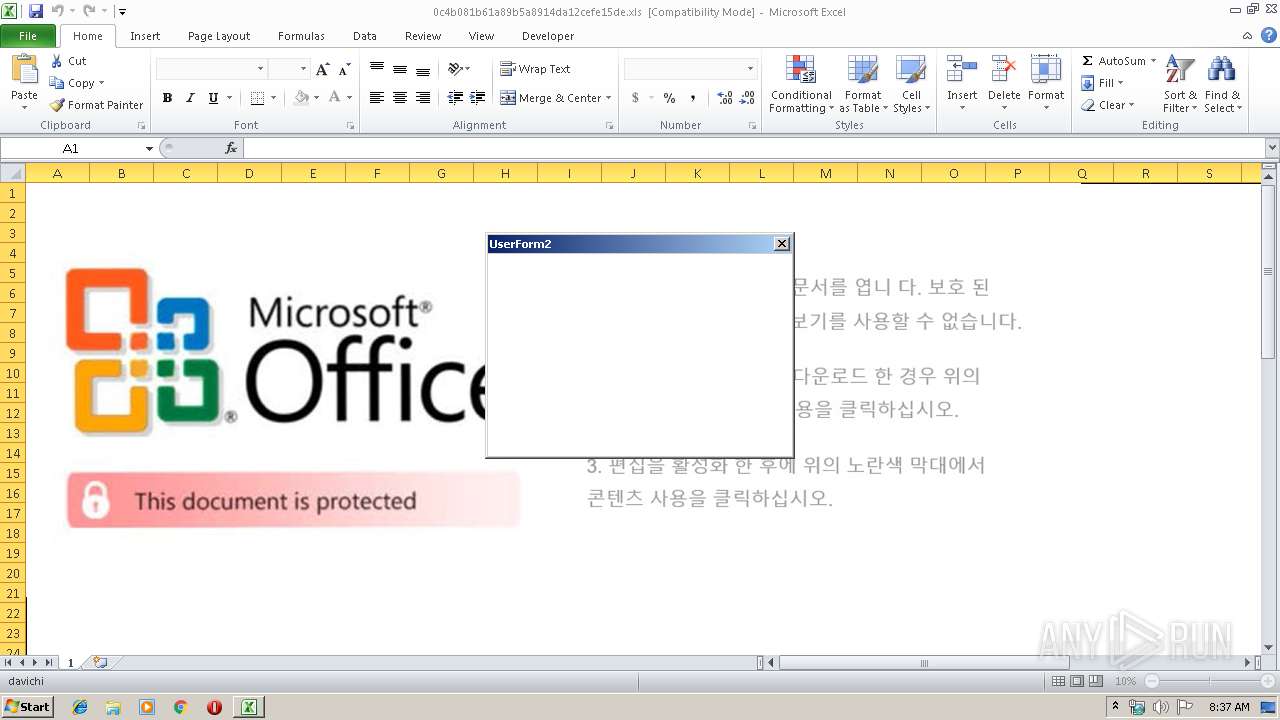
| File name: | 0c4b081b61a89b5a8914da12cefe15de.xls |
| Full analysis: | https://app.any.run/tasks/2fbc10b0-162f-49bc-aeaa-14581c370db8 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 07:37:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: kerio, Last Saved By: alex, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat May 18 08:27:21 2019, Last Saved Time/Date: Sun Jun 2 21:56:10 2019, Security: 0 |
| MD5: | 0C4B081B61A89B5A8914DA12CEFE15DE |
| SHA1: | 46B61D7C99EF0D57899BEBAC401EC3FF706A9000 |
| SHA256: | D5347F95512BE99C463877AF379C9A7CEFF4166BAB4567F79A0FBE043AF072F2 |
| SSDEEP: | 3072:mKpb8rGYrMPelwhKmFV5xtezEsg8/dgQk4/ikCf8TJijkpht6rJBgyLMYpE4y:mKpb8rGYrMPelwhKmFV5xtuEsg8/dgyL |
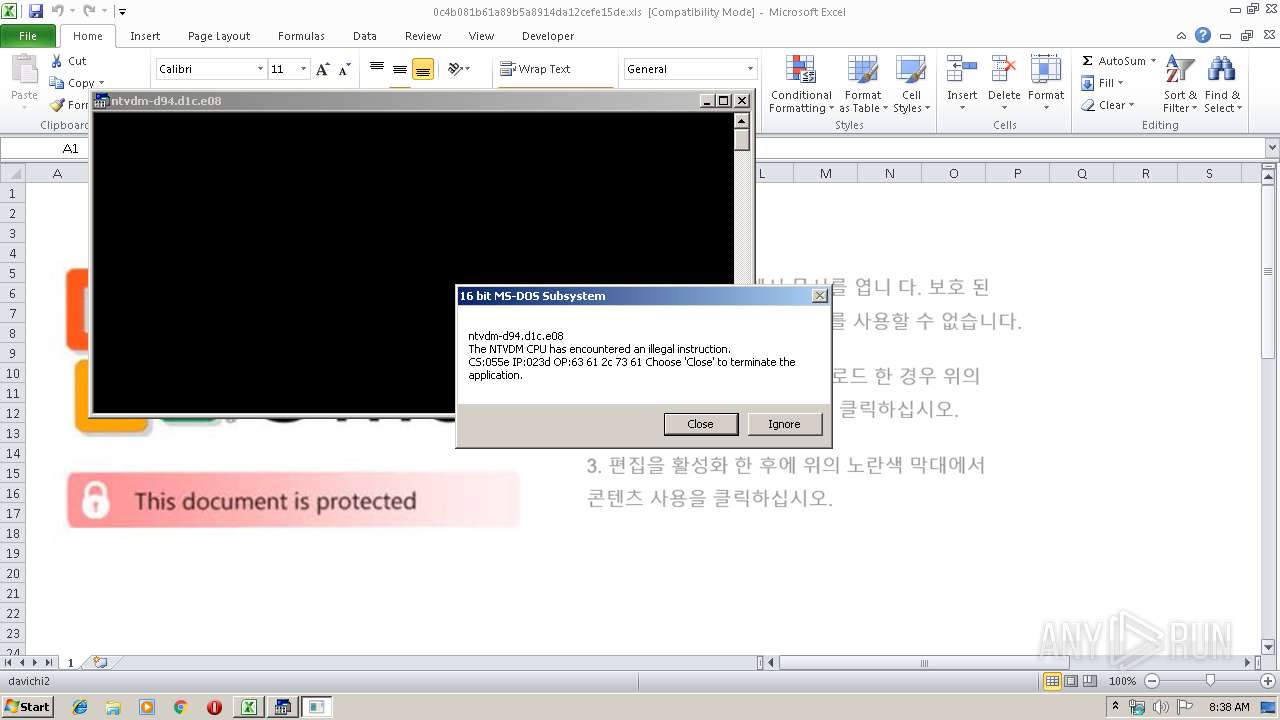
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3348)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3348)
SUSPICIOUS
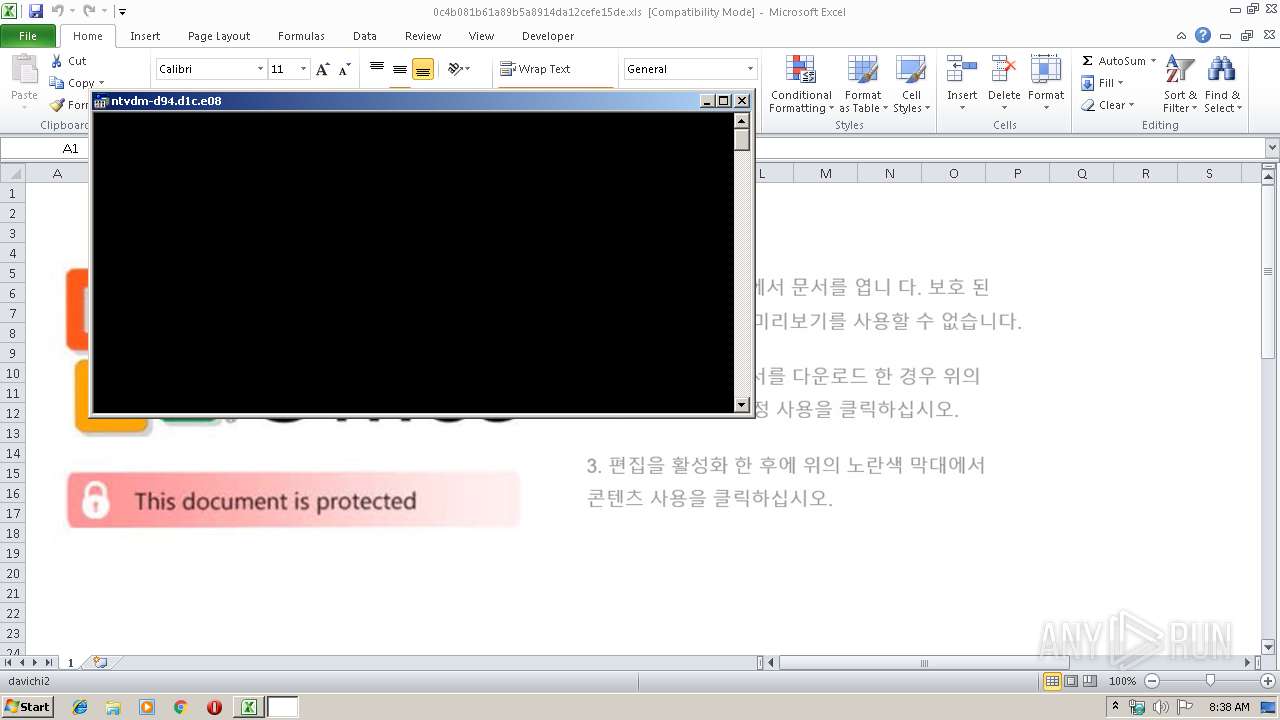
Executes application which crashes
- cmd.exe (PID: 1876)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 3348)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 25 |
|---|---|
| CompObjUserType: | Microsoft Forms 2.0 Form |
| CodePage: | Windows Cyrillic |
| Author: | kerio |
| LastModifiedBy: | alex |
| Software: | Microsoft Excel |
| CreateDate: | 2019:05:18 07:27:21 |
| ModifyDate: | 2019:06:02 20:56:10 |
| Security: | None |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1876 | cmd.exe /c start "" xlx.exe | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3476 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
646
Read events
548
Write events
91
Delete events
7
Modification events
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | !`& |
Value: 21602600140D0000010000000000000000000000 | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 140D0000C6ED25AE3B3DD50100000000 | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | !`& |
Value: 21602600140D0000010000000000000000000000 | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3348) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\17D562 |
| Operation: | write | Name: | 17D562 |
Value: 04000000140D00004600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00300063003400620030003800310062003600310061003800390062003500610038003900310034006400610031003200630065006600650031003500640065002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000605C3AAF3B3DD50162D5170062D5170000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD021.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3476 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs31D9.tmp | — | |
MD5:— | SHA256:— | |||
| 3476 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs31DA.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3348 | EXCEL.EXE | C:\Users\admin\Documents\xlx.exe | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | EXCEL.EXE | GET | 200 | 151.237.80.80:80 | http://vairina.top/t1 | BG | html | 669 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | EXCEL.EXE | 151.237.80.80:80 | vairina.top | IPACCT Ltd. | BG | malicious |
3348 | EXCEL.EXE | 151.237.138.38:80 | vairina.top | IPACCT Ltd. | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vairina.top |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3348 | EXCEL.EXE | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3348 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |