| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/3e9f88ea-0f34-47de-a1a8-2f49316fbe5a |
| Verdict: | No threats detected |
| Analysis date: | June 24, 2018, 08:27:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA7C0E67969F178AF8C936BFEDECCF4D |
| SHA1: | 8E2CEA07A64A1C6B448011AB63D3EB026CFD2EE5 |
| SHA256: | D52BCE3789146D2321CD35B4112DF6914F9E3959C220DB7BC161C3AA0D7DBDAF |
| SSDEEP: | 49152:19C/VunEfB21wOUwgLSPg7dC+ib2xbFcGwQ/S:T8uoB2eOU1LSYxC0SGZK |
MALICIOUS
Application was dropped or rewritten from another process
- netpad.exe (PID: 1132)
- wyUpdate.exe (PID: 2480)
Changes settings of System certificates
- netpad.exe (PID: 1132)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup.exe (PID: 3880)
- Setup.exe (PID: 600)
- Setup.tmp (PID: 3576)
Modifies the open verb of a shell class
- Setup.tmp (PID: 3576)
Adds / modifies Windows certificates
- netpad.exe (PID: 1132)
Creates files in the user directory
- netpad.exe (PID: 1132)
INFO
Application was dropped or rewritten from another process
- Setup.tmp (PID: 1824)
- Setup.tmp (PID: 3576)
Dropped object may contain URL's
- Setup.exe (PID: 3880)
- Setup.exe (PID: 600)
- Setup.tmp (PID: 3576)
- netpad.exe (PID: 1132)
Loads dropped or rewritten executable
- Setup.tmp (PID: 3576)
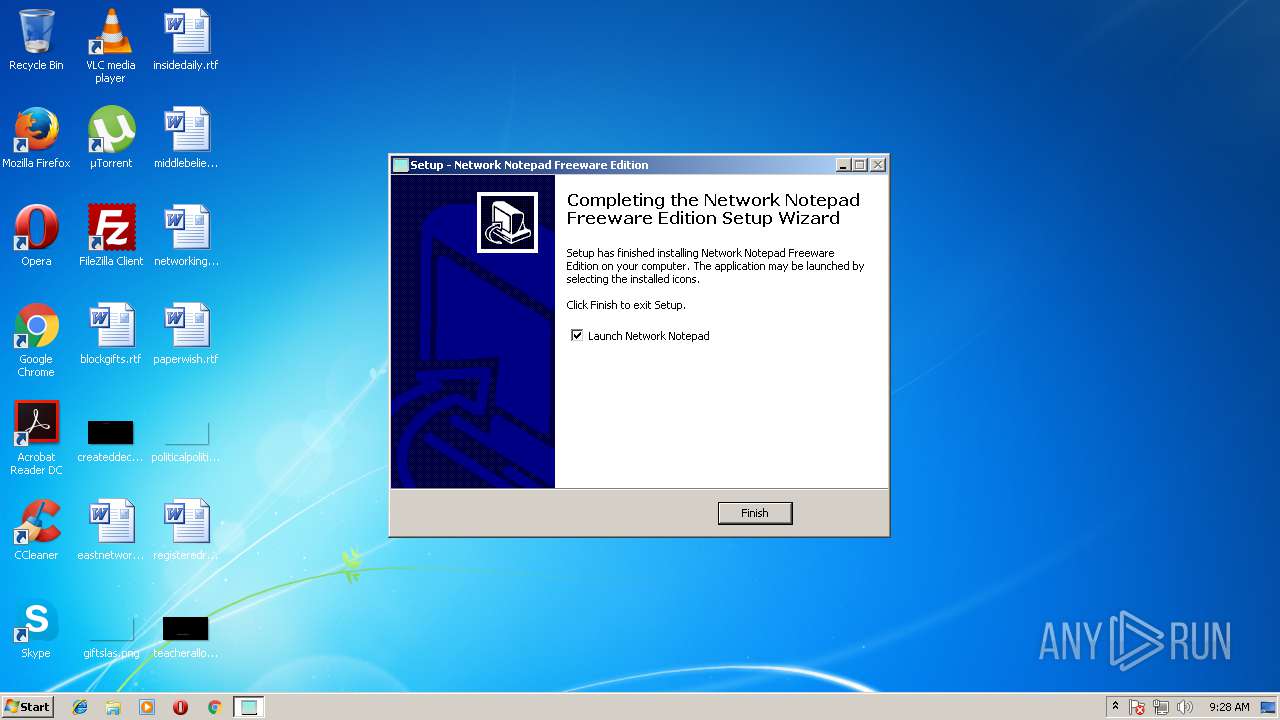
Creates a software uninstall entry
- Setup.tmp (PID: 3576)
Creates files in the program directory
- Setup.tmp (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 23552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
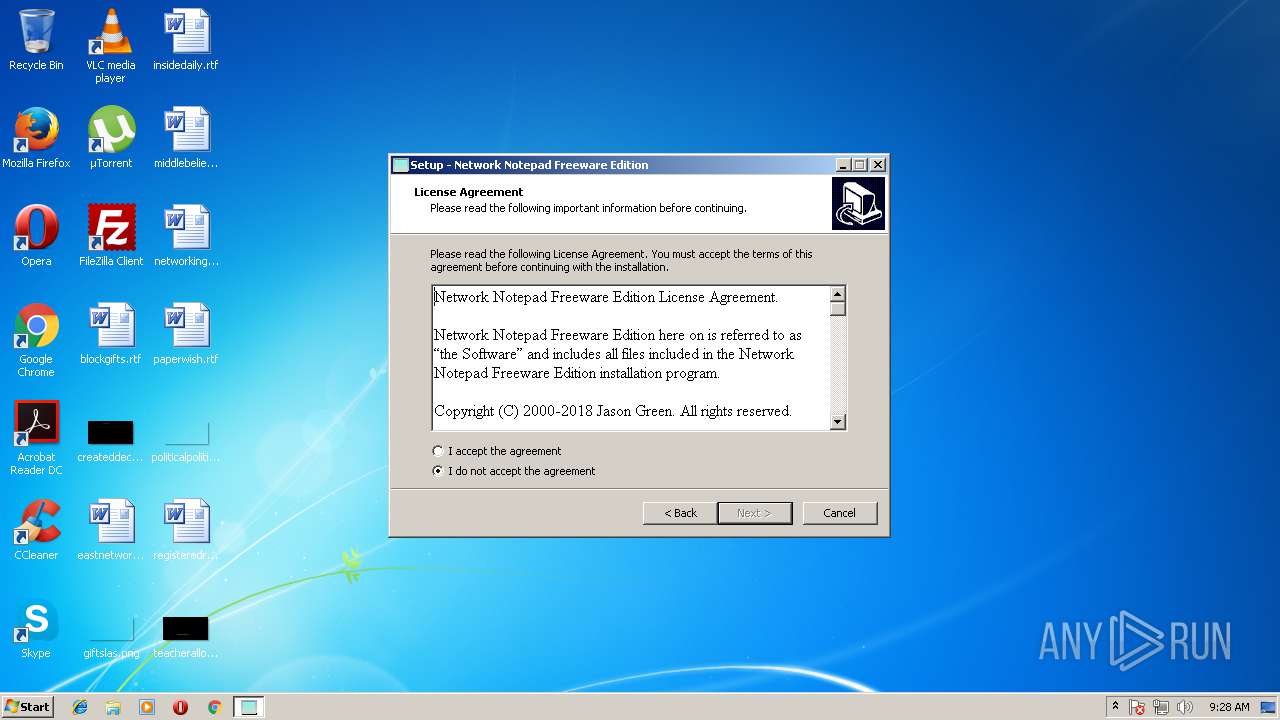
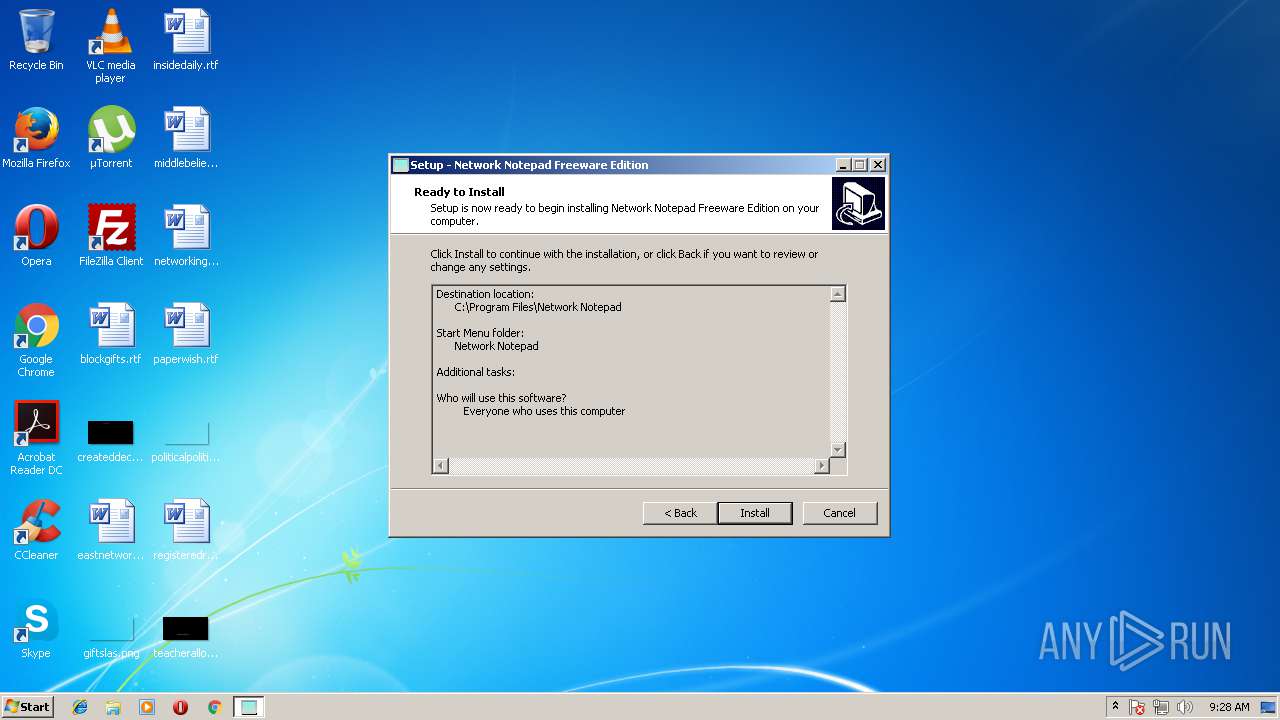
| CompanyName: | Jason Green |
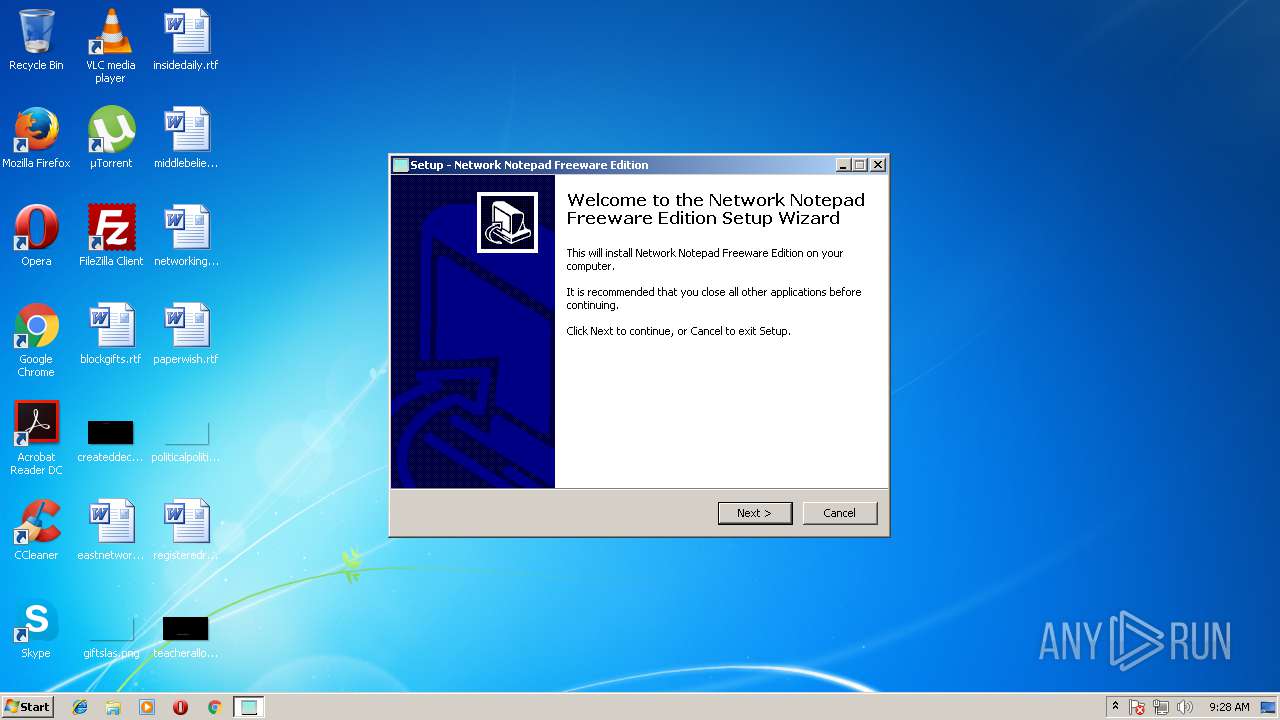
| FileDescription: | Network Notepad Freeware Edition Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Network Notepad Freeware Edition |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jason Green |
| FileDescription: | Network Notepad Freeware Edition Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Network Notepad Freeware Edition |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63177 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00004A60 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.02099 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.70445 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 1.5789 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
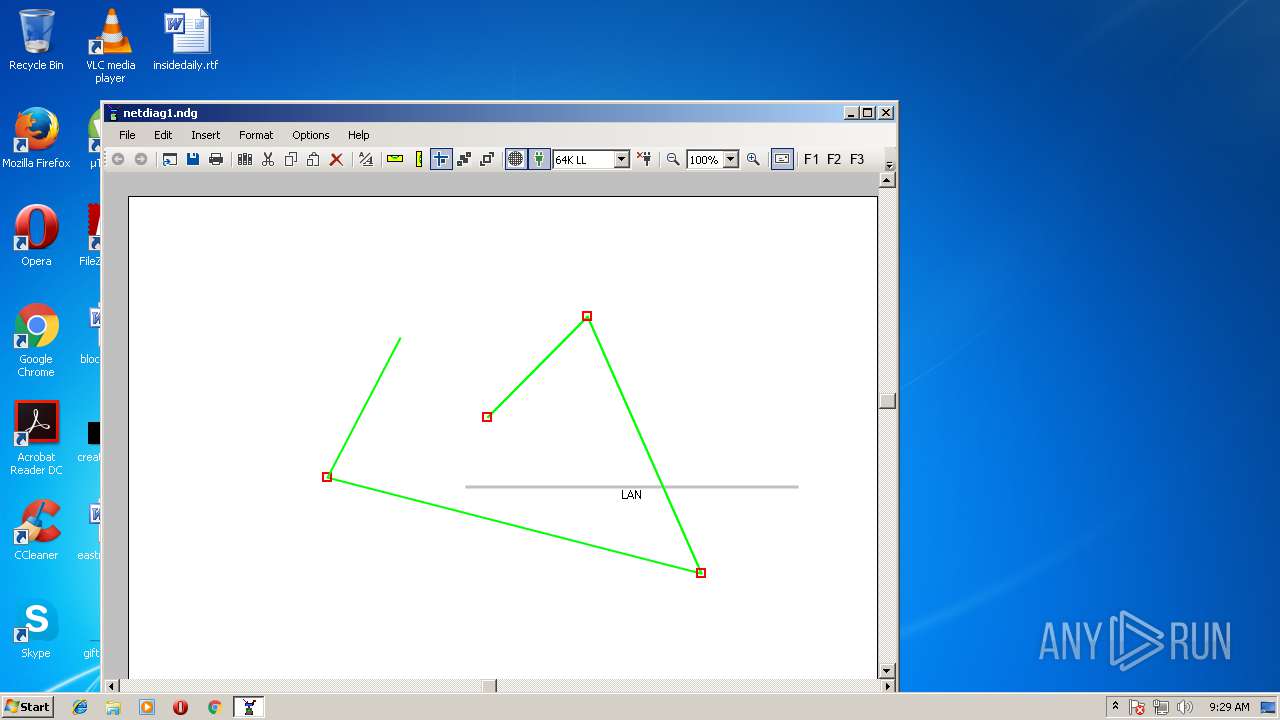
Total processes
42
Monitored processes
6
Malicious processes
4
Suspicious processes
1
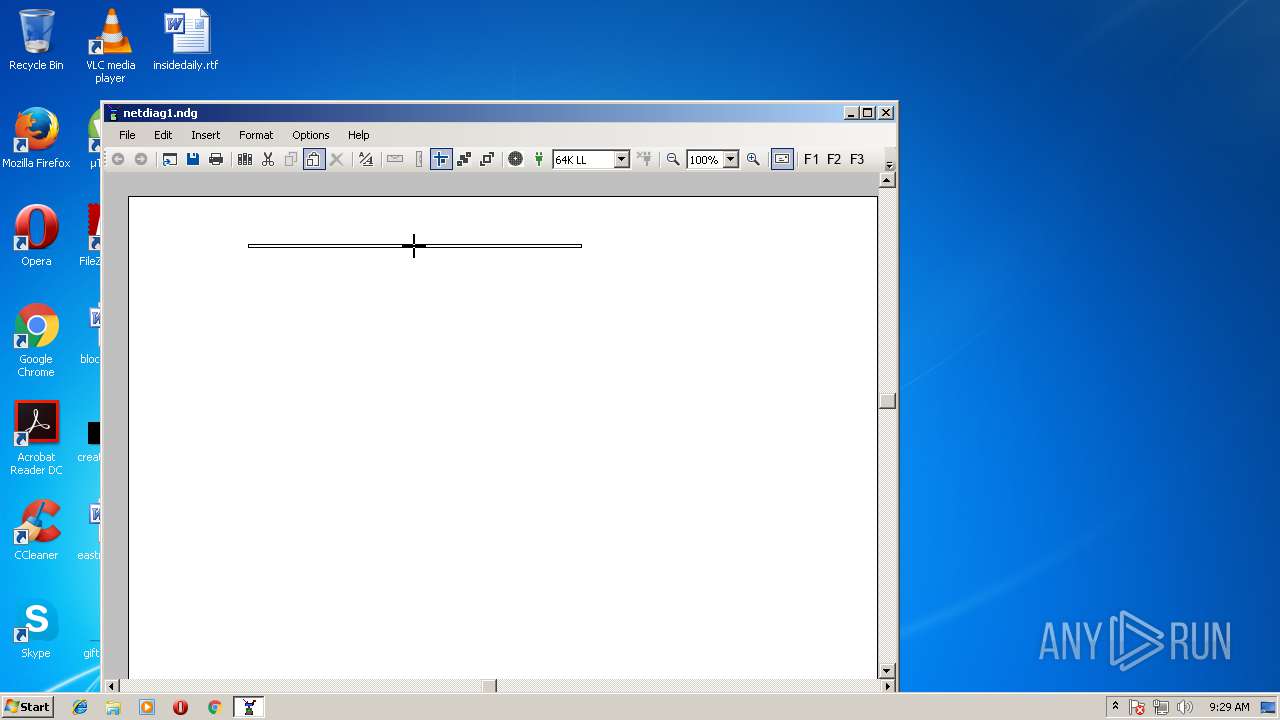
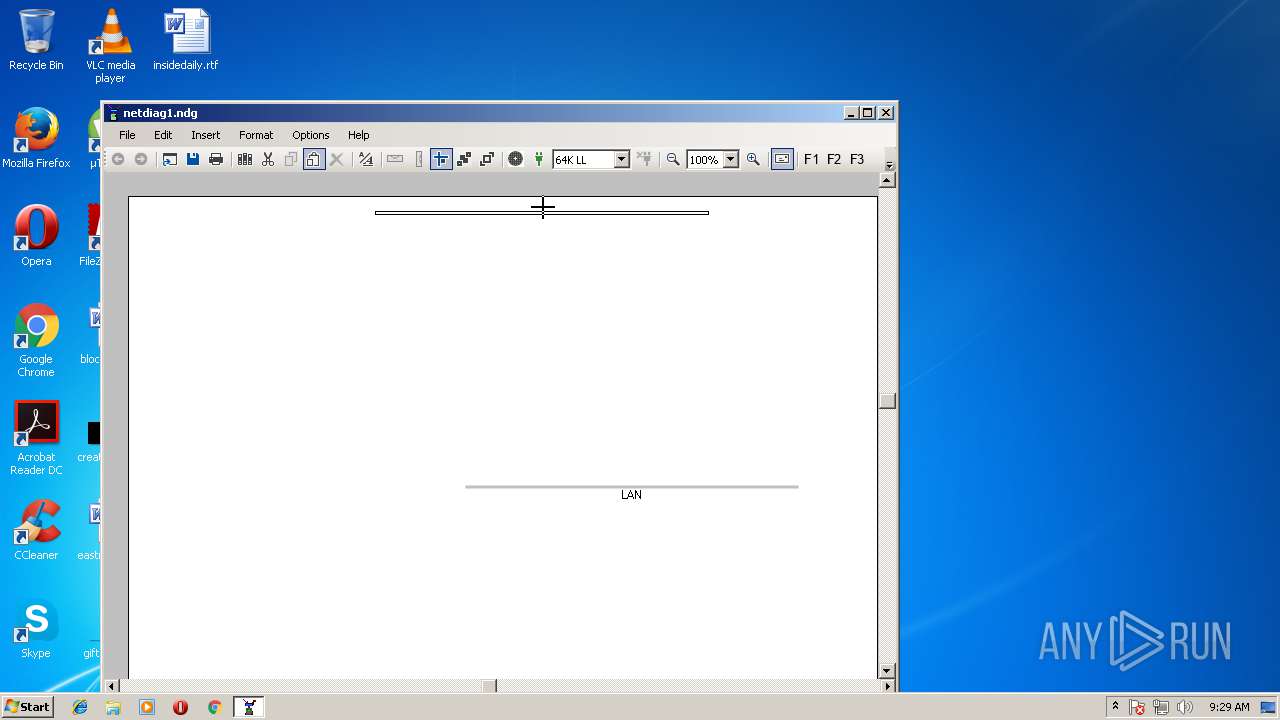
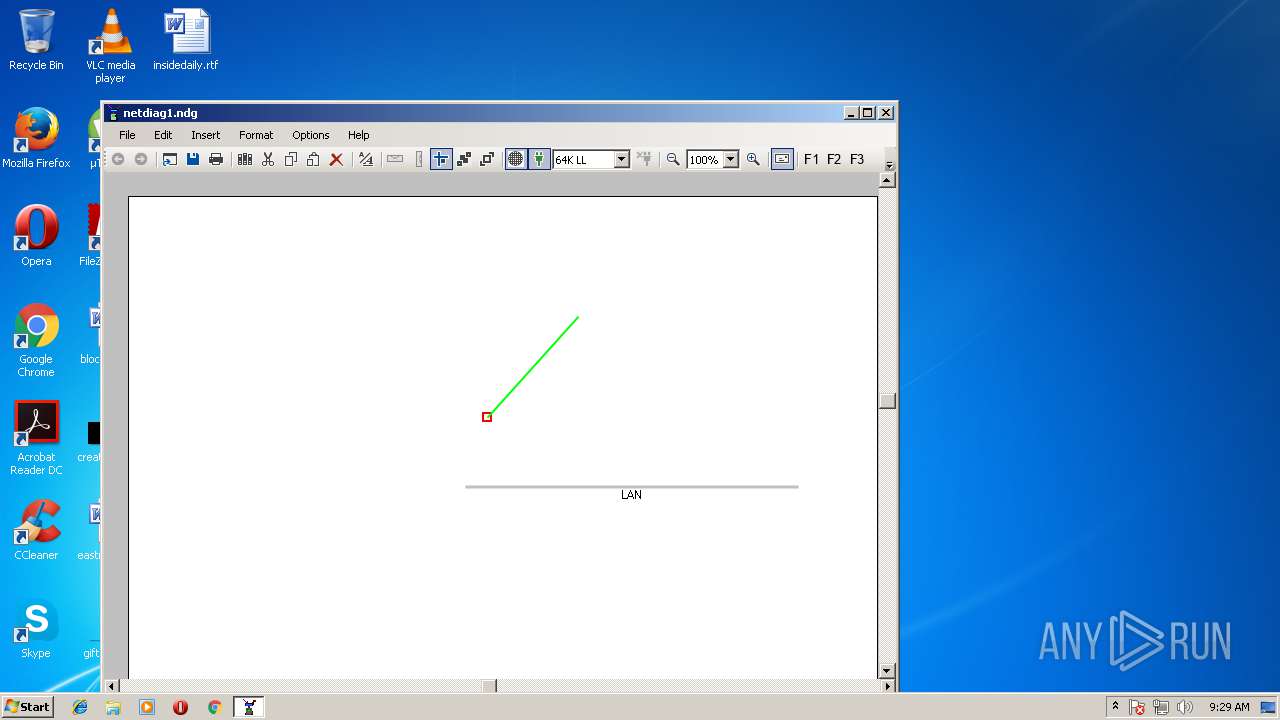
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Jason Green Integrity Level: MEDIUM Description: Network Notepad Freeware Edition Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Network Notepad\netpad.exe" | C:\Program Files\Network Notepad\netpad.exe | Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Network Notepad Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\AppData\Local\Temp\is-J9AAG.tmp\Setup.tmp" /SL5="$E0214,1429342,65024,C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-J9AAG.tmp\Setup.tmp | — | Setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Network Notepad\wyUpdate.exe" /autoupdate | C:\Program Files\Network Notepad\wyUpdate.exe | netpad.exe | ||||||||||||
User: admin Company: wyDay Integrity Level: HIGH Description: wyUpdate Exit code: 3 Version: 2.6.18.4 Modules
| |||||||||||||||
| 3576 | "C:\Users\admin\AppData\Local\Temp\is-0A85U.tmp\Setup.tmp" /SL5="$D01F6,1429342,65024,C:\Users\admin\AppData\Local\Temp\Setup.exe" /SPAWNWND=$E01FA /NOTIFYWND=$E0214 | C:\Users\admin\AppData\Local\Temp\is-0A85U.tmp\Setup.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" /SPAWNWND=$E01FA /NOTIFYWND=$E0214 | C:\Users\admin\AppData\Local\Temp\Setup.exe | Setup.tmp | ||||||||||||
User: admin Company: Jason Green Integrity Level: HIGH Description: Network Notepad Freeware Edition Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
741
Read events
642
Write events
93
Delete events
6
Modification events
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F80D000004846D4D950BD401 | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1000A5465A9331B470382AA7909CF40CF02244CF0AF02EE336327D1E82D47042 | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Network Notepad\netpad.exe | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 02B6A9C805C7357EF437B1F90F01BB3F16E912D6D8D77DA074B041B6A1D6B569 | |||
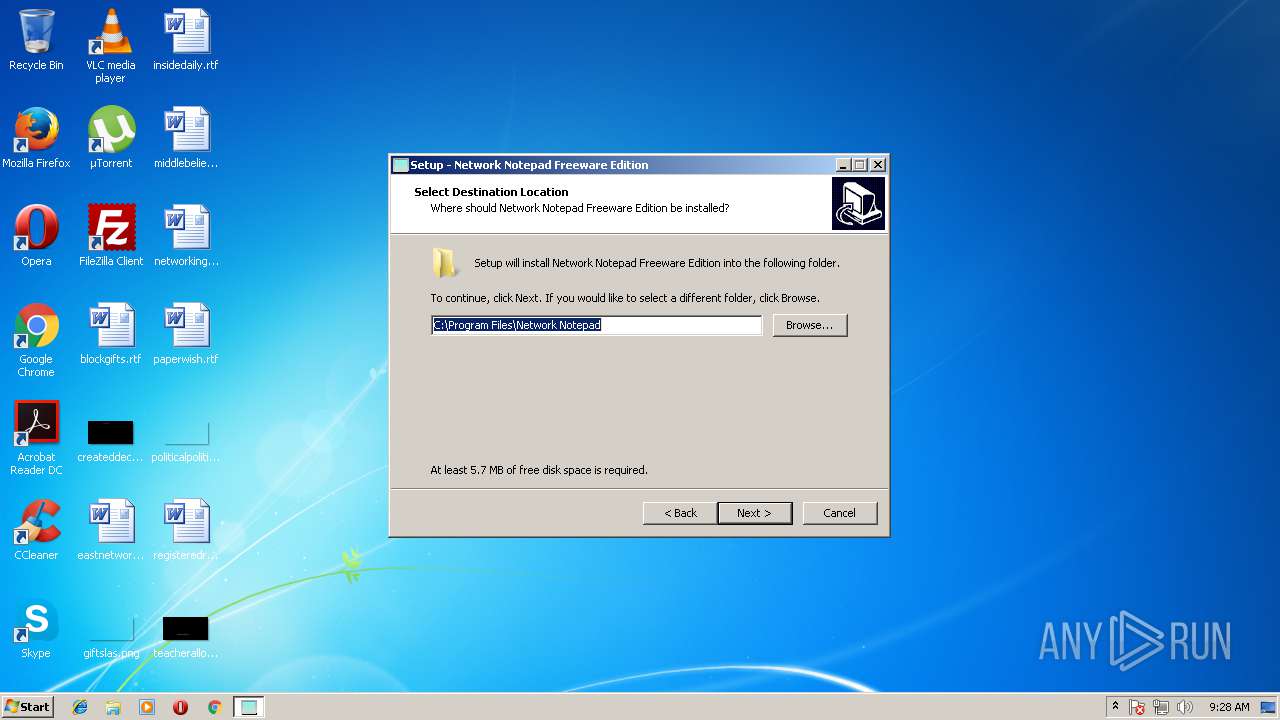
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\dotNetPad.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Network Notepad\NetPad.exe | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ndg |
| Operation: | write | Name: | |
Value: Netnotep | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ndg\PersistentHandler |
| Operation: | write | Name: | |
Value: {5e941d80-bf96-11cd-b579-08002b30bfeb}} | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Netnotep |
| Operation: | write | Name: | |
Value: Network Notepad Diagram | |||
| (PID) Process: | (3576) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Netnotep\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\Network Notepad\ndg.ico,0 | |||
Executable files
6
Suspicious files
5
Text files
155
Unknown types
992
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-MEE5A.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-0KAKI.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-JSCGU.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-THVG3.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-BPM27.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-Q95BV.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\Program Files\Network Notepad\is-8QI8V.tmp | — | |
MD5:— | SHA256:— | |||
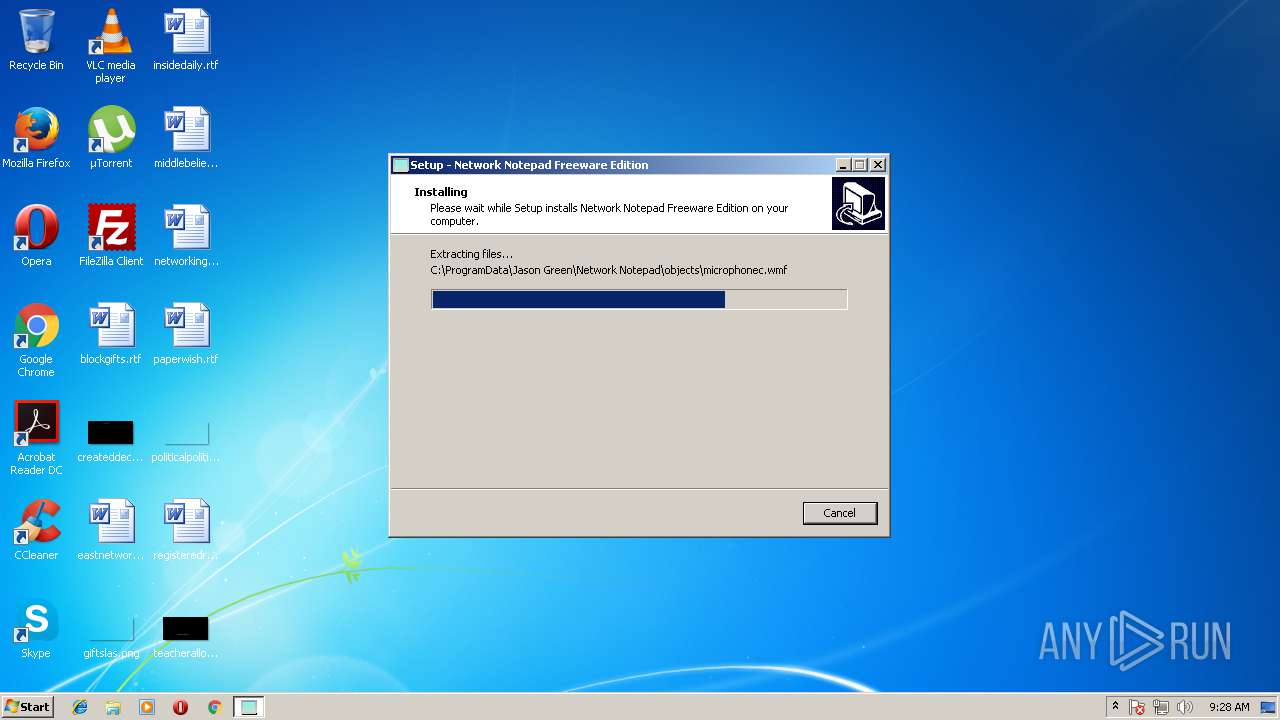
| 3576 | Setup.tmp | C:\ProgramData\Jason Green\Network Notepad\objects\is-0PSNB.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\ProgramData\Jason Green\Network Notepad\objects\is-05AHB.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | Setup.tmp | C:\ProgramData\Jason Green\Network Notepad\objects\is-I2NEM.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | wyUpdate.exe | GET | 200 | 217.34.133.54:80 | http://www.networknotepad.com/Updates3/wyserver.wys | GB | compressed | 960 b | malicious |
1132 | netpad.exe | GET | 200 | 104.16.93.188:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | US | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1132 | netpad.exe | 104.16.93.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
2480 | wyUpdate.exe | 217.34.133.54:80 | www.networknotepad.com | British Telecommunications PLC | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.comodoca.com |
| whitelisted |
www.networknotepad.com |
| malicious |