| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/3b82fce6-35de-4177-a277-309c035ee526 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 06:33:45 |
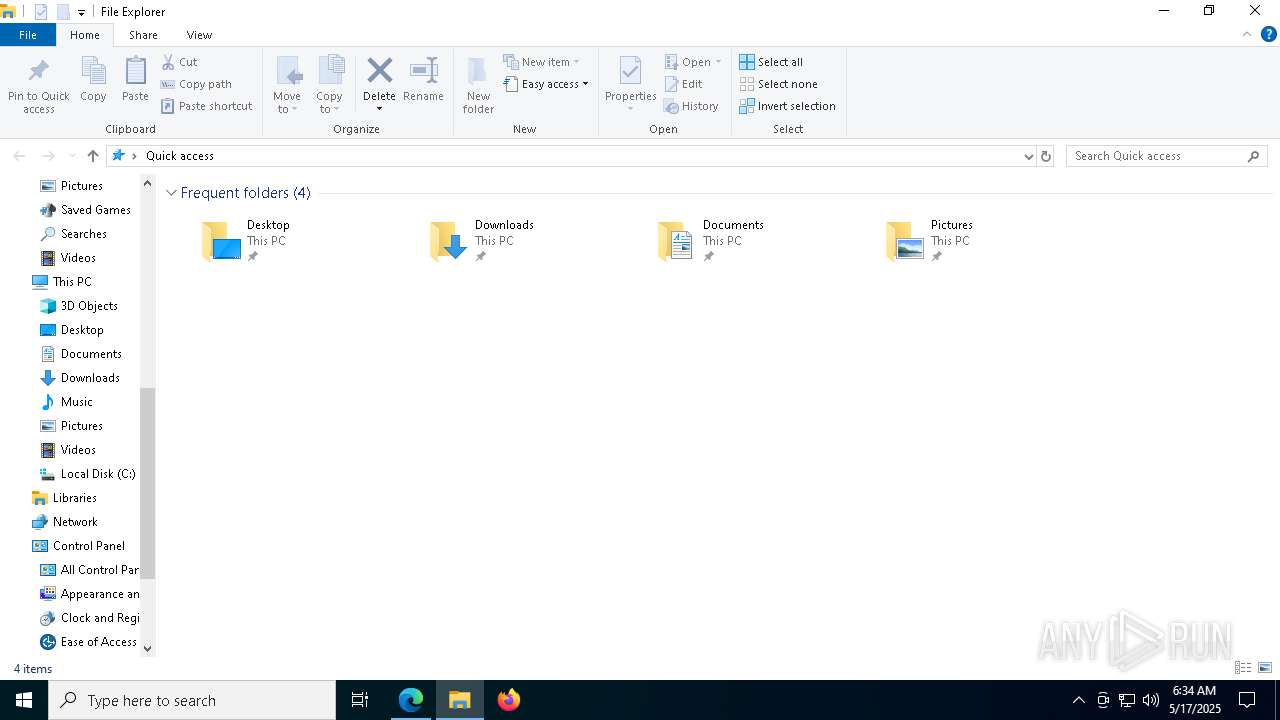
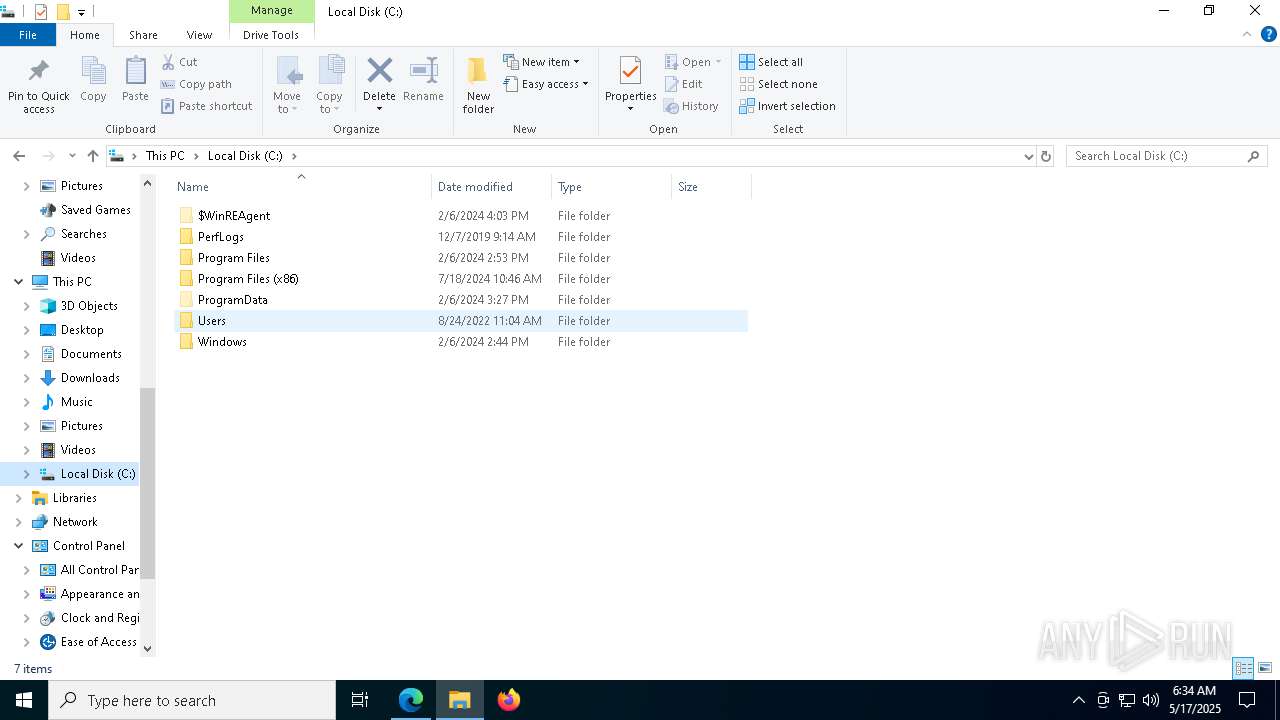
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
MALICIOUS
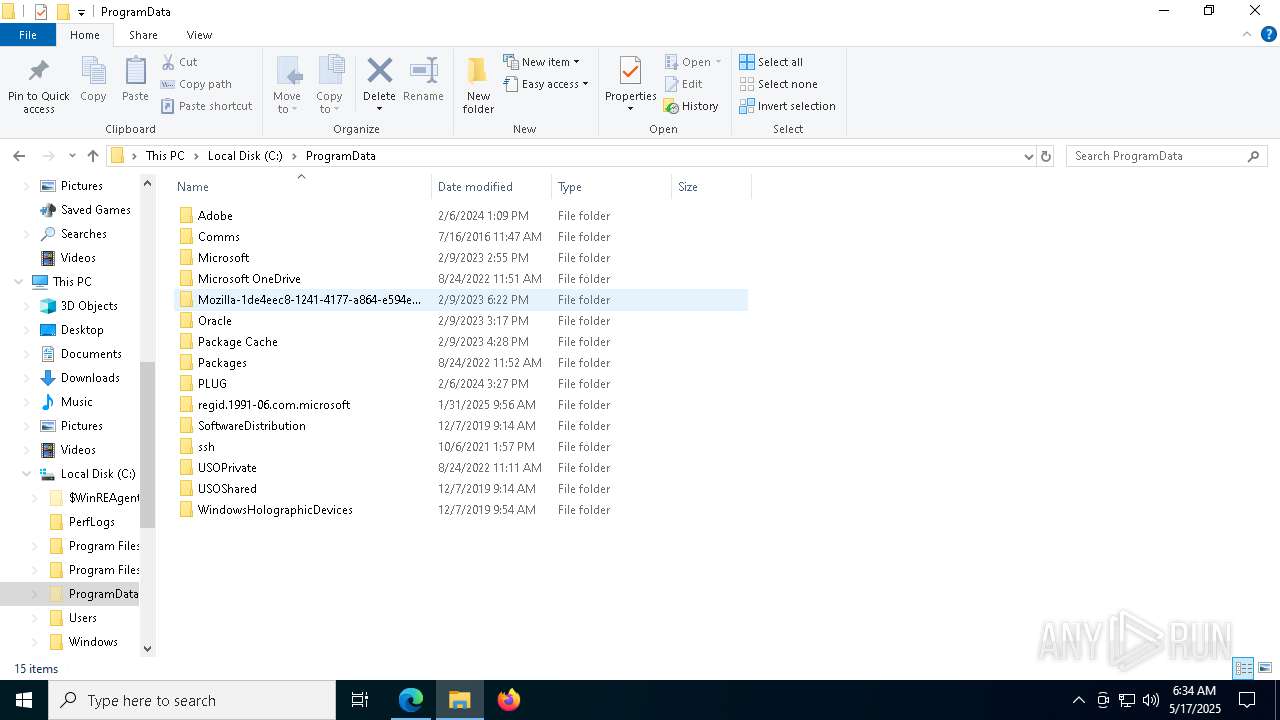
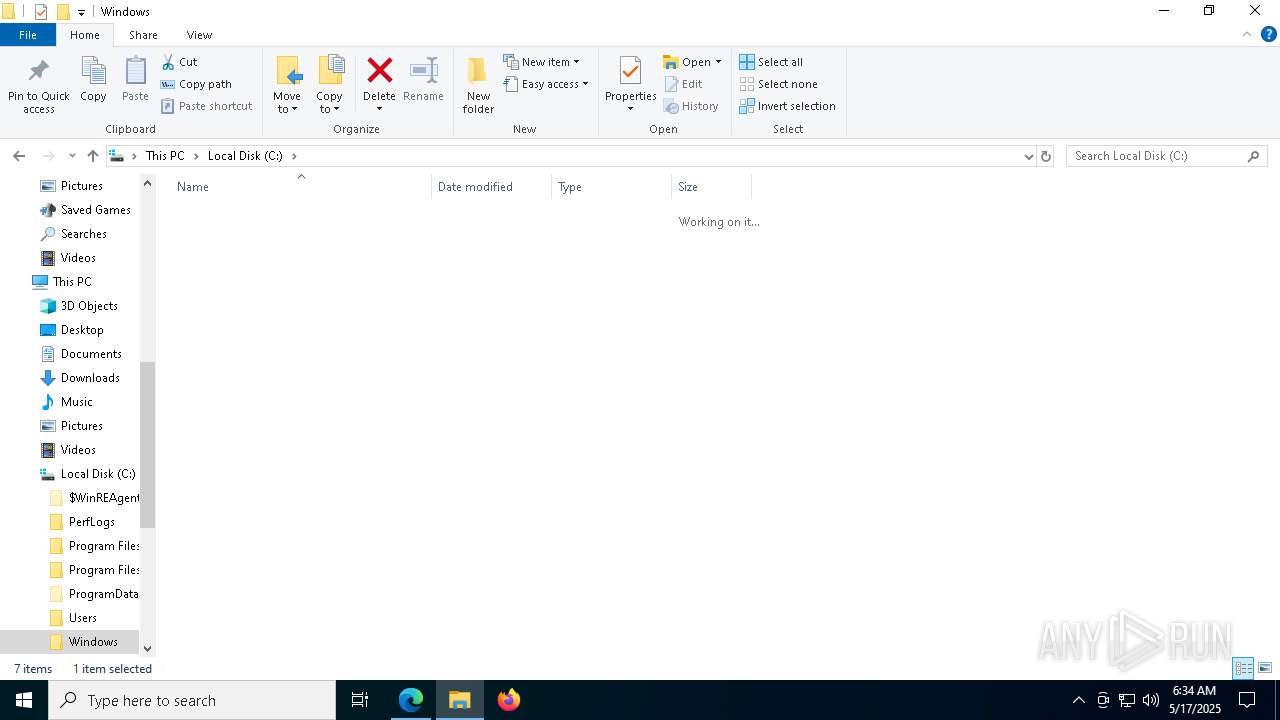
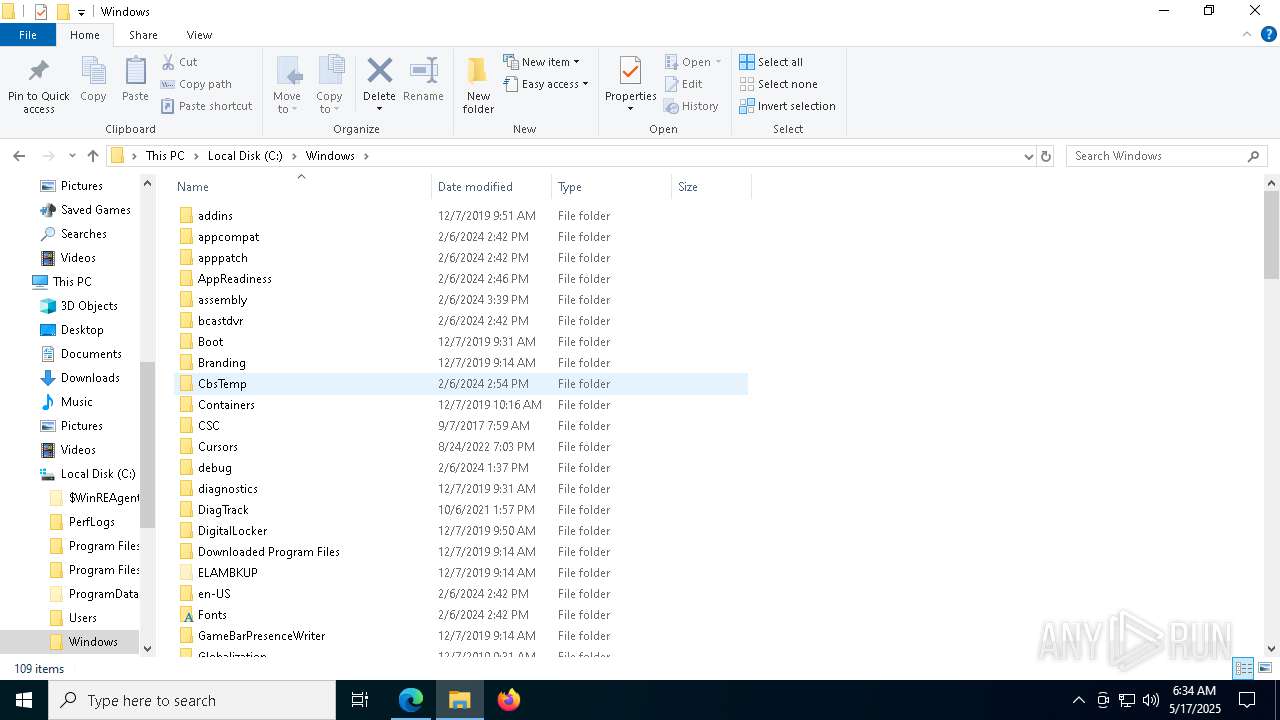
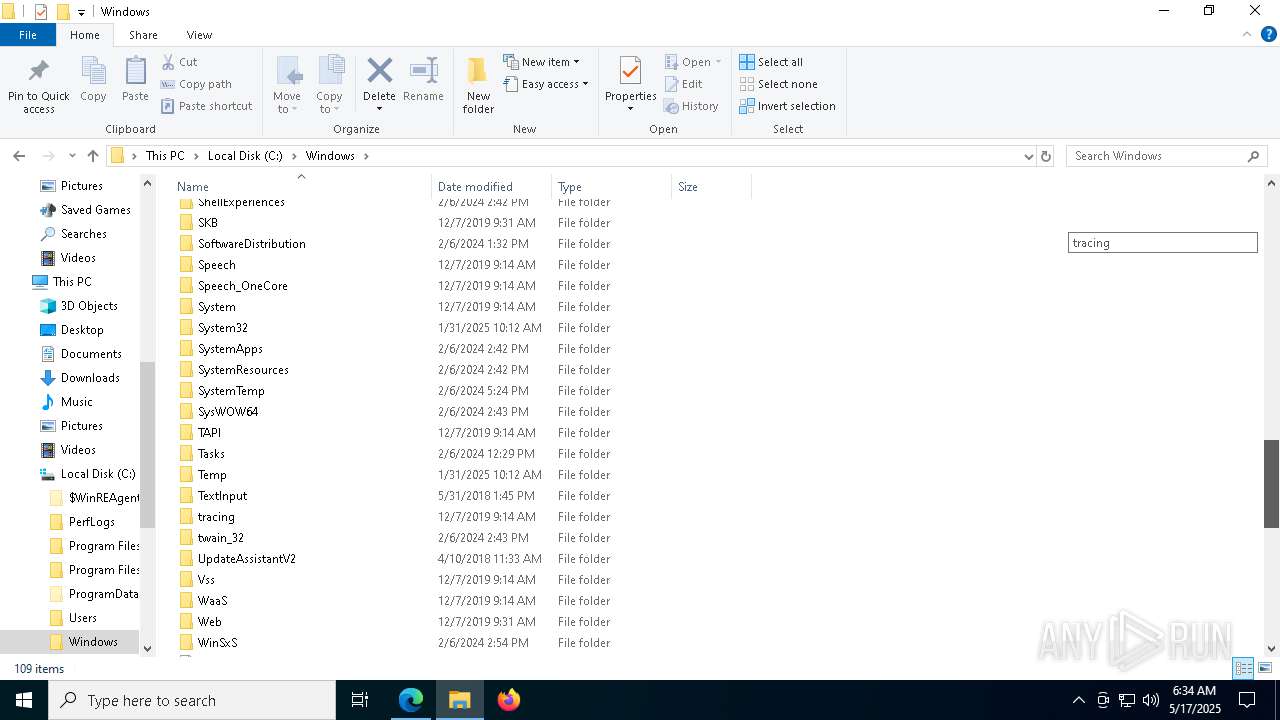
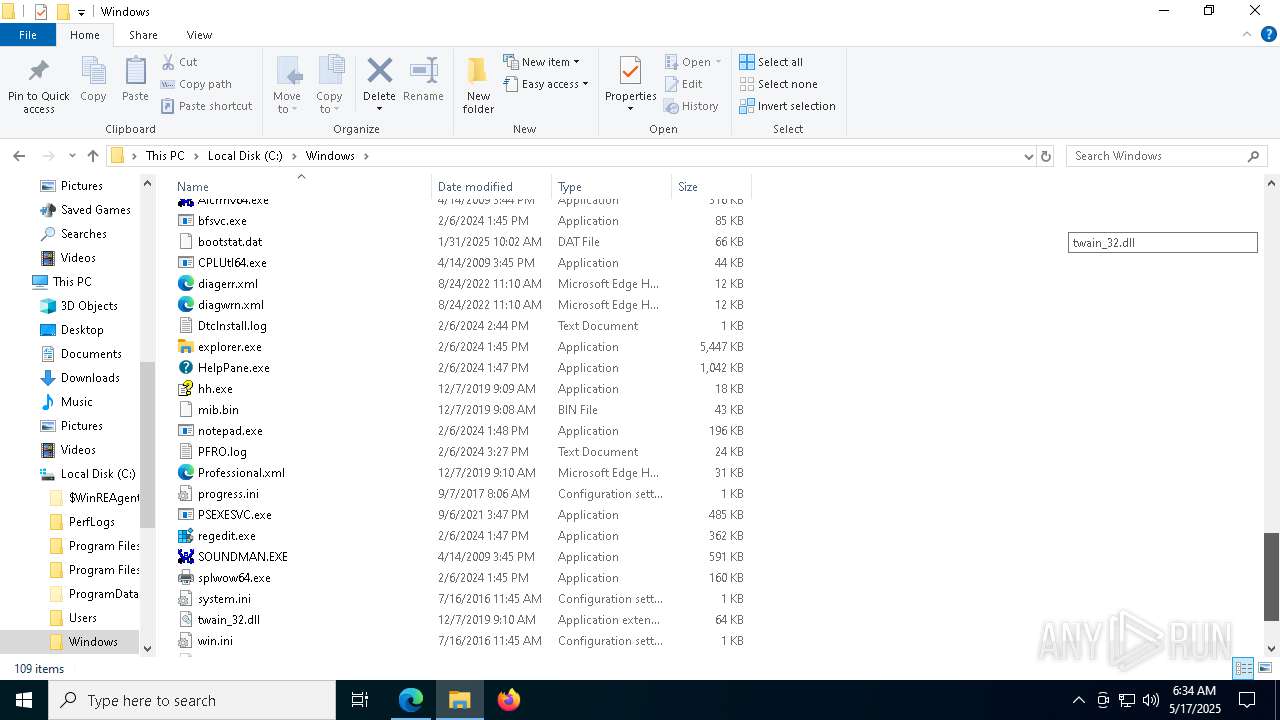
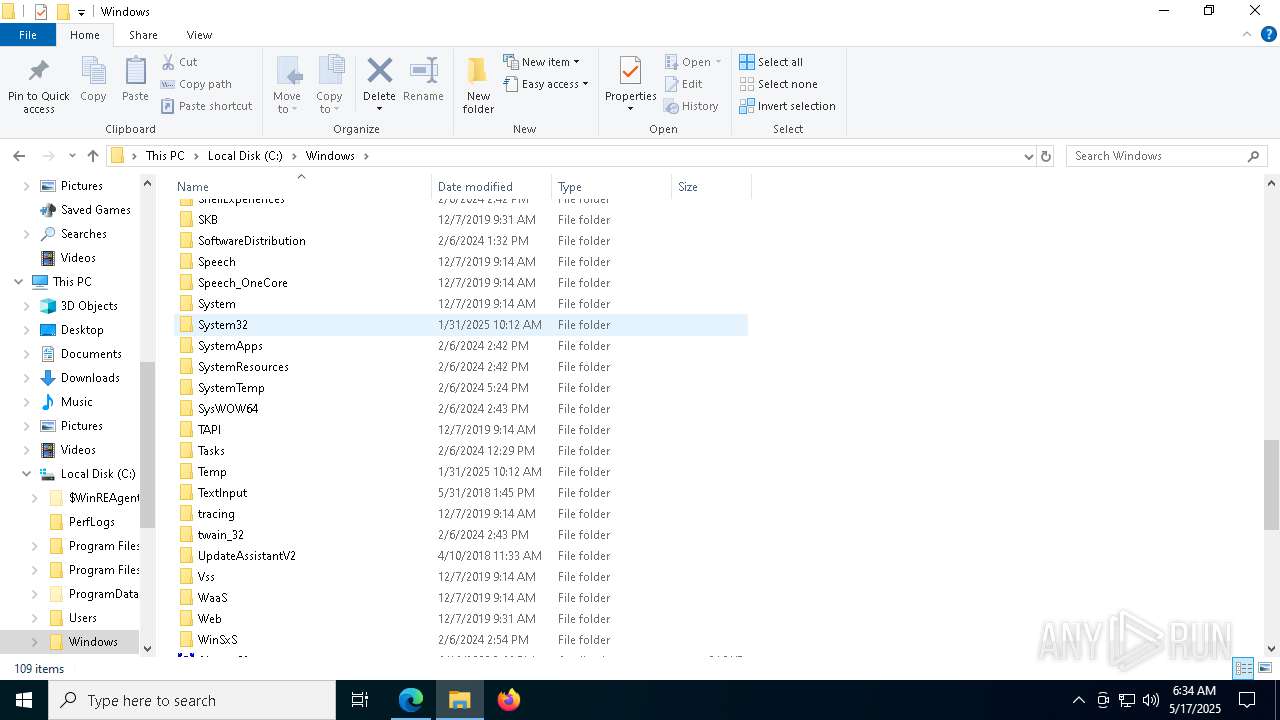
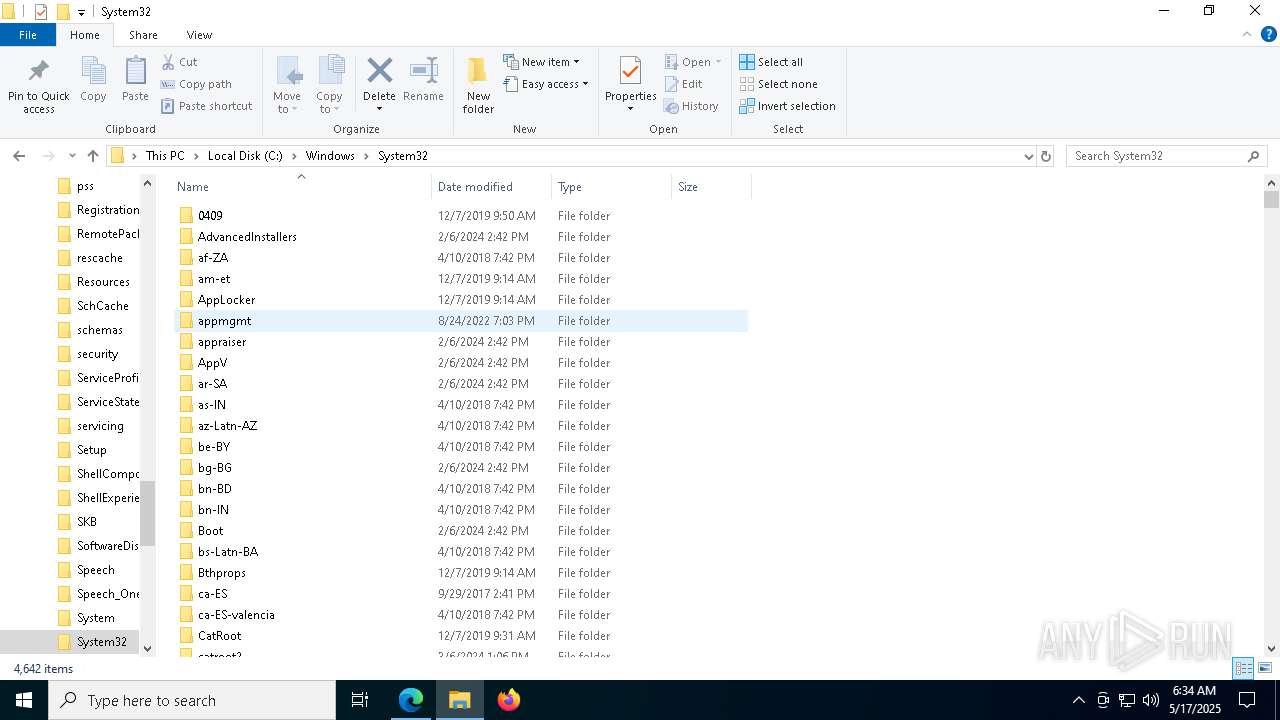
Creates a new folder (SCRIPT)
- cscript.exe (PID: 7224)
SUSPICIOUS
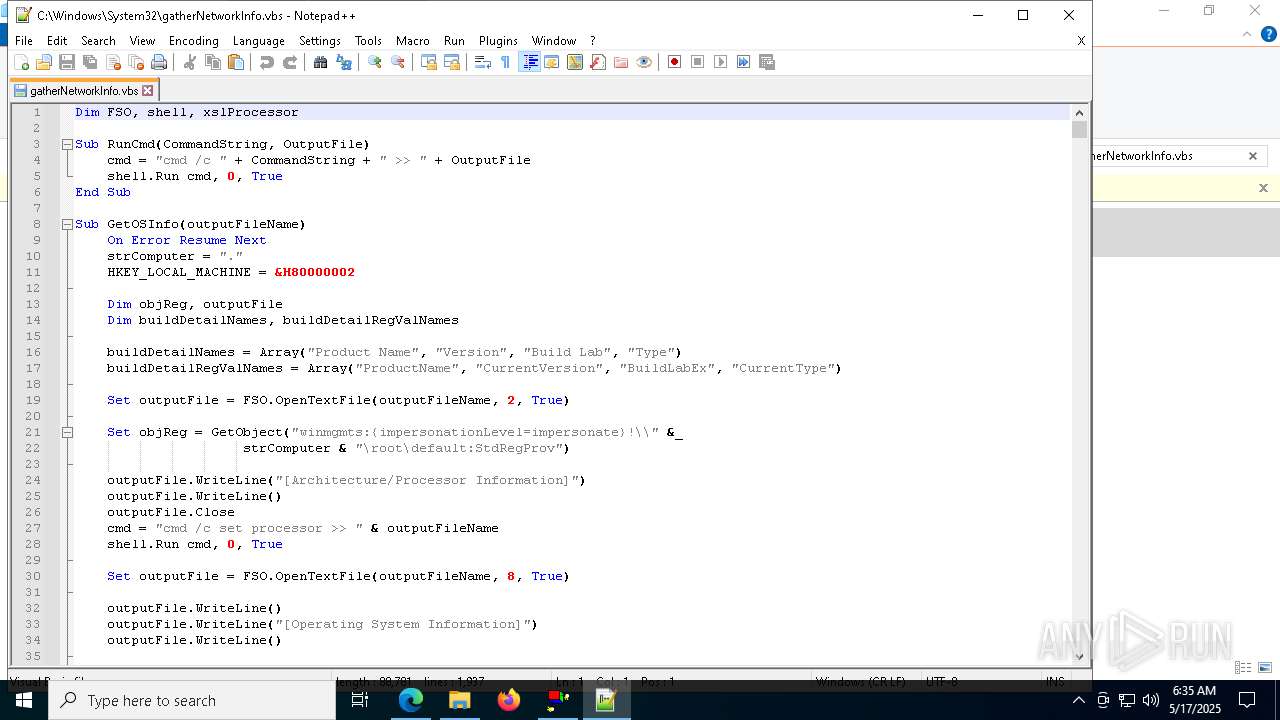
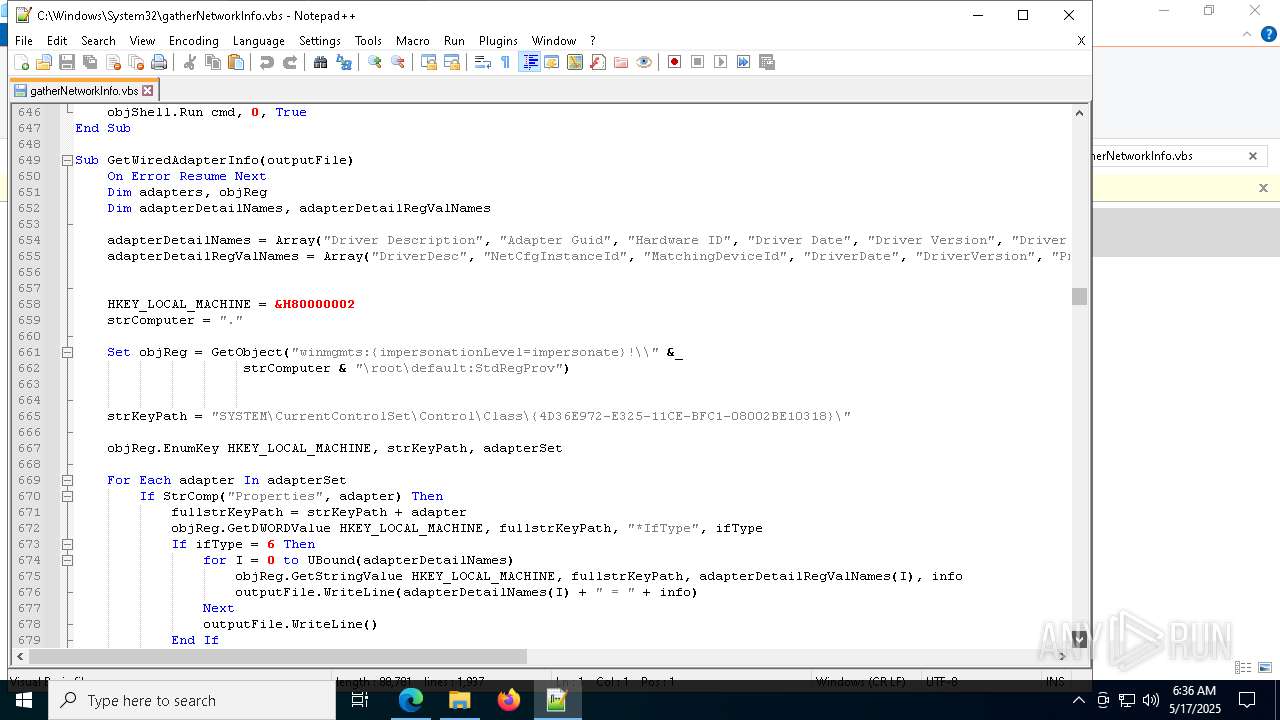
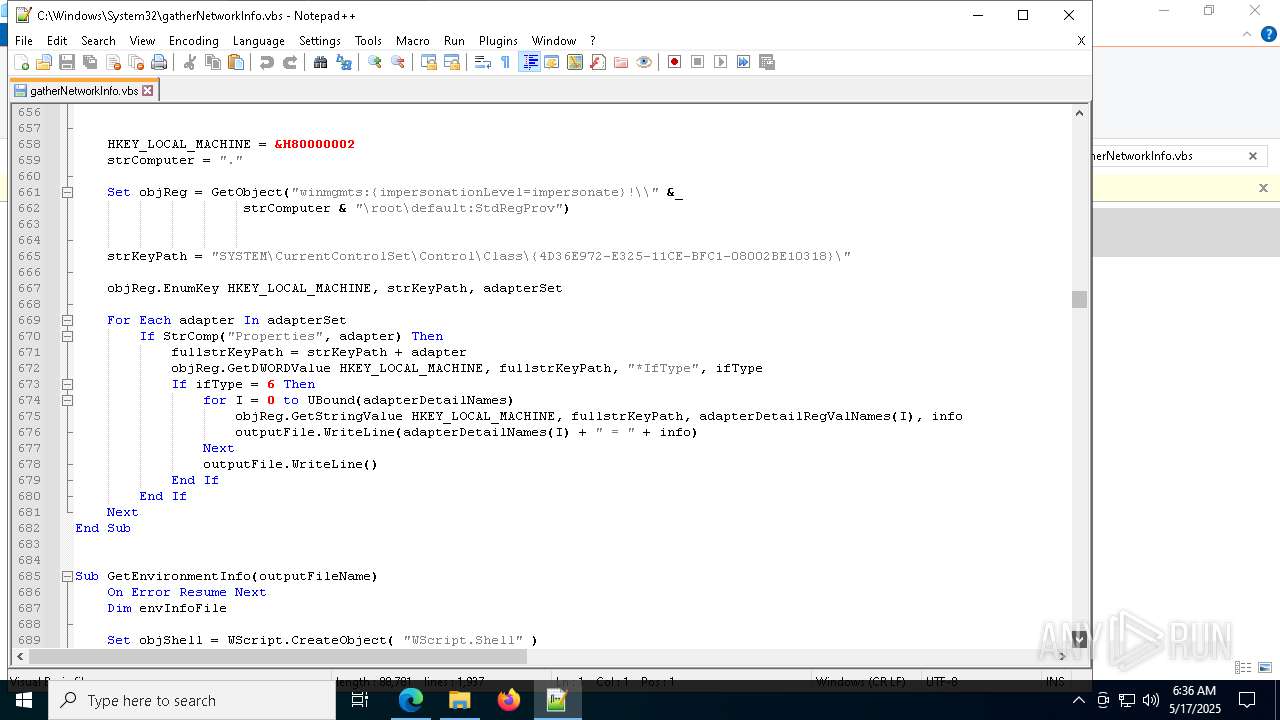
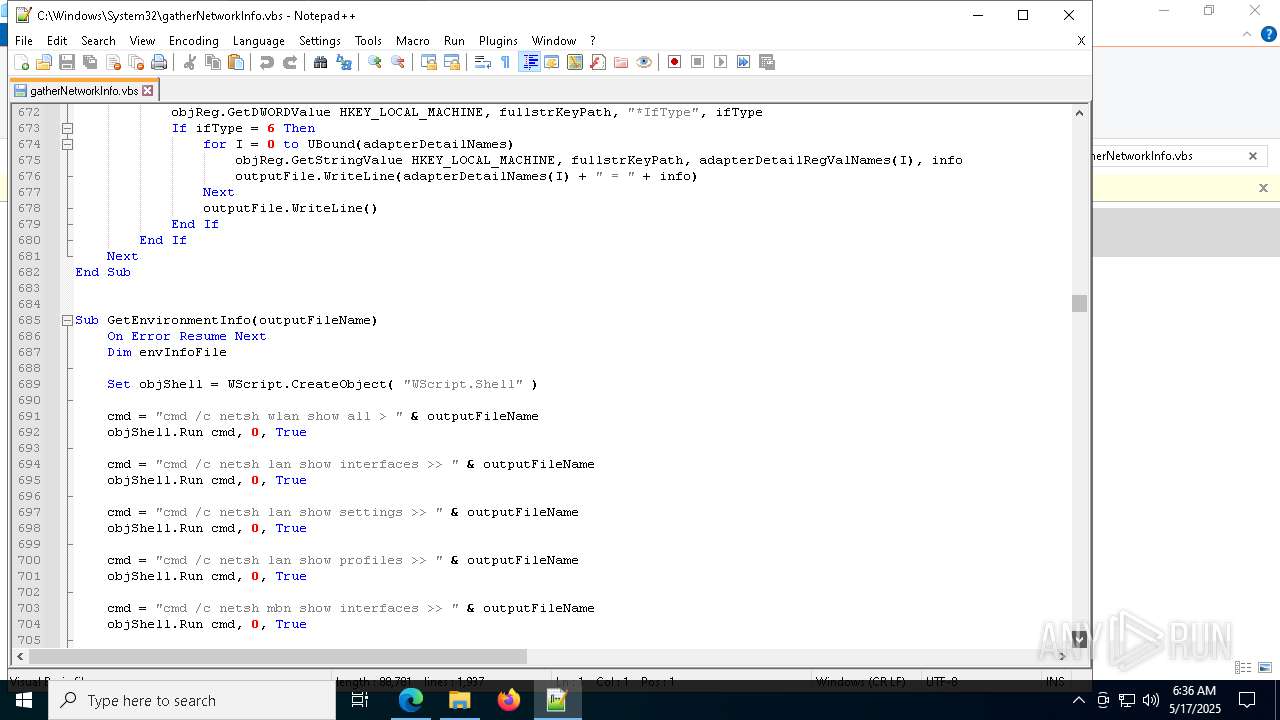
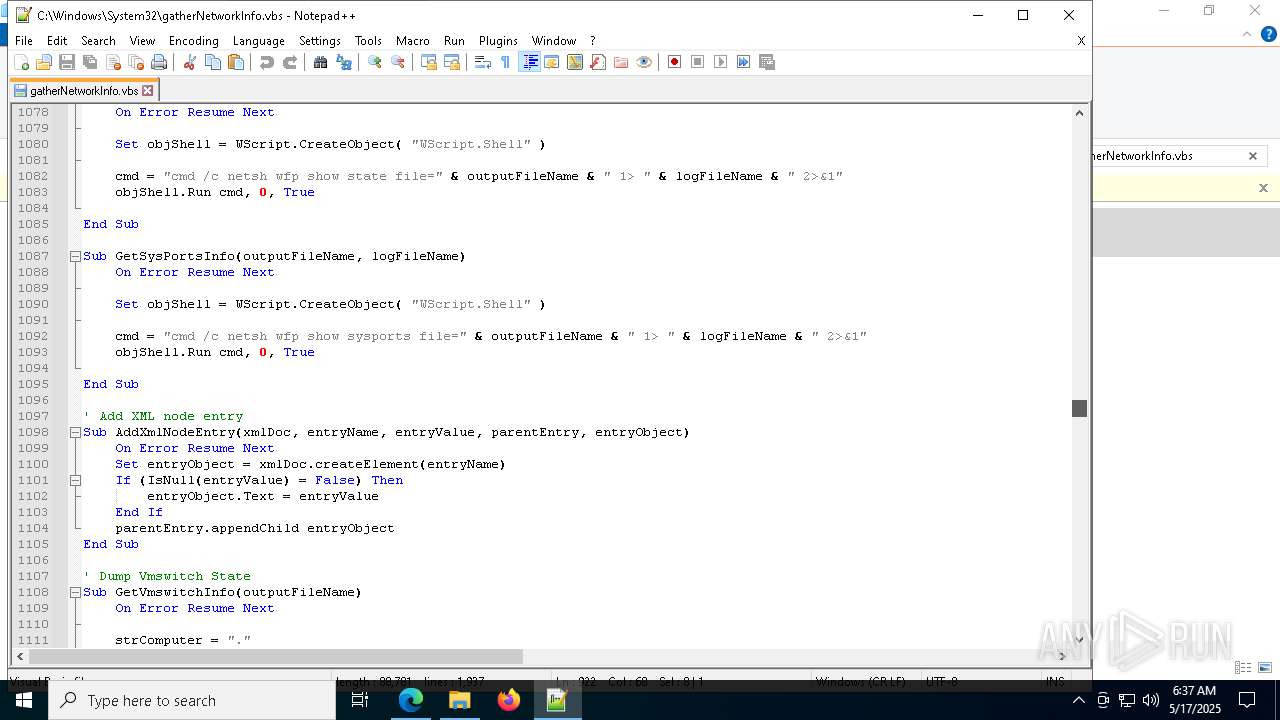
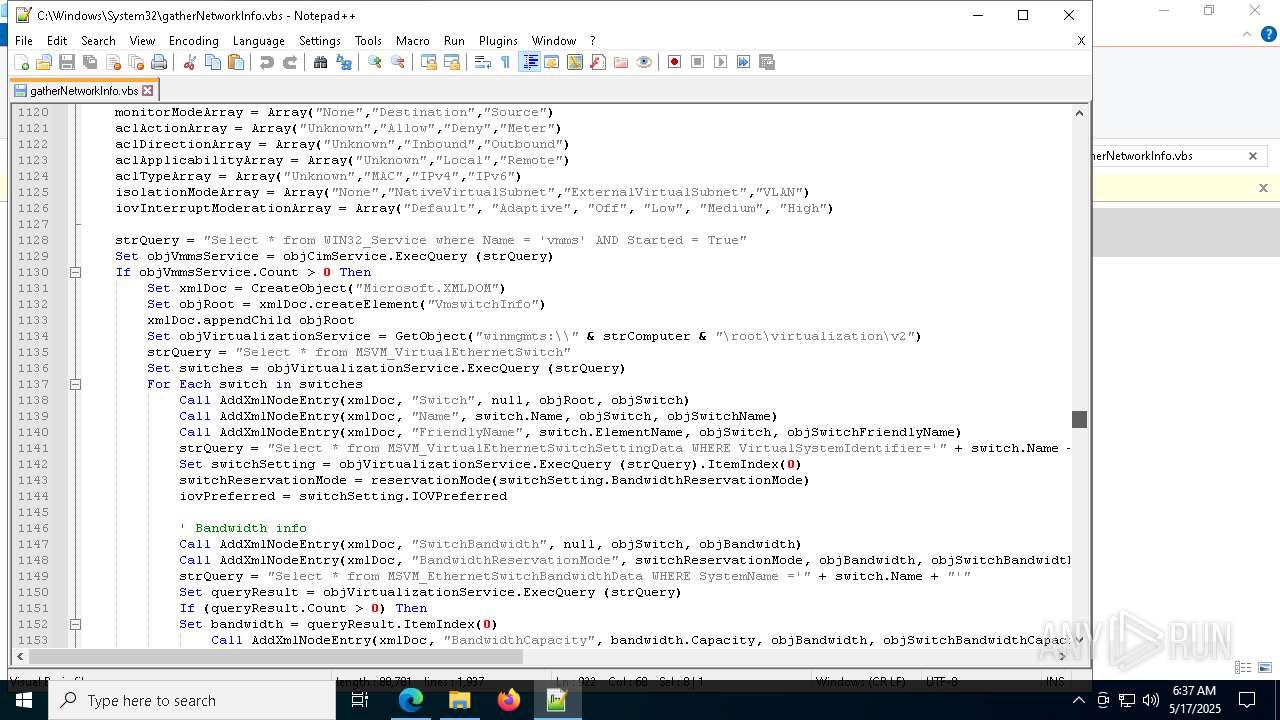
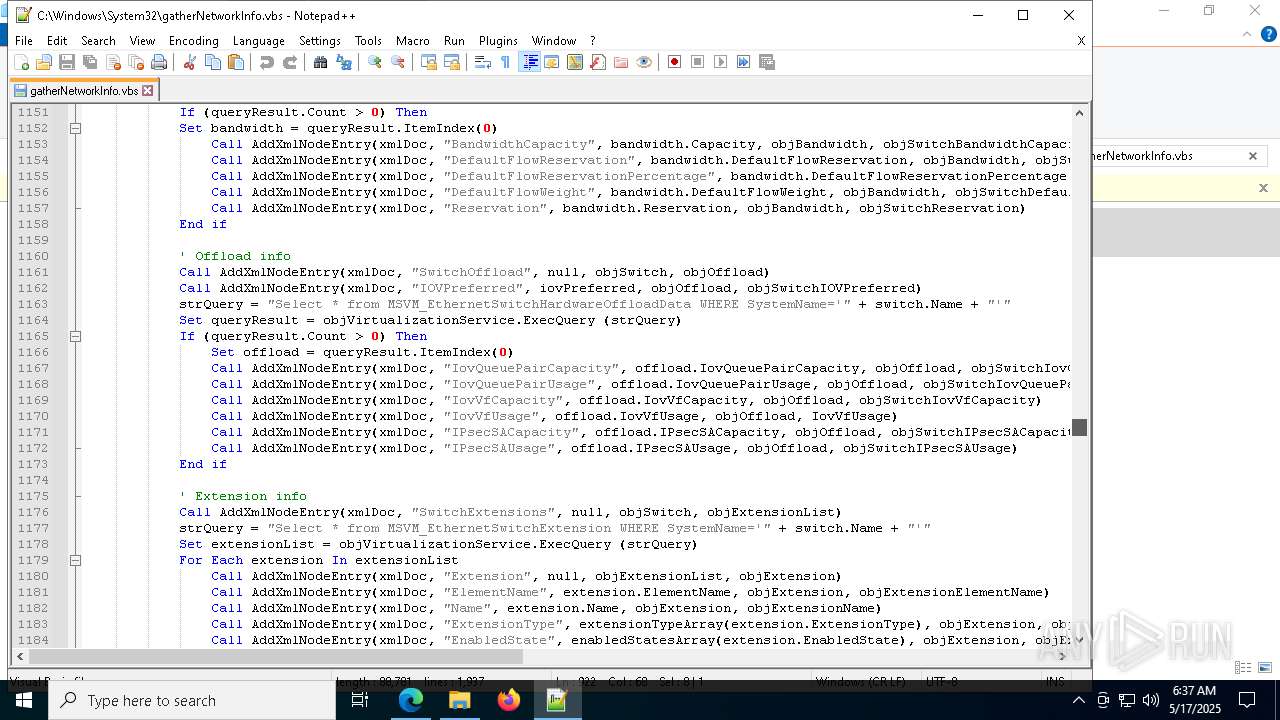
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7224)
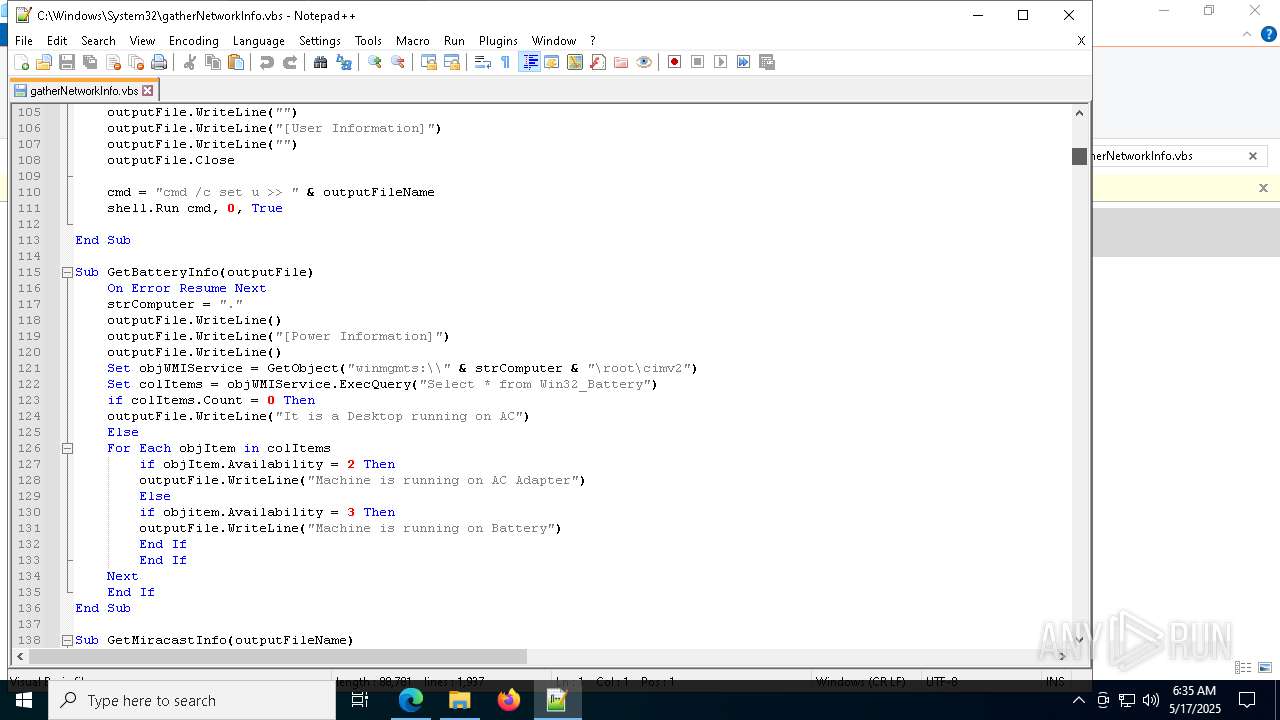
Starts CMD.EXE for commands execution
- cscript.exe (PID: 7224)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 3768)
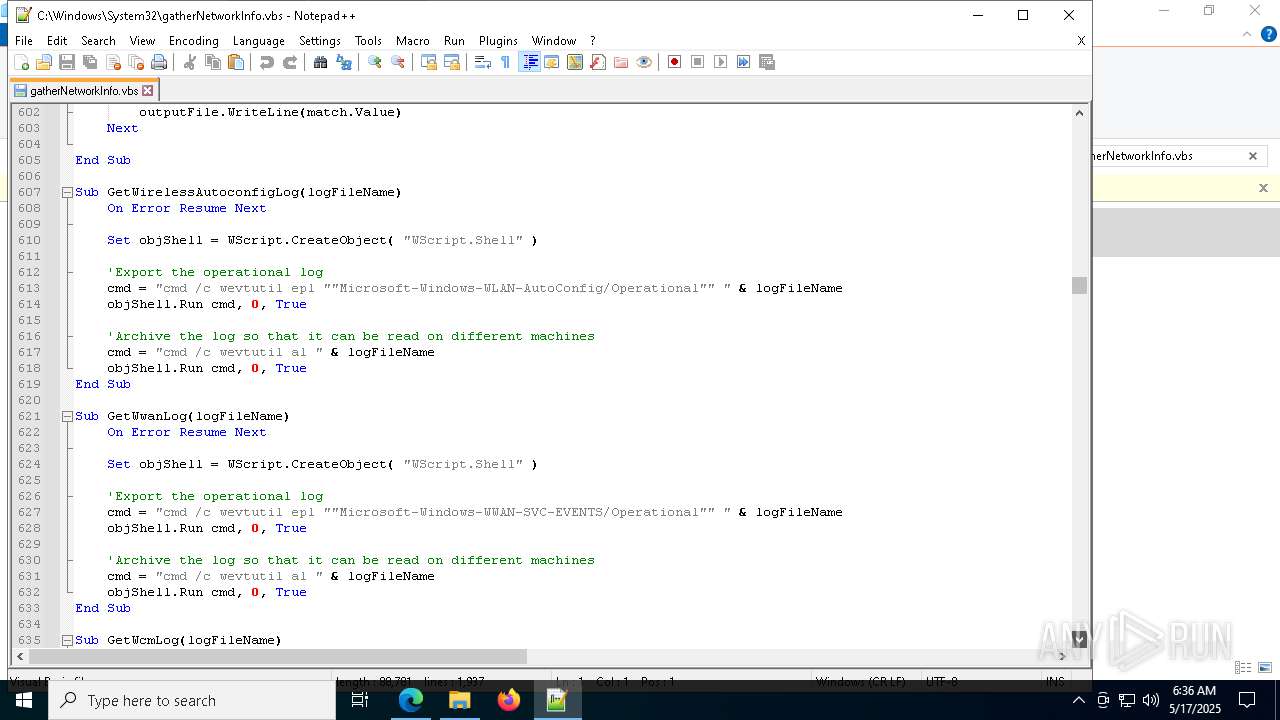
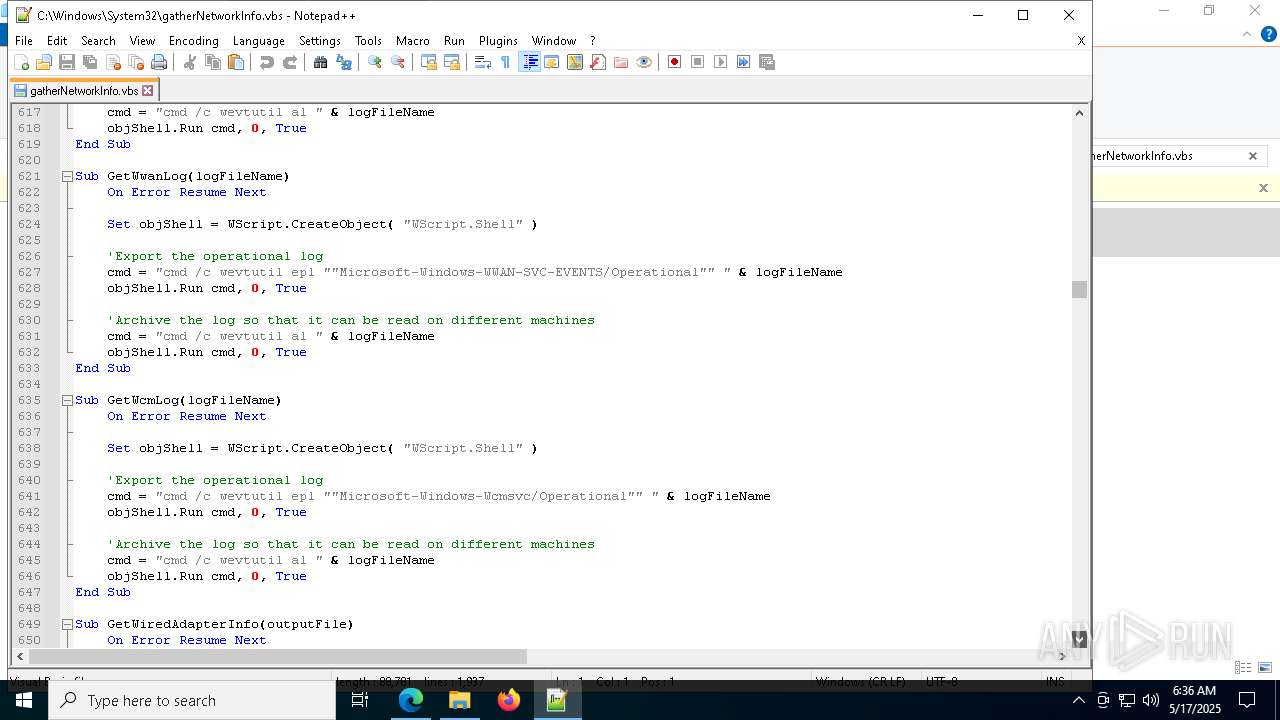
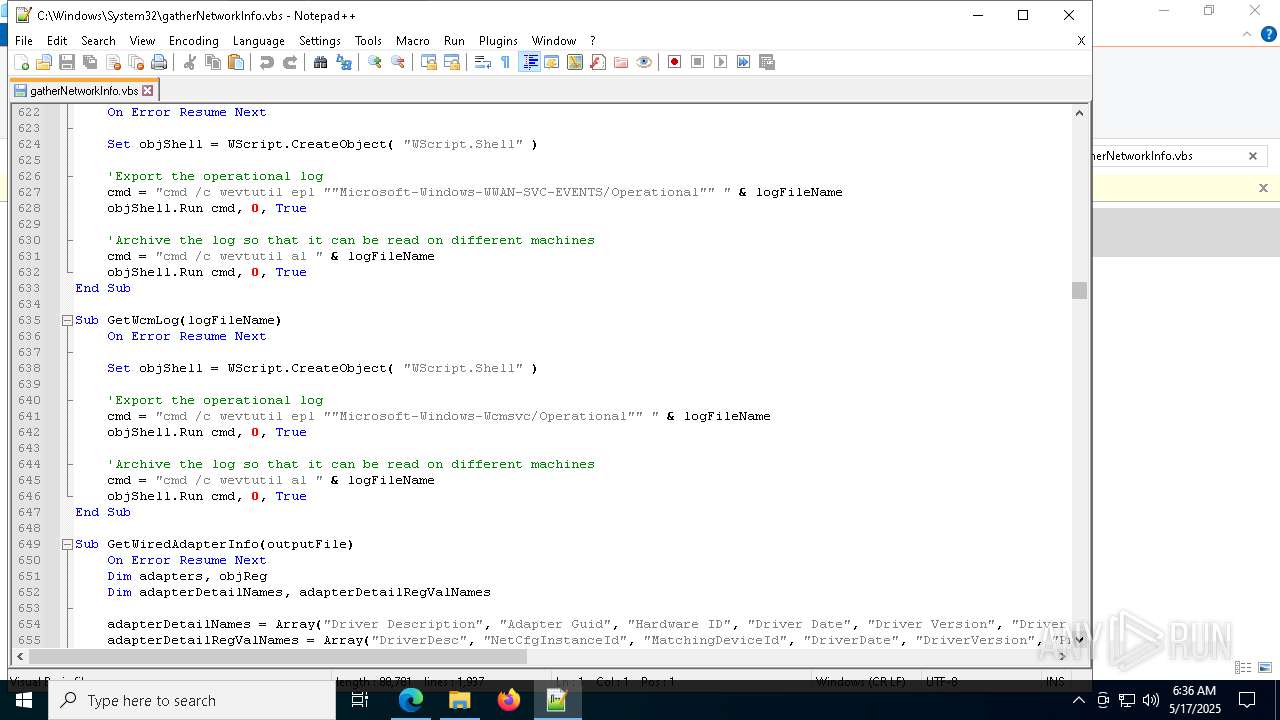
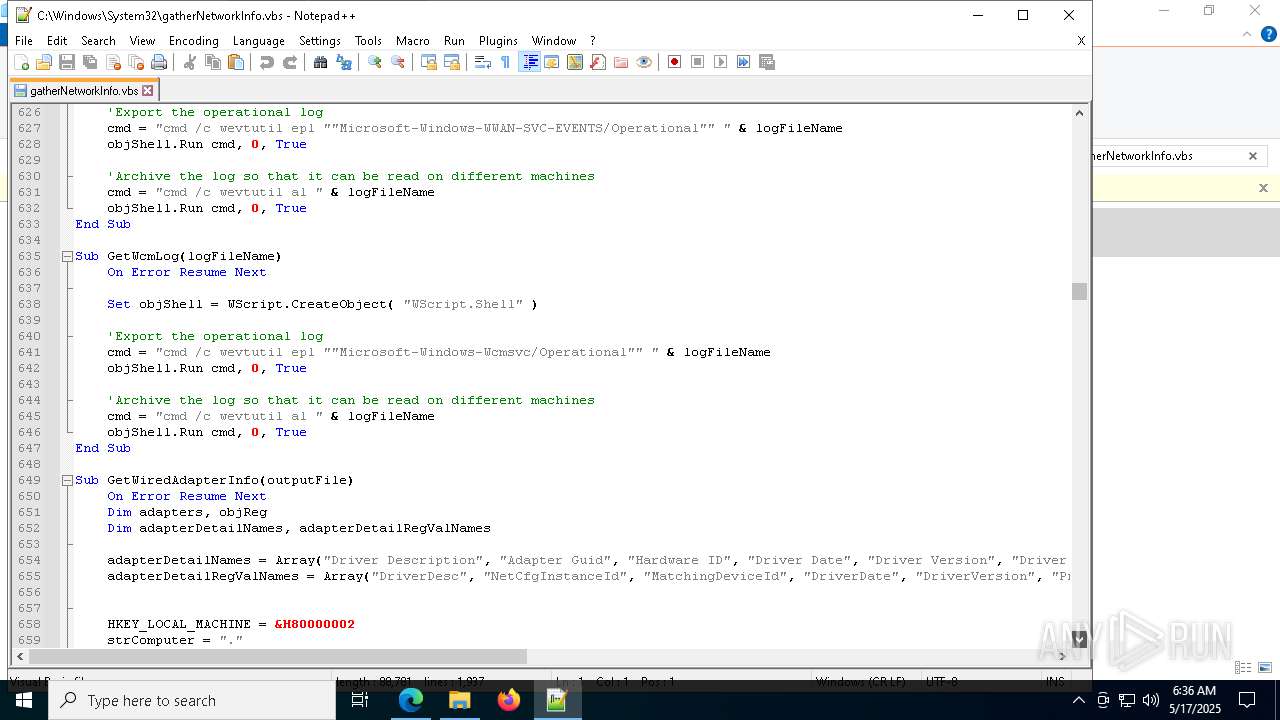
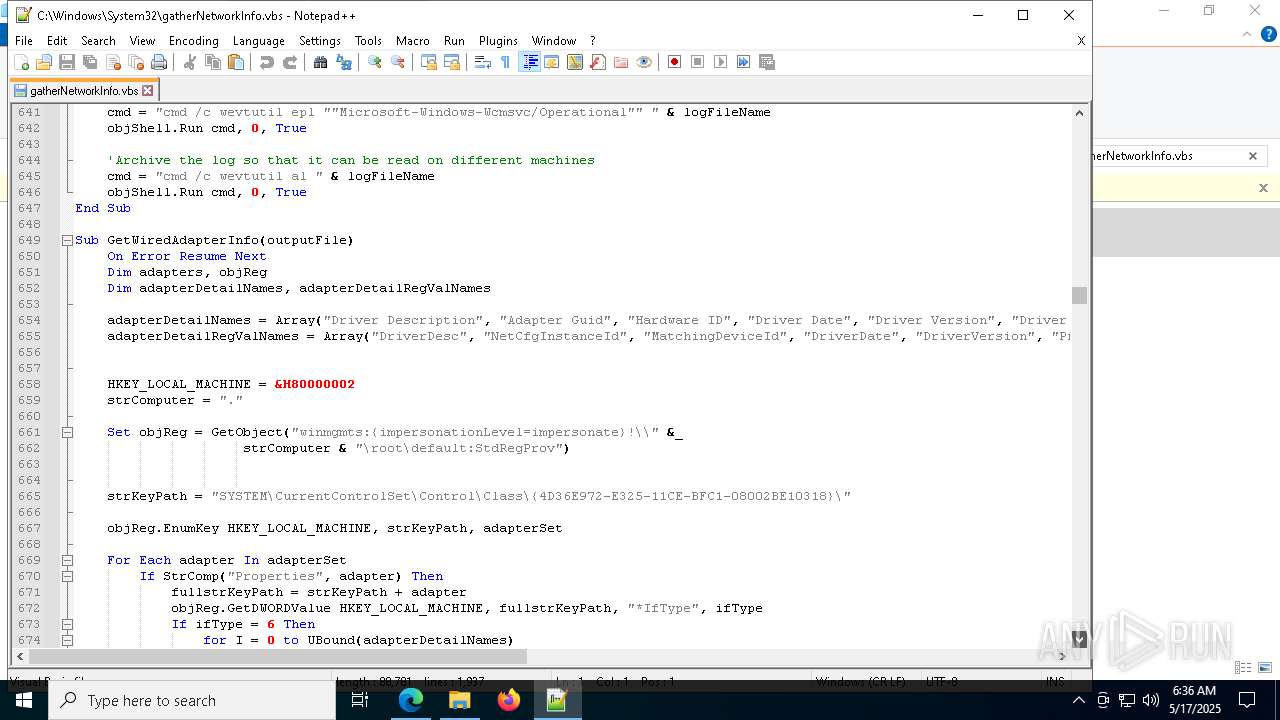
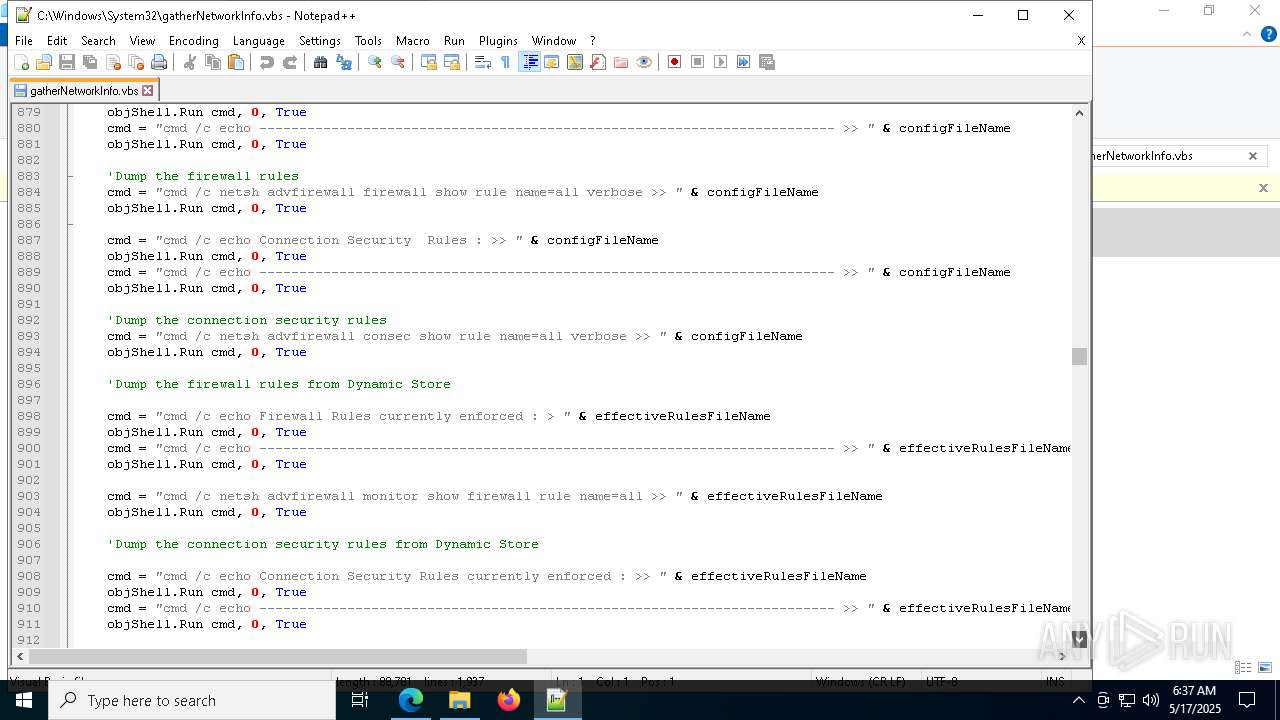
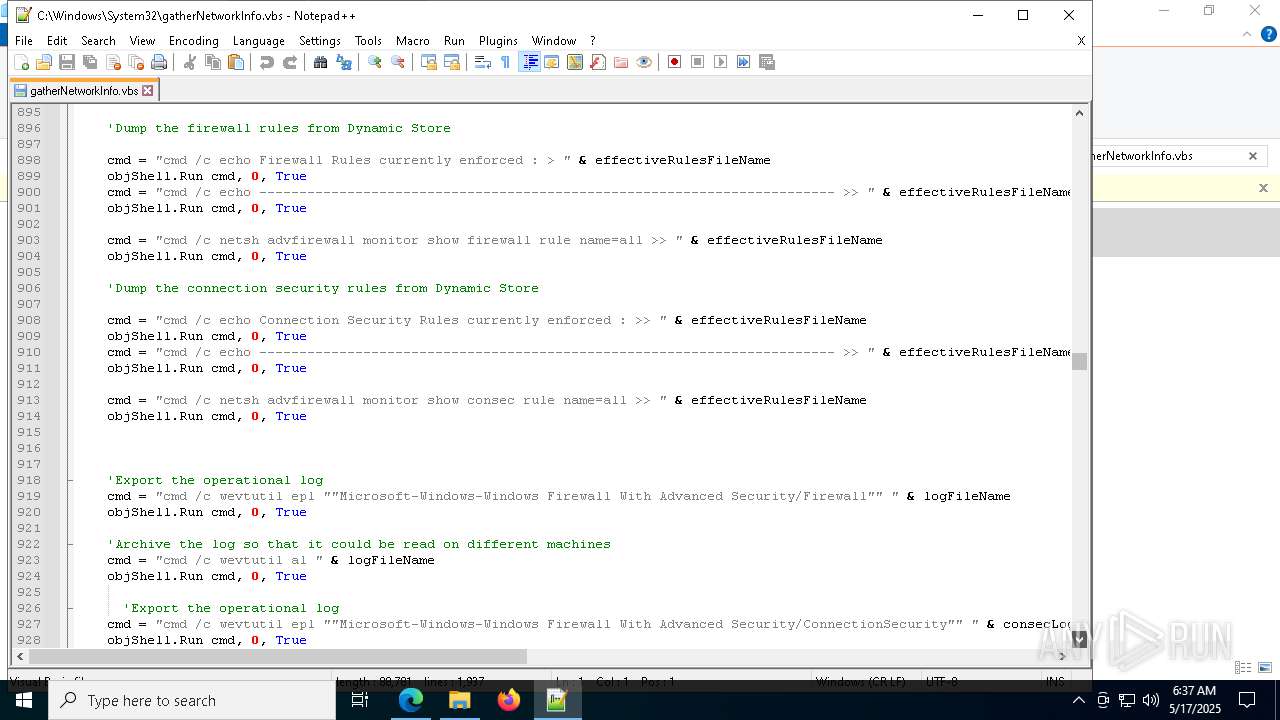
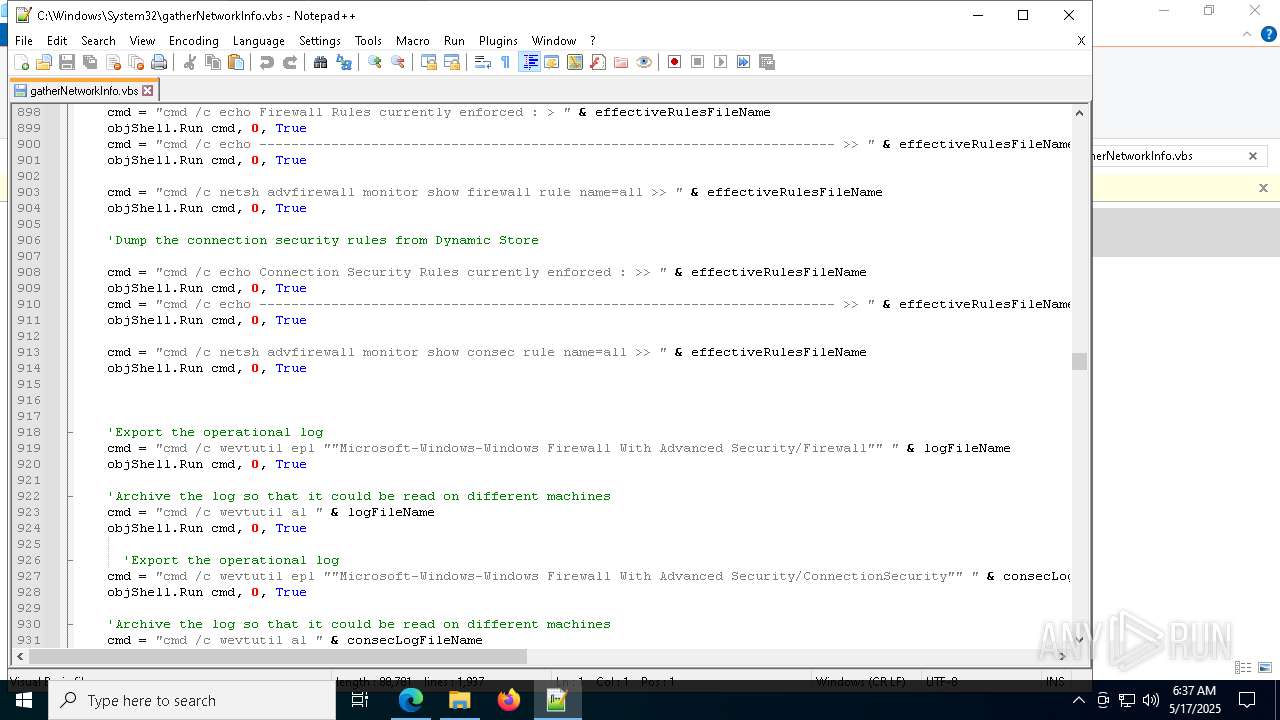
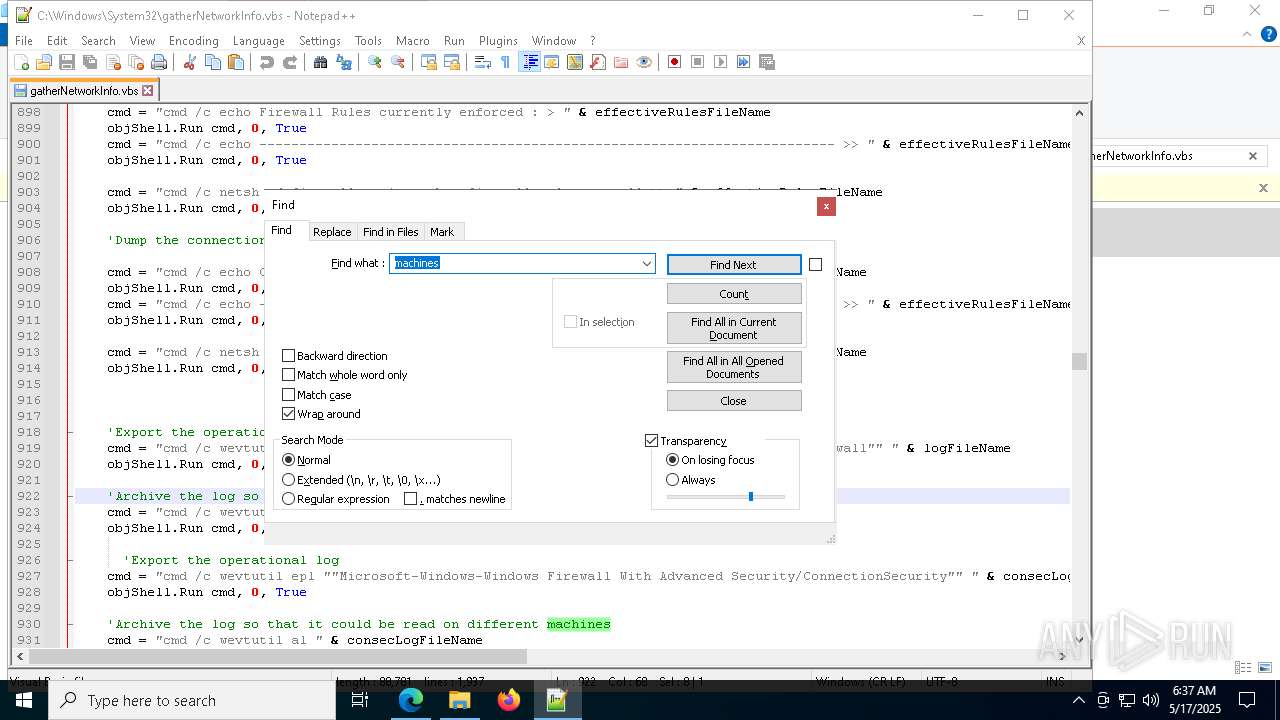
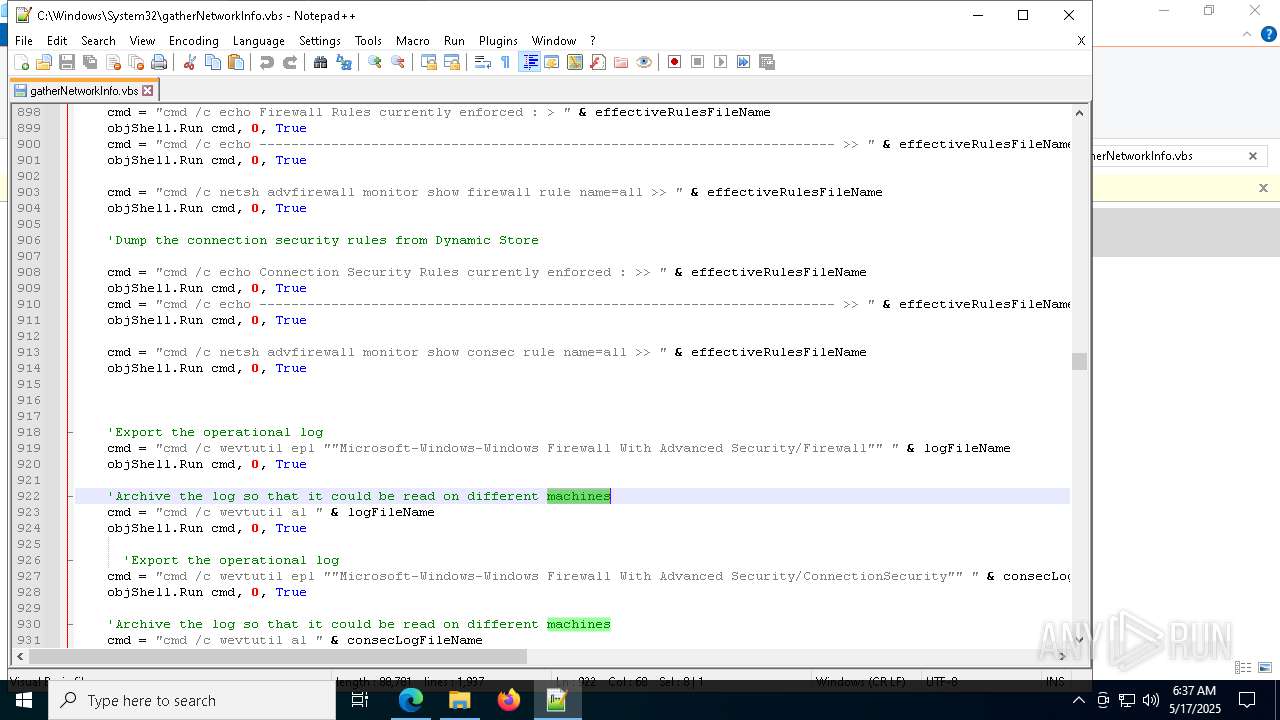
Uses WEVTUTIL.EXE to export log
- cmd.exe (PID: 3796)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 1600)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 8076)
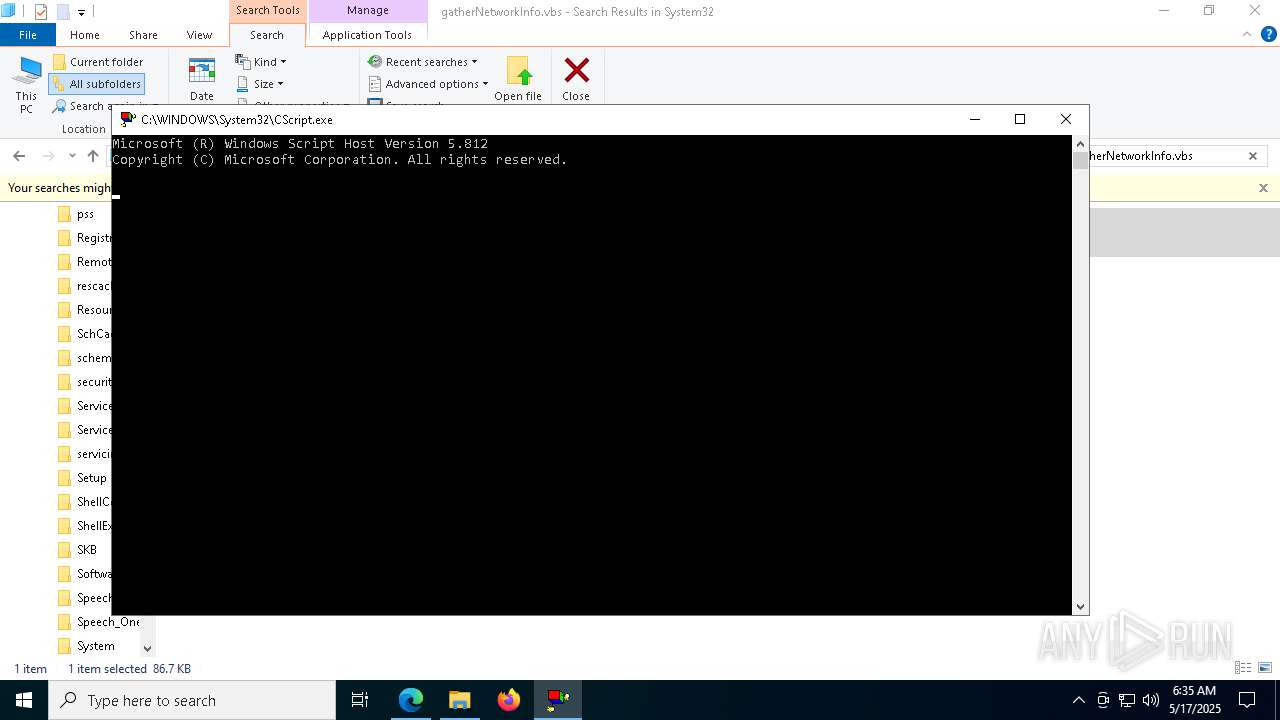
Runs shell command (SCRIPT)
- cscript.exe (PID: 7224)
Uses WEVTUTIL.EXE to archive the exported log
- cmd.exe (PID: 6512)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 7952)
Get information on the list of running processes
- cscript.exe (PID: 7224)
Executes application which crashes
- cscript.exe (PID: 7224)
INFO
Checks supported languages
- identity_helper.exe (PID: 1184)
Reads the computer name
- identity_helper.exe (PID: 1184)
Application launched itself
- msedge.exe (PID: 6040)
Reads the software policy settings
- slui.exe (PID: 7680)
Reads Environment values
- identity_helper.exe (PID: 1184)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7224)
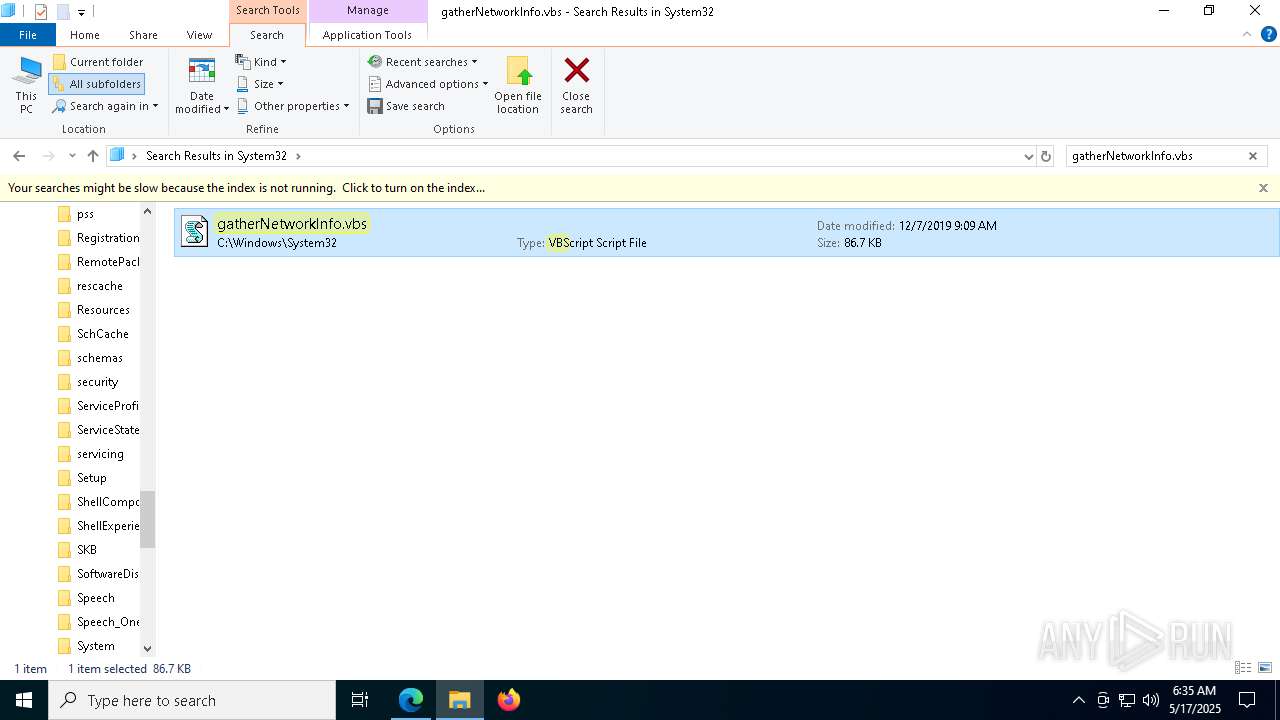
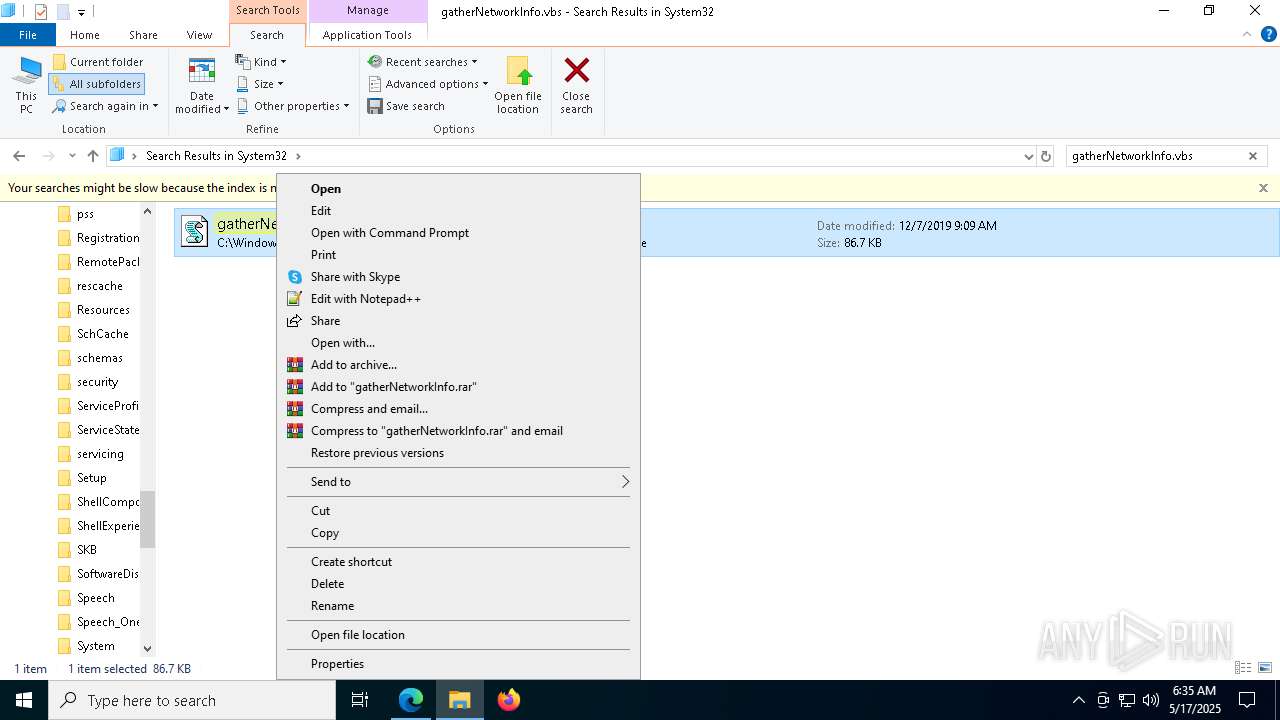
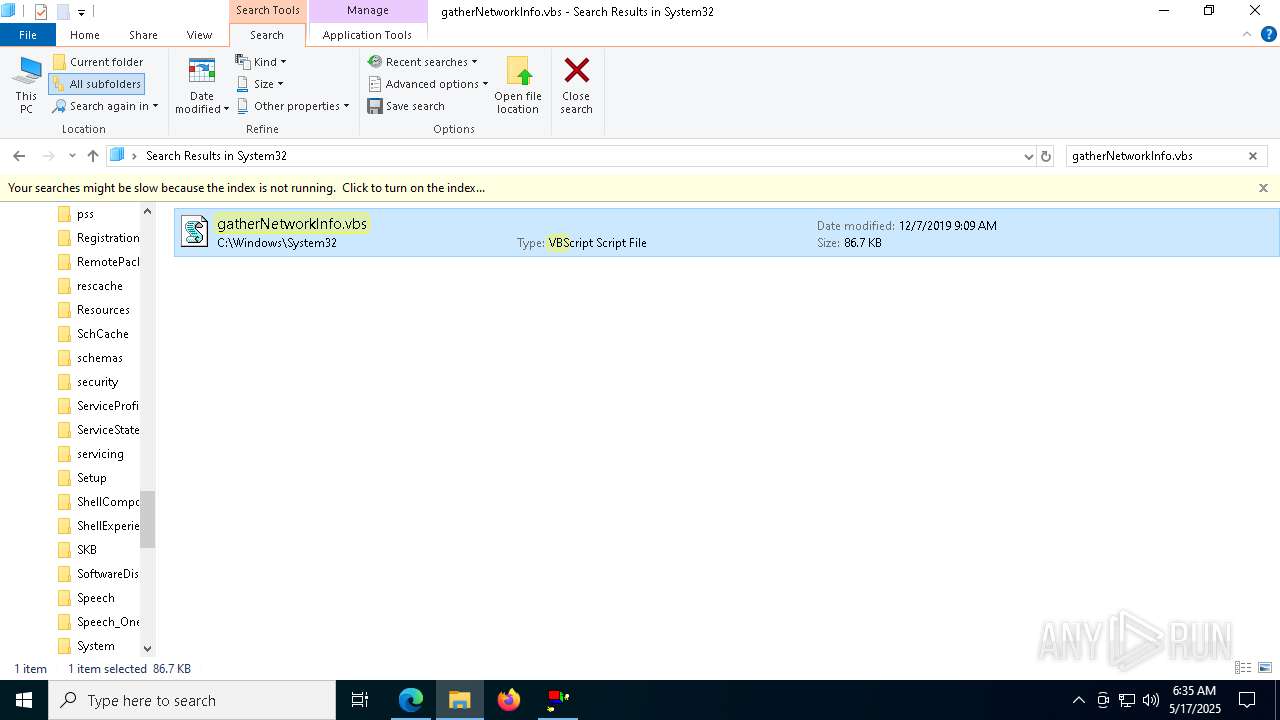
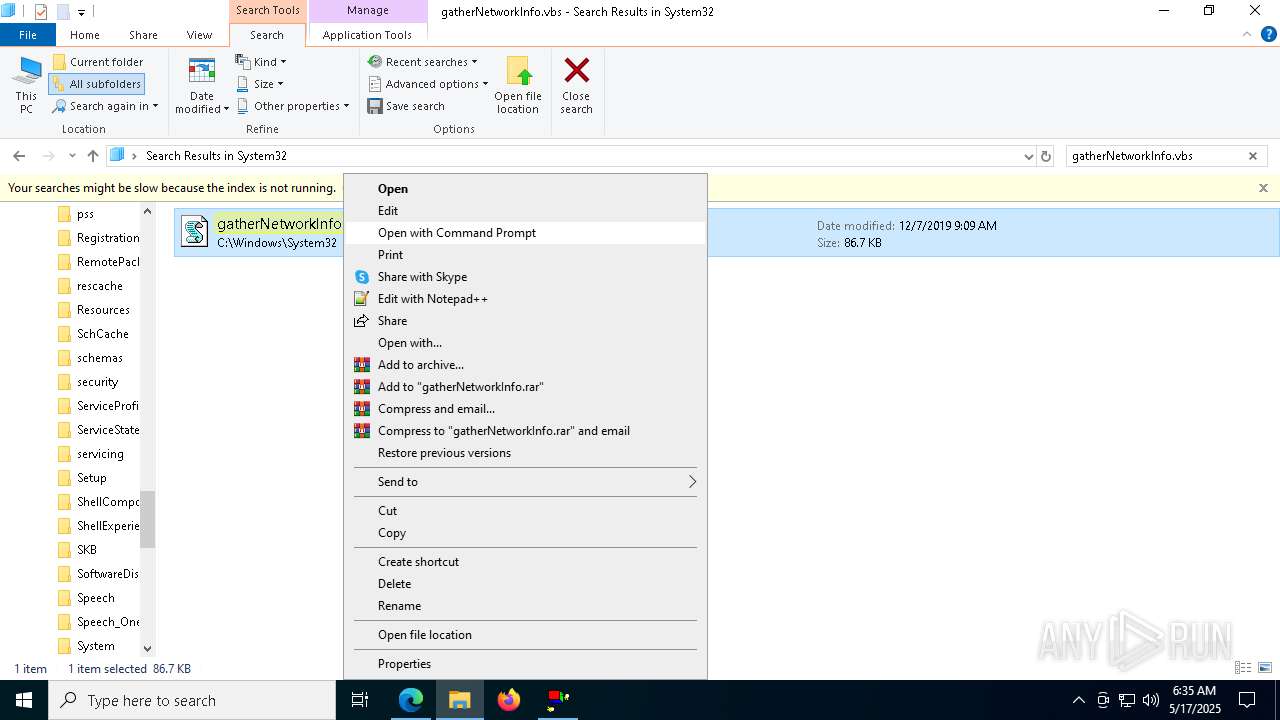
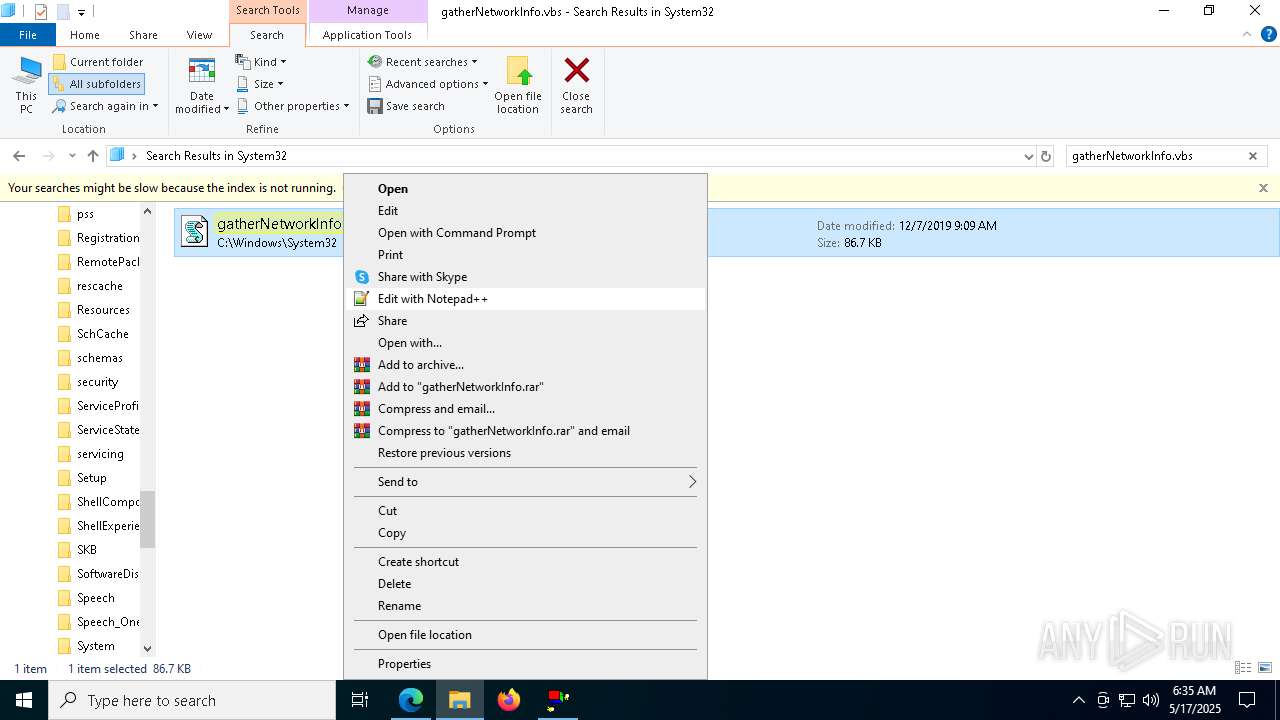
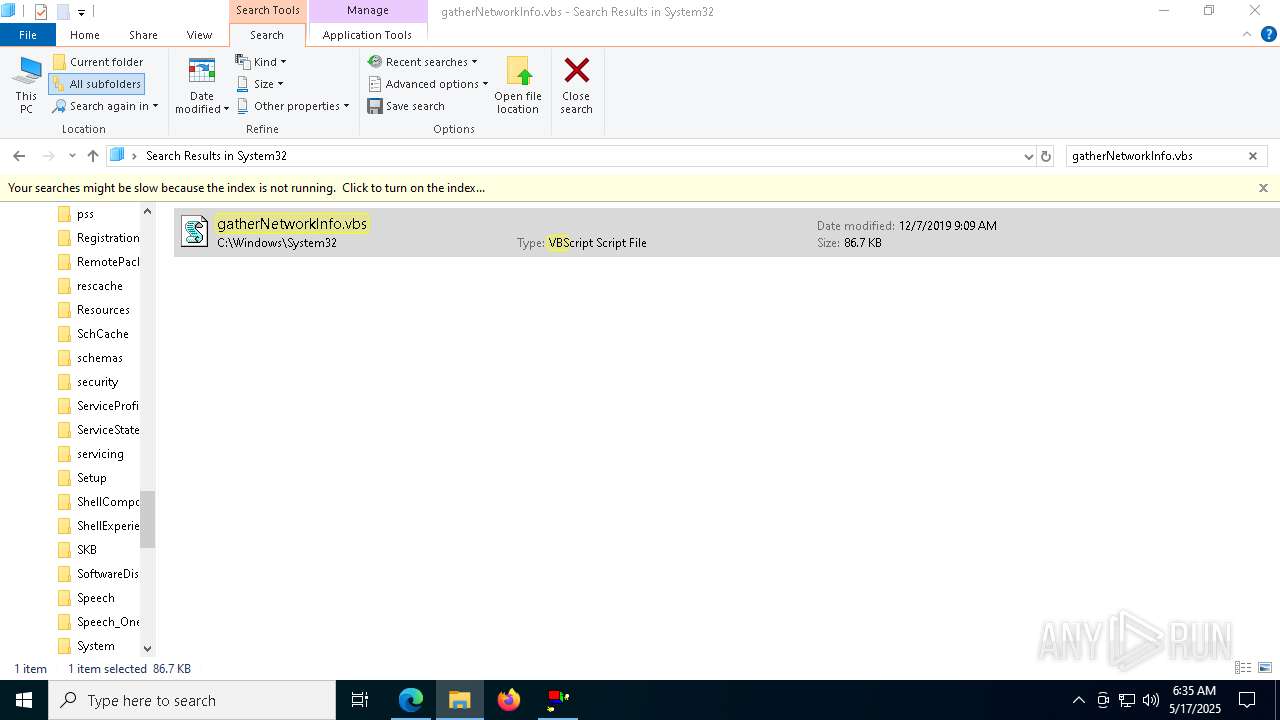
Manual execution by a user
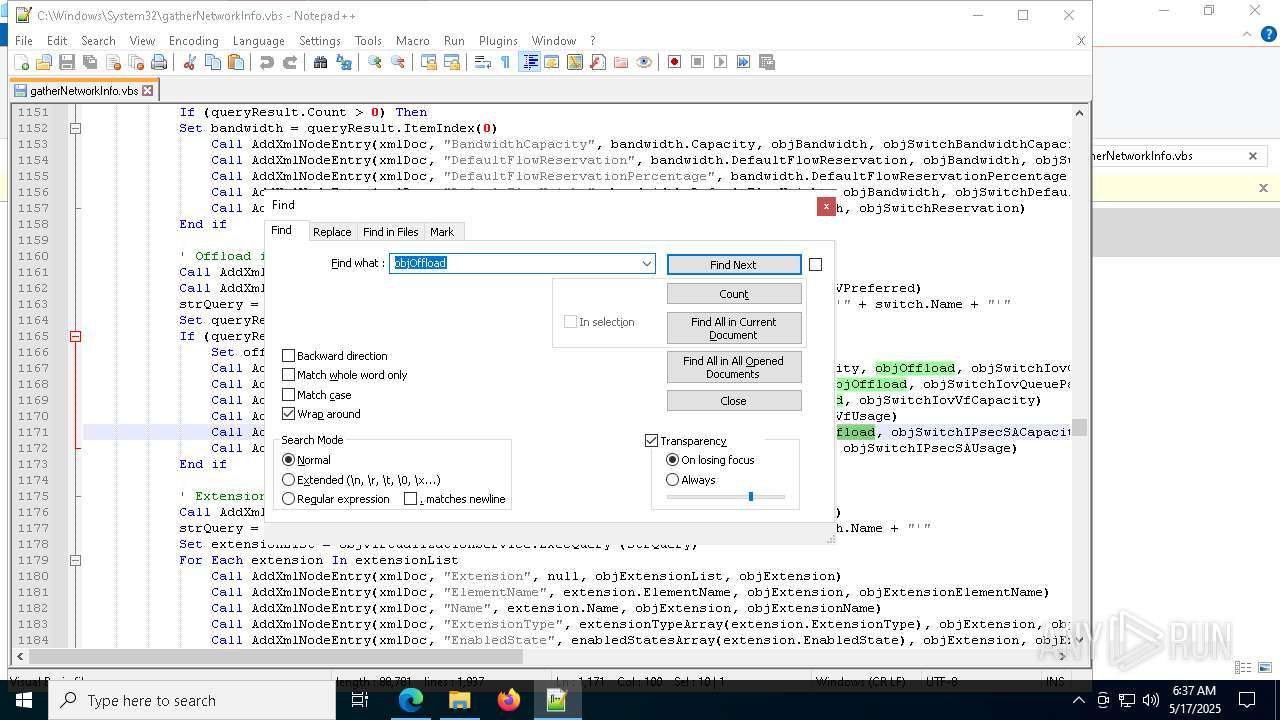
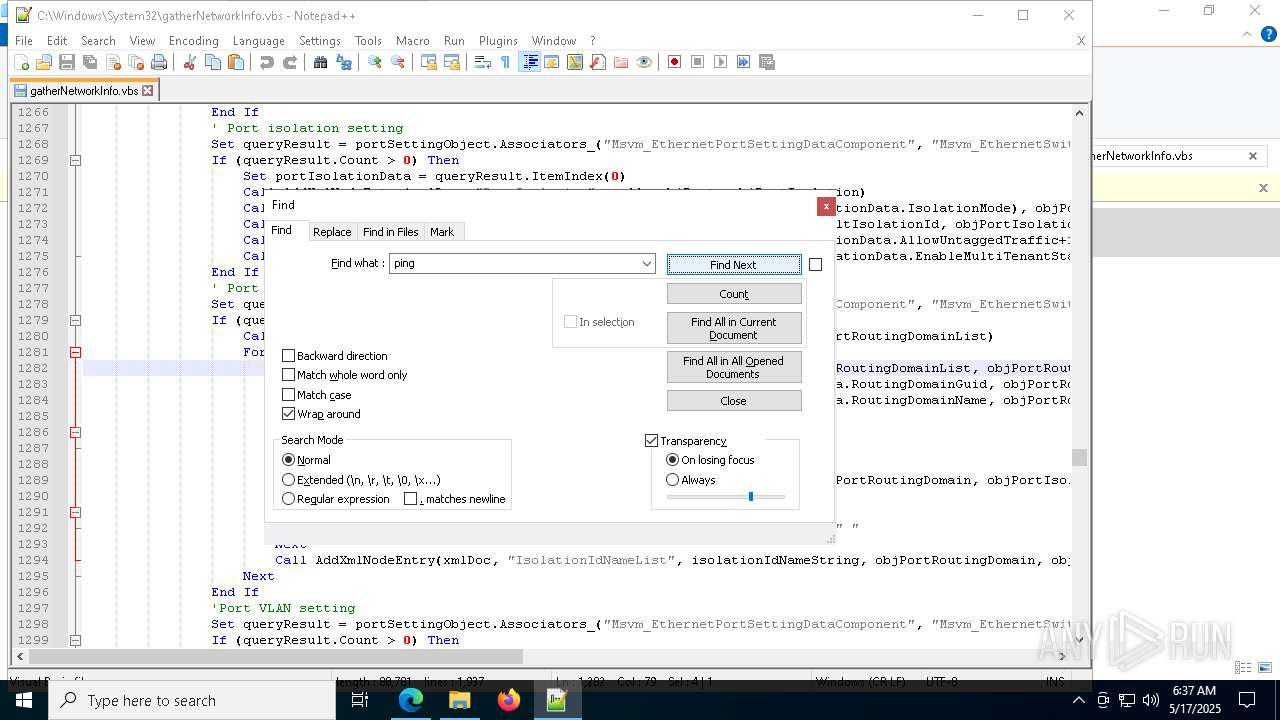
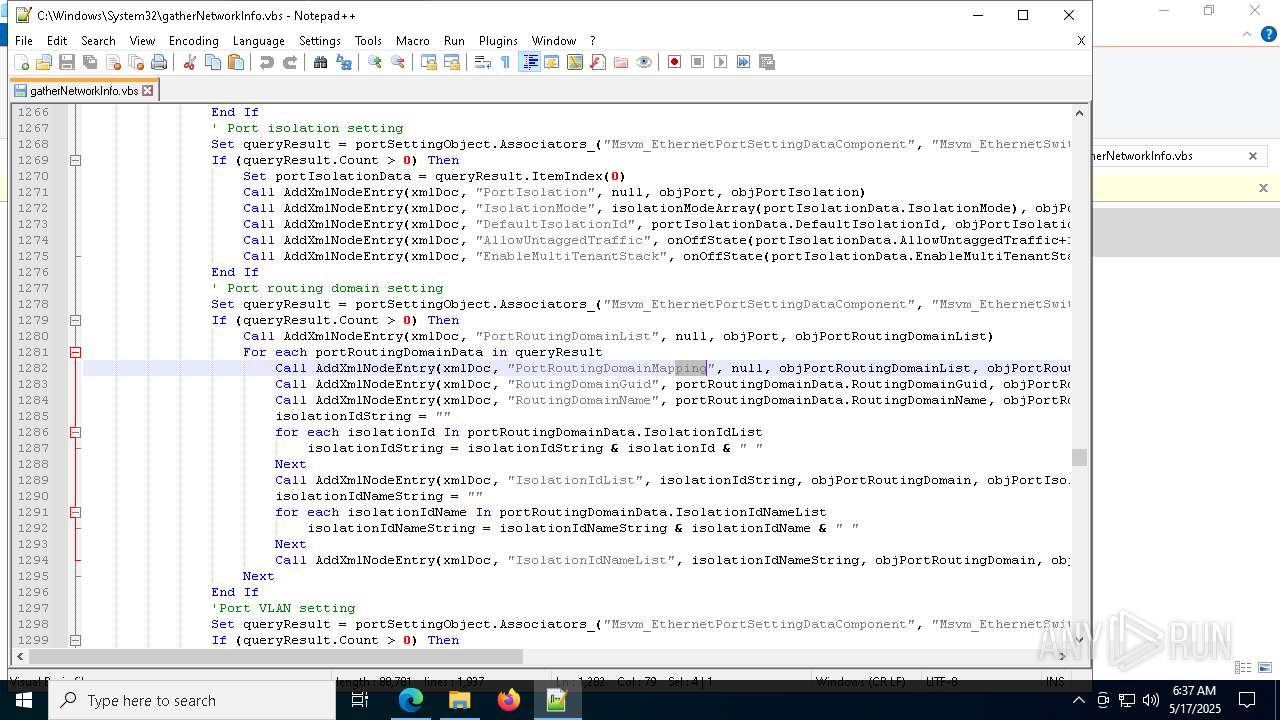
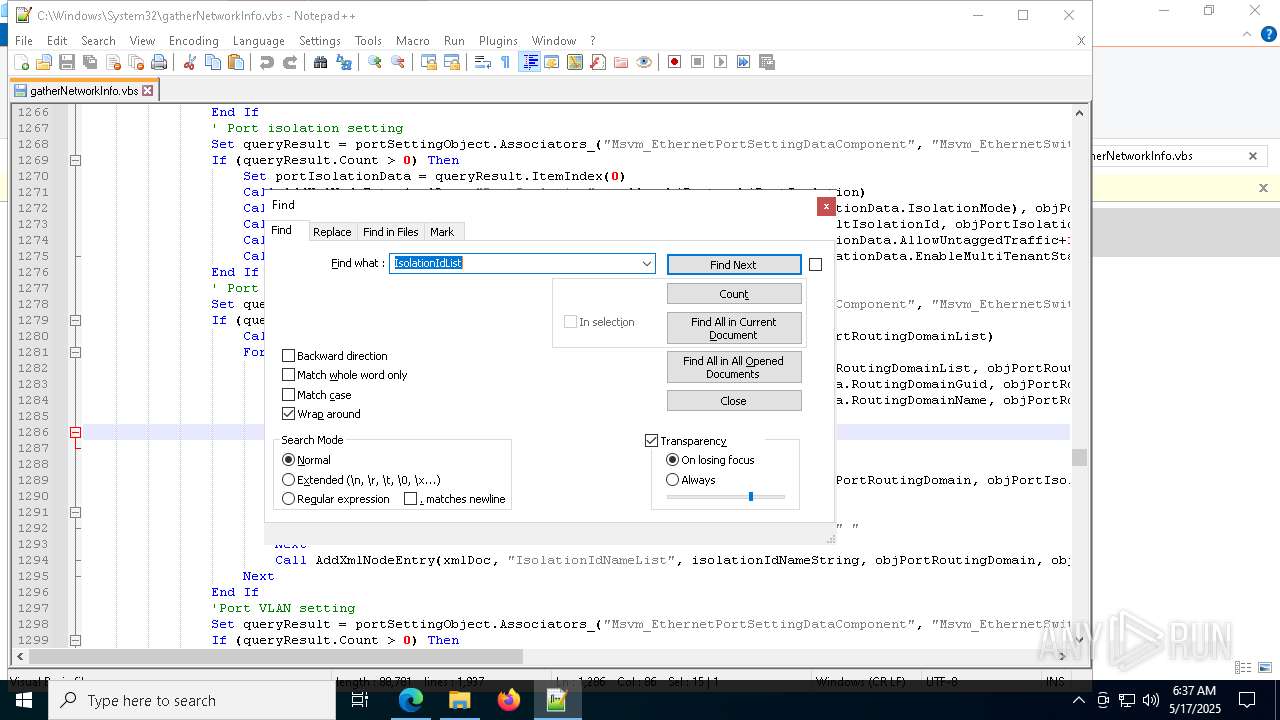
- cscript.exe (PID: 7224)
- notepad++.exe (PID: 5188)
The sample compiled with english language support
- msedge.exe (PID: 6972)
Executable content was dropped or overwritten
- msedge.exe (PID: 6972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
416
Monitored processes
278
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Windows\System32\cmd.exe" /c certutil -v -store -silent -user My >> config\envinfo.txt | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | wevtutil al config\WCMLog.evtx | C:\Windows\System32\wevtutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Eventing Command Line Utility Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6948 --field-trial-handle=1948,i,11402451219974256979,5665856888969007330,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\cmd.exe" /c echo Firewall Rules currently enforced : > config\WindowsFirewallEffectiveRules.txt | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | wevtutil epl "Microsoft-Windows-Windows Firewall With Advanced Security/Firewall" config\WindowsFirewallLog.evtx | C:\Windows\System32\wevtutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Eventing Command Line Utility Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 965
Read events
19 837
Write events
107
Delete events
21
Modification events
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6BFE935DE5932F00 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D7D9E5DE5932F00 | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {96E2EED2-D289-46CC-AFCF-305829381E45} | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {903F632B-5D6F-4A3A-962C-141D656B7DF0} | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {67DF9CE8-5E16-4474-A72F-07343128649C} | |||
| (PID) Process: | (6040) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {331B448B-729C-42C8-8728-83FD5D7227DA} | |||
Executable files
12
Suspicious files
416
Text files
100
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bbd0.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bbd0.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bbd0.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bbdf.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc0e.TMP | — | |
MD5:— | SHA256:— | |||
| 6040 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
72
DNS requests
81
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5352 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5352 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
536 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747700435&P2=404&P3=2&P4=JYCtrevM8vpMn2Cw%2f2aISEeCBb1MekbWk0vsZXdcV5OaCH%2bSFoF1P%2fijr92x5f%2fbeVVf8hYVr3%2fe3q56jq9mAQ%3d%3d | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747700435&P2=404&P3=2&P4=JYCtrevM8vpMn2Cw%2f2aISEeCBb1MekbWk0vsZXdcV5OaCH%2bSFoF1P%2fijr92x5f%2fbeVVf8hYVr3%2fe3q56jq9mAQ%3d%3d | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747700435&P2=404&P3=2&P4=JYCtrevM8vpMn2Cw%2f2aISEeCBb1MekbWk0vsZXdcV5OaCH%2bSFoF1P%2fijr92x5f%2fbeVVf8hYVr3%2fe3q56jq9mAQ%3d%3d | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747700435&P2=404&P3=2&P4=JYCtrevM8vpMn2Cw%2f2aISEeCBb1MekbWk0vsZXdcV5OaCH%2bSFoF1P%2fijr92x5f%2fbeVVf8hYVr3%2fe3q56jq9mAQ%3d%3d | unknown | — | — | whitelisted |
536 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747700435&P2=404&P3=2&P4=JYCtrevM8vpMn2Cw%2f2aISEeCBb1MekbWk0vsZXdcV5OaCH%2bSFoF1P%2fijr92x5f%2fbeVVf8hYVr3%2fe3q56jq9mAQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6040 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7360 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |