| File name: | Oxygen Virus.exe |
| Full analysis: | https://app.any.run/tasks/a627ddd3-dd00-4b13-a7ec-4ea6082a1e44 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 17:54:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 4B5CDBF3F04D76C07A1B4436430A51C3 |
| SHA1: | 8AC95AF8A700F7436A87B7A97DF24FC17F406B31 |
| SHA256: | D53581041CF4C5C6BB99D5F0BFA352ABC42F47CB54689D982B79CF25129C4982 |
| SSDEEP: | 6144:TE+9PPJwWcDaKGsbSo0Af6ltI2VwxiTiIPI30fWpb6GTu:TEMPJPcDaKd10Af6ltIKwxiTi/30fM6G |
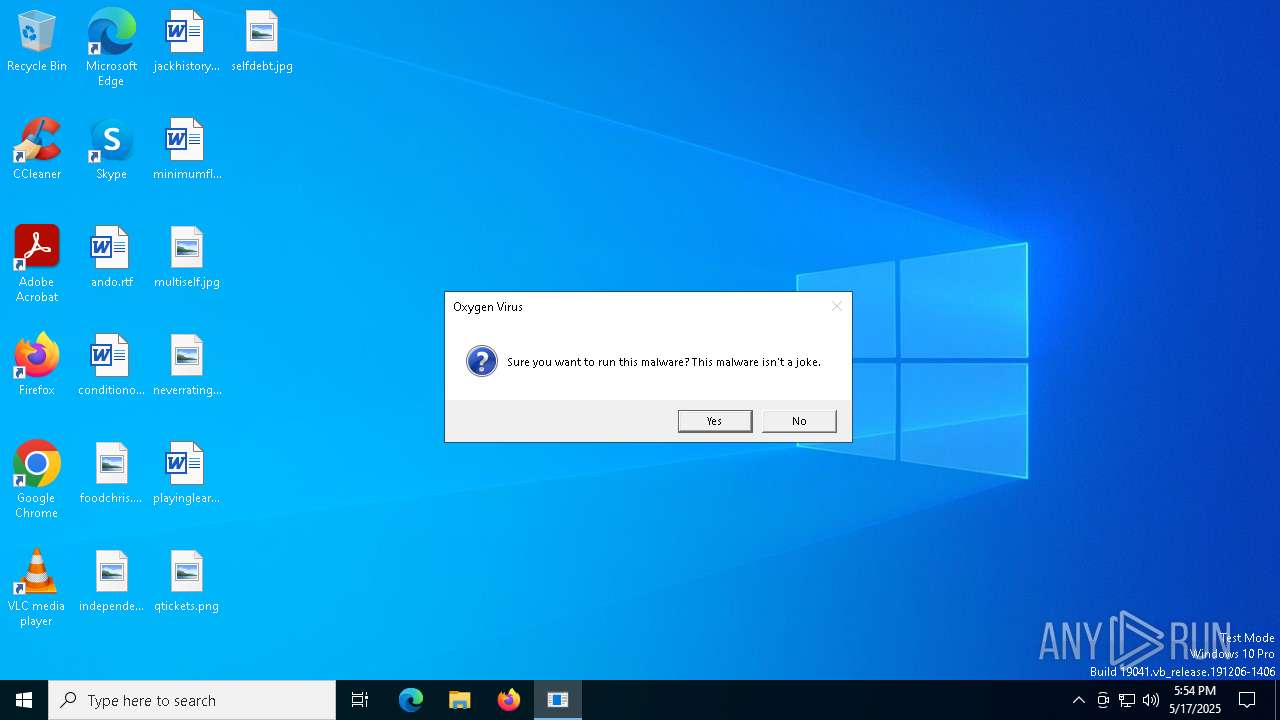
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 4652)
Disables task manager
- Oxygen Virus.exe (PID: 2616)
Disables the Command Prompt (cmd)
- Oxygen Virus.exe (PID: 2616)
SUSPICIOUS
Executable content was dropped or overwritten
- Oxygen Virus.exe (PID: 7012)
Reads the date of Windows installation
- Oxygen Virus.exe (PID: 7012)
- StartMenuExperienceHost.exe (PID: 4608)
Reads security settings of Internet Explorer
- Oxygen Virus.exe (PID: 7012)
- StartMenuExperienceHost.exe (PID: 4608)
Starts itself from another location
- Oxygen Virus.exe (PID: 7012)
Starts CMD.EXE for commands execution
- Oxygen Virus.exe (PID: 2616)
INFO
Checks supported languages
- Oxygen Virus.exe (PID: 7012)
- Oxygen Virus.exe (PID: 2616)
- TextInputHost.exe (PID: 3140)
- StartMenuExperienceHost.exe (PID: 4608)
- SearchApp.exe (PID: 6012)
Process checks computer location settings
- Oxygen Virus.exe (PID: 7012)
- StartMenuExperienceHost.exe (PID: 4608)
- SearchApp.exe (PID: 6012)
Reads the computer name
- Oxygen Virus.exe (PID: 7012)
- StartMenuExperienceHost.exe (PID: 4608)
- TextInputHost.exe (PID: 3140)
- SearchApp.exe (PID: 6012)
- Oxygen Virus.exe (PID: 2616)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 6012)
Checks proxy server information
- SearchApp.exe (PID: 6012)
Reads the software policy settings
- SearchApp.exe (PID: 6012)
Reads Environment values
- SearchApp.exe (PID: 6012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:17 17:53:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 158720 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9820 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
151
Monitored processes
13
Malicious processes
2
Suspicious processes
0
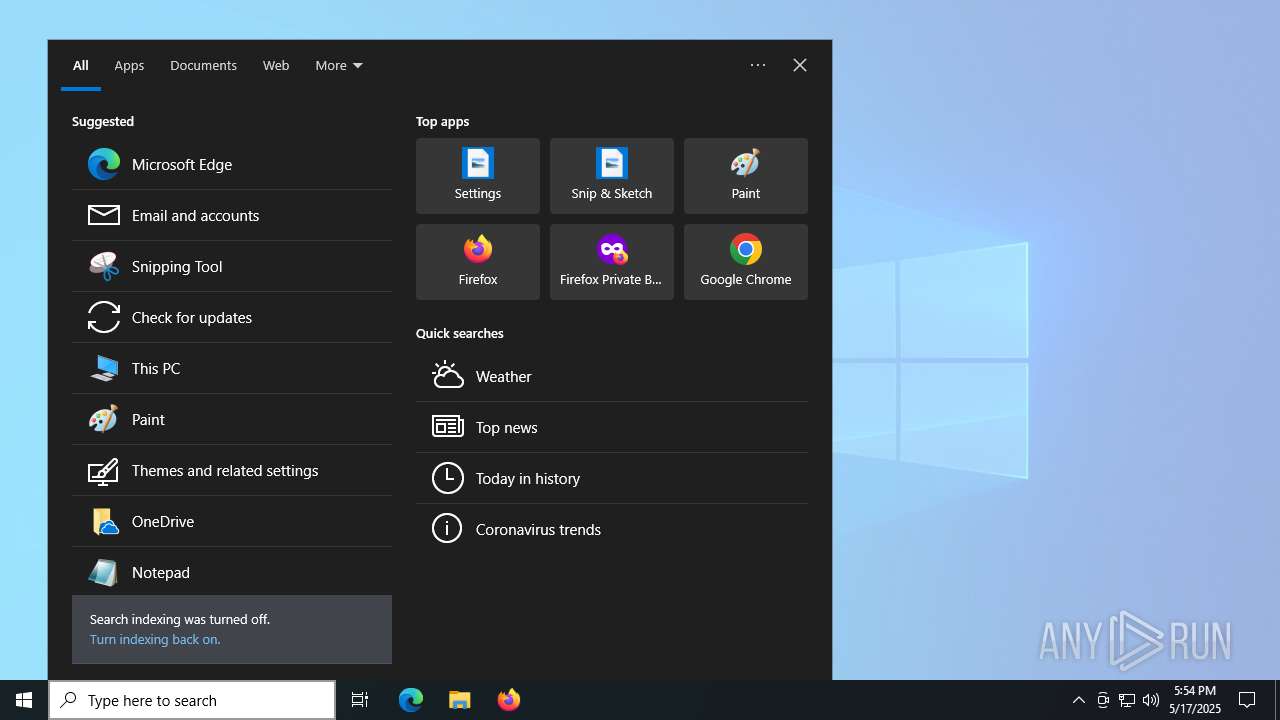
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | schtasks /Create /F /RL HIGHEST /SC ONLOGON /TN "" /TR "\"C:\WINDOWS\system32\Oxygen Virus.exe\" --autorun" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\WINDOWS\system32\Oxygen Virus.exe" --moved | C:\Windows\System32\Oxygen Virus.exe | — | Oxygen Virus.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3140 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\AppData\Local\Temp\Oxygen Virus.exe" | C:\Users\admin\AppData\Local\Temp\Oxygen Virus.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4444 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4608 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4652 | C:\WINDOWS\system32\cmd.exe /c schtasks /Create /F /RL HIGHEST /SC ONLOGON /TN "" /TR "\"C:\WINDOWS\system32\Oxygen Virus.exe\" --autorun" | C:\Windows\System32\cmd.exe | Oxygen Virus.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Oxygen Virus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6012 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 109
Read events
9 025
Write events
82
Delete events
2
Modification events
| (PID) Process: | (4608) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{daf1f2dd-bfc1-d6c3-0cbd-21e7d2687eb5}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 01000000B8CE5BC454C7DB01 | |||
| (PID) Process: | (4608) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (4608) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_AppUsageData |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (4608) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_TargetedContentTiles |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | \REGISTRY\A\{03c206d3-b9d5-f68b-cdb7-d003ccd909a7}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 00007308B4C454C7DB01 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | \REGISTRY\A\{03c206d3-b9d5-f68b-cdb7-d003ccd909a7}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPETEXT |
Value: 00007308B4C454C7DB01 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | \REGISTRY\A\{03c206d3-b9d5-f68b-cdb7-d003ccd909a7}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 00007308B4C454C7DB01 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | \REGISTRY\A\{03c206d3-b9d5-f68b-cdb7-d003ccd909a7}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 4E006F006E00650000007308B4C454C7DB01 | |||
| (PID) Process: | (6012) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | delete value | Name: | CachedFeatureString |
Value: | |||
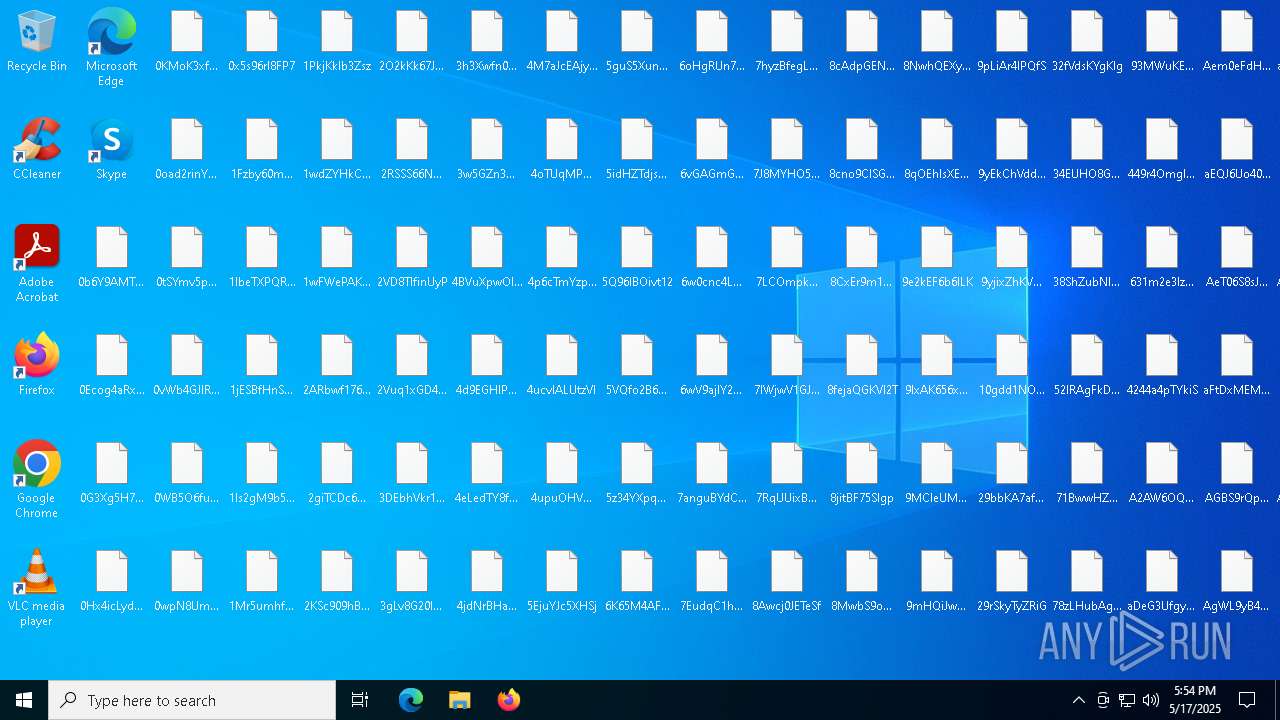
Executable files
1
Suspicious files
63
Text files
1 016
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7012 | Oxygen Virus.exe | C:\Windows\System32\Oxygen Virus.exe | executable | |
MD5:4B5CDBF3F04D76C07A1B4436430A51C3 | SHA256:D53581041CF4C5C6BB99D5F0BFA352ABC42F47CB54689D982B79CF25129C4982 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\DH9X9c1MA4PP | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\pKk0YuxZVbQl | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\TLdN5vhcZ4N3 | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\Co2fCMmQcUH3 | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\SUaAmhUdcGun | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\0Hx4icLyd43h | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\0vWb4GJlR21x | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\J6elYf9Wlzoy | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
| 2616 | Oxygen Virus.exe | C:\Users\admin\Desktop\dzFpxXqCsDkW | text | |
MD5:1DC0CDA9AFD5F3E09C2835CF245EB83F | SHA256:C75D0F58F707789FAF1217151478EE946BF09714FBC8D8DB3CBEEFE71CA5D541 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6012 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4628 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |