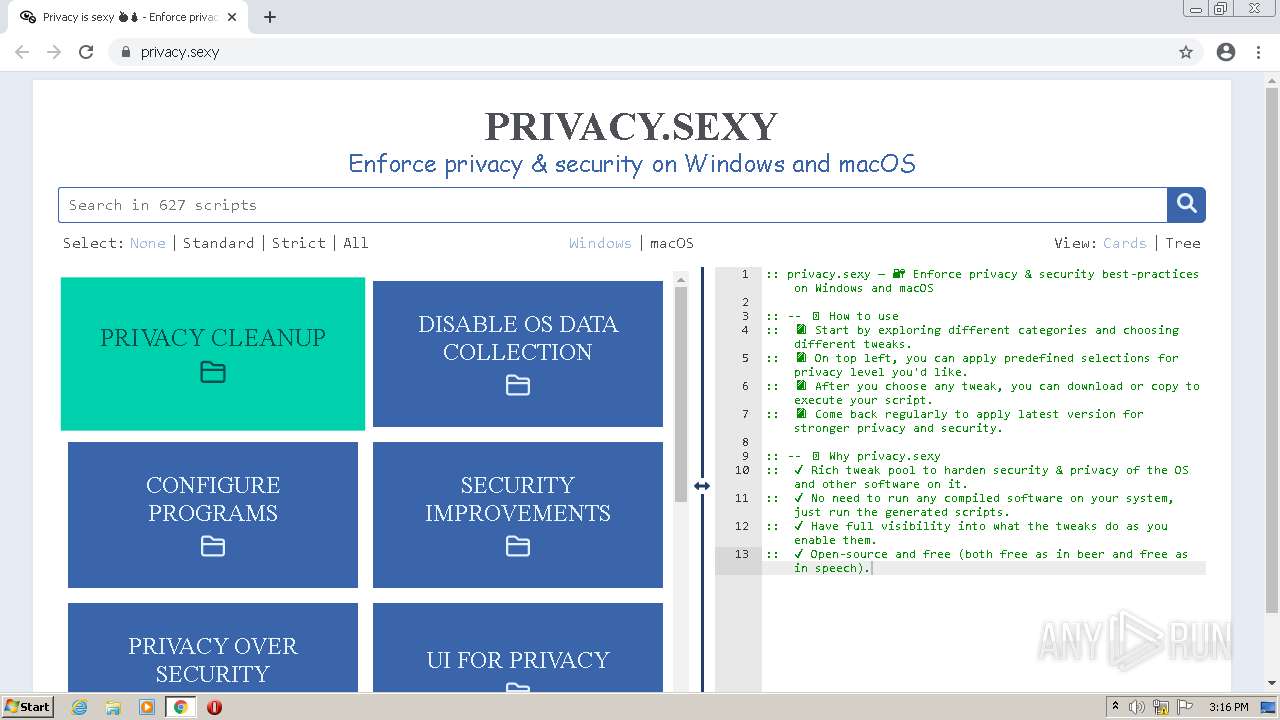
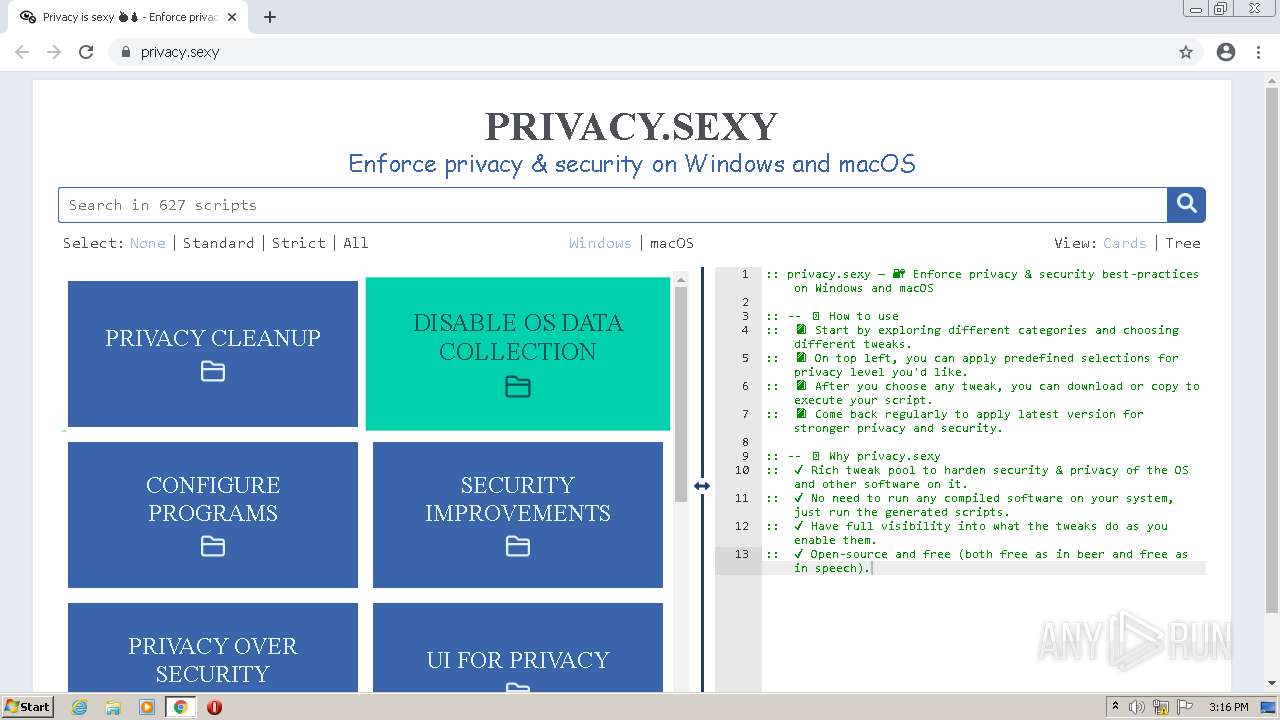
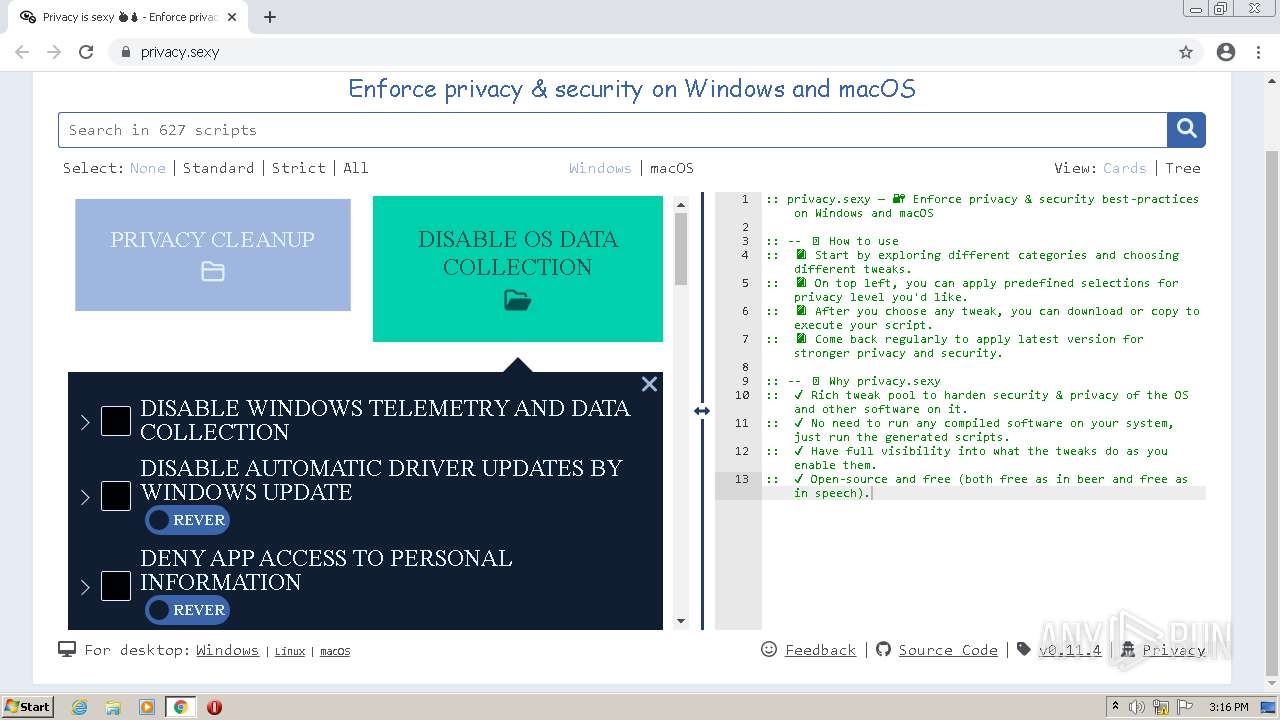
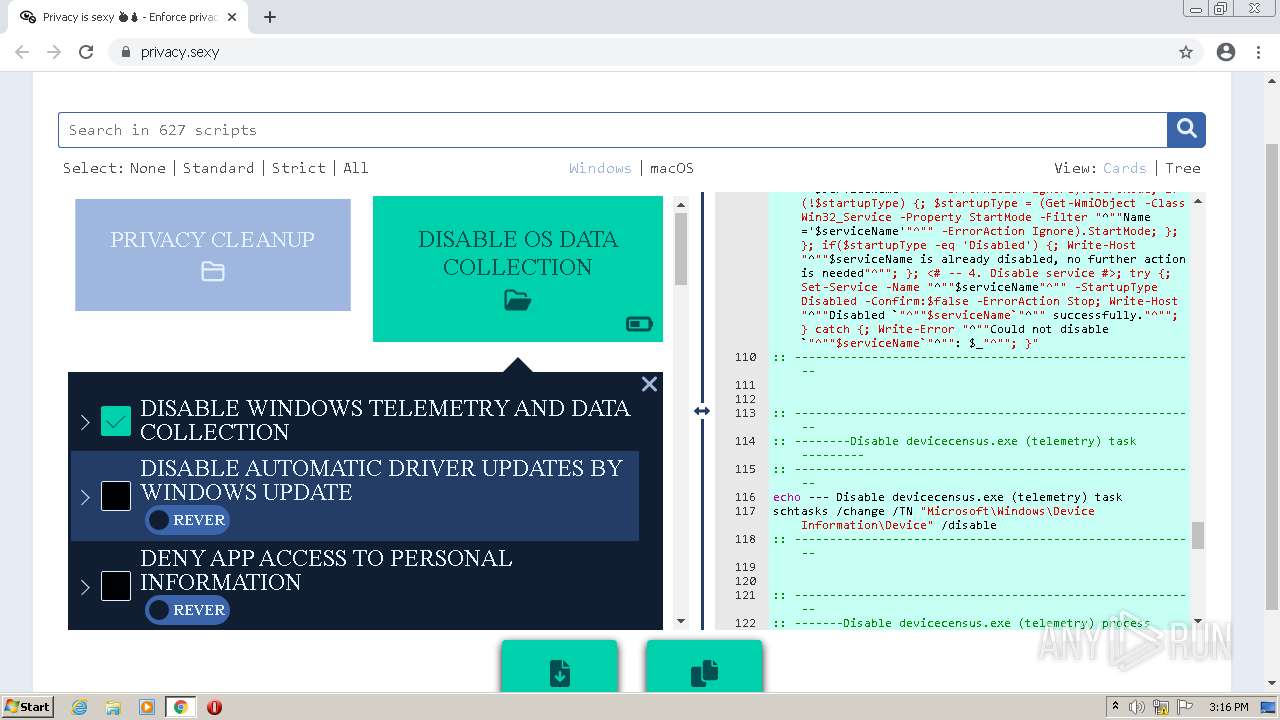
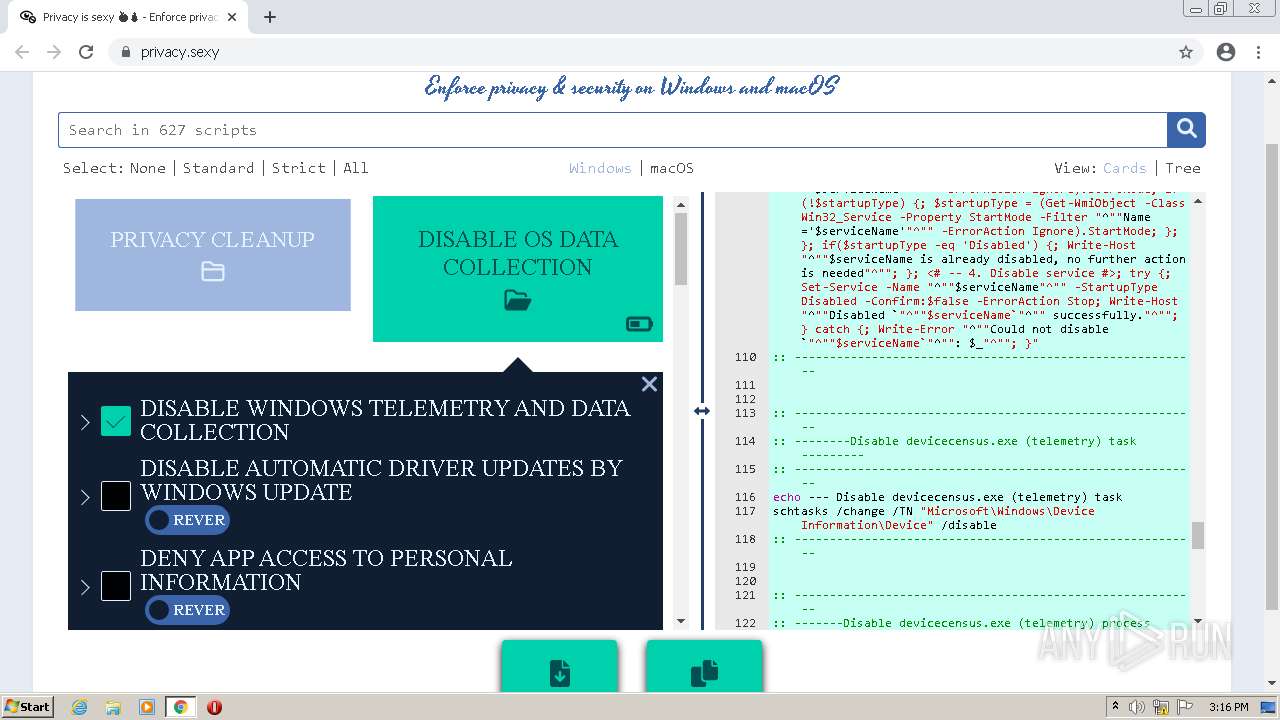
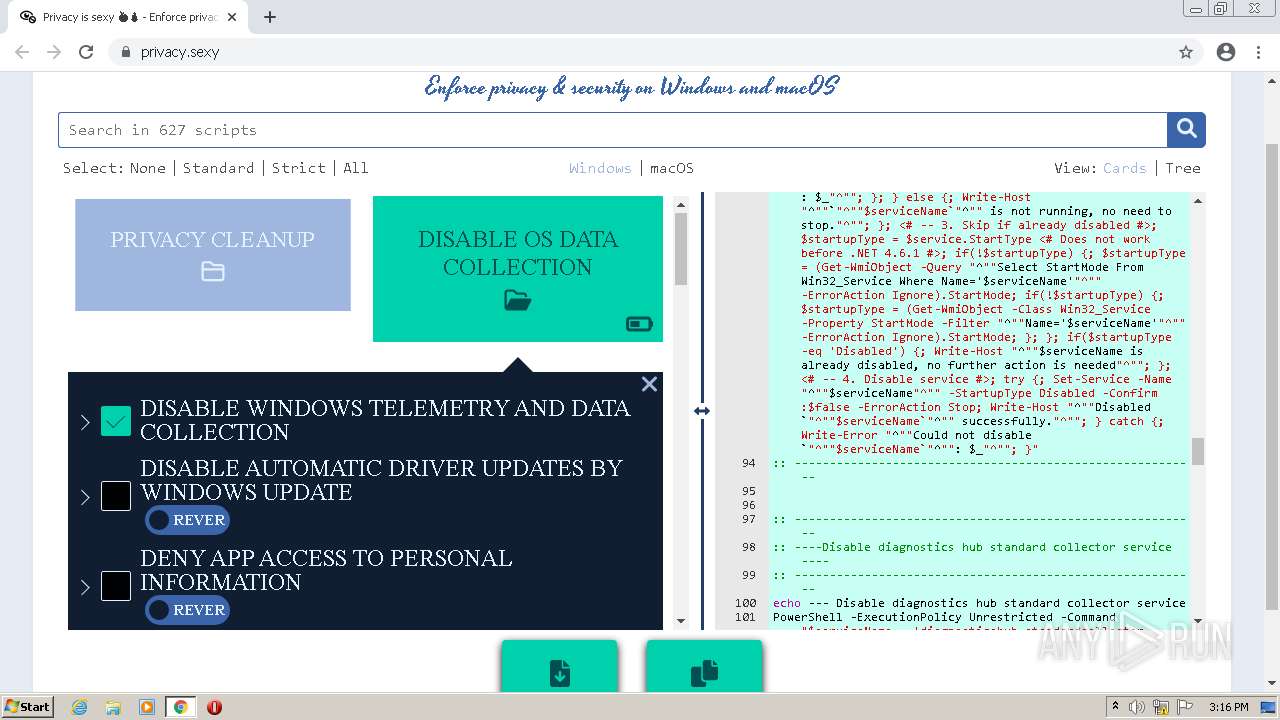
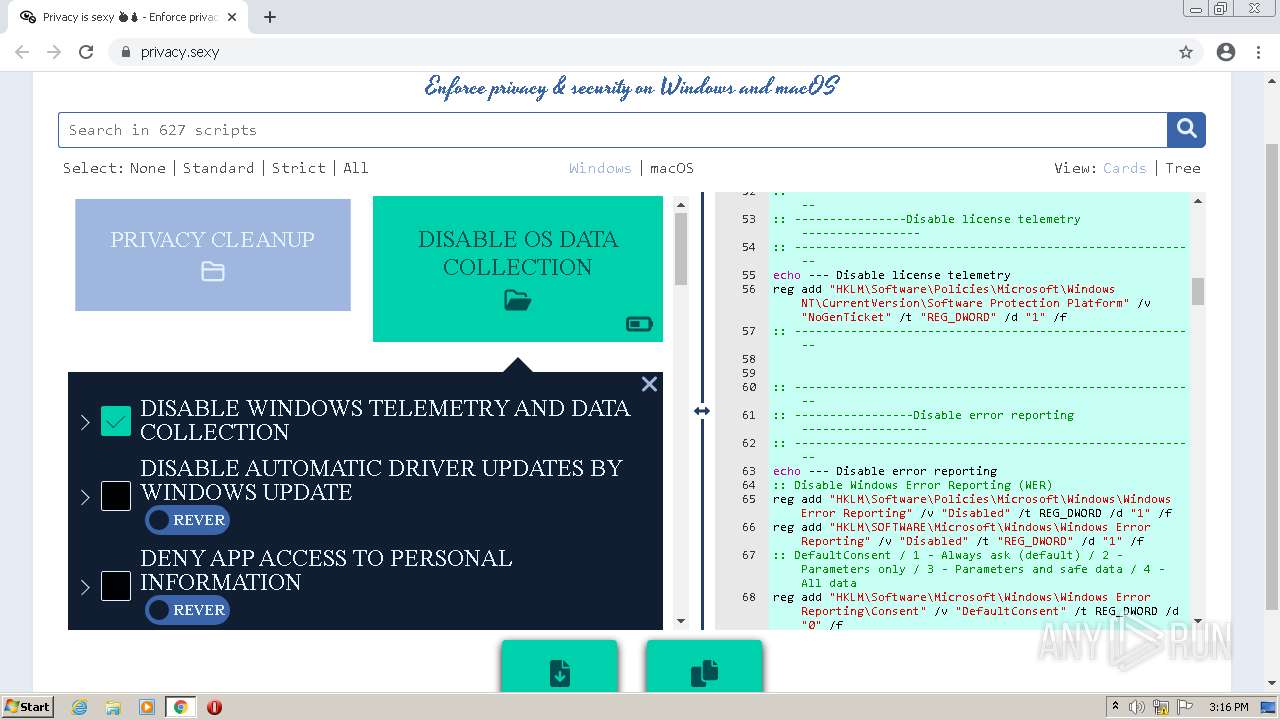
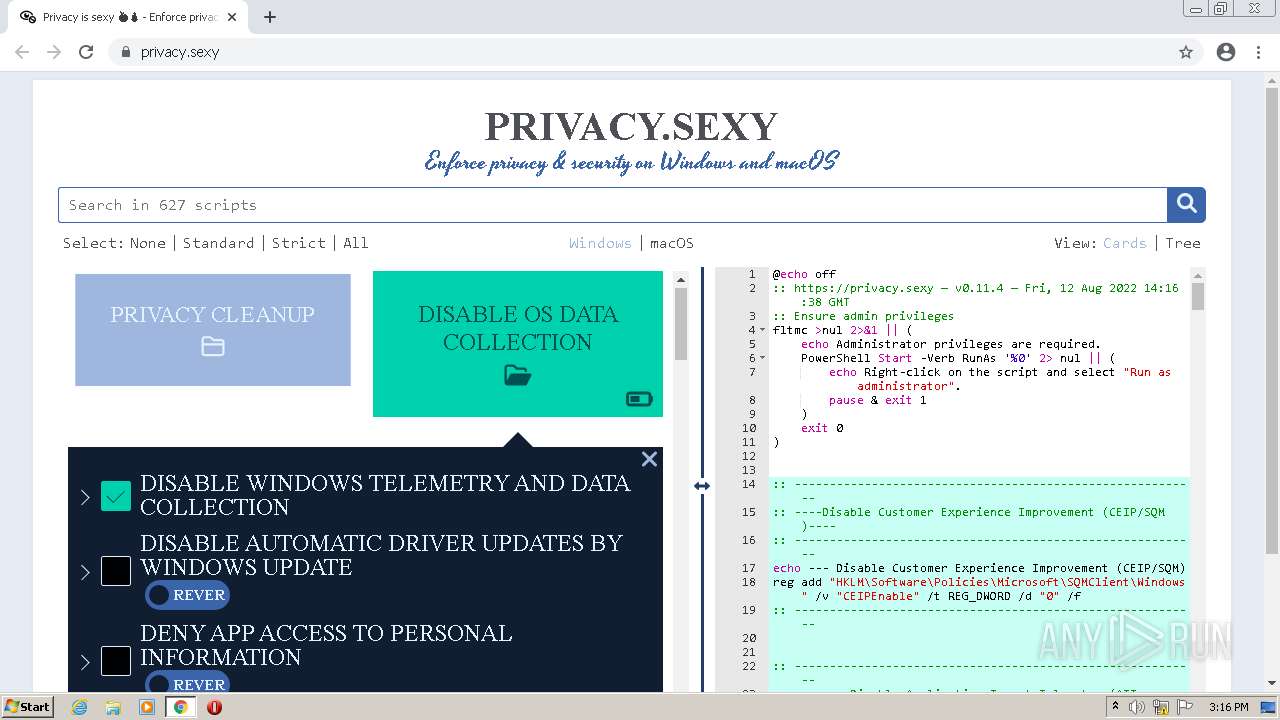
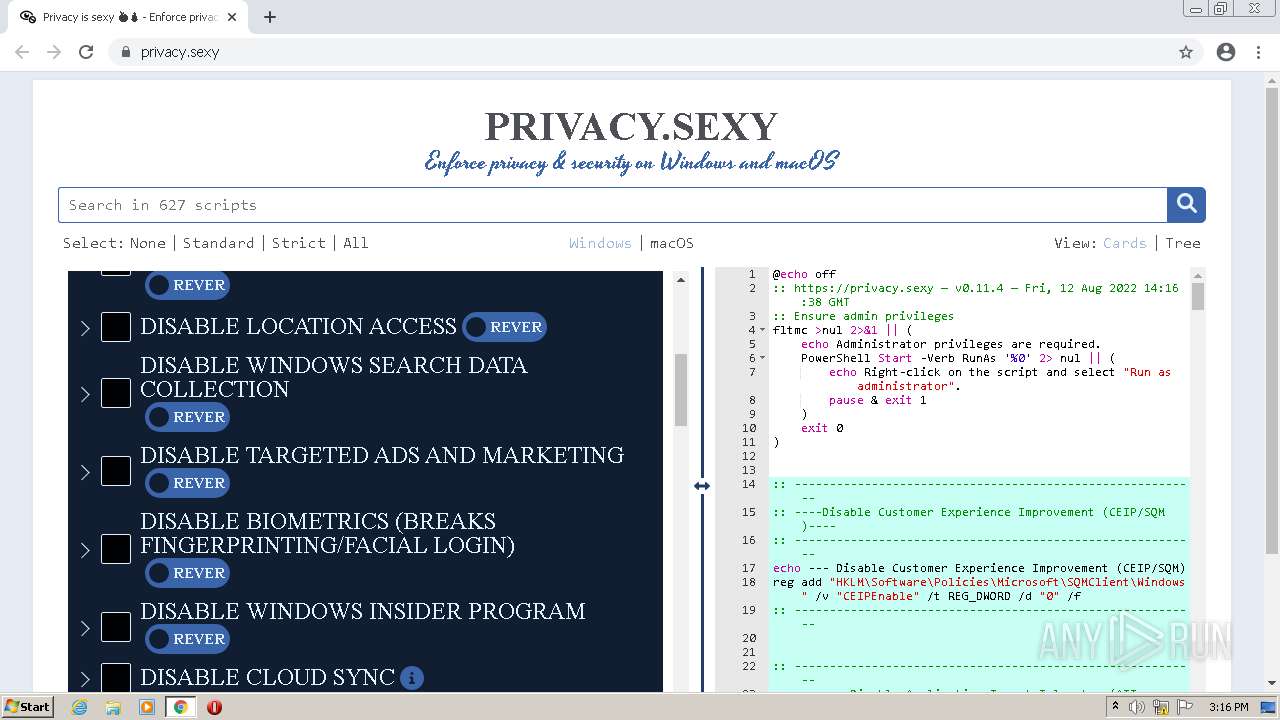
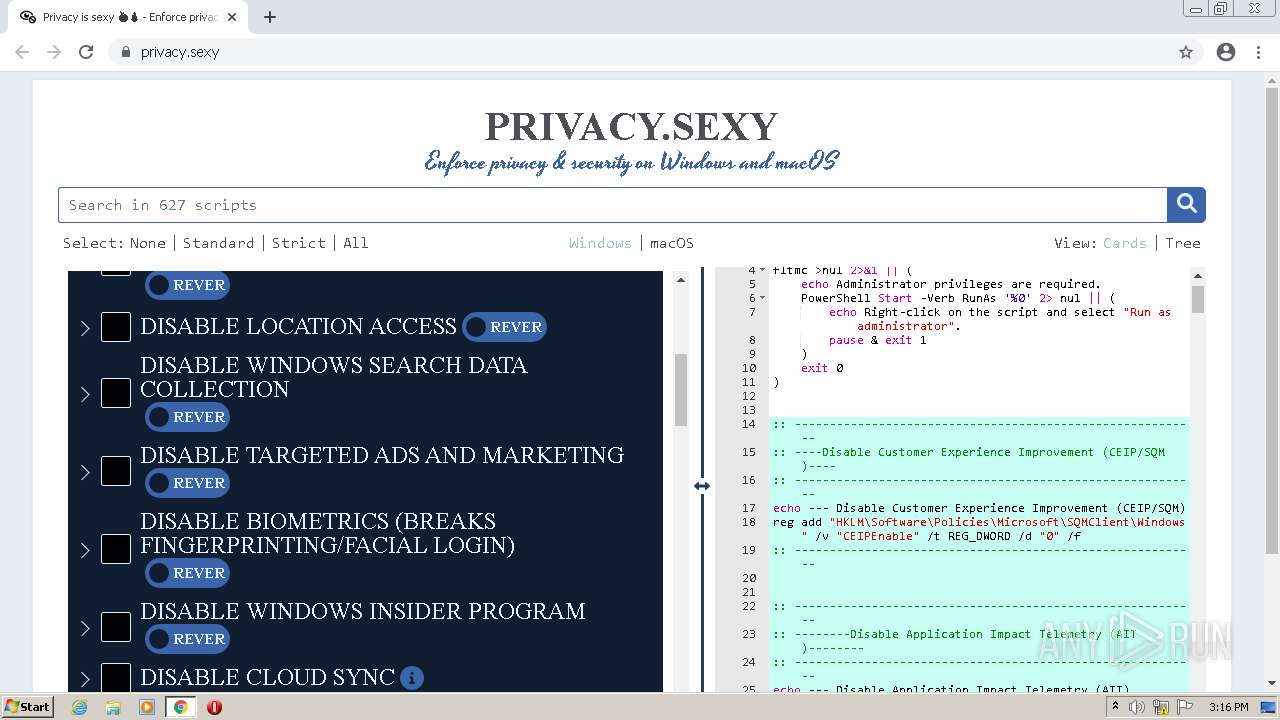
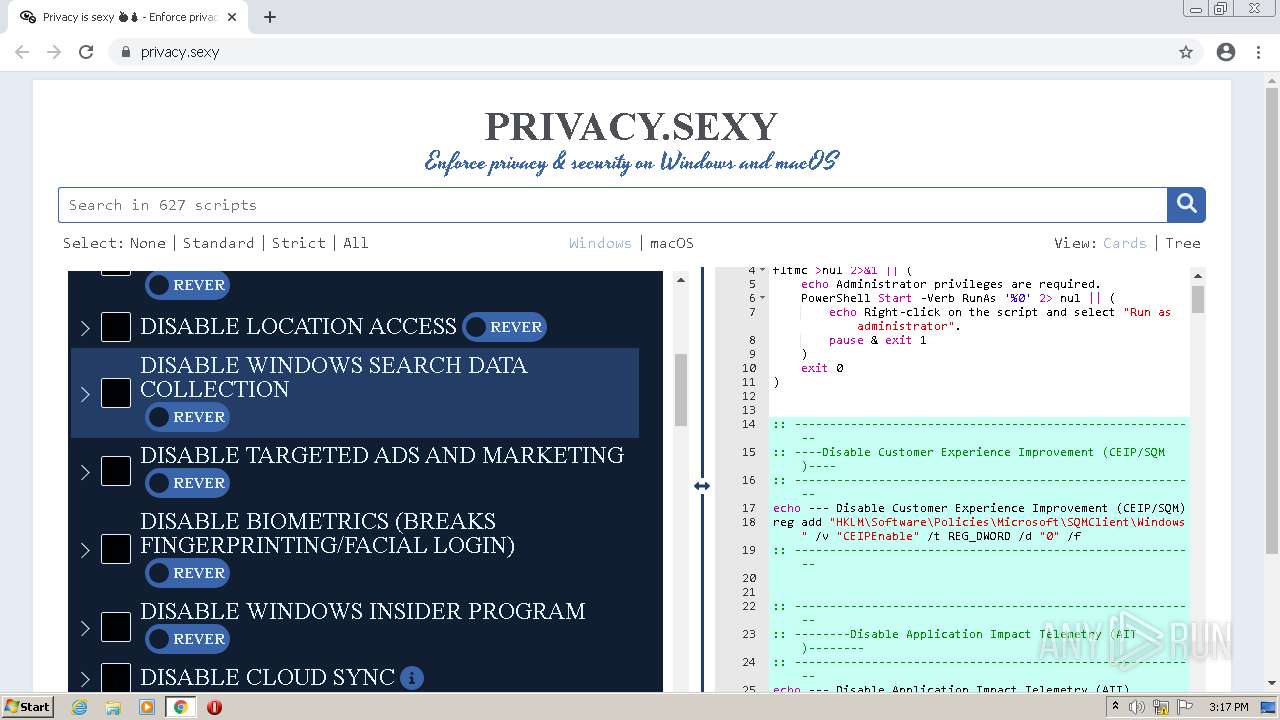
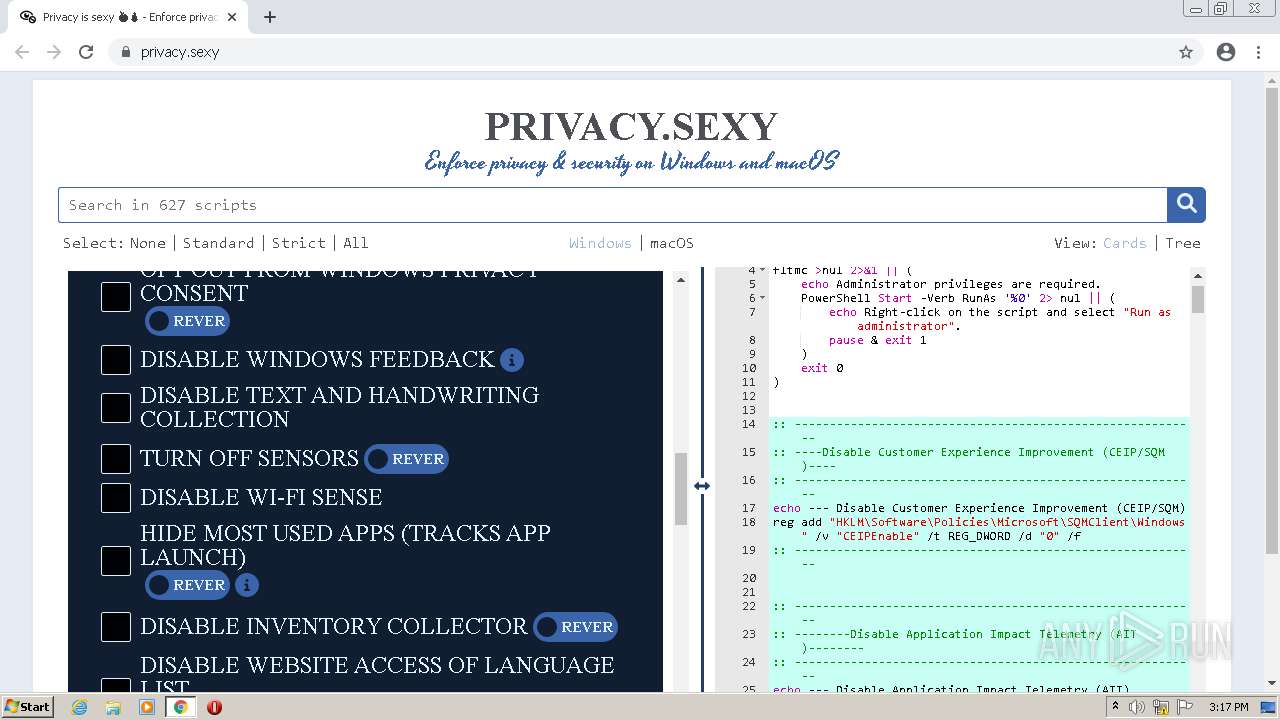
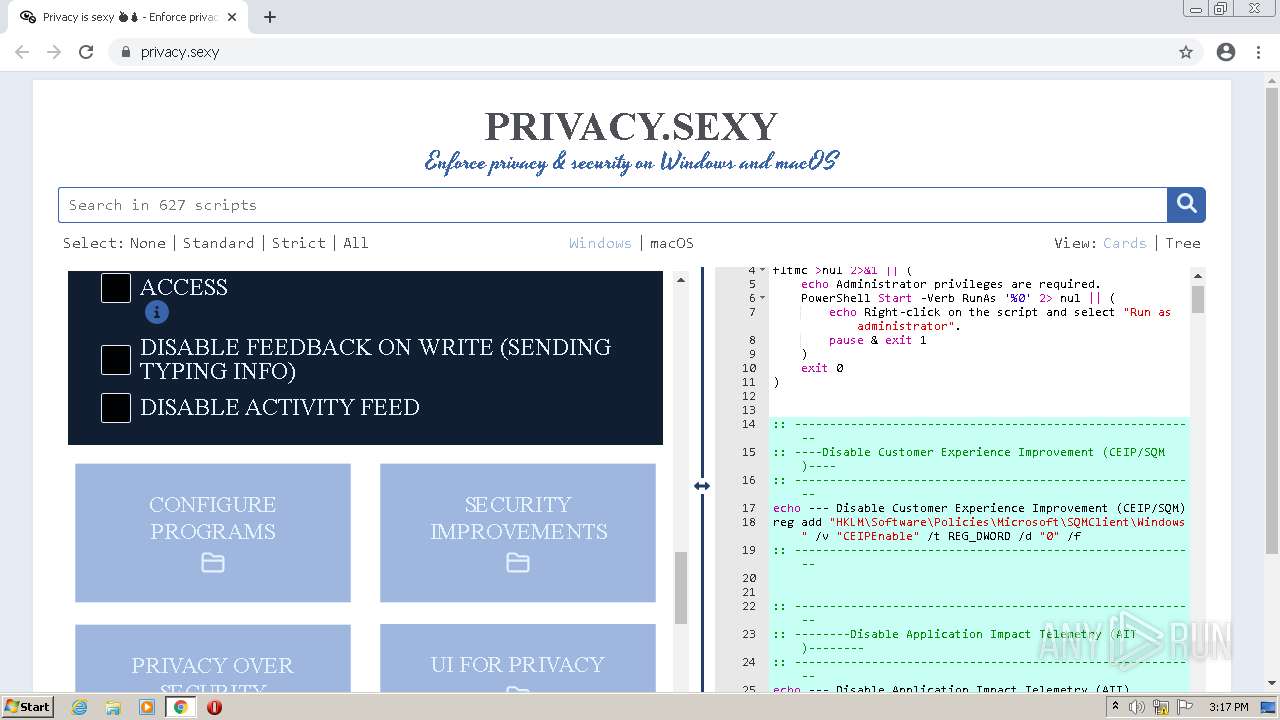
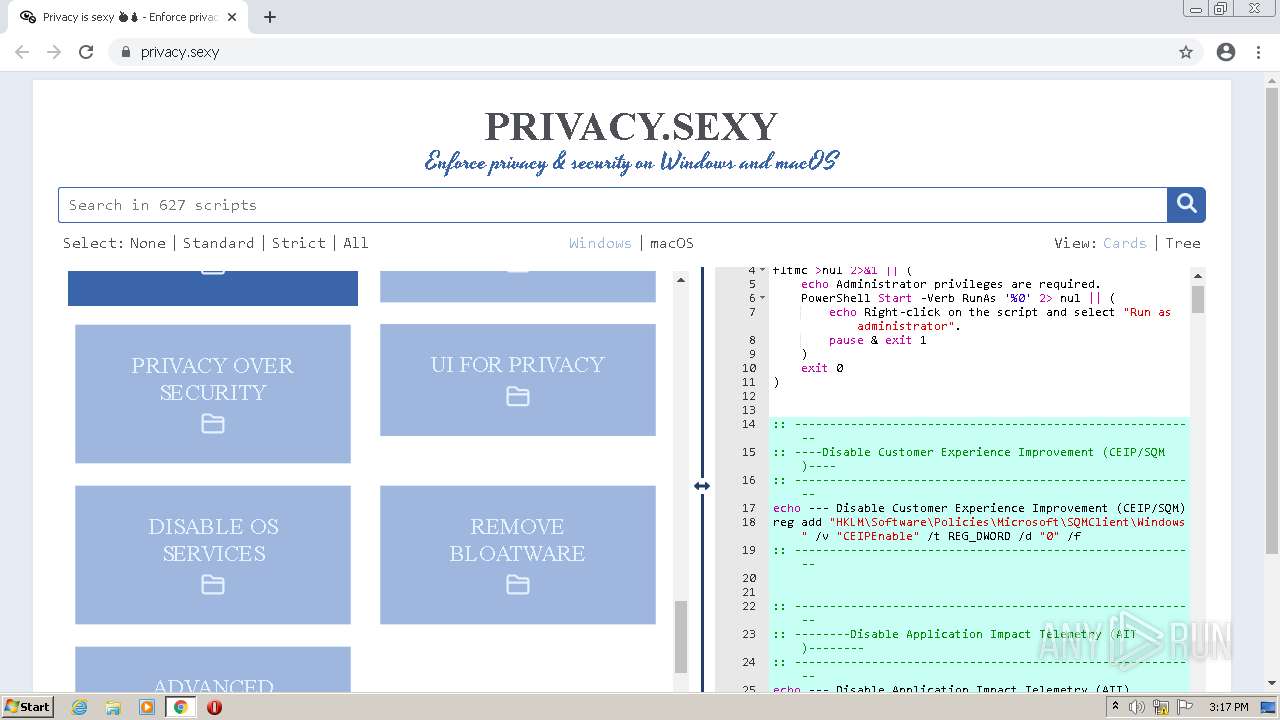
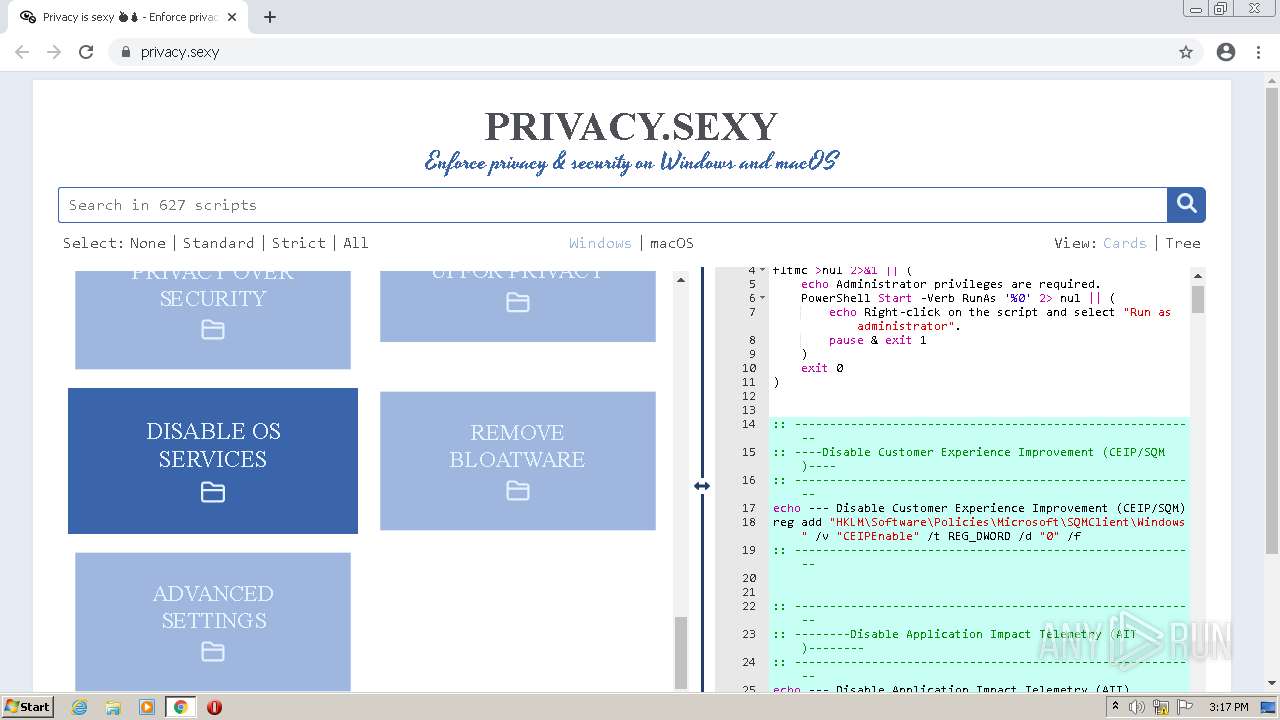
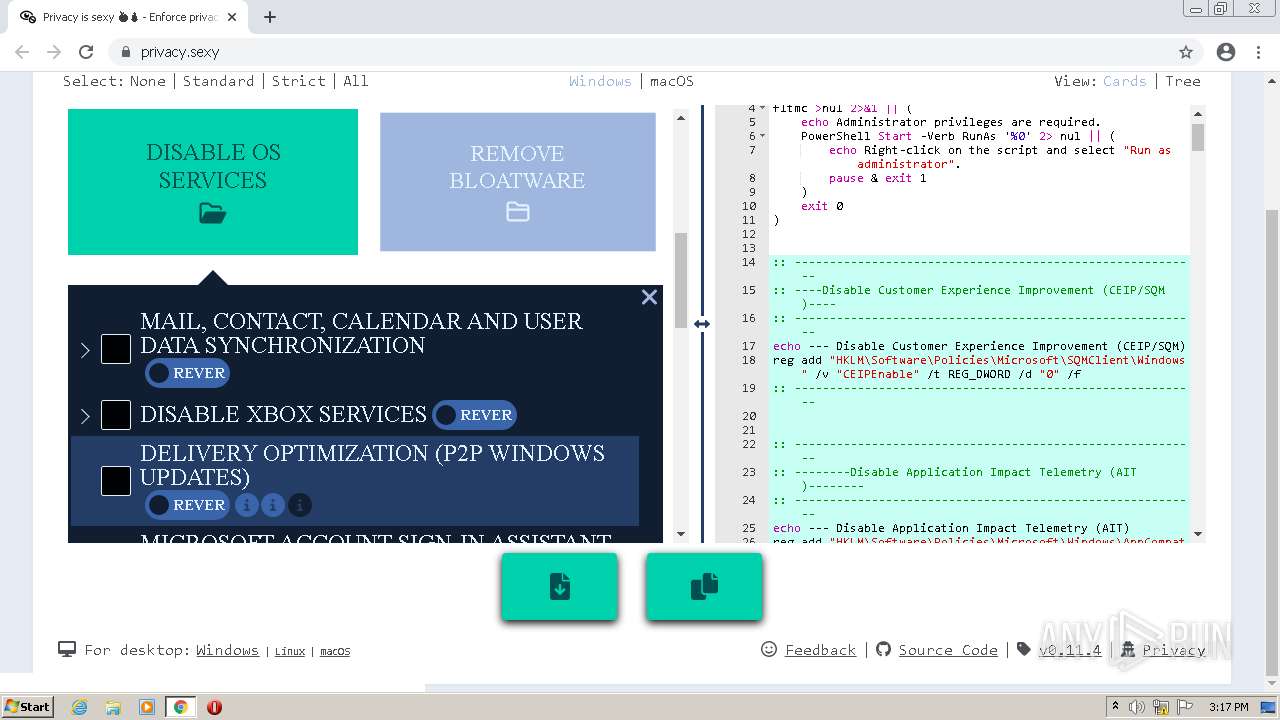
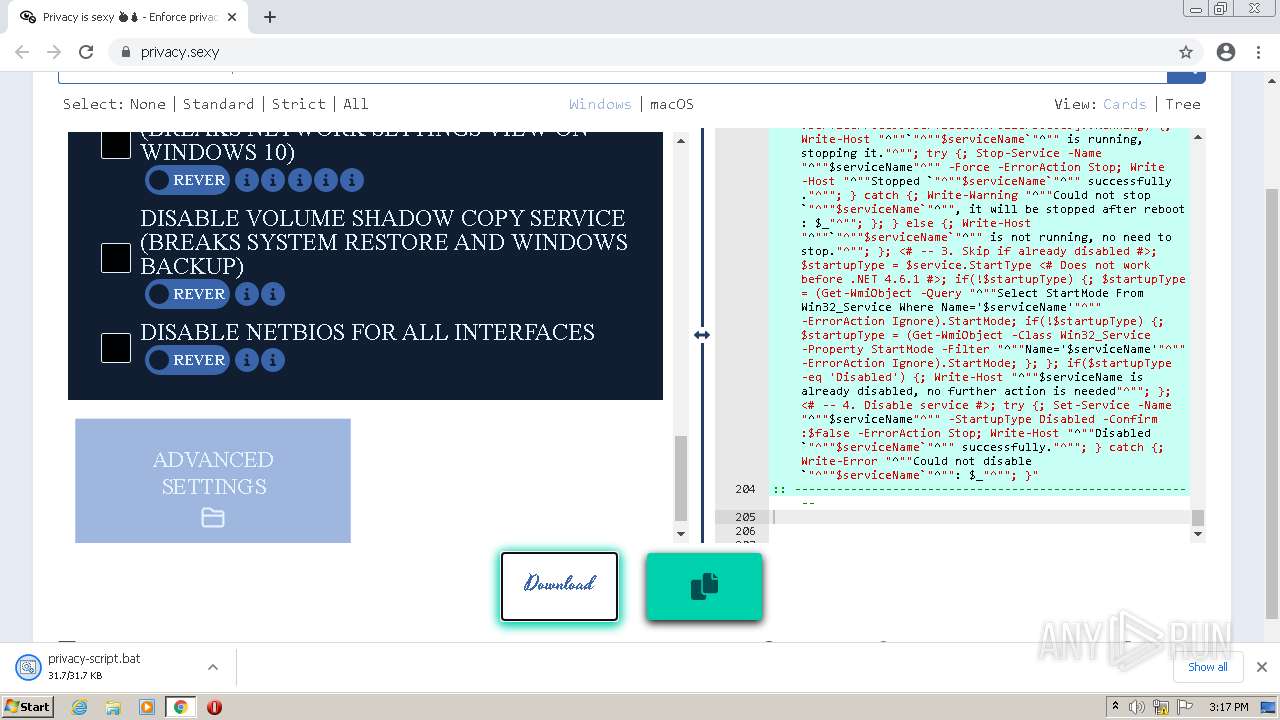
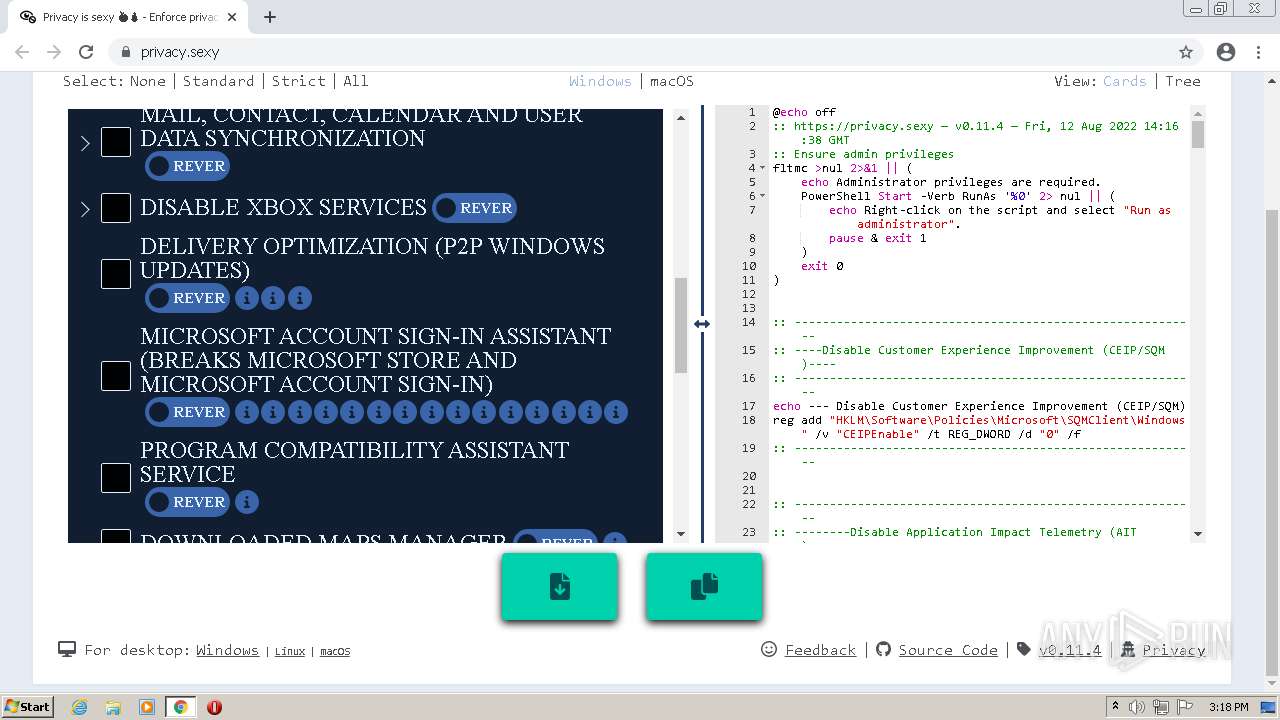
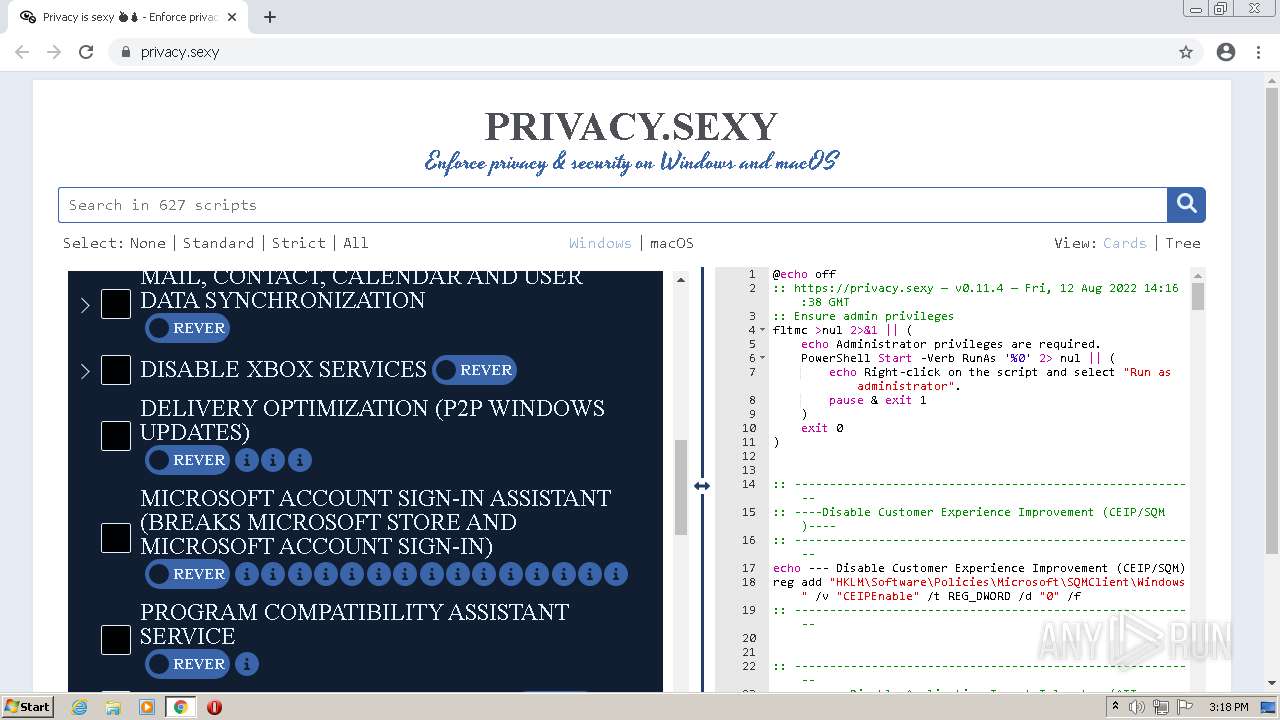
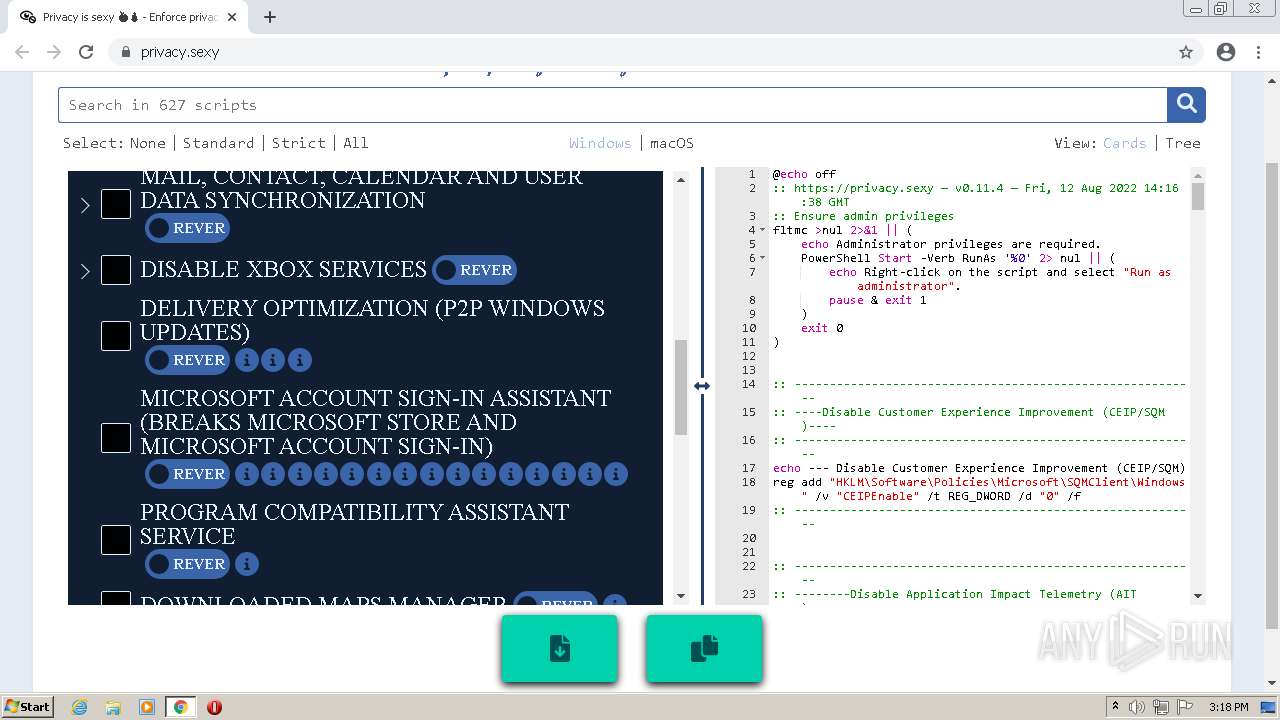
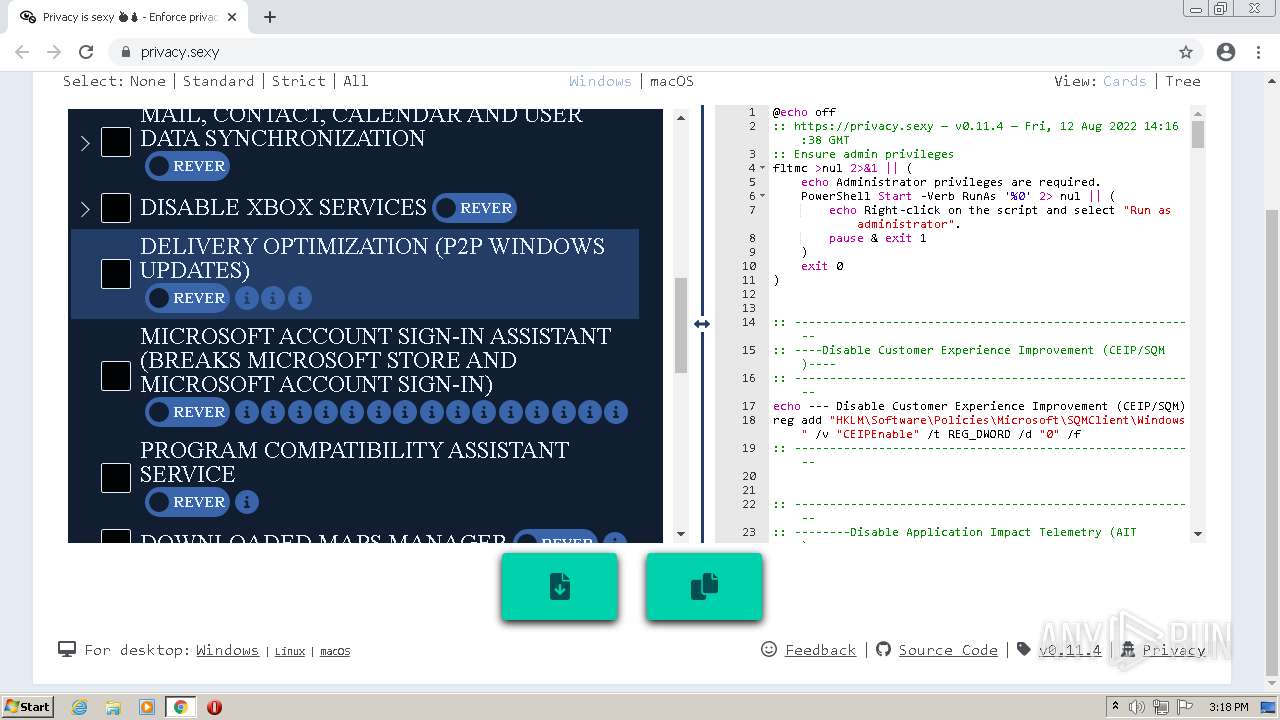
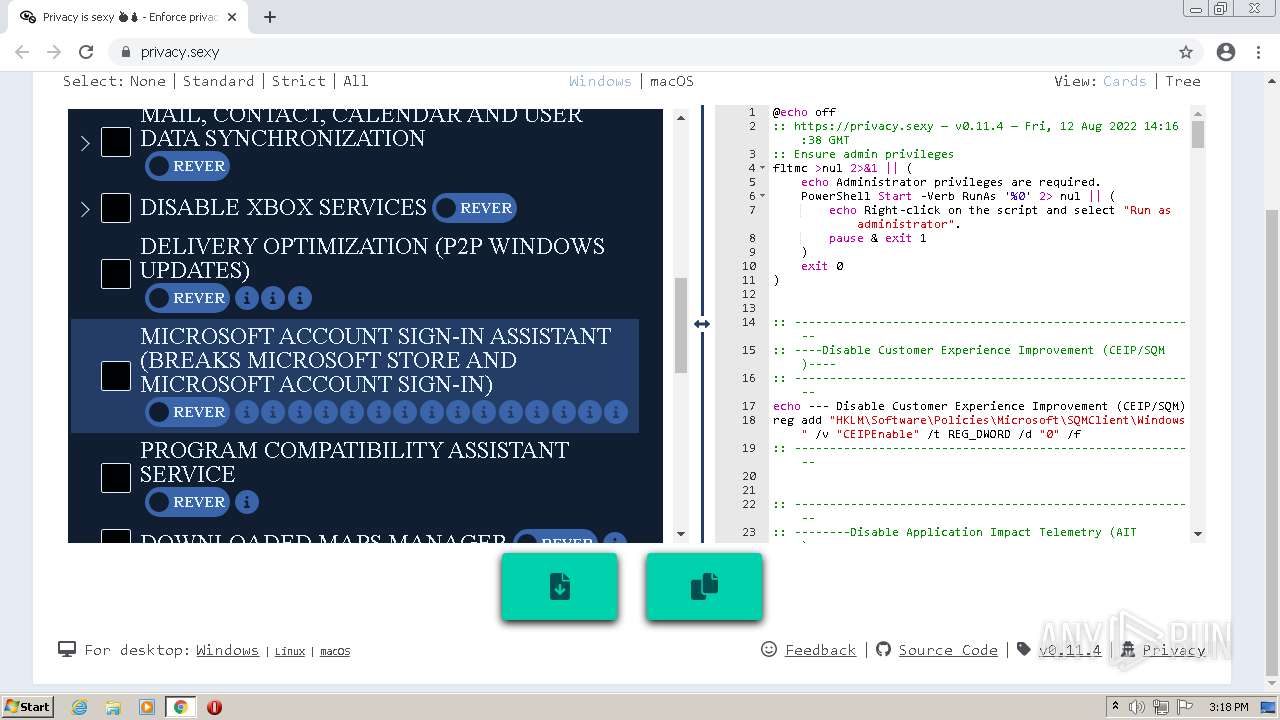
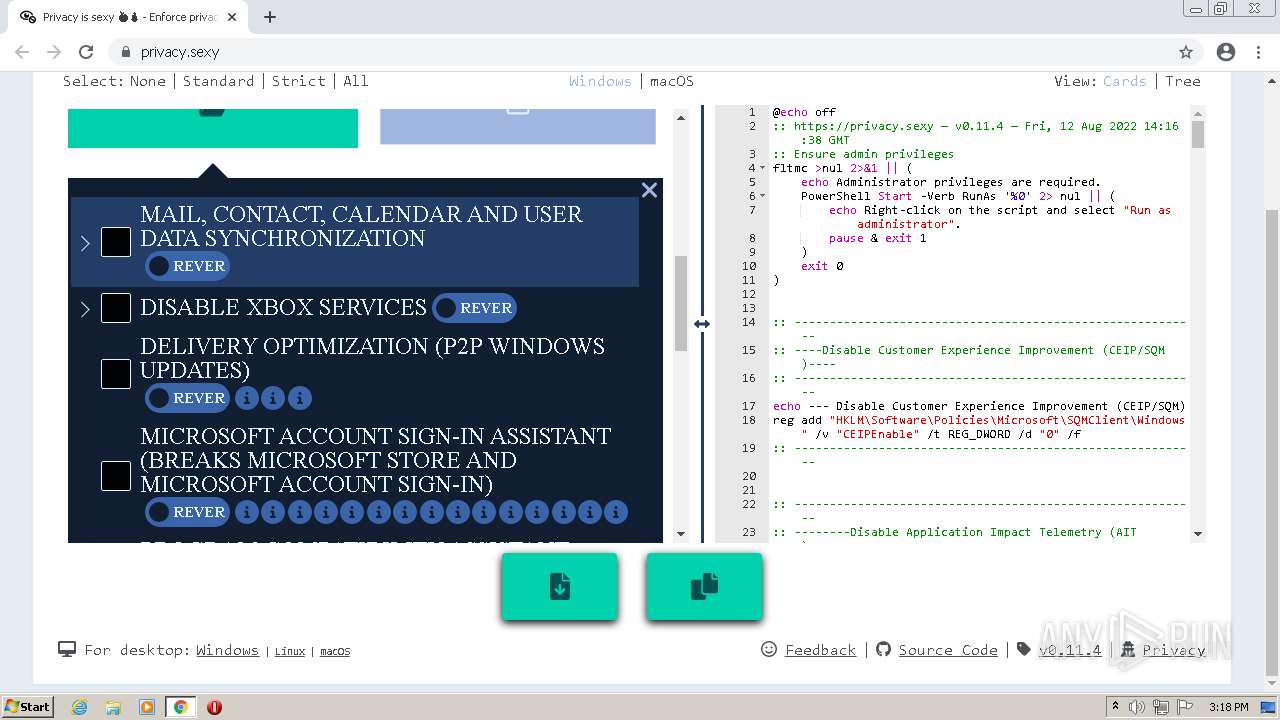
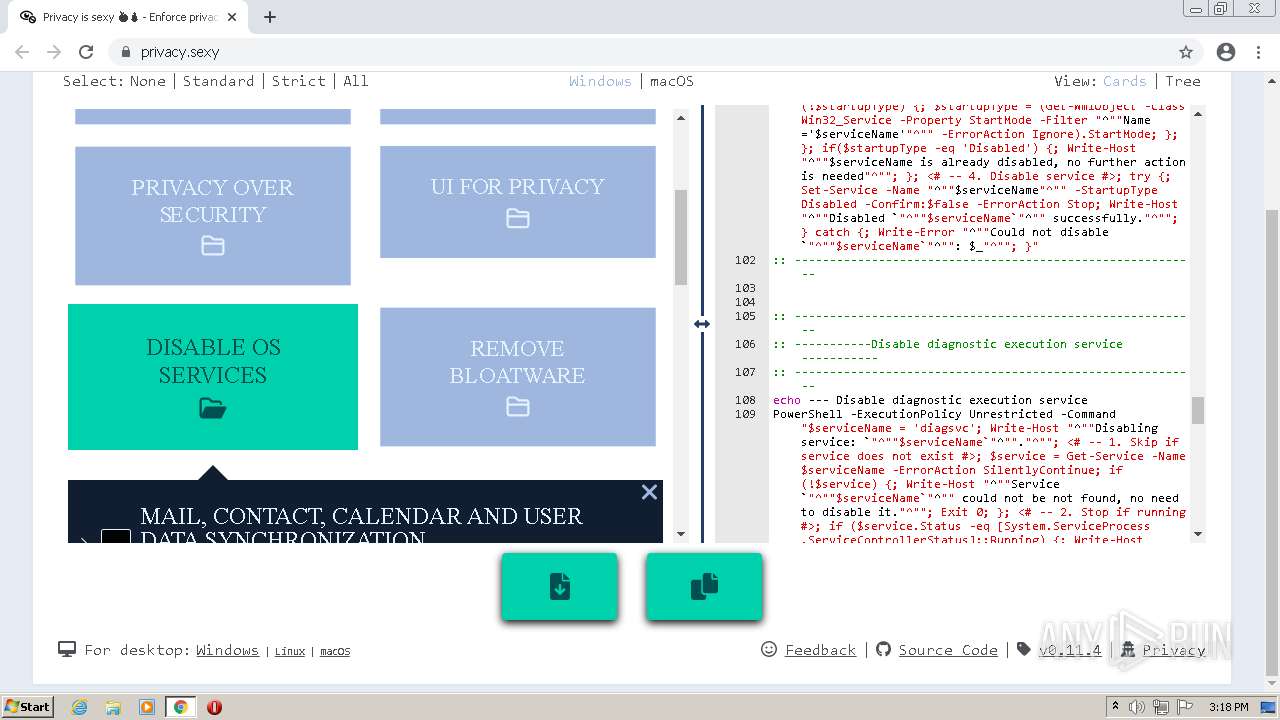
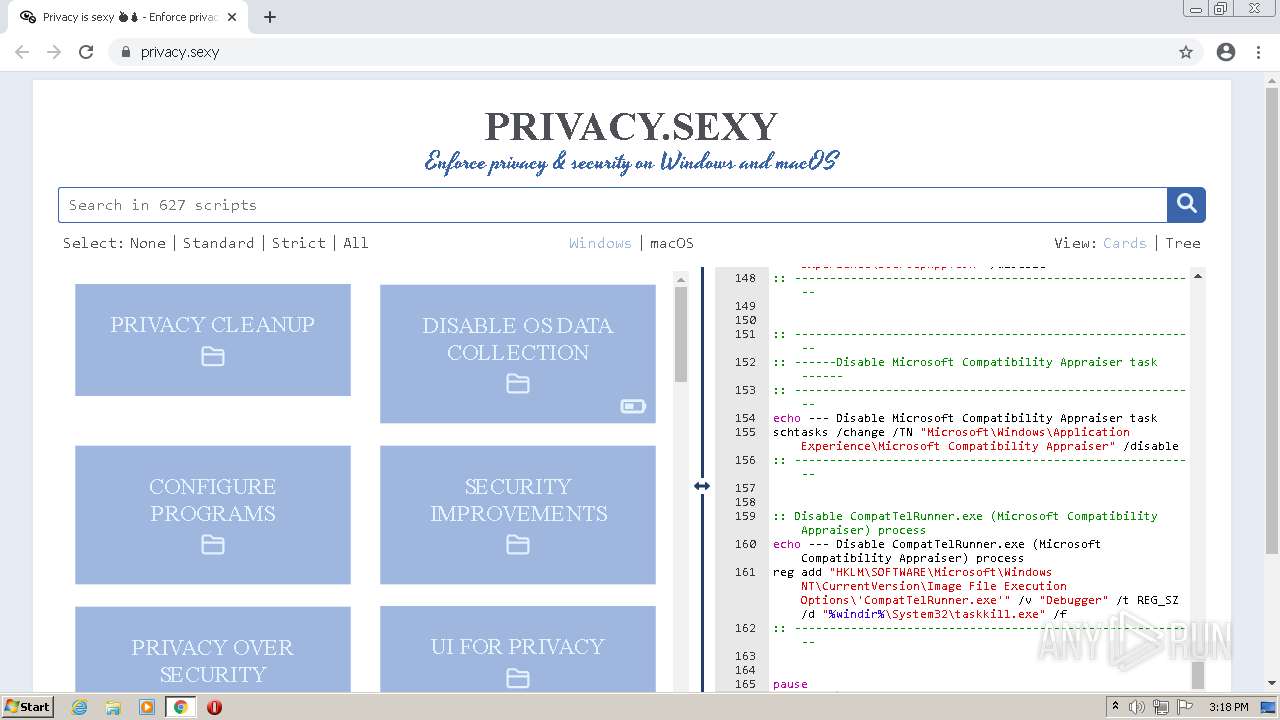
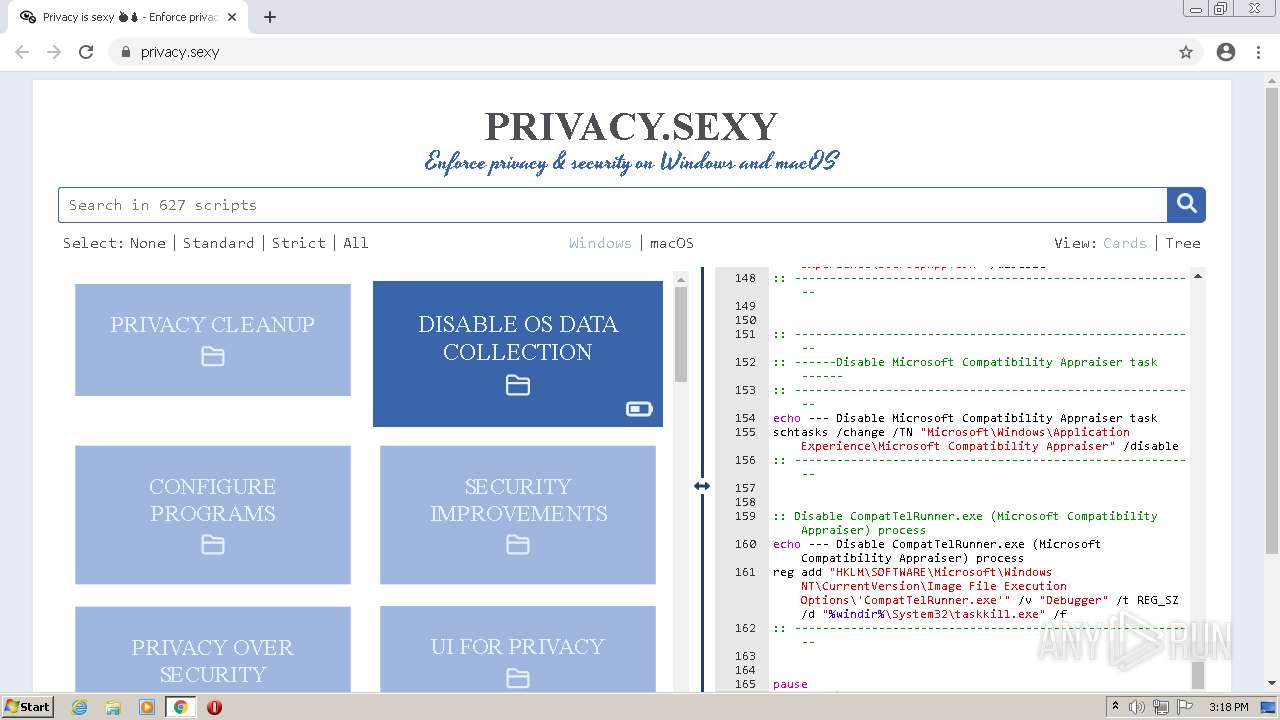
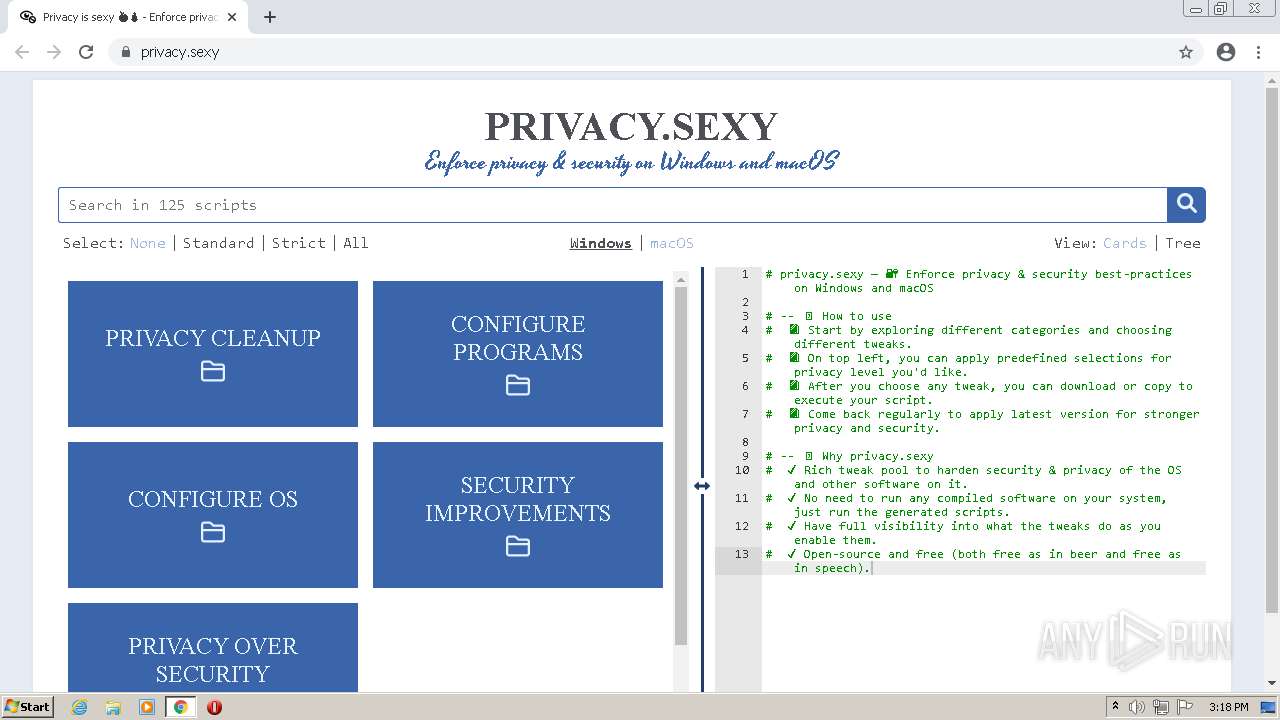
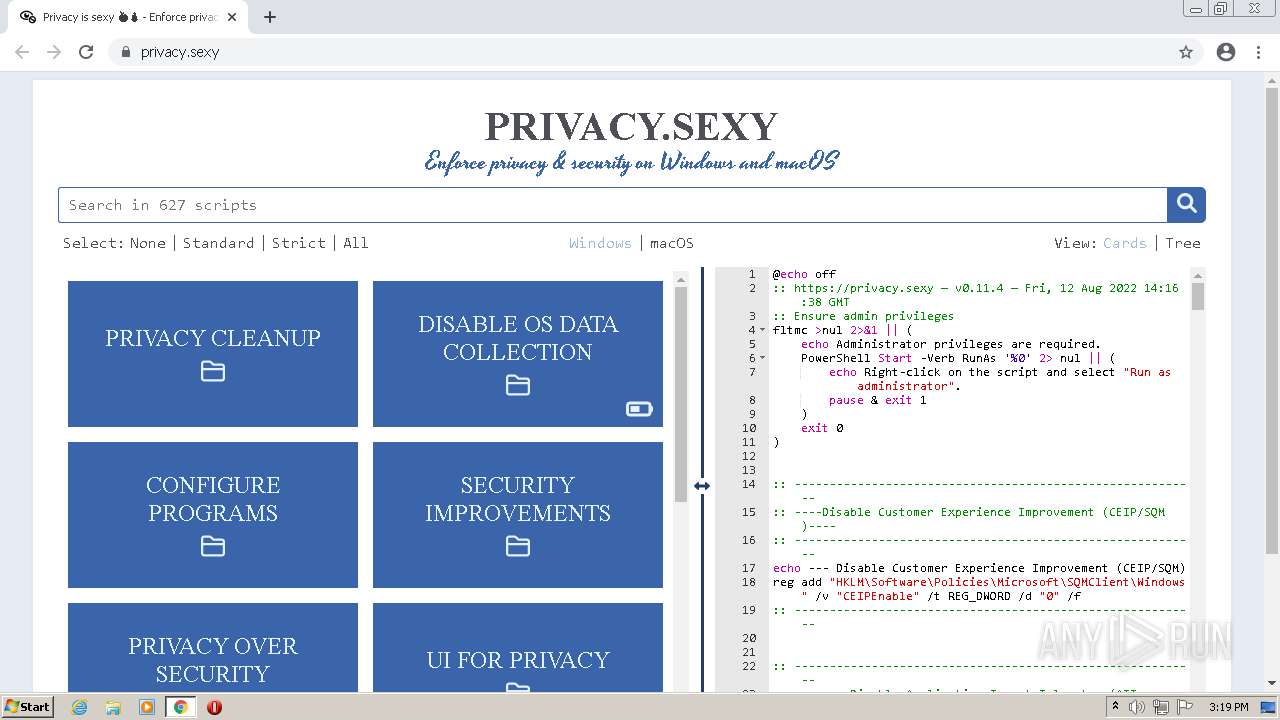
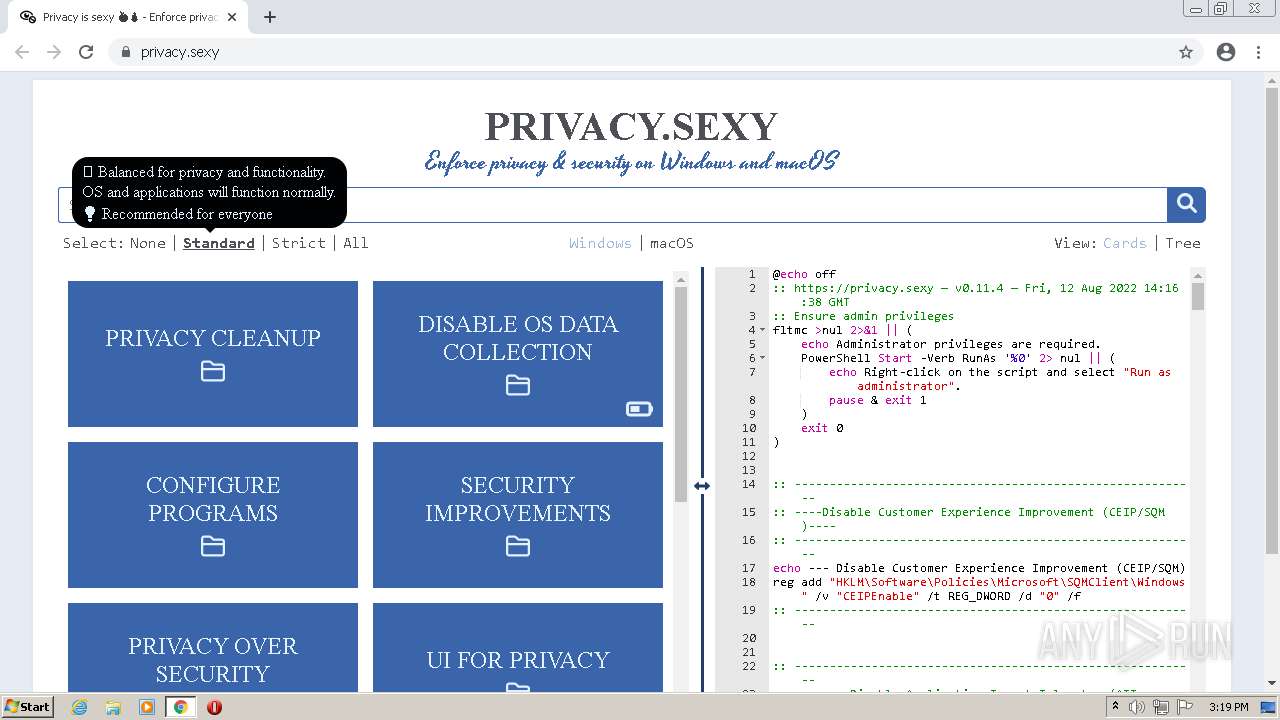
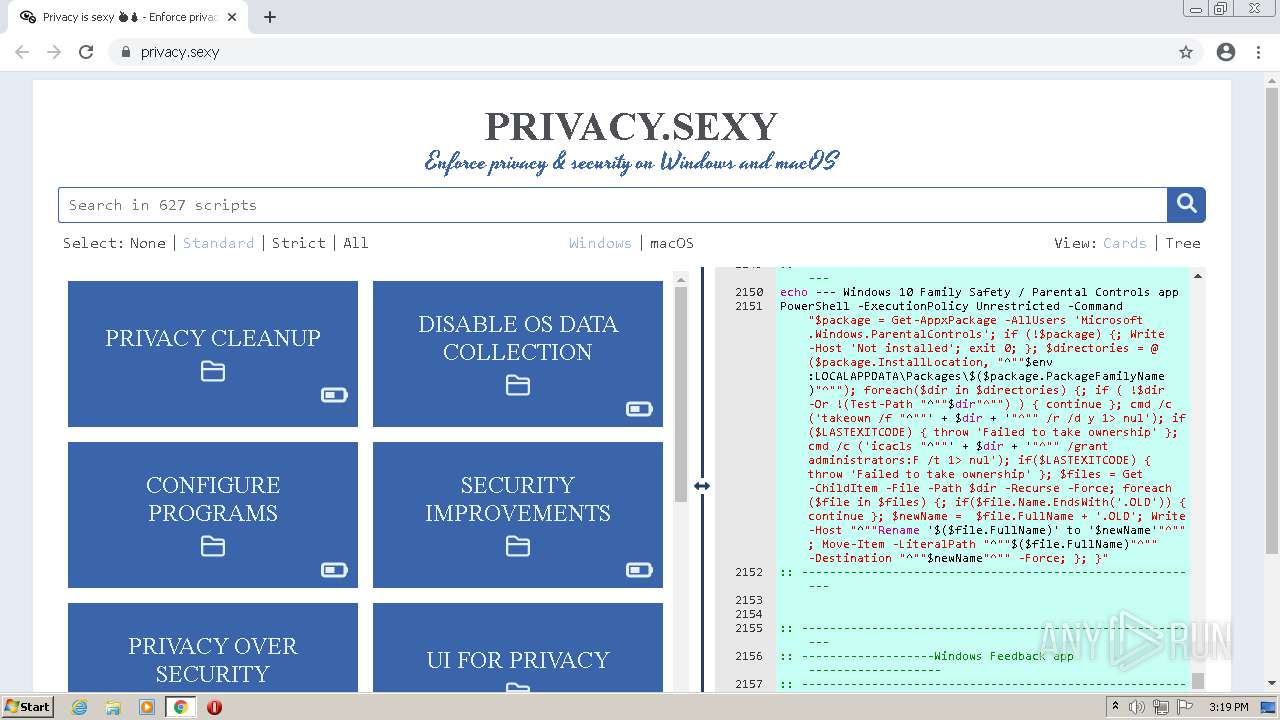
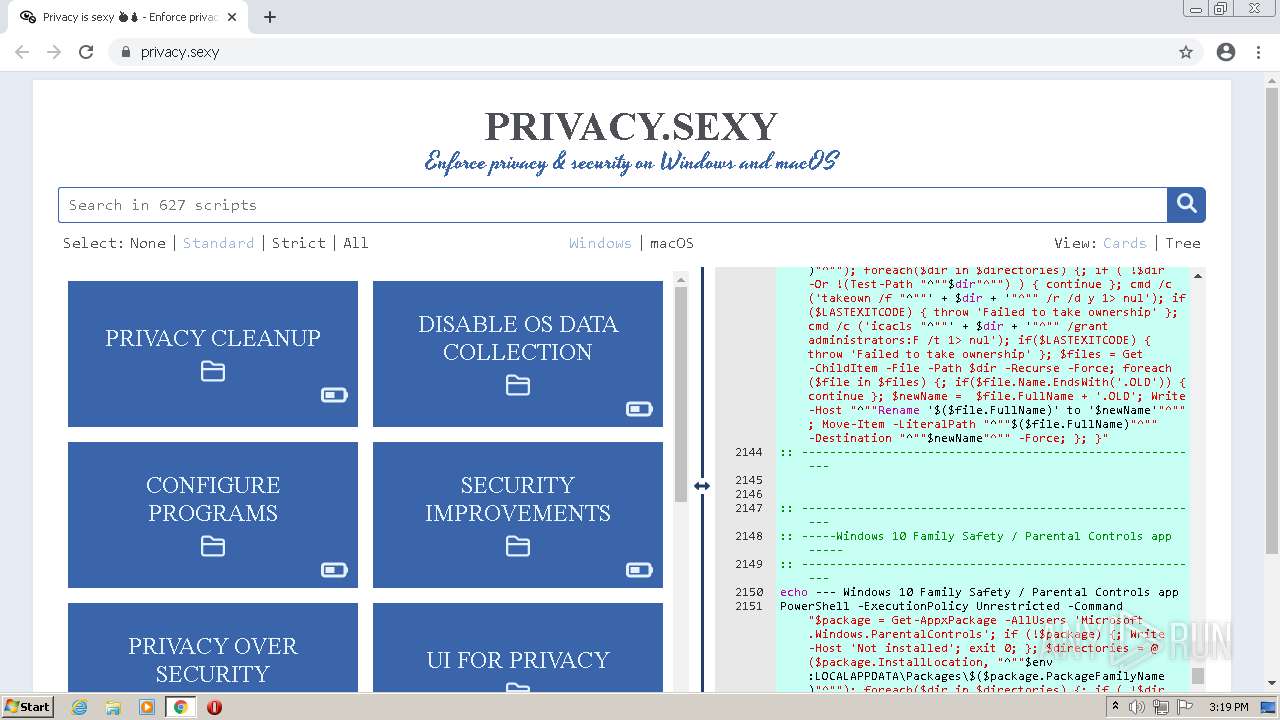
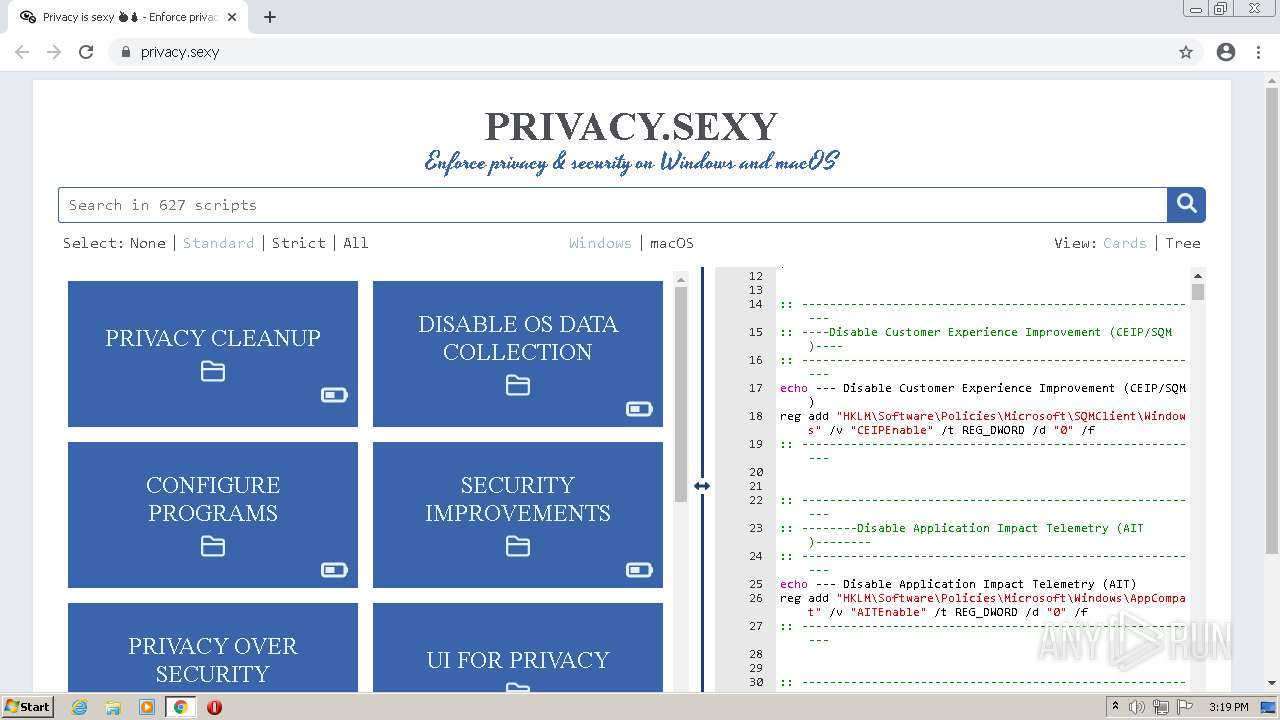
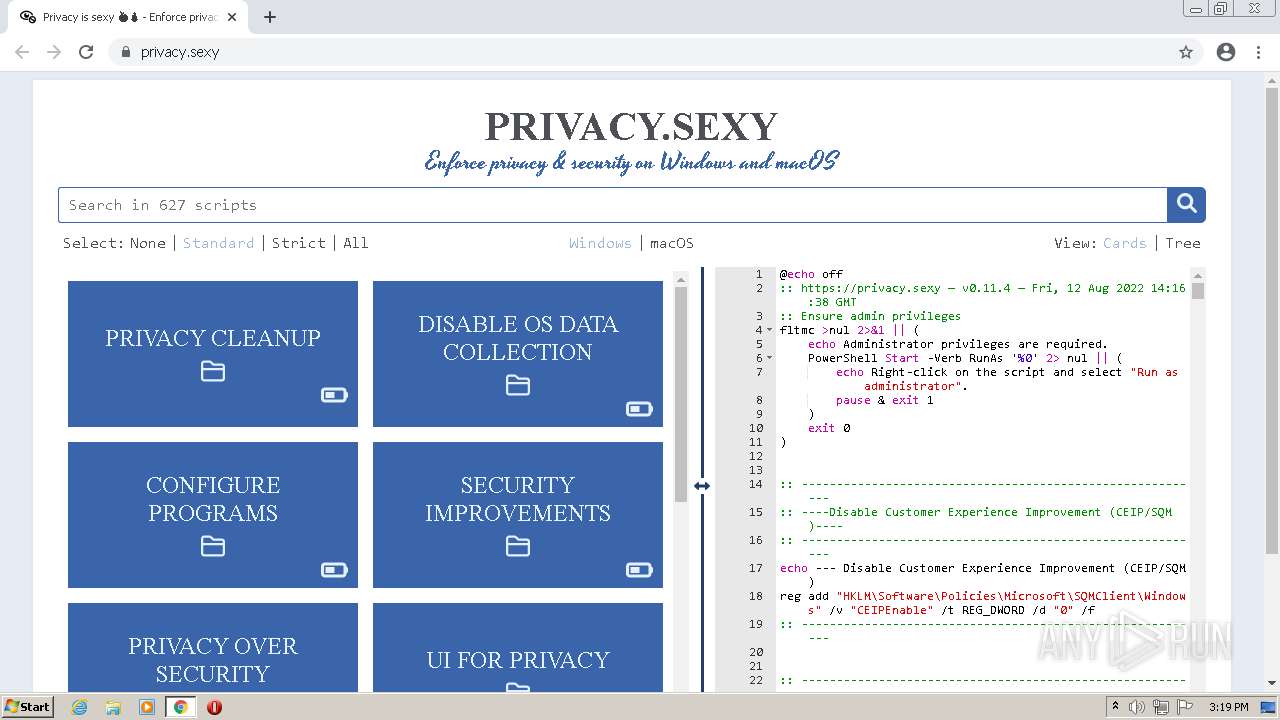
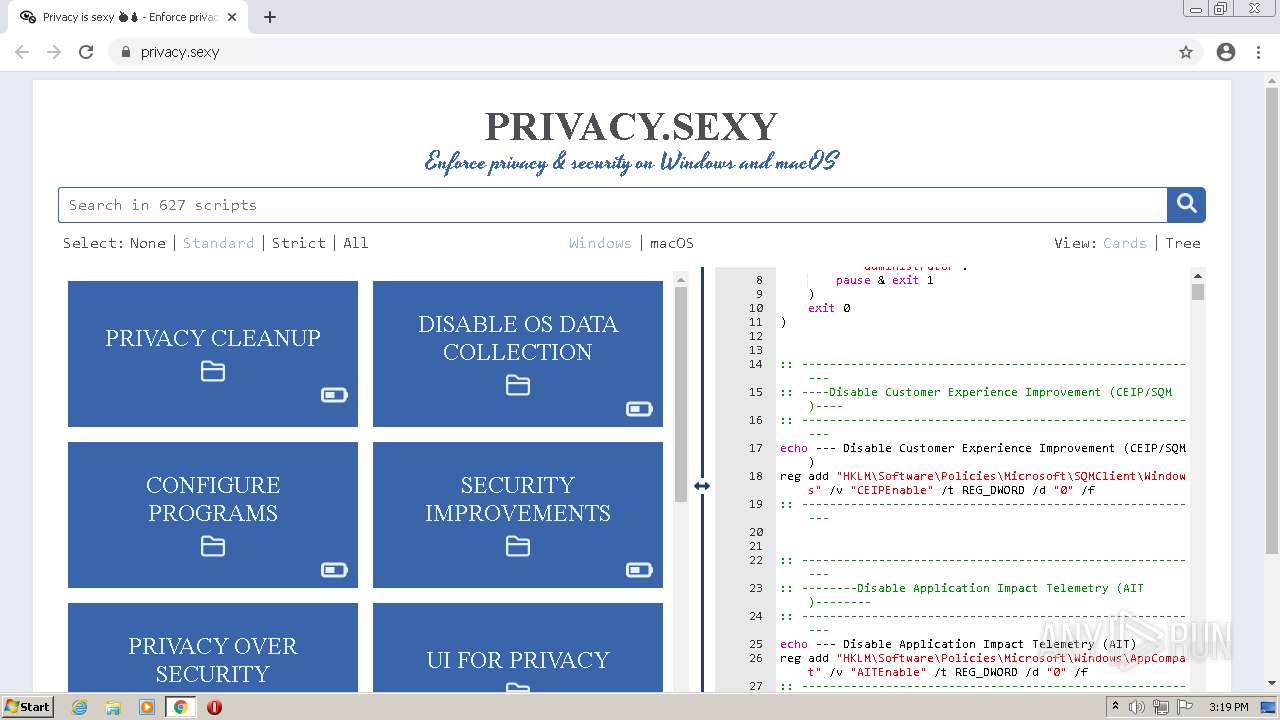
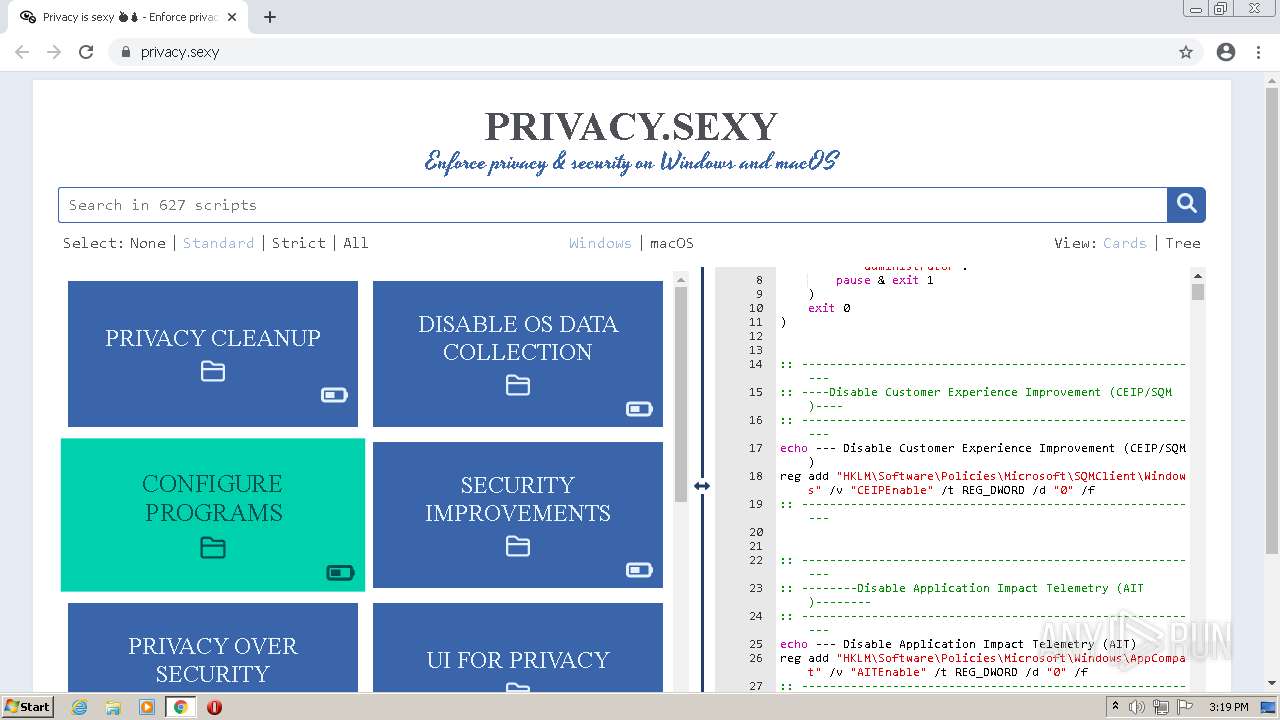
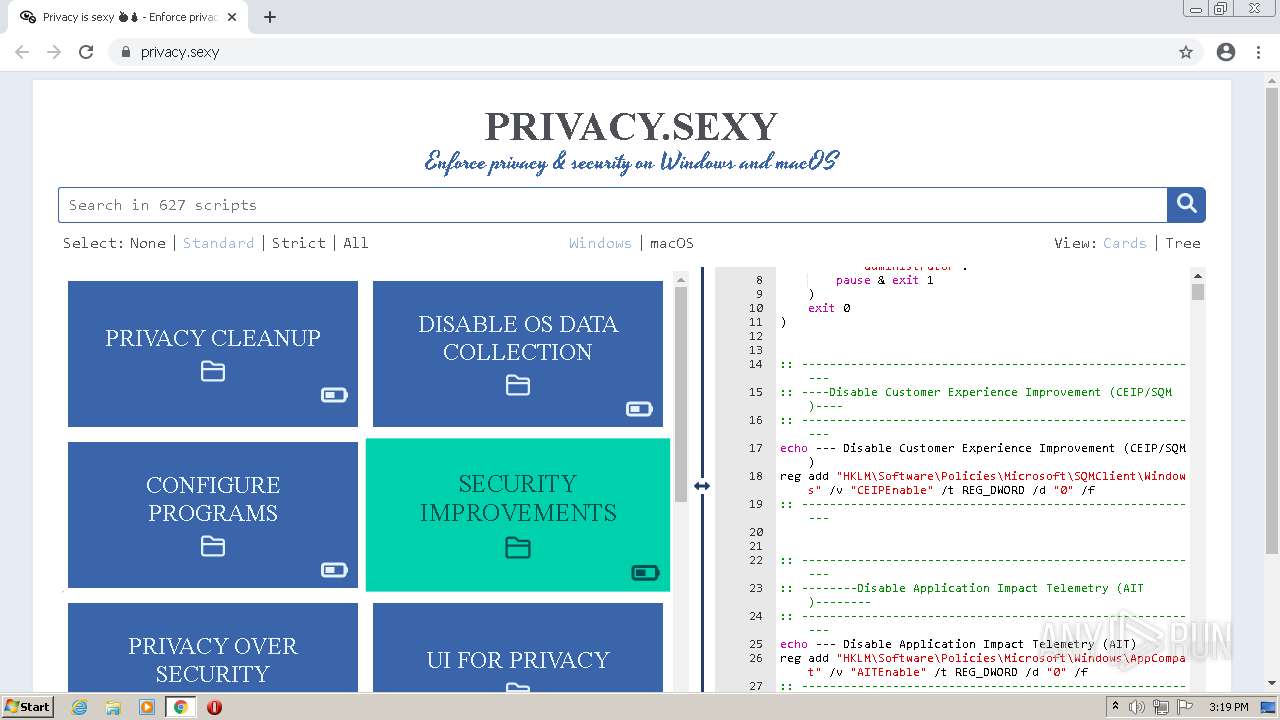
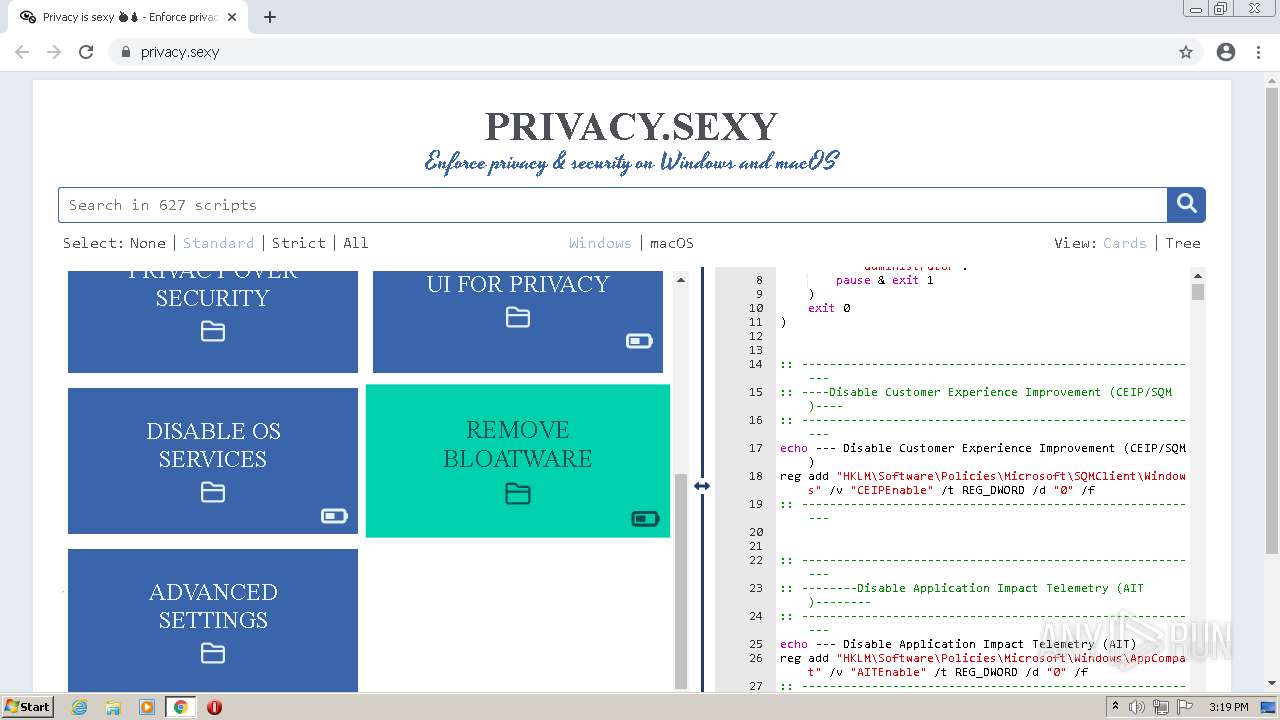
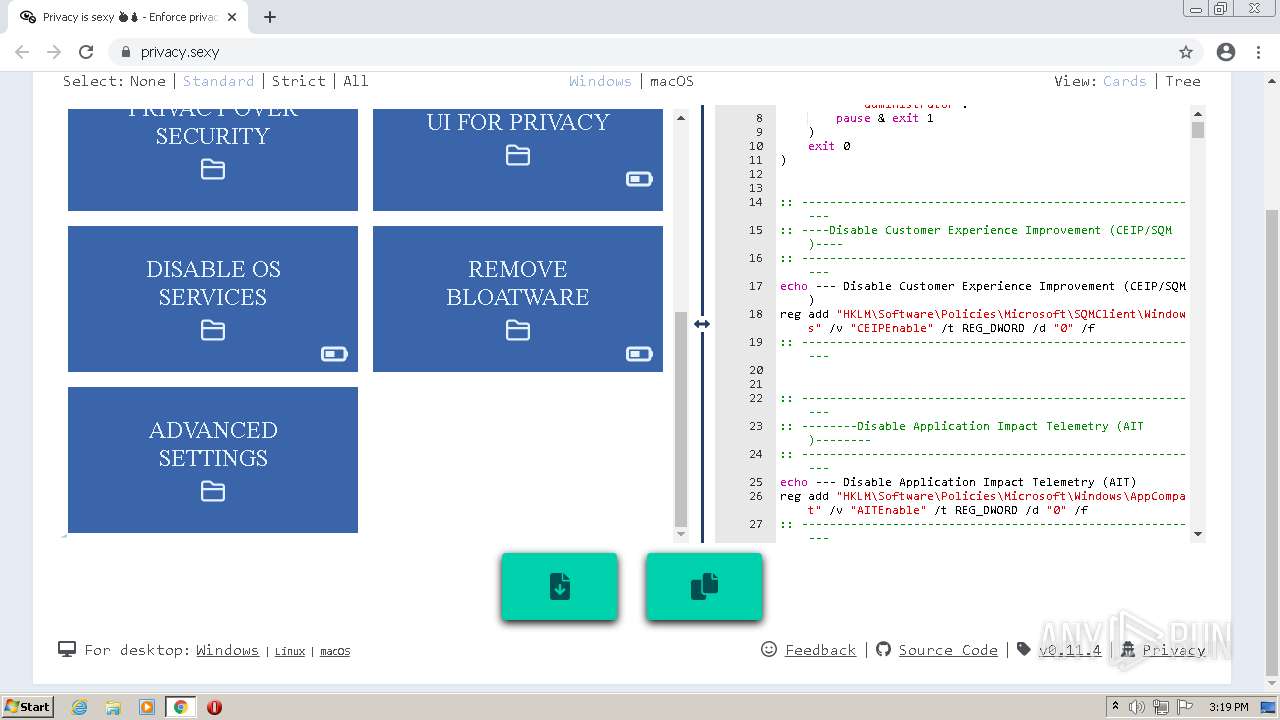
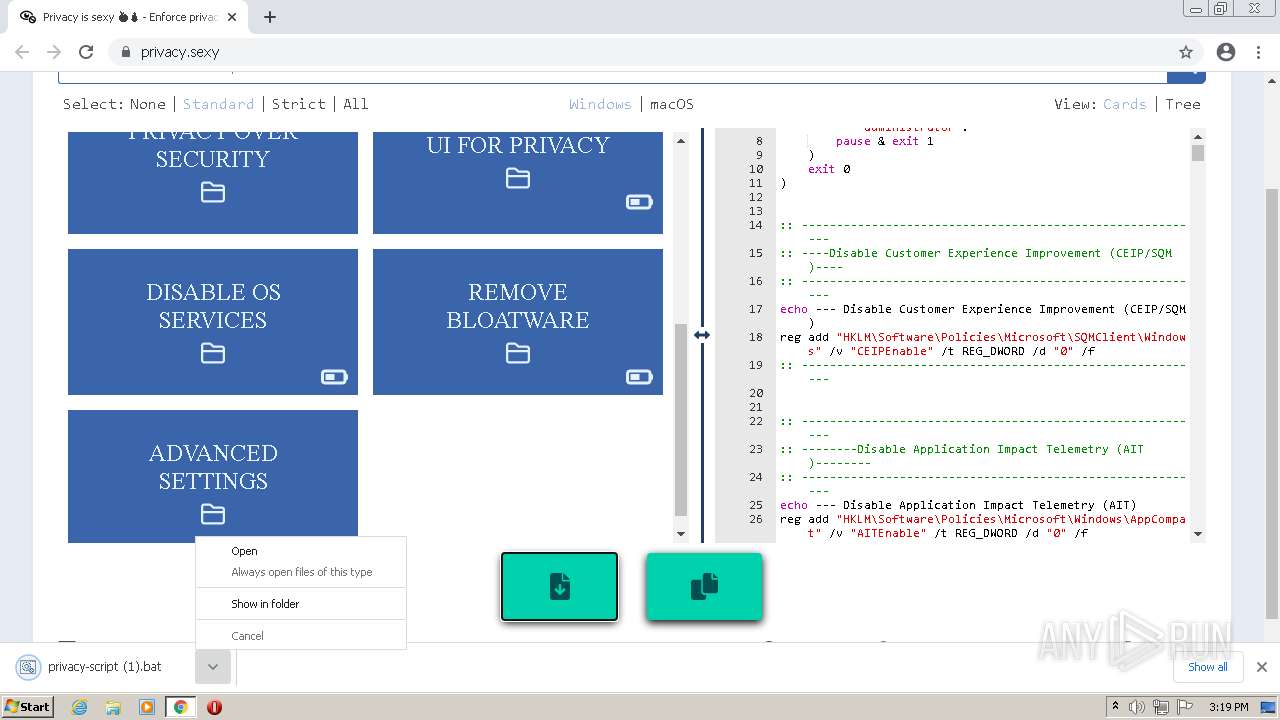
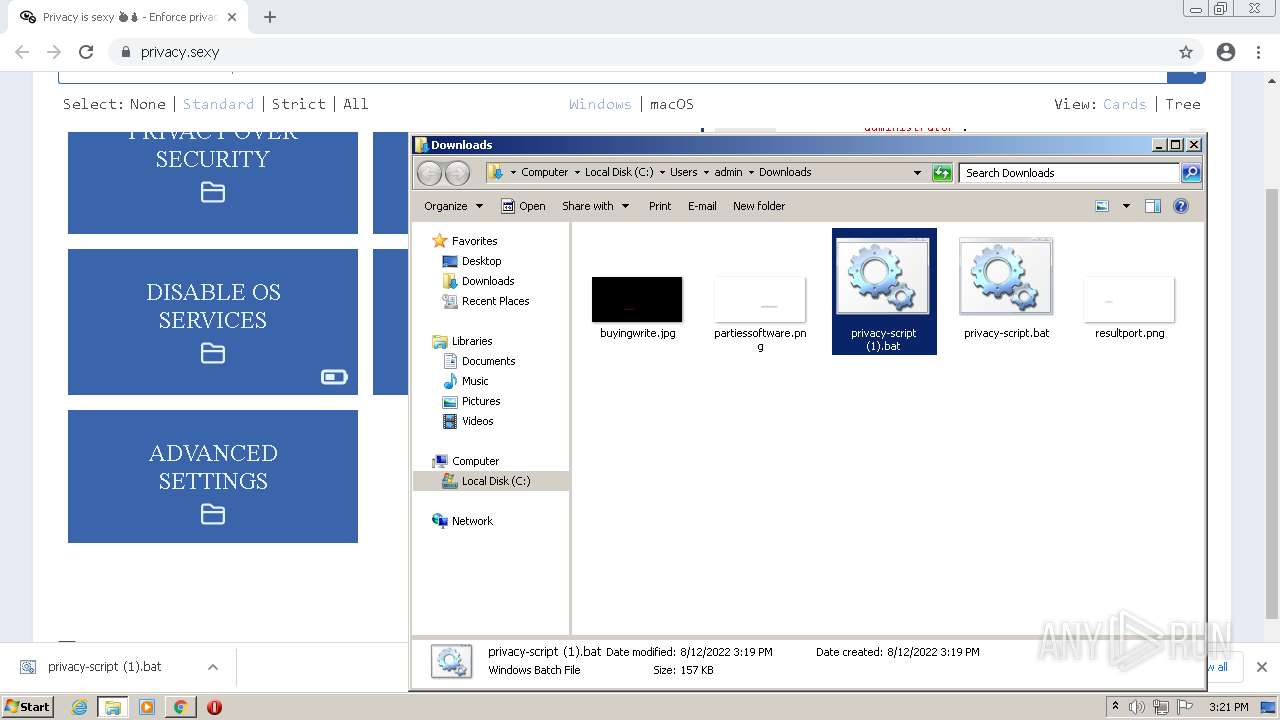
| URL: | https://privacy.sexy/ |
| Full analysis: | https://app.any.run/tasks/4bd68174-5170-4b4f-b8c2-2f1f04001dfb |
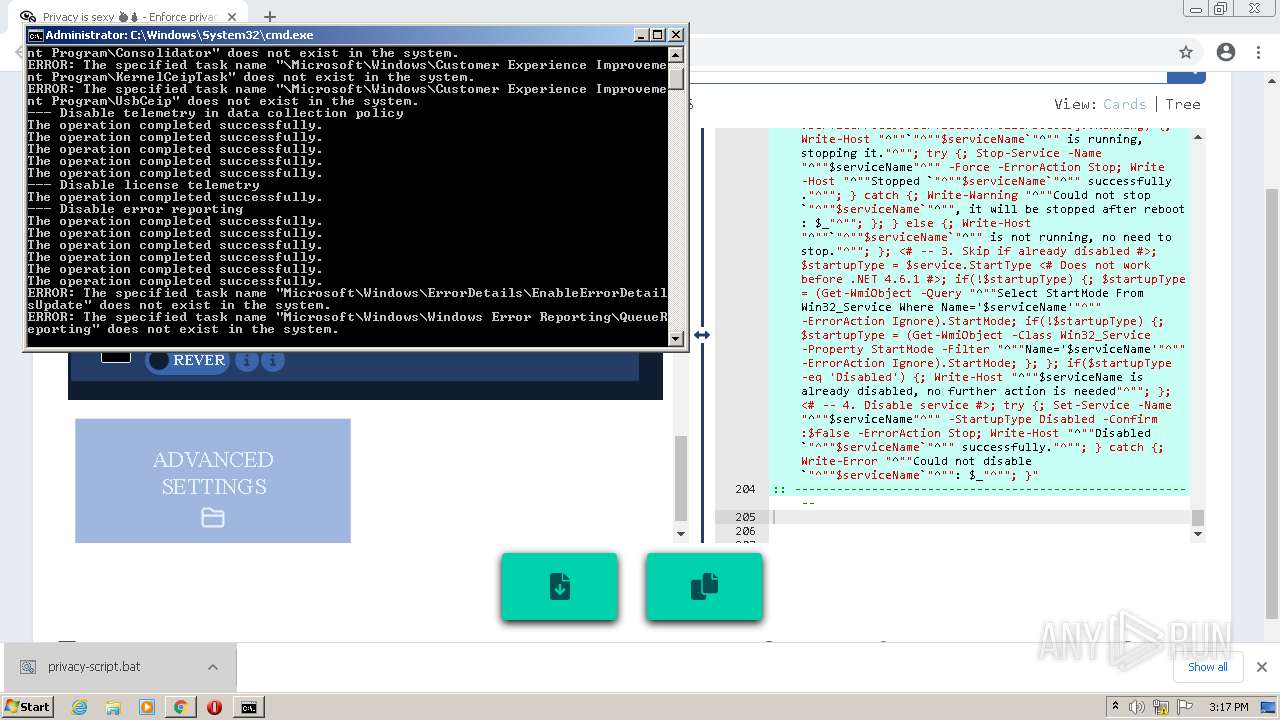
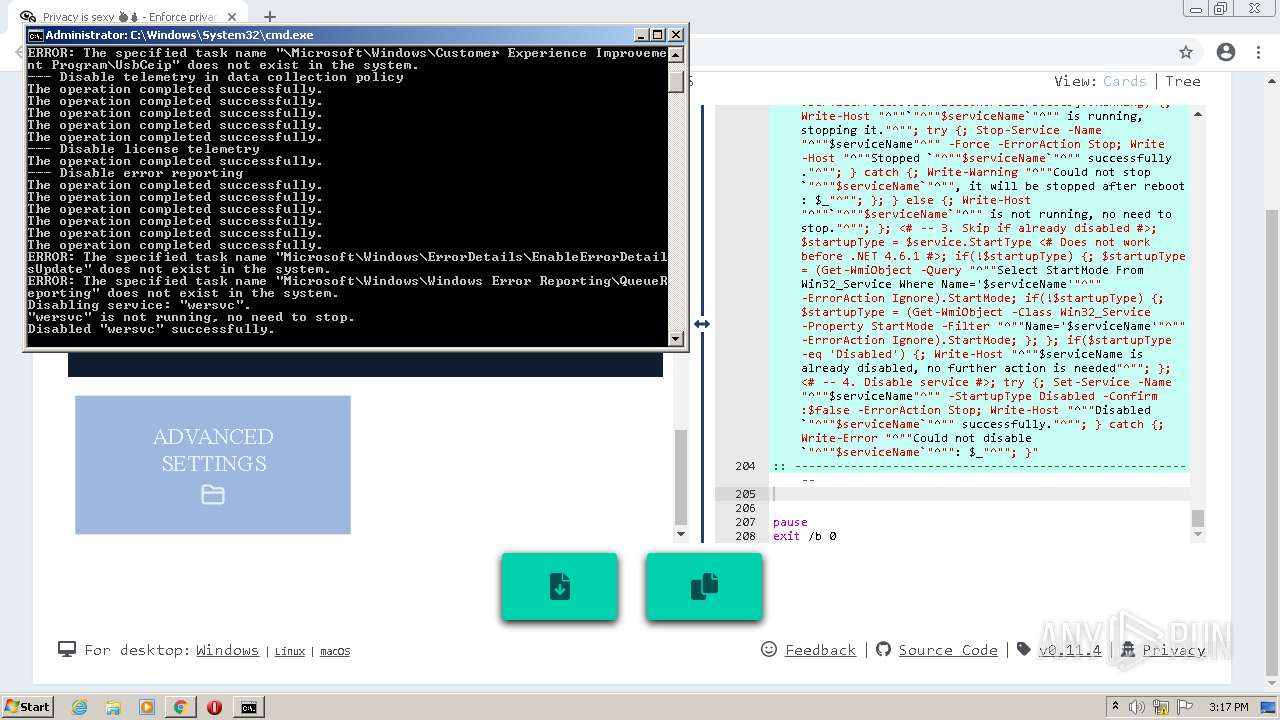
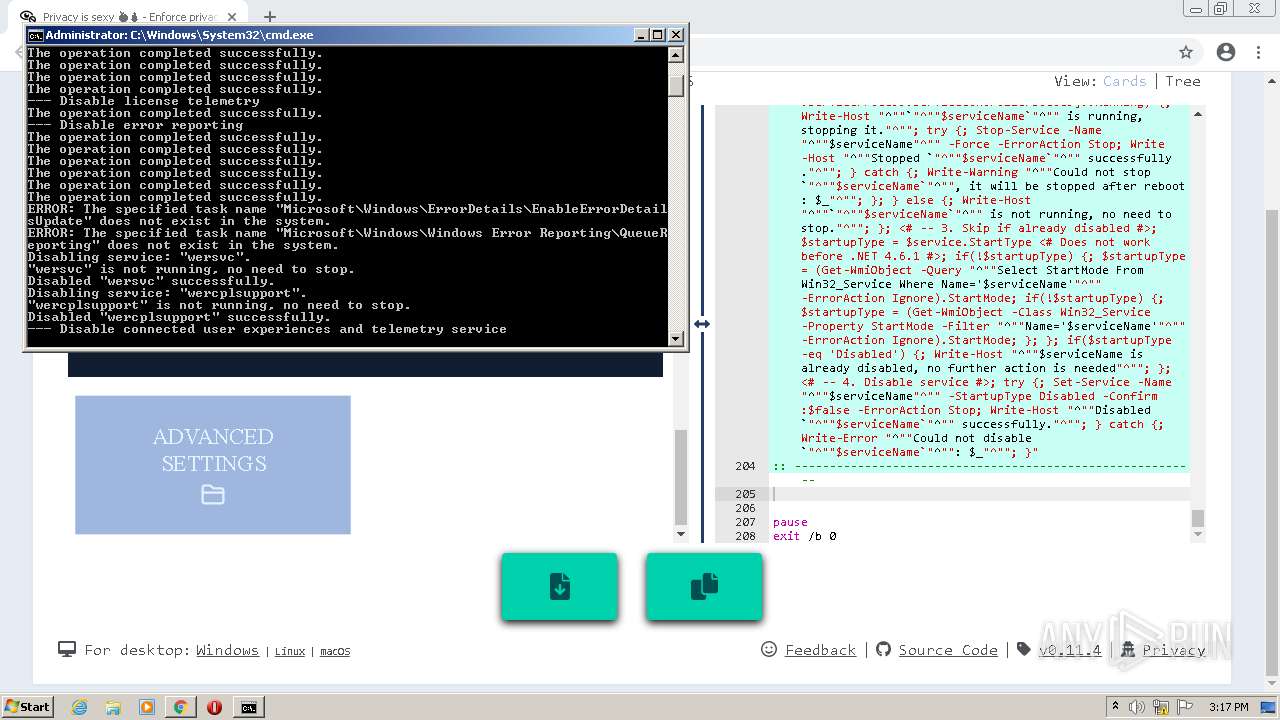
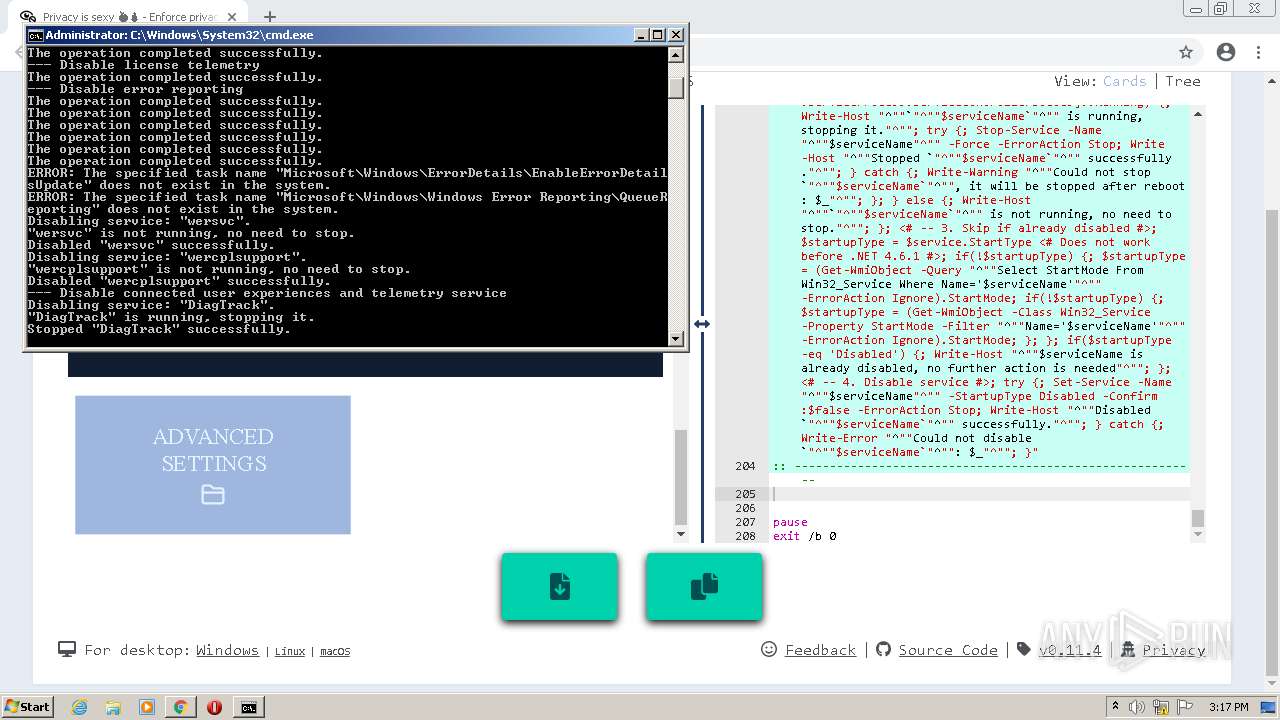
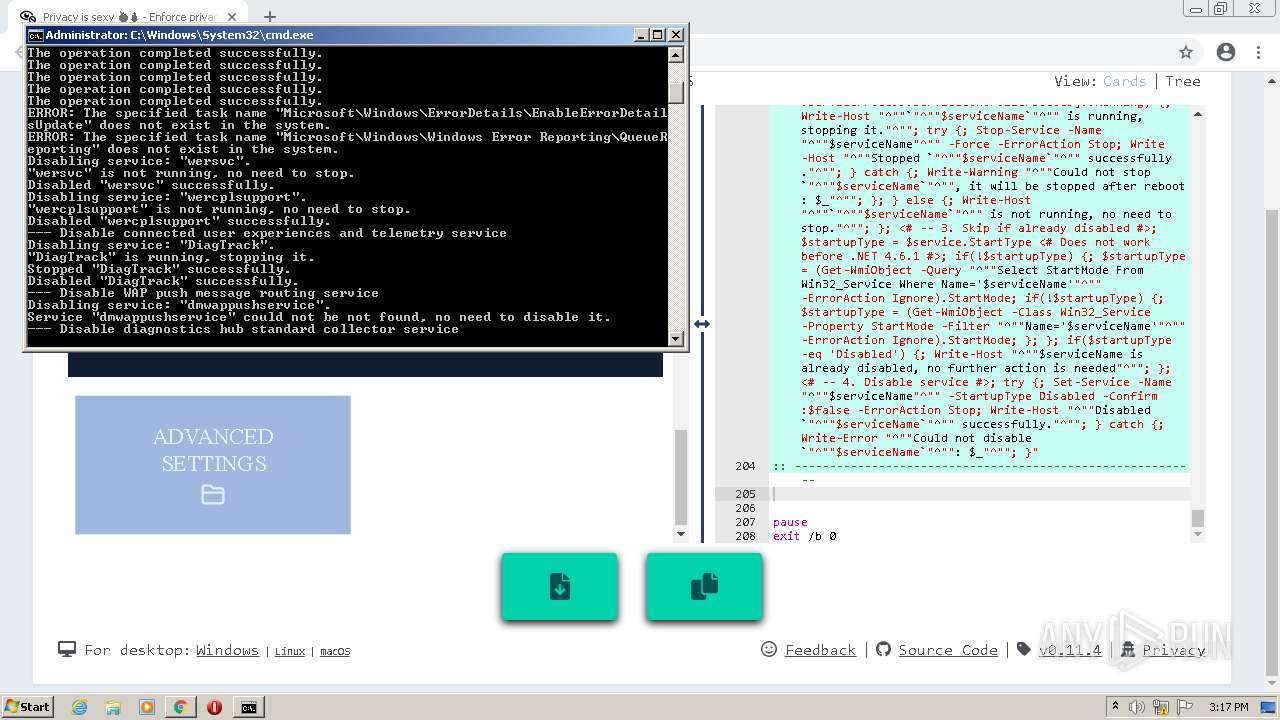
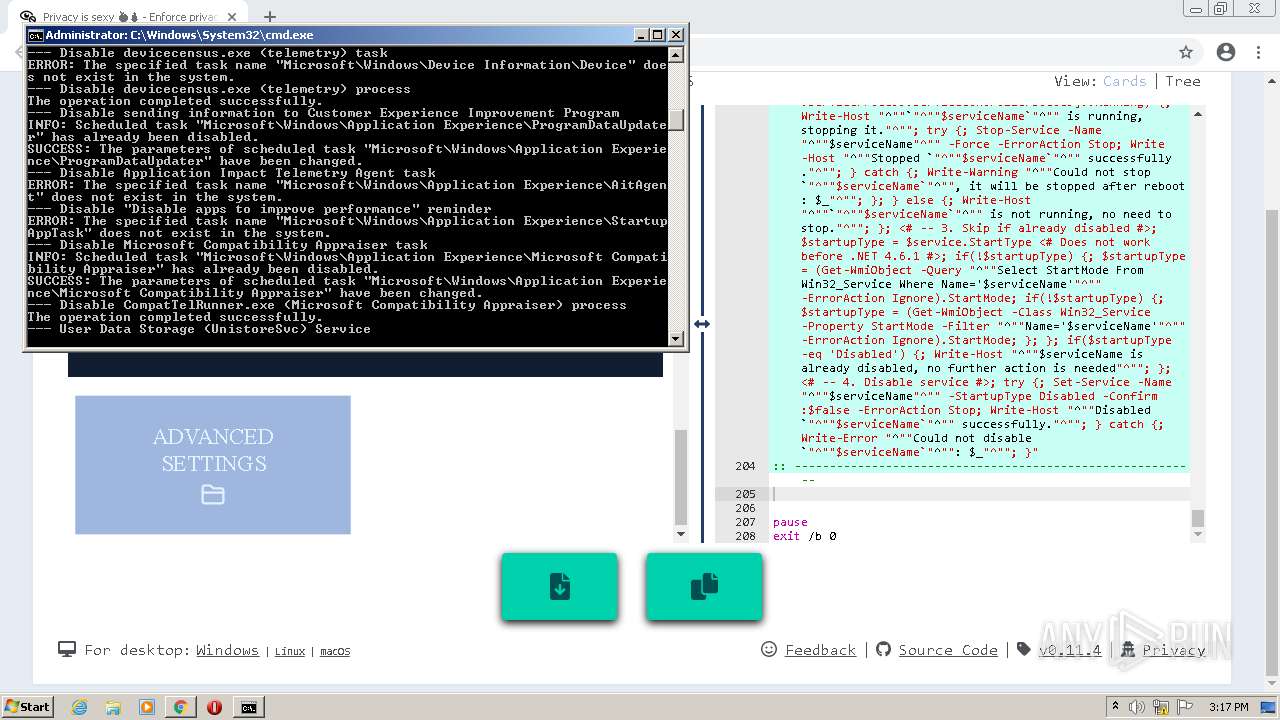
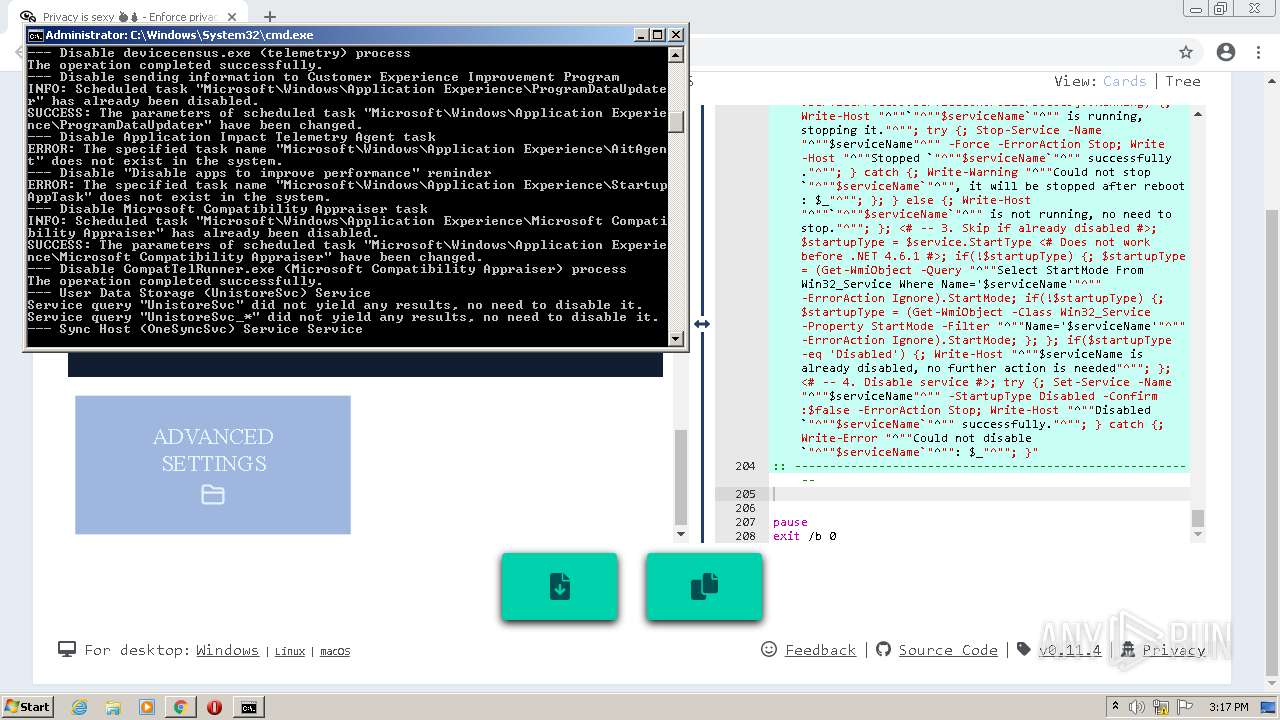
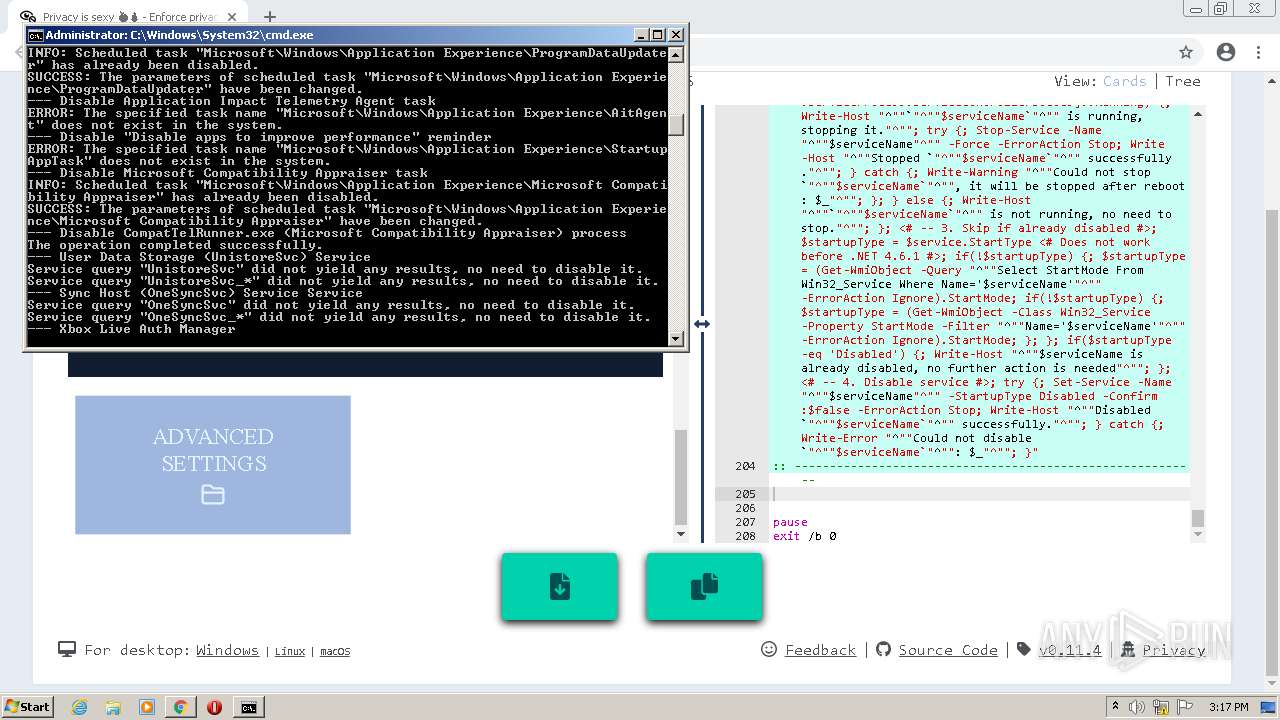
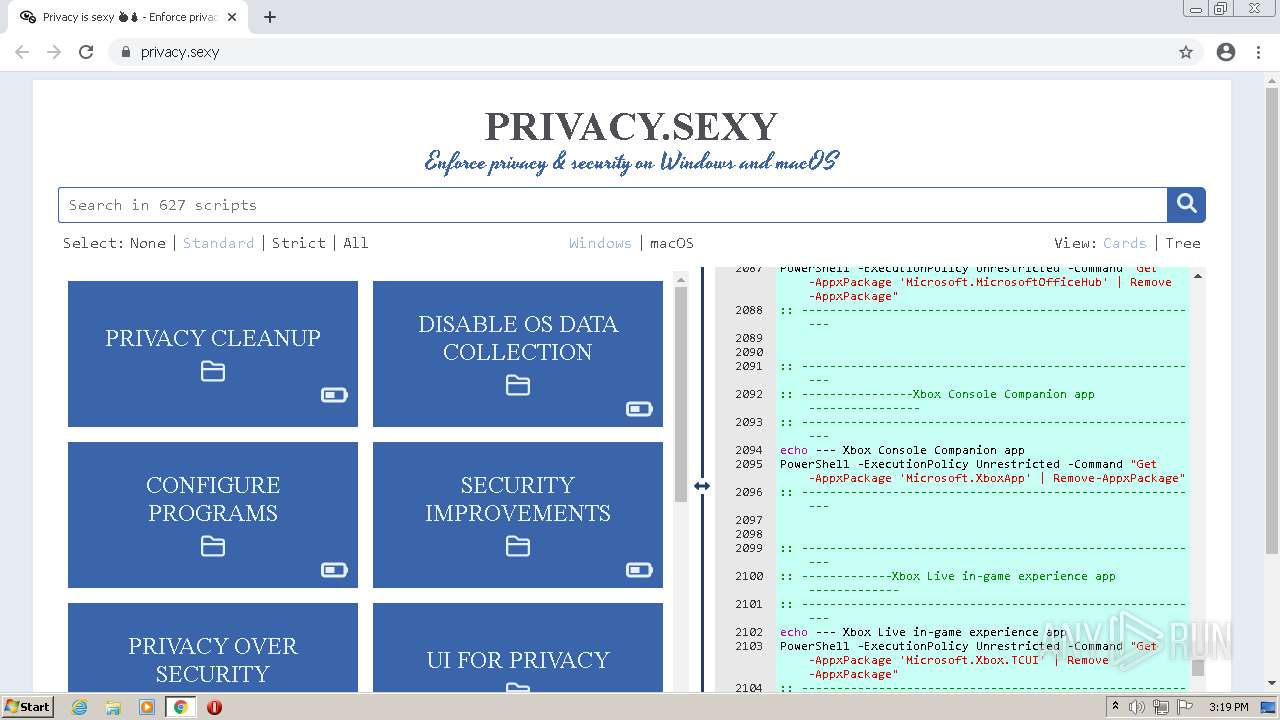
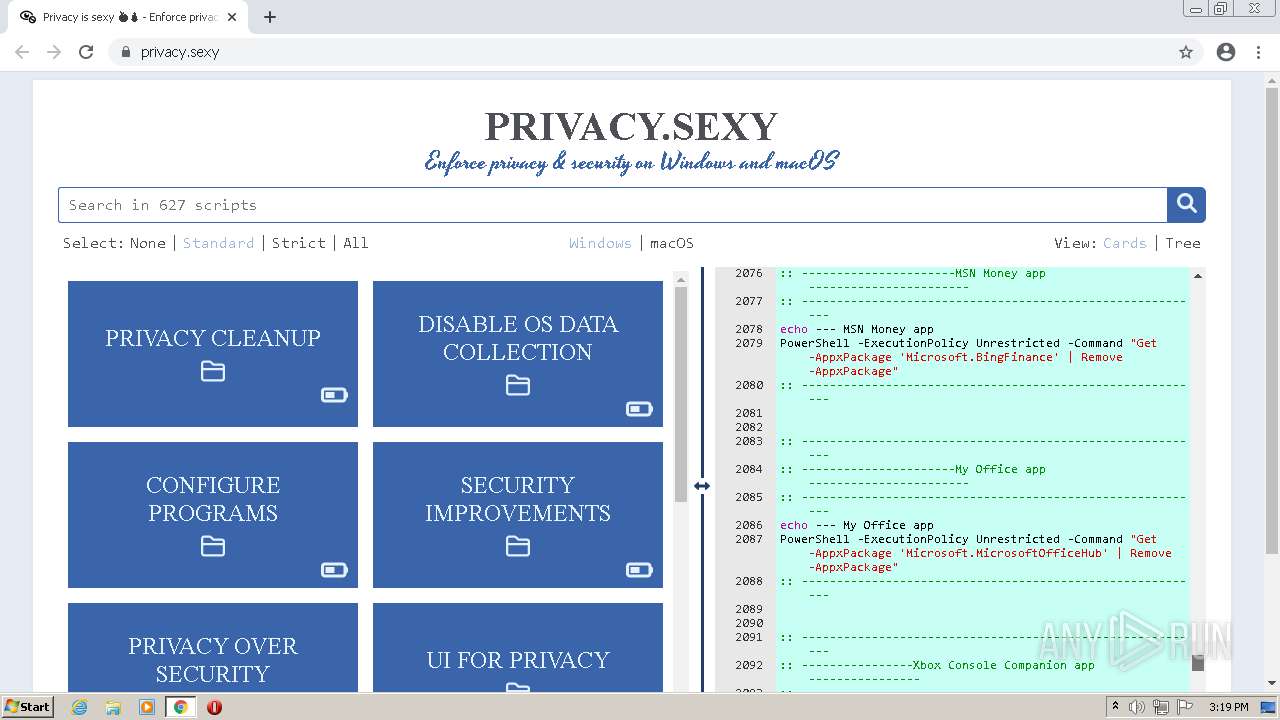
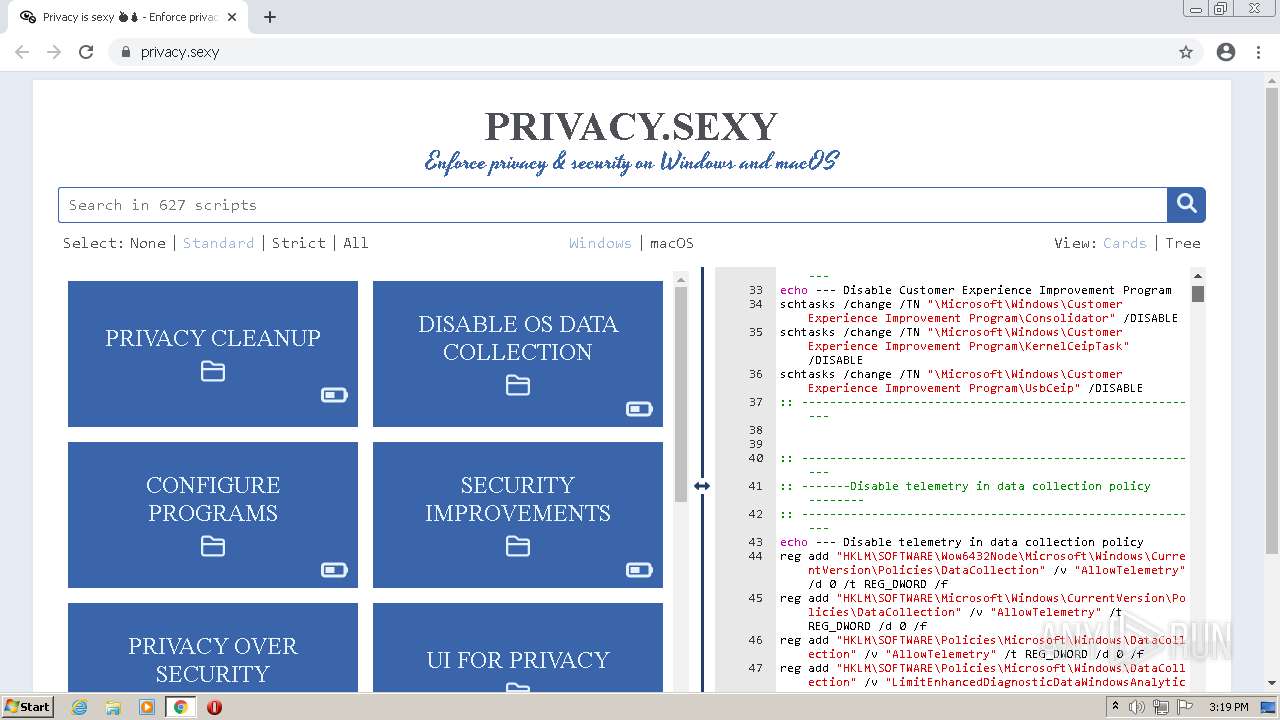
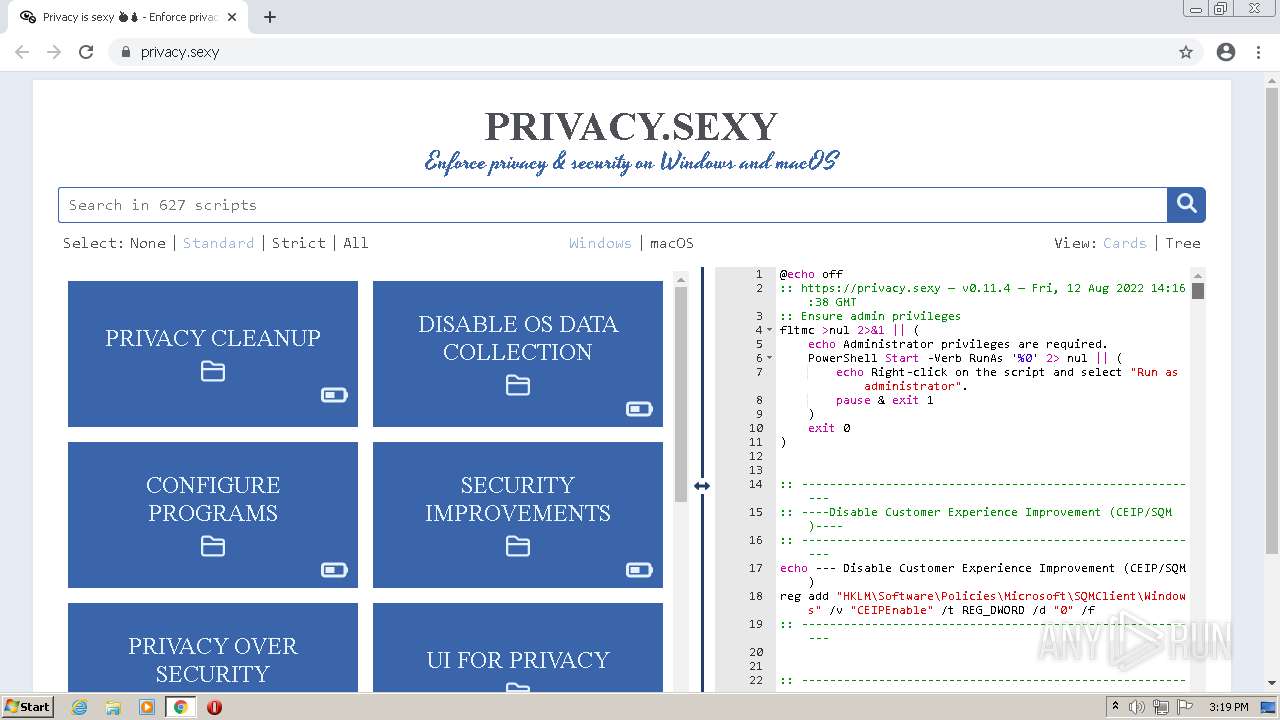
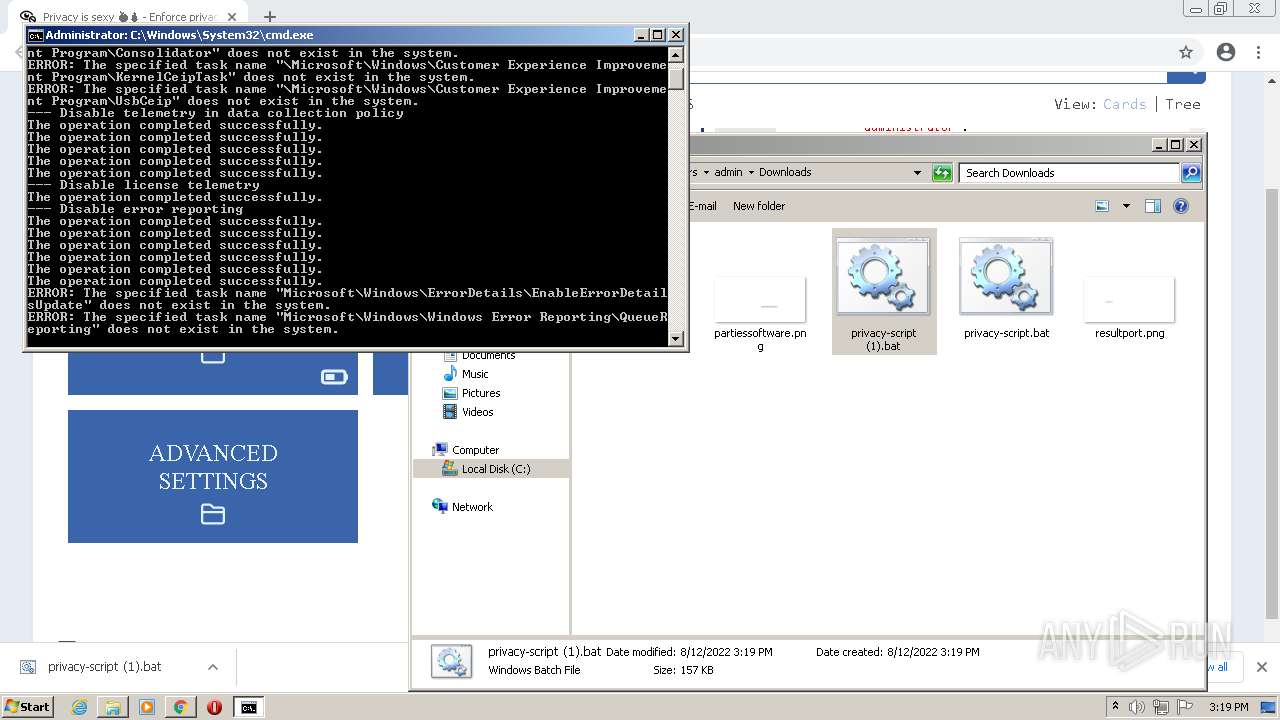
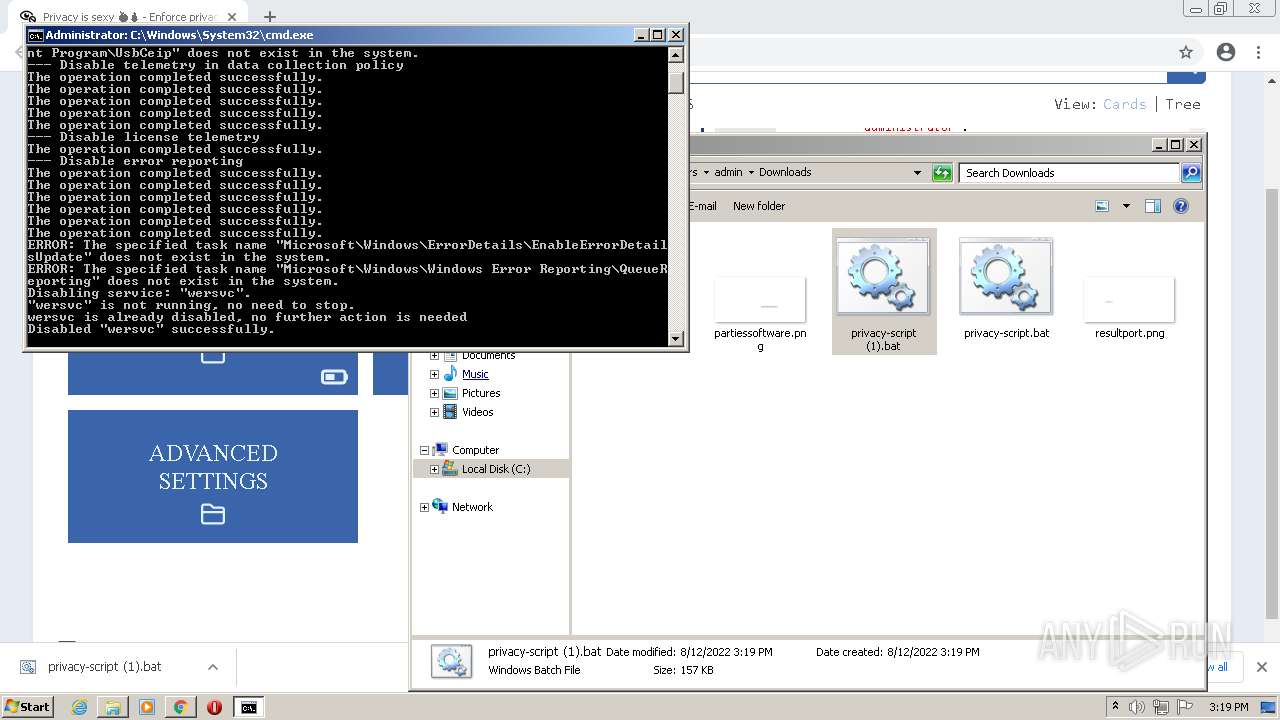
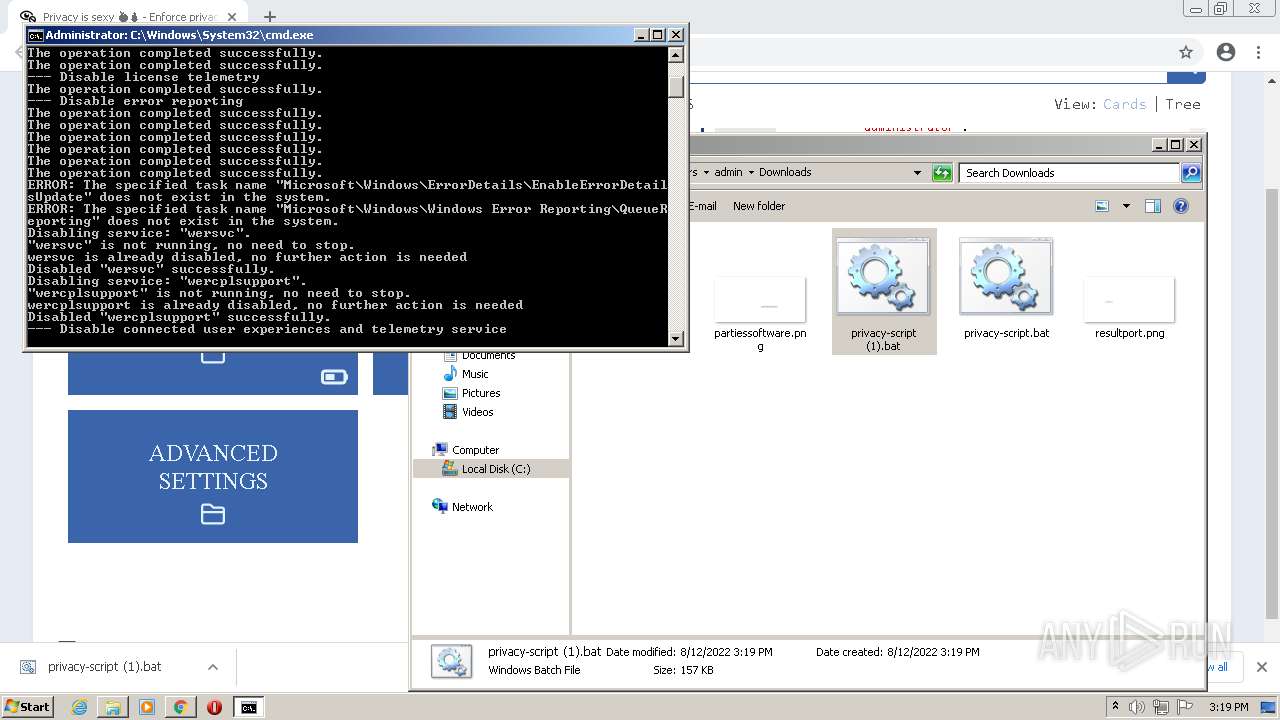
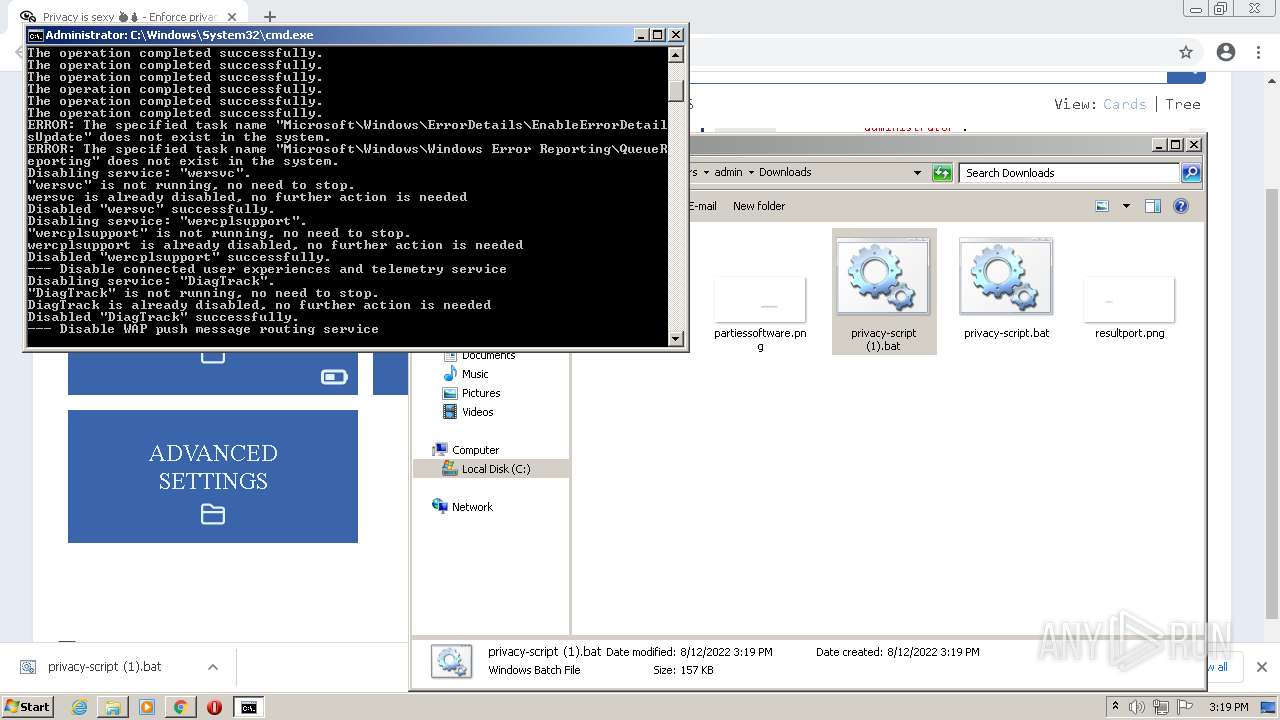
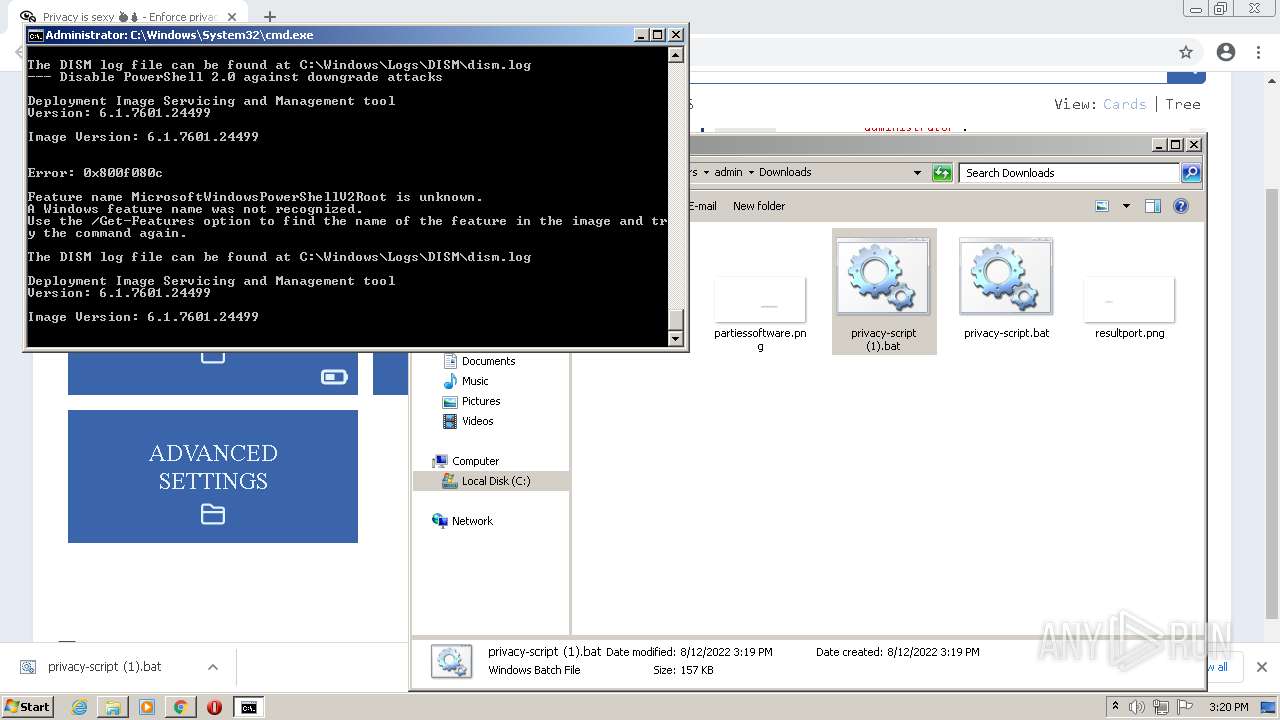
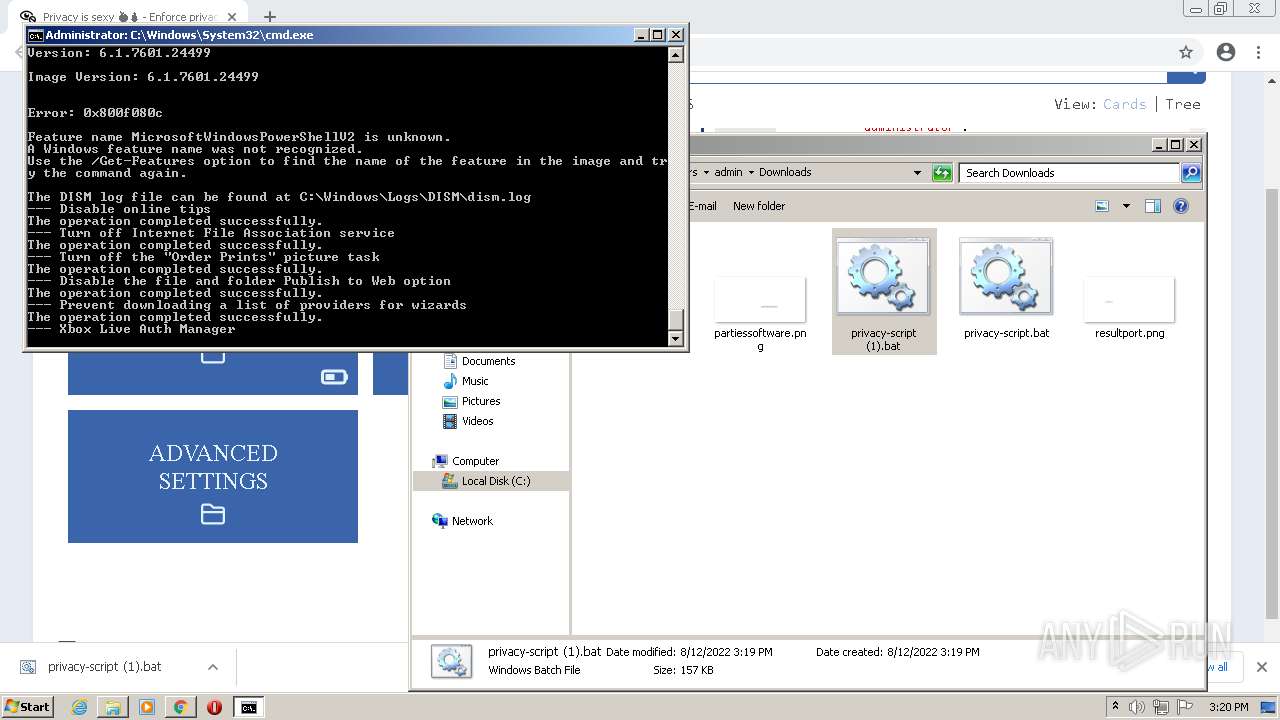
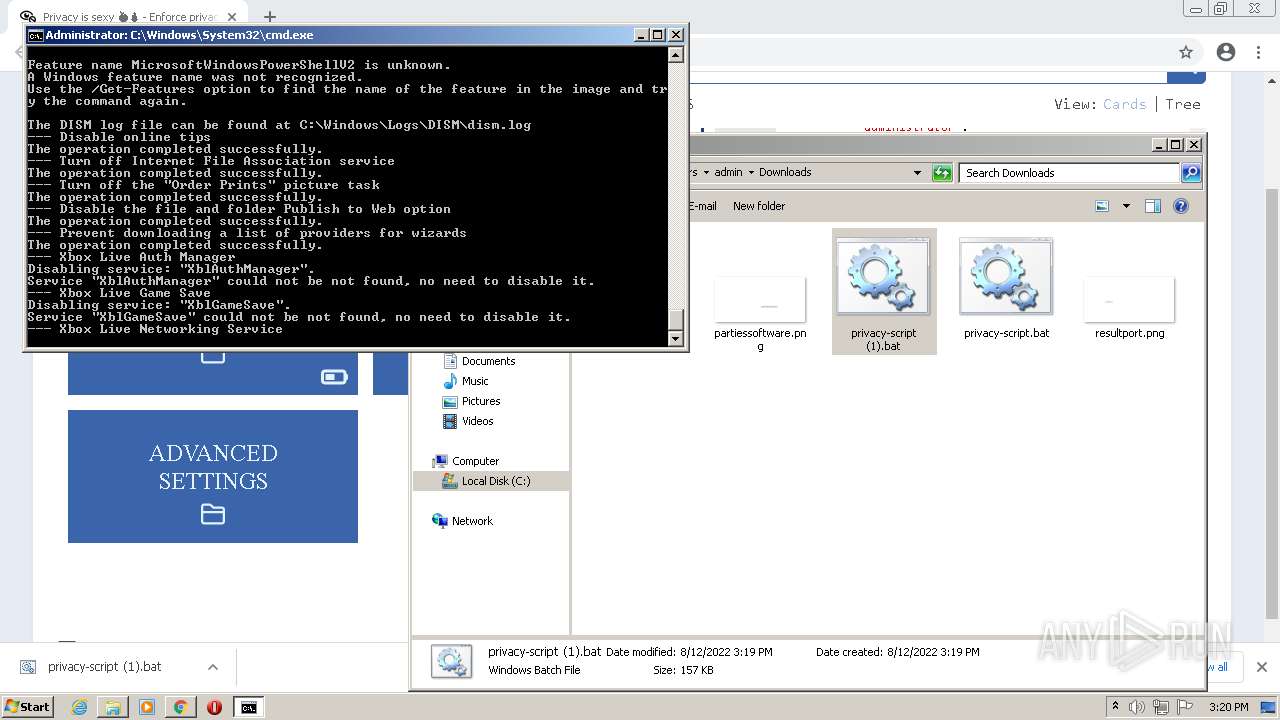
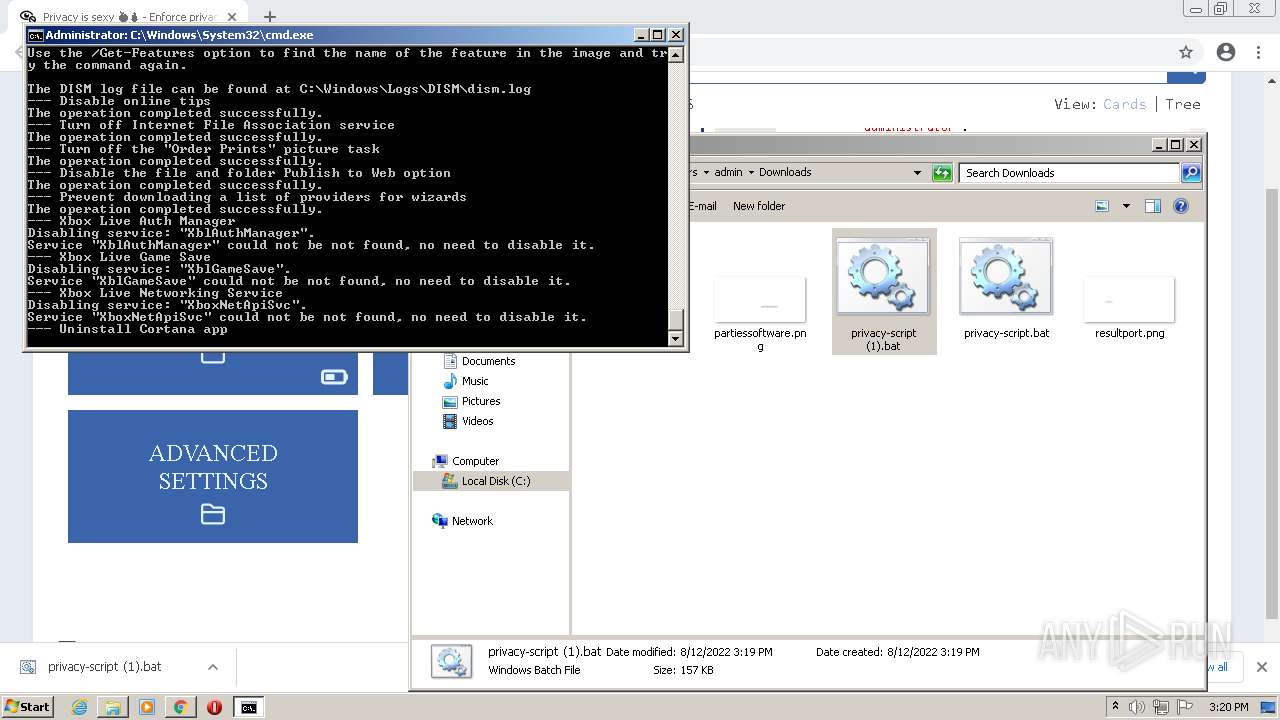
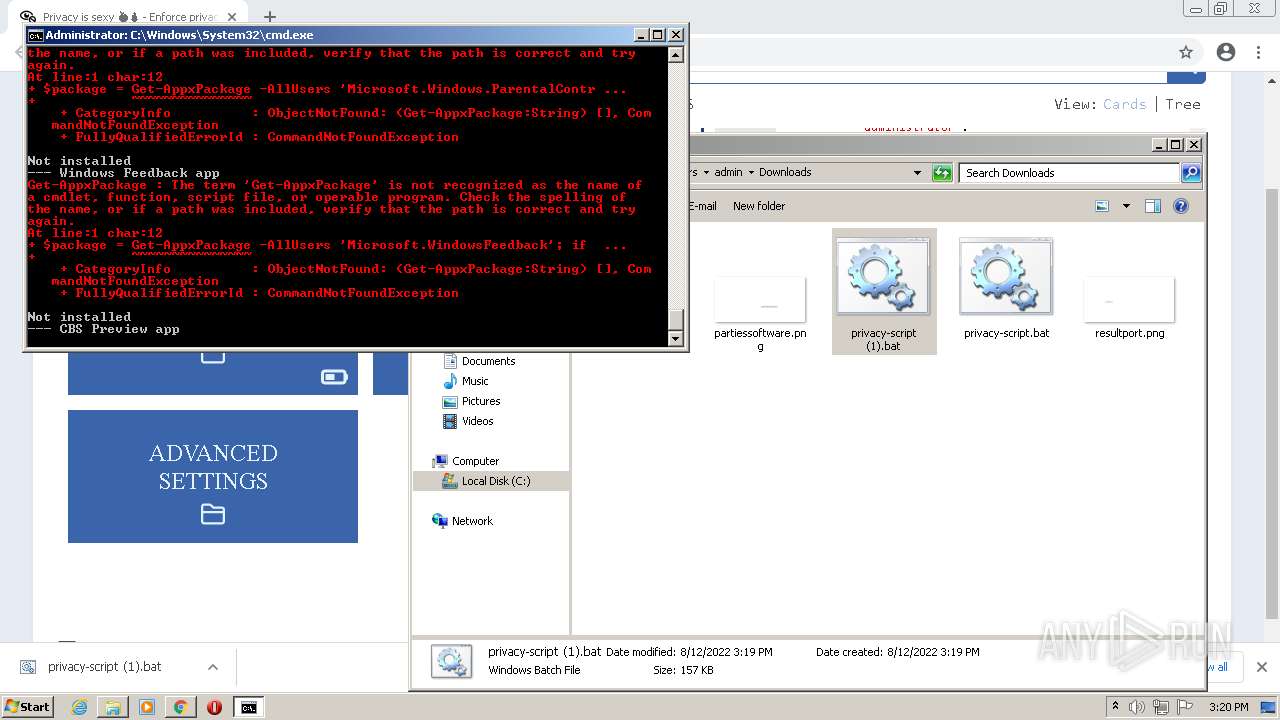
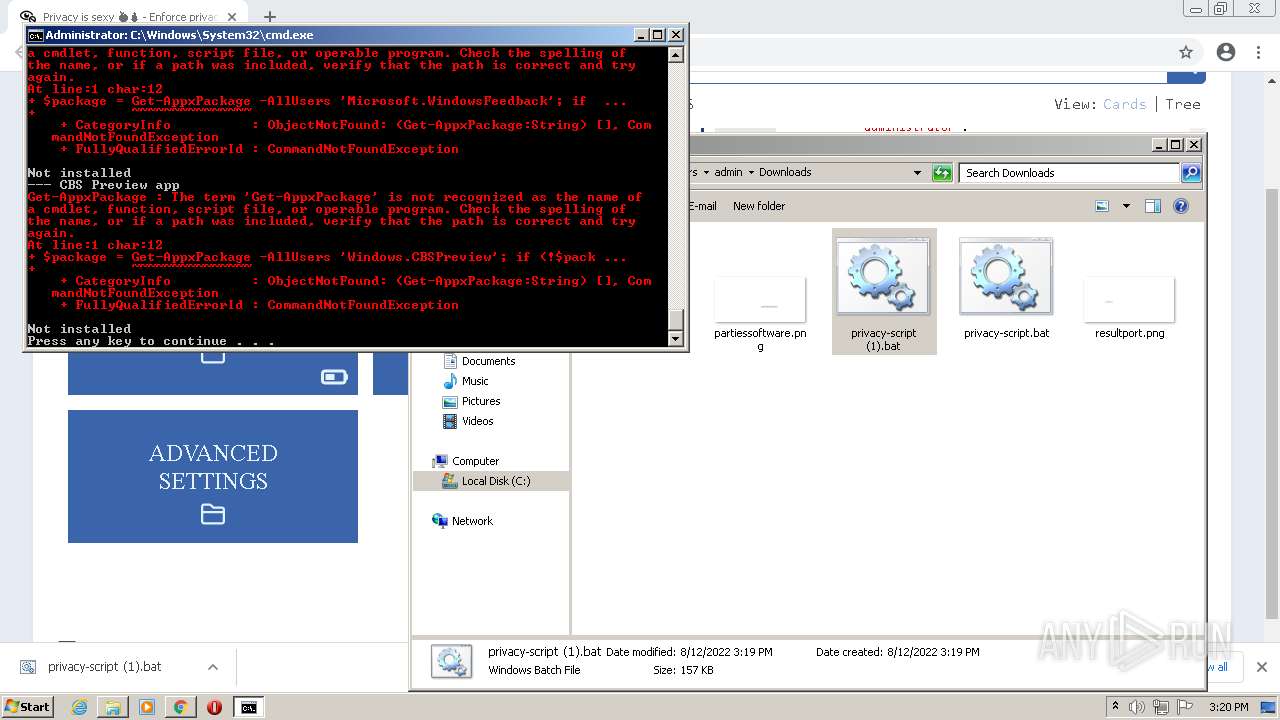
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 14:16:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
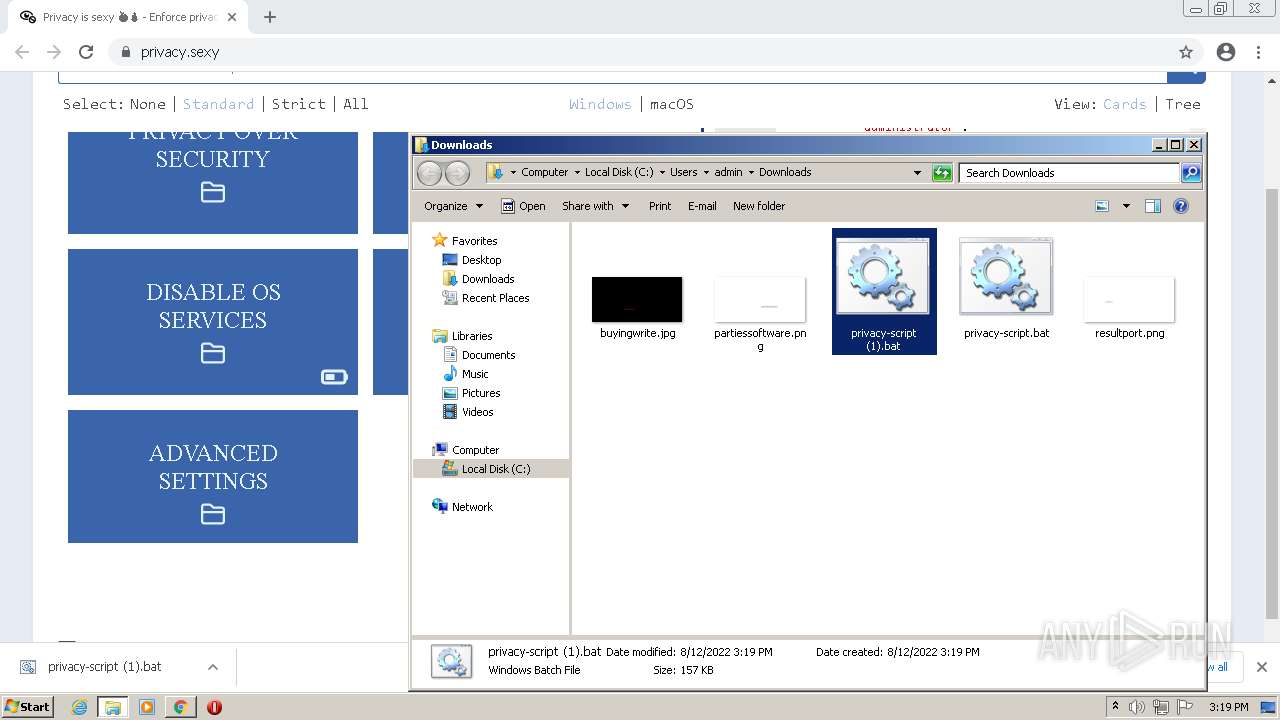
| MD5: | E129D0115610C3CE2696BB4DE42B3C3C |
| SHA1: | 7D62F73A086B69EFD4876F479E87EBB5F4A3B615 |
| SHA256: | D4F8B50CD8781C04B705C090D8510B1BEA7491C1D19FB3DA1C616F6F54A62E16 |
| SSDEEP: | 3:N8TMILis:2B |
MALICIOUS
Changes Windows Error Reporting flag
- reg.exe (PID: 3324)
- reg.exe (PID: 4076)
Changes Image File Execution Options
- reg.exe (PID: 2692)
- reg.exe (PID: 3352)
- reg.exe (PID: 2040)
- reg.exe (PID: 3268)
Drops executable file immediately after starts
- chrome.exe (PID: 3832)
- Dism.exe (PID: 1716)
- Dism.exe (PID: 2864)
- Dism.exe (PID: 488)
- Dism.exe (PID: 1016)
- Dism.exe (PID: 2064)
- Dism.exe (PID: 2124)
Loads dropped or rewritten executable
- dismhost.exe (PID: 3272)
- Dism.exe (PID: 1716)
- TrustedInstaller.exe (PID: 1940)
- Dism.exe (PID: 2864)
- dismhost.exe (PID: 516)
- Dism.exe (PID: 488)
- dismhost.exe (PID: 2508)
- Dism.exe (PID: 1016)
- dismhost.exe (PID: 2376)
- Dism.exe (PID: 2064)
- dismhost.exe (PID: 2580)
- Dism.exe (PID: 2124)
- dismhost.exe (PID: 1464)
Application was dropped or rewritten from another process
- dismhost.exe (PID: 3272)
- dismhost.exe (PID: 516)
- dismhost.exe (PID: 2508)
- dismhost.exe (PID: 2580)
- dismhost.exe (PID: 2376)
- dismhost.exe (PID: 1464)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2652)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 2312)
- chrome.exe (PID: 2104)
Checks supported languages
- cmd.exe (PID: 3252)
- cmd.exe (PID: 2132)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 3492)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 1596)
- powershell.exe (PID: 404)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 1252)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 3588)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 3164)
- cmd.exe (PID: 472)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 460)
- dismhost.exe (PID: 3272)
- TrustedInstaller.exe (PID: 1940)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 3544)
- powershell.exe (PID: 2920)
- powershell.exe (PID: 740)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 128)
- powershell.exe (PID: 2924)
- powershell.exe (PID: 3732)
- powershell.exe (PID: 280)
- powershell.exe (PID: 3520)
- powershell.exe (PID: 456)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 1476)
- powershell.exe (PID: 3496)
- powershell.exe (PID: 3444)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 3584)
- powershell.exe (PID: 2676)
- dismhost.exe (PID: 516)
- dismhost.exe (PID: 2508)
- dismhost.exe (PID: 2376)
- dismhost.exe (PID: 2580)
- powershell.exe (PID: 2272)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 508)
- dismhost.exe (PID: 1464)
- powershell.exe (PID: 2556)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 3940)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 508)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 1716)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 720)
- powershell.exe (PID: 2252)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 2760)
- powershell.exe (PID: 3088)
Reads the computer name
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 1596)
- powershell.exe (PID: 404)
- powershell.exe (PID: 3492)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 1252)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 3588)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 460)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 4004)
- TrustedInstaller.exe (PID: 1940)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 2920)
- powershell.exe (PID: 3544)
- powershell.exe (PID: 740)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 2924)
- dismhost.exe (PID: 3272)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 128)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 3732)
- powershell.exe (PID: 280)
- powershell.exe (PID: 3520)
- powershell.exe (PID: 456)
- powershell.exe (PID: 3496)
- powershell.exe (PID: 3444)
- powershell.exe (PID: 3584)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 2676)
- dismhost.exe (PID: 516)
- dismhost.exe (PID: 2508)
- dismhost.exe (PID: 2376)
- dismhost.exe (PID: 2580)
- dismhost.exe (PID: 1464)
- powershell.exe (PID: 2272)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 508)
- powershell.exe (PID: 2556)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 3940)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 508)
- powershell.exe (PID: 1716)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 720)
- powershell.exe (PID: 2252)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 2760)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 3088)
Drops a file with a compile date too recent
- chrome.exe (PID: 3832)
- Dism.exe (PID: 1716)
- Dism.exe (PID: 2864)
- Dism.exe (PID: 488)
- Dism.exe (PID: 1016)
- Dism.exe (PID: 2064)
- Dism.exe (PID: 2124)
Executable content was dropped or overwritten
- chrome.exe (PID: 3832)
- Dism.exe (PID: 1716)
- Dism.exe (PID: 2864)
- Dism.exe (PID: 488)
- Dism.exe (PID: 1016)
- Dism.exe (PID: 2064)
- Dism.exe (PID: 2124)
Application launched itself
- cmd.exe (PID: 472)
INFO
Application launched itself
- chrome.exe (PID: 2652)
Checks supported languages
- chrome.exe (PID: 324)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2312)
- fltMC.exe (PID: 3876)
- reg.exe (PID: 364)
- schtasks.exe (PID: 2144)
- fltMC.exe (PID: 404)
- reg.exe (PID: 988)
- schtasks.exe (PID: 2504)
- reg.exe (PID: 3636)
- reg.exe (PID: 3728)
- reg.exe (PID: 3220)
- reg.exe (PID: 1016)
- reg.exe (PID: 2360)
- reg.exe (PID: 2736)
- reg.exe (PID: 1648)
- schtasks.exe (PID: 444)
- reg.exe (PID: 3048)
- reg.exe (PID: 3324)
- reg.exe (PID: 1584)
- reg.exe (PID: 2568)
- schtasks.exe (PID: 3920)
- reg.exe (PID: 3560)
- schtasks.exe (PID: 2588)
- reg.exe (PID: 2692)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 972)
- schtasks.exe (PID: 3340)
- schtasks.exe (PID: 3796)
- reg.exe (PID: 3352)
- schtasks.exe (PID: 3308)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 1740)
- fltMC.exe (PID: 1104)
- reg.exe (PID: 3668)
- reg.exe (PID: 460)
- schtasks.exe (PID: 3012)
- reg.exe (PID: 2576)
- reg.exe (PID: 1332)
- reg.exe (PID: 464)
- reg.exe (PID: 1116)
- schtasks.exe (PID: 3324)
- reg.exe (PID: 3316)
- reg.exe (PID: 1412)
- reg.exe (PID: 3816)
- reg.exe (PID: 692)
- reg.exe (PID: 3856)
- reg.exe (PID: 1720)
- schtasks.exe (PID: 776)
- reg.exe (PID: 852)
- schtasks.exe (PID: 1092)
- reg.exe (PID: 4076)
- schtasks.exe (PID: 740)
- reg.exe (PID: 2040)
- schtasks.exe (PID: 1708)
- schtasks.exe (PID: 1436)
- schtasks.exe (PID: 992)
- schtasks.exe (PID: 3584)
- net.exe (PID: 2304)
- net1.exe (PID: 3576)
- Dism.exe (PID: 1716)
- reg.exe (PID: 3268)
- chrome.exe (PID: 2104)
- reg.exe (PID: 3188)
- find.exe (PID: 1744)
- net1.exe (PID: 2700)
- net.exe (PID: 508)
- net1.exe (PID: 3284)
- reg.exe (PID: 2004)
- find.exe (PID: 1016)
- net.exe (PID: 3380)
- reg.exe (PID: 3984)
- reg.exe (PID: 1504)
- reg.exe (PID: 3880)
- reg.exe (PID: 3848)
- reg.exe (PID: 2408)
- reg.exe (PID: 1552)
- reg.exe (PID: 2352)
- reg.exe (PID: 1236)
- reg.exe (PID: 3048)
- reg.exe (PID: 3516)
- reg.exe (PID: 3272)
- reg.exe (PID: 2348)
- reg.exe (PID: 3500)
- reg.exe (PID: 1536)
- reg.exe (PID: 3584)
- reg.exe (PID: 3836)
- reg.exe (PID: 3944)
- reg.exe (PID: 2408)
- reg.exe (PID: 1744)
- reg.exe (PID: 2104)
- reg.exe (PID: 2084)
- reg.exe (PID: 3508)
- reg.exe (PID: 484)
- reg.exe (PID: 2504)
- reg.exe (PID: 1540)
- reg.exe (PID: 2064)
- schtasks.exe (PID: 2180)
- reg.exe (PID: 3164)
- reg.exe (PID: 3484)
- setx.exe (PID: 1352)
- reg.exe (PID: 2176)
- reg.exe (PID: 2352)
- setx.exe (PID: 3380)
- schtasks.exe (PID: 1876)
- schtasks.exe (PID: 1744)
- schtasks.exe (PID: 3132)
- reg.exe (PID: 484)
- reg.exe (PID: 2128)
- reg.exe (PID: 2404)
- reg.exe (PID: 2856)
- reg.exe (PID: 1504)
- sc.exe (PID: 2312)
- reg.exe (PID: 3060)
- schtasks.exe (PID: 3148)
- schtasks.exe (PID: 3248)
- reg.exe (PID: 3288)
- reg.exe (PID: 1536)
- reg.exe (PID: 3796)
- reg.exe (PID: 2984)
- reg.exe (PID: 3520)
- reg.exe (PID: 2932)
- reg.exe (PID: 3540)
- reg.exe (PID: 2360)
- reg.exe (PID: 3148)
- reg.exe (PID: 3788)
- reg.exe (PID: 2924)
- reg.exe (PID: 1448)
- reg.exe (PID: 1092)
- reg.exe (PID: 2544)
- reg.exe (PID: 2068)
- reg.exe (PID: 3920)
- reg.exe (PID: 3932)
- takeown.exe (PID: 2596)
- reg.exe (PID: 3296)
- reg.exe (PID: 2616)
- reg.exe (PID: 3528)
- reg.exe (PID: 1352)
- reg.exe (PID: 368)
- reg.exe (PID: 1152)
- reg.exe (PID: 3088)
- icacls.exe (PID: 852)
- reg.exe (PID: 1504)
- reg.exe (PID: 2908)
- reg.exe (PID: 1420)
- reg.exe (PID: 1560)
- reg.exe (PID: 2456)
- reg.exe (PID: 3832)
- reg.exe (PID: 3076)
- reg.exe (PID: 3432)
- reg.exe (PID: 588)
- reg.exe (PID: 2008)
- icacls.exe (PID: 2092)
- reg.exe (PID: 2276)
- reg.exe (PID: 3932)
- reg.exe (PID: 2692)
- reg.exe (PID: 4080)
- reg.exe (PID: 2772)
- reg.exe (PID: 424)
- reg.exe (PID: 3044)
- takeown.exe (PID: 508)
- takeown.exe (PID: 2220)
- reg.exe (PID: 2296)
- icacls.exe (PID: 3520)
- reg.exe (PID: 3584)
- reg.exe (PID: 4076)
- reg.exe (PID: 2716)
- reg.exe (PID: 3492)
- reg.exe (PID: 1164)
- reg.exe (PID: 1016)
- reg.exe (PID: 3576)
- reg.exe (PID: 3560)
- reg.exe (PID: 372)
- reg.exe (PID: 3380)
- reg.exe (PID: 2836)
- reg.exe (PID: 1300)
- reg.exe (PID: 444)
- reg.exe (PID: 3308)
- reg.exe (PID: 1336)
- reg.exe (PID: 2248)
- reg.exe (PID: 628)
- reg.exe (PID: 1196)
- reg.exe (PID: 2304)
- reg.exe (PID: 3944)
- reg.exe (PID: 3036)
- reg.exe (PID: 1020)
- reg.exe (PID: 2420)
- reg.exe (PID: 1584)
- reg.exe (PID: 4068)
- reg.exe (PID: 3364)
- reg.exe (PID: 3852)
- reg.exe (PID: 1496)
- reg.exe (PID: 1736)
- reg.exe (PID: 1032)
- reg.exe (PID: 1308)
- reg.exe (PID: 3320)
- reg.exe (PID: 3904)
- reg.exe (PID: 3176)
- reg.exe (PID: 2268)
- reg.exe (PID: 1012)
- reg.exe (PID: 2340)
- reg.exe (PID: 2264)
- reg.exe (PID: 2976)
- reg.exe (PID: 3544)
- reg.exe (PID: 3212)
- reg.exe (PID: 628)
- reg.exe (PID: 1708)
- reg.exe (PID: 2916)
- reg.exe (PID: 2884)
- reg.exe (PID: 3280)
- reg.exe (PID: 3744)
- reg.exe (PID: 1092)
- reg.exe (PID: 2760)
- reg.exe (PID: 1596)
- reg.exe (PID: 3960)
- reg.exe (PID: 3144)
- reg.exe (PID: 1764)
- reg.exe (PID: 3848)
- reg.exe (PID: 2580)
- reg.exe (PID: 3628)
- reg.exe (PID: 2308)
- reg.exe (PID: 1448)
- reg.exe (PID: 2544)
- reg.exe (PID: 1176)
- reg.exe (PID: 1560)
- reg.exe (PID: 2232)
- reg.exe (PID: 740)
- reg.exe (PID: 2480)
- reg.exe (PID: 3932)
- reg.exe (PID: 2516)
- reg.exe (PID: 3620)
- reg.exe (PID: 3348)
- reg.exe (PID: 1648)
- reg.exe (PID: 2700)
- reg.exe (PID: 1240)
- reg.exe (PID: 3520)
- reg.exe (PID: 1316)
- reg.exe (PID: 3036)
- reg.exe (PID: 3164)
- reg.exe (PID: 3580)
- reg.exe (PID: 3588)
- reg.exe (PID: 2892)
- reg.exe (PID: 576)
- reg.exe (PID: 1644)
- reg.exe (PID: 3860)
- reg.exe (PID: 2680)
- reg.exe (PID: 3624)
- reg.exe (PID: 3296)
- reg.exe (PID: 3128)
- reg.exe (PID: 2460)
- reg.exe (PID: 1584)
- reg.exe (PID: 1520)
- reg.exe (PID: 2904)
- reg.exe (PID: 3196)
- reg.exe (PID: 2064)
- reg.exe (PID: 3272)
- reg.exe (PID: 3840)
- reg.exe (PID: 3264)
- reg.exe (PID: 2244)
- reg.exe (PID: 408)
- reg.exe (PID: 372)
- reg.exe (PID: 3852)
- reg.exe (PID: 3996)
- reg.exe (PID: 776)
- reg.exe (PID: 1584)
- reg.exe (PID: 1532)
- reg.exe (PID: 508)
- reg.exe (PID: 444)
- reg.exe (PID: 2064)
- reg.exe (PID: 128)
- reg.exe (PID: 460)
- reg.exe (PID: 3072)
- reg.exe (PID: 1608)
- reg.exe (PID: 2736)
- reg.exe (PID: 2672)
- reg.exe (PID: 4048)
- reg.exe (PID: 1336)
- reg.exe (PID: 1892)
- reg.exe (PID: 1016)
- reg.exe (PID: 3484)
- reg.exe (PID: 3924)
- reg.exe (PID: 3248)
- reg.exe (PID: 776)
- reg.exe (PID: 1532)
- reg.exe (PID: 2512)
- reg.exe (PID: 2080)
- reg.exe (PID: 2428)
- reg.exe (PID: 2040)
- reg.exe (PID: 3856)
- reg.exe (PID: 3268)
- reg.exe (PID: 2596)
- reg.exe (PID: 3180)
- reg.exe (PID: 1164)
- reg.exe (PID: 3104)
- reg.exe (PID: 4048)
- reg.exe (PID: 4040)
- reg.exe (PID: 1152)
- reg.exe (PID: 3480)
- reg.exe (PID: 1604)
- reg.exe (PID: 4044)
- reg.exe (PID: 2904)
- reg.exe (PID: 2088)
- reg.exe (PID: 4036)
- reg.exe (PID: 3640)
- reg.exe (PID: 3244)
- reg.exe (PID: 3920)
- reg.exe (PID: 3128)
- reg.exe (PID: 2556)
- reg.exe (PID: 2796)
- reg.exe (PID: 1764)
- reg.exe (PID: 320)
- reg.exe (PID: 2676)
- reg.exe (PID: 2436)
- reg.exe (PID: 3860)
- reg.exe (PID: 3844)
- reg.exe (PID: 408)
- reg.exe (PID: 3552)
- schtasks.exe (PID: 4080)
- reg.exe (PID: 508)
- reg.exe (PID: 3260)
- reg.exe (PID: 3104)
- reg.exe (PID: 3176)
- reg.exe (PID: 2728)
- reg.exe (PID: 3484)
- reg.exe (PID: 3344)
- reg.exe (PID: 460)
- reg.exe (PID: 1608)
- schtasks.exe (PID: 1988)
- reg.exe (PID: 3772)
- reg.exe (PID: 2772)
- reg.exe (PID: 3500)
- reg.exe (PID: 1680)
- schtasks.exe (PID: 2132)
- reg.exe (PID: 1904)
- reg.exe (PID: 2444)
- reg.exe (PID: 2928)
- reg.exe (PID: 2516)
- reg.exe (PID: 4064)
- reg.exe (PID: 2084)
- reg.exe (PID: 2700)
- reg.exe (PID: 2276)
- reg.exe (PID: 3684)
- reg.exe (PID: 3872)
- schtasks.exe (PID: 3628)
- reg.exe (PID: 3816)
- schtasks.exe (PID: 3996)
- schtasks.exe (PID: 4088)
- reg.exe (PID: 3188)
- reg.exe (PID: 2676)
- reg.exe (PID: 1308)
- reg.exe (PID: 2752)
- reg.exe (PID: 3188)
- reg.exe (PID: 2516)
- reg.exe (PID: 4064)
- reg.exe (PID: 3840)
- reg.exe (PID: 3644)
- reg.exe (PID: 3176)
- reg.exe (PID: 628)
- reg.exe (PID: 2772)
- reg.exe (PID: 2712)
- schtasks.exe (PID: 3576)
- reg.exe (PID: 2928)
- reg.exe (PID: 2380)
- reg.exe (PID: 3848)
- reg.exe (PID: 3852)
- reg.exe (PID: 888)
- reg.exe (PID: 1176)
- reg.exe (PID: 2312)
- reg.exe (PID: 3060)
- icacls.exe (PID: 4048)
- reg.exe (PID: 2488)
- reg.exe (PID: 3244)
- reg.exe (PID: 3944)
- reg.exe (PID: 1960)
- reg.exe (PID: 1648)
- reg.exe (PID: 2400)
- reg.exe (PID: 1336)
- schtasks.exe (PID: 2856)
- schtasks.exe (PID: 3472)
- Dism.exe (PID: 2864)
- reg.exe (PID: 3984)
- reg.exe (PID: 2580)
- reg.exe (PID: 124)
- reg.exe (PID: 2260)
- Dism.exe (PID: 488)
- Dism.exe (PID: 1016)
- Dism.exe (PID: 2124)
- Dism.exe (PID: 2064)
- reg.exe (PID: 3496)
- reg.exe (PID: 444)
- reg.exe (PID: 2104)
- reg.exe (PID: 3464)
- reg.exe (PID: 1680)
- cacls.exe (PID: 2524)
Reads the computer name
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 2928)
- schtasks.exe (PID: 2144)
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 2504)
- chrome.exe (PID: 2964)
- schtasks.exe (PID: 3920)
- schtasks.exe (PID: 2588)
- schtasks.exe (PID: 972)
- schtasks.exe (PID: 3796)
- schtasks.exe (PID: 3308)
- schtasks.exe (PID: 3340)
- schtasks.exe (PID: 444)
- chrome.exe (PID: 1740)
- schtasks.exe (PID: 3324)
- chrome.exe (PID: 2104)
- schtasks.exe (PID: 3012)
- schtasks.exe (PID: 776)
- schtasks.exe (PID: 1092)
- schtasks.exe (PID: 740)
- schtasks.exe (PID: 3584)
- schtasks.exe (PID: 1708)
- schtasks.exe (PID: 992)
- schtasks.exe (PID: 1436)
- net1.exe (PID: 3576)
- Dism.exe (PID: 1716)
- net1.exe (PID: 2700)
- sc.exe (PID: 2312)
- net1.exe (PID: 3284)
- schtasks.exe (PID: 2180)
- schtasks.exe (PID: 1876)
- schtasks.exe (PID: 1744)
- schtasks.exe (PID: 3132)
- schtasks.exe (PID: 3248)
- schtasks.exe (PID: 3148)
- takeown.exe (PID: 2596)
- icacls.exe (PID: 852)
- takeown.exe (PID: 2220)
- icacls.exe (PID: 3520)
- takeown.exe (PID: 508)
- icacls.exe (PID: 2092)
- schtasks.exe (PID: 1988)
- schtasks.exe (PID: 4080)
- schtasks.exe (PID: 2132)
- schtasks.exe (PID: 3996)
- schtasks.exe (PID: 3628)
- schtasks.exe (PID: 4088)
- schtasks.exe (PID: 3576)
- icacls.exe (PID: 4048)
- cacls.exe (PID: 2524)
- Dism.exe (PID: 2864)
- schtasks.exe (PID: 3472)
- schtasks.exe (PID: 2856)
- Dism.exe (PID: 488)
- Dism.exe (PID: 1016)
- Dism.exe (PID: 2064)
- Dism.exe (PID: 2124)
Reads settings of System Certificates
- chrome.exe (PID: 3452)
- TrustedInstaller.exe (PID: 1940)
- powershell.exe (PID: 2556)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 508)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 2252)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 1716)
- powershell.exe (PID: 720)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 3940)
- powershell.exe (PID: 2760)
Reads the date of Windows installation
- chrome.exe (PID: 2928)
Checks Windows Trust Settings
- chrome.exe (PID: 2652)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 3492)
- powershell.exe (PID: 2900)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 1596)
- powershell.exe (PID: 404)
- powershell.exe (PID: 1252)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 3588)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 460)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 2920)
- powershell.exe (PID: 740)
- powershell.exe (PID: 3544)
- powershell.exe (PID: 2492)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 3540)
- powershell.exe (PID: 128)
- powershell.exe (PID: 2924)
- powershell.exe (PID: 456)
- powershell.exe (PID: 3520)
- powershell.exe (PID: 3732)
- powershell.exe (PID: 280)
- powershell.exe (PID: 3496)
- powershell.exe (PID: 3444)
- powershell.exe (PID: 2312)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 3584)
- powershell.exe (PID: 2676)
- TrustedInstaller.exe (PID: 1940)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 2272)
- powershell.exe (PID: 508)
- powershell.exe (PID: 2556)
- powershell.exe (PID: 1904)
- powershell.exe (PID: 3940)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 1740)
- powershell.exe (PID: 508)
- powershell.exe (PID: 1716)
- powershell.exe (PID: 720)
- powershell.exe (PID: 2252)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 1932)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 3844)
- powershell.exe (PID: 2760)
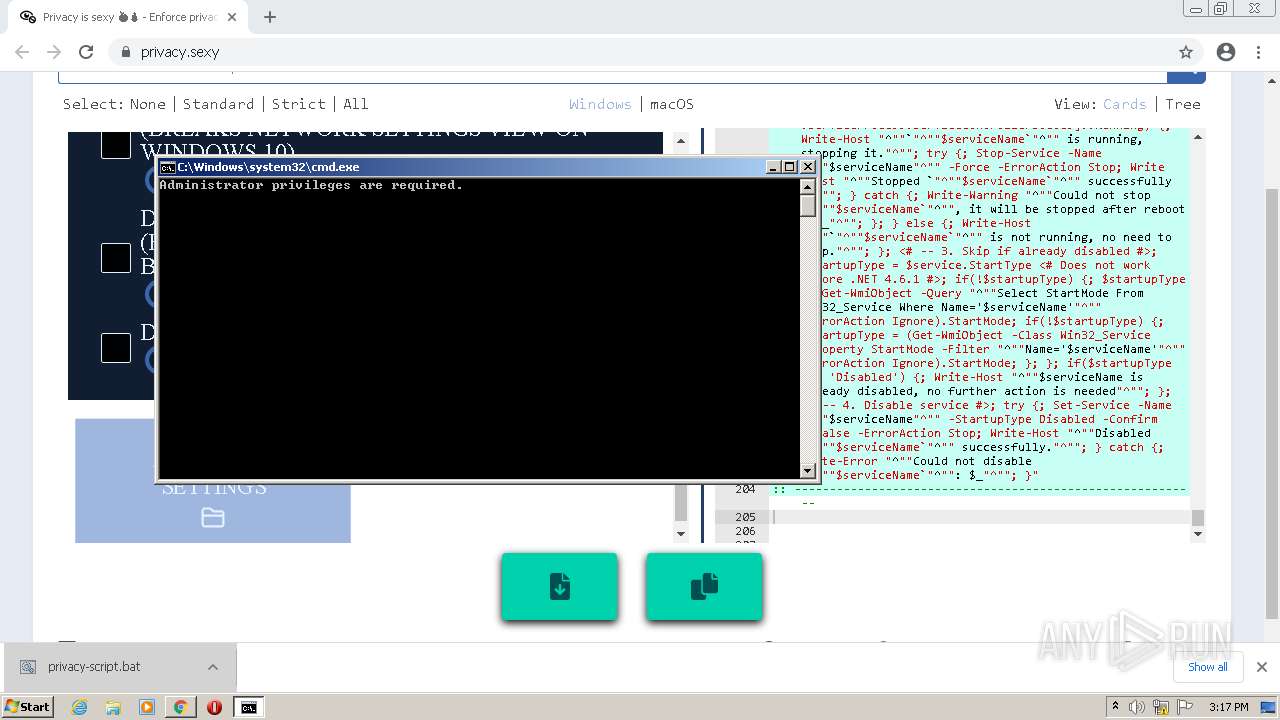
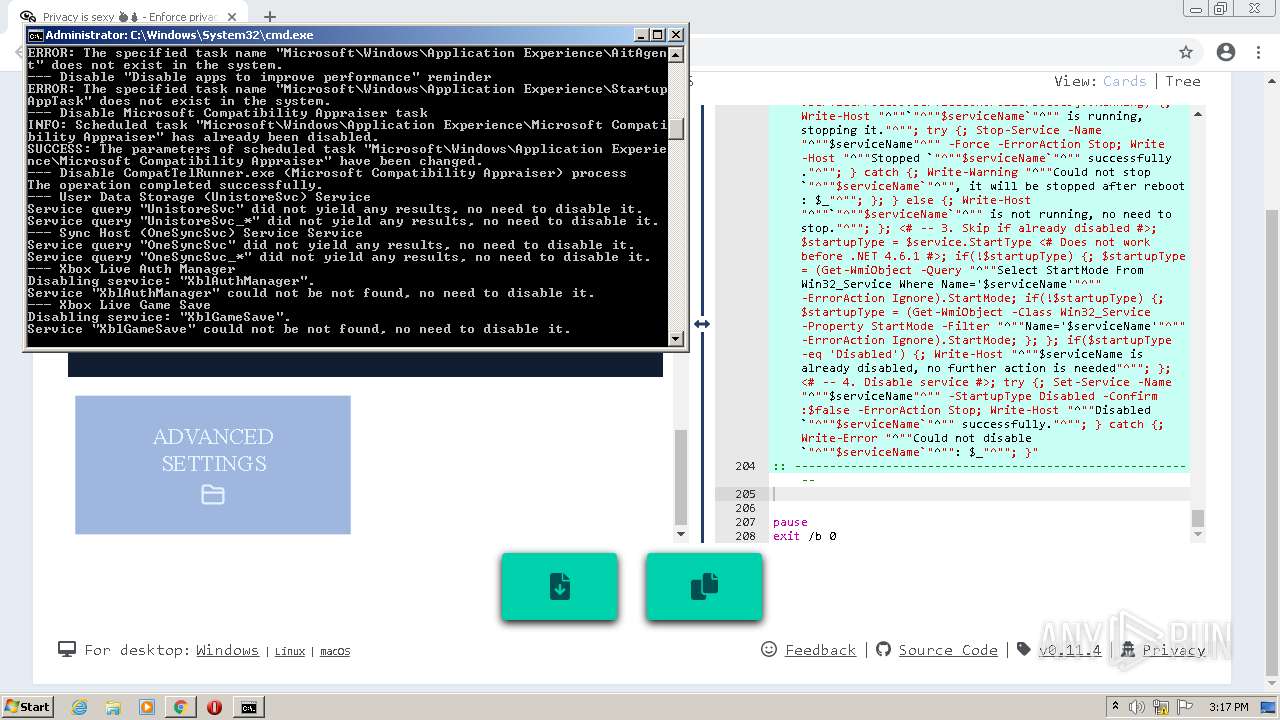
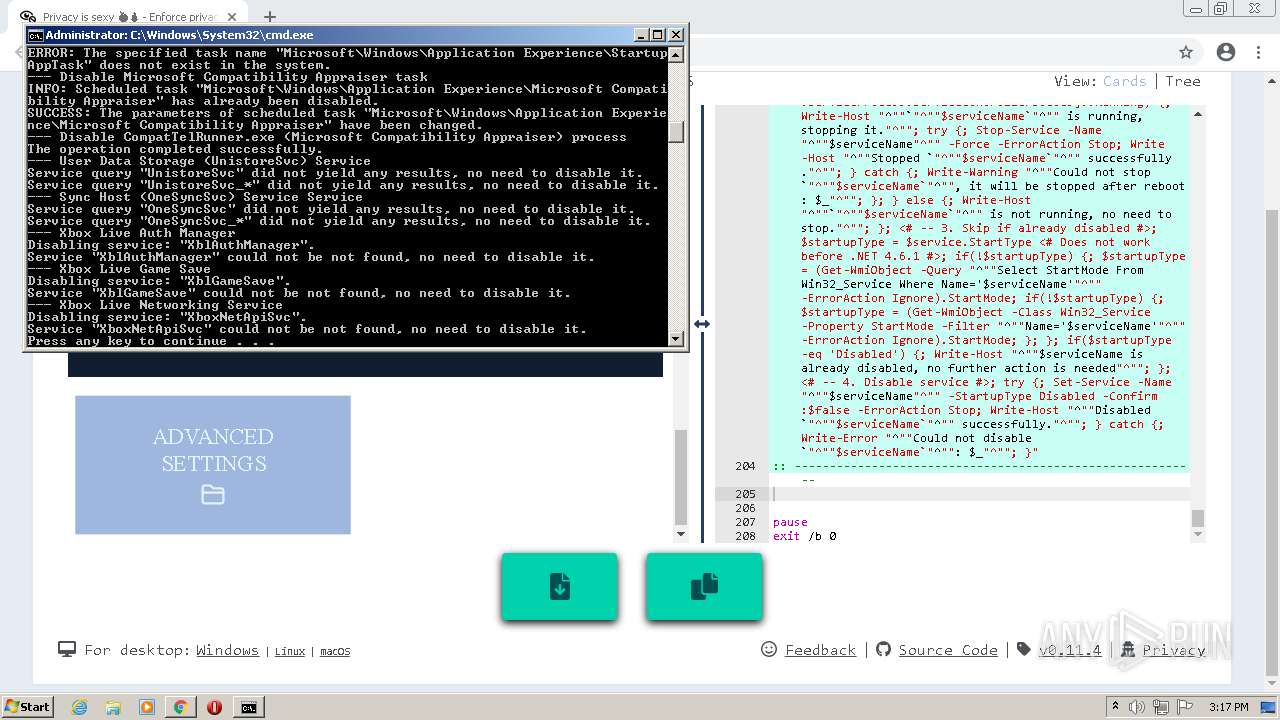
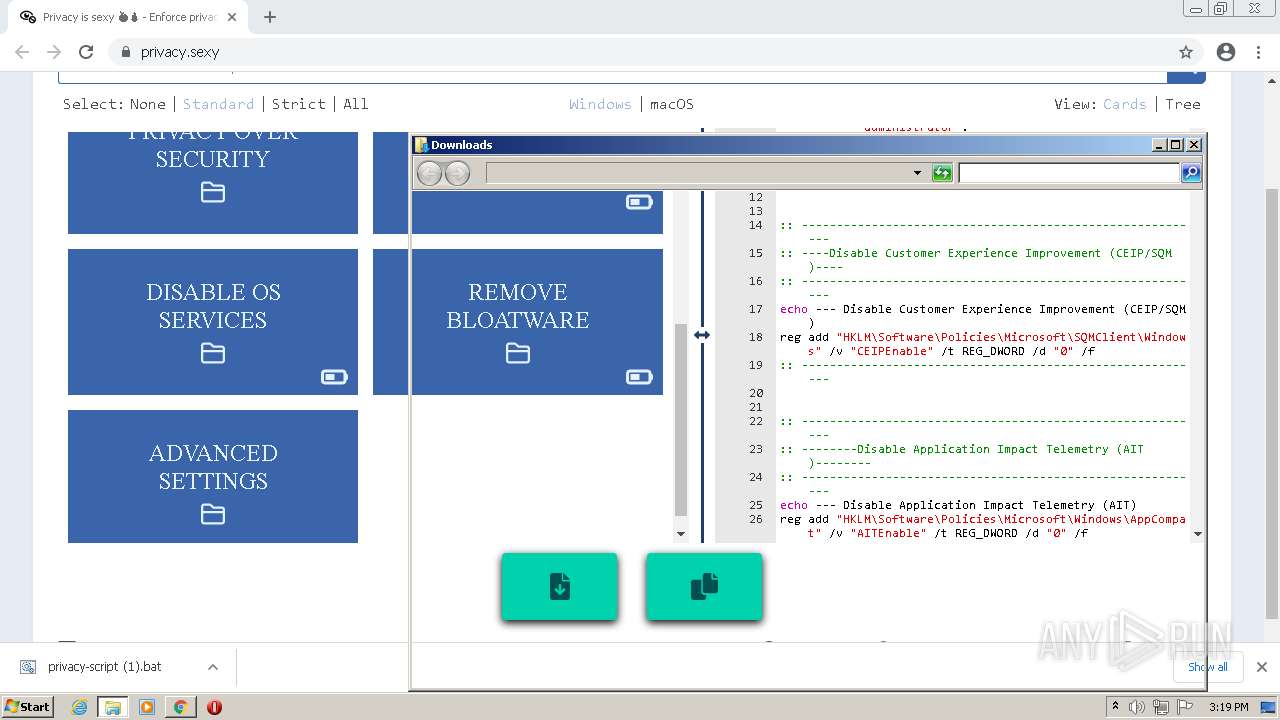
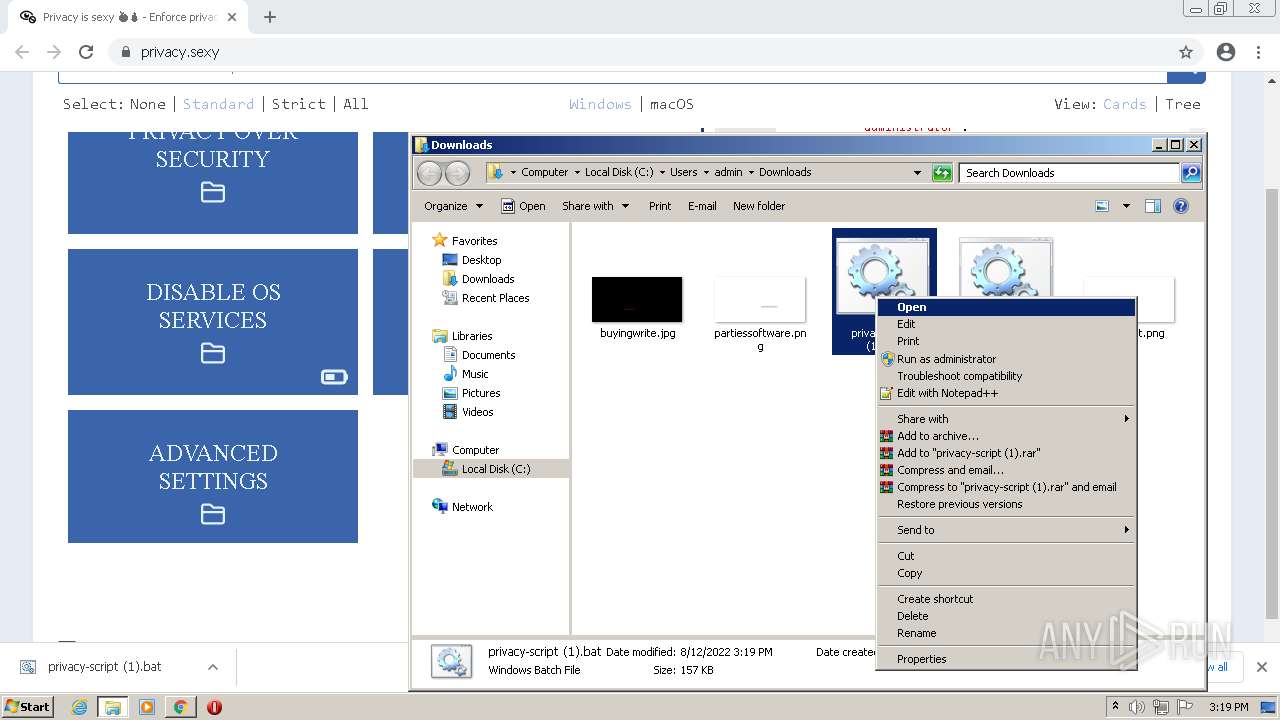
Manual execution by user
- cmd.exe (PID: 472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
528
Monitored processes
477
Malicious processes
17
Suspicious processes
64
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | reg add "HKLM\SOFTWARE\Policies\Google\Chrome" /v "ChromeCleanupReportingEnabled" /t REG_DWORD /d 0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | PowerShell -ExecutionPolicy Unrestricted -Command "$serviceName = 'LogiRegistryService'; Write-Host """Disabling service: `"""$serviceName`"""."""; <# -- 1. Skip if service does not exist #>; $service = Get-Service -Name $serviceName -ErrorAction SilentlyContinue; if(!$service) {; Write-Host """Service `"""$serviceName`""" could not be not found, no need to disable it."""; Exit 0; }; <# -- 2. Stop if running #>; if ($service.Status -eq [System.ServiceProcess.ServiceControllerStatus]::Running) {; Write-Host """`"""$serviceName`""" is running, stopping it."""; try {; Stop-Service -Name """$serviceName""" -Force -ErrorAction Stop; Write-Host """Stopped `"""$serviceName`""" successfully."""; } catch {; Write-Warning """Could not stop `"""$serviceName`""", it will be stopped after reboot: $_"""; }; } else {; Write-Host """`"""$serviceName`""" is not running, no need to stop."""; }; <# -- 3. Skip if already disabled #>; $startupType = $service.StartType <# Does not work before .NET 4.6.1 #>; if(!$startupType) {; $startupType = (Get-WmiObject -Query """Select StartMode From Win32_Service Where Name='$serviceName'""" -ErrorAction Ignore).StartMode; if(!$startupType) {; $startupType = (Get-WmiObject -Class Win32_Service -Property StartMode -Filter """Name='$serviceName'""" -ErrorAction Ignore).StartMode; }; }; if($startupType -eq 'Disabled') {; Write-Host """$serviceName is already disabled, no further action is needed"""; }; <# -- 4. Disable service #>; try {; Set-Service -Name """$serviceName""" -StartupType Disabled -Confirm:$false -ErrorAction Stop; Write-Host """Disabled `"""$serviceName`""" successfully."""; } catch {; Write-Error """Could not disable `"""$serviceName`""": $_"""; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 128 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows\SettingSync" /v "DisableCredentialsSettingSyncUserOverride" /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | PowerShell -ExecutionPolicy Unrestricted -Command "$serviceName = 'PcaSvc'; Write-Host """Disabling service: `"""$serviceName`"""."""; <# -- 1. Skip if service does not exist #>; $service = Get-Service -Name $serviceName -ErrorAction SilentlyContinue; if(!$service) {; Write-Host """Service `"""$serviceName`""" could not be not found, no need to disable it."""; Exit 0; }; <# -- 2. Stop if running #>; if ($service.Status -eq [System.ServiceProcess.ServiceControllerStatus]::Running) {; Write-Host """`"""$serviceName`""" is running, stopping it."""; try {; Stop-Service -Name """$serviceName""" -Force -ErrorAction Stop; Write-Host """Stopped `"""$serviceName`""" successfully."""; } catch {; Write-Warning """Could not stop `"""$serviceName`""", it will be stopped after reboot: $_"""; }; } else {; Write-Host """`"""$serviceName`""" is not running, no need to stop."""; }; <# -- 3. Skip if already disabled #>; $startupType = $service.StartType <# Does not work before .NET 4.6.1 #>; if(!$startupType) {; $startupType = (Get-WmiObject -Query """Select StartMode From Win32_Service Where Name='$serviceName'""" -ErrorAction Ignore).StartMode; if(!$startupType) {; $startupType = (Get-WmiObject -Class Win32_Service -Property StartMode -Filter """Name='$serviceName'""" -ErrorAction Ignore).StartMode; }; }; if($startupType -eq 'Disabled') {; Write-Host """$serviceName is already disabled, no further action is needed"""; }; <# -- 4. Disable service #>; try {; Set-Service -Name """$serviceName""" -StartupType Disabled -Confirm:$false -ErrorAction Stop; Write-Host """Disabled `"""$serviceName`""" successfully."""; } catch {; Write-Error """Could not disable `"""$serviceName`""": $_"""; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 320 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows\Windows Search" /v "AllowCortanaAboveLock" /t REG_DWORD /d 0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,5122788229929906378,17220220202499454328,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 364 | reg add "HKLM\Software\Policies\Microsoft\Windows\AppCompat" /v "AITEnable" /t REG_DWORD /d "0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | reg delete "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Map Network Drive MRU" /va /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows\AppPrivacy" /v "LetAppsAccessMotion_ForceAllowTheseApps" /t REG_MULTI_SZ /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows\Windows Search" /v "DisableWebSearch" /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
156 774
Read events
155 794
Write events
931
Delete events
49
Modification events
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
187
Suspicious files
134
Text files
108
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F660BE-A5C.pma | — | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d1f12404-abdd-4601-9906-051eee7dad46.tmp | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFf62b8.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf618f.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf618f.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
21
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
912 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
912 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 178 Kb | whitelisted |
912 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 259 Kb | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 520 Kb | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 21.0 Kb | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | binary | 5.68 Kb | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | pgc | 3.61 Kb | whitelisted |
912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 1.02 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3452 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 18.66.139.46:443 | privacy.sexy | Massachusetts Institute of Technology | US | suspicious |
3452 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3452 | chrome.exe | 142.250.185.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 18.66.139.69:443 | privacy.sexy | Massachusetts Institute of Technology | US | suspicious |
3452 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 18.66.139.49:443 | privacy.sexy | Massachusetts Institute of Technology | US | malicious |
3452 | chrome.exe | 142.250.186.35:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 142.250.179.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
912 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
privacy.sexy |
| suspicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Dism.exe | PID=1716 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=1716 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=1716 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=1716 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=1716 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=1716 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
Dism.exe | PID=1716 Getting Provider OSServices - CDISMProviderStore::GetProvider |
Dism.exe | PID=1716 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
Dism.exe | PID=1716 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |
dismhost.exe | PID=3272 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |