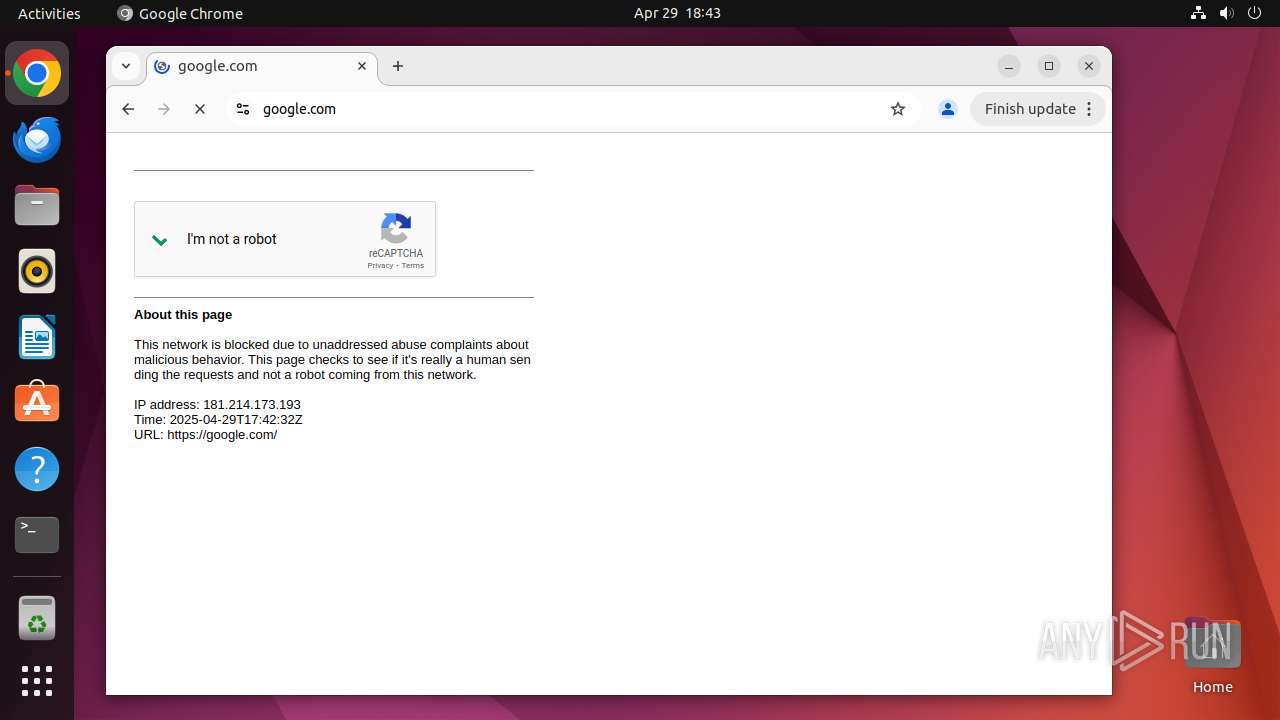
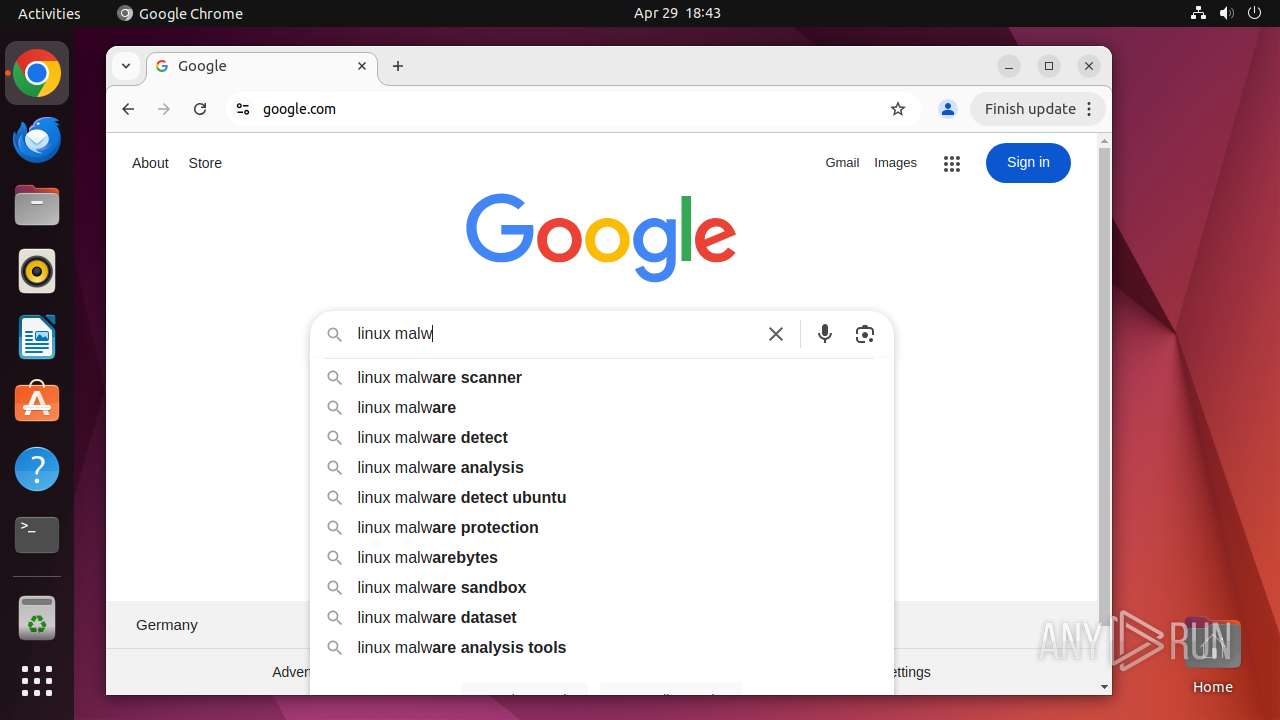
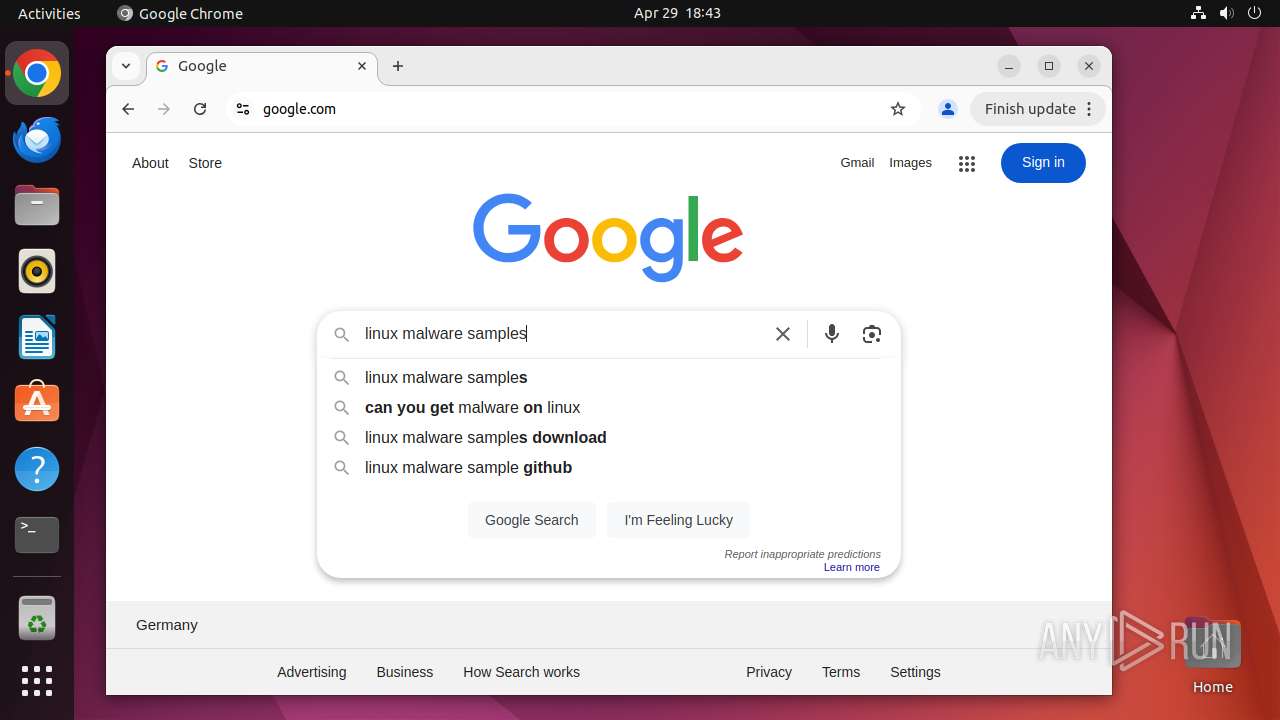
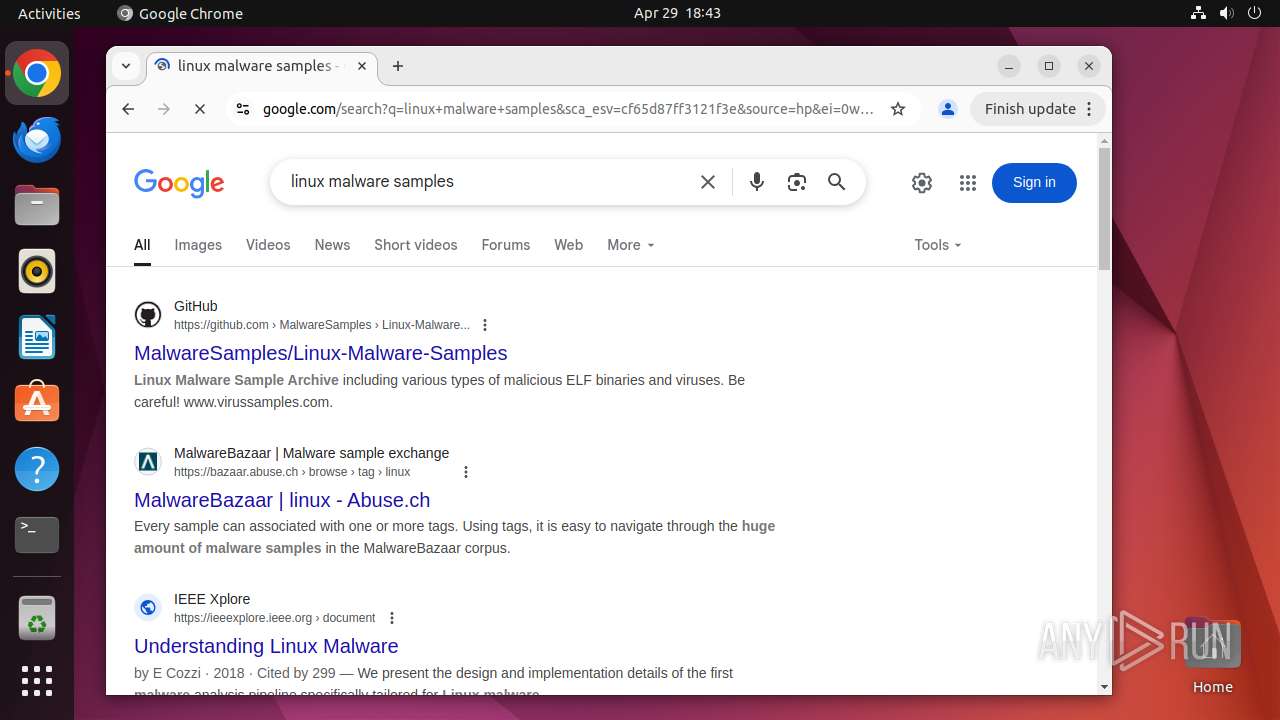
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/ff0ac0a8-c27f-4925-87df-417aba73f821 |
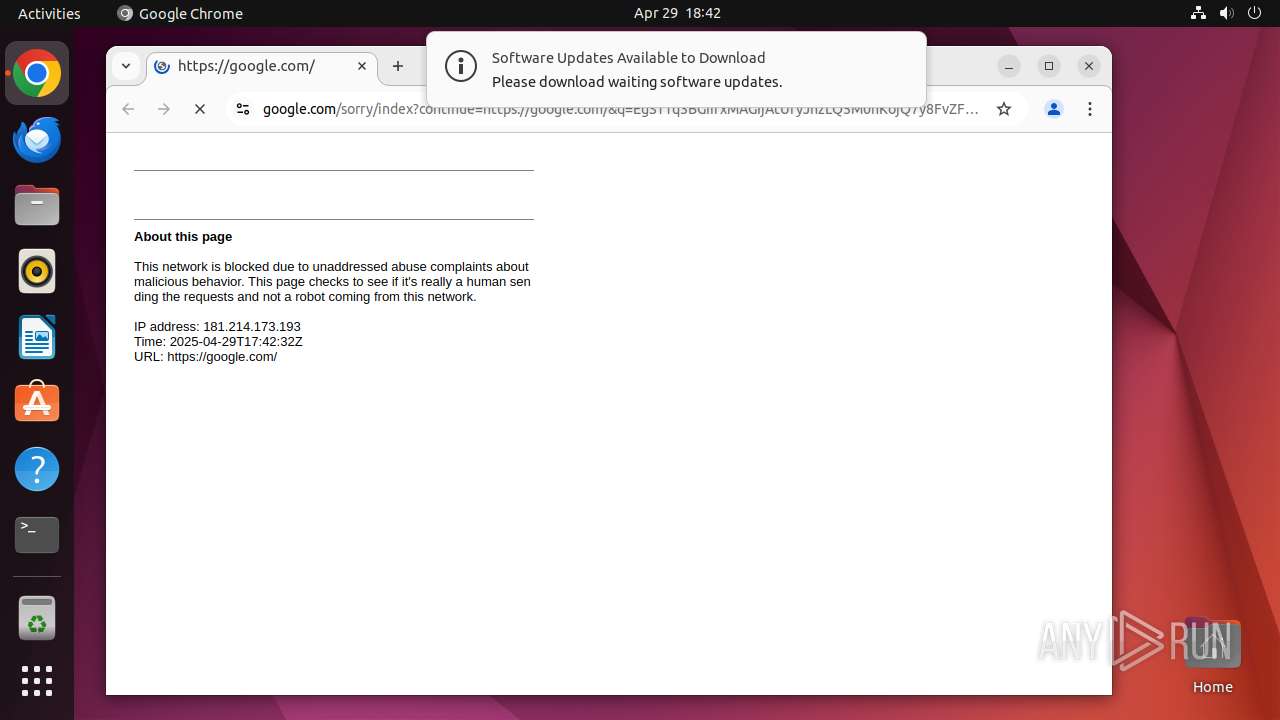
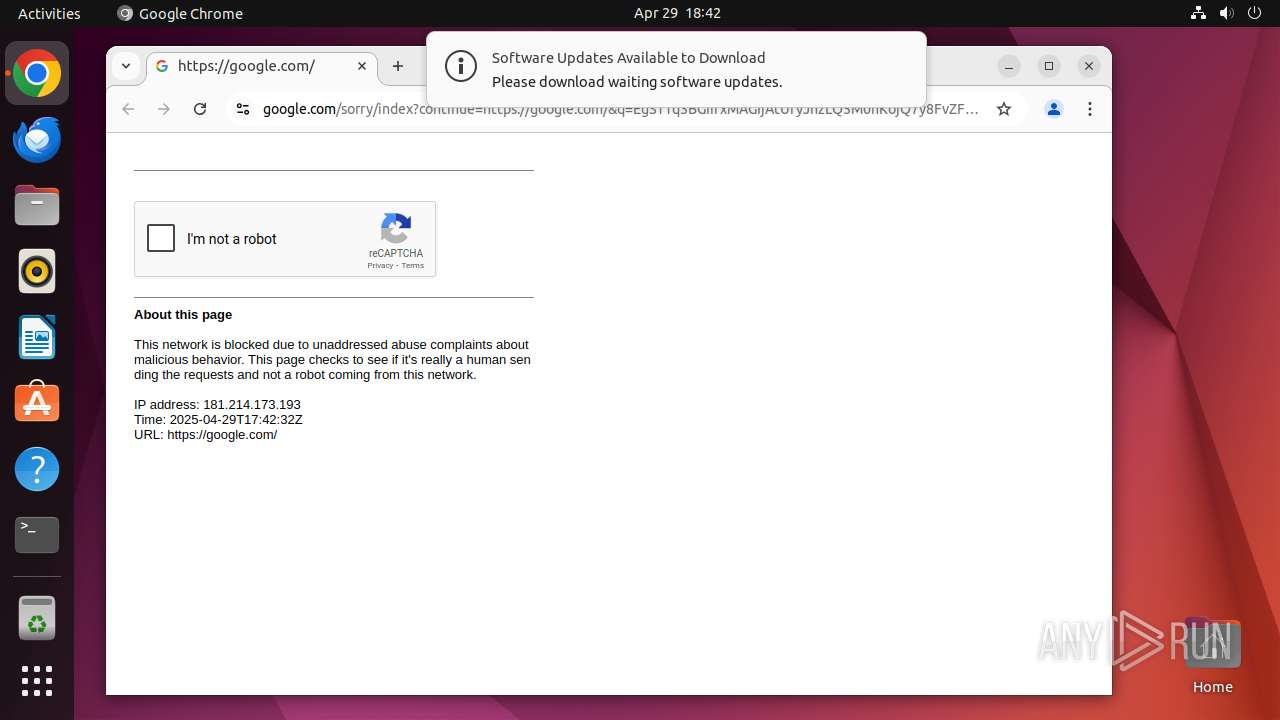
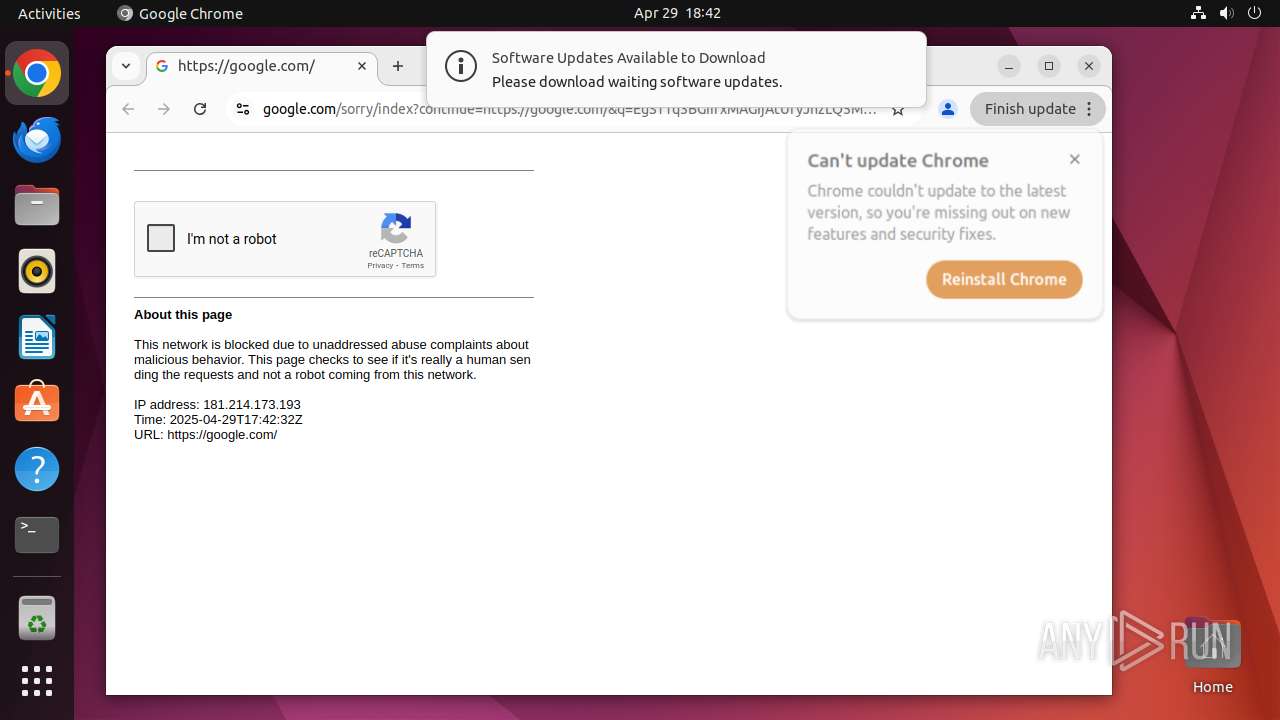
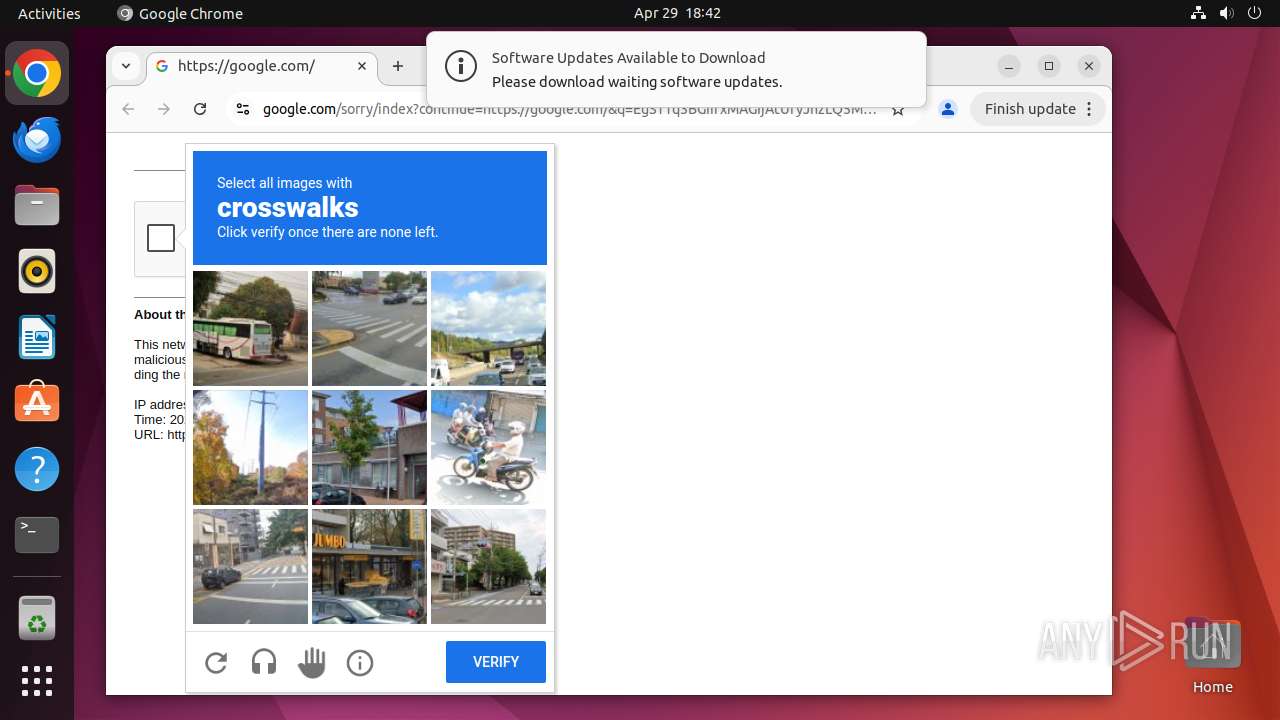
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 17:42:26 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
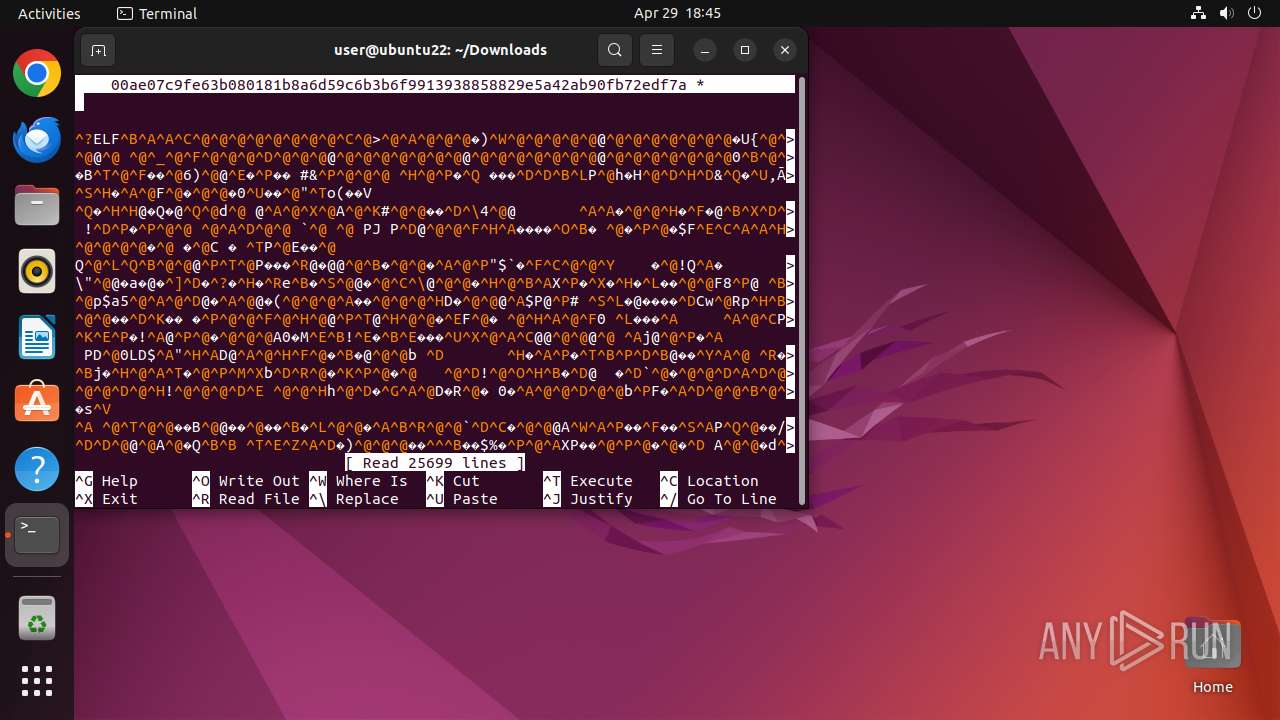
MALICIOUS
No malicious indicators.SUSPICIOUS
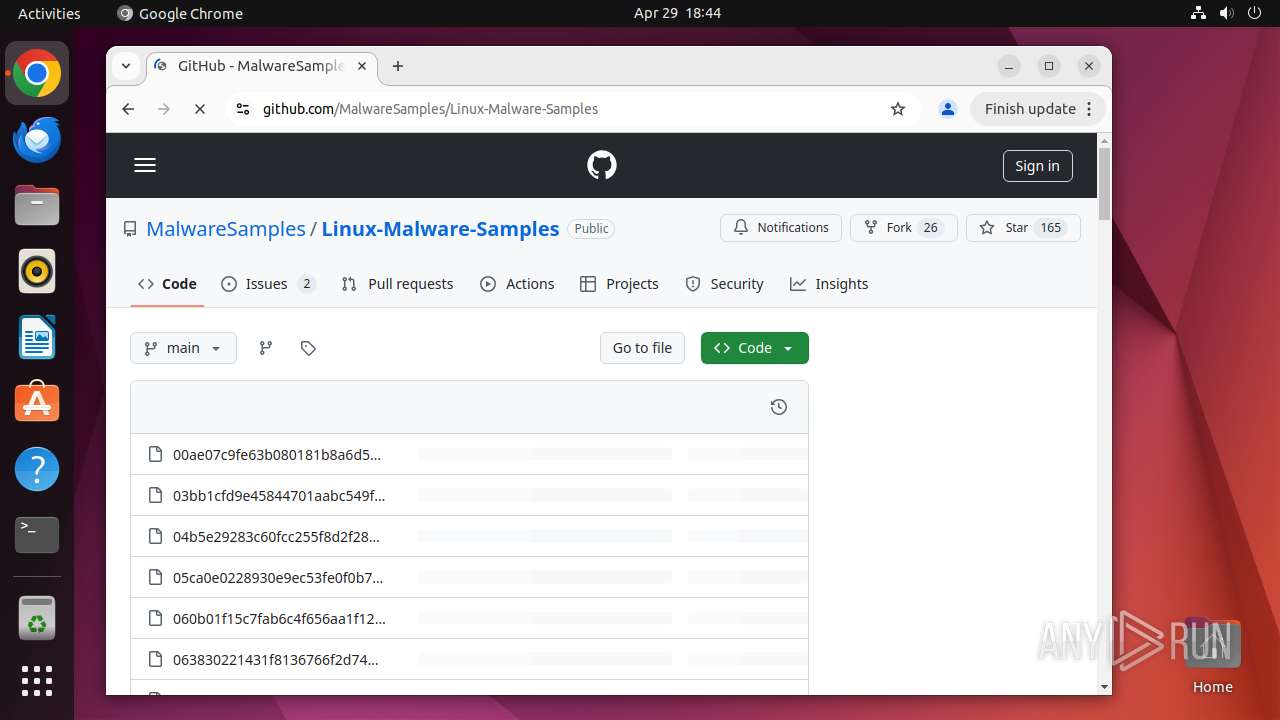
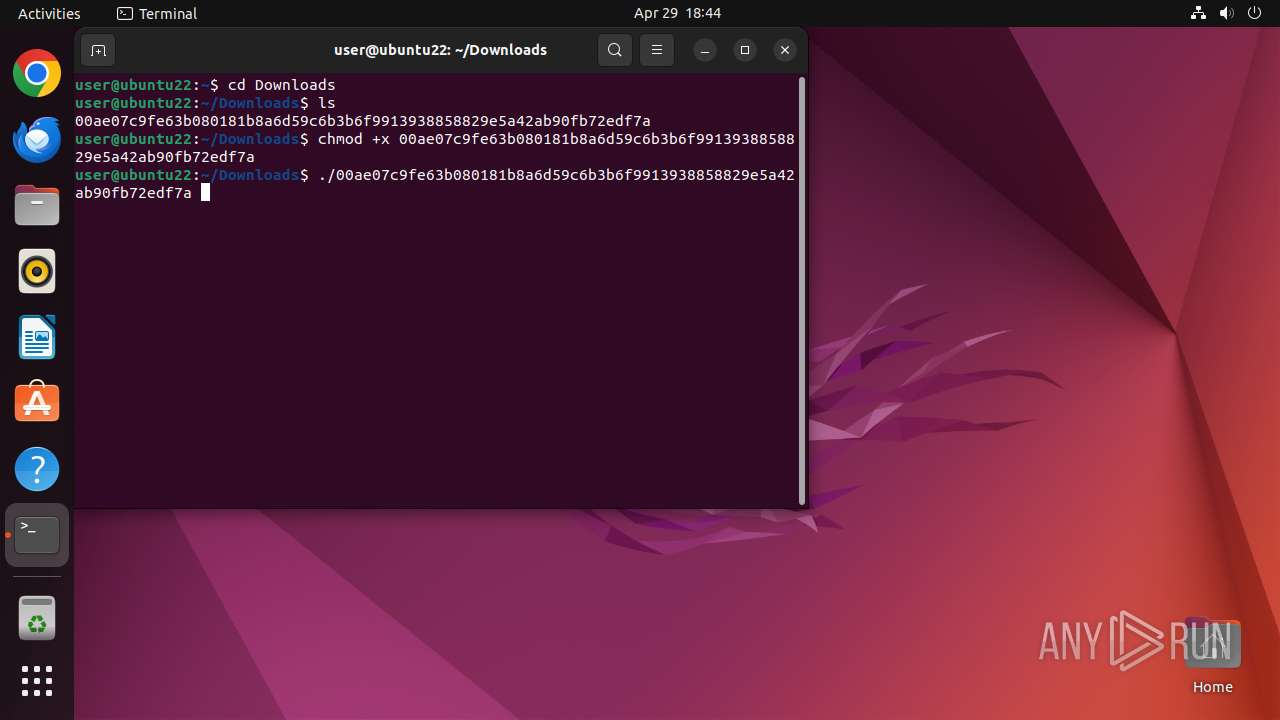
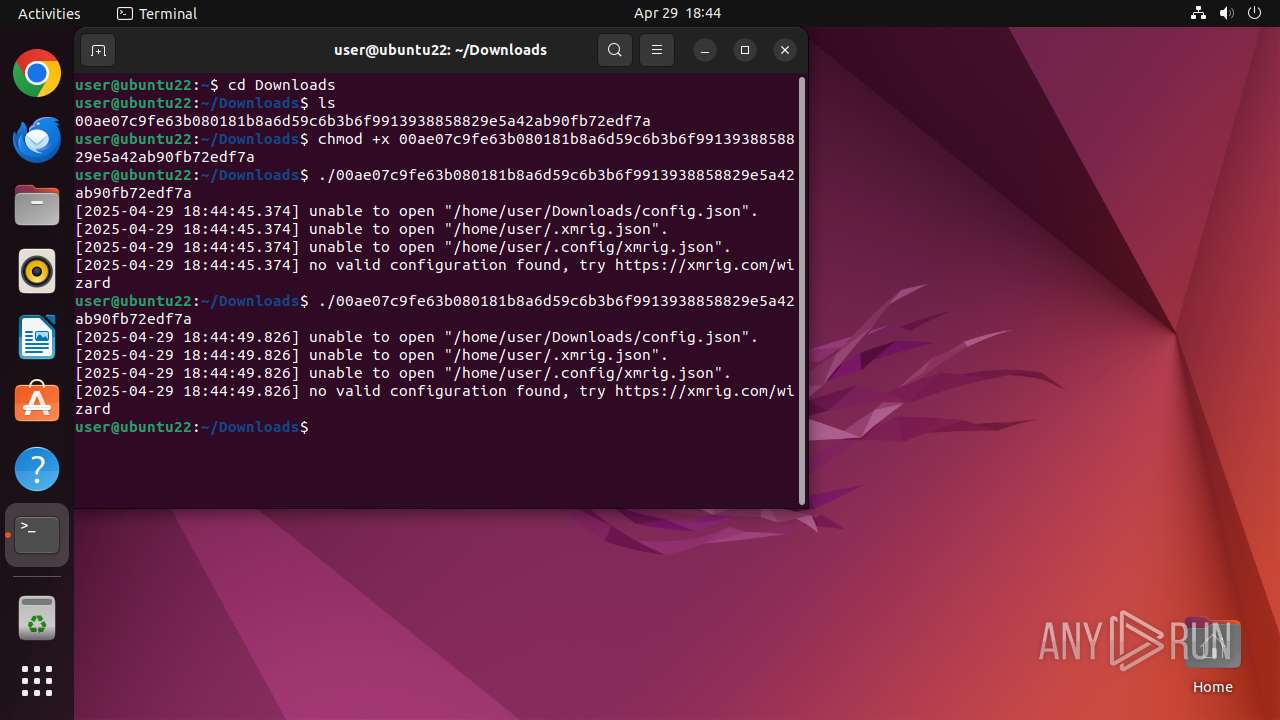
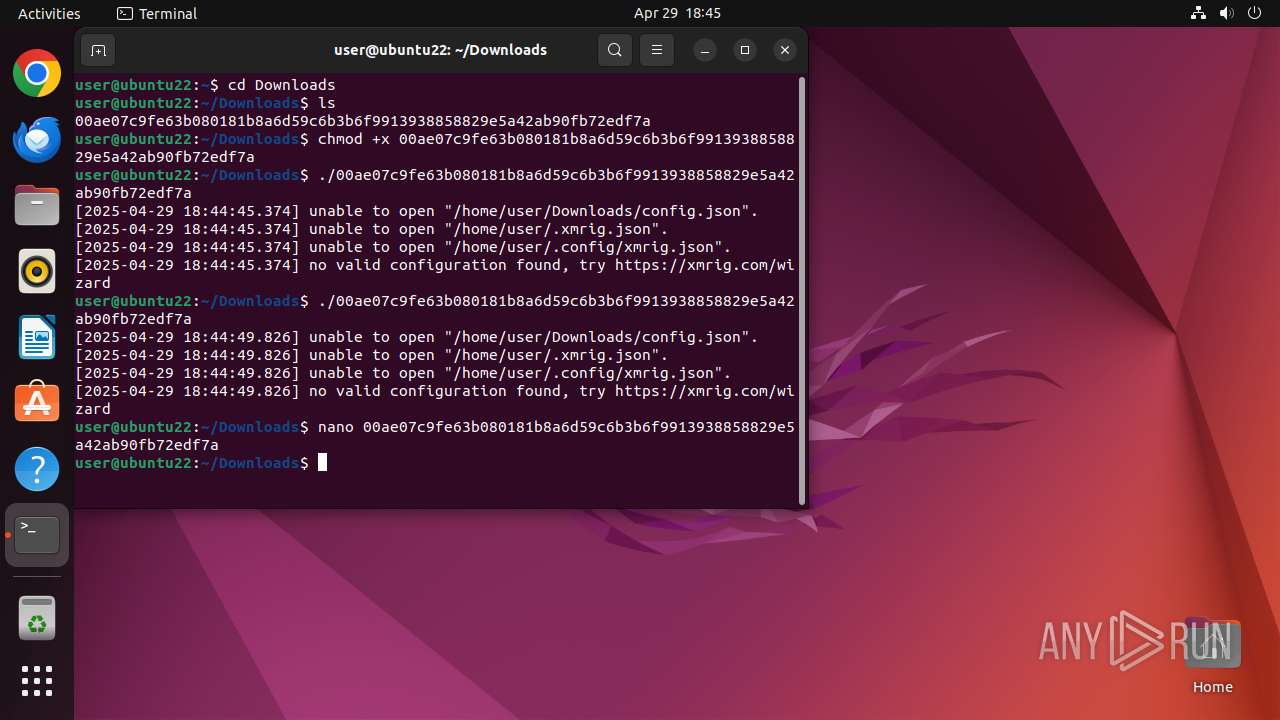
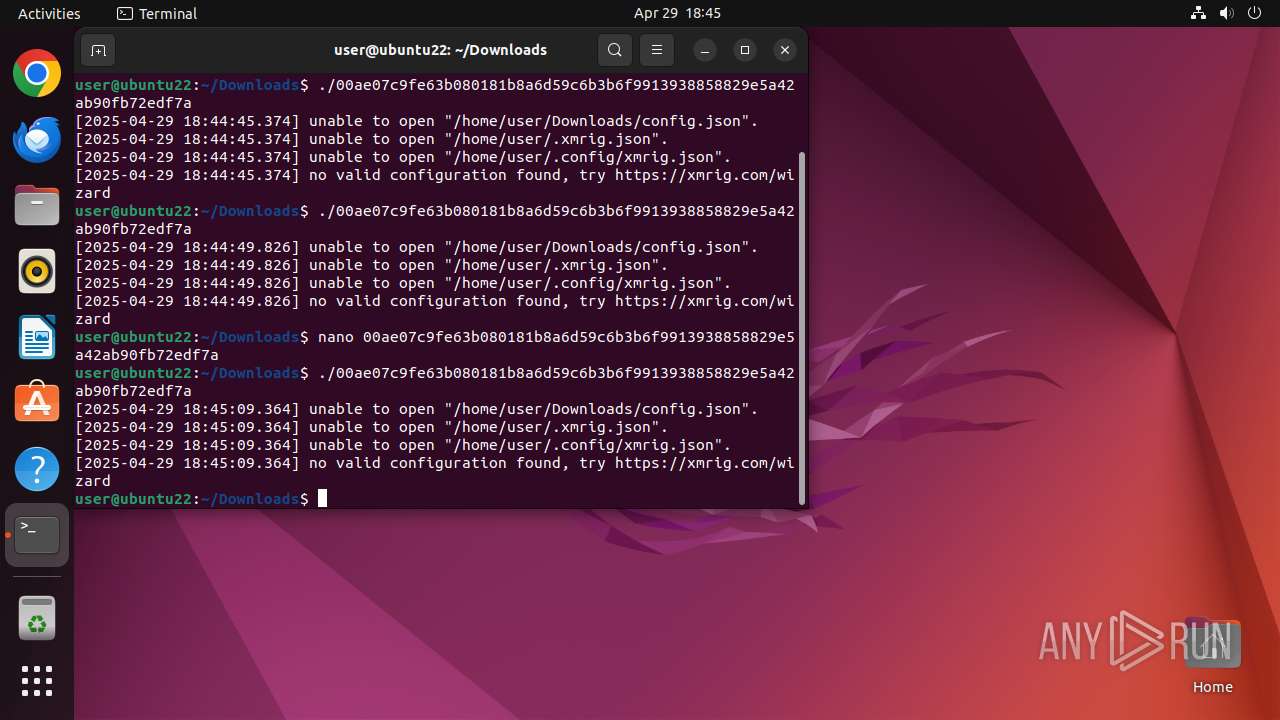
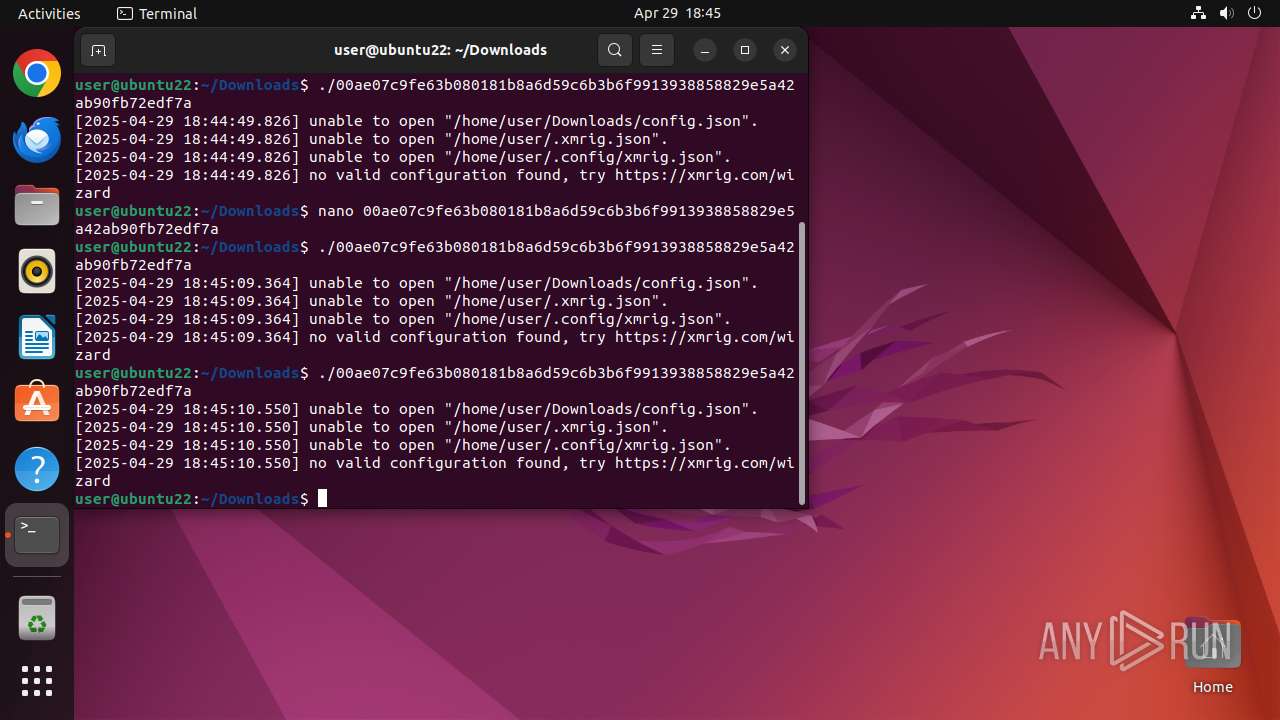
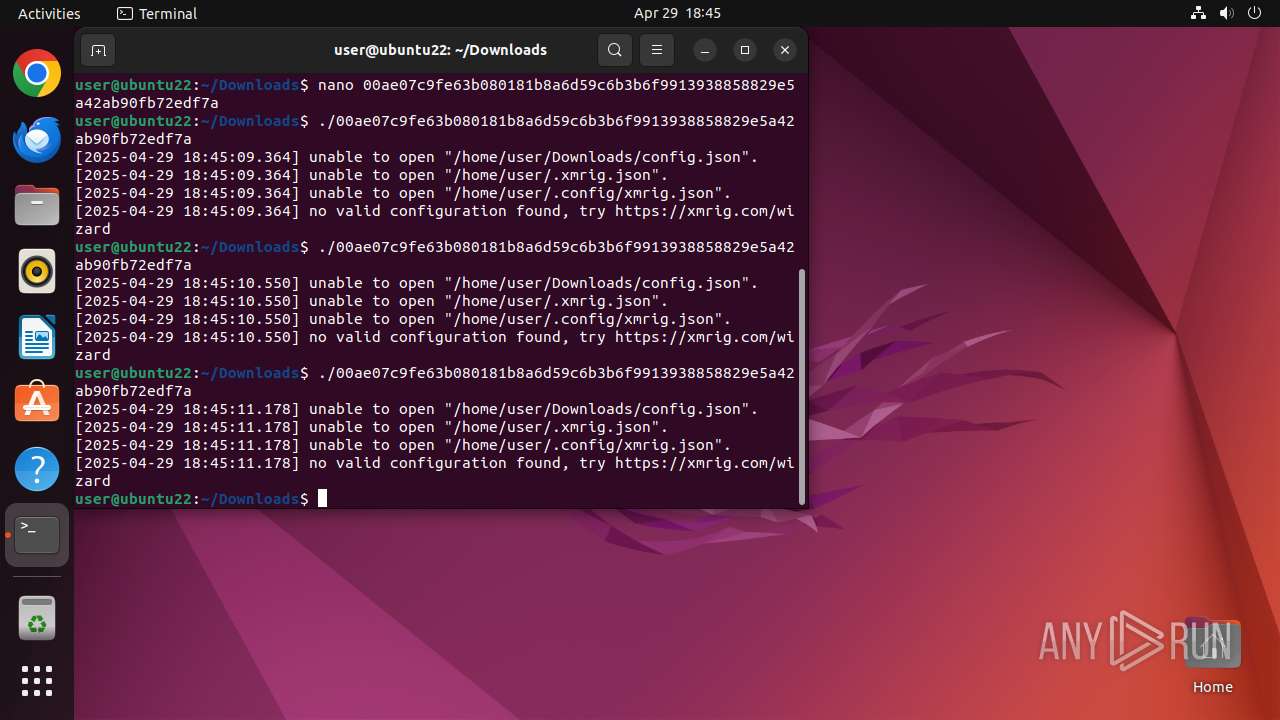
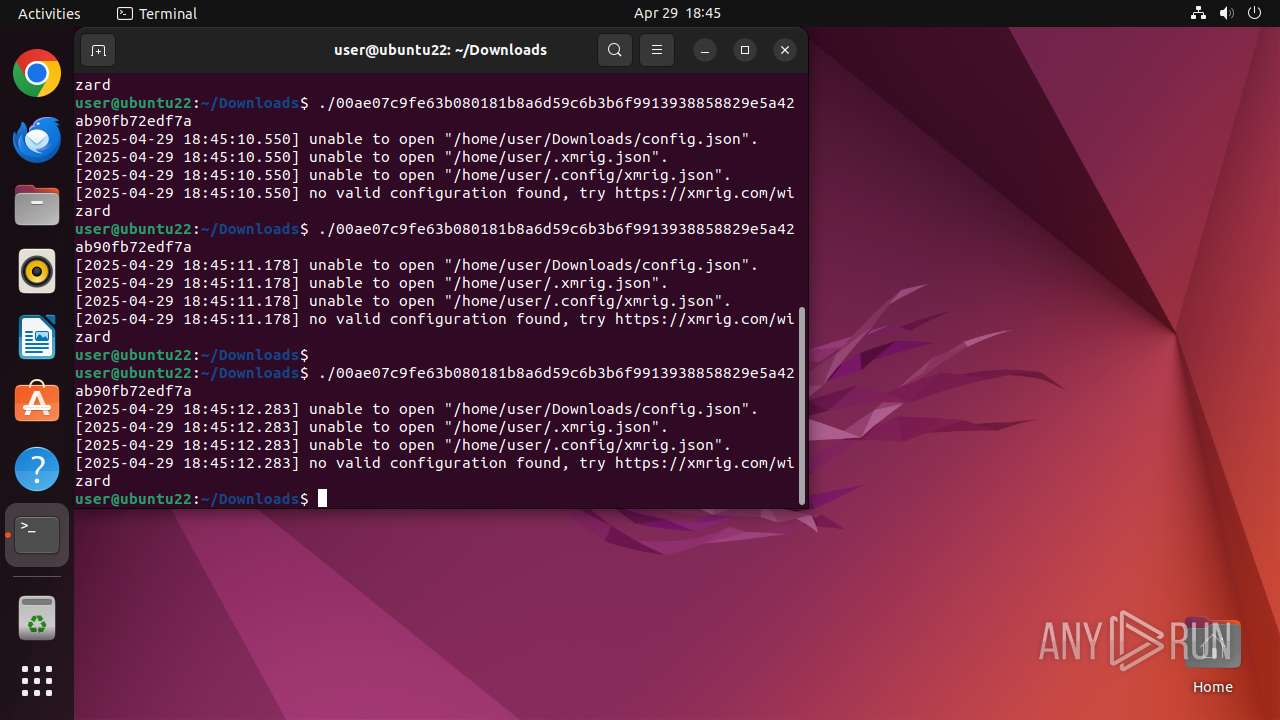
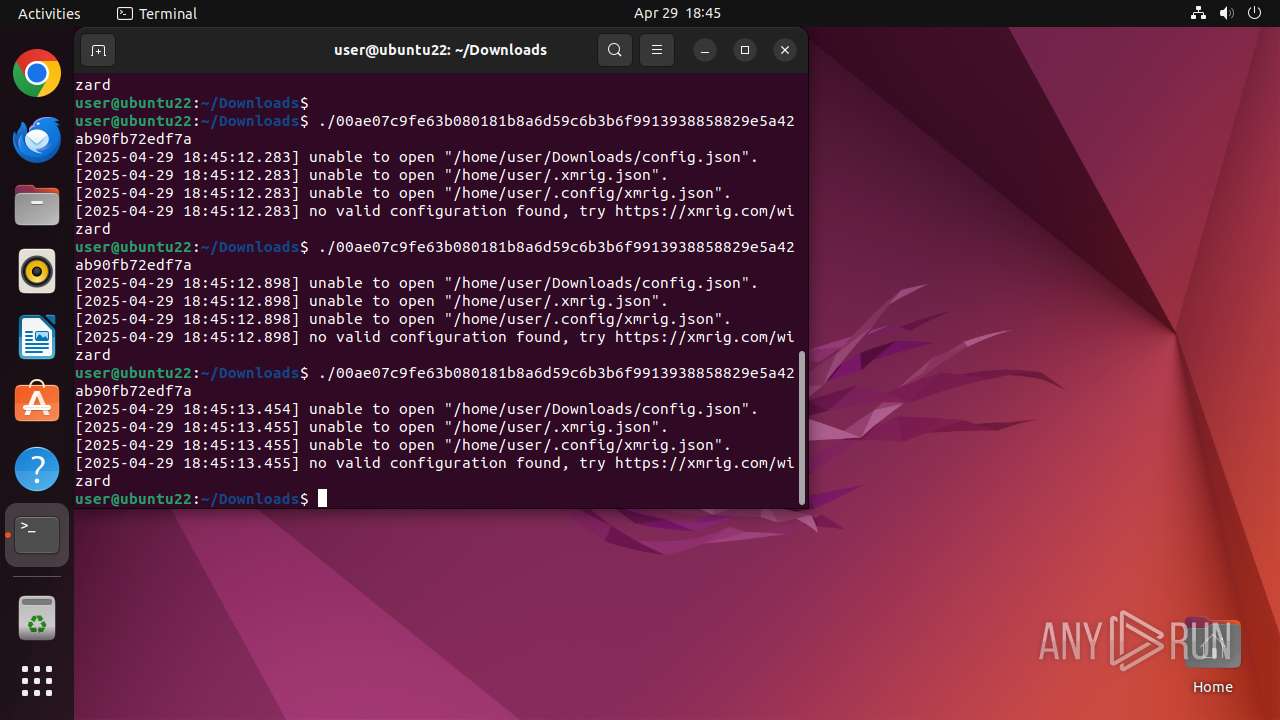
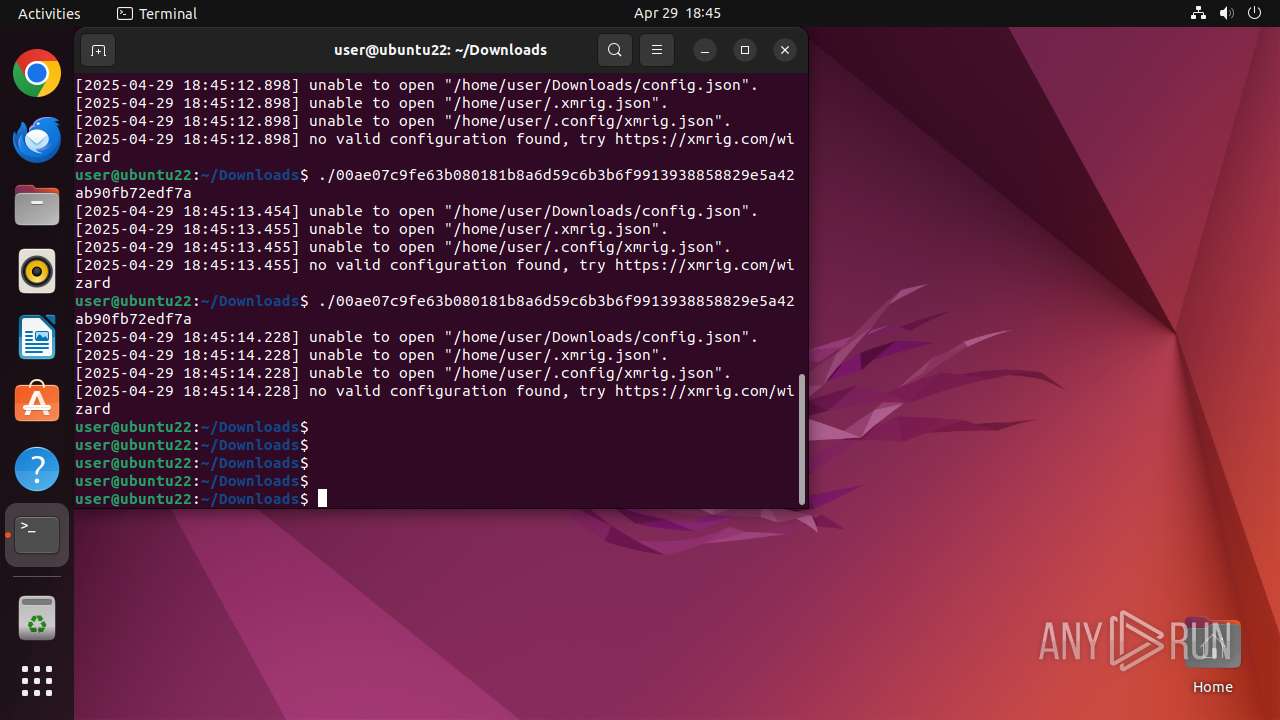
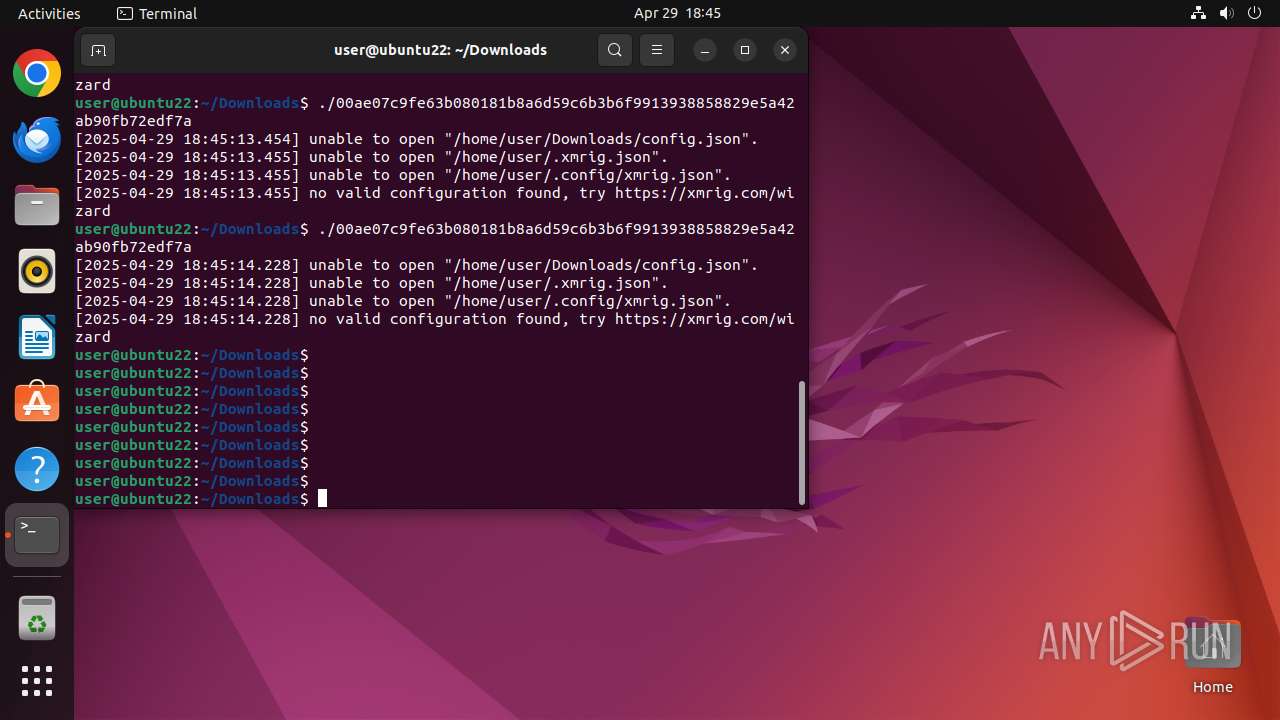
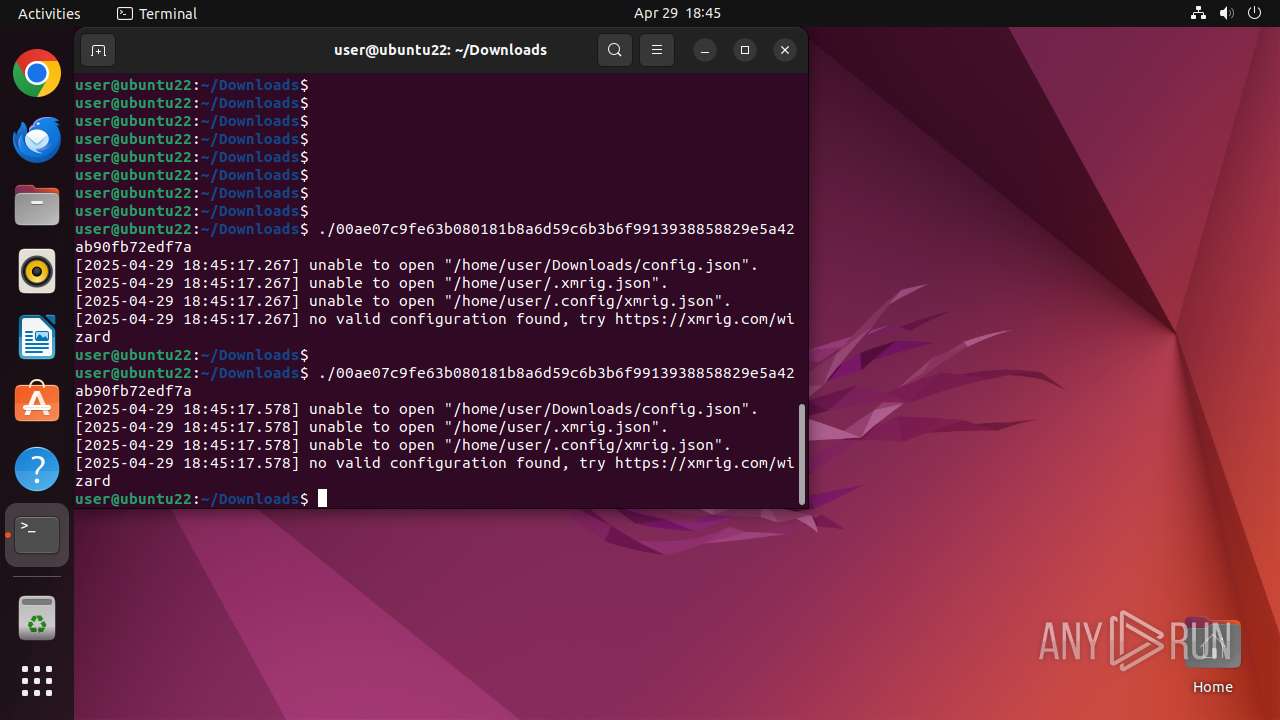
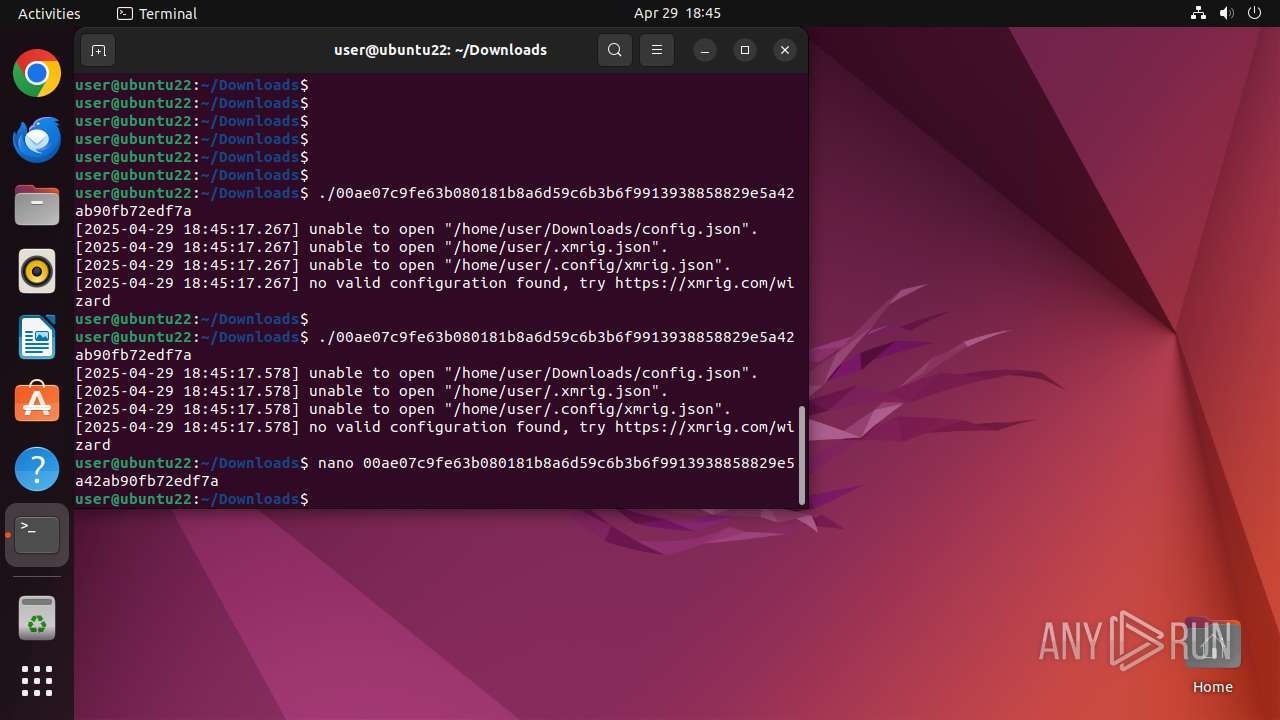
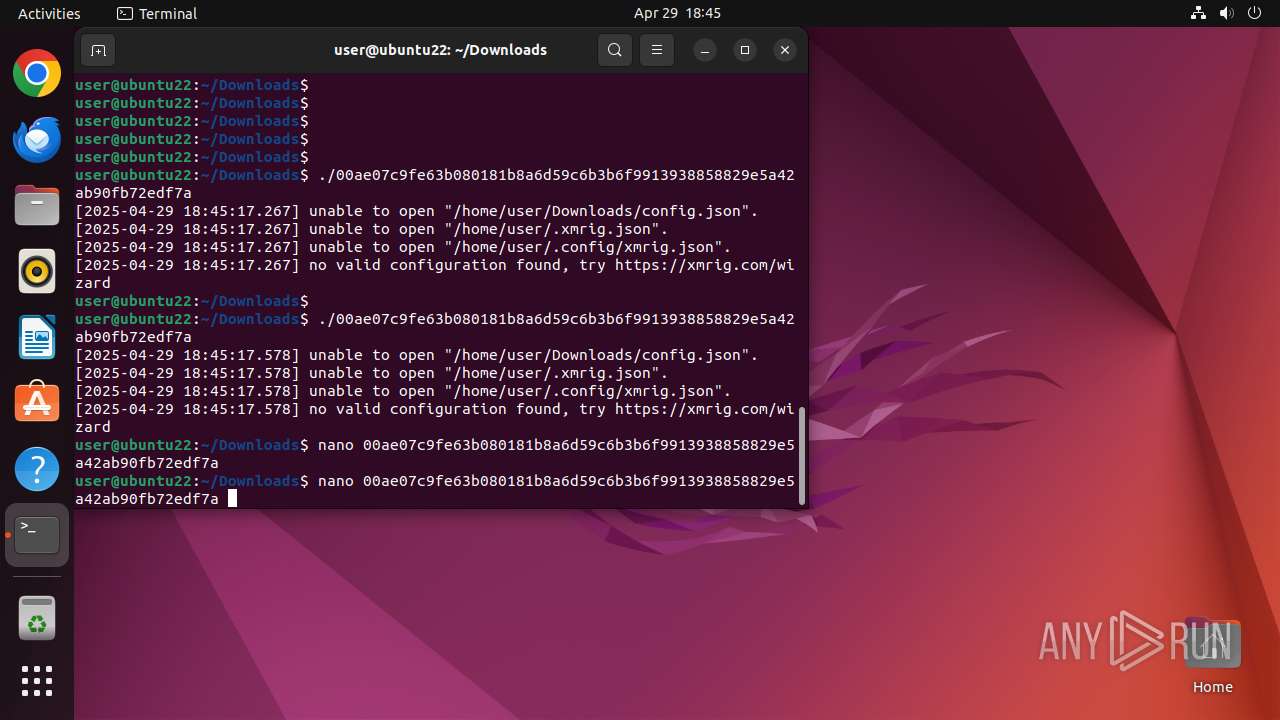
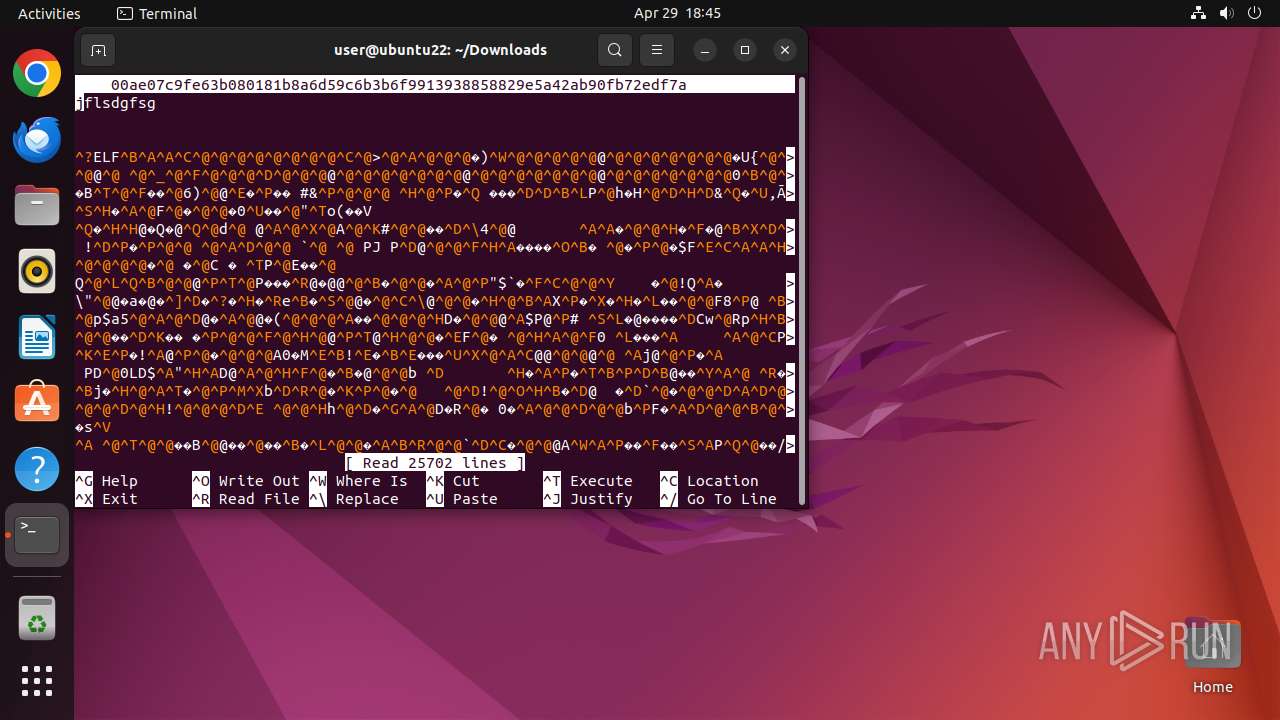
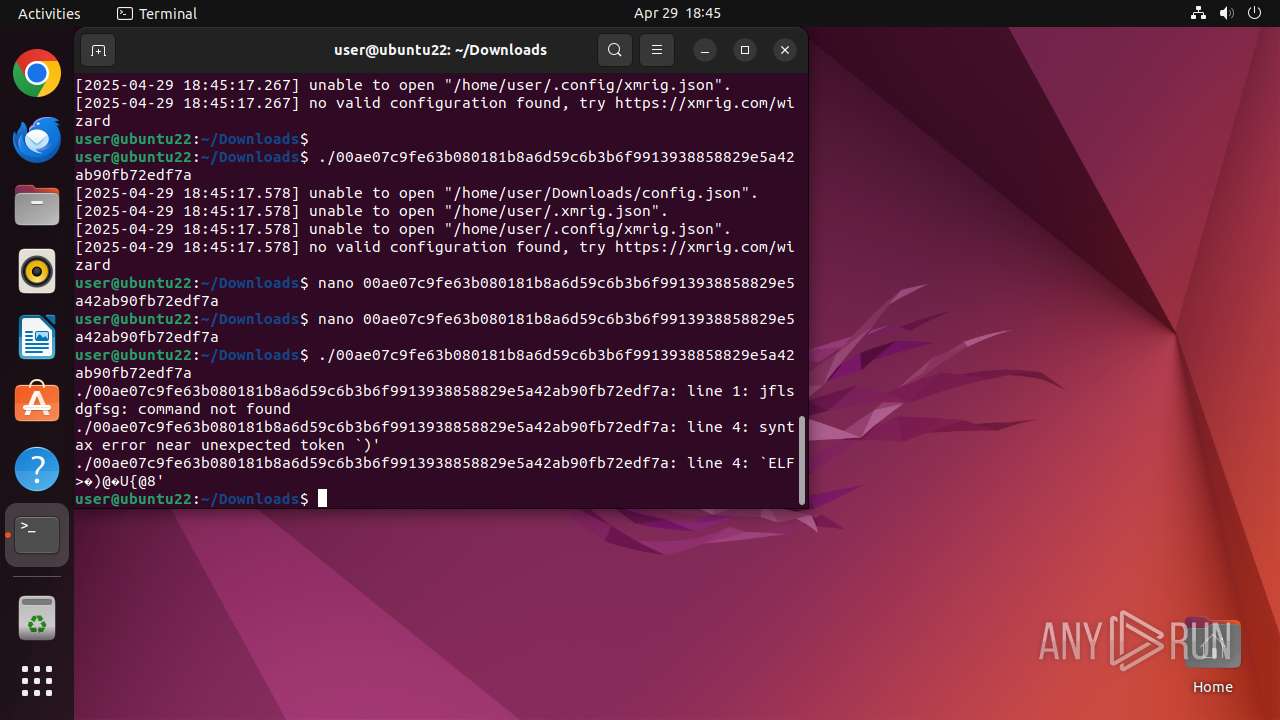
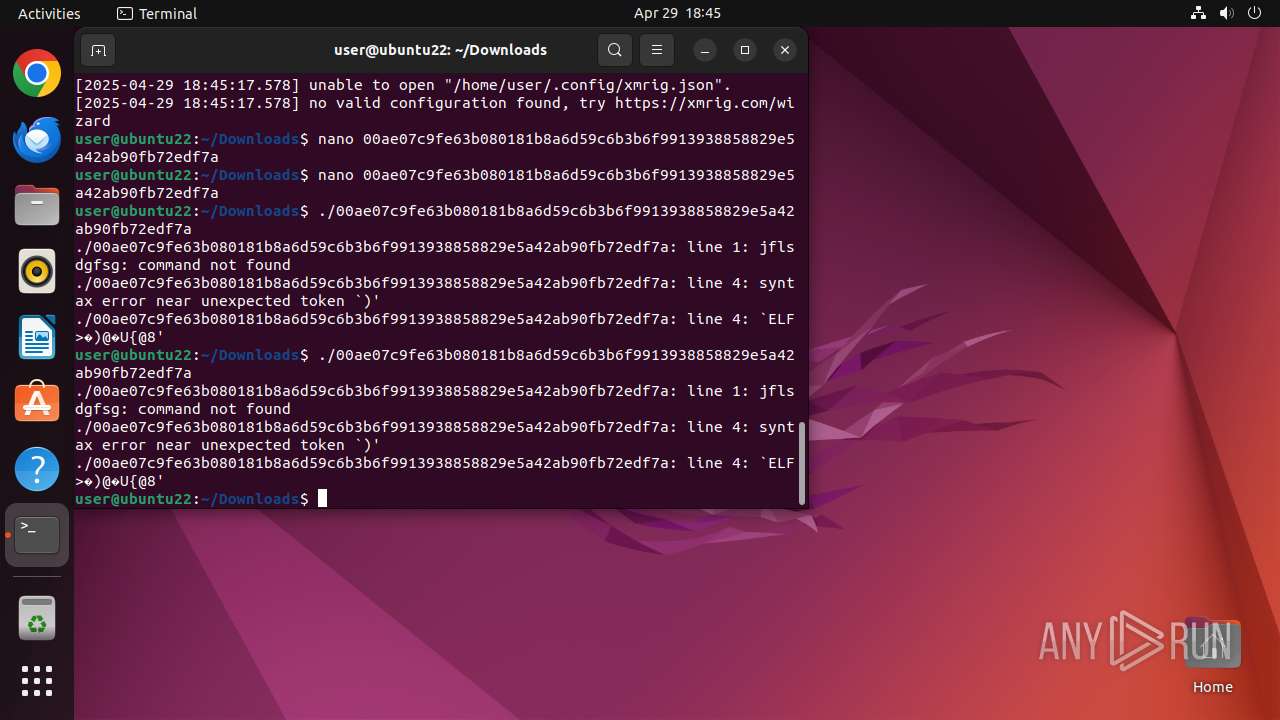
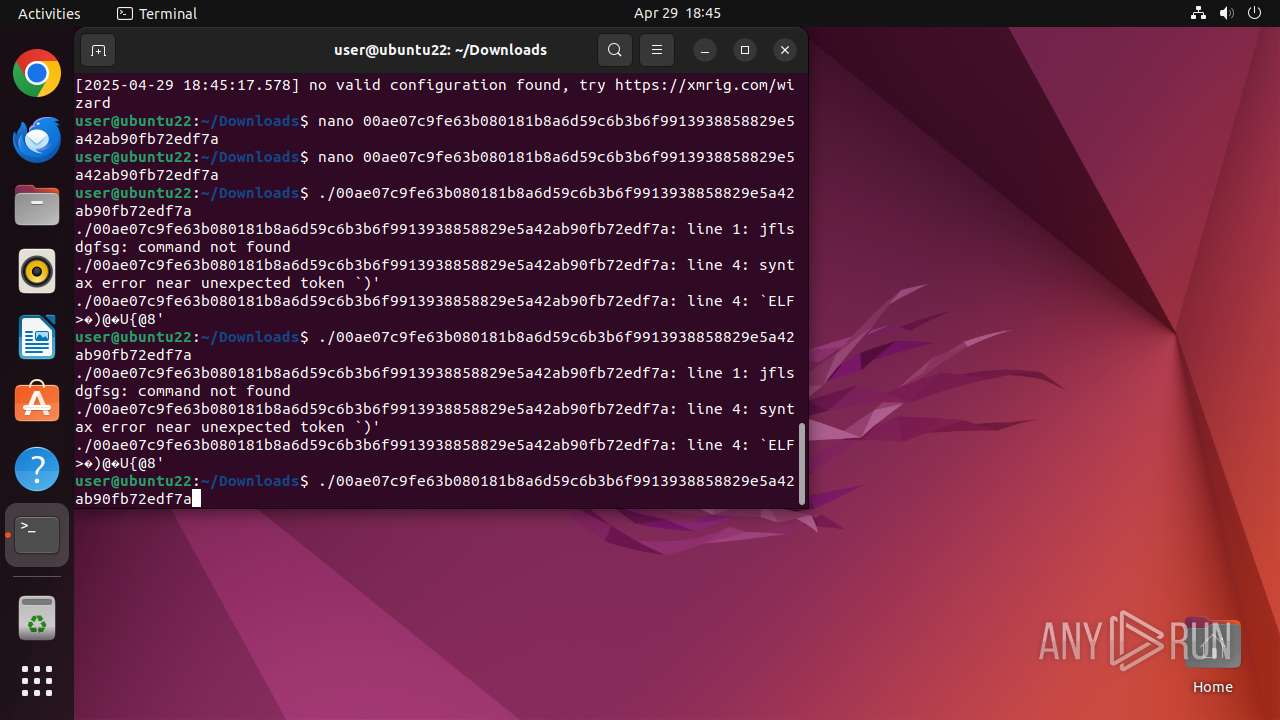
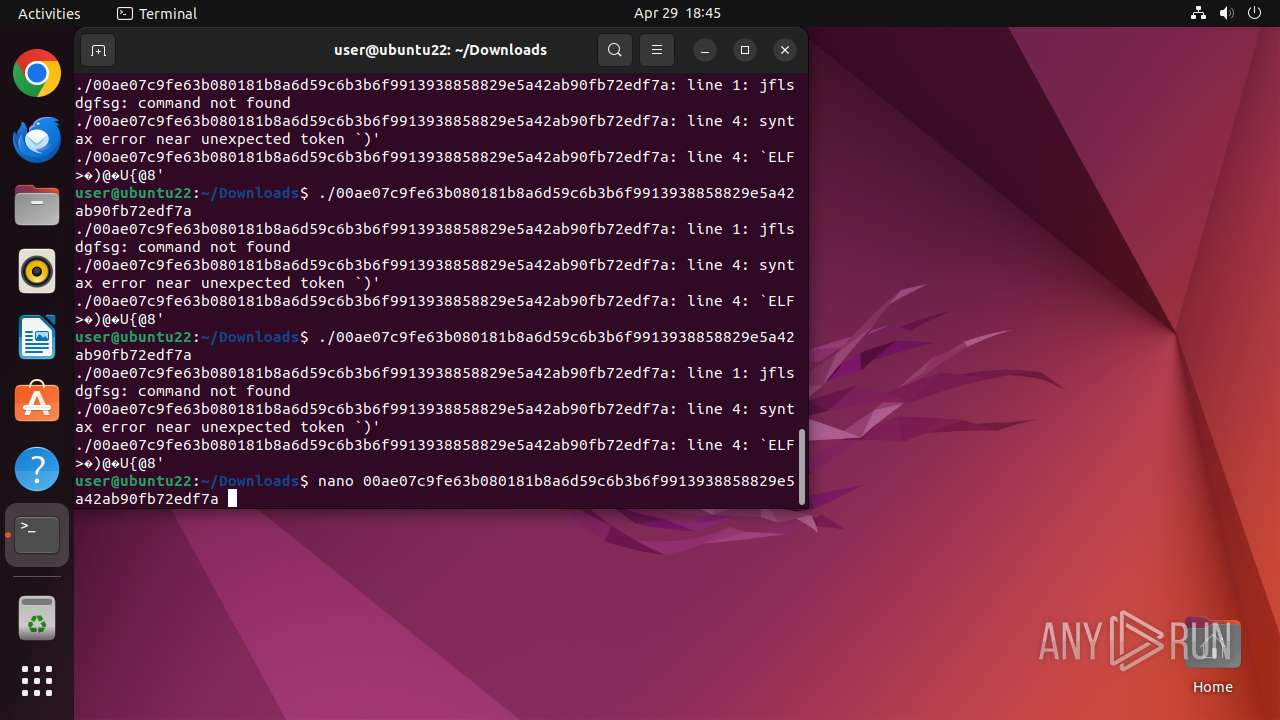
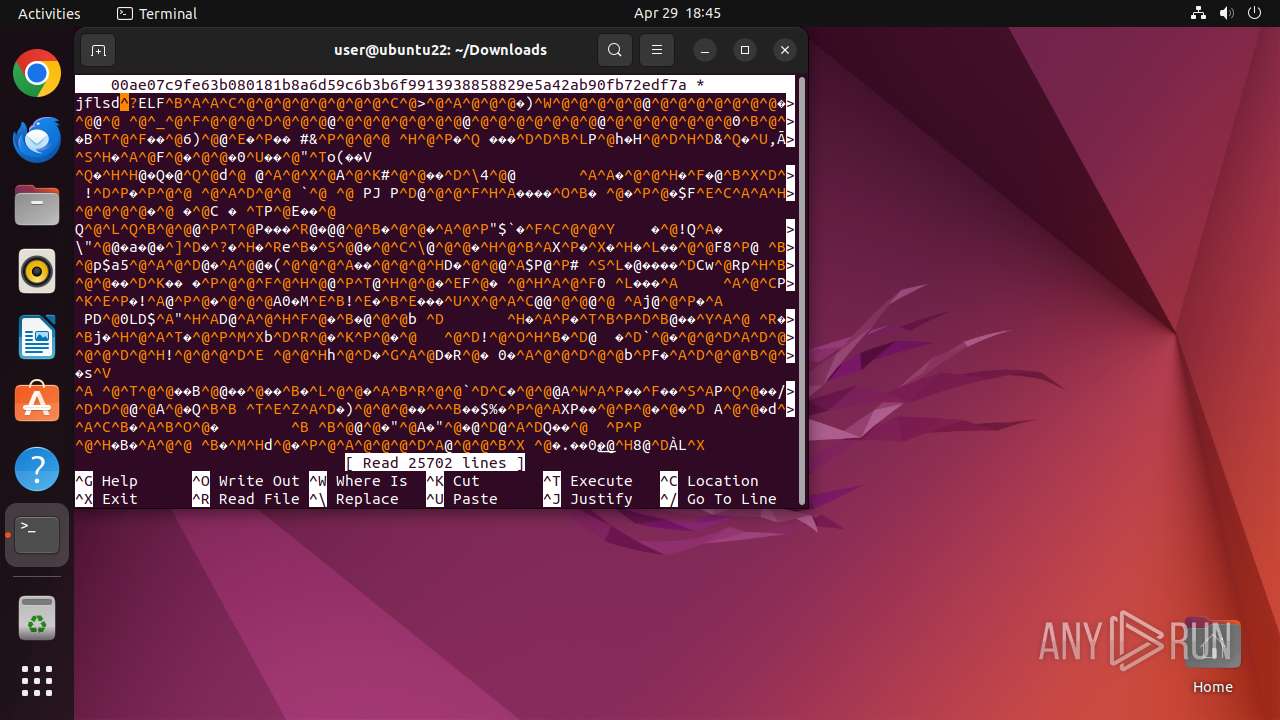
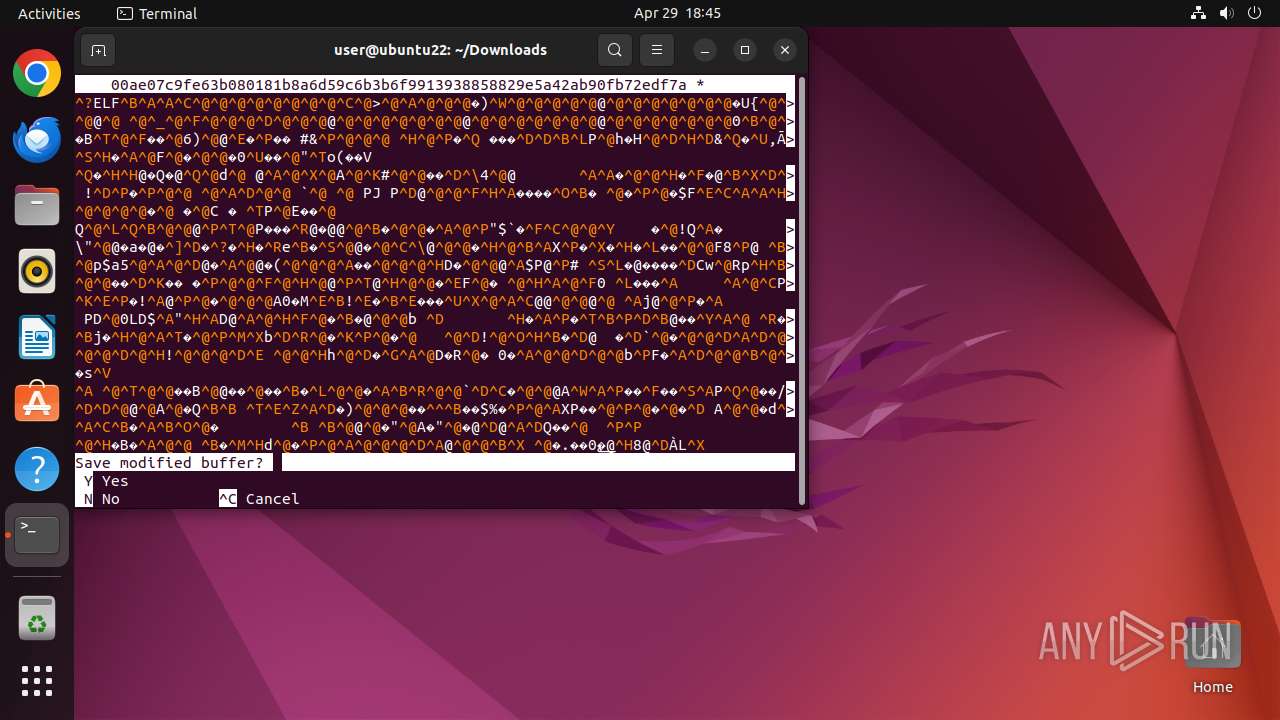
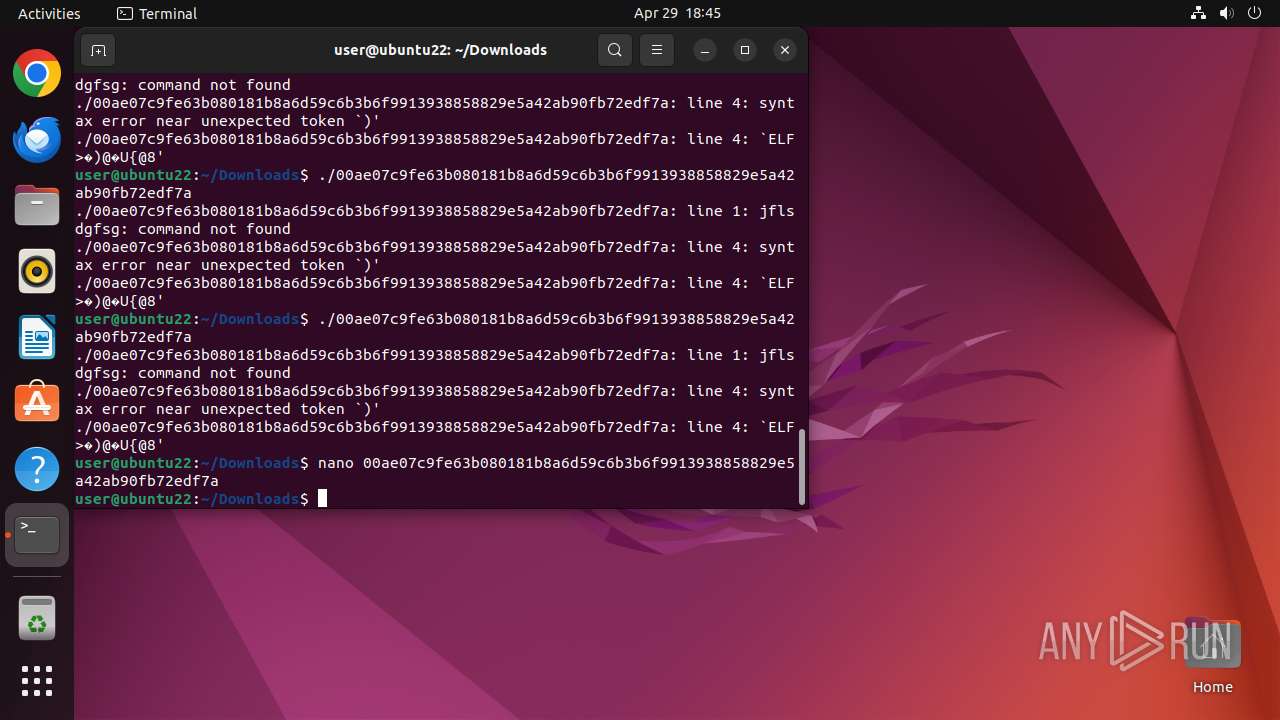
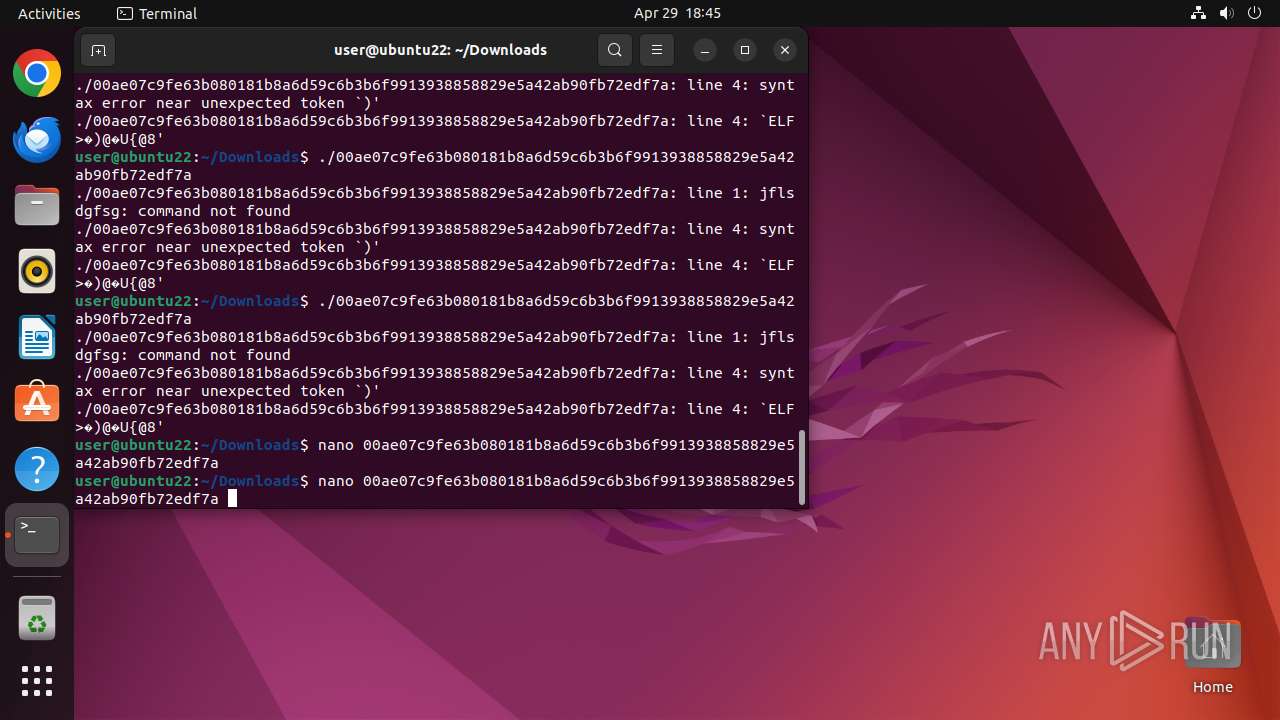
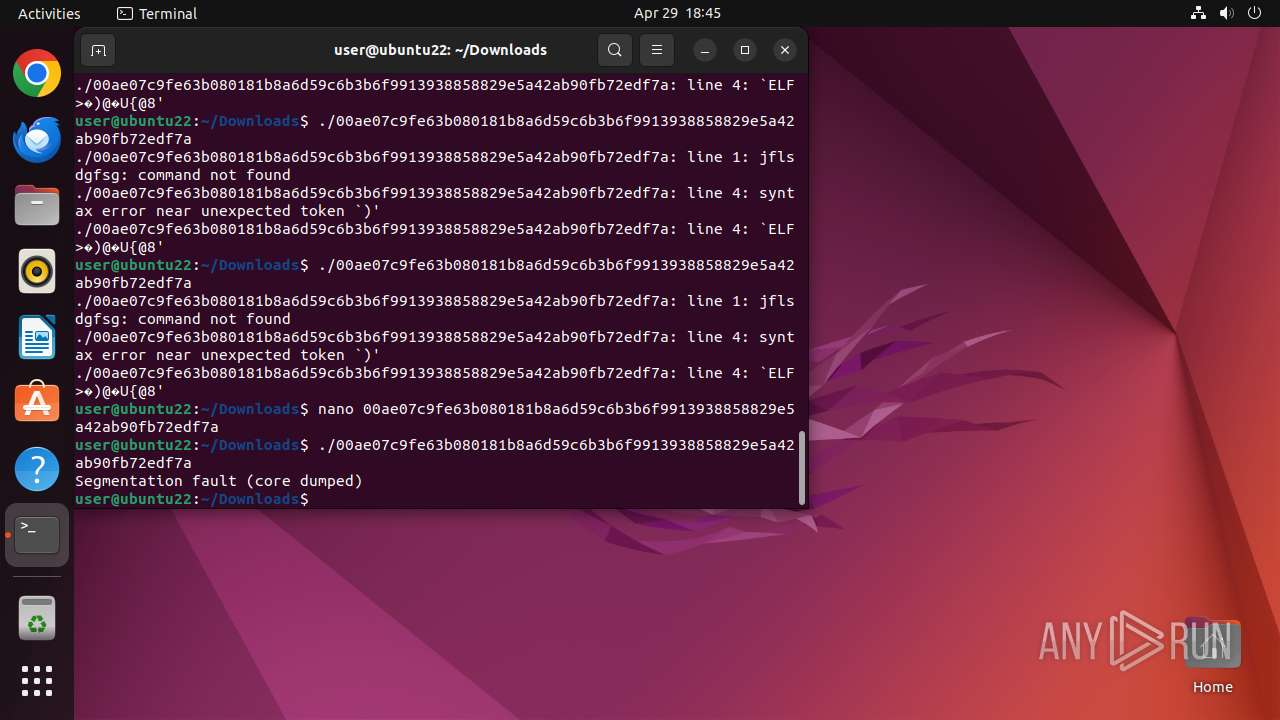
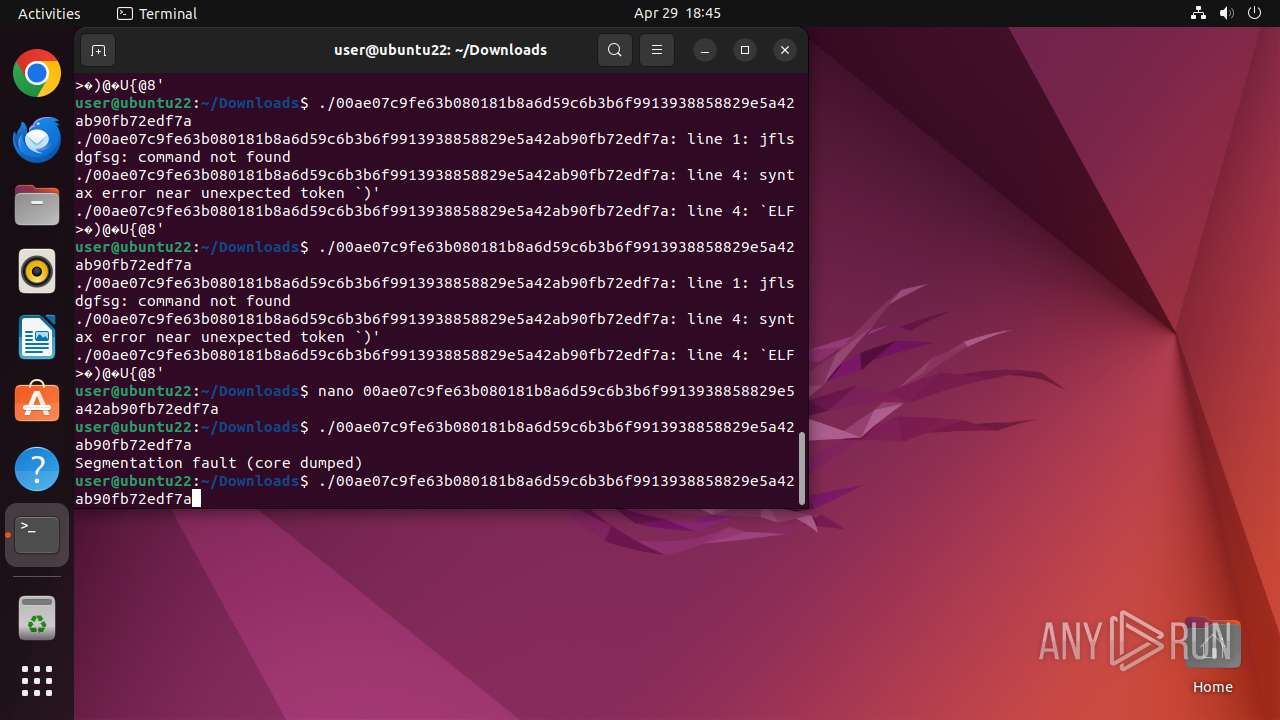
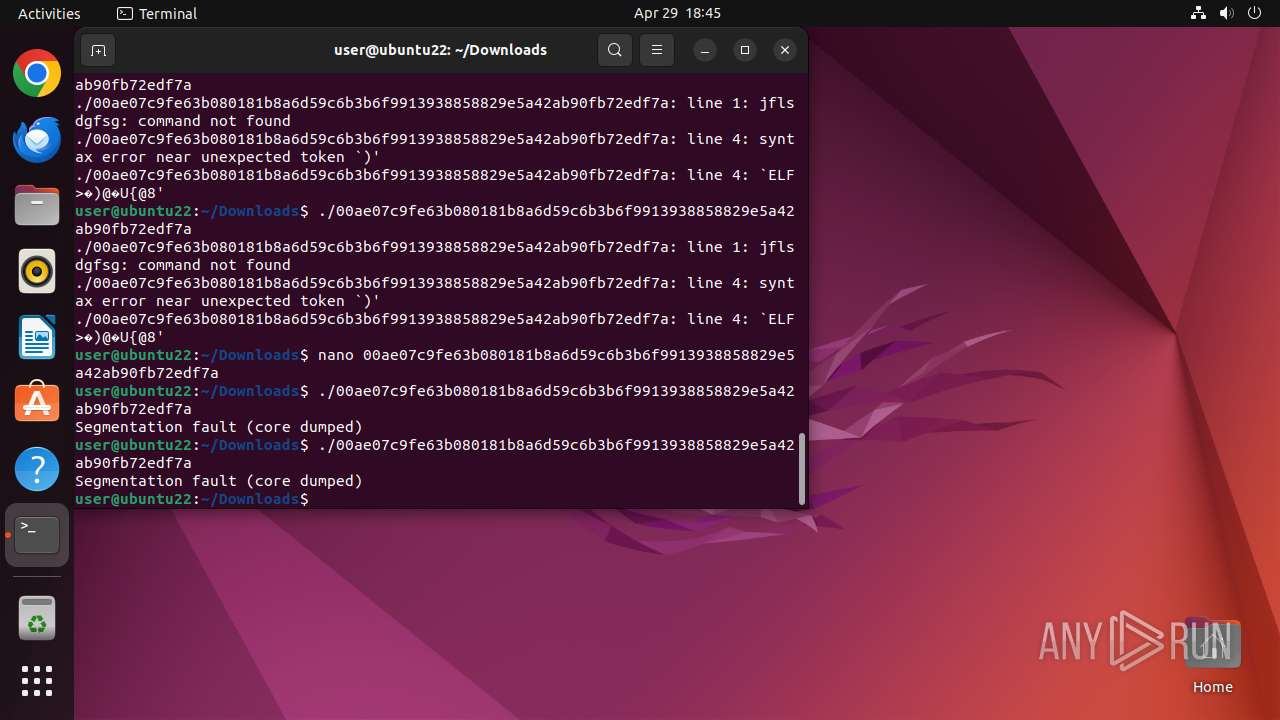
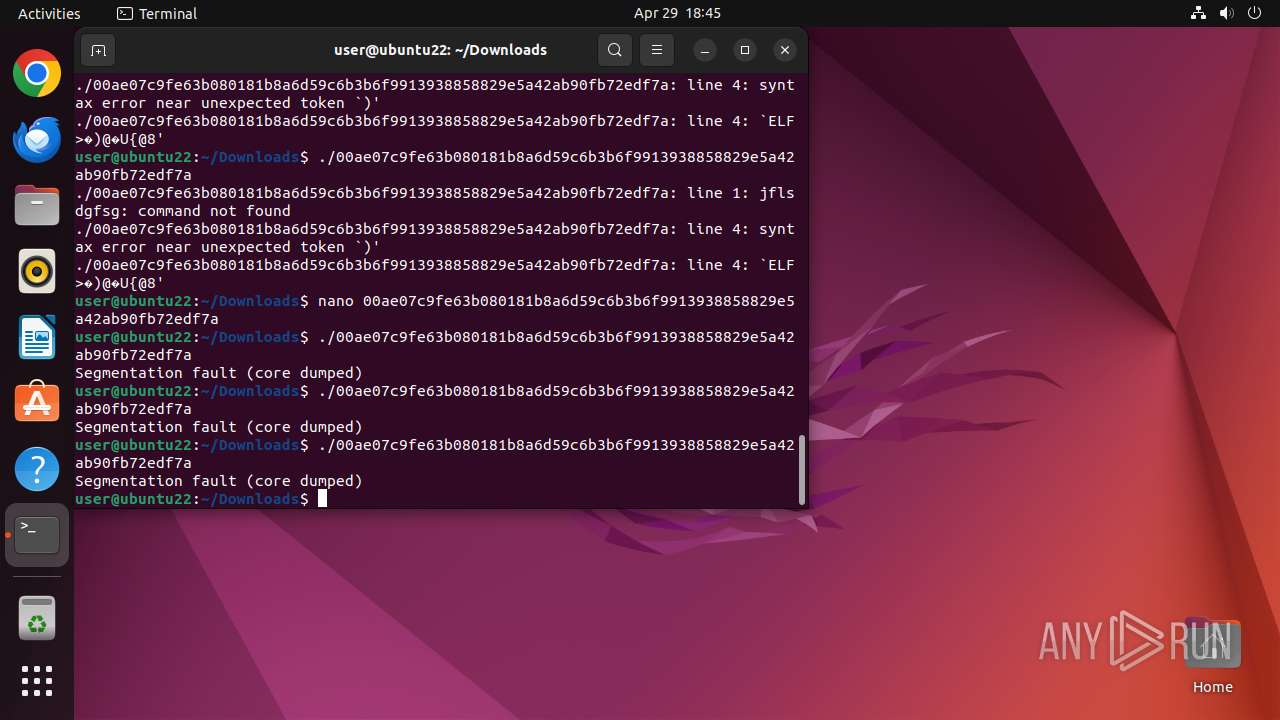
Executes commands using command-line interpreter
- sudo (PID: 40666)
- chrome (PID: 40668)
- gnome-terminal-server (PID: 41062)
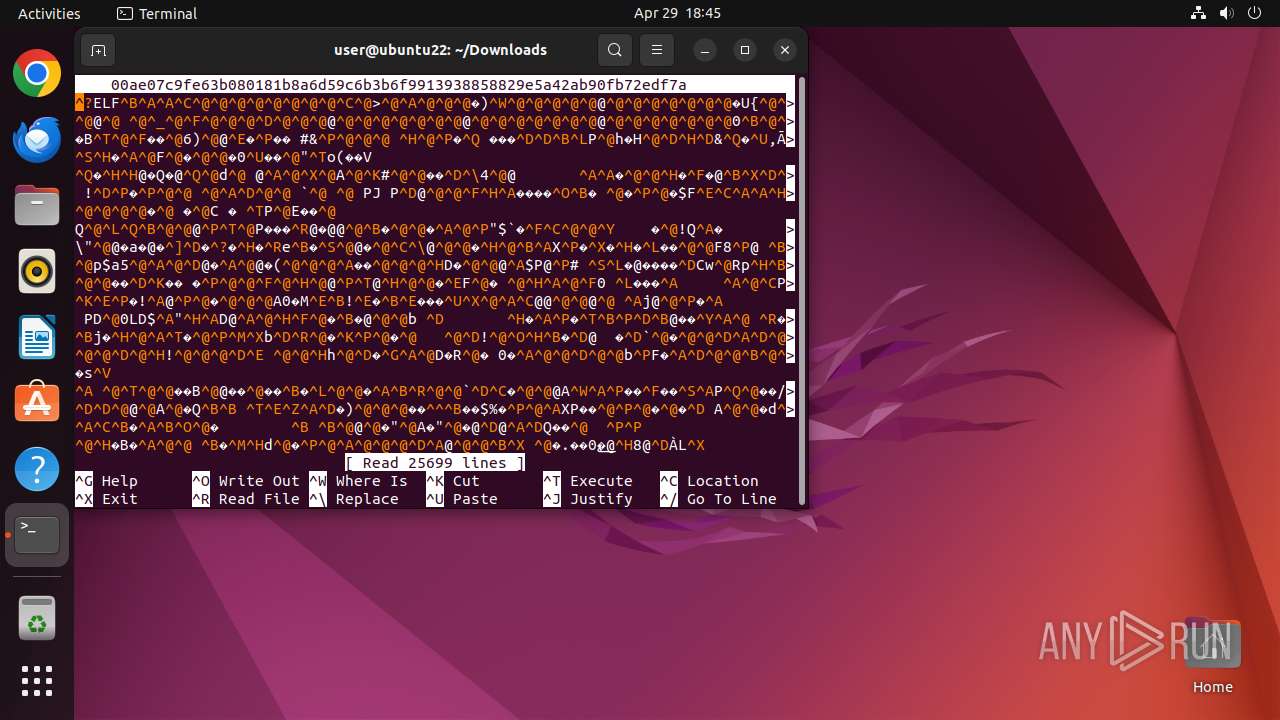
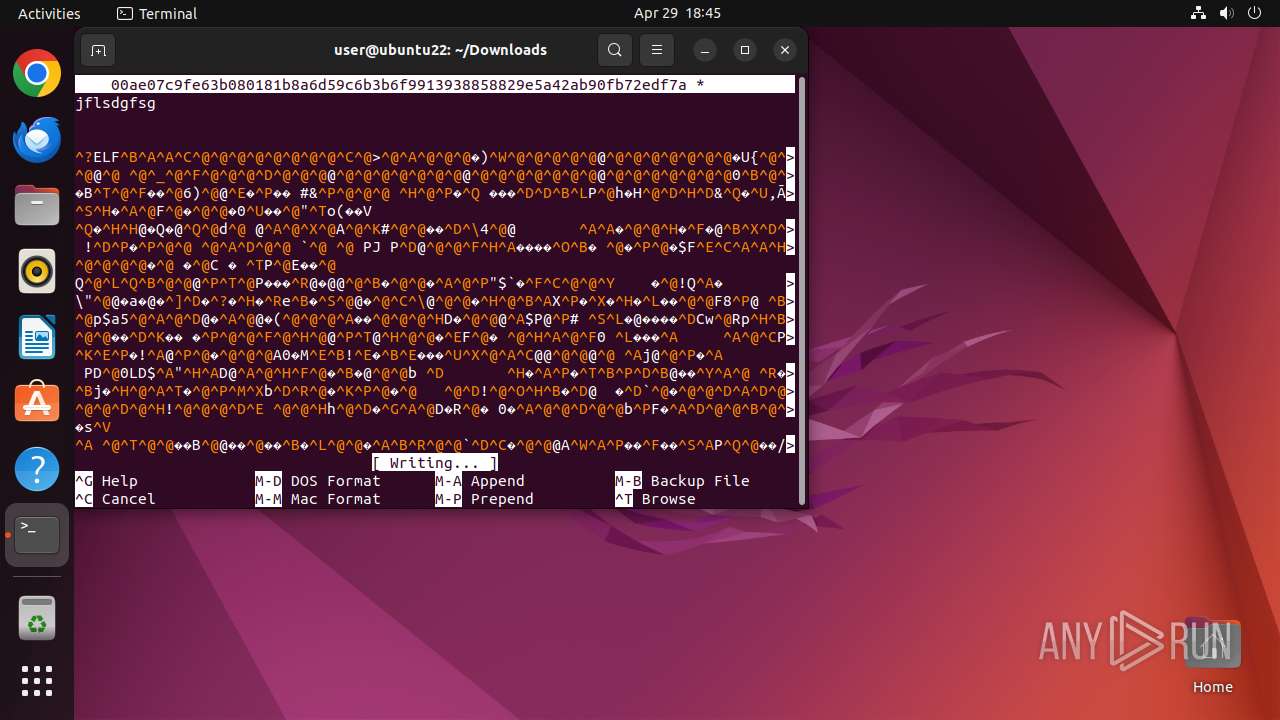
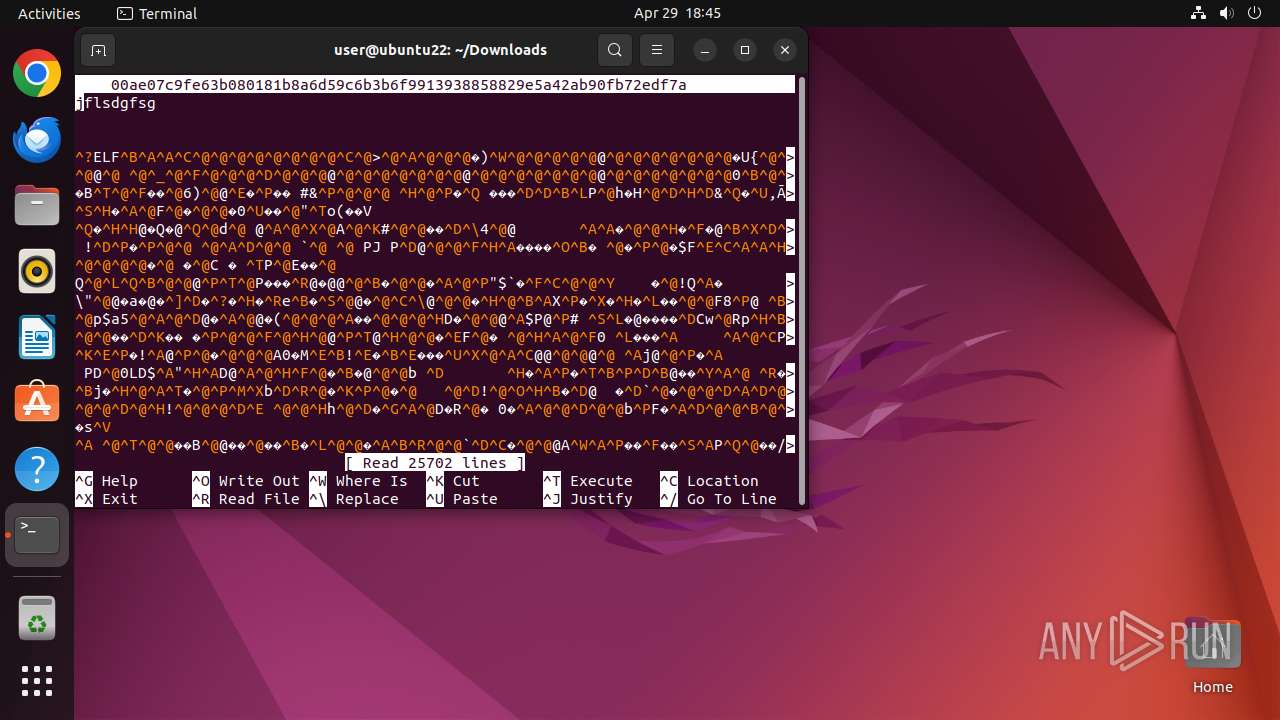
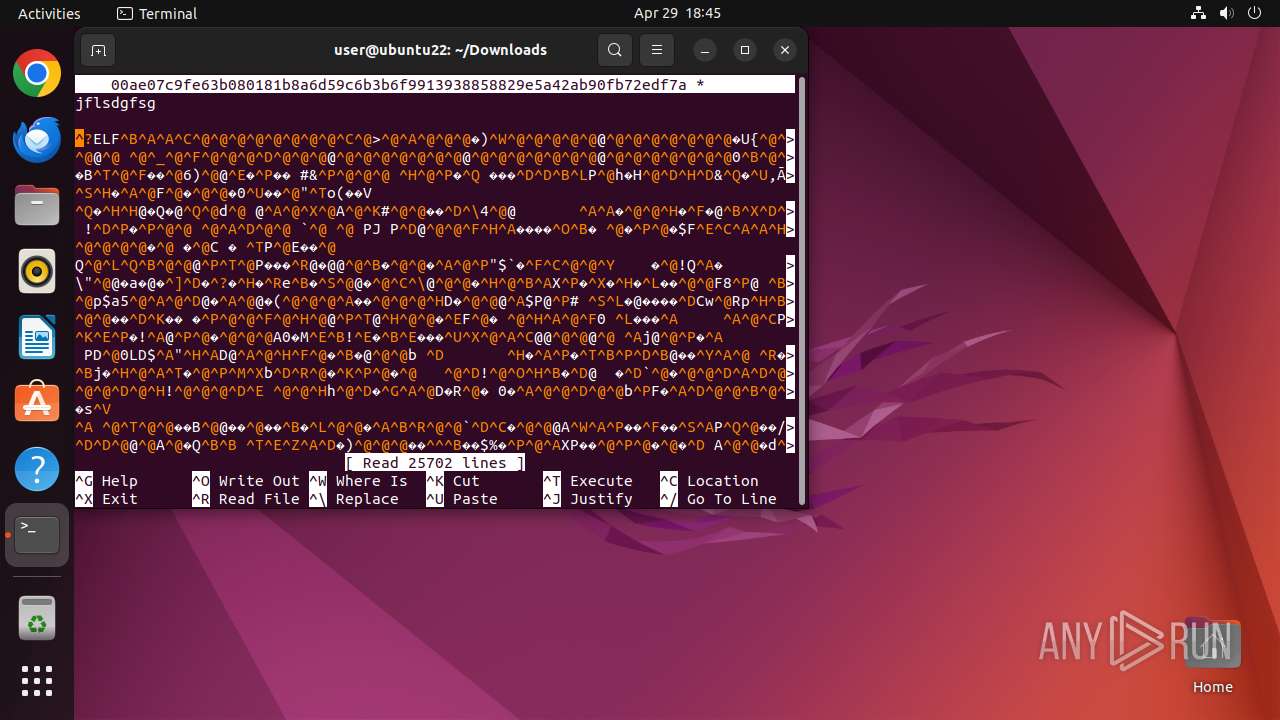
Reads passwd file
- nano (PID: 41102)
- nano (PID: 41114)
- nano (PID: 41122)
- nano (PID: 41132)
INFO
Checks timezone
- python3.10 (PID: 41054)
- chrome (PID: 40668)
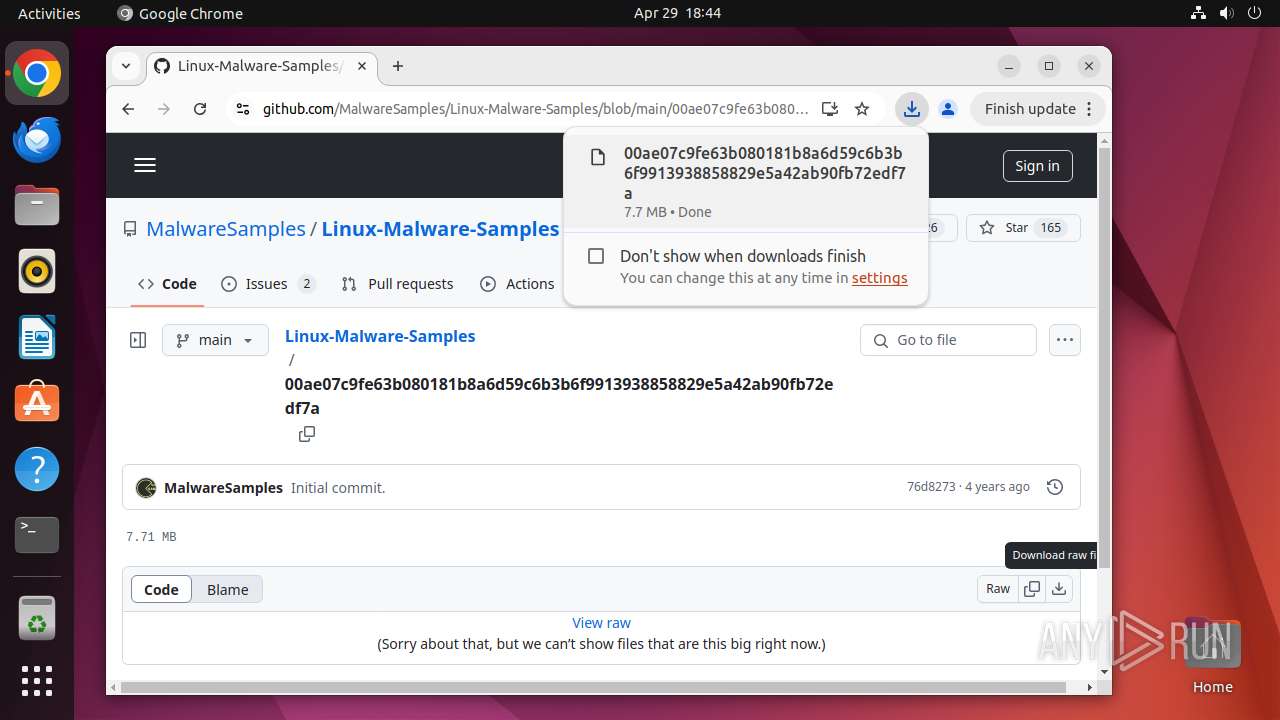
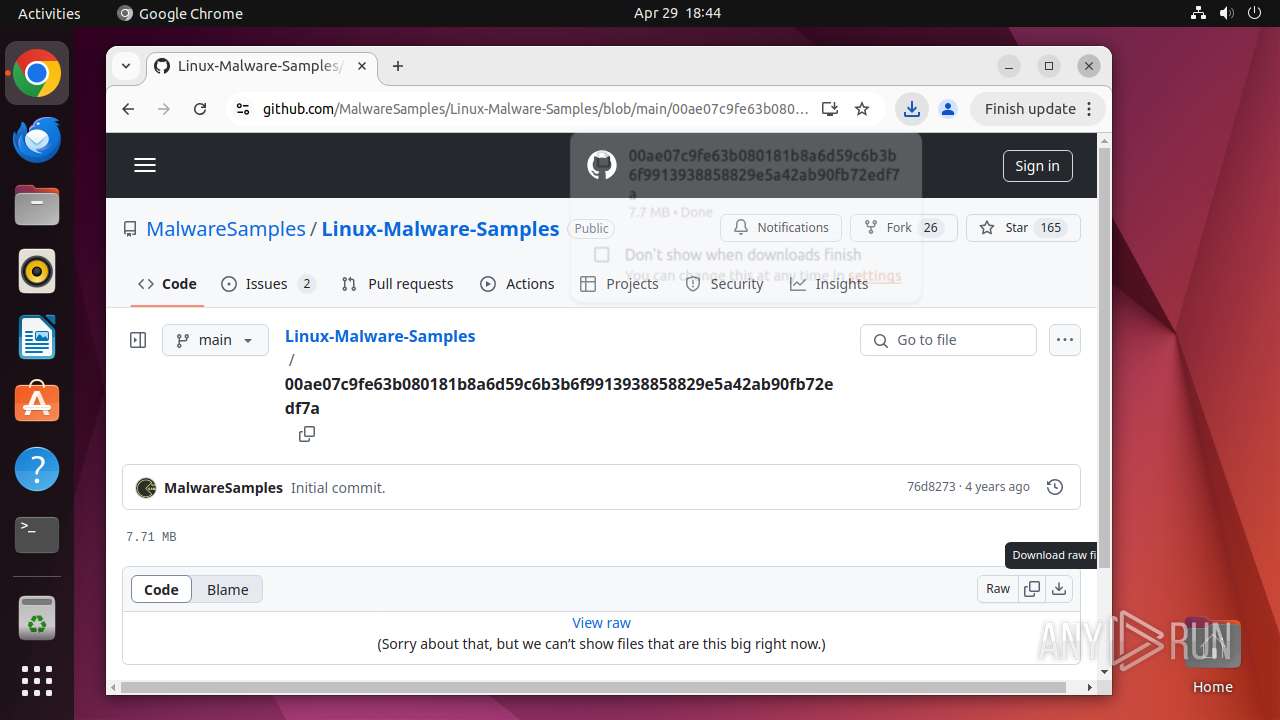
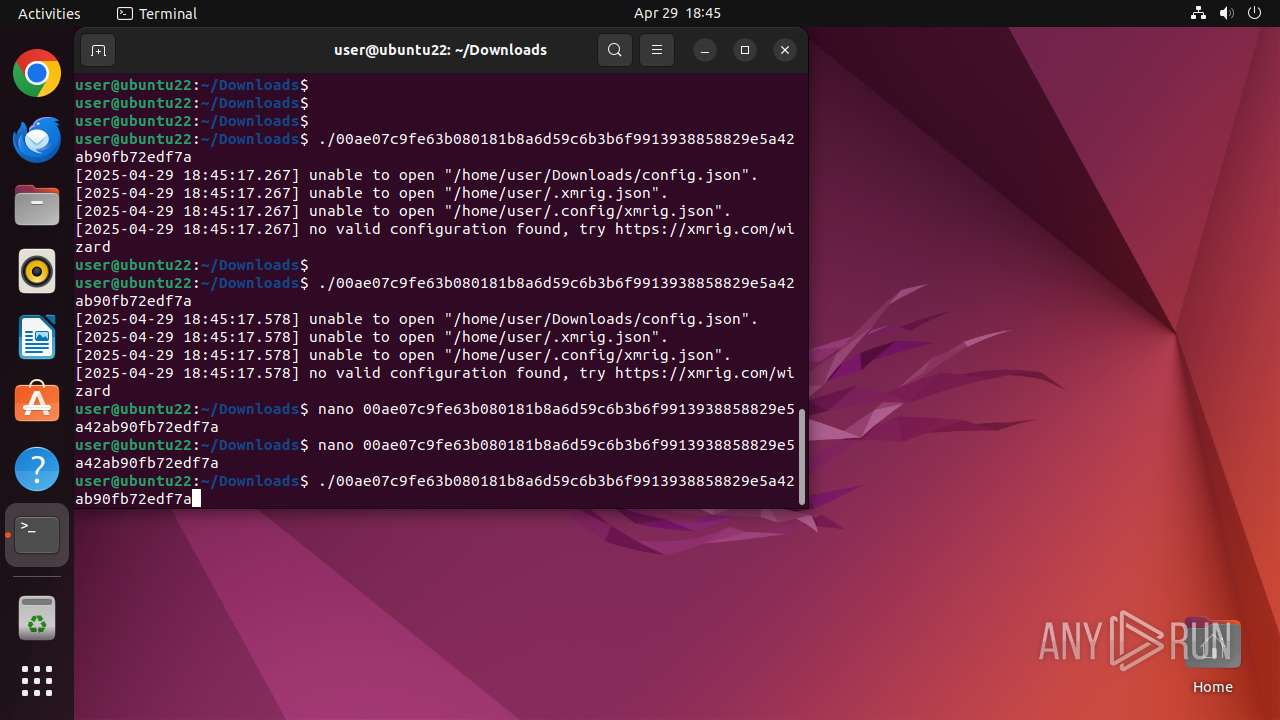
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41099)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41105)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41098)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41106)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41107)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41108)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41109)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41110)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41111)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41112)
- 00ae07c9fe63b080181b8a6d59c6b3b6f9913938858829e5a42ab90fb72edf7a (PID: 41113)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
361
Monitored processes
139
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40665 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome google\.com " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | sudo -iu user google-chrome google.com | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40667 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40668 | /usr/bin/google-chrome google.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40669 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40670 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40671 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40672 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40673 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40674 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
12
Suspicious files
571
Text files
31
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40668 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
90
DNS requests
83
Threats
112
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackabrtjqqtlkfg42dx6l6he4s7q_20250411.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250411.743742949.14_all_ENGB500000_ad6zlqy7zvlwybrc56kgnjb2psiq.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/advsmb52xq3kv4d7uo3oa25kja5q_9747/hfnkpimlhhgieaddgfemjhofmfblmnib_9747_all_adgo3gm7255tv6igd7ufn4zh2r5q.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p4hk7t7ztumoqzhiq26rtjdhc4_3068/jflookgnkcckhobaglndicnbbgbonegd_3068_all_lvzxw5k2be7wzytqtigjjre2qy.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adfsnc2pdt3qaf4hwbwm6urhgf5a_2025.4.23.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.23.00_all_cumg7qttmli5i4tswkgpwksdxe.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrovrpquemobbwthbstjwffhima_2025.1.17.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.01.17.01_all_dd5w5blqtgwb4xkyhfpmehllye.crx3 | unknown | — | — | whitelisted |
40714 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kjzx44qbwip7coqbzqqhrmlbxq_1298/efniojlnjndmcbiieegkicadnoecjjef_1298_all_hlxap3ertzvsxflisbgujhagiu.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.18:80 | — | Canonical Group Limited | GB | unknown |
— | — | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.190.49:80 | — | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40714 | chrome | 216.58.212.132:443 | www.google.com | — | — | whitelisted |
40714 | chrome | 142.250.185.206:443 | google.com | — | — | whitelisted |
40714 | chrome | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40714 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |