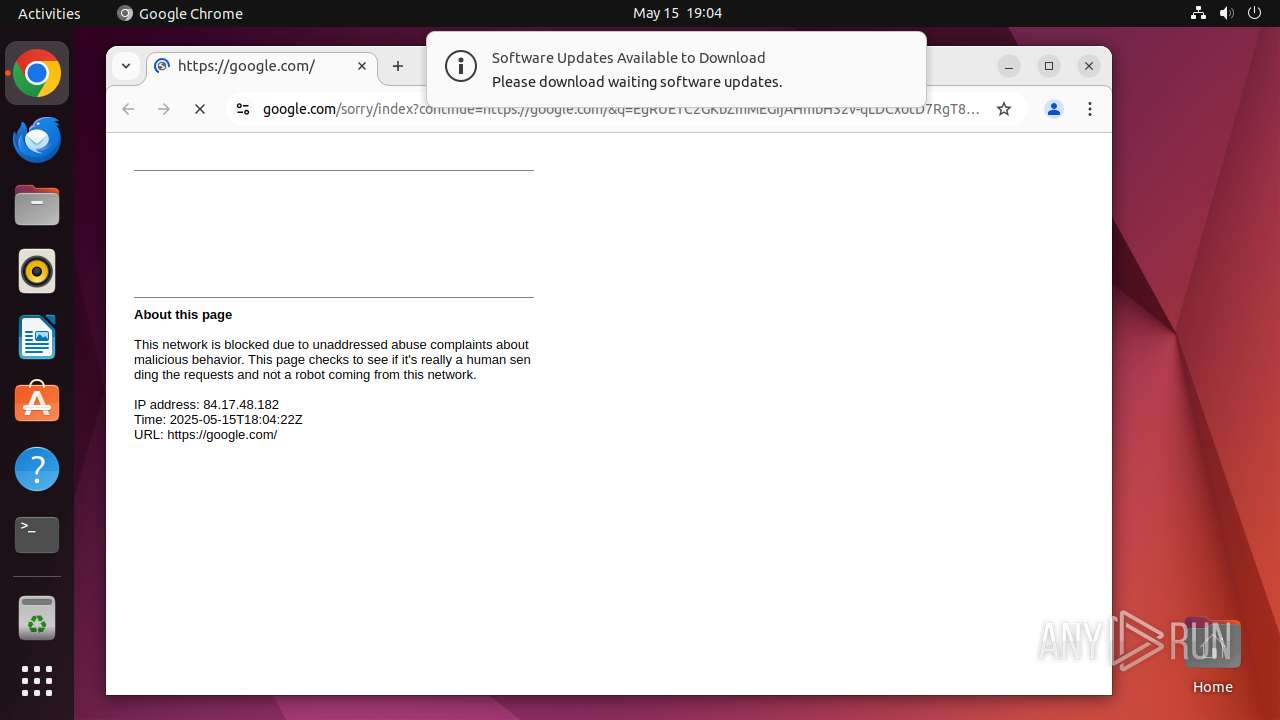
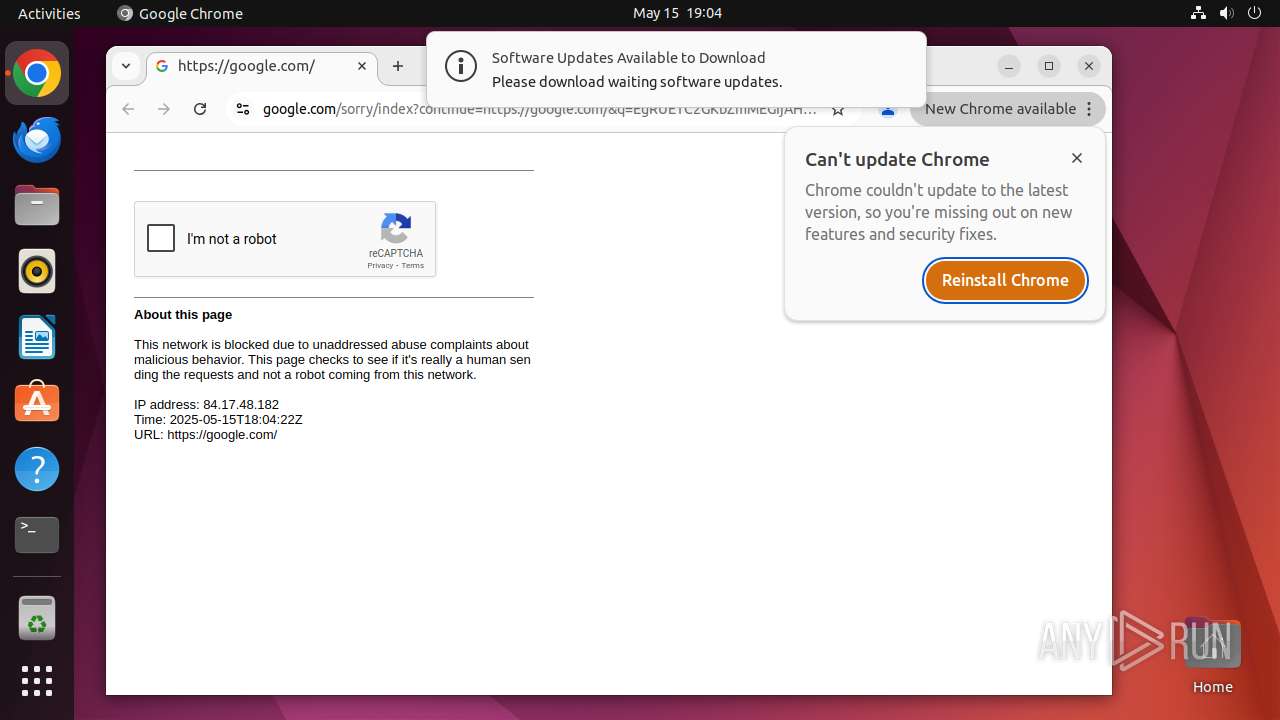
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/f78d6adc-f65d-4d5d-abd1-aa95c8ba0f35 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 18:04:16 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
No malicious indicators.SUSPICIOUS
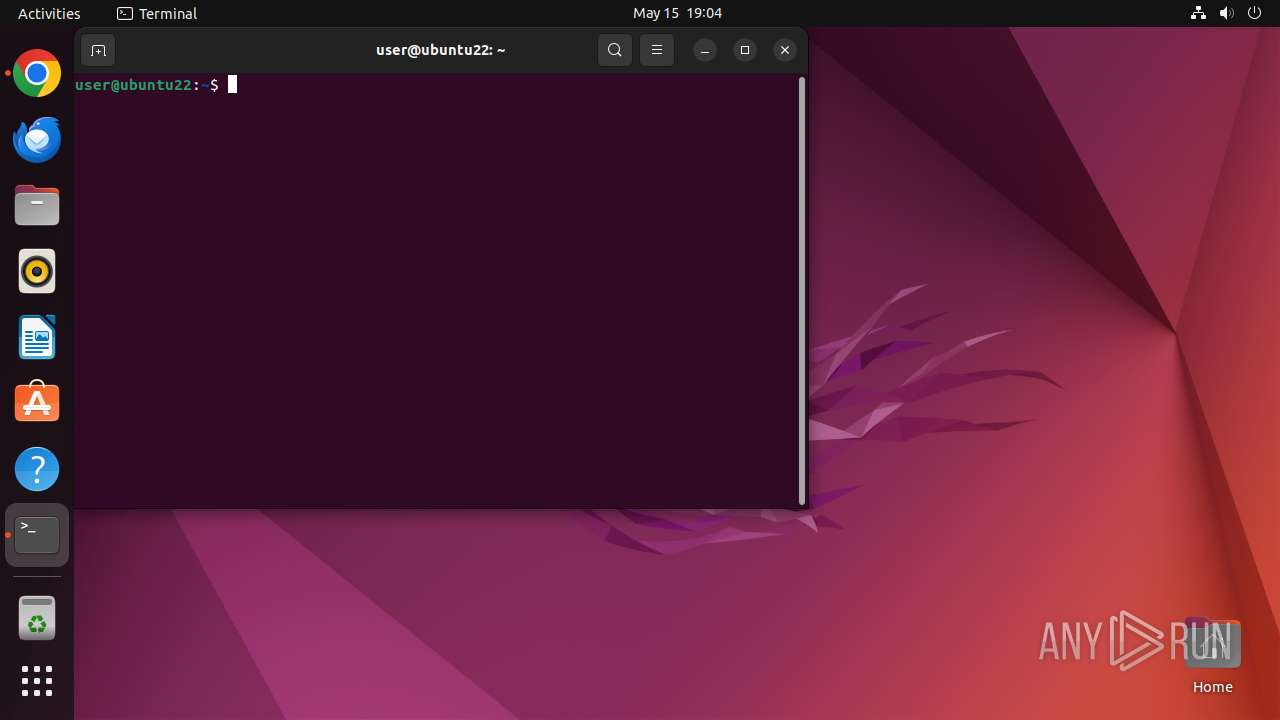
Executes commands using command-line interpreter
- chrome (PID: 40663)
- sudo (PID: 40662)
- gnome-terminal-server (PID: 40920)
Reads passwd file
- dumpe2fs (PID: 40967)
- dumpe2fs (PID: 40974)
- curl (PID: 40948)
Check the Environment Variables Related to System Identification (os-release)
- curl (PID: 40948)
Connects to the server without a host name
- curl (PID: 40948)
INFO
Checks timezone
- chrome (PID: 40663)
- python3.10 (PID: 40912)
- dumpe2fs (PID: 40967)
- dumpe2fs (PID: 40974)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
318
Monitored processes
98
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40661 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome google\.com " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 40662 | sudo -iu user google-chrome google.com | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40663 | /usr/bin/google-chrome google.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40664 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40665 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40667 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40668 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40669 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40670 | "/opt/google/chrome/chrome google\.c" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
85
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40663 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40707 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40798 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 40663 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
28
DNS requests
31
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.18:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
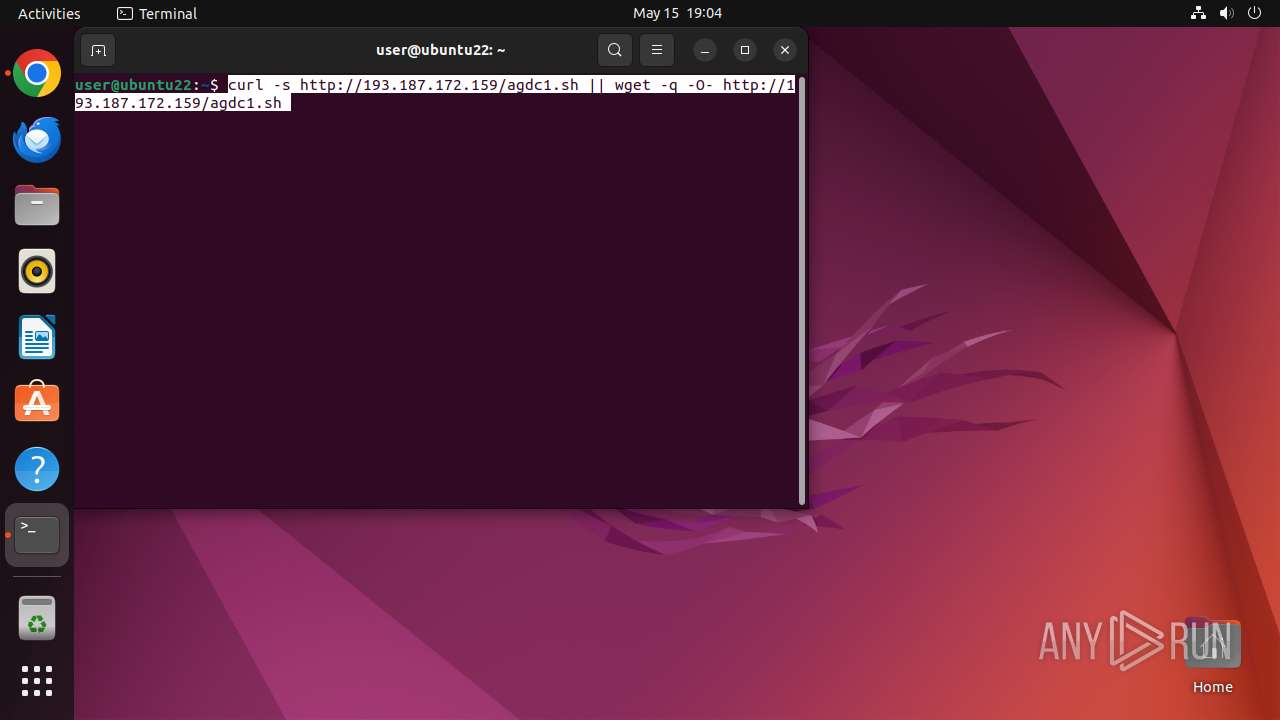
40948 | curl | GET | 404 | 193.187.172.159:80 | http://193.187.172.159/agdc1.sh | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 169.150.255.180:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40710 | chrome | 142.250.181.238:443 | google.com | — | — | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40710 | chrome | 142.250.185.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40710 | chrome | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |