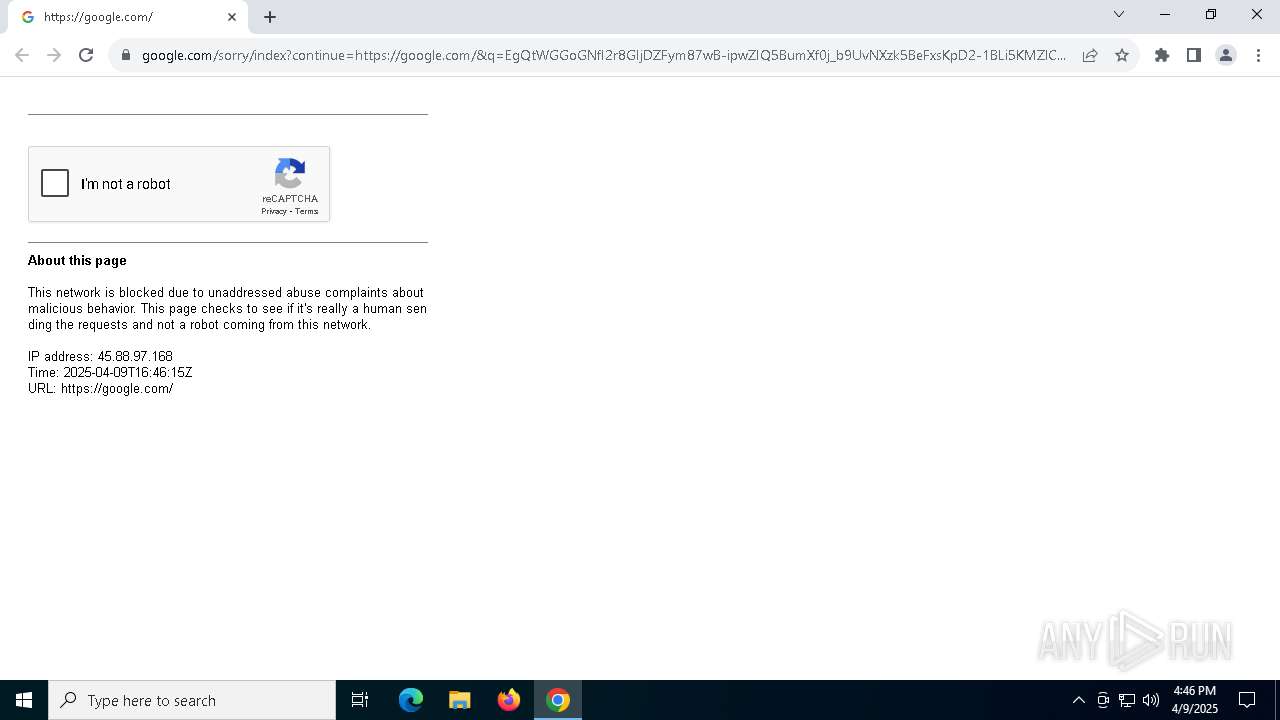
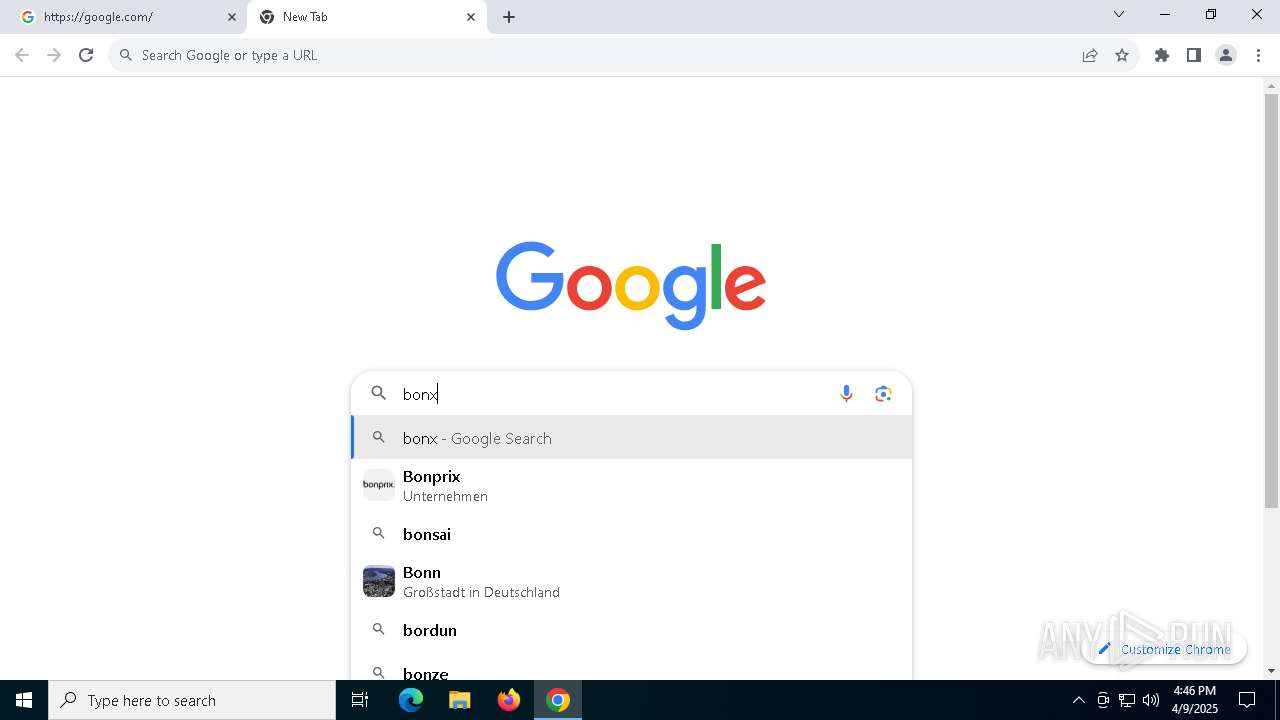
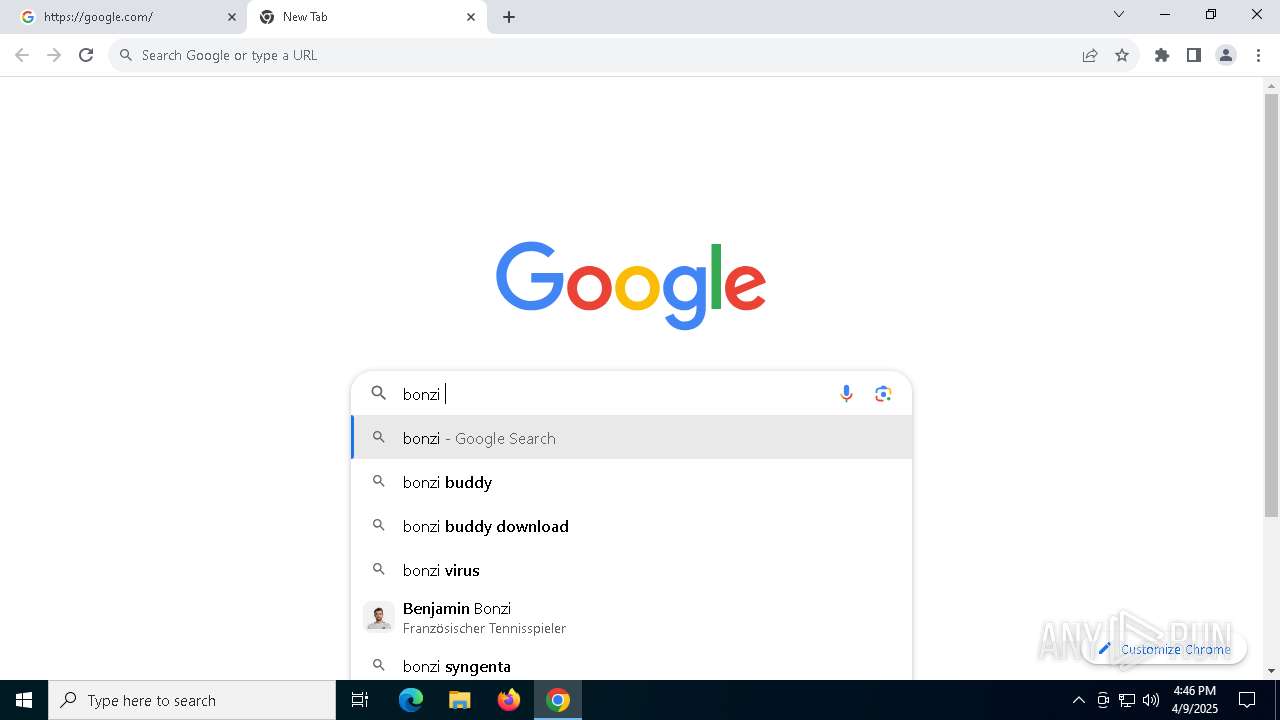
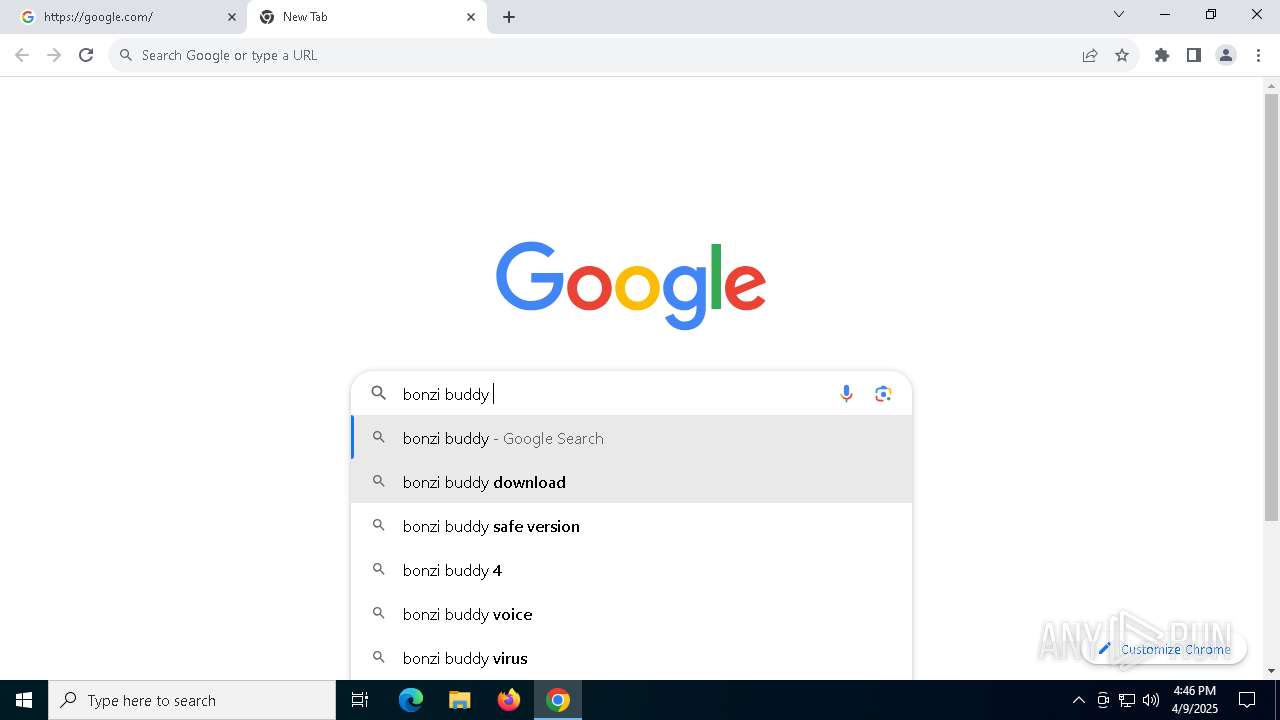
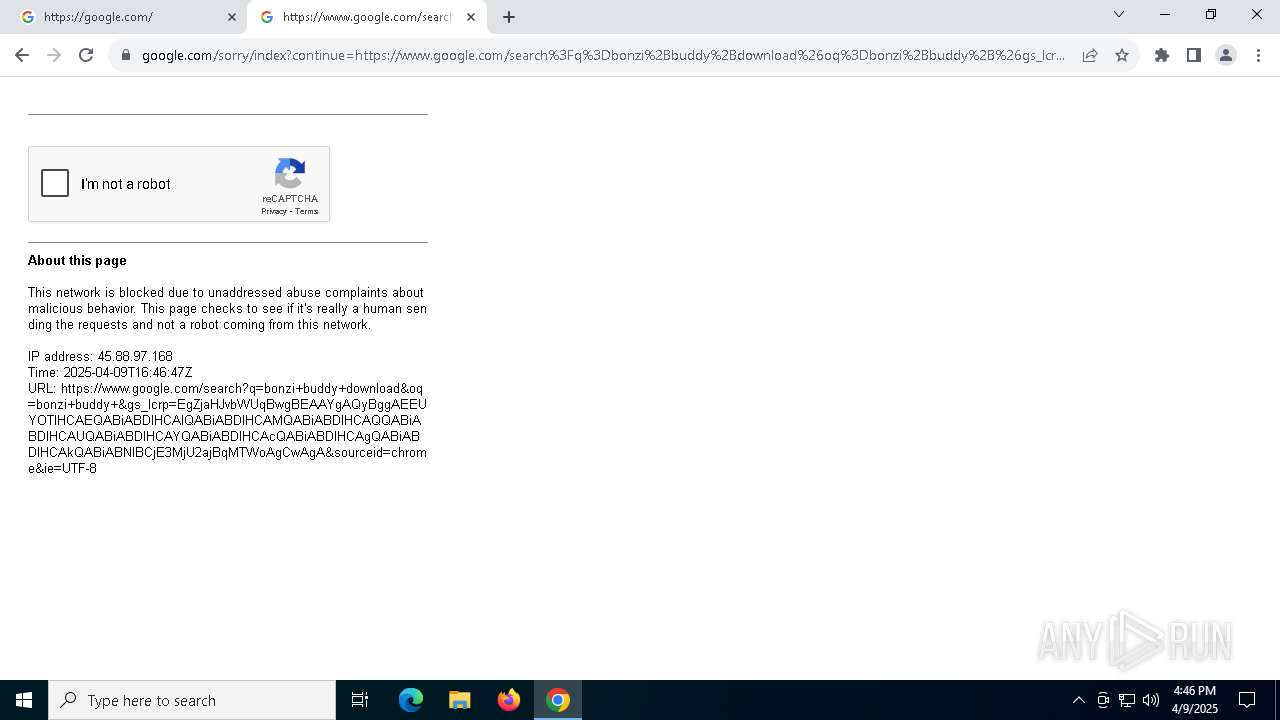
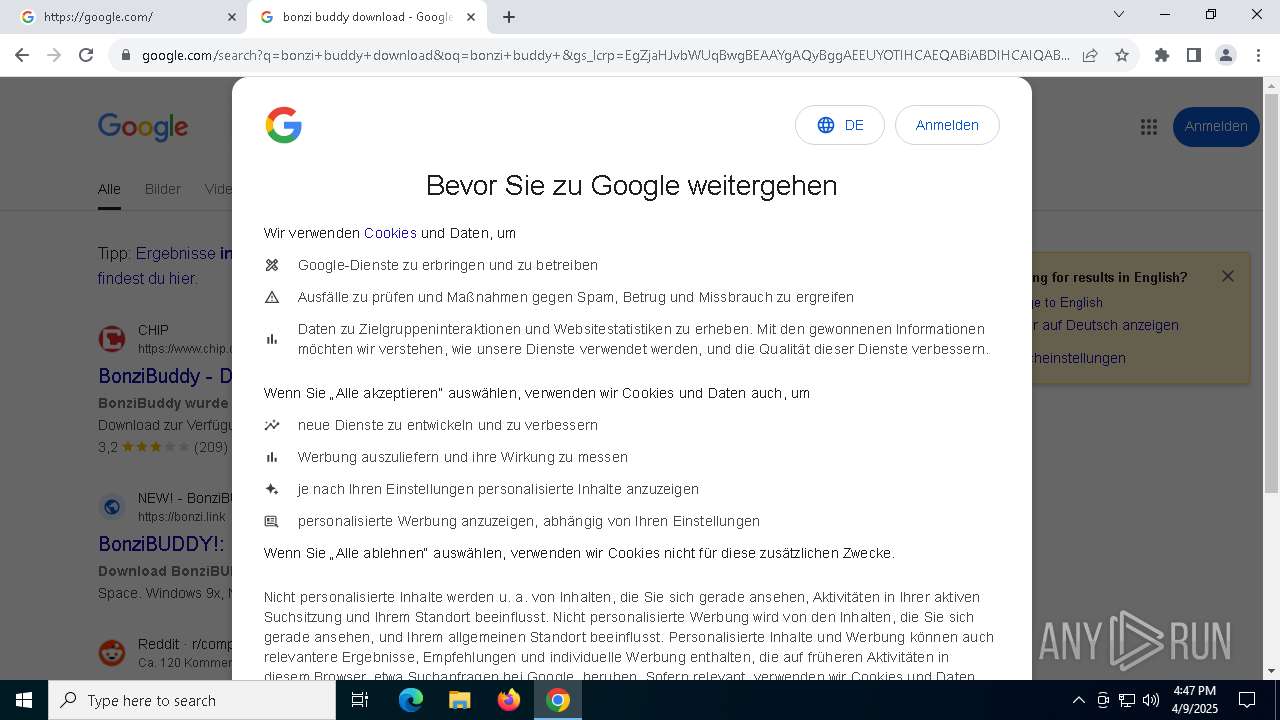
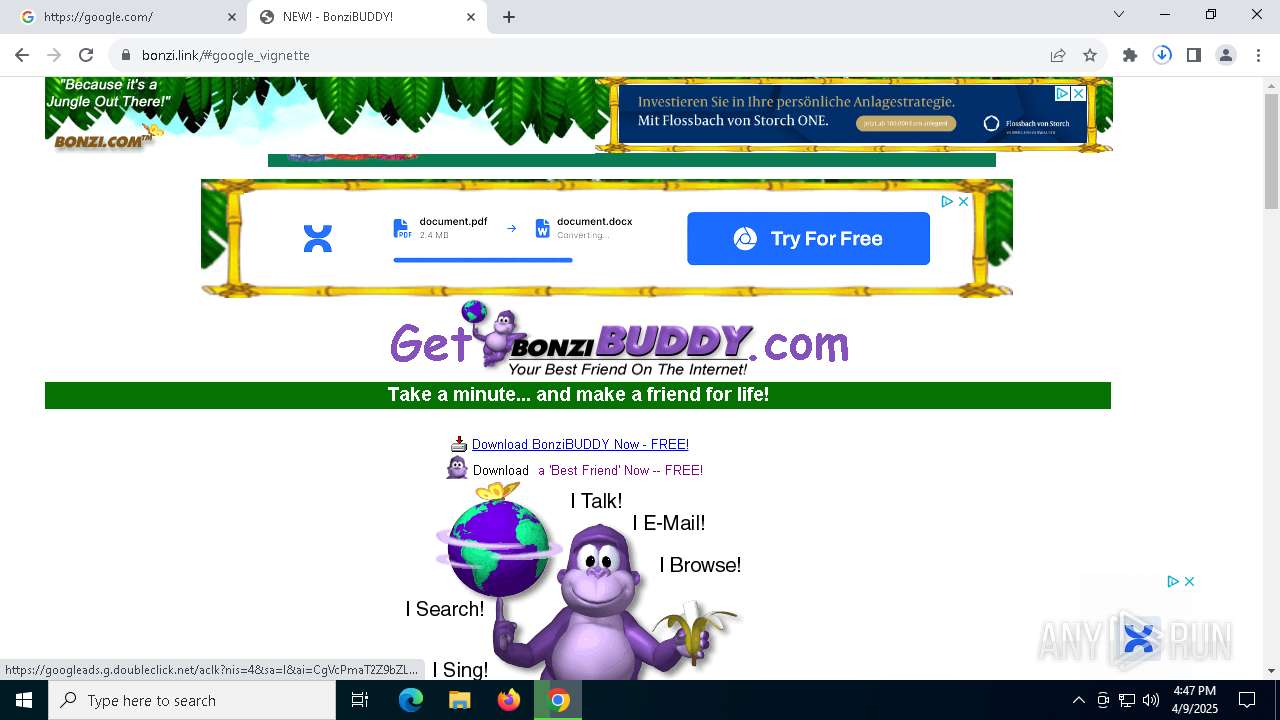
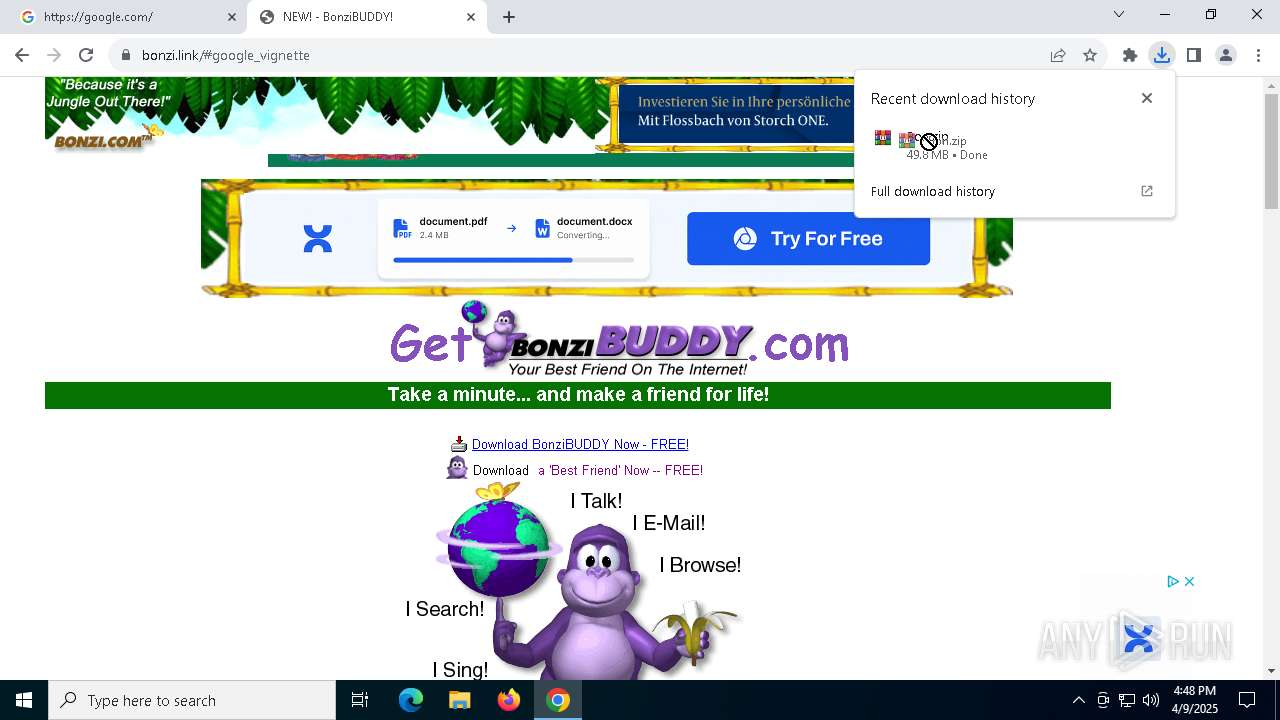
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/6fbefbfd-b7e3-4950-a59c-99c84199843d |
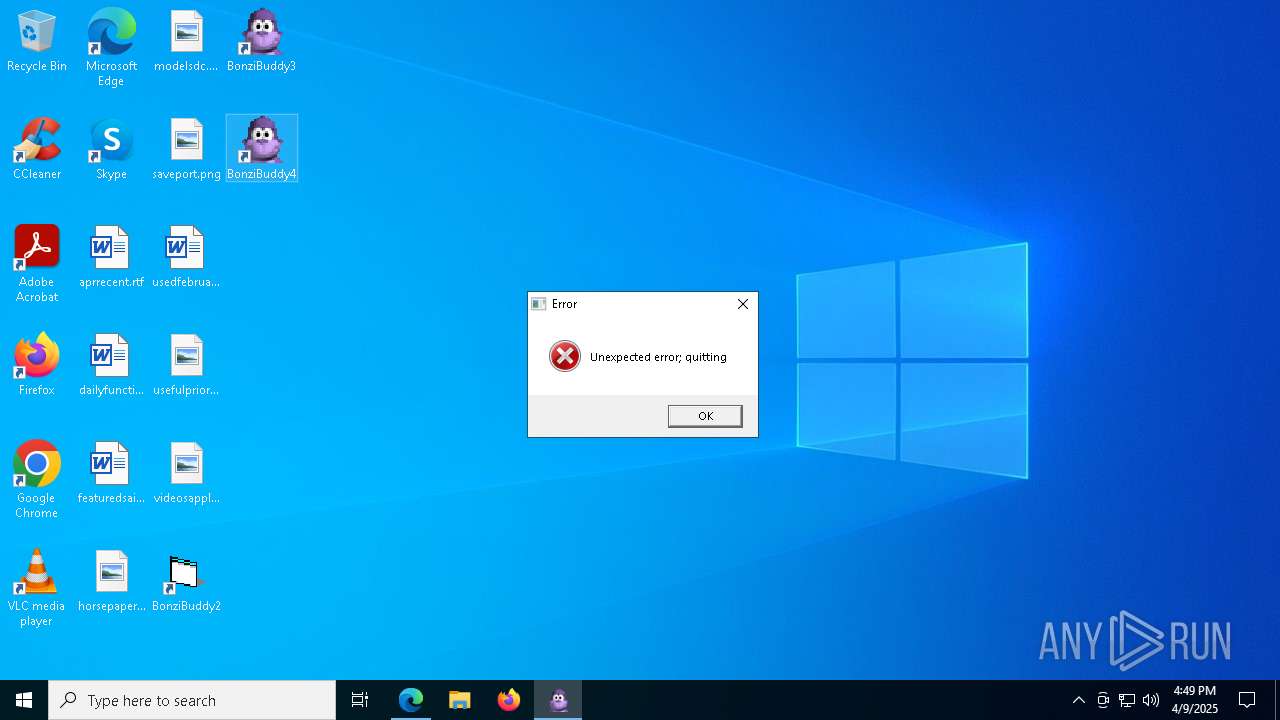
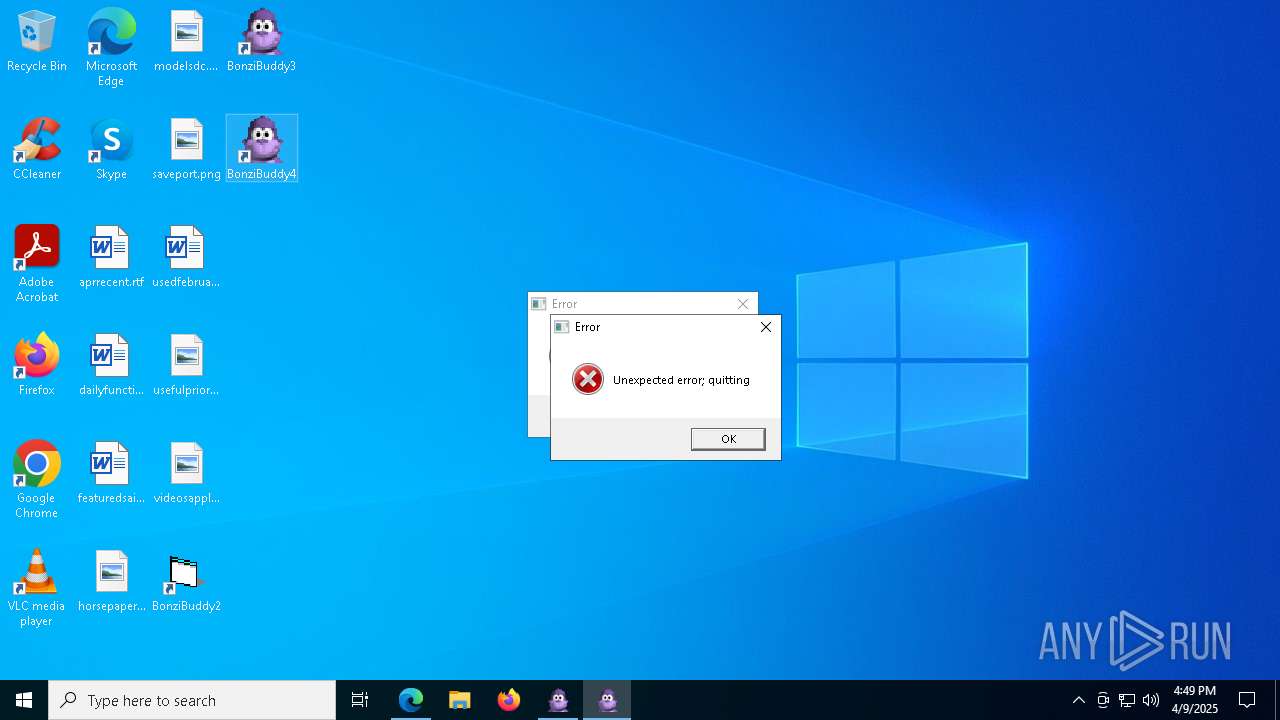
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2025, 16:46:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
Executing a file with an untrusted certificate
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
Changes the autorun value in the registry
- tv_enua.exe (PID: 2392)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 904)
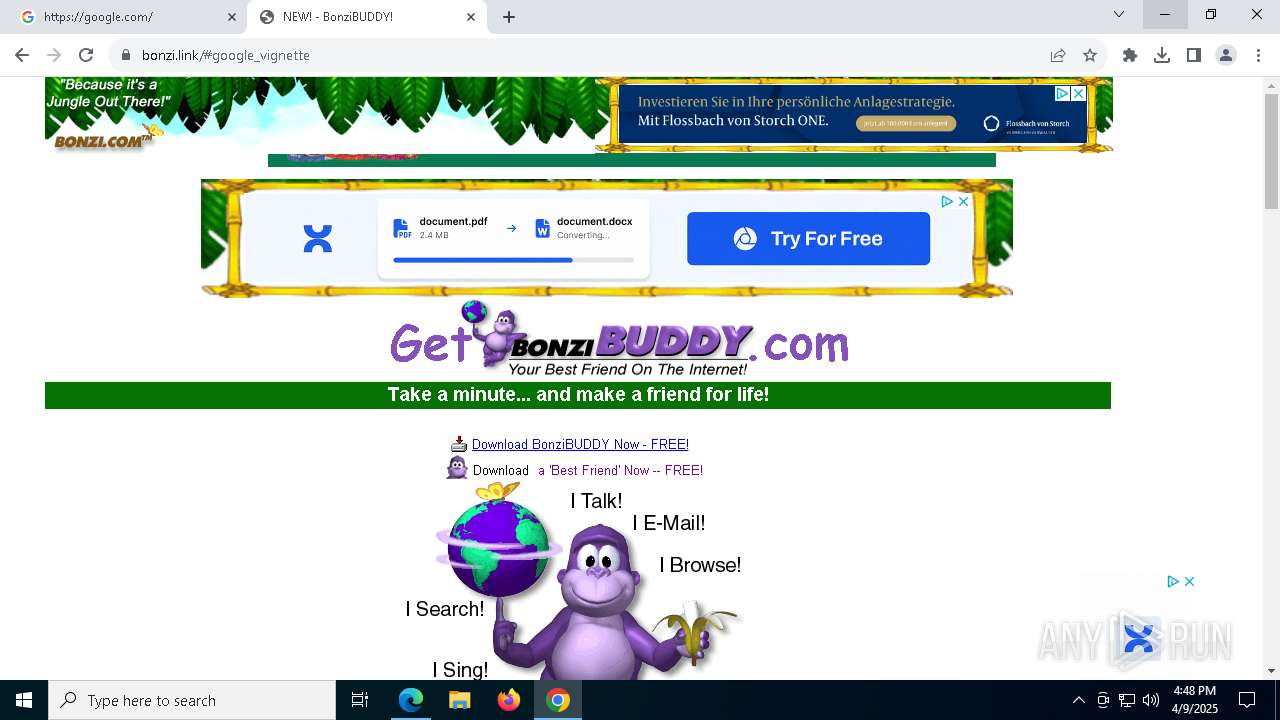
- BonziBuddy432.exe (PID: 4056)
- WinRAR.exe (PID: 1240)
- BonziBuddy432.exe (PID: 7548)
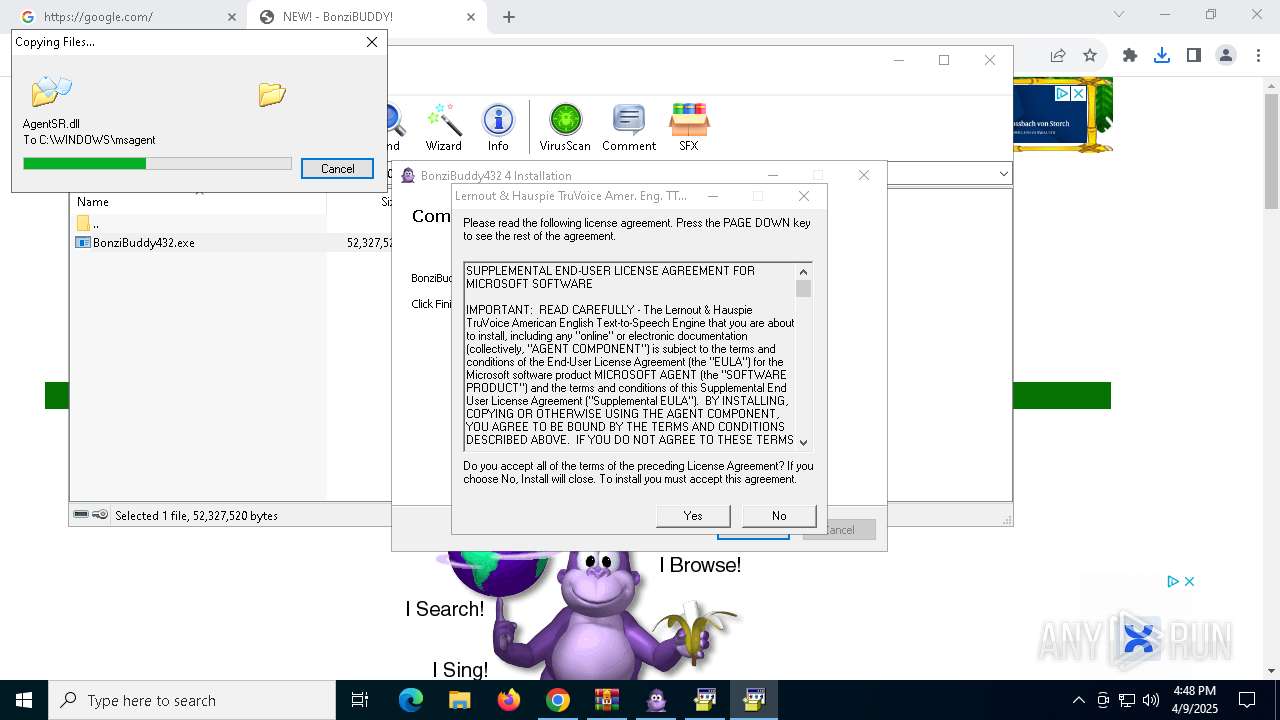
Process drops legitimate windows executable
- BonziBuddy432.exe (PID: 4056)
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
- BonziBuddy432.exe (PID: 7548)
Executable content was dropped or overwritten
- BonziBuddy432.exe (PID: 4056)
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
- BonziBuddy432.exe (PID: 7548)
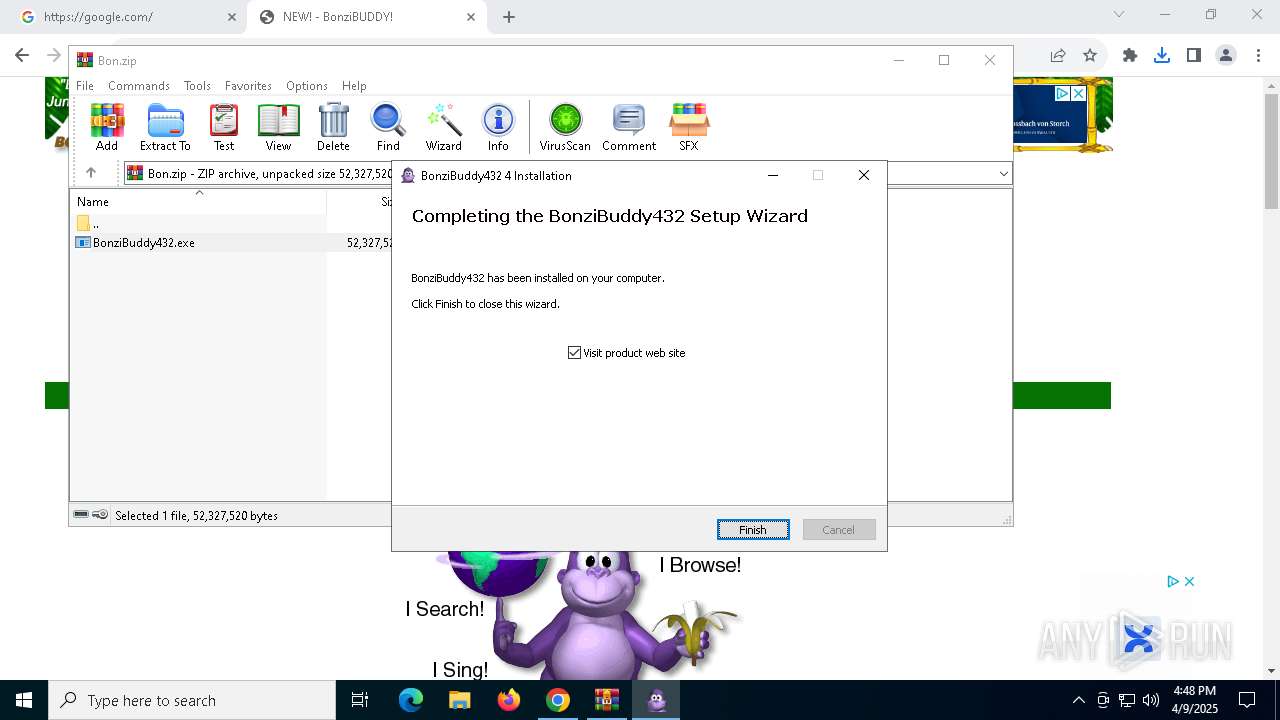
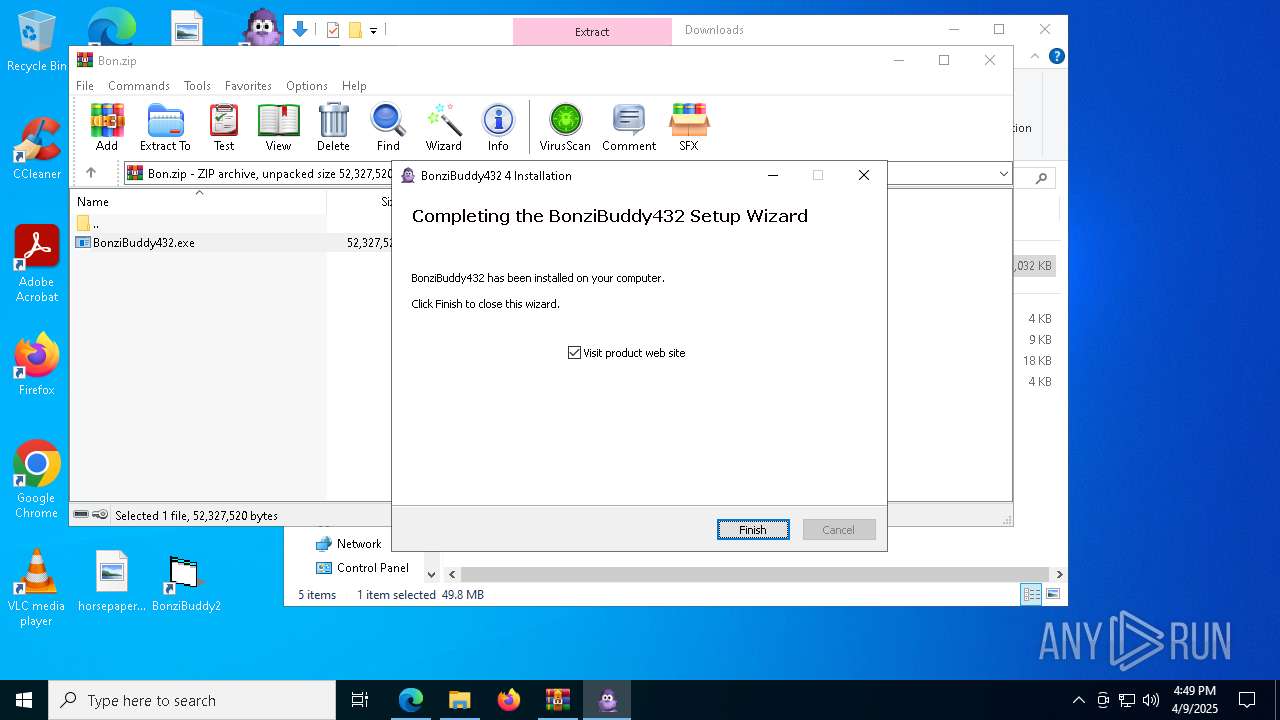
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 4056)
- tv_enua.exe (PID: 2392)
- BonziBuddy432.exe (PID: 7548)
There is functionality for taking screenshot (YARA)
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
Creates/Modifies COM task schedule object
- BonziBuddy432.exe (PID: 4056)
- regsvr32.exe (PID: 5952)
- regsvr32.exe (PID: 3028)
- regsvr32.exe (PID: 1660)
- regsvr32.exe (PID: 6072)
- regsvr32.exe (PID: 7896)
- regsvr32.exe (PID: 4224)
- regsvr32.exe (PID: 7228)
- regsvr32.exe (PID: 8040)
- regsvr32.exe (PID: 2148)
- BonziBuddy432.exe (PID: 7548)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
Executing commands from a ".bat" file
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 4108)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 4108)
INFO
Reads the software policy settings
- slui.exe (PID: 7668)
- slui.exe (PID: 4380)
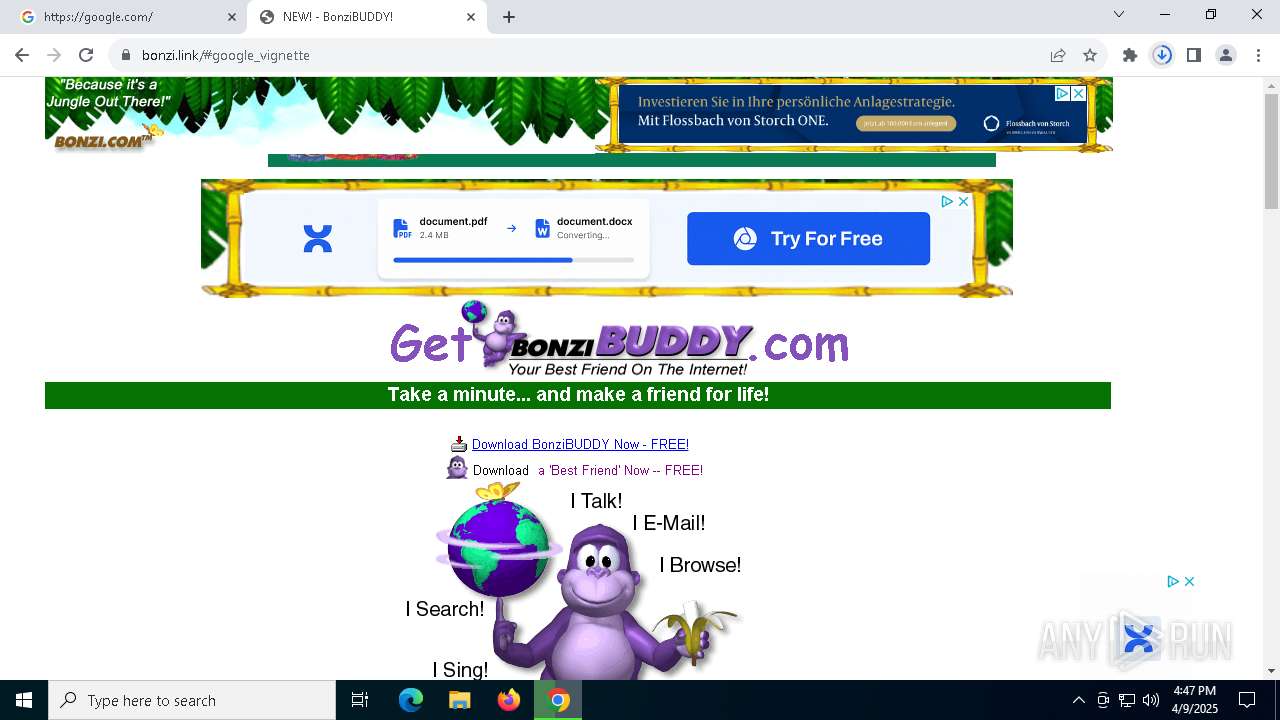
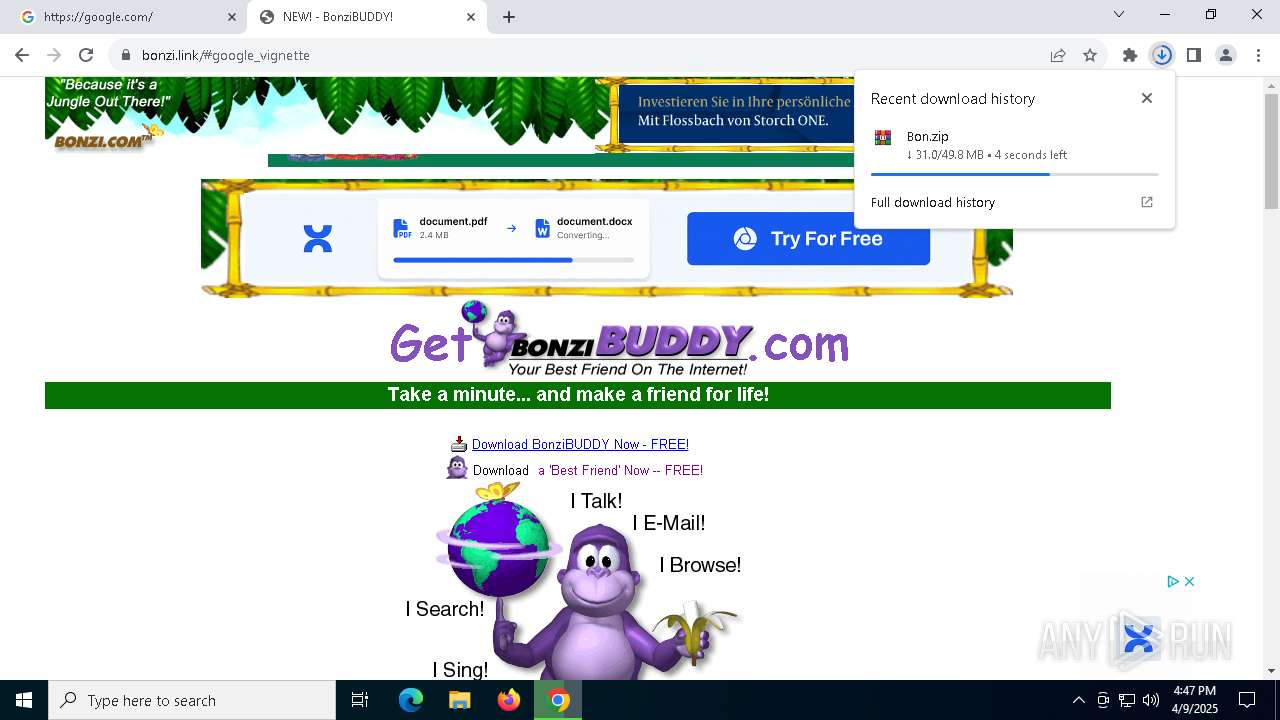
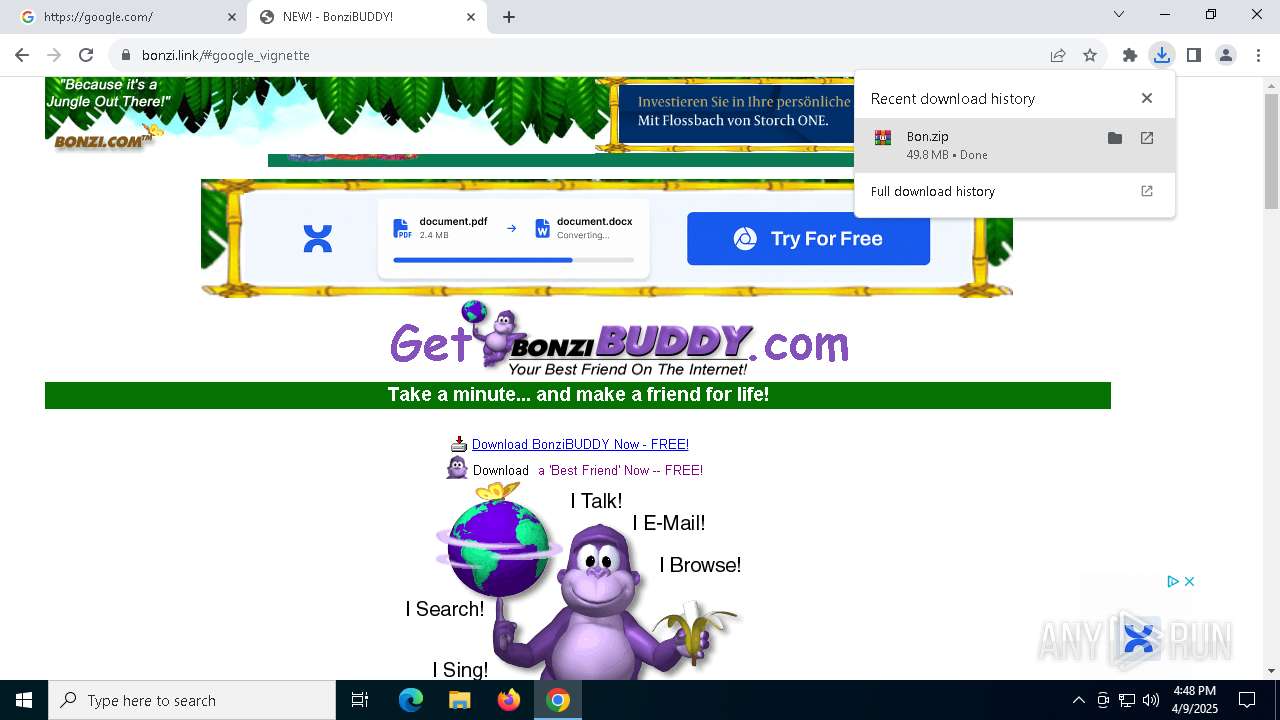
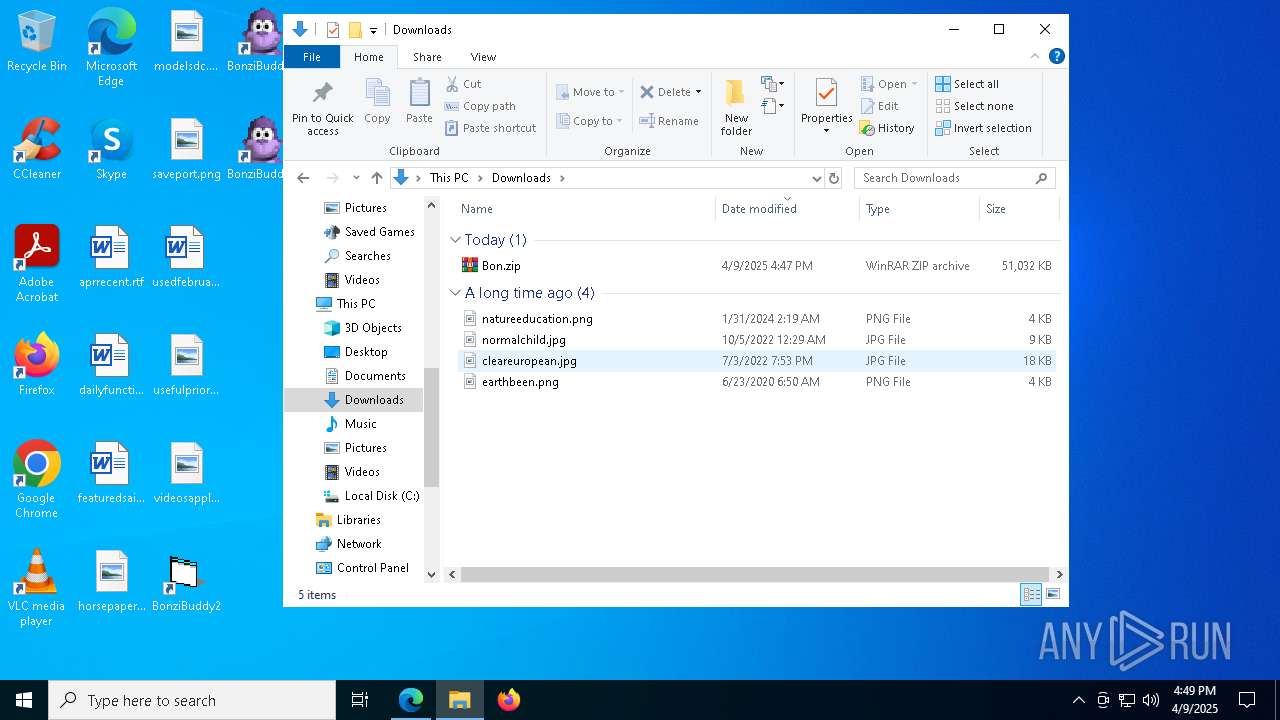
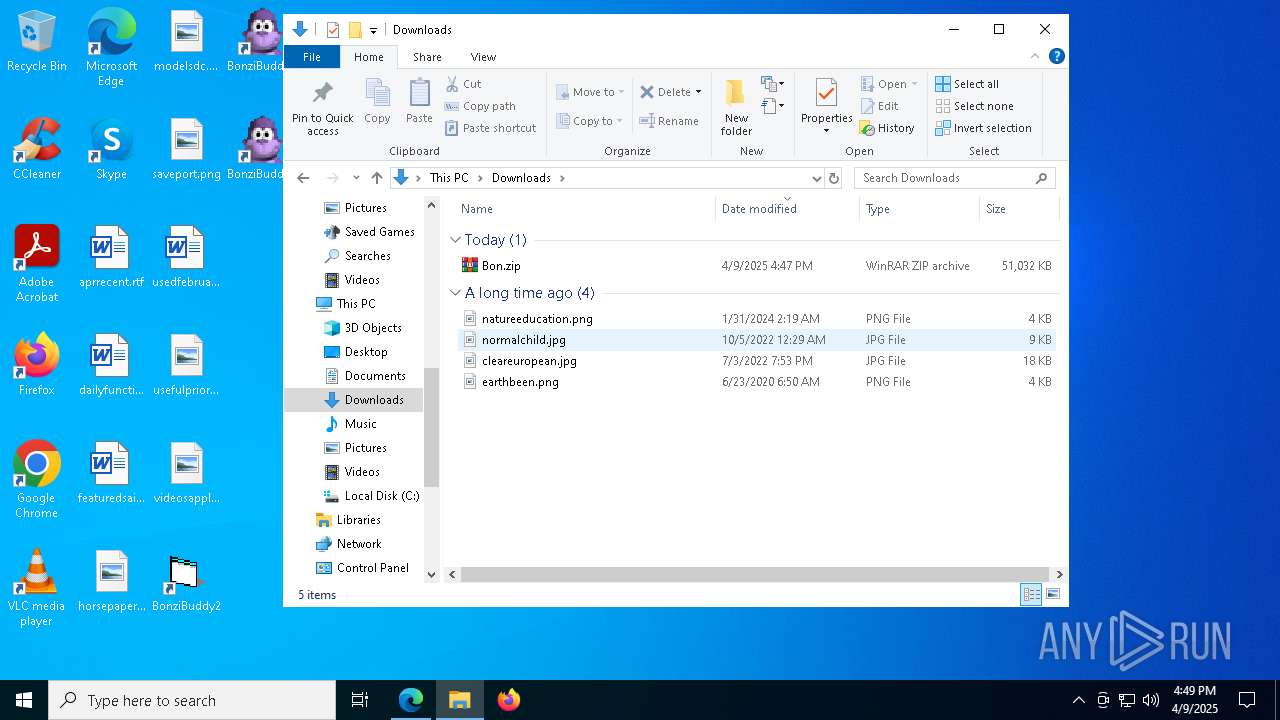
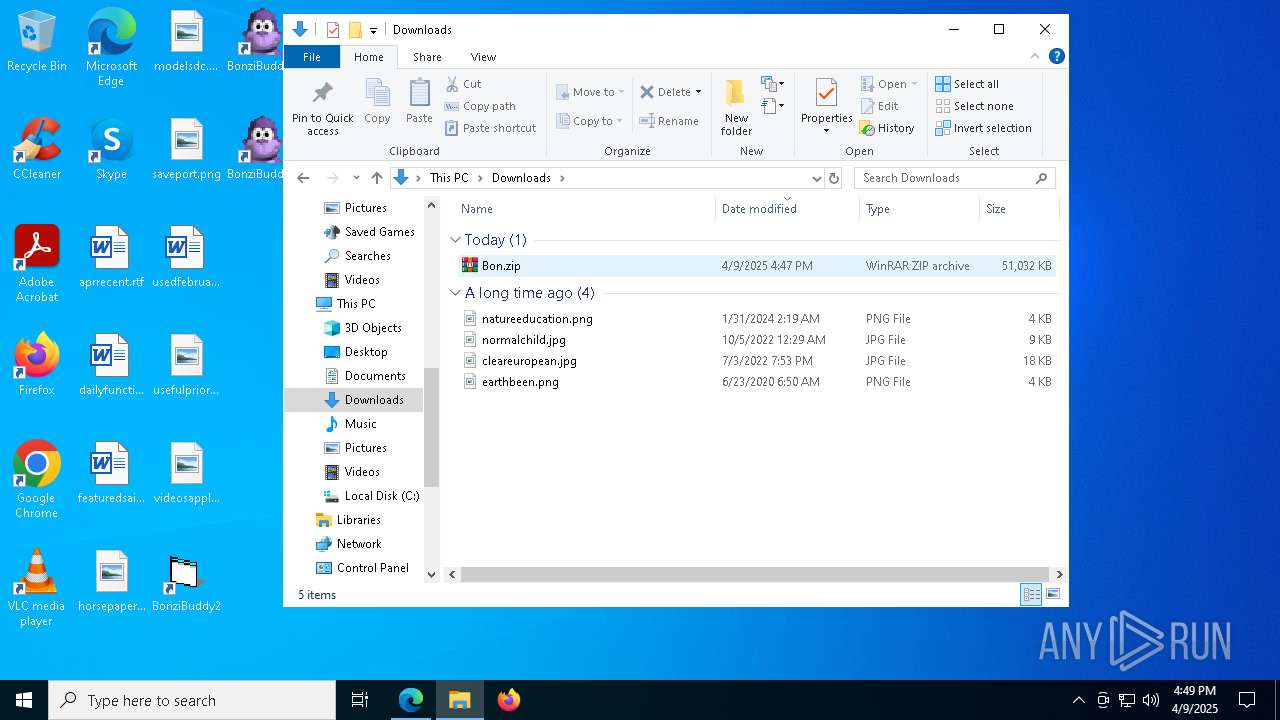
Autorun file from Downloads
- chrome.exe (PID: 8008)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6404)
Checks proxy server information
- slui.exe (PID: 4380)
Executable content was dropped or overwritten
- chrome.exe (PID: 5136)
The sample compiled with english language support
- chrome.exe (PID: 5136)
- BonziBuddy432.exe (PID: 4056)
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
- BonziBuddy432.exe (PID: 7548)
Checks supported languages
- BonziBuddy432.exe (PID: 4056)
- tv_enua.exe (PID: 2392)
- MSAGENT.EXE (PID: 5508)
- AgentSvr.exe (PID: 5812)
- identity_helper.exe (PID: 8068)
- BonziBDY_4.EXE (PID: 7636)
- BonziBDY_4.EXE (PID: 3828)
- BonziBDY_35.EXE (PID: 6824)
- BonziBuddy432.exe (PID: 7548)
- default-browser-agent.exe (PID: 4108)
- BonziBuddy432.exe (PID: 3100)
Reads the computer name
- BonziBuddy432.exe (PID: 4056)
- tv_enua.exe (PID: 2392)
- MSAGENT.EXE (PID: 5508)
- AgentSvr.exe (PID: 5812)
- BonziBDY_35.EXE (PID: 6824)
- BonziBDY_4.EXE (PID: 3828)
- BonziBuddy432.exe (PID: 7548)
- identity_helper.exe (PID: 8068)
- BonziBuddy432.exe (PID: 3100)
- BonziBDY_4.EXE (PID: 7636)
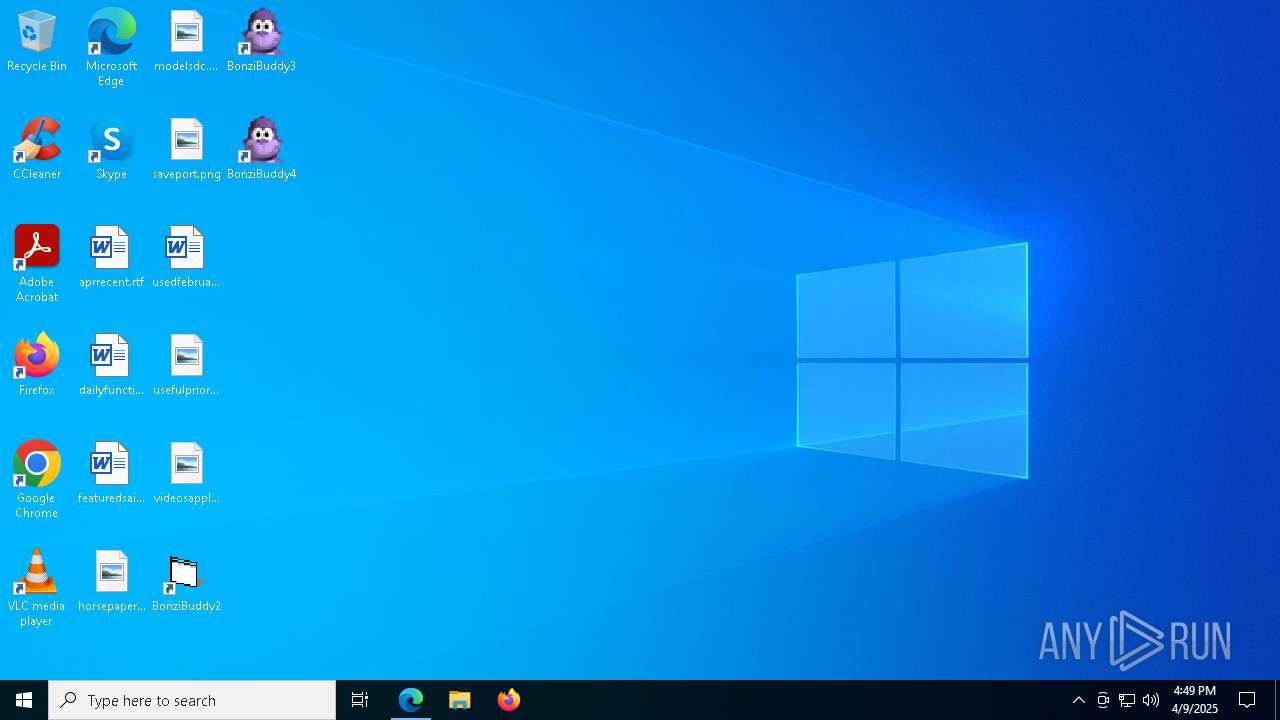
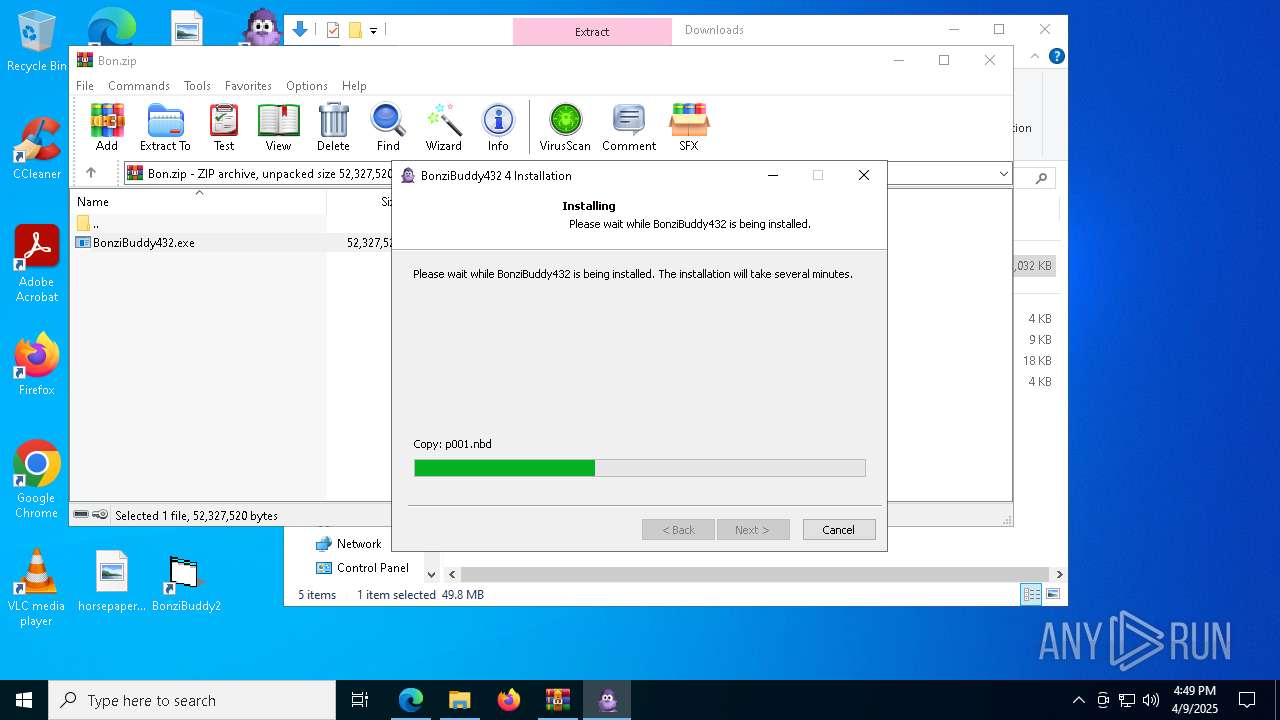
Creates files in the program directory
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
Create files in a temporary directory
- BonziBuddy432.exe (PID: 4056)
- MSAGENT.EXE (PID: 5508)
- tv_enua.exe (PID: 2392)
- BonziBuddy432.exe (PID: 7548)
- BonziBuddy432.exe (PID: 3100)
Creates files or folders in the user directory
- BonziBuddy432.exe (PID: 4056)
Application launched itself
- chrome.exe (PID: 6404)
- msedge.exe (PID: 7308)
- msedge.exe (PID: 7964)
- firefox.exe (PID: 6516)
Reads mouse settings
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
Process checks computer location settings
- BonziBuddy432.exe (PID: 4056)
- BonziBuddy432.exe (PID: 7548)
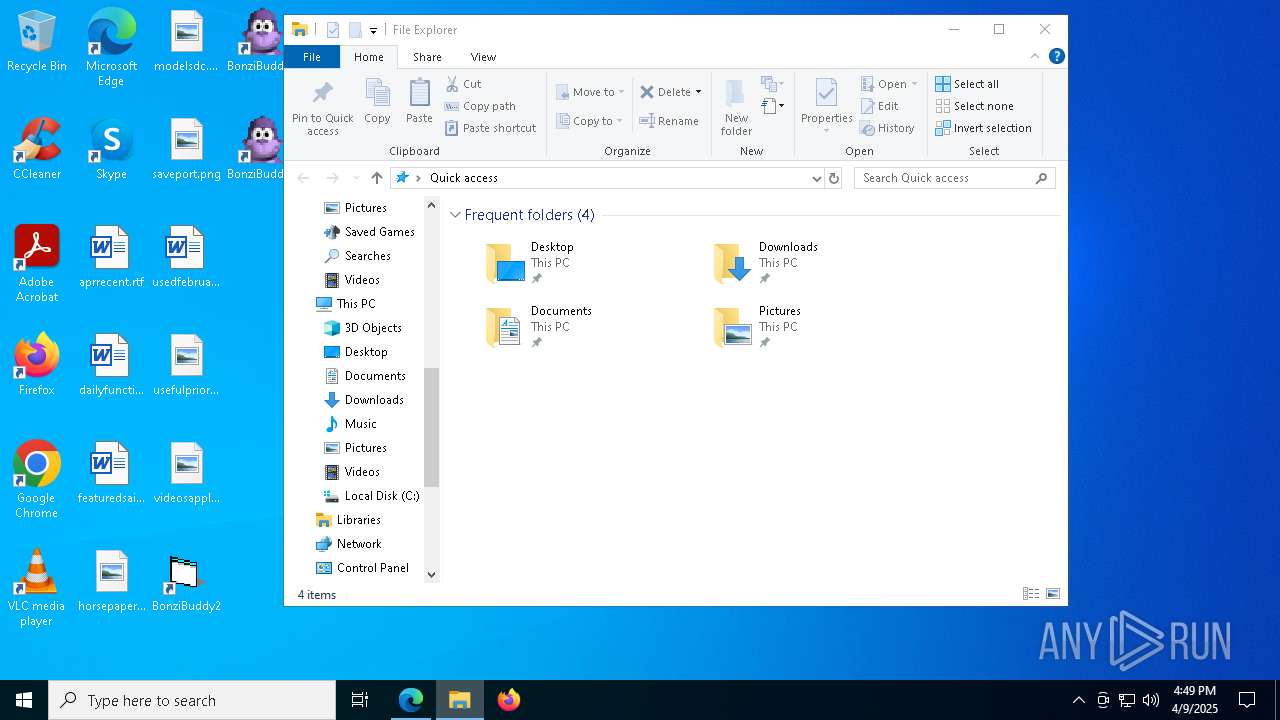
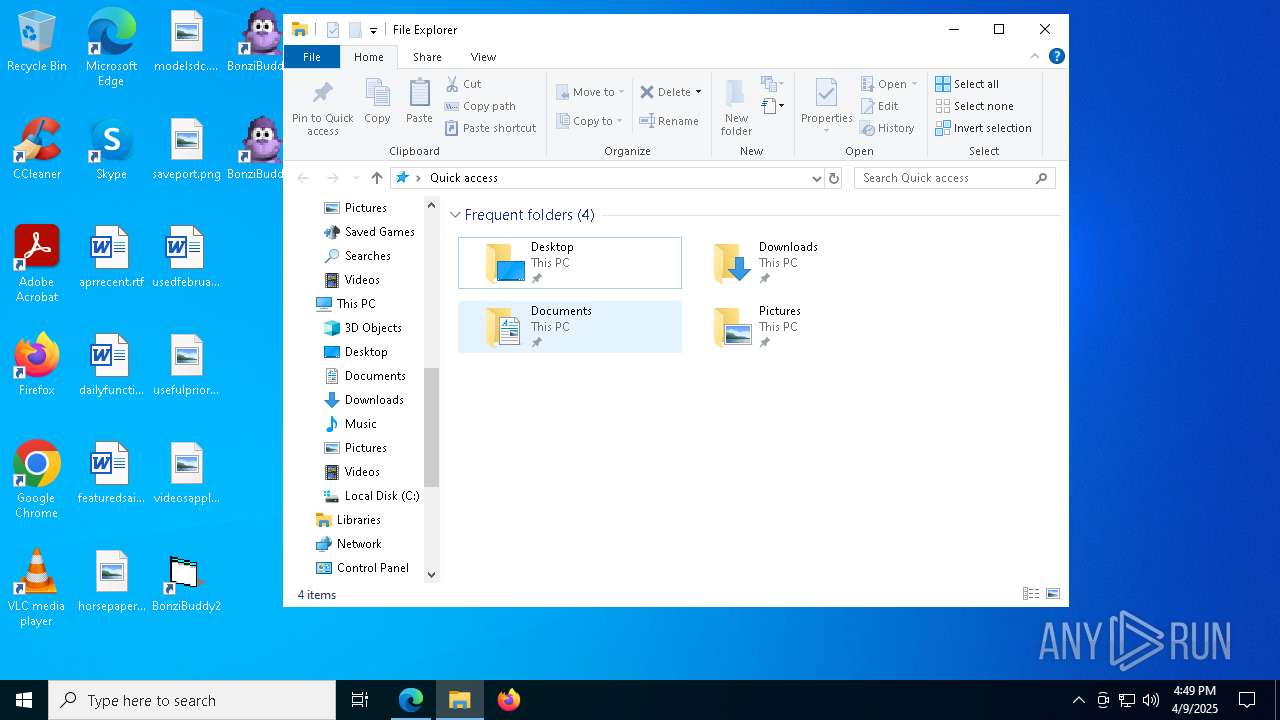
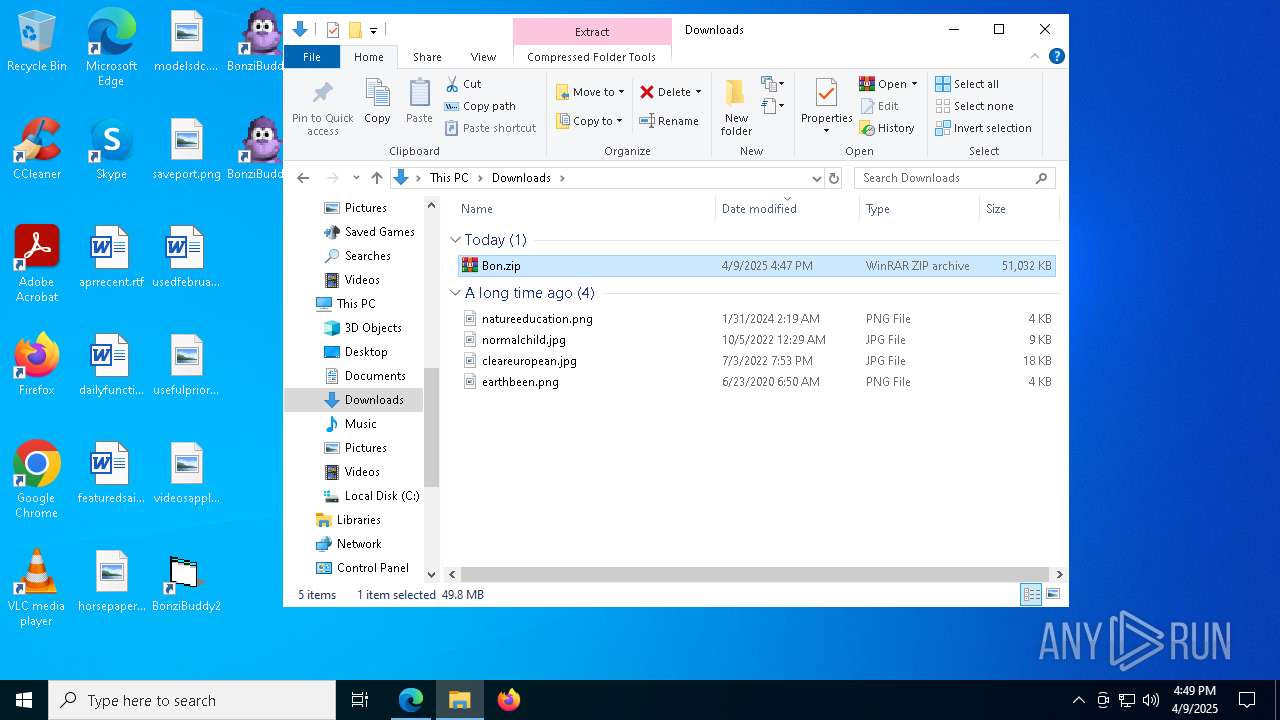
Manual execution by a user
- msedge.exe (PID: 7964)
- BonziBDY_4.EXE (PID: 7636)
- WinRAR.exe (PID: 1240)
- BonziBDY_35.EXE (PID: 6824)
- BonziBDY_4.EXE (PID: 3828)
Reads Environment values
- identity_helper.exe (PID: 8068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
106
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | grpconv.exe -o | C:\Windows\SysWOW64\grpconv.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3468 --field-trial-handle=2360,i,6525325266922573238,14609575511291556300,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2728 --field-trial-handle=2360,i,6525325266922573238,14609575511291556300,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=5364 --field-trial-handle=1936,i,32879958138643877,18088350186614454743,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
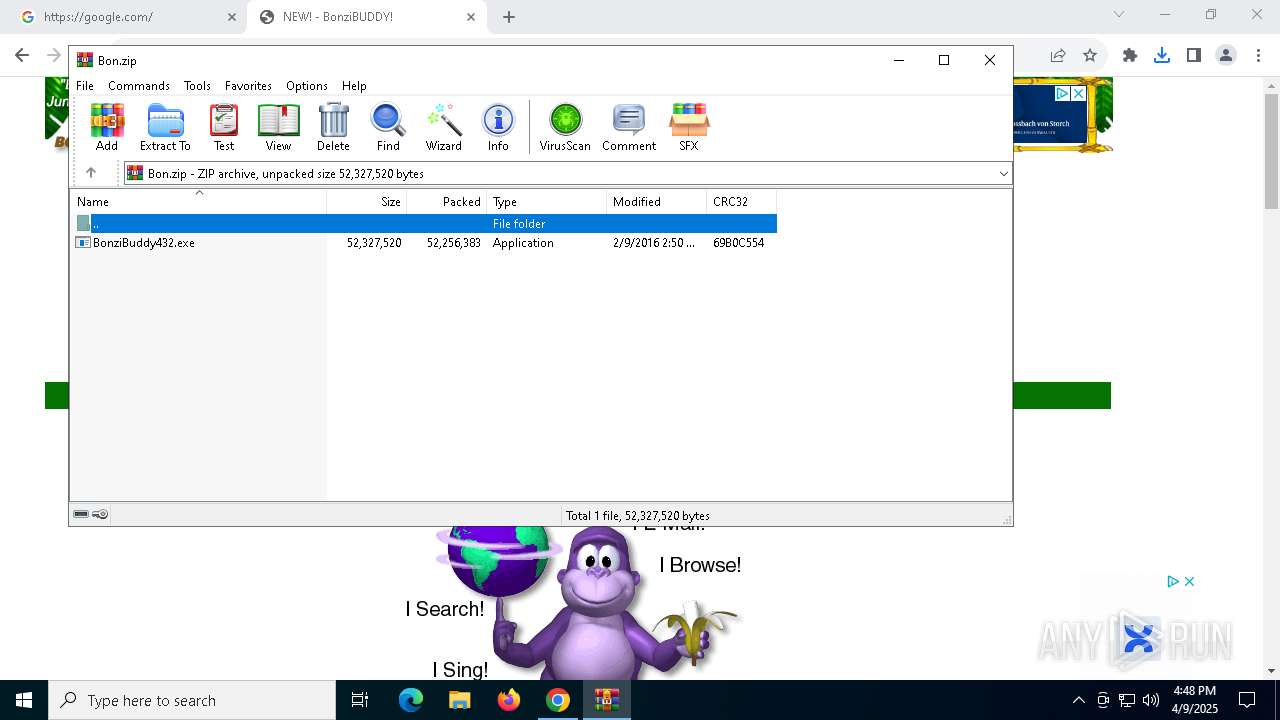
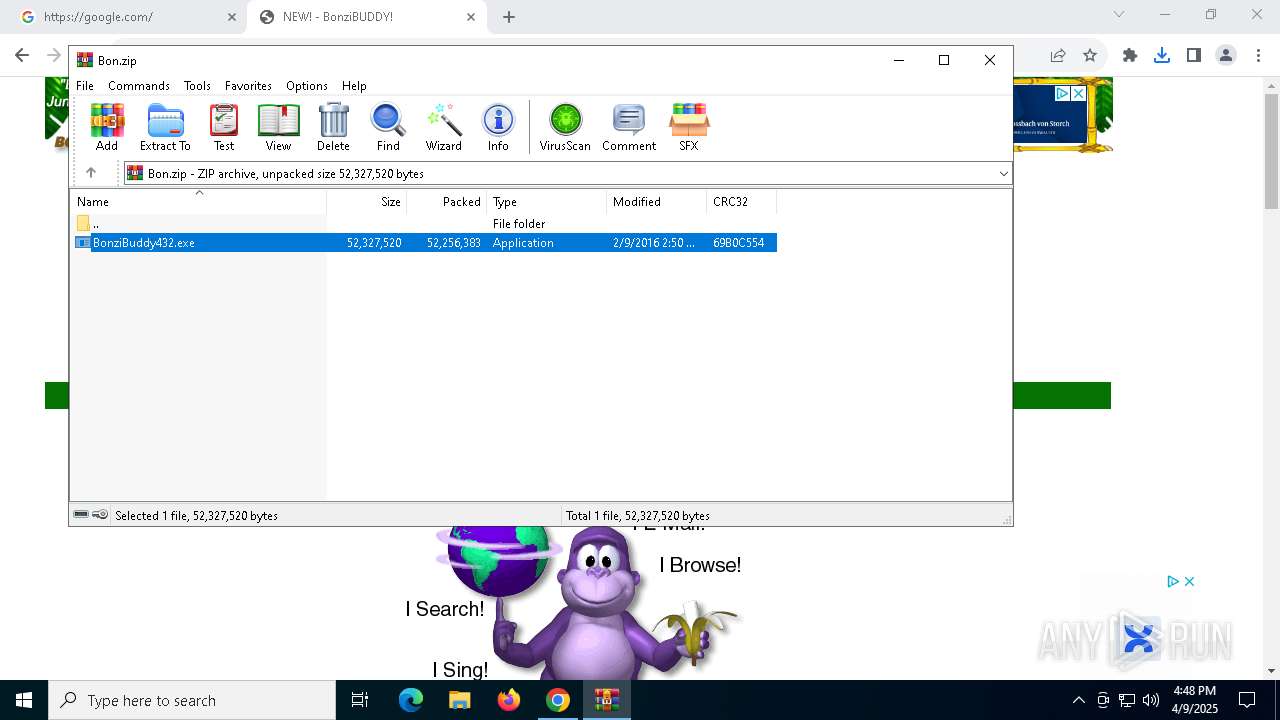
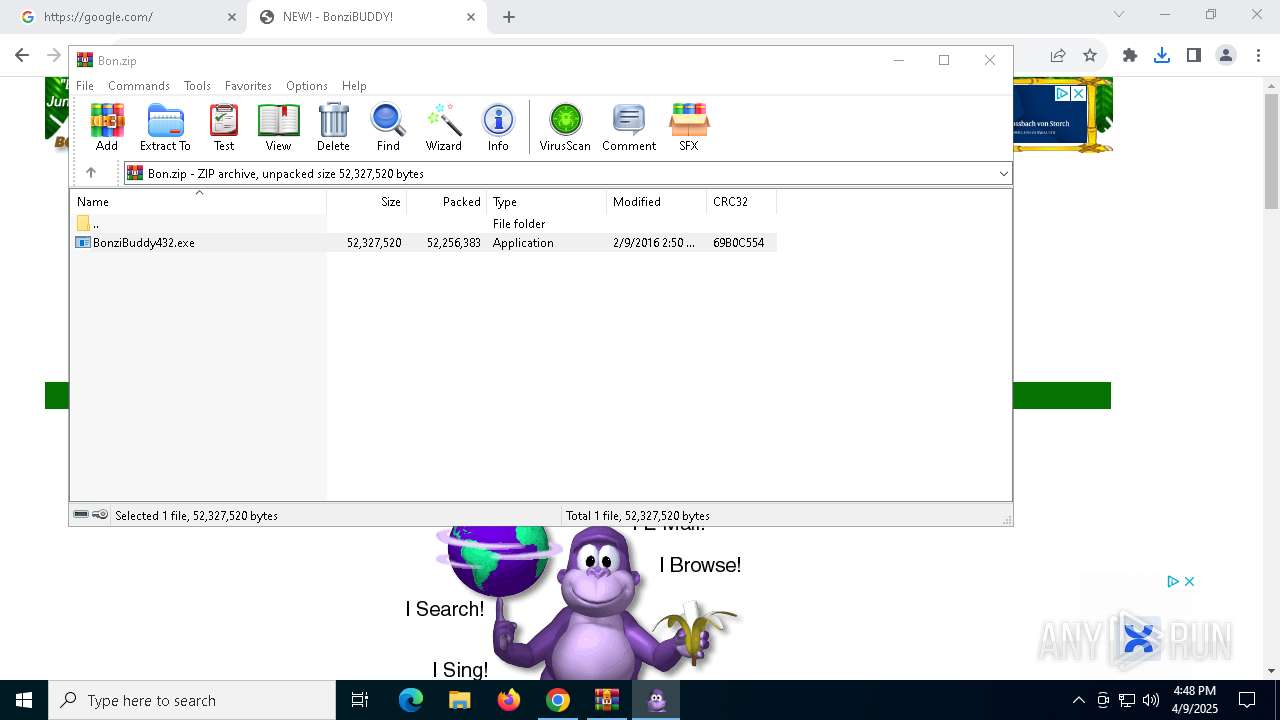
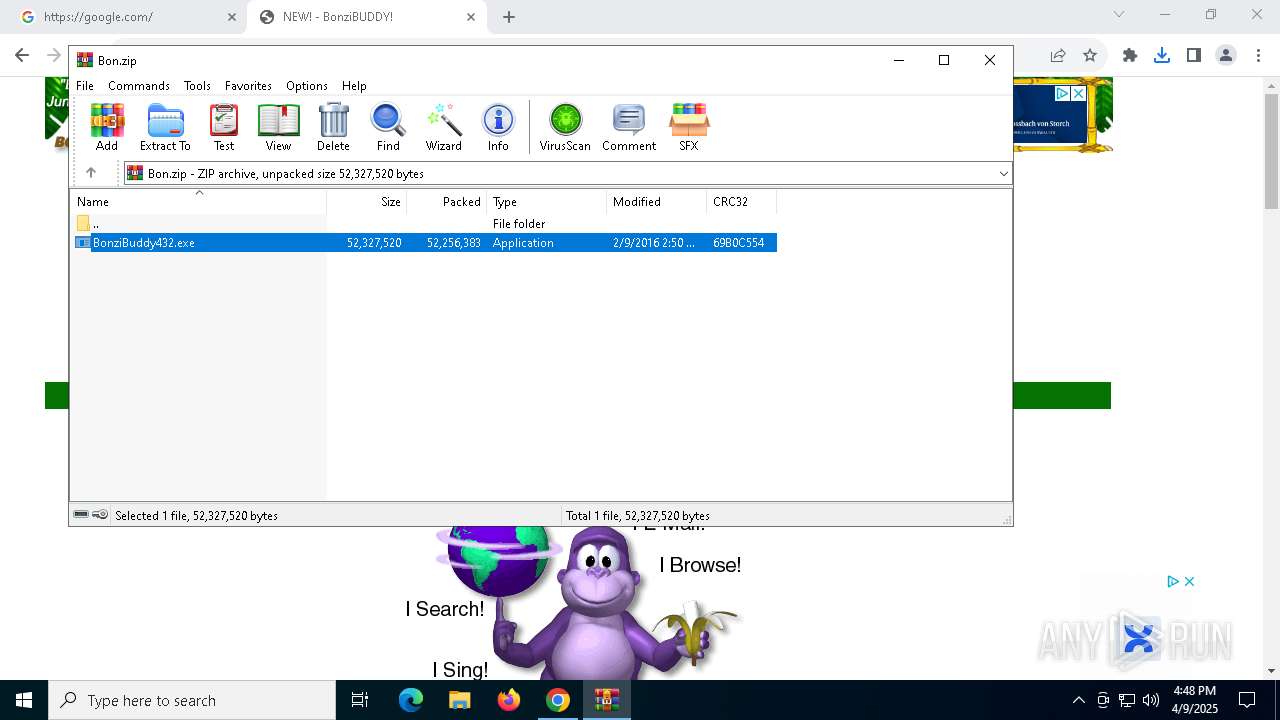
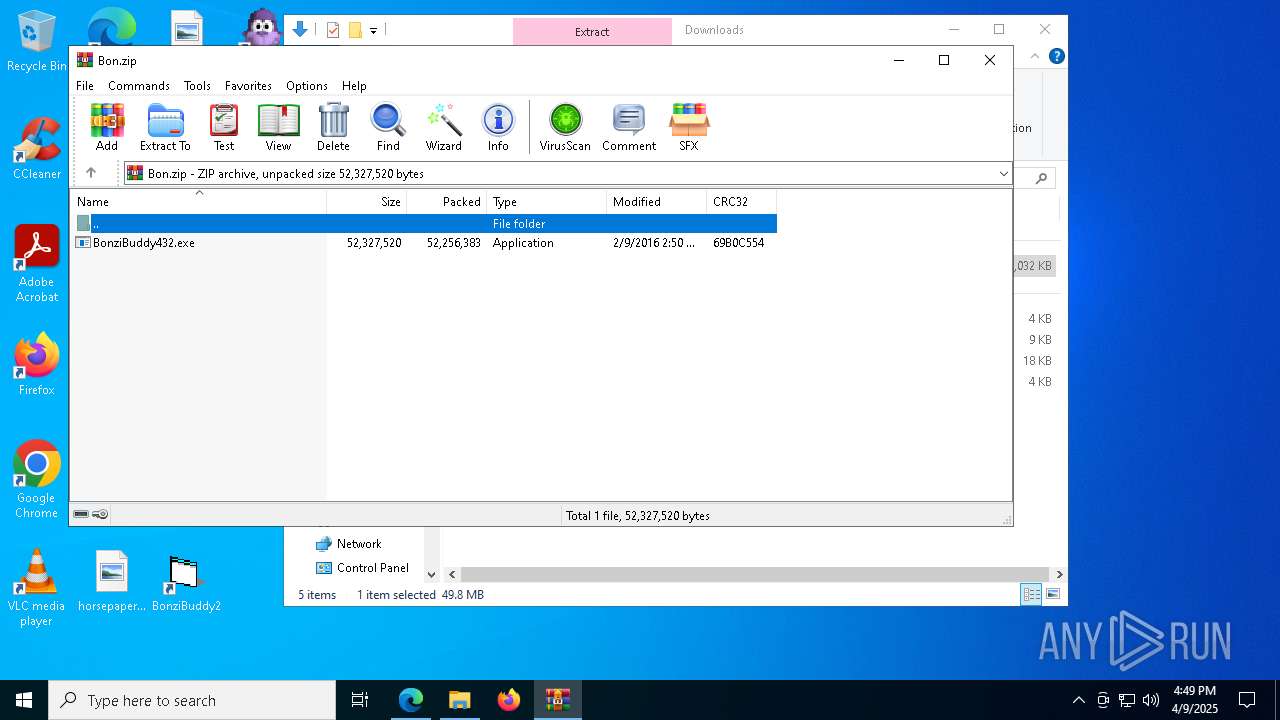
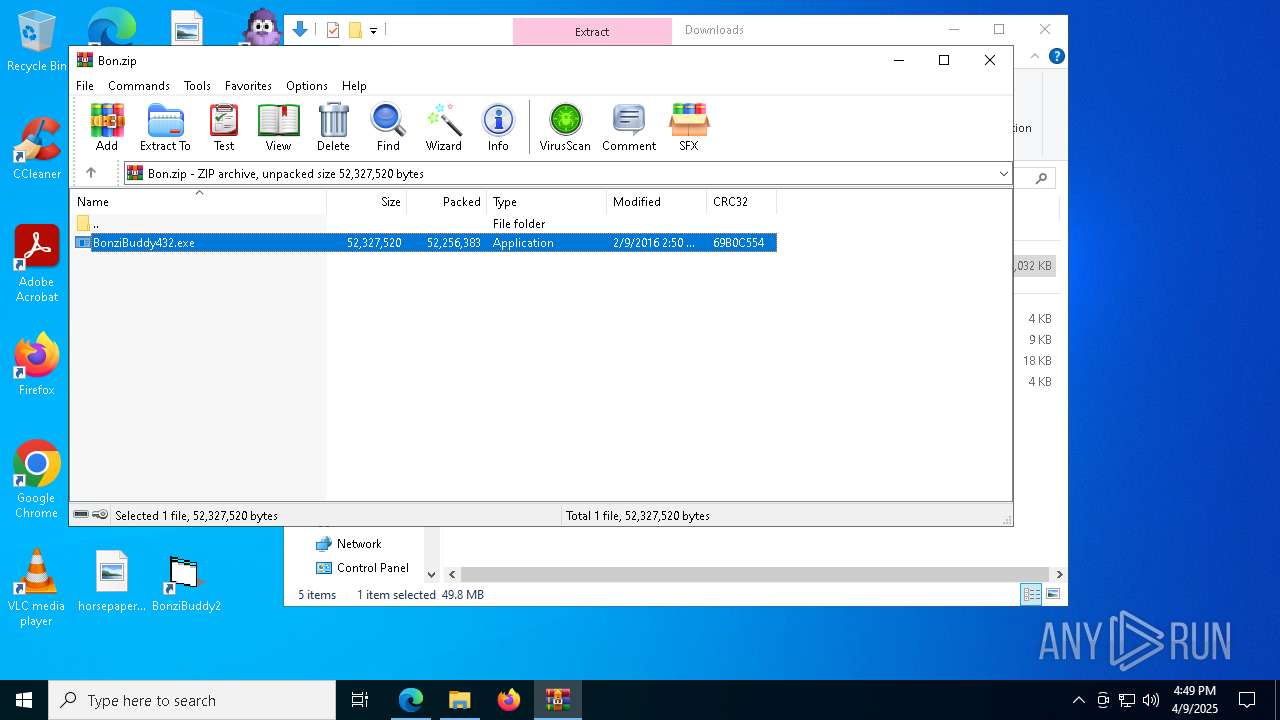
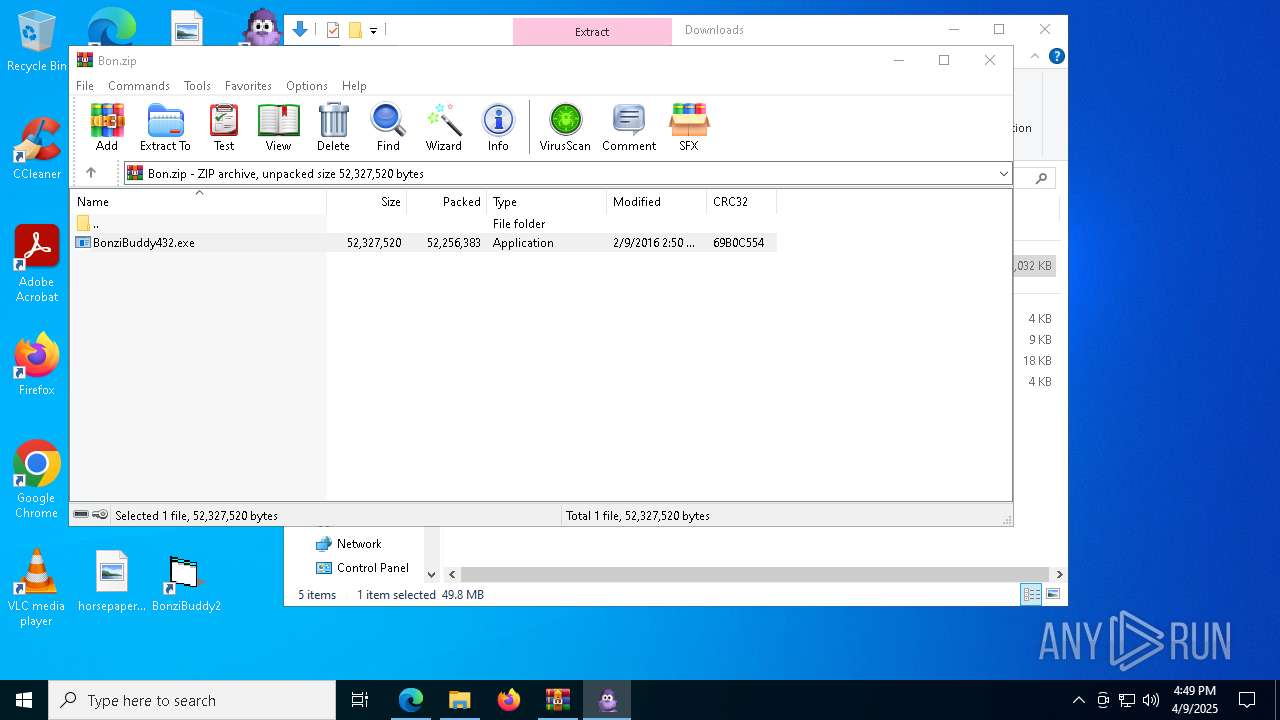
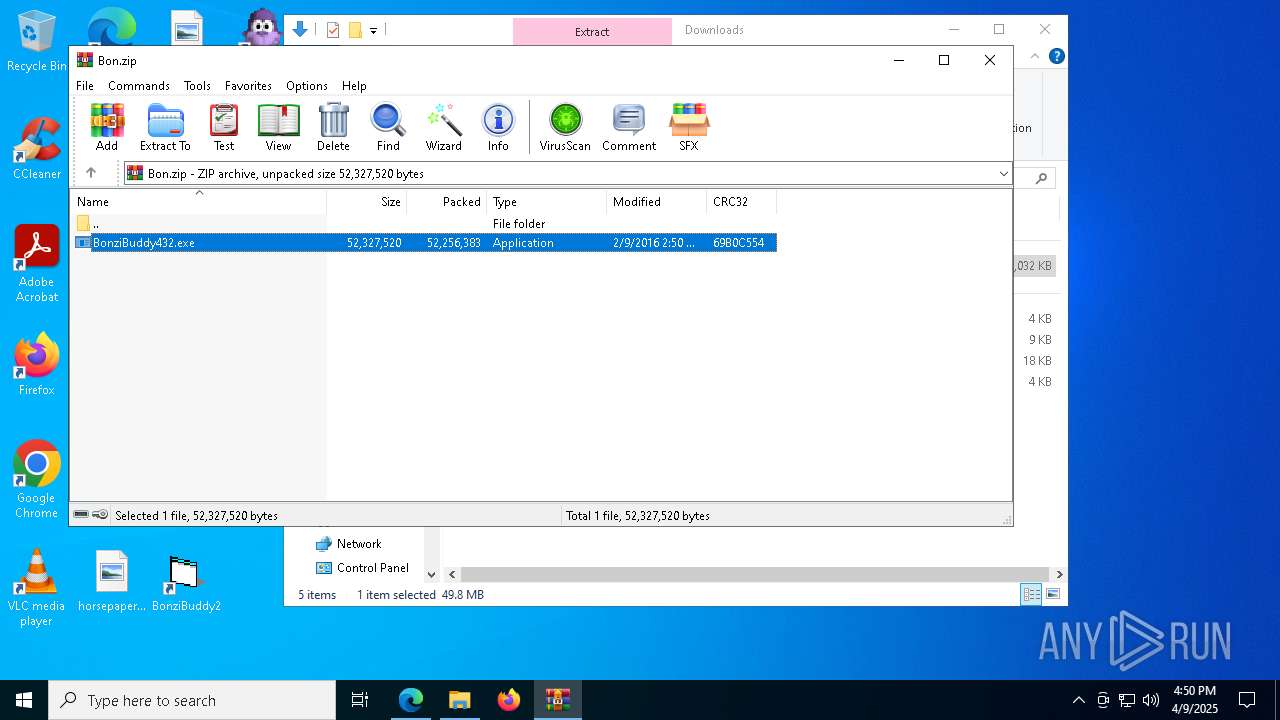
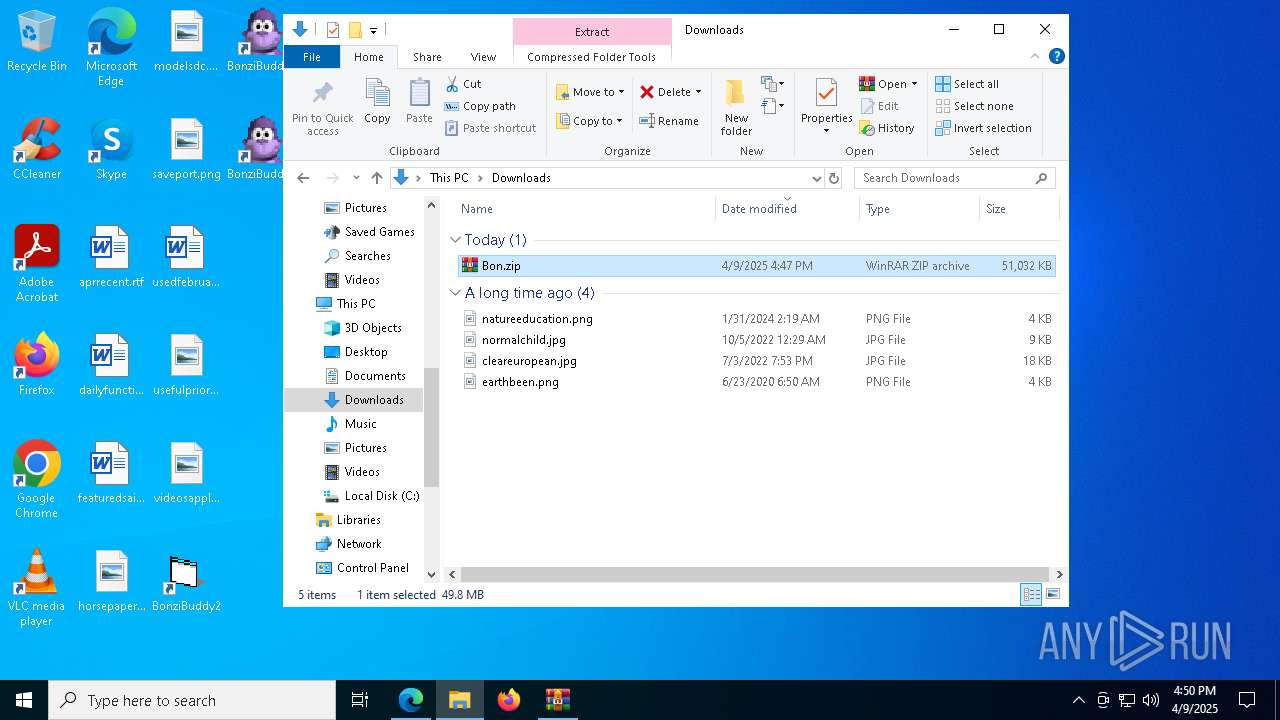
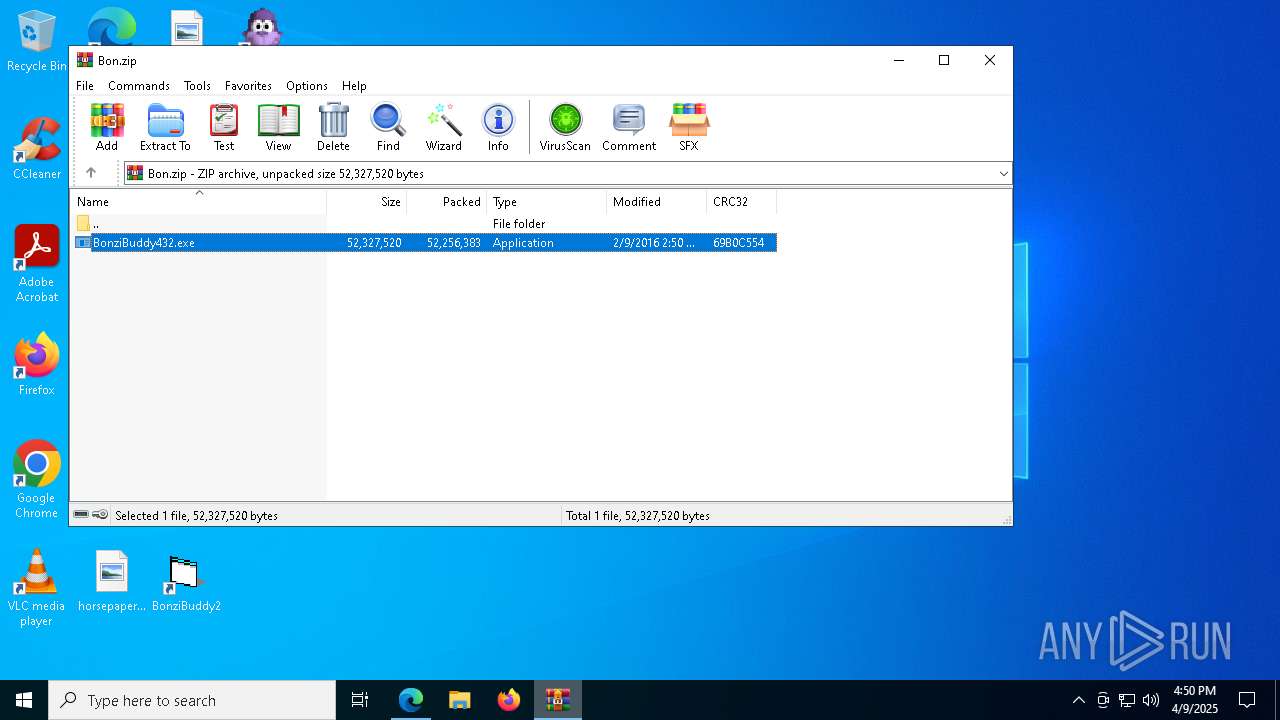
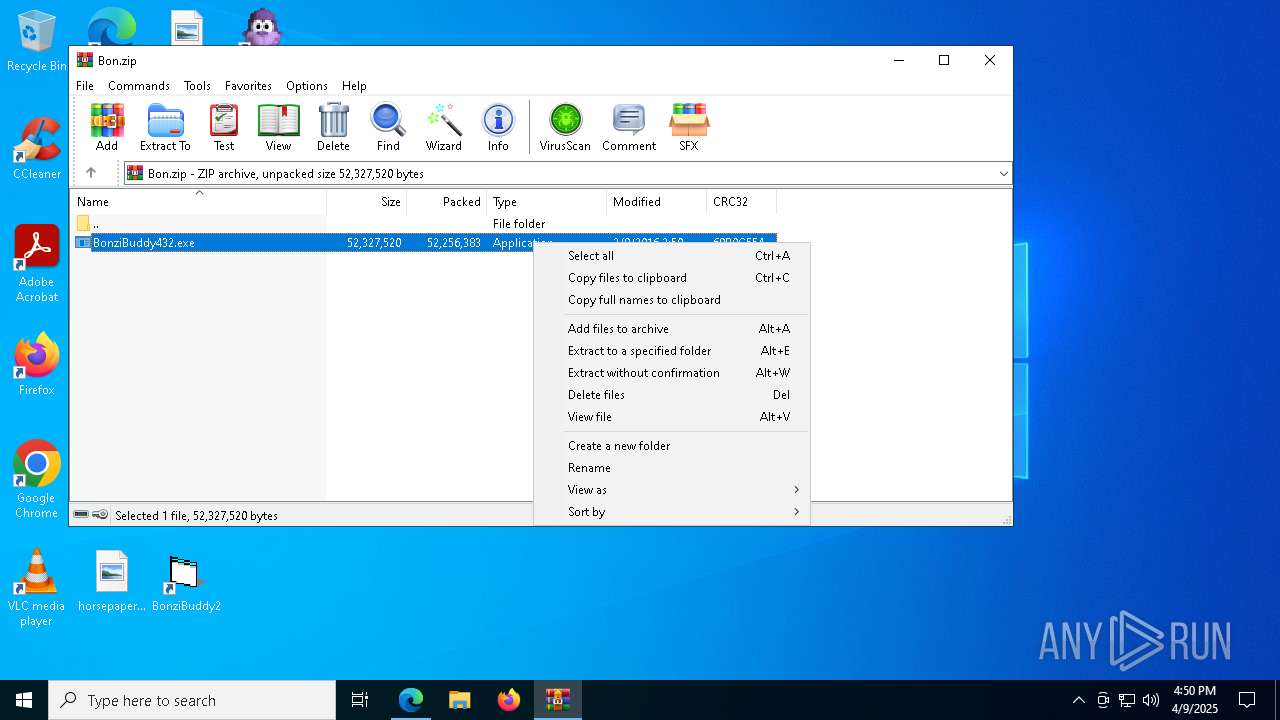
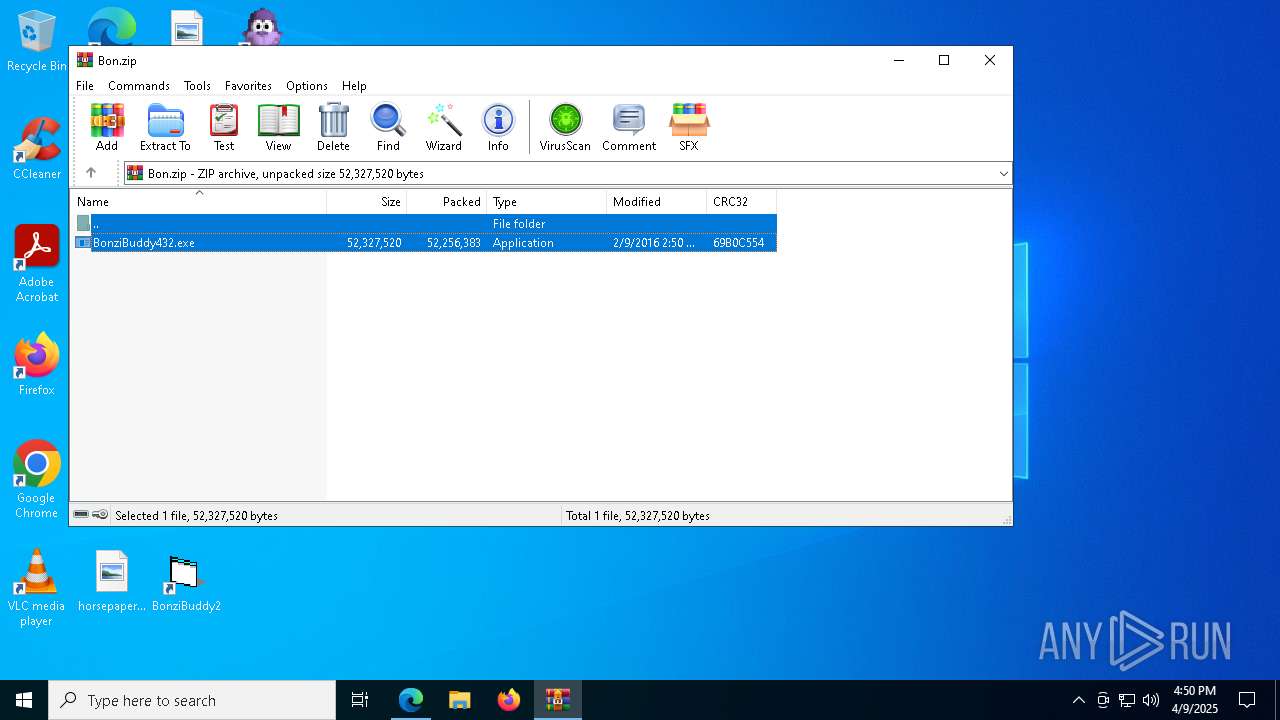
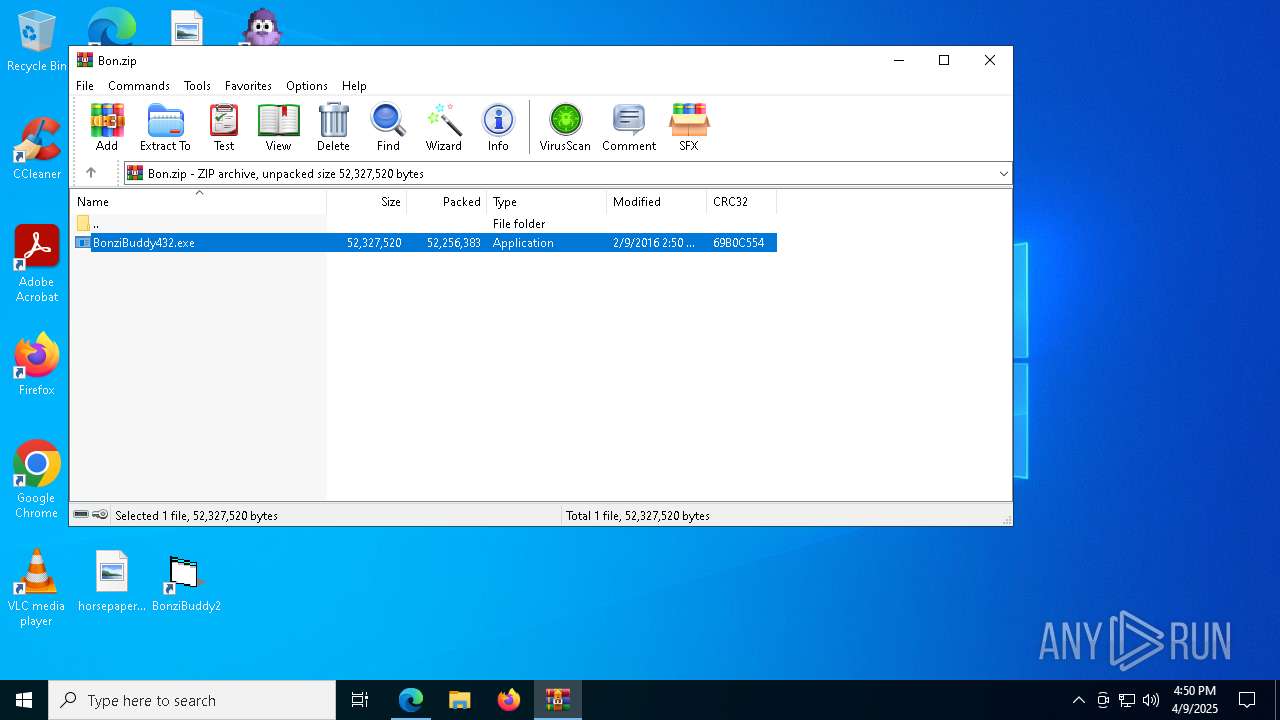
| 904 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Bon.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=5416 --field-trial-handle=1936,i,32879958138643877,18088350186614454743,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=3880 --field-trial-handle=2360,i,6525325266922573238,14609575511291556300,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Bon.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6196 --field-trial-handle=1936,i,32879958138643877,18088350186614454743,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
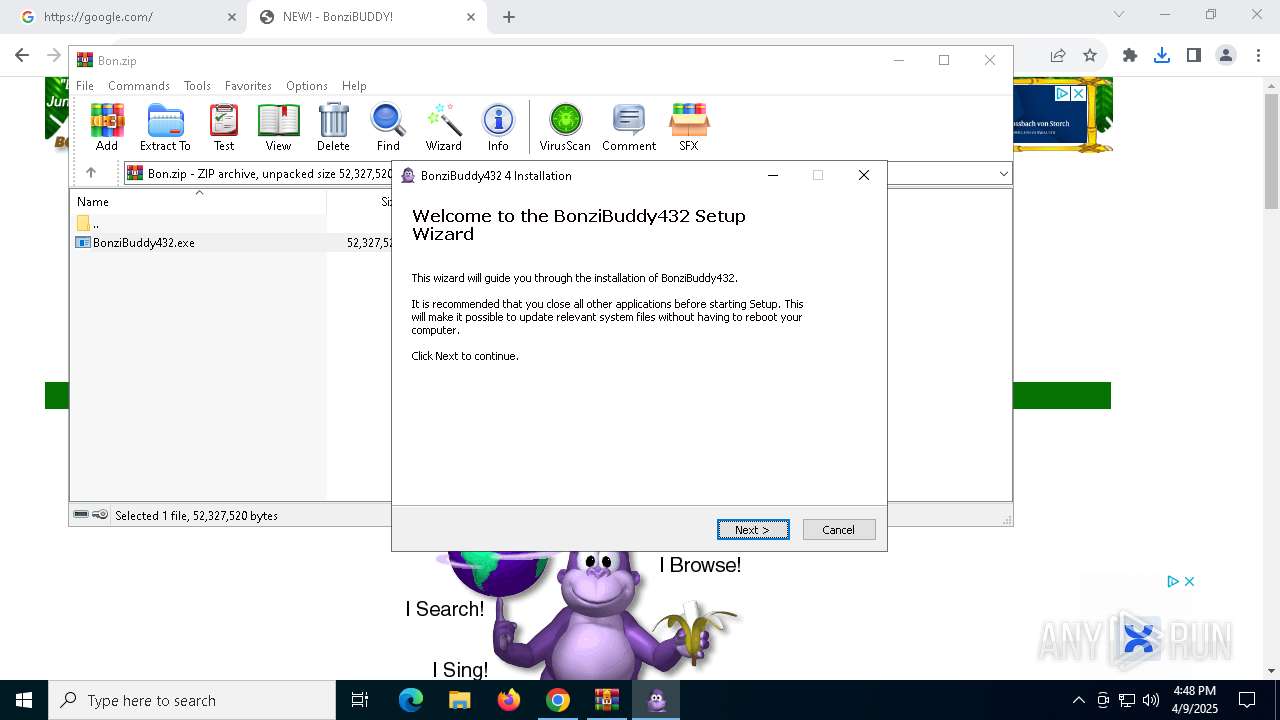
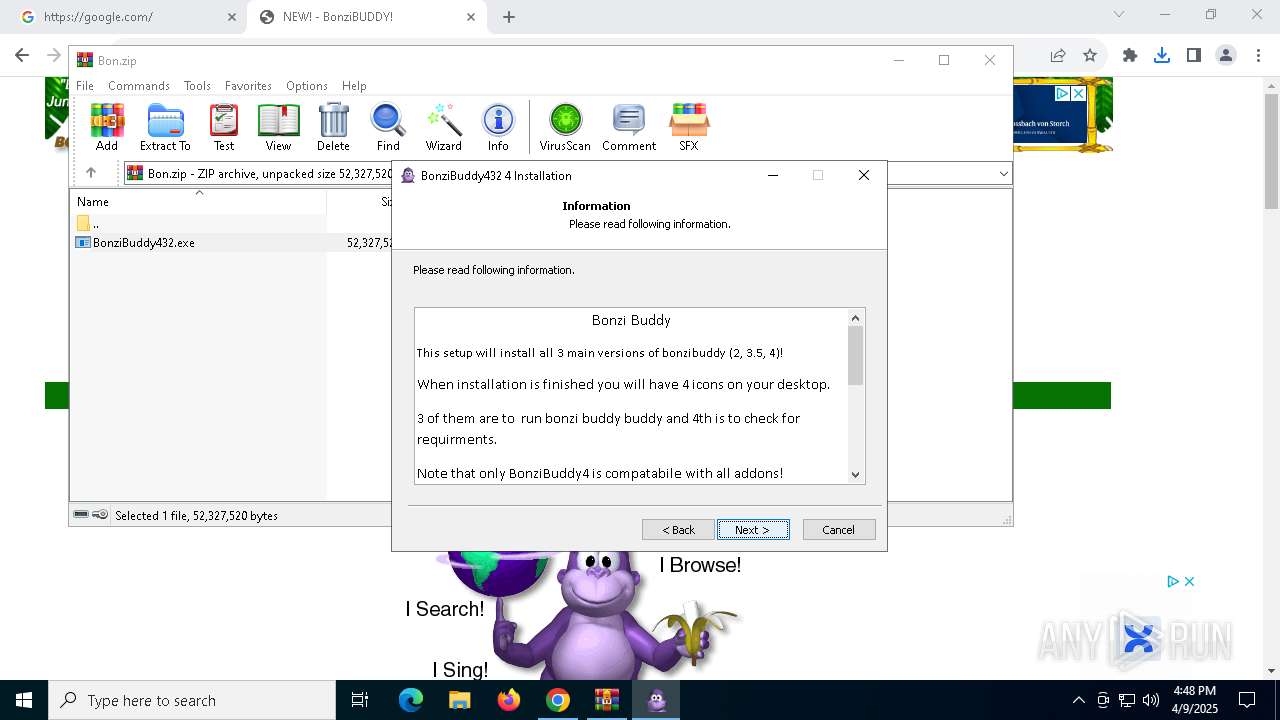
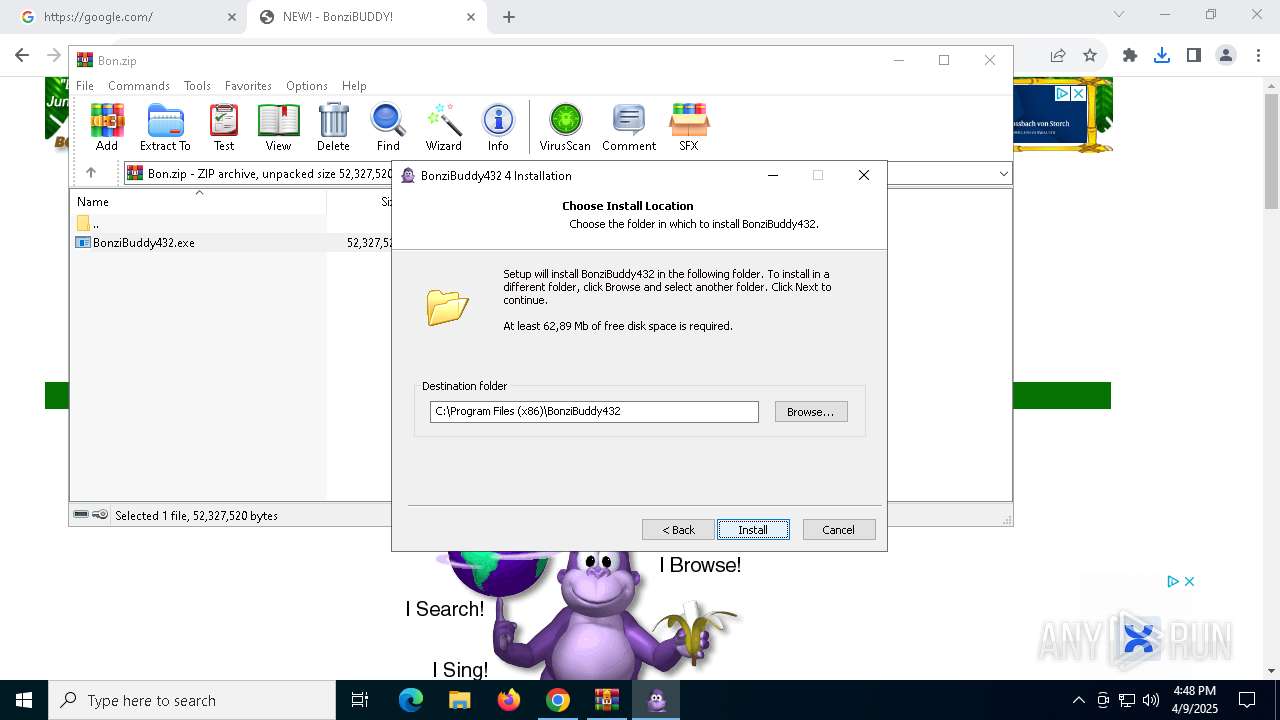
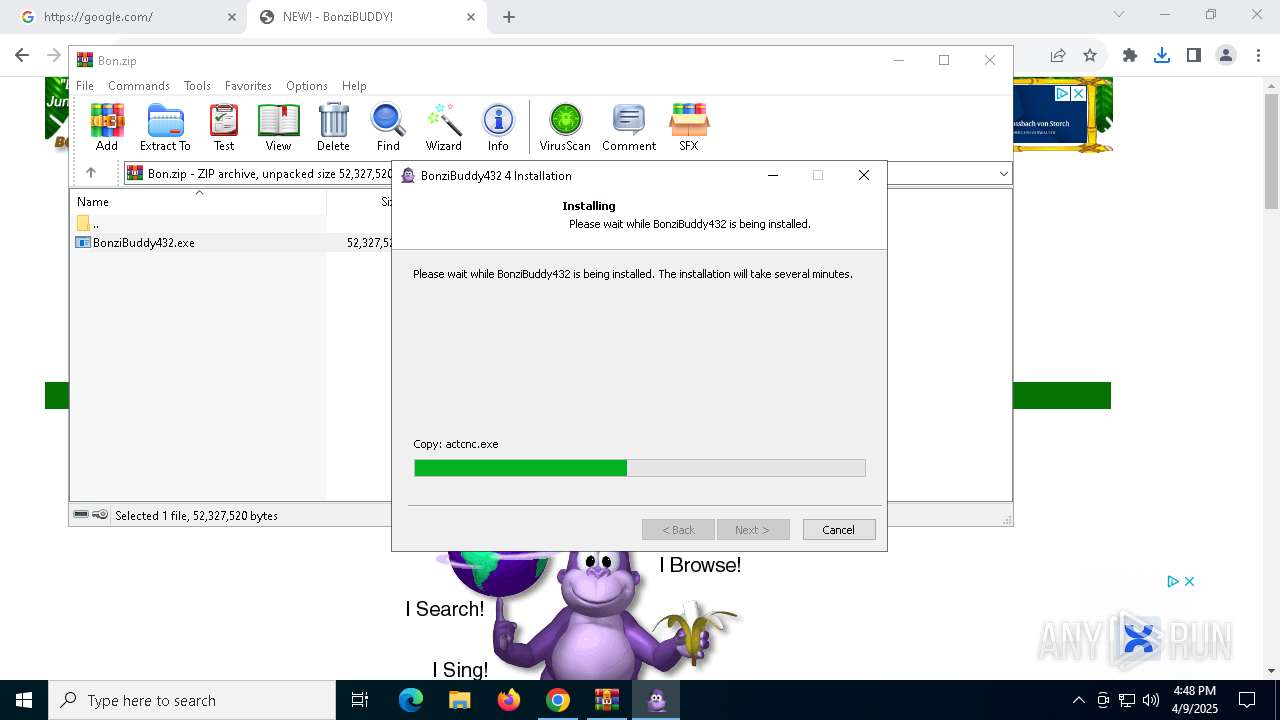
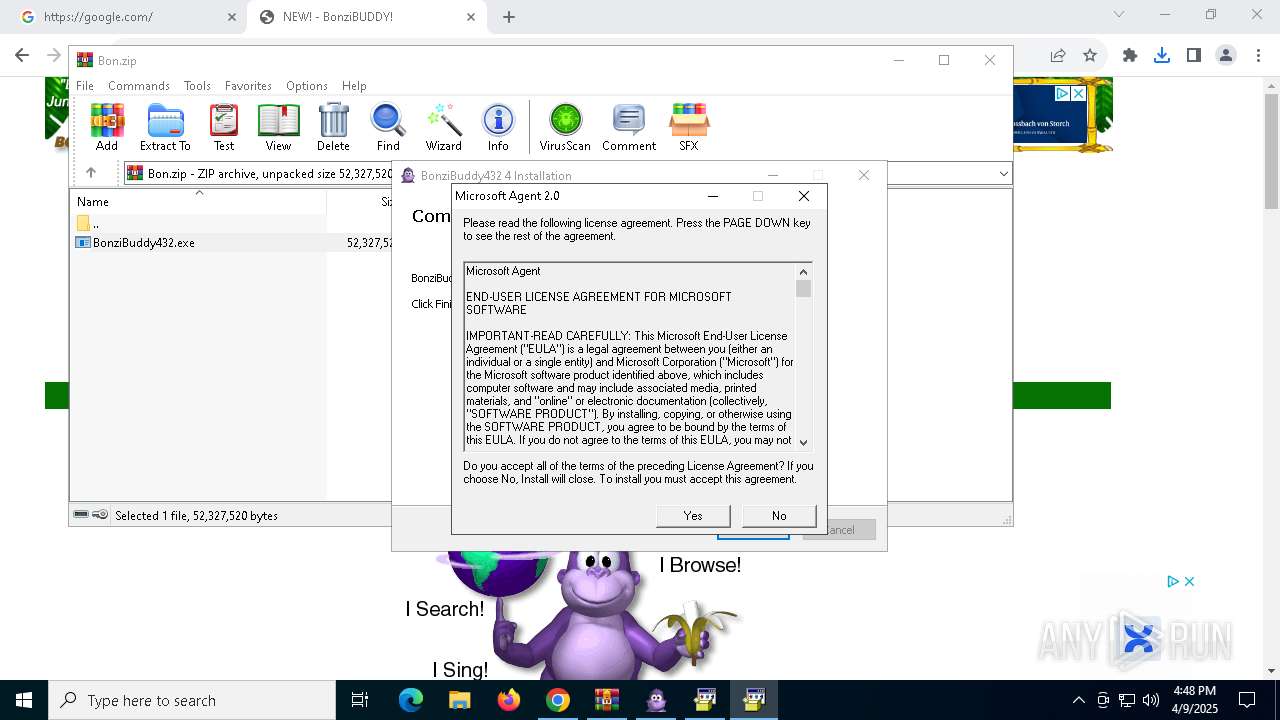
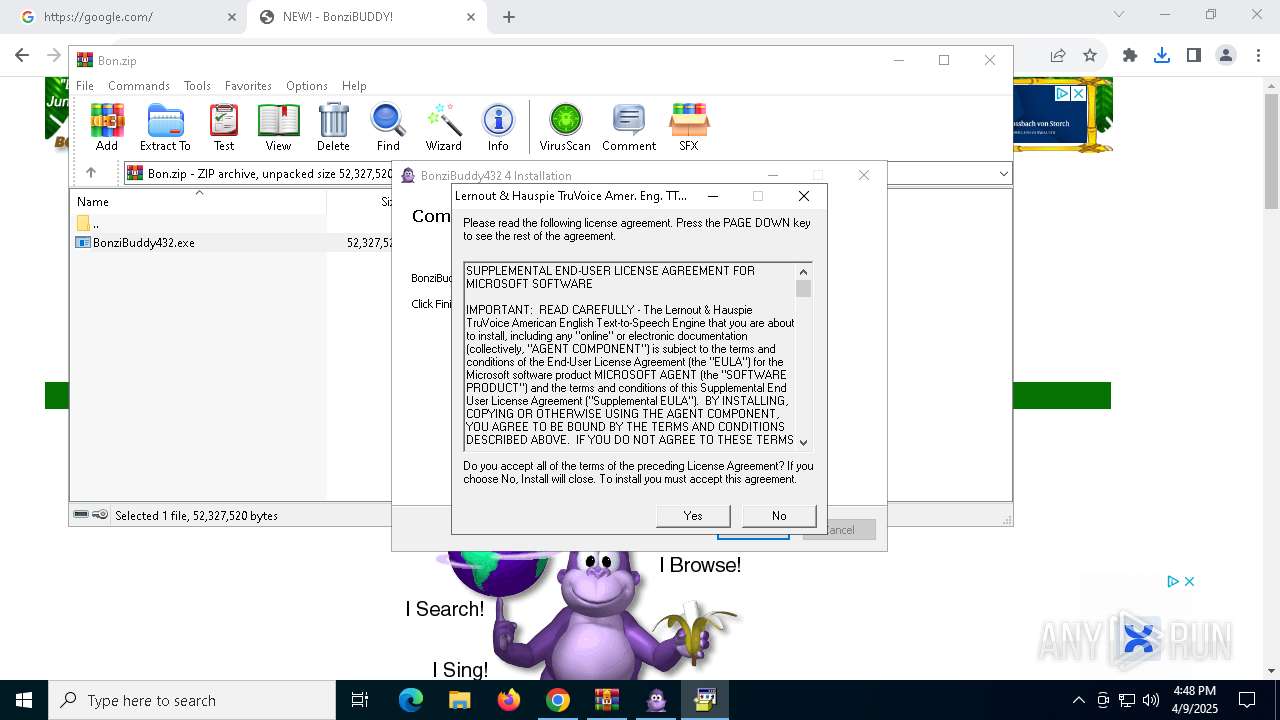
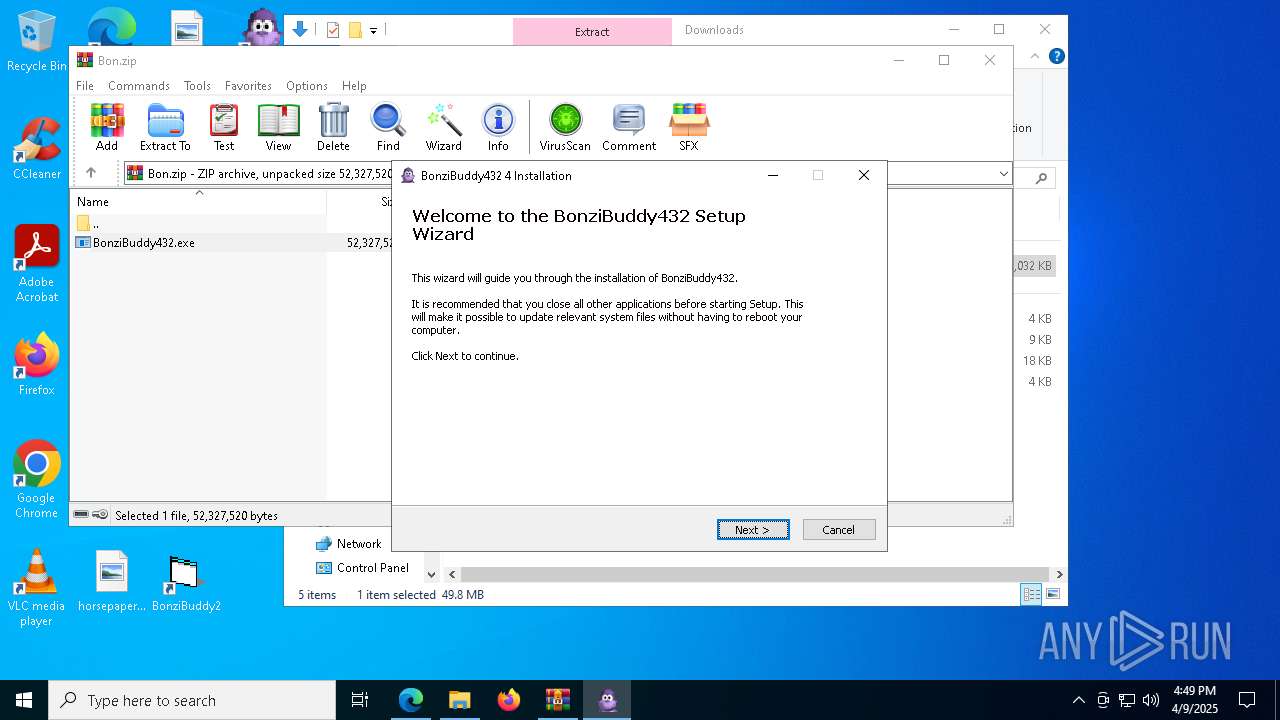
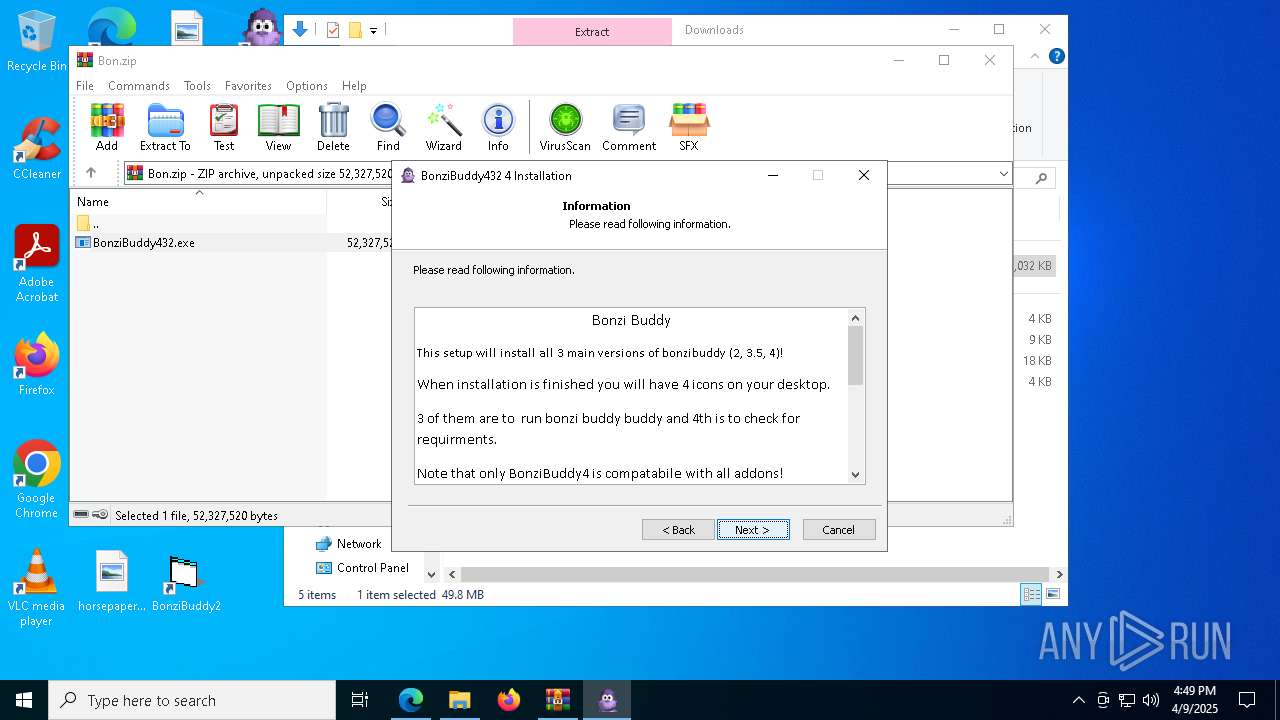
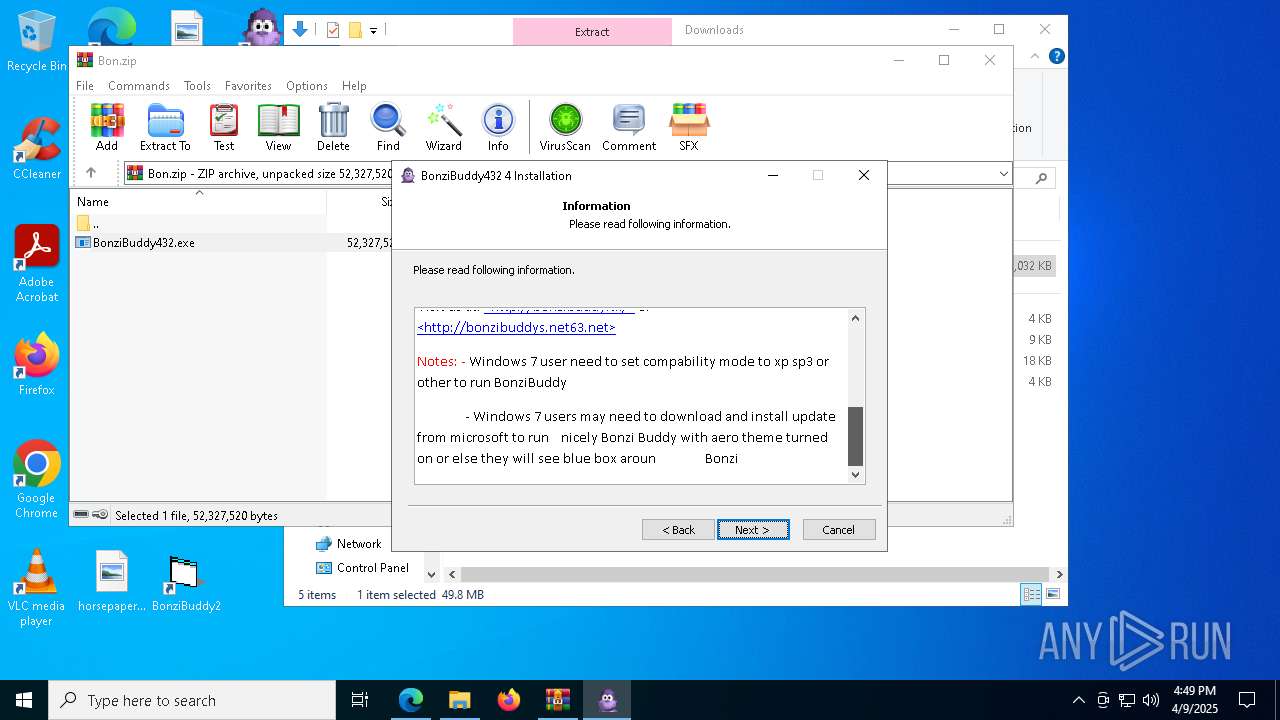
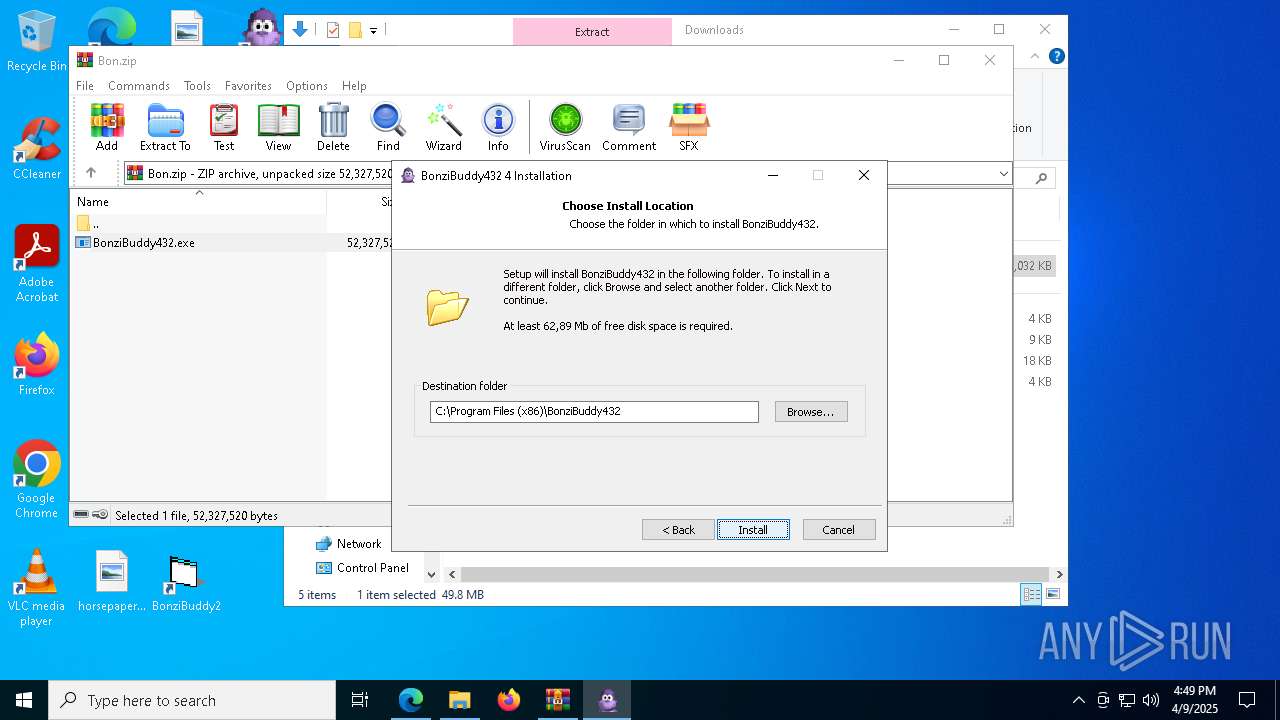
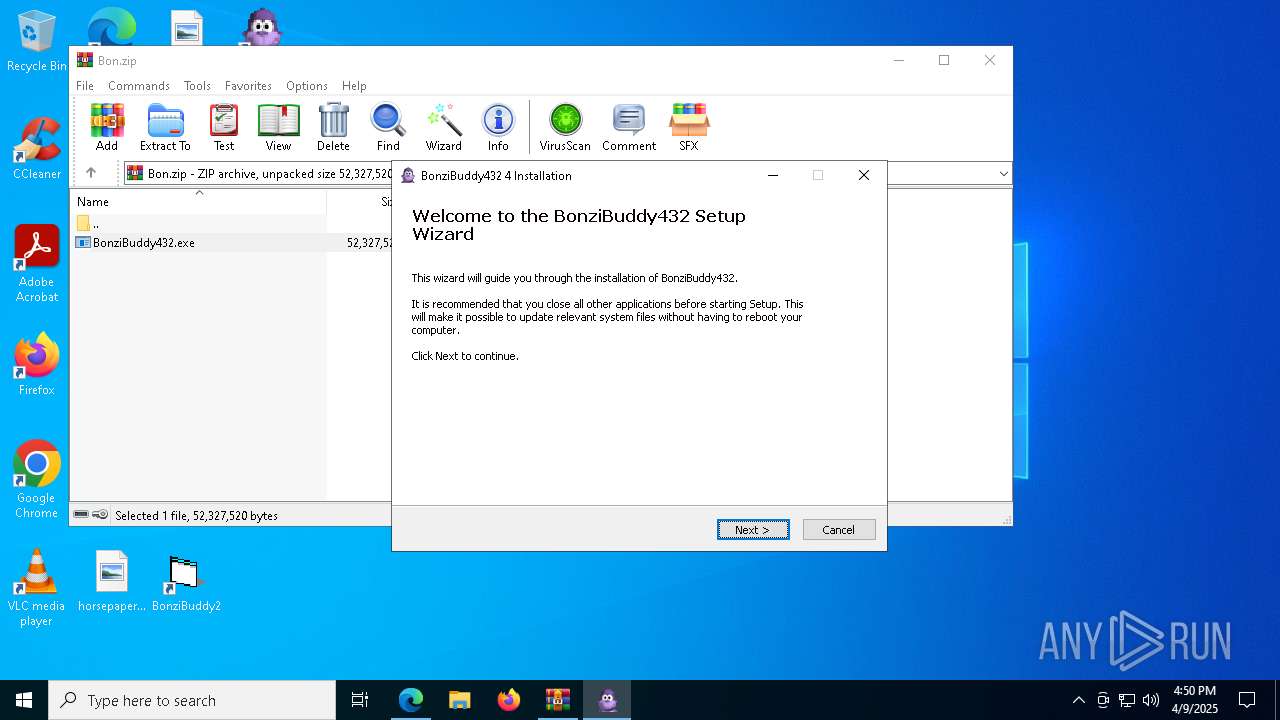
| 1300 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1240.23347\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1240.23347\BonziBuddy432.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bonzi Software Integrity Level: MEDIUM Description: BonziBuddy432 4 Installation Exit code: 3221226540 Version: 4 Modules
| |||||||||||||||
Total events
21 747
Read events
20 541
Write events
833
Delete events
373
Modification events
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
128
Suspicious files
469
Text files
342
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c342.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c342.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c352.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c352.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c352.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
162
DNS requests
163
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8064 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7712 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6404 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6048 | chrome.exe | 216.58.206.78:80 | google.com | GOOGLE | US | whitelisted |
6048 | chrome.exe | 216.58.206.78:443 | google.com | GOOGLE | US | whitelisted |
6048 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6048 | chrome.exe | 172.217.23.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
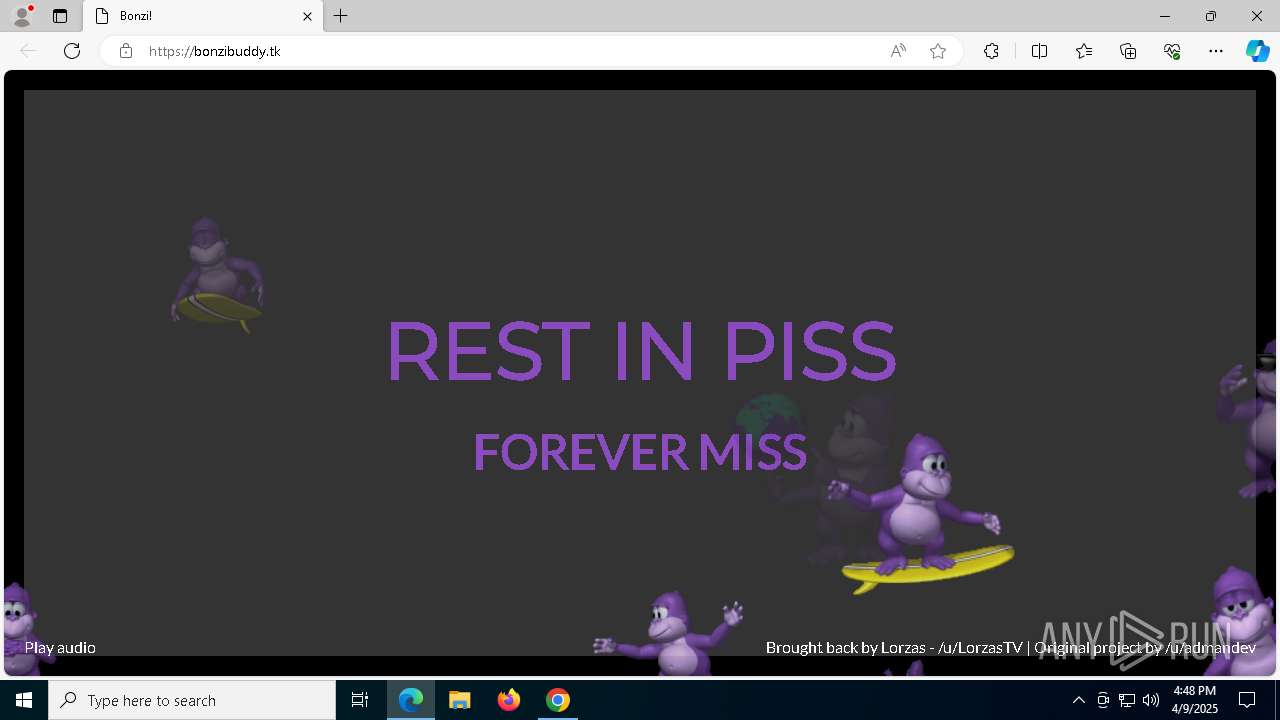
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
8092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
8092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
8092 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |