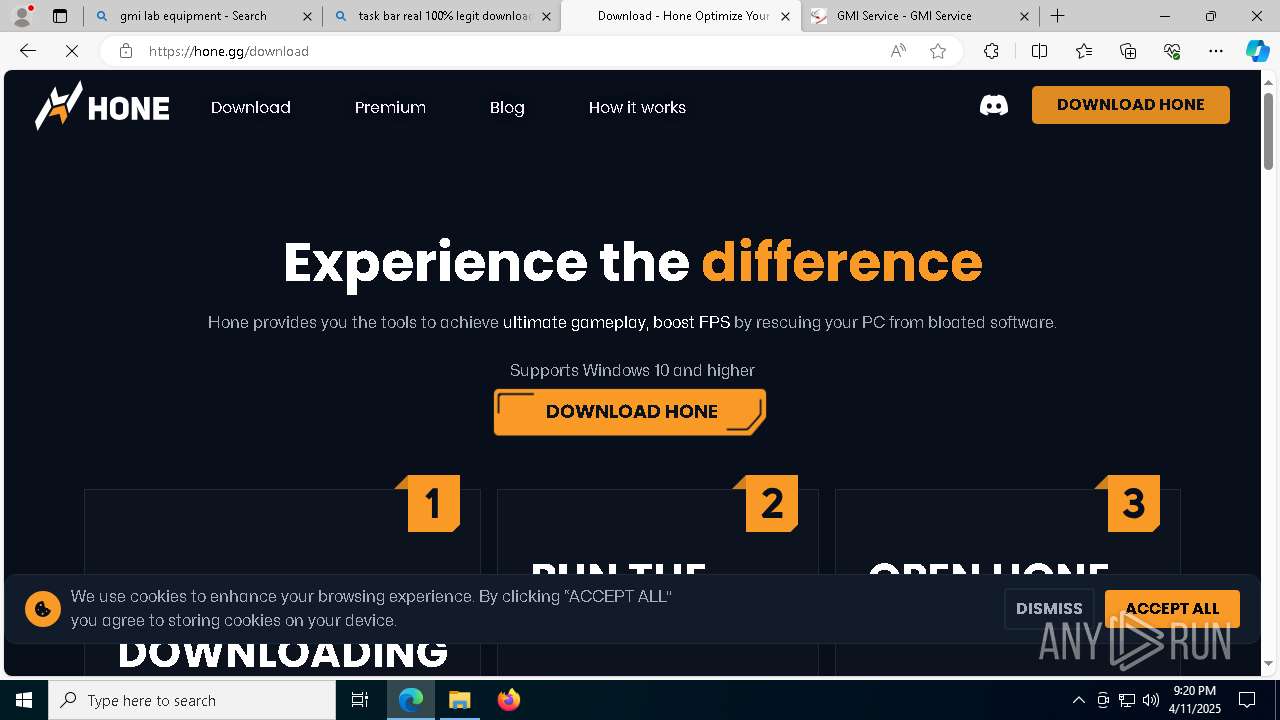
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/c33e0579-dbfa-424d-bbcd-394f3506058c |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 21:17:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
Vulnerable driver has been detected
- ow-electron-setup.exe (PID: 1616)
Changes powershell execution policy (Unrestricted)
- Hone.exe (PID: 6068)
SUSPICIOUS
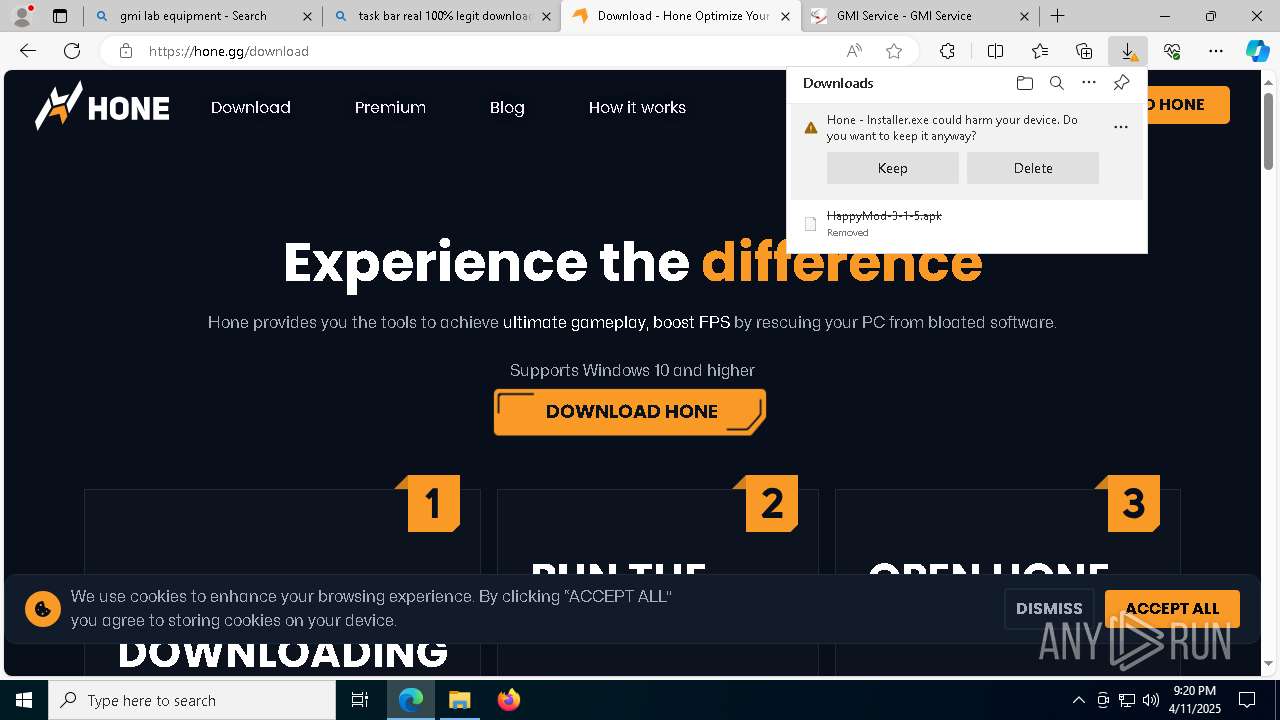
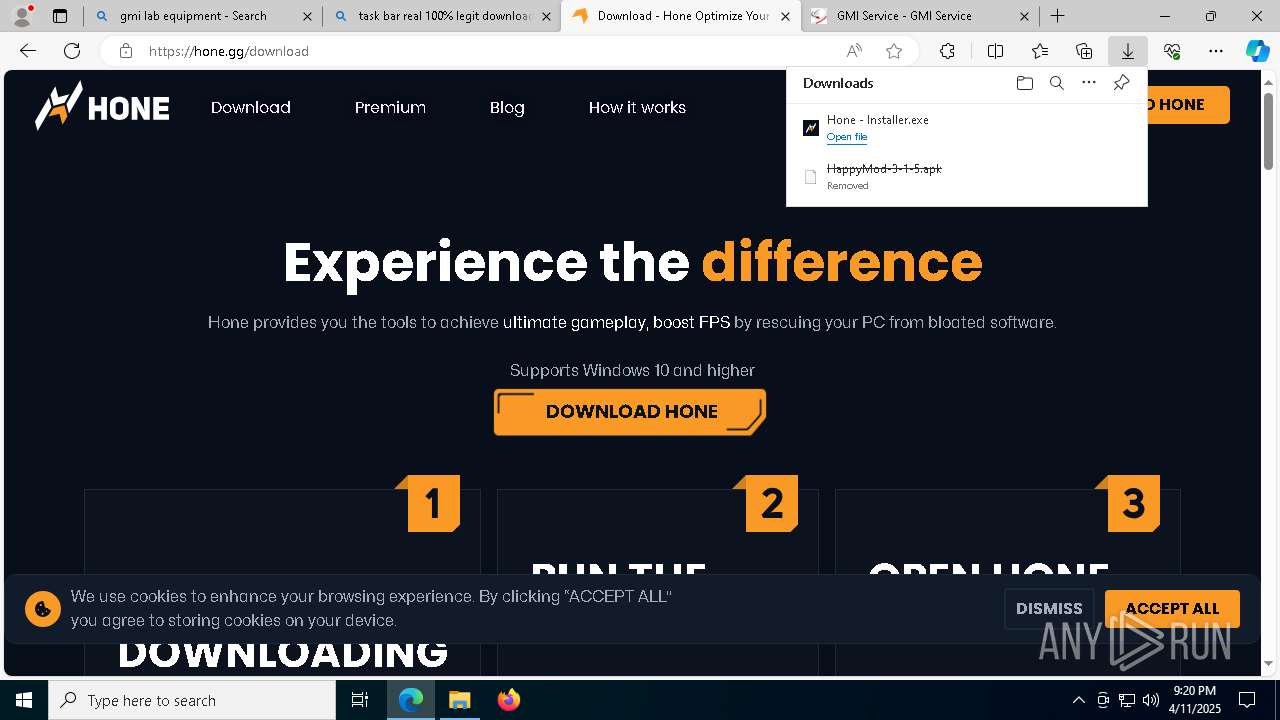
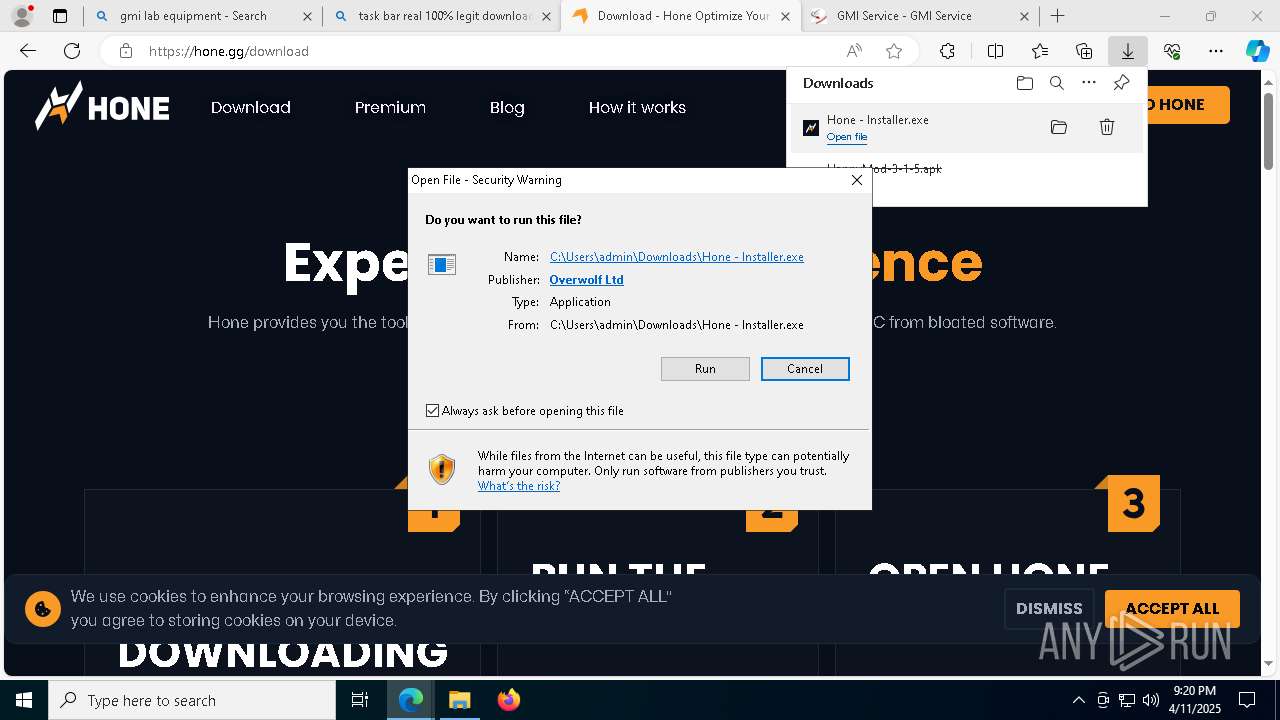
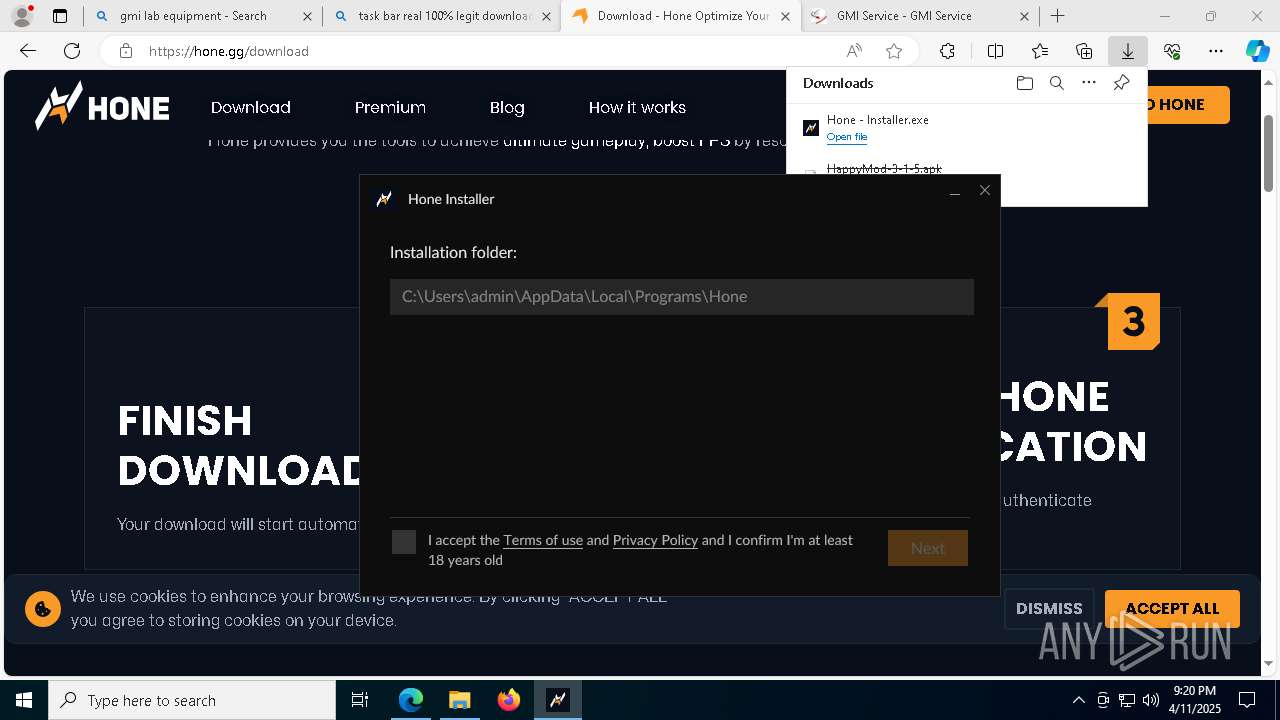
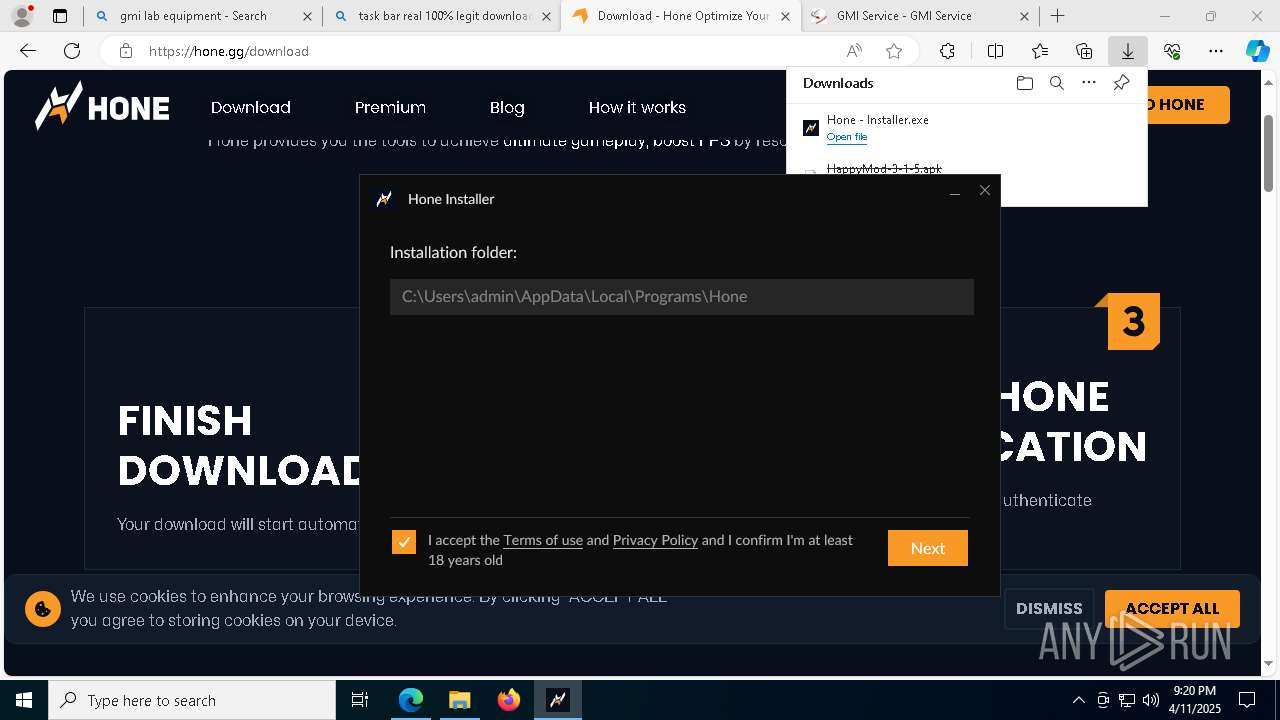
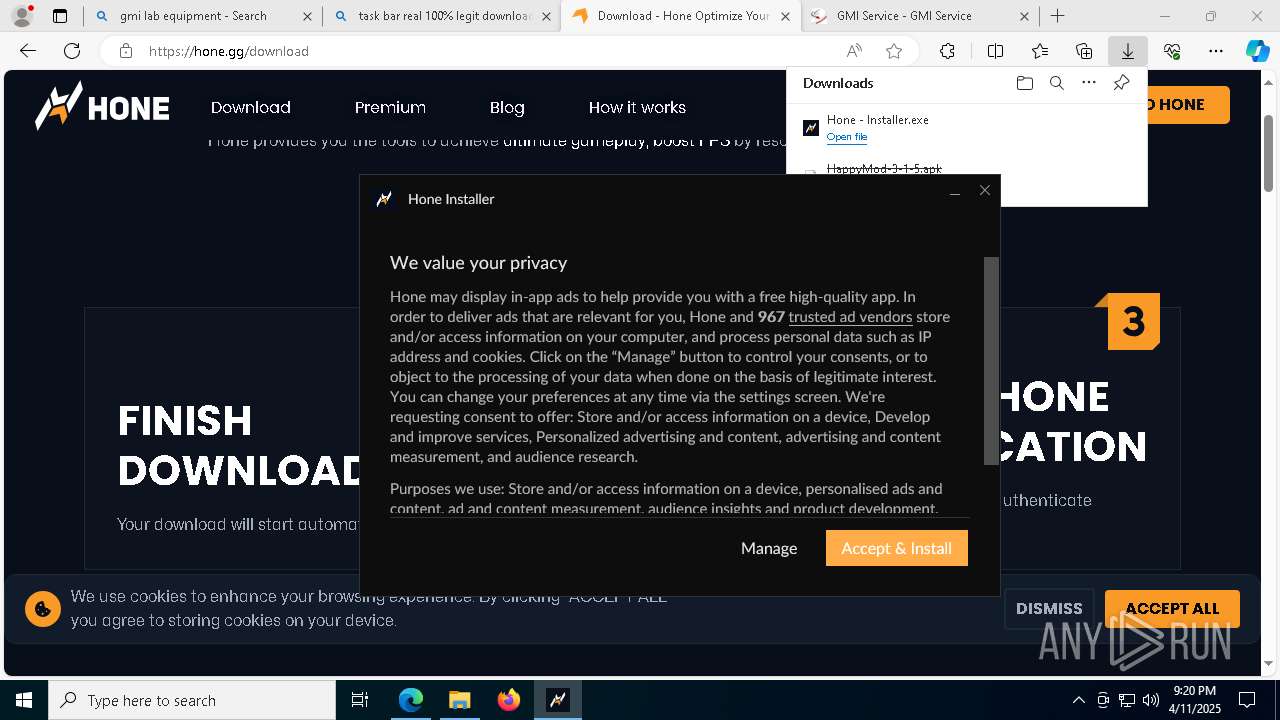
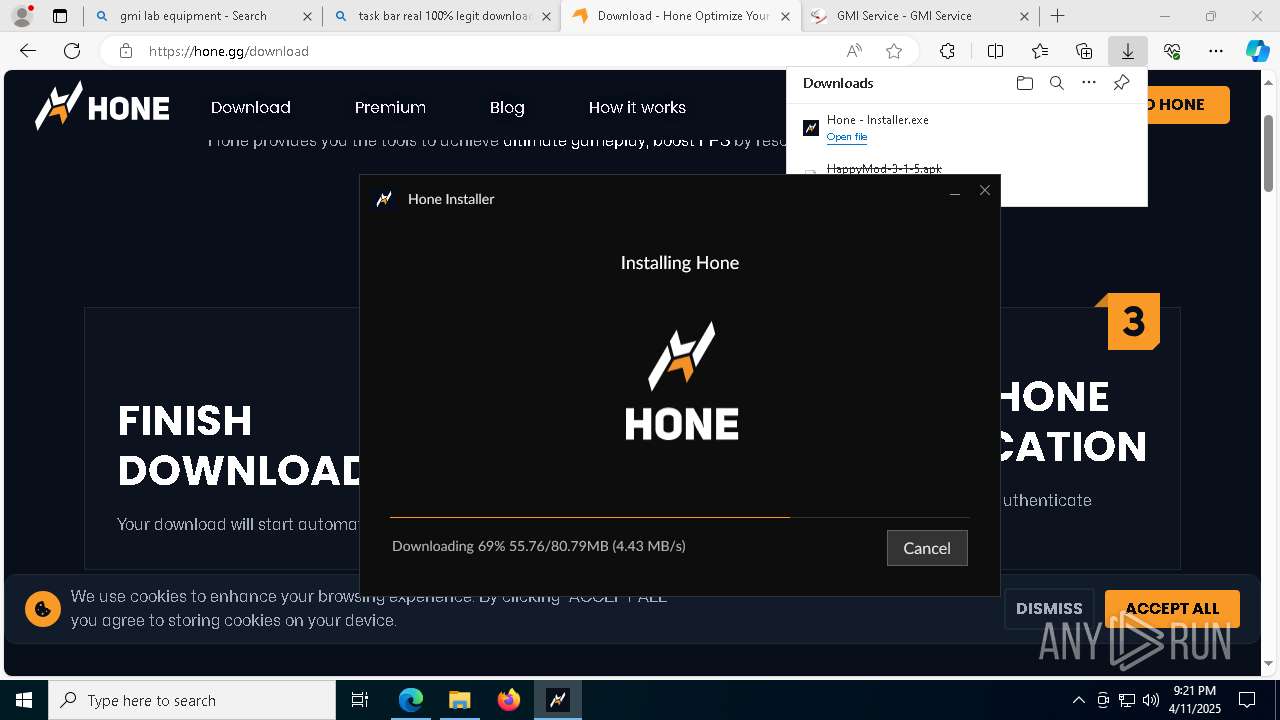
Executable content was dropped or overwritten
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 8392)
Malware-specific behavior (creating "System.dll" in Temp)
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- ow-electron-setup.exe (PID: 1616)
The process creates files with name similar to system file names
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- ow-electron-setup.exe (PID: 1616)
Reads security settings of Internet Explorer
- Hone - Installer.exe (PID: 7492)
- Hone - Installer.exe (PID: 6256)
- OWInstaller.exe (PID: 8092)
- Hone.exe (PID: 6068)
Drops 7-zip archiver for unpacking
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
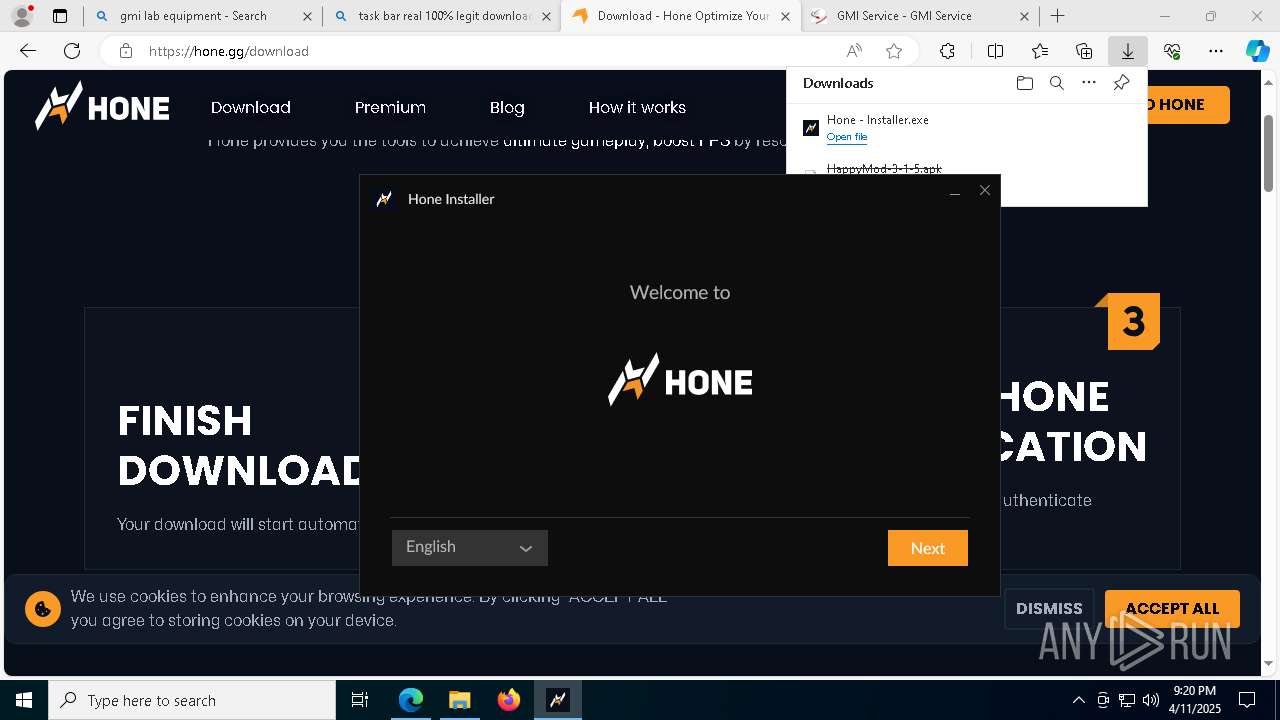
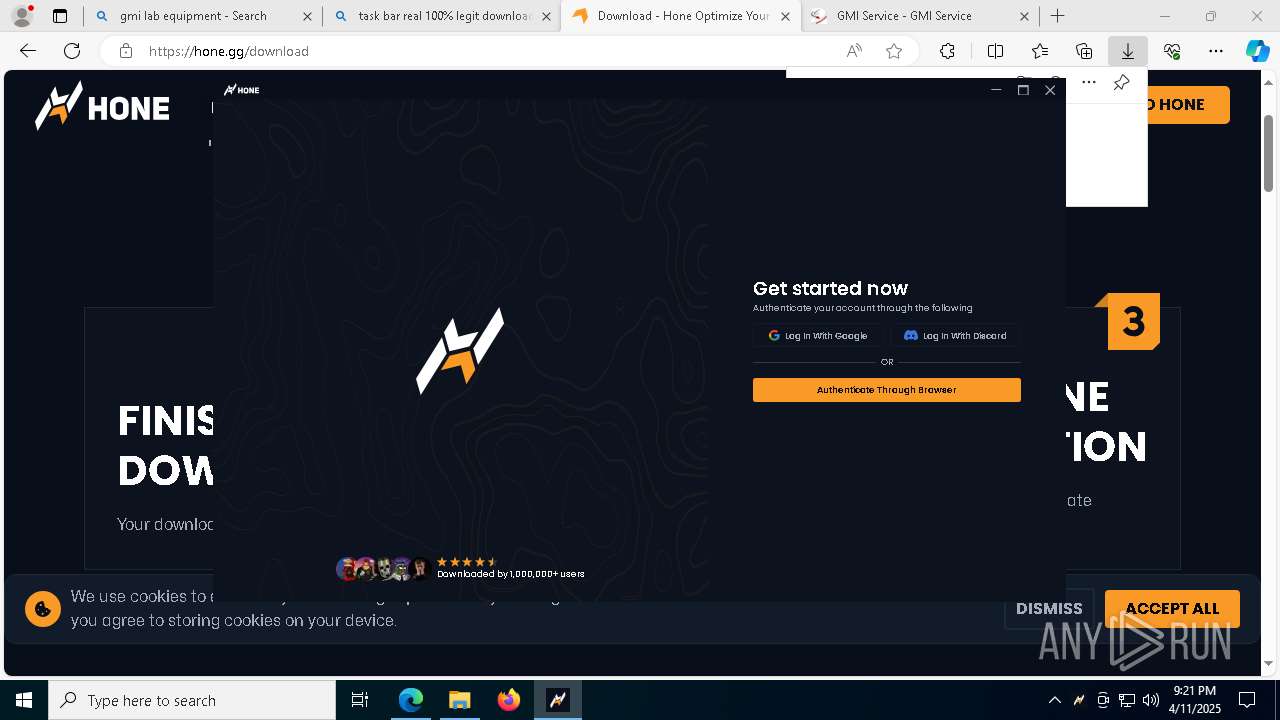
Application launched itself
- Hone - Installer.exe (PID: 6256)
- Hone.exe (PID: 6068)
- HoneStartup.exe (PID: 5708)
- HoneStartup.exe (PID: 4732)
- HoneStartup.exe (PID: 1520)
Reads Microsoft Outlook installation path
- OWInstaller.exe (PID: 8092)
Reads Internet Explorer settings
- OWInstaller.exe (PID: 8092)
There is functionality for taking screenshot (YARA)
- Hone - Installer.exe (PID: 7492)
- Hone - Installer.exe (PID: 6256)
Reads the date of Windows installation
- OWInstaller.exe (PID: 8092)
Starts CMD.EXE for commands execution
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 6068)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1348)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 5812)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 5328)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 6072)
Process drops legitimate windows executable
- ow-electron-setup.exe (PID: 1616)
Drops a system driver (possible attempt to evade defenses)
- ow-electron-setup.exe (PID: 1616)
The process drops C-runtime libraries
- ow-electron-setup.exe (PID: 1616)
Creates a software uninstall entry
- ow-electron-setup.exe (PID: 1616)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5436)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 664)
Starts POWERSHELL.EXE for commands execution
- Hone.exe (PID: 6068)
The process hides Powershell's copyright startup banner
- Hone.exe (PID: 6068)
The process bypasses the loading of PowerShell profile settings
- Hone.exe (PID: 6068)
INFO
Create files in a temporary directory
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- OWInstaller.exe (PID: 8092)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 8392)
The sample compiled with english language support
- msedge.exe (PID: 7312)
- msedge.exe (PID: 6240)
- msedge.exe (PID: 7576)
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 8392)
Checks proxy server information
- slui.exe (PID: 5544)
- Hone - Installer.exe (PID: 7492)
- OWInstaller.exe (PID: 8092)
- Hone.exe (PID: 6068)
Reads Environment values
- identity_helper.exe (PID: 4620)
- OWInstaller.exe (PID: 8092)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 8392)
Application launched itself
- msedge.exe (PID: 7312)
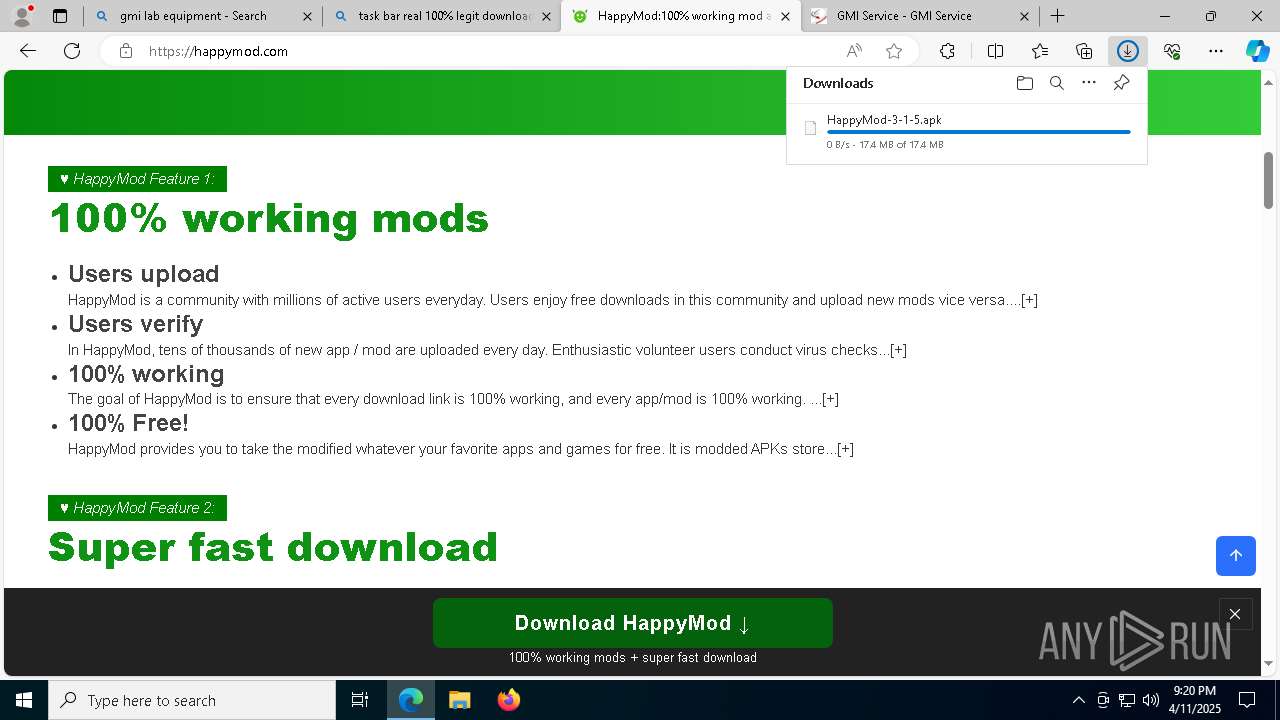
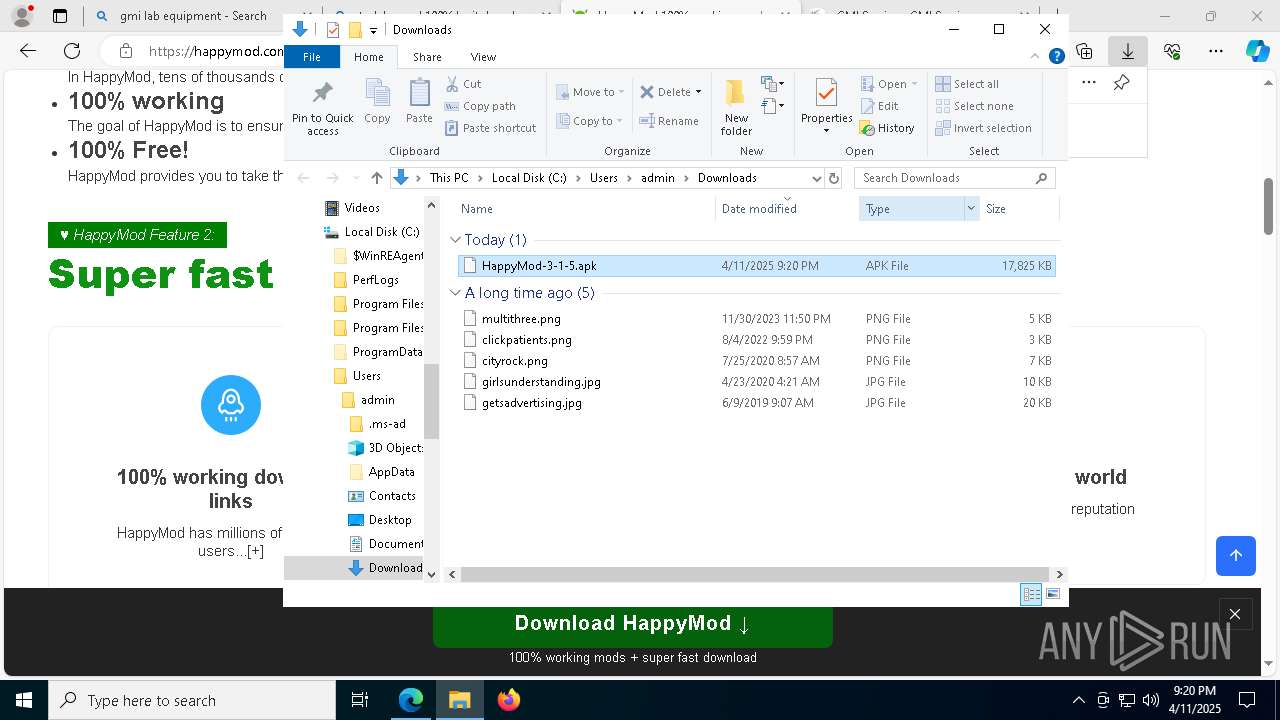
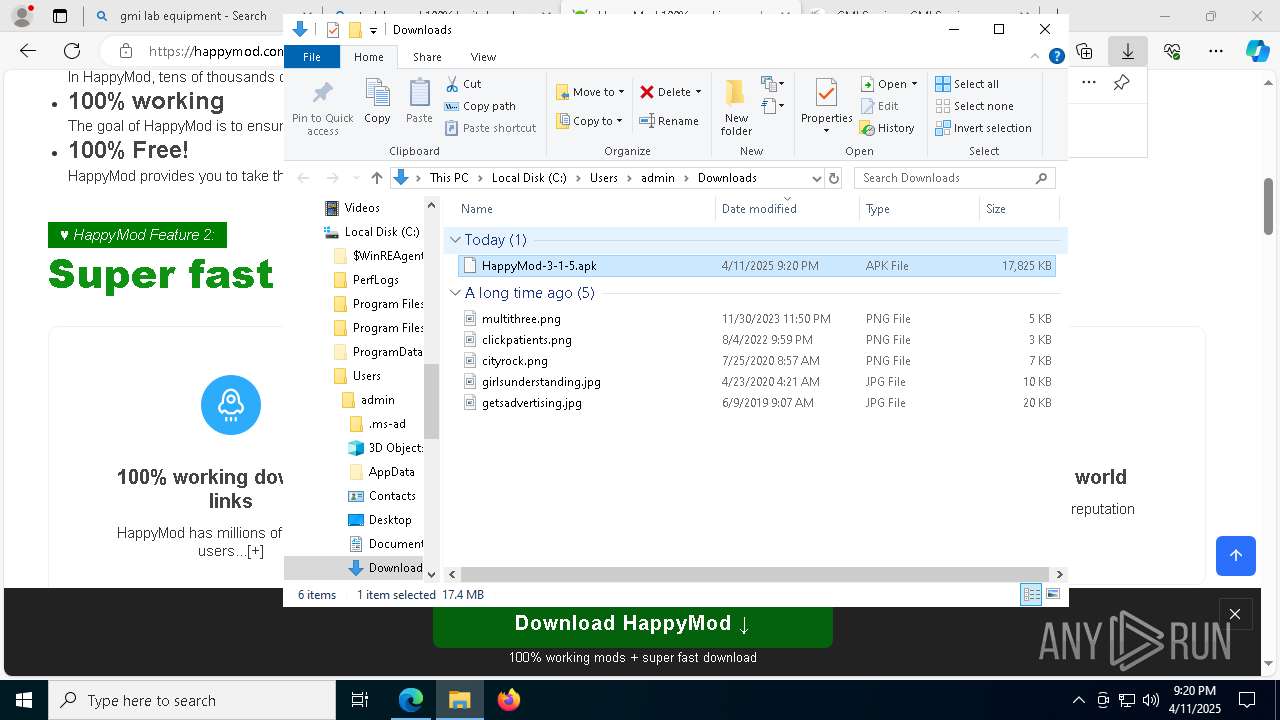
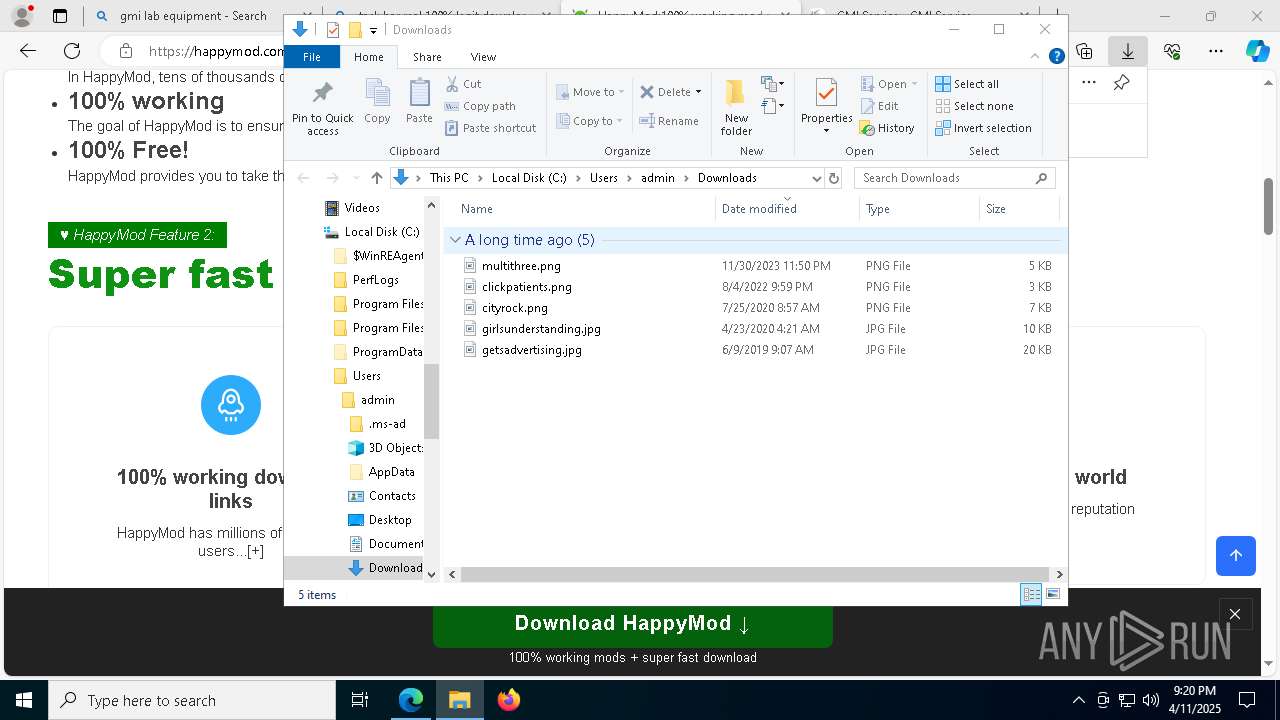
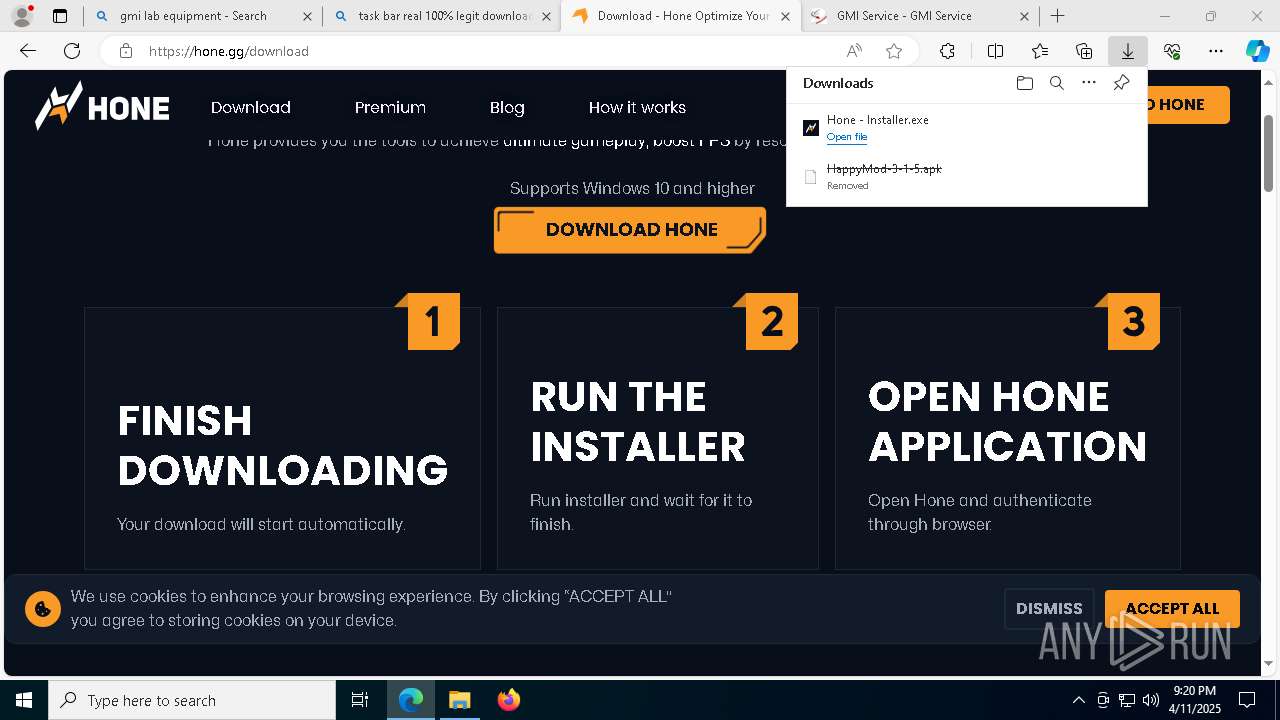
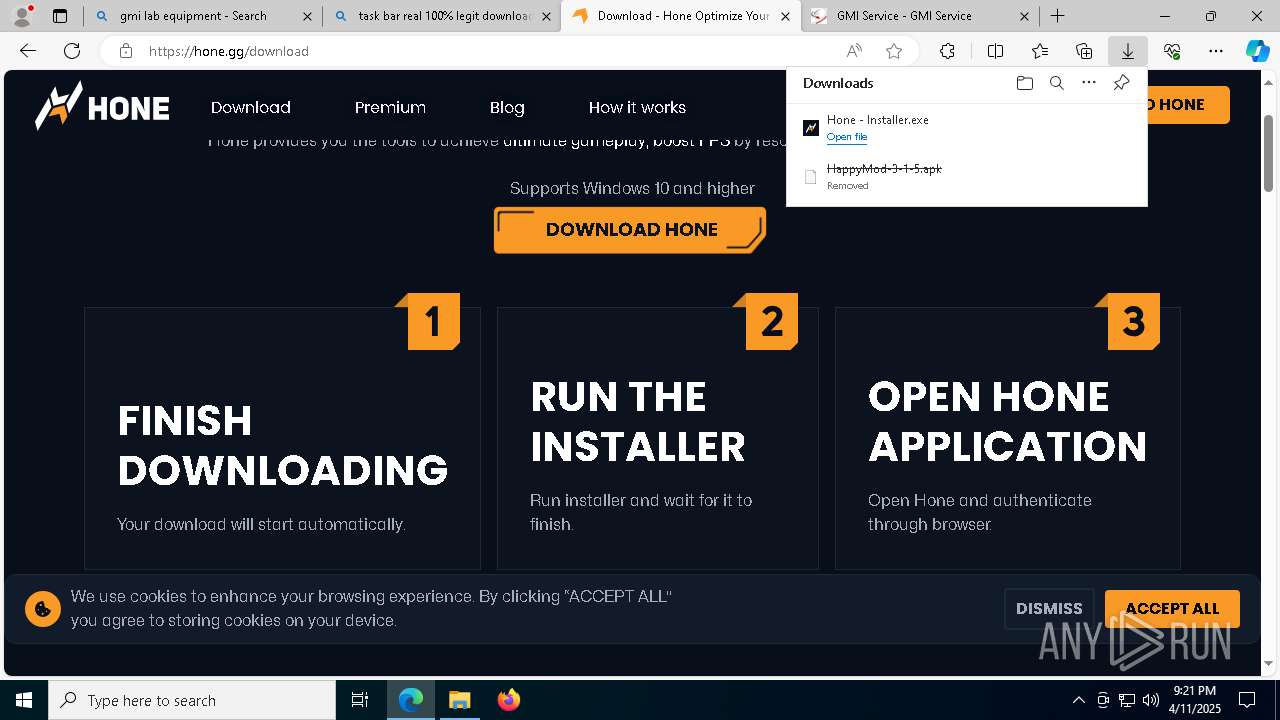
Autorun file from Downloads
- msedge.exe (PID: 9176)
- msedge.exe (PID: 7312)
- msedge.exe (PID: 2392)
Reads the software policy settings
- slui.exe (PID: 2236)
- slui.exe (PID: 5544)
- OWInstaller.exe (PID: 8092)
- Hone.exe (PID: 5324)
Checks supported languages
- Hone - Installer.exe (PID: 6256)
- identity_helper.exe (PID: 4620)
- Hone - Installer.exe (PID: 7492)
- OWInstaller.exe (PID: 8092)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 7104)
- Hone.exe (PID: 5324)
- Hone.exe (PID: 4280)
- Hone.exe (PID: 2268)
- Hone.exe (PID: 1584)
- HoneStartup.exe (PID: 5708)
- HoneStartup.exe (PID: 4732)
- gamefinder472.exe (PID: 7124)
- Hone.exe (PID: 8392)
- HoneStartup.exe (PID: 4164)
- HoneStartup.exe (PID: 7148)
- HoneStartup.exe (PID: 496)
- HoneStartup.exe (PID: 8220)
- HoneStartup.exe (PID: 2776)
- HoneStartup.exe (PID: 1132)
- HoneStartup.exe (PID: 8296)
- HoneStartup.exe (PID: 9156)
- HoneStartup.exe (PID: 1852)
- HoneStartup.exe (PID: 6644)
- HoneStartup.exe (PID: 868)
- HoneStartup.exe (PID: 4648)
- HoneStartup.exe (PID: 1520)
- HoneStartup.exe (PID: 3132)
- HoneStartup.exe (PID: 7084)
- HoneStartup.exe (PID: 8424)
- HoneStartup.exe (PID: 8256)
- HoneStartup.exe (PID: 5588)
- HoneStartup.exe (PID: 6820)
Executable content was dropped or overwritten
- msedge.exe (PID: 7312)
- msedge.exe (PID: 6240)
Reads the computer name
- identity_helper.exe (PID: 4620)
- Hone - Installer.exe (PID: 6256)
- Hone - Installer.exe (PID: 7492)
- OWInstaller.exe (PID: 8092)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 5324)
- HoneStartup.exe (PID: 4732)
- Hone.exe (PID: 7104)
- HoneStartup.exe (PID: 5708)
- gamefinder472.exe (PID: 7124)
- HoneStartup.exe (PID: 4164)
- Hone.exe (PID: 8392)
- HoneStartup.exe (PID: 1132)
- HoneStartup.exe (PID: 8220)
- HoneStartup.exe (PID: 7148)
- HoneStartup.exe (PID: 2776)
- HoneStartup.exe (PID: 8296)
- HoneStartup.exe (PID: 4648)
- HoneStartup.exe (PID: 1852)
- HoneStartup.exe (PID: 9156)
- HoneStartup.exe (PID: 6644)
- HoneStartup.exe (PID: 496)
- HoneStartup.exe (PID: 1520)
- HoneStartup.exe (PID: 7084)
- HoneStartup.exe (PID: 8424)
- HoneStartup.exe (PID: 8256)
- HoneStartup.exe (PID: 868)
- HoneStartup.exe (PID: 3132)
- HoneStartup.exe (PID: 6820)
- HoneStartup.exe (PID: 5588)
Process checks computer location settings
- Hone - Installer.exe (PID: 6256)
- OWInstaller.exe (PID: 8092)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 2268)
- Hone.exe (PID: 1584)
- Hone.exe (PID: 4280)
- Hone.exe (PID: 8392)
Creates files or folders in the user directory
- Hone - Installer.exe (PID: 7492)
- OWInstaller.exe (PID: 8092)
- ow-electron-setup.exe (PID: 1616)
- Hone.exe (PID: 6068)
- Hone.exe (PID: 7104)
- Hone.exe (PID: 8392)
Disables trace logs
- OWInstaller.exe (PID: 8092)
Reads the machine GUID from the registry
- OWInstaller.exe (PID: 8092)
- HoneStartup.exe (PID: 4732)
- Hone.exe (PID: 6068)
- HoneStartup.exe (PID: 5708)
- gamefinder472.exe (PID: 7124)
- HoneStartup.exe (PID: 4164)
- HoneStartup.exe (PID: 1132)
- HoneStartup.exe (PID: 8220)
- HoneStartup.exe (PID: 7148)
- HoneStartup.exe (PID: 496)
- HoneStartup.exe (PID: 2776)
- HoneStartup.exe (PID: 8296)
- HoneStartup.exe (PID: 4648)
- HoneStartup.exe (PID: 1852)
- HoneStartup.exe (PID: 9156)
- HoneStartup.exe (PID: 6644)
- HoneStartup.exe (PID: 868)
- HoneStartup.exe (PID: 1520)
- HoneStartup.exe (PID: 3132)
- HoneStartup.exe (PID: 8256)
- HoneStartup.exe (PID: 8424)
- HoneStartup.exe (PID: 7084)
- HoneStartup.exe (PID: 6820)
- HoneStartup.exe (PID: 5588)
Reads product name
- Hone.exe (PID: 6068)
- Hone.exe (PID: 8392)
Creates files in the program directory
- ow-electron-setup.exe (PID: 1616)
Reads CPU info
- Hone.exe (PID: 6068)
Attempting to use instant messaging service
- msedge.exe (PID: 7576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
370
Monitored processes
225
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | taskkill /IM SCEWIN_64.exe /T /F | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4084 --field-trial-handle=2368,i,4025391929248054762,1748925202805591889,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "HoneStartup.exe" "-sett" "service" "RpcSs" "2" | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\HoneStartup.exe | HoneStartup.exe | ||||||||||||
User: SYSTEM Company: AuraSide, Inc Integrity Level: SYSTEM Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=5920 --field-trial-handle=2368,i,4025391929248054762,1748925202805591889,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | C:\WINDOWS\system32\cmd.exe /d /s /c "reg add "hklm\Software\Classes\hone" /v "URL Protocol" /t REG_SZ /d "" /f" | C:\Windows\System32\cmd.exe | — | Hone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HoneStartup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | taskkill /IM SetDpi.exe /T /F | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | "HoneStartup.exe" "-sett" "service" "SystemEventsBroker" "2" | C:\Users\admin\AppData\Local\Programs\Hone\resources\assets\hone-resources\HoneStartup.exe | HoneStartup.exe | ||||||||||||
User: SYSTEM Company: AuraSide, Inc Integrity Level: SYSTEM Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=9816 --field-trial-handle=2368,i,4025391929248054762,1748925202805591889,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | reg query "hklm\Software\Classes\hone" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 440
Read events
34 230
Write events
190
Delete events
20
Modification events
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D8314B821D912F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 46165A821D912F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262922 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {03B58ACA-053E-4C42-9324-A37CAD1F2848} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262922 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C4018203-7D97-4C0D-96D7-9CEC7263C584} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262922 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CF01F339-58CF-41D1-88F8-E13FFE1B8E19} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262922 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {78739CAE-9803-46BA-B272-74F58673D160} | |||
Executable files
123
Suspicious files
1 488
Text files
279
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b567.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b577.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b567.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
342
DNS requests
377
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2040 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744955560&P2=404&P3=2&P4=KIGIs%2fcML2iro4ETn5Fc4teyC51xMroJYxIdznZc0ggtZ3VkAF8w7nOYXEzSjuSlHeQ%2fKkcKXIzN11hBBrQzLg%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8944 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2040 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955560&P2=404&P3=2&P4=nLQfFtyVXQnEx6%2byx%2ft6oqCkXoa5CV9LrtW%2fvkJ3VSMF5WCFCzMIwbwEyJQ8wQ90dwf2UMNiLyqTHZvTAtL59w%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955560&P2=404&P3=2&P4=nLQfFtyVXQnEx6%2byx%2ft6oqCkXoa5CV9LrtW%2fvkJ3VSMF5WCFCzMIwbwEyJQ8wQ90dwf2UMNiLyqTHZvTAtL59w%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955560&P2=404&P3=2&P4=nLQfFtyVXQnEx6%2byx%2ft6oqCkXoa5CV9LrtW%2fvkJ3VSMF5WCFCzMIwbwEyJQ8wQ90dwf2UMNiLyqTHZvTAtL59w%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955560&P2=404&P3=2&P4=nLQfFtyVXQnEx6%2byx%2ft6oqCkXoa5CV9LrtW%2fvkJ3VSMF5WCFCzMIwbwEyJQ8wQ90dwf2UMNiLyqTHZvTAtL59w%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955560&P2=404&P3=2&P4=nLQfFtyVXQnEx6%2byx%2ft6oqCkXoa5CV9LrtW%2fvkJ3VSMF5WCFCzMIwbwEyJQ8wQ90dwf2UMNiLyqTHZvTAtL59w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6652 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7576 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7576 | msedge.exe | 142.250.184.206:80 | google.com | GOOGLE | US | whitelisted |
7576 | msedge.exe | 142.250.184.206:443 | google.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7576 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7576 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7492 | Hone - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7104 | Hone.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |