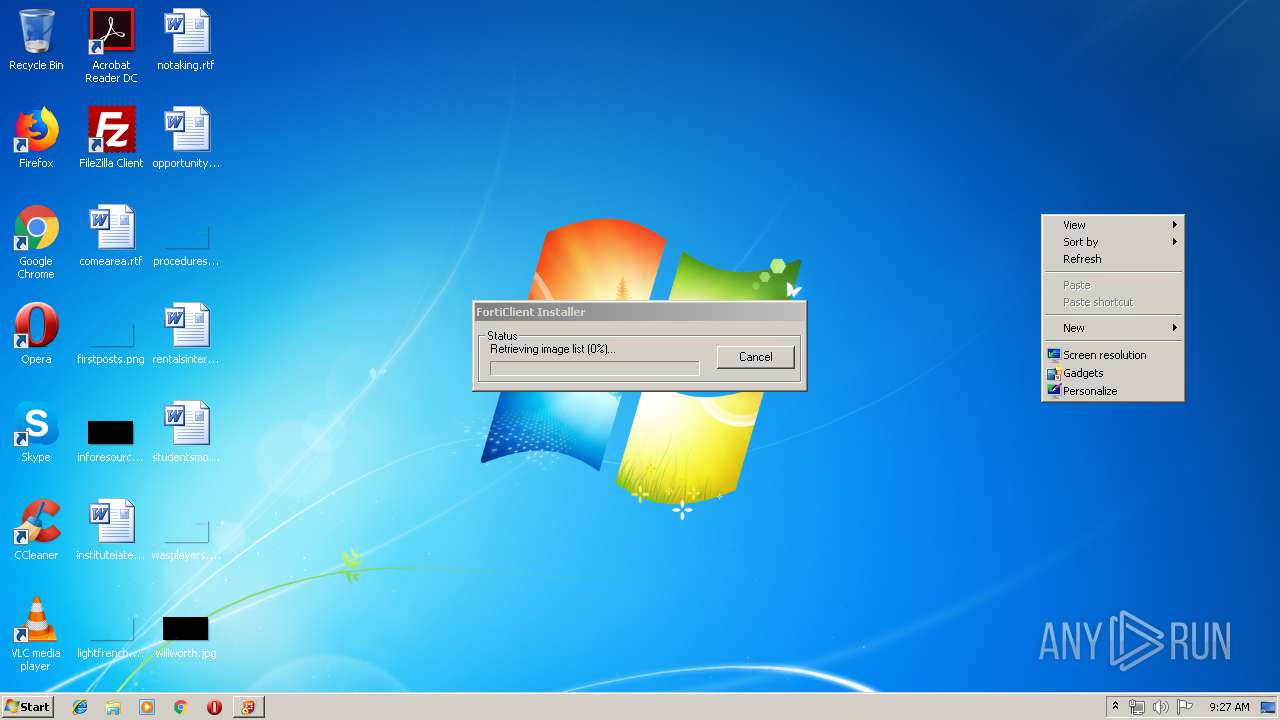
| File name: | FortiClientOnlineInstaller_6.0.exe |
| Full analysis: | https://app.any.run/tasks/a7a8c66c-f450-488b-bb13-c66c8d0b98ca |
| Verdict: | No threats detected |
| Analysis date: | April 18, 2019, 08:26:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA39F1518D9BE7A23787413872CC0018 |
| SHA1: | AA5D08564446A1C2F1AA8E5EE1041E282A45ED99 |
| SHA256: | D527D7175FA28FE18F1C1603DAF7488FF7F2FBDCAC37015483900C4F1A1B42B3 |
| SSDEEP: | 24576:iJiy6Oqi4+64wyCRsGneJZDaTOzAP31gCJq7ZE:zyGqZDaTdpY7ZE |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- FortiClientOnlineInstaller_6.0.exe (PID: 2516)
Connects to server without host name
- FortiClientOnlineInstaller_6.0.exe (PID: 3568)
Creates COM task schedule object
- FortiClientOnlineInstaller_6.0.exe (PID: 3568)
Low-level read access rights to disk partition
- FortiClientOnlineInstaller_6.0.exe (PID: 3568)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:31 02:06:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.11 |
| CodeSize: | 308736 |
| InitializedDataSize: | 552960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x249b0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.0.67 |
| ProductVersionNumber: | 6.0.0.67 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Fortinet Inc. |
| FileDescription: | FortiClient Online Installation |
| FileVersion: | 6.0.0.0067 |
| InternalName: | FCInstallerLight |
| LegalCopyright: | 2018 Fortinet Inc. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | FortiClientInstaller.exe |
| PrivateBuild: | - |
| ProductName: | FortiClient Online Installation |
| ProductVersion: | 6.0.0.0067 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-May-2018 00:06:23 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Fortinet Inc. |
| FileDescription: | FortiClient Online Installation |
| FileVersion: | 6.0.0.0067 |
| InternalName: | FCInstallerLight |
| LegalCopyright: | 2018 Fortinet Inc. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFilename: | FortiClientInstaller.exe |
| PrivateBuild: | - |
| ProductName: | FortiClient Online Installation |
| ProductVersion: | 6.0.0.0067 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 31-May-2018 00:06:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004B5BC | 0x0004B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64544 |
.rdata | 0x0004D000 | 0x0001F782 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.56263 |
.data | 0x0006D000 | 0x00005724 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.71099 |
.didat | 0x00073000 | 0x0000001C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.267013 |
.rsrc | 0x00074000 | 0x0005DA18 | 0x0005DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09061 |
.reloc | 0x000D2000 | 0x000041F0 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68626 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24015 | 1251 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.51726 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.51271 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.2636 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.21727 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.247 | 740 | UNKNOWN | Spanish - Spain (International sort) | RT_STRING |
8 | 3.30633 | 922 | UNKNOWN | Spanish - Spain (International sort) | RT_STRING |
9 | 3.22006 | 2218 | UNKNOWN | Spanish - Spain (International sort) | RT_STRING |
10 | 3.07725 | 528 | UNKNOWN | Spanish - Spain (International sort) | RT_STRING |
100 | 5.1788 | 195 | UNKNOWN | UNKNOWN | REGISTRY |
Imports
ADVAPI32.dll |
COMCTL32.dll (delay-loaded) |
CRYPT32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHLWAPI.dll |
USER32.dll |
USERENV.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
BeginHttpRequest | 1 | 0x000113E0 |
BeginHttpResponse | 2 | 0x00011480 |
FCP_add_param | 3 | 0x0000E680 |
FCP_append_objdata_ff | 4 | 0x0000E6D0 |
FCP_break_obj_header | 5 | 0x0000EA20 |
FCP_breakup_data_item | 6 | 0x0000EB20 |
FCP_calculate_obj_head_chksum | 7 | 0x00010900 |
FCP_chk_partial_obj_files | 8 | 0x0000EBA0 |
FCP_cleanup | 9 | 0x0000EE40 |
FCP_clear_object_storage | 10 | 0x0000EE50 |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2516 | "C:\Users\admin\AppData\Local\Temp\FortiClientOnlineInstaller_6.0.exe" | C:\Users\admin\AppData\Local\Temp\FortiClientOnlineInstaller_6.0.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Online Installation Exit code: 0 Version: 6.0.0.0067 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\FortiClientOnlineInstaller_6.0.exe" | C:\Users\admin\AppData\Local\Temp\FortiClientOnlineInstaller_6.0.exe | FortiClientOnlineInstaller_6.0.exe | ||||||||||||
User: admin Company: Fortinet Inc. Integrity Level: HIGH Description: FortiClient Online Installation Exit code: 0 Version: 6.0.0.0067 Modules
| |||||||||||||||
Total events
355
Read events
348
Write events
7
Delete events
0
Modification events
| (PID) Process: | (2516) FortiClientOnlineInstaller_6.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) FortiClientOnlineInstaller_6.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3568) FortiClientOnlineInstaller_6.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{8052F904-874D-4d28-9380-AA9BDBF13AFD}\InProcServer32 |
| Operation: | write | Name: | |
Value: diskcopy.dll | |||
| (PID) Process: | (3568) FortiClientOnlineInstaller_6.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{8052F904-874D-4d28-9380-AA9BDBF13AFD}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: diskcopy.dll | |||
| (PID) Process: | (3568) FortiClientOnlineInstaller_6.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{8052F904-874D-4d28-9380-AA9BDBF13AFD}\InProcServer32 |
| Operation: | write | Name: | AppID |
Value: {3E345CC5-C179-4DF8-A02D-54BF809DED6C} | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | FortiClientOnlineInstaller_6.0.exe | C:\Users\admin\AppData\Local\Temp\obj_1_a01440 | — | |
MD5:— | SHA256:— | |||
| 3568 | FortiClientOnlineInstaller_6.0.exe | C:\Users\admin\AppData\Local\Temp\obj_1_a01440__unpacked | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | FortiClientOnlineInstaller_6.0.exe | POST | — | 173.243.138.108:80 | http://173.243.138.108/fdsupdate | US | — | — | suspicious |
3568 | FortiClientOnlineInstaller_6.0.exe | POST | 200 | 96.45.33.105:80 | http://96.45.33.105/fdsupdate | US | binary | 22.7 Kb | suspicious |
3568 | FortiClientOnlineInstaller_6.0.exe | POST | 200 | 173.243.138.98:80 | http://173.243.138.98/fdsupdate | US | binary | 760 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3568 | FortiClientOnlineInstaller_6.0.exe | 173.243.138.98:80 | forticlient.fortinet.net | Fortinet Inc. | US | suspicious |
3568 | FortiClientOnlineInstaller_6.0.exe | 173.243.138.108:80 | — | Fortinet Inc. | US | suspicious |
3568 | FortiClientOnlineInstaller_6.0.exe | 96.45.33.105:80 | forticlient.fortinet.net | Fortinet Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forticlient.fortinet.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3568 | FortiClientOnlineInstaller_6.0.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |