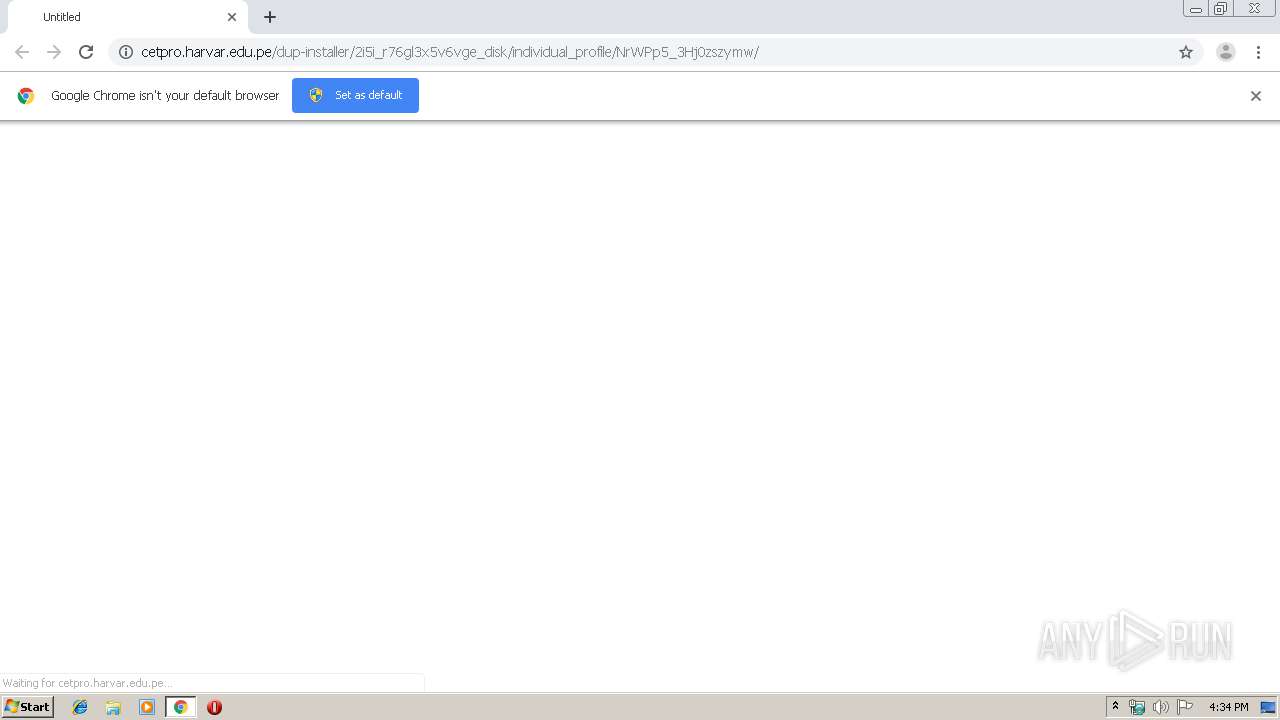
| URL: | http://cetpro.harvar.edu.pe/dup-installer/2i5i_r76gl3x5v6vge_disk/individual_profile/NrWPp5_3Hj0zszymw/ |
| Full analysis: | https://app.any.run/tasks/28c0dab3-32c3-4236-8b35-8cc481dccc25 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 16:33:46 |
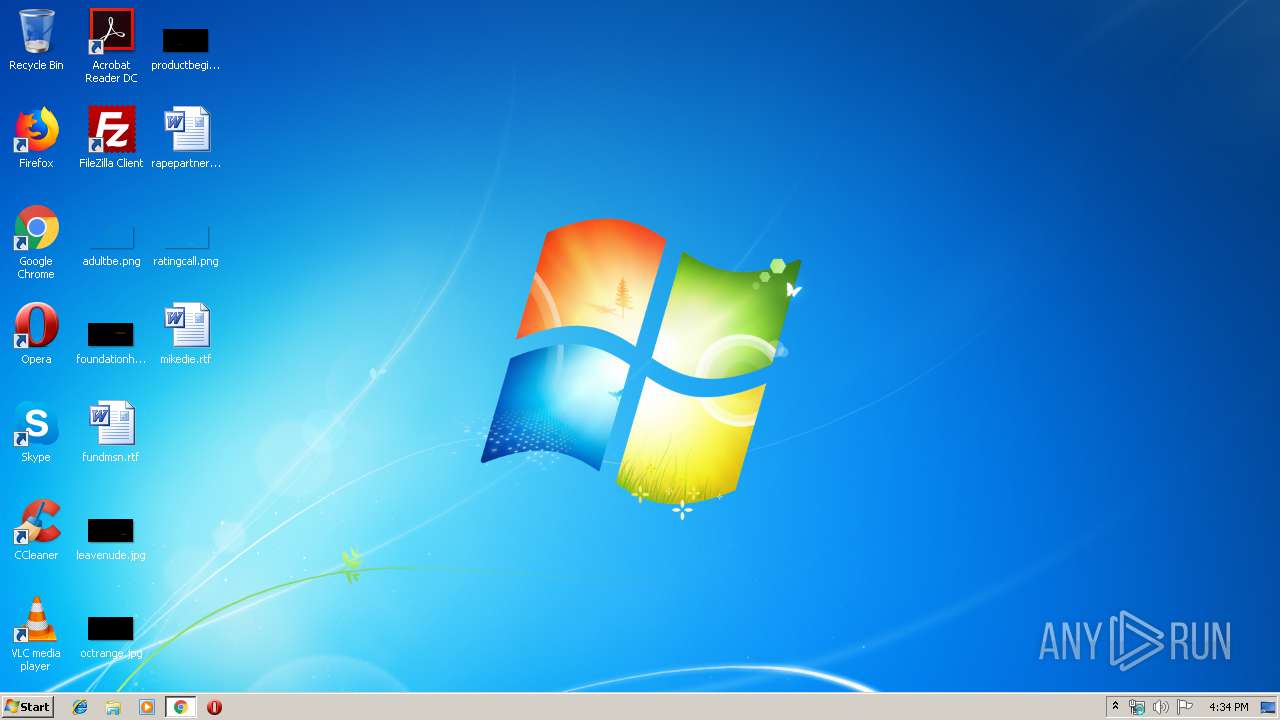
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CB4078DA3C7C1C21E02A96290FC2FB52 |
| SHA1: | 1FA1C205E5D5E044EF8192B80DA770186271A304 |
| SHA256: | D51D40C3BF3FD6303D94B28137A11570F8EF90A2FDADF622D22C385AA77AA5F5 |
| SSDEEP: | 3:N1KdAzmbXrMLWBXKaDaTOWLg/VIMOcttWf5SKn:CCKW8XLaZLg/e9cvY55 |
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 1780)
- chrome.exe (PID: 1732)
- WINWORD.EXE (PID: 2332)
Application was dropped or rewritten from another process
- 543.exe (PID: 1400)
- 543.exe (PID: 2148)
- serialfunc.exe (PID: 2840)
- serialfunc.exe (PID: 2636)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2636)
Downloads executable files from the Internet
- powershell.exe (PID: 3528)
Connects to CnC server
- serialfunc.exe (PID: 2636)
Emotet process was detected
- 543.exe (PID: 2148)
EMOTET was detected
- serialfunc.exe (PID: 2636)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2332)
PowerShell script executed
- powershell.exe (PID: 3528)
Executed via WMI
- powershell.exe (PID: 3528)
Starts Microsoft Office Application
- chrome.exe (PID: 1732)
- WINWORD.EXE (PID: 2332)
Executable content was dropped or overwritten
- powershell.exe (PID: 3528)
- 543.exe (PID: 2148)
Creates files in the user directory
- powershell.exe (PID: 3528)
Connects to unusual port
- serialfunc.exe (PID: 2636)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1732)
Starts itself from another location
- 543.exe (PID: 2148)
Connects to server without host name
- serialfunc.exe (PID: 2636)
Connects to SMTP port
- serialfunc.exe (PID: 2636)
INFO
Reads the hosts file
- chrome.exe (PID: 1732)
- chrome.exe (PID: 1780)
Creates files in the user directory
- chrome.exe (PID: 1732)
- WINWORD.EXE (PID: 2332)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 4024)
Reads Internet Cache Settings
- chrome.exe (PID: 1732)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 3528)
- 543.exe (PID: 2148)
Application launched itself
- chrome.exe (PID: 1732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
33
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17693873924062372113 --mojo-platform-channel-handle=1024 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6428565216133433650 --mojo-platform-channel-handle=1940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\543.exe" | C:\Users\admin\543.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4652553480985802384 --mojo-platform-channel-handle=4848 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4183869435986301672 --mojo-platform-channel-handle=4128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10208396474383059319 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://cetpro.harvar.edu.pe/dup-installer/2i5i_r76gl3x5v6vge_disk/individual_profile/NrWPp5_3Hj0zszymw/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17062338269870000296 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10834858996197924596 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2998238914357060590 --mojo-platform-channel-handle=4648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 474
Read events
3 474
Write events
823
Delete events
177
Modification events
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1732-13220123642154875 |
Value: 259 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
35
Text files
231
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3a6a5e90-5d37-4c7b-88a4-65ac1343ee42.tmp | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a60e.TMP | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a66c.TMP | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a64d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
318
DNS requests
247
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3528 | powershell.exe | GET | 200 | 206.221.182.74:80 | http://recreate.bigfilmproduction.com/wp-includes/2x8vf9j1507/ | US | executable | 464 Kb | malicious |
2636 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/eP31kzCTKEXcdG | LT | binary | 148 b | malicious |
2636 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/d26ra9sT1RLV2zG1D | US | binary | 1.45 Mb | malicious |
2636 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/q9pl | LT | binary | 3.27 Kb | malicious |
2636 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/OvtlsPdhQ | LT | binary | 3.16 Kb | malicious |
1780 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2636 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/lu92mnMRnrG3M | LT | binary | 2.97 Kb | malicious |
1780 | chrome.exe | GET | 200 | 190.117.128.134:80 | http://cetpro.harvar.edu.pe/dup-installer/2i5i_r76gl3x5v6vge_disk/individual_profile/NrWPp5_3Hj0zszymw/ | PE | document | 87.5 Kb | suspicious |
2636 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/h6zh7mmB | LT | binary | 4.25 Kb | malicious |
1780 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.105.212&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1575650121&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1780 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 190.117.128.134:80 | cetpro.harvar.edu.pe | America Movil Peru S.A.C. | PE | suspicious |
1780 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3528 | powershell.exe | 185.126.218.176:443 | nagel.pintogood.com | Netinternet Bilisim Teknolojileri AS | TR | suspicious |
1780 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3528 | powershell.exe | 206.221.182.74:80 | recreate.bigfilmproduction.com | Choopa, LLC | US | malicious |
2636 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
1780 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cetpro.harvar.edu.pe |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
nagel.pintogood.com |
| suspicious |
recreate.bigfilmproduction.com |
| malicious |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1780 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1780 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3528 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3528 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3528 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2636 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2636 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2636 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2636 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2636 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |