| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/716b9b01-f3b6-4708-b982-469d039bef70 |
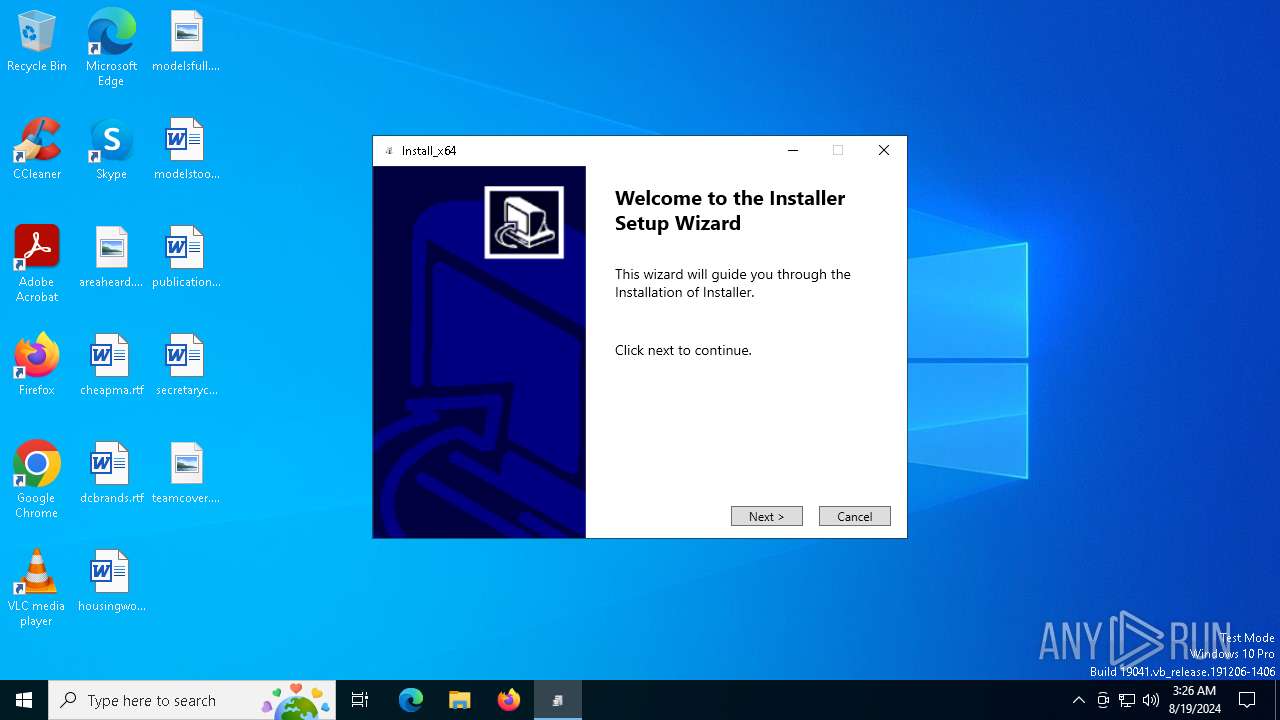
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | August 19, 2024, 03:23:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 7048)
- BitLockerToGo.exe (PID: 6736)
- powershell.exe (PID: 6216)
GOINJECTOR has been detected (YARA)
- 2.exe (PID: 7808)
- 3.exe (PID: 6676)
Stealers network behavior
- BitLockerToGo.exe (PID: 7048)
- BitLockerToGo.exe (PID: 6736)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 7048)
STEALC has been detected (SURICATA)
- BitLockerToGo.exe (PID: 6736)
Connects to the CnC server
- BitLockerToGo.exe (PID: 6736)
Steals credentials from Web Browsers
- BitLockerToGo.exe (PID: 6736)
Bypass execution policy to execute commands
- powershell.exe (PID: 6216)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6216)
Changes powershell execution policy (Bypass)
- BitLockerToGo.exe (PID: 252)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6216)
SUSPICIOUS
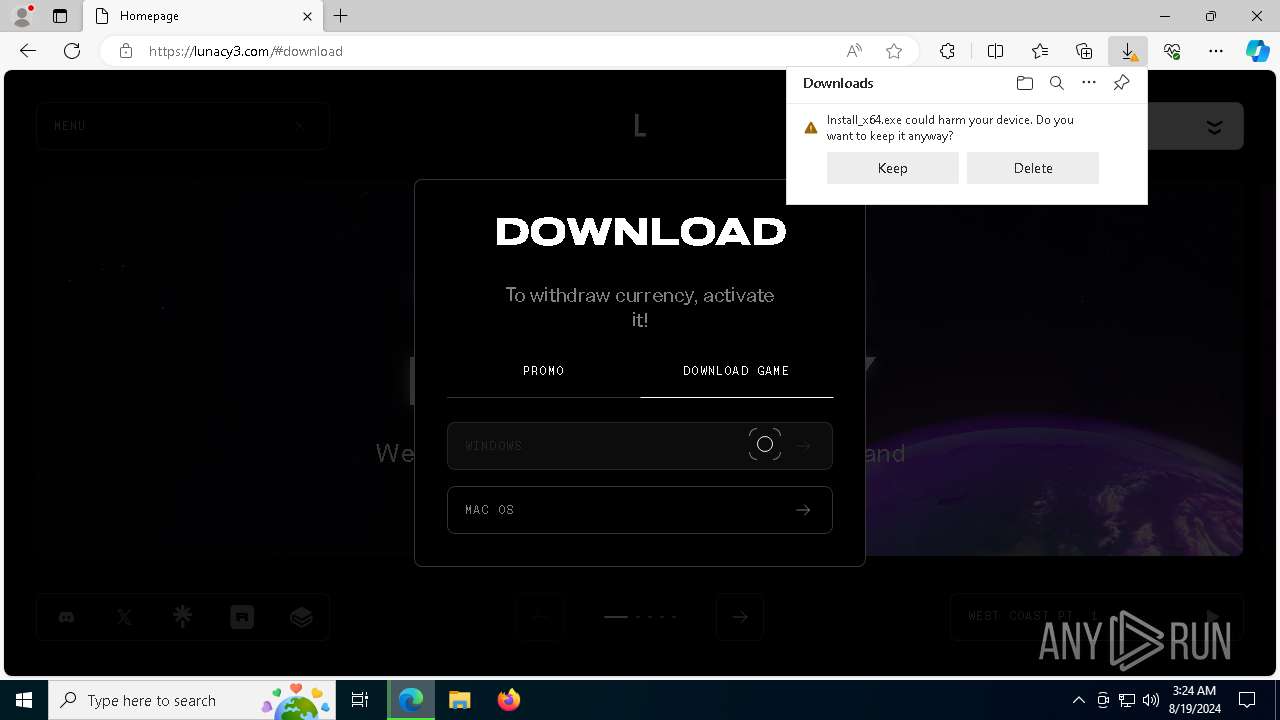
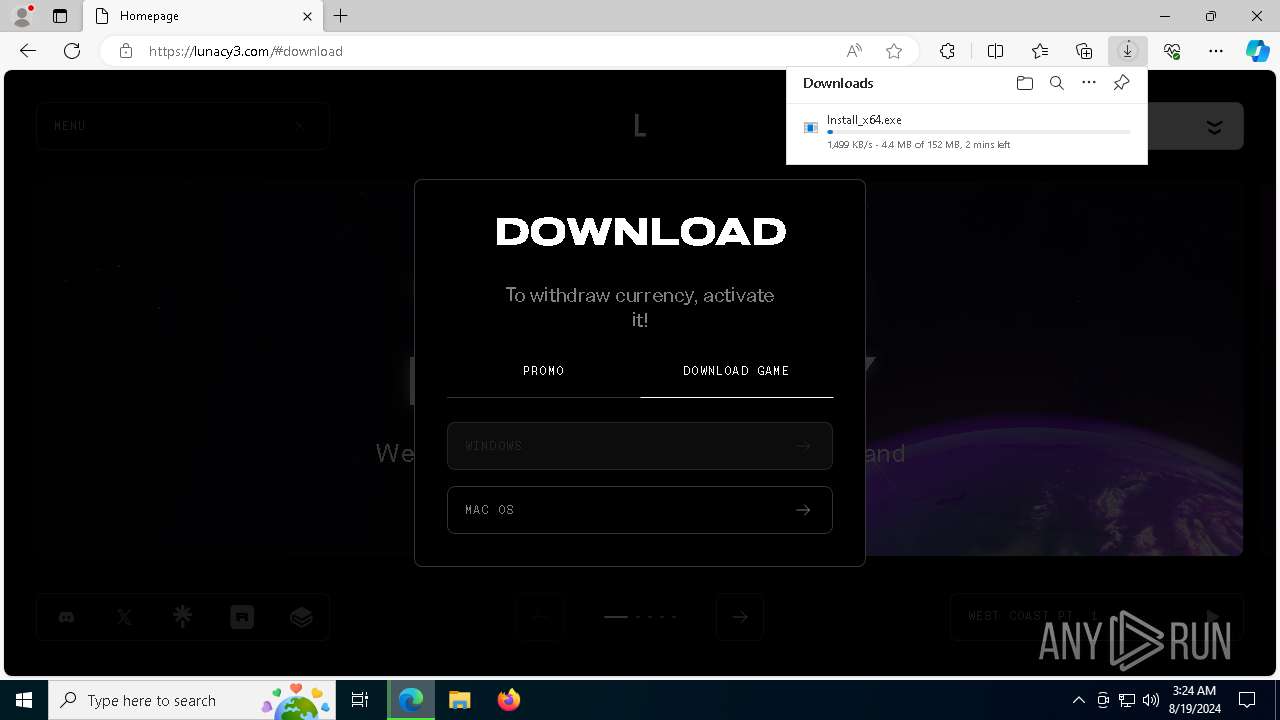
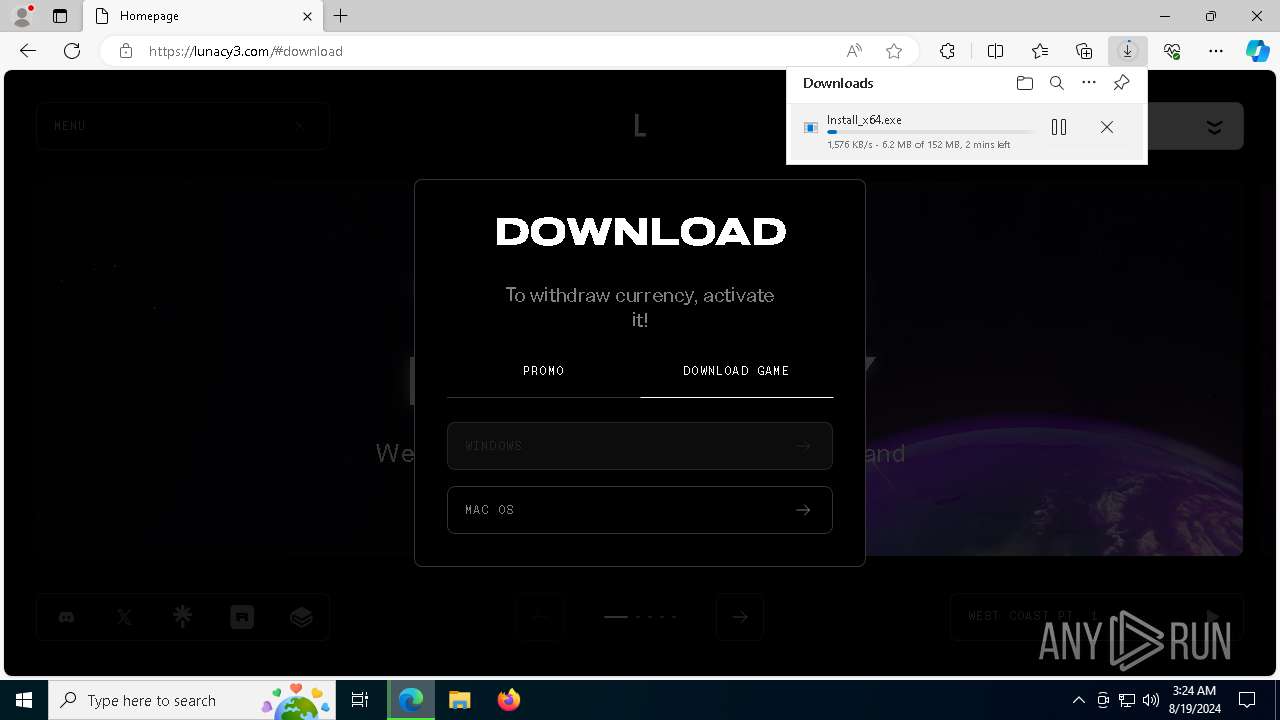
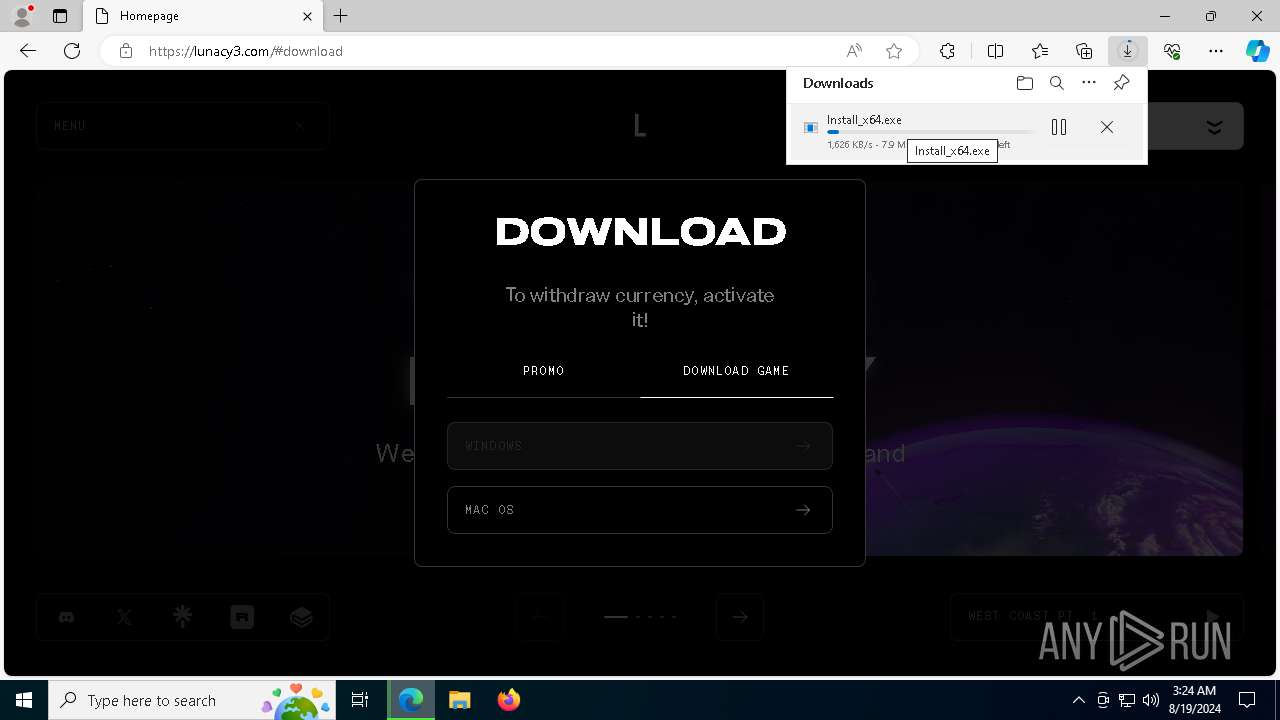
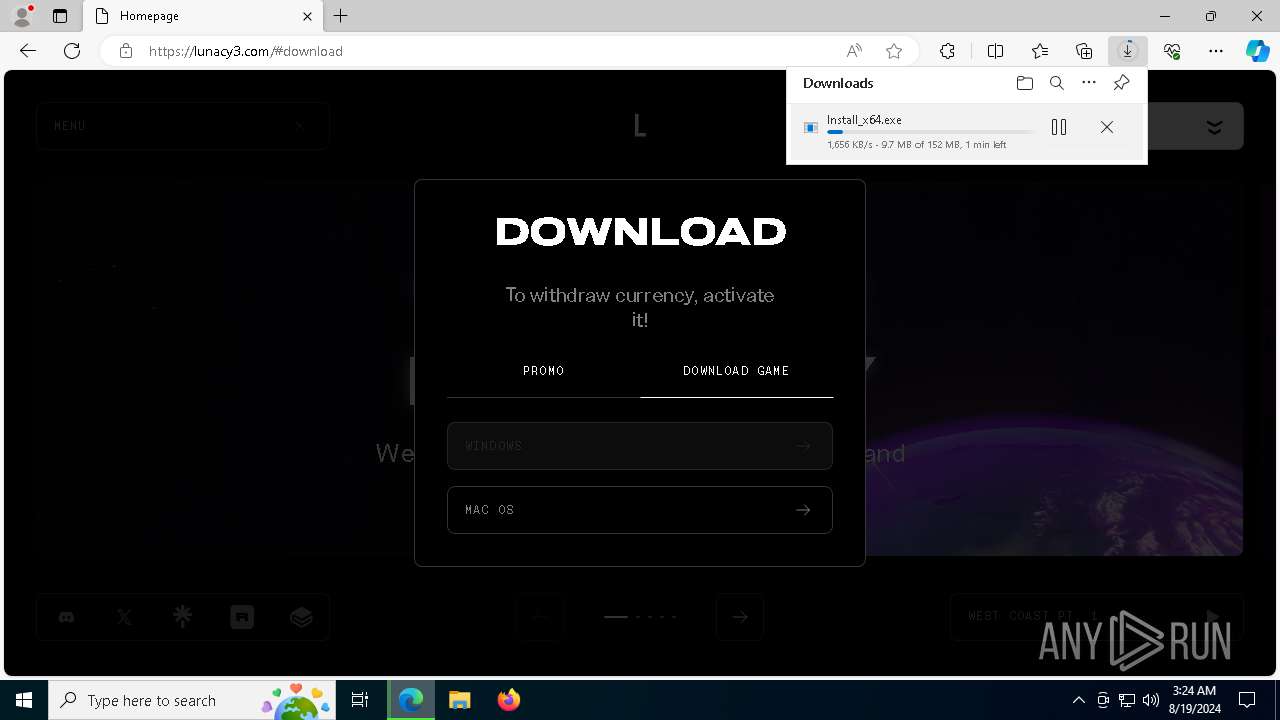
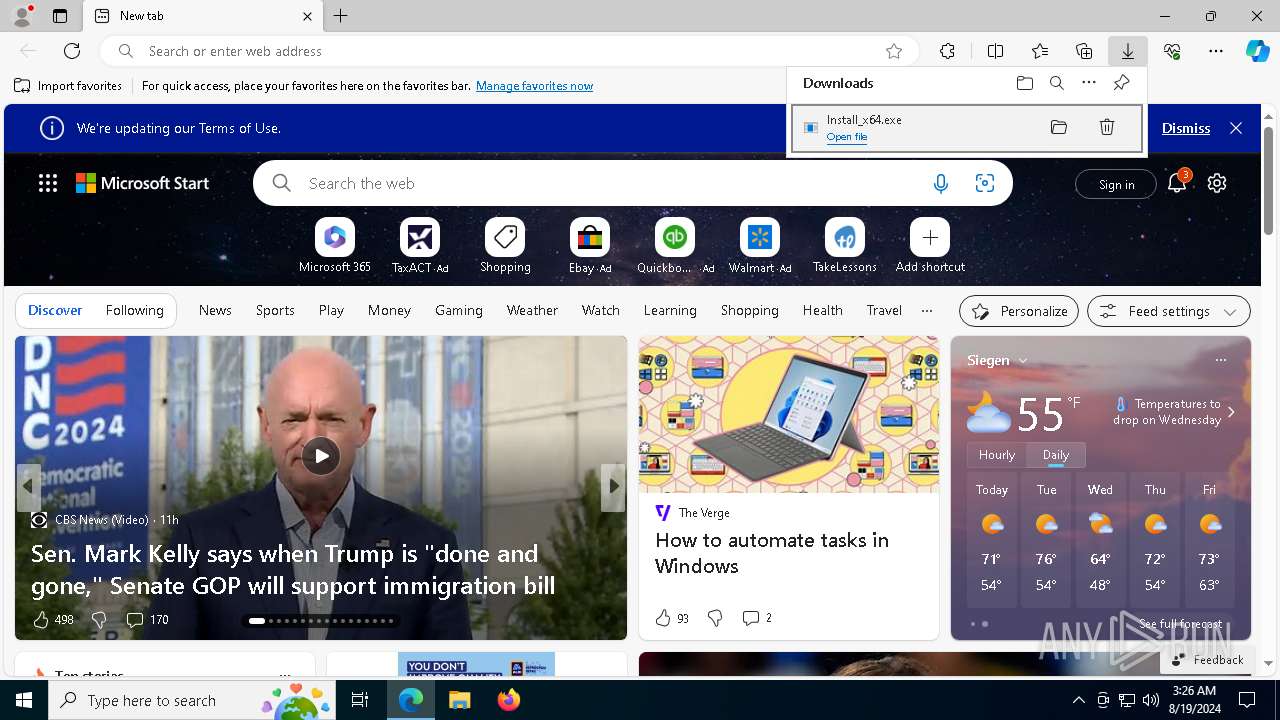
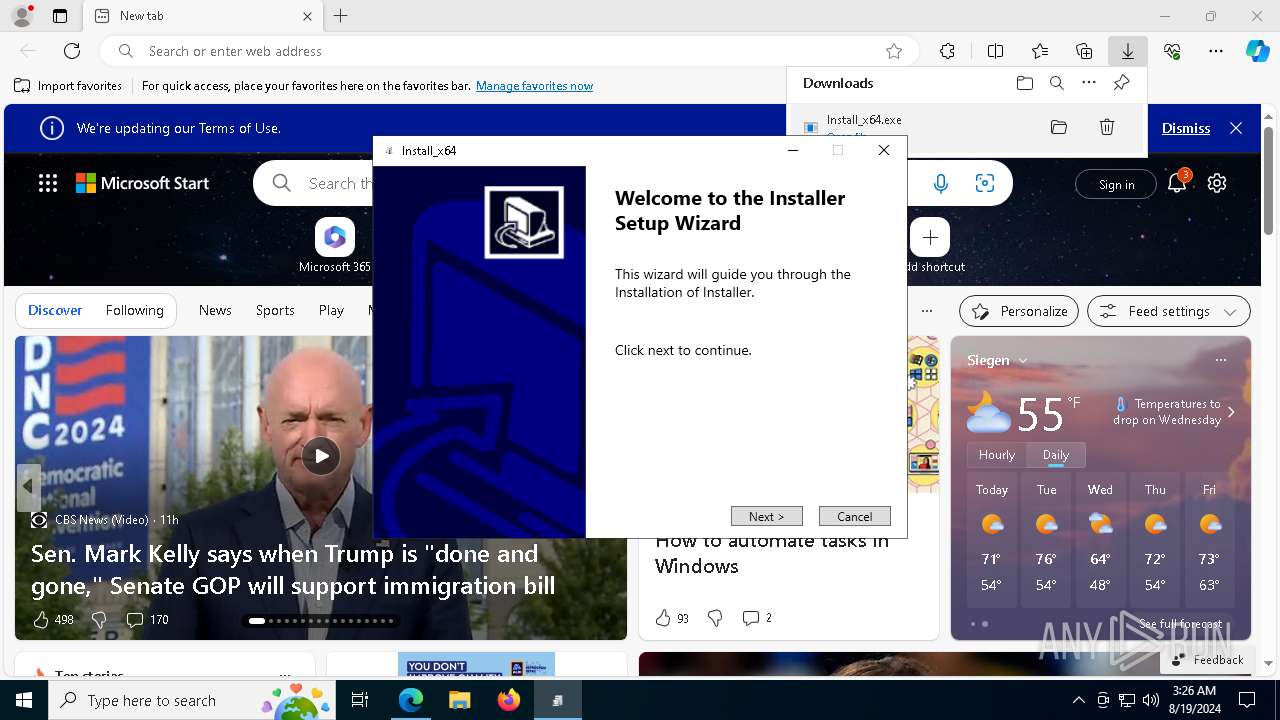
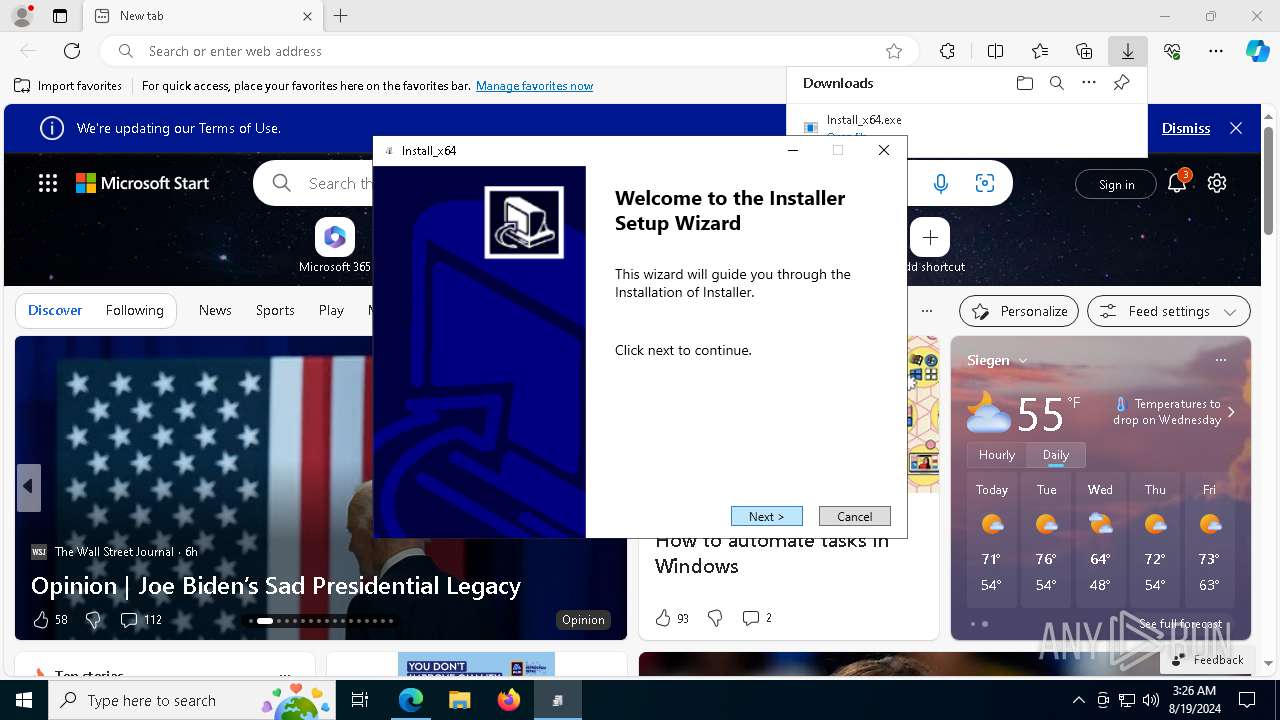
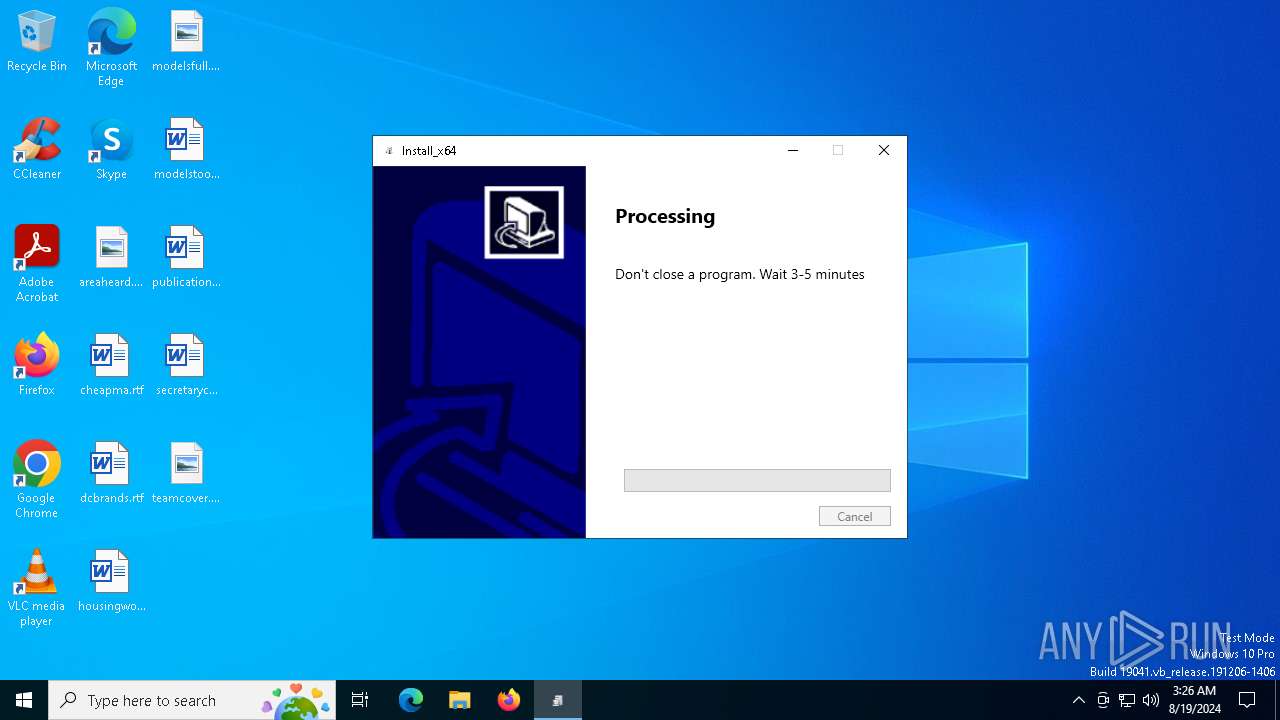
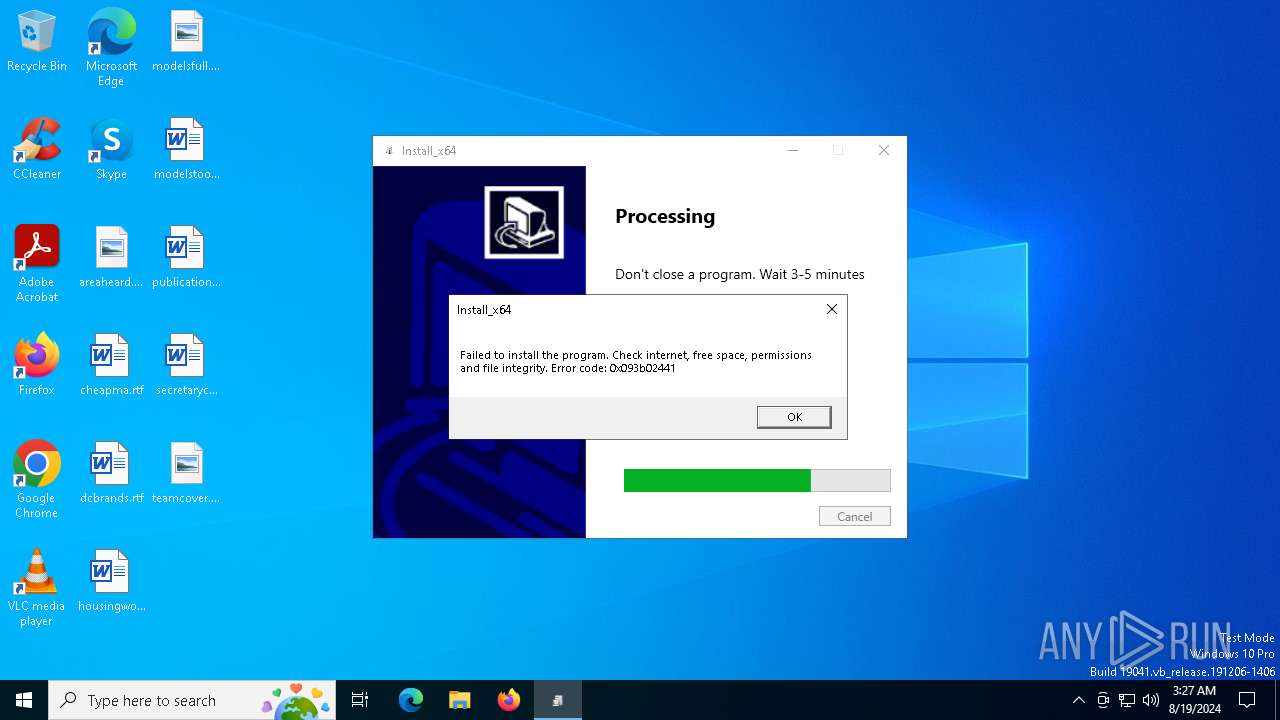
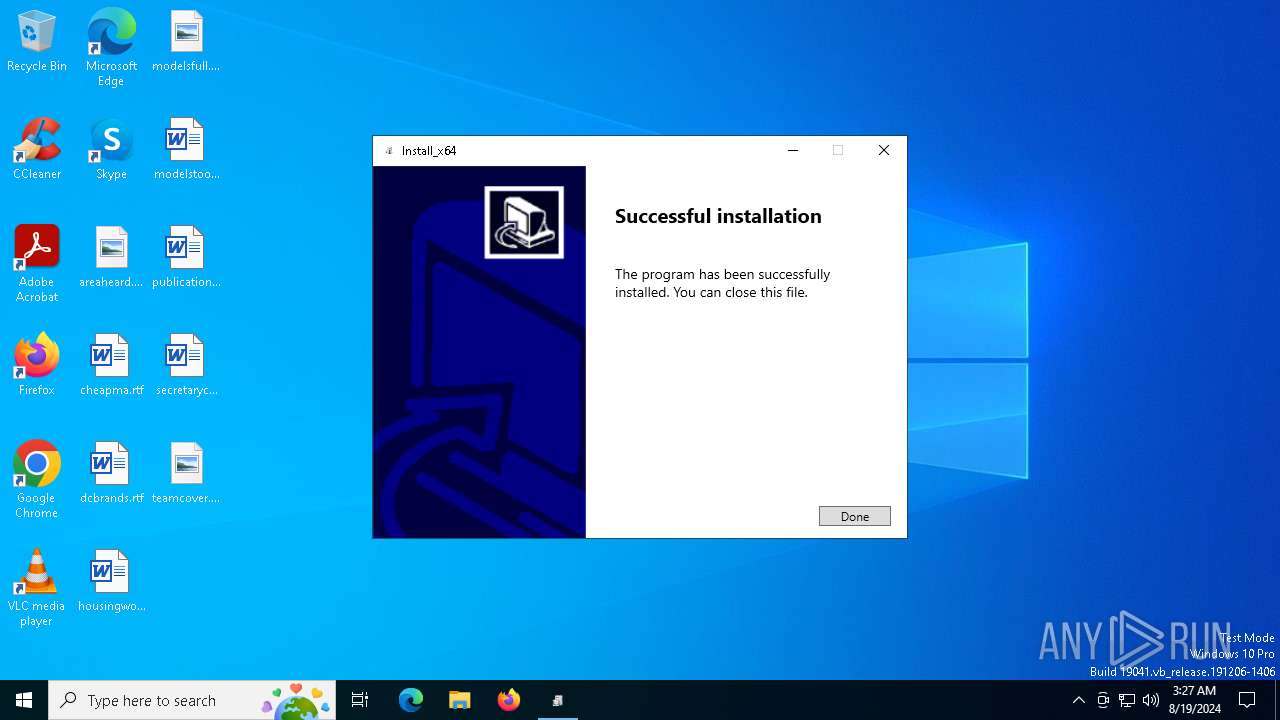
Process drops legitimate windows executable
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
The process drops C-runtime libraries
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
Reads security settings of Internet Explorer
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
Drops the executable file immediately after the start
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
Executable content was dropped or overwritten
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
Windows Defender mutex has been found
- BitLockerToGo.exe (PID: 6736)
Found regular expressions for crypto-addresses (YARA)
- 2.exe (PID: 7808)
Searches for installed software
- BitLockerToGo.exe (PID: 7048)
- BitLockerToGo.exe (PID: 6736)
There is functionality for communication over UDP network (YARA)
- 2.exe (PID: 7808)
- 3.exe (PID: 6676)
Contacting a server suspected of hosting an CnC
- BitLockerToGo.exe (PID: 6736)
Potential Corporate Privacy Violation
- BitLockerToGo.exe (PID: 6736)
Connects to the server without a host name
- BitLockerToGo.exe (PID: 6736)
Process requests binary or script from the Internet
- BitLockerToGo.exe (PID: 6736)
The process drops Mozilla's DLL files
- BitLockerToGo.exe (PID: 6736)
Starts CMD.EXE for commands execution
- BitLockerToGo.exe (PID: 252)
Request a resource from the Internet using PowerShell's cmdlet
- BitLockerToGo.exe (PID: 252)
Starts POWERSHELL.EXE for commands execution
- BitLockerToGo.exe (PID: 252)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6216)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6216)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6216)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 6216)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6216)
Checks for external IP
- powershell.exe (PID: 6216)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 6216)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- powershell.exe (PID: 6216)
Identifying current user with WHOAMI command
- powershell.exe (PID: 6216)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 2132)
- msedge.exe (PID: 7664)
Reads the computer name
- TextInputHost.exe (PID: 1556)
- identity_helper.exe (PID: 7956)
- identity_helper.exe (PID: 1020)
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 7048)
- BitLockerToGo.exe (PID: 6736)
Checks supported languages
- TextInputHost.exe (PID: 1556)
- identity_helper.exe (PID: 7956)
- identity_helper.exe (PID: 1020)
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 7048)
- BitLockerToGo.exe (PID: 6736)
- 1.exe (PID: 6912)
- 2.exe (PID: 7808)
- 3.exe (PID: 6676)
- BitLockerToGo.exe (PID: 252)
Executable content was dropped or overwritten
- msedge.exe (PID: 2132)
Reads Environment values
- identity_helper.exe (PID: 7956)
- identity_helper.exe (PID: 1020)
- BitLockerToGo.exe (PID: 6736)
The process uses the downloaded file
- msedge.exe (PID: 7860)
- msedge.exe (PID: 2132)
Create files in a temporary directory
- Install_x64.exe (PID: 7076)
Application launched itself
- msedge.exe (PID: 2132)
- msedge.exe (PID: 7664)
Creates files in the program directory
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
Checks proxy server information
- Install_x64.exe (PID: 7076)
- BitLockerToGo.exe (PID: 6736)
- powershell.exe (PID: 6216)
Reads the software policy settings
- BitLockerToGo.exe (PID: 7048)
- Install_x64.exe (PID: 7076)
Creates files or folders in the user directory
- BitLockerToGo.exe (PID: 6736)
Reads CPU info
- BitLockerToGo.exe (PID: 6736)
Reads product name
- BitLockerToGo.exe (PID: 6736)
Disables trace logs
- powershell.exe (PID: 6216)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6216)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6216)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6216)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6216)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6216)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6216)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
93
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2384,i,18008828516361400274,15739765712065310273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 252 | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1508 --field-trial-handle=2384,i,18008828516361400274,15739765712065310273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4928 --field-trial-handle=2364,i,6021300070728620922,1022881060860506874,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5528 --field-trial-handle=2364,i,6021300070728620922,1022881060860506874,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1580 --field-trial-handle=2364,i,6021300070728620922,1022881060860506874,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1860 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5900 --field-trial-handle=2384,i,18008828516361400274,15739765712065310273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4368 --field-trial-handle=2384,i,18008828516361400274,15739765712065310273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2128 | "C:\WINDOWS\system32\whoami.exe" /groups /fo csv | C:\Windows\SysWOW64\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 652
Read events
34 209
Write events
427
Delete events
16
Modification events
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
42
Suspicious files
704
Text files
259
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe56a7.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe56e6.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe56f5.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe56f5.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe5724.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
77
TCP/UDP connections
137
DNS requests
168
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6828 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6436 | msedge.exe | GET | 304 | 23.32.238.51:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
6436 | msedge.exe | GET | 304 | 23.192.153.142:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
2424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3044 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7216 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724413090&P2=404&P3=2&P4=JD4JmixgSUSj2iyGuSIIesHfqhss23R2jQlV6d2kHWhUFi2CtOANVgn%2b4HNw4edON1y21jLdbxdDTJw0HELfLw%3d%3d | unknown | — | — | whitelisted |
6436 | msedge.exe | GET | 304 | 23.192.153.142:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724413090&P2=404&P3=2&P4=JD4JmixgSUSj2iyGuSIIesHfqhss23R2jQlV6d2kHWhUFi2CtOANVgn%2b4HNw4edON1y21jLdbxdDTJw0HELfLw%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724413090&P2=404&P3=2&P4=JD4JmixgSUSj2iyGuSIIesHfqhss23R2jQlV6d2kHWhUFi2CtOANVgn%2b4HNw4edON1y21jLdbxdDTJw0HELfLw%3d%3d | unknown | — | — | whitelisted |
7216 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724413090&P2=404&P3=2&P4=JD4JmixgSUSj2iyGuSIIesHfqhss23R2jQlV6d2kHWhUFi2CtOANVgn%2b4HNw4edON1y21jLdbxdDTJw0HELfLw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3972 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4016 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6436 | msedge.exe | 216.58.206.78:443 | google.com | — | — | whitelisted |
2132 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6436 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6436 | msedge.exe | 216.58.206.78:80 | google.com | GOOGLE | US | whitelisted |
6436 | msedge.exe | 13.107.246.67:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6436 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6436 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6436 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6436 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6436 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7048 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
6736 | BitLockerToGo.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
6736 | BitLockerToGo.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Stealc HTTP POST Request |
2 ETPRO signatures available at the full report