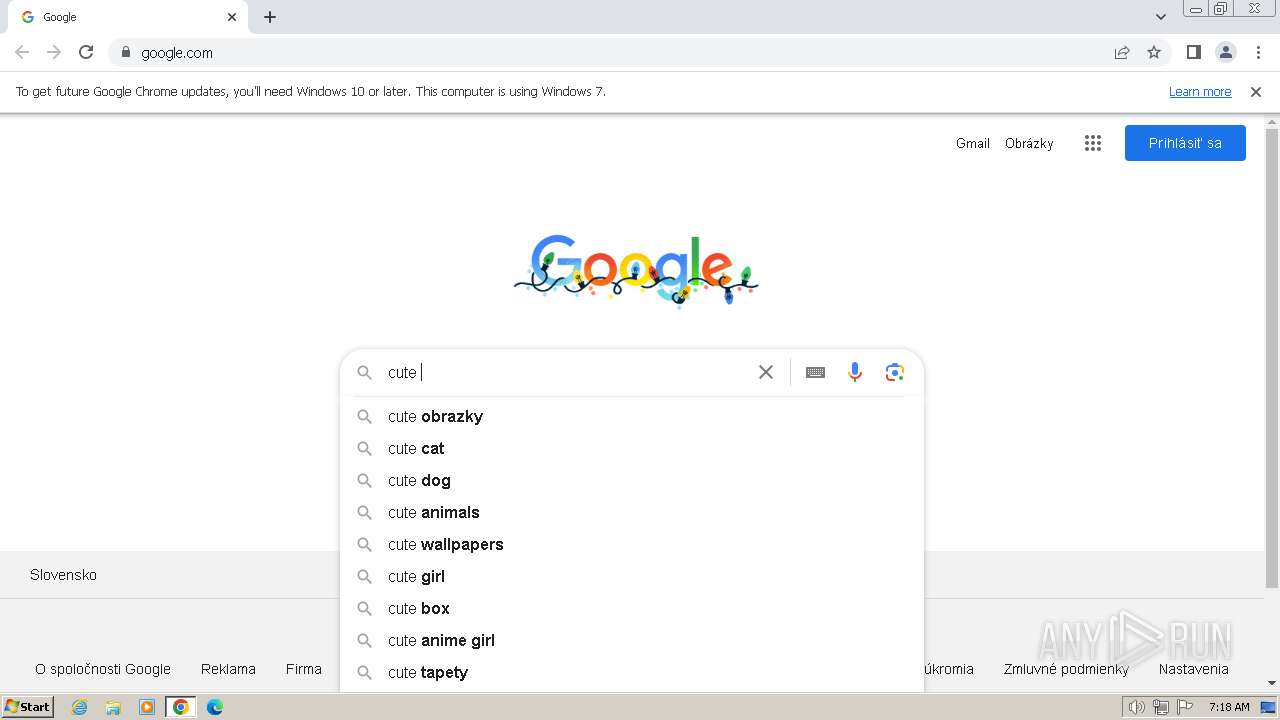
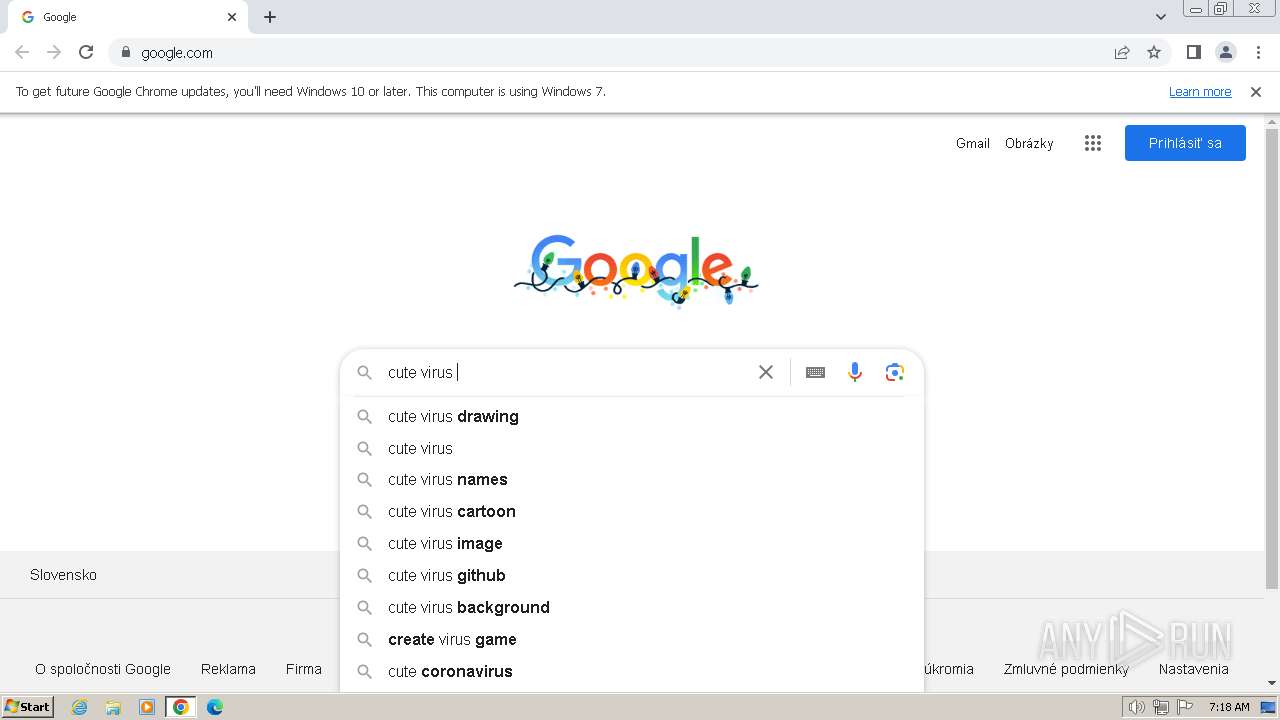
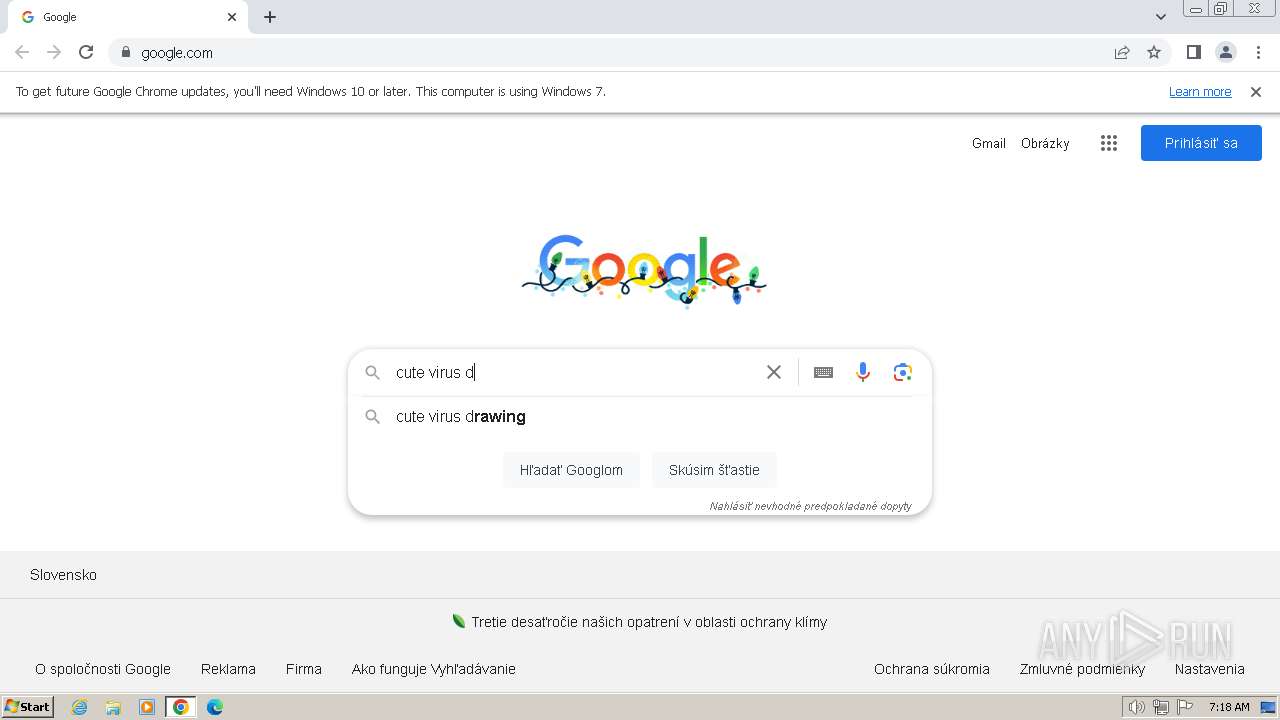
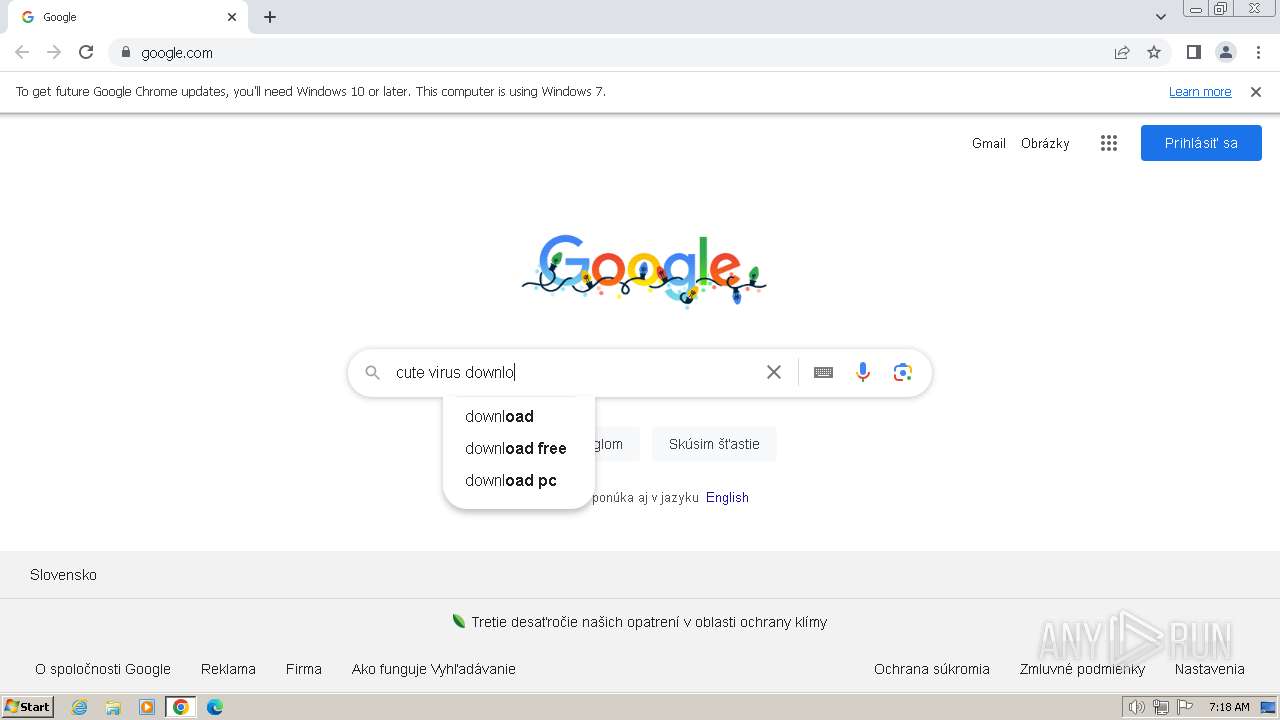
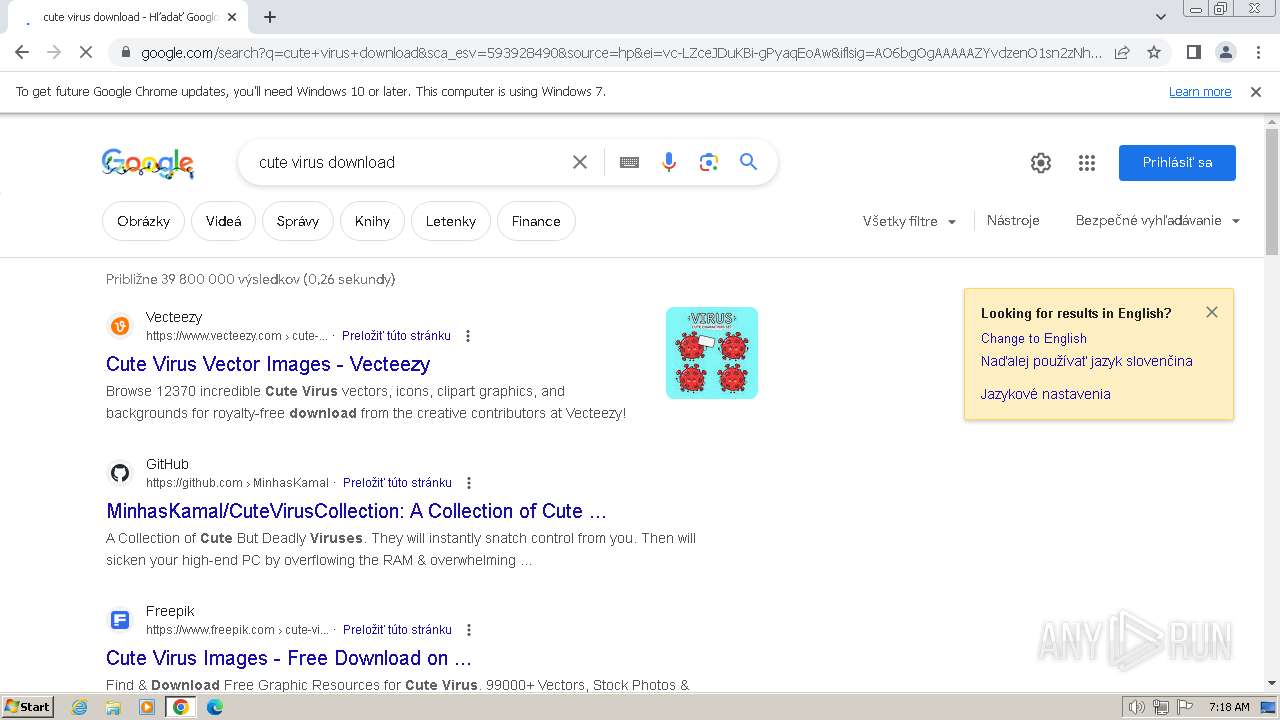
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/7f2ca199-f7df-4f6b-8ae5-c1e5591352f3 |
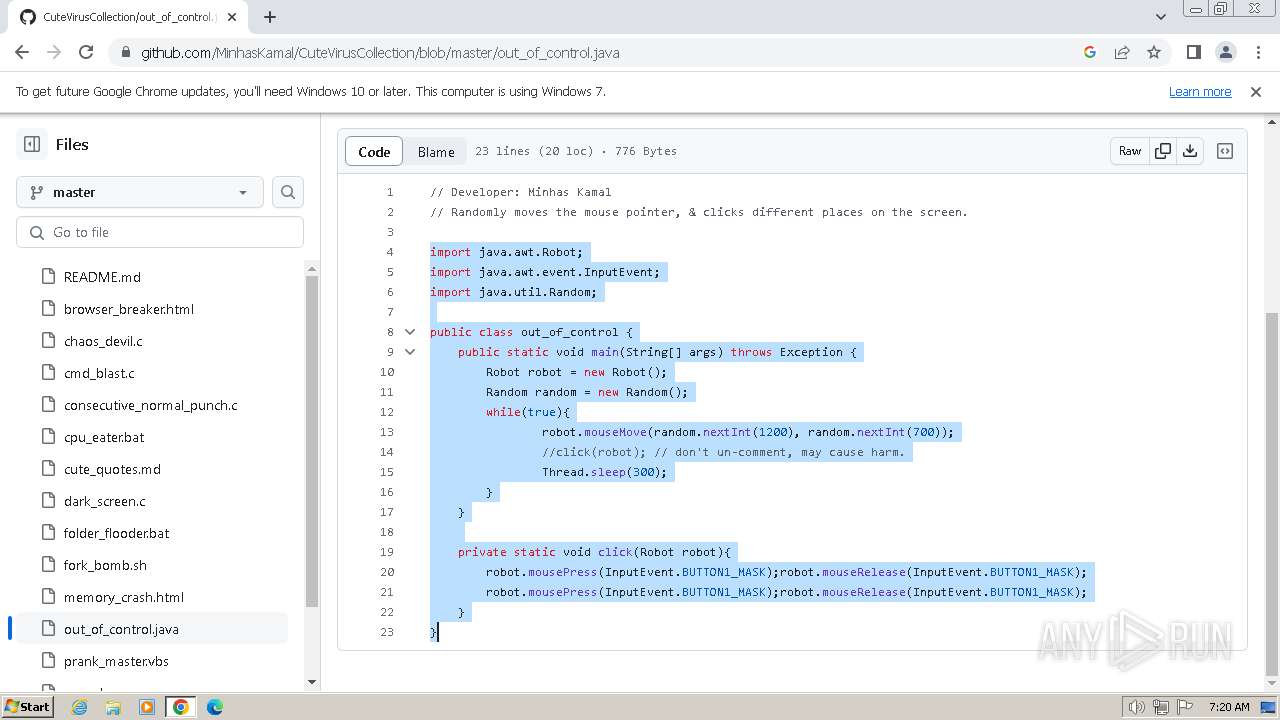
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2023, 07:18:12 |
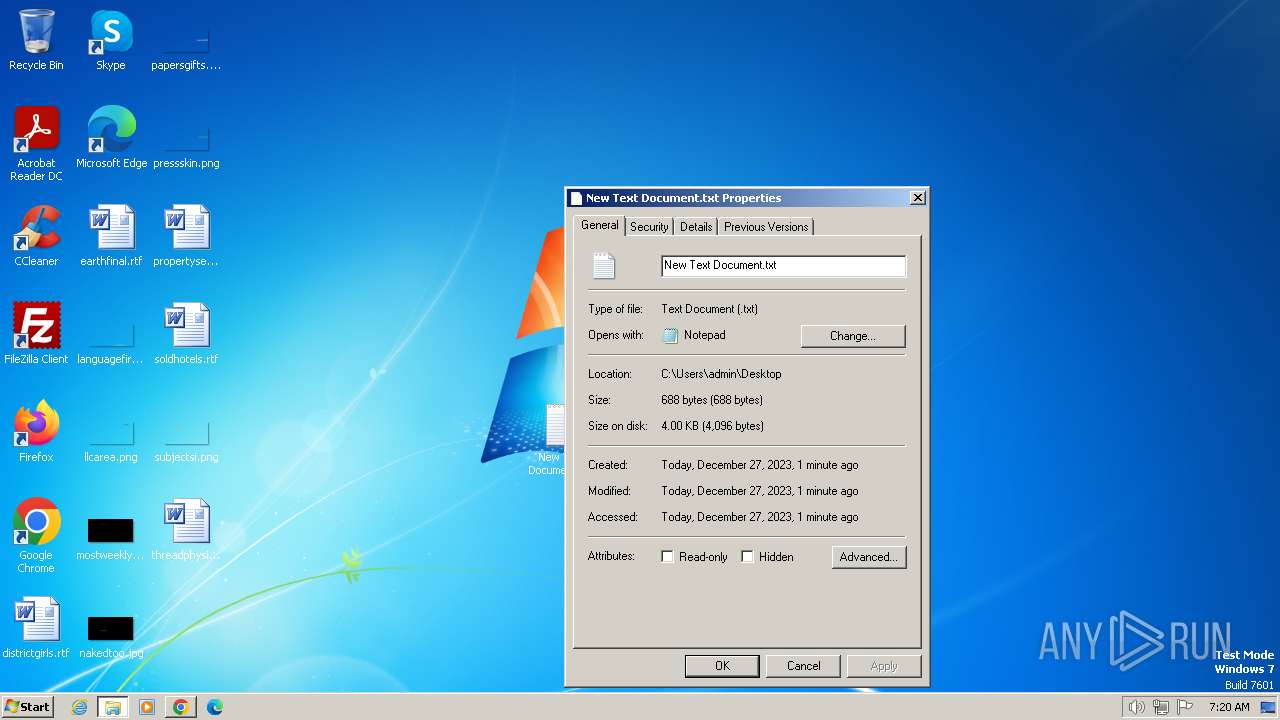
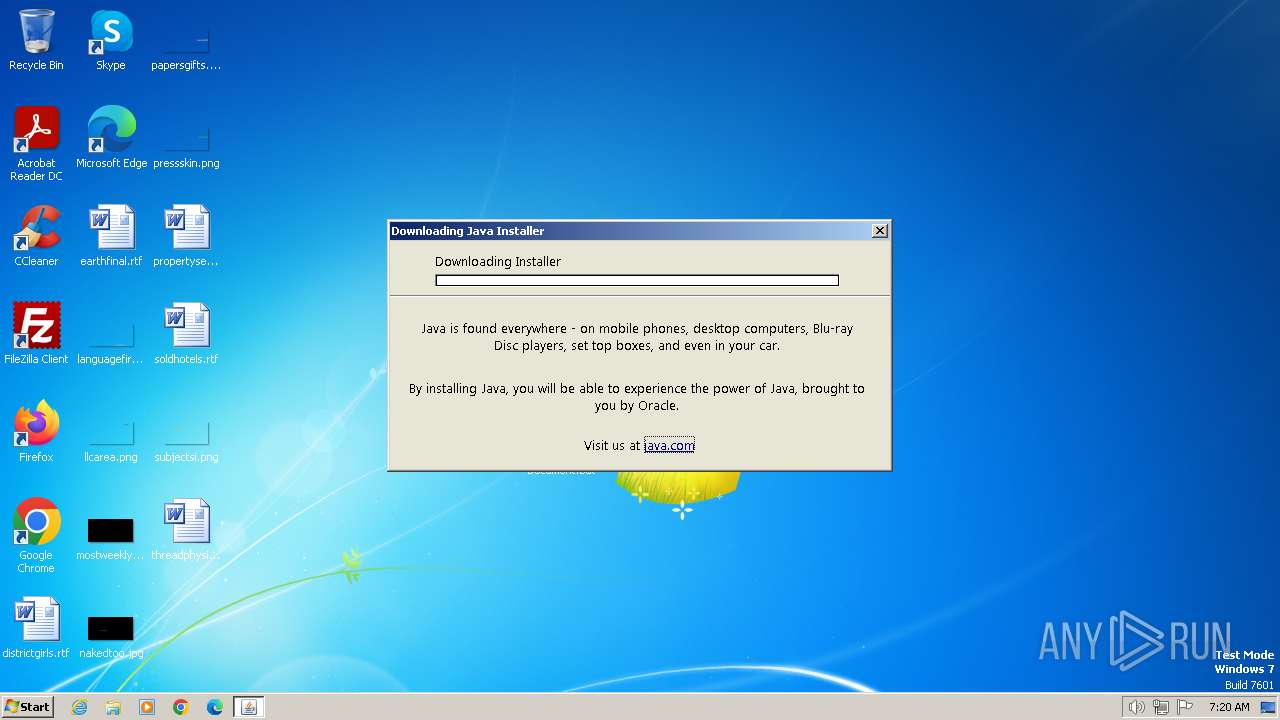
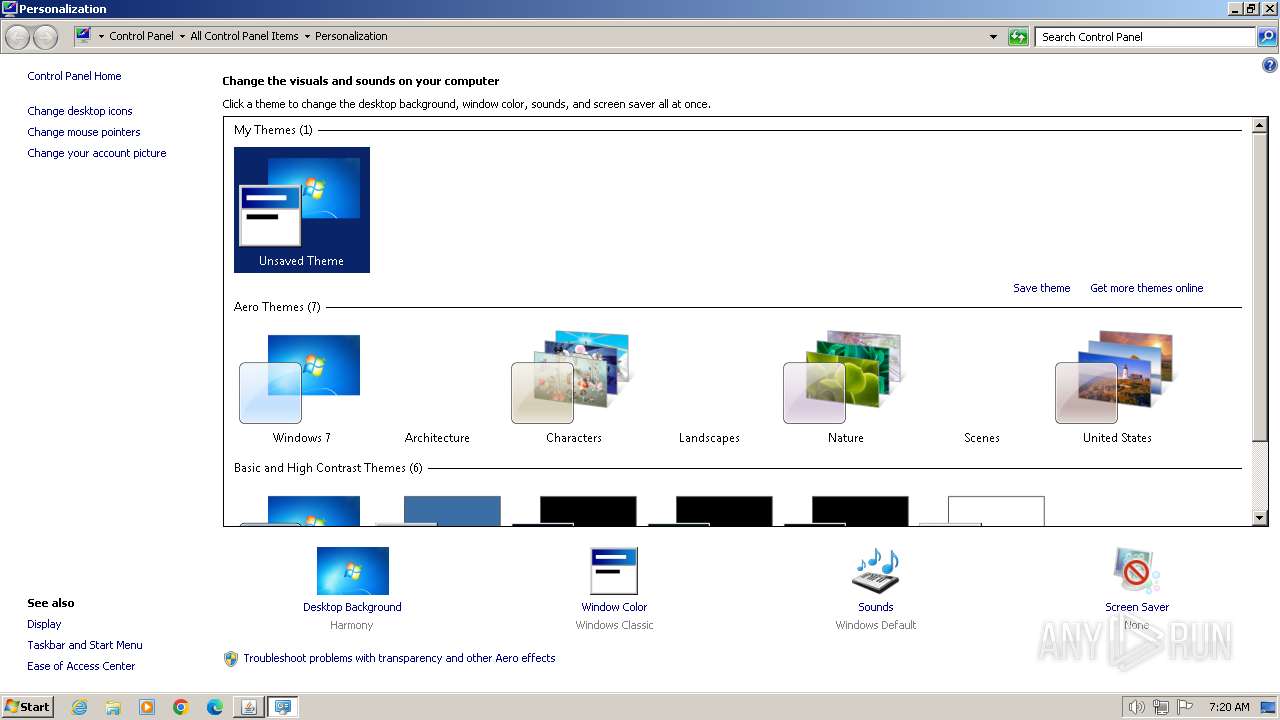
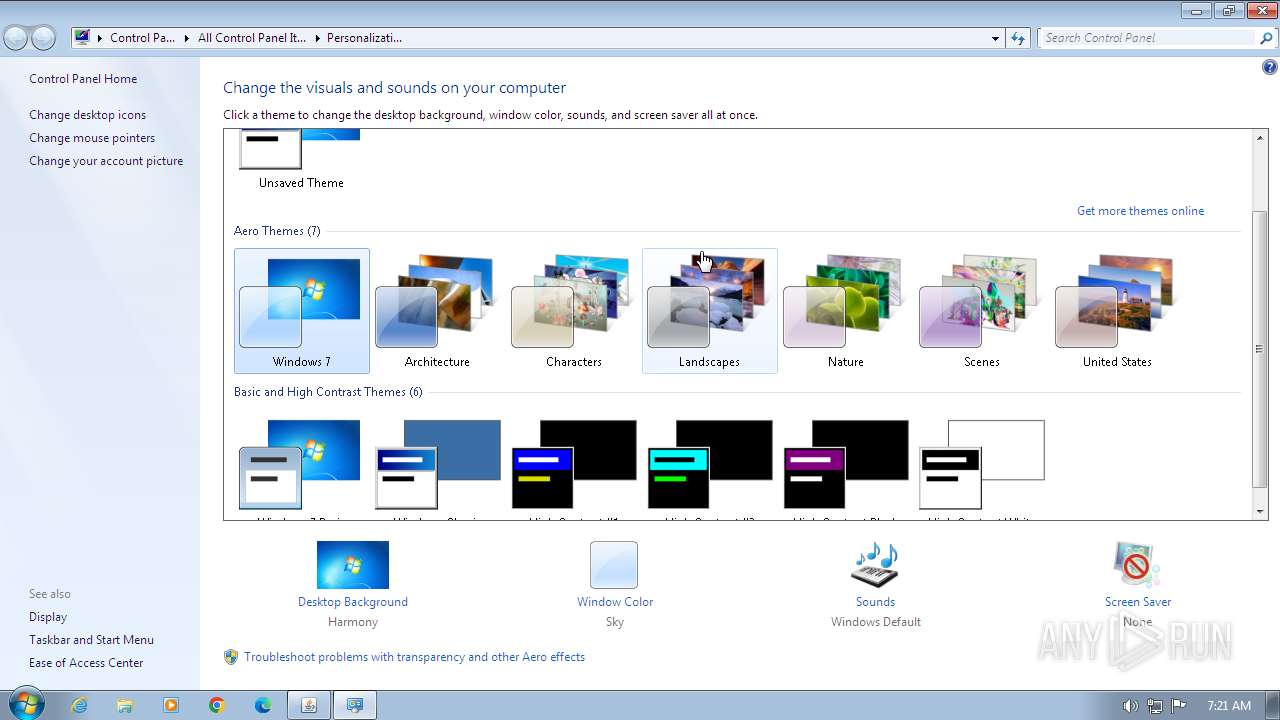
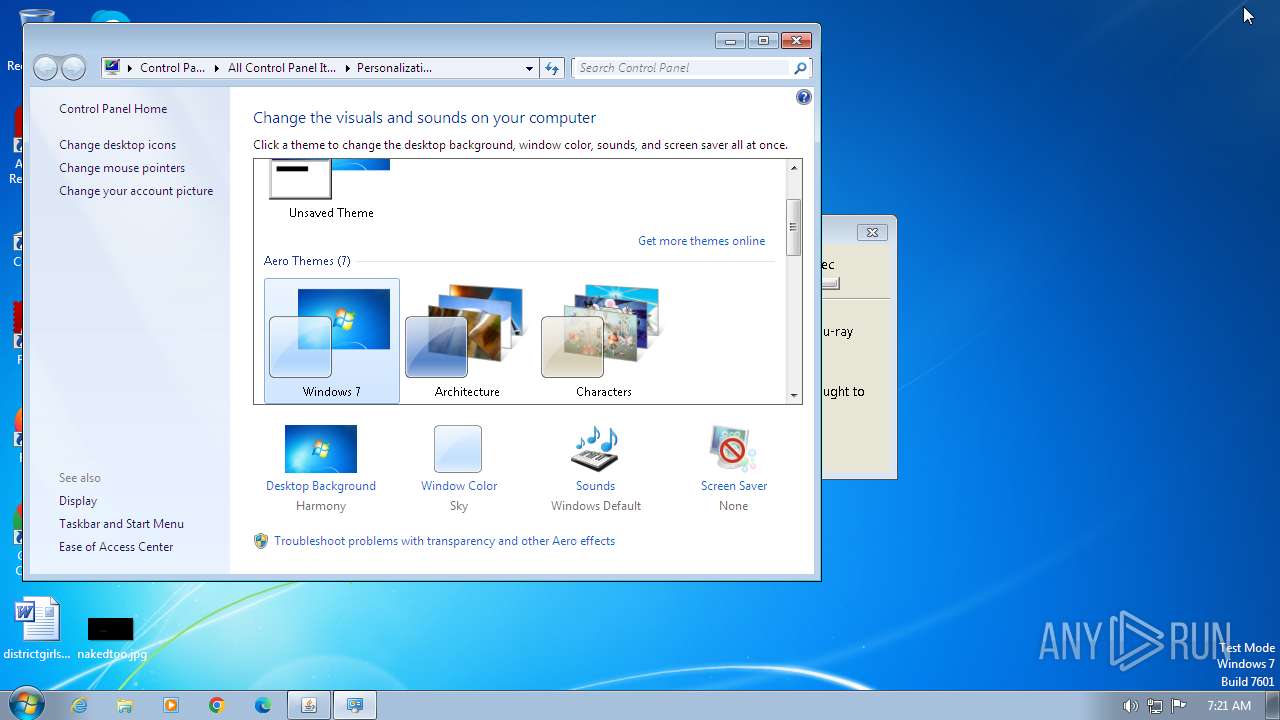
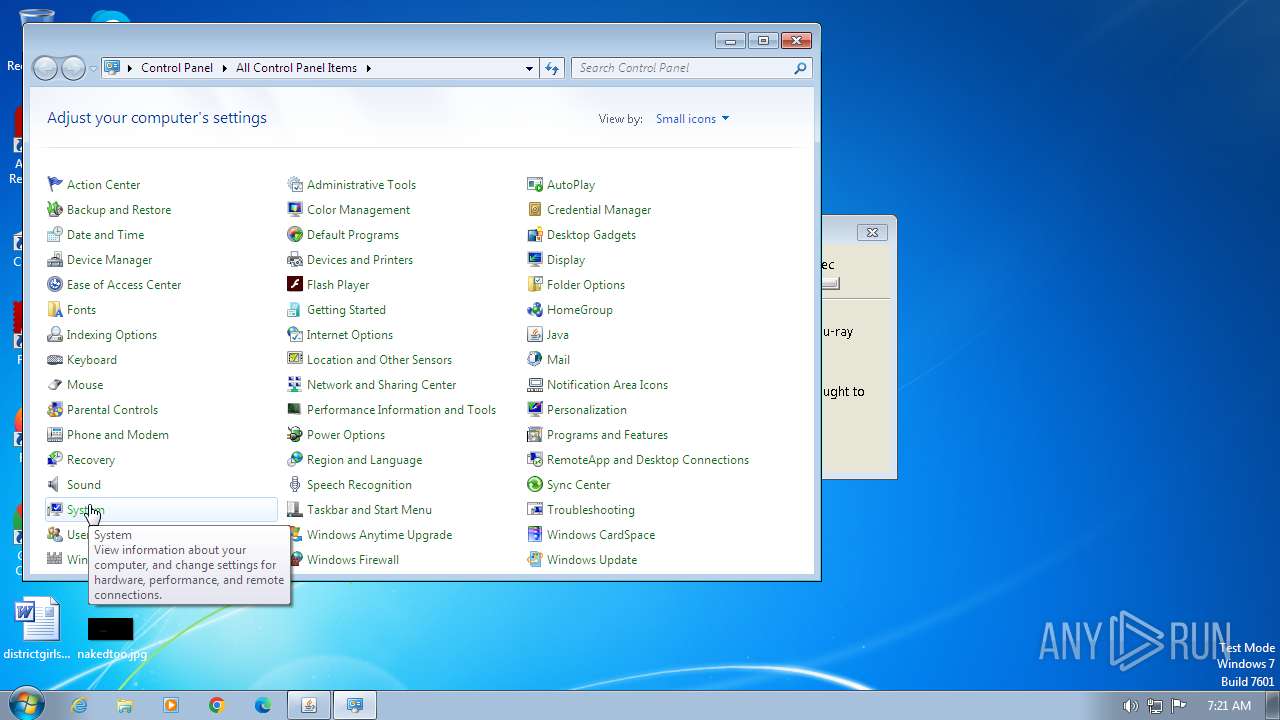
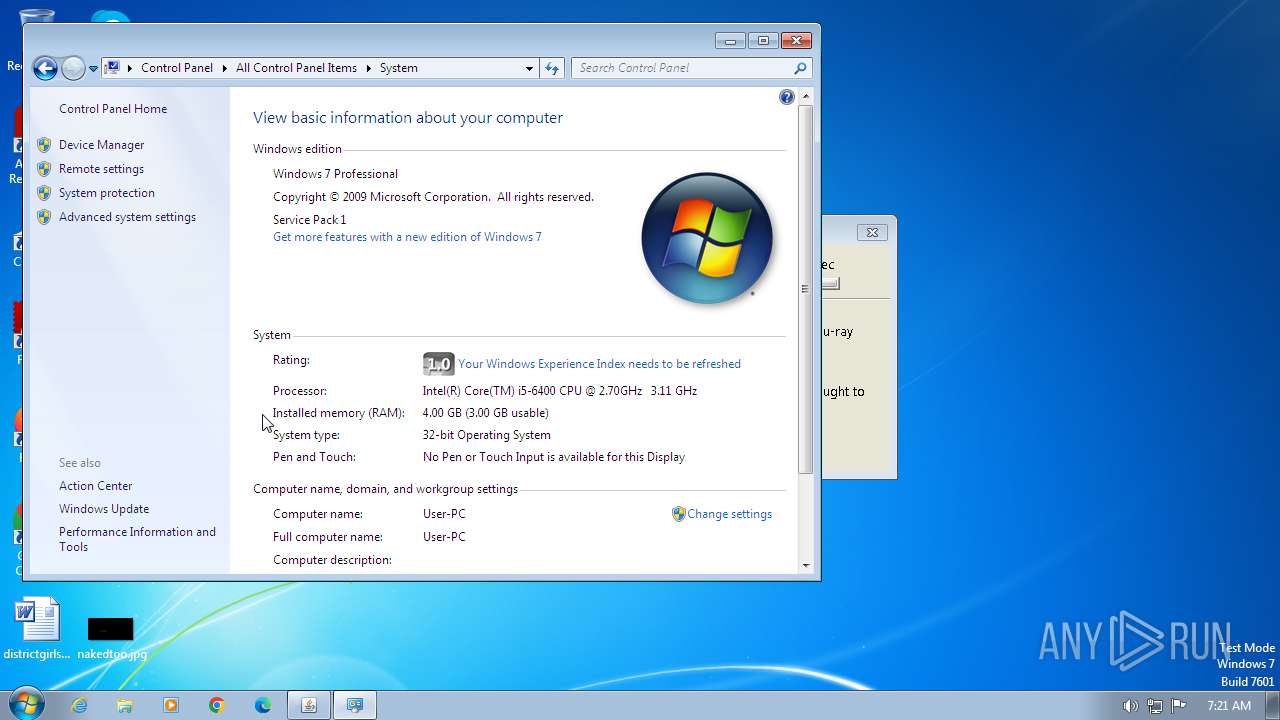
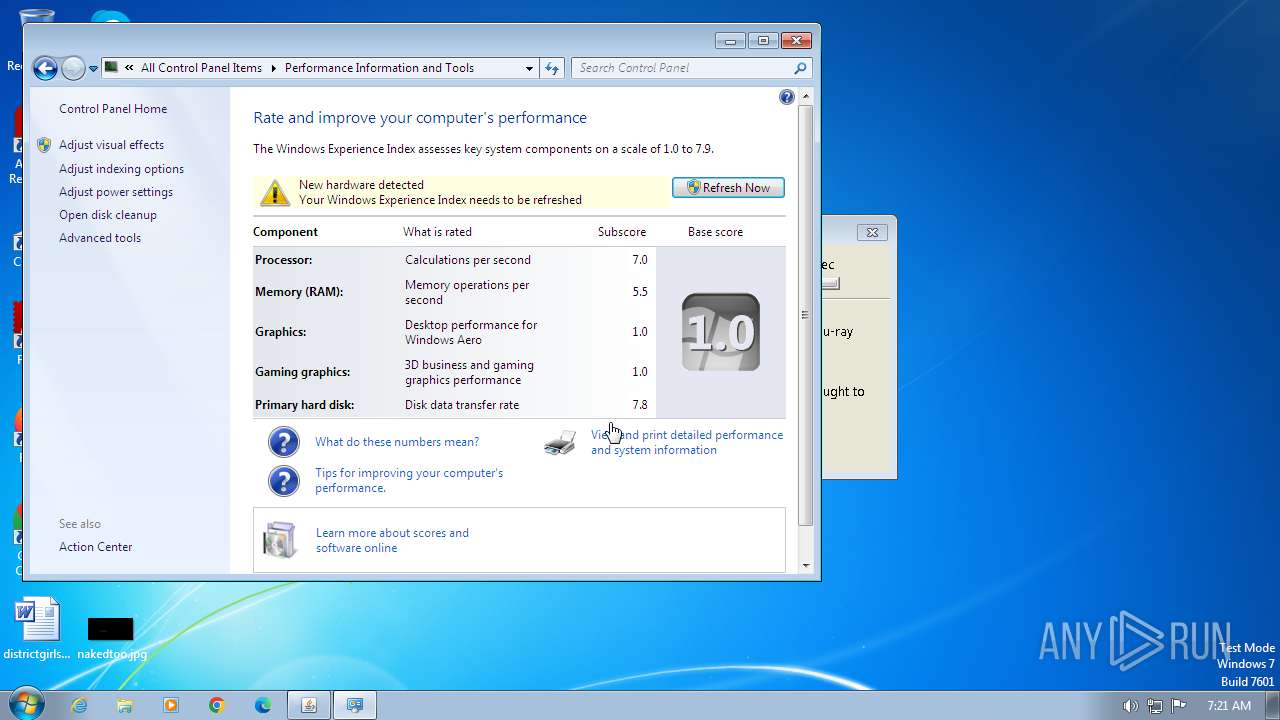
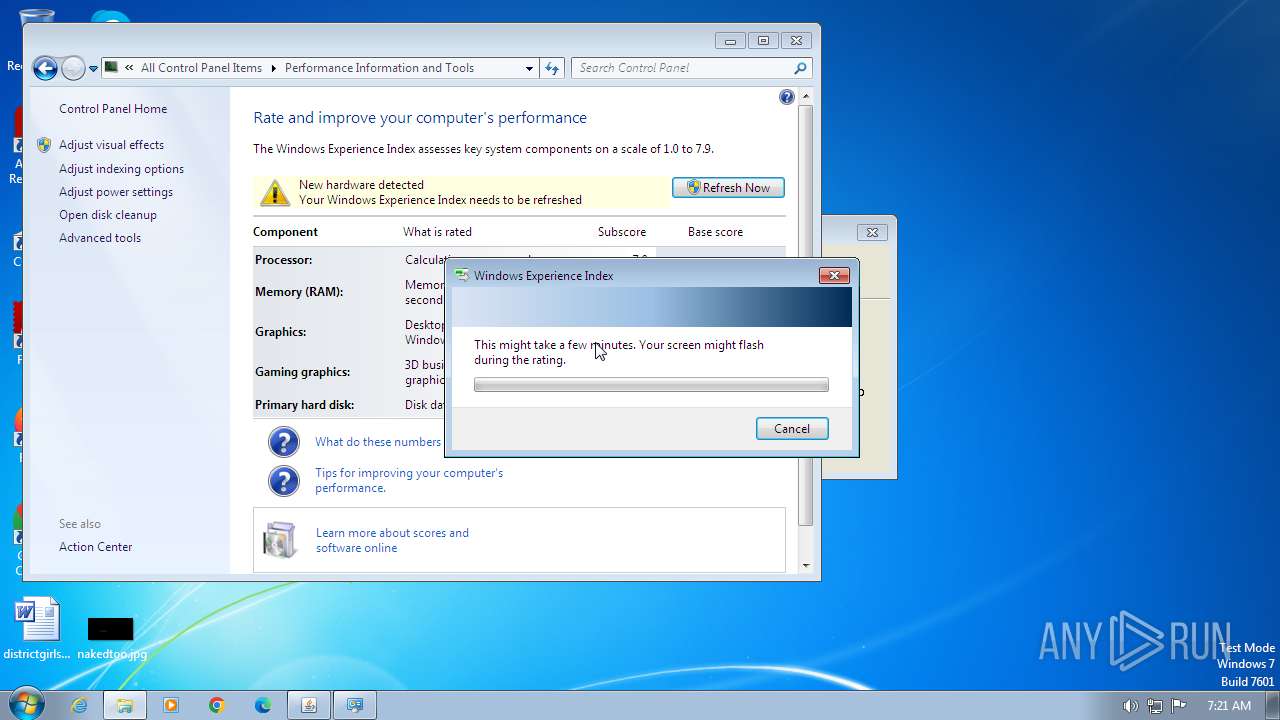
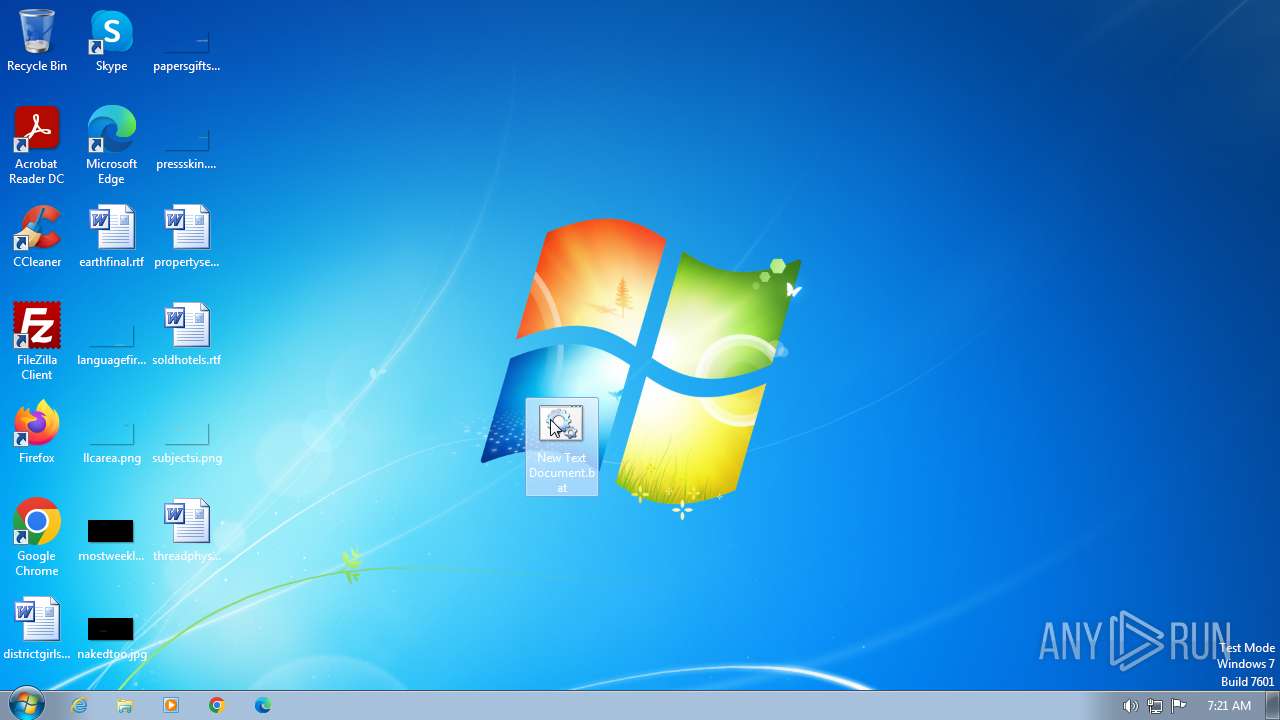
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
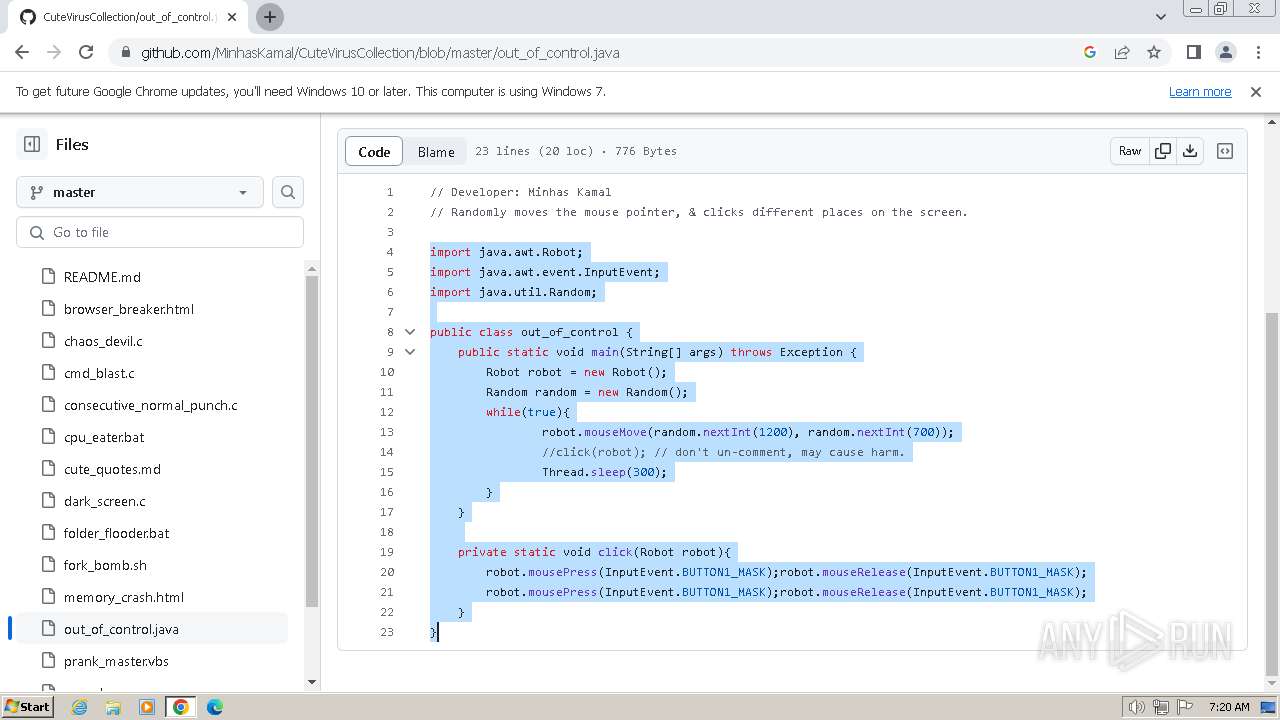
MALICIOUS
Creates a writable file in the system directory
- installer.exe (PID: 3800)
SUSPICIOUS
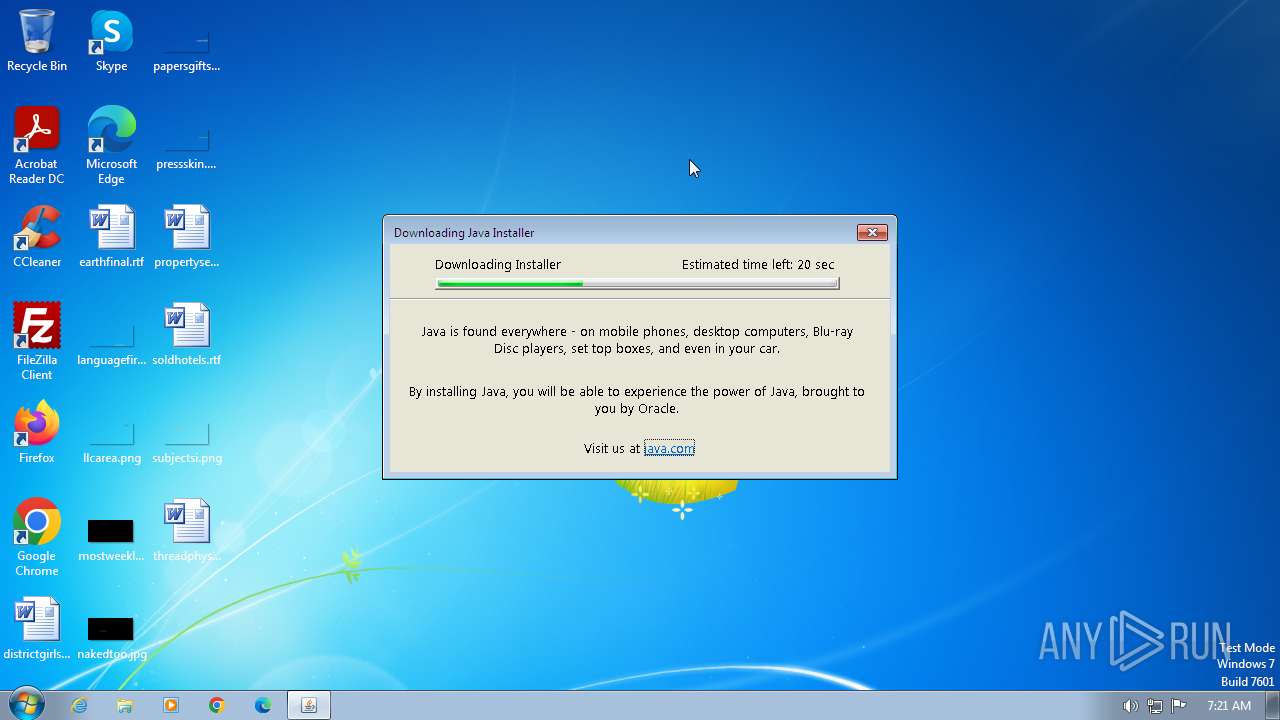
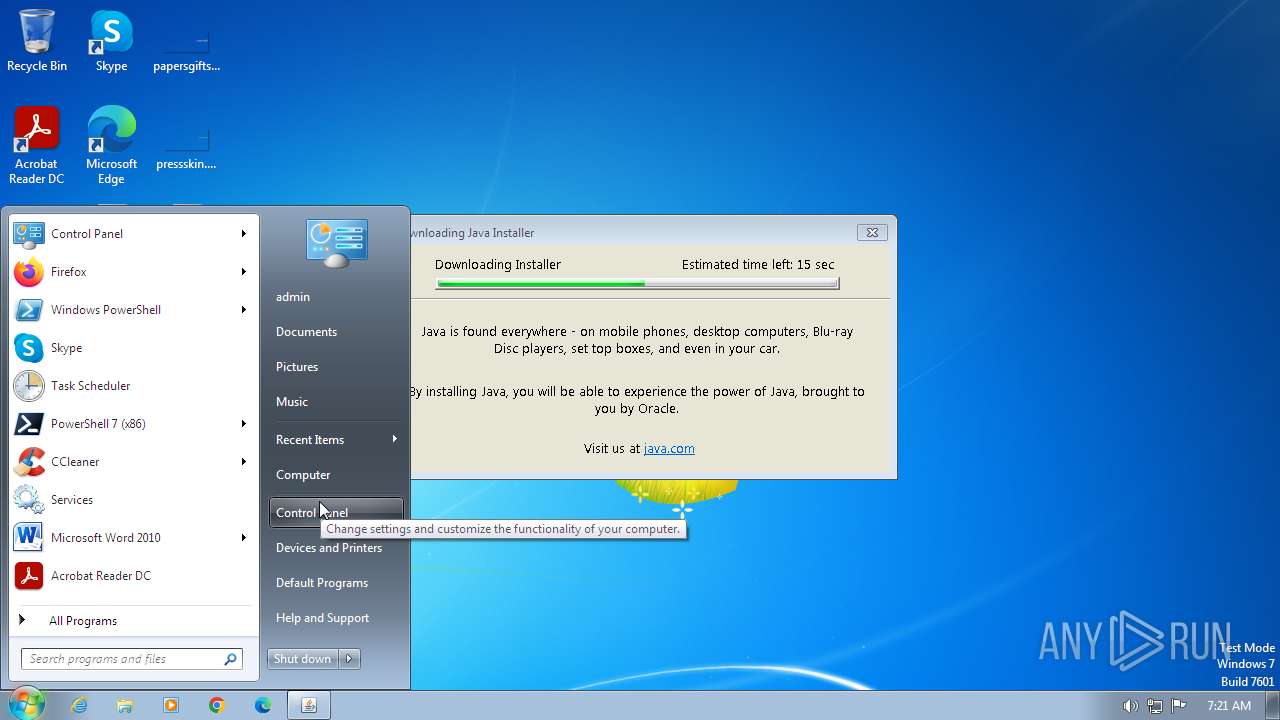
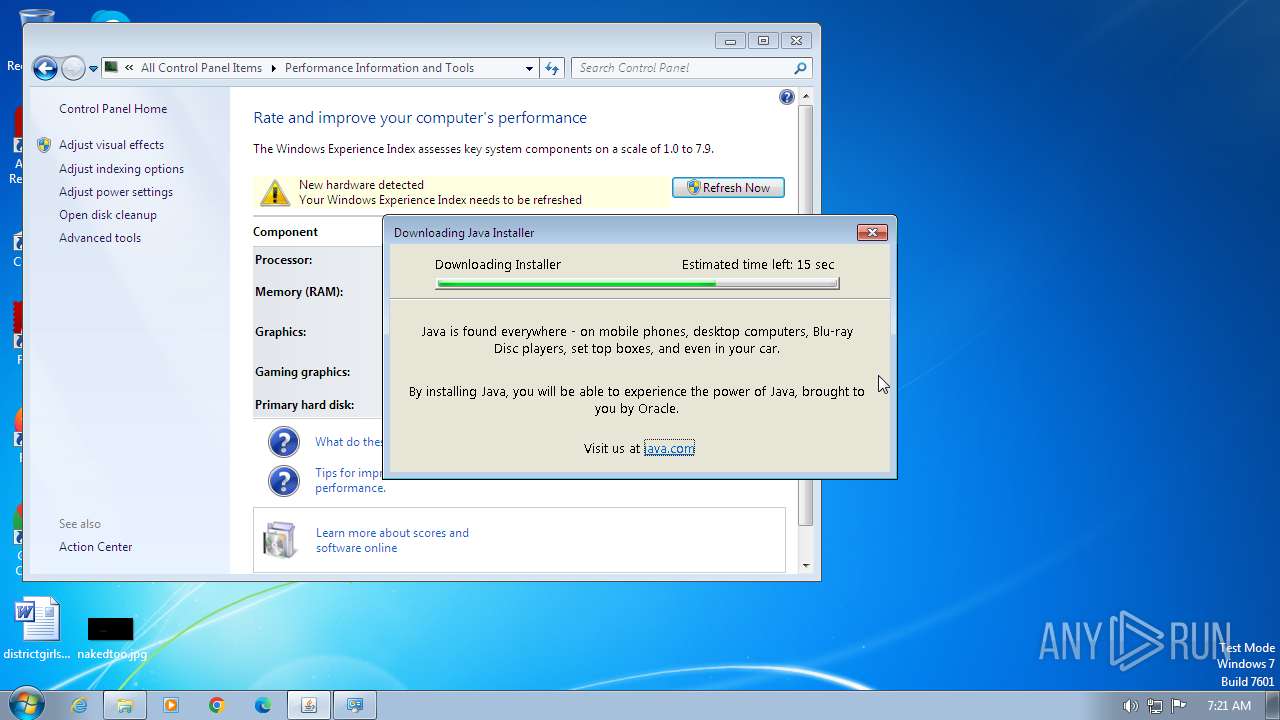
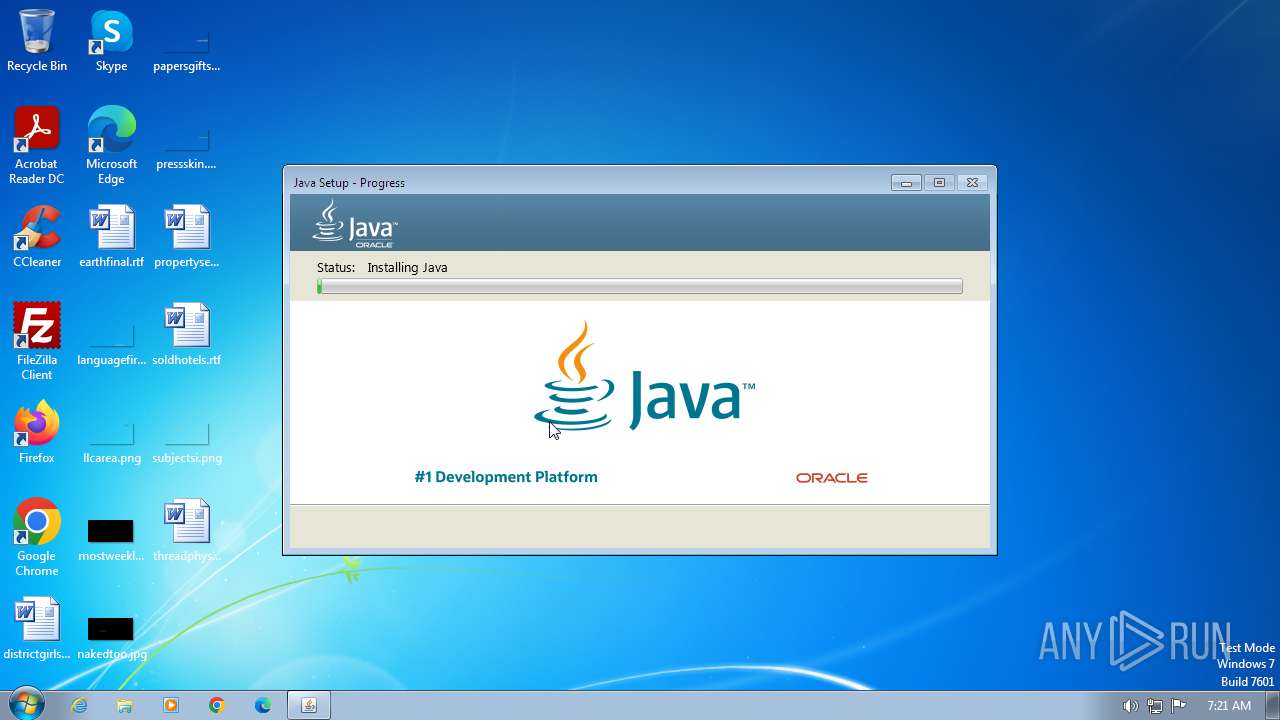
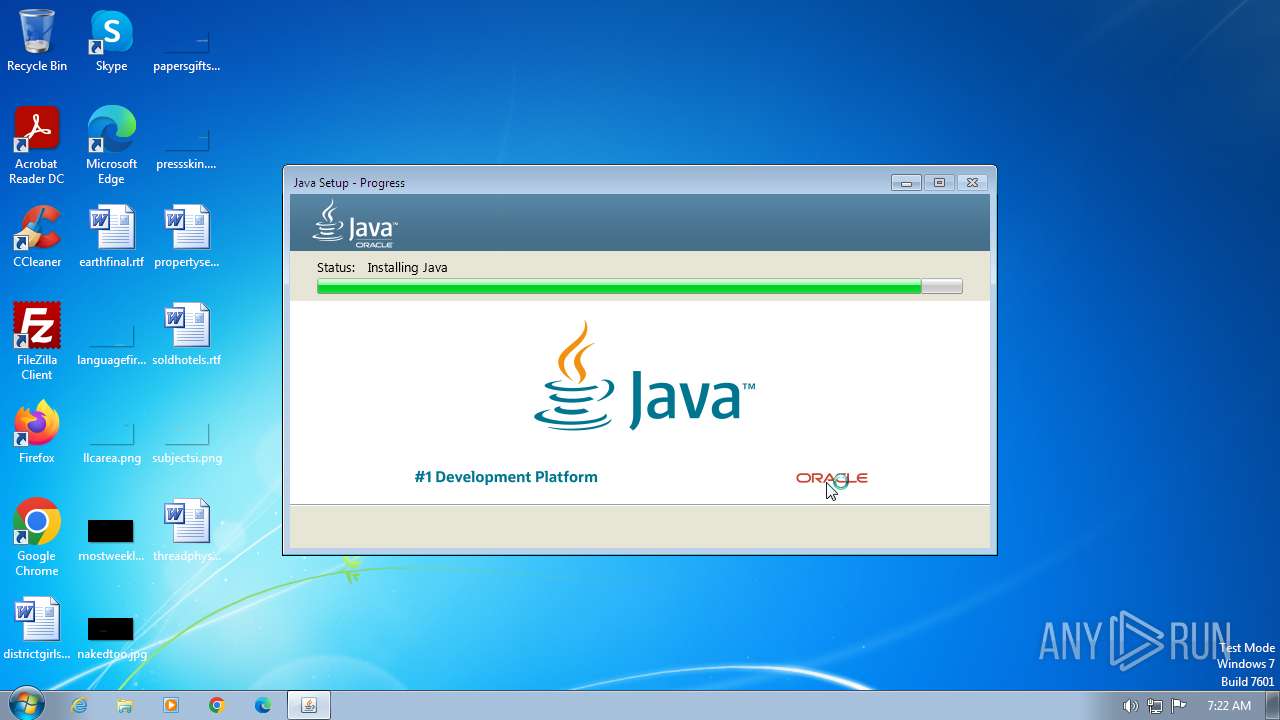
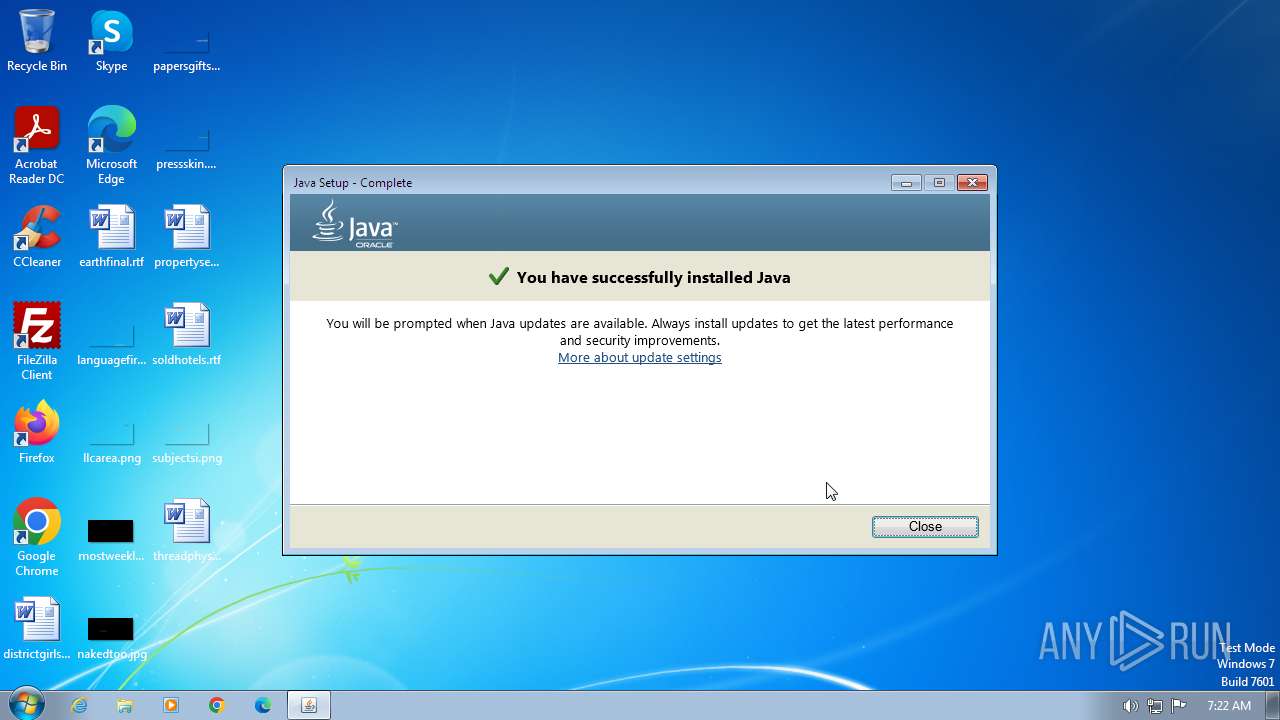
Reads the Internet Settings
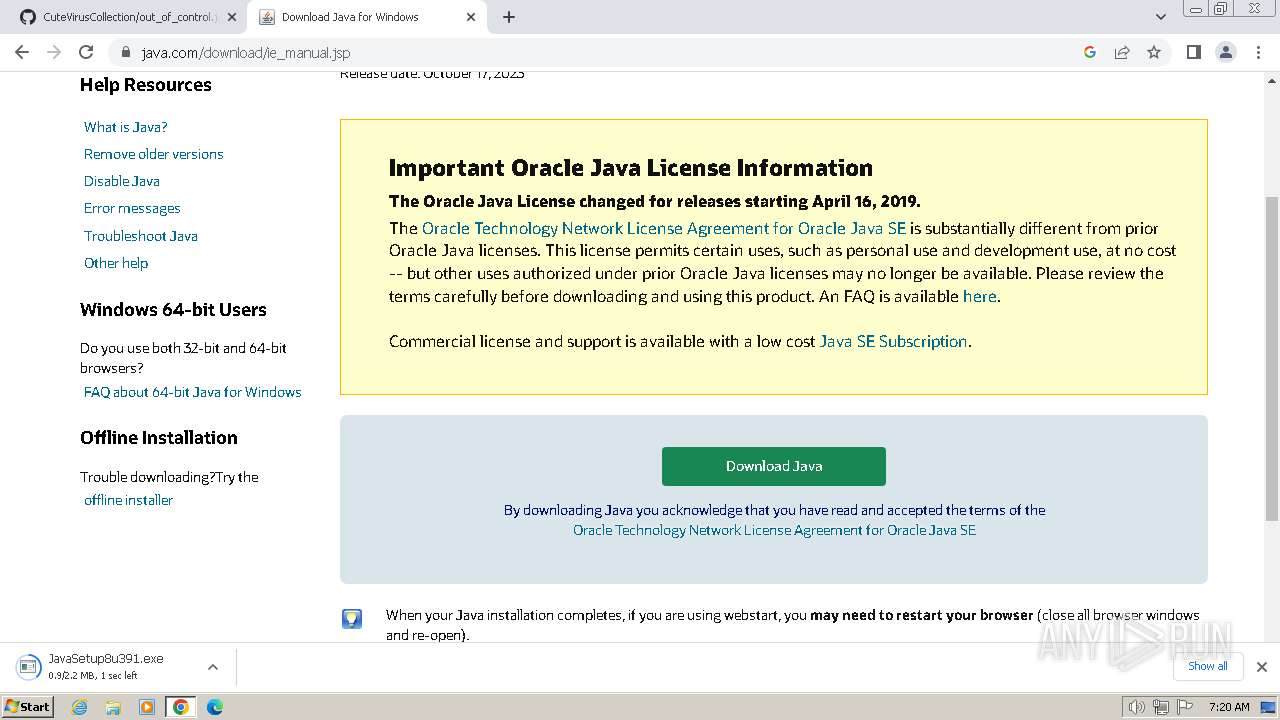
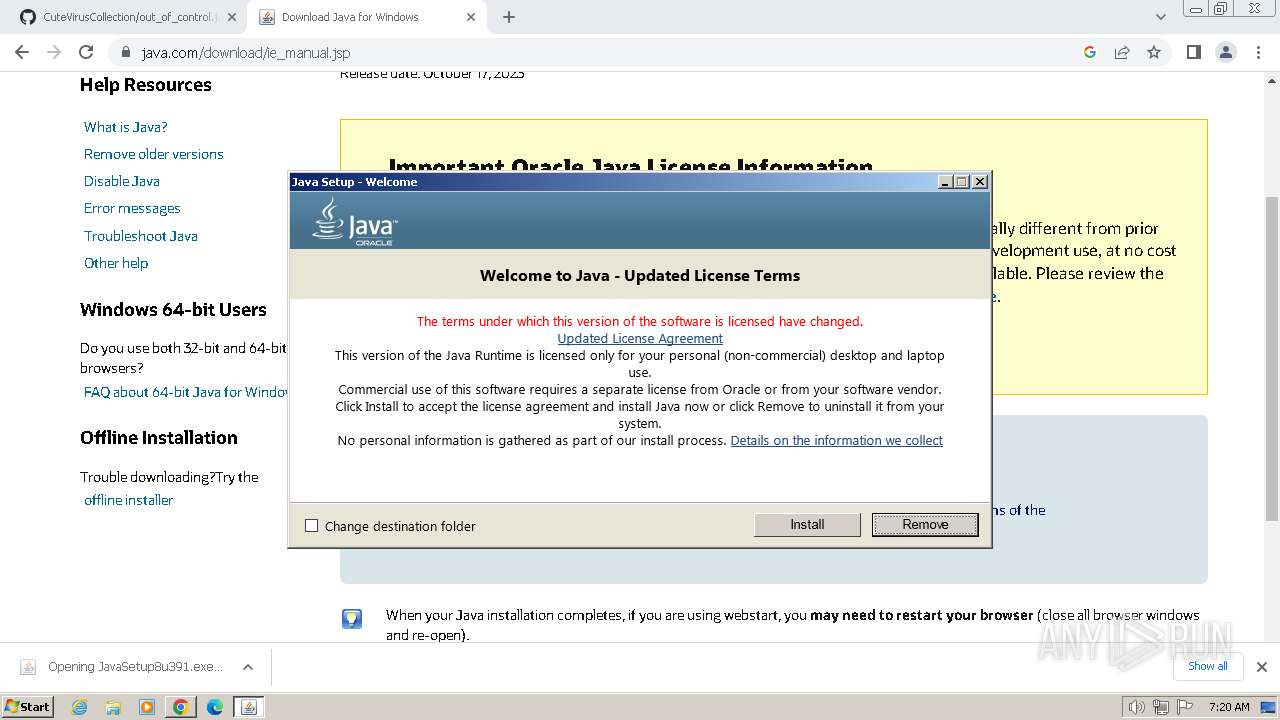
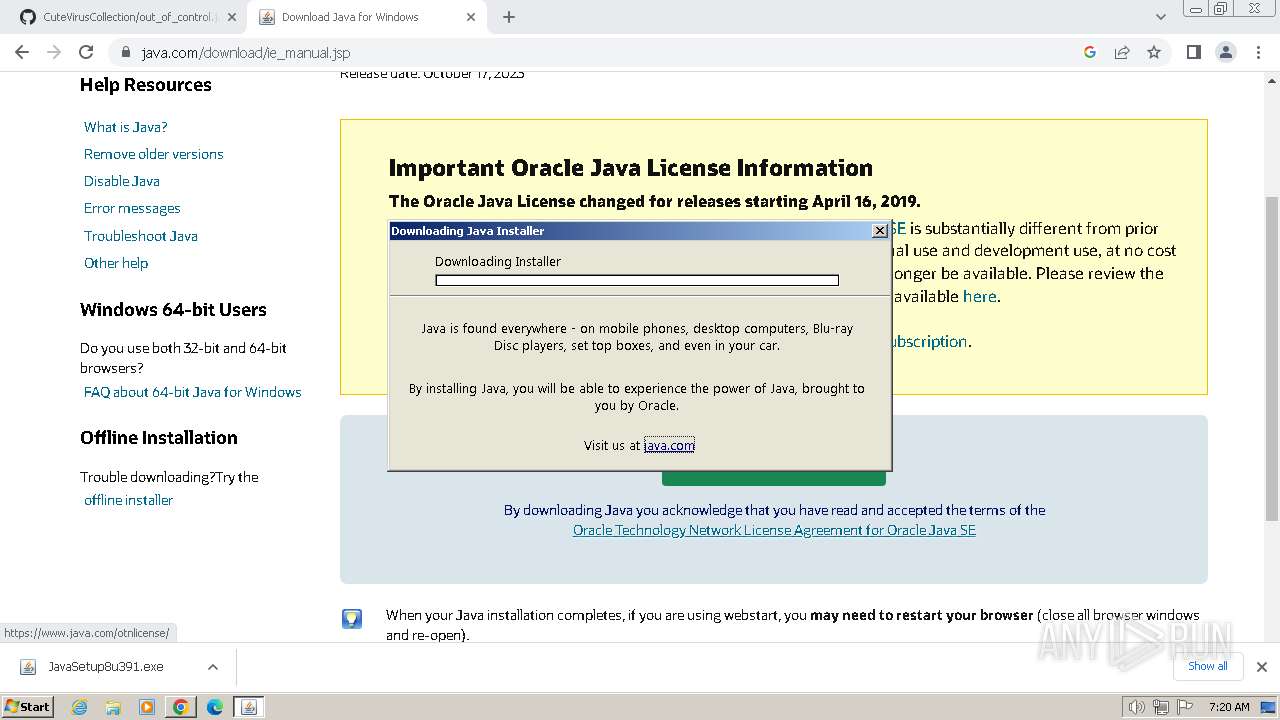
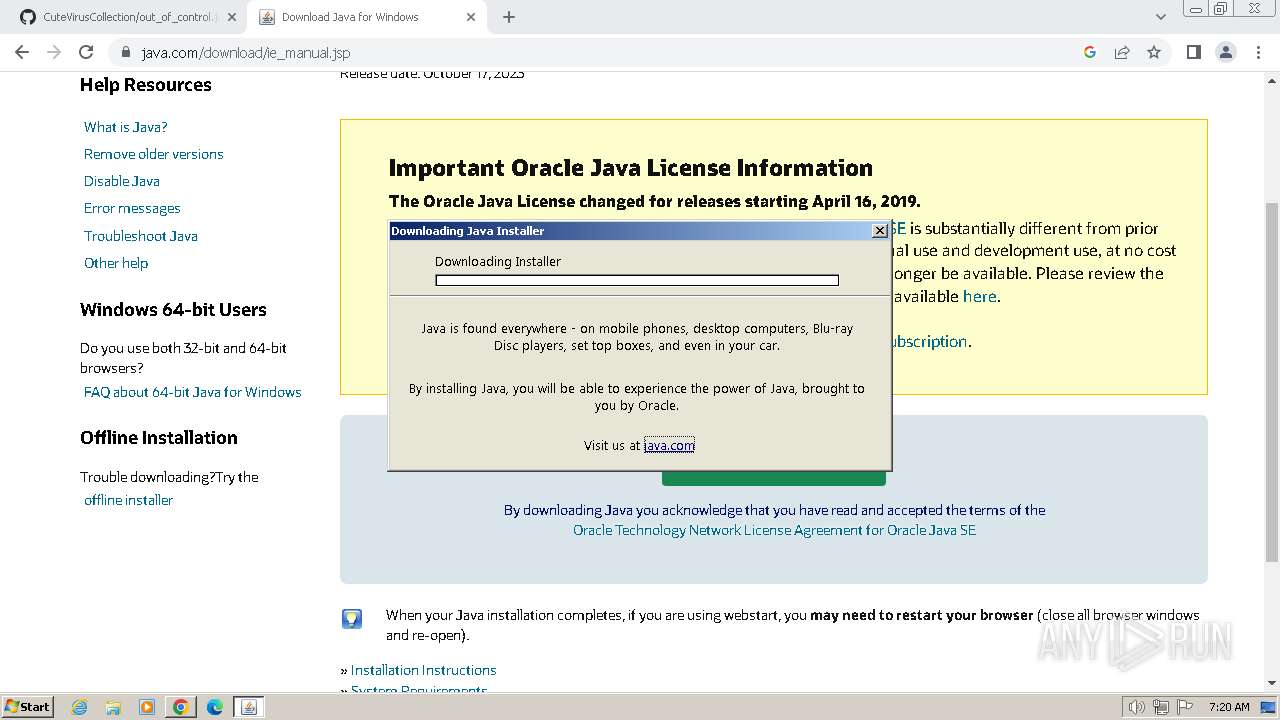
- JavaSetup8u391.exe (PID: 3732)
- WinSAT.exe (PID: 3932)
Reads security settings of Internet Explorer
- JavaSetup8u391.exe (PID: 3732)
Reads settings of System Certificates
- JavaSetup8u391.exe (PID: 3732)
Reads Internet Explorer settings
- JavaSetup8u391.exe (PID: 3732)
Starts application with an unusual extension
- JavaSetup8u391.exe (PID: 3732)
Reads Microsoft Outlook installation path
- JavaSetup8u391.exe (PID: 3732)
Checks Windows Trust Settings
- JavaSetup8u391.exe (PID: 3732)
- msiexec.exe (PID: 3880)
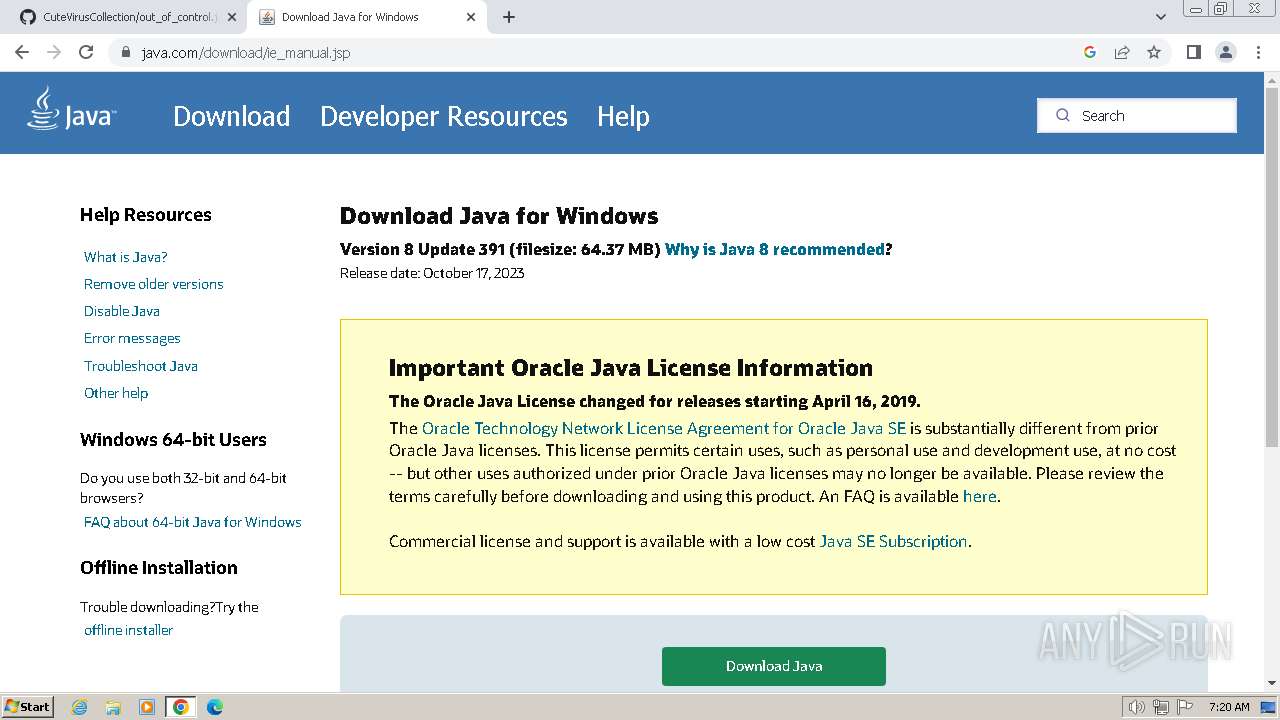
Checks for Java to be installed
- msiexec.exe (PID: 3880)
- ssvagent.exe (PID: 4036)
- jp2launcher.exe (PID: 268)
- installer.exe (PID: 3800)
- jp2launcher.exe (PID: 1652)
- javaw.exe (PID: 2516)
Reads Mozilla Firefox installation path
- MSI5A8C.tmp (PID: 1584)
- installer.exe (PID: 3800)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3880)
INFO
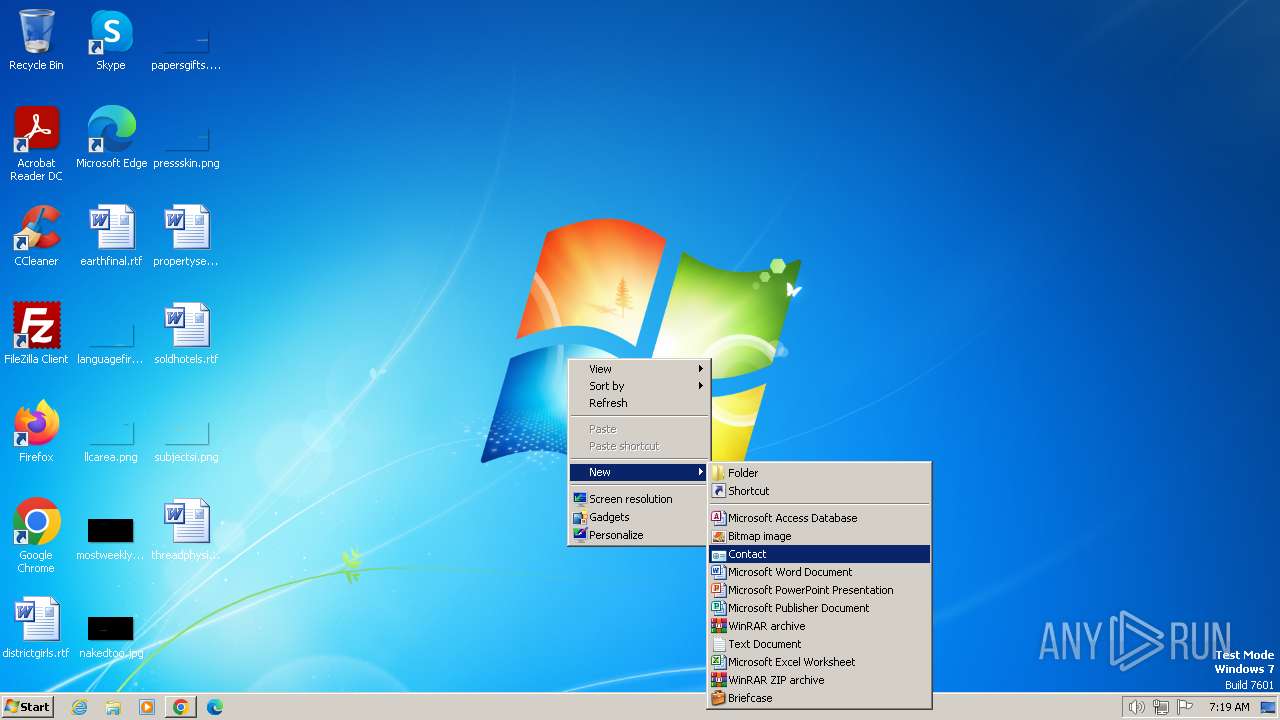
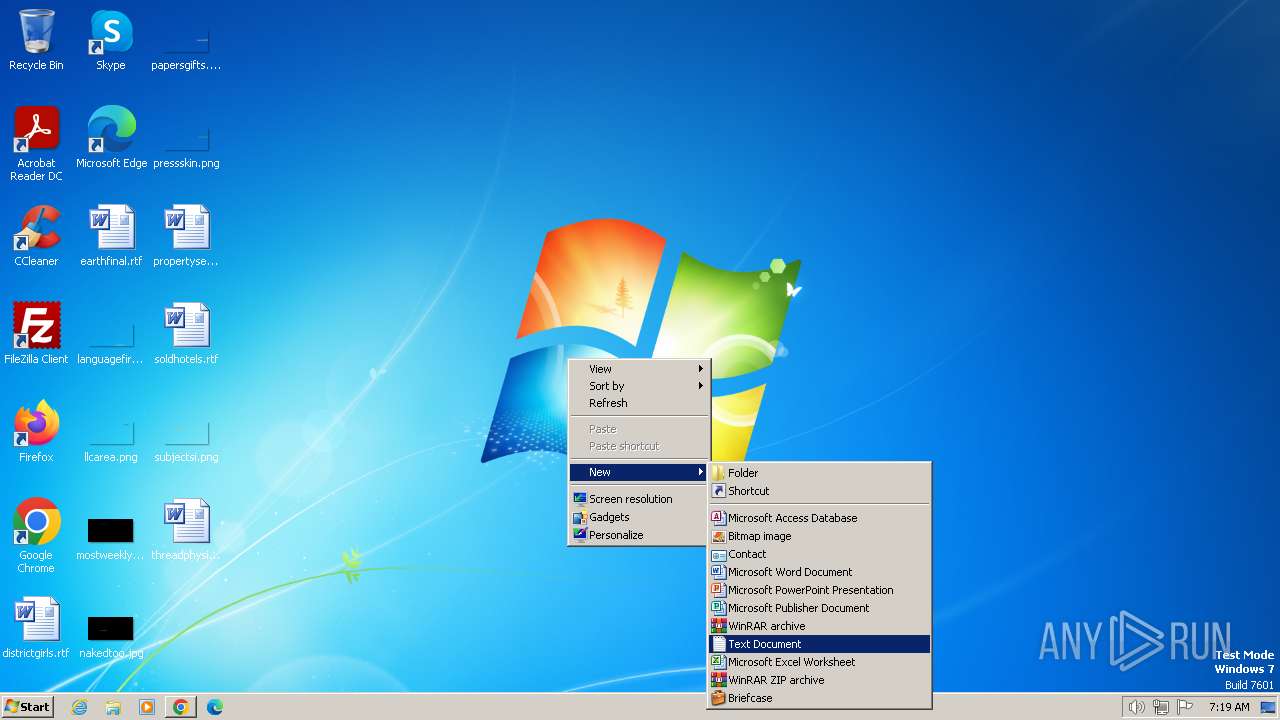
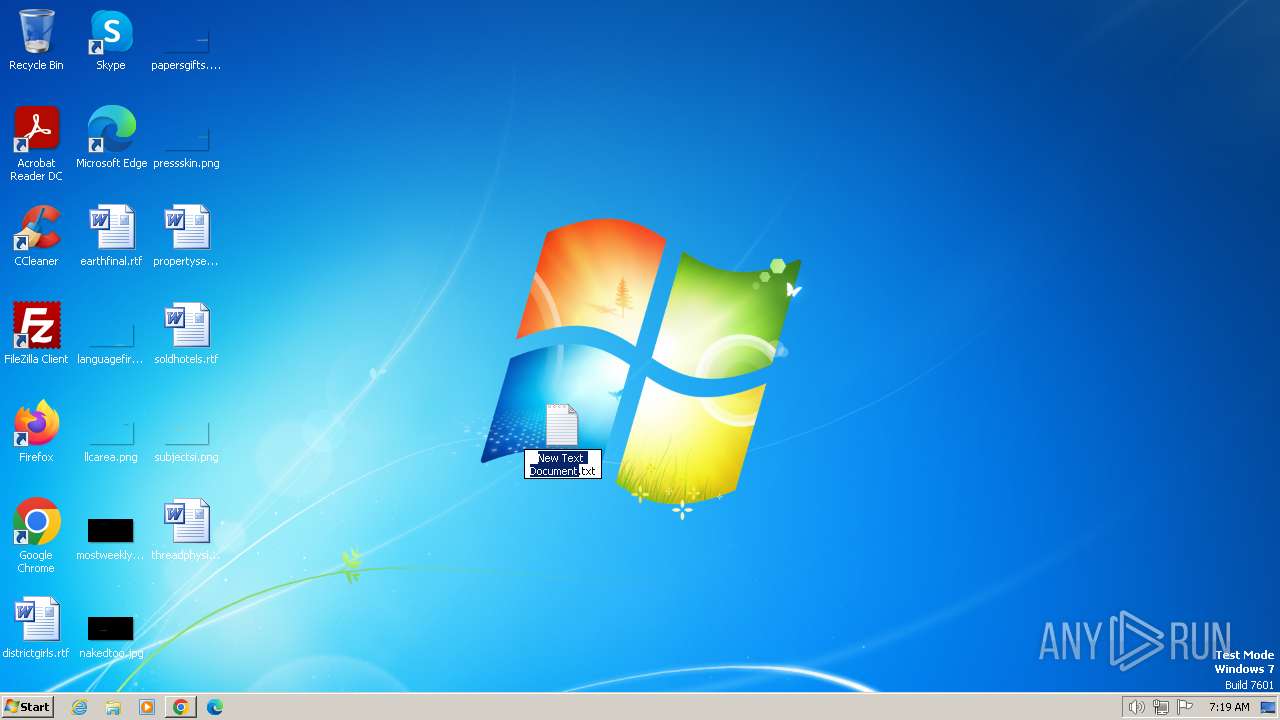
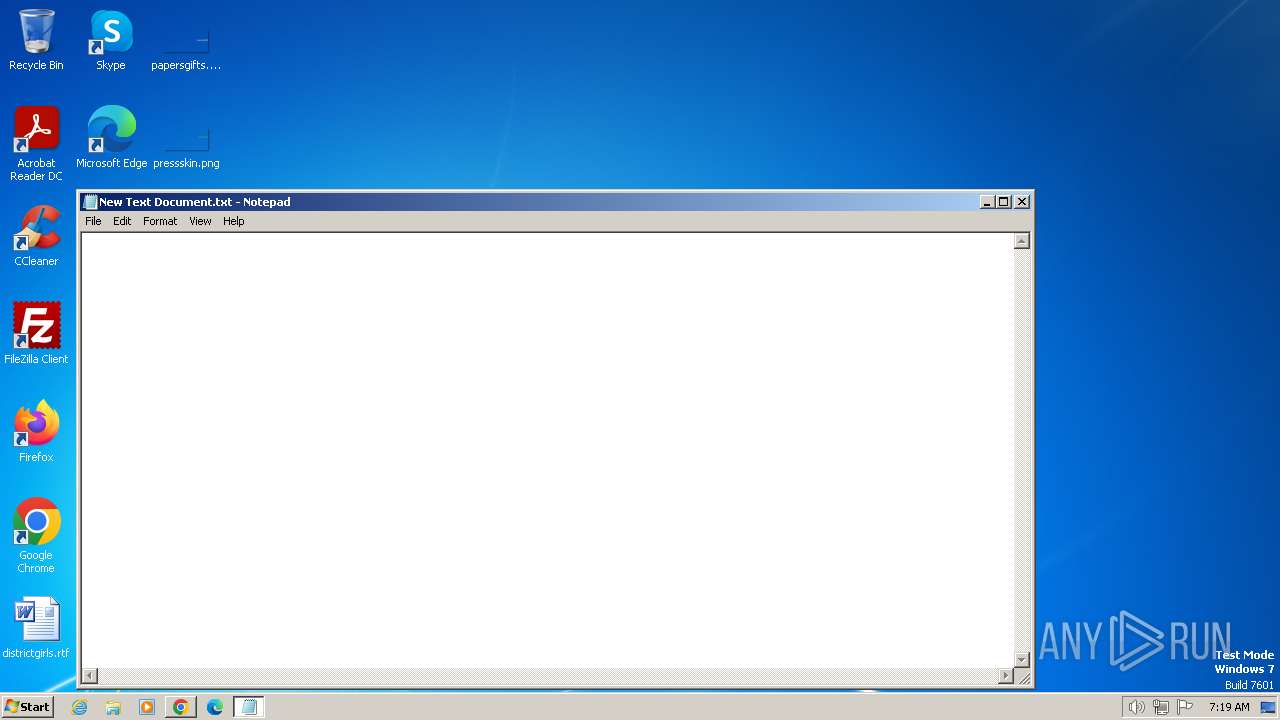
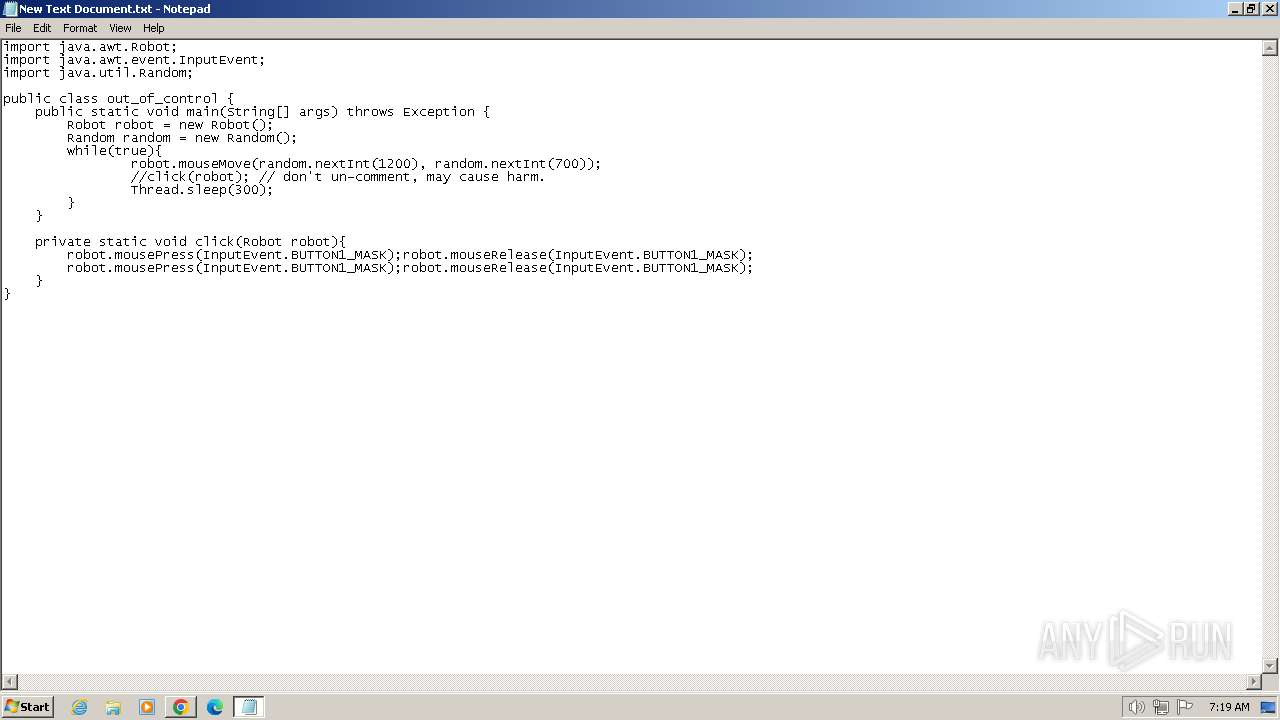
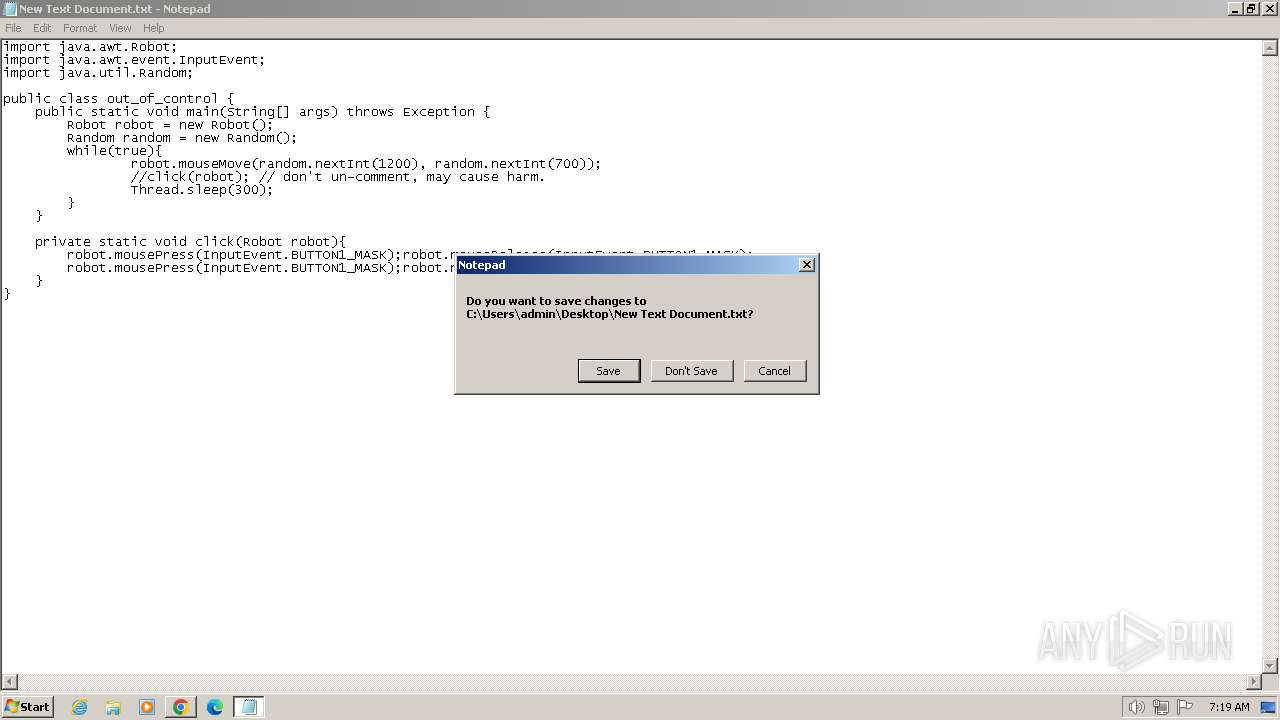
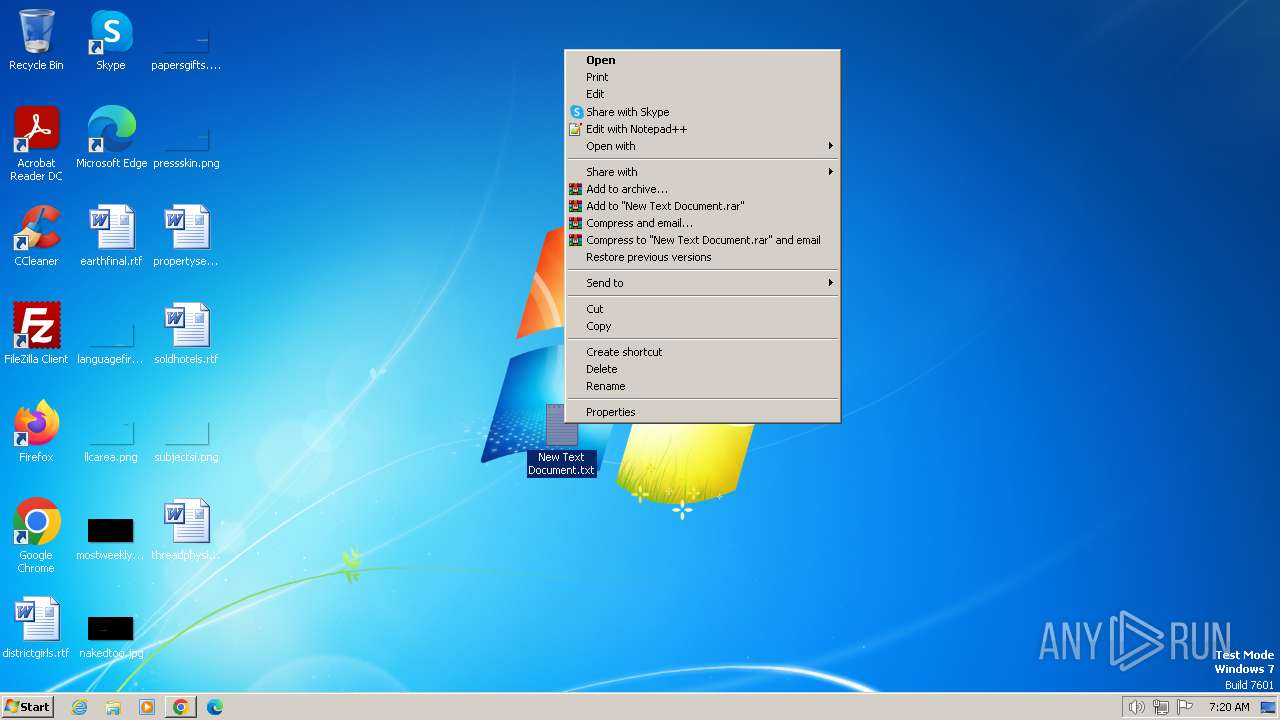
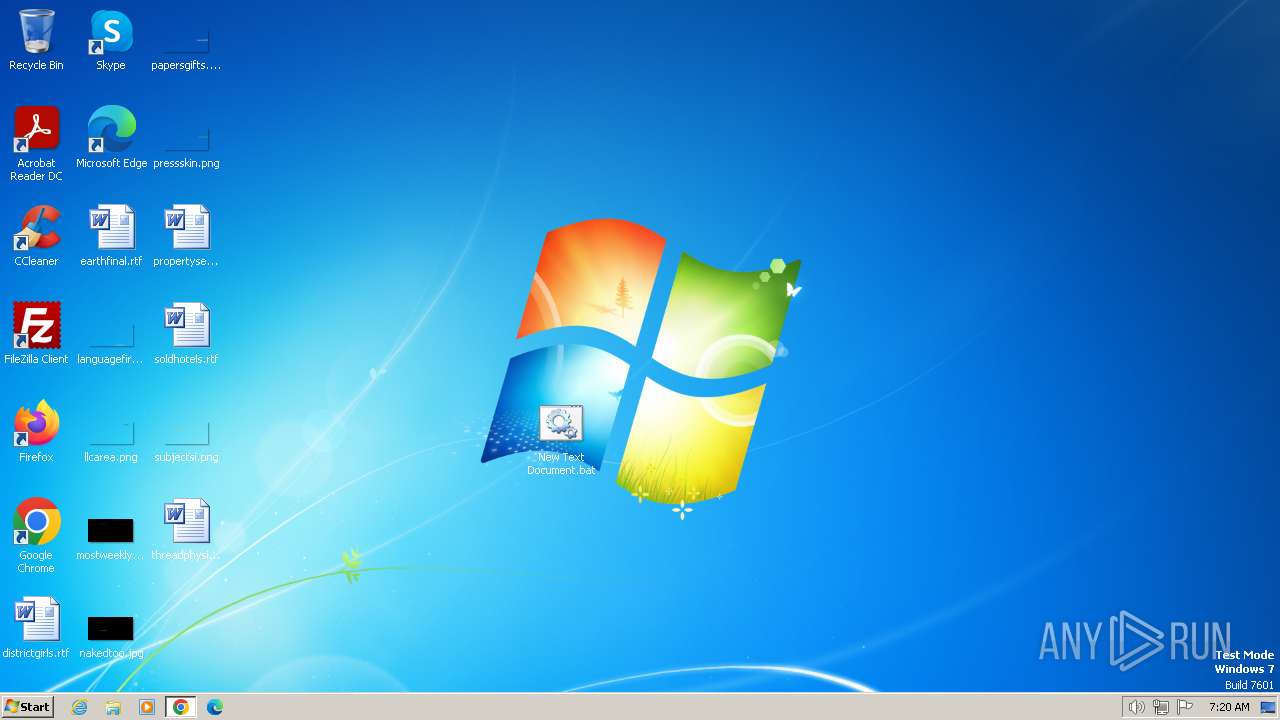
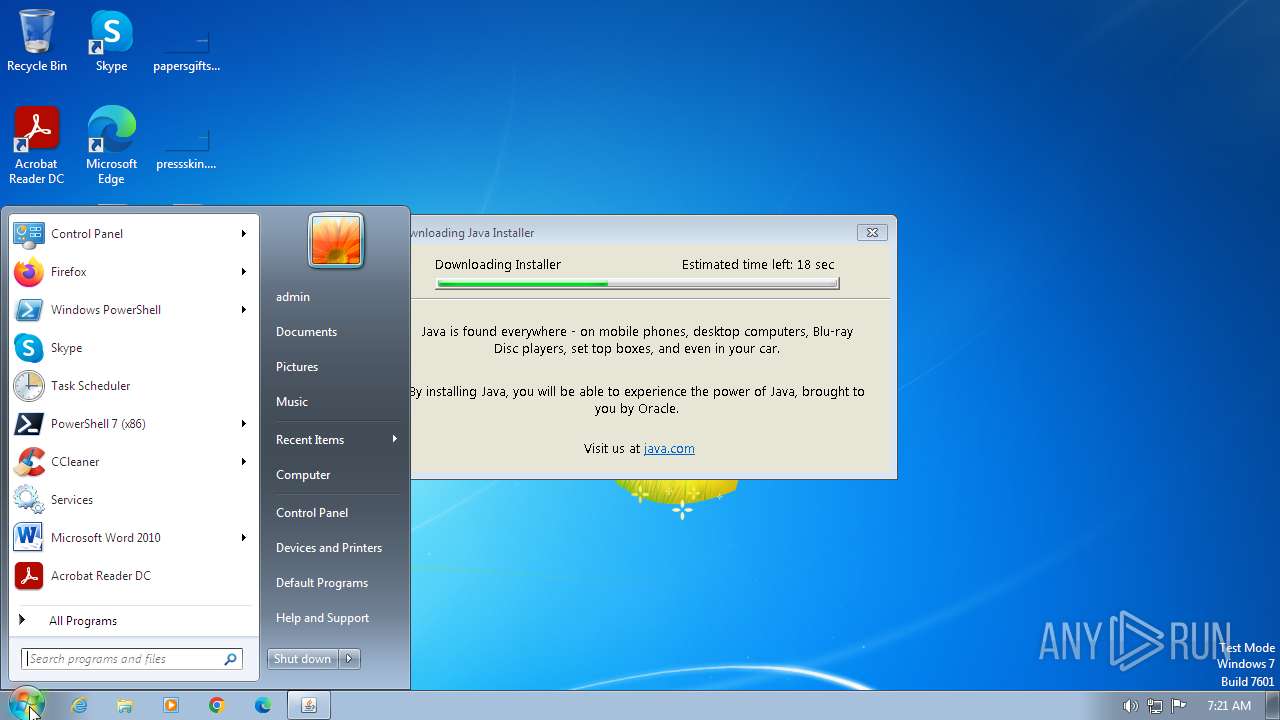
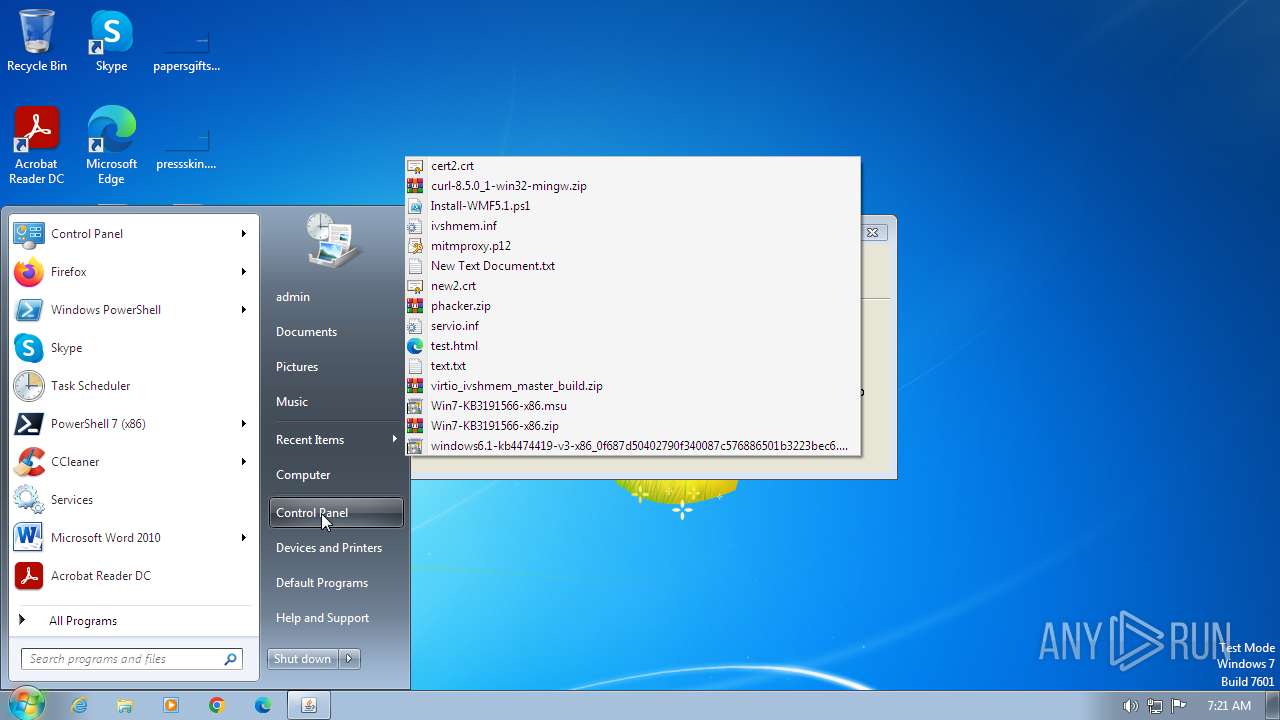
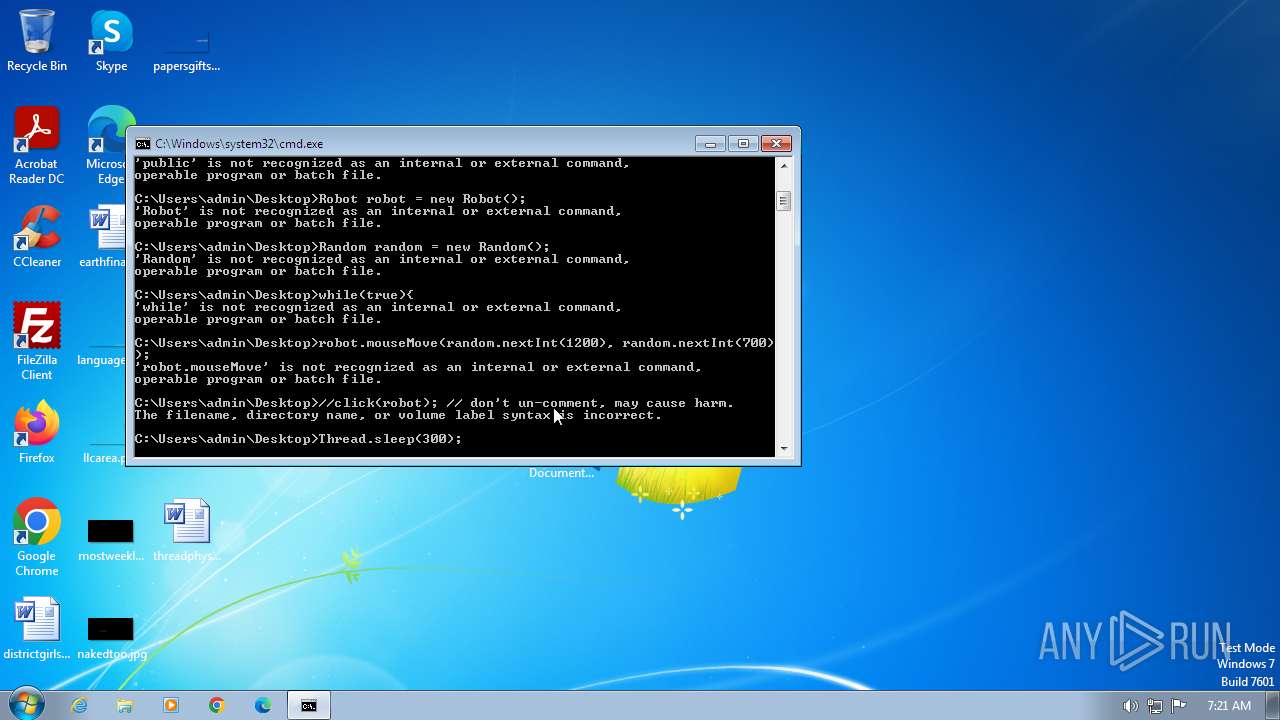
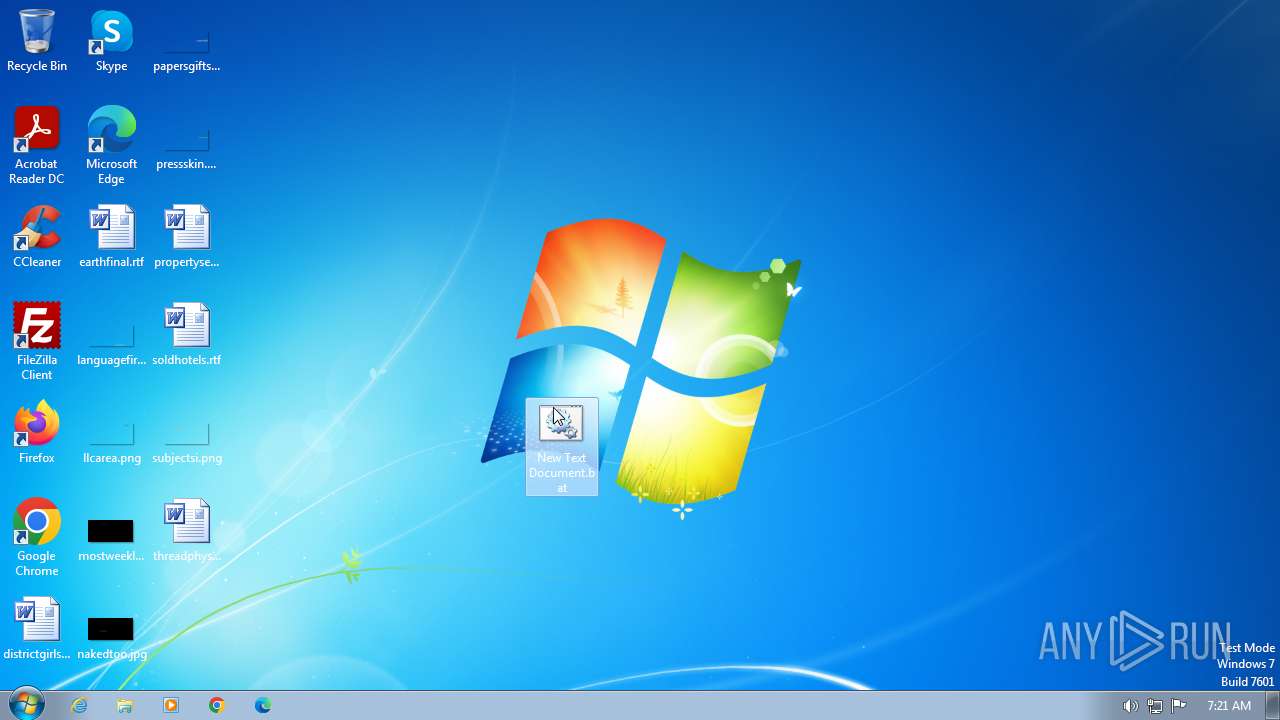
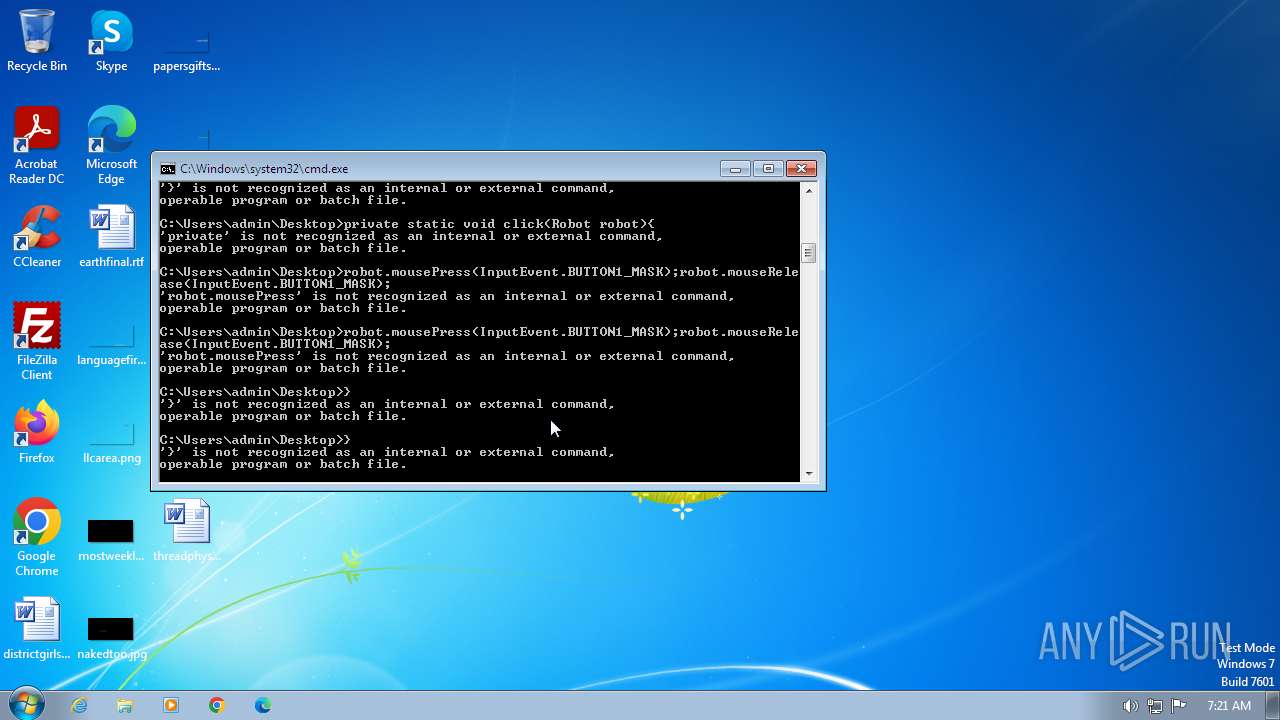
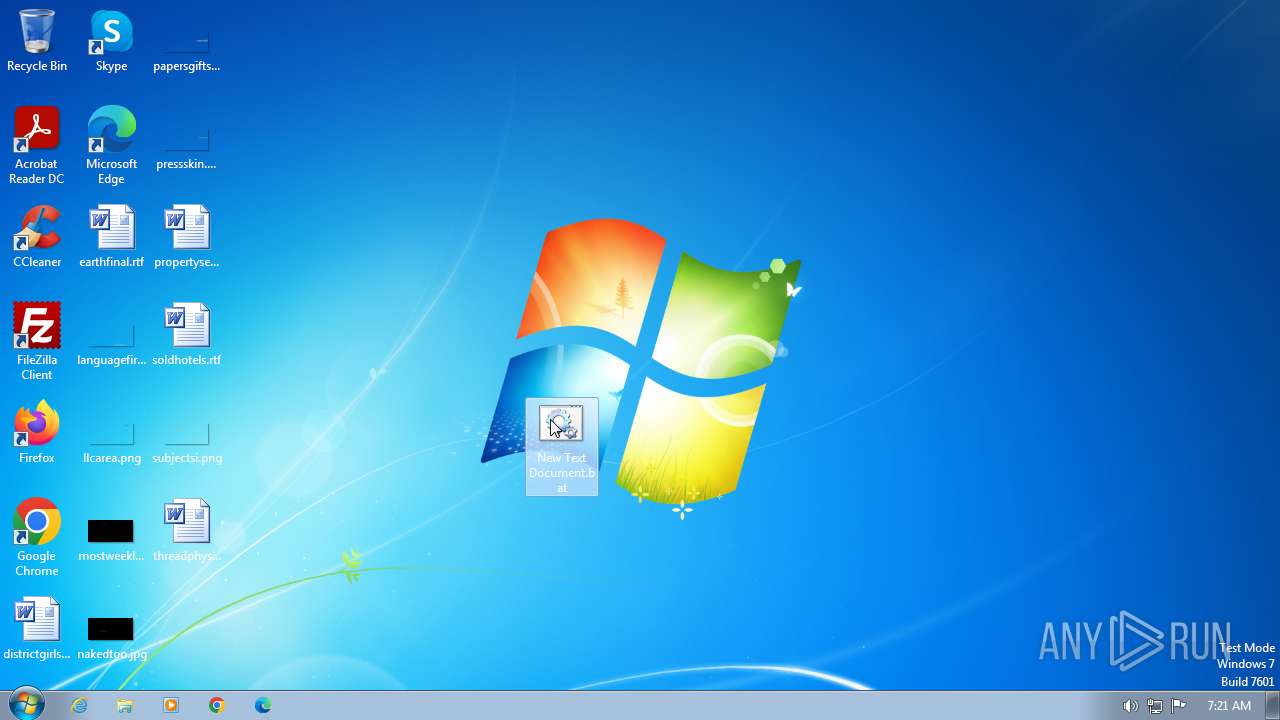
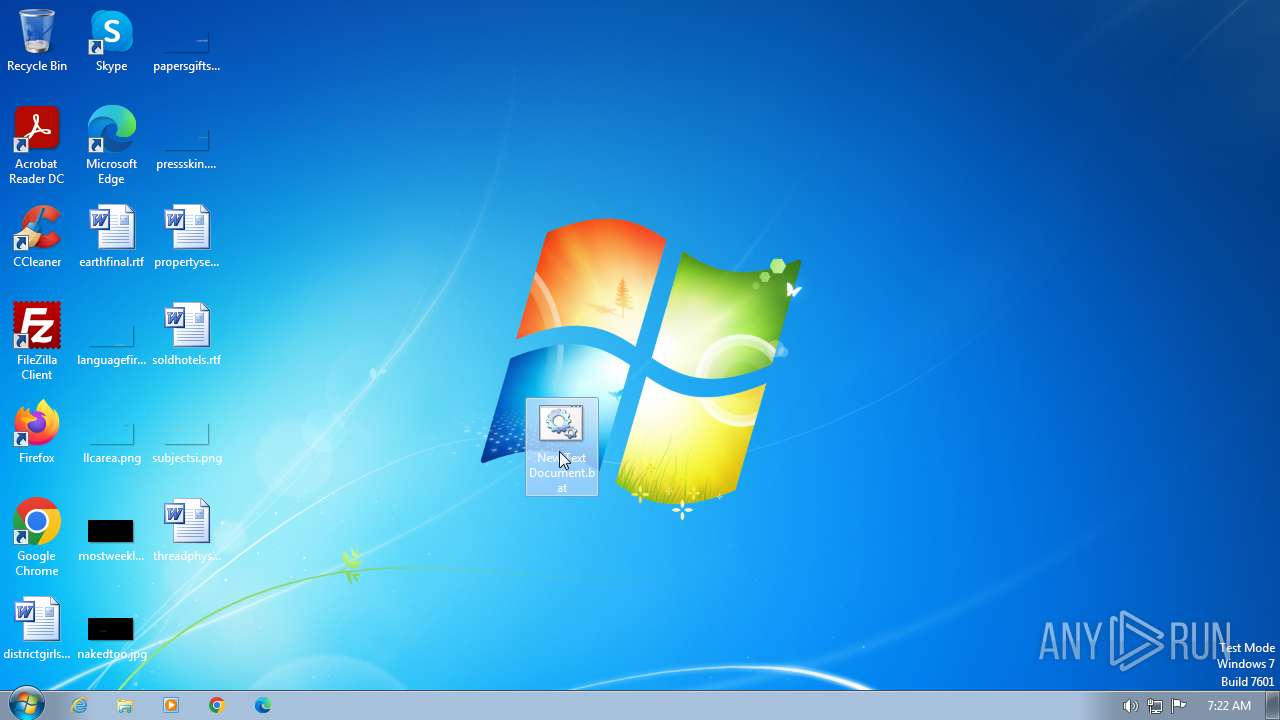
Manual execution by a user
- notepad.exe (PID: 3000)
- wmpnscfg.exe (PID: 2760)
- cmd.exe (PID: 3124)
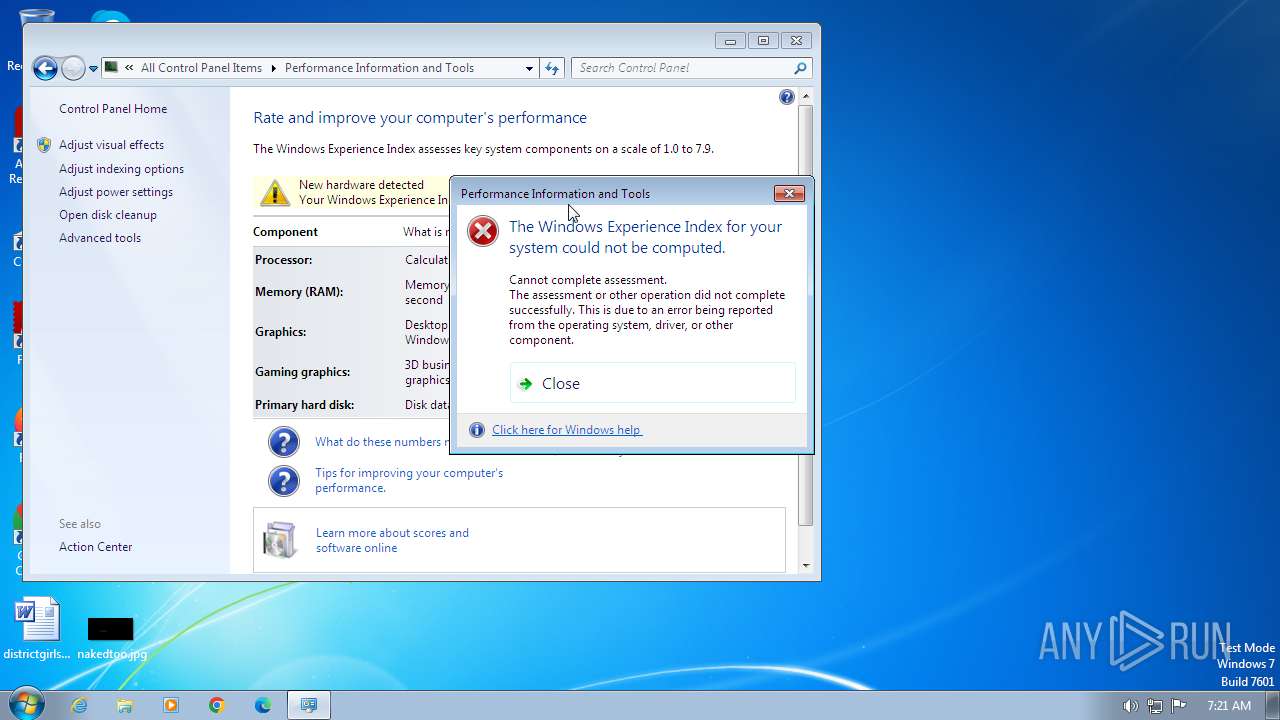
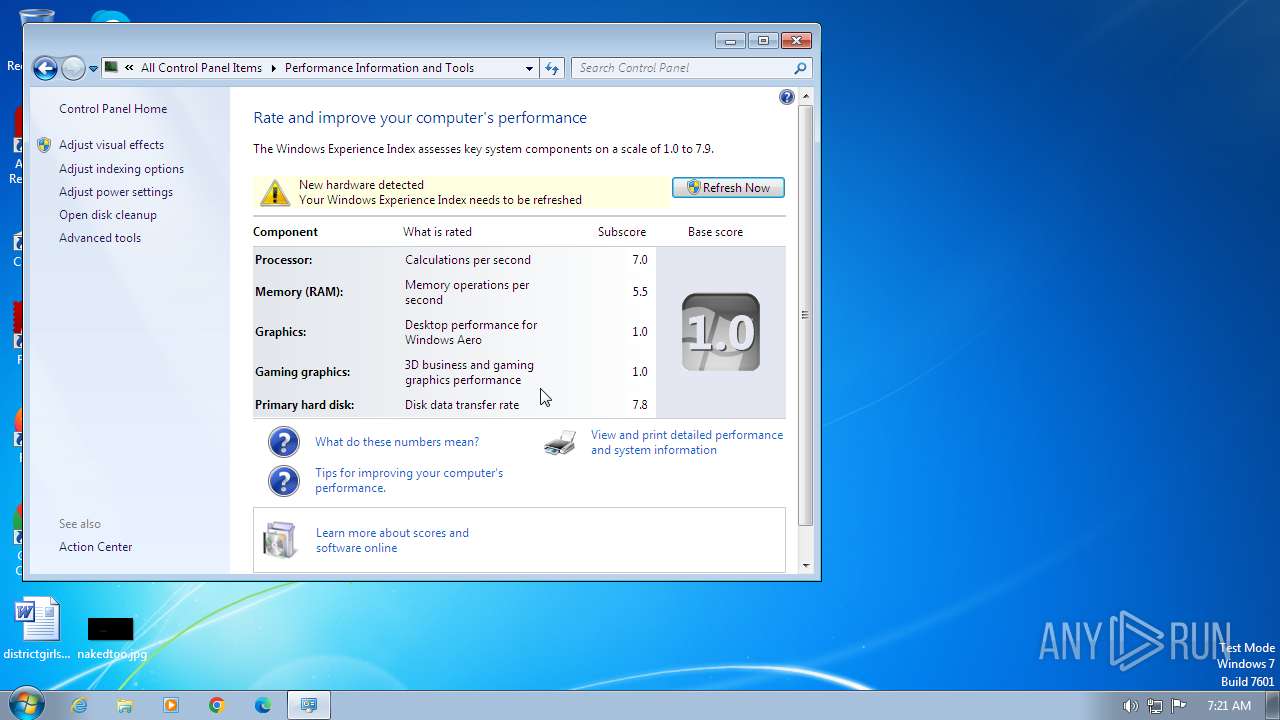
- WinSAT.exe (PID: 2396)
- WinSAT.exe (PID: 3932)
- cmd.exe (PID: 984)
- cmd.exe (PID: 752)
- cmd.exe (PID: 3472)
- cmd.exe (PID: 2584)
Application launched itself
- chrome.exe (PID: 2044)
- msiexec.exe (PID: 3880)
Reads the computer name
- wmpnscfg.exe (PID: 2760)
- JavaSetup8u391.exe (PID: 3712)
- JavaSetup8u391.exe (PID: 3732)
- msiexec.exe (PID: 3880)
- msiexec.exe (PID: 2424)
- MSI5A8C.tmp (PID: 1584)
- installer.exe (PID: 3800)
- javaws.exe (PID: 3796)
- jp2launcher.exe (PID: 268)
- javaws.exe (PID: 480)
- jp2launcher.exe (PID: 1652)
- msiexec.exe (PID: 3460)
- msiexec.exe (PID: 3668)
- msiexec.exe (PID: 680)
- msiexec.exe (PID: 3152)
- javaw.exe (PID: 2516)
- javaw.exe (PID: 2976)
Checks supported languages
- wmpnscfg.exe (PID: 2760)
- JavaSetup8u391.exe (PID: 3712)
- JavaSetup8u391.exe (PID: 3732)
- LZMA_EXE (PID: 3488)
- LZMA_EXE (PID: 3784)
- msiexec.exe (PID: 3880)
- msiexec.exe (PID: 2424)
- MSI5A8C.tmp (PID: 1584)
- jaureg.exe (PID: 3740)
- installer.exe (PID: 3800)
- ssvagent.exe (PID: 4036)
- javaws.exe (PID: 3796)
- jp2launcher.exe (PID: 268)
- javaw.exe (PID: 1380)
- javaws.exe (PID: 480)
- jp2launcher.exe (PID: 1652)
- msiexec.exe (PID: 3460)
- msiexec.exe (PID: 3668)
- msiexec.exe (PID: 680)
- msiexec.exe (PID: 3152)
- javaw.exe (PID: 2516)
- javaw.exe (PID: 2976)
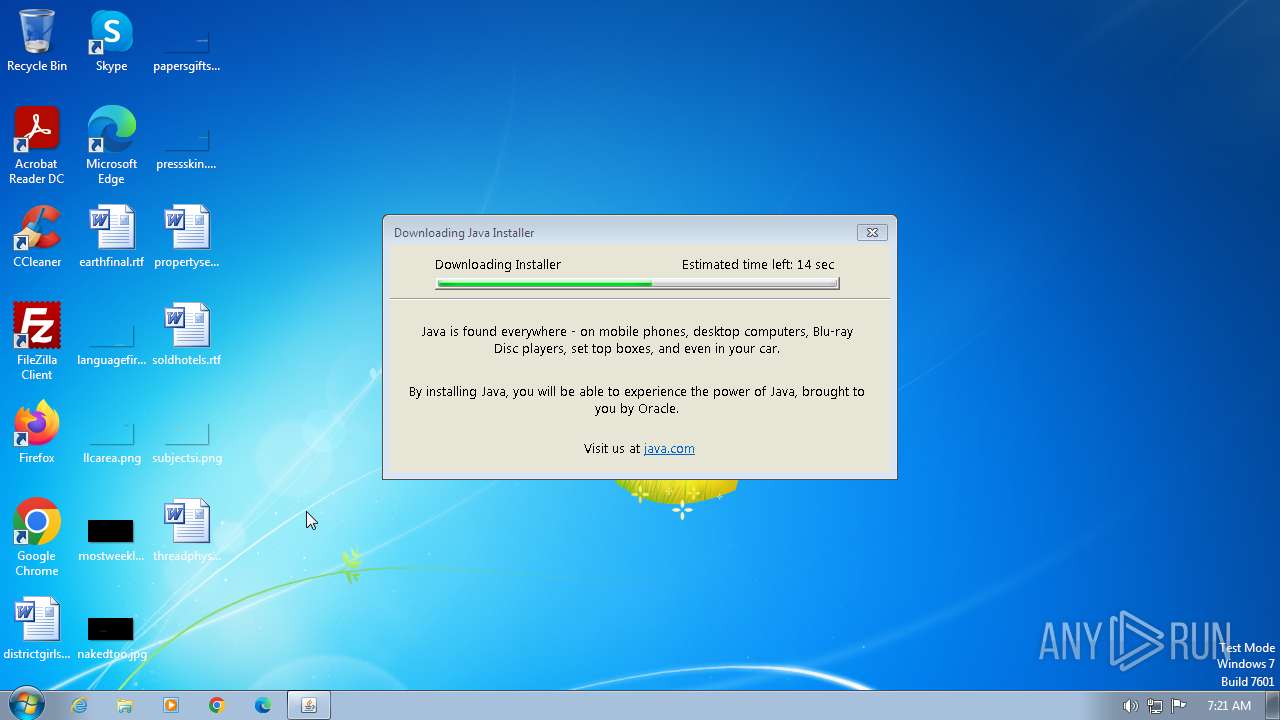
Drops the executable file immediately after the start
- chrome.exe (PID: 2936)
- chrome.exe (PID: 2044)
- JavaSetup8u391.exe (PID: 3712)
- JavaSetup8u391.exe (PID: 3732)
- msiexec.exe (PID: 3880)
- installer.exe (PID: 3800)
The process uses the downloaded file
- chrome.exe (PID: 2044)
- chrome.exe (PID: 1572)
Create files in a temporary directory
- JavaSetup8u391.exe (PID: 3712)
- msiexec.exe (PID: 3880)
- MSI5A8C.tmp (PID: 1584)
- javaw.exe (PID: 1380)
- jp2launcher.exe (PID: 268)
- jp2launcher.exe (PID: 1652)
Reads the machine GUID from the registry
- JavaSetup8u391.exe (PID: 3732)
- msiexec.exe (PID: 3880)
- msiexec.exe (PID: 2424)
- installer.exe (PID: 3800)
- jp2launcher.exe (PID: 268)
- msiexec.exe (PID: 3152)
- msiexec.exe (PID: 680)
- msiexec.exe (PID: 3460)
- msiexec.exe (PID: 3668)
- jp2launcher.exe (PID: 1652)
Checks proxy server information
- JavaSetup8u391.exe (PID: 3732)
Creates files or folders in the user directory
- JavaSetup8u391.exe (PID: 3732)
- LZMA_EXE (PID: 3784)
- LZMA_EXE (PID: 3488)
Reads CPU info
- msiexec.exe (PID: 3880)
Starts application with an unusual extension
- msiexec.exe (PID: 3880)
Process drops legitimate windows executable
- msiexec.exe (PID: 3880)
The process drops C-runtime libraries
- msiexec.exe (PID: 3880)
Creates files in the program directory
- javaw.exe (PID: 1380)
- installer.exe (PID: 3800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
126
Monitored processes
62
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Java\jre-1.8\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre-1.8" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlLTEuOFxsaWJcZGVwbG95LmphcgAtRGphdmEuc2VjdXJpdHkucG9saWN5PWZpbGU6QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZS0xLjhcbGliXHNlY3VyaXR5XGphdmF3cy5wb2xpY3kALUR0cnVzdFByb3h5PXRydWUALVh2ZXJpZnk6cmVtb3RlAC1Eam5scHguaG9tZT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlLTEuOFxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUtMS44XGxpYlxqYXZhd3MuamFyO0M6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUtMS44XGxpYlxkZXBsb3kuamFyO0M6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUtMS44XGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlLTEuOFxiaW5camF2YXcuZXhl -ma LXdhaXQALWZpeAAtcGVybWlzc2lvbnMALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre-1.8\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.391.2.13 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=3956 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1508 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Java\jre-1.8\bin\javaws.exe" -wait -fix -shortcut -silent | C:\Program Files\Java\jre-1.8\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.391.2.13 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1072 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1272 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4208 --field-trial-handle=1140,i,3383376463072567869,12800647618785462383,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | C:\Windows\system32\MsiExec.exe -Embedding 712427A1F127EB3DFC71B61233A781D9 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\New Text Document.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 984 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\New Text Document.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
41 148
Read events
20 773
Write events
197
Delete events
20 178
Modification events
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
341
Suspicious files
199
Text files
245
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdfc81.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdfc81.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe0059.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe0fca.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
76
DNS requests
99
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 5.63 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.83 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.89 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 13.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 75.9 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 36.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 164 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 239 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
532 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
532 | chrome.exe | 142.250.186.174:443 | google.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.186.74:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
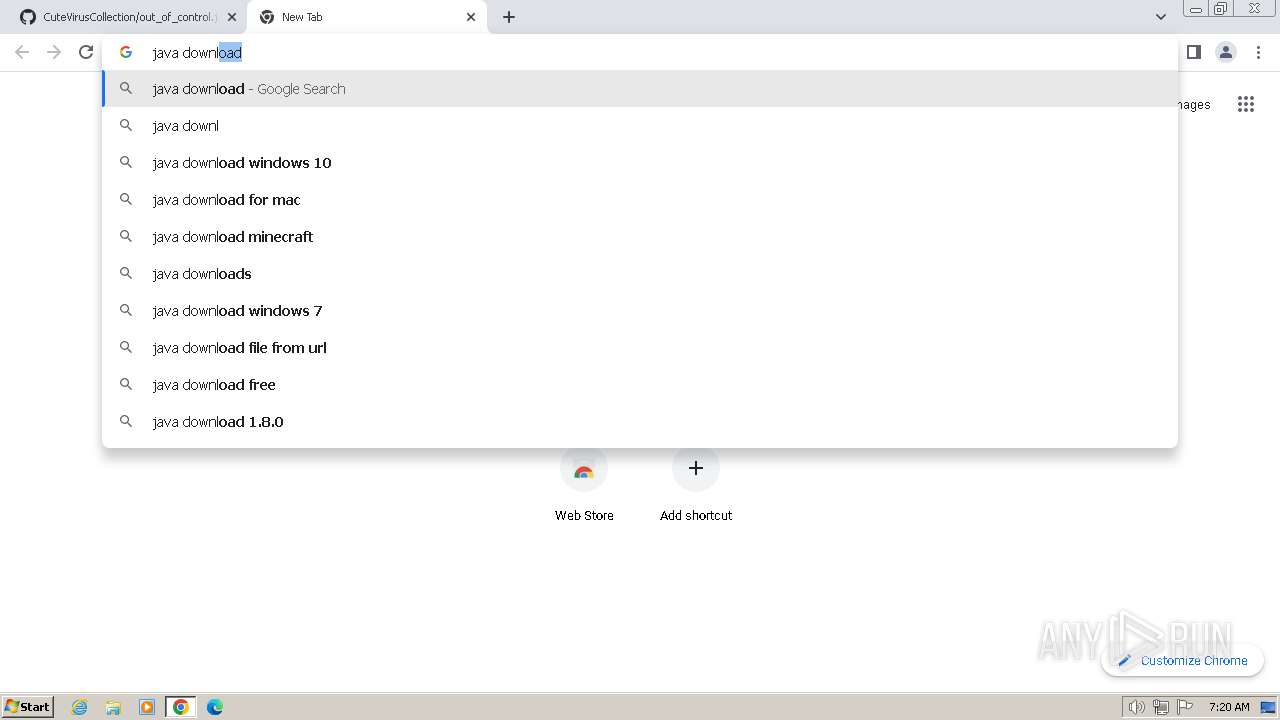
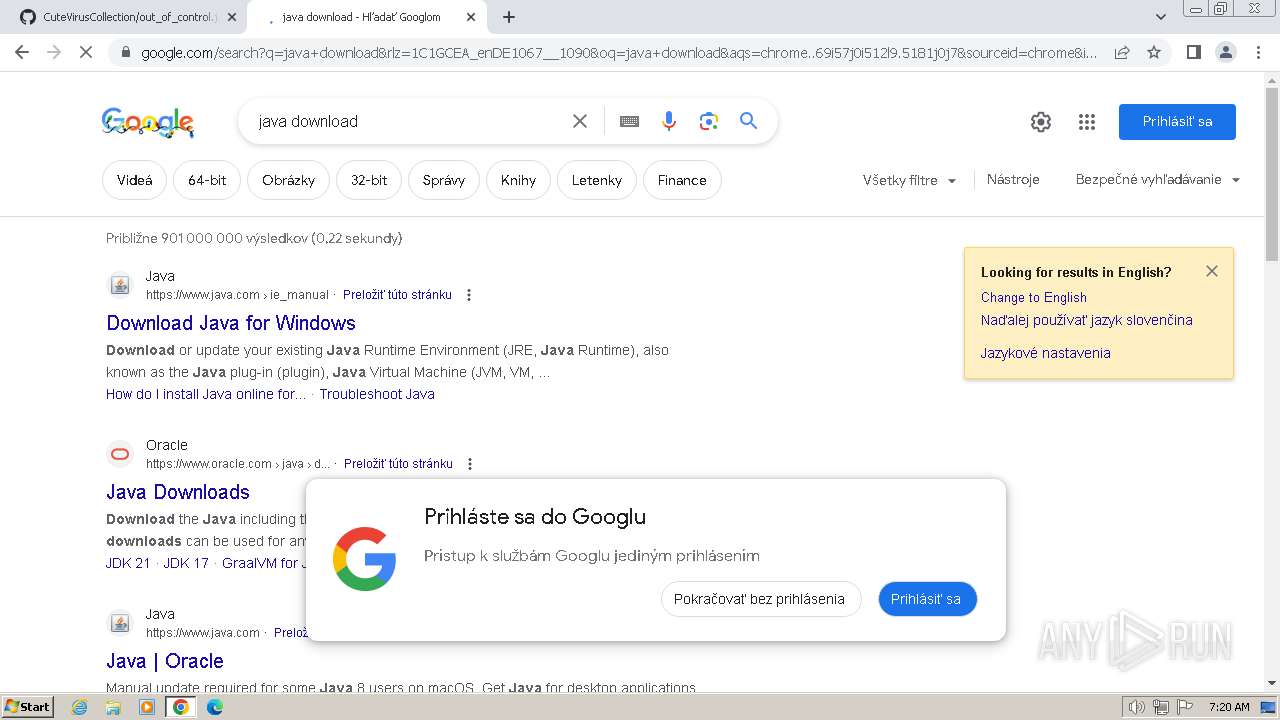
google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |