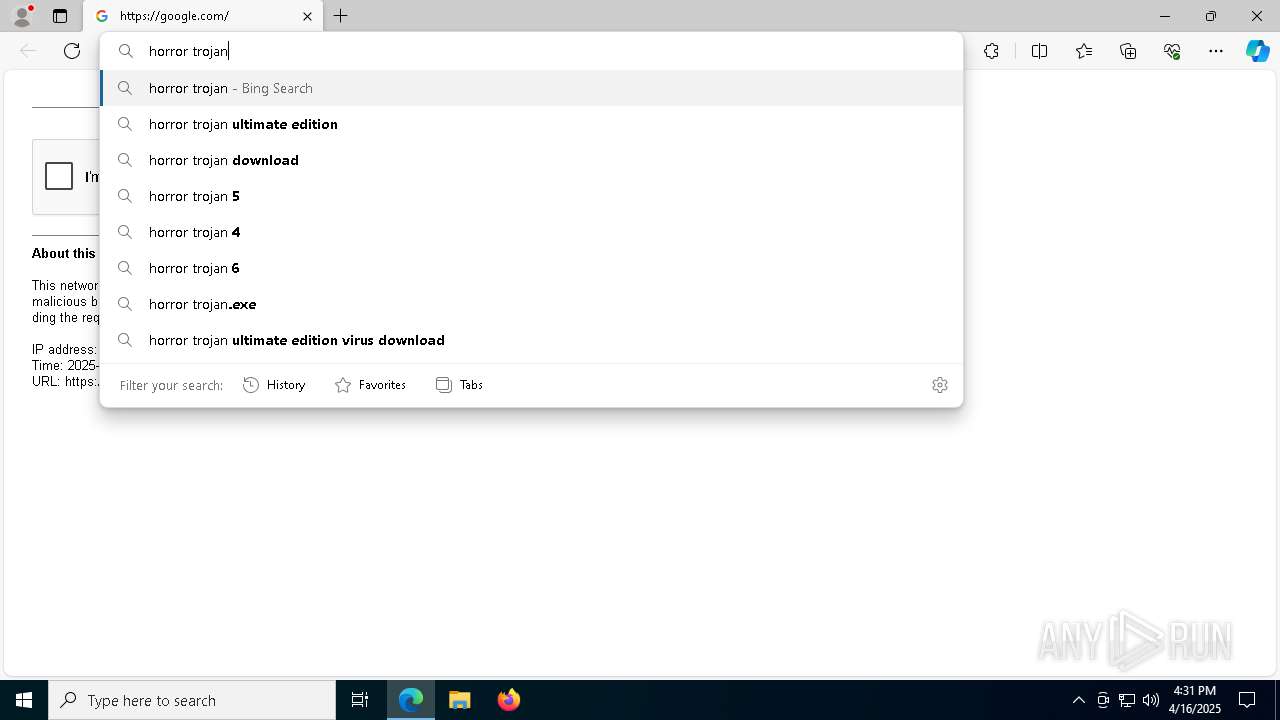
| URL: | google.com |
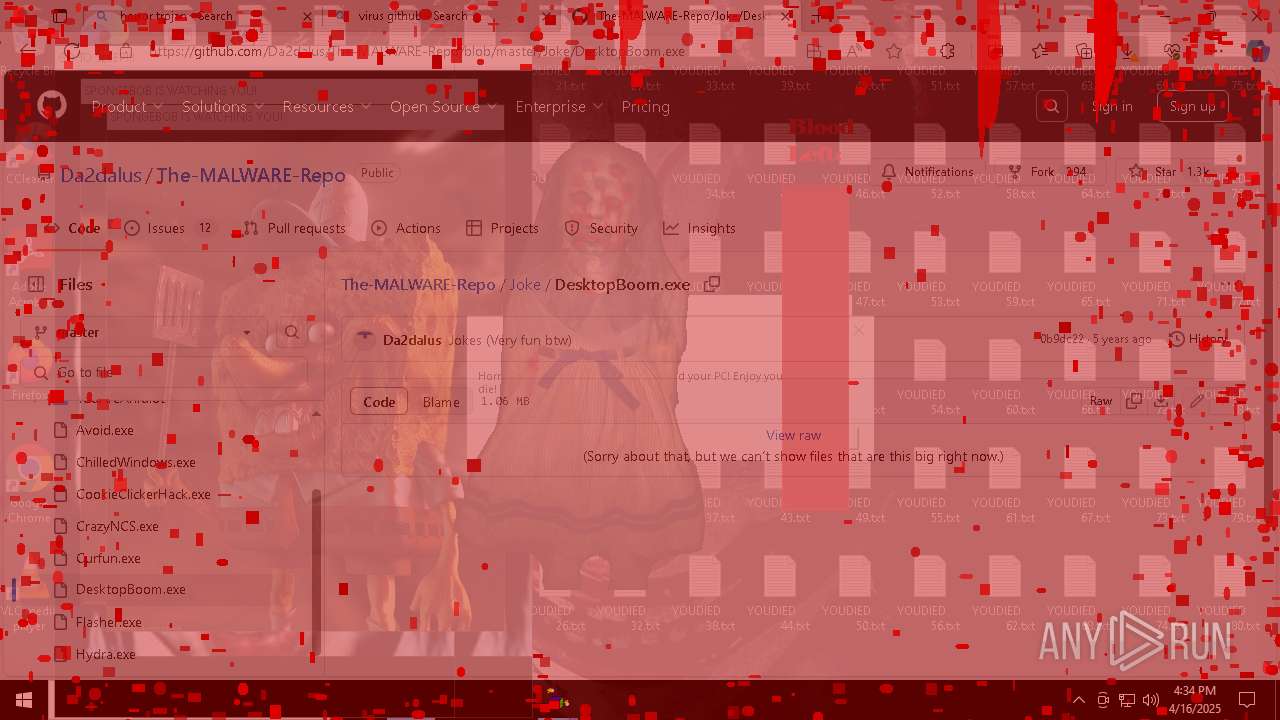
| Full analysis: | https://app.any.run/tasks/f0b4f48d-72c5-4c56-8cb3-40dc37a0607e |
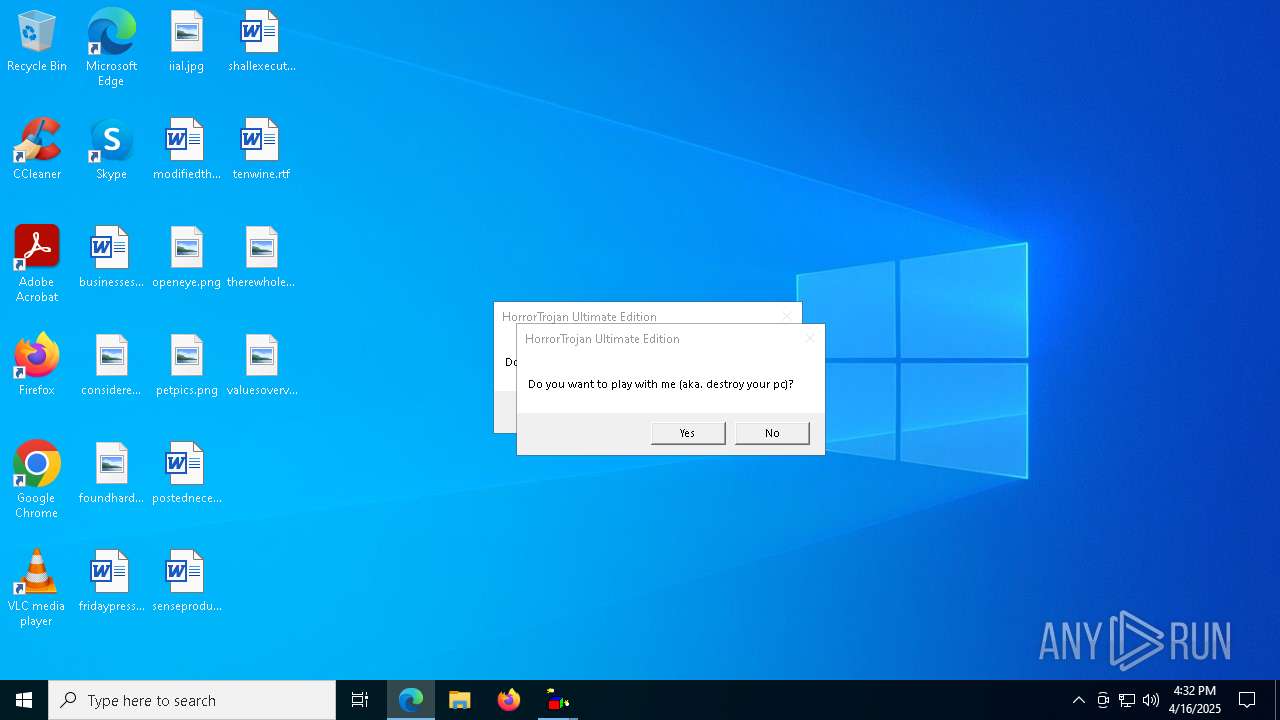
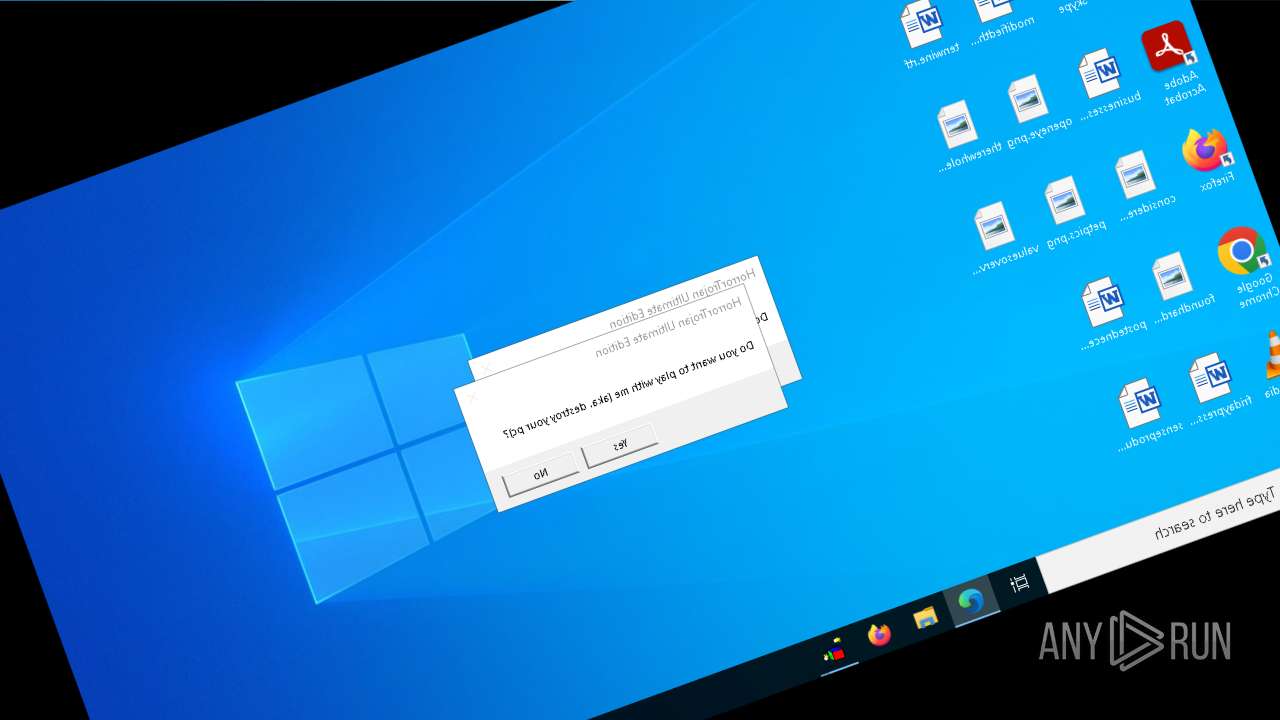
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 16:30:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
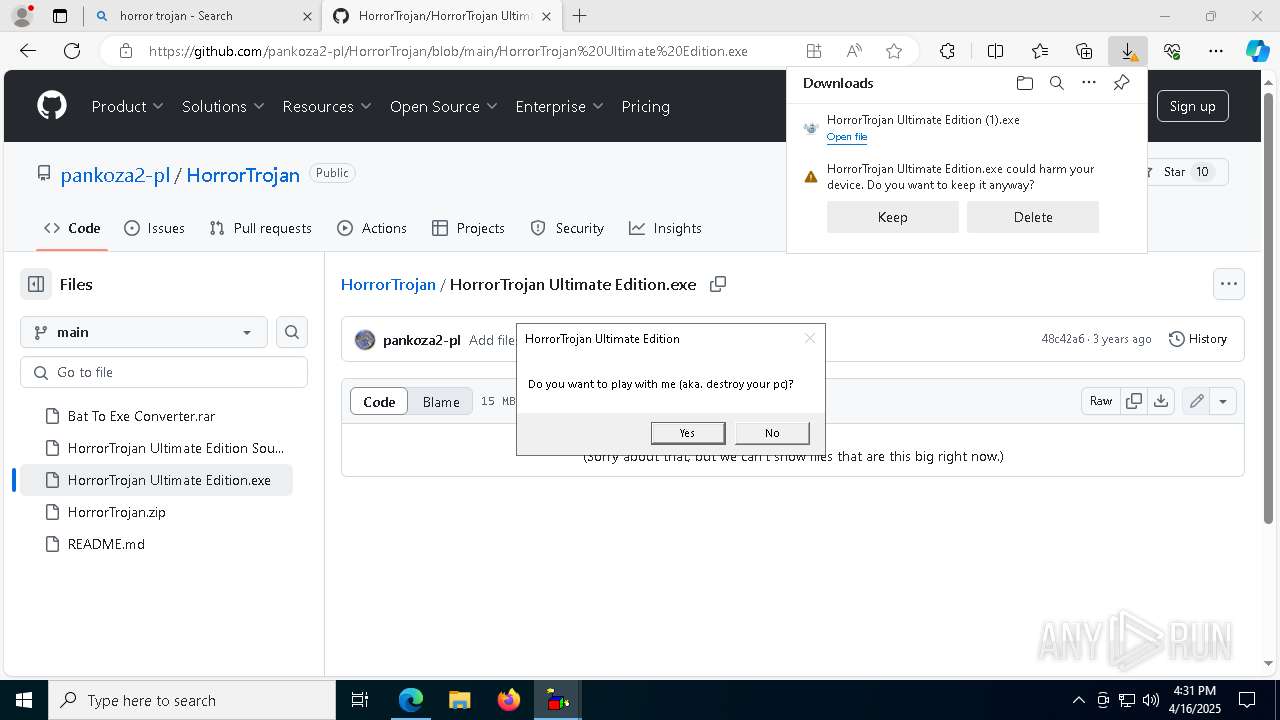
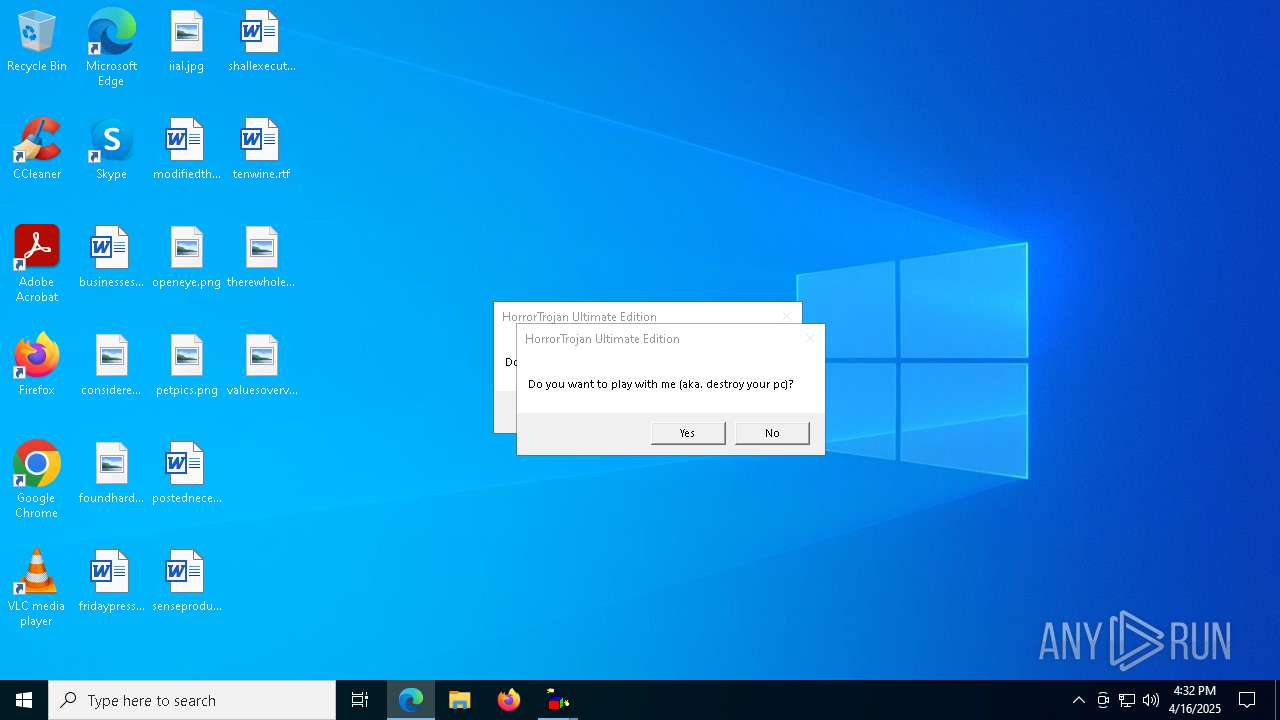
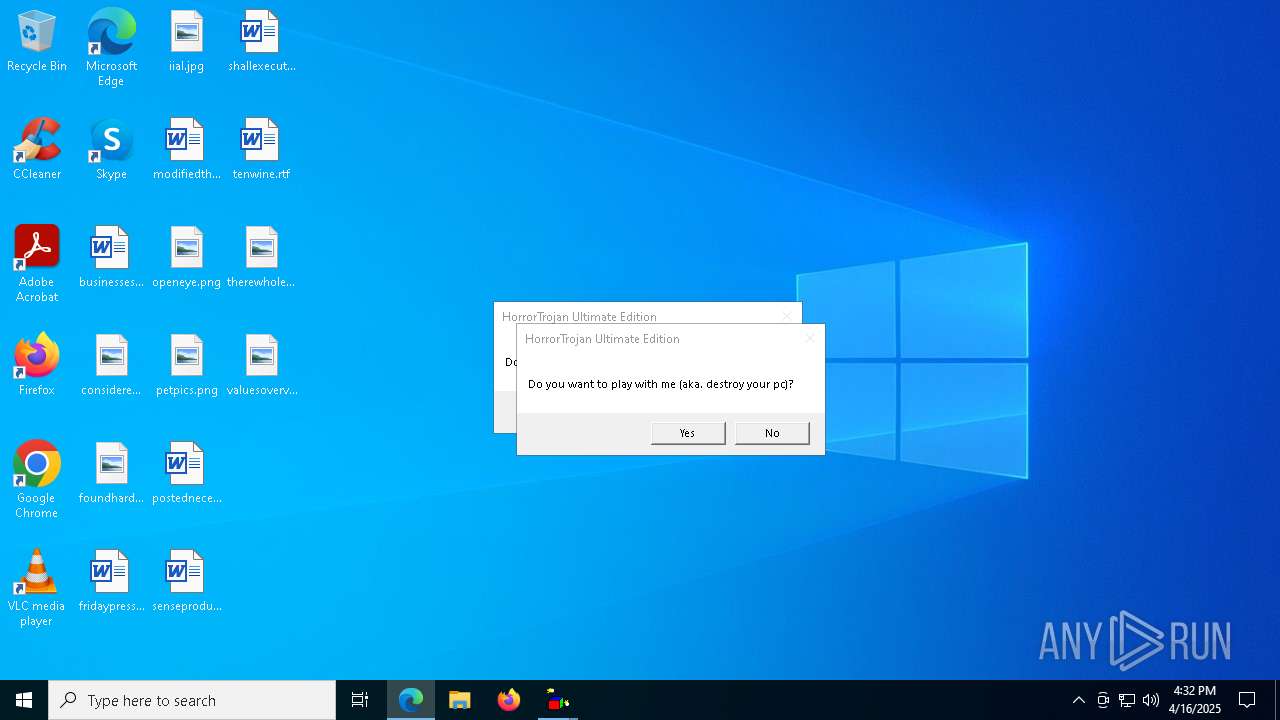
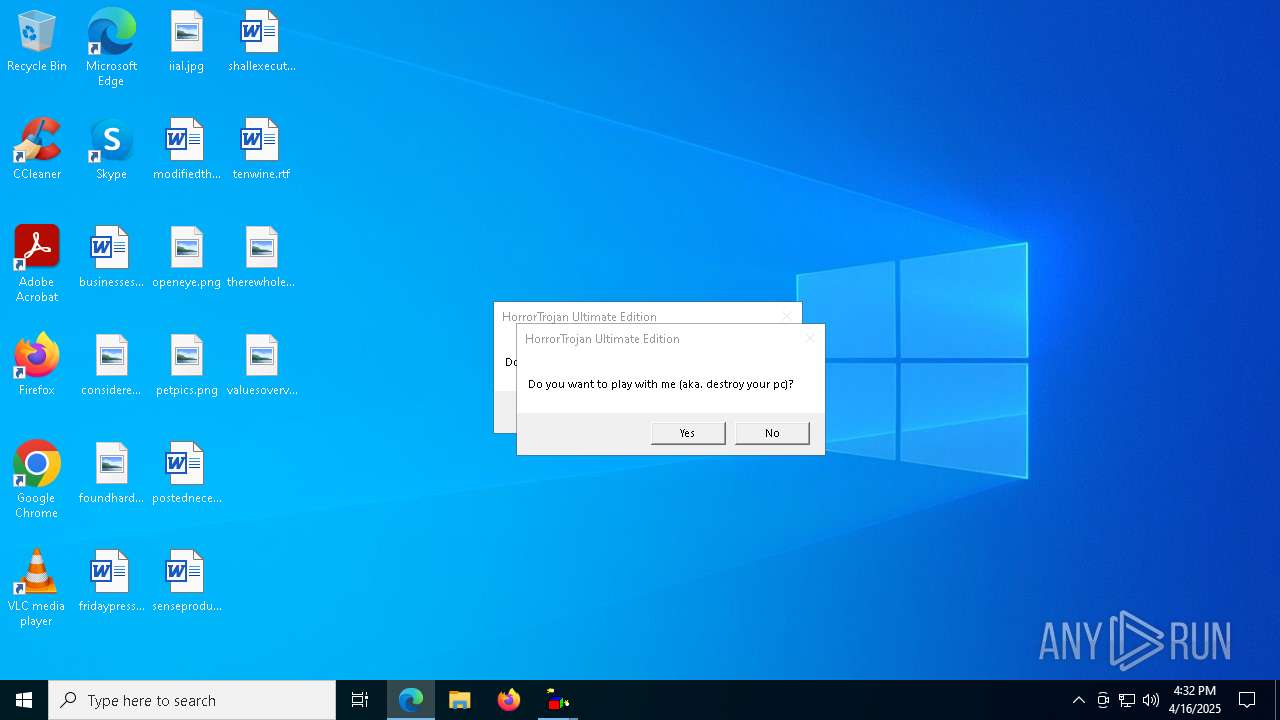
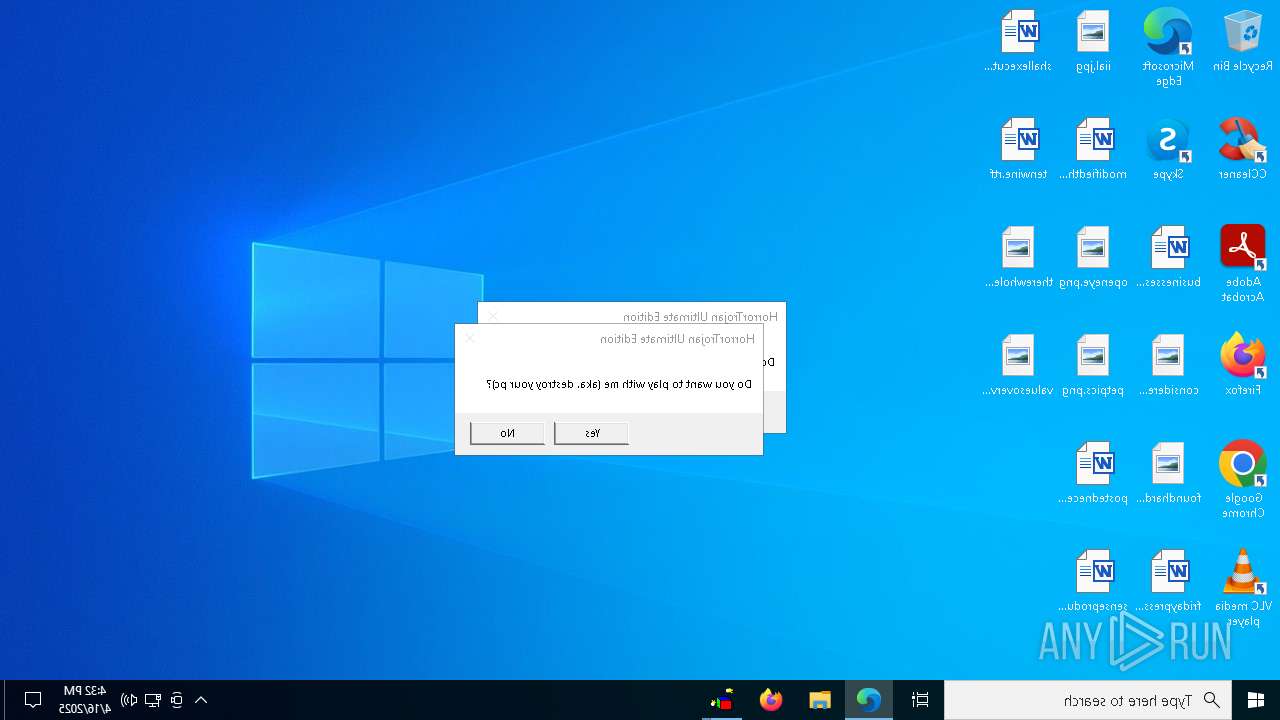
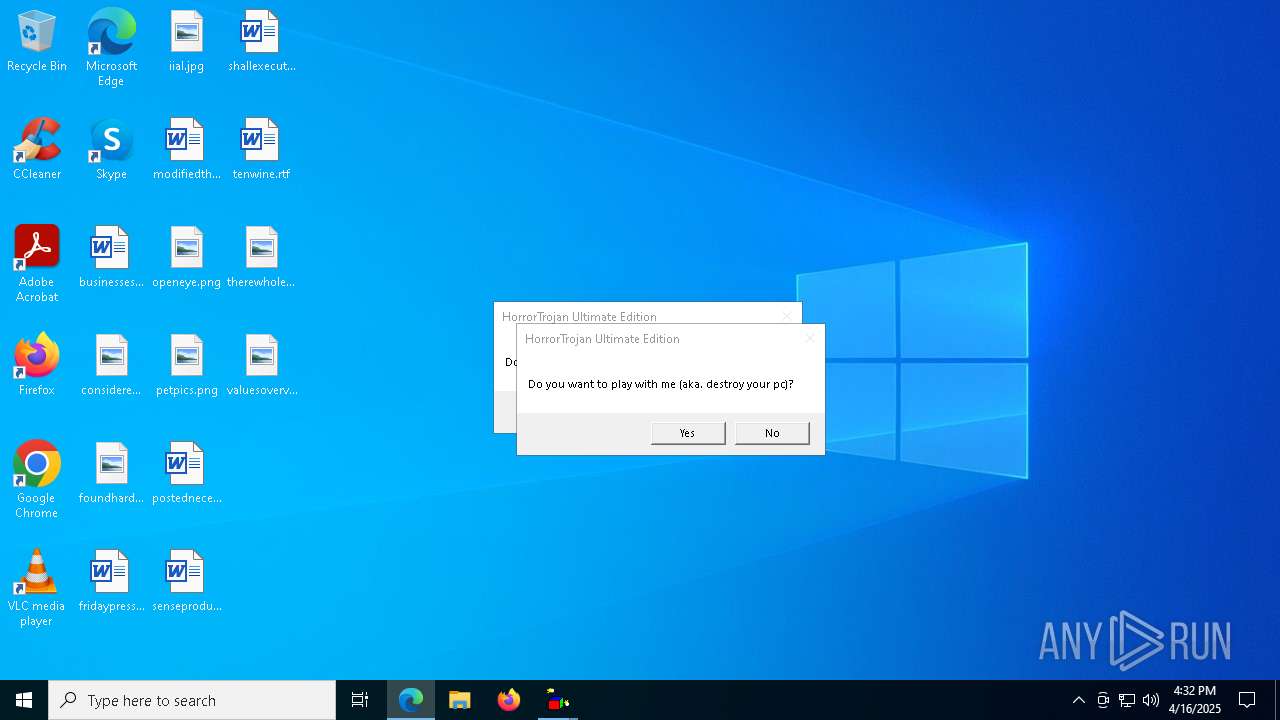
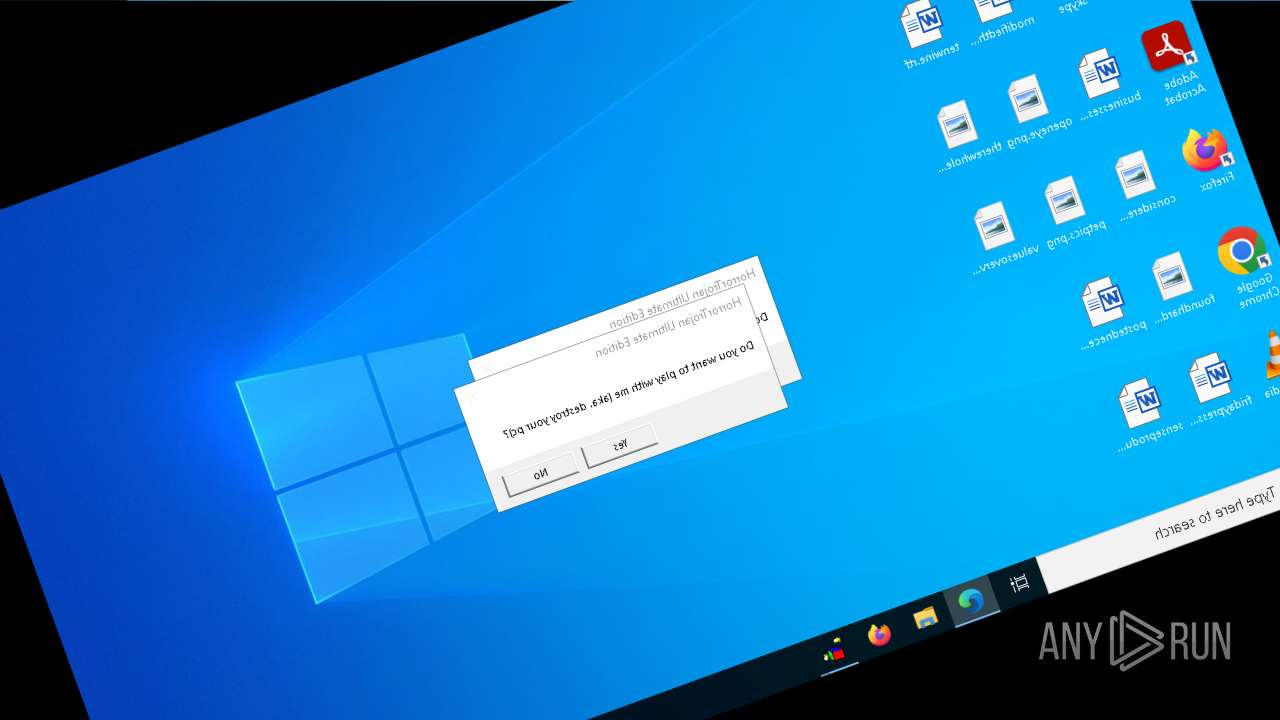
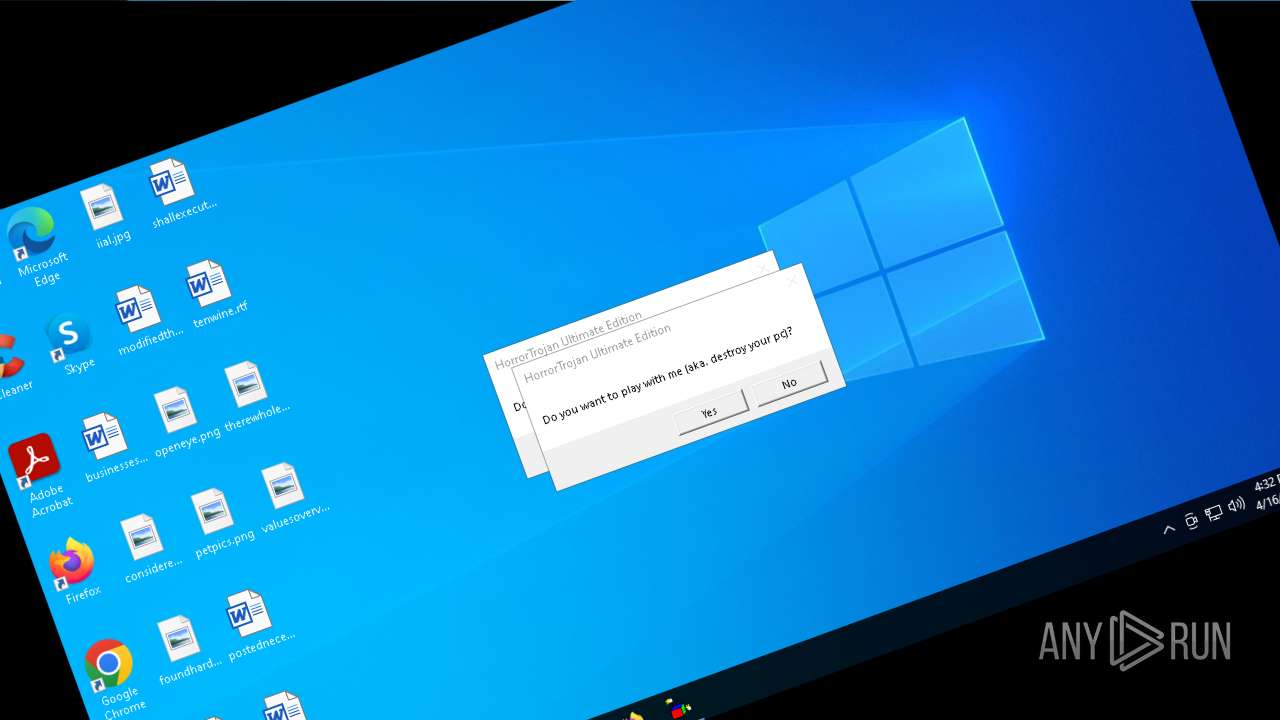
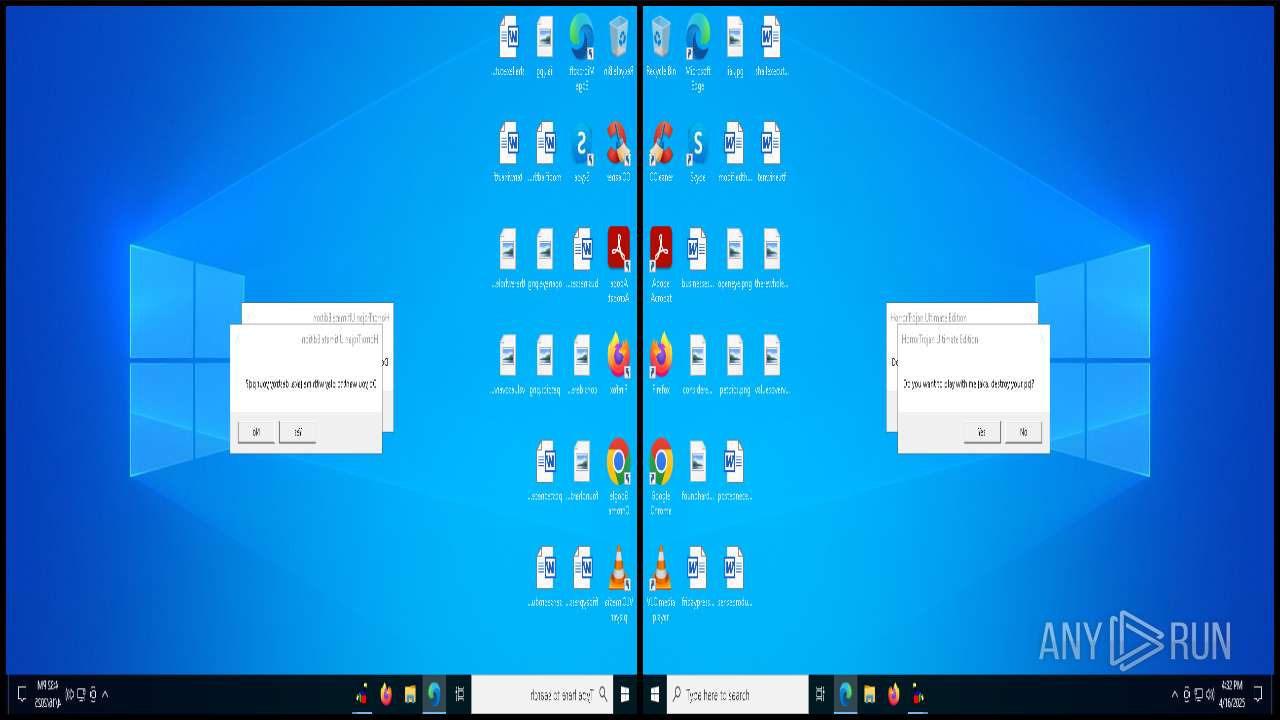
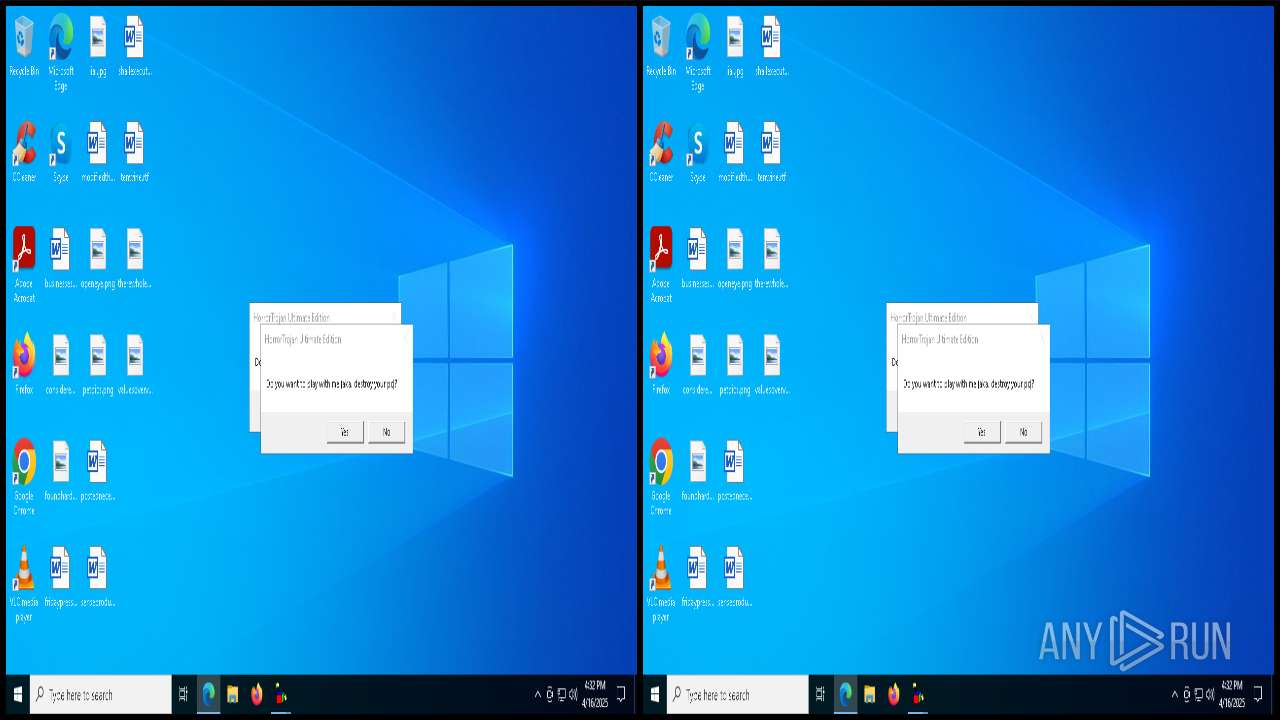
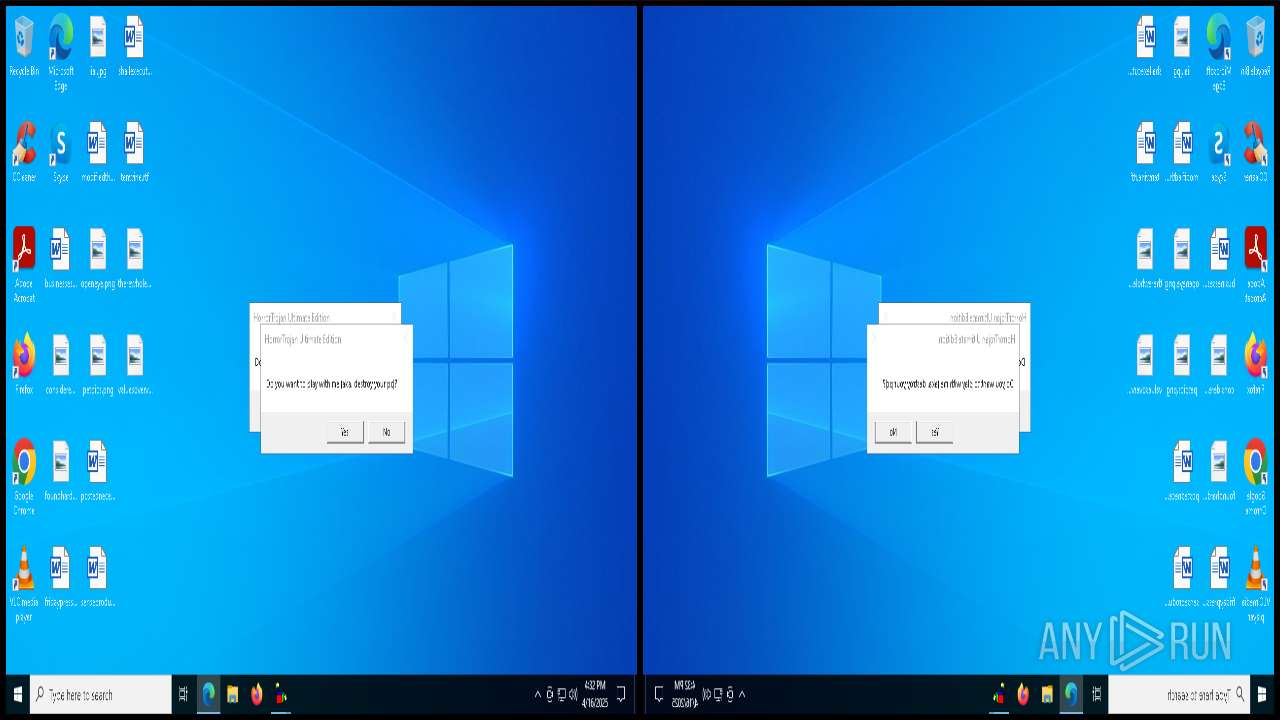
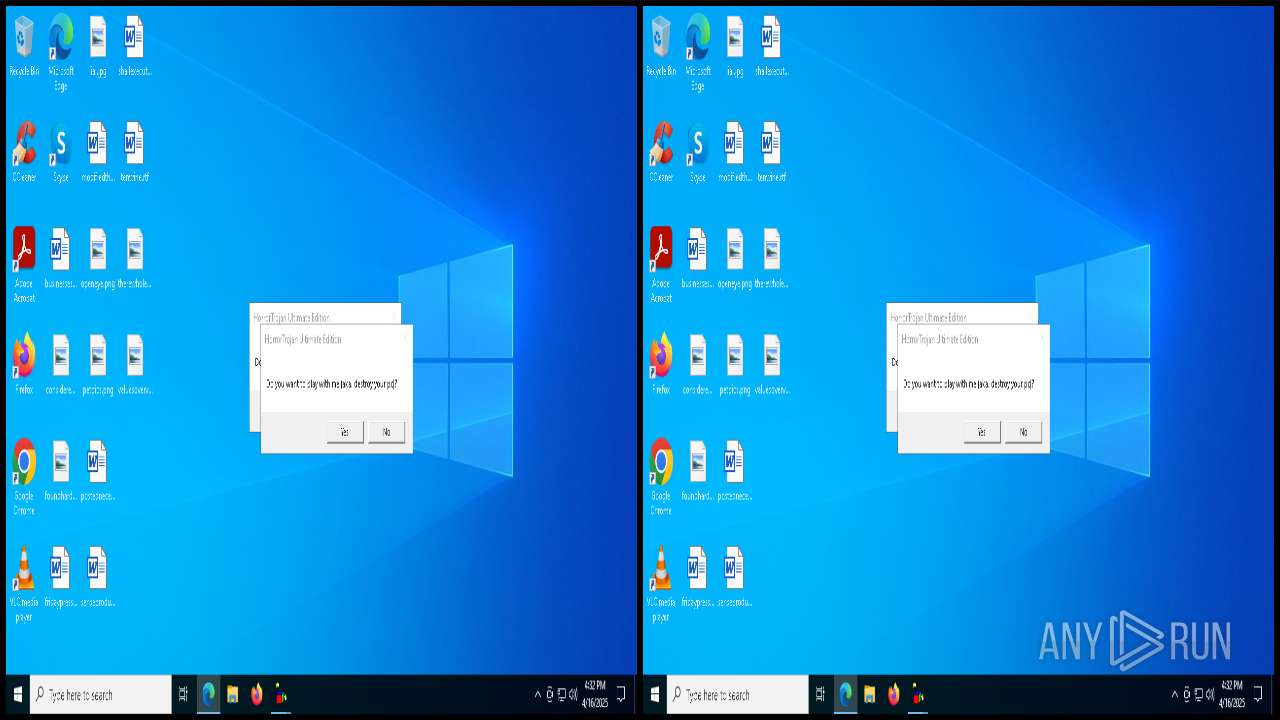
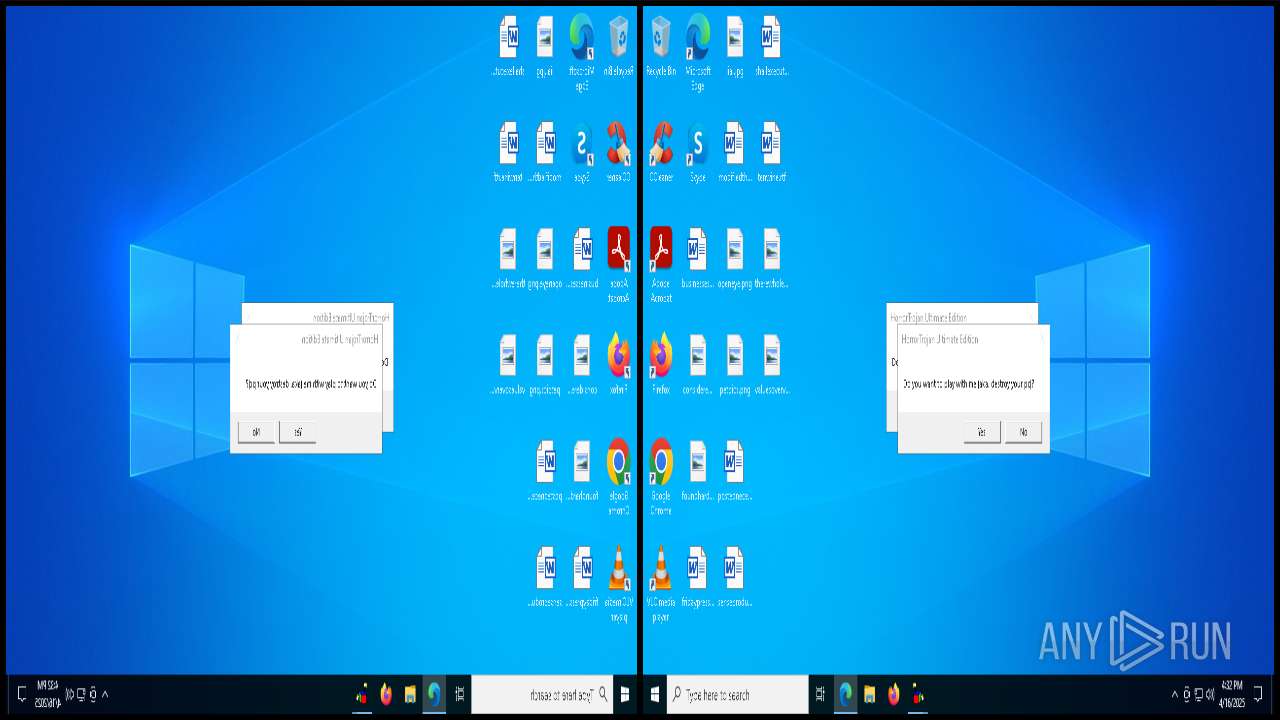
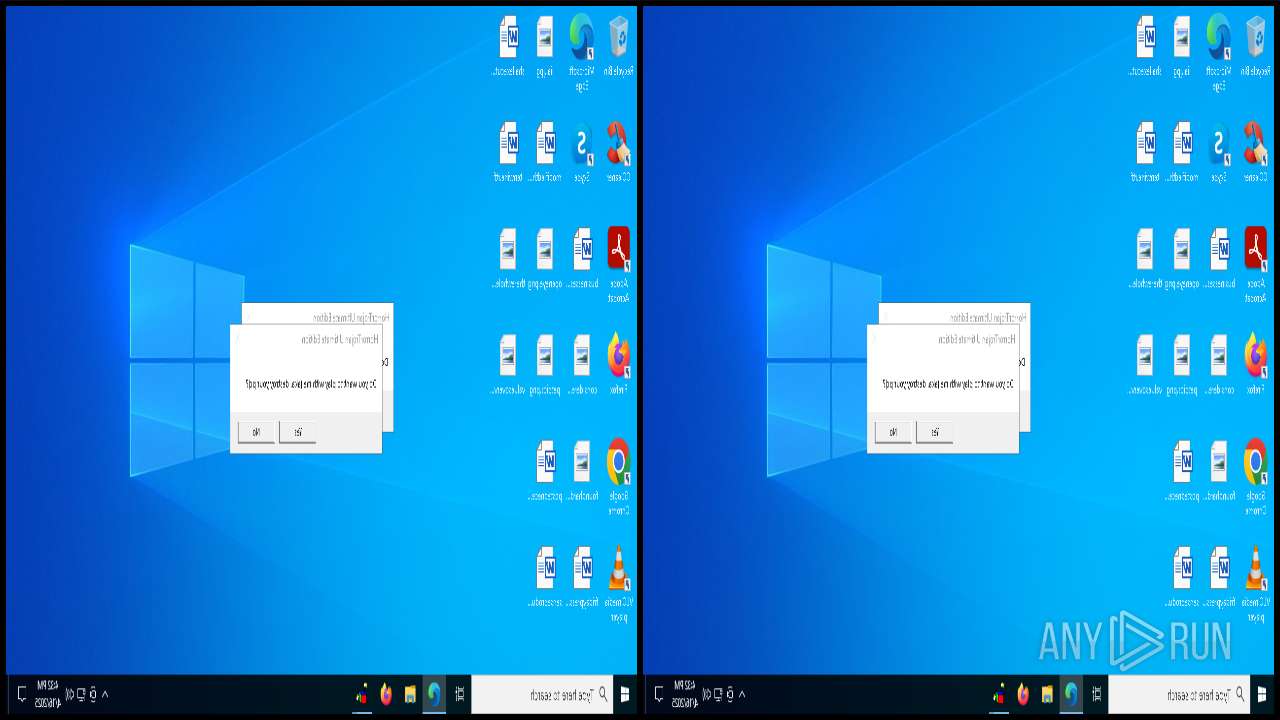
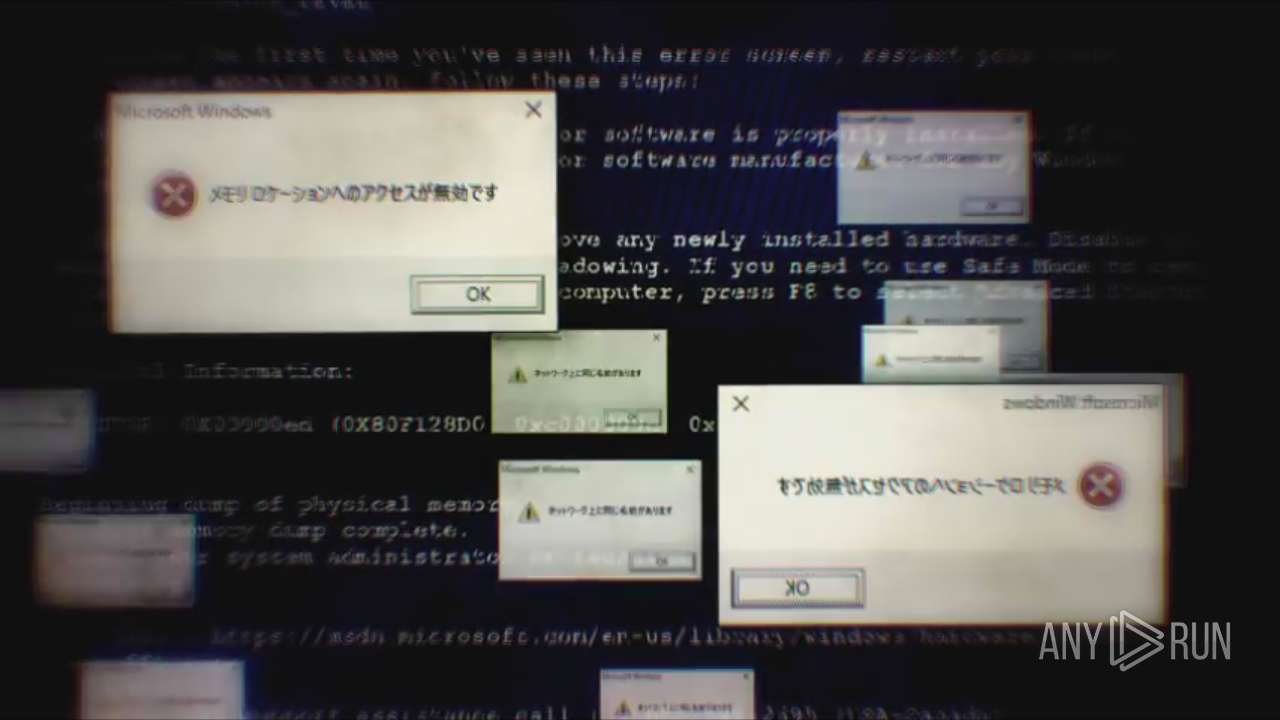
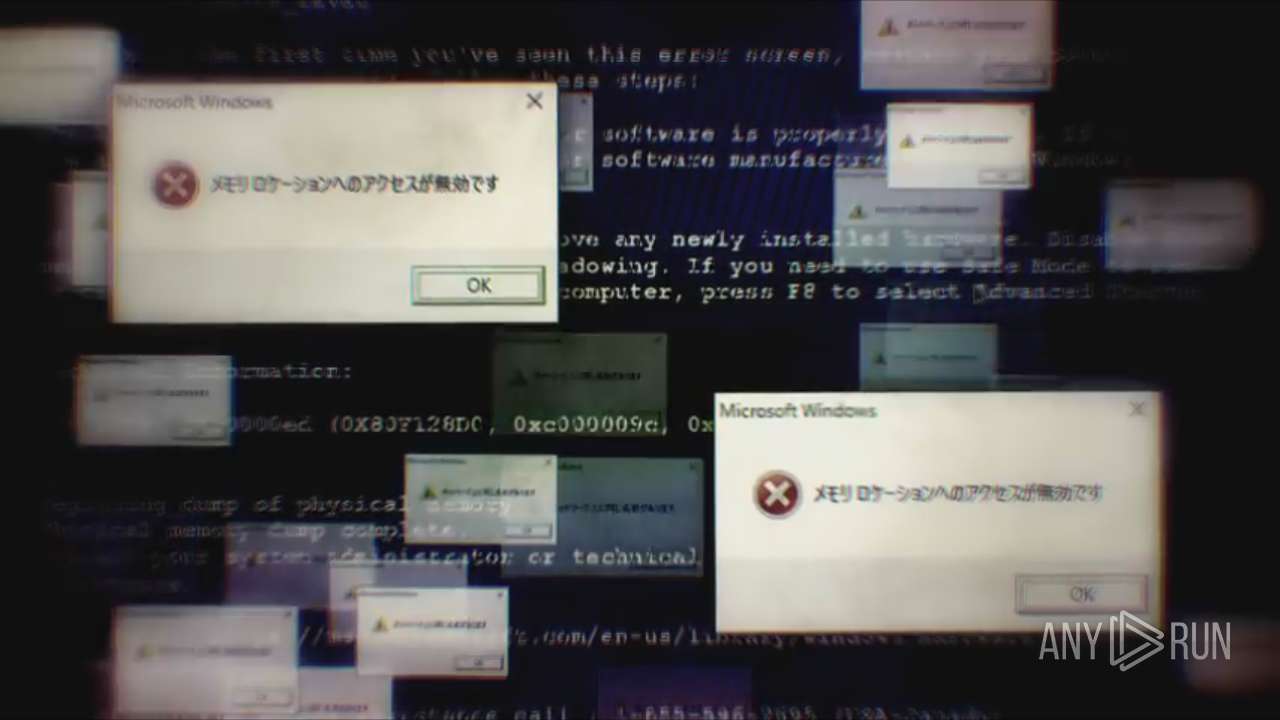
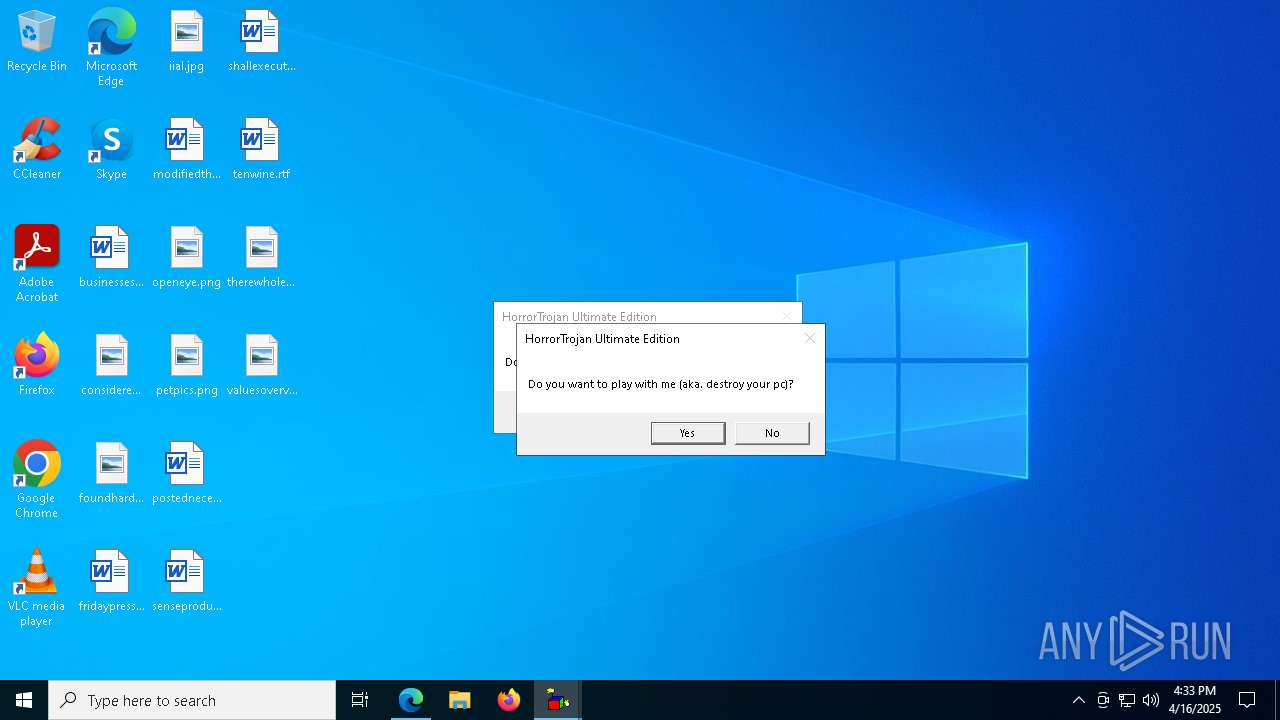
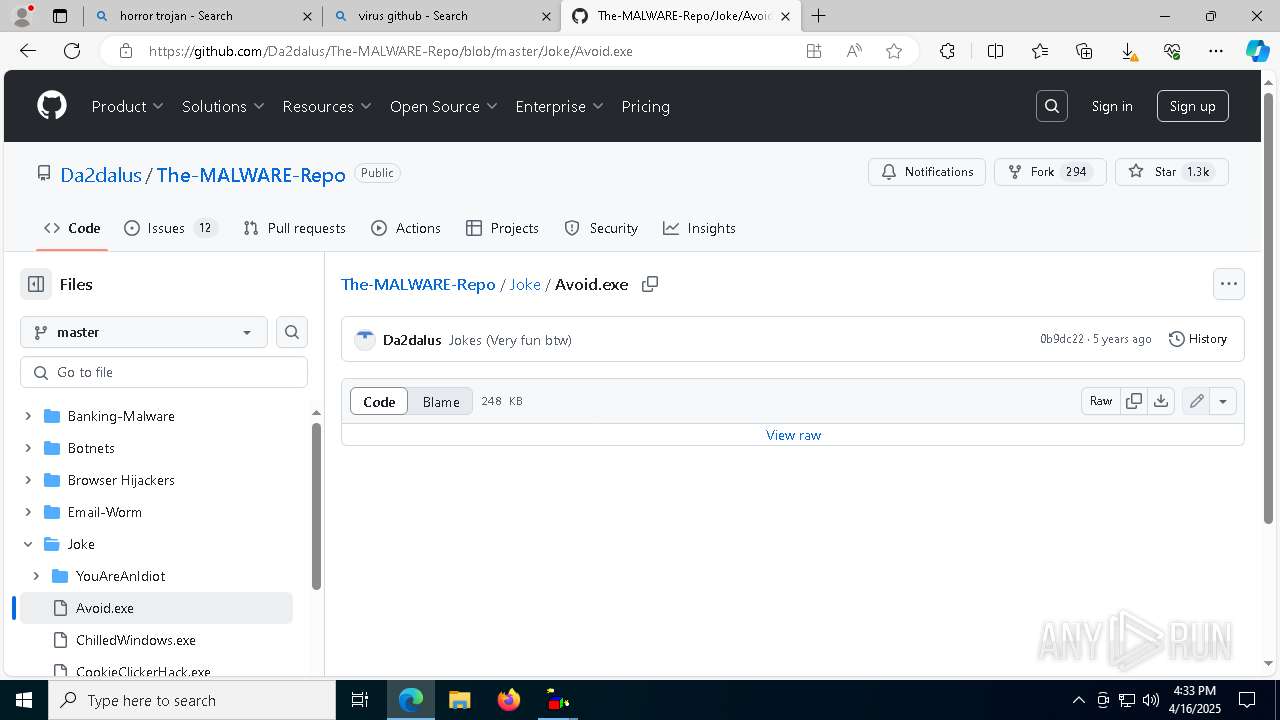
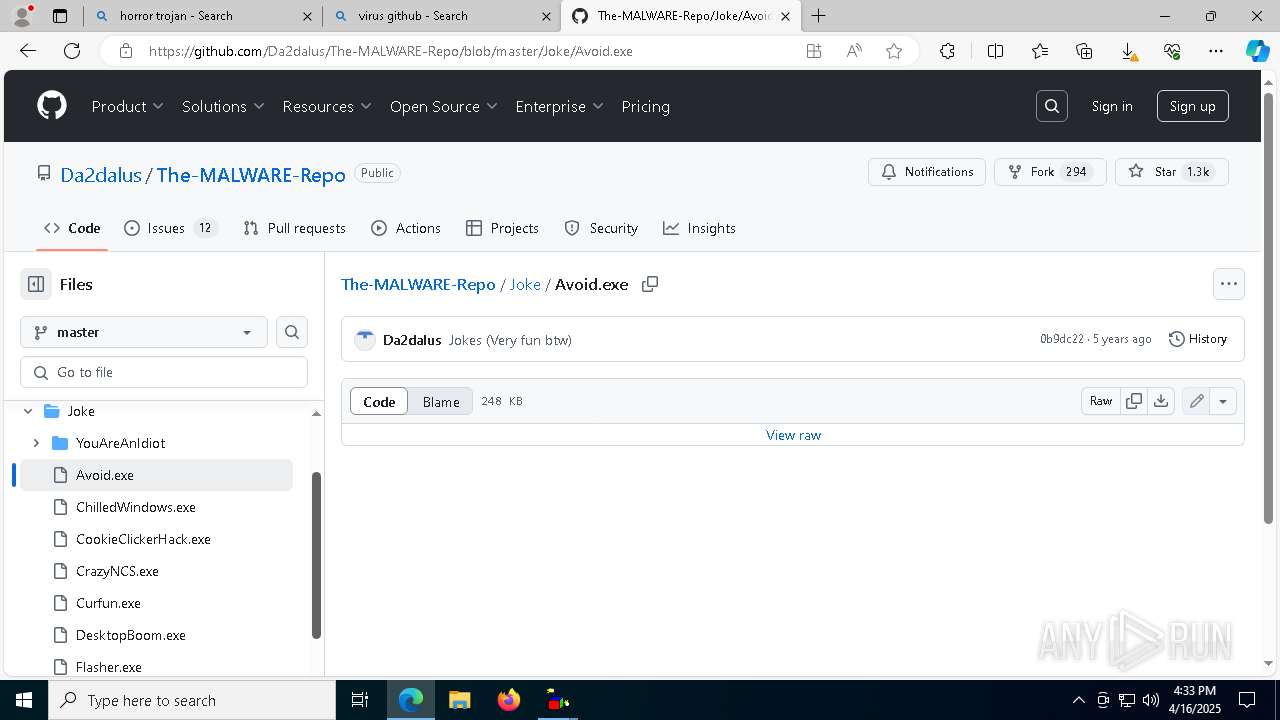
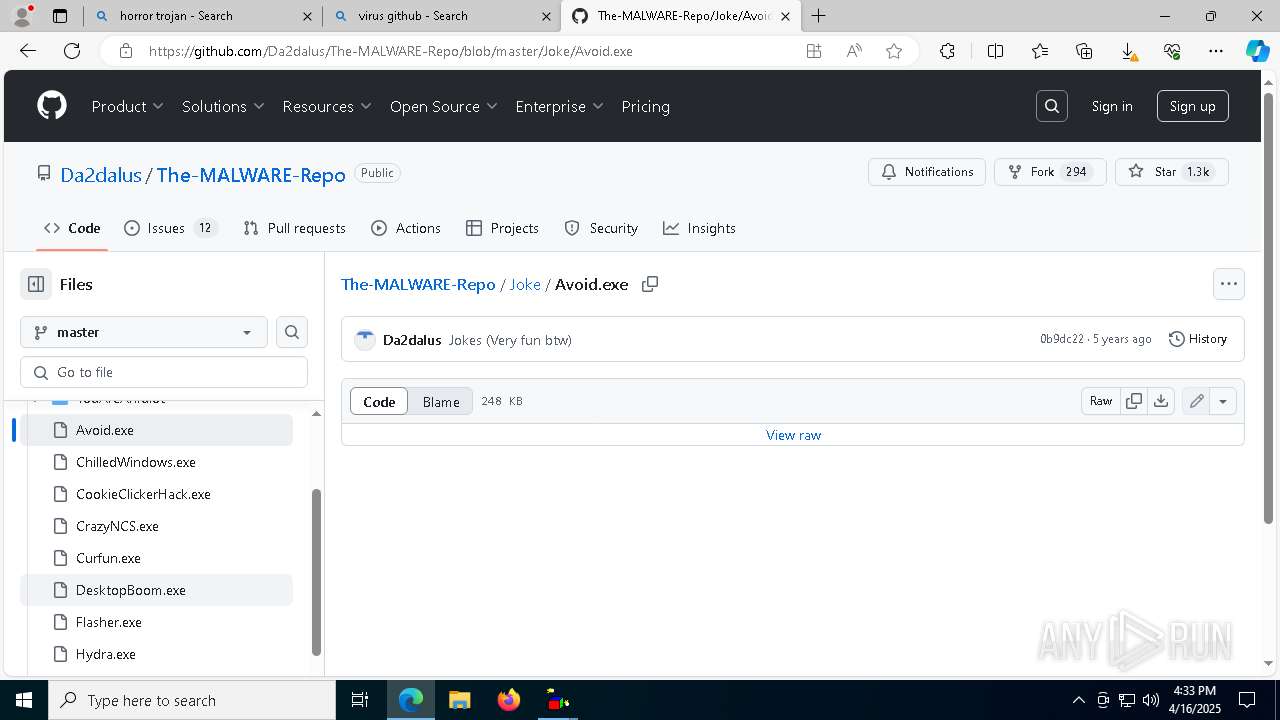
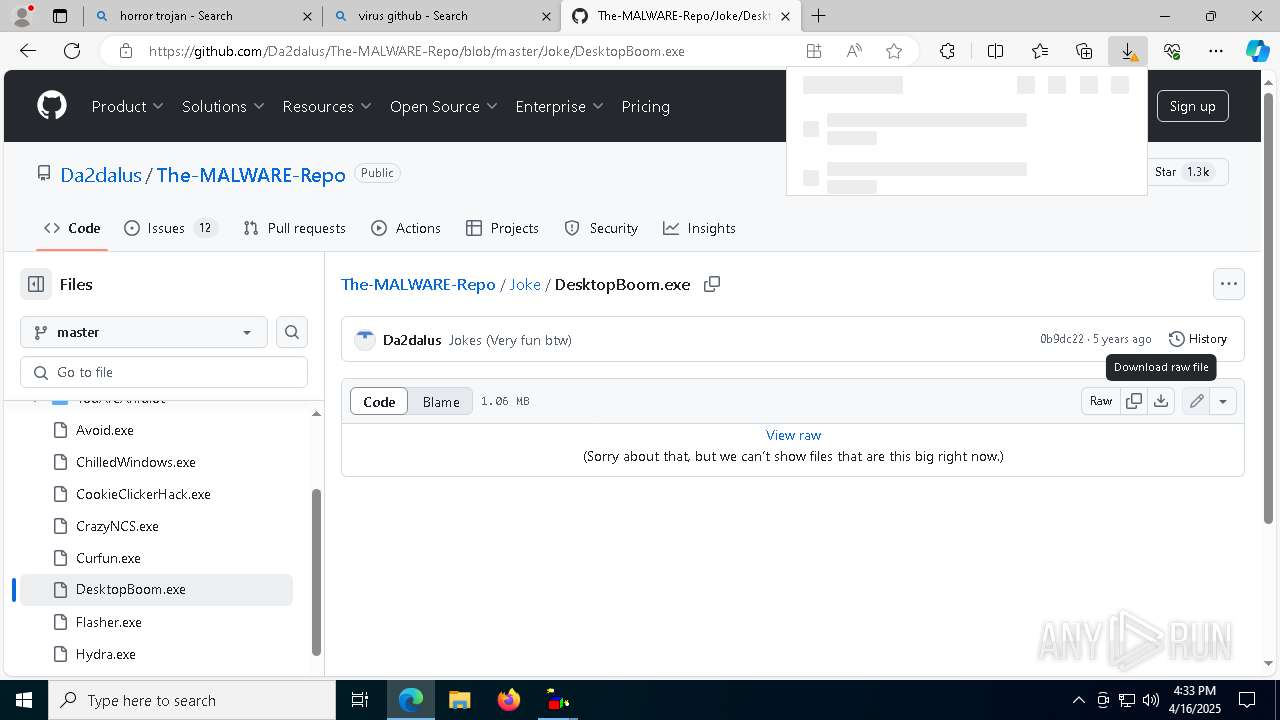
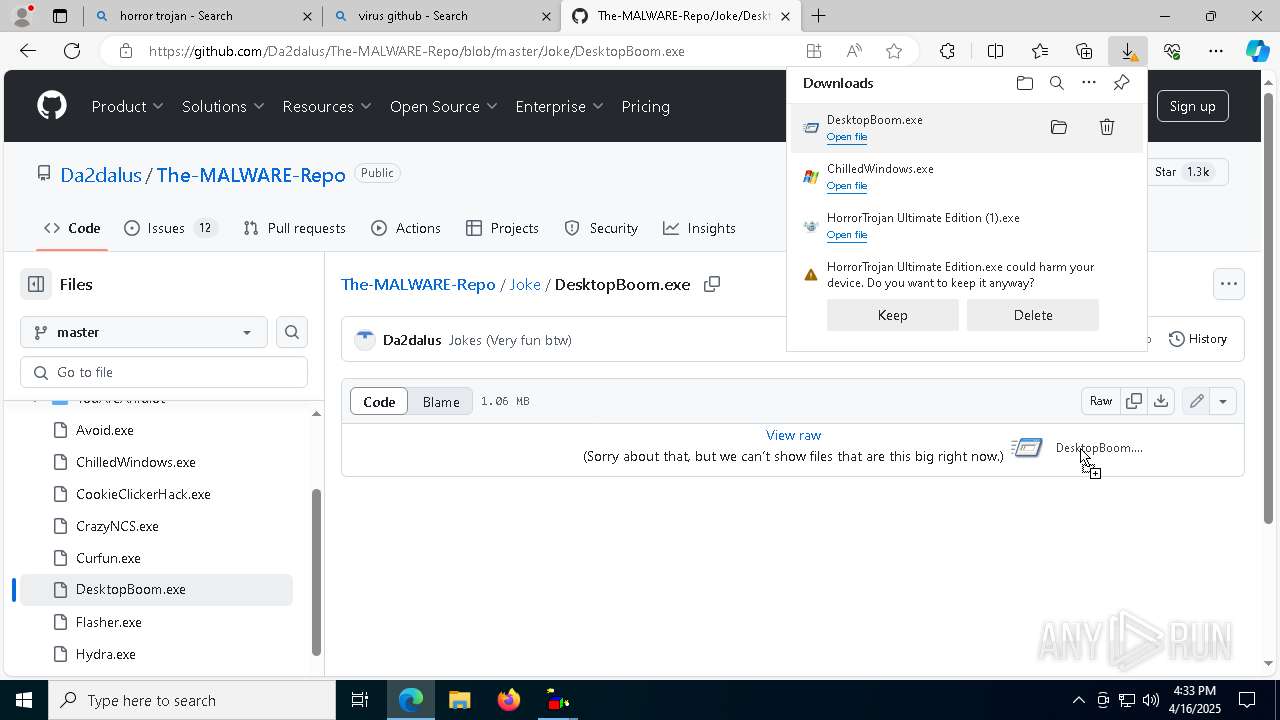
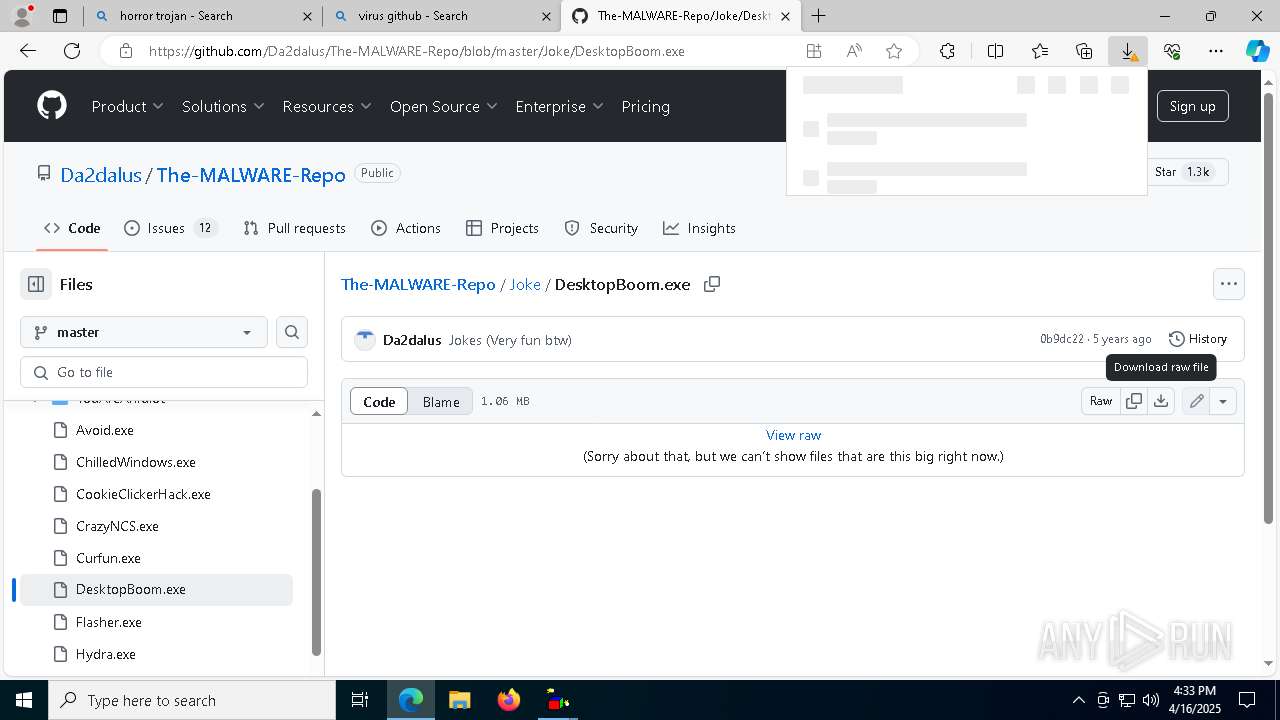
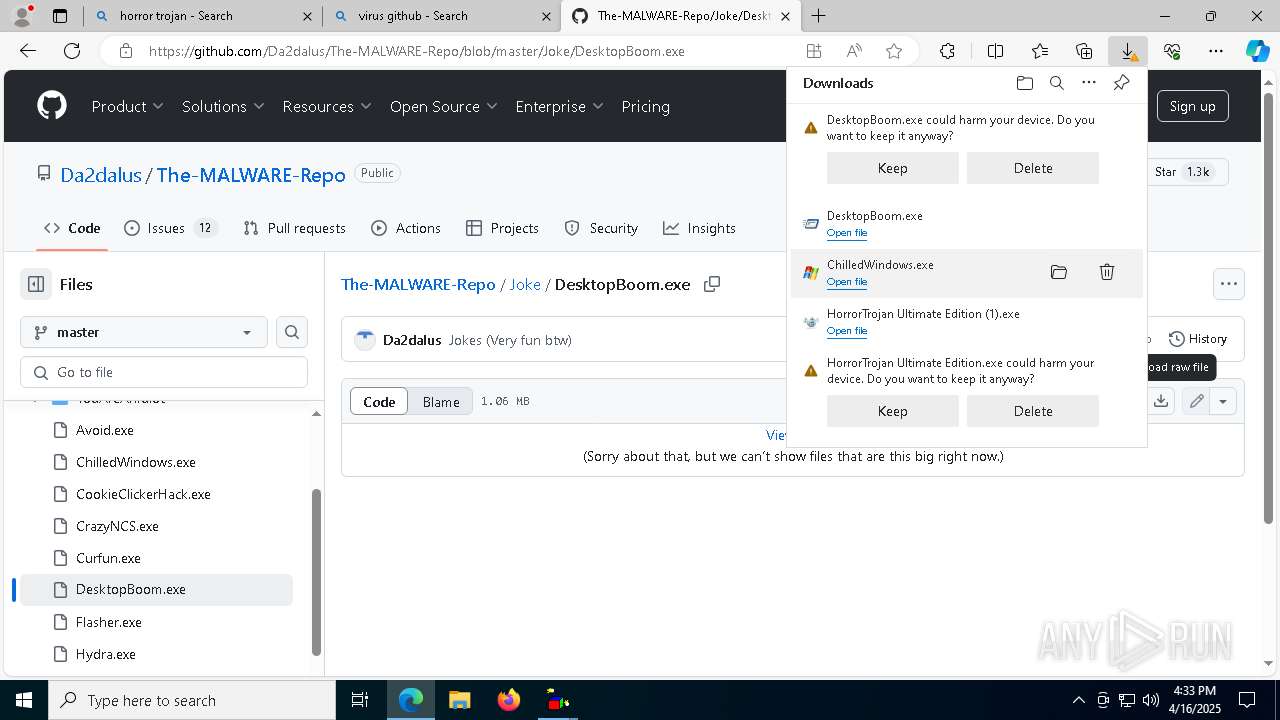
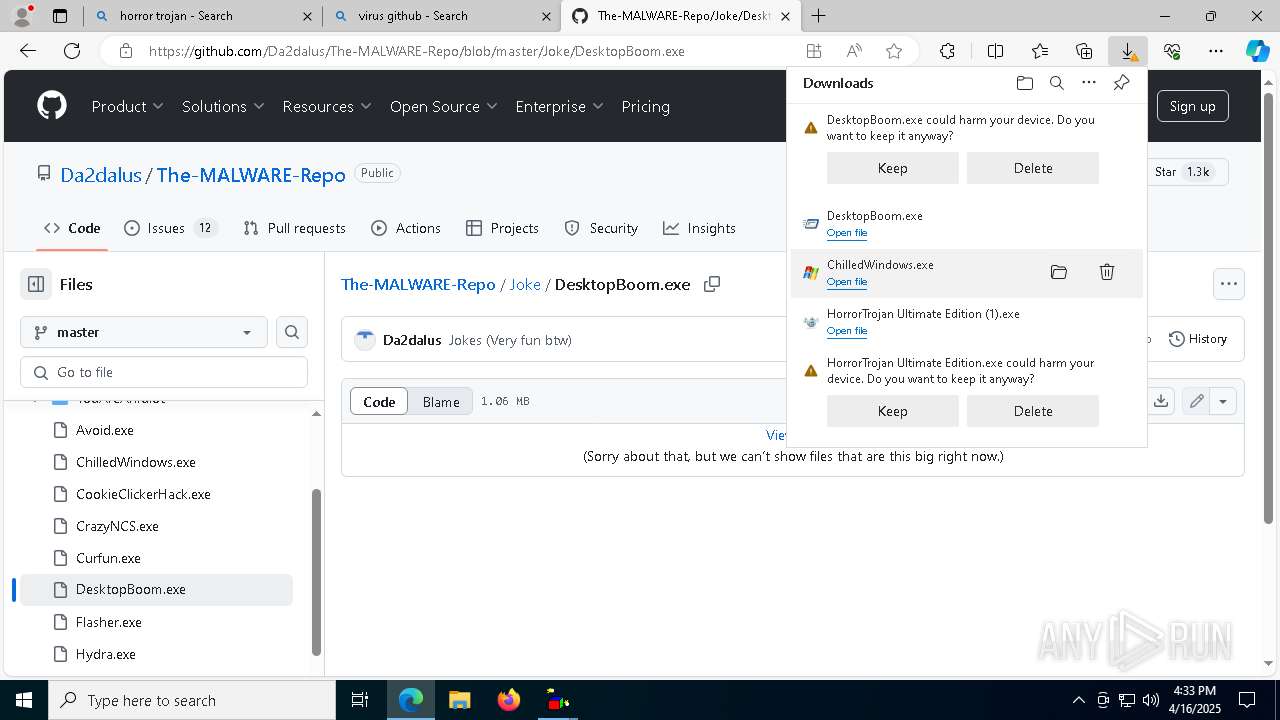
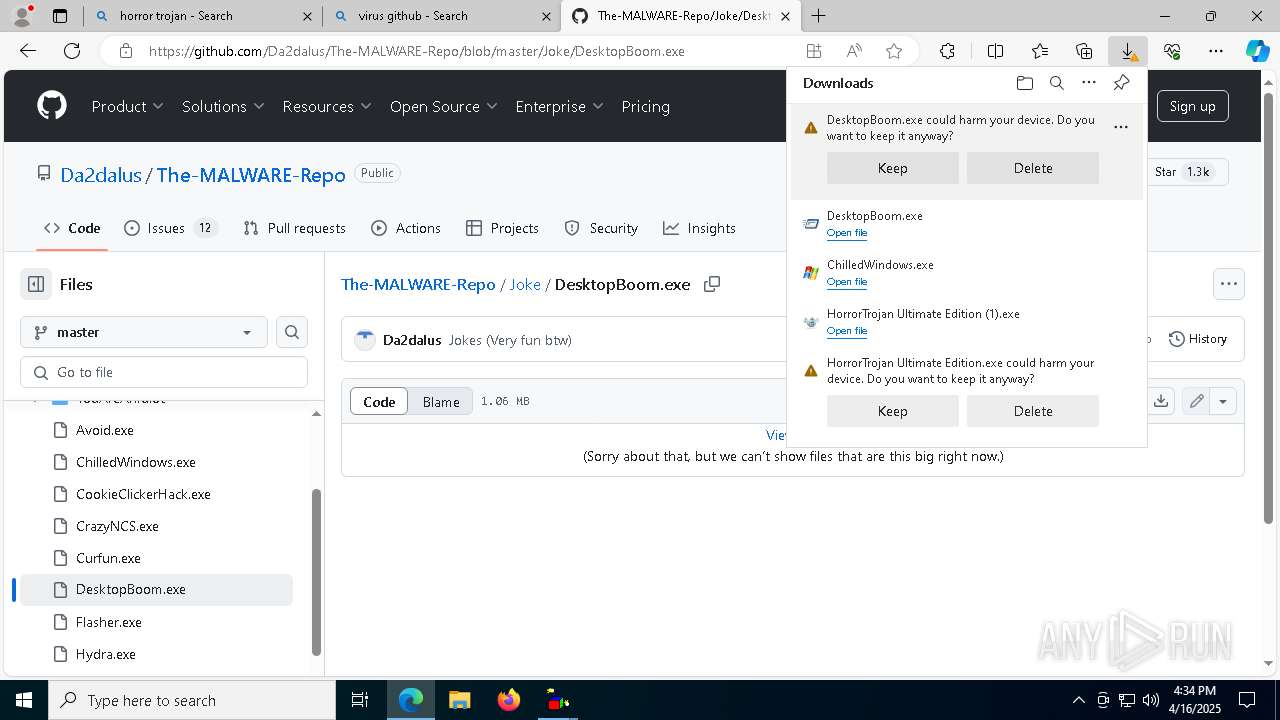
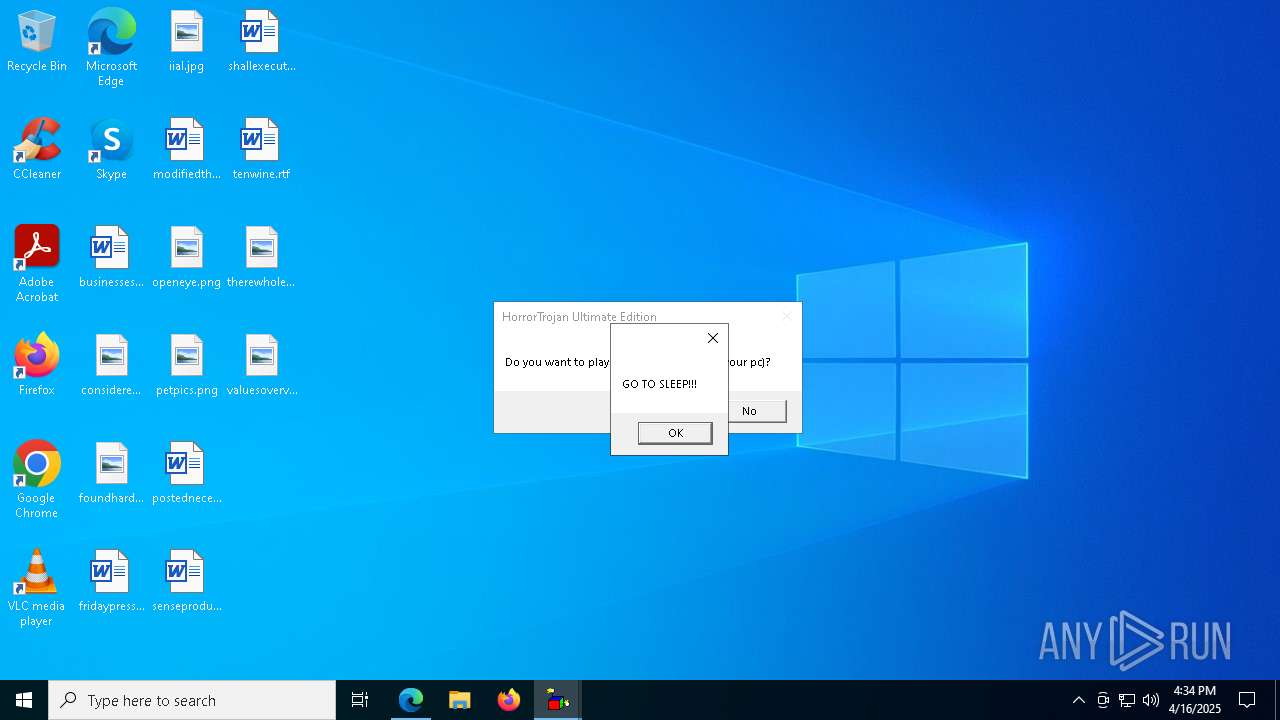
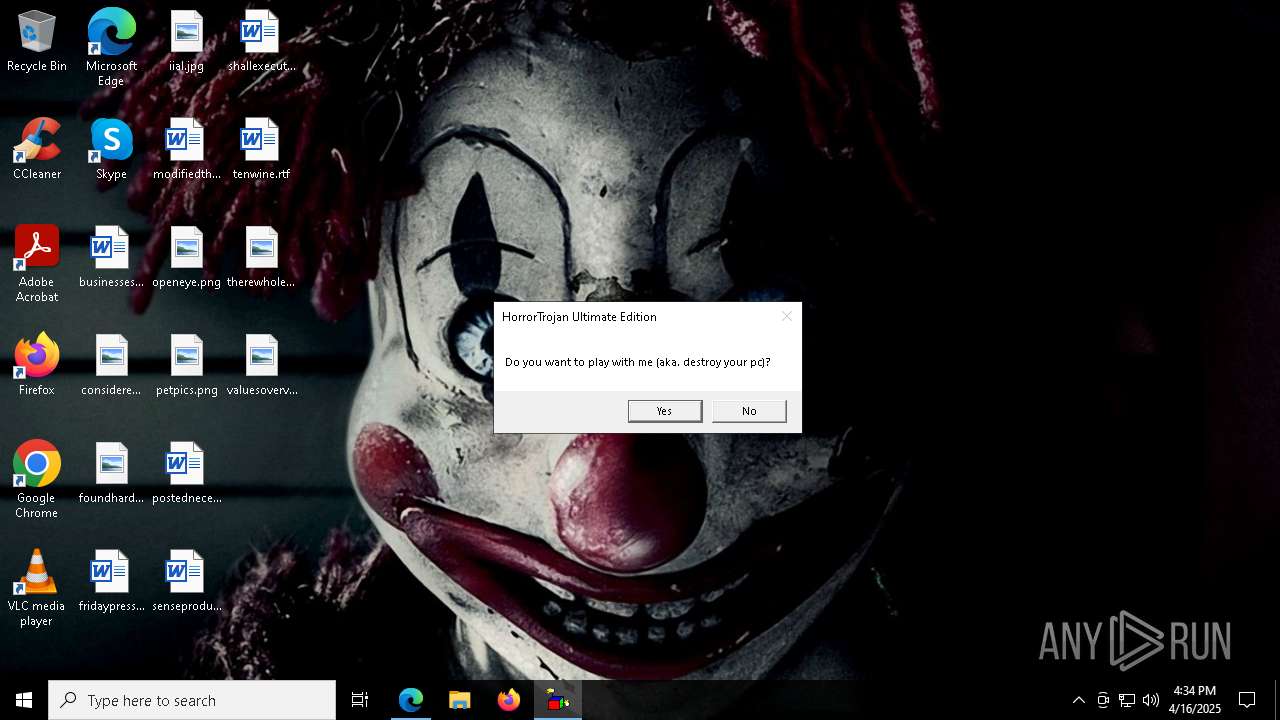
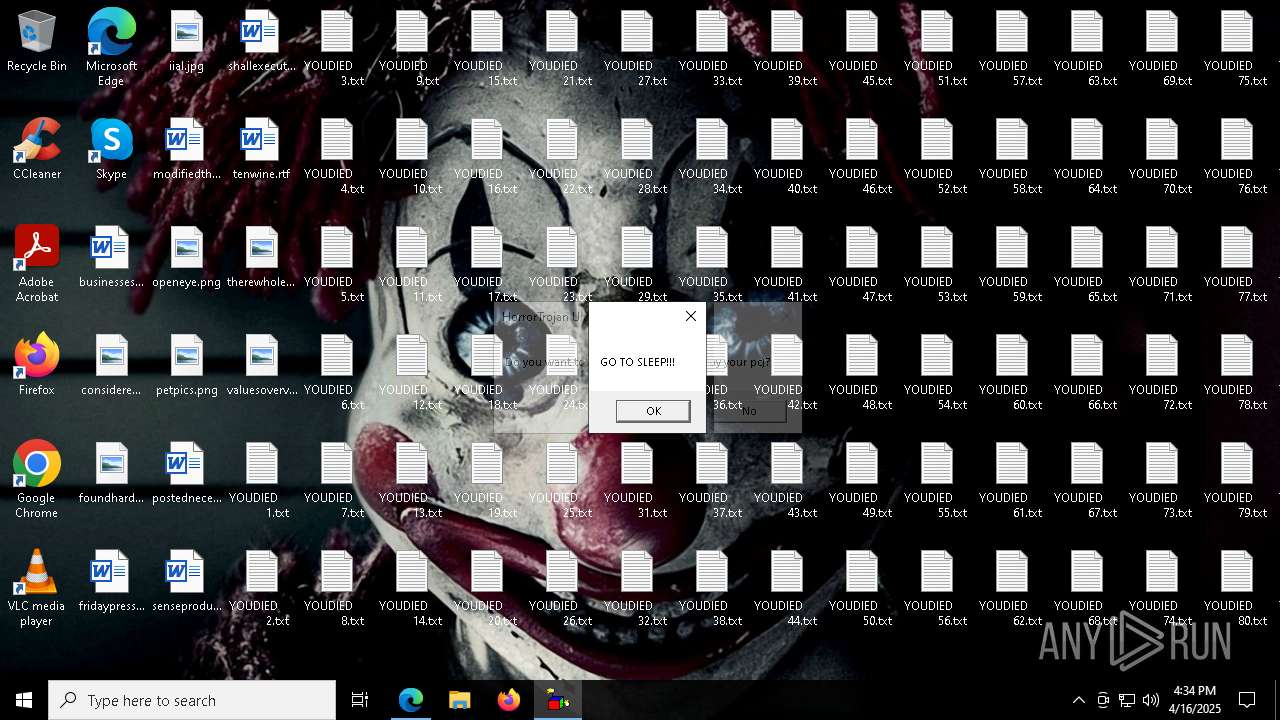
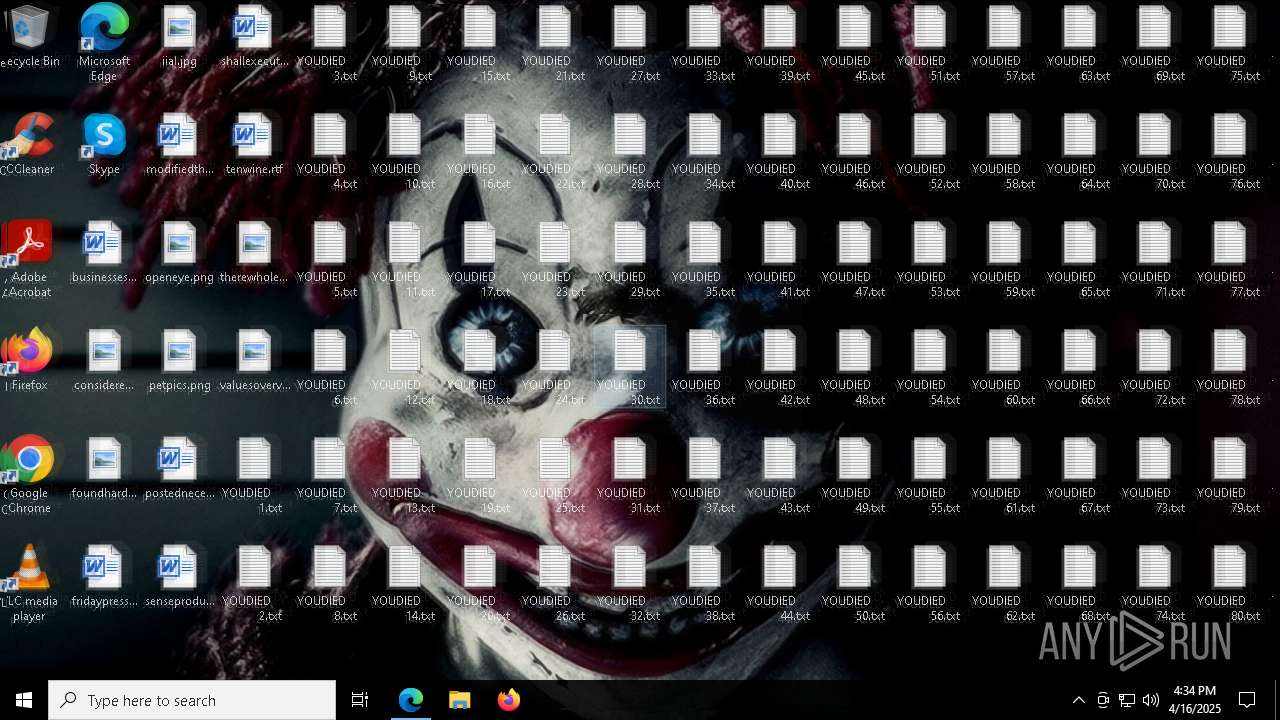
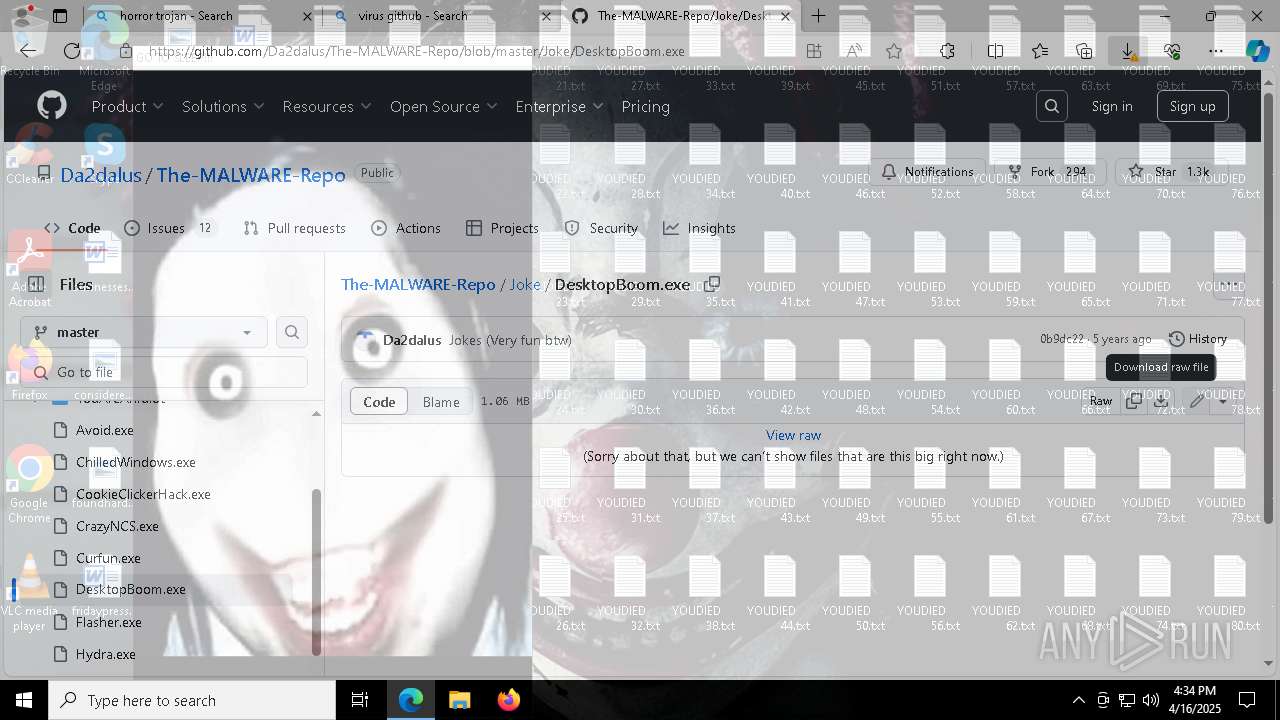
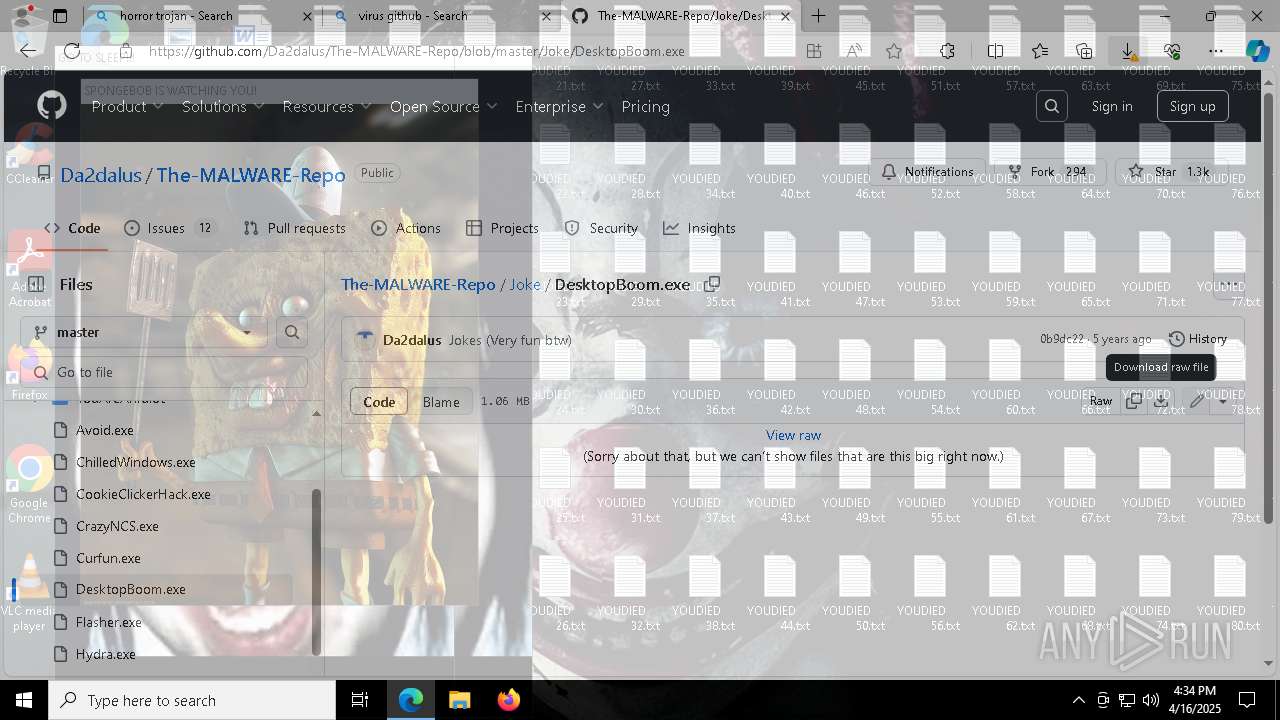
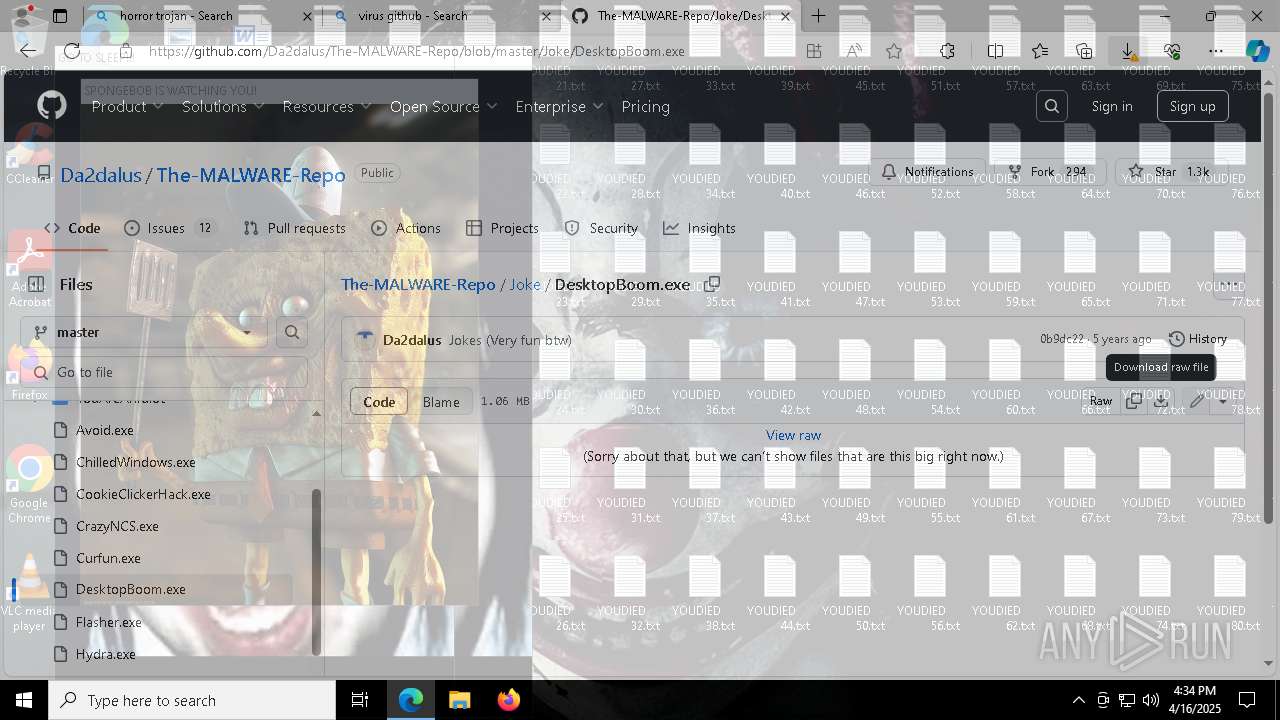
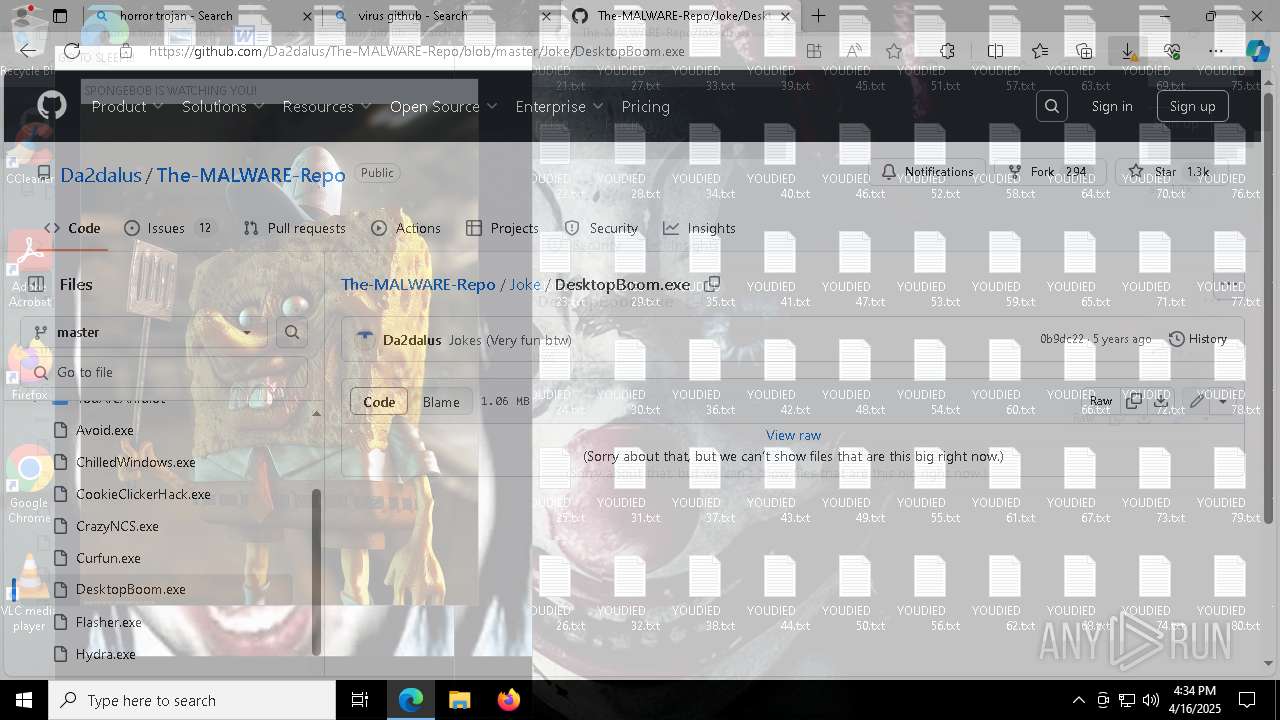
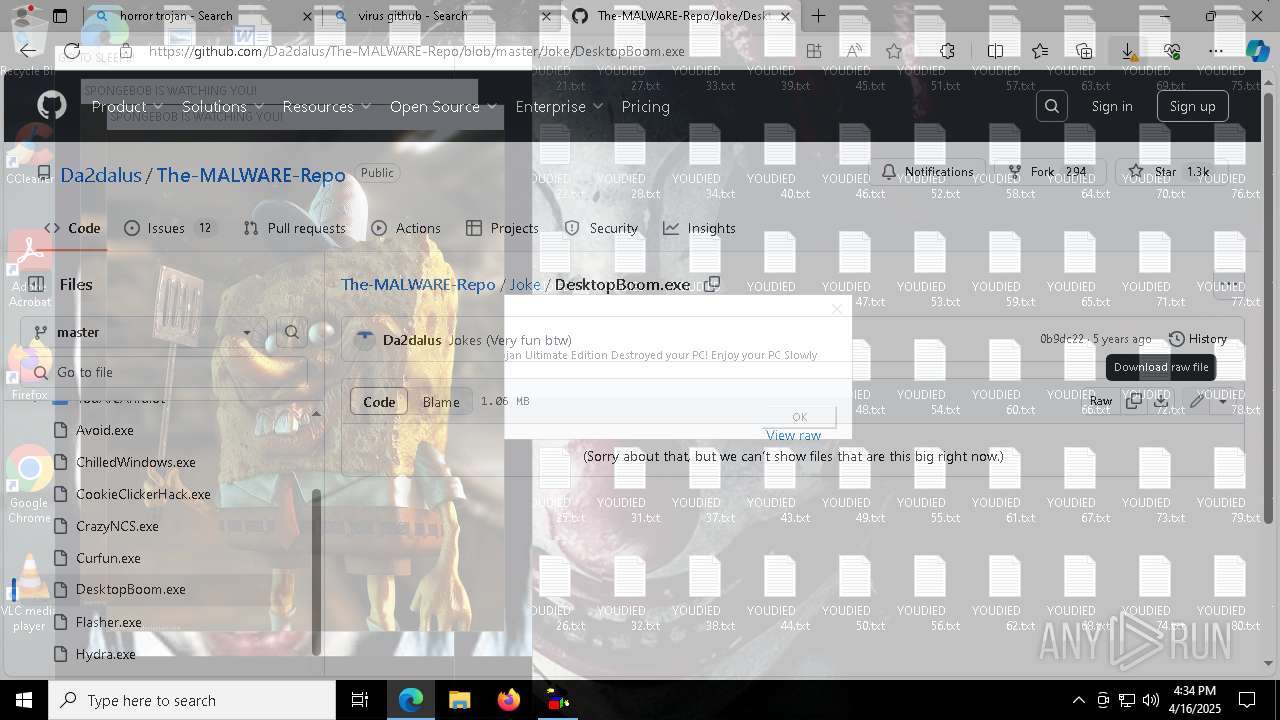
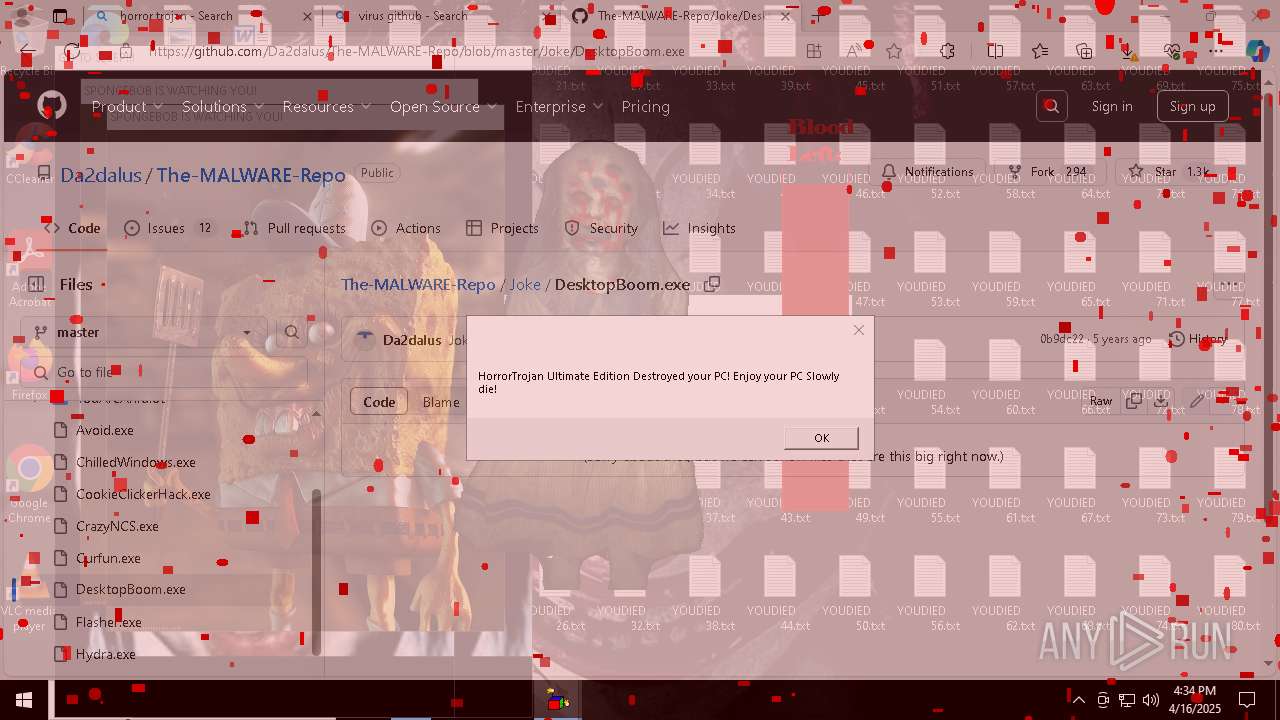
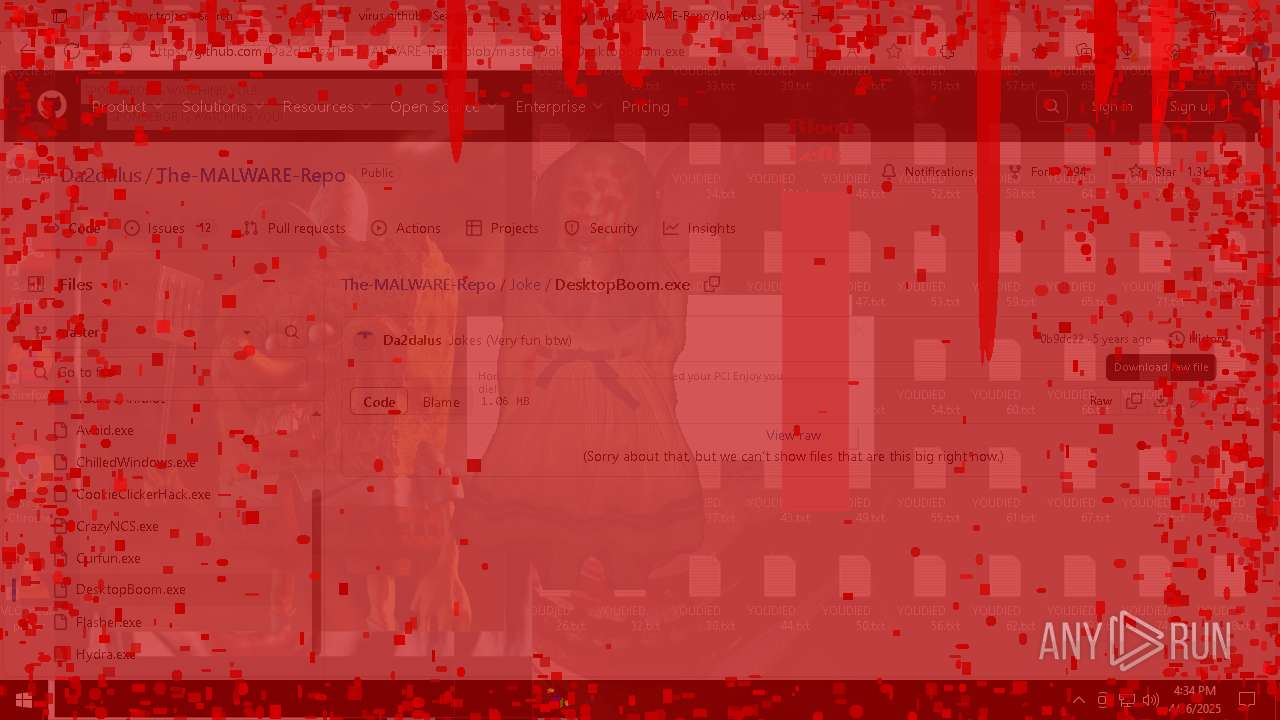
MALICIOUS
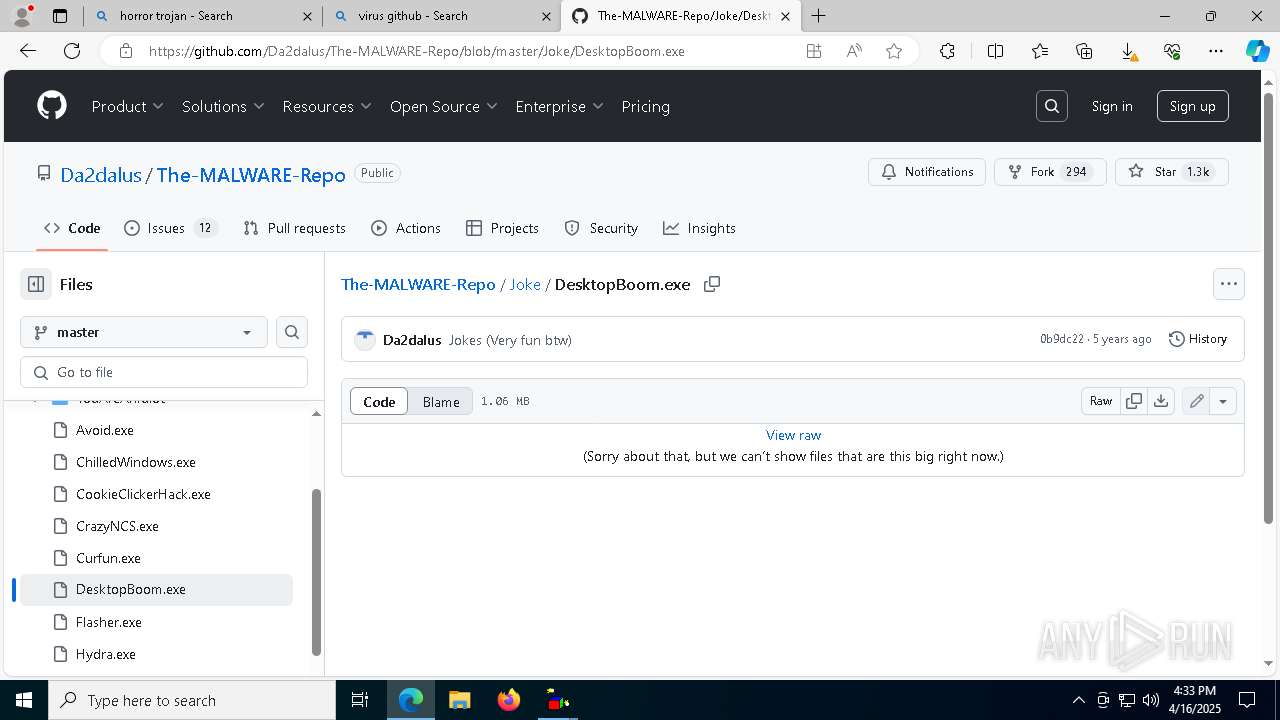
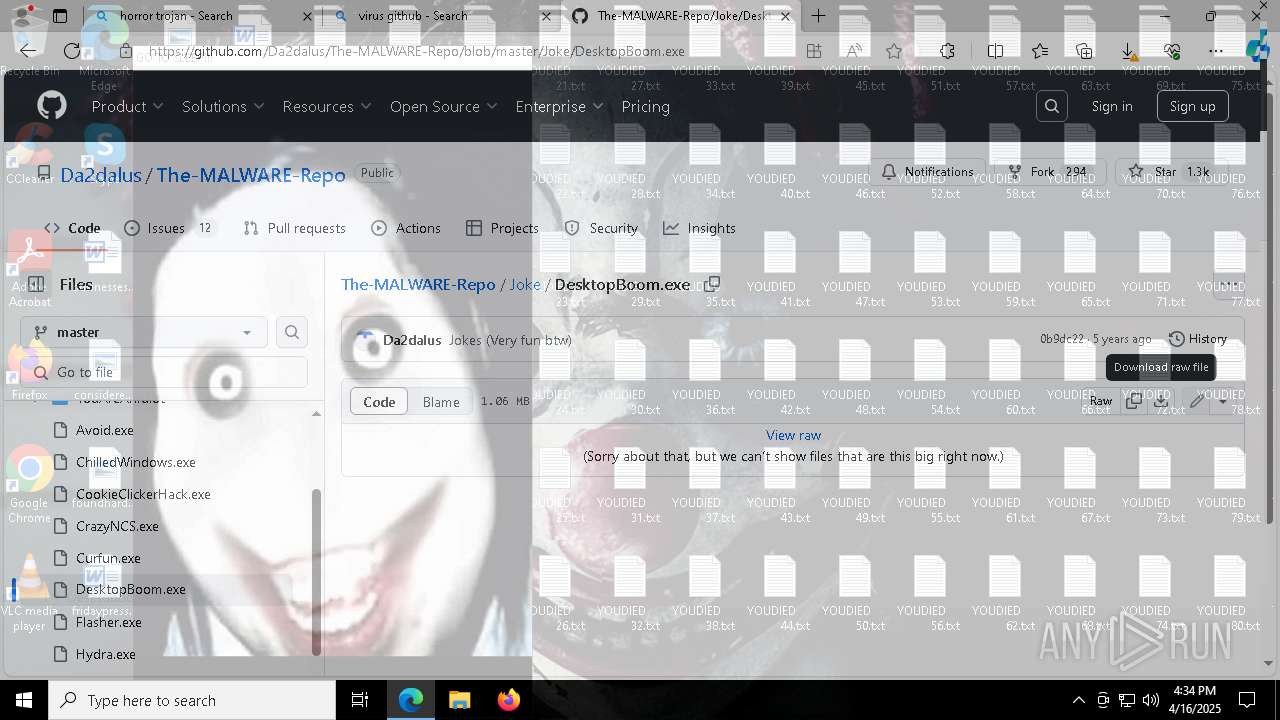
DESKTOPBOOM has been detected
- msedge.exe (PID: 7560)
- msedge.exe (PID: 7264)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
Disables task manager
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
Disables the Run the Start menu
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
Disables Windows Defender
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
Task Manager has been disabled (taskmgr)
- gdifuncs.exe (PID: 4028)
- gdifuncs.exe (PID: 4844)
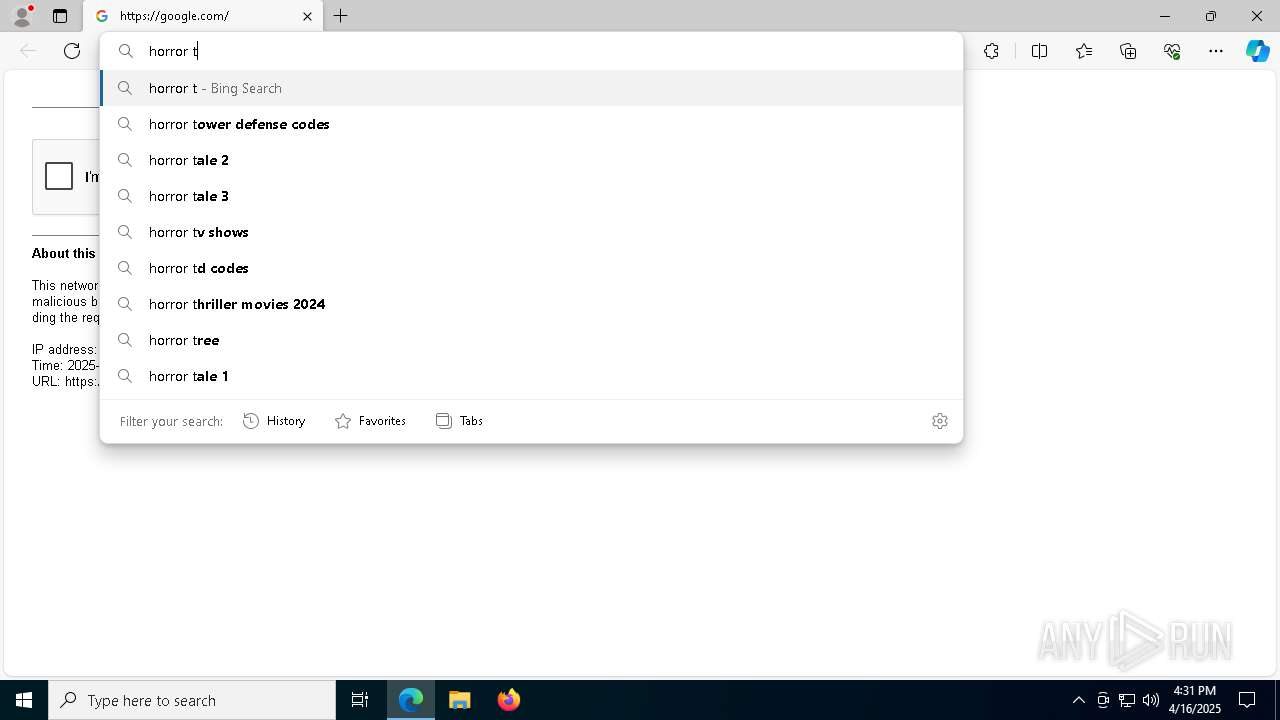
SUSPICIOUS
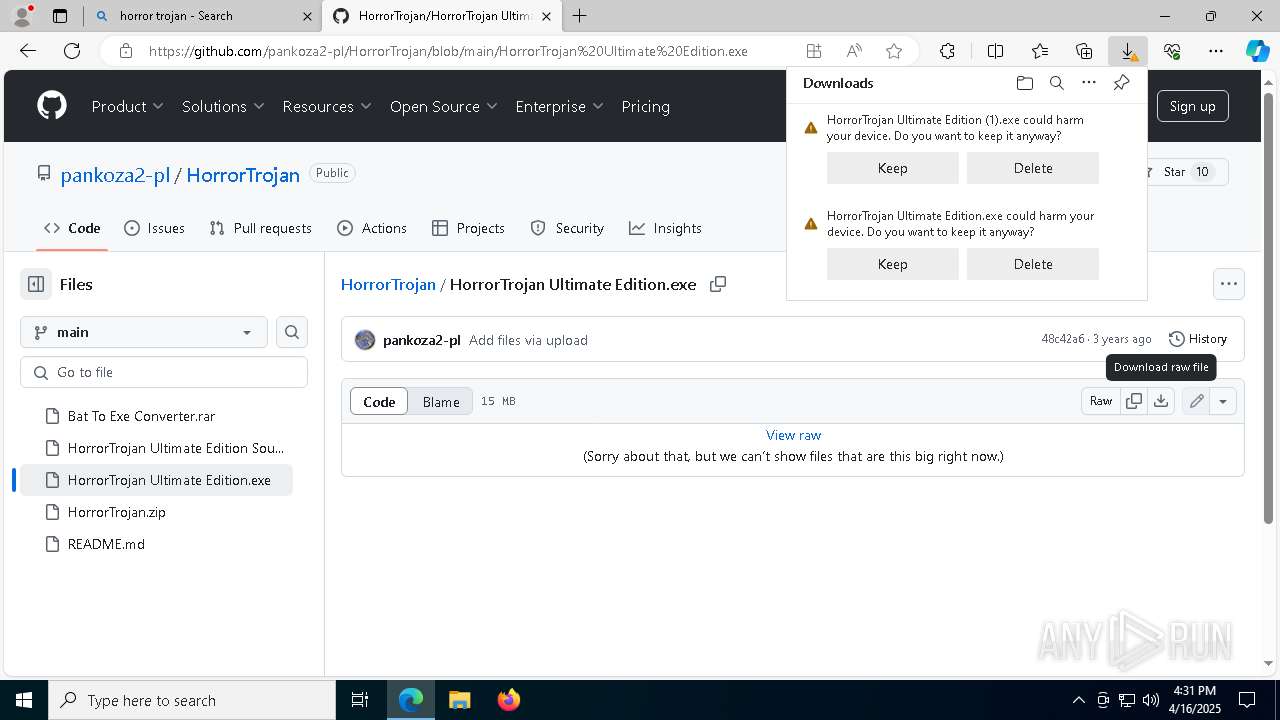
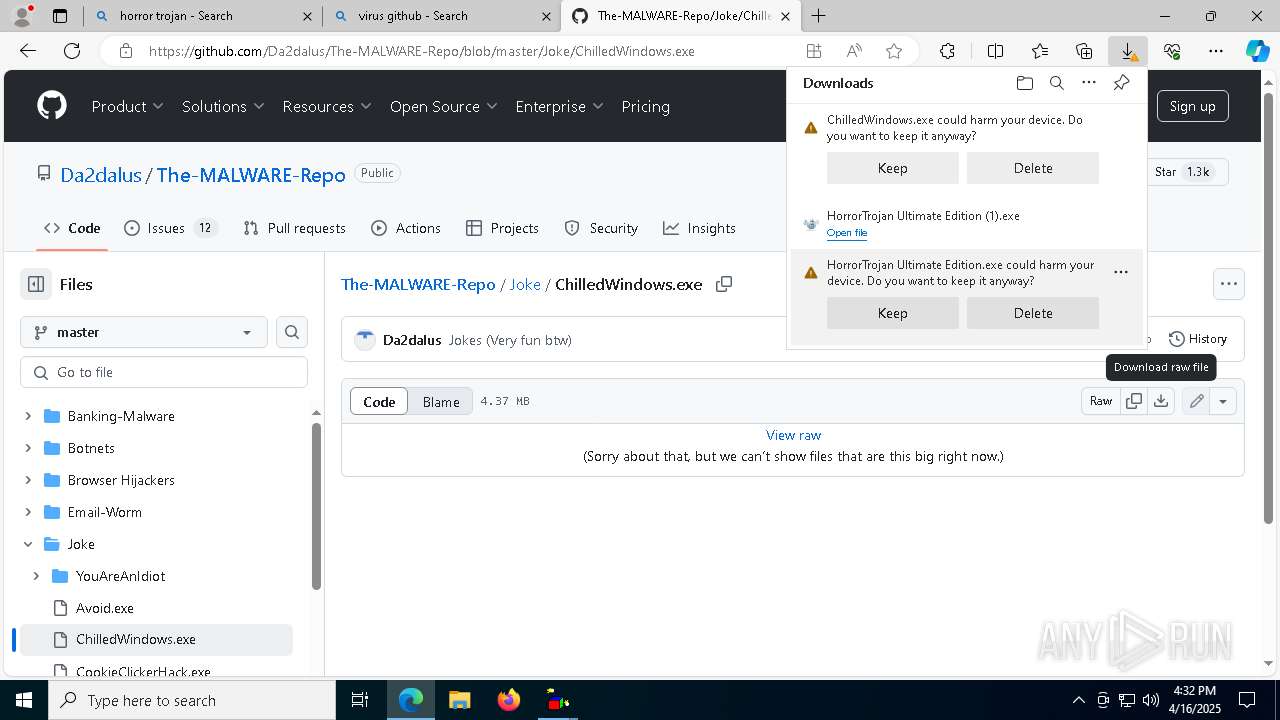
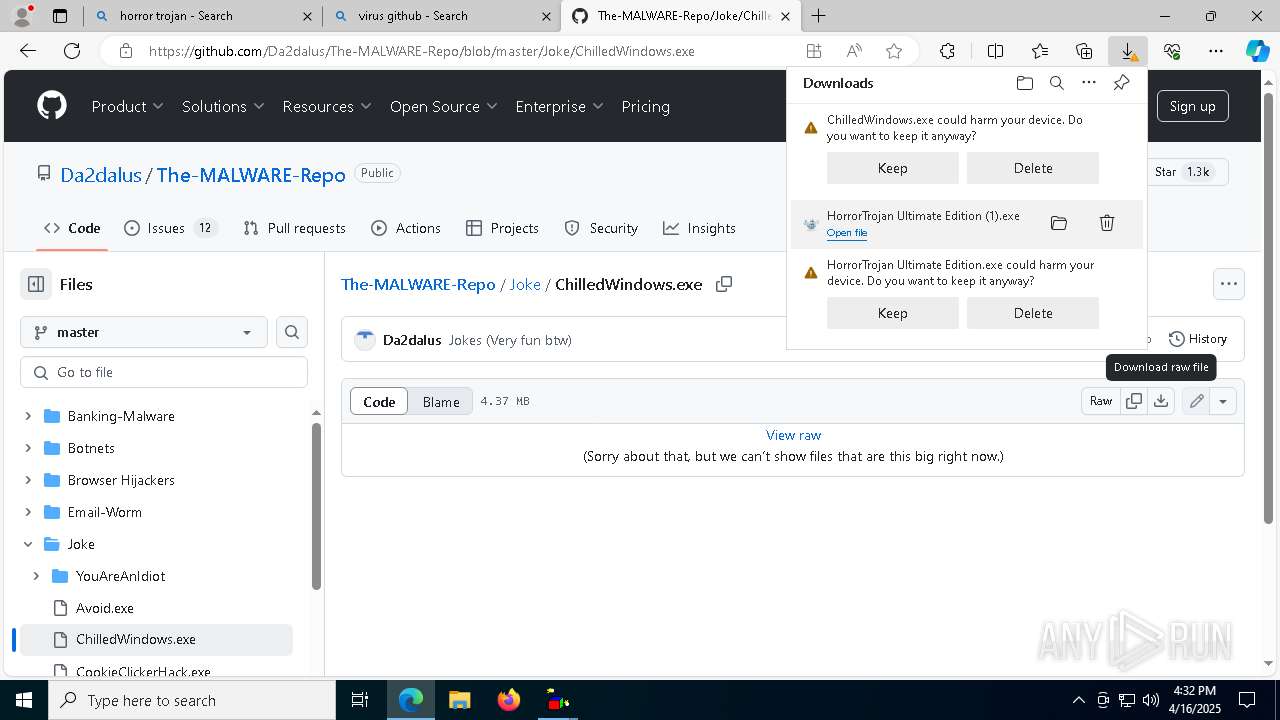
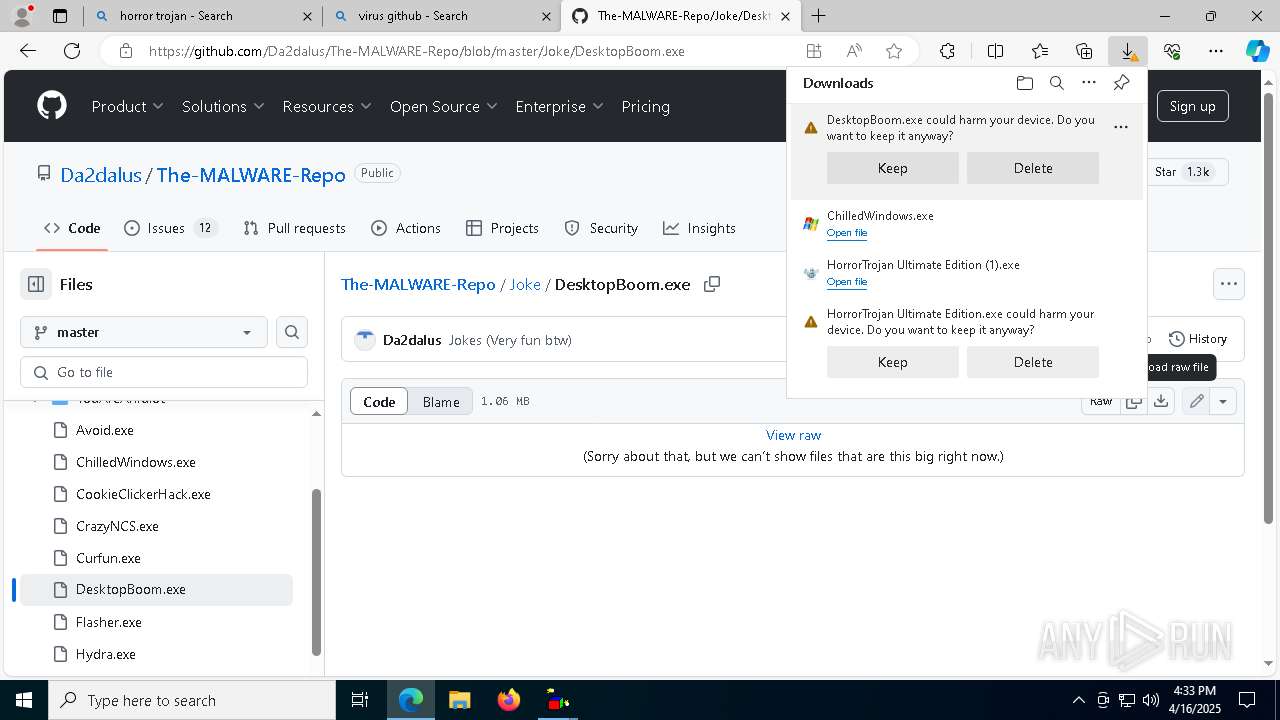
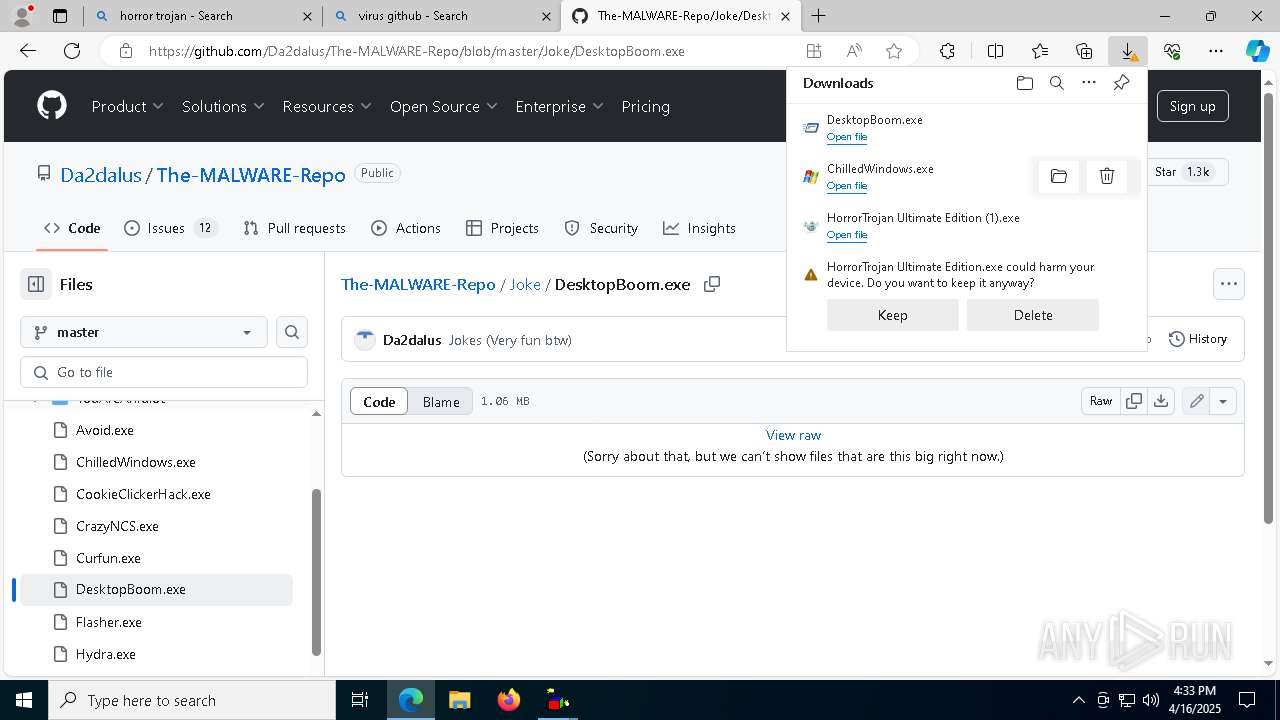
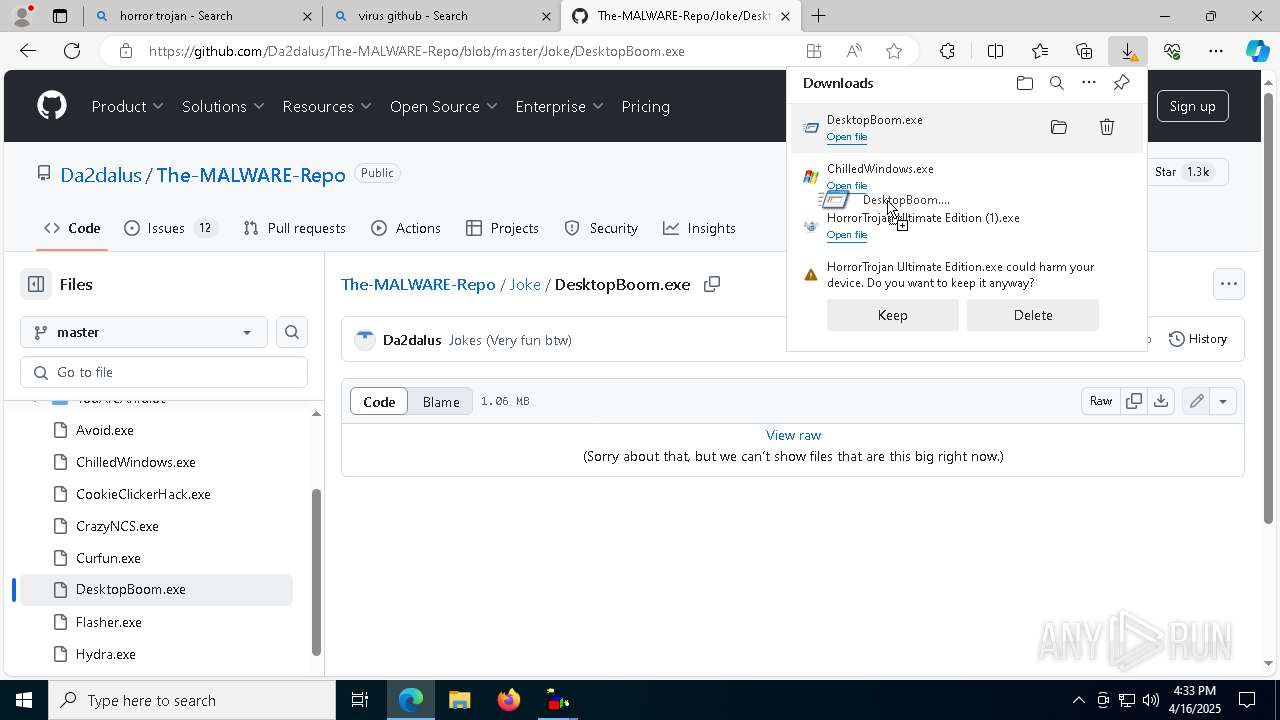
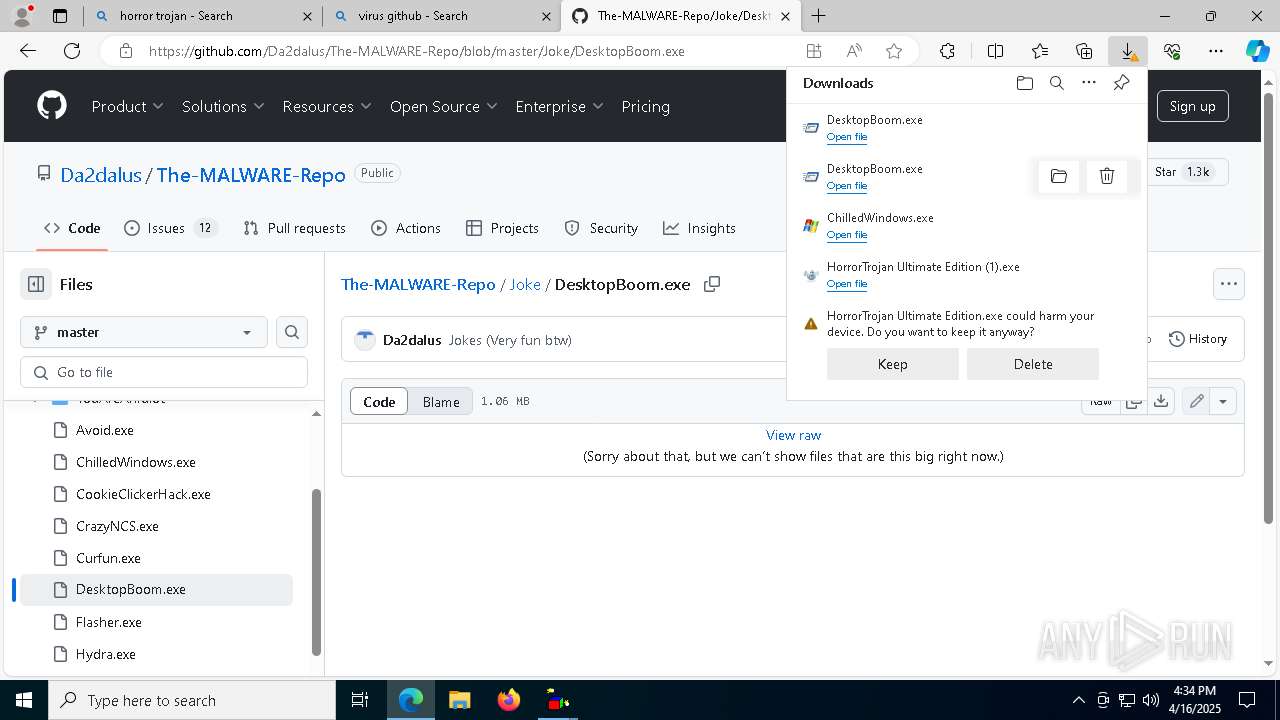
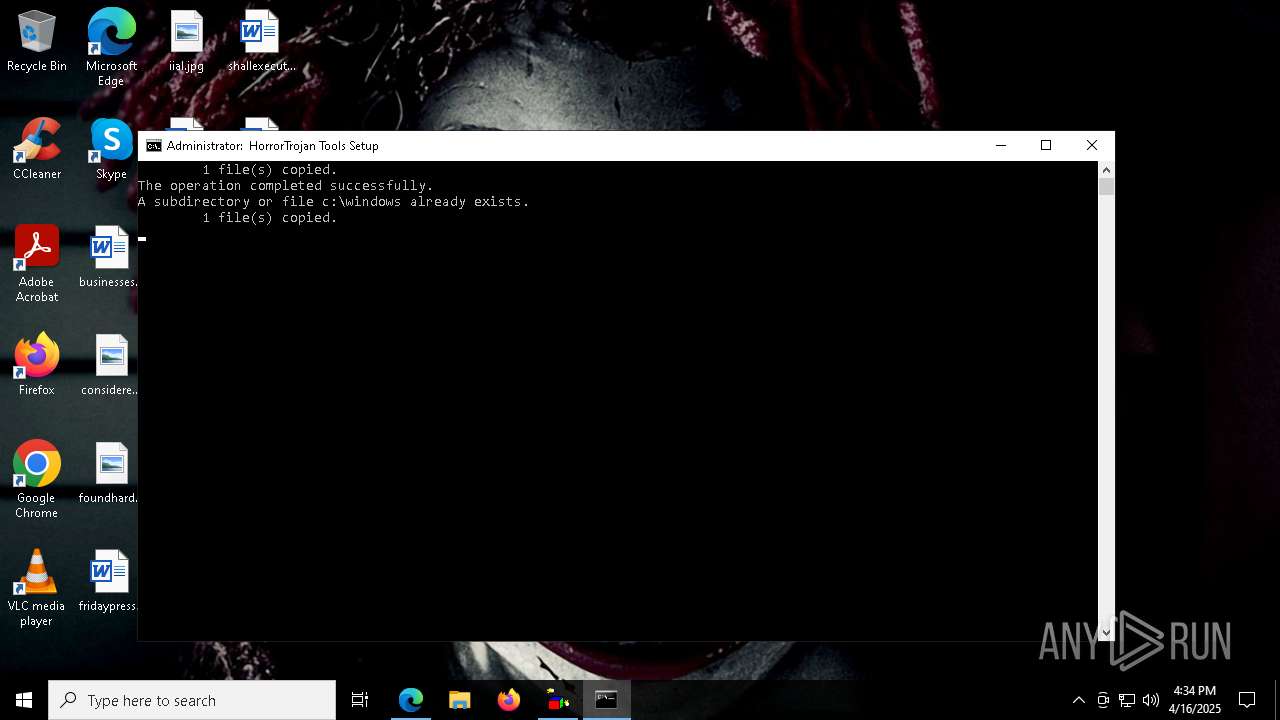
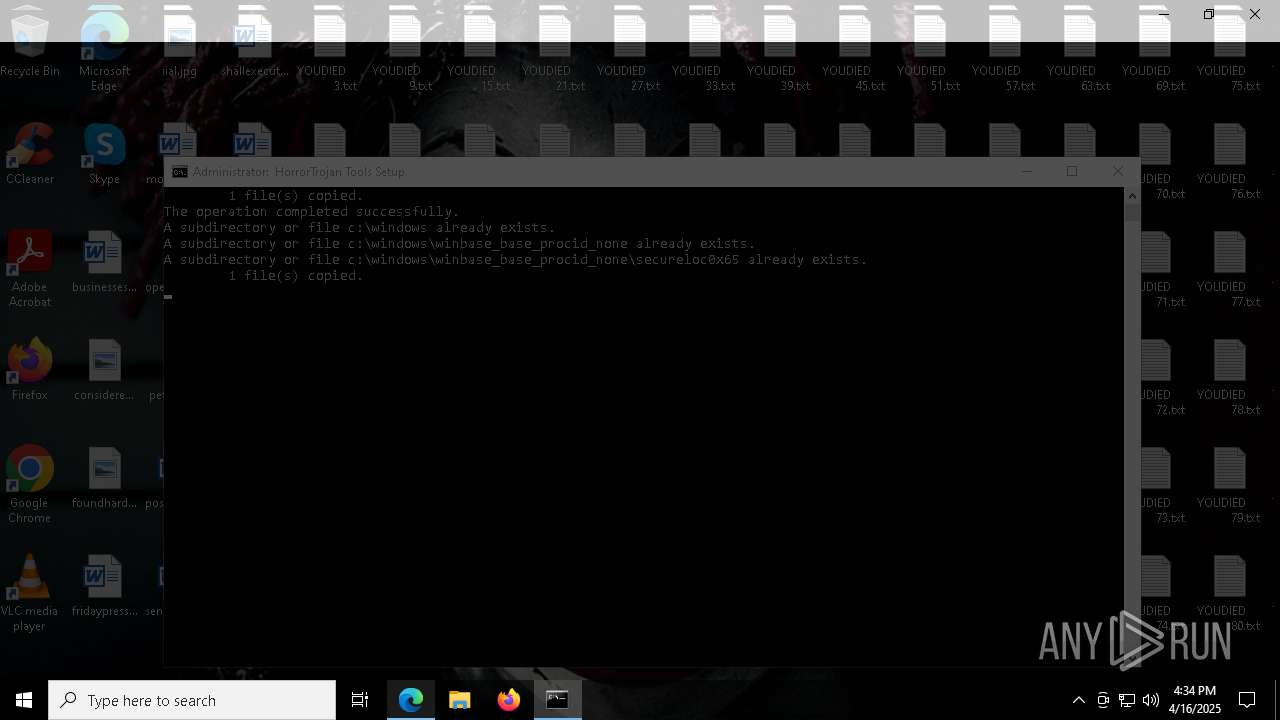
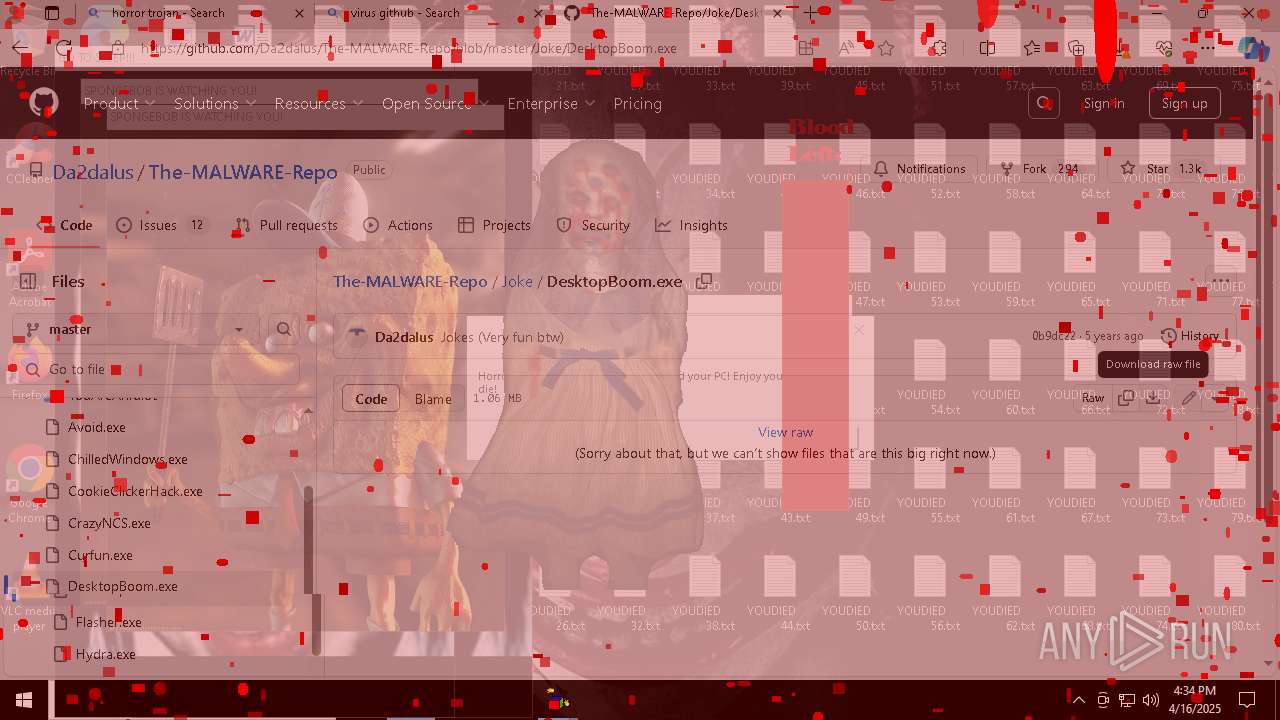
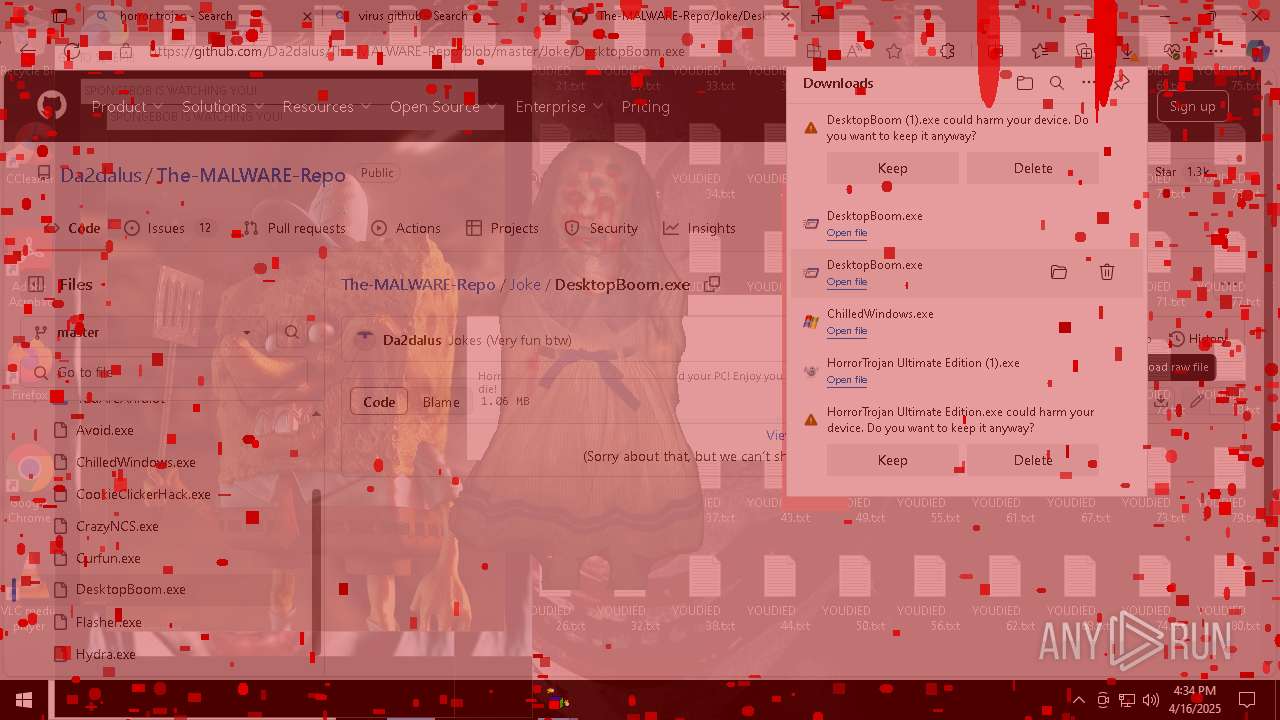
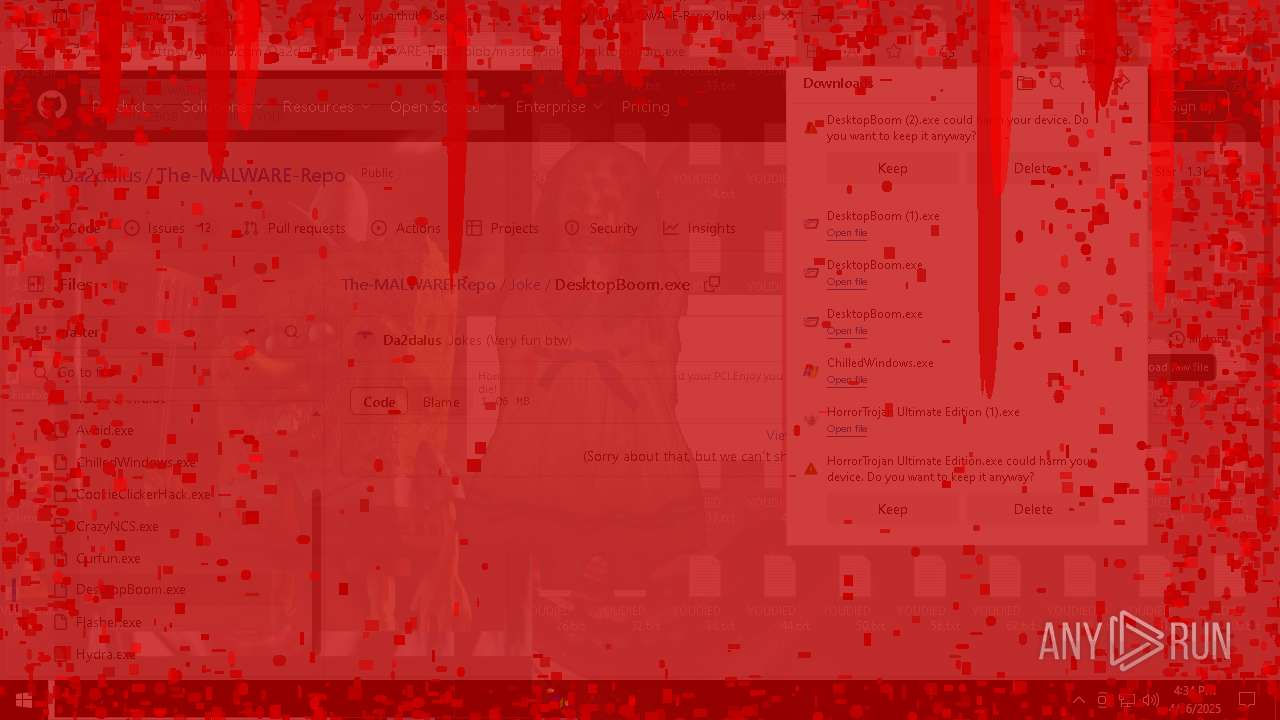
Executable content was dropped or overwritten
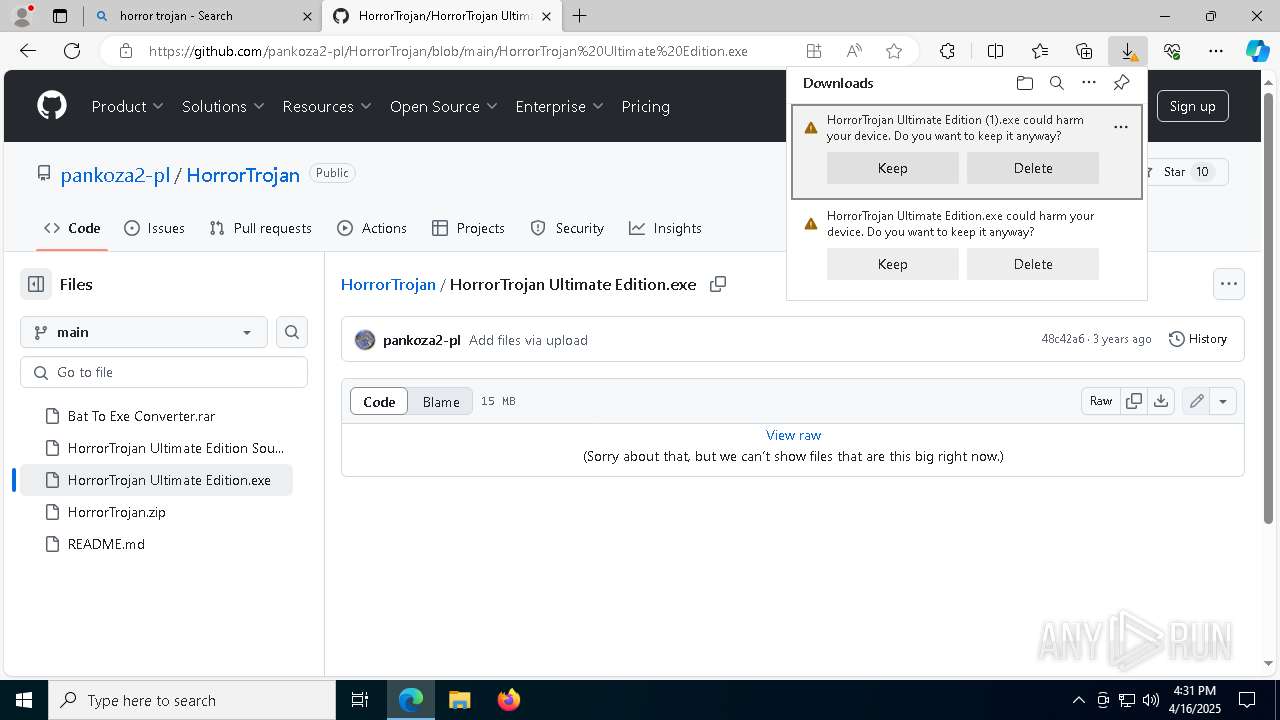
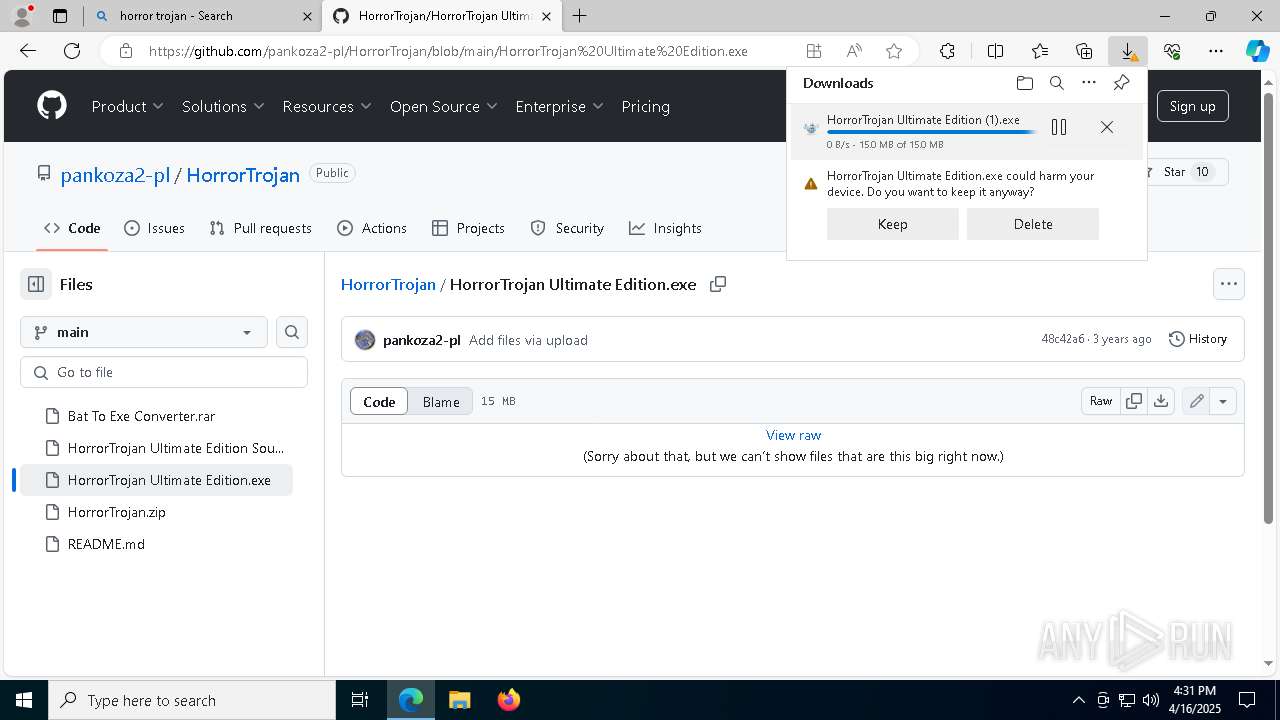
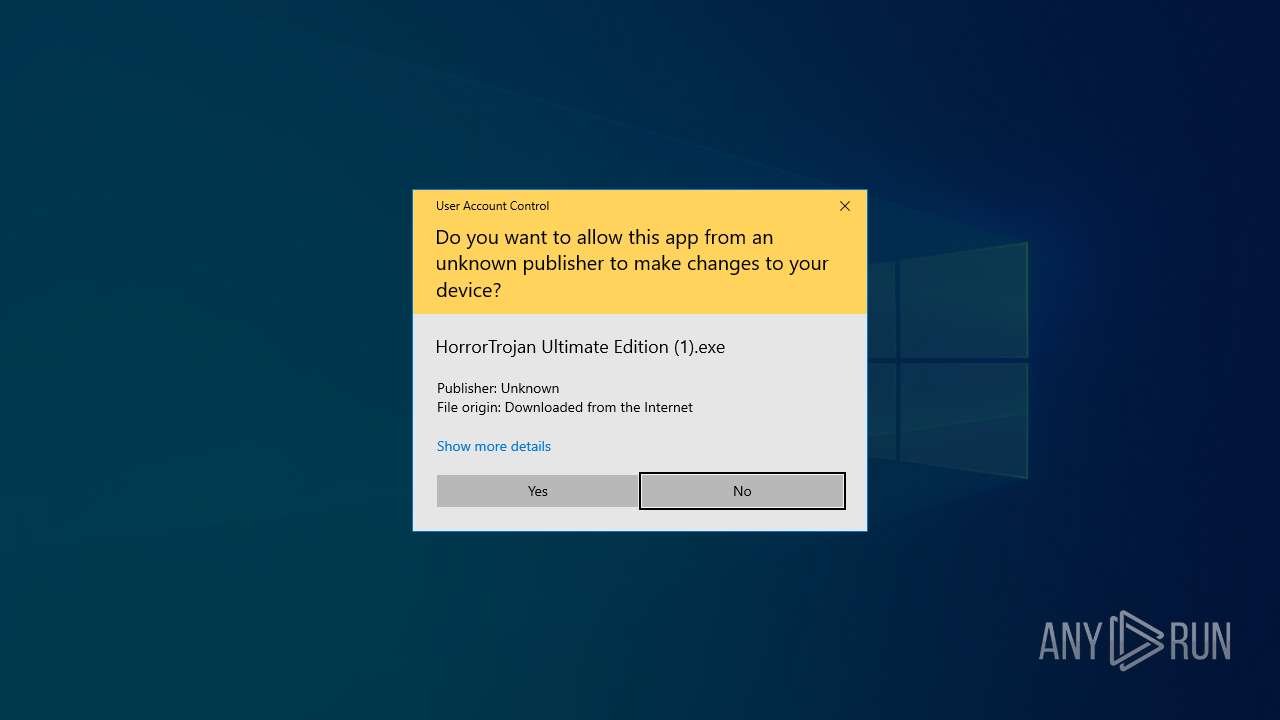
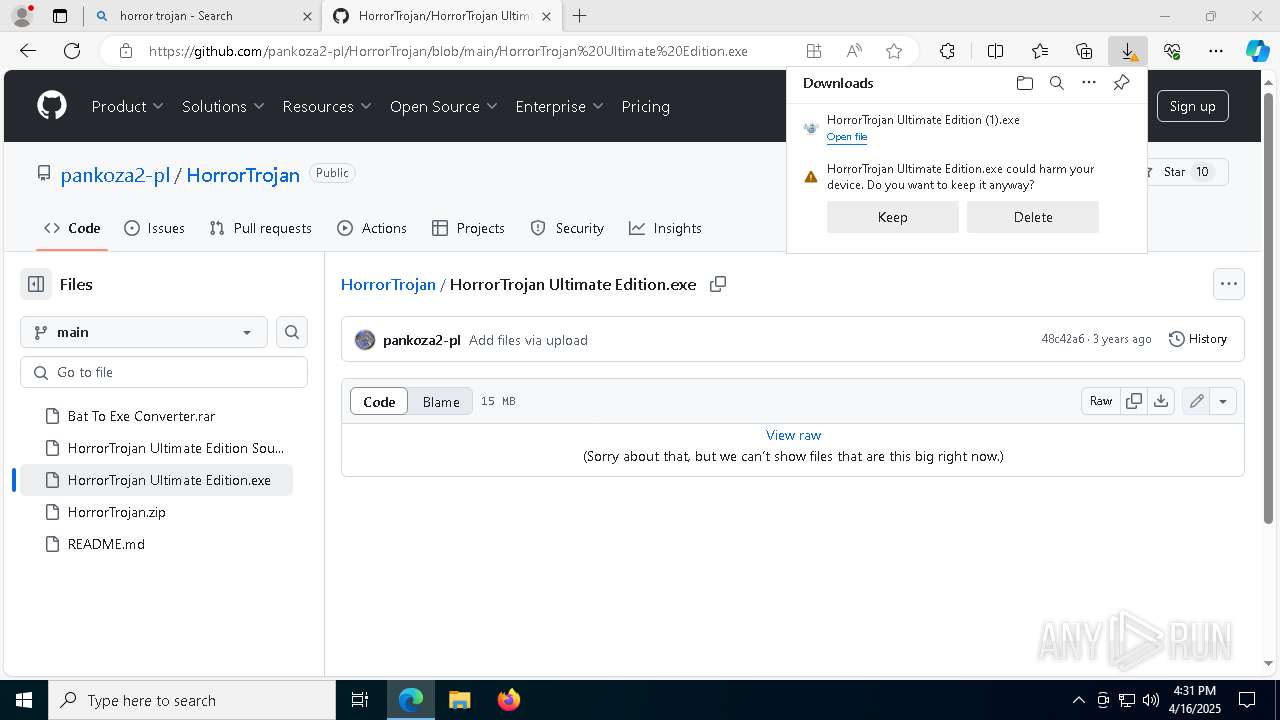
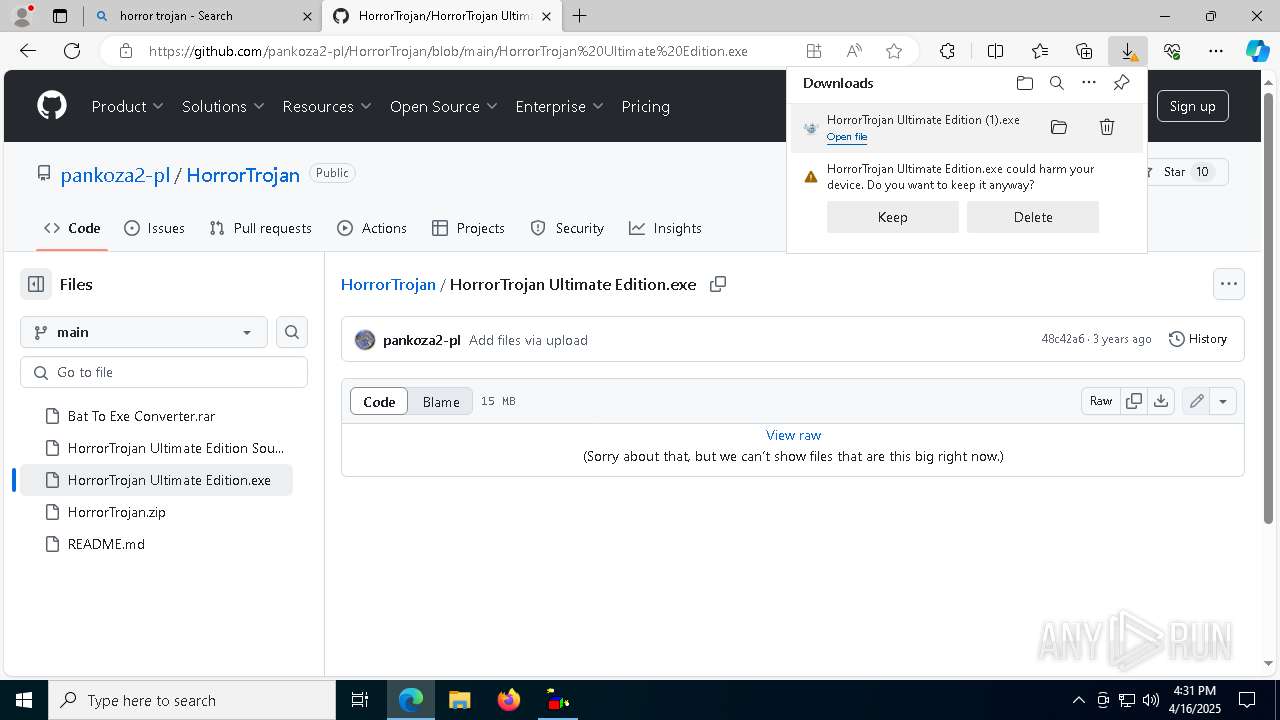
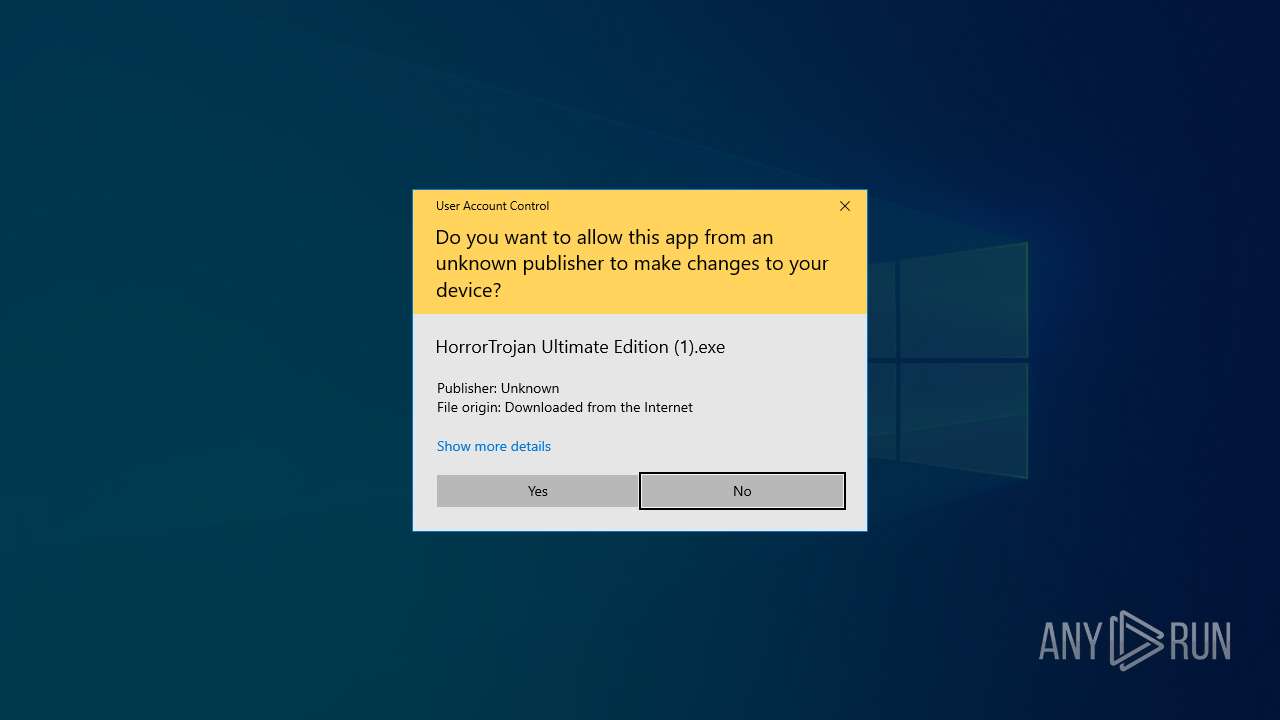
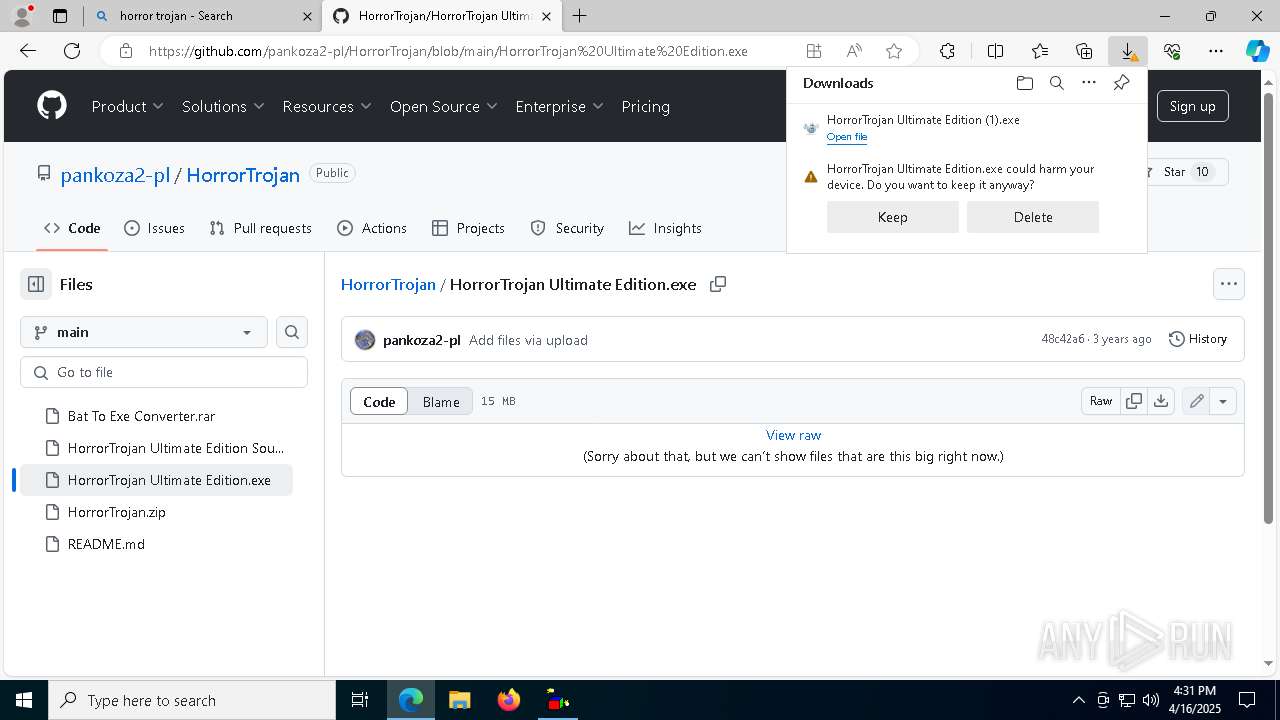
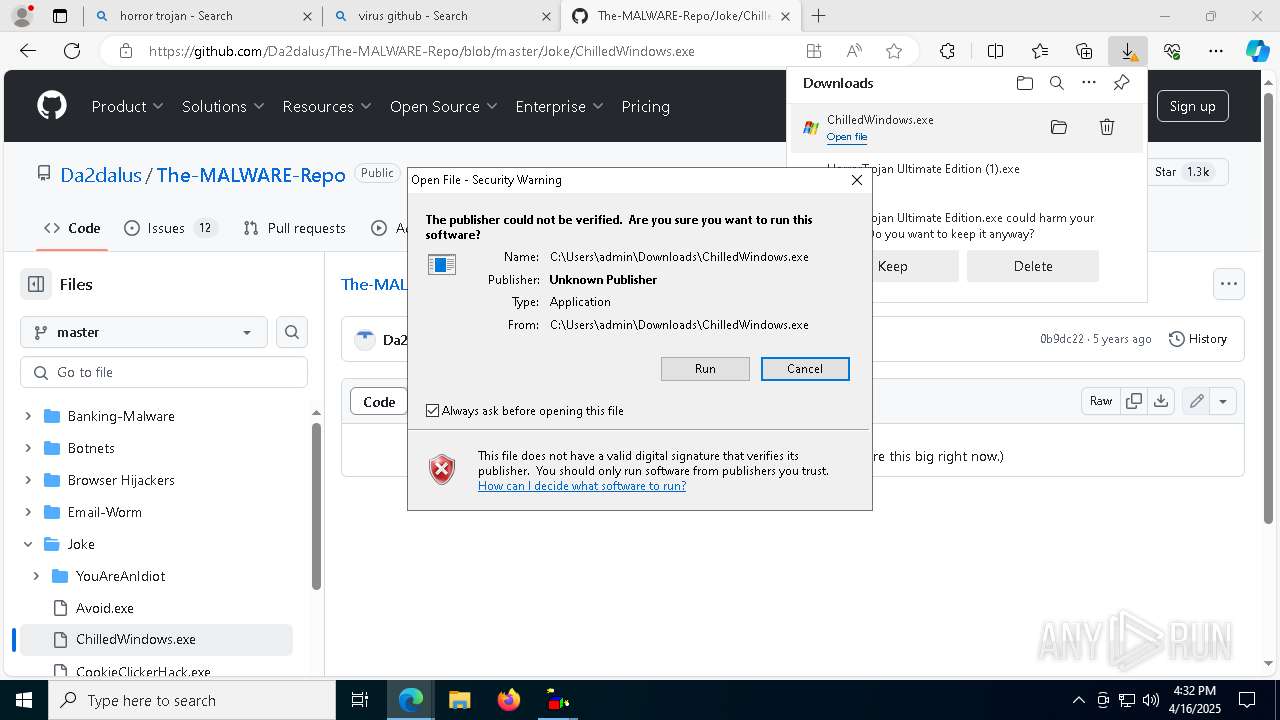
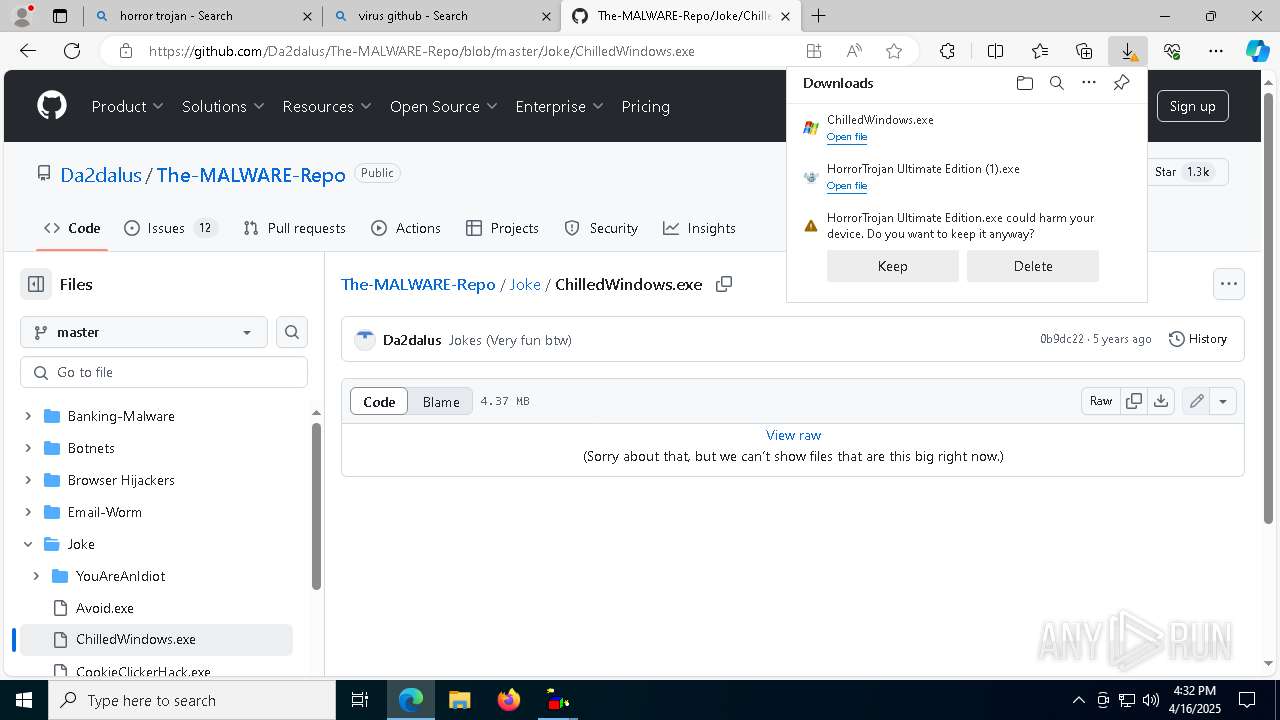
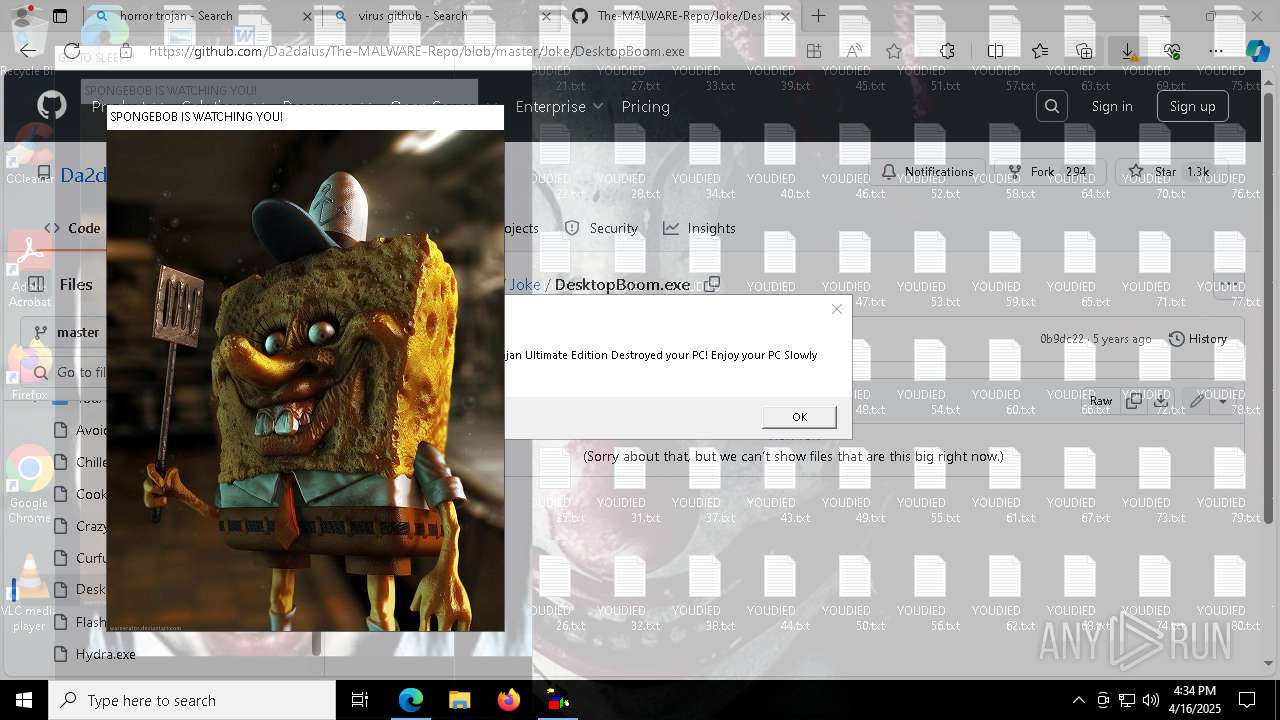
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- cmd.exe (PID: 5552)
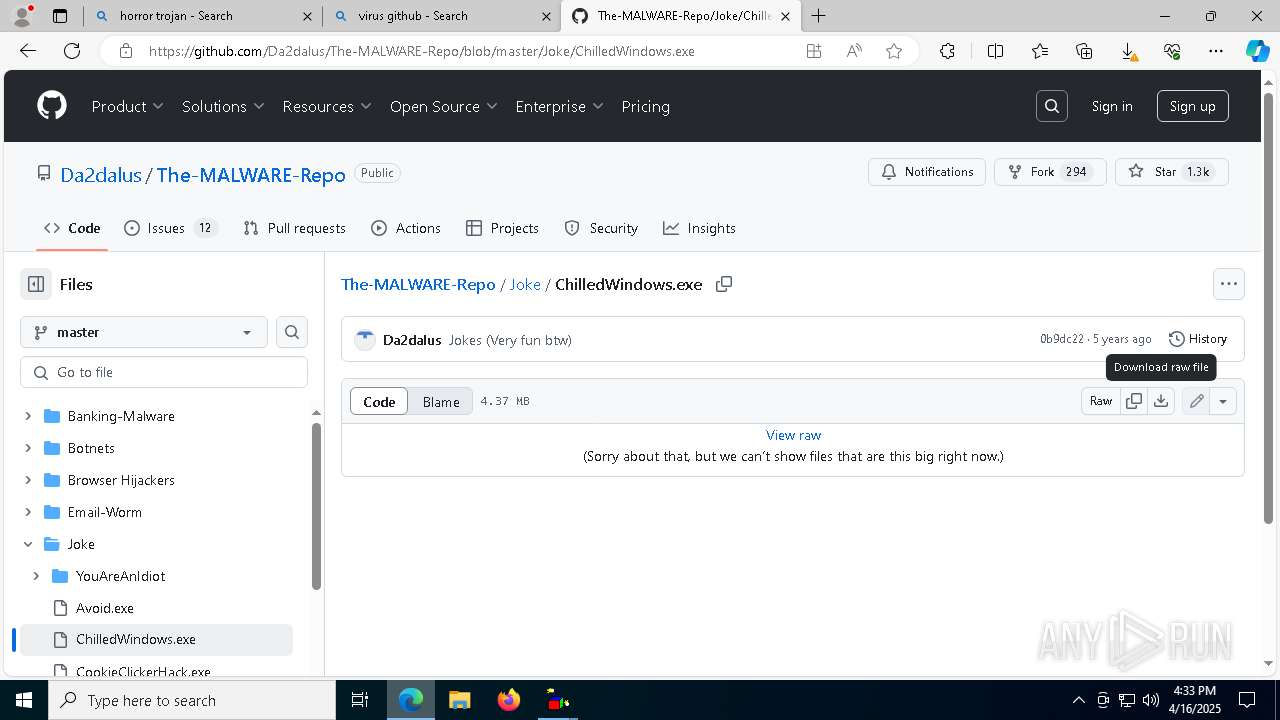
Reads security settings of Internet Explorer
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- ChilledWindows.exe (PID: 4120)
Runs WScript without displaying logo
- wscript.exe (PID: 8536)
- wscript.exe (PID: 8816)
The process executes VB scripts
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5552)
- cmd.exe (PID: 5136)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
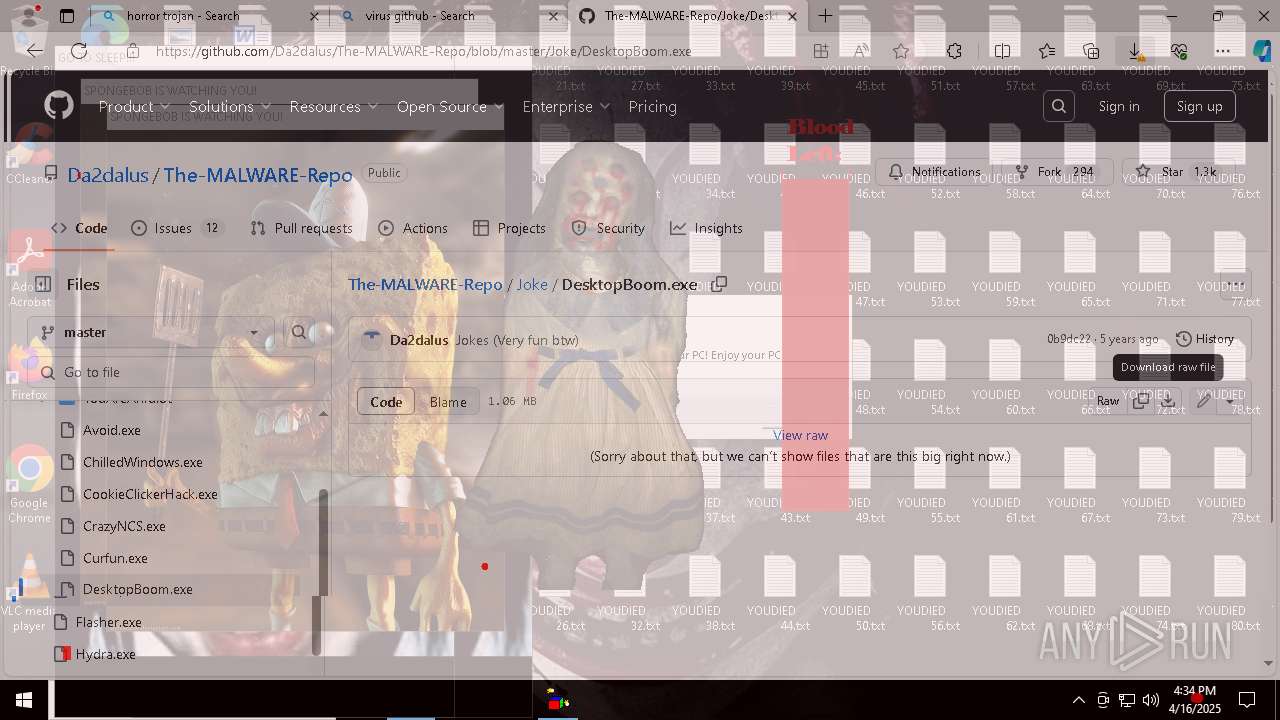
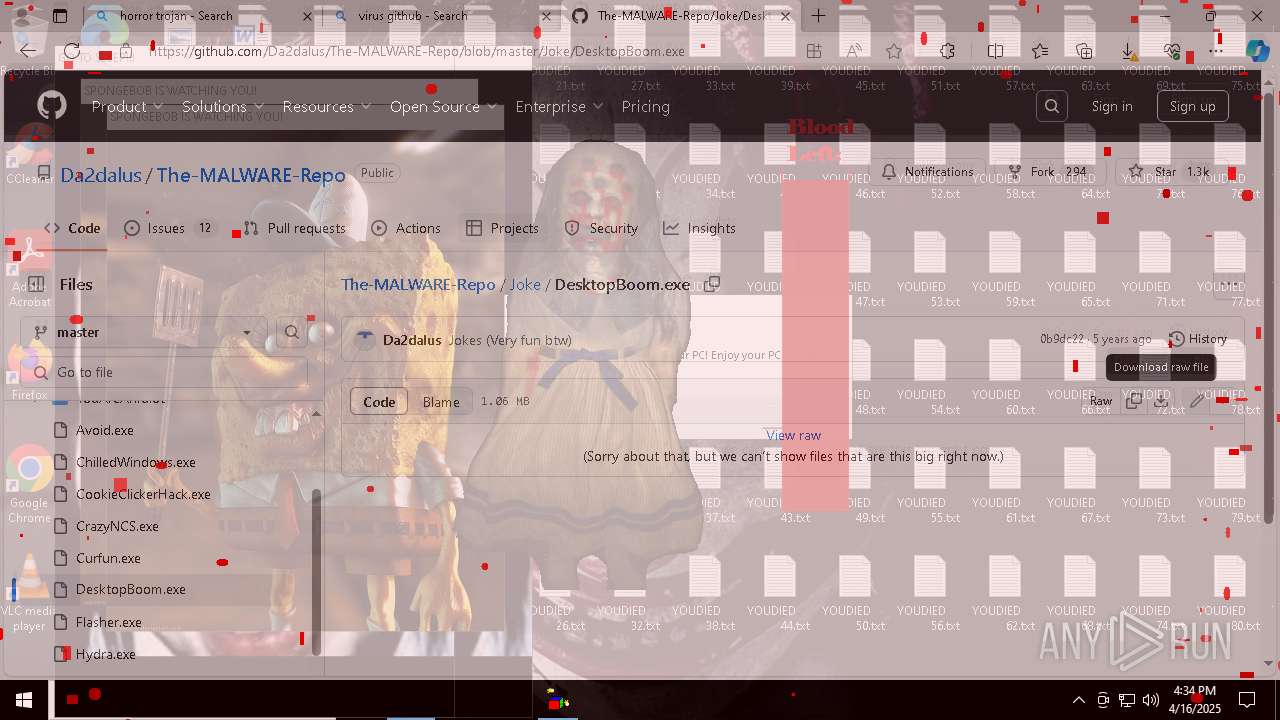
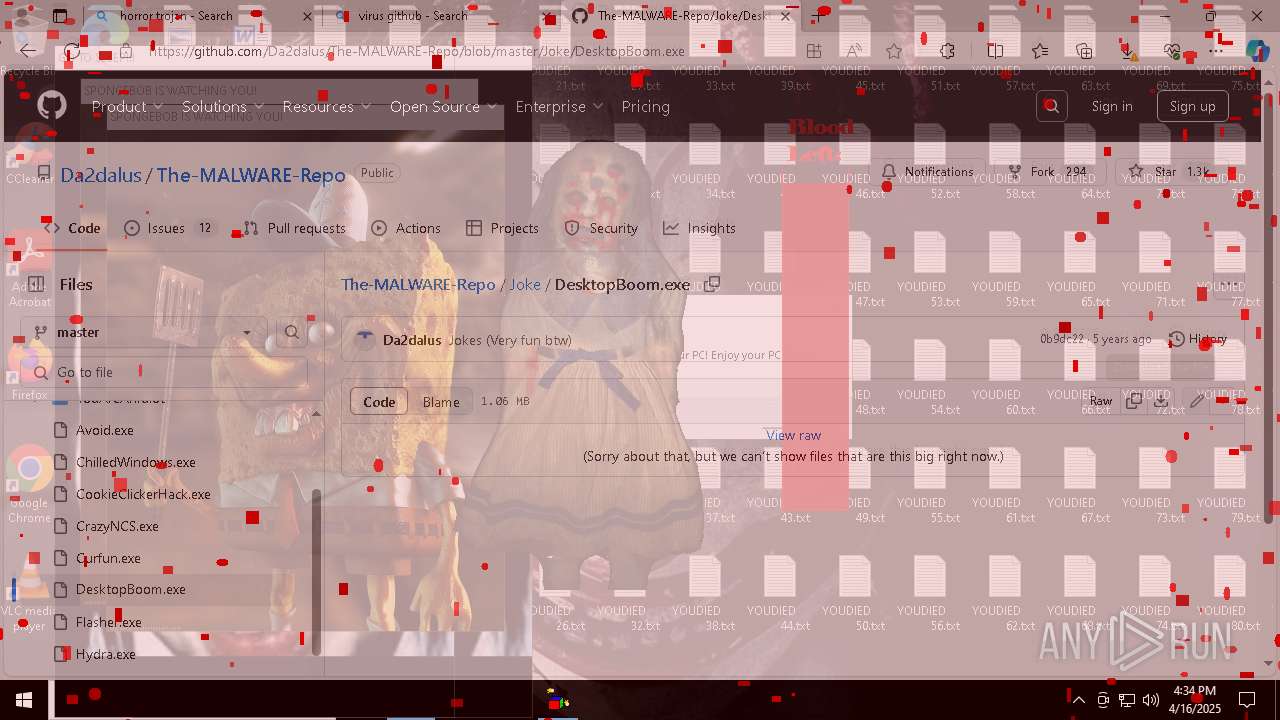
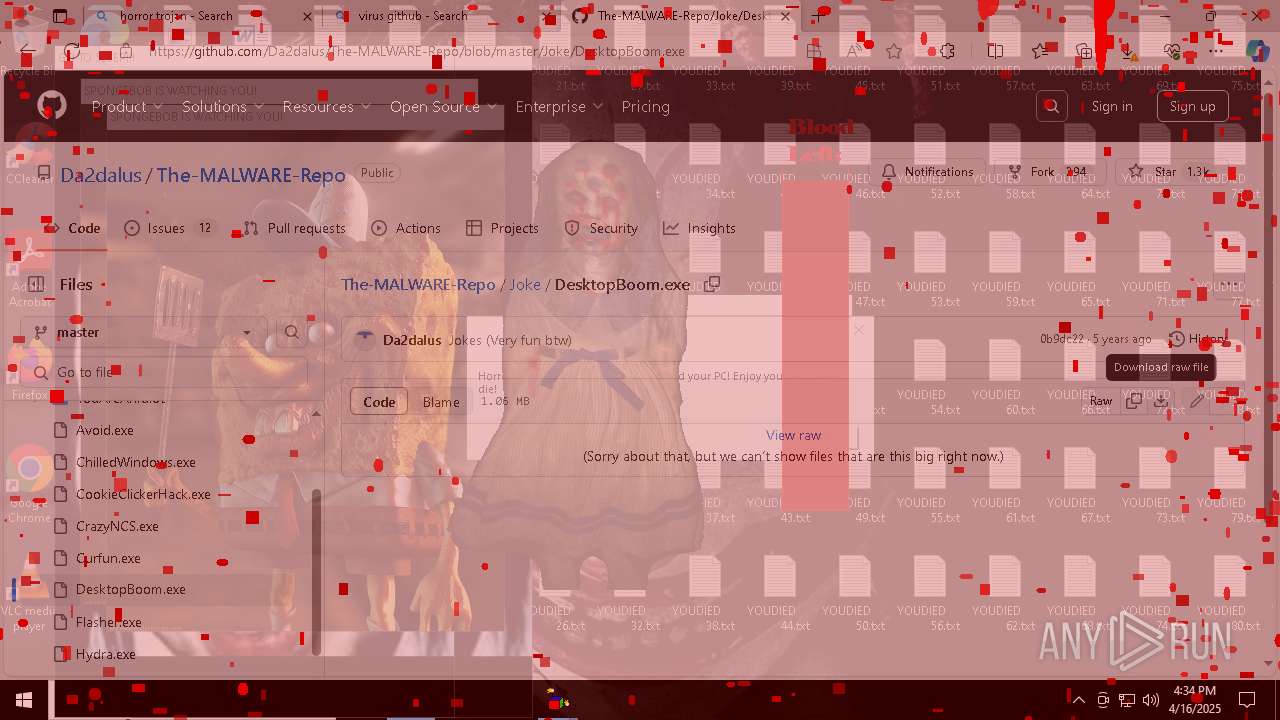
Changes the desktop background image
- reg.exe (PID: 6044)
- reg.exe (PID: 8212)
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
Creates file in the systems drive root
- cmd.exe (PID: 5552)
- cmd.exe (PID: 5136)
Executing commands from ".cmd" file
- wscript.exe (PID: 8816)
- wscript.exe (PID: 8536)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 5552)
- cmd.exe (PID: 5136)
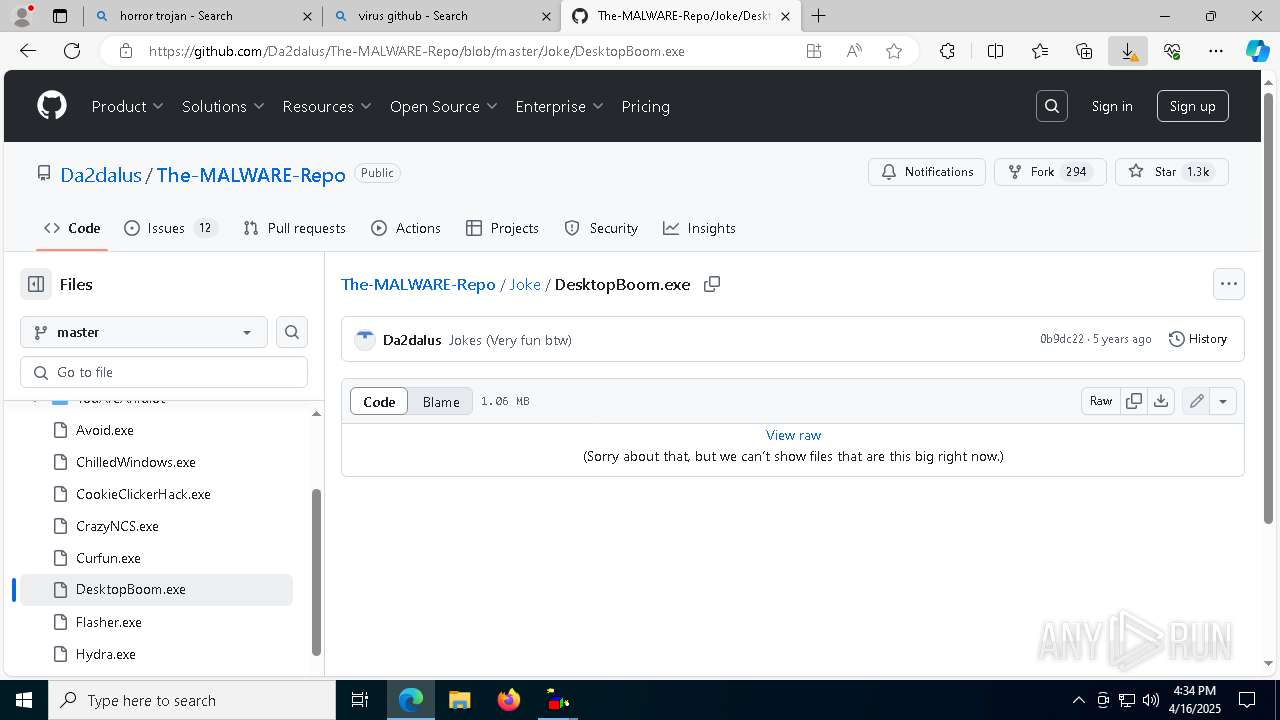
Creates or modifies Windows services
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
INFO
Application launched itself
- msedge.exe (PID: 7264)
Reads Environment values
- identity_helper.exe (PID: 1052)
Reads the computer name
- identity_helper.exe (PID: 1052)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
- ChilledWindows.exe (PID: 4120)
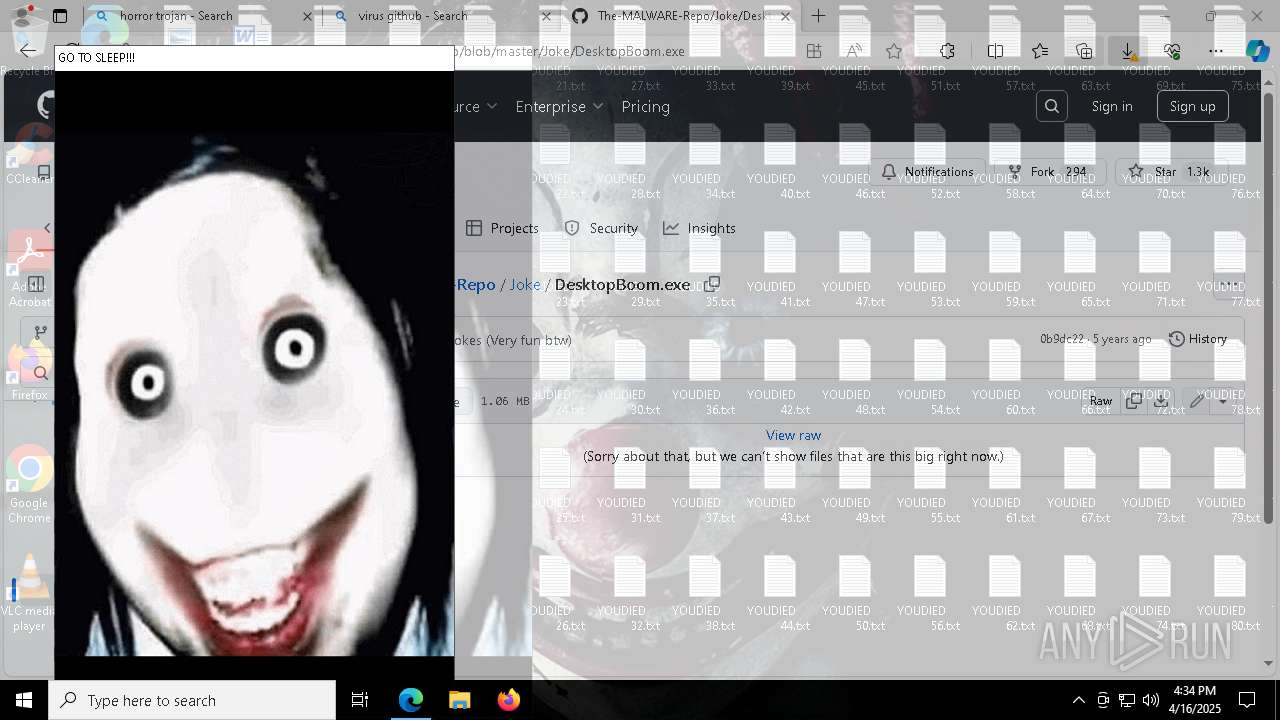
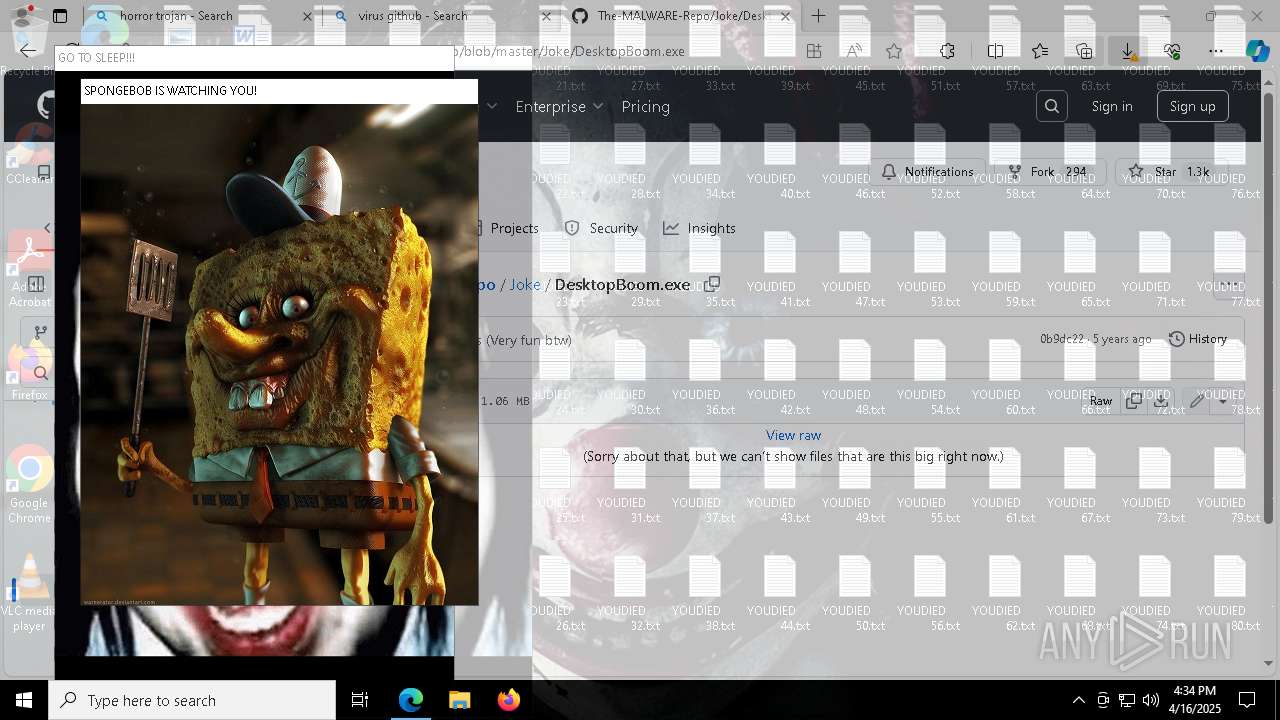
- jeffpopup.exe (PID: 5172)
- gdifuncs.exe (PID: 4844)
- jeffpopup.exe (PID: 8160)
- bobcreep.exe (PID: 7916)
- bobcreep.exe (PID: 5968)
- gdifuncs.exe (PID: 4028)
Checks supported languages
- identity_helper.exe (PID: 1052)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
- ChilledWindows.exe (PID: 4120)
- DesktopBoom.exe (PID: 4172)
- mbr.exe (PID: 2104)
- mbr.exe (PID: 4884)
- jeffpopup.exe (PID: 5172)
- jeffpopup.exe (PID: 8160)
- bobcreep.exe (PID: 5968)
- bobcreep.exe (PID: 7916)
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
- DesktopBoom.exe (PID: 7784)
- DesktopBoom.exe (PID: 8748)
The sample compiled with english language support
- msedge.exe (PID: 7560)
- msedge.exe (PID: 7264)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
- msedge.exe (PID: 4976)
Executable content was dropped or overwritten
- msedge.exe (PID: 7264)
- msedge.exe (PID: 7560)
- msedge.exe (PID: 4976)
Create files in a temporary directory
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
Process checks computer location settings
- HorrorTrojan Ultimate Edition (1).exe (PID: 8460)
- HorrorTrojan Ultimate Edition (1).exe (PID: 8764)
Reads security settings of Internet Explorer
- wscript.exe (PID: 8536)
- wscript.exe (PID: 8816)
Reads the machine GUID from the registry
- ChilledWindows.exe (PID: 4120)
- gdifuncs.exe (PID: 4844)
- gdifuncs.exe (PID: 4028)
Creates files or folders in the user directory
- ChilledWindows.exe (PID: 4120)
Reads the software policy settings
- slui.exe (PID: 7804)
- slui.exe (PID: 6540)
Checks proxy server information
- ChilledWindows.exe (PID: 4120)
- slui.exe (PID: 6540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
333
Monitored processes
194
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6884 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=6956 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 444 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7056 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5584 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=8728 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5620 --field-trial-handle=2320,i,10192358573623739259,11552641864673109238,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 918
Read events
22 007
Write events
909
Delete events
2
Modification events
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DF1C58187E912F00 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF9E6C187E912F00 | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262752 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {54E2220D-B0FA-448C-8527-F94D8EB867C9} | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262752 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {791AC7E1-5FB1-40DF-9DB5-CCC265AABDEE} | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262752 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DFFD346B-D5C8-454F-98EA-C854DAB3019F} | |||
| (PID) Process: | (7264) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262752 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B388C4C-99C7-4C0F-A692-5A9E7CD4654D} | |||
Executable files
56
Suspicious files
837
Text files
318
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d14c.TMP | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d15b.TMP | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d15b.TMP | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d15b.TMP | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d17b.TMP | — | |
MD5:— | SHA256:— | |||
| 7264 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
144
DNS requests
155
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745358531&P2=404&P3=2&P4=GRrZCj5JZ%2bqwYRCOONEDSBmJHc%2f6YxRngO%2bMK%2buyKWtQpw9SLoP3SeEZkXKlkmLoggselWeAa75RyR%2fm9HmaRw%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745358531&P2=404&P3=2&P4=GRrZCj5JZ%2bqwYRCOONEDSBmJHc%2f6YxRngO%2bMK%2buyKWtQpw9SLoP3SeEZkXKlkmLoggselWeAa75RyR%2fm9HmaRw%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745358531&P2=404&P3=2&P4=Mm8EJh4lii%2fWgUXbRAT13qWdrlMEqAJz4%2bZ98f9TmiQY1Xx8iuTMzXgzfyjq0Tus9f8HqzArVNRjA5HR9ciO%2bg%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745358531&P2=404&P3=2&P4=GRrZCj5JZ%2bqwYRCOONEDSBmJHc%2f6YxRngO%2bMK%2buyKWtQpw9SLoP3SeEZkXKlkmLoggselWeAa75RyR%2fm9HmaRw%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745358531&P2=404&P3=2&P4=Mm8EJh4lii%2fWgUXbRAT13qWdrlMEqAJz4%2bZ98f9TmiQY1Xx8iuTMzXgzfyjq0Tus9f8HqzArVNRjA5HR9ciO%2bg%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745358531&P2=404&P3=2&P4=RVbz2q9hRnZDs%2bmXCRqDEl9Aw2v1tBcIhdQLZ259QC1ERHgZn36g1Uv%2bRW%2bTMZitL%2bE148Sv6ZbVSImNQfmAbg%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745358531&P2=404&P3=2&P4=Mm8EJh4lii%2fWgUXbRAT13qWdrlMEqAJz4%2bZ98f9TmiQY1Xx8iuTMzXgzfyjq0Tus9f8HqzArVNRjA5HR9ciO%2bg%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1745358533&P2=404&P3=2&P4=A2CW0y964Zu6L0hZOgcaMWmSi2mJYKCKsGL6py0ZZyulY%2fuXwyYTzjj0dACe%2f0WN8vx5ea5sy16IoITPOf3qlQ%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745358531&P2=404&P3=2&P4=RVbz2q9hRnZDs%2bmXCRqDEl9Aw2v1tBcIhdQLZ259QC1ERHgZn36g1Uv%2bRW%2bTMZitL%2bE148Sv6ZbVSImNQfmAbg%3d%3d | unknown | — | — | whitelisted |
9108 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1745358531&P2=404&P3=2&P4=Mm8EJh4lii%2fWgUXbRAT13qWdrlMEqAJz4%2bZ98f9TmiQY1Xx8iuTMzXgzfyjq0Tus9f8HqzArVNRjA5HR9ciO%2bg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.148:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
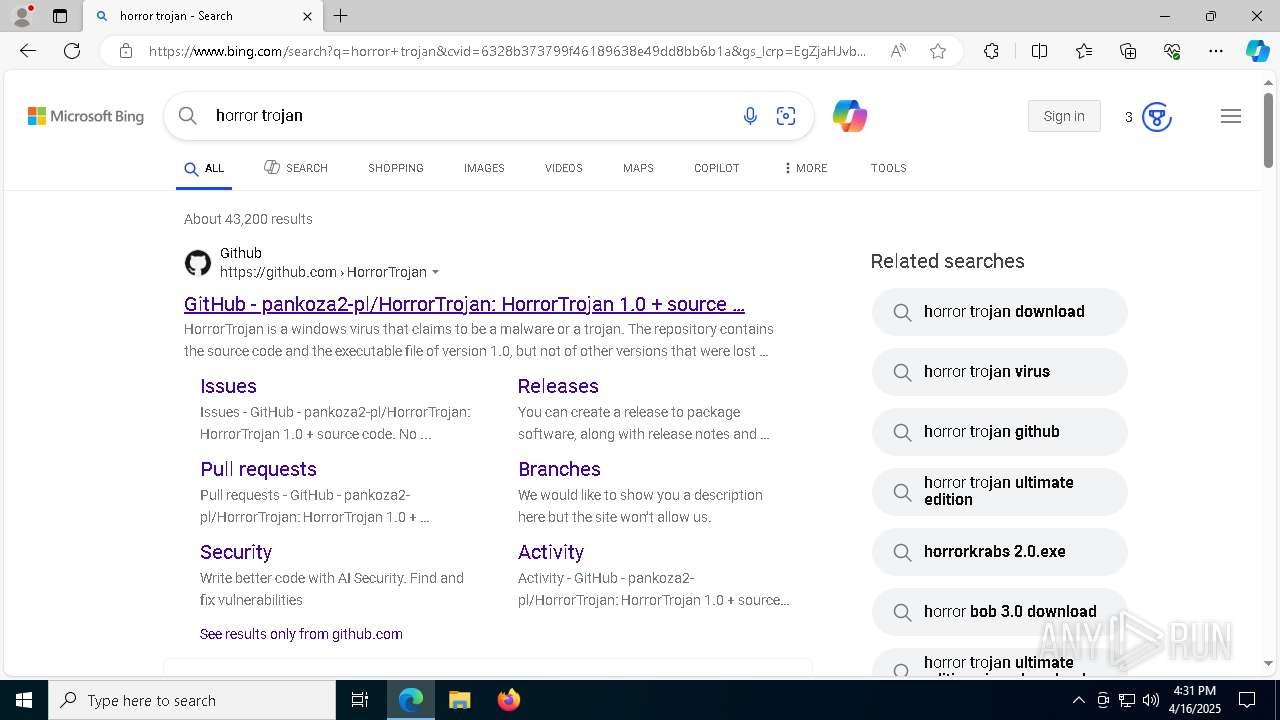
7560 | msedge.exe | 142.250.184.196:443 | www.google.com | — | — | whitelisted |
7560 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7560 | msedge.exe | 216.58.206.78:443 | google.com | — | — | whitelisted |
7264 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7560 | msedge.exe | 216.58.206.78:80 | google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
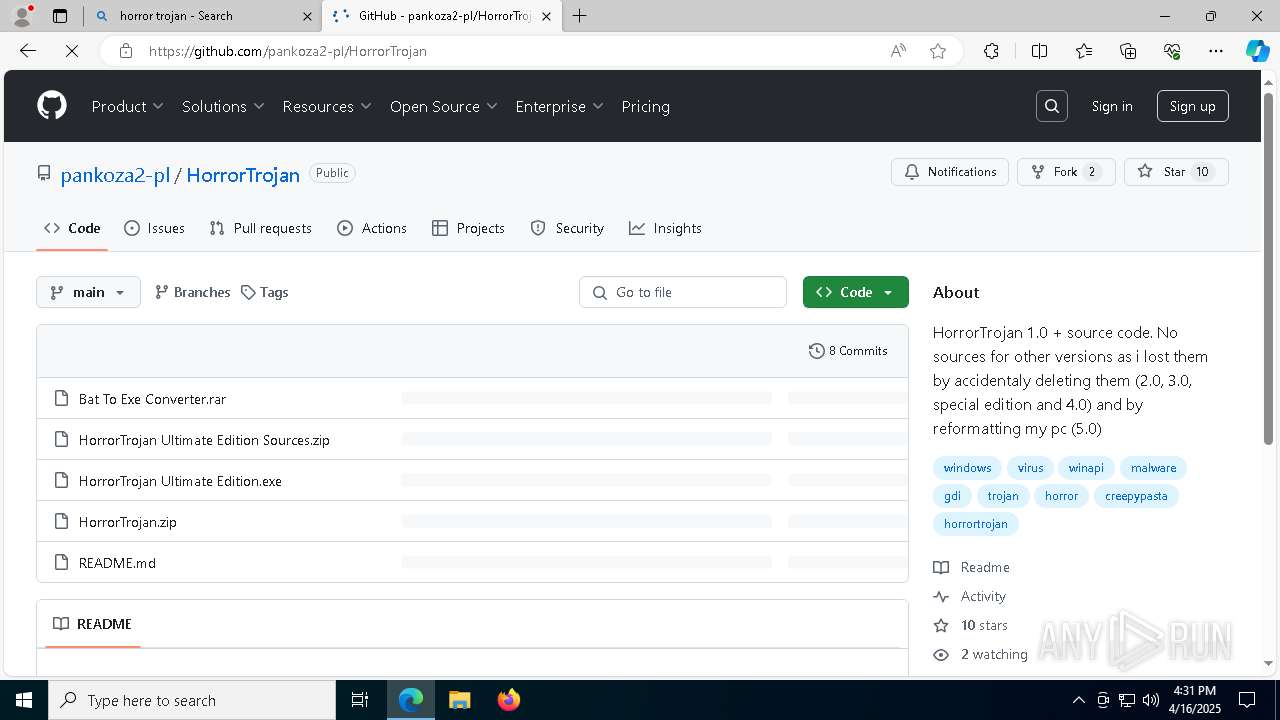
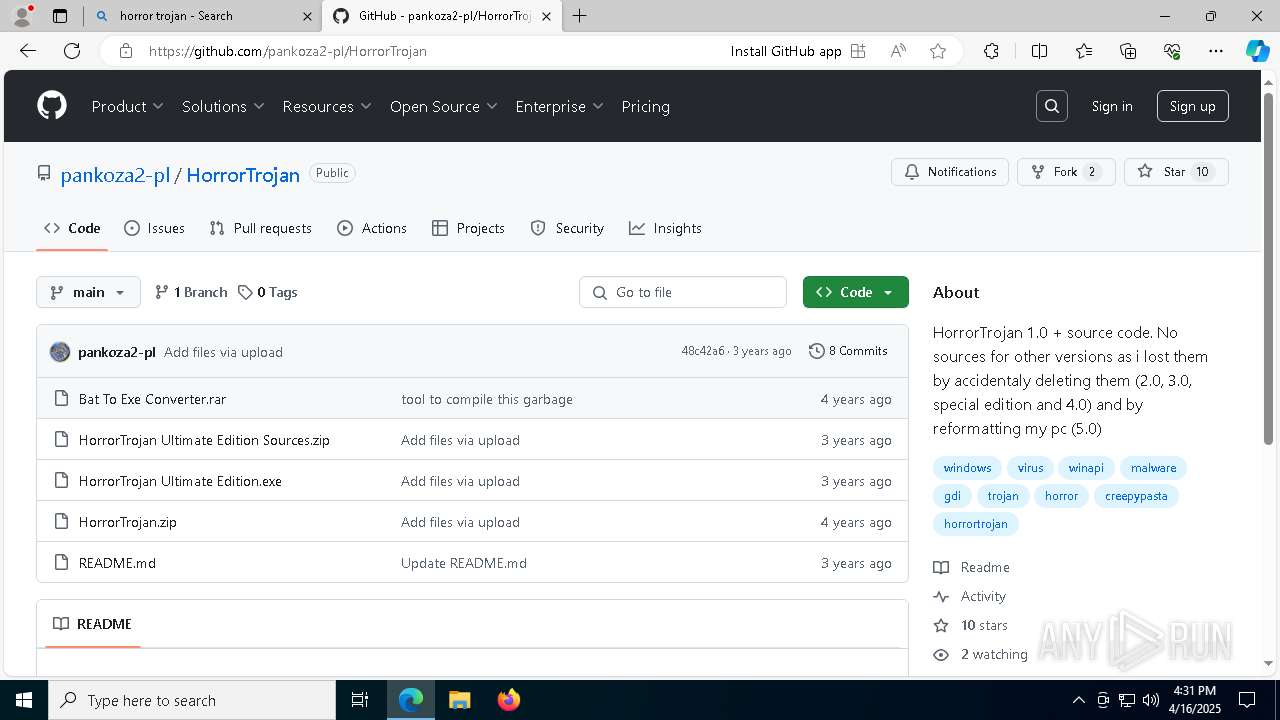
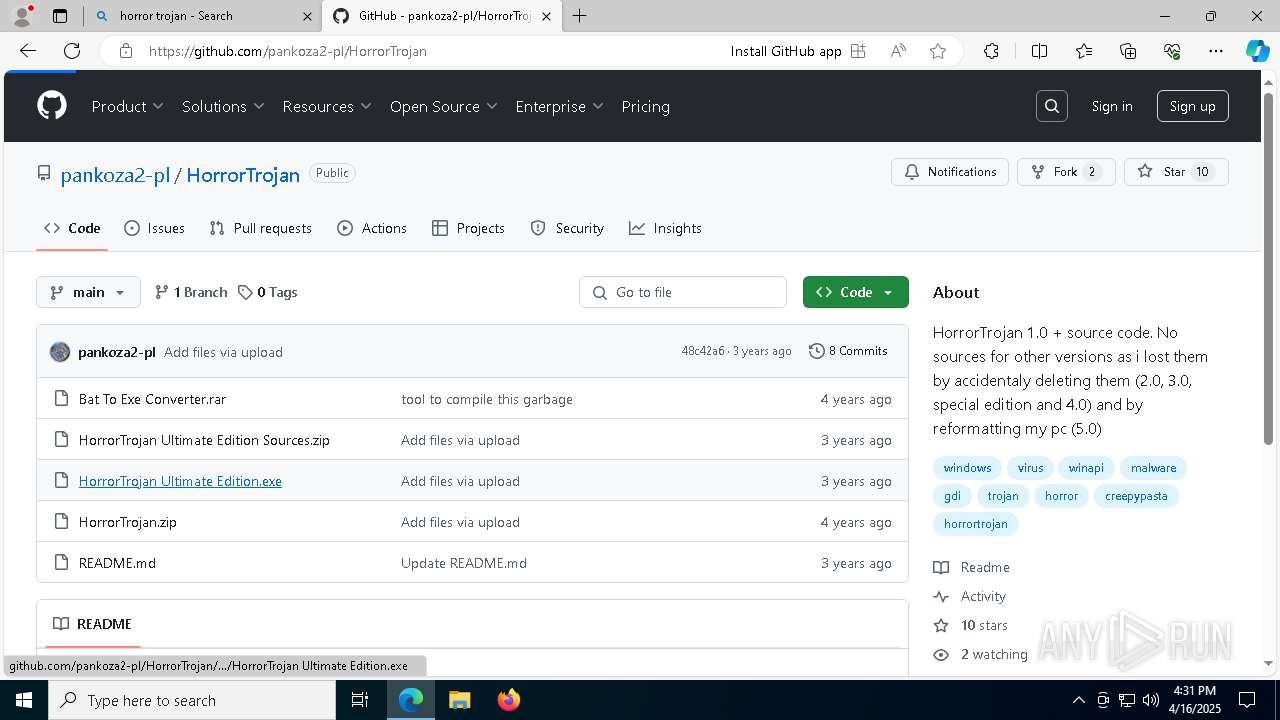
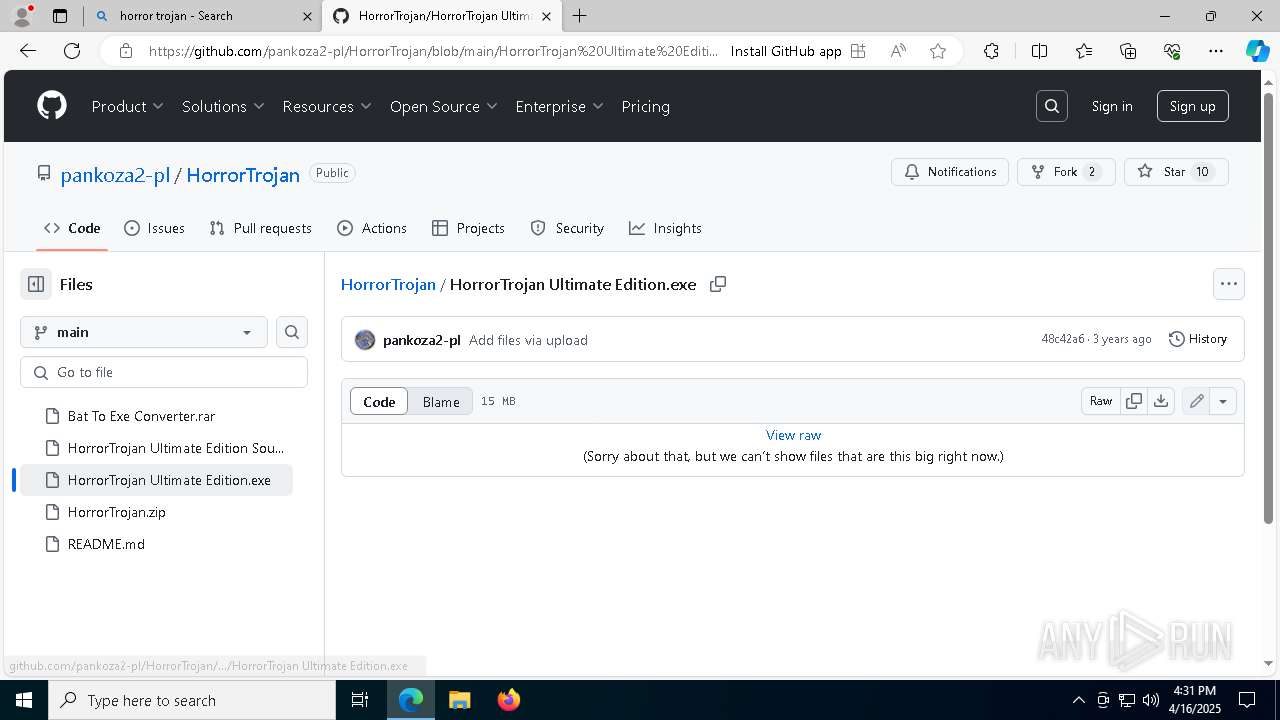
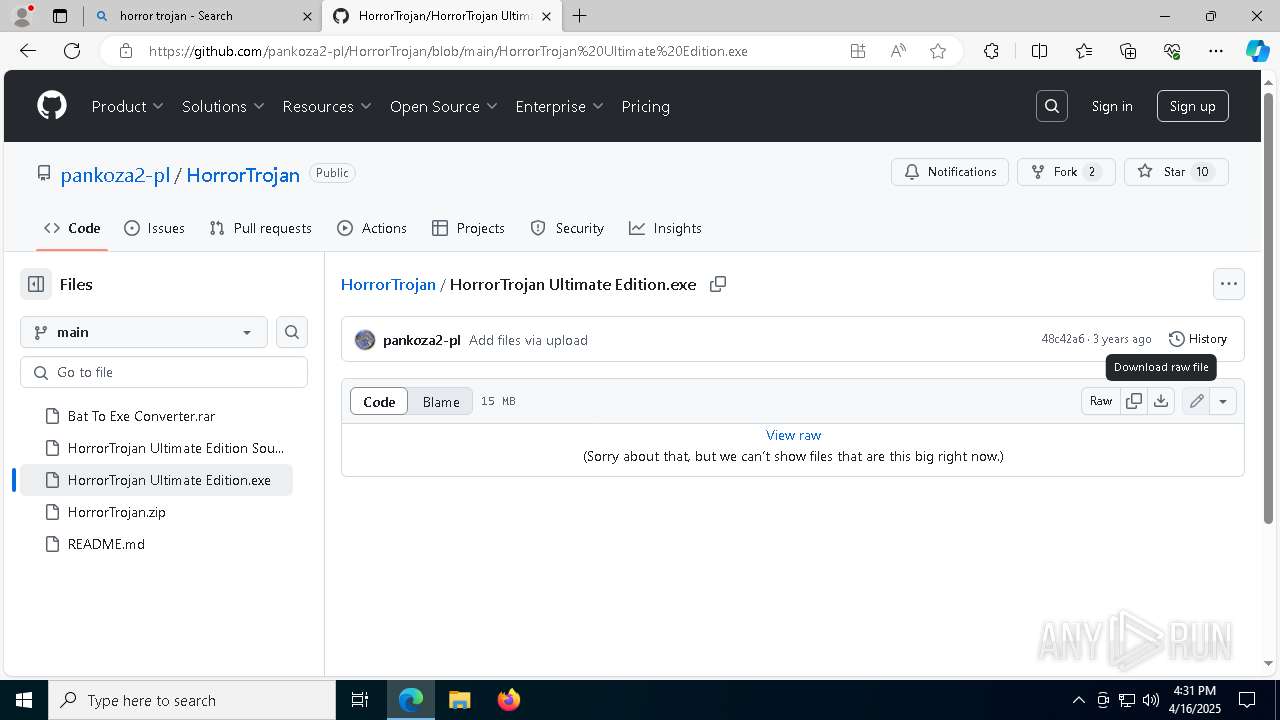
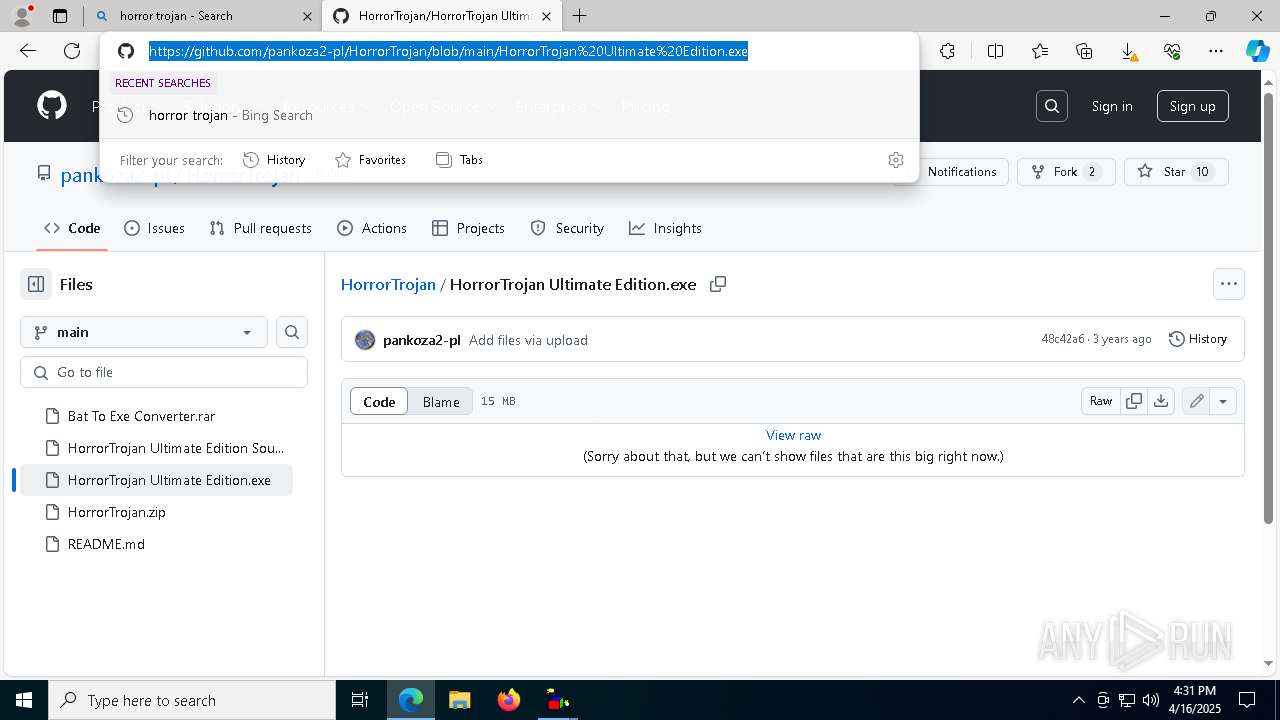
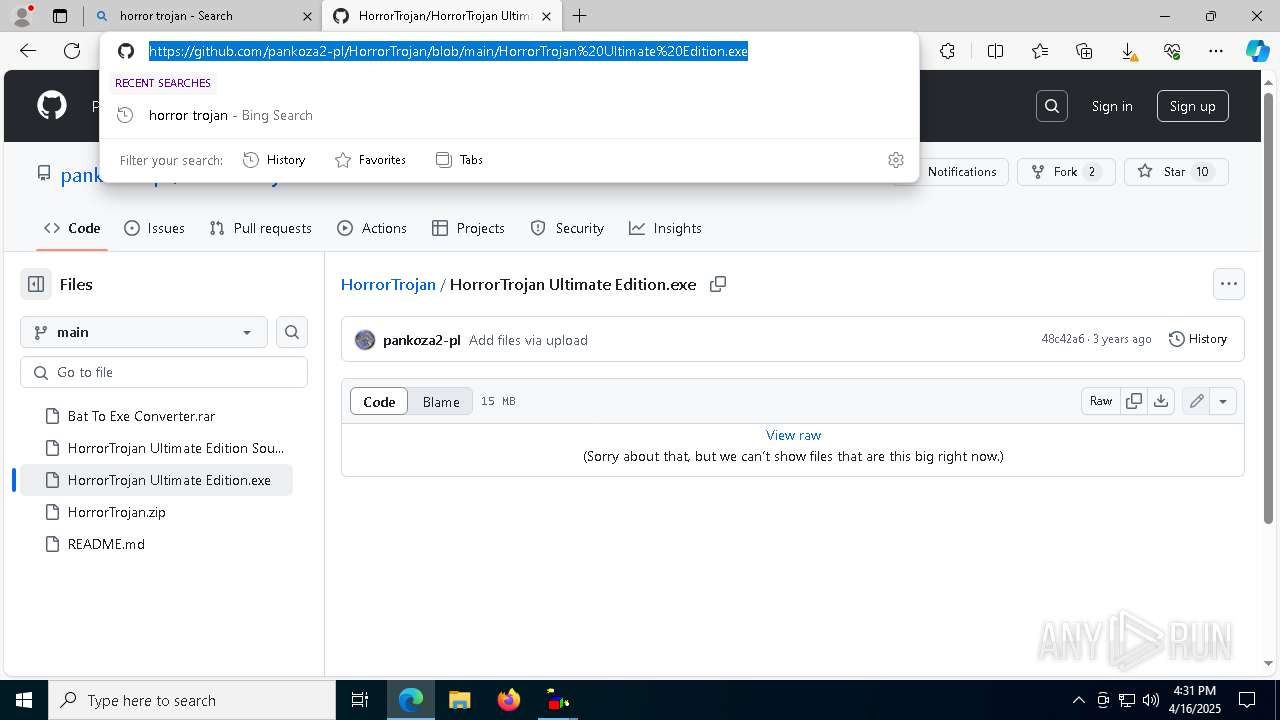
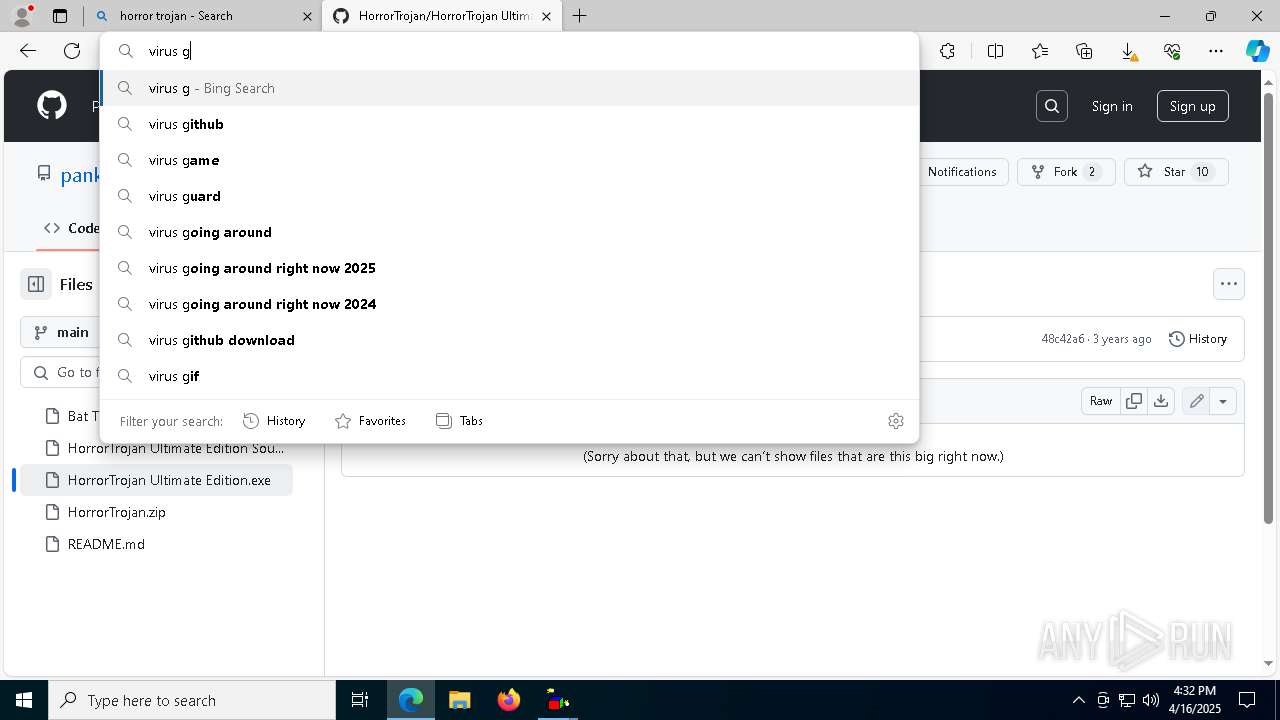
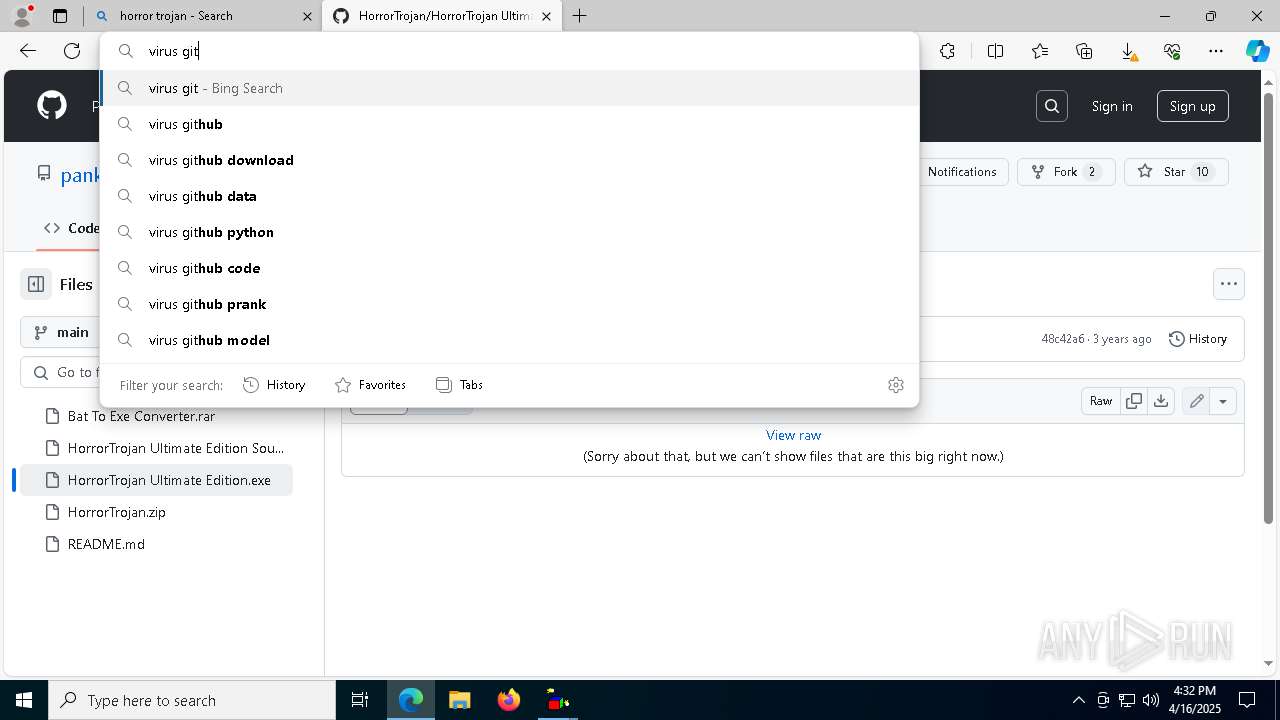
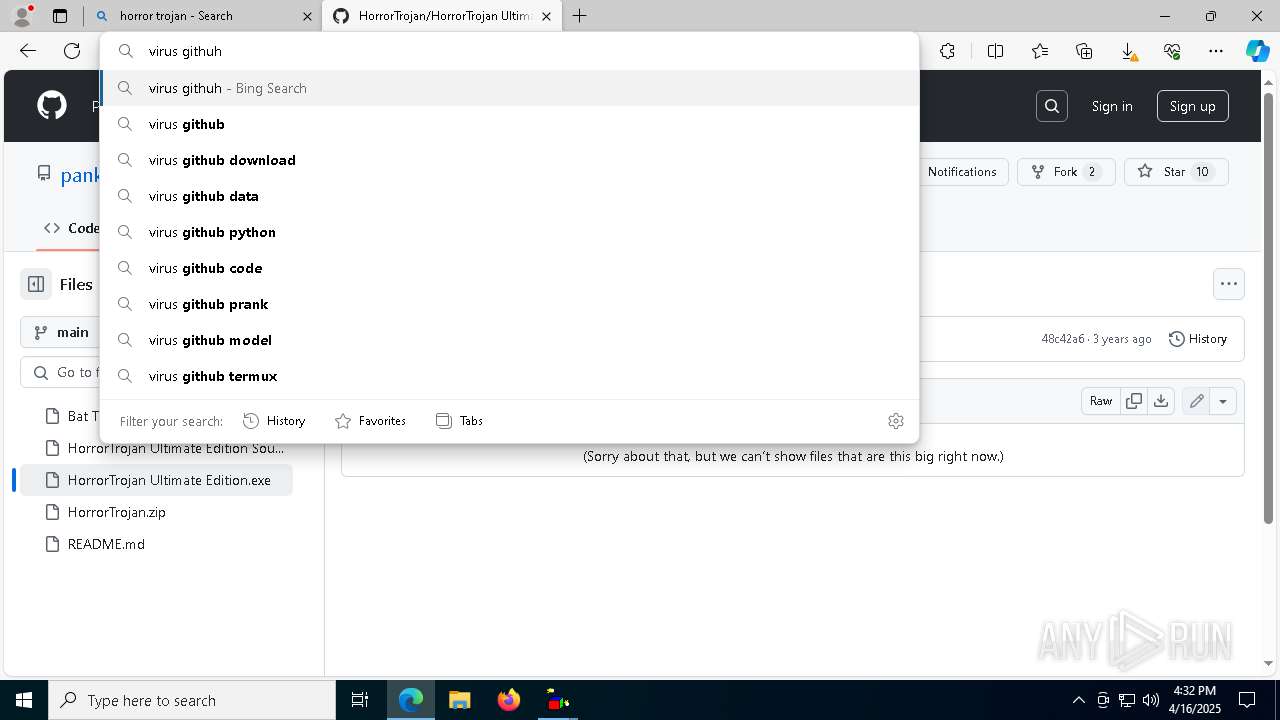
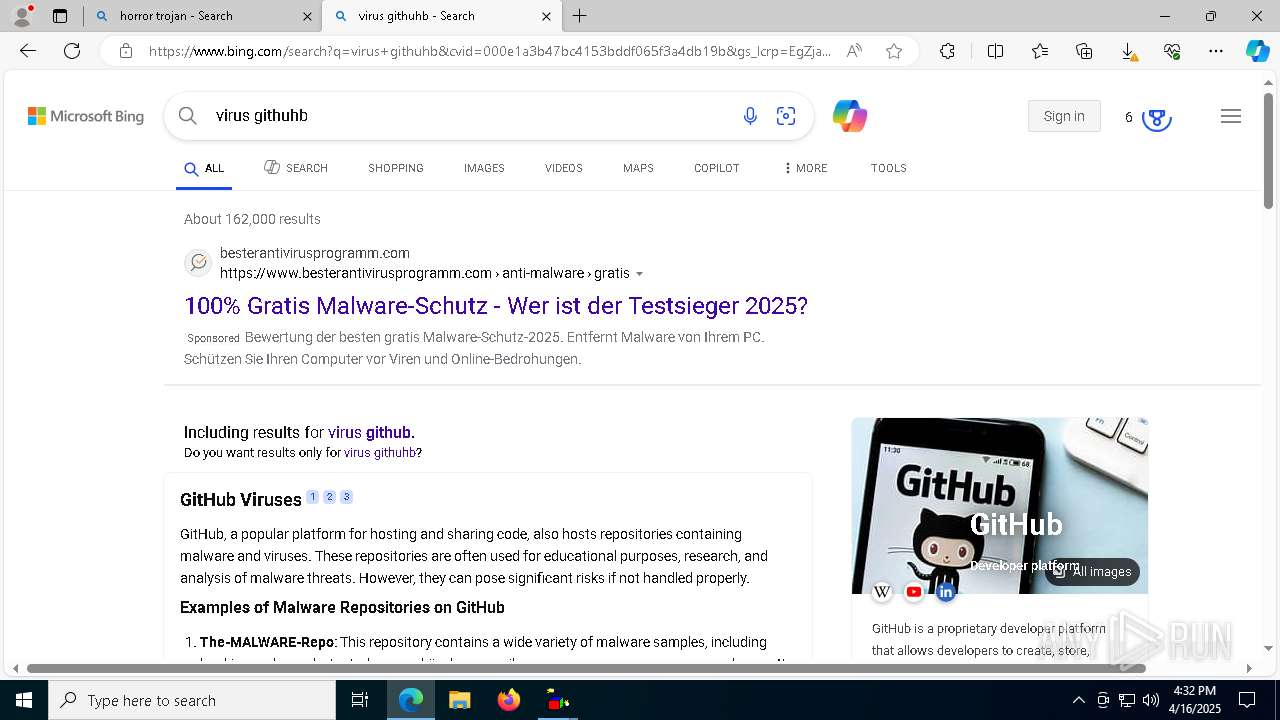
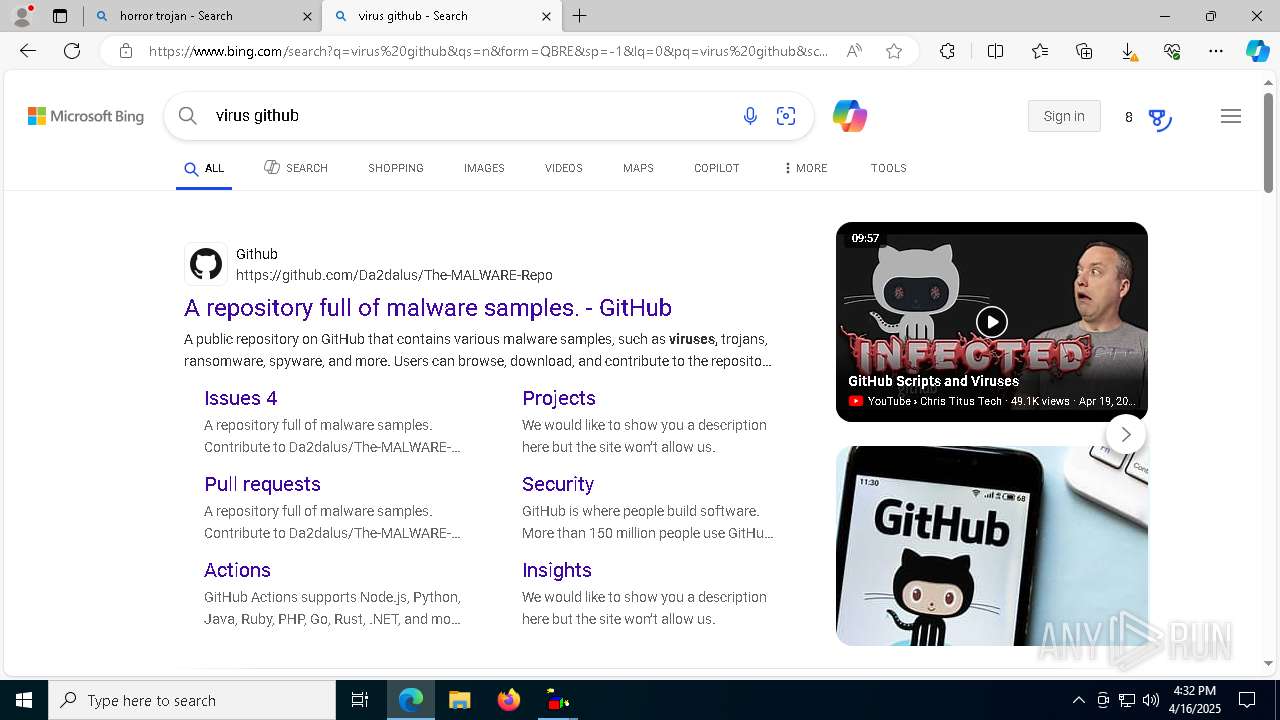
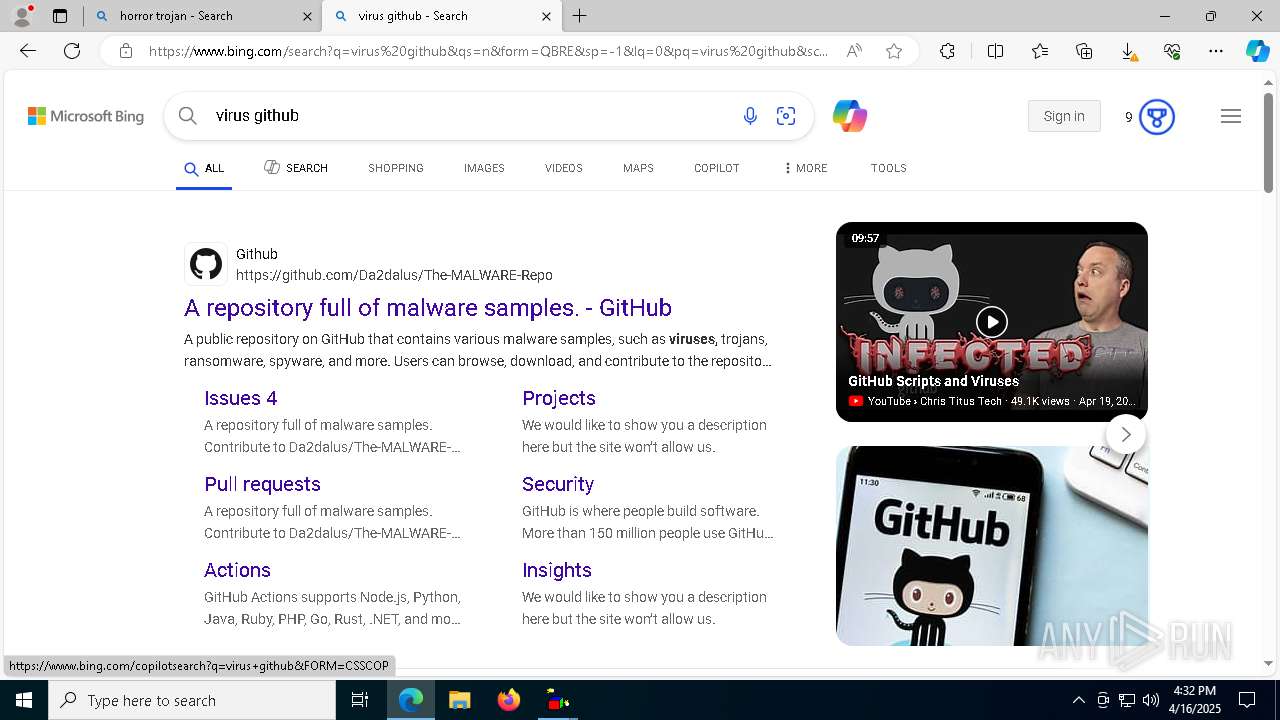
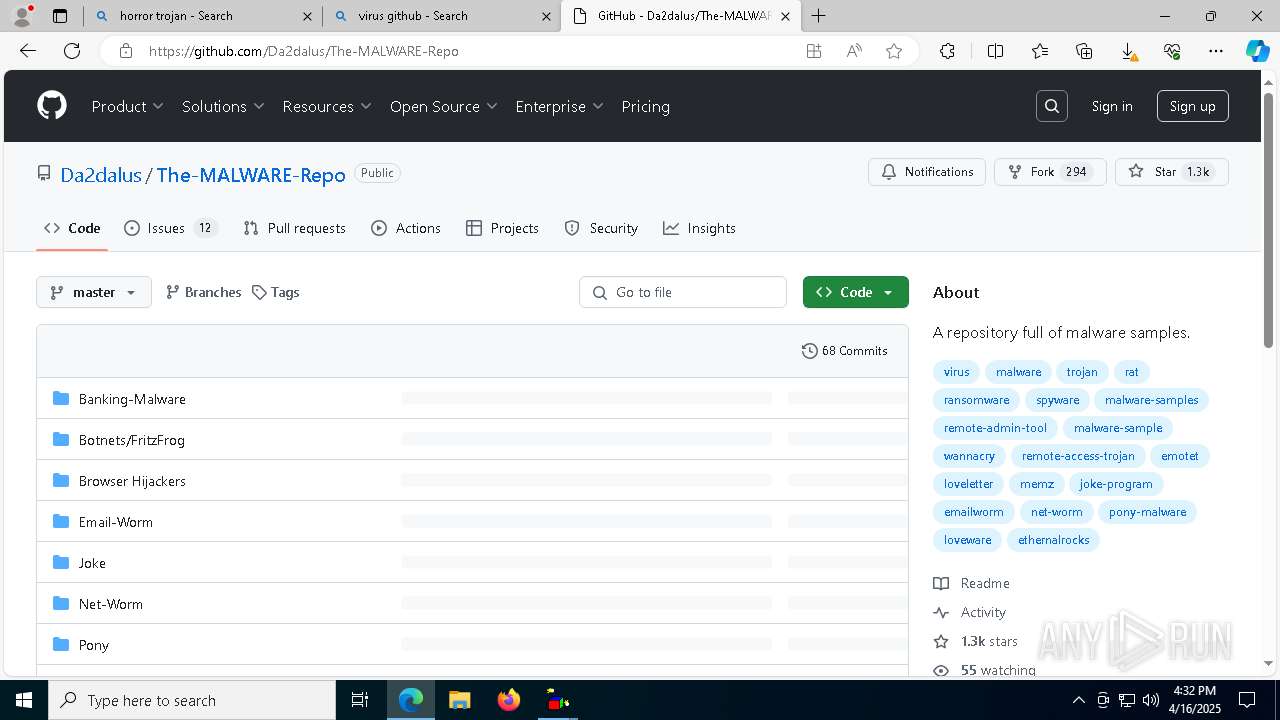
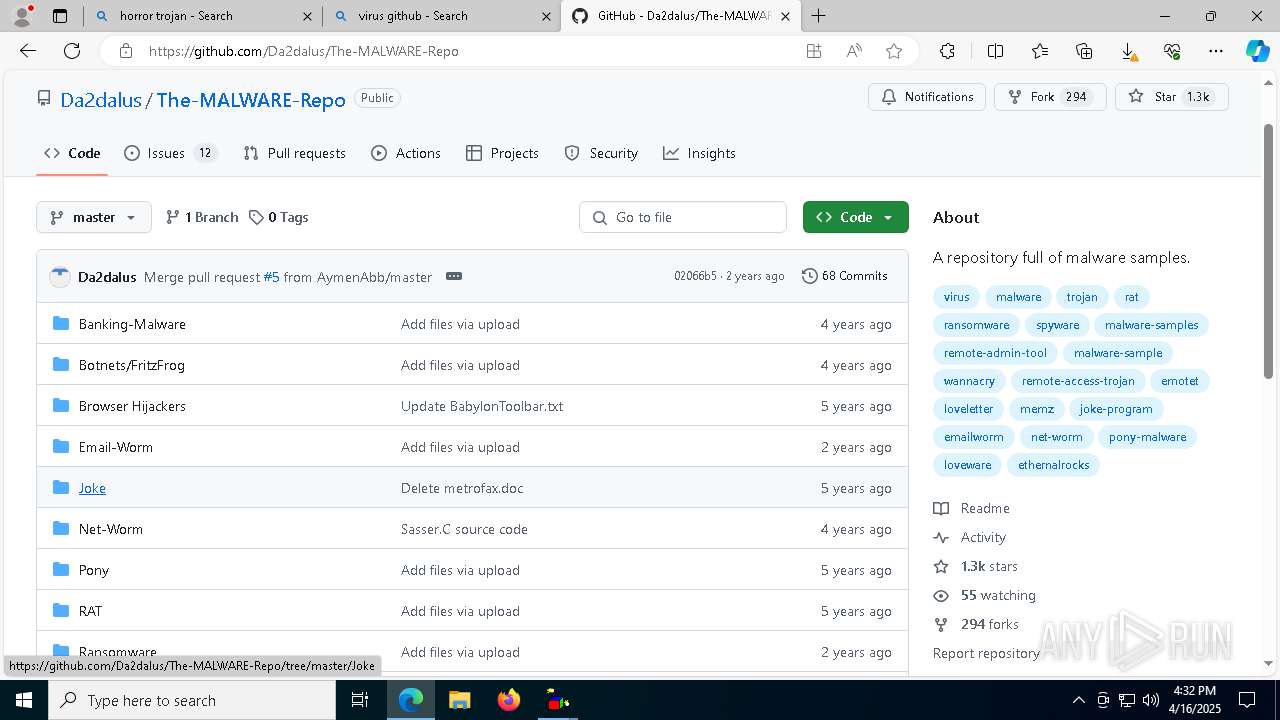
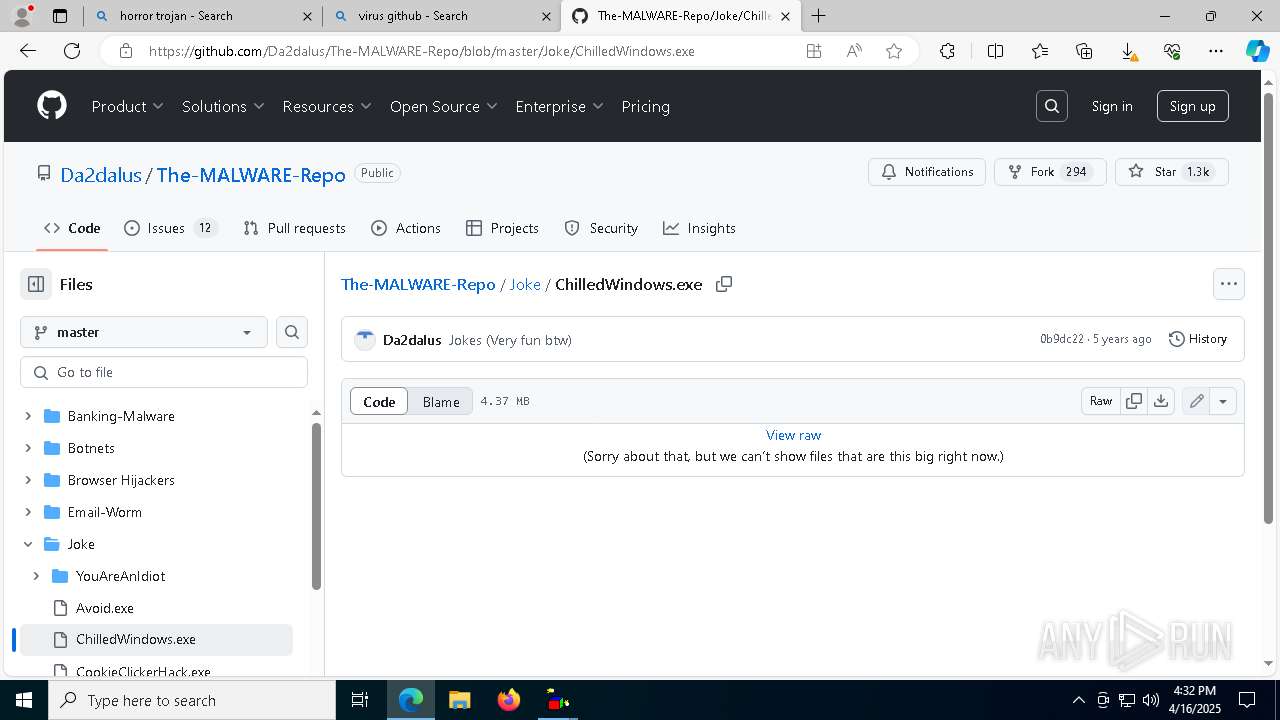
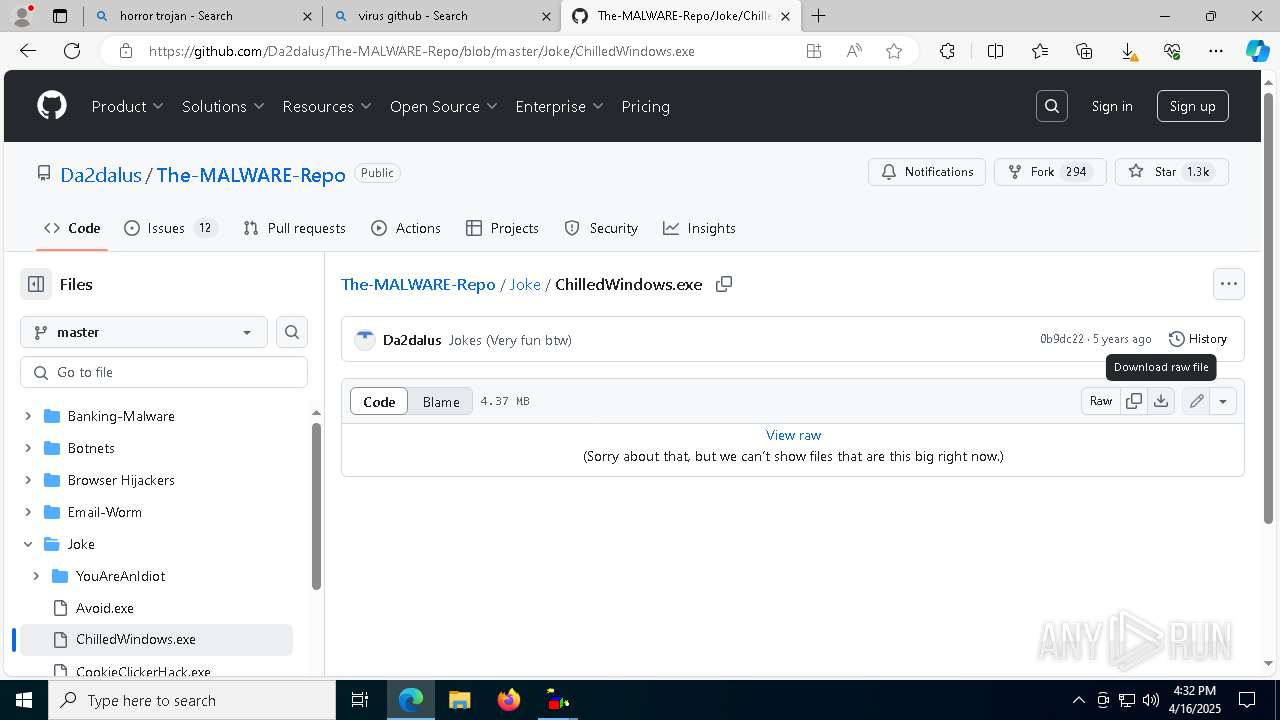
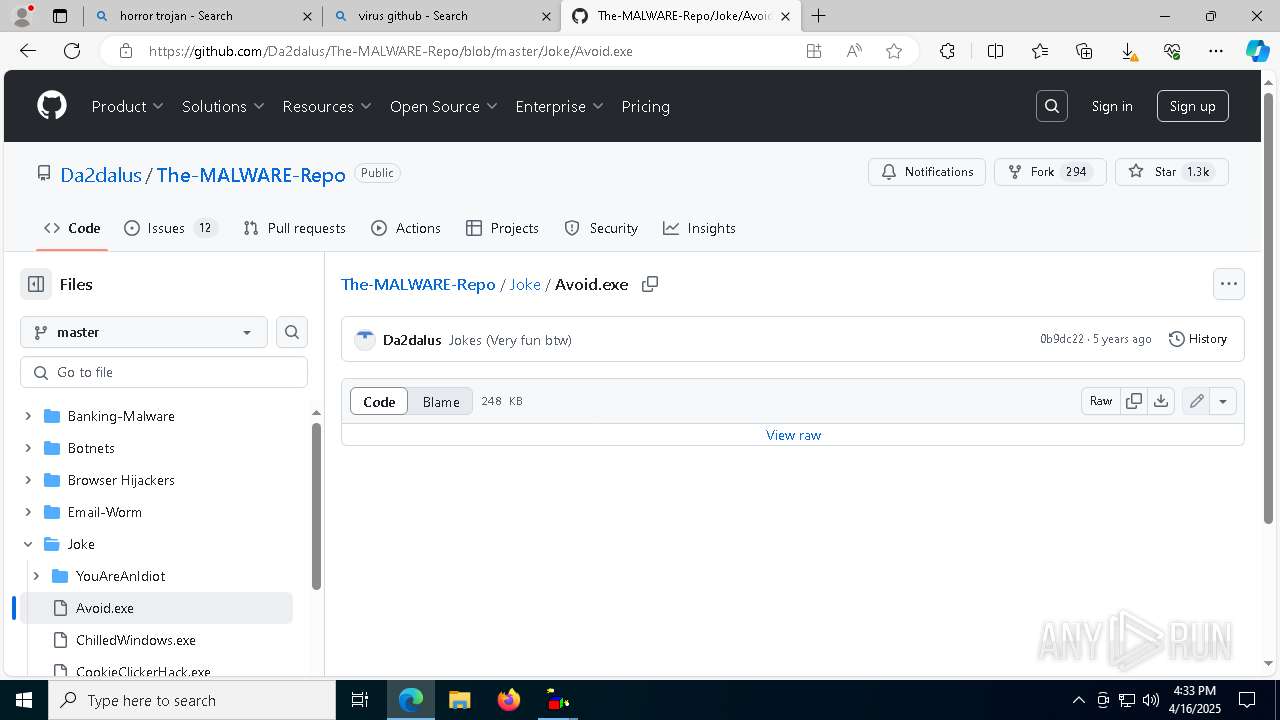
7560 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7560 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7560 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7560 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |