexplore.exe (PID: 3560)
Reads settings of System Certificates
- chrome.exe (PID: 276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
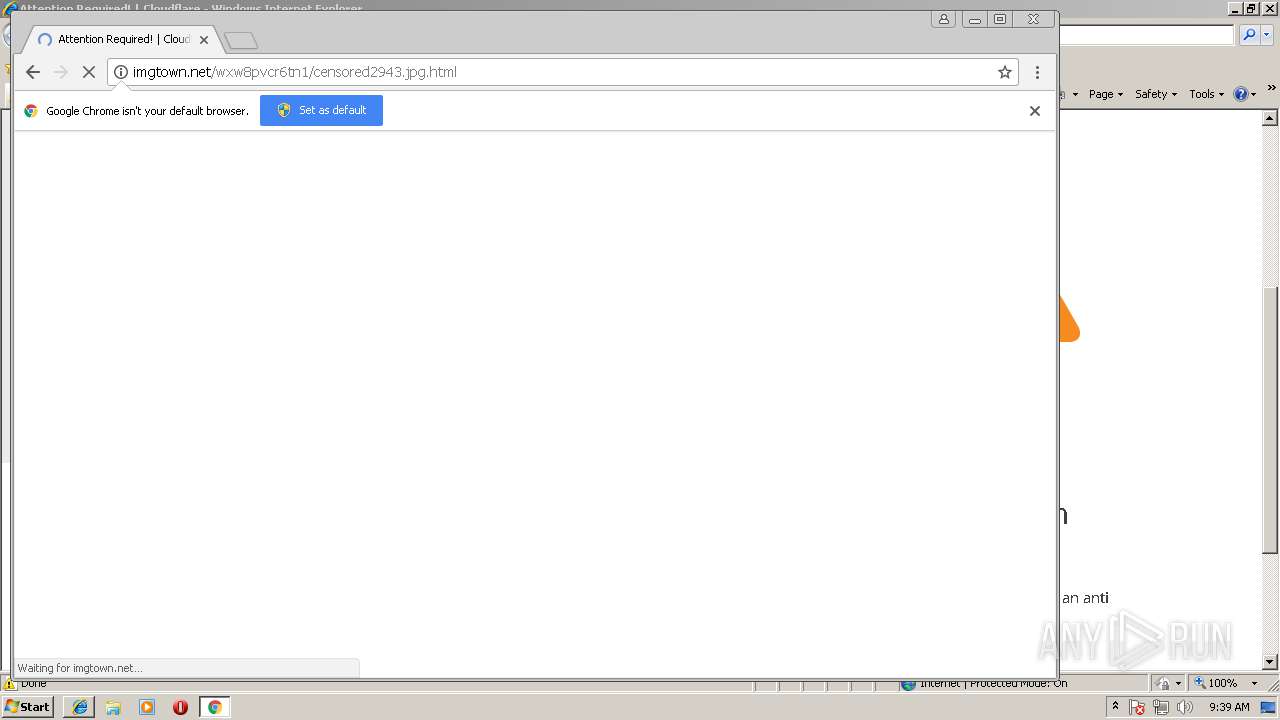
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1788,8245205071164355946,17133081488534888326,131072 --service-pipe-token=16BD1D4BCCA6AF58E83C33A8E2E2D795 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=16BD1D4BCCA6AF58E83C33A8E2E2D795 --renderer-client-id=4 --mojo-platform-channel-handle=1800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Internet Explorer\iexplore.exe" http://imgtown.net/wxw8pvcr6tn1/censored2943.jpg.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.91 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6d127d7c,0x6d127da4,0x6d127d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1788,8245205071164355946,17133081488534888326,131072 --service-pipe-token=517944C5A1B4E5FF392320512E6963B1 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=517944C5A1B4E5FF392320512E6963B1 --renderer-client-id=5 --mojo-platform-channel-handle=3348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1788,8245205071164355946,17133081488534888326,131072 --service-pipe-token=B5FECC04DA66D28A96289C2FCFC19981 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=B5FECC04DA66D28A96289C2FCFC19981 --renderer-client-id=2 --mojo-platform-channel-handle=1284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4012 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 3560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2192 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
565
Read events
418
Write events
138
Delete events
9
Modification events
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {90D395C5-9AE6-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2192) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207080003000800080027001F001800 | |||
Executable files
0
Suspicious files
37
Text files
53
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DSILEDM7\opensans-700[1].eot | eot | |
MD5:— | SHA256:— | |||
| 276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000008.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XBSSZHSR\cf.challenge[1].js | text | |
MD5:— | SHA256:— | |||
| 3560 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@imgtown[1].txt | text | |
MD5:— | SHA256:— | |||
| 3560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DSILEDM7\opensans-300i[1].eot | eot | |
MD5:— | SHA256:— | |||
| 2192 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[2].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 276 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ee802c9-b882-4756-b97d-d3996a15629f.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\opensans-600[1].eot | eot | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
33
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
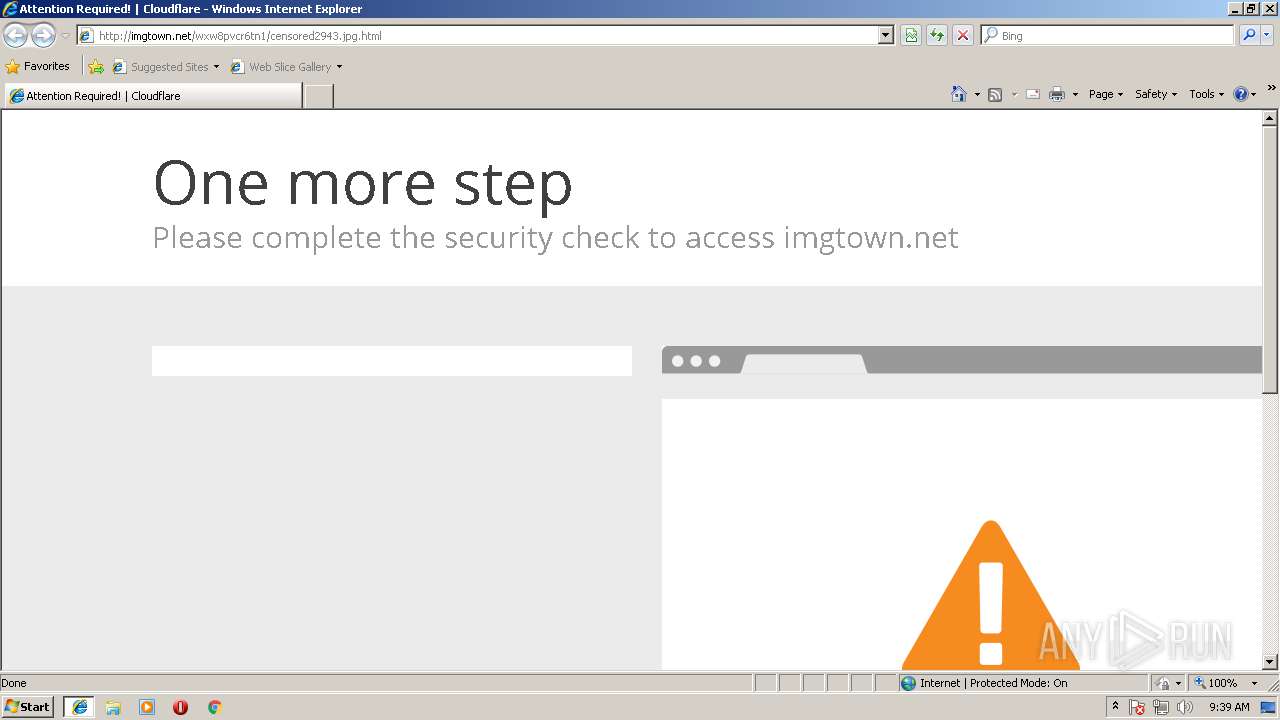
3560 | iexplore.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | suspicious |
3560 | iexplore.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/scripts/cf.challenge.js | US | text | 3.17 Kb | suspicious |
3560 | iexplore.exe | GET | 403 | 104.28.25.28:80 | http://imgtown.net/wxw8pvcr6tn1/censored2943.jpg.html | US | html | 1.92 Kb | suspicious |
3560 | iexplore.exe | GET | 302 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/l/chk_captcha?id=4470ac4886429cde | US | html | 159 b | suspicious |
3560 | iexplore.exe | GET | 403 | 104.28.25.28:80 | http://imgtown.net/wxw8pvcr6tn1/censored2943.jpg.html | US | html | 1.91 Kb | suspicious |
276 | chrome.exe | GET | 403 | 104.28.25.28:80 | http://imgtown.net/wxw8pvcr6tn1/censored2943.jpg.html | US | html | 2.03 Kb | suspicious |
276 | chrome.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/scripts/zepto.min.js | US | text | 9.12 Kb | suspicious |
276 | chrome.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | suspicious |
276 | chrome.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/scripts/cf.challenge.js | US | text | 3.17 Kb | suspicious |
276 | chrome.exe | GET | 200 | 104.28.25.28:80 | http://imgtown.net/cdn-cgi/scripts/cf.common.js | US | text | 1.94 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | iexplore.exe | 104.28.25.28:80 | imgtown.net | Cloudflare Inc | US | shared |
2192 | iexplore.exe | 204.79.197.229:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3560 | iexplore.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
276 | chrome.exe | 172.217.20.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3560 | iexplore.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
276 | chrome.exe | 172.217.20.195:443 | www.google.de | Google Inc. | US | whitelisted |
276 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
276 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
276 | chrome.exe | 104.28.25.28:80 | imgtown.net | Cloudflare Inc | US | shared |
276 | chrome.exe | 172.217.20.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
imgtown.net |
| suspicious |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.de |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.cloudflare.com |
| whitelisted |