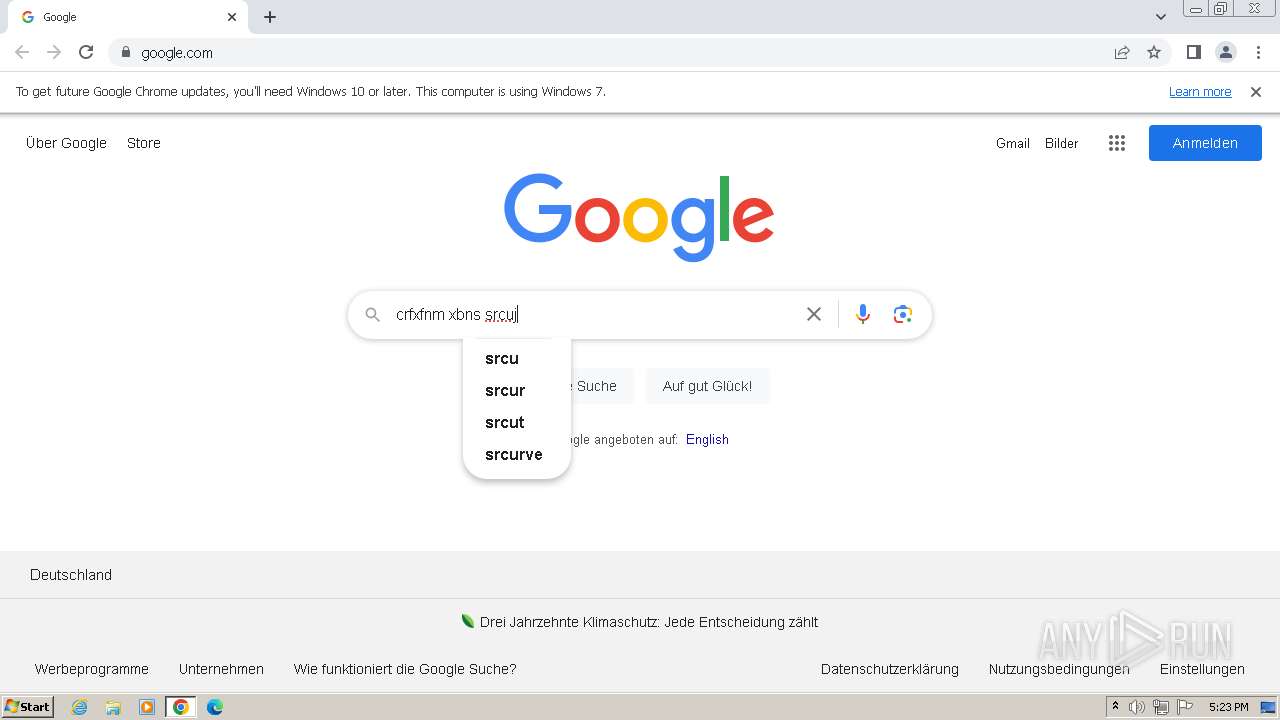
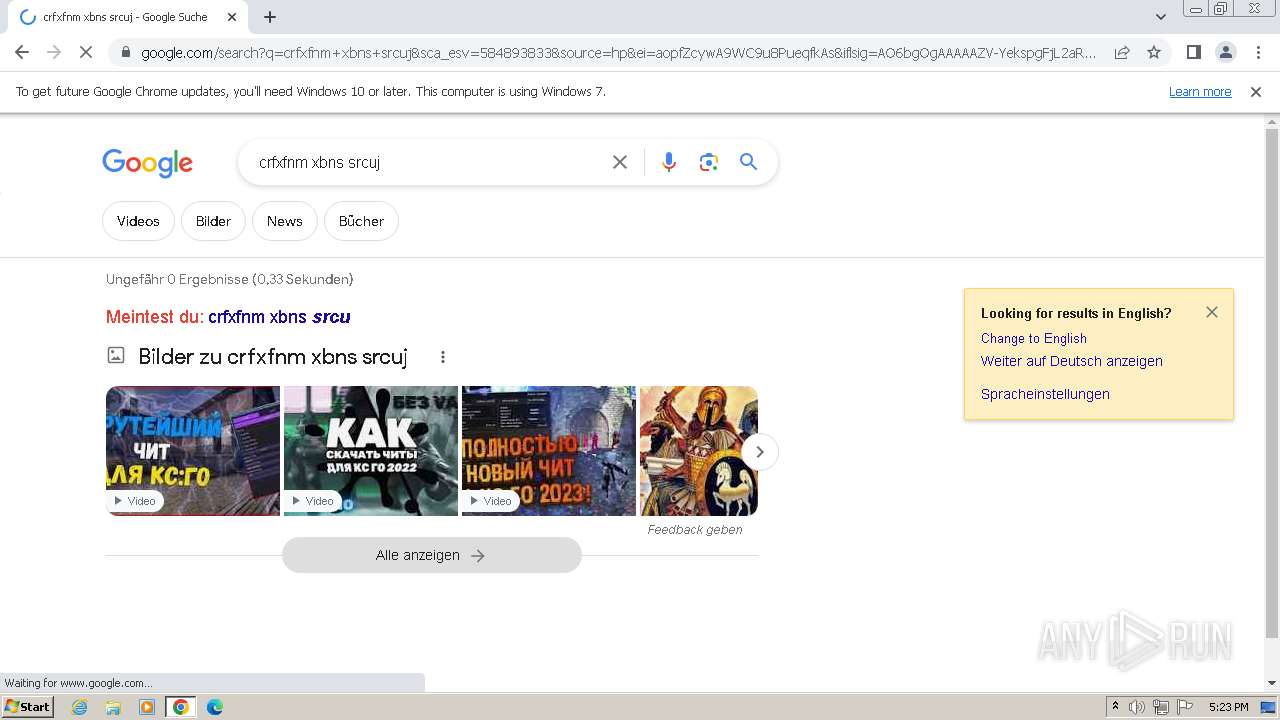
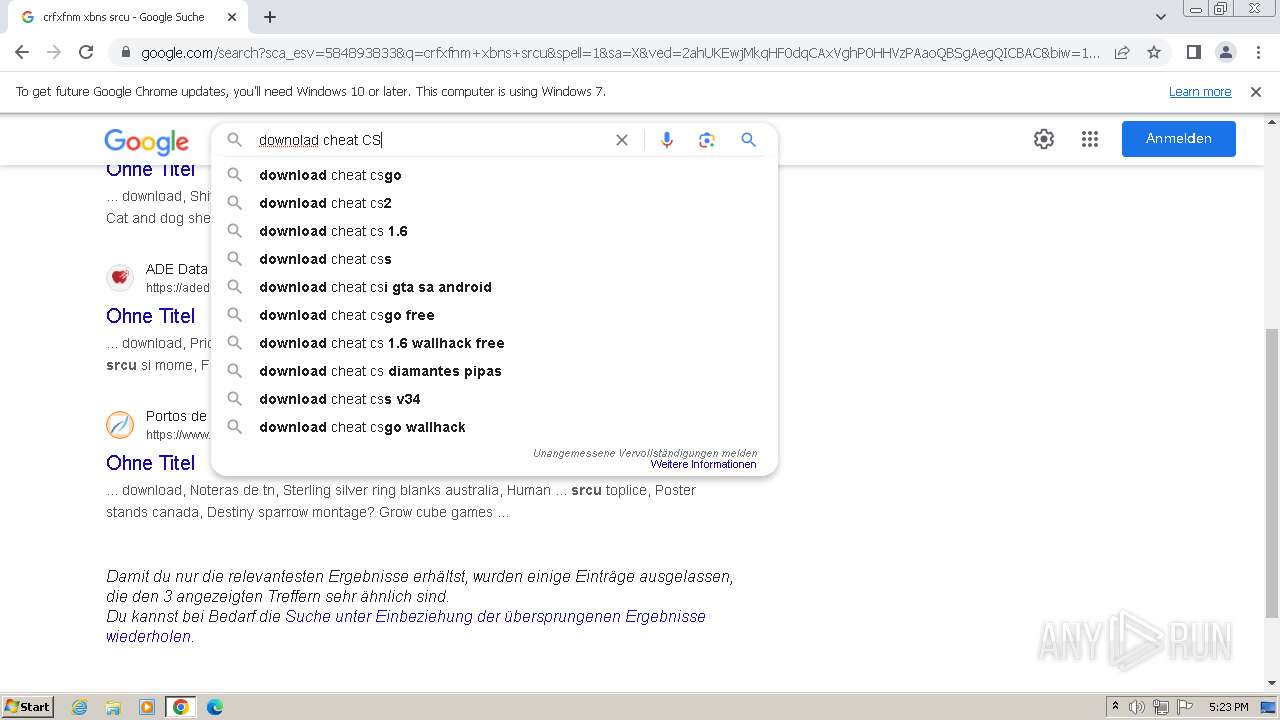
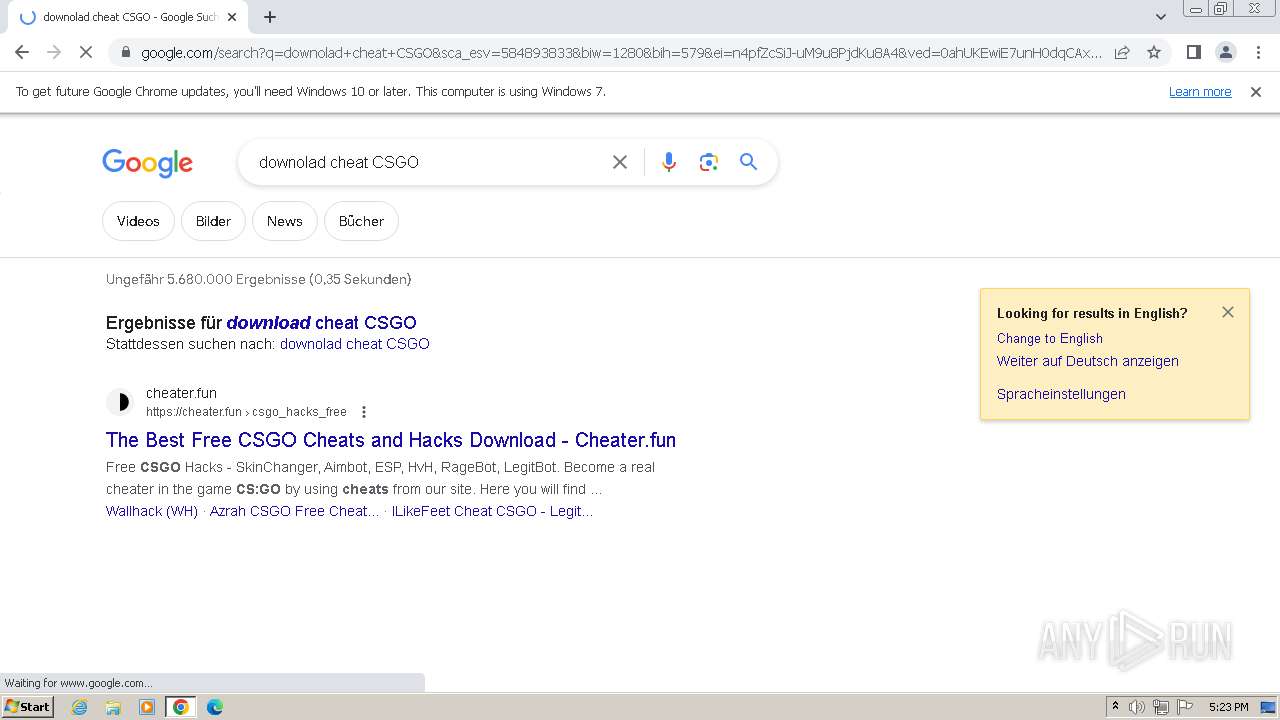
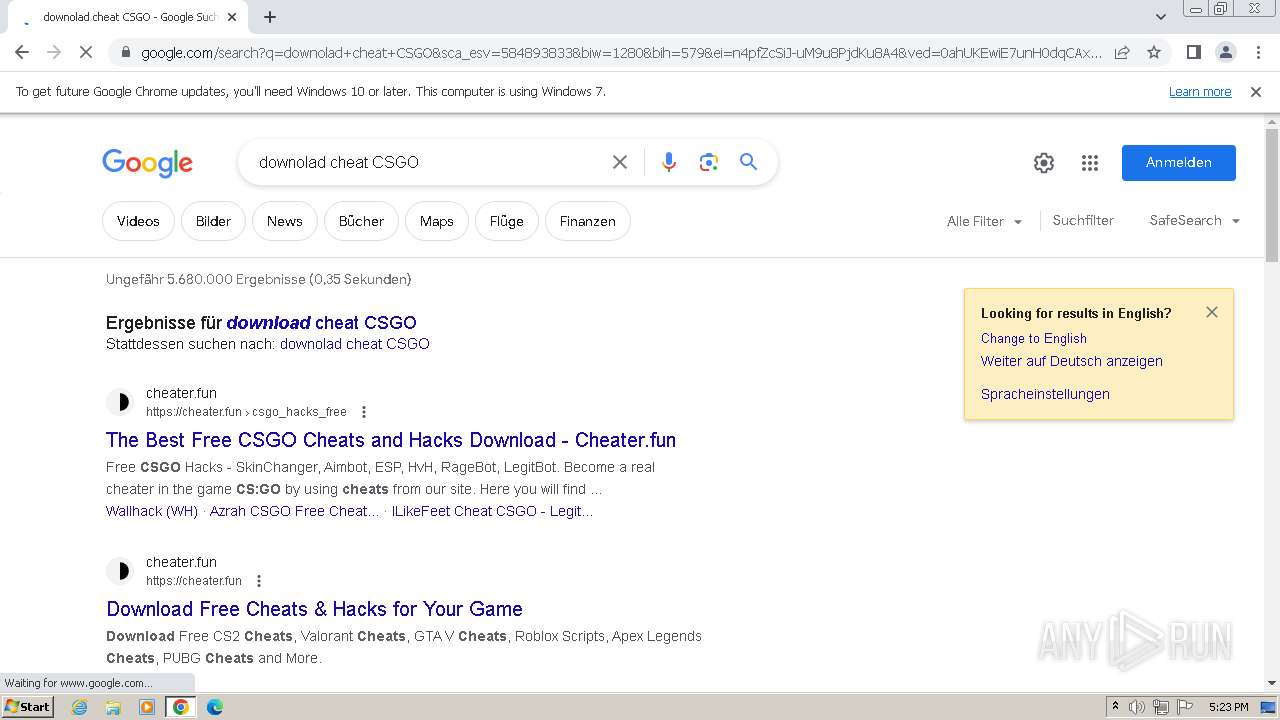
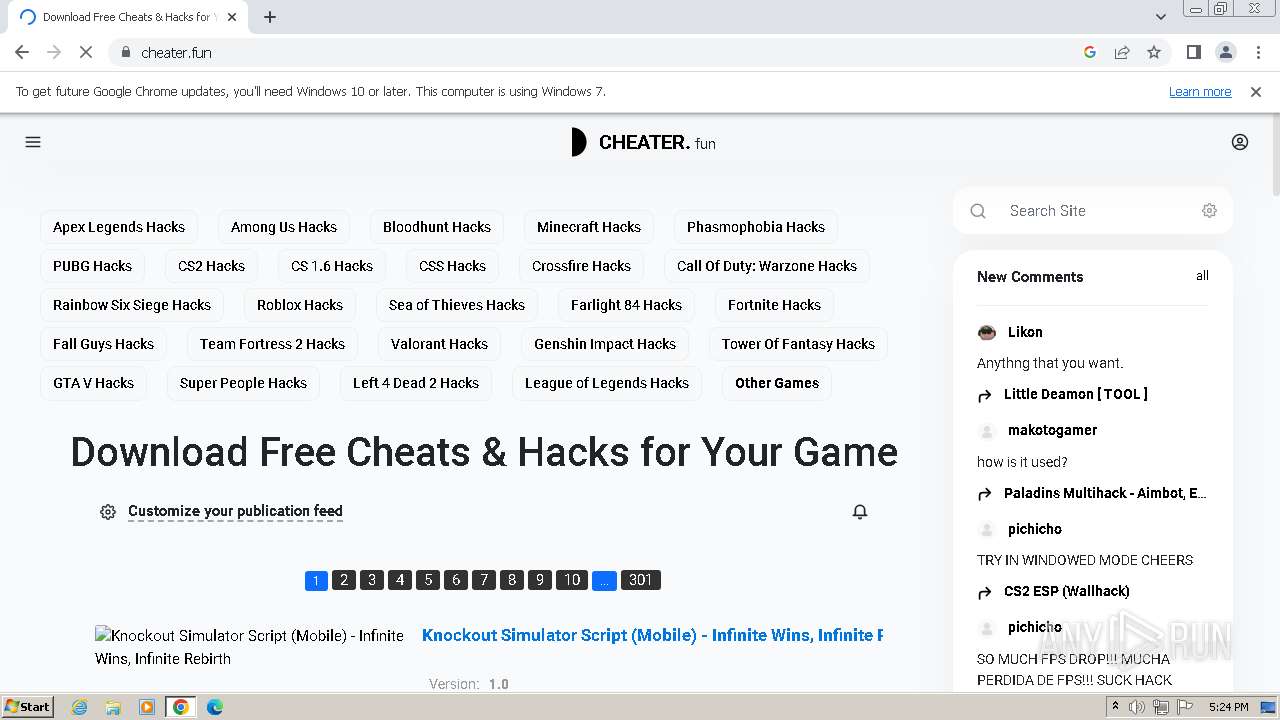
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/e944eab0-dbc9-48c6-97be-9ba170206652 |
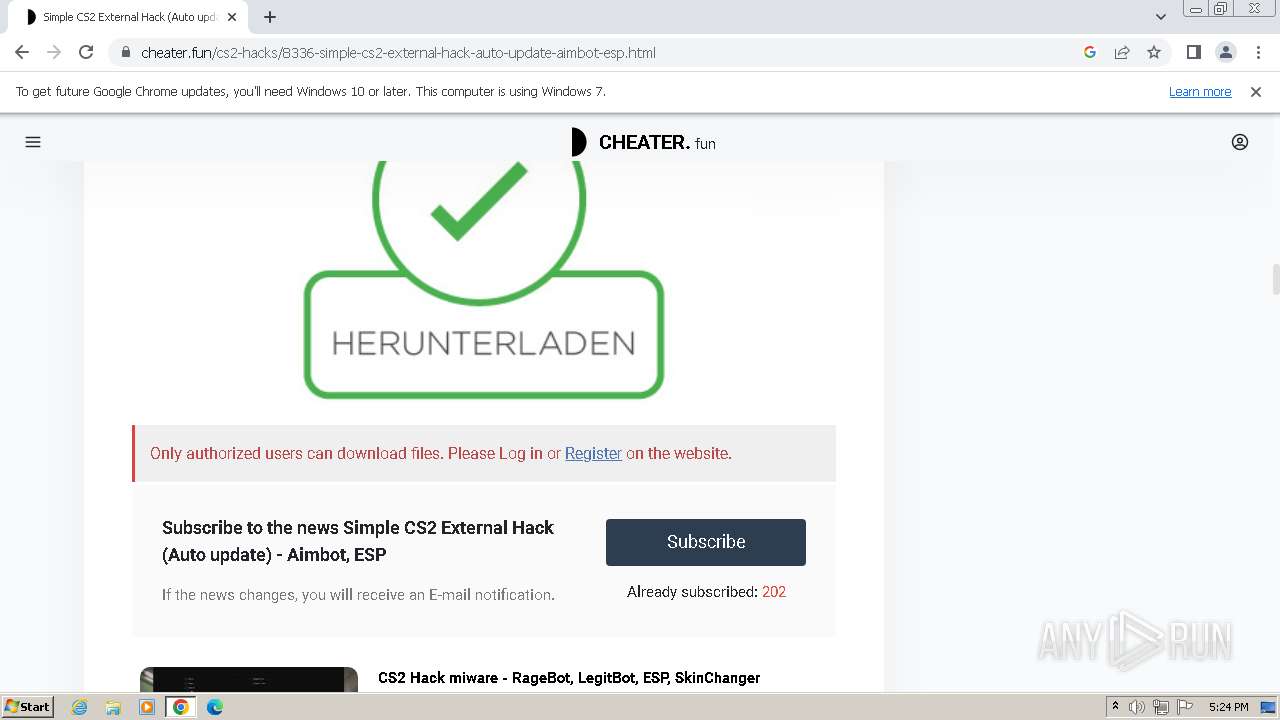
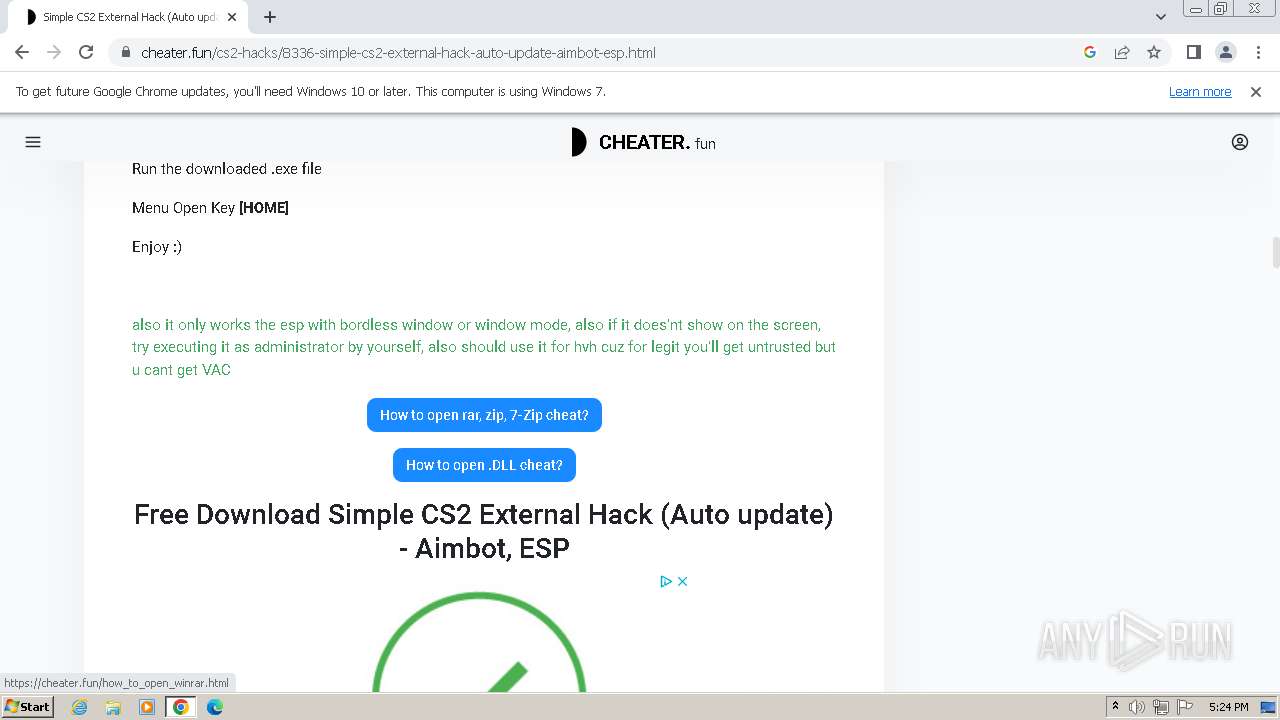
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 17:22:41 |
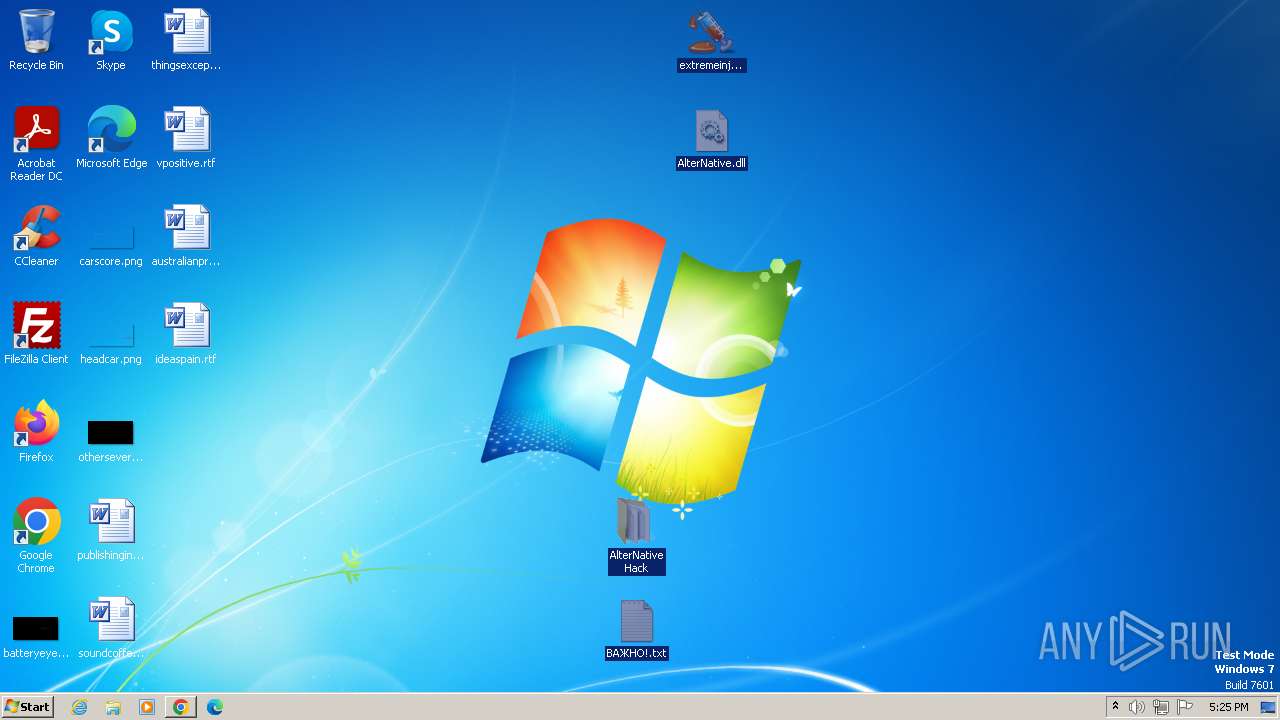
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
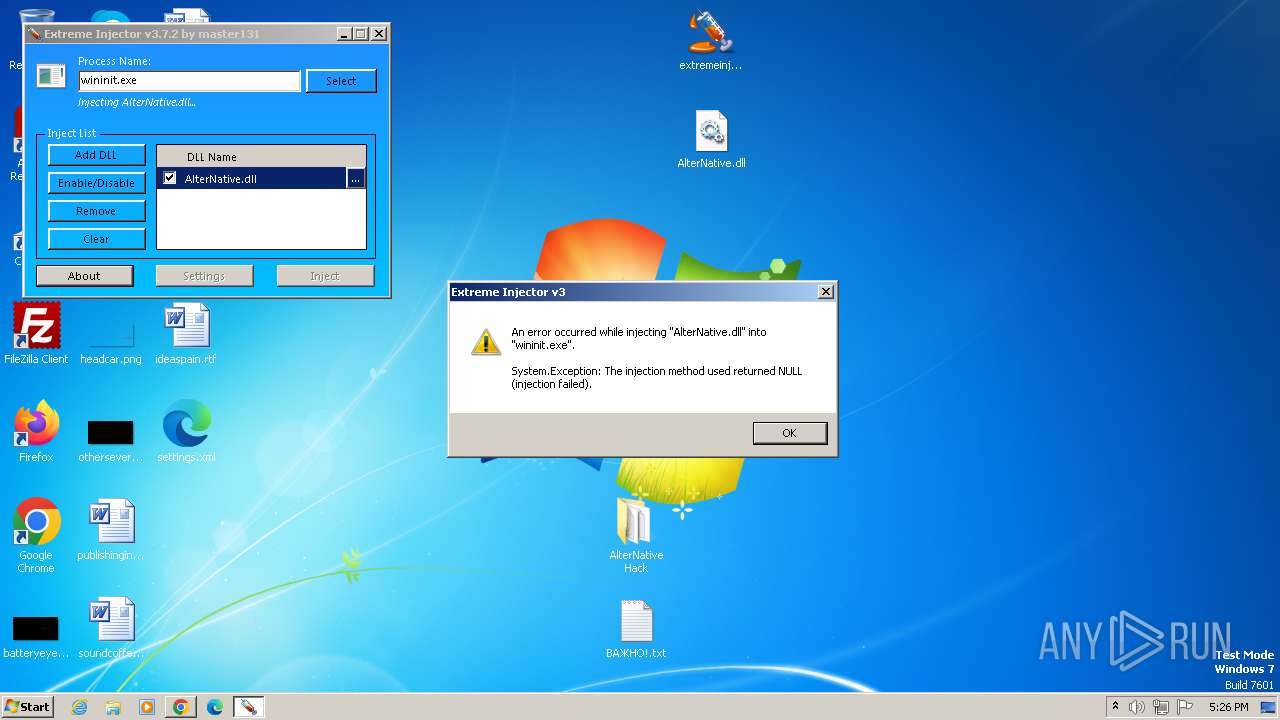
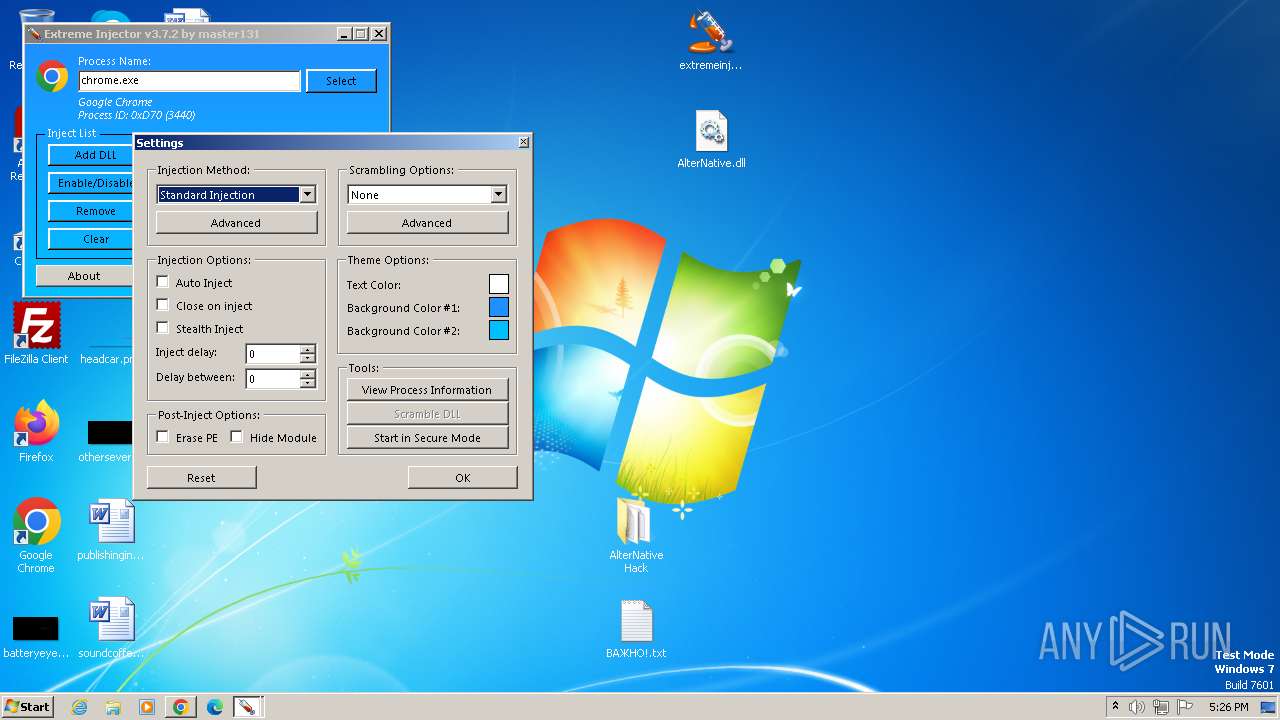
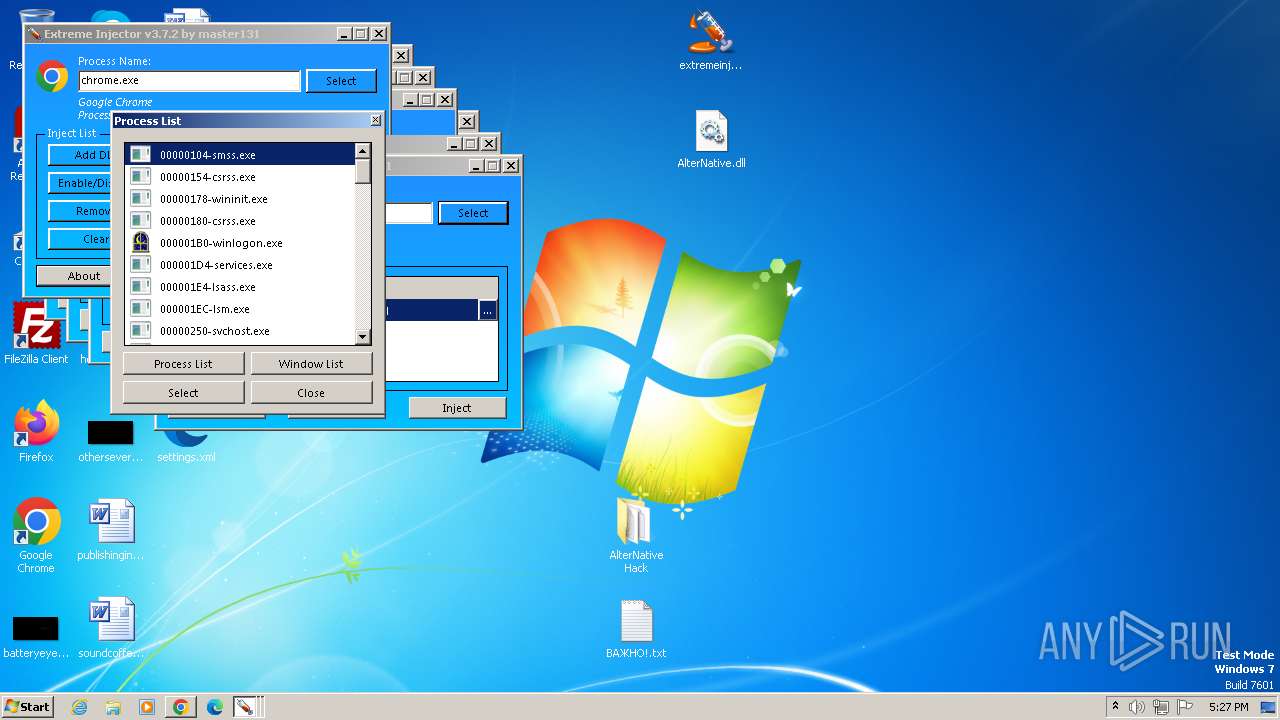
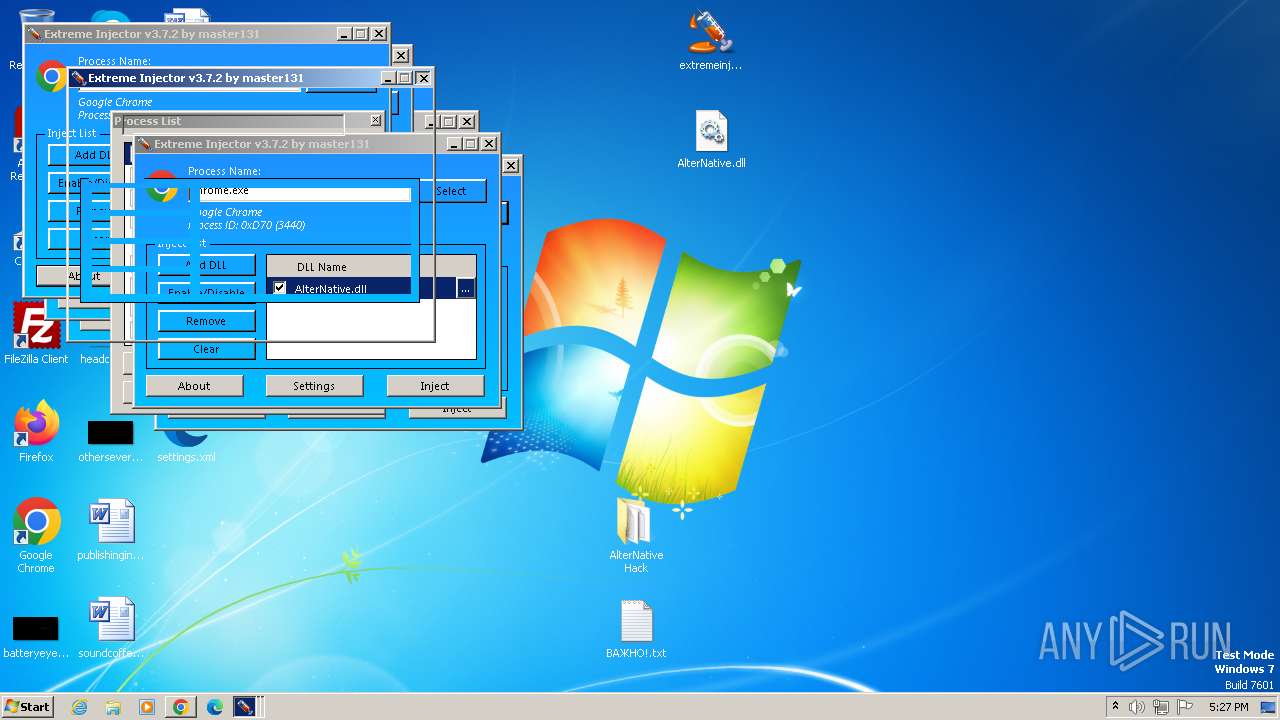
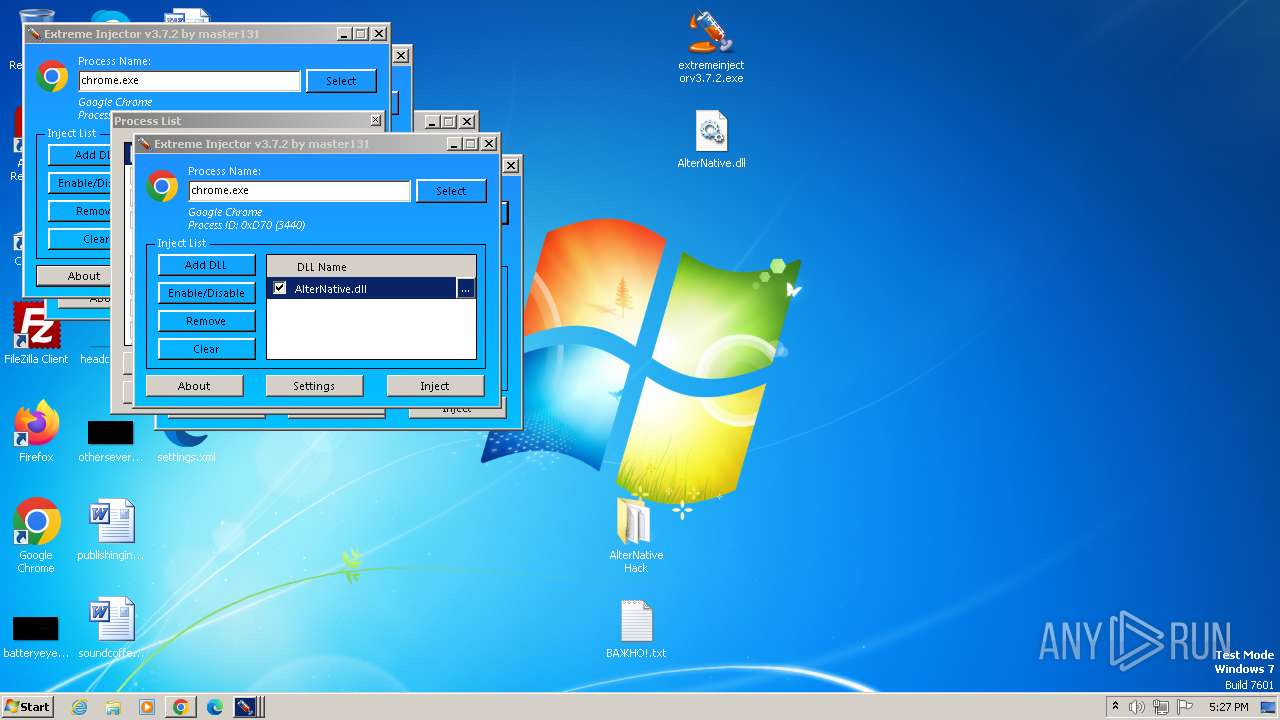
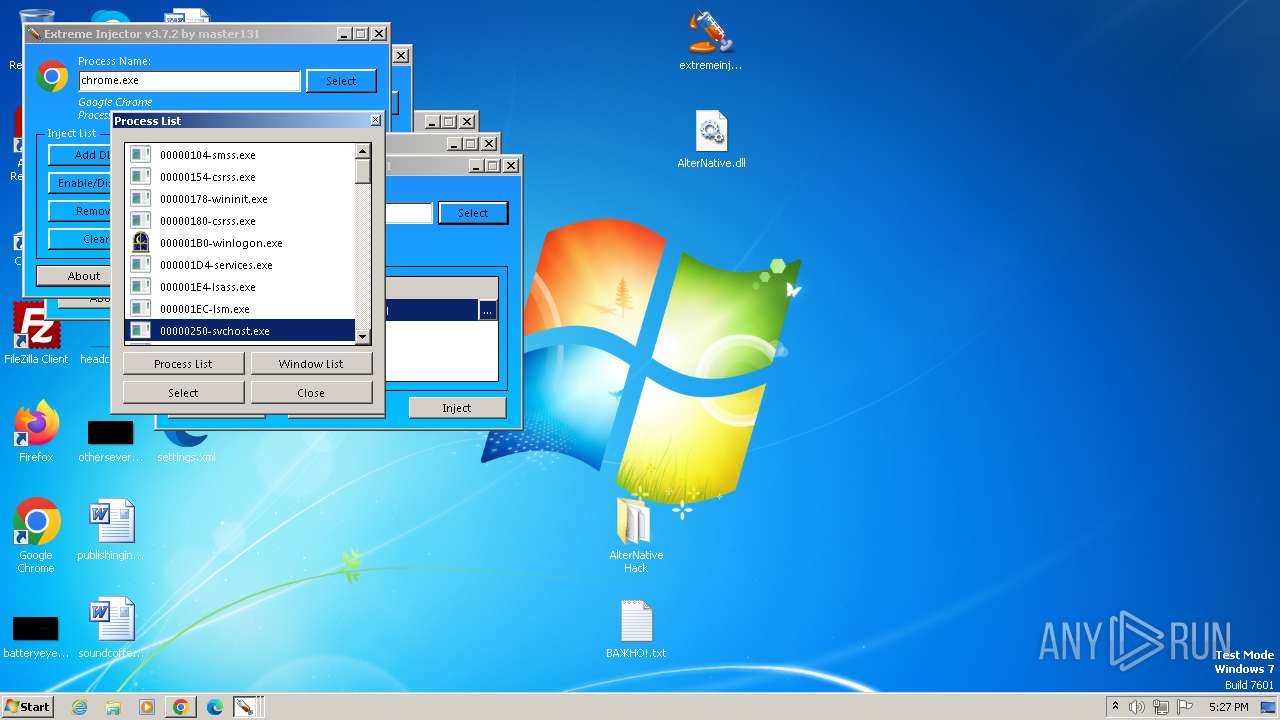
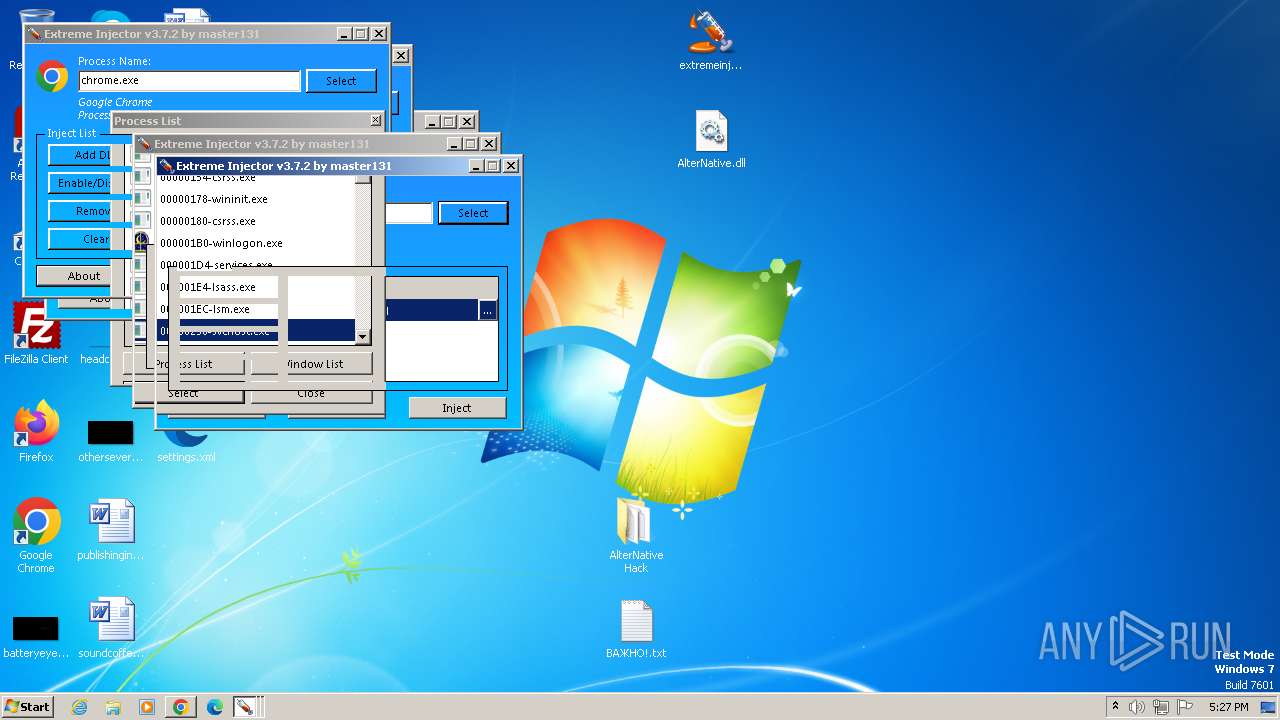
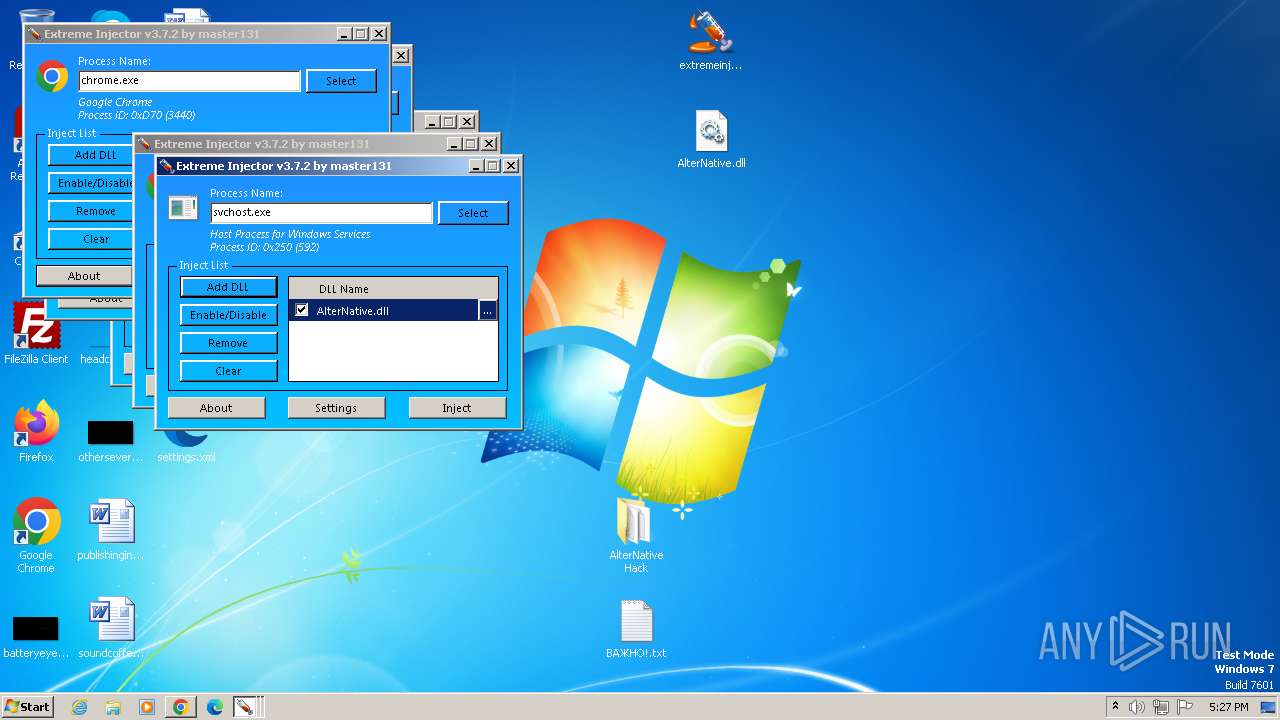
MALICIOUS
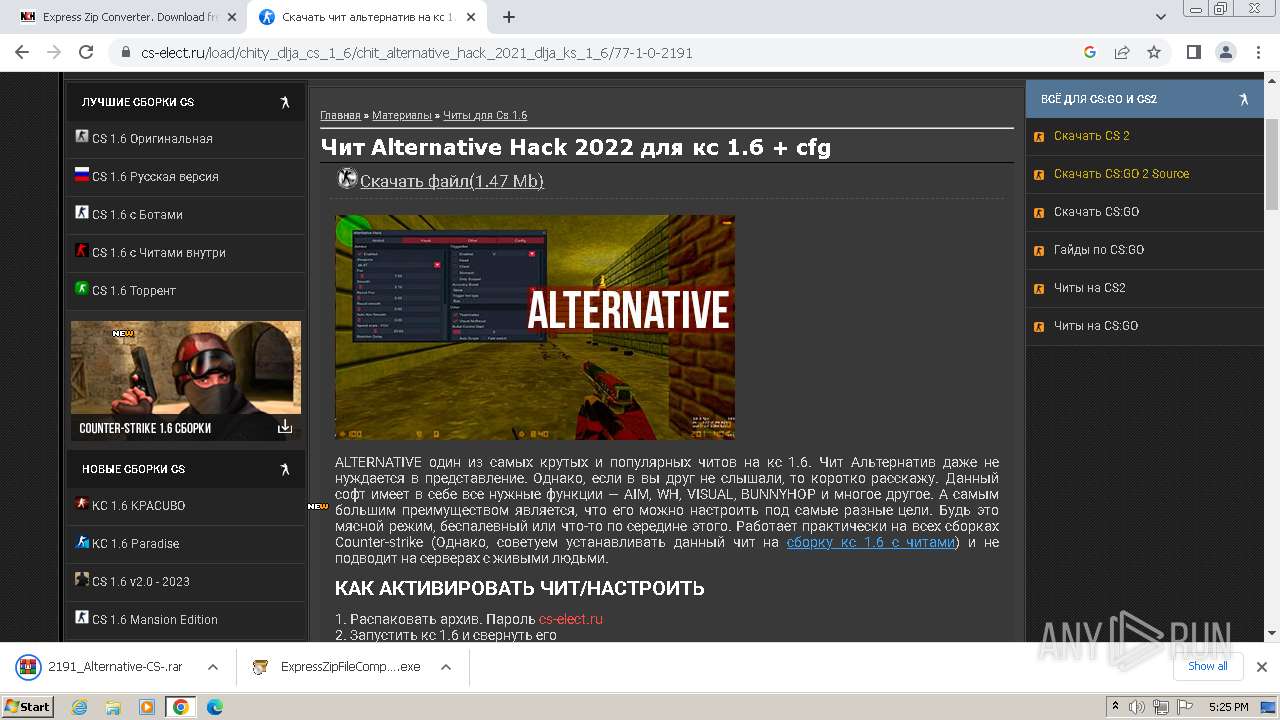
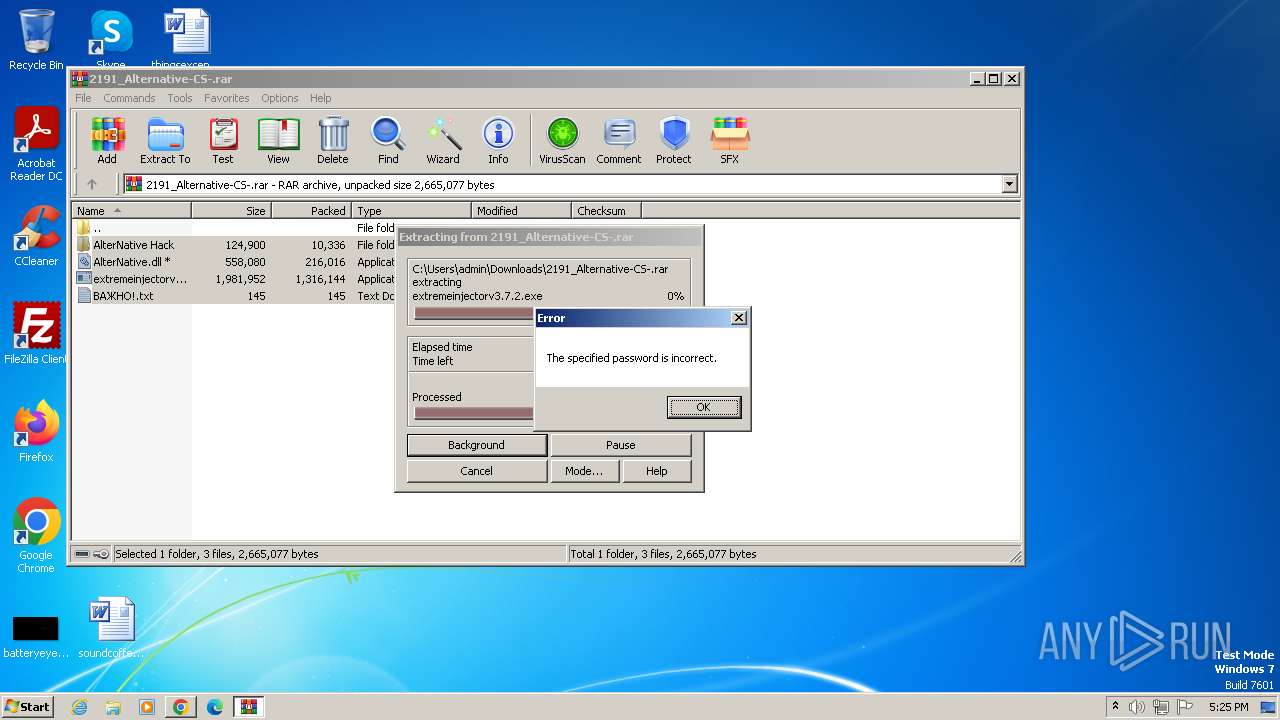
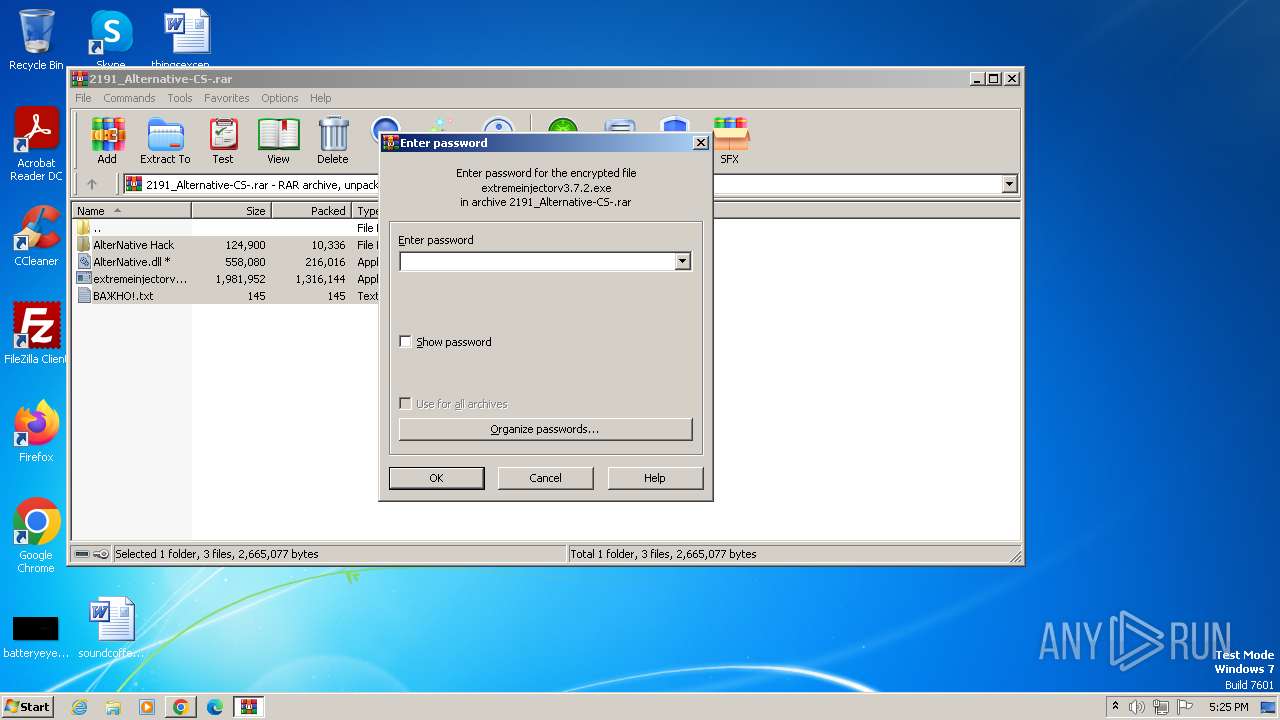
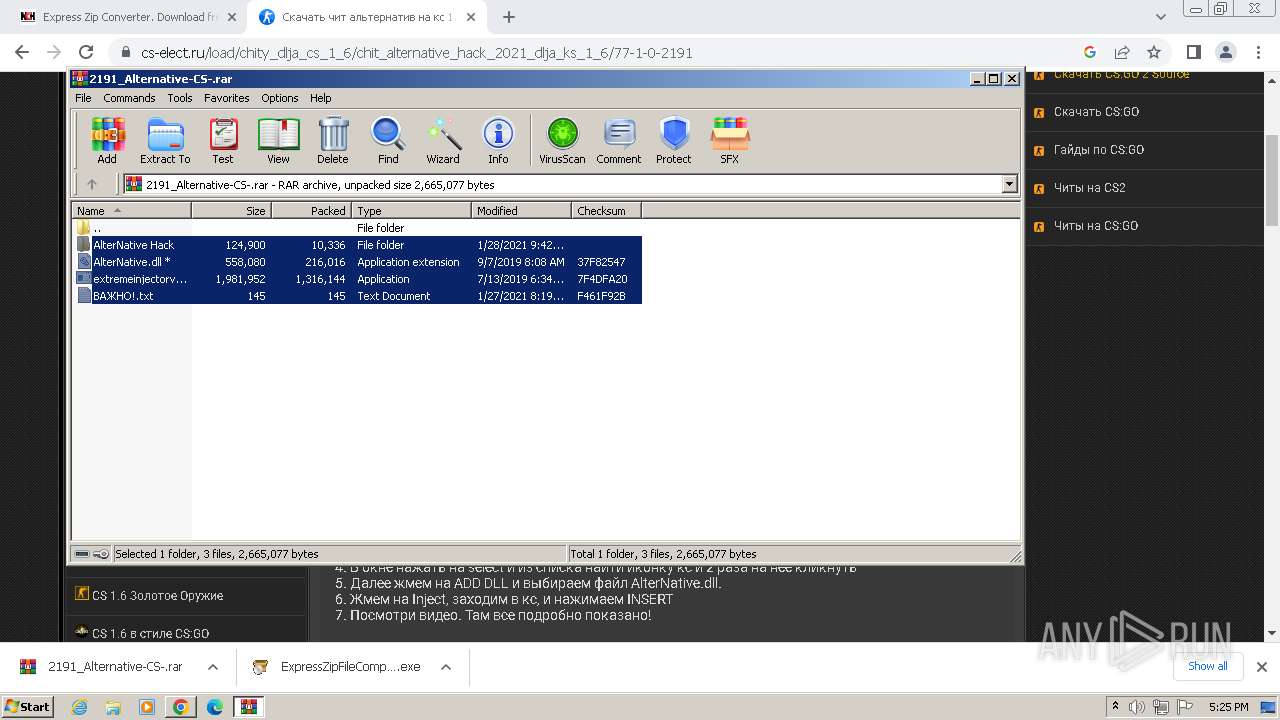
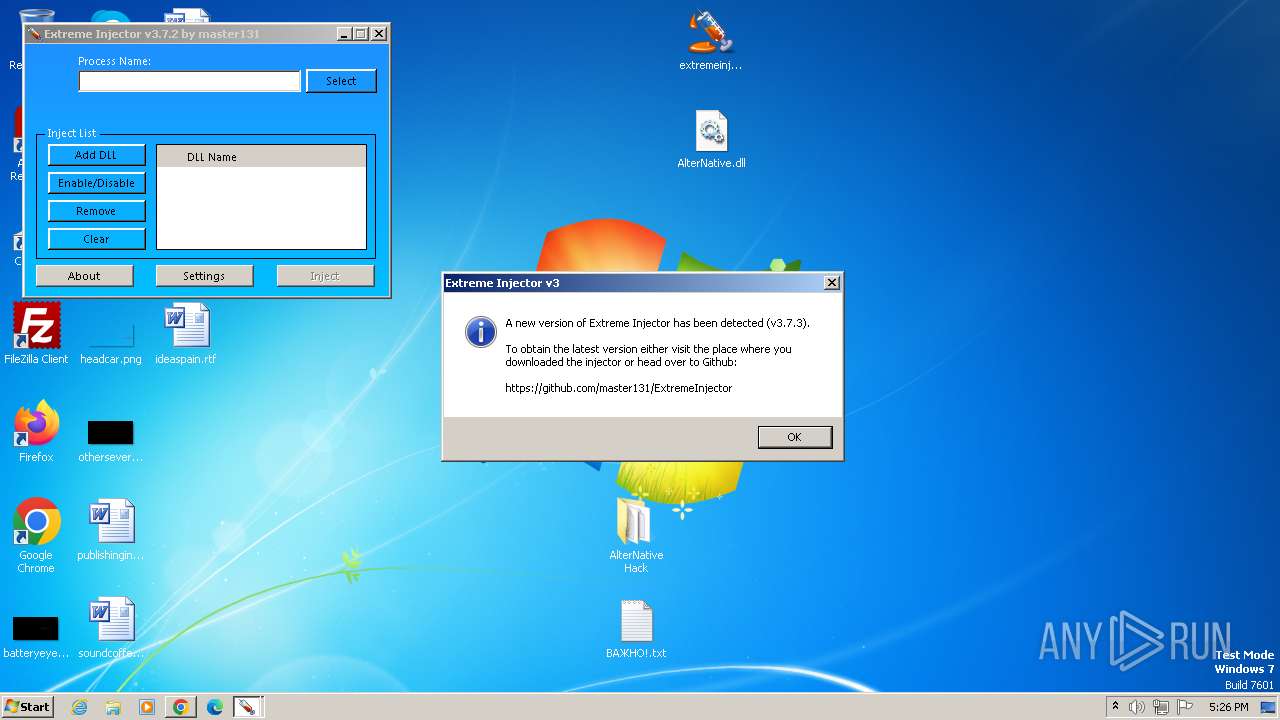
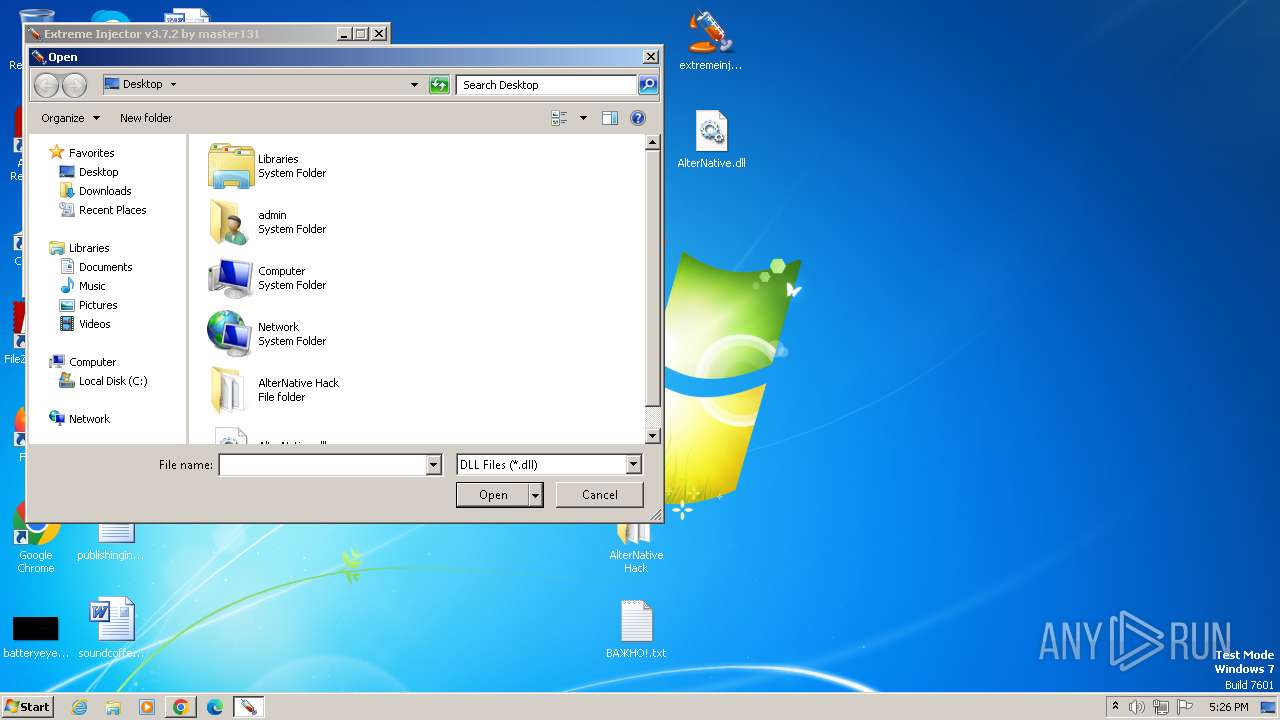
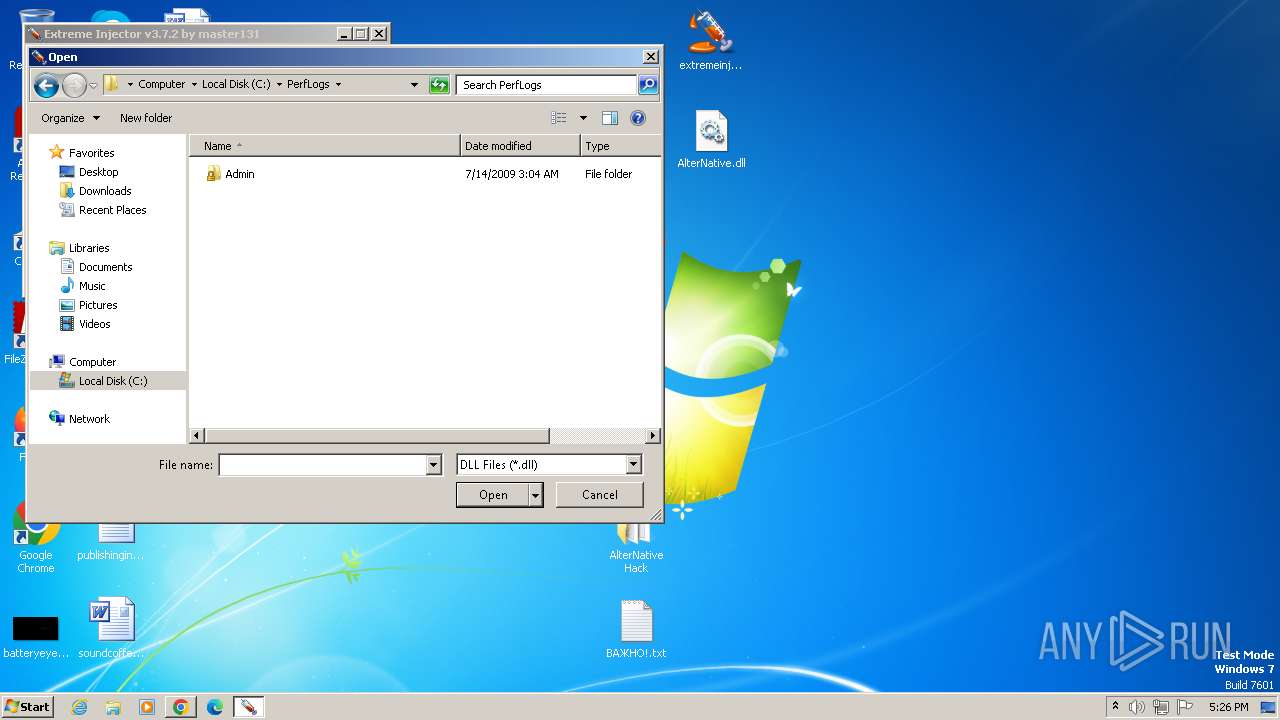
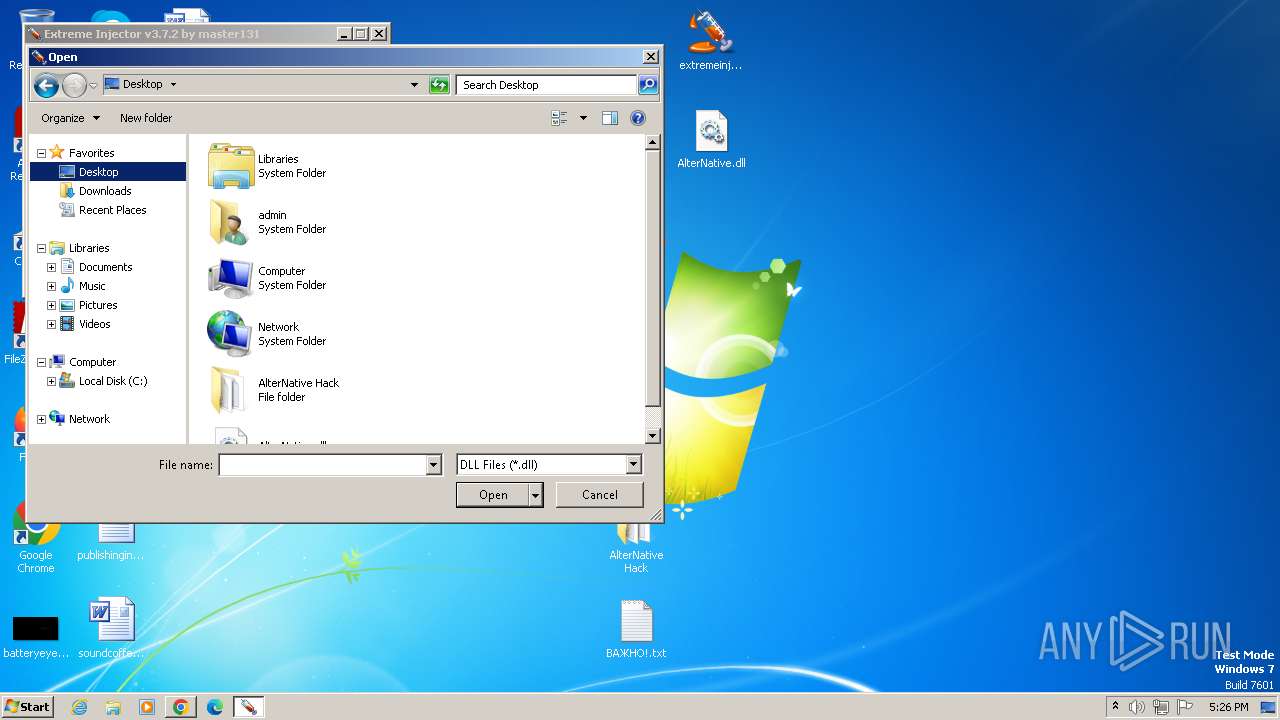
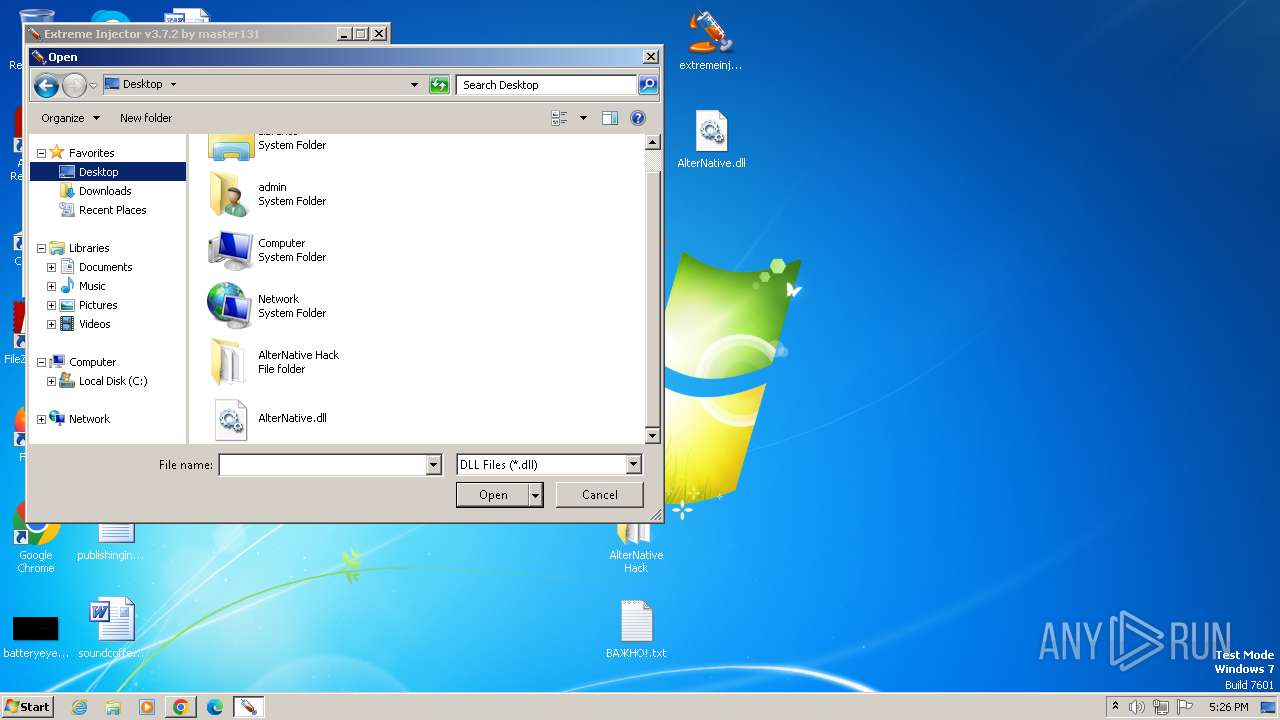
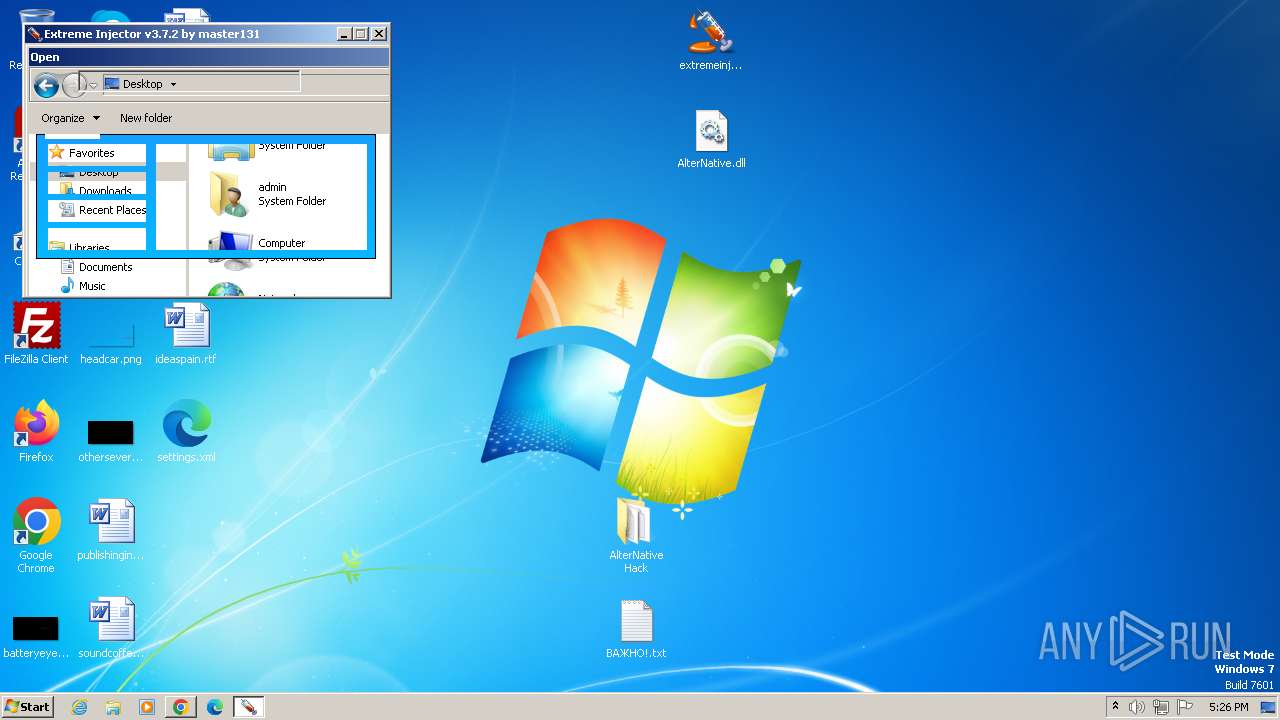
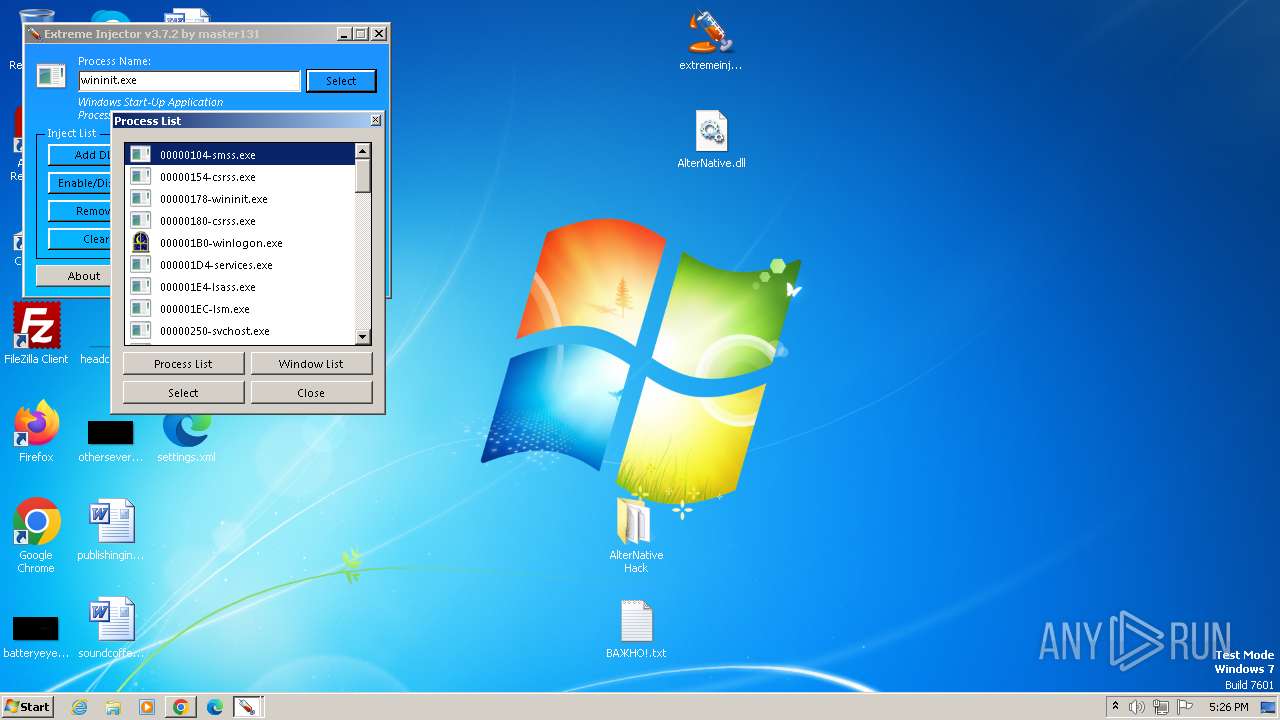
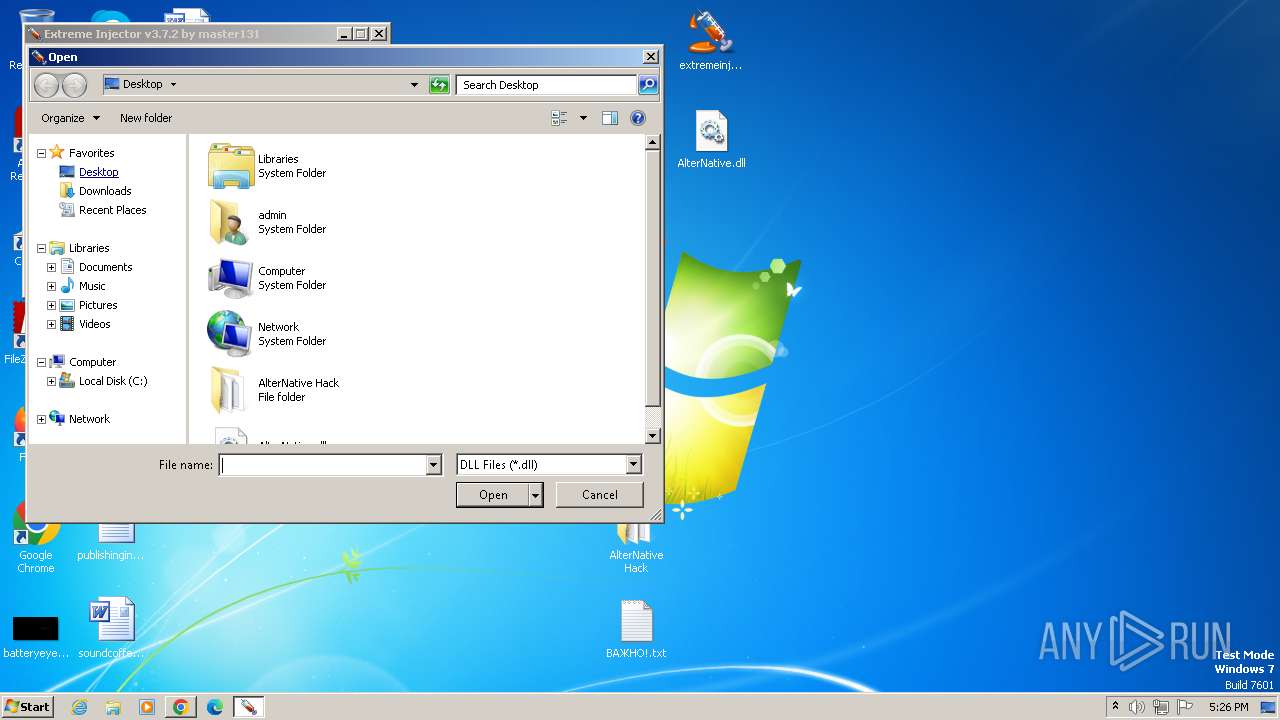
Runs injected code in another process
- extremeinjectorv3.7.2.exe (PID: 3500)
Application was injected by another process
- wininit.exe (PID: 376)
SUSPICIOUS
Reads the Internet Settings
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 3500)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 2628)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 680)
Application launched itself
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 2628)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 680)
Reads Internet Explorer settings
- extremeinjectorv3.7.2.exe (PID: 3500)
Reads settings of System Certificates
- extremeinjectorv3.7.2.exe (PID: 3500)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3700)
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 3500)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 3120)
- extremeinjectorv3.7.2.exe (PID: 2144)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3148)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 1892)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2496)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 664)
- extremeinjectorv3.7.2.exe (PID: 2628)
- extremeinjectorv3.7.2.exe (PID: 1880)
- extremeinjectorv3.7.2.exe (PID: 2864)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3704)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 2308)
- extremeinjectorv3.7.2.exe (PID: 680)
- extremeinjectorv3.7.2.exe (PID: 2632)
- extremeinjectorv3.7.2.exe (PID: 284)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3700)
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 3500)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 3120)
- extremeinjectorv3.7.2.exe (PID: 2144)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3148)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 1892)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2496)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 664)
- extremeinjectorv3.7.2.exe (PID: 2628)
- extremeinjectorv3.7.2.exe (PID: 2864)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 1880)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3704)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 680)
- extremeinjectorv3.7.2.exe (PID: 2308)
- extremeinjectorv3.7.2.exe (PID: 2632)
- extremeinjectorv3.7.2.exe (PID: 284)
Reads the computer name
- wmpnscfg.exe (PID: 3700)
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 3500)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 3120)
- extremeinjectorv3.7.2.exe (PID: 2144)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3148)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 2496)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 664)
- extremeinjectorv3.7.2.exe (PID: 1892)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2628)
- extremeinjectorv3.7.2.exe (PID: 1880)
- extremeinjectorv3.7.2.exe (PID: 2864)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3704)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 2308)
- extremeinjectorv3.7.2.exe (PID: 680)
- extremeinjectorv3.7.2.exe (PID: 2632)
- extremeinjectorv3.7.2.exe (PID: 284)
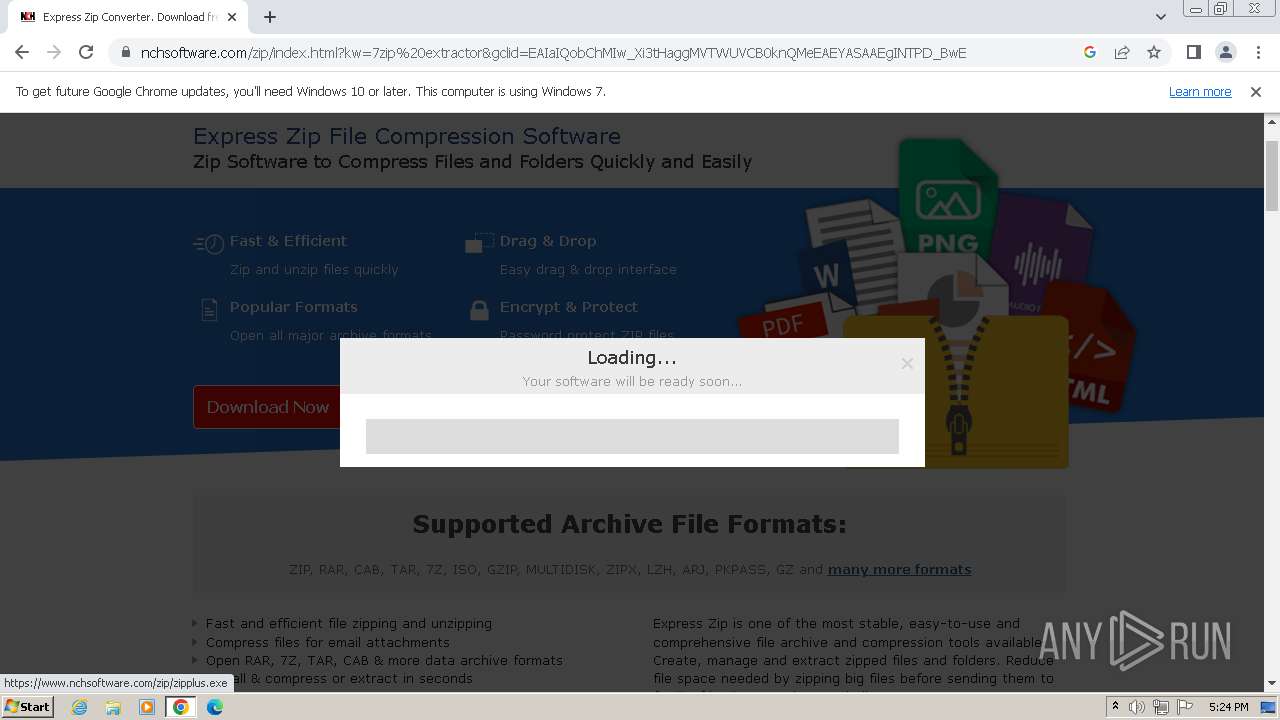
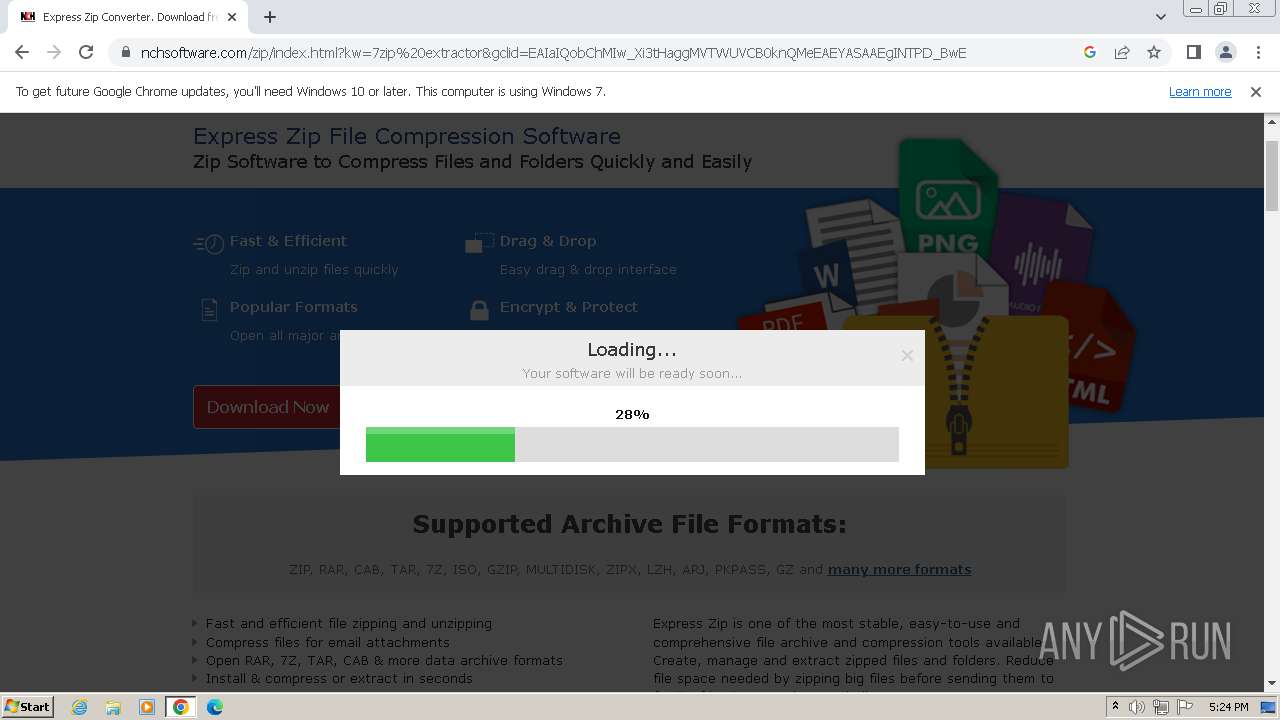
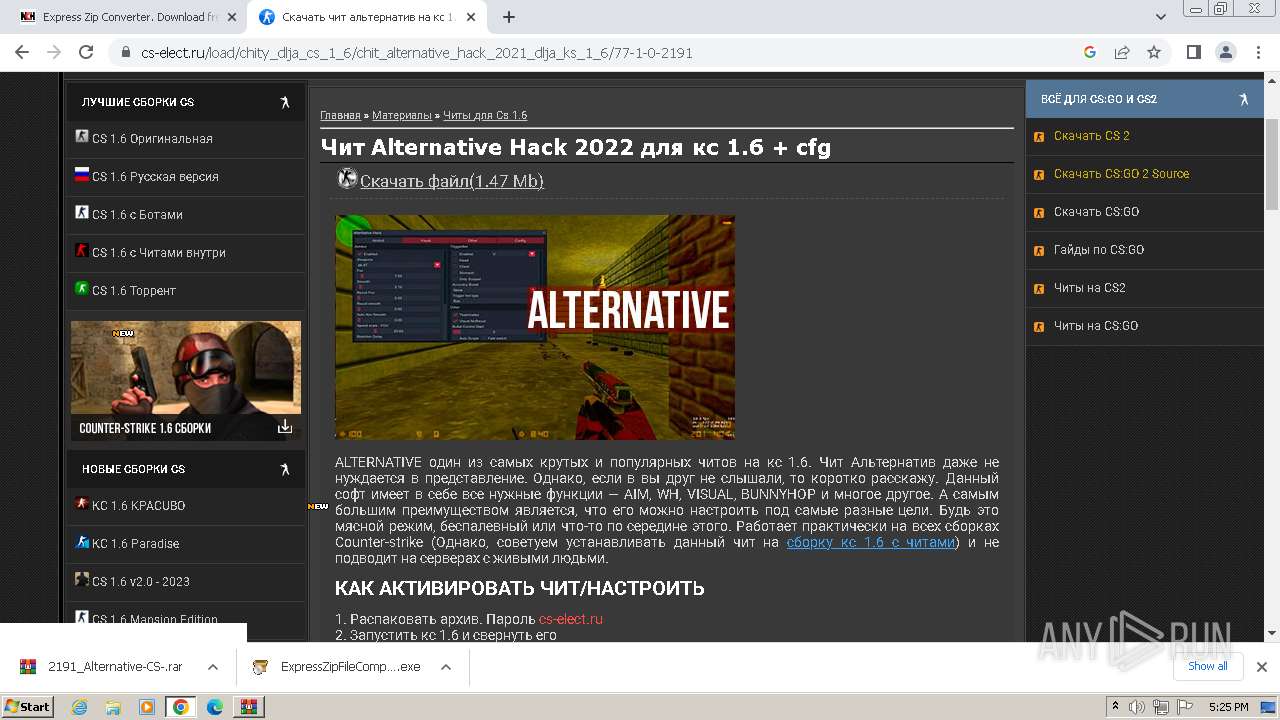
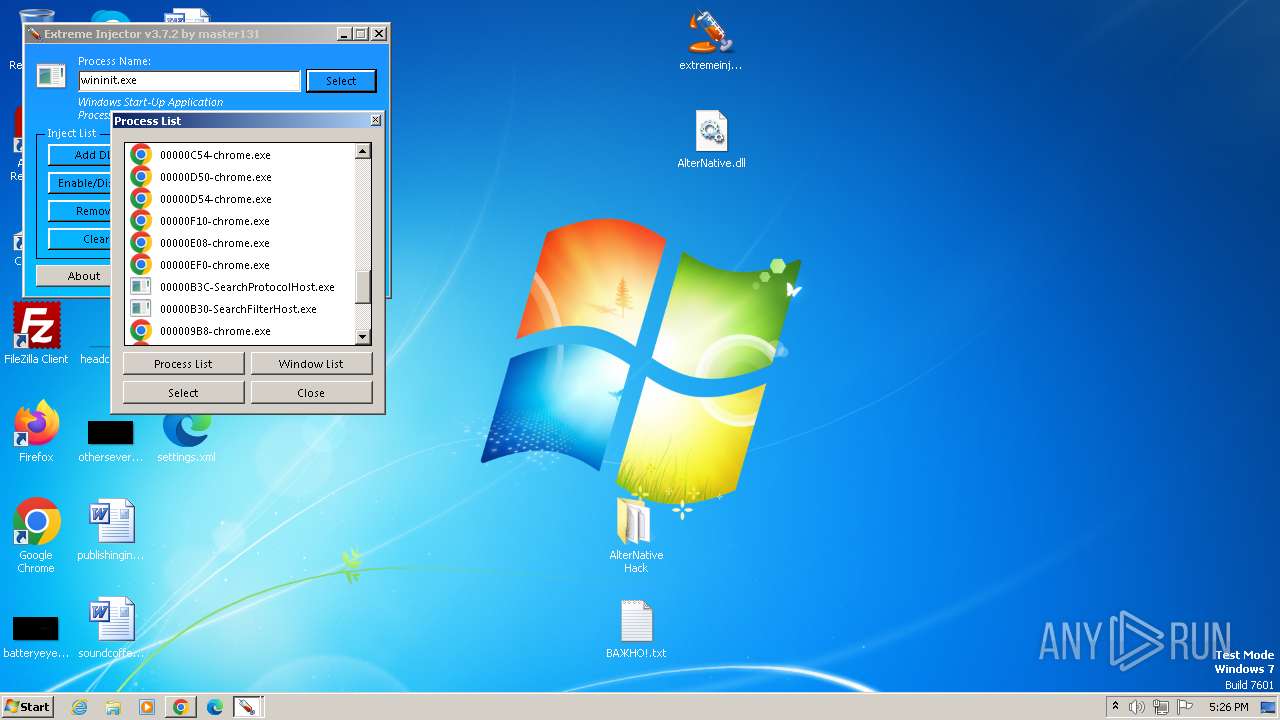
The process uses the downloaded file
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 1808)
- WinRAR.exe (PID: 3476)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 1352)
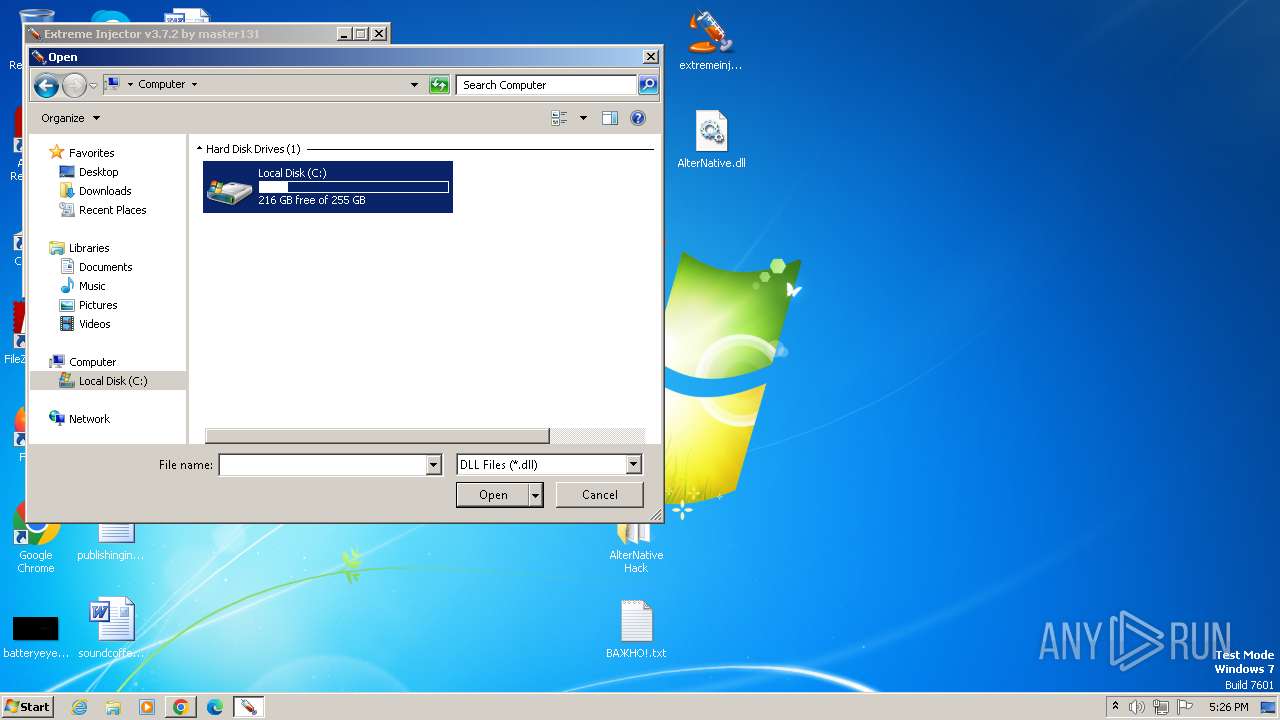
Manual execution by a user
- wmpnscfg.exe (PID: 3700)
- extremeinjectorv3.7.2.exe (PID: 2460)
- extremeinjectorv3.7.2.exe (PID: 4080)
- extremeinjectorv3.7.2.exe (PID: 2028)
- extremeinjectorv3.7.2.exe (PID: 1436)
- extremeinjectorv3.7.2.exe (PID: 1576)
- extremeinjectorv3.7.2.exe (PID: 3316)
- extremeinjectorv3.7.2.exe (PID: 1528)
- extremeinjectorv3.7.2.exe (PID: 2108)
- extremeinjectorv3.7.2.exe (PID: 4088)
- extremeinjectorv3.7.2.exe (PID: 2164)
- extremeinjectorv3.7.2.exe (PID: 3904)
- extremeinjectorv3.7.2.exe (PID: 680)
- extremeinjectorv3.7.2.exe (PID: 2628)
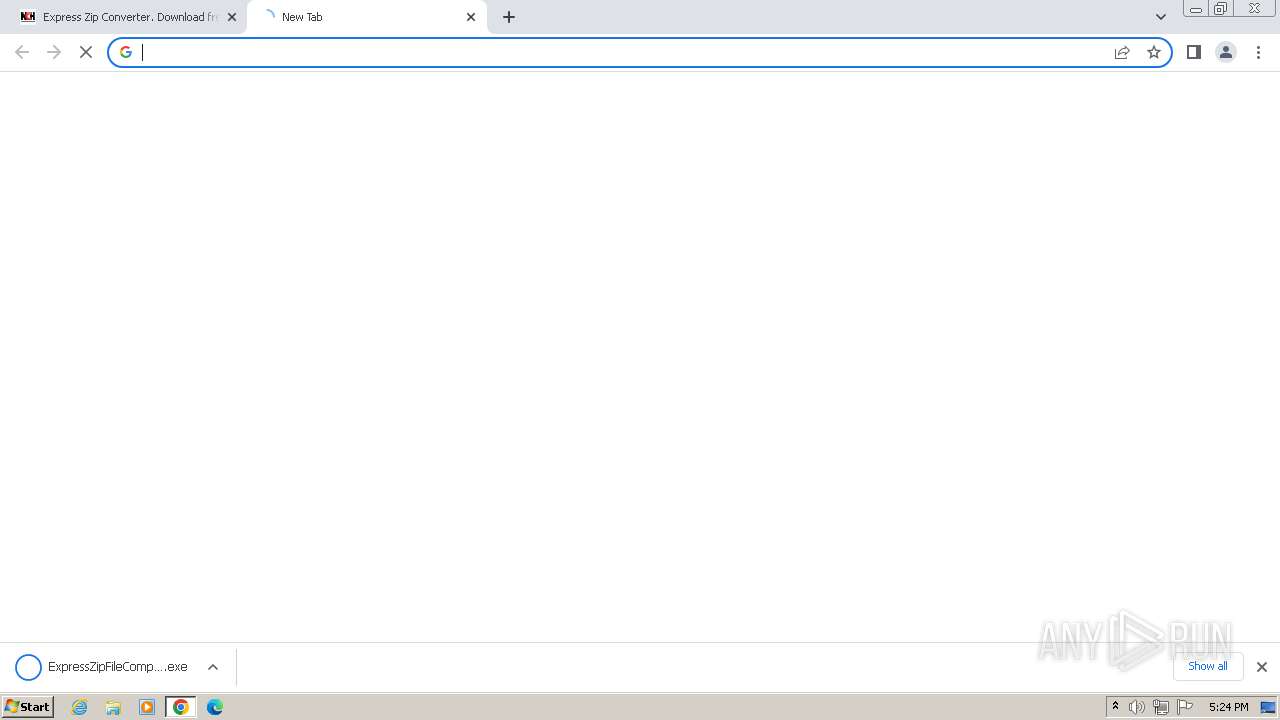
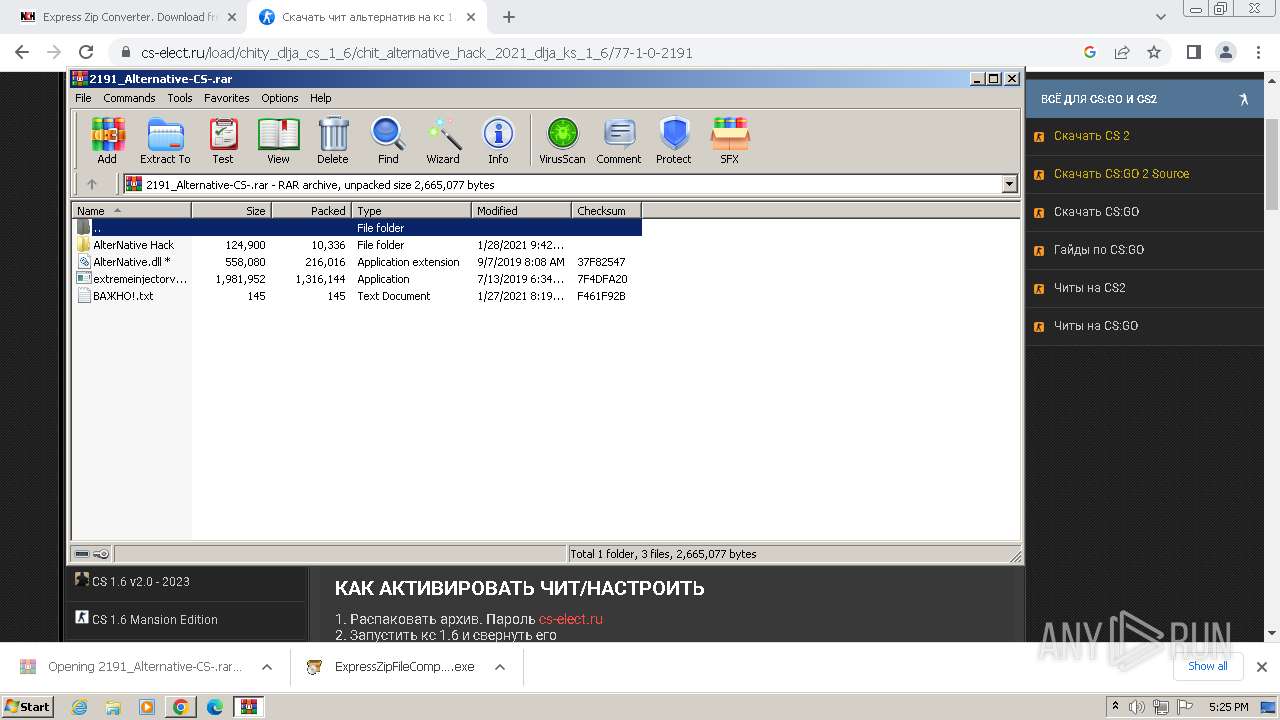
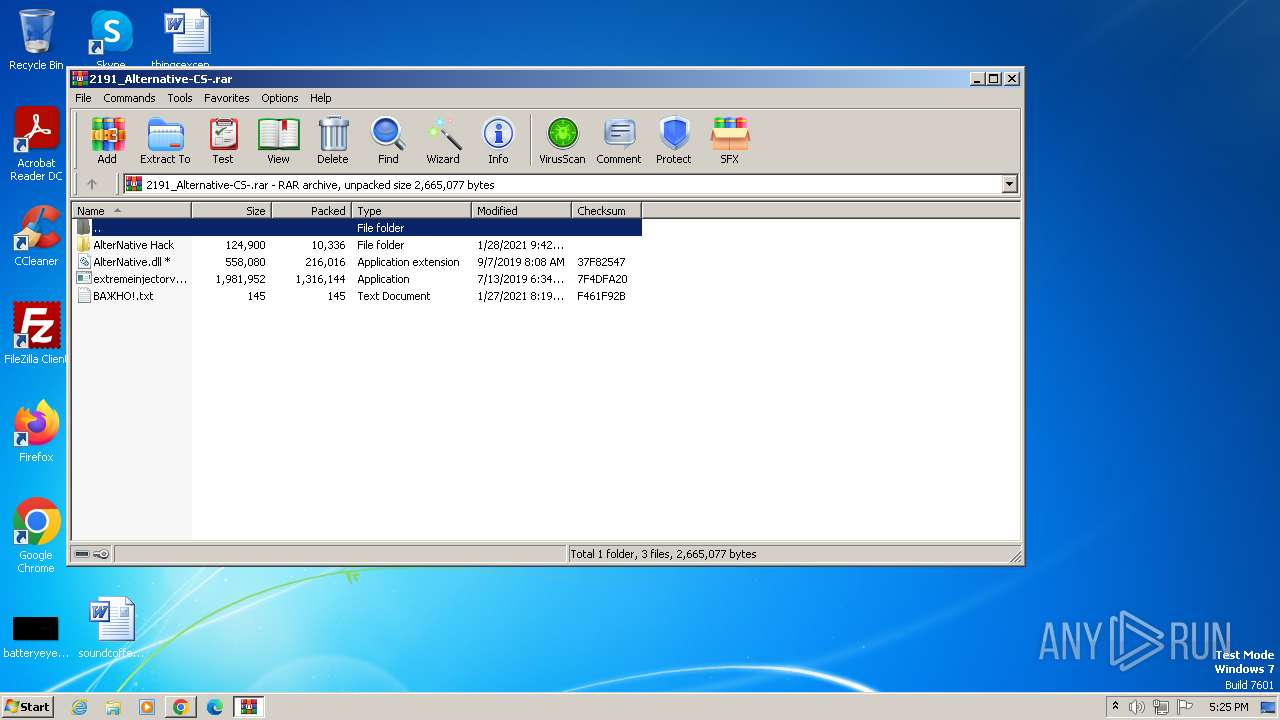
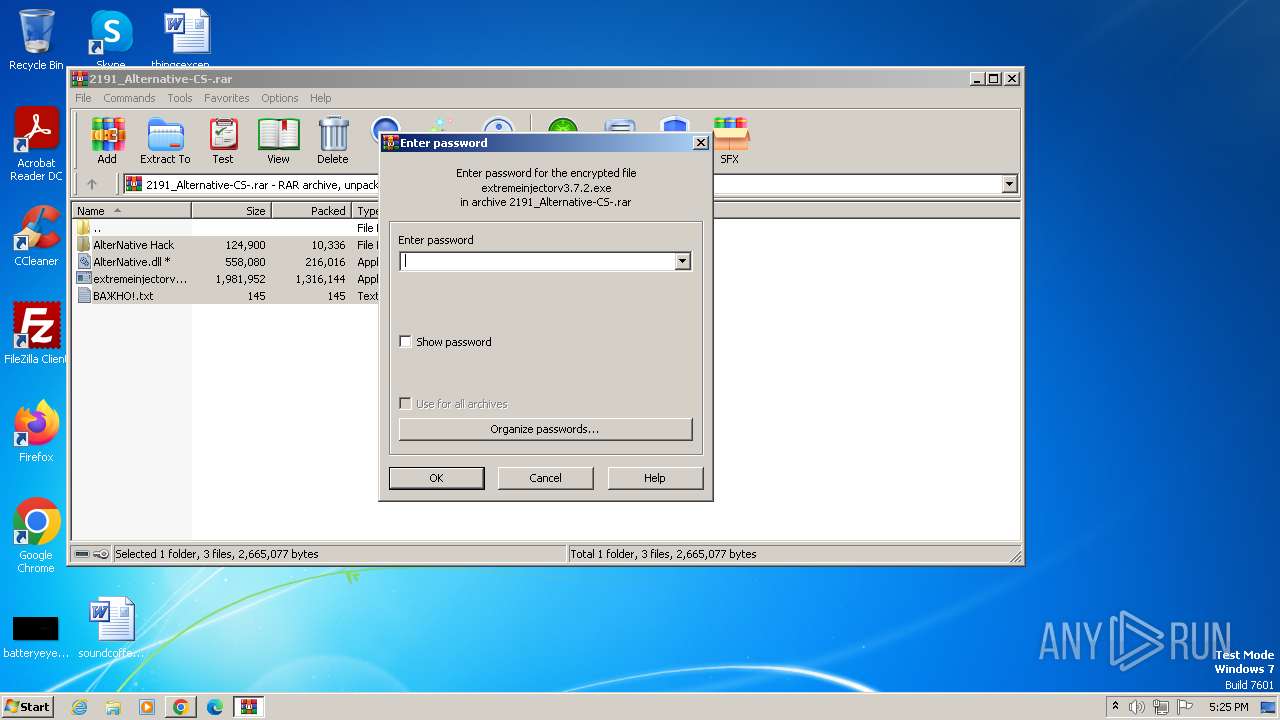
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3476)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2448)
Application launched itself
- chrome.exe (PID: 3440)
Reads Environment values
- extremeinjectorv3.7.2.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
78
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=3572 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3280 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 284 | "C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe" | C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe | extremeinjectorv3.7.2.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Exit code: 0 Version: 3.7.2.0 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=1368 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 376 | wininit.exe | C:\Windows\System32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=608 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe" | C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe | extremeinjectorv3.7.2.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Exit code: 0 Version: 3.7.2.0 Modules
| |||||||||||||||
| 680 | "C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe" | C:\Users\admin\Desktop\extremeinjectorv3.7.2.exe | — | explorer.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.2.0 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=3044 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4388 --field-trial-handle=1160,i,405155622980348945,17309403731922007499,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
21 179
Read events
20 719
Write events
454
Delete events
6
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
16
Suspicious files
225
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF167331.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF167331.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1676fa.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF167525.TMP | text | |
MD5:56C75810BDDDD686D123E6E36F56E012 | SHA256:3D51A6EF85A51056E1A379D795F55C84A321EC2000DD69F5D70ABA038C61522E | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RF1686e8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
253
DNS requests
259
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 198 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 5.36 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.52 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.58 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.76 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 36.1 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.76 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 17.8 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 93.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3440 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3408 | chrome.exe | 142.250.185.196:443 | www.google.com | — | — | whitelisted |
3408 | chrome.exe | 142.250.185.173:443 | accounts.google.com | GOOGLE | US | unknown |
3408 | chrome.exe | 142.250.186.174:443 | google.com | GOOGLE | US | whitelisted |
3408 | chrome.exe | 142.250.185.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3408 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |
lh5.googleusercontent.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |