| URL: | https://mail.163.com/large-attachment-download/index.html?p=X-NETEASE-HUGE-ATTACHMENT&file=nnGYnyG93ldcd-zH9r3Sj-kPTbWpF9_REw7lqxBNczkp86n-R-jVo2JjgRGCEDMQ2fEj0vFotbL9hya5_yHPIg&title=%EF%BC%B291.324%E4%B8%89%E7%BB%B4%E7%A1%AE%E8%AE%A4%E5%B0%BA%E5%AF%B8 |
| Full analysis: | https://app.any.run/tasks/5f399303-2525-4b9a-9e67-8d991e07f294 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2022, 07:28:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5B29D44530376AA822DAC6390535C4B1 |
| SHA1: | 70932E6865DFB490AE691AEA1B8C71BB86C3B796 |
| SHA256: | D4BFE9CFF924AA7EA0F2B586B56F43D29E361CEFA0816A589AB2586932092926 |
| SSDEEP: | 6:23WG+wNy7e3H4JIeiVjEq0VOf5RosBwJLen:2GGxNy7e3H8I1ErOnosu0n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3328)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3760)
- AdobeARM.exe (PID: 4092)
- Reader_sl.exe (PID: 3860)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3760)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3760)
- AdobeARM.exe (PID: 4092)
INFO
Checks supported languages
- iexplore.exe (PID: 2960)
- iexplore.exe (PID: 3328)
- AcroRd32.exe (PID: 668)
- RdrCEF.exe (PID: 3428)
- AcroRd32.exe (PID: 3060)
- RdrCEF.exe (PID: 2084)
- RdrCEF.exe (PID: 3180)
- RdrCEF.exe (PID: 3664)
- RdrCEF.exe (PID: 372)
- RdrCEF.exe (PID: 2912)
- RdrCEF.exe (PID: 1368)
- RdrCEF.exe (PID: 2296)
Application launched itself
- iexplore.exe (PID: 2960)
- AcroRd32.exe (PID: 668)
- RdrCEF.exe (PID: 3428)
Reads the computer name
- iexplore.exe (PID: 2960)
- iexplore.exe (PID: 3328)
- AcroRd32.exe (PID: 668)
- AcroRd32.exe (PID: 3060)
- RdrCEF.exe (PID: 3428)
Changes internet zones settings
- iexplore.exe (PID: 2960)
Reads settings of System Certificates
- iexplore.exe (PID: 2960)
- iexplore.exe (PID: 3328)
- AcroRd32.exe (PID: 668)
- RdrCEF.exe (PID: 3428)
Checks Windows Trust Settings
- iexplore.exe (PID: 2960)
- iexplore.exe (PID: 3328)
- AcroRd32.exe (PID: 668)
Reads internet explorer settings
- iexplore.exe (PID: 3328)
Changes settings of System certificates
- iexplore.exe (PID: 2960)
Reads CPU info
- iexplore.exe (PID: 3328)
- AcroRd32.exe (PID: 3060)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2960)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2960)
Searches for installed software
- AcroRd32.exe (PID: 668)
- AcroRd32.exe (PID: 3060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=3403778137636970609 --mojo-platform-channel-handle=1392 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
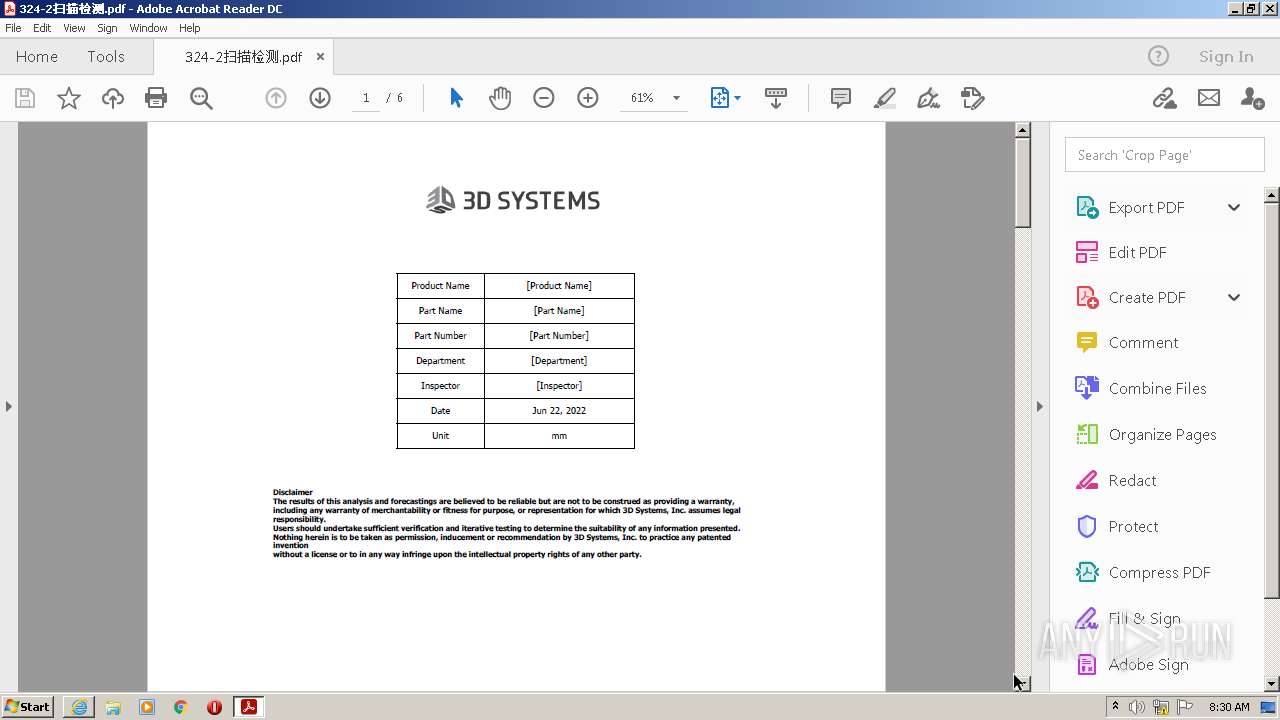
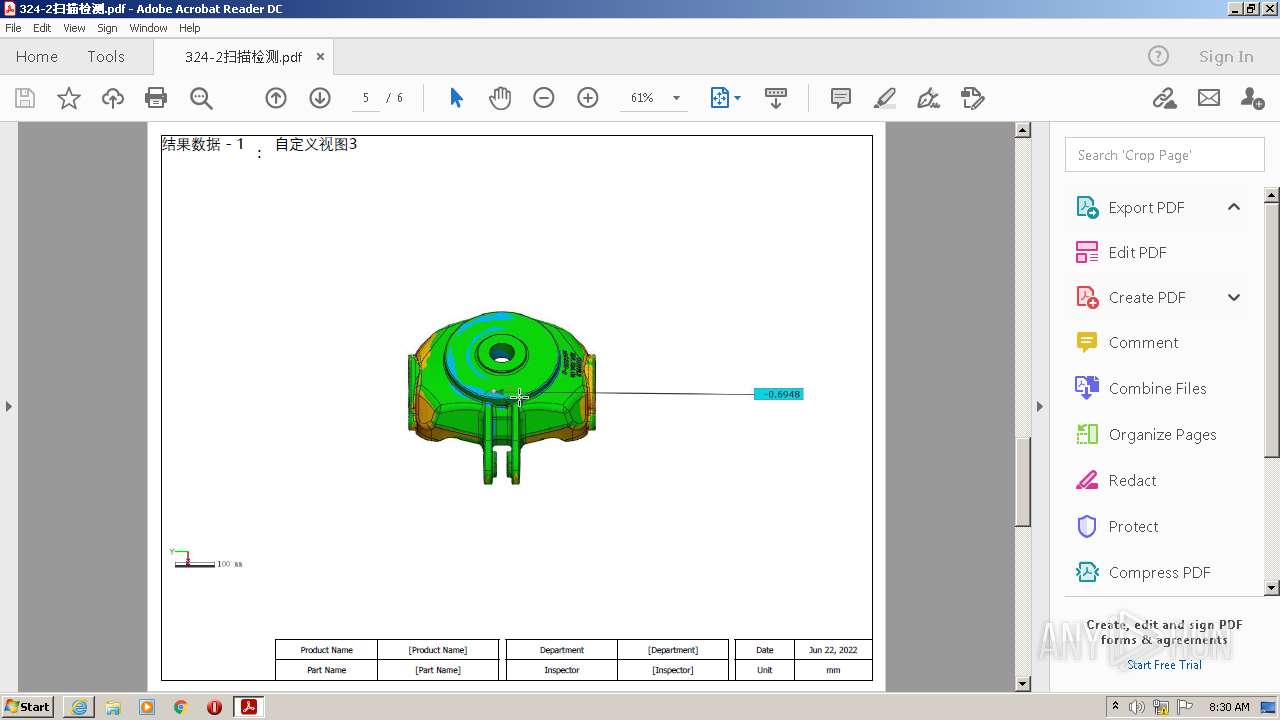
| 668 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\324-2扫描检测.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | iexplore.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=9592262503456255940 --mojo-platform-channel-handle=1220 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7326511533478026251 --renderer-client-id=2 --mojo-platform-channel-handle=1196 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16890138469103403363 --renderer-client-id=7 --mojo-platform-channel-handle=1520 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15241685438301829866 --renderer-client-id=8 --mojo-platform-channel-handle=1768 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
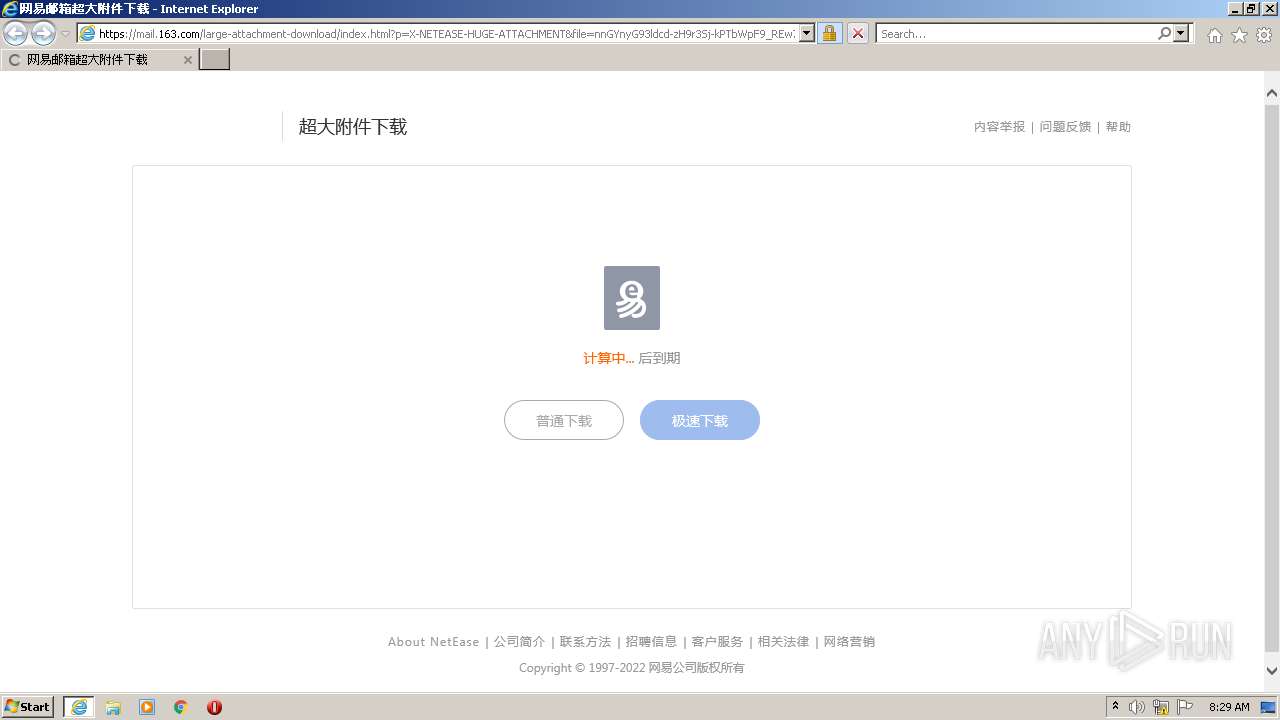
| 2960 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://mail.163.com/large-attachment-download/index.html?p=X-NETEASE-HUGE-ATTACHMENT&file=nnGYnyG93ldcd-zH9r3Sj-kPTbWpF9_REw7lqxBNczkp86n-R-jVo2JjgRGCEDMQ2fEj0vFotbL9hya5_yHPIg&title=%EF%BC%B291.324%E4%B8%89%E7%BB%B4%E7%A1%AE%E8%AE%A4%E5%B0%BA%E5%AF%B8" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\324-2扫描检测.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1188,85718841245736257,3914662693010480535,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=8192862687605964880 --mojo-platform-channel-handle=1244 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2960 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
27 982
Read events
27 584
Write events
391
Delete events
7
Modification events
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30974748 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30974748 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
169
Text files
46
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3FE2BD01AB6BC312BF0DADE7F797388F_F7F9B7BDCC367A8E3539D28F7D4D4BA2 | der | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3FE2BD01AB6BC312BF0DADE7F797388F_F7F9B7BDCC367A8E3539D28F7D4D4BA2 | binary | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7229E30BCFD0992128433D951137A421_FD2099B82B7ECA34B64FB7EDB1A29E84 | der | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7229E30BCFD0992128433D951137A421_FC6EA1A63E483919C35F226C5CABD5F6 | binary | |
MD5:— | SHA256:— | |||
| 2960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7229E30BCFD0992128433D951137A421_FD2099B82B7ECA34B64FB7EDB1A29E84 | binary | |
MD5:— | SHA256:— | |||
| 3328 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\hdurs-0.1.1[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
58
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3328 | iexplore.exe | GET | 200 | 163.181.56.157:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTRXf%2BqAIajMnZeiQcx27p1CzET2wQUJG%2BRP4mHhw4ywkAY38VM60%2FISTICEA4zqJ5wmZpHT49HS1mt5Bg%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 163.181.56.157:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTRXf%2BqAIajMnZeiQcx27p1CzET2wQUJG%2BRP4mHhw4ywkAY38VM60%2FISTICEAZMimqt30%2FgikSjk3vXWMo%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 163.181.56.157:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTRXf%2BqAIajMnZeiQcx27p1CzET2wQUJG%2BRP4mHhw4ywkAY38VM60%2FISTICEAcjz4F72CtBq03CvpIh2lM%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 163.181.56.157:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTRXf%2BqAIajMnZeiQcx27p1CzET2wQUJG%2BRP4mHhw4ywkAY38VM60%2FISTICEAbd%2FBKAv0Oq9cNIYDHCV2A%3D | US | der | 471 b | whitelisted |
668 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 163.181.56.157:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAsTYrbuap0%2Blokw8W4gfTk%3D | US | der | 471 b | whitelisted |
2960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2960 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b682bb52a5665d1 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3328 | iexplore.exe | 103.129.252.34:443 | mail.163.com | — | — | unknown |
2960 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2960 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2960 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3328 | iexplore.exe | 163.181.56.157:80 | ocsp.digicert.cn | — | US | suspicious |
2960 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3328 | iexplore.exe | 163.181.56.168:443 | urswebzj.nosdn.127.net | — | US | suspicious |
2960 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2960 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | — | US | unknown |
3428 | RdrCEF.exe | 23.35.236.137:443 | geo2.adobe.com | Zayo Bandwidth Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.163.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.digicert.cn |
| whitelisted |
mimg.127.net |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
urswebzj.nosdn.127.net |
| malicious |