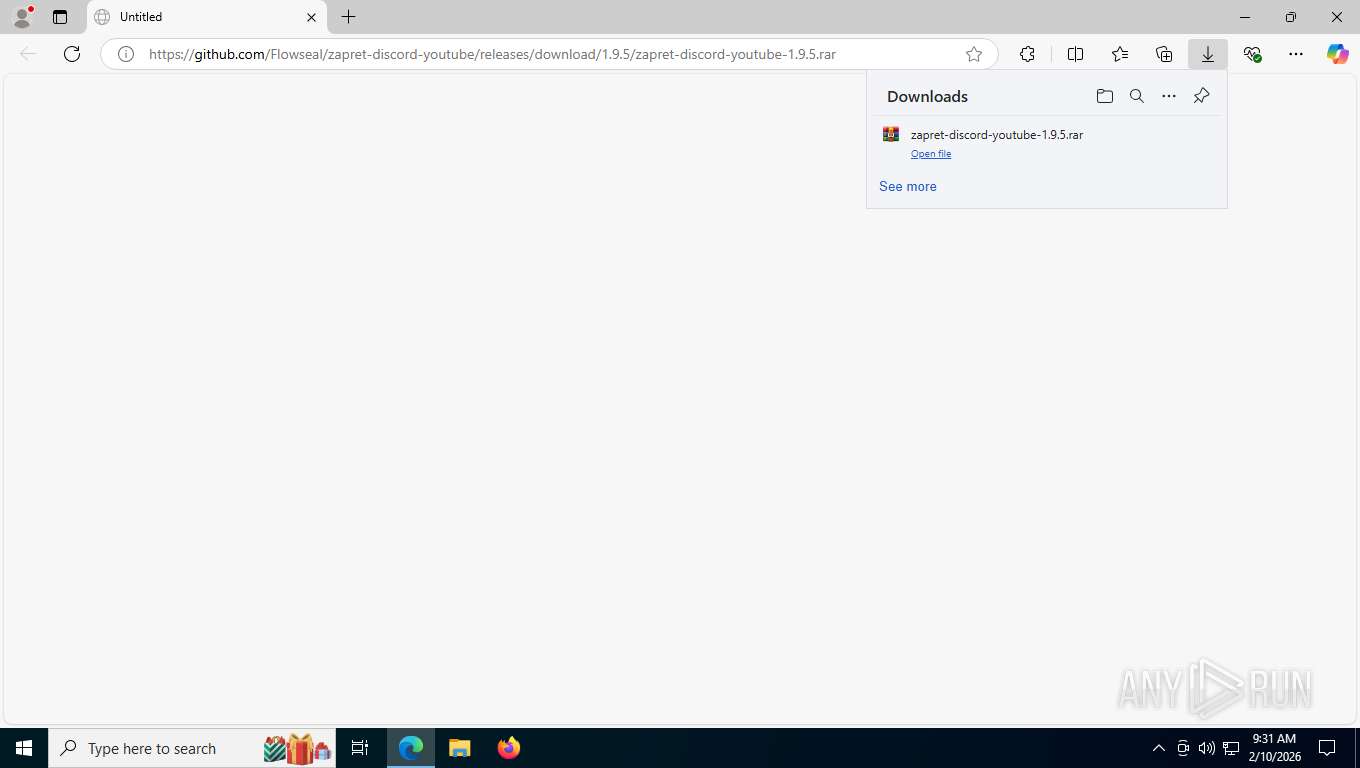
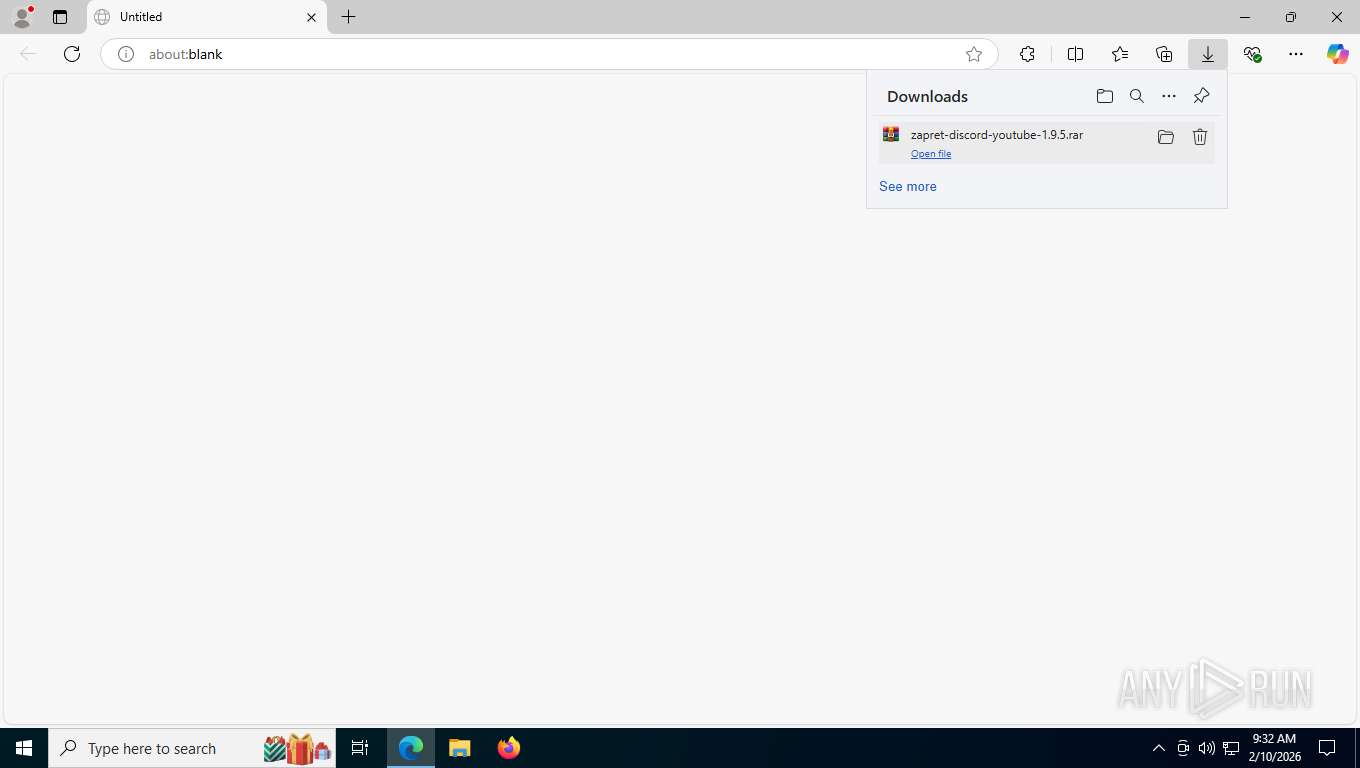
| URL: | https://github.com/Flowseal/zapret-discord-youtube/releases/download/1.9.5/zapret-discord-youtube-1.9.5.rar |
| Full analysis: | https://app.any.run/tasks/dd2a80b7-0752-42ea-9256-53d2bb6e1449 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2026, 14:31:43 |
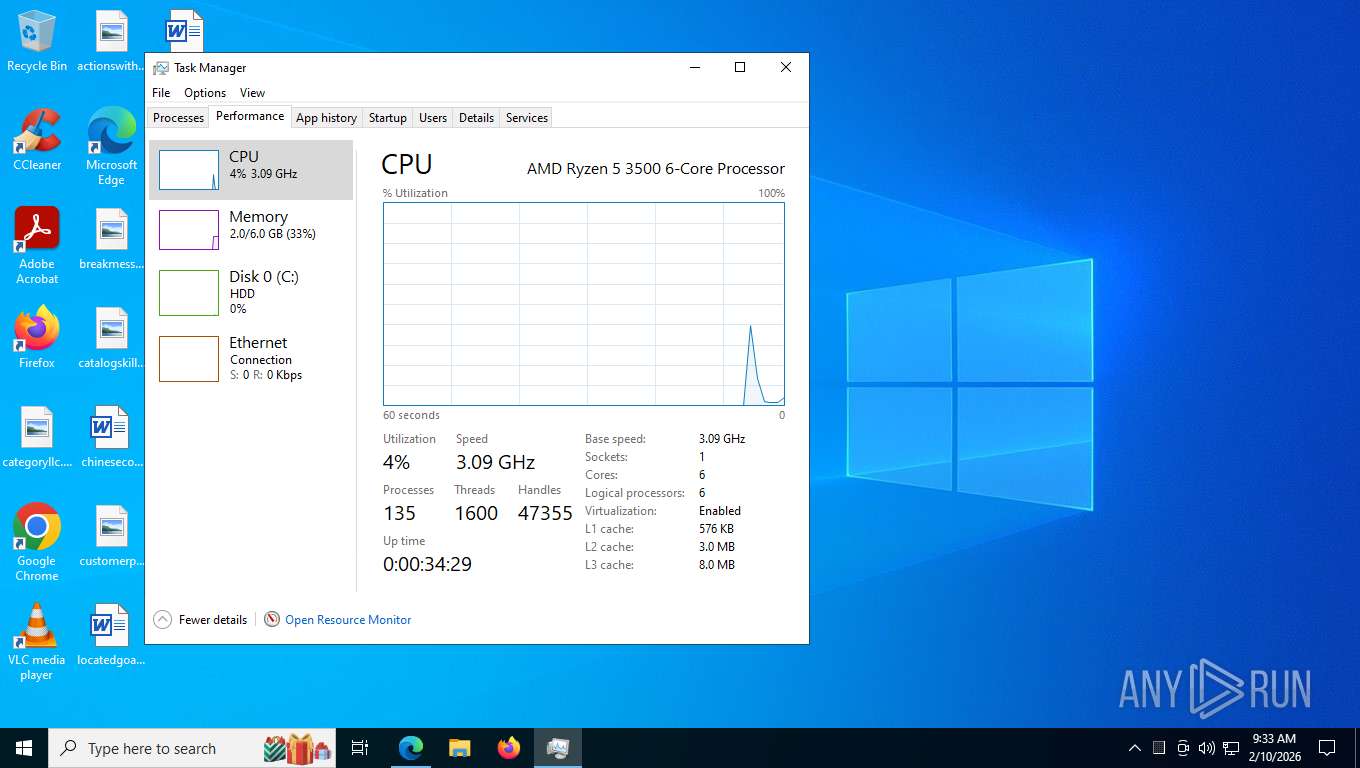
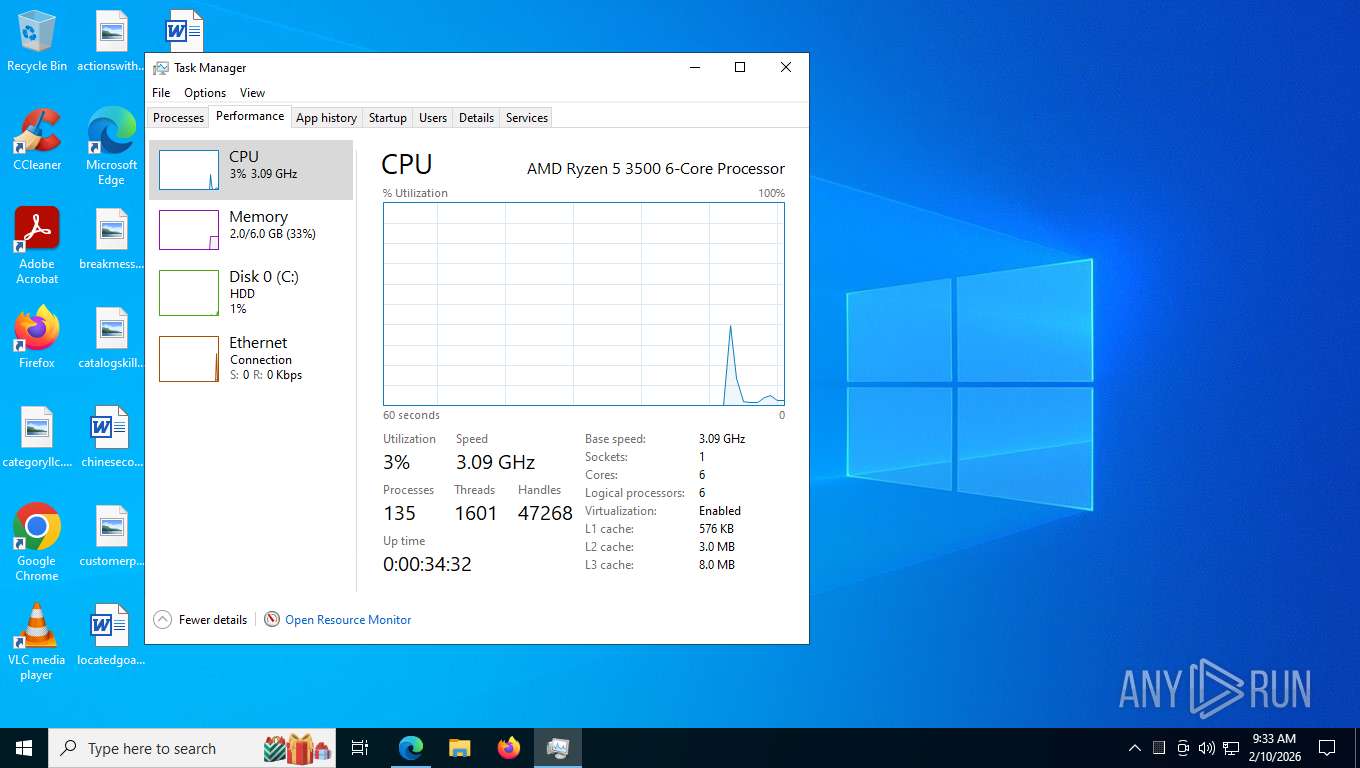
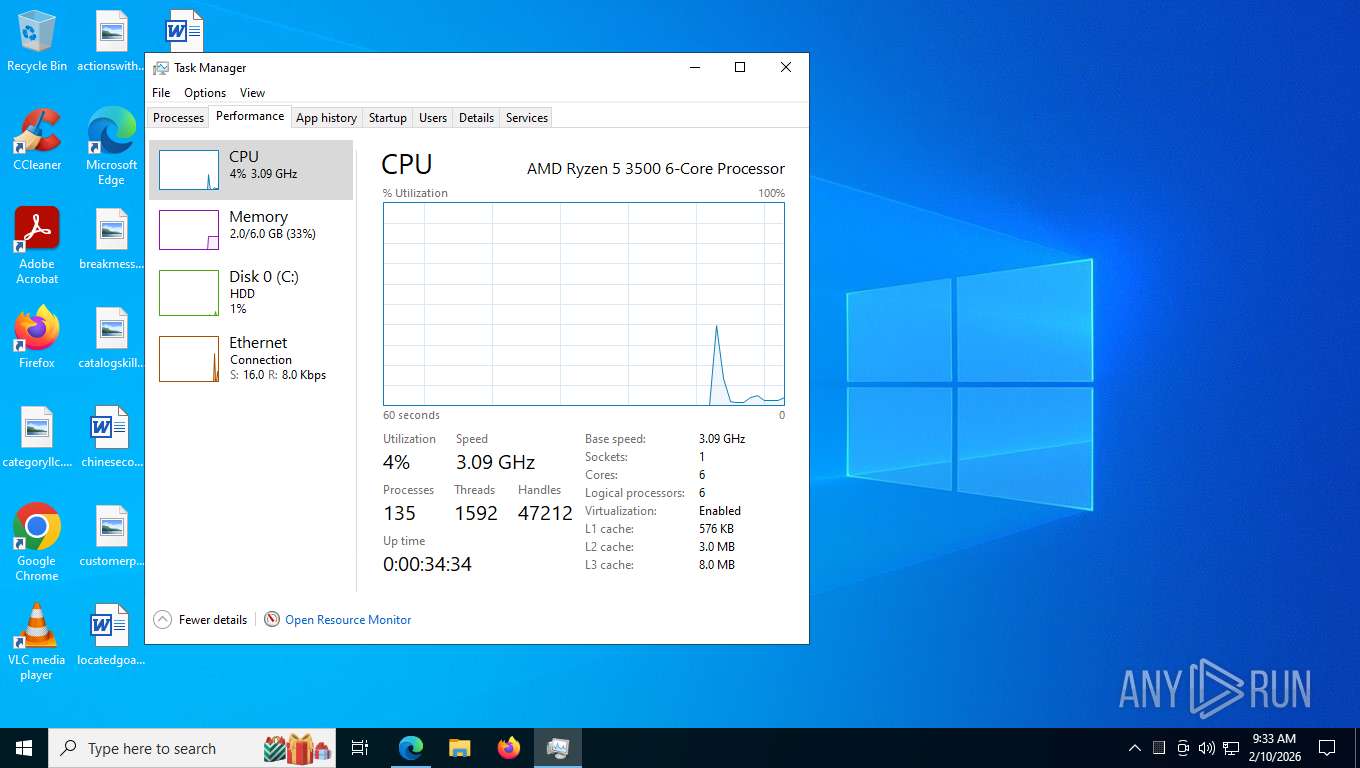
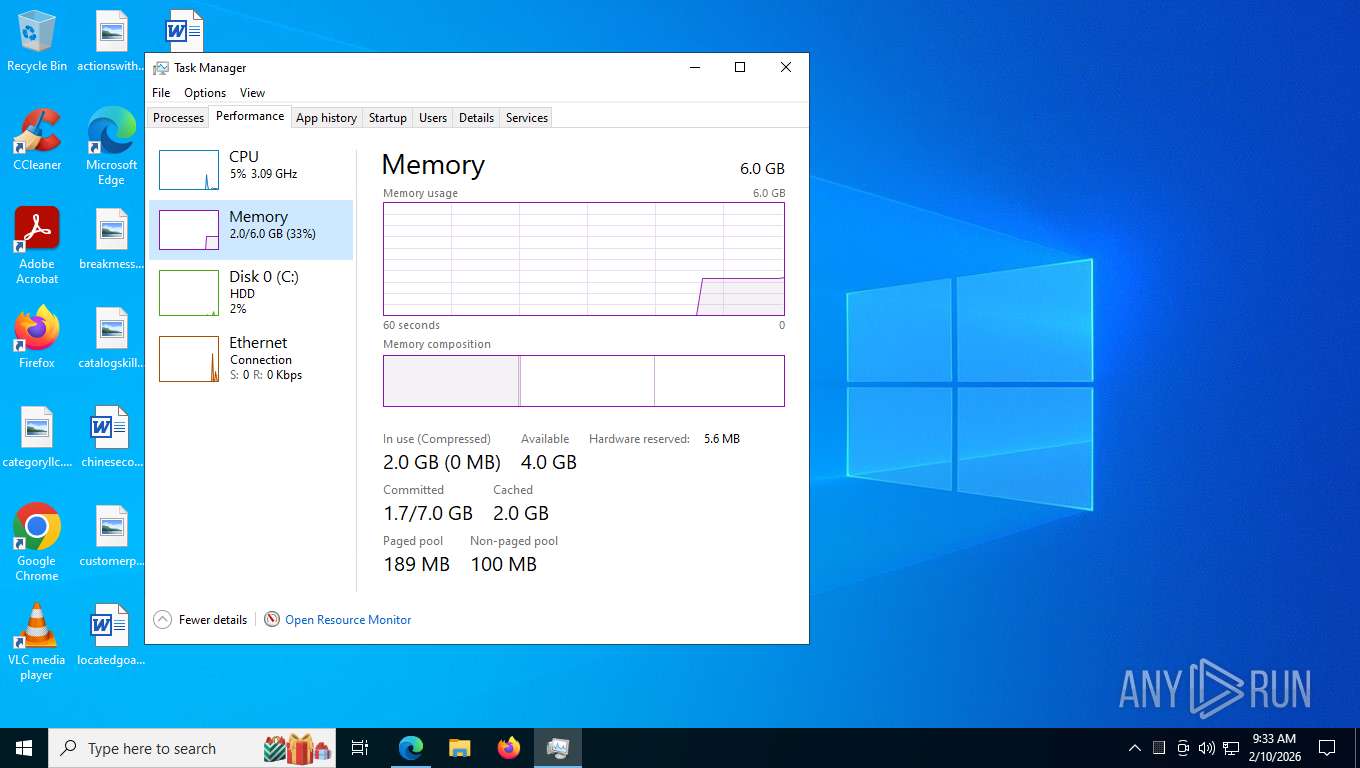
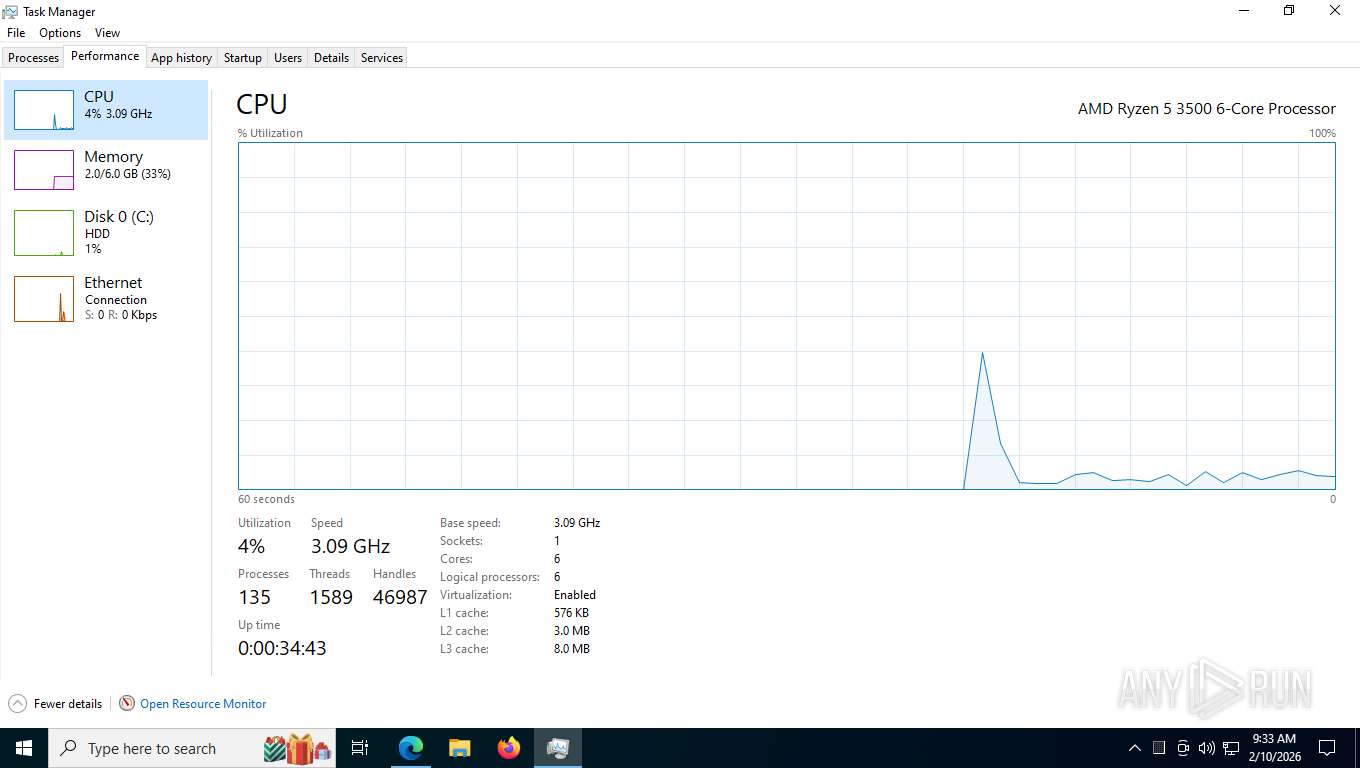
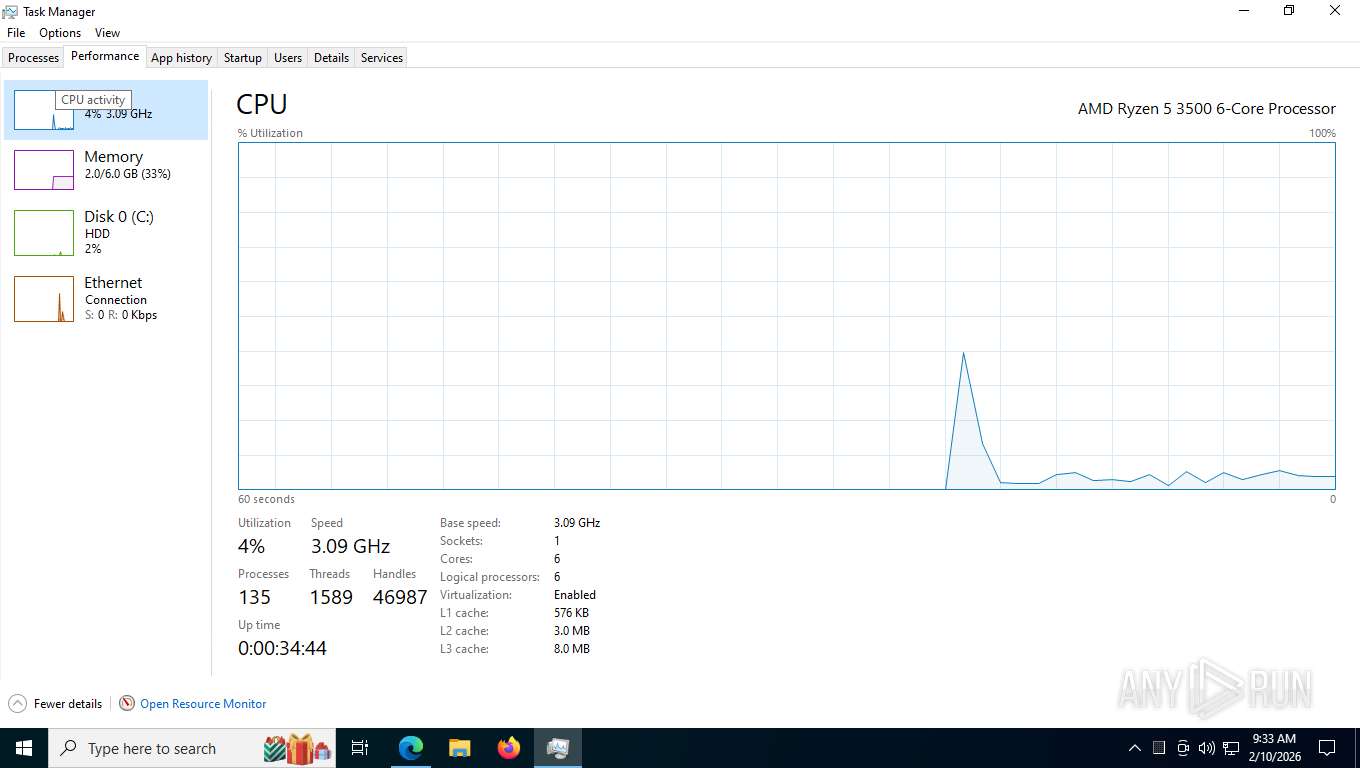
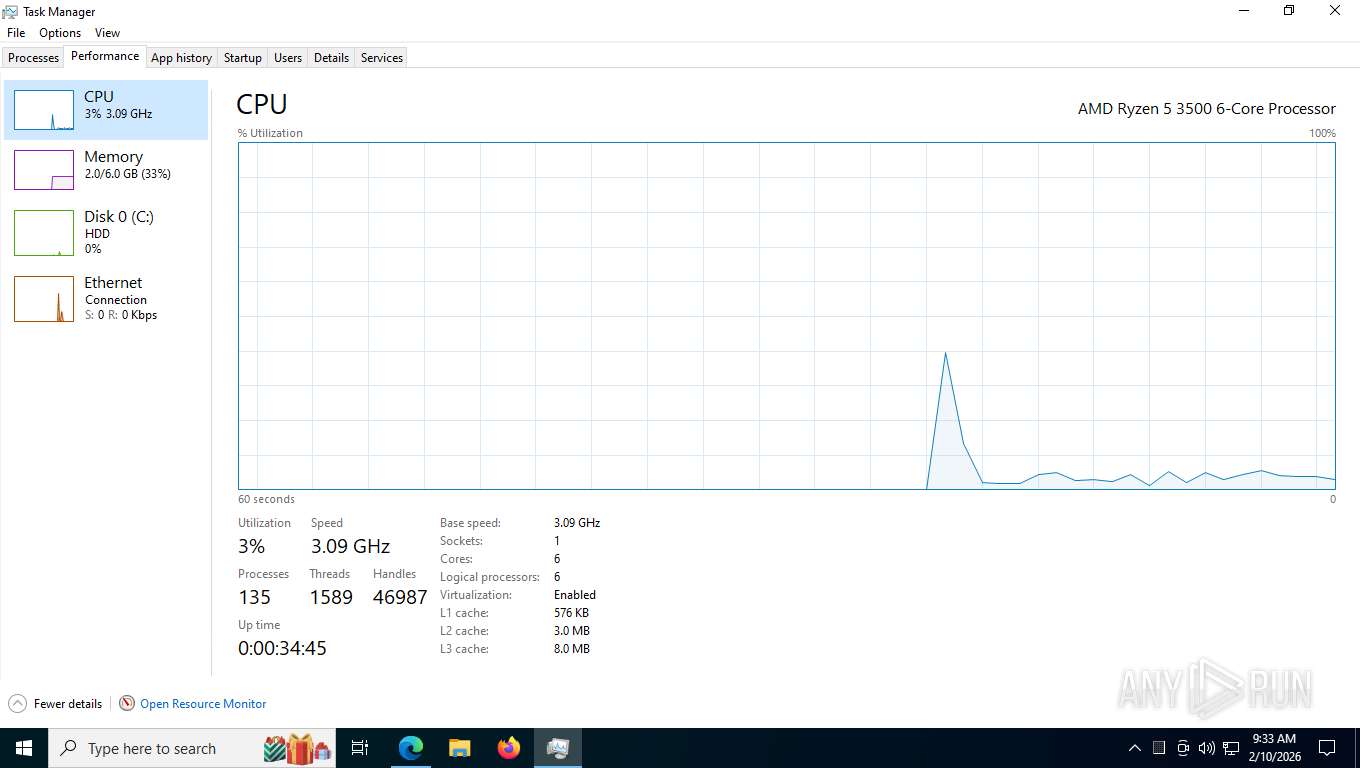
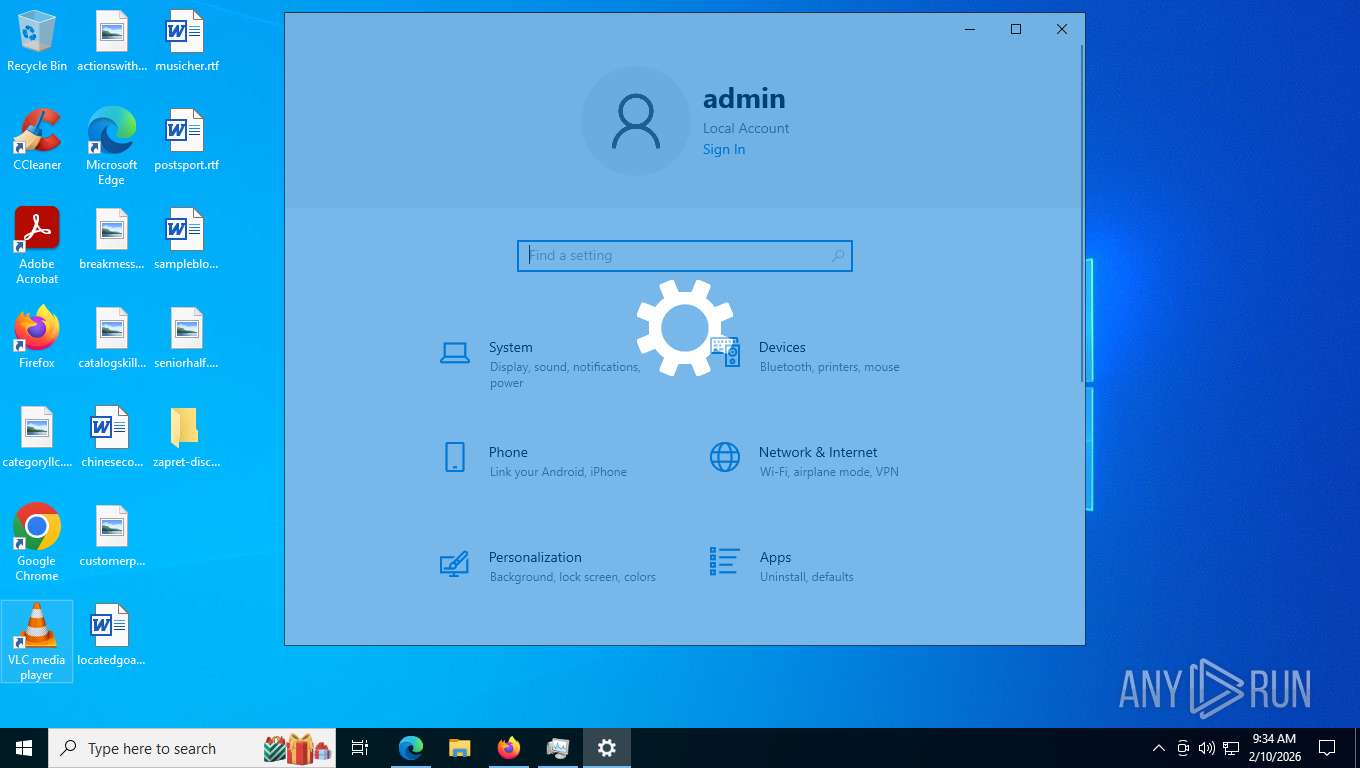
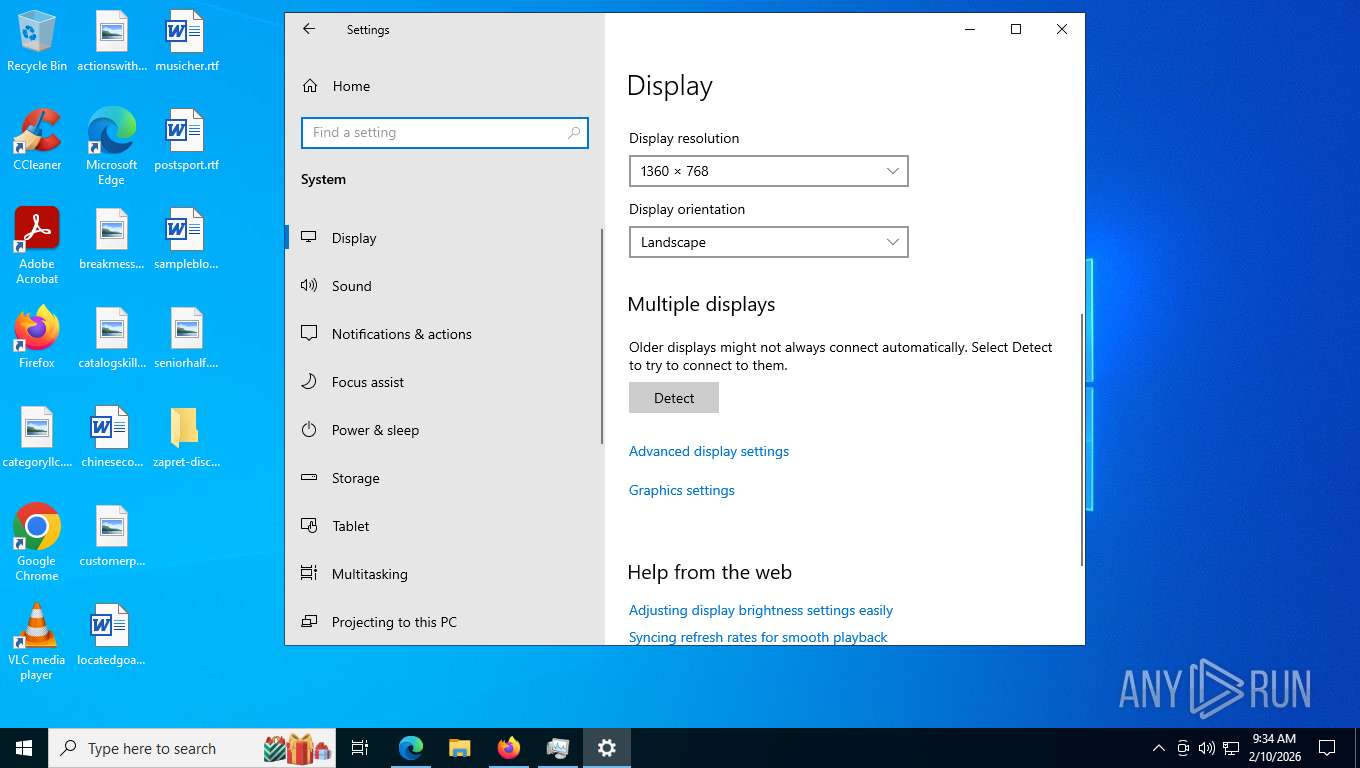
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B3D73847F3A0577D1FA774909CCC2A91 |
| SHA1: | 623C06364AA69E4633459D6F2D0A05451A0AC3BD |
| SHA256: | D4D538B7D160DA9F856CDC1626854D02A7D48429F594A995D5DE474D79B2DF0F |
| SSDEEP: | 3:N8tEdFtE2Eyd8WPtkCUW38Ed8WN9:2uBE2BdFl6UBdFz |
MALICIOUS
Malicious driver has been detected
- msedge.exe (PID: 1612)
- msedge.exe (PID: 7376)
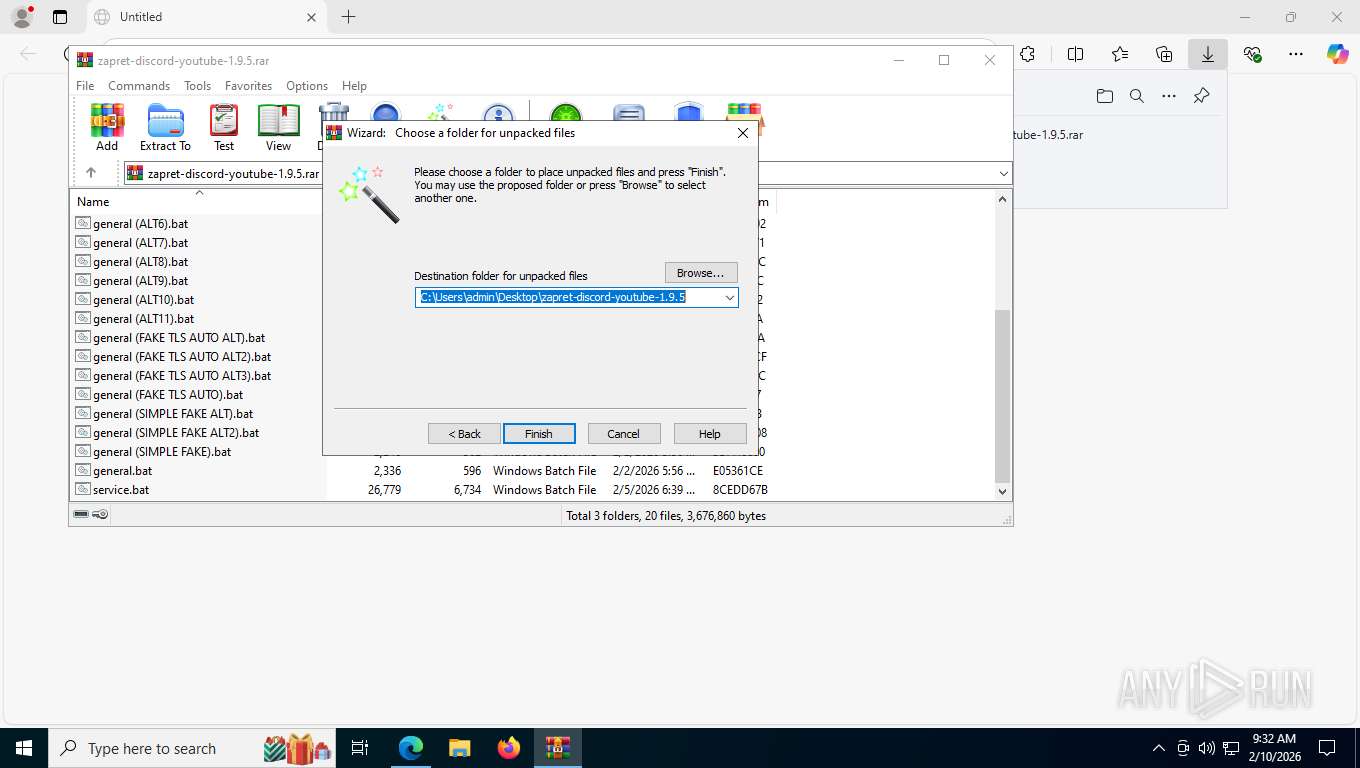
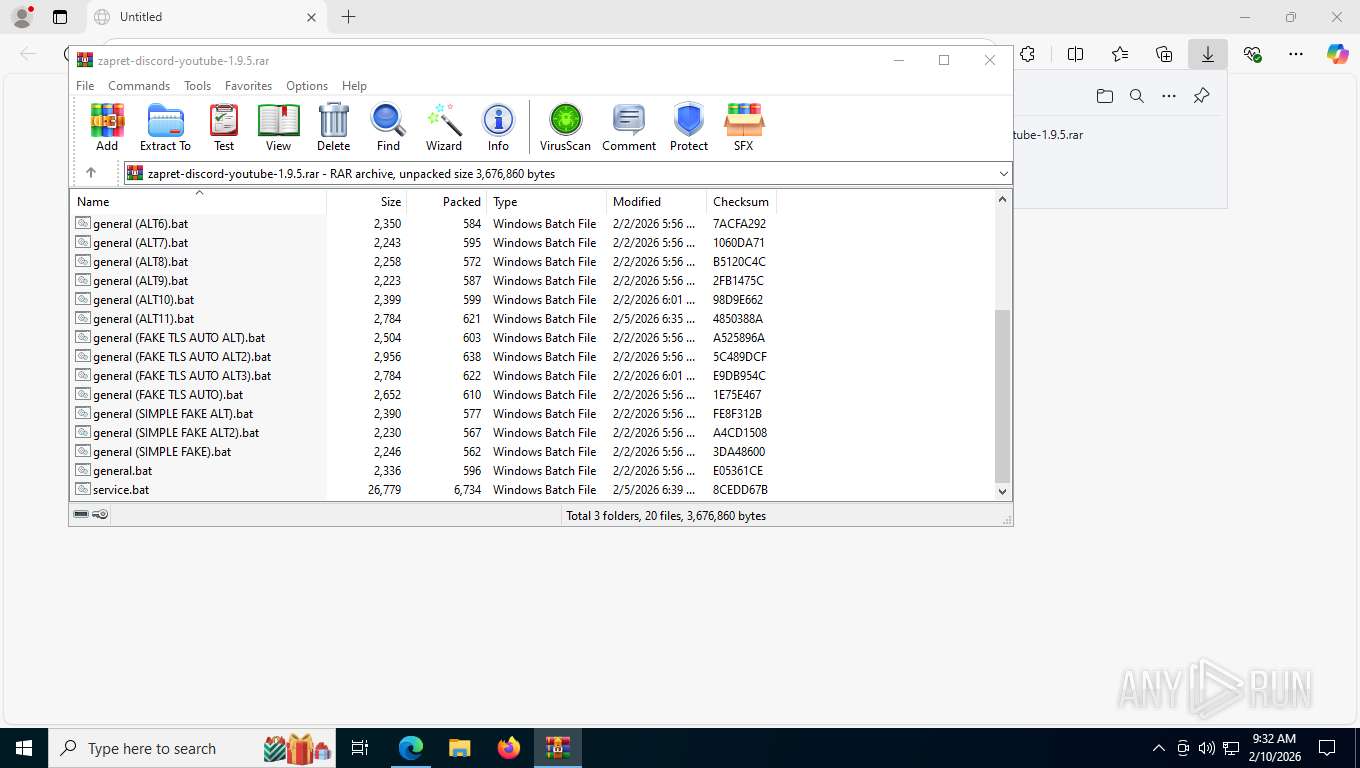
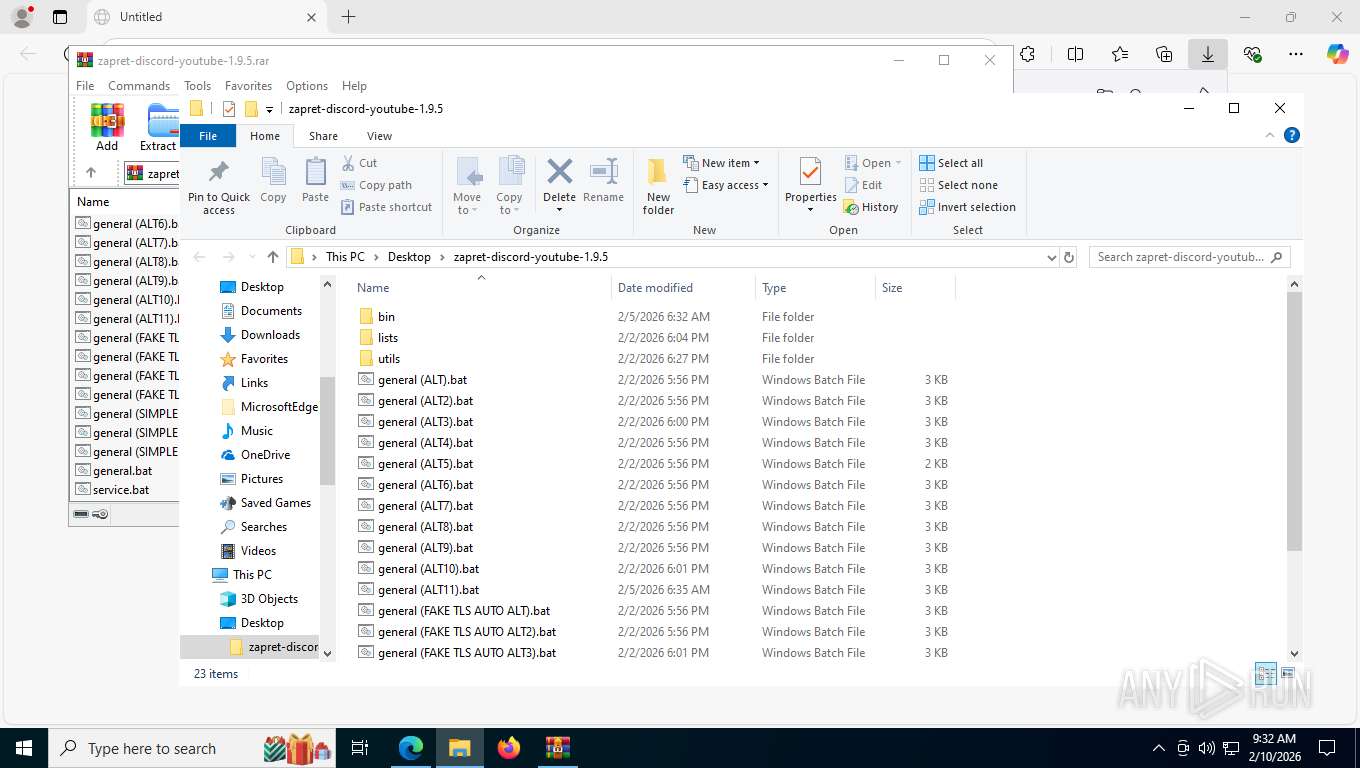
- WinRAR.exe (PID: 848)
Detects Cygwin installation
- WinRAR.exe (PID: 848)
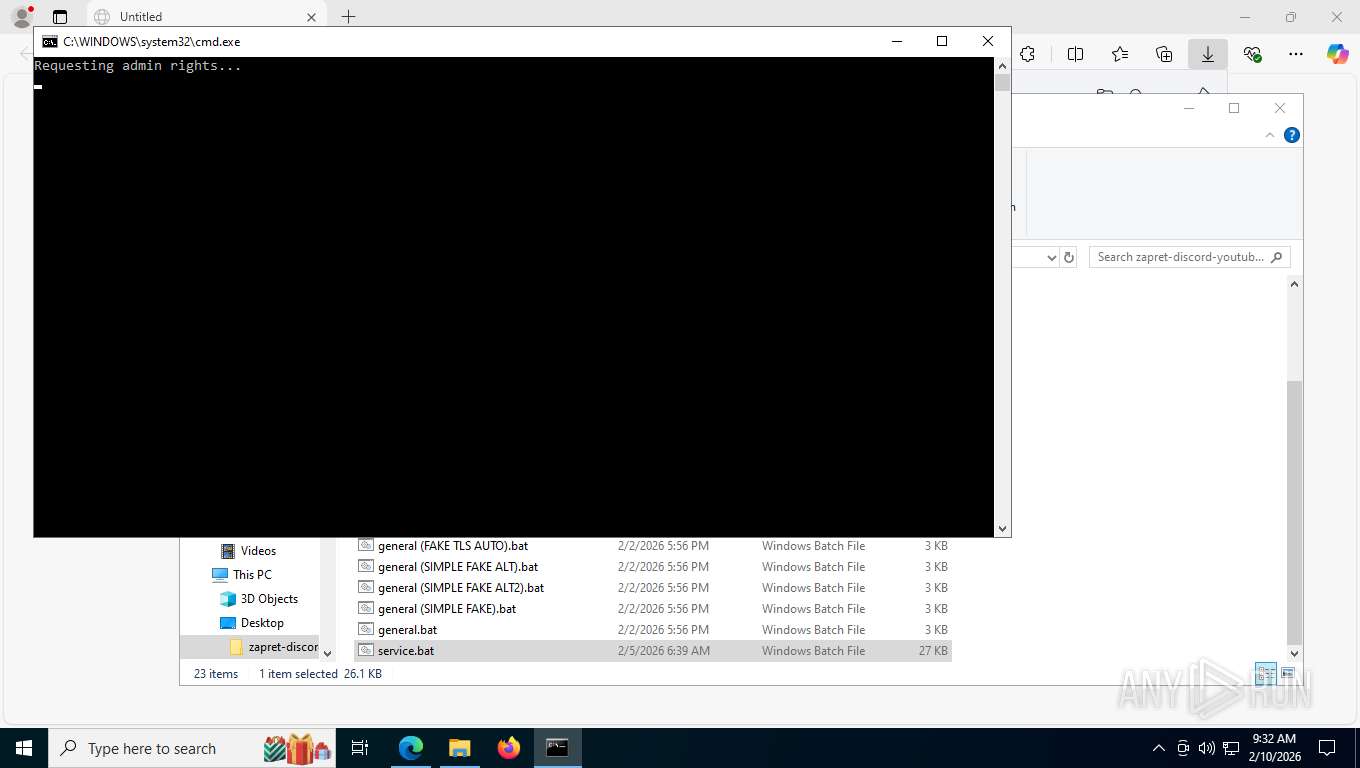
Starts NET.EXE for service management
- cmd.exe (PID: 7544)
- net.exe (PID: 7652)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 848)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7408)
- cmd.exe (PID: 796)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7408)
- cmd.exe (PID: 796)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7764)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 6360)
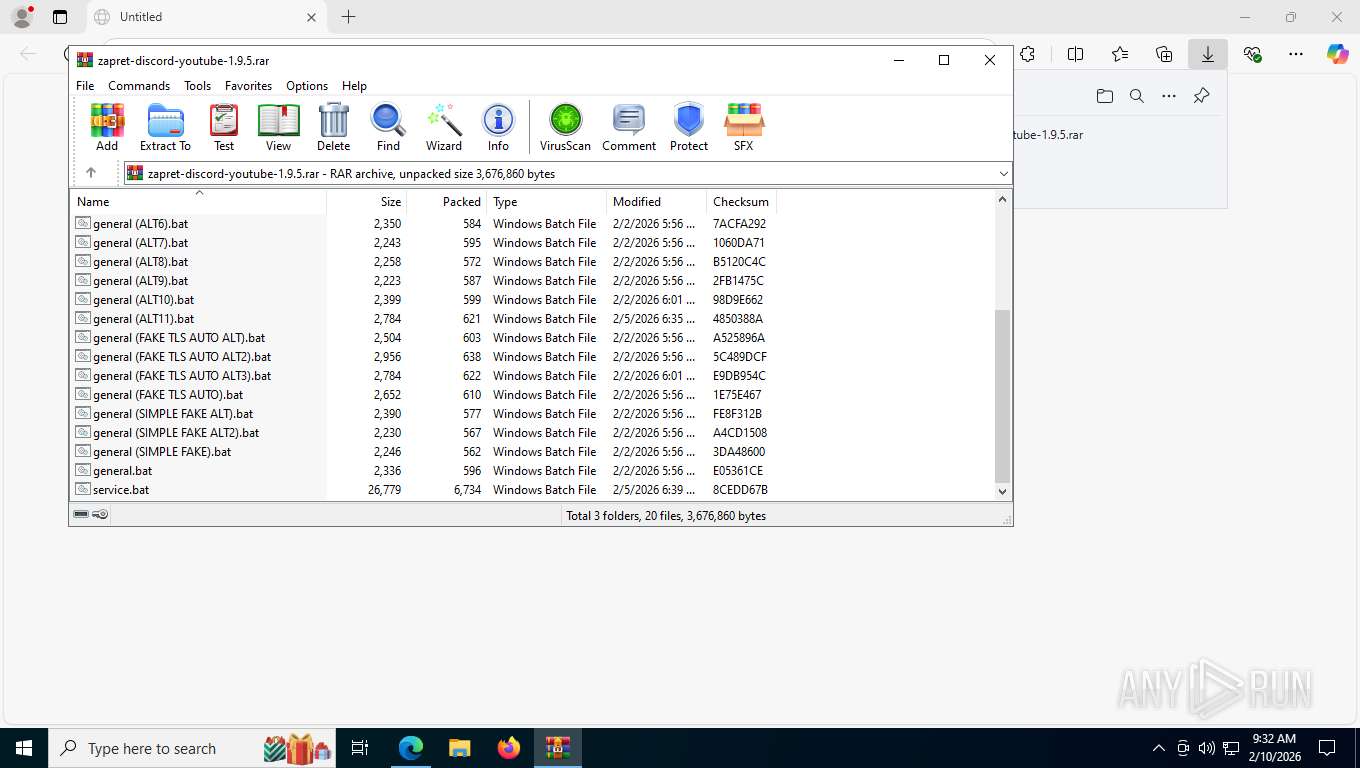
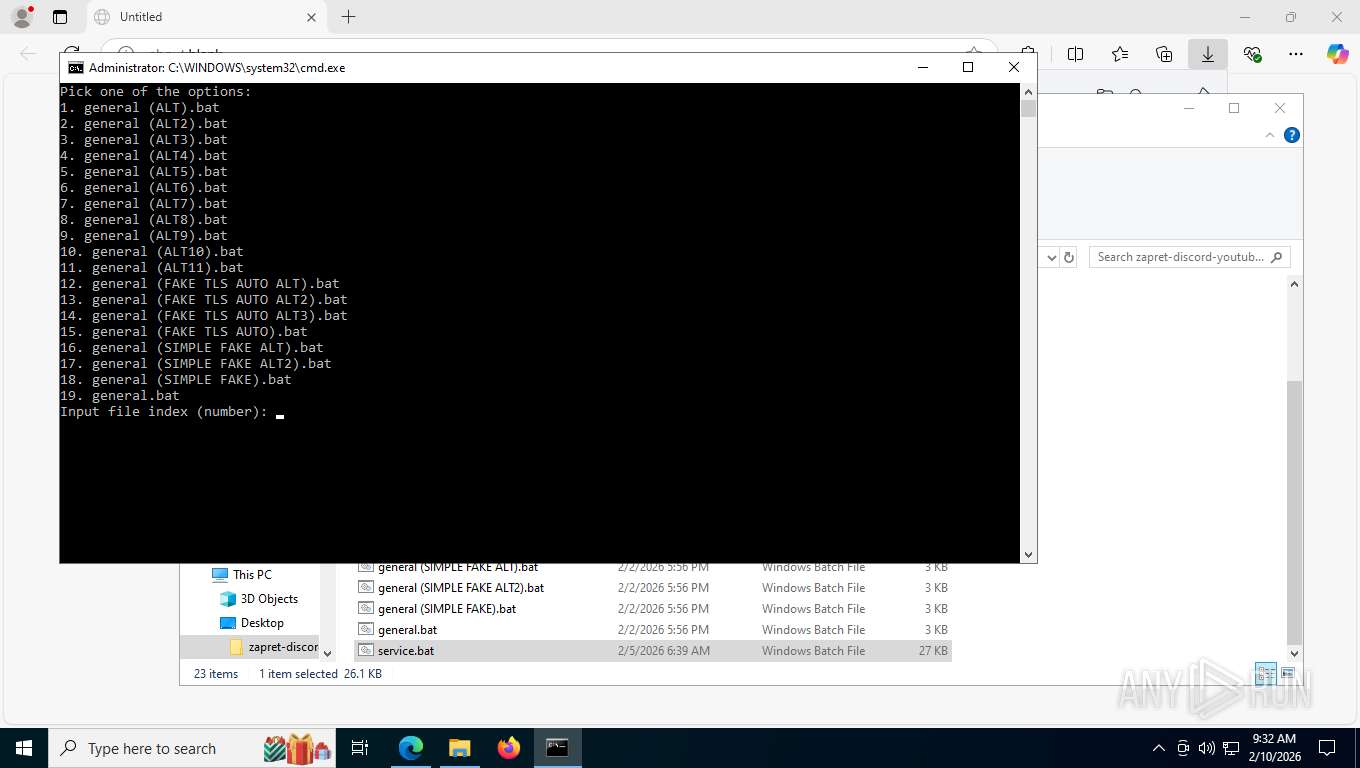
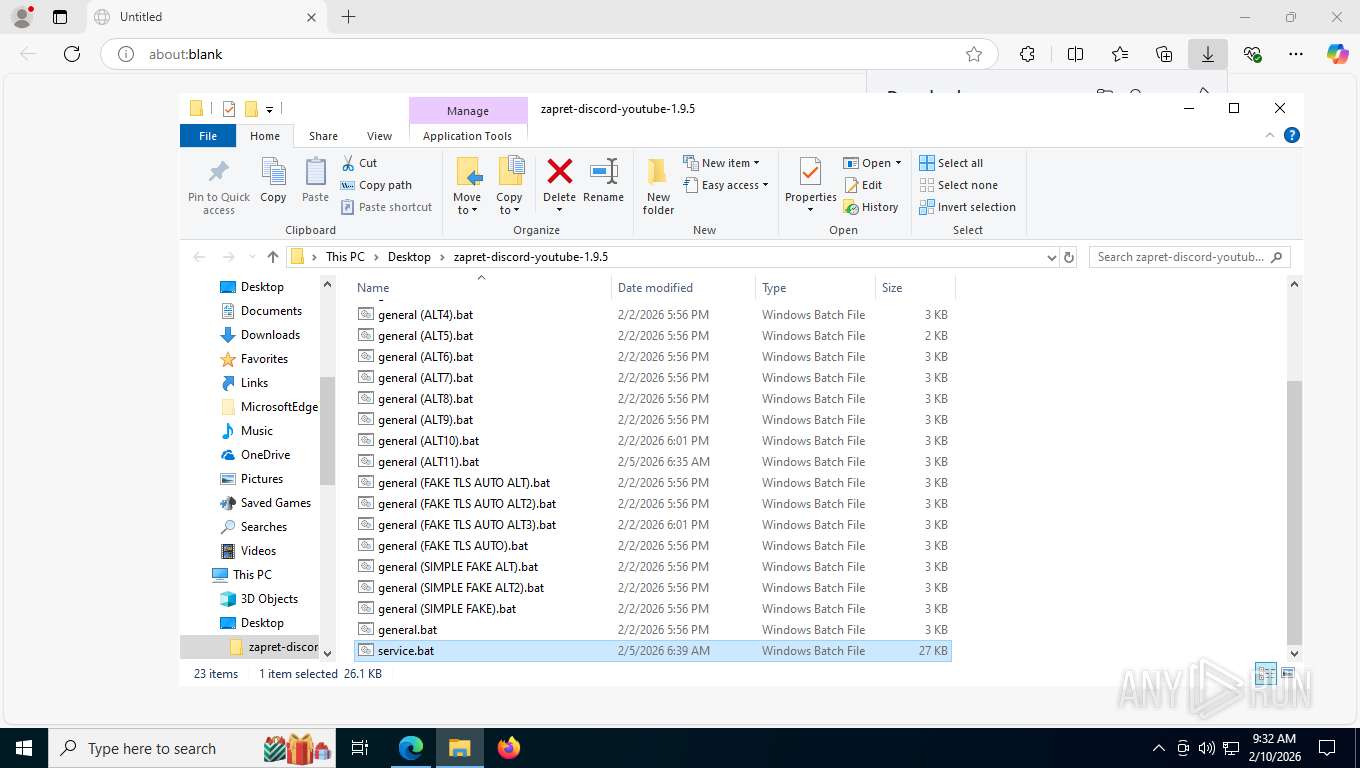
Executing commands from a ".bat" file
- powershell.exe (PID: 7764)
- cmd.exe (PID: 7544)
Application launched itself
- cmd.exe (PID: 7544)
- cmd.exe (PID: 6360)
Starts application with an unusual extension
- cmd.exe (PID: 7544)
Hides command output
- cmd.exe (PID: 6360)
- cmd.exe (PID: 7296)
Starts process via Powershell
- powershell.exe (PID: 7764)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 1632)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 796)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7544)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7544)
Filtering the input of cmdlet (POWERSHELL)
- powershell.exe (PID: 1632)
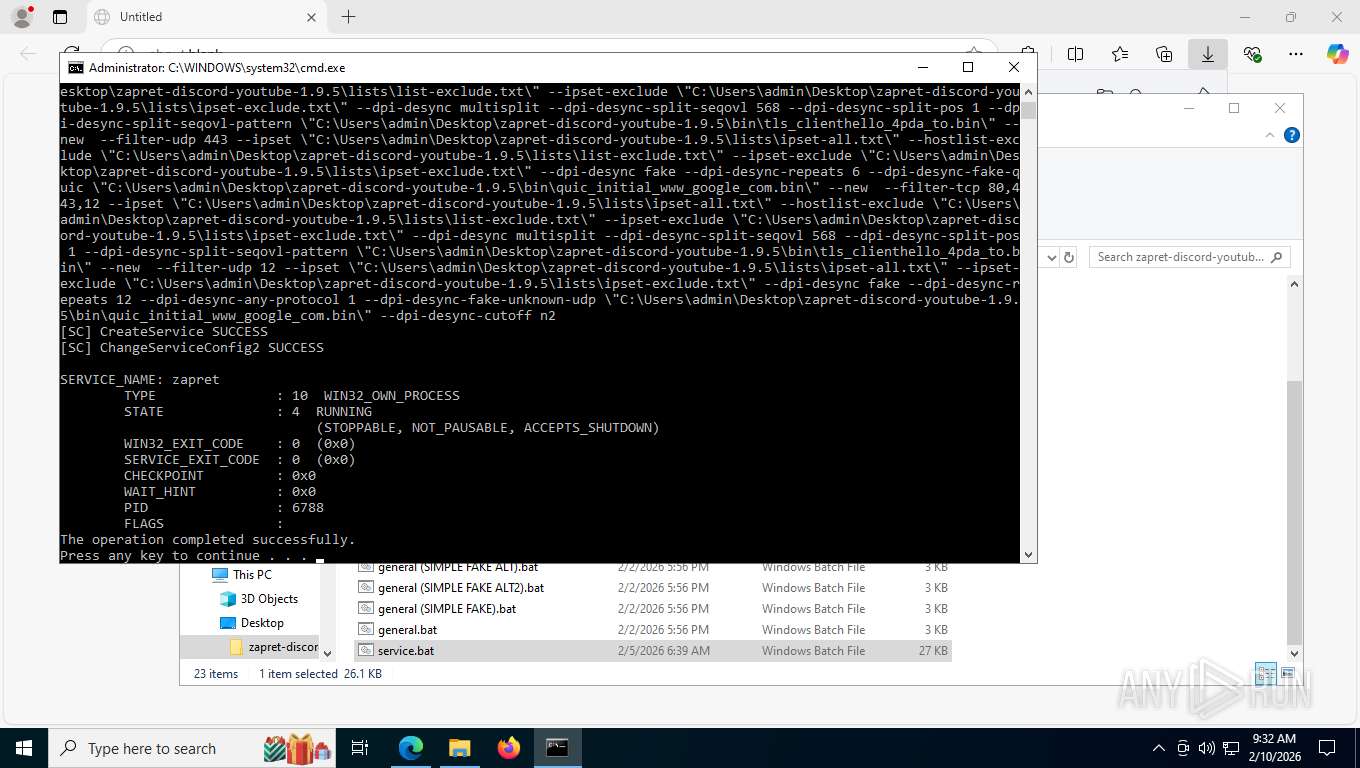
Windows service management via SC.EXE
- sc.exe (PID: 5460)
- sc.exe (PID: 6904)
- sc.exe (PID: 7408)
Creates a new Windows service
- sc.exe (PID: 6392)
Starts SC.EXE for service management
- cmd.exe (PID: 7544)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7544)
Creates or modifies Windows services
- reg.exe (PID: 7552)
Executes as Windows Service
- winws.exe (PID: 6788)
Reads the date of Windows installation
- SystemSettings.exe (PID: 1956)
INFO
The sample compiled with english language support
- msedge.exe (PID: 7376)
- msedge.exe (PID: 1612)
- WinRAR.exe (PID: 848)
Drops script file
- msedge.exe (PID: 1612)
- msedge.exe (PID: 7376)
- msedge.exe (PID: 6600)
- WinRAR.exe (PID: 848)
- cmd.exe (PID: 7408)
- powershell.exe (PID: 7764)
- cmd.exe (PID: 7544)
- powershell.exe (PID: 1632)
- cmd.exe (PID: 9168)
- firefox.exe (PID: 9168)
Reads Environment values
- identity_helper.exe (PID: 1876)
Reads the computer name
- identity_helper.exe (PID: 1876)
- winws.exe (PID: 6788)
- SystemSettings.exe (PID: 1956)
Checks supported languages
- identity_helper.exe (PID: 1876)
- chcp.com (PID: 8956)
- chcp.com (PID: 8176)
- chcp.com (PID: 1856)
- chcp.com (PID: 7648)
- winws.exe (PID: 6788)
- SystemSettings.exe (PID: 1956)
Launching a file from the Downloads directory
- msedge.exe (PID: 7376)
Application launched itself
- msedge.exe (PID: 7376)
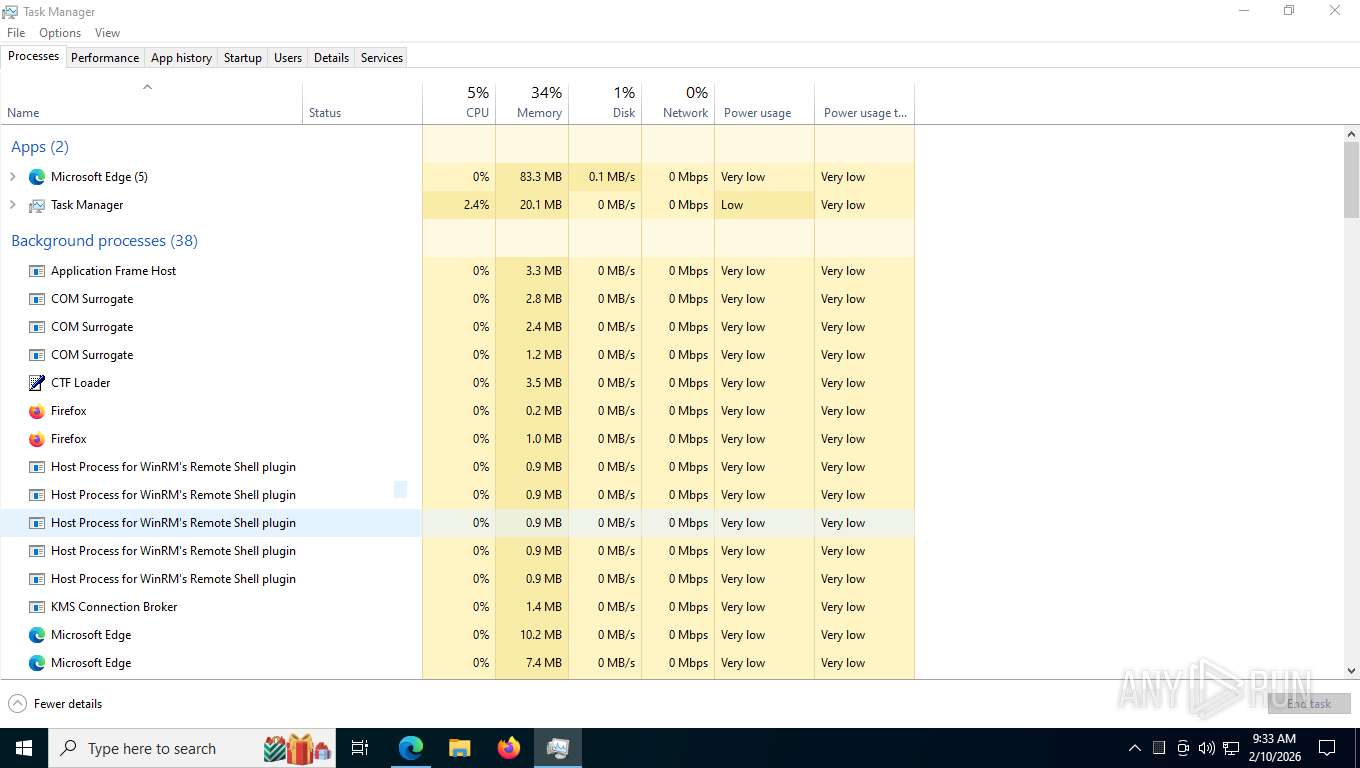
- firefox.exe (PID: 6608)
- firefox.exe (PID: 9168)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 848)
- firefox.exe (PID: 9168)
Reads security settings of Internet Explorer
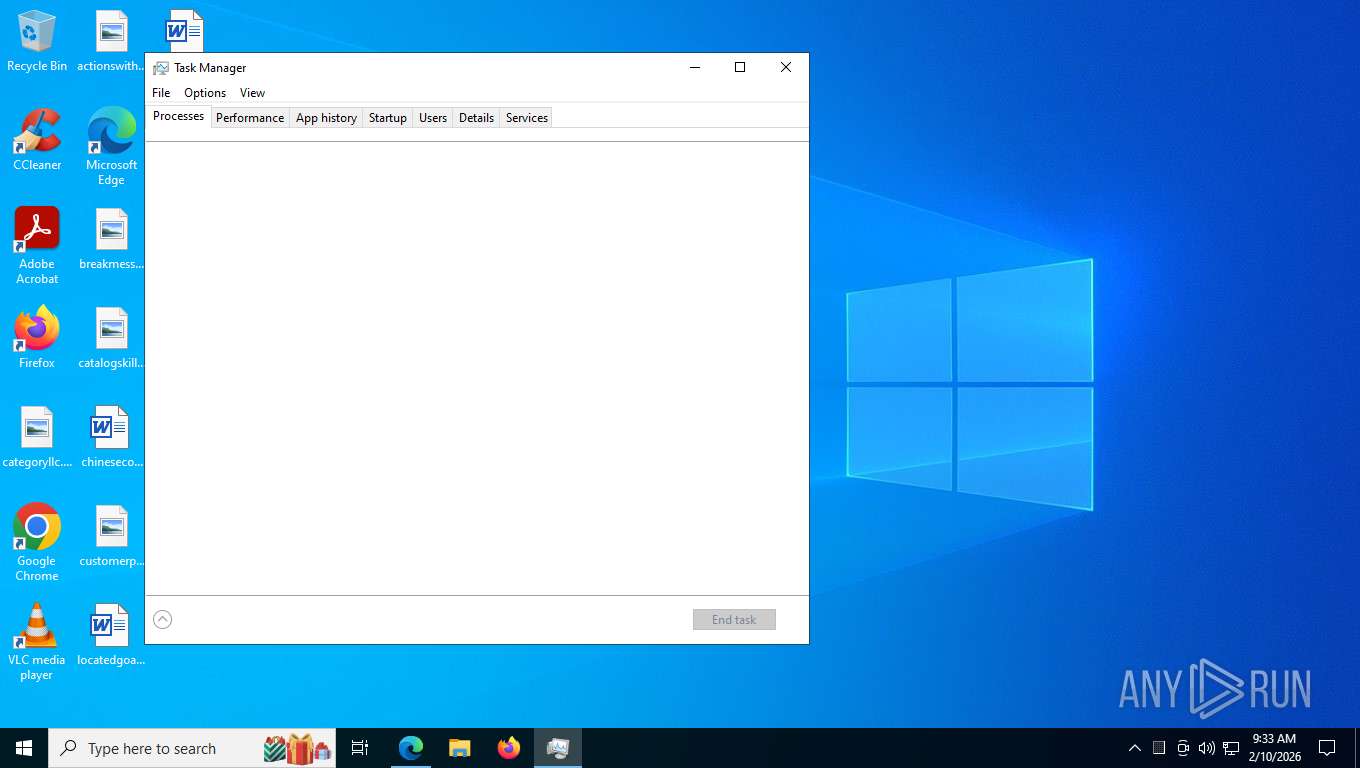
- WinRAR.exe (PID: 848)
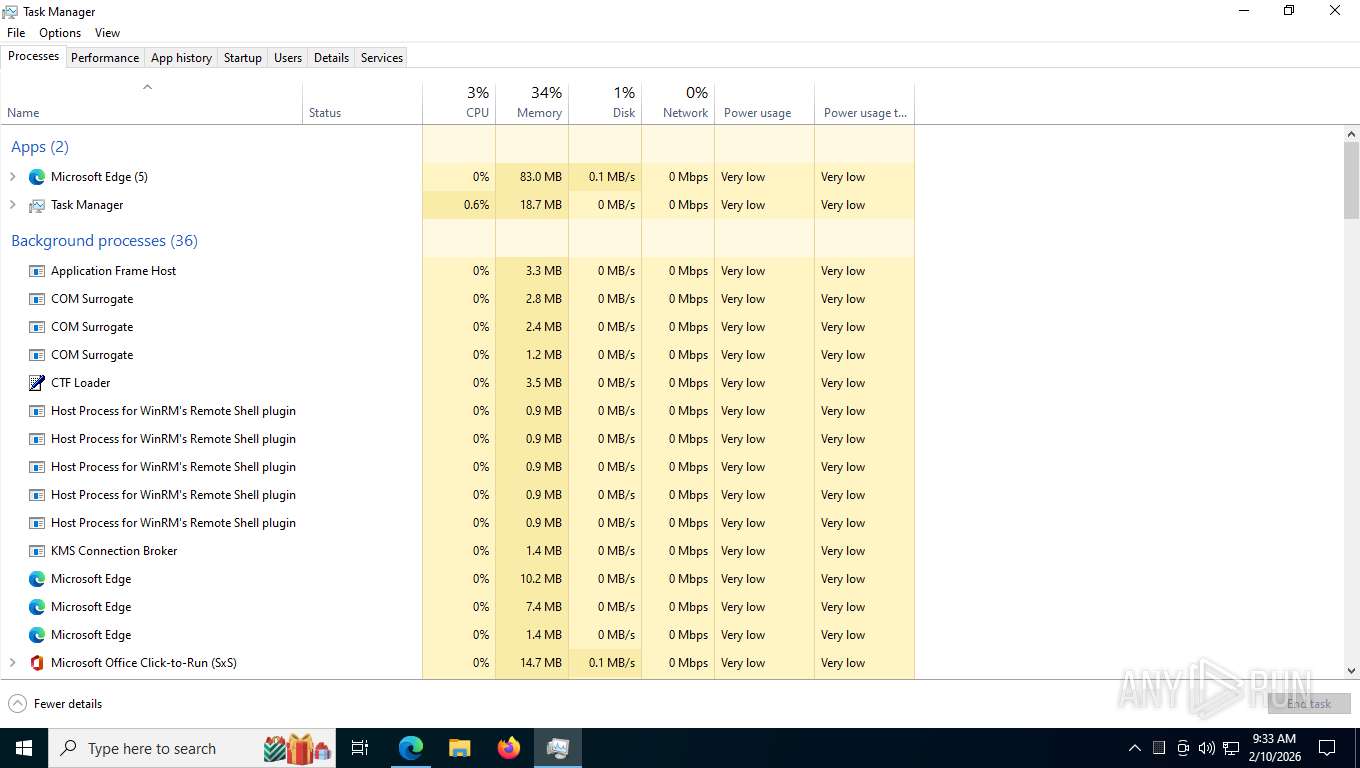
- Taskmgr.exe (PID: 5108)
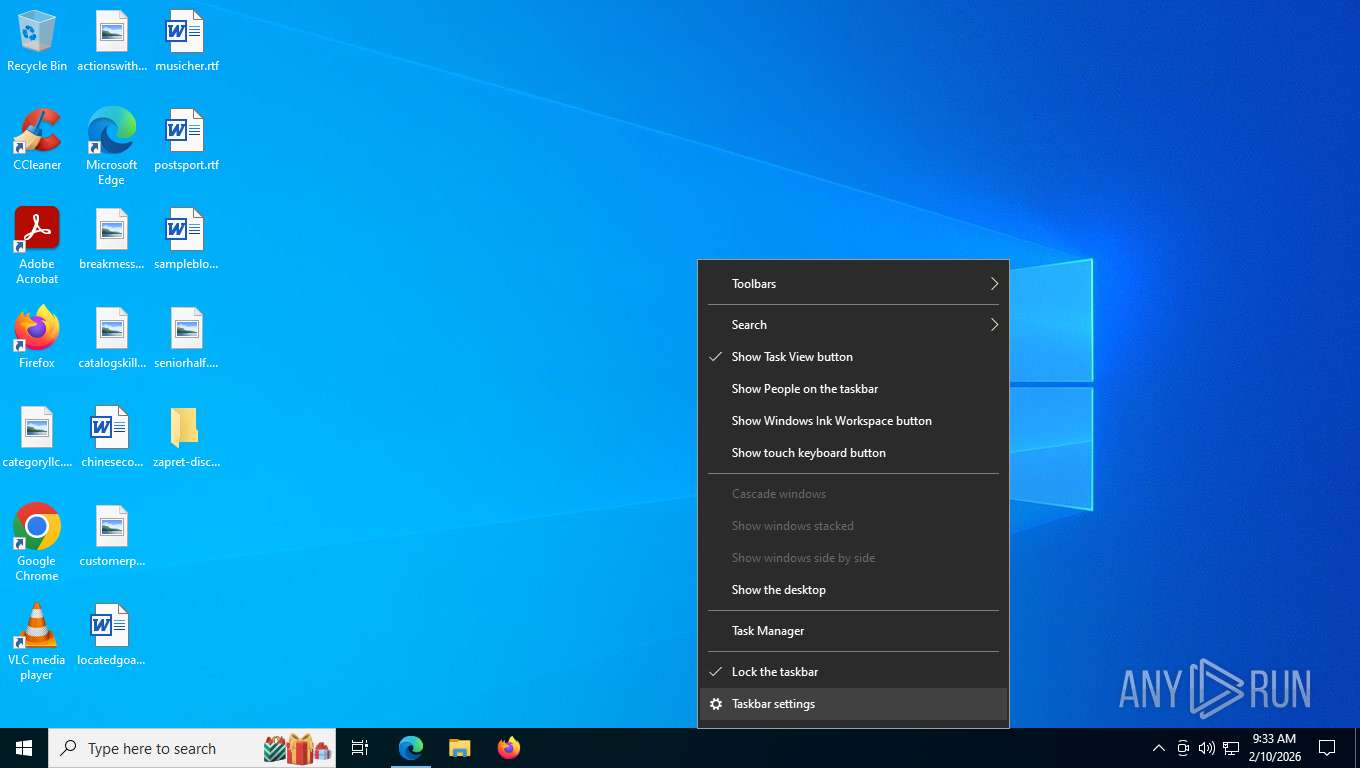
Manual execution by a user
- cmd.exe (PID: 7408)
- Taskmgr.exe (PID: 5108)
- firefox.exe (PID: 6608)
- Taskmgr.exe (PID: 8796)
Changes the display of characters in the console
- cmd.exe (PID: 7544)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1632)
Disables trace logs
- netsh.exe (PID: 8284)
- netsh.exe (PID: 1084)
Checks proxy server information
- slui.exe (PID: 7600)
Creates files or folders in the user directory
- SystemSettings.exe (PID: 1956)
Reads the machine GUID from the registry
- SystemSettings.exe (PID: 1956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
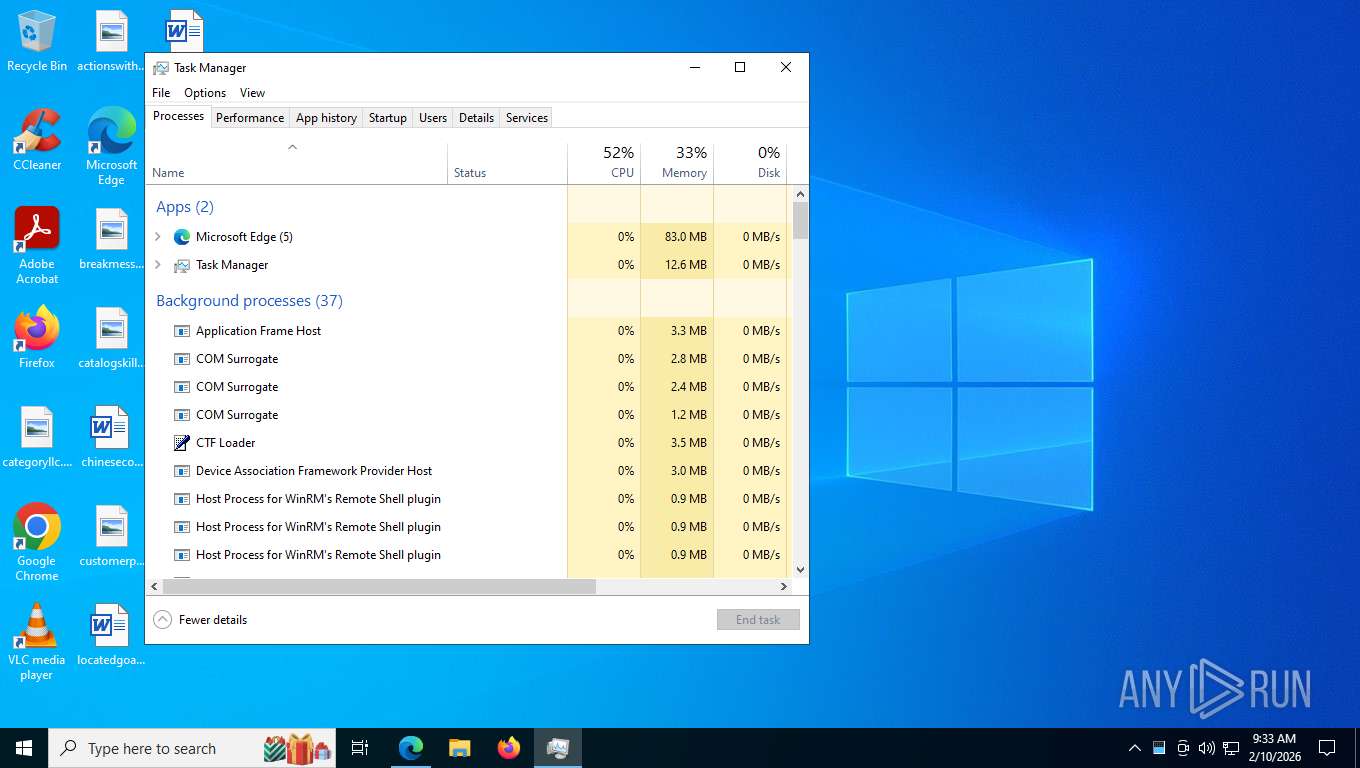
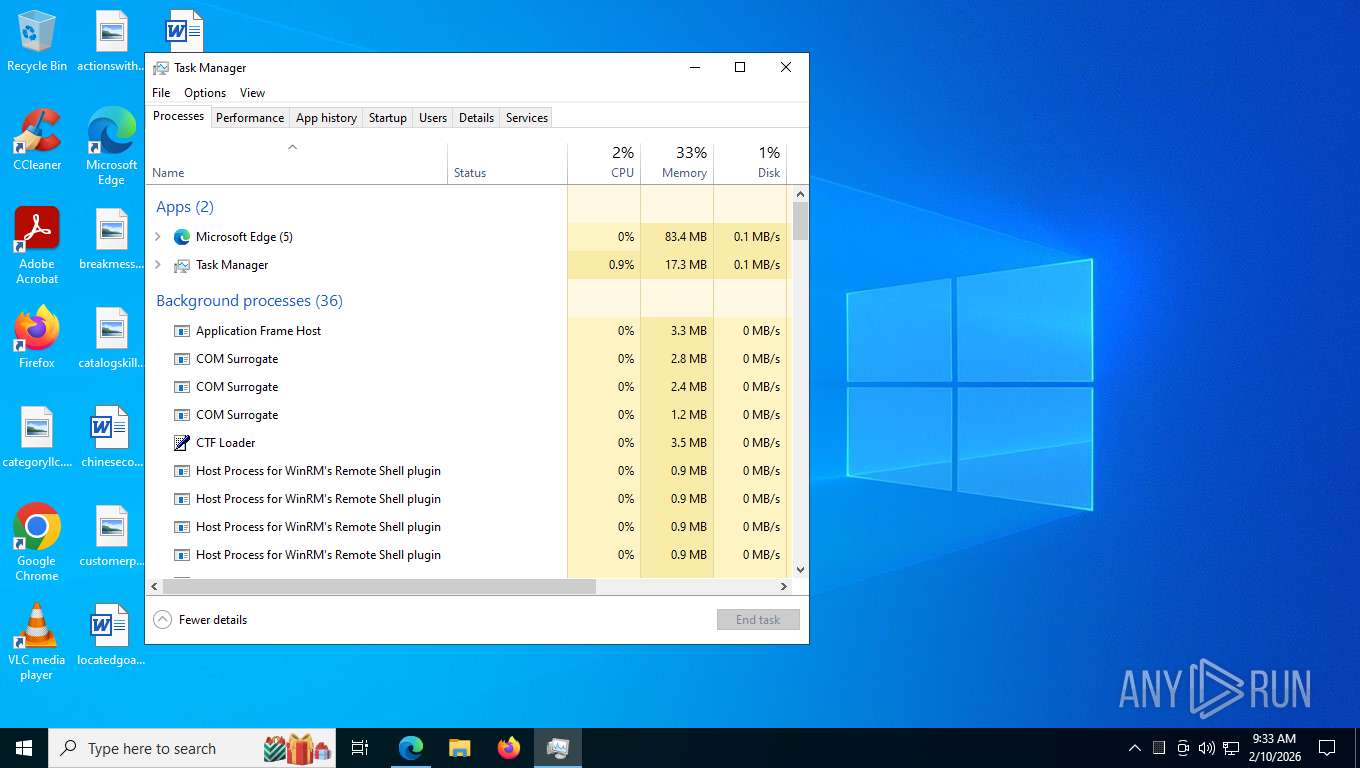
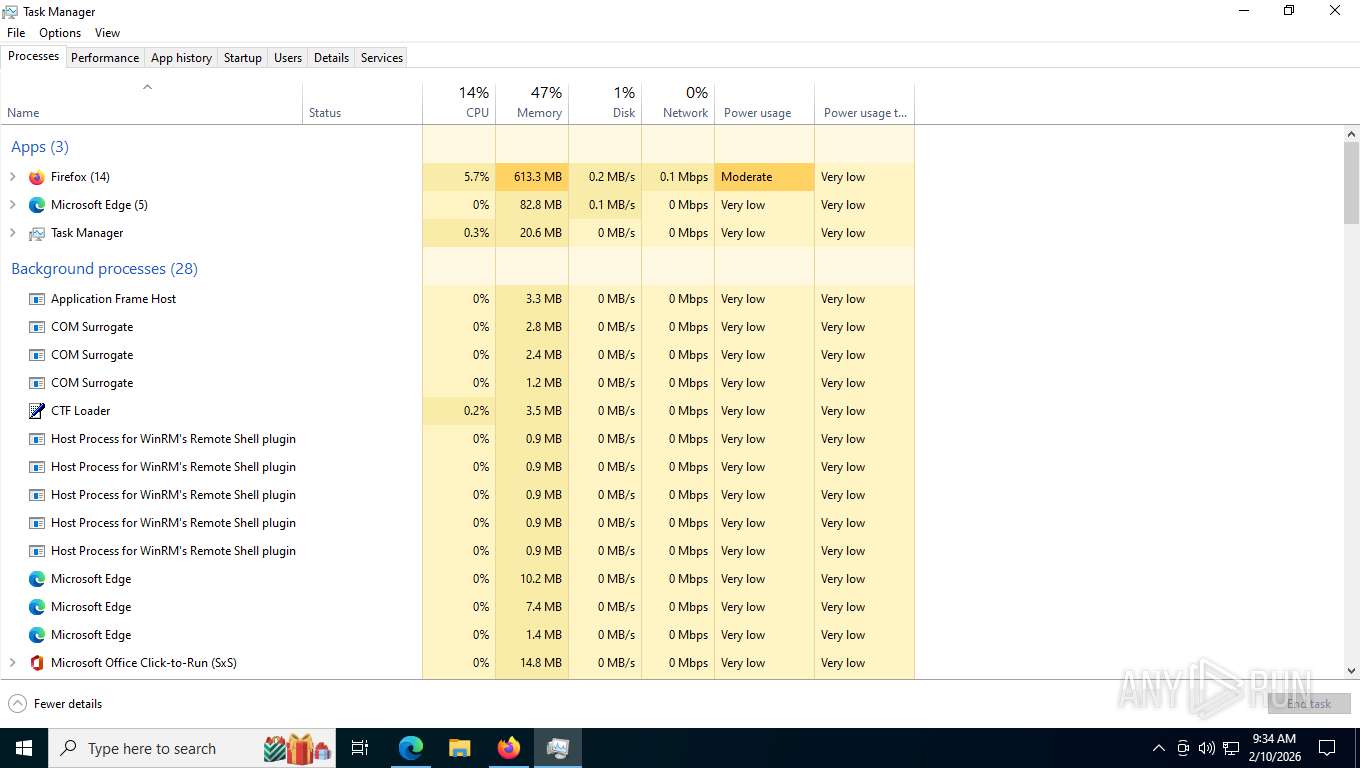
Total processes
334
Monitored processes
174
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | findstr /R "^203\.0\.113\.113/32f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "C:\Users\admin\Desktop\zapret-discord-youtube-1.9.5\lists\ipset-all.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo %BIN%tls_clienthello_www_google_com.bin " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4940,i,12602928155495514479,7828574647921879058,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5948 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 476 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3600,i,12602928155495514479,7828574647921879058,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5508,i,12602928155495514479,7828574647921879058,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5284 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4924 -prefsLen 39330 -prefMapHandle 4928 -prefMapSize 272981 -jsInitHandle 4932 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4944 -initialChannelId {01b84676-77dc-4181-9f0c-85fbba06eac5} -parentPid 9168 -crashReporter "\\.\pipe\gecko-crash-server-pipe.9168" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 796 | C:\WINDOWS\system32\cmd.exe /c powershell -NoProfile -Command "Get-ChildItem -LiteralPath '.' -Filter '*.bat' | Where-Object { $_.Name -notlike 'service*' } | Sort-Object { [Regex]::Replace($_.Name, '(\d+)', { $args[0].Value.PadLeft(8, '0') }) } | ForEach-Object { $_.Name }" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
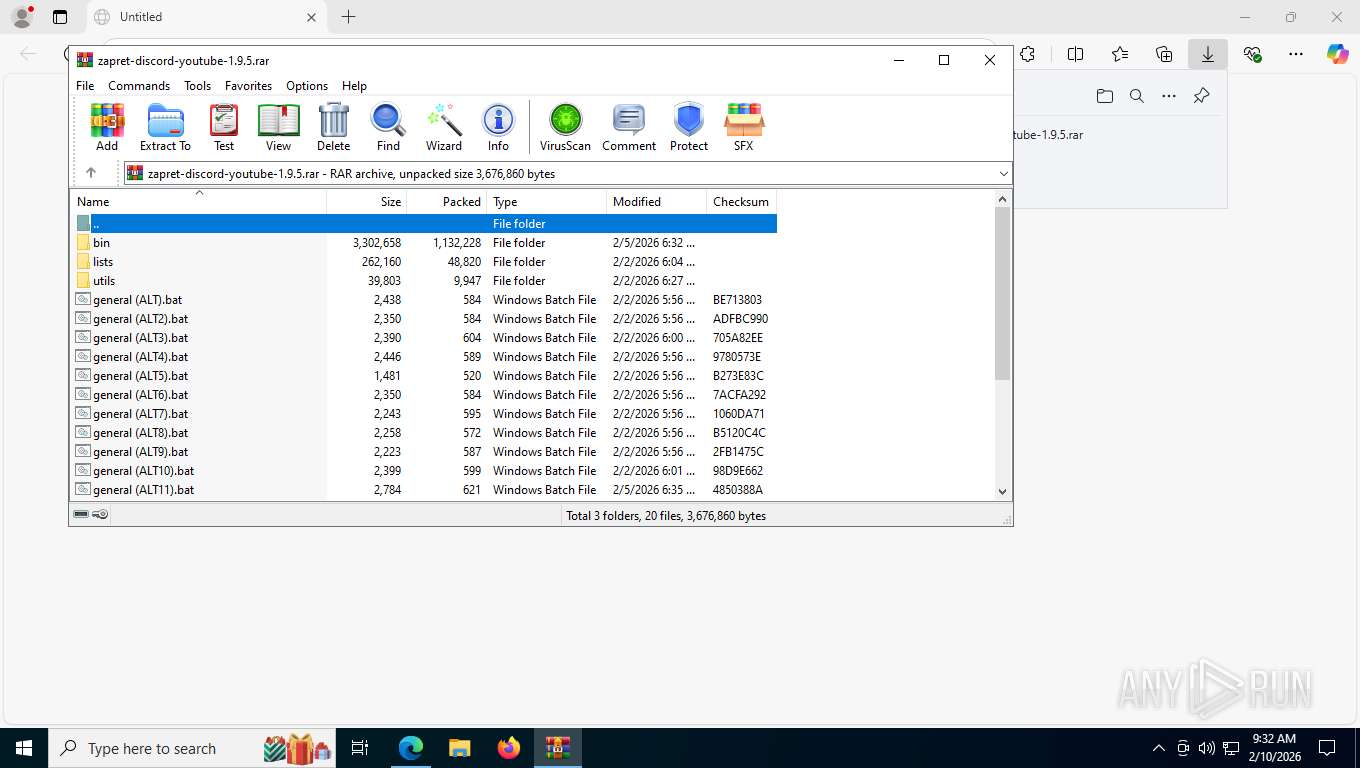
| 848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\zapret-discord-youtube-1.9.5.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1084 | netsh interface tcp set global timestamps=enabled | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1316 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo start "zapret: %~n0" /min "%BIN%winws.exe" --wf-tcp=80,443,2053,2083,2087,2096,8443,%GameFilter% --wf-udp=443,19294-19344,50000-50100,%GameFilter% ^ " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 064
Read events
21 011
Write events
39
Delete events
14
Modification events
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\zapret-discord-youtube-1.9.5.rar | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
7
Suspicious files
573
Text files
443
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e55af.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e55bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e55bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e55bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e55de.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1e560d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
410
TCP/UDP connections
128
DNS requests
181
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1612 | msedge.exe | GET | 302 | 140.82.121.3:443 | https://github.com/Flowseal/zapret-discord-youtube/releases/download/1.9.5/zapret-discord-youtube-1.9.5.rar | unknown | — | — | unknown |
1612 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
1612 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:xNQBhaRcFjz7K4gZEZStEJjT5ILcxHR-205OlvuxCZg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
5568 | SearchApp.exe | GET | 200 | 104.82.114.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
1612 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=edge_hub_apps_manifest_gz&version=4.11.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | unknown | text | 266 b | whitelisted |
1612 | msedge.exe | POST | 200 | 142.250.186.67:443 | https://update.googleapis.com/service/update2/json?cup2key=14:qygbn_Nk3WPg1se6viPycdGSkRNSNOueamtac0GW6dg&cup2hreq=f6641f2759f8e6083f209ec548b2275d40acc4ebd44f4dba213f5bf5461dd1fe | unknown | text | 891 b | whitelisted |
1612 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://edgeassetservice.azureedge.net/assets/edge_hub_apps_manifest_gz/4.11.79/asset?assetgroup=Shoreline | unknown | text | 989 Kb | unknown |
1612 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.47 Kb | whitelisted |
1612 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4936 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4256 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.156:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 104.82.114.5:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1612 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
4936 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5568 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |