| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/c5bf6dde-839f-4ebe-9795-773cab2346e2 |
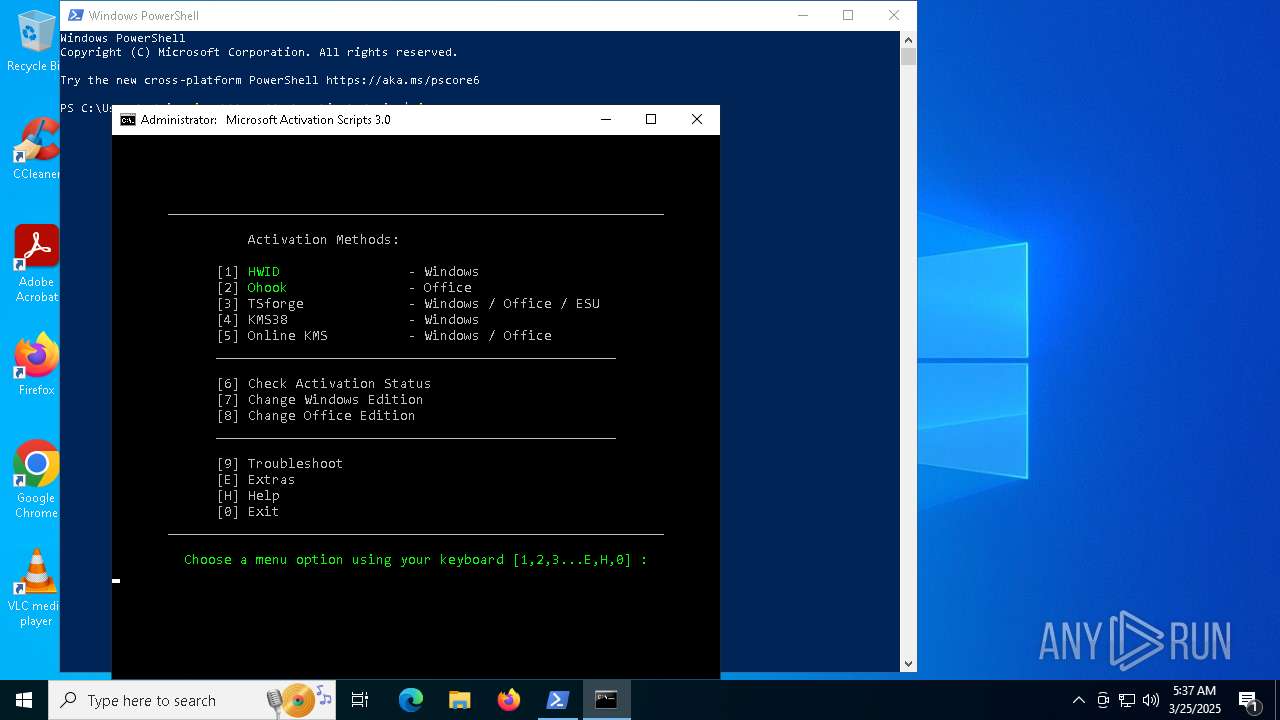
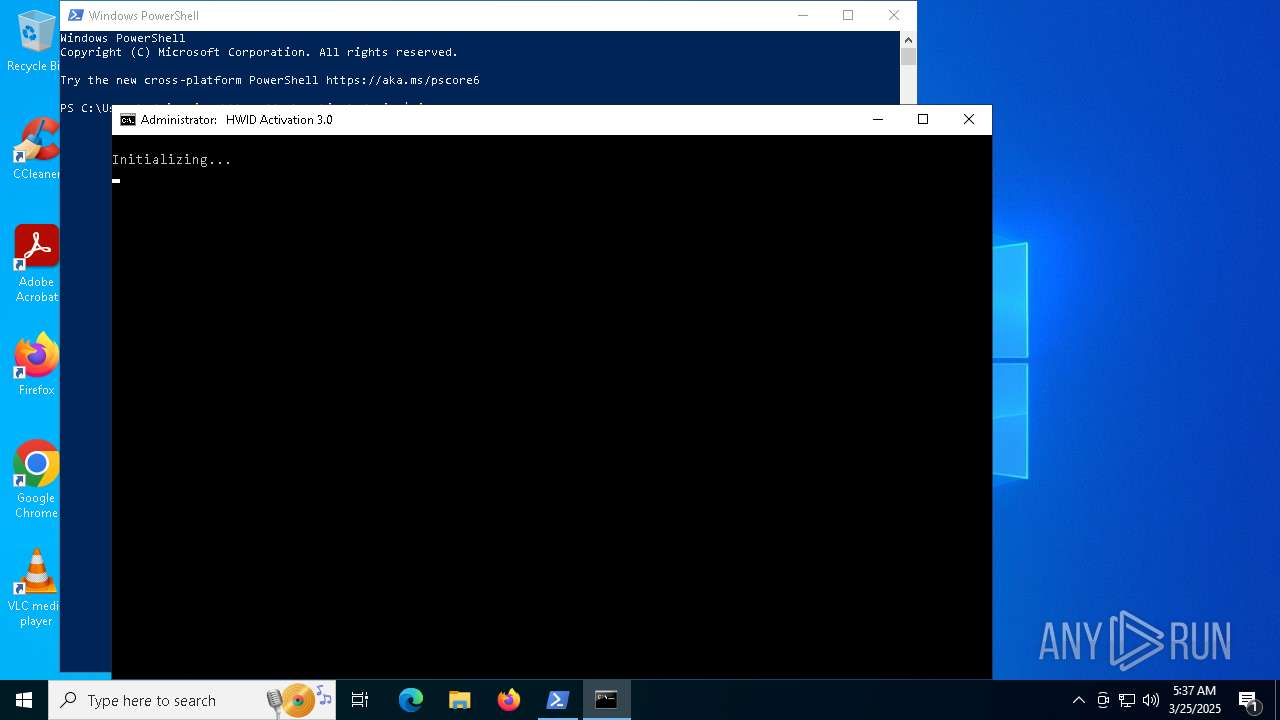
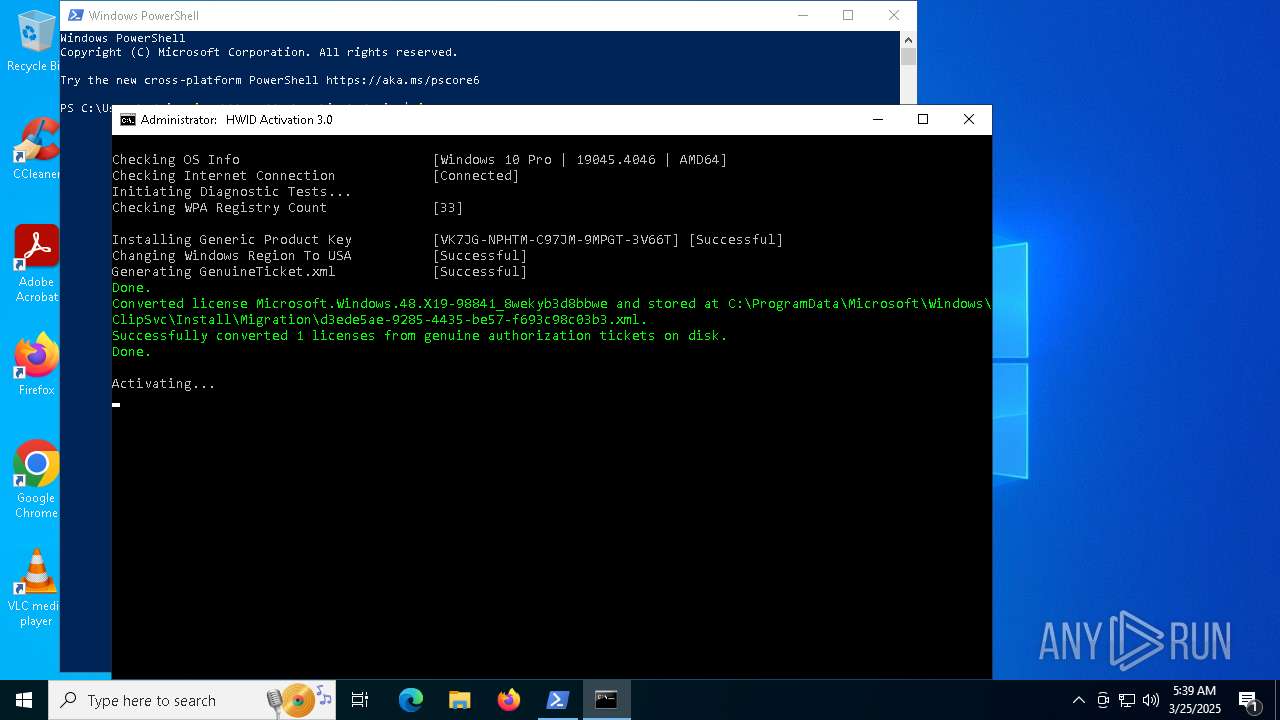
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 05:35:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 6724)
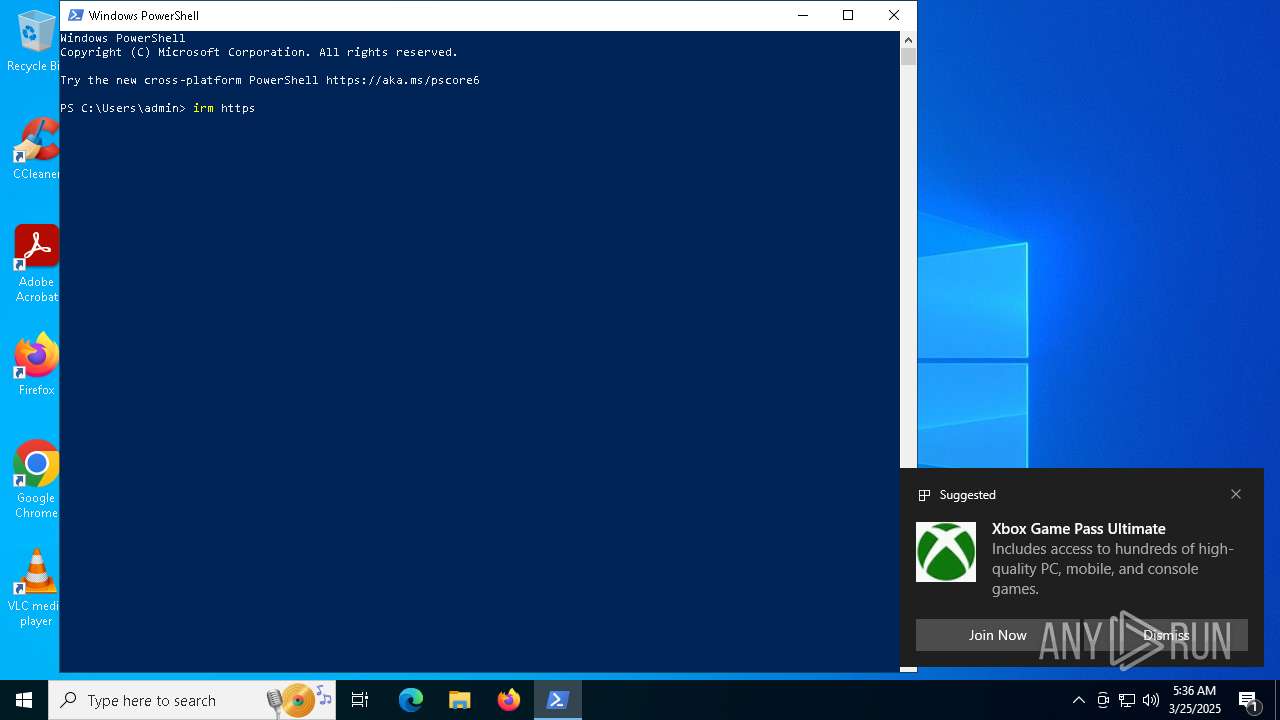
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7500)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7652)
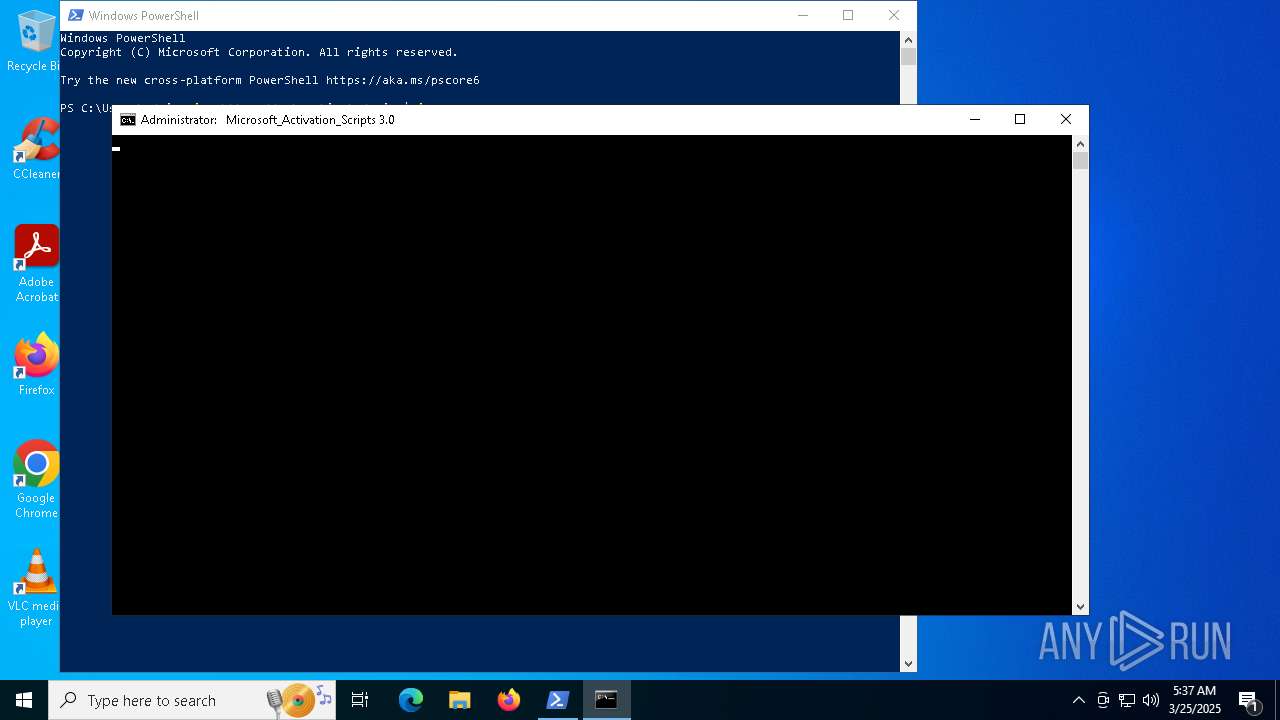
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7500)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8508)
- powershell.exe (PID: 7324)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 8764)
- powershell.exe (PID: 5352)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7616)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7500)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 7892)
- powershell.exe (PID: 8112)
Starts SC.EXE for service management
- cmd.exe (PID: 8508)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 7616)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 7892)
Executing commands from ".cmd" file
- powershell.exe (PID: 7500)
- cmd.exe (PID: 8508)
- powershell.exe (PID: 7324)
- cmd.exe (PID: 8824)
- powershell.exe (PID: 5352)
- cmd.exe (PID: 7616)
Windows service management via SC.EXE
- sc.exe (PID: 7816)
- sc.exe (PID: 920)
- sc.exe (PID: 7416)
- sc.exe (PID: 2596)
- sc.exe (PID: 5736)
- sc.exe (PID: 7840)
- sc.exe (PID: 1672)
- sc.exe (PID: 6852)
- sc.exe (PID: 7376)
- sc.exe (PID: 2416)
- sc.exe (PID: 7312)
- sc.exe (PID: 6436)
- sc.exe (PID: 6572)
- sc.exe (PID: 7784)
- sc.exe (PID: 8404)
- sc.exe (PID: 8168)
- sc.exe (PID: 3028)
- sc.exe (PID: 132)
- sc.exe (PID: 8944)
- sc.exe (PID: 7052)
- sc.exe (PID: 8868)
- sc.exe (PID: 2664)
- sc.exe (PID: 5216)
- sc.exe (PID: 2596)
- sc.exe (PID: 2560)
- sc.exe (PID: 7240)
- sc.exe (PID: 8896)
- sc.exe (PID: 2108)
- sc.exe (PID: 8424)
- sc.exe (PID: 7640)
- sc.exe (PID: 8328)
- sc.exe (PID: 7456)
- sc.exe (PID: 7424)
- sc.exe (PID: 4880)
- sc.exe (PID: 8924)
- sc.exe (PID: 8920)
- sc.exe (PID: 8076)
Application launched itself
- cmd.exe (PID: 8508)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 8764)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7616)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 812)
- ClipUp.exe (PID: 7448)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 6468)
- powershell.exe (PID: 8608)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8508)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 7616)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7692)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7920)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7692)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7920)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7692)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 7532)
- powershell.exe (PID: 7856)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 9056)
- powershell.exe (PID: 812)
- powershell.exe (PID: 8608)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 6468)
- cmd.exe (PID: 8636)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 7892)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7616)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5216)
- cmd.exe (PID: 7616)
Hides command output
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 2984)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7676)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7856)
- powershell.exe (PID: 812)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 6468)
- powershell.exe (PID: 8608)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 2152)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7856)
- powershell.exe (PID: 812)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 6468)
- powershell.exe (PID: 8608)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7616)
INFO
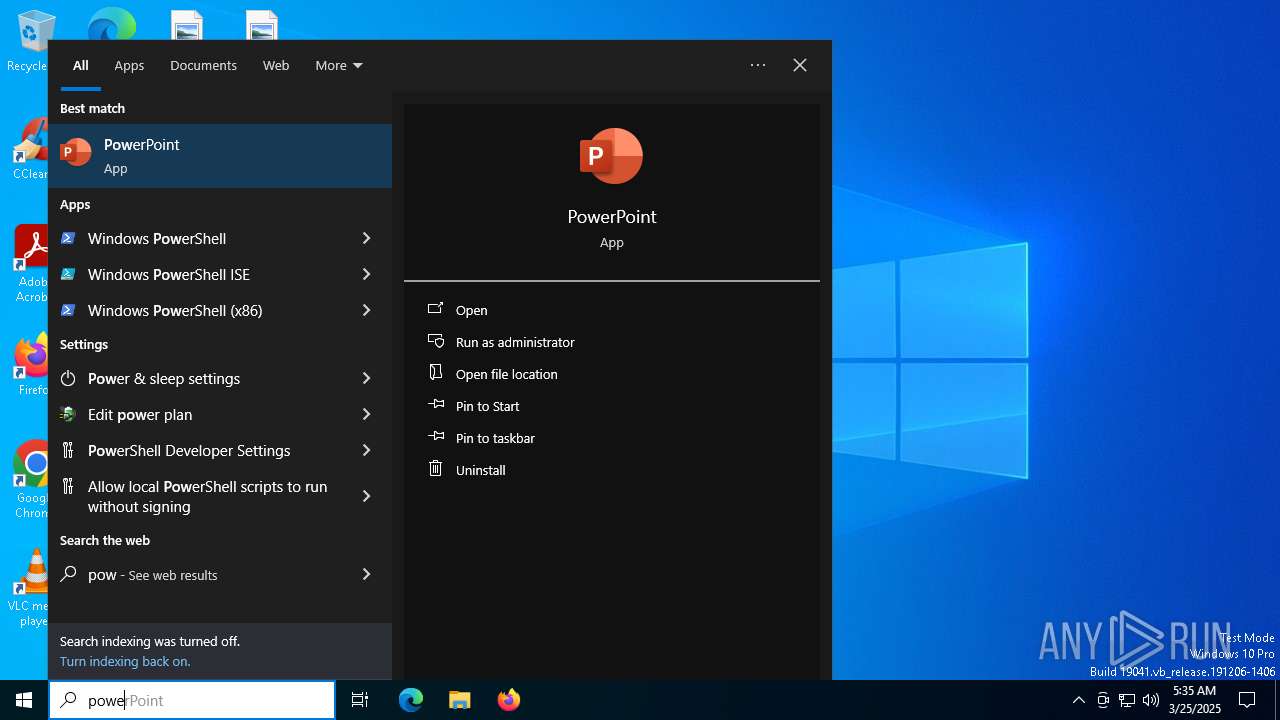
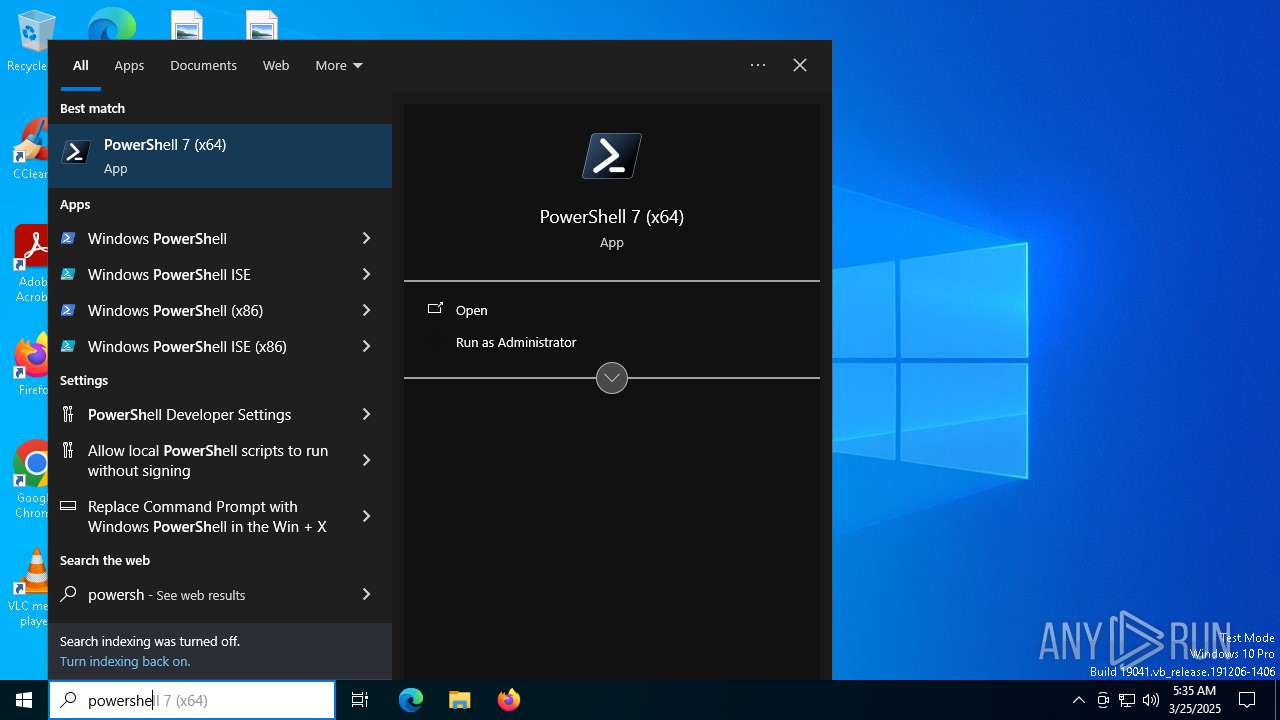
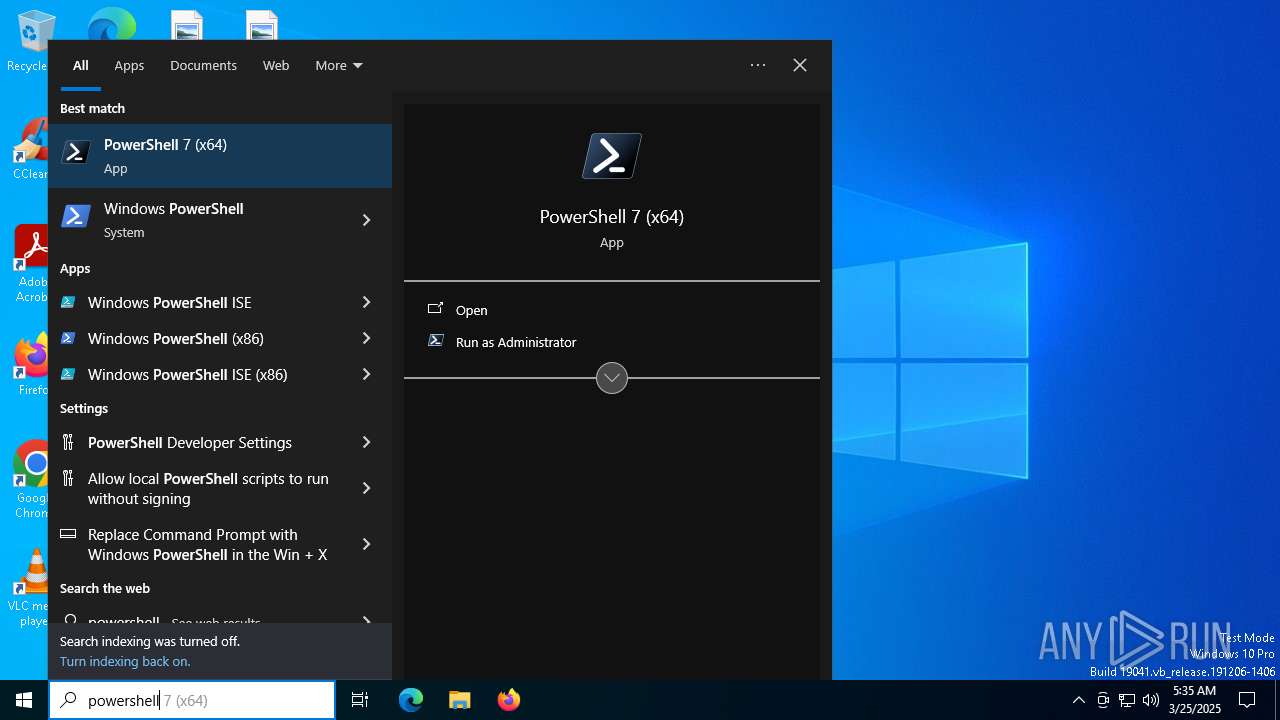
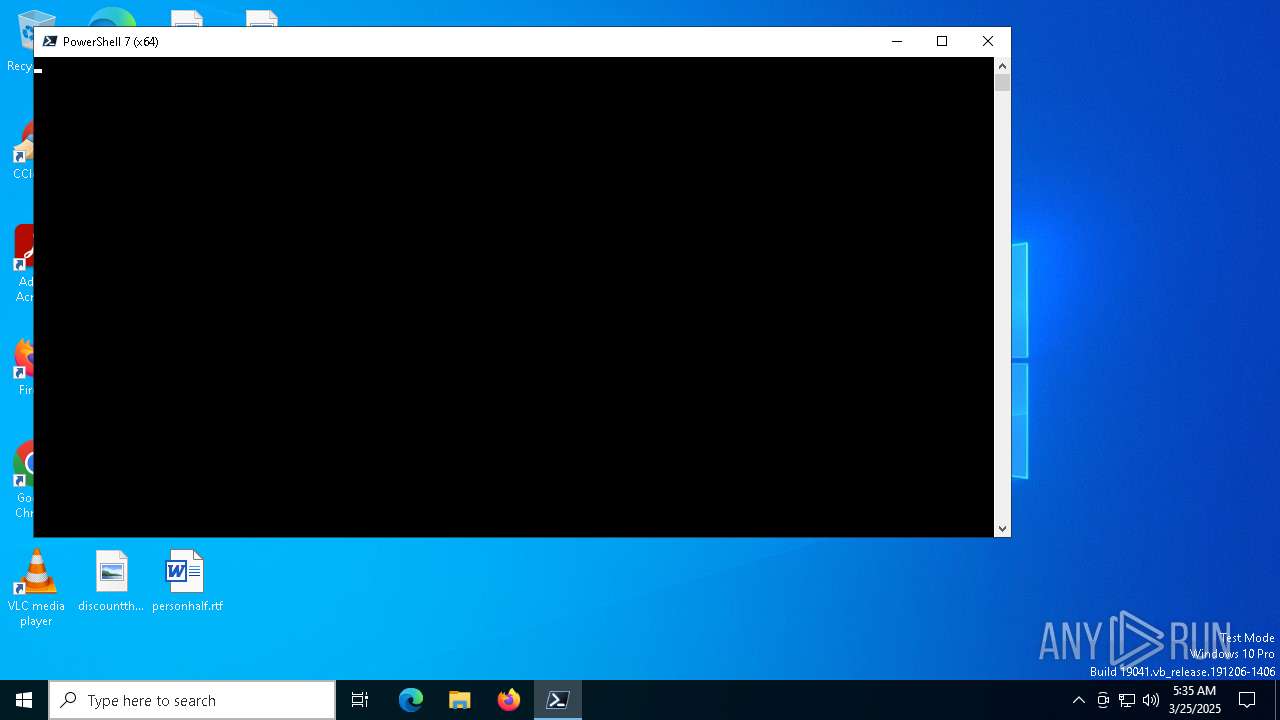
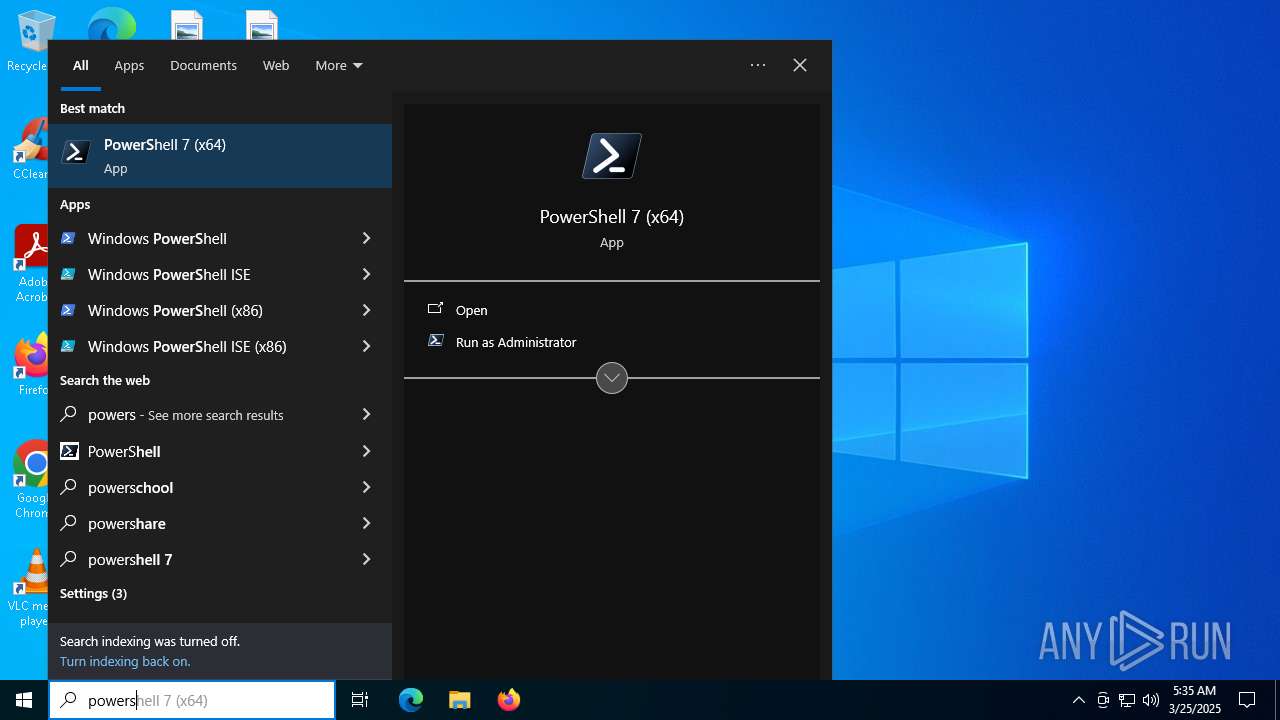
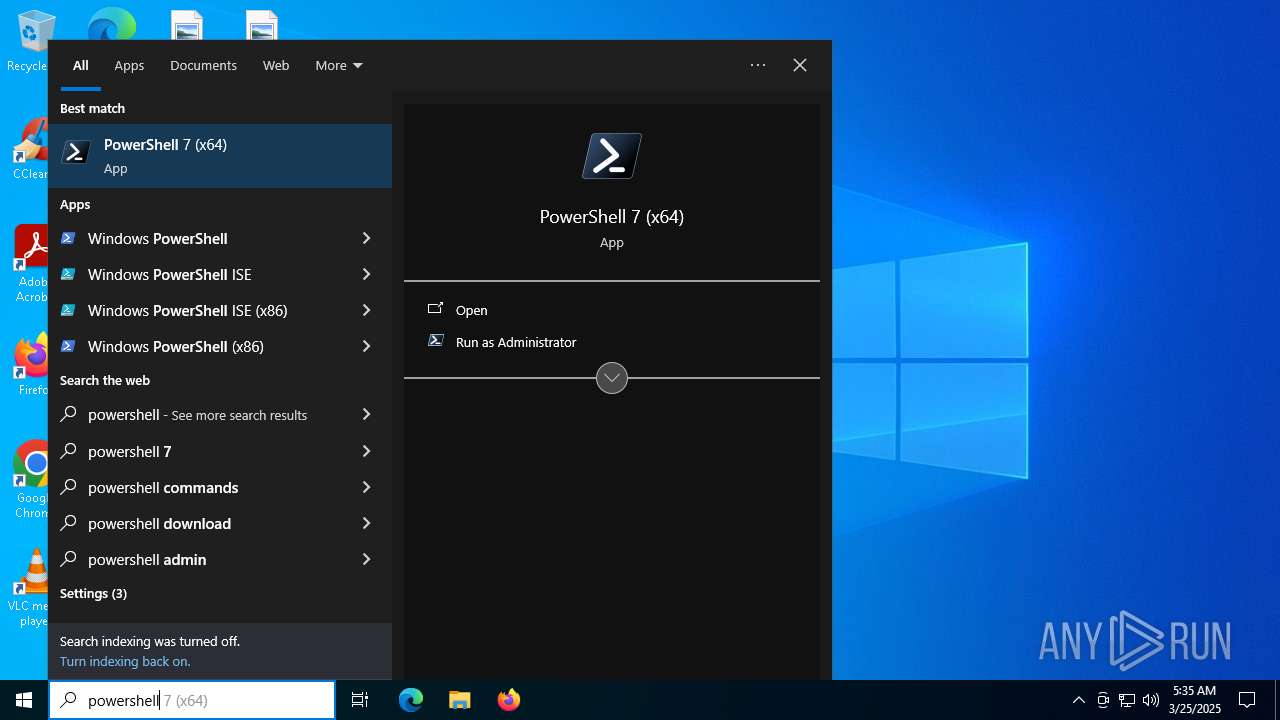
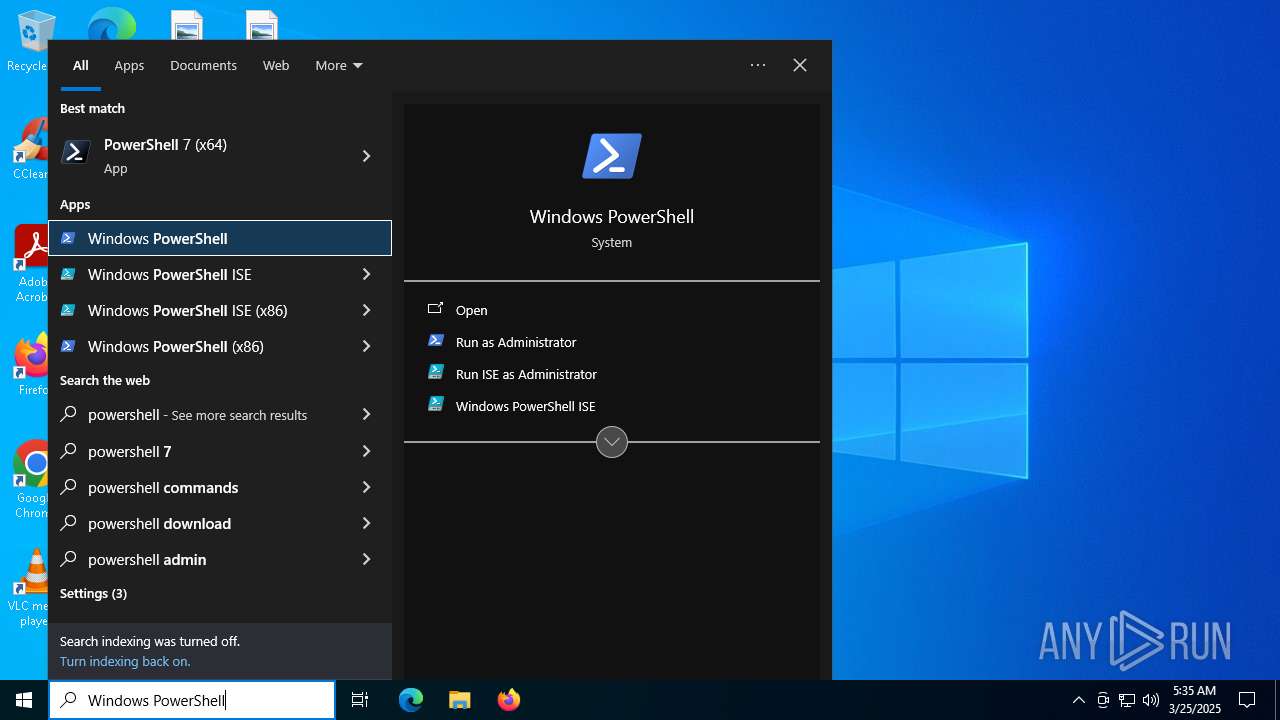
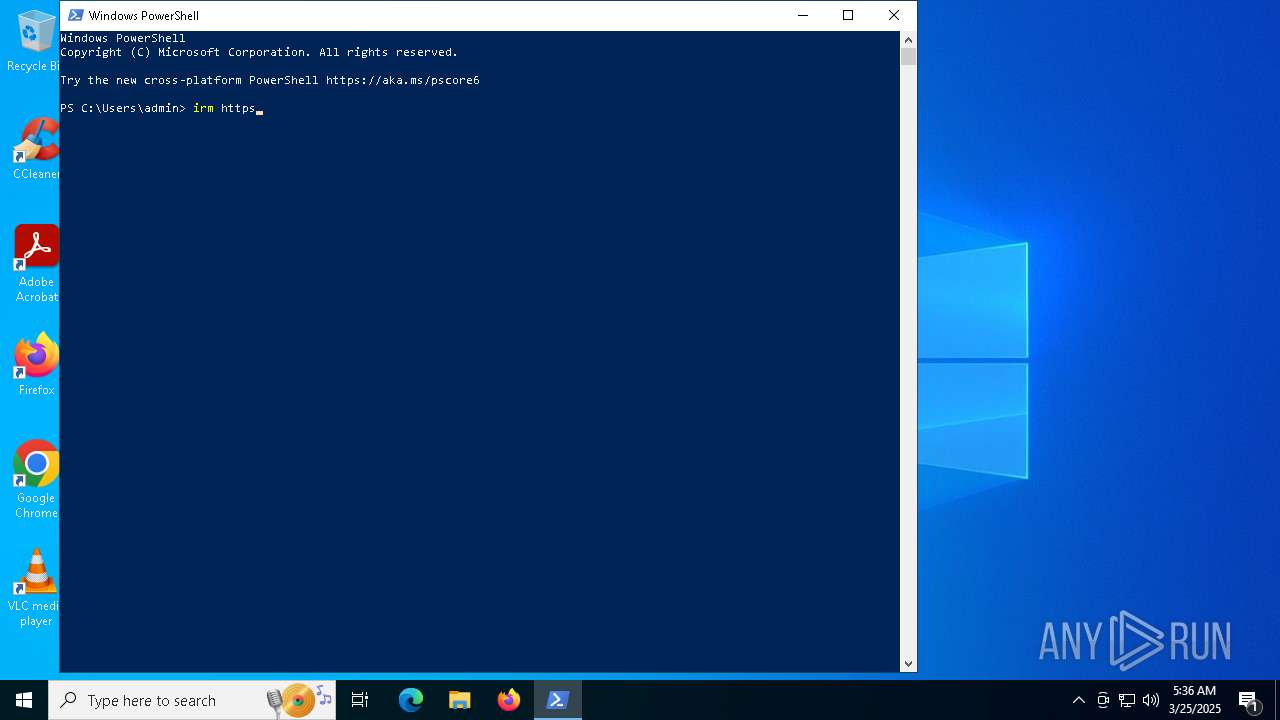
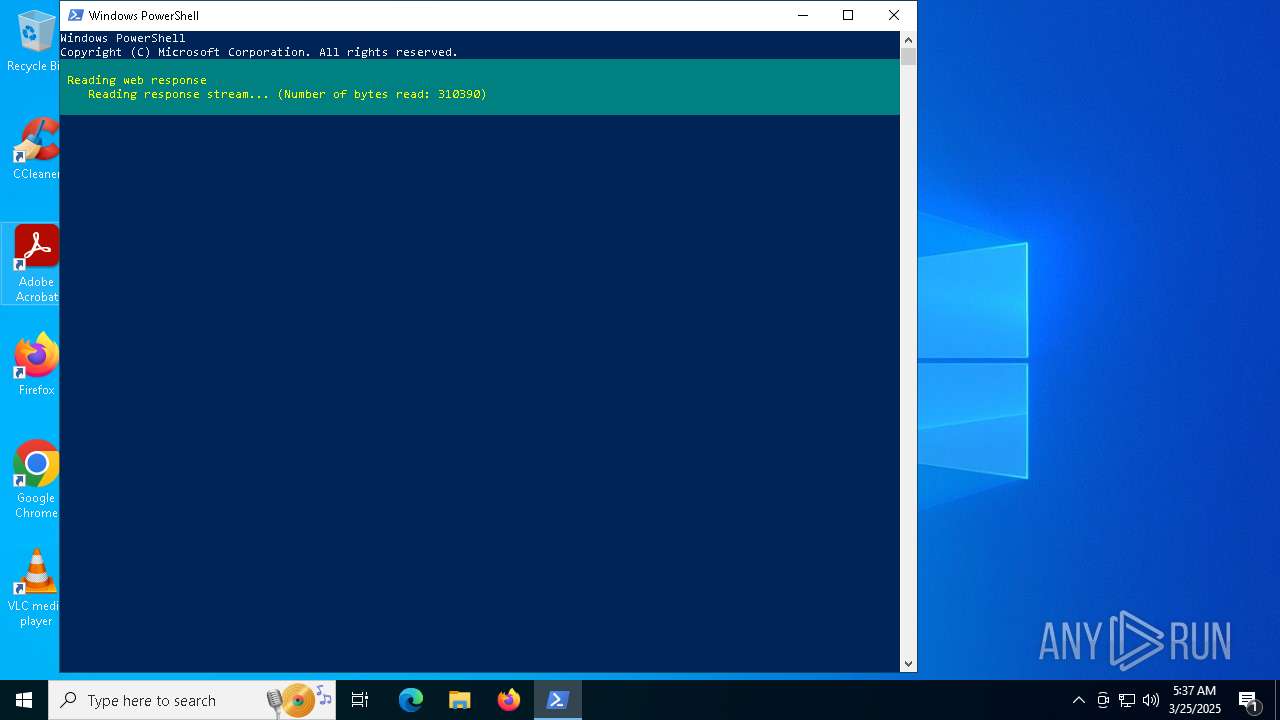
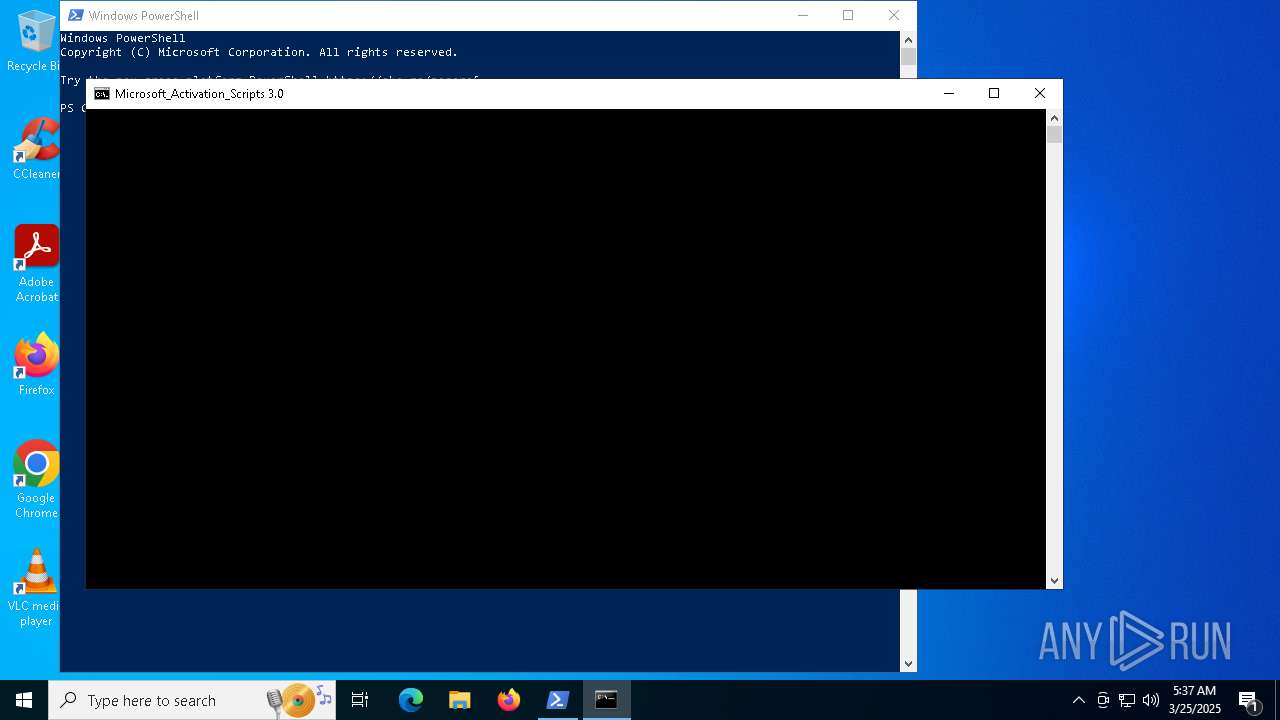
Manual execution by a user
- pwsh.exe (PID: 6724)
- powershell.exe (PID: 7500)
Application launched itself
- firefox.exe (PID: 7248)
- firefox.exe (PID: 7228)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8184)
- BackgroundTransferHost.exe (PID: 7848)
Checks supported languages
- pwsh.exe (PID: 6724)
- ShellExperienceHost.exe (PID: 7652)
- mode.com (PID: 5812)
- mode.com (PID: 8368)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8184)
- BackgroundTransferHost.exe (PID: 7240)
- BackgroundTransferHost.exe (PID: 1348)
- BackgroundTransferHost.exe (PID: 9008)
- BackgroundTransferHost.exe (PID: 4268)
- BackgroundTransferHost.exe (PID: 7848)
- BackgroundTransferHost.exe (PID: 7260)
- WMIC.exe (PID: 8896)
- WMIC.exe (PID: 7672)
- WMIC.exe (PID: 668)
- WMIC.exe (PID: 8984)
- WMIC.exe (PID: 7832)
- WMIC.exe (PID: 7756)
- WMIC.exe (PID: 3956)
- WMIC.exe (PID: 2780)
- WMIC.exe (PID: 7936)
- WMIC.exe (PID: 5392)
- WMIC.exe (PID: 5572)
- WMIC.exe (PID: 8572)
- WMIC.exe (PID: 8592)
Reads the computer name
- pwsh.exe (PID: 6724)
- ShellExperienceHost.exe (PID: 7652)
Process checks computer location settings
- pwsh.exe (PID: 6724)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7848)
- BackgroundTransferHost.exe (PID: 8184)
- powershell.exe (PID: 7500)
- slui.exe (PID: 5384)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7848)
- BackgroundTransferHost.exe (PID: 8184)
- slui.exe (PID: 8532)
- slui.exe (PID: 5384)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7500)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 7892)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 7892)
Disables trace logs
- powershell.exe (PID: 7500)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 7892)
Checks operating system version
- cmd.exe (PID: 8508)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 7616)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 8924)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 7892)
Starts MODE.COM to configure console settings
- mode.com (PID: 8368)
- mode.com (PID: 5812)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7688)
Creates files in the program directory
- cmd.exe (PID: 7616)
- ClipUp.exe (PID: 7676)
Create files in a temporary directory
- ClipUp.exe (PID: 7676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
471
Monitored processes
319
Malicious processes
6
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | sc query Winmgmt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | powershell.exe "$TB = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); [void]$TB.DefinePInvokeMethod('GetConsoleWindow', 'kernel32.dll', 22, 1, [IntPtr], @(), 1, 3).SetImplementationFlags(128); [void]$TB.DefinePInvokeMethod('SendMessageW', 'user32.dll', 22, 1, [IntPtr], @([IntPtr], [UInt32], [IntPtr], [IntPtr]), 1, 3).SetImplementationFlags(128); $hIcon = $TB.CreateType(); $hWnd = $hIcon::GetConsoleWindow(); echo $($hIcon::SendMessageW($hWnd, 127, 0, 0) -ne [IntPtr]::Zero);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wlidsvc /v ErrorControl | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | wmic path SoftwareLicensingProduct where (LicenseStatus='1' and GracePeriodRemaining='0' and PartialProductKey is not NULL AND LicenseDependsOn is NULL) get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | find /i "mcafee.com" C:\WINDOWS\System32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | findstr "577 225" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | find /i "avira.com" C:\WINDOWS\System32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | powershell.exe "Start-Job { Restart-Service ClipSVC } | Wait-Job -Timeout 20 | Out-Null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
165 453
Read events
165 420
Write events
26
Delete events
7
Modification events
| (PID) Process: | (7248) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1348) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1348) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1348) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7240) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7240) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7240) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
154
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:460F0B2A77B815D921CBF0AF0E60AD7F | SHA256:50F10024F3DF5BE029B368D9568AC1B40370DBE56023E5D84DD574E0E768F64D | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:DAF04721D12C216A508E57E8C419FC5E | SHA256:5DFFC905720869DE0BC5B2F2F63747328D5BC823A52D4B171D6AC8F94A5B00E8 | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:D30F5B10F3D4B3992E4D666F622163F4 | SHA256:2585819A7401A308DA879FA416278E473CEA5F6D0D24C59F514C5A698C61D03A | |||
| 7248 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
108
DNS requests
131
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 302 | 216.58.212.132:80 | http://www.google.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.217.18.3:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 142.250.185.174:80 | google.com | GOOGLE | US | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
ipv4only.arpa |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |