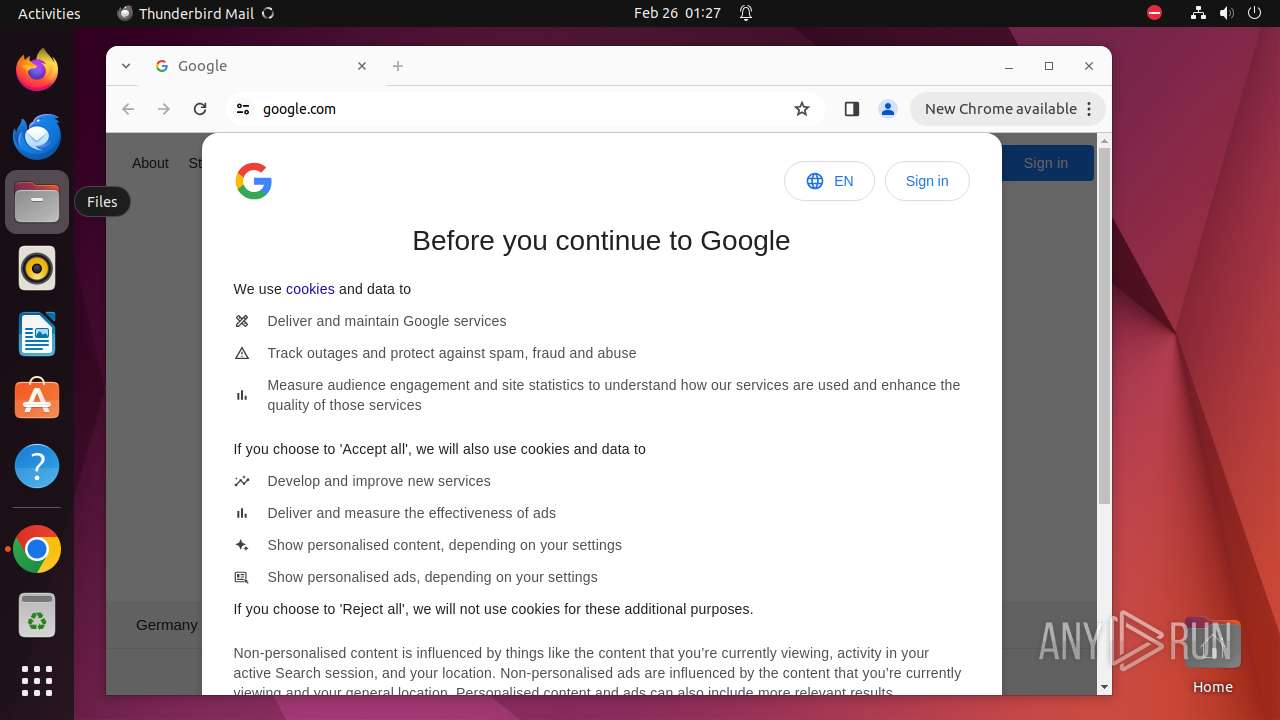
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/df2be0a0-5481-4593-b5b0-04b2070c5d7c |
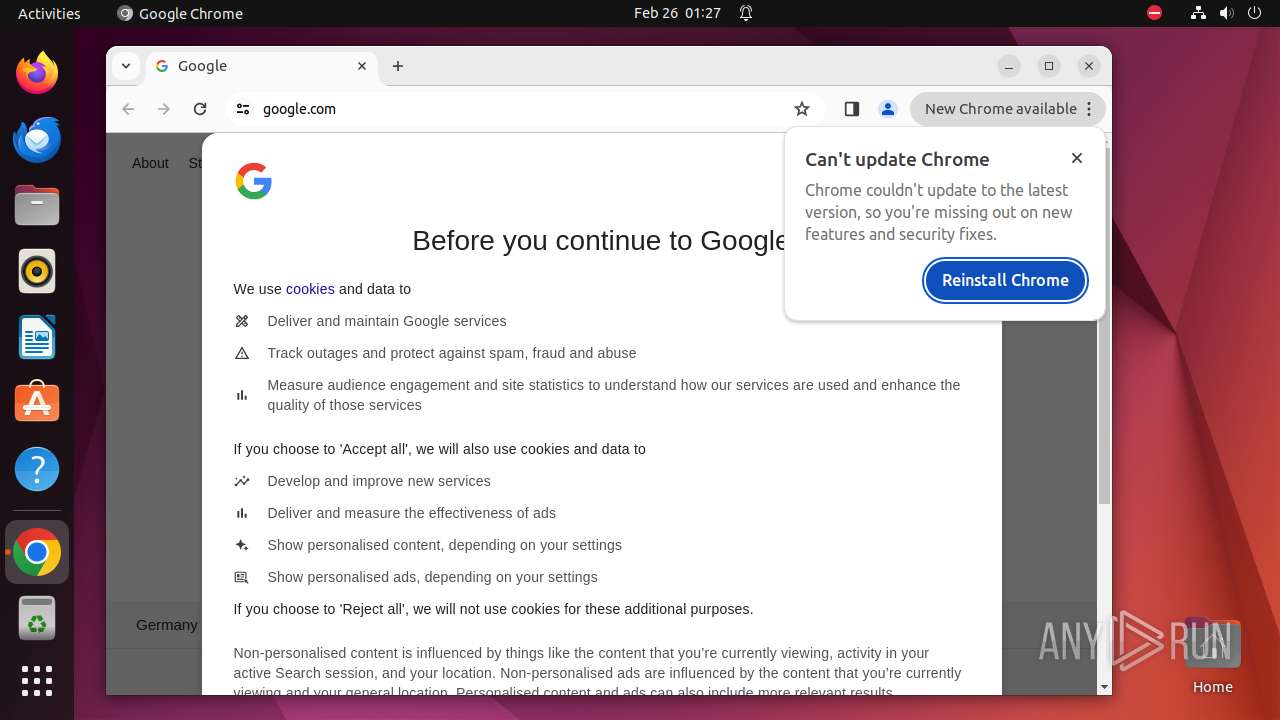
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2024, 01:26:56 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
No malicious indicators.SUSPICIOUS
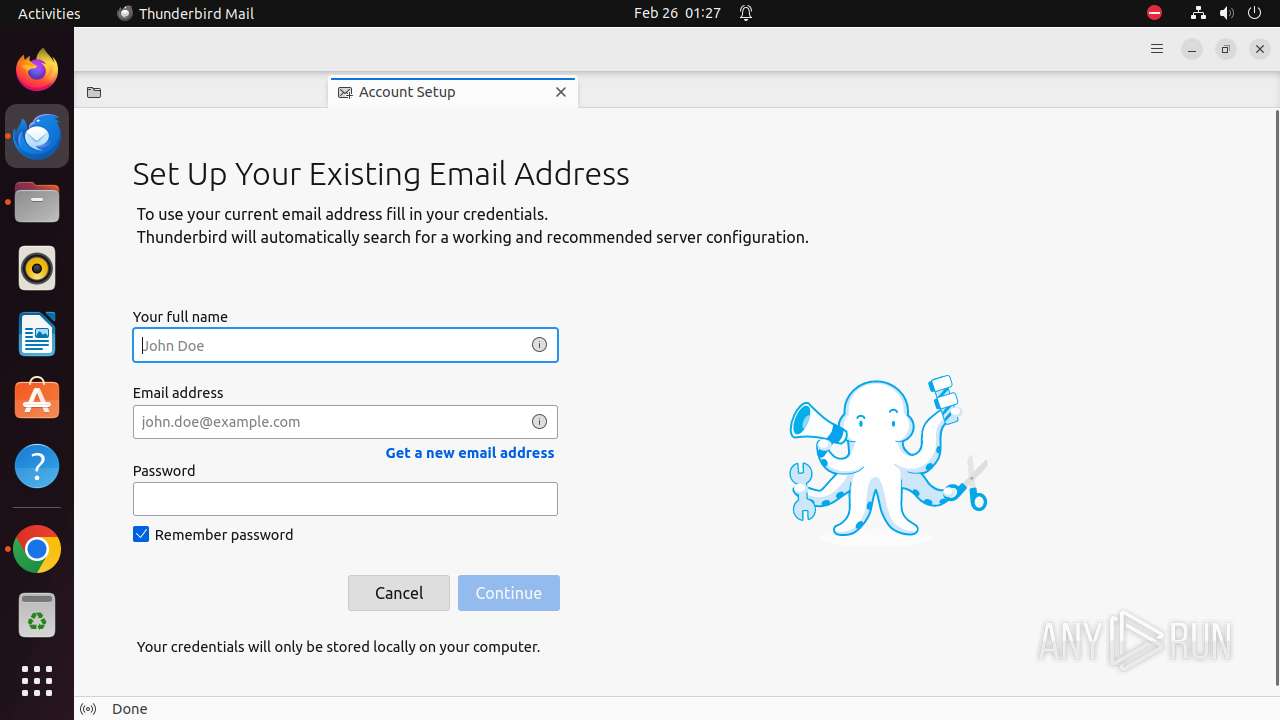
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 8189)
Reads /proc/mounts (likely used to find writable filesystems)
- thunderbird (PID: 8130)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
339
Monitored processes
119
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7926 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"google\.com\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7927 | sudo -iu user google-chrome google.com | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7928 | /usr/bin/google-chrome google.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7929 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7930 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7931 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7932 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7933 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7934 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7935 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7928 | chrome | /7928/fd/63 | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65DBE8E7-1EF8.pma | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /.com.google.Chrome.VW4GtM | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /.com.google.Chrome.UJp5kZ | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /.com.google.Chrome.GMXhtA | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /.com.google.Chrome.56CNq0 | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /.com.google.Chrome.lJLLsA | — | |
MD5:— | SHA256:— | |||
| 7928 | chrome | /home/user/.config/google-chrome/Default/Session Storage/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
58
DNS requests
53
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.1379eef506ab6fba0188245b16a8443df9500ddd8553bfb2f6f3903f4a7c6e1a/1.6fcc02a365d39485c49c9da8679a9fd979832315b2d47ff7f0ab395b10e303bd/3d2f8e760c9c6839d43e3e3004945ff5d33819ab285335201ef6a9749b28da69.puff | unknown | binary | 17.8 Kb | unknown |
— | — | POST | 200 | 95.101.54.131:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acfxlrp5viwchbuphckmvomvnw3q_2024.2.23.0/niikhdgajlphfehepabhhblakbdgeefj_2024.02.23.00_all_fu35rmvtot47476jnmknlqqxru.crx3 | unknown | binary | 5.80 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/1.5bdc69c131996e6e6abeeba649e5a21c2f62a0b40bce413f8a728108c0d4fe06/1.1c9ef13b7a63abd8f89d0cbad98858b9e8f54fc3951160950403c72b45812d07/865d7f70f7a9d5db0e532d532dcdac720827d84b53c19d9201854f1c174ccfe7.puff | unknown | binary | 2.27 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adntsu7c2i6rqgpdez3sjfuq367a_2024.2.23.1/jflhchccmppkfebkiaminageehmchikm_2024.02.23.01_all_eoyb64giamrgjvhtv54527gmti.crx3 | unknown | binary | 7.84 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/act6xyjtfqstmyiq32bv6f5pf6ka_8569/hfnkpimlhhgieaddgfemjhofmfblmnib_8569_all_acmx3zvomstjcmnrnikybm5alzza.crx3 | unknown | binary | 26.2 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.af8fa6822a4a3a4aeaf78dd2b562b3b76ed3ef0b362f8ebc822df79717c996df/1.ab8da5b849ba36382f26992fe1b52d72aa457549f31246a0c386d6880fca8afc/3c8c4f546e4fa8003cf45c6c7acda068b295a9b5c871927c28fcffb32827dc42.puff | unknown | binary | 41.2 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gonpemdgkjcecdgbnaabipppbmgfggbe/1.5eb999428f0762c5d05ef5b922c551c2dc27c134c4d10fb57e27c24c28d00c5a/1.48fecfa3c6f59eb6c34fdd5e8f19e0678699e2f27dc8ebfa7025c246d4575c68/c49b41a0d32bb08a342a5f0eee242cff9d1927d3cf04d0682bffee86620adc66.puff | unknown | binary | 2.93 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
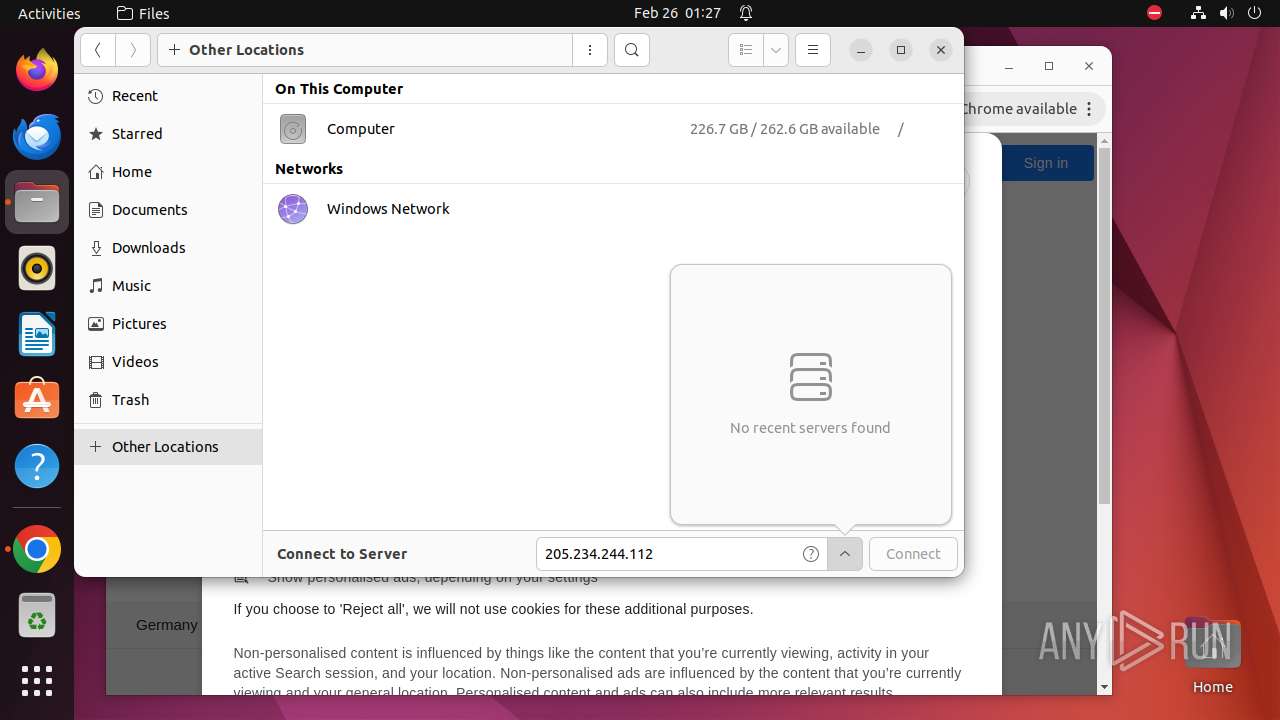
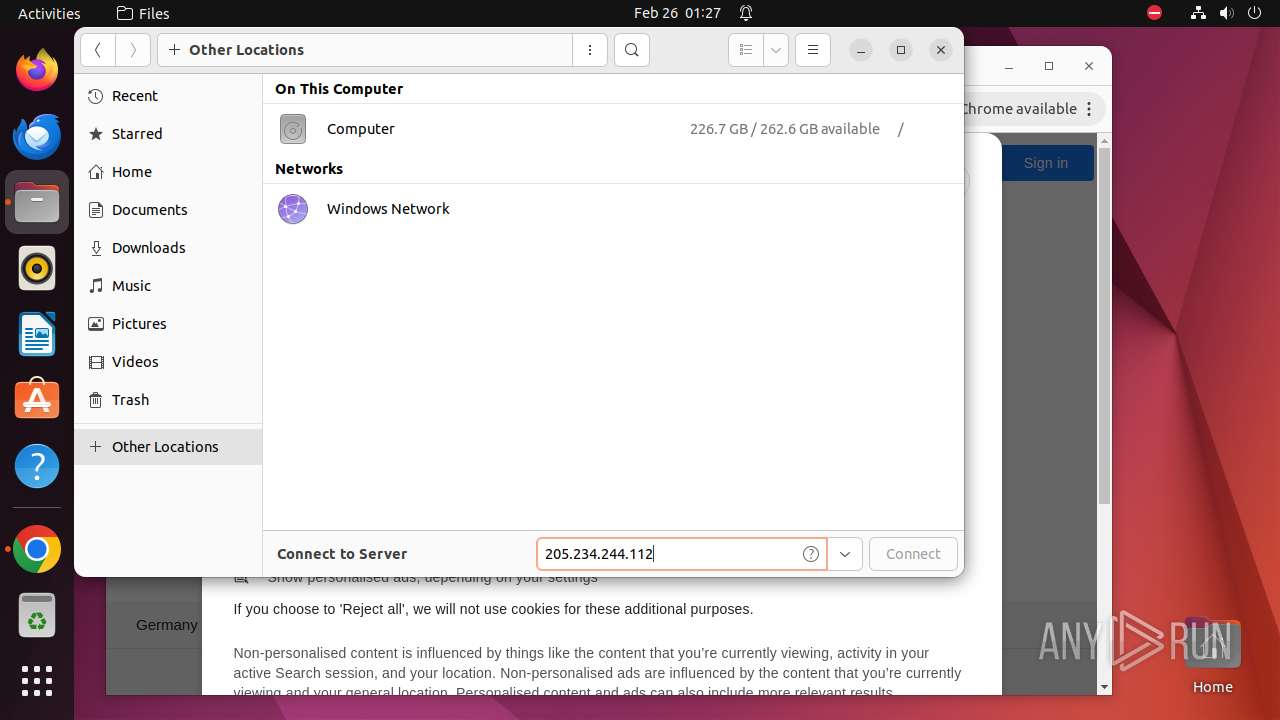
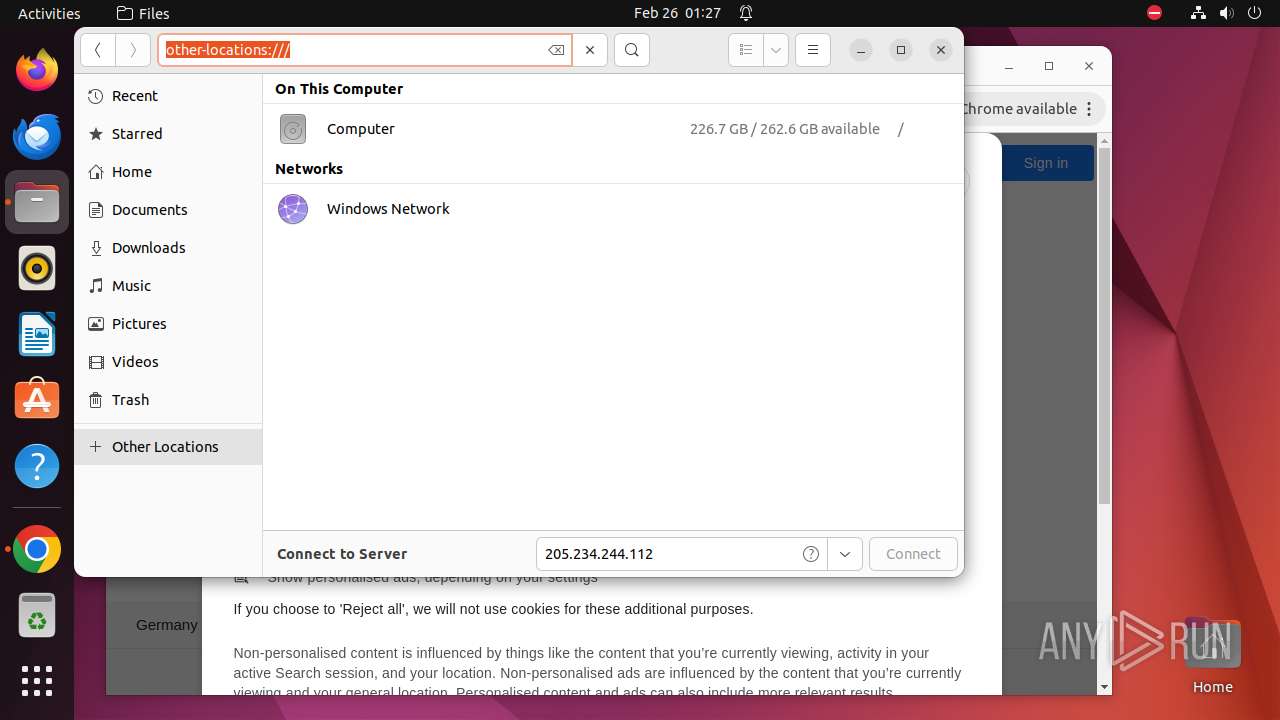
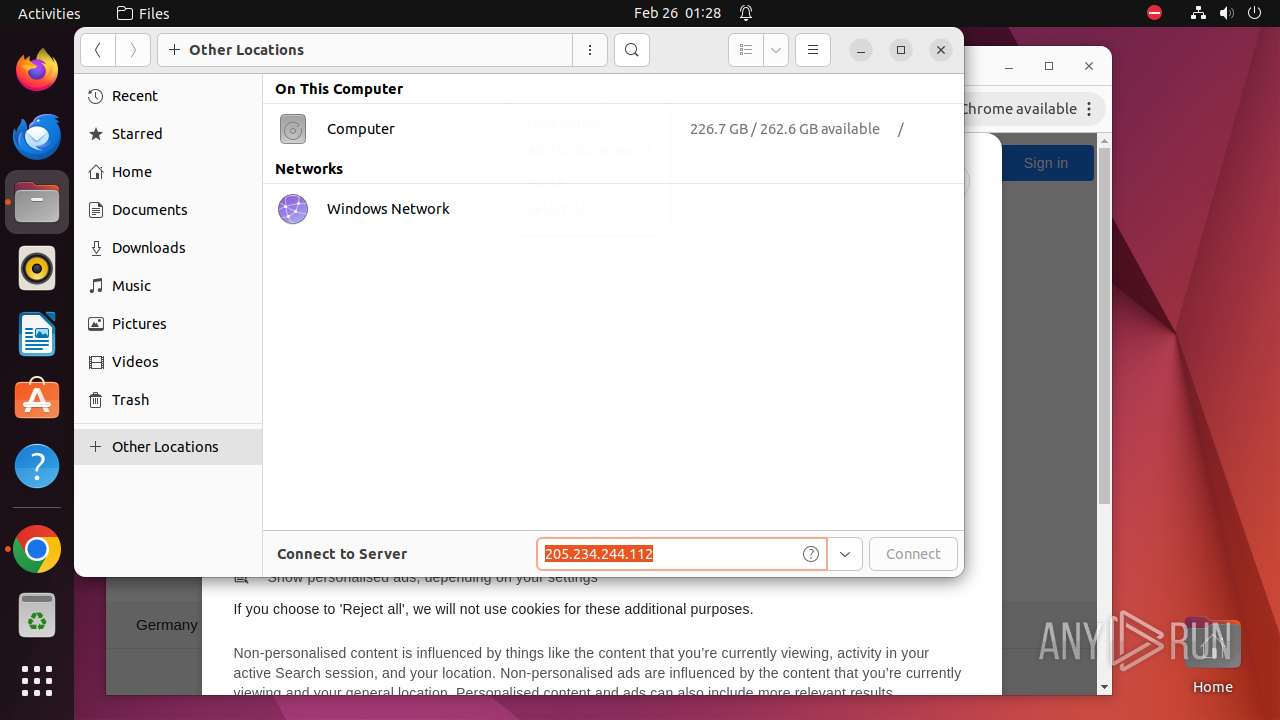
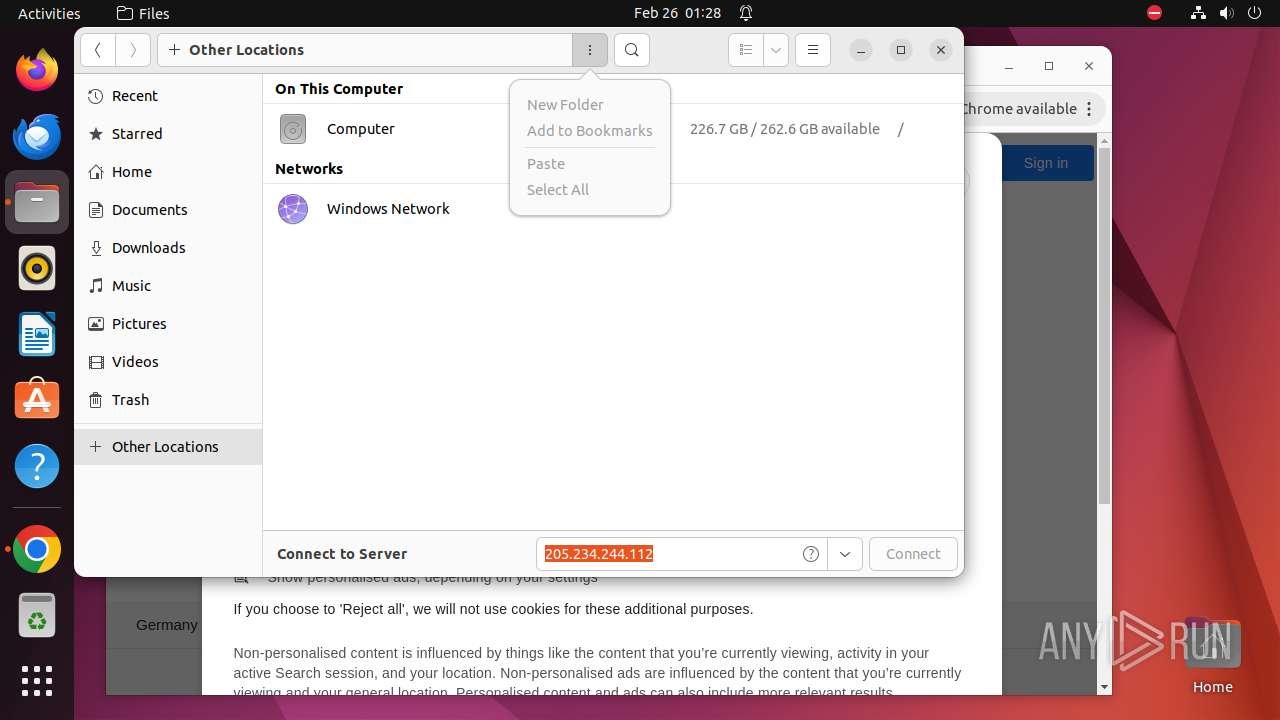
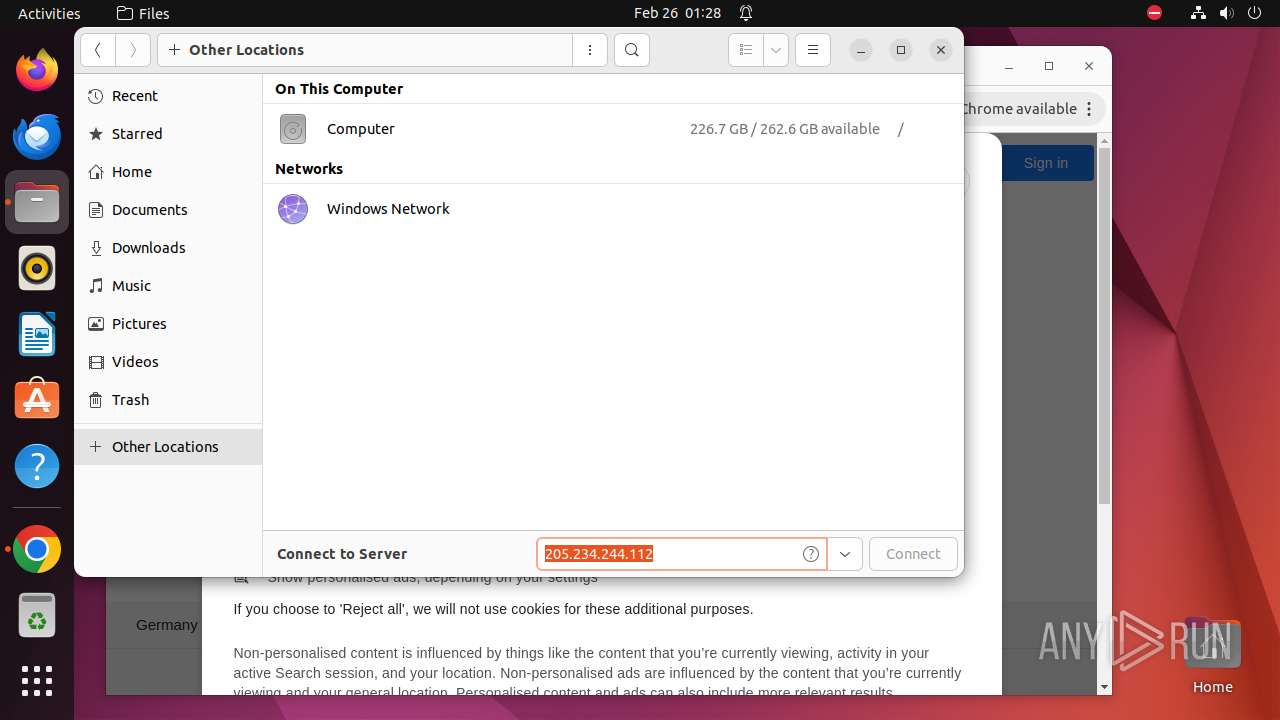
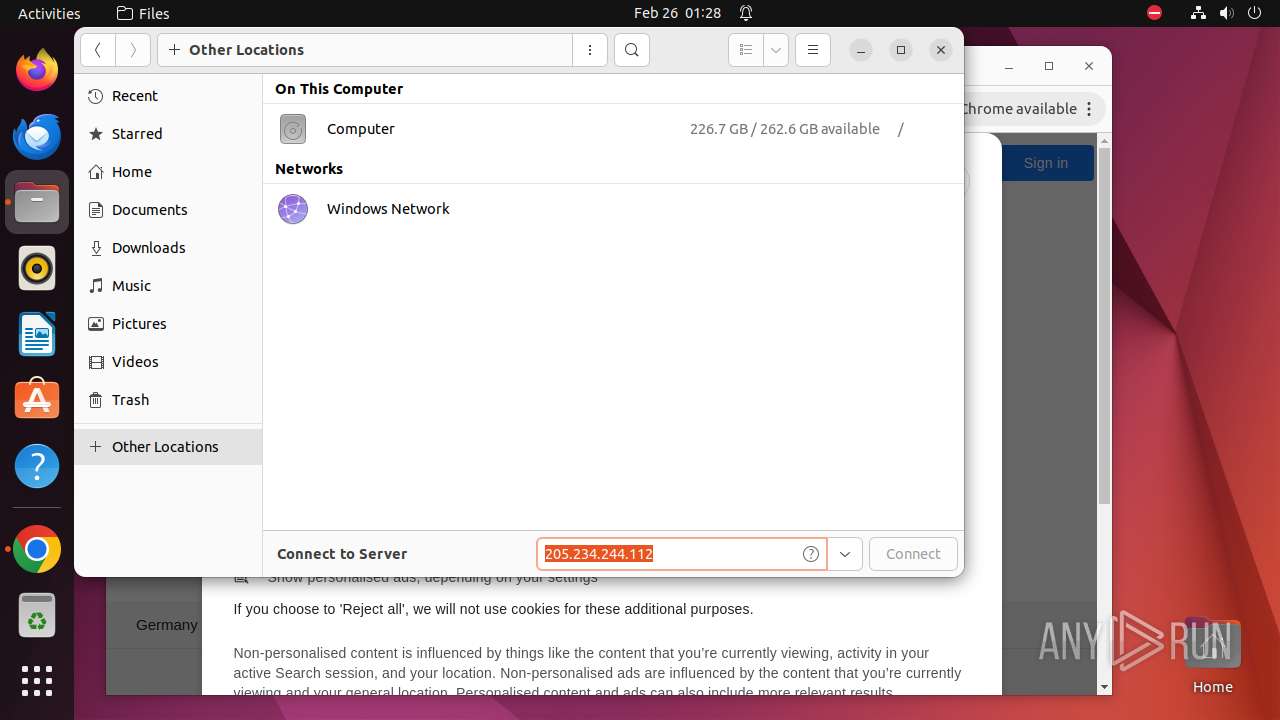
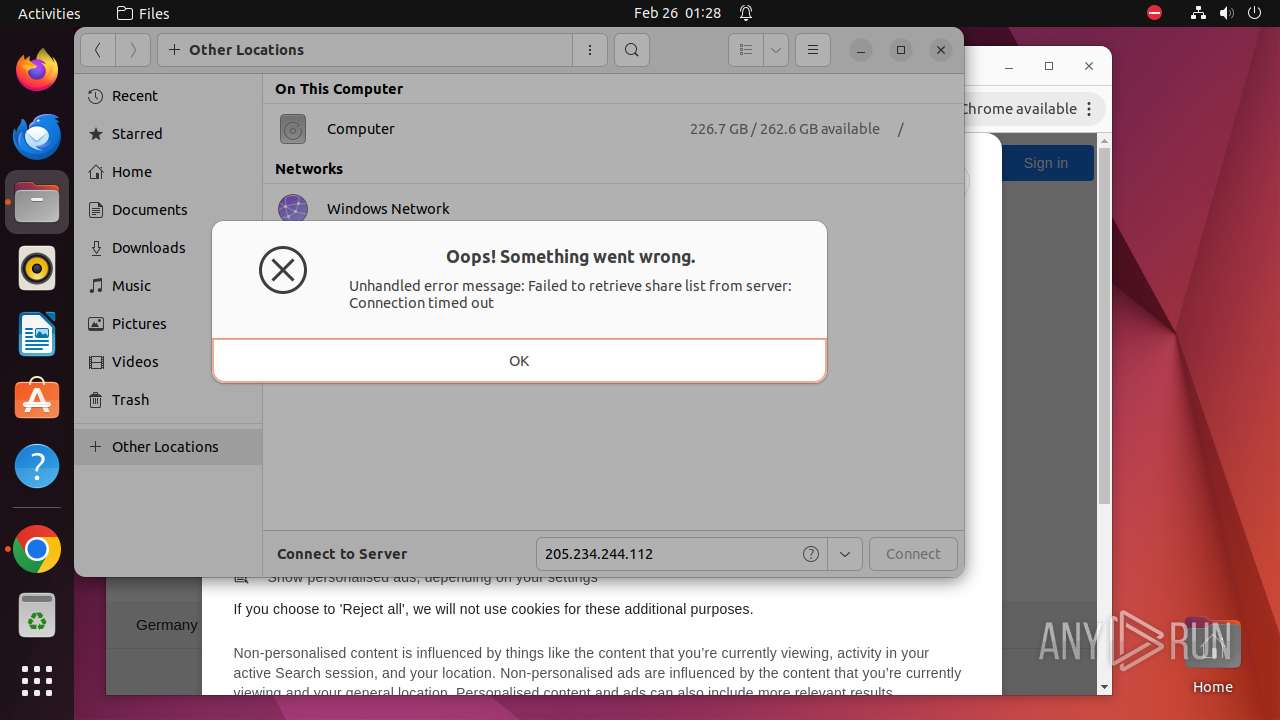
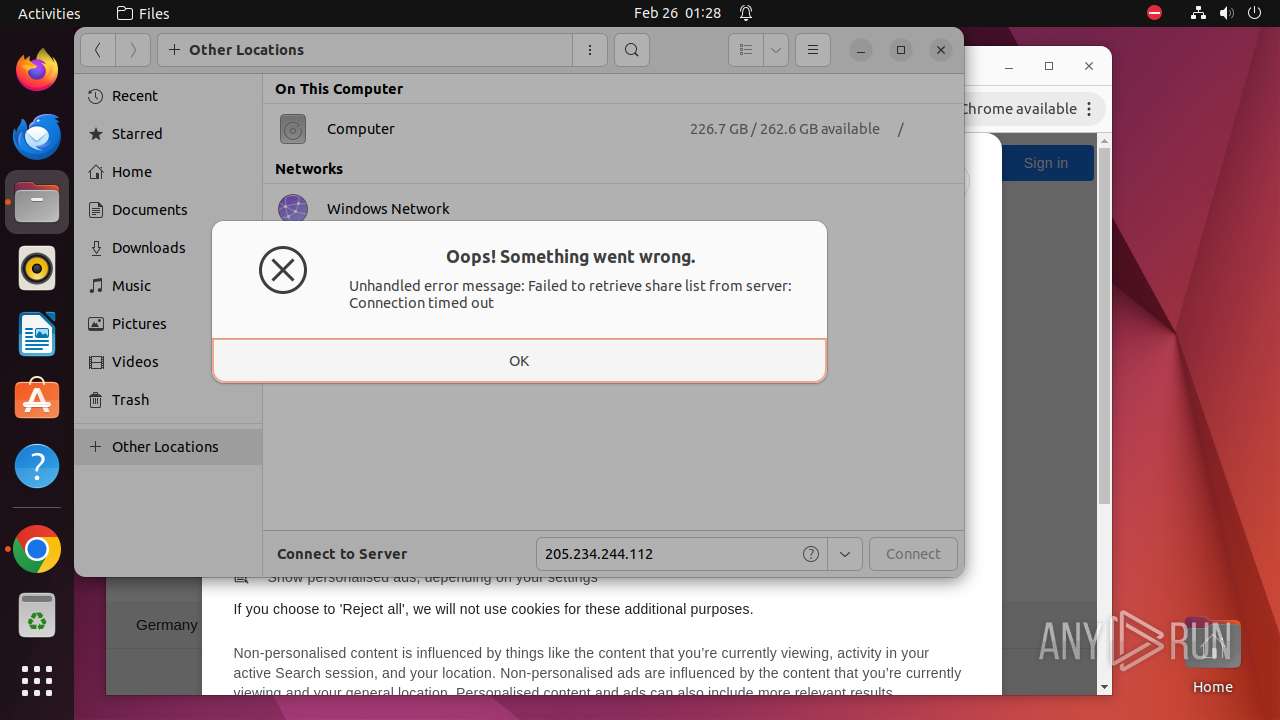
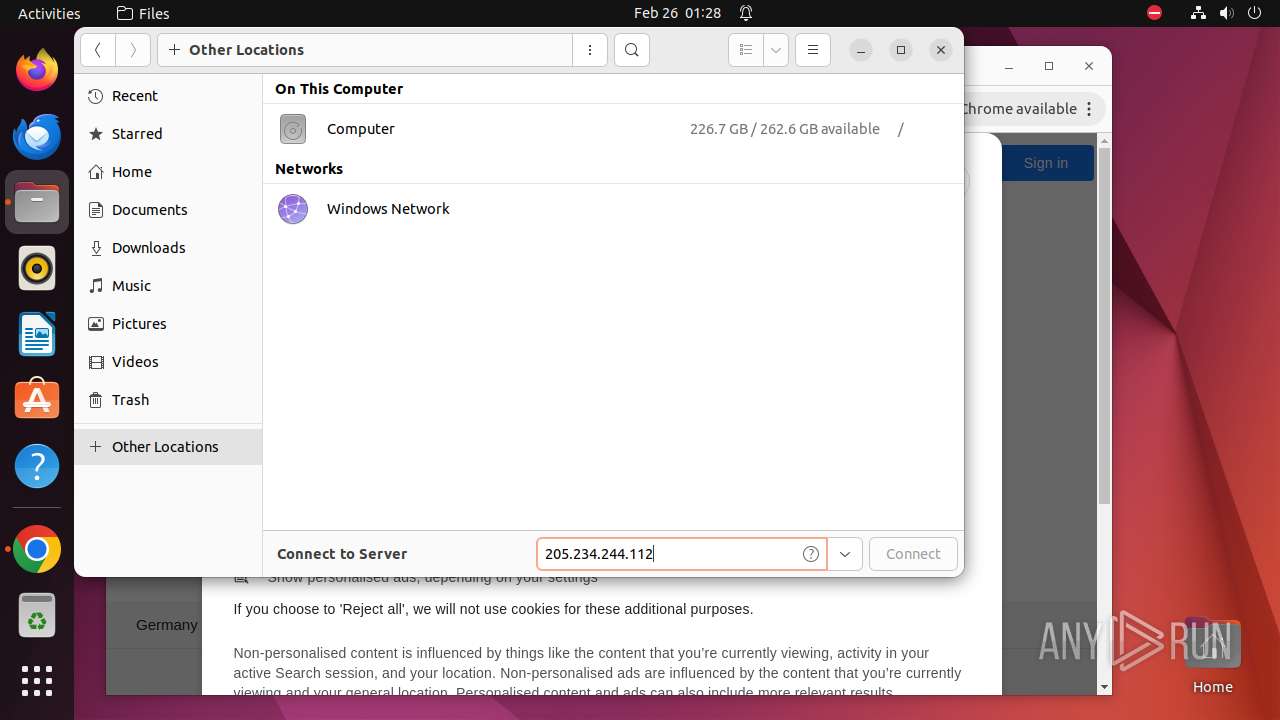
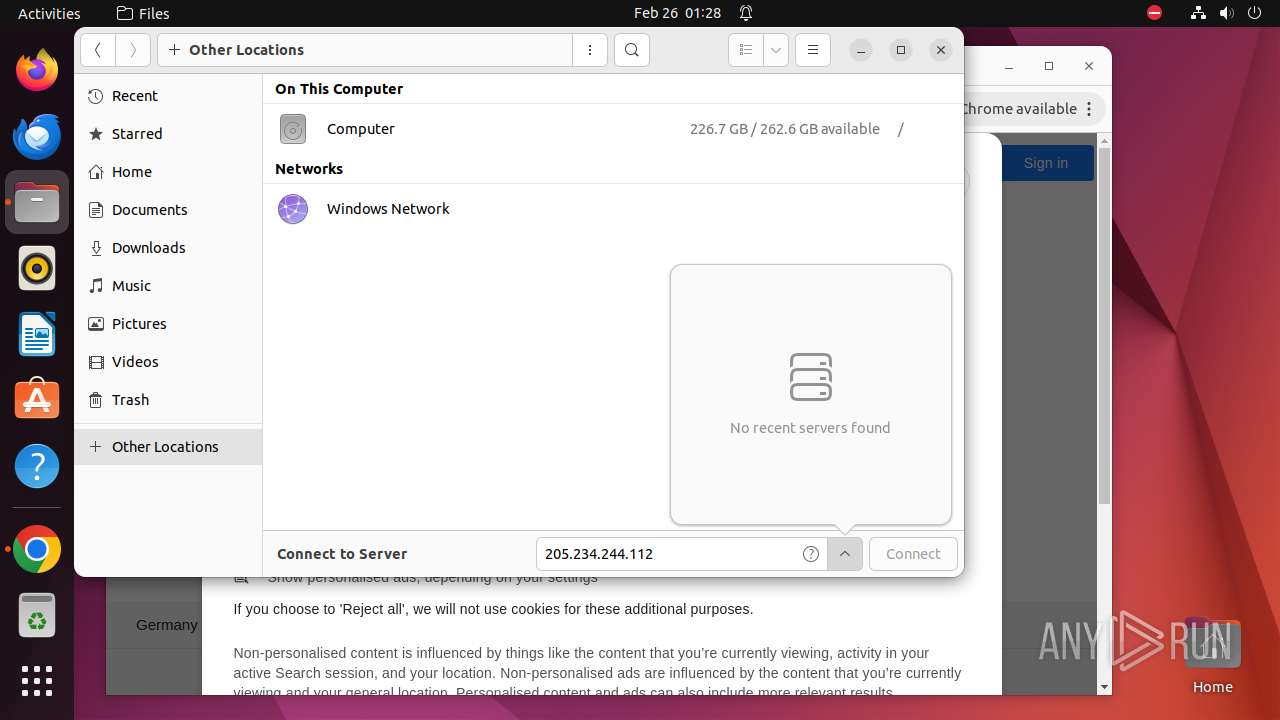
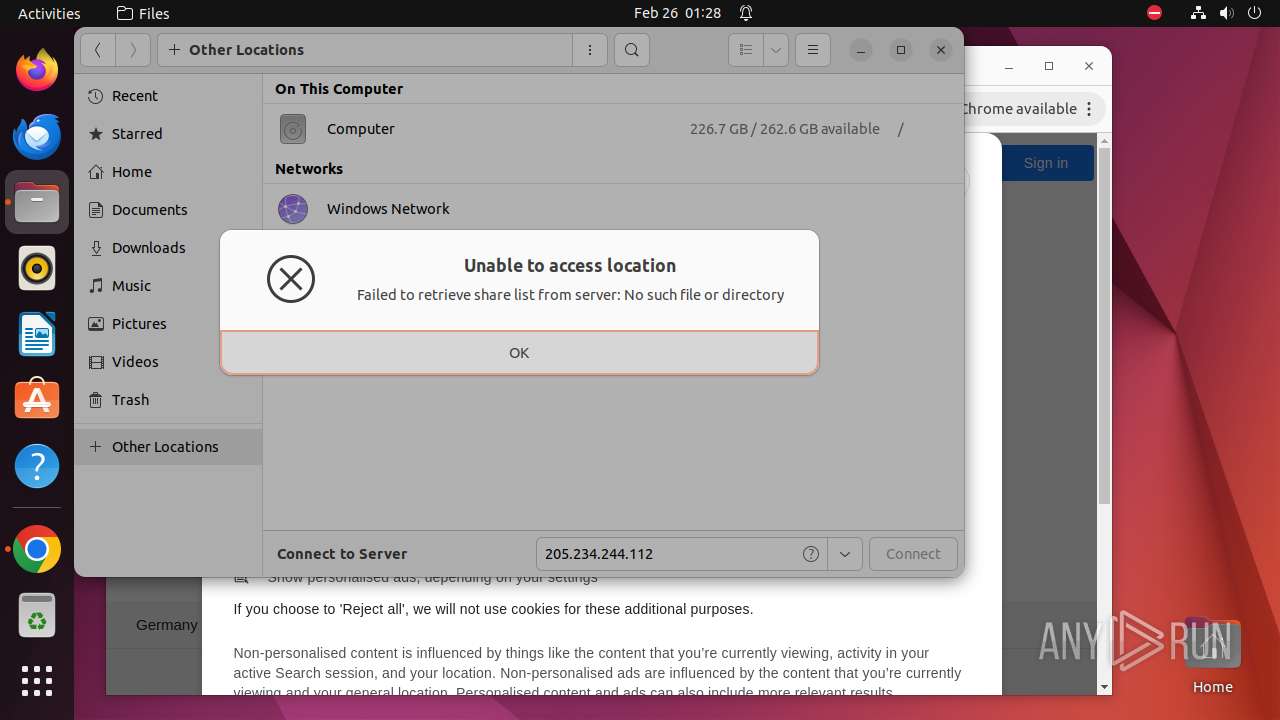
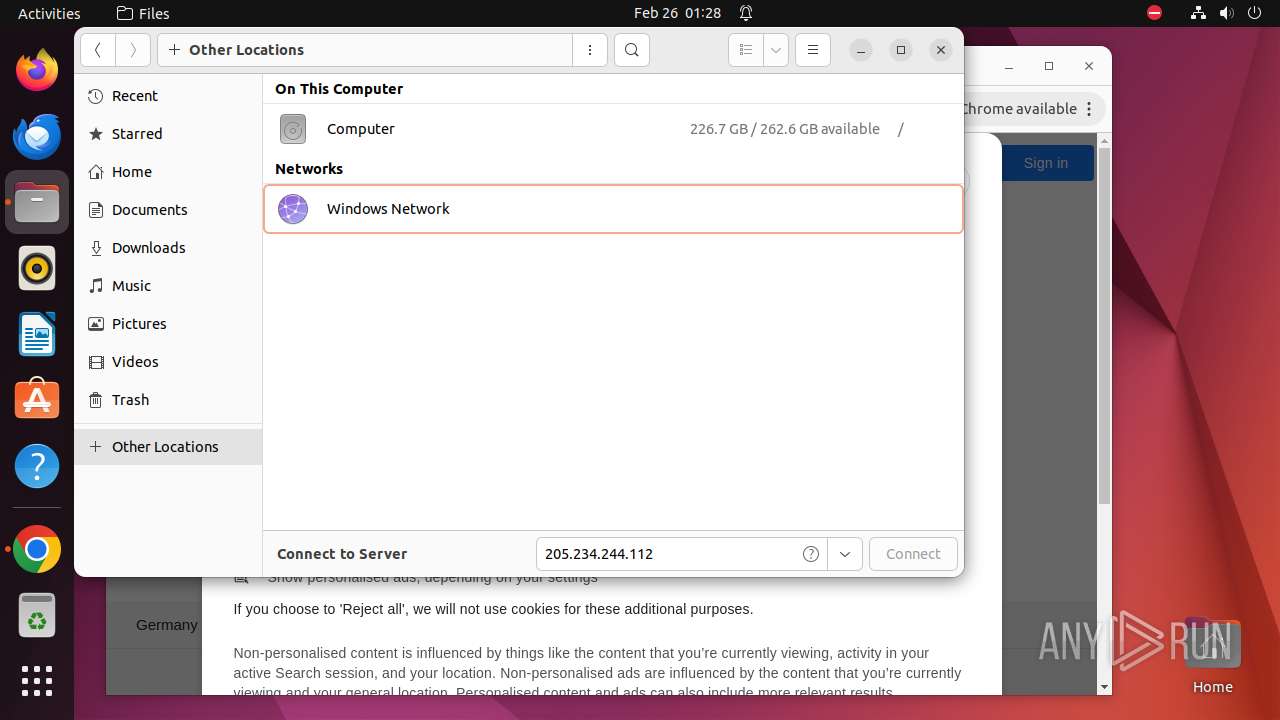
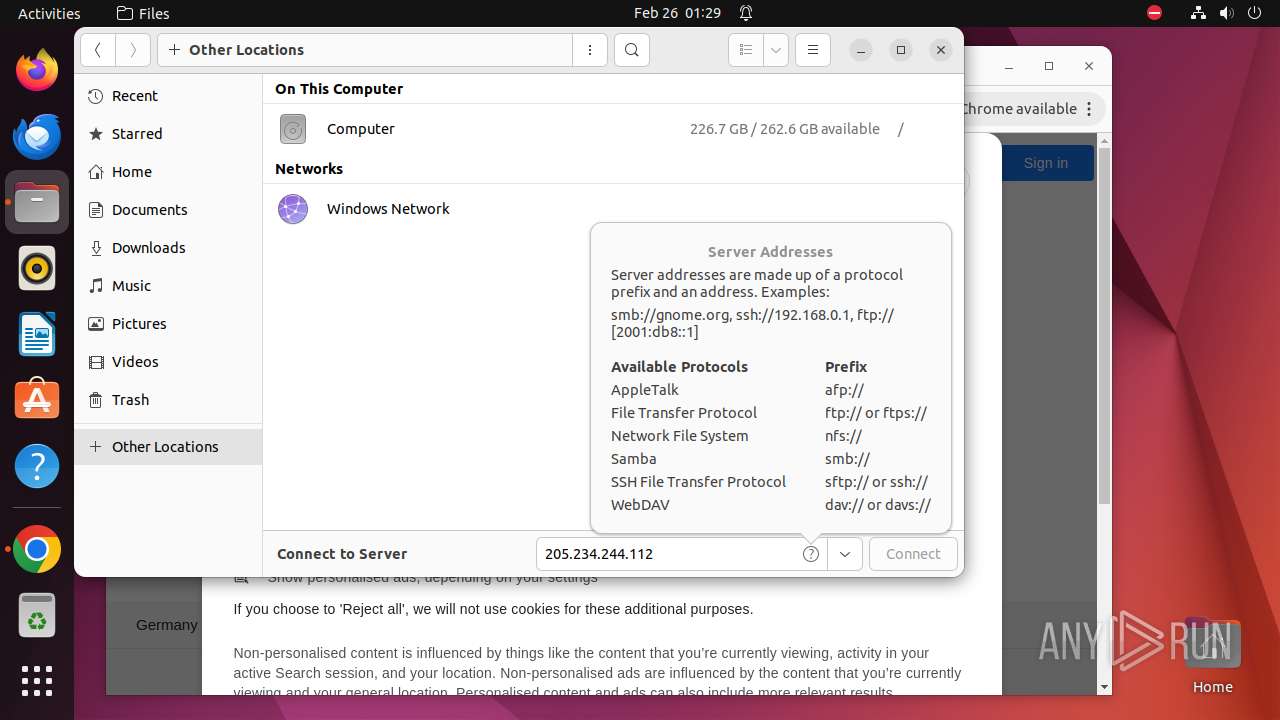
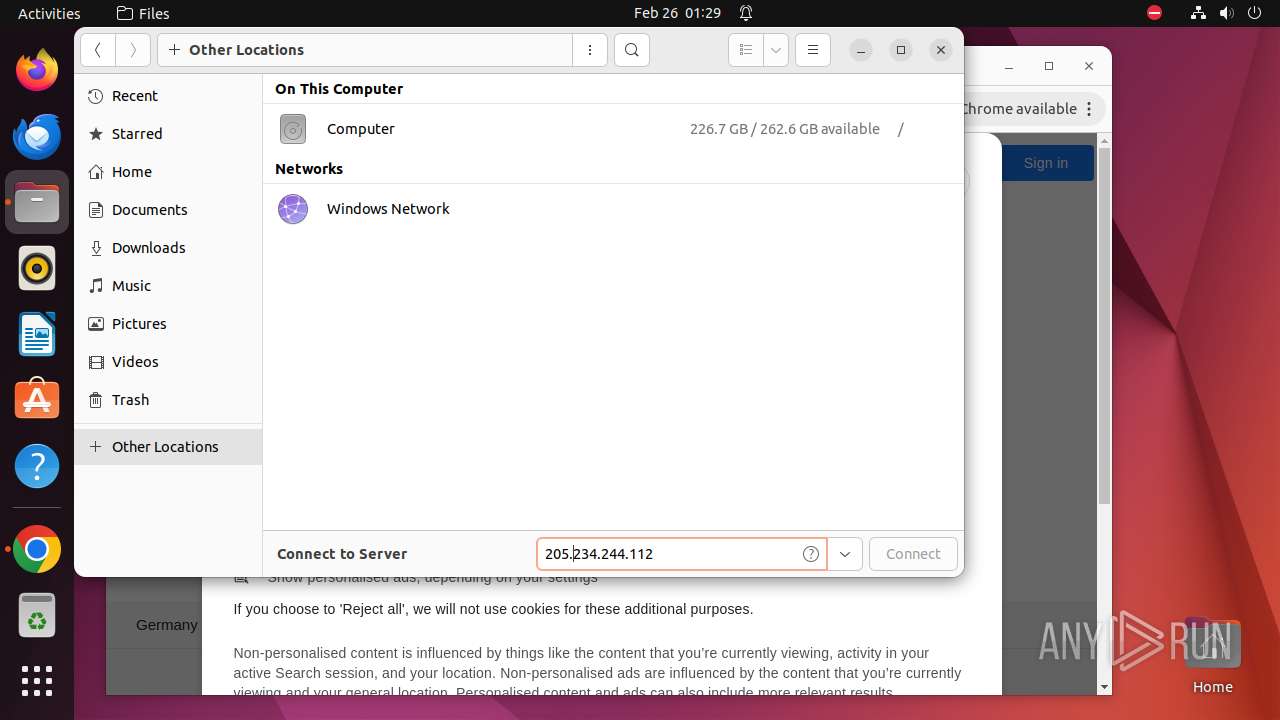
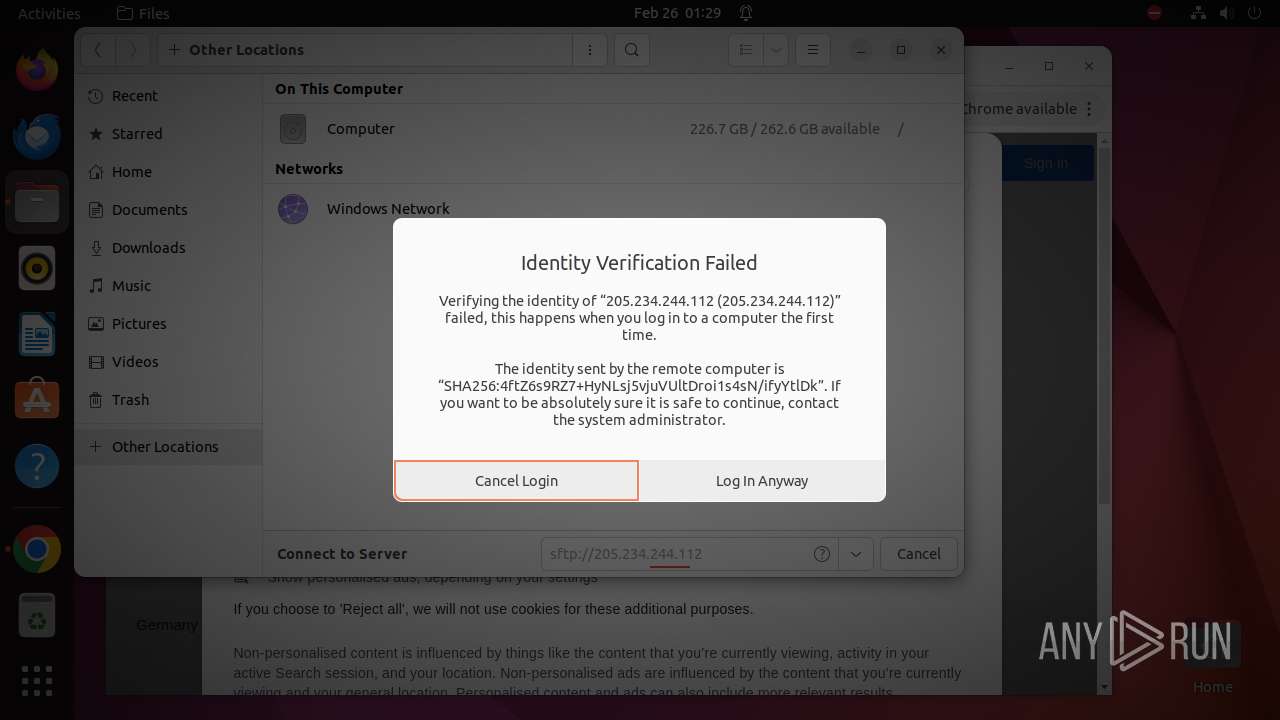
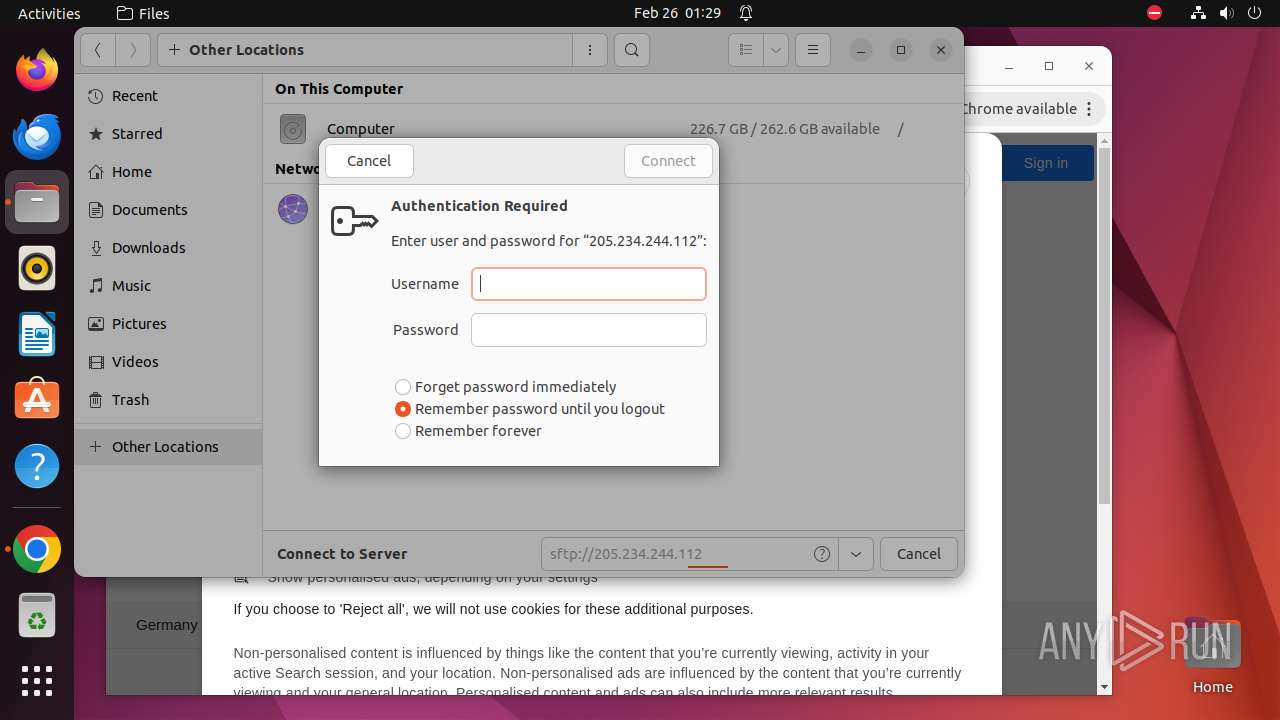
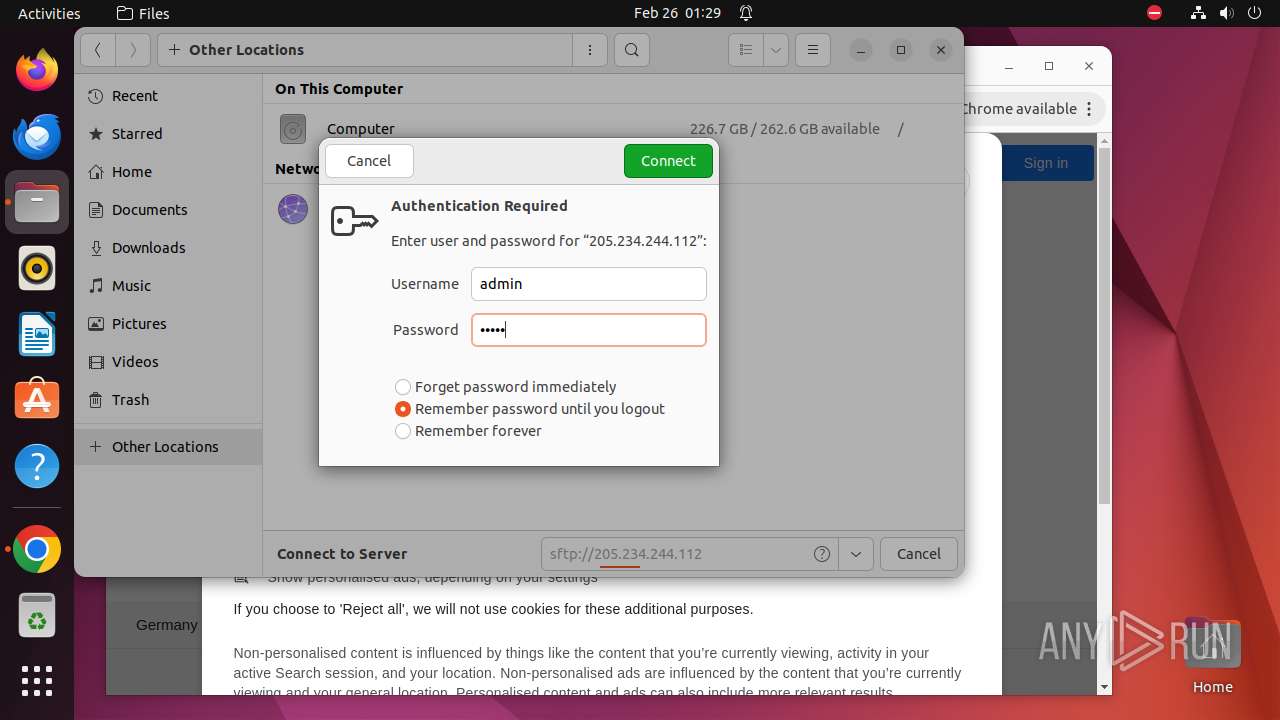
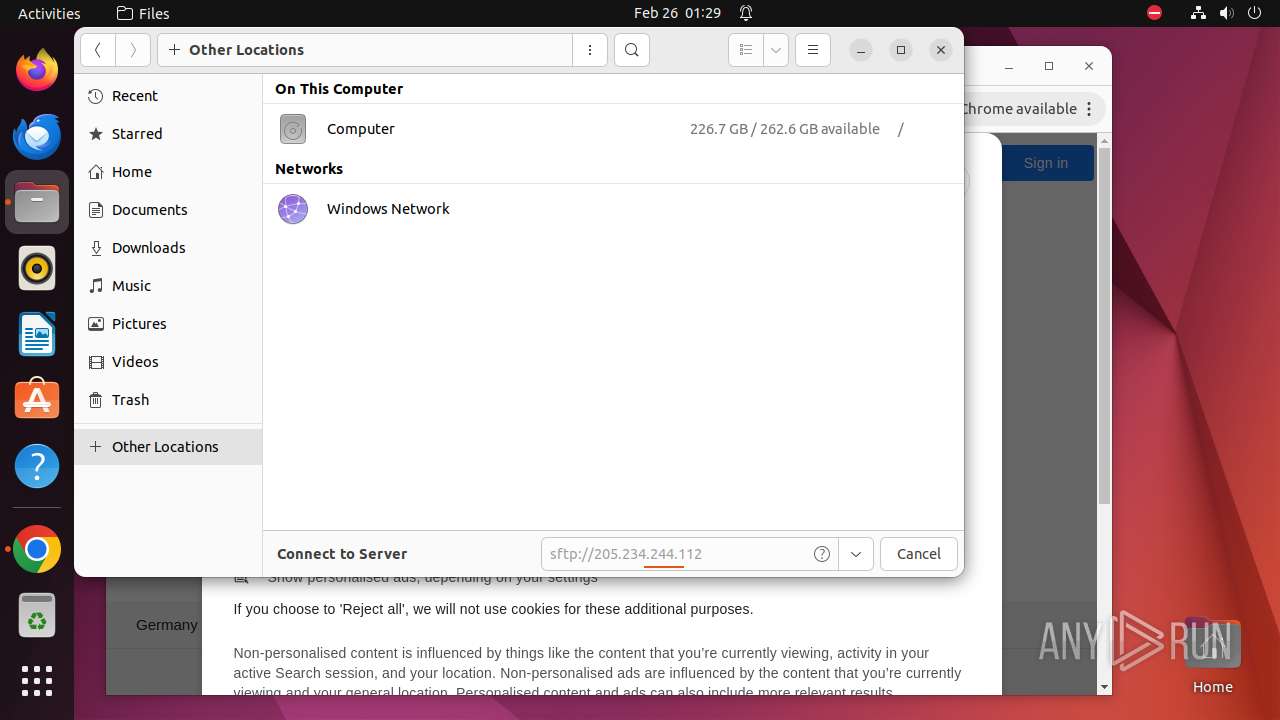
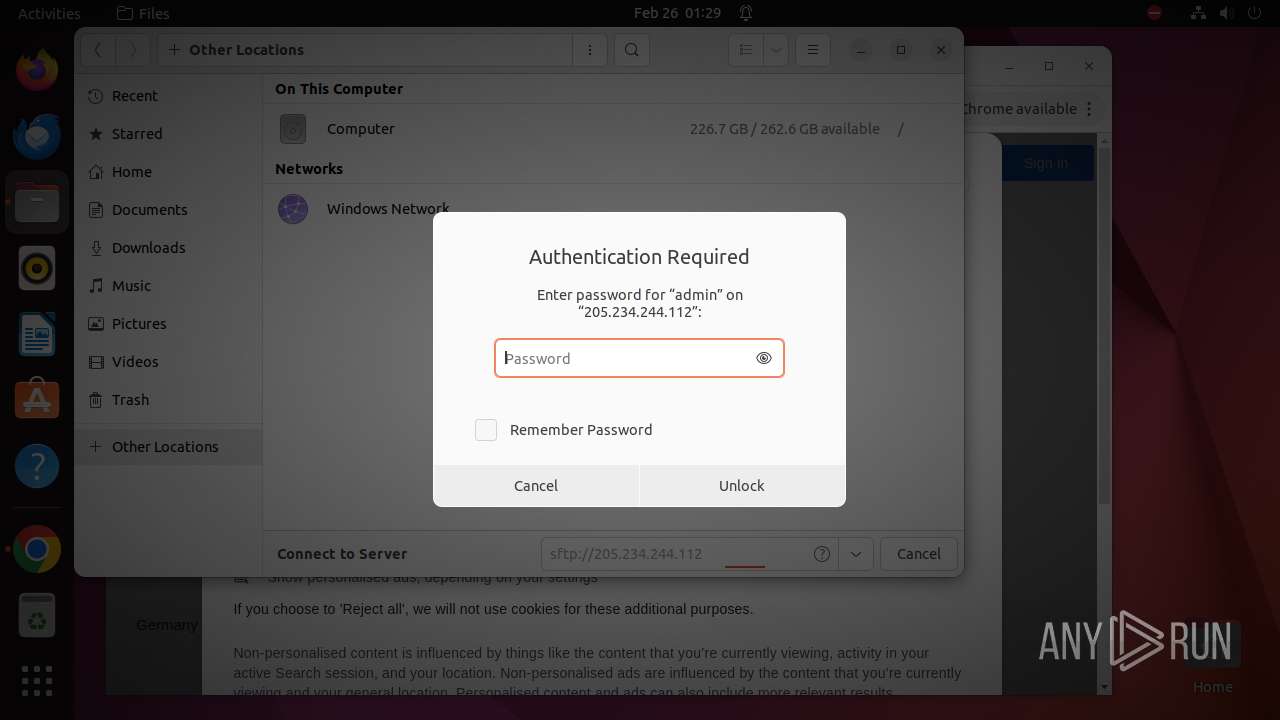
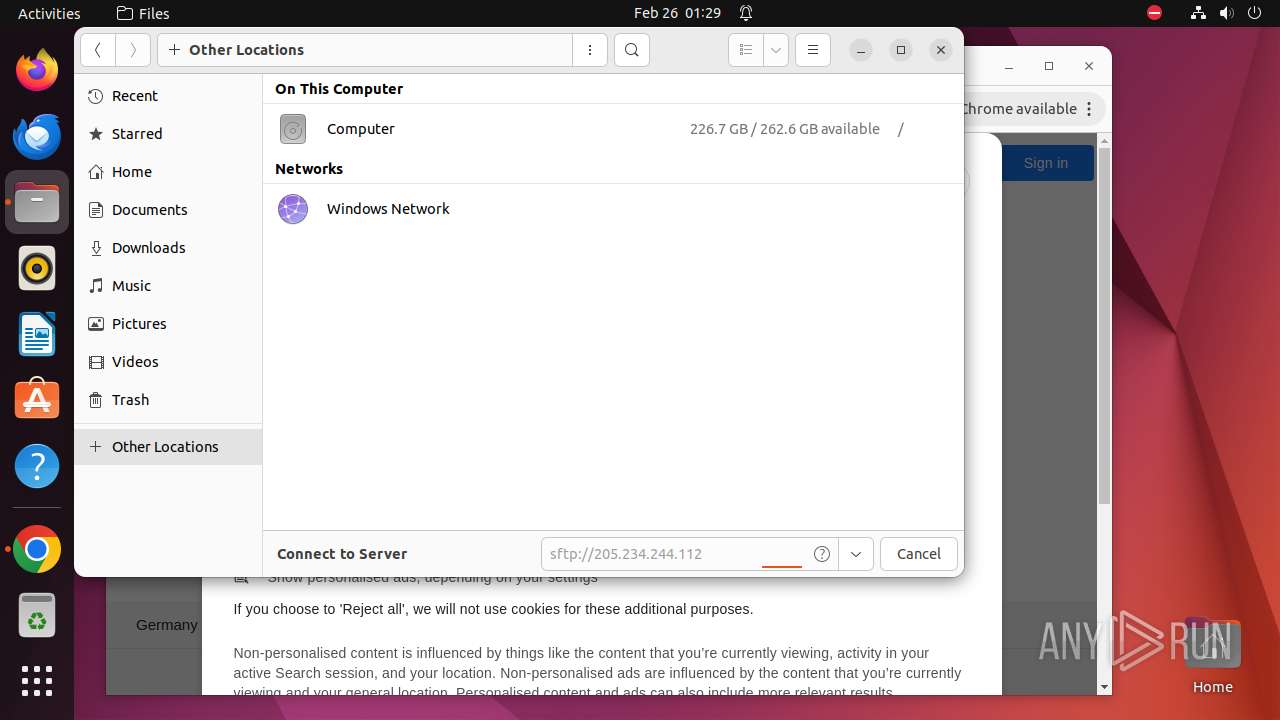
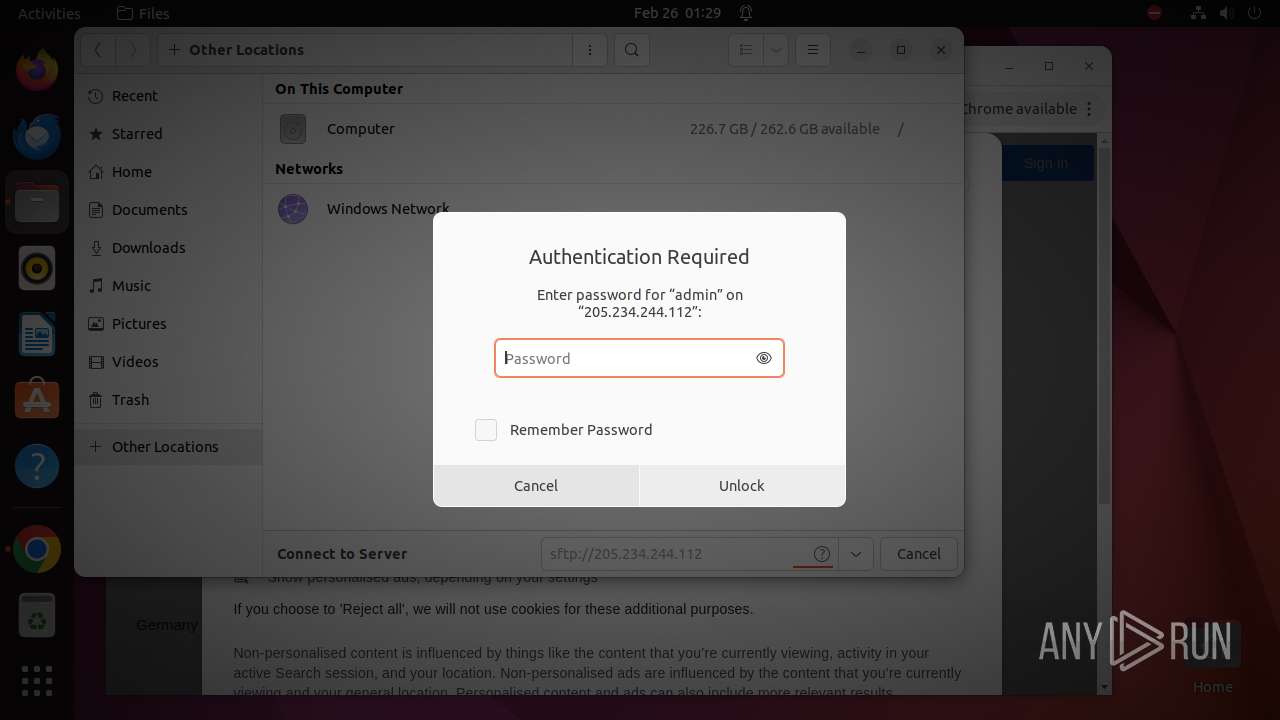
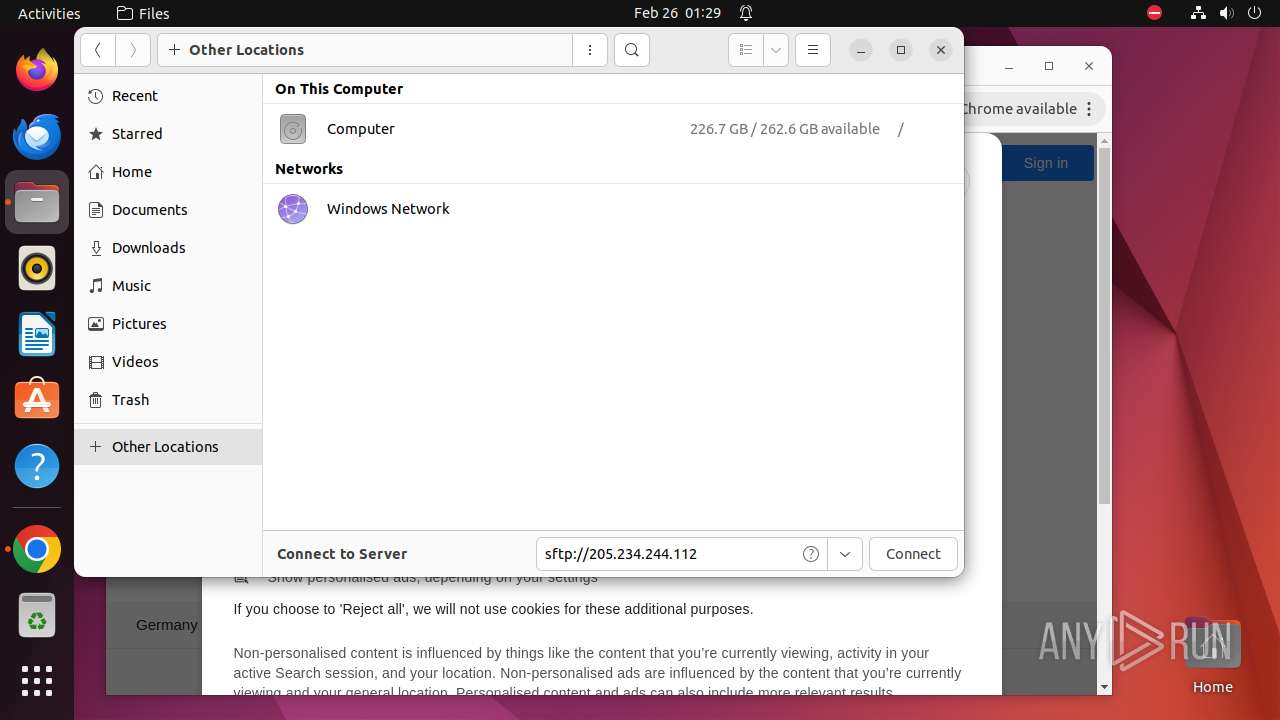
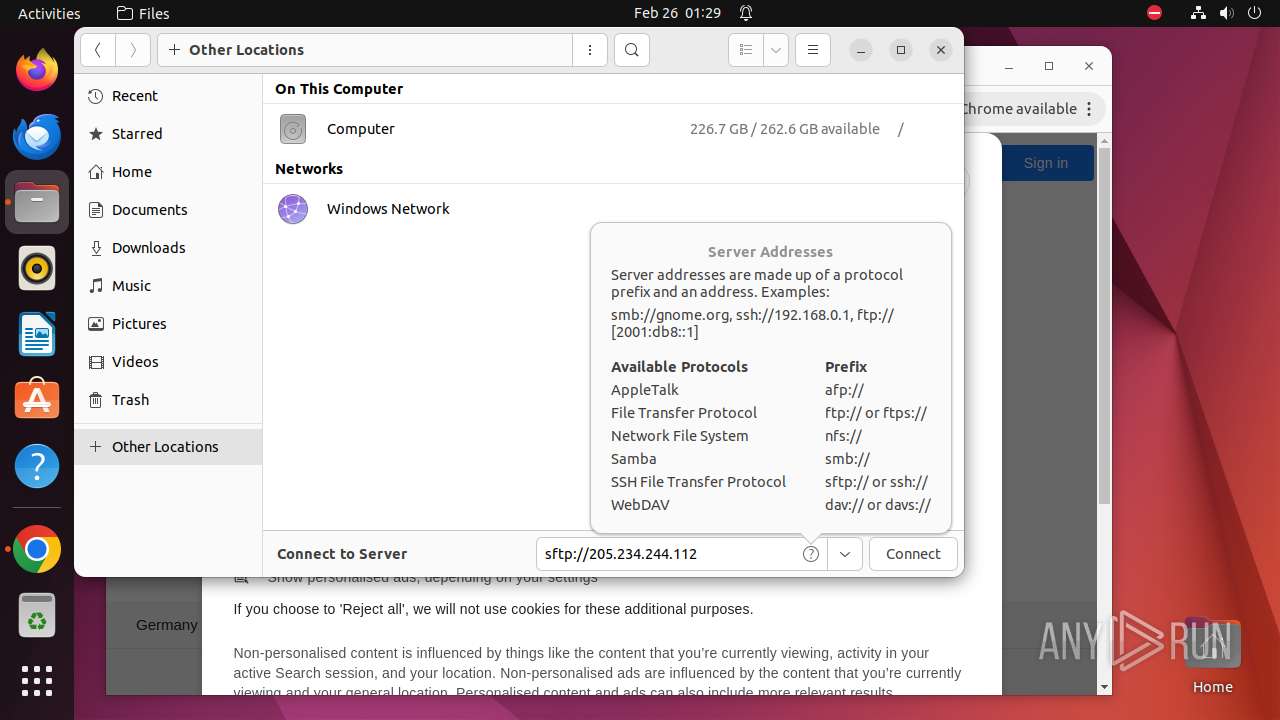
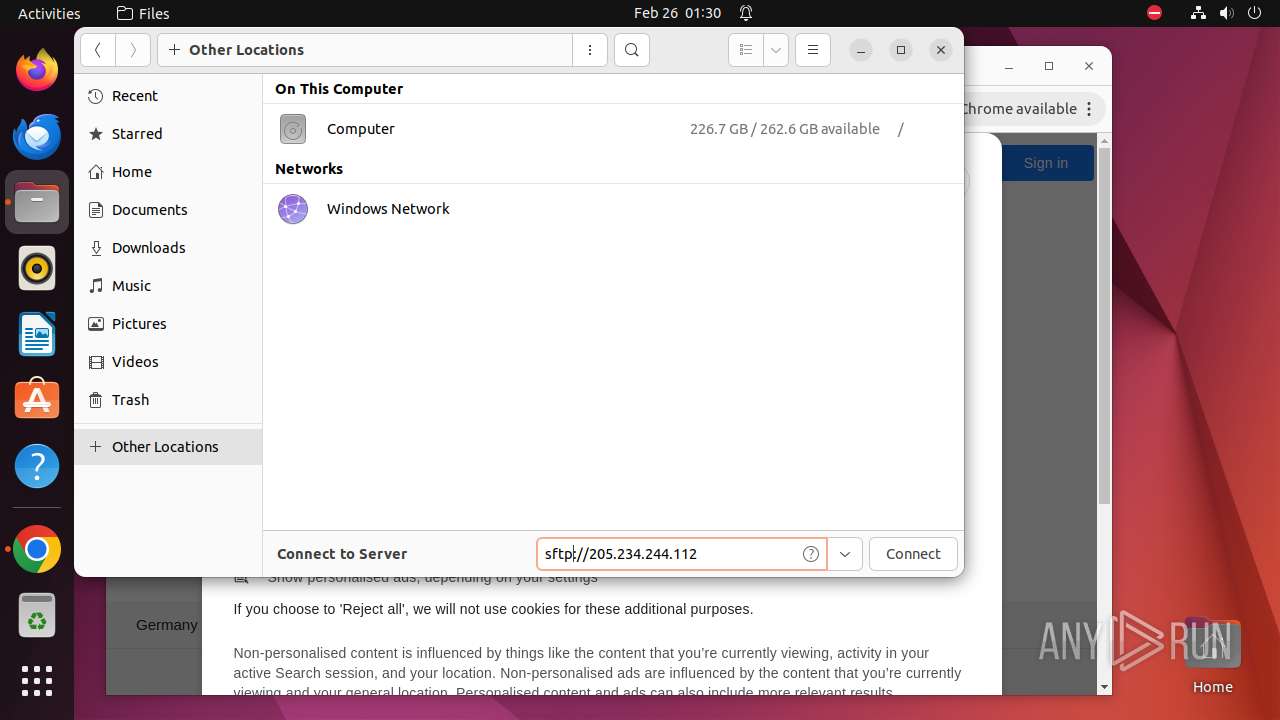
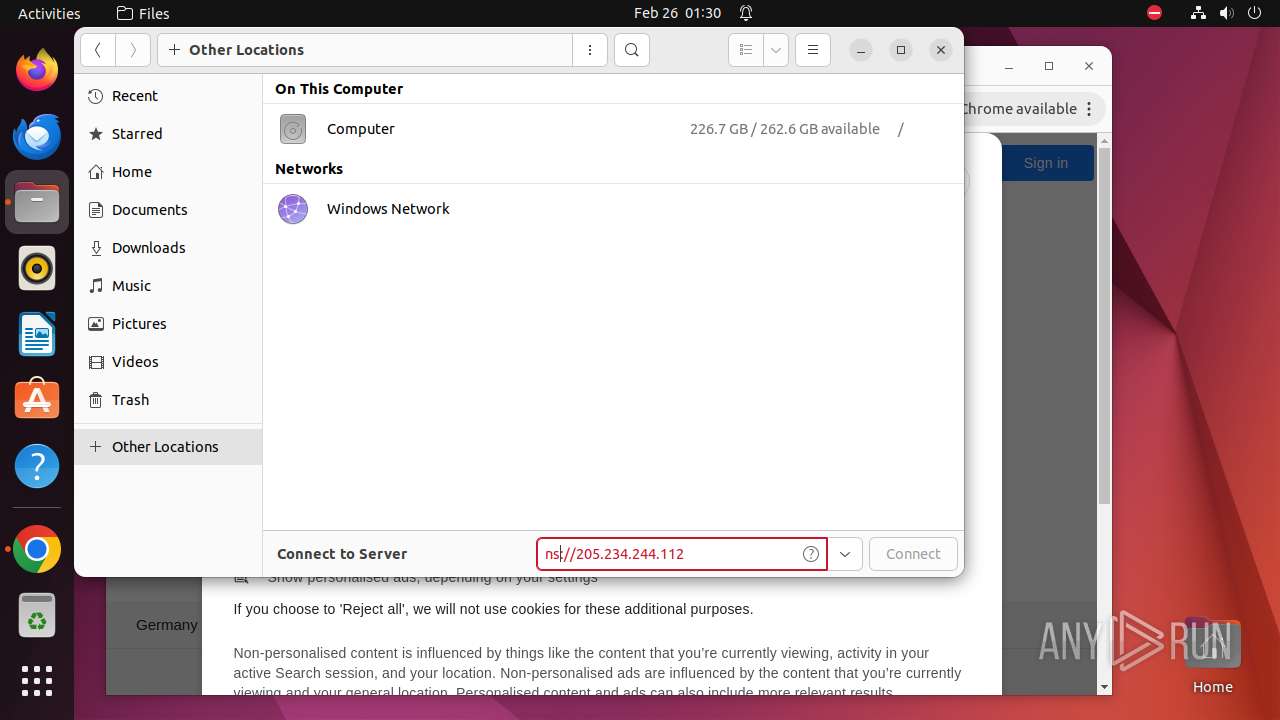
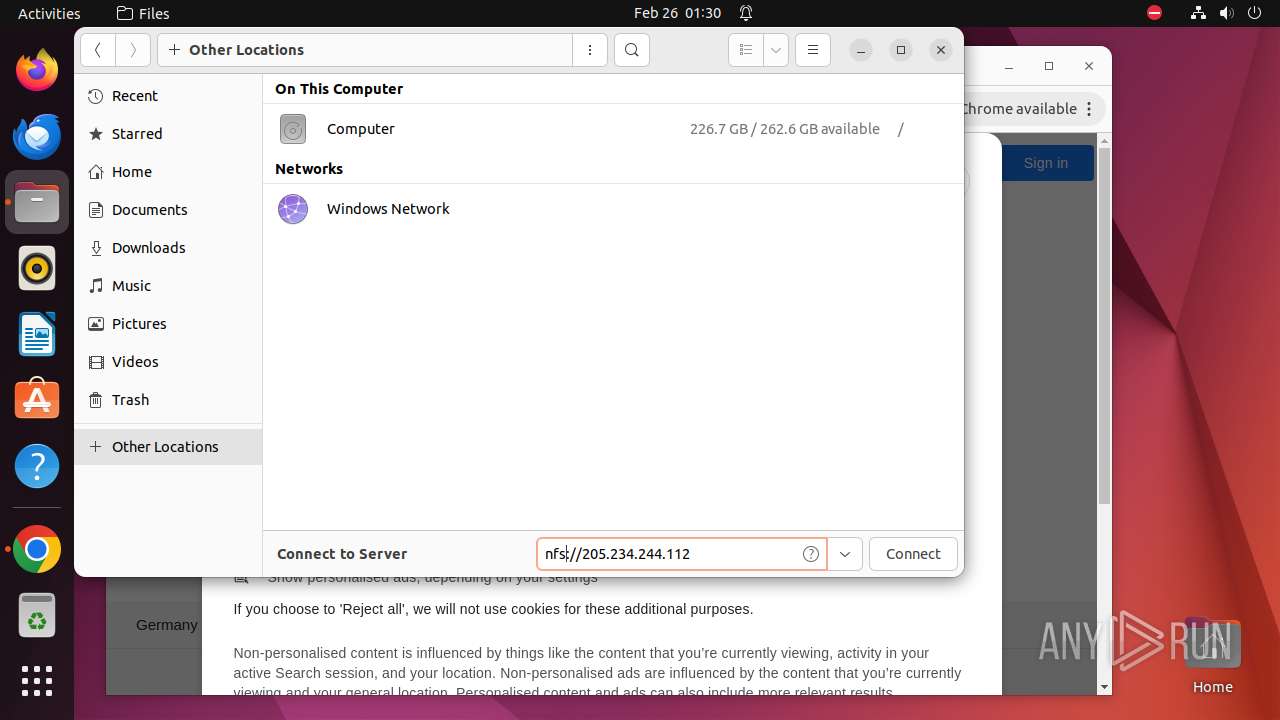
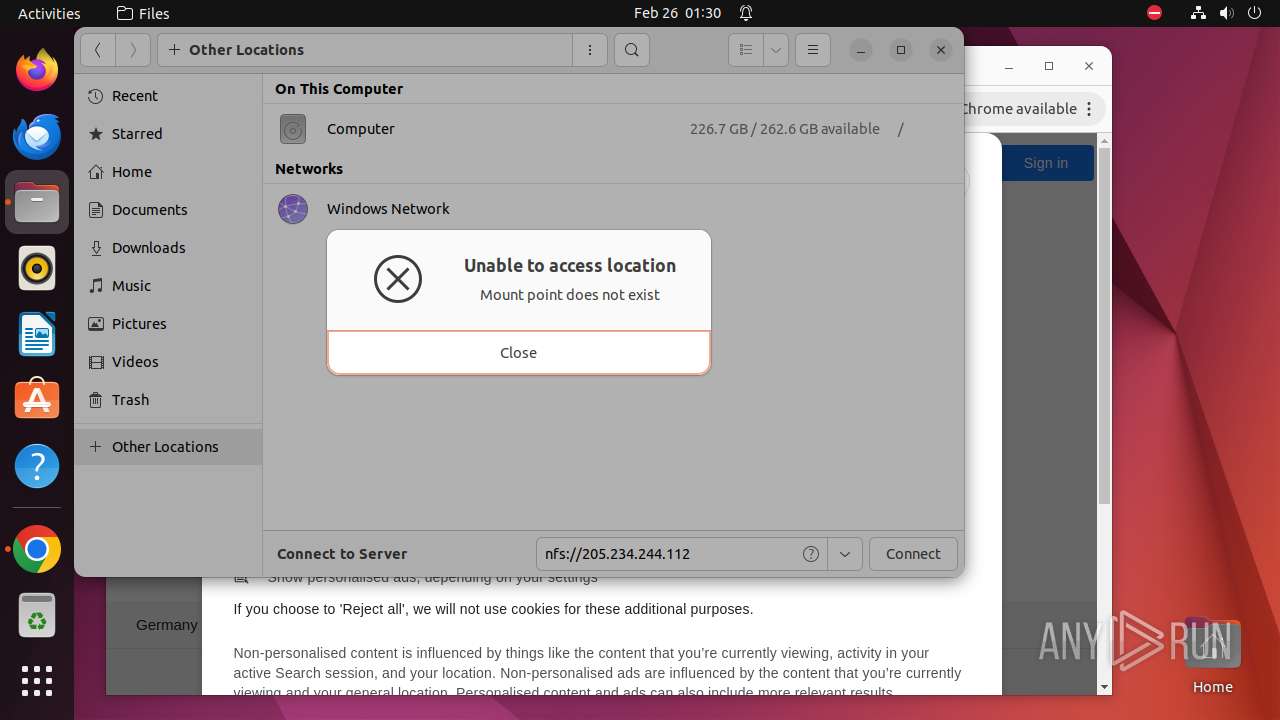
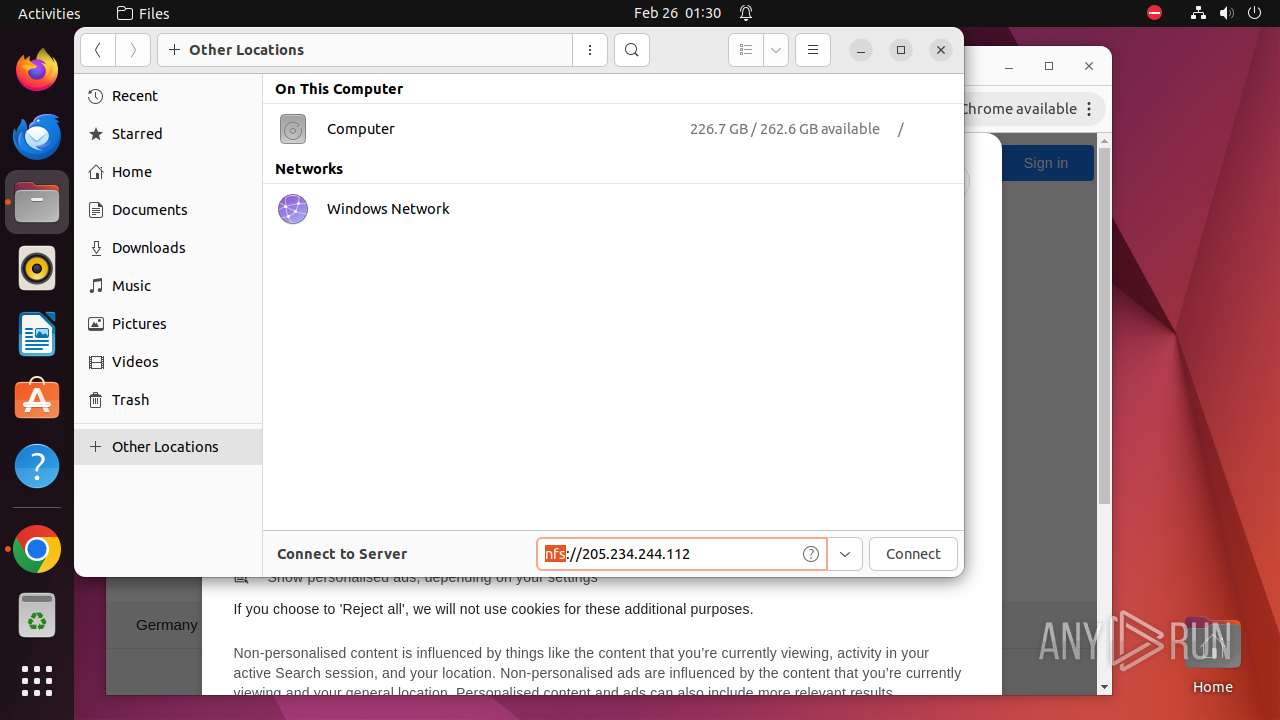
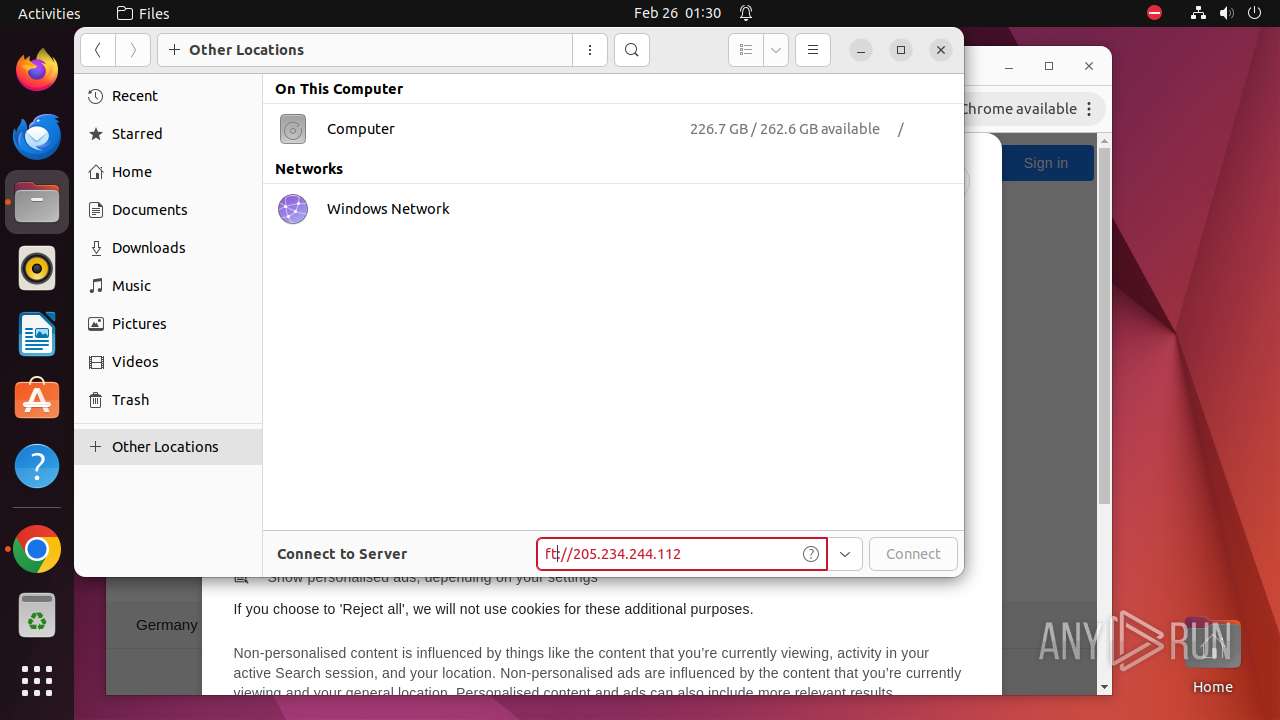
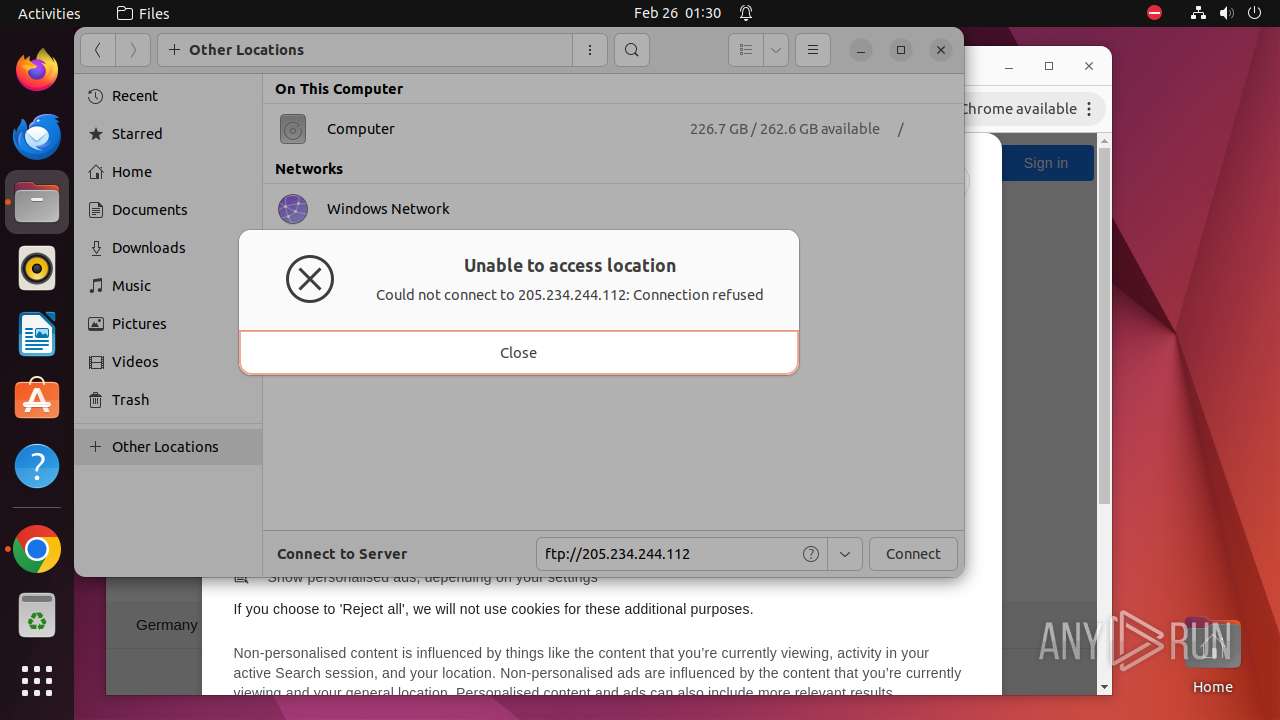
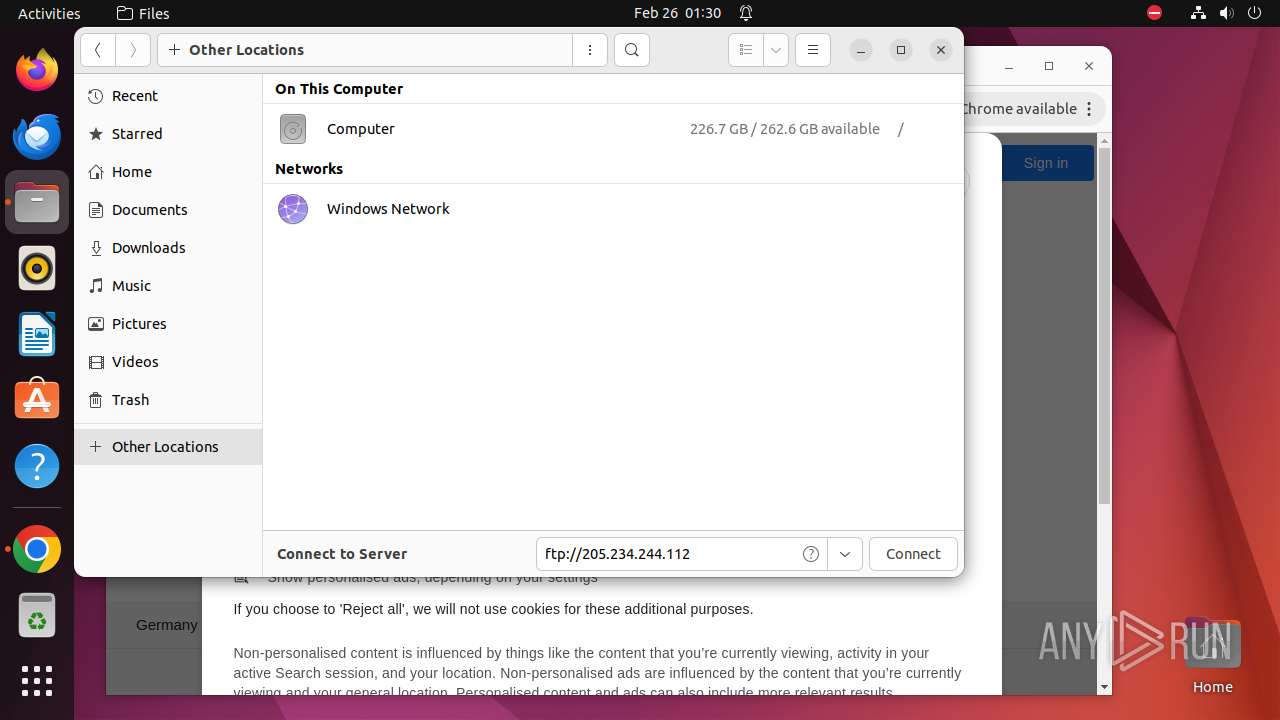
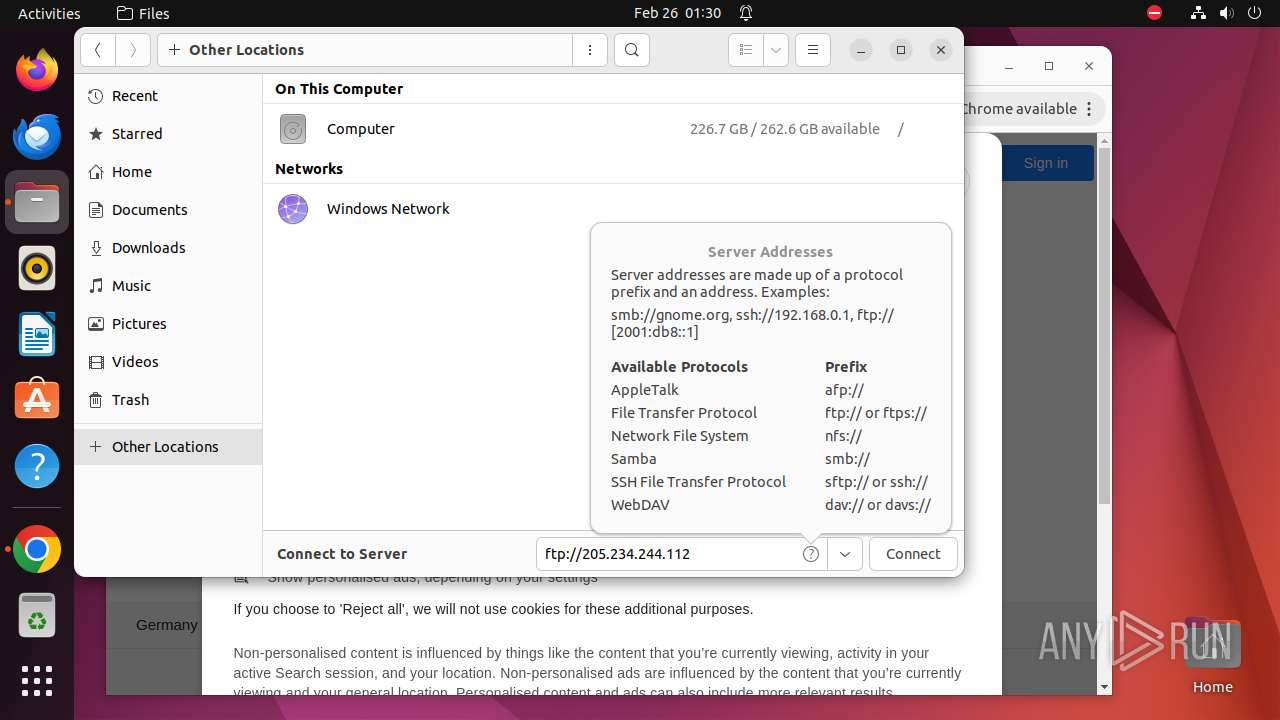
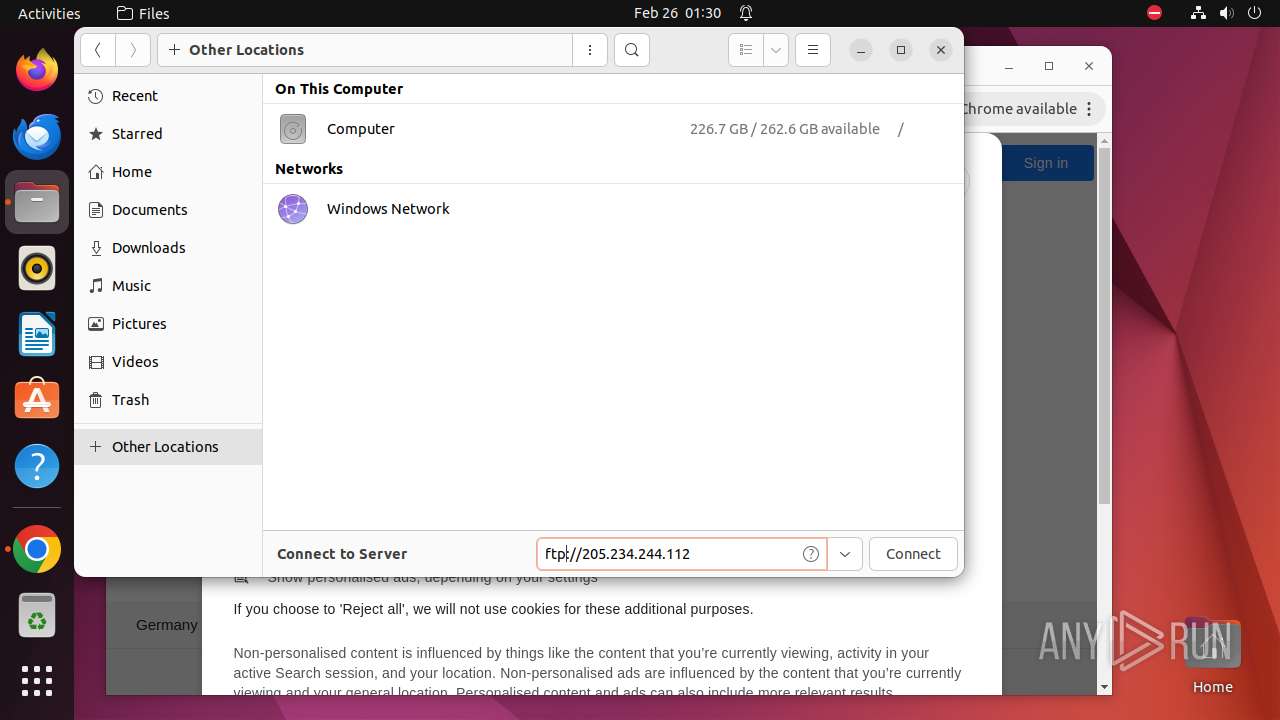
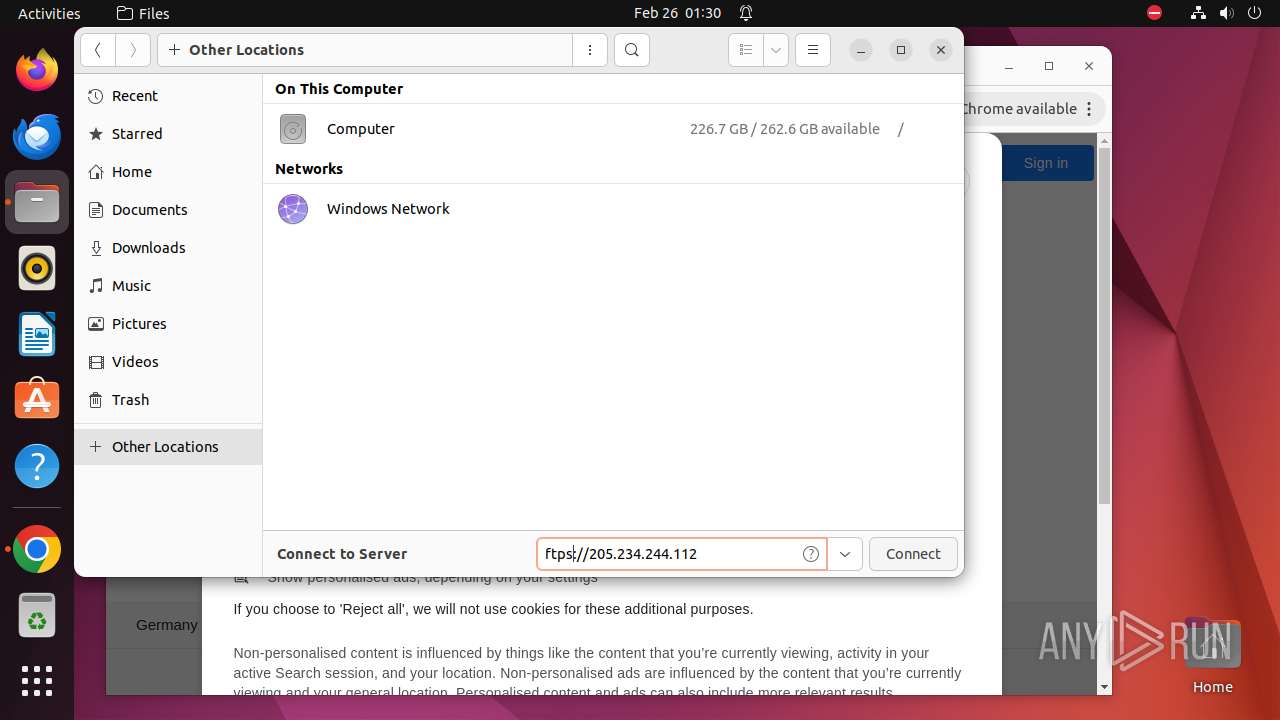
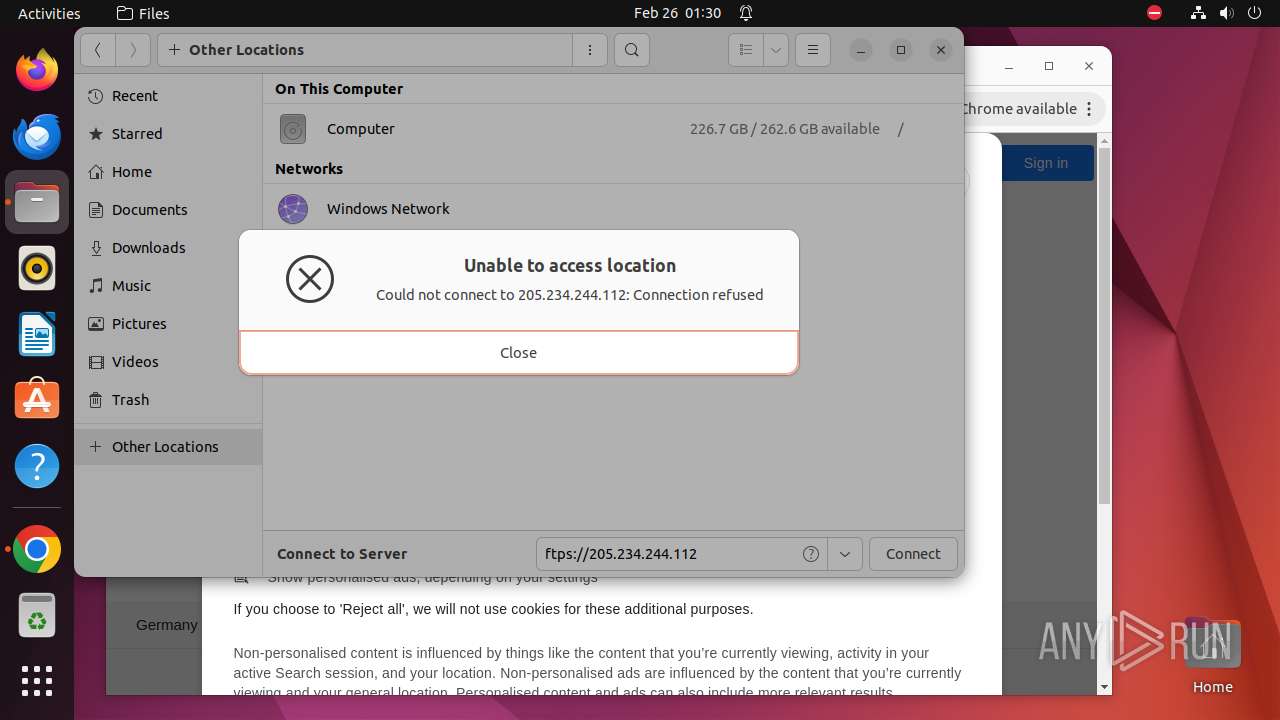
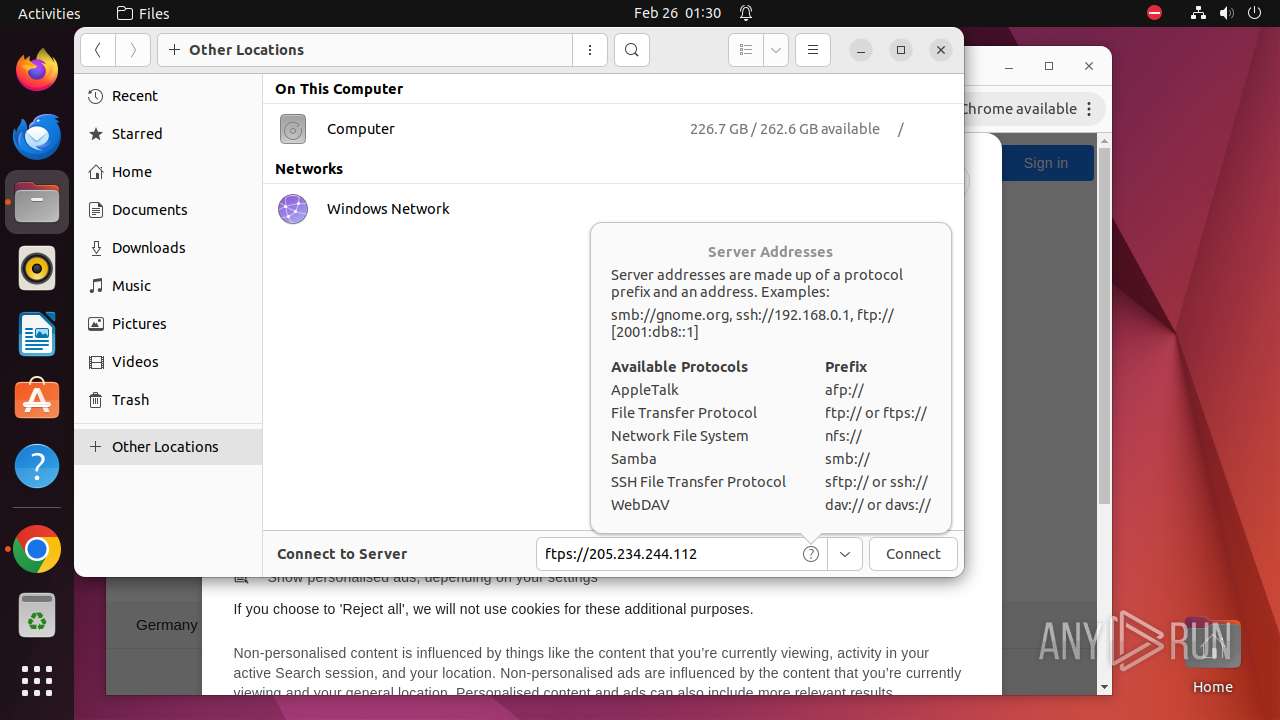
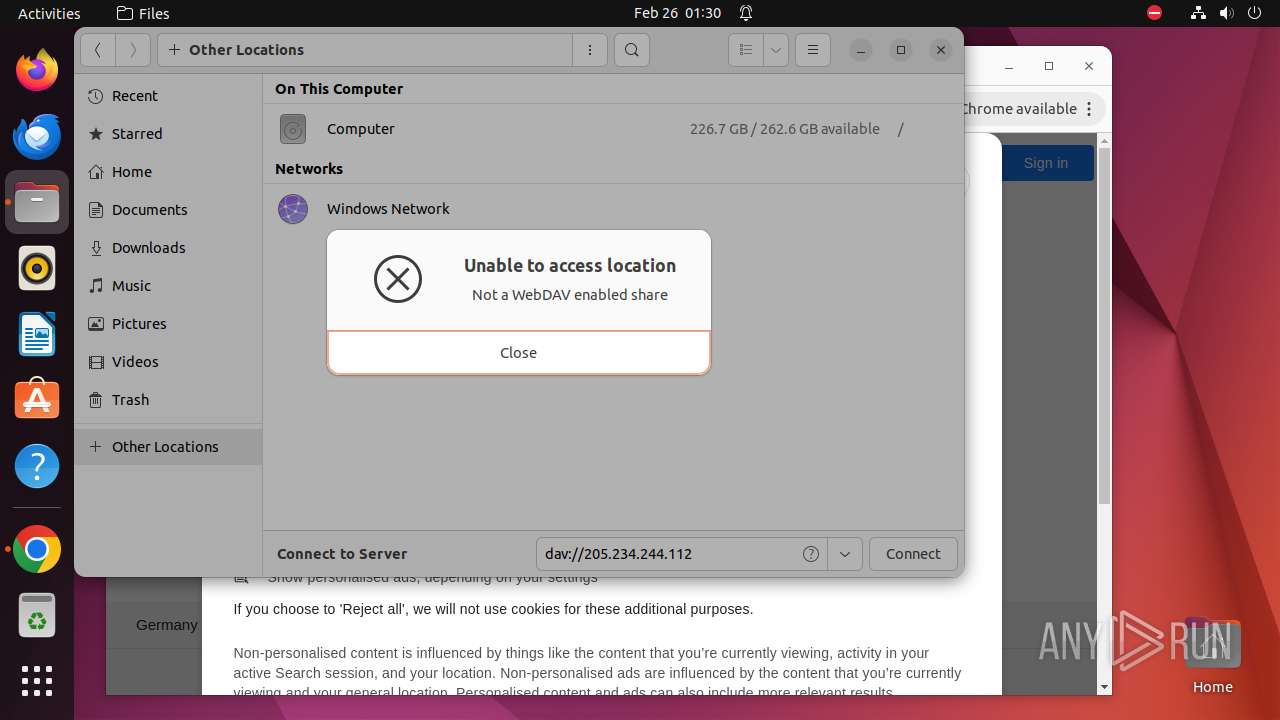
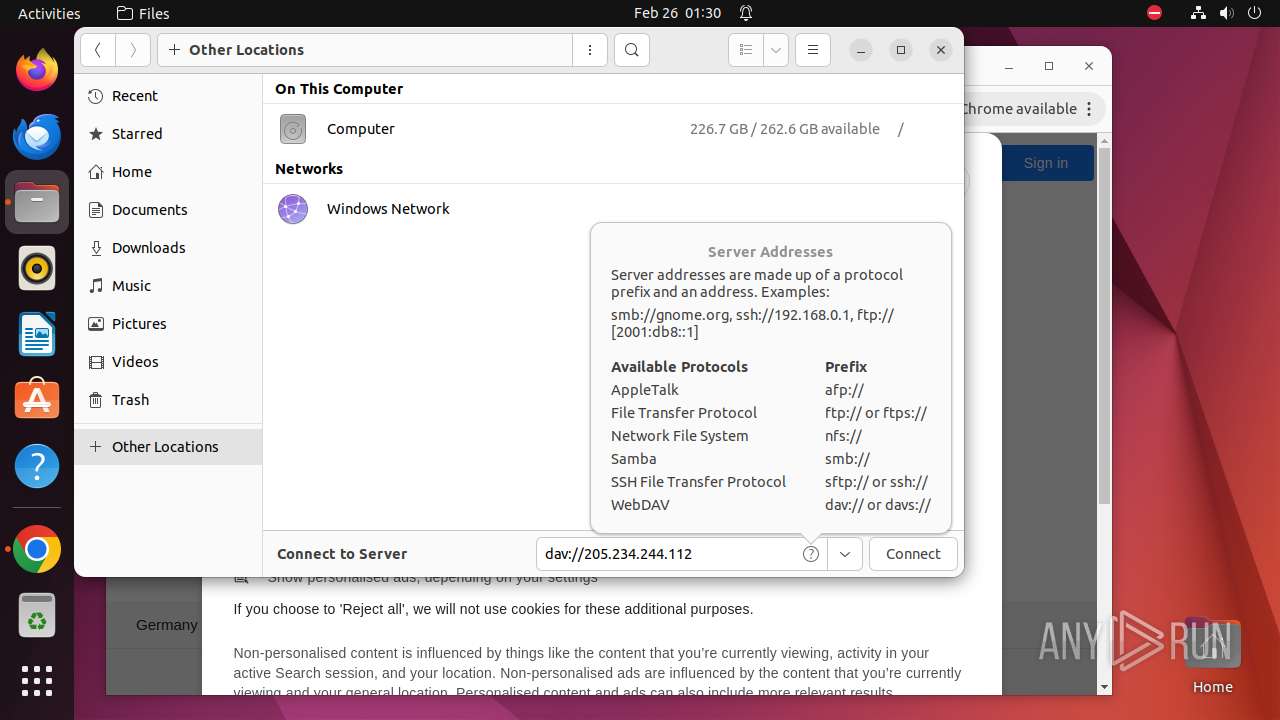
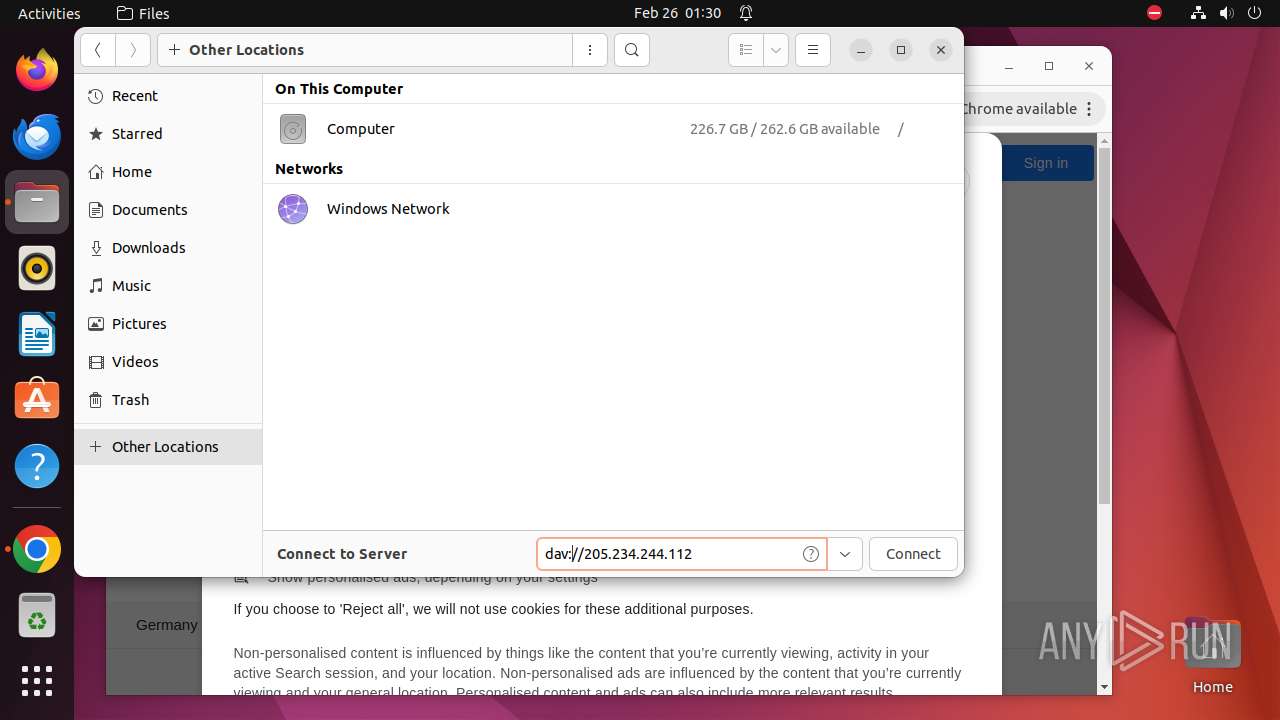
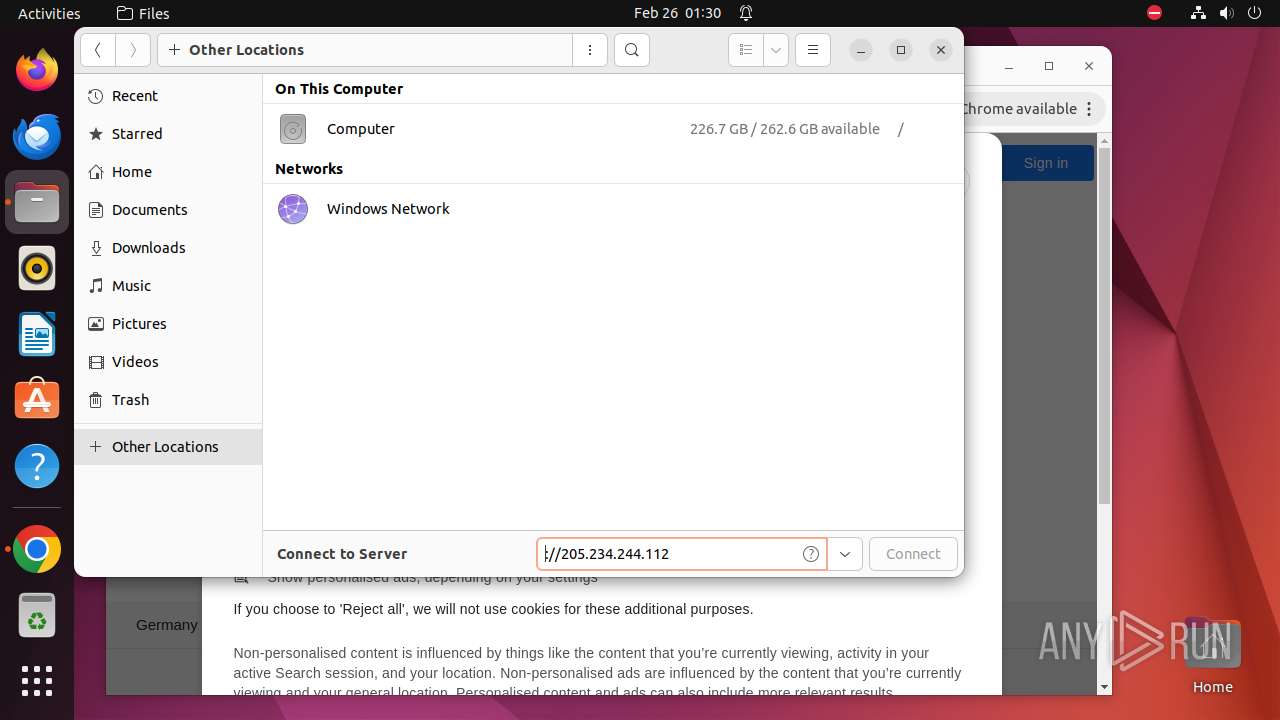
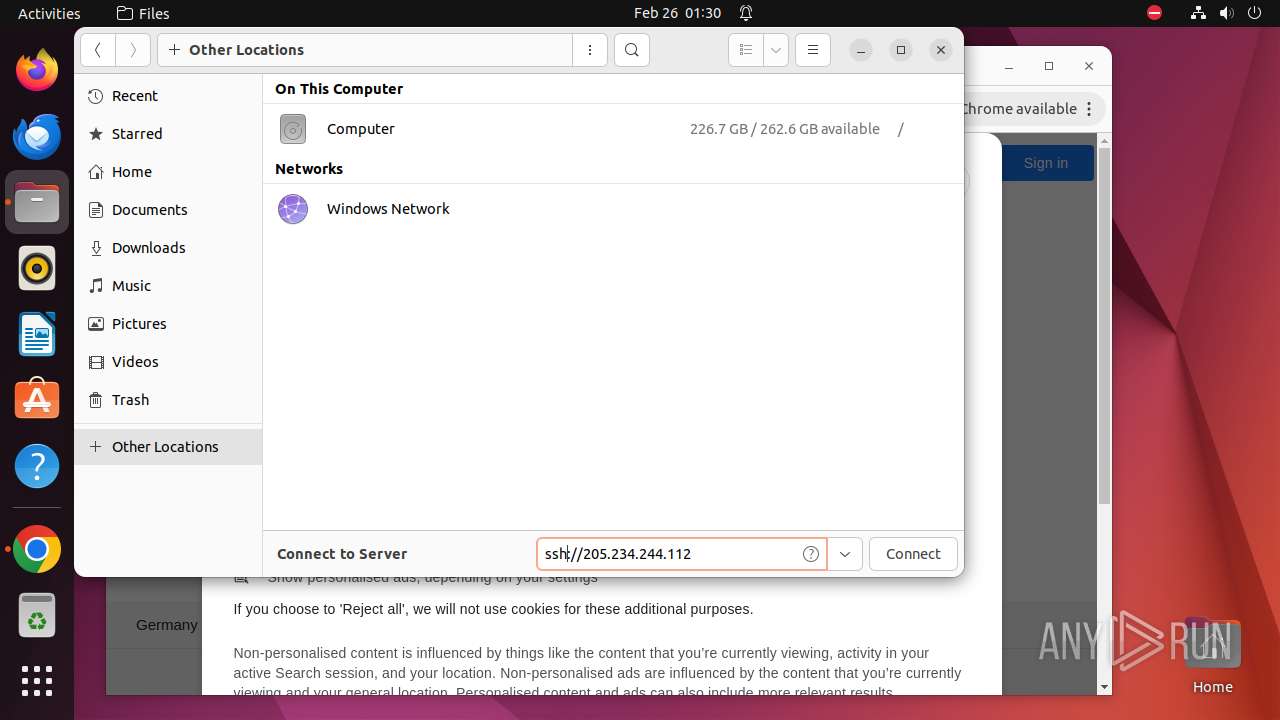
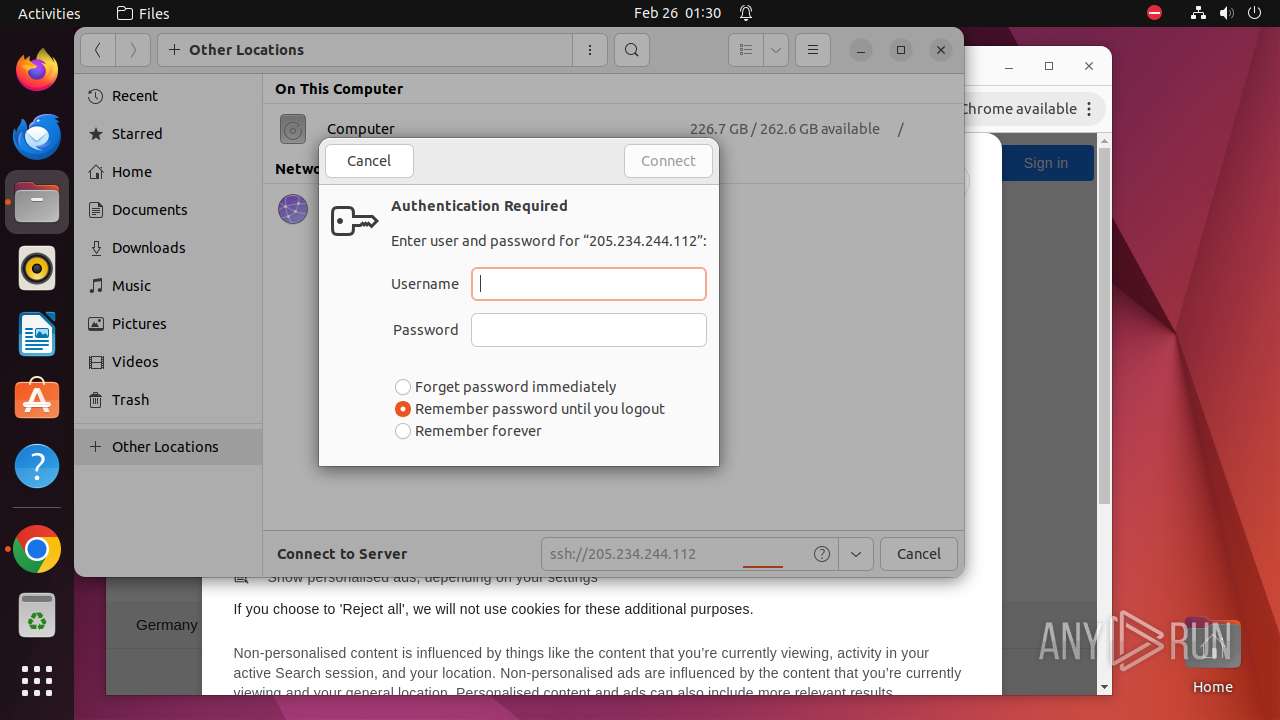
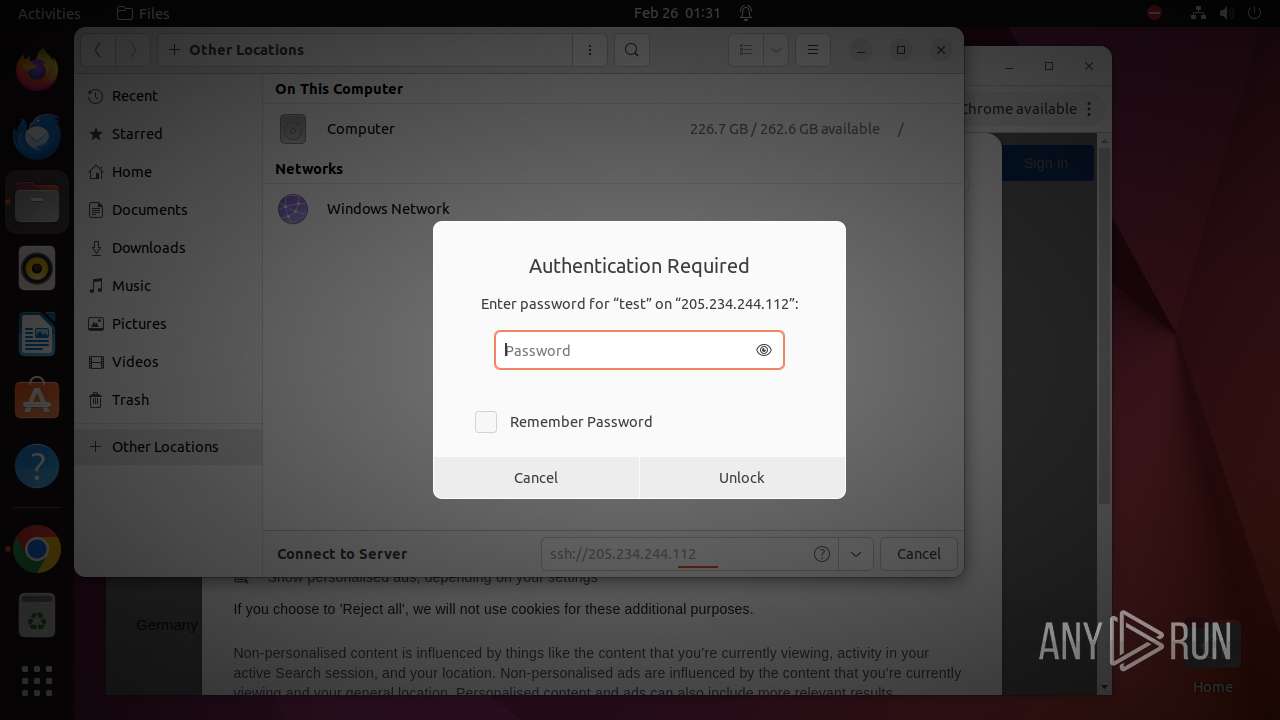
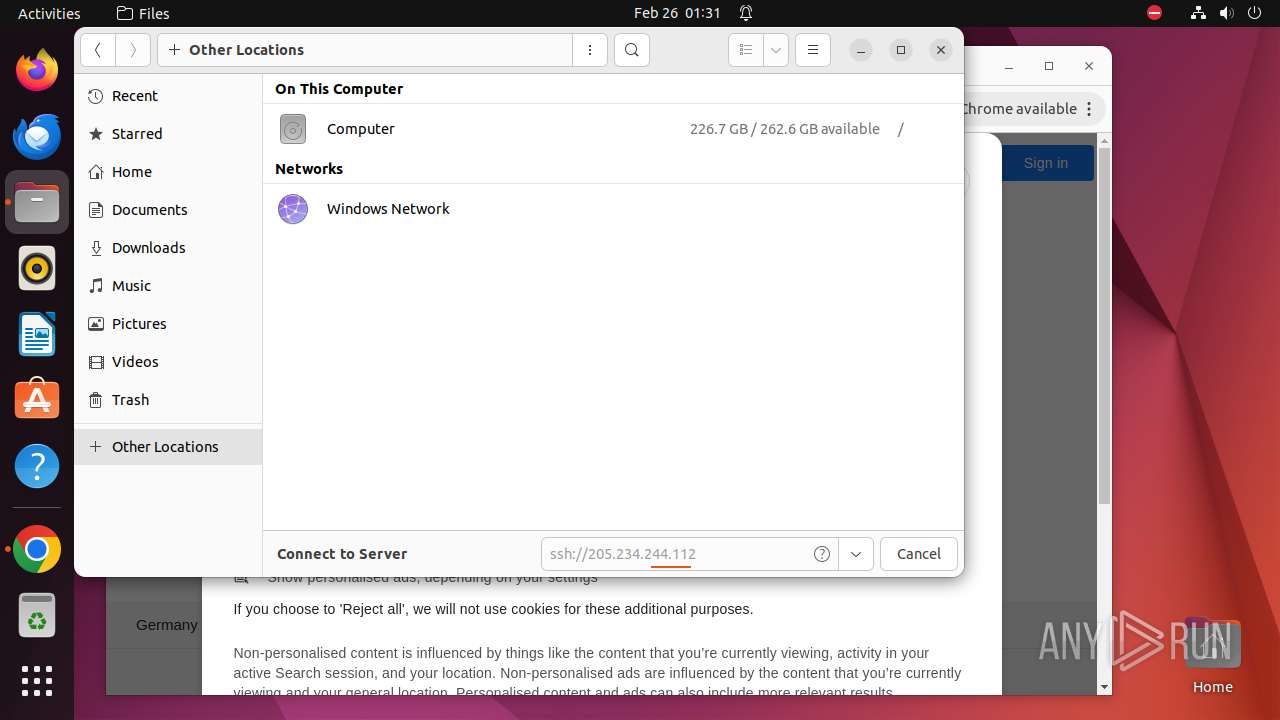
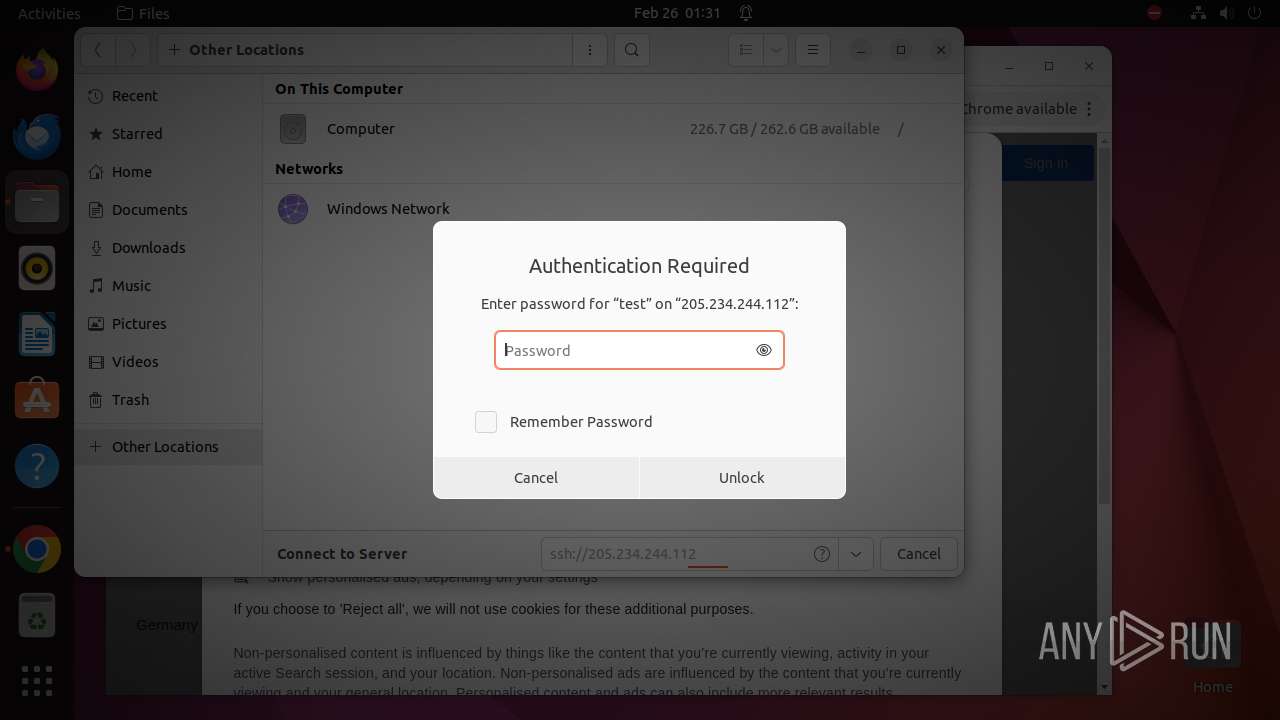
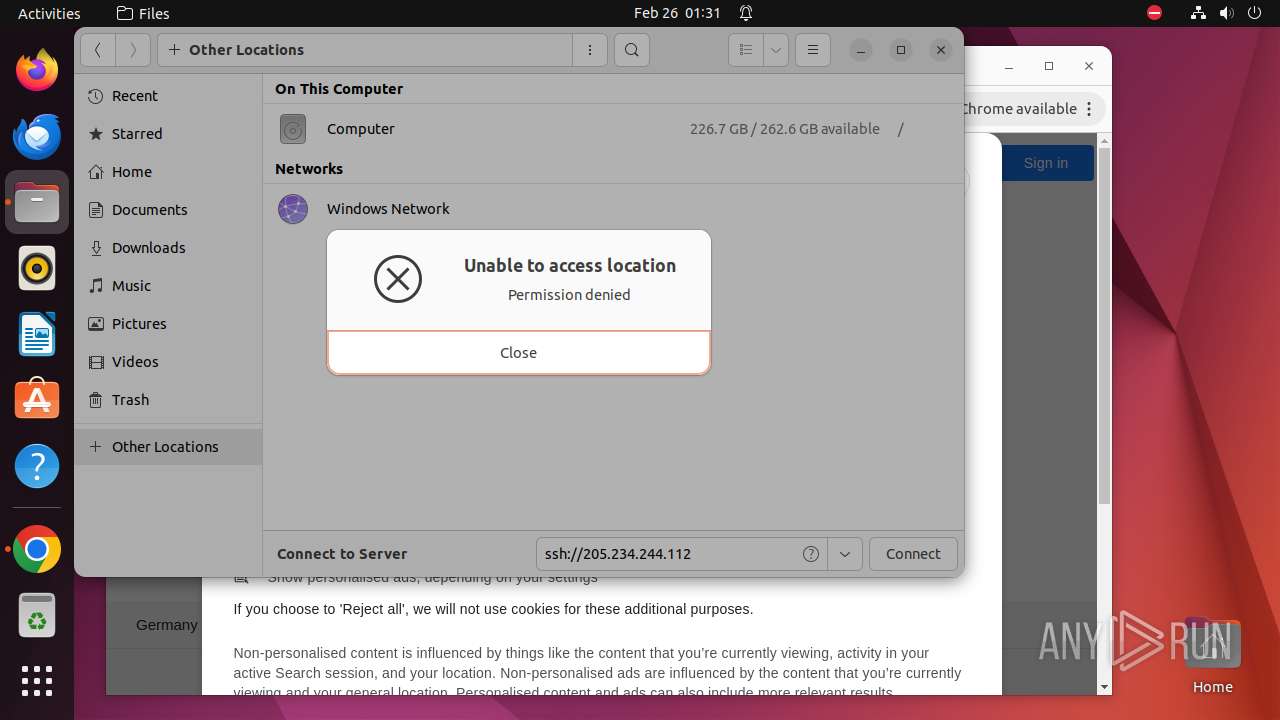
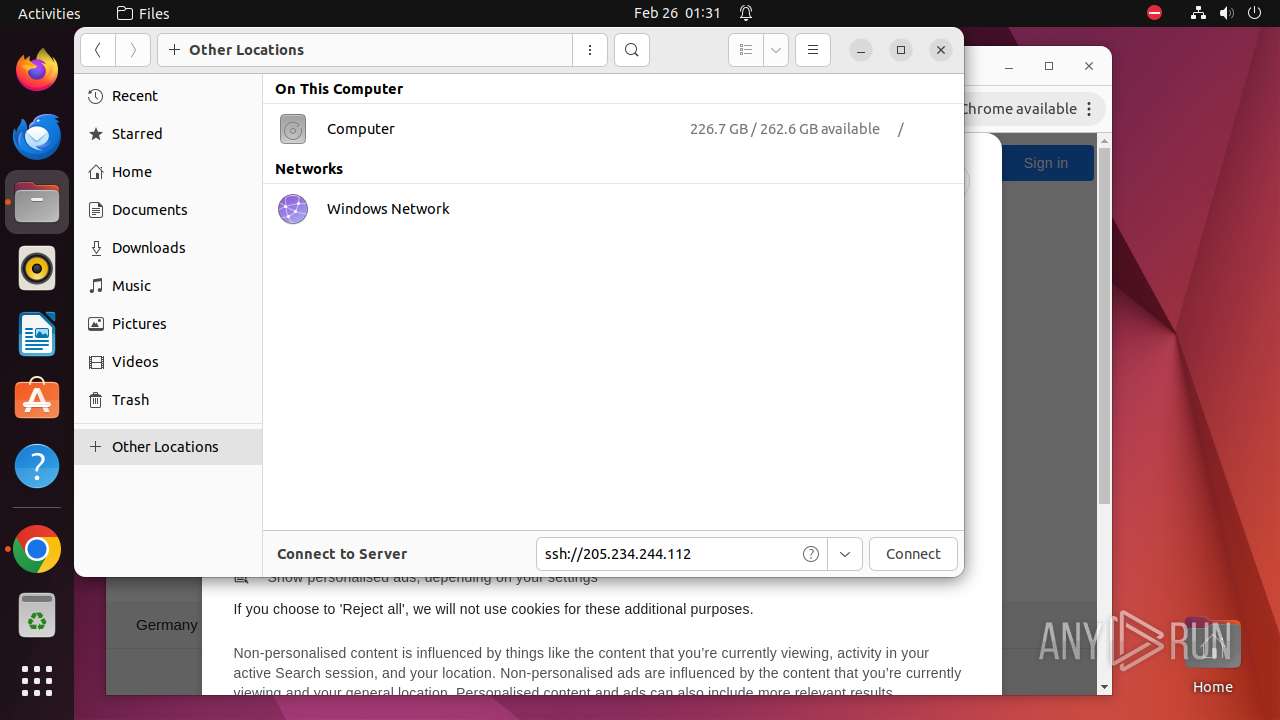
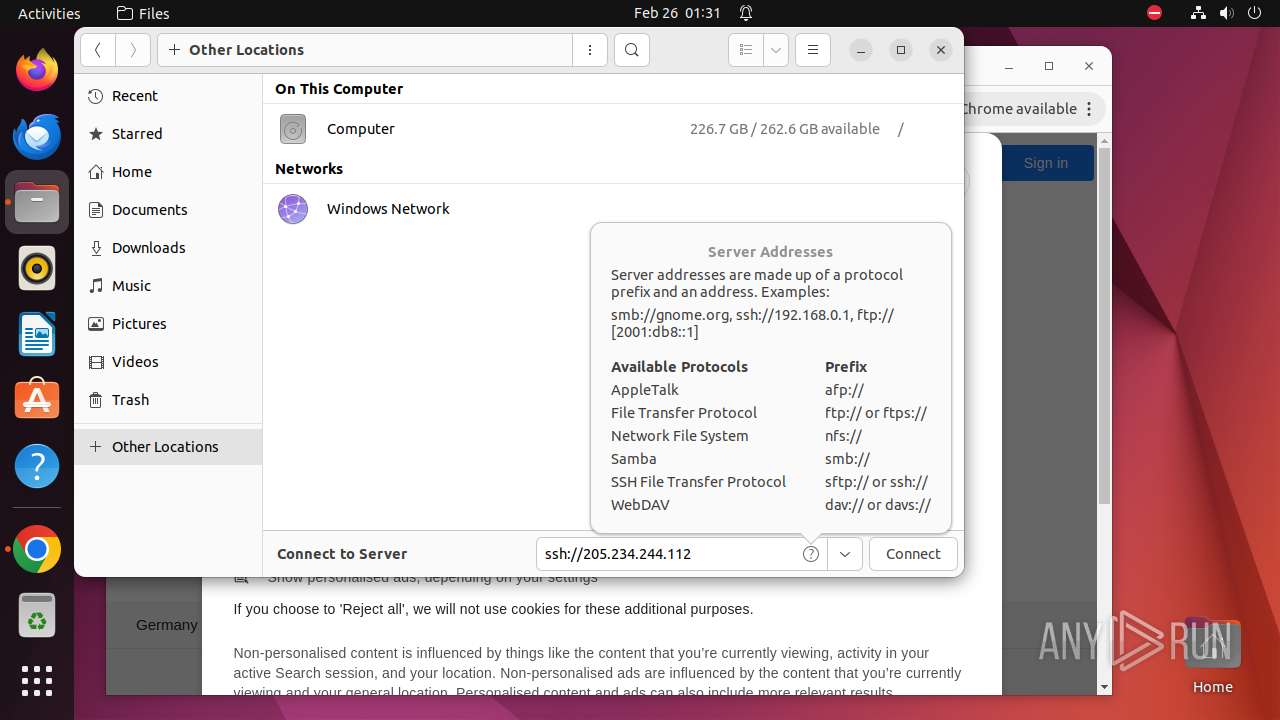
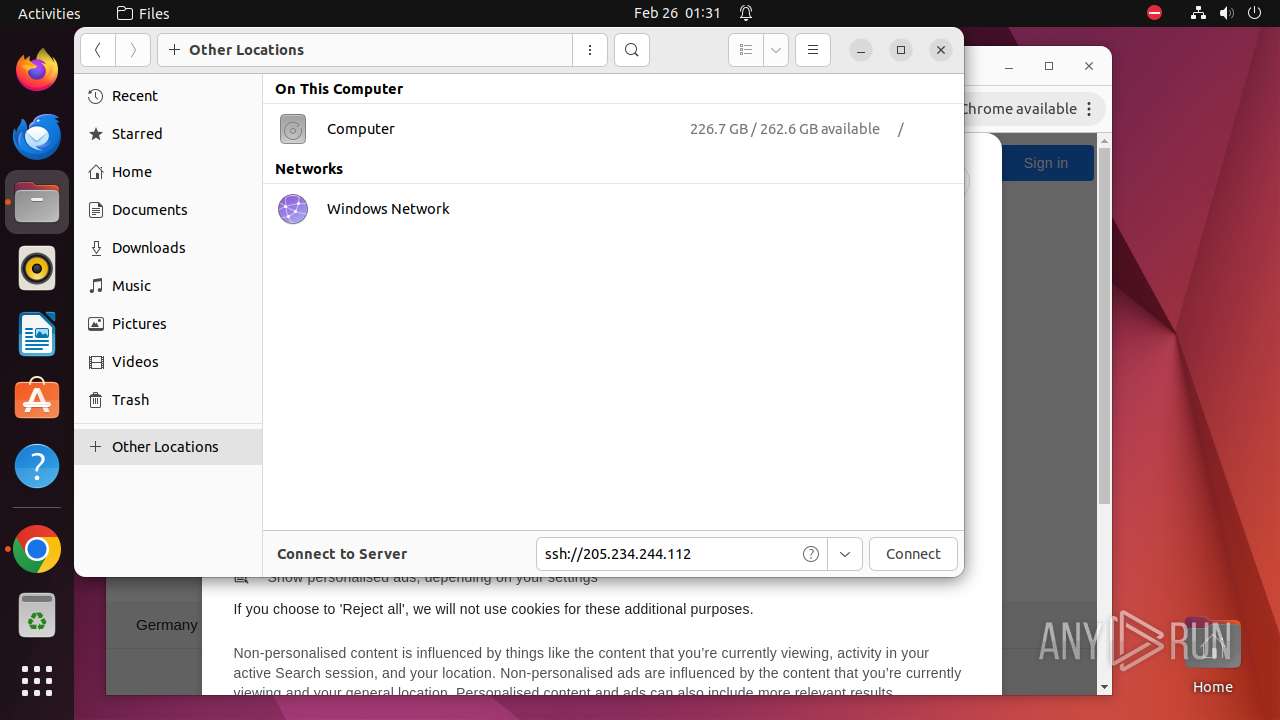
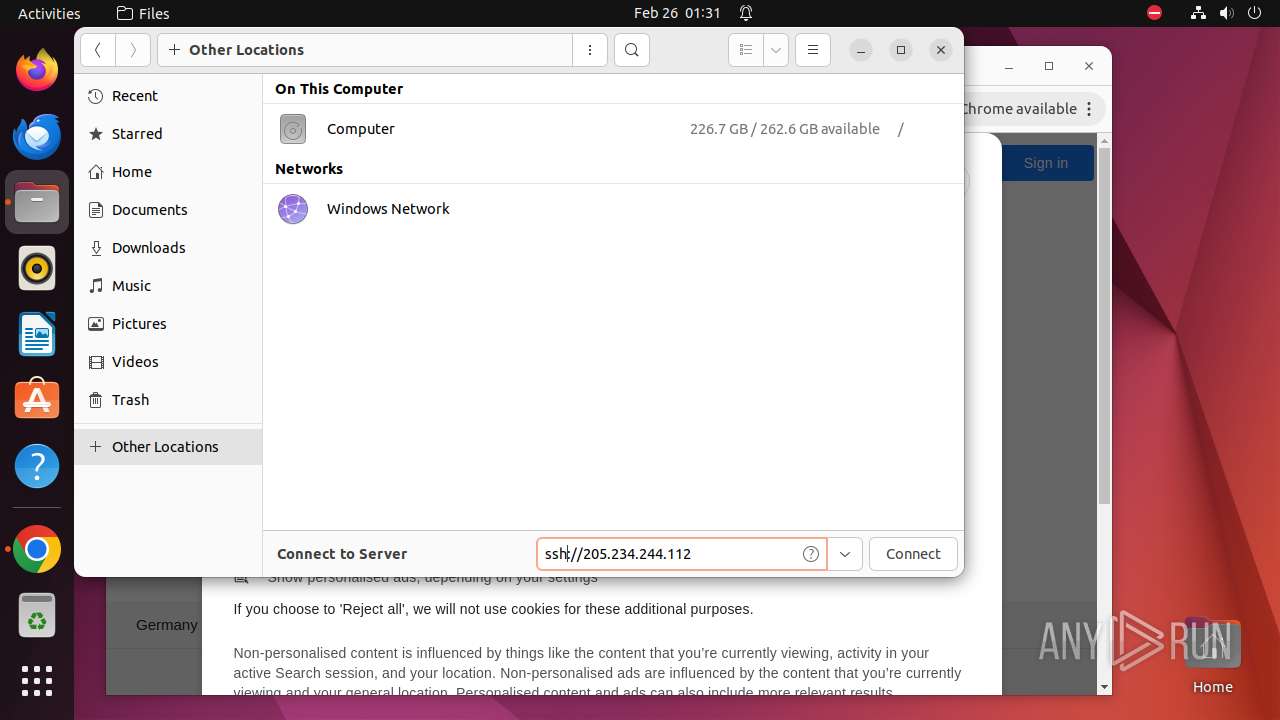
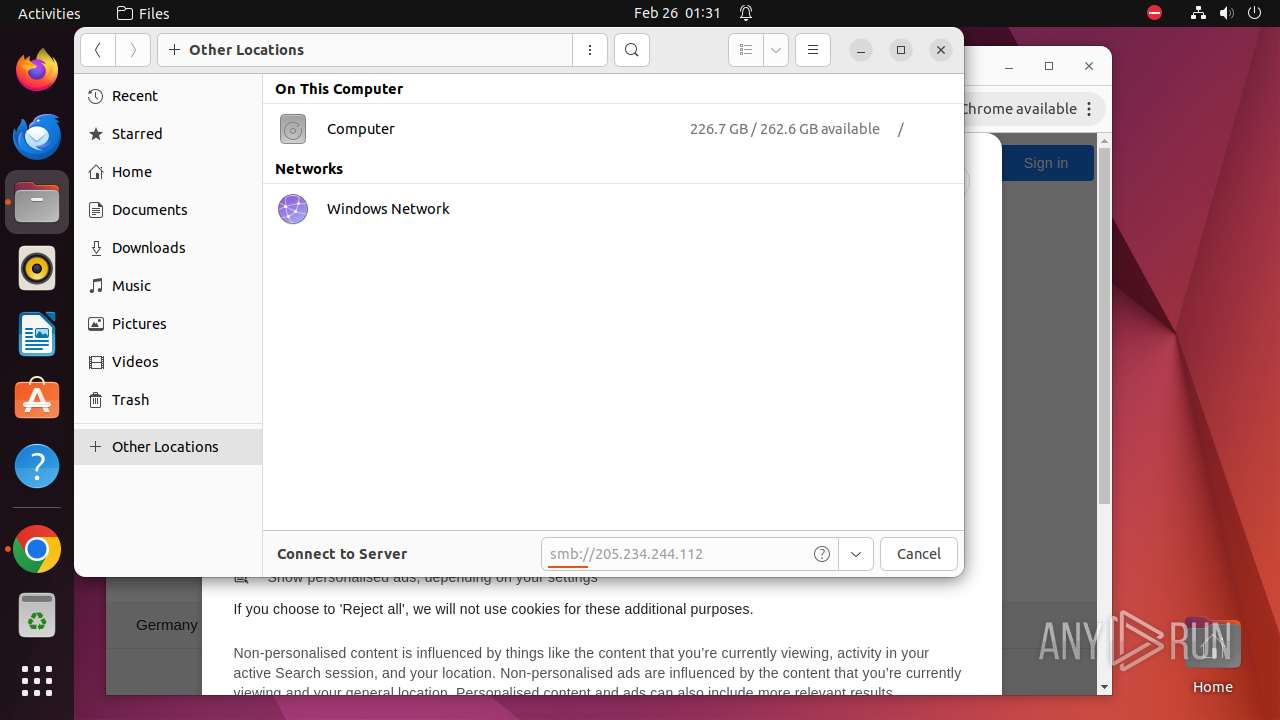
— | — | OPTIONS | 200 | 205.234.244.112:80 | http://205.234.244.112/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.185.100:443 | www.google.com | — | — | unknown |
— | — | 142.250.186.78:443 | — | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.185.131:443 | www.gstatic.com | GOOGLE | US | unknown |
— | — | 172.217.16.202:443 | content-autofill.googleapis.com | GOOGLE | US | unknown |
— | — | 142.250.186.46:443 | apis.google.com | GOOGLE | US | unknown |
— | — | 172.217.16.195:443 | update.googleapis.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
google.com |
| unknown |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
plus.l.google.com |
| unknown |
update.googleapis.com |
| whitelisted |
105.100.168.192.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
— | — | Potential Corporate Privacy Violation | POLICY [ANY.RUN] NTLM Over SMB (NTLMSSP_NEGOTIATE) |