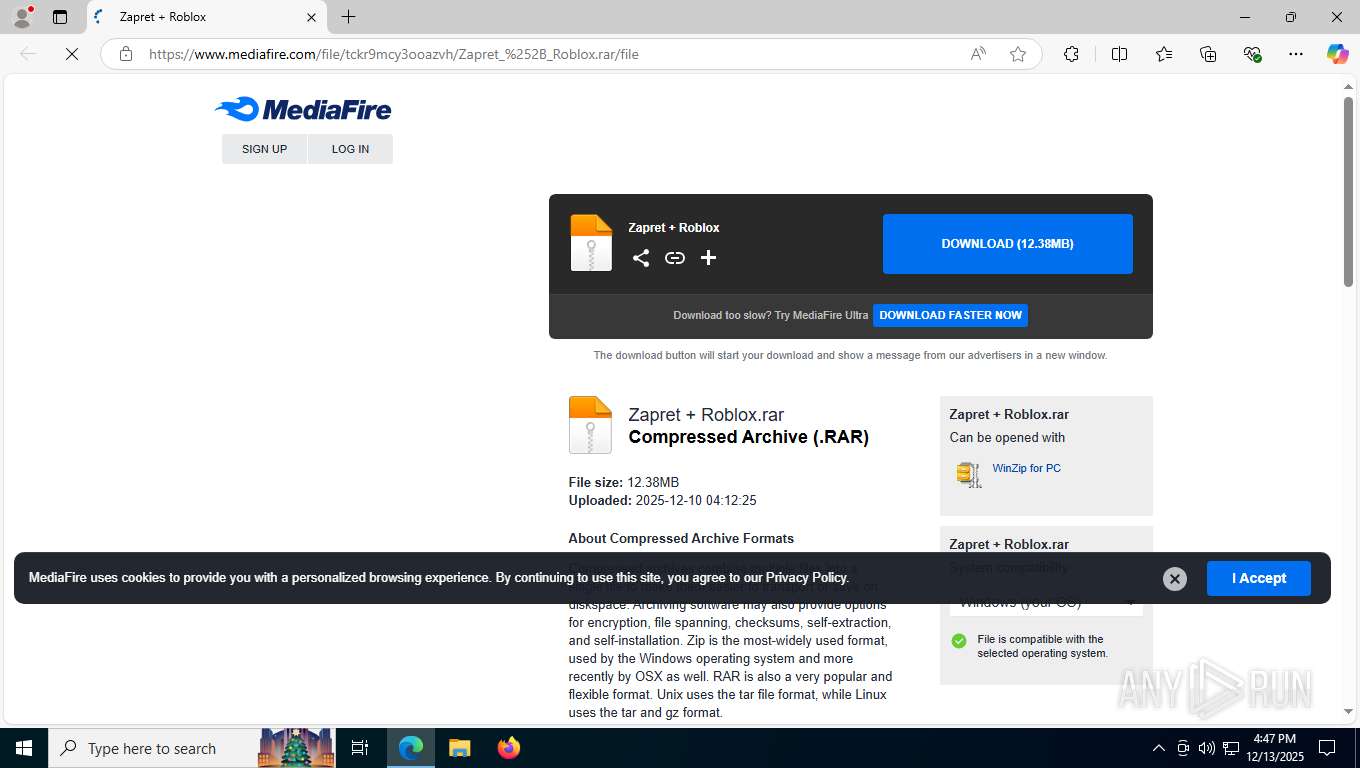
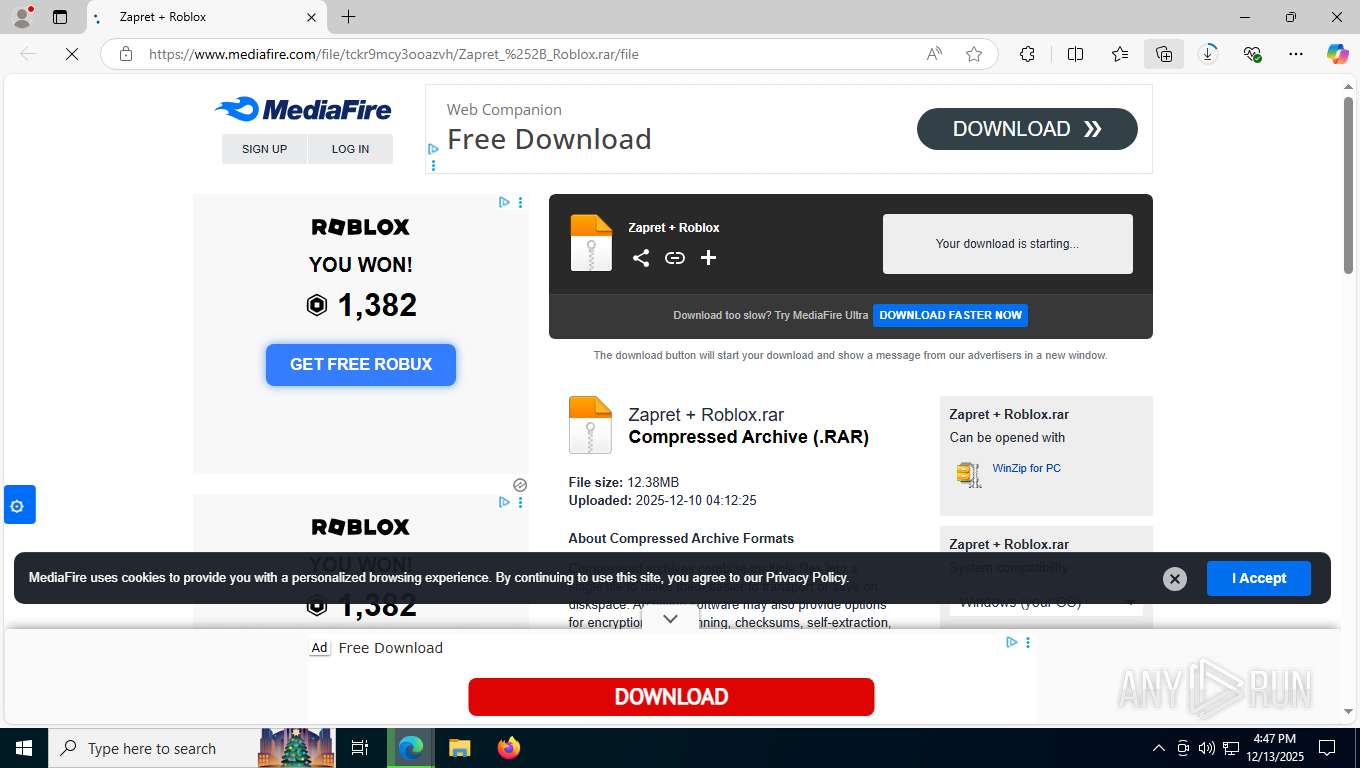
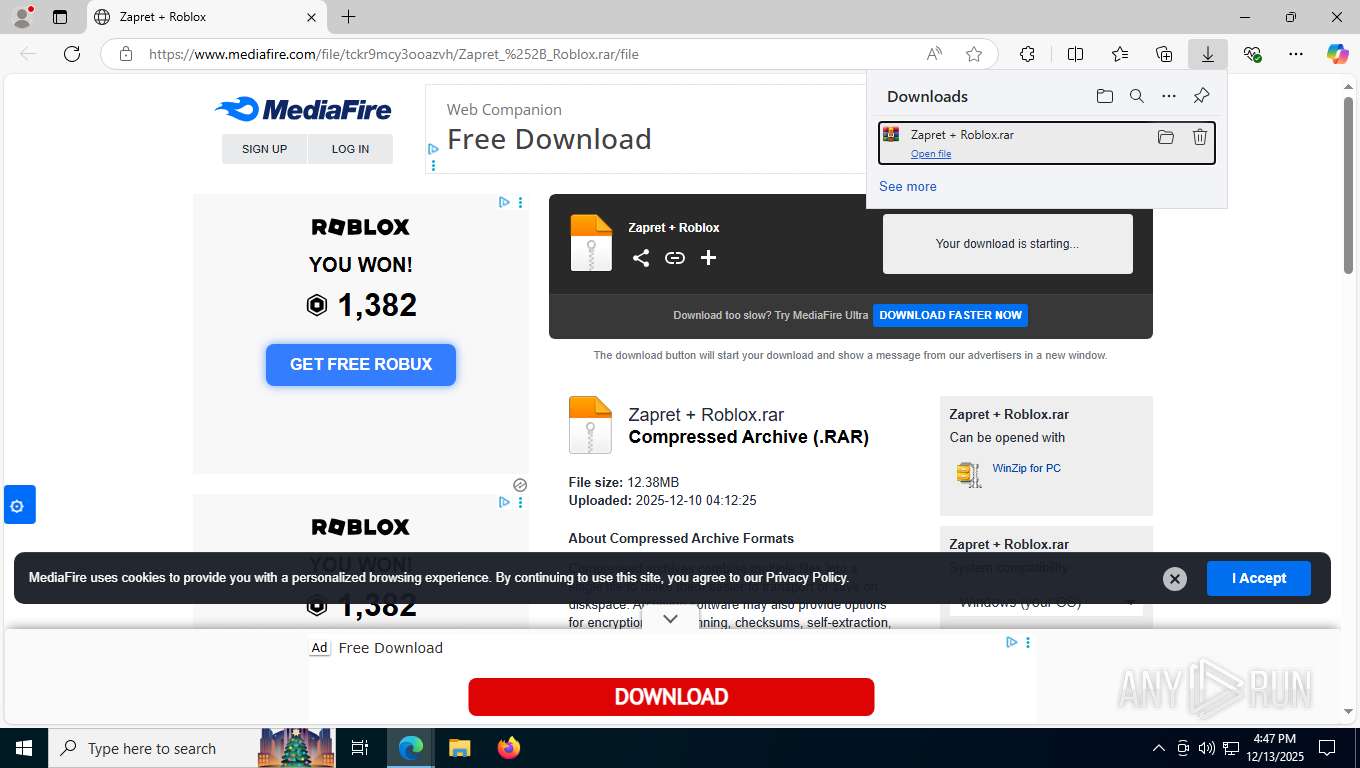
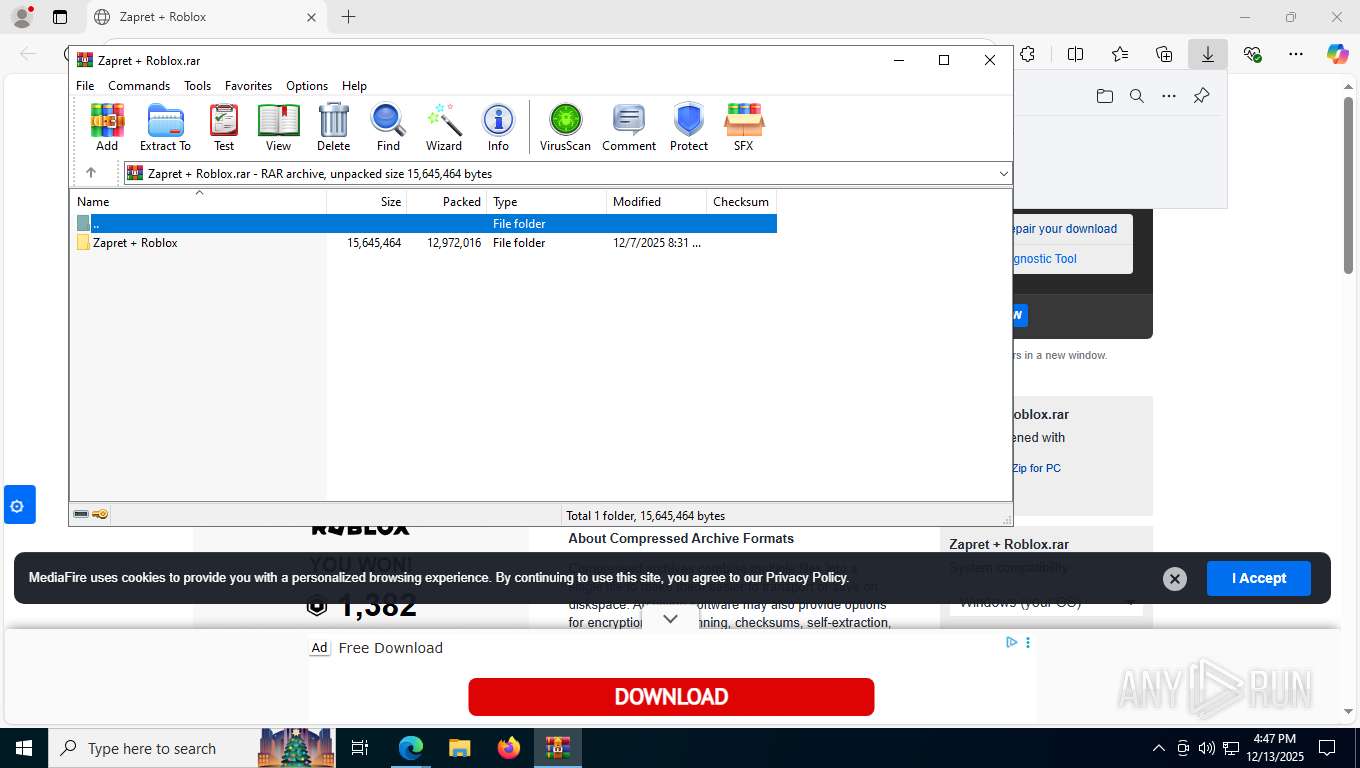
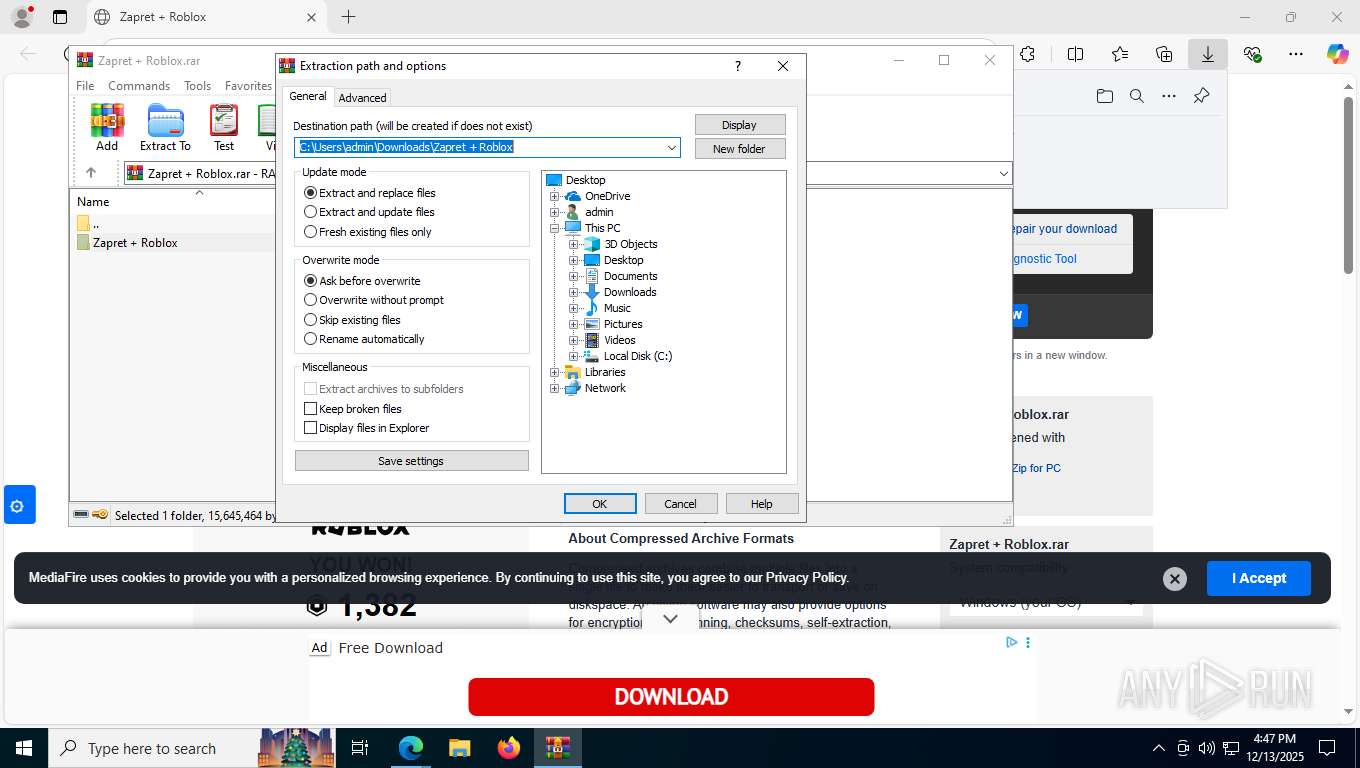
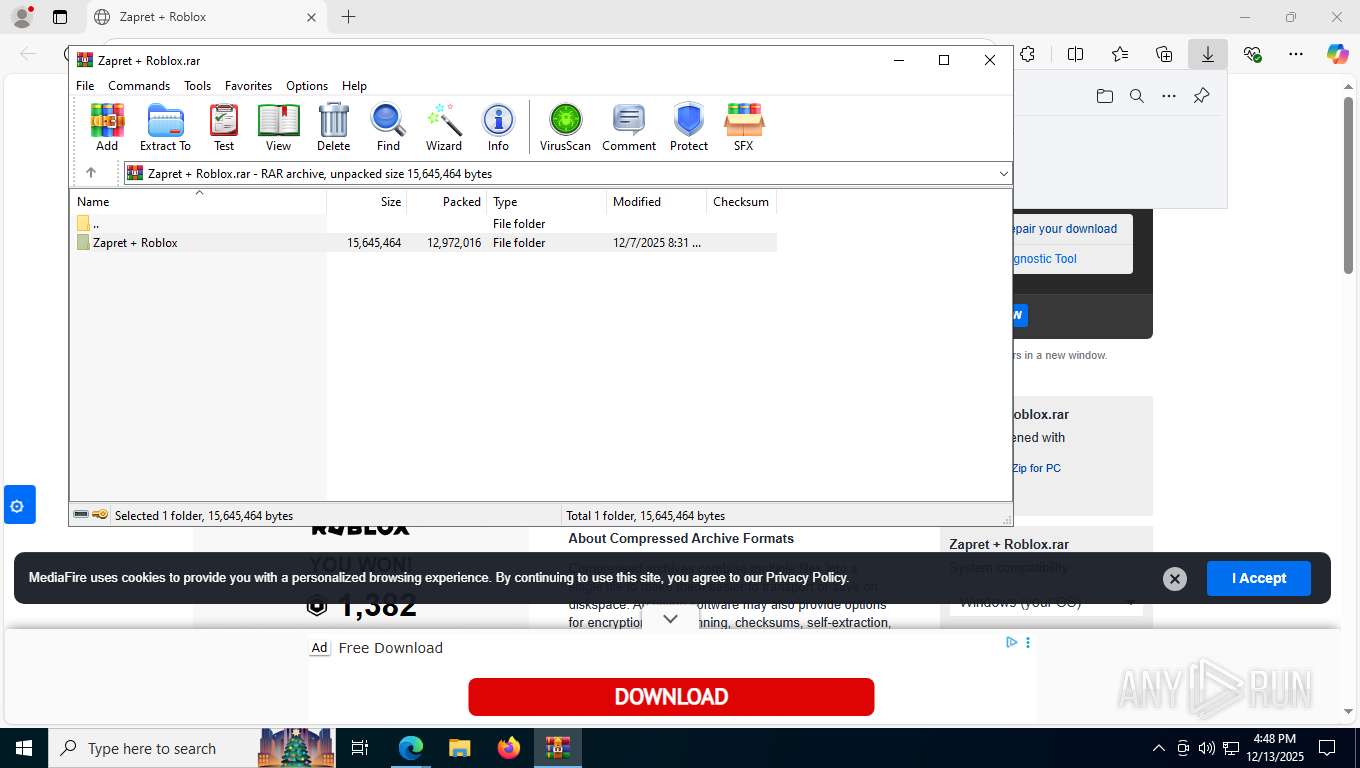
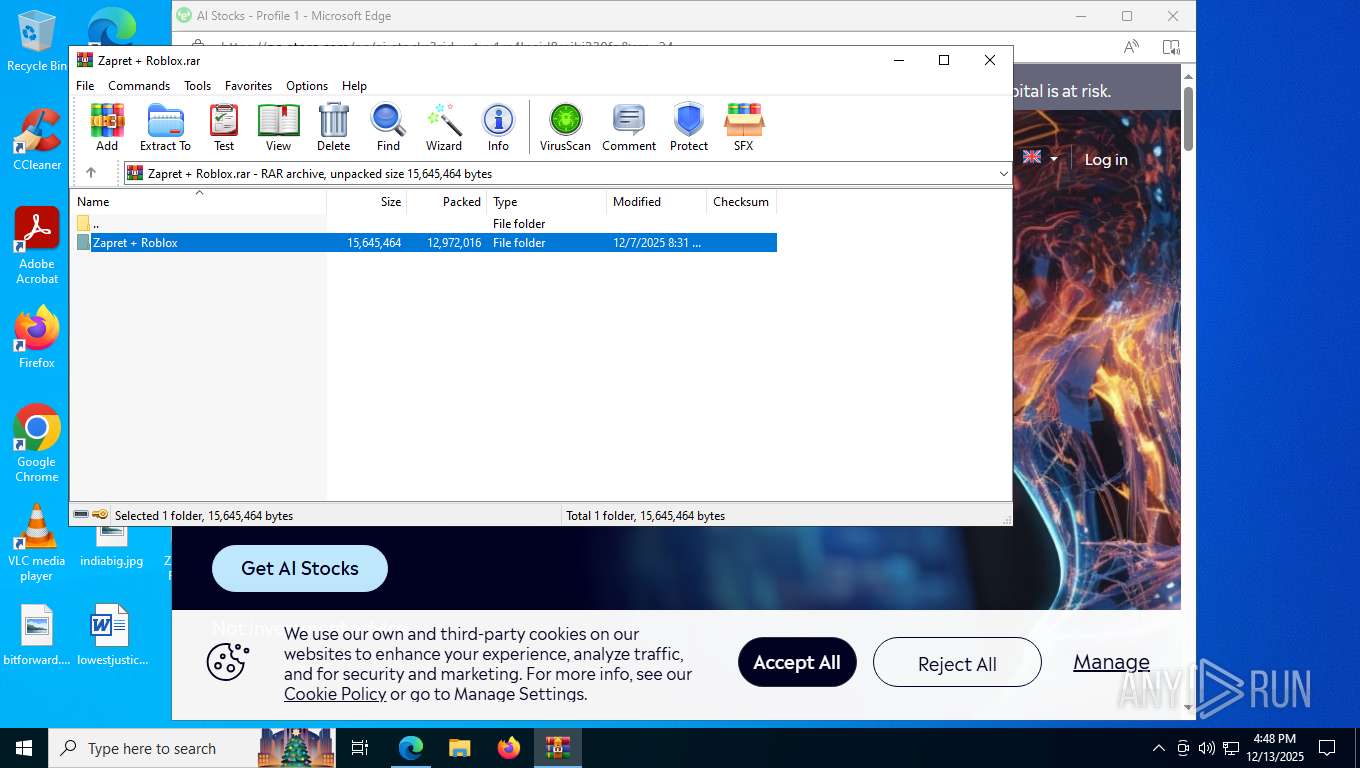
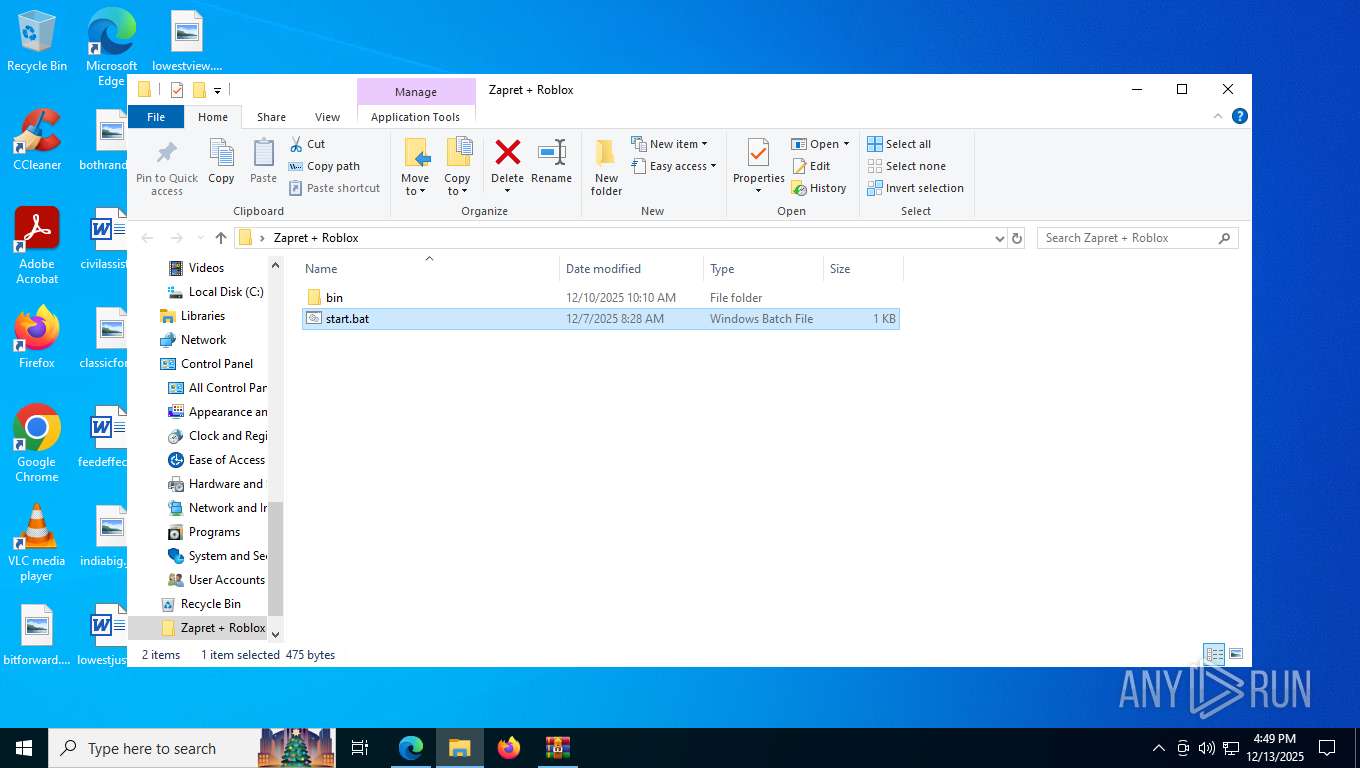
| URL: | https://www.mediafire.com/file/tckr9mcy3ooazvh/Zapret_%252B_Roblox.rar/file |
| Full analysis: | https://app.any.run/tasks/e476f2c6-730e-430e-848c-7874f1ae2ccb |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | December 13, 2025, 16:47:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 42C341455CCCE09E77E5635B9A049C56 |
| SHA1: | 43AF61F6DBCC91B18704DF8EAE96B71753187261 |
| SHA256: | D4BF2FEE3B0240830B91B7E55B24739CFA1C616ACE081CBEC9AD2CC25FD53C30 |
| SSDEEP: | 3:N8DSLw3eGUoLIcnNpDwnIA:2OLw3eGPIe9wIA |
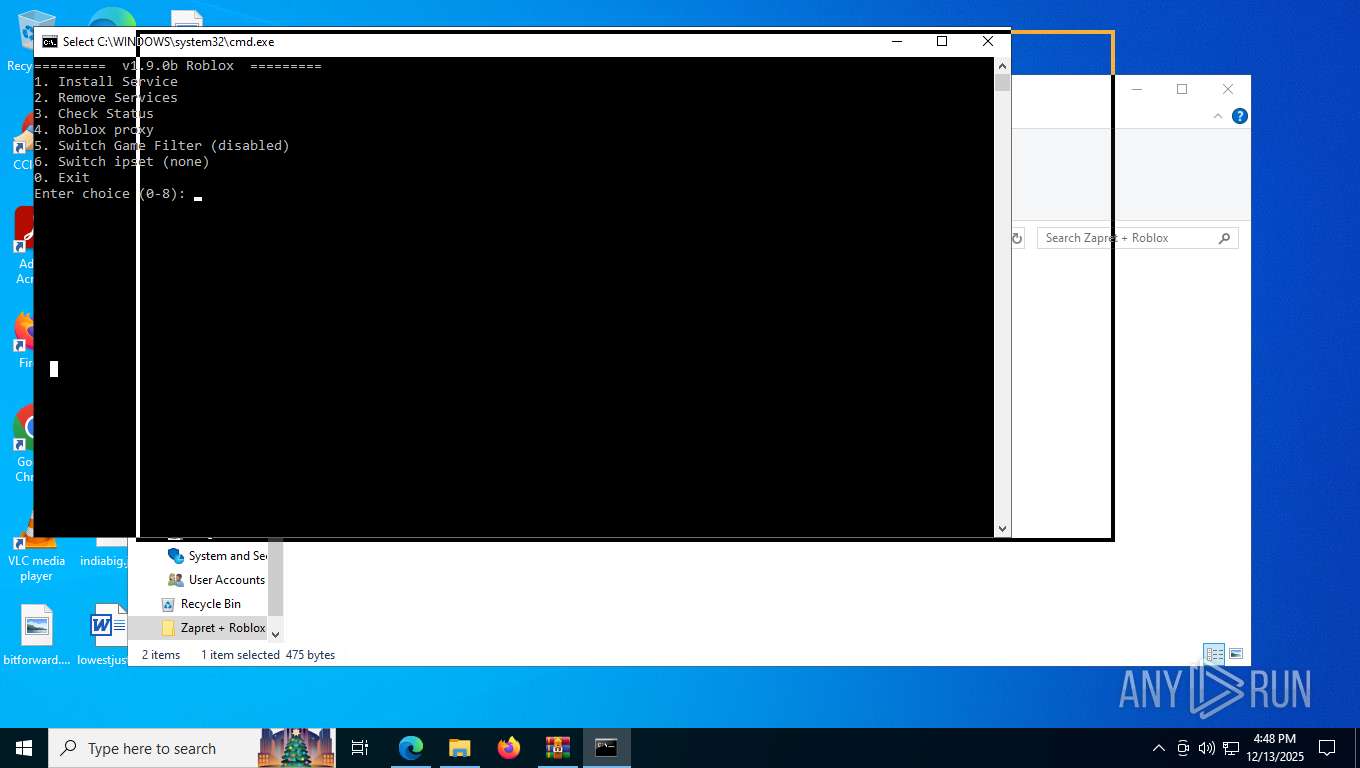
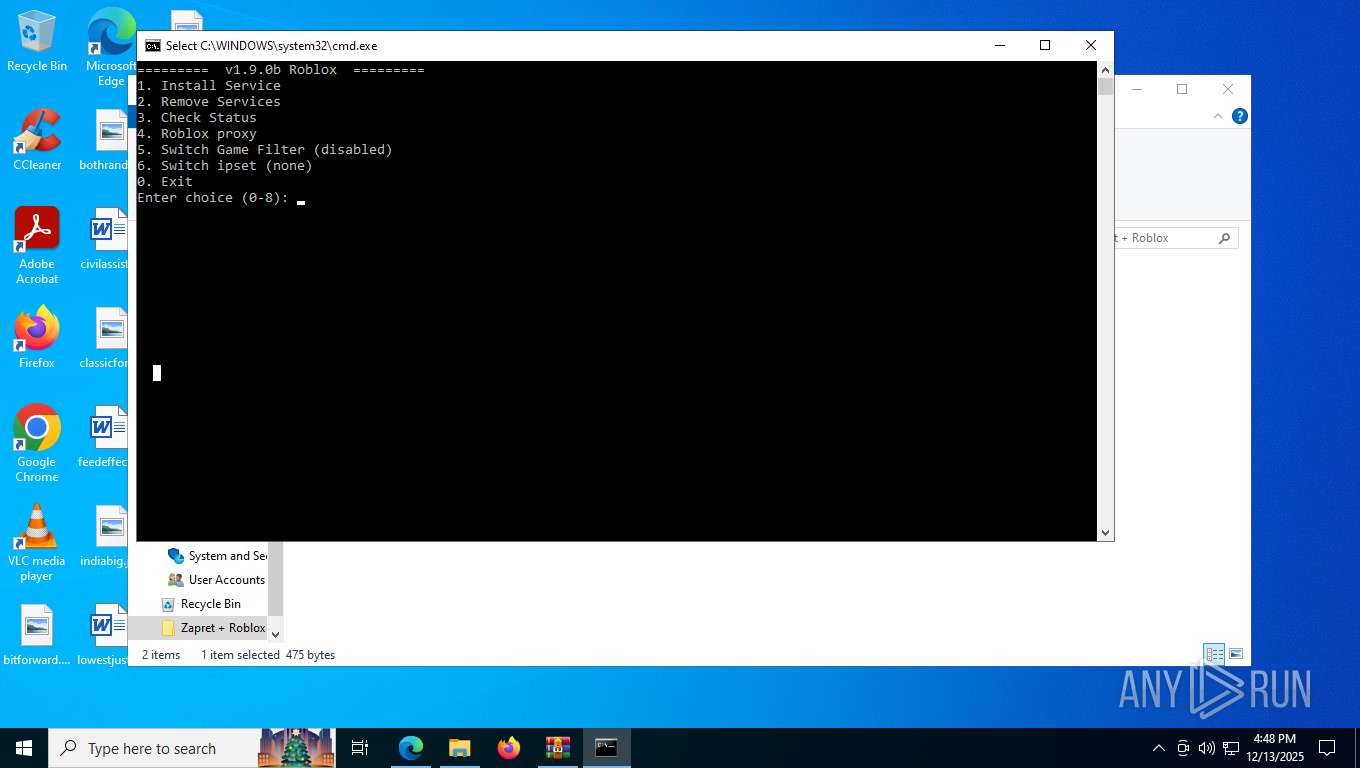
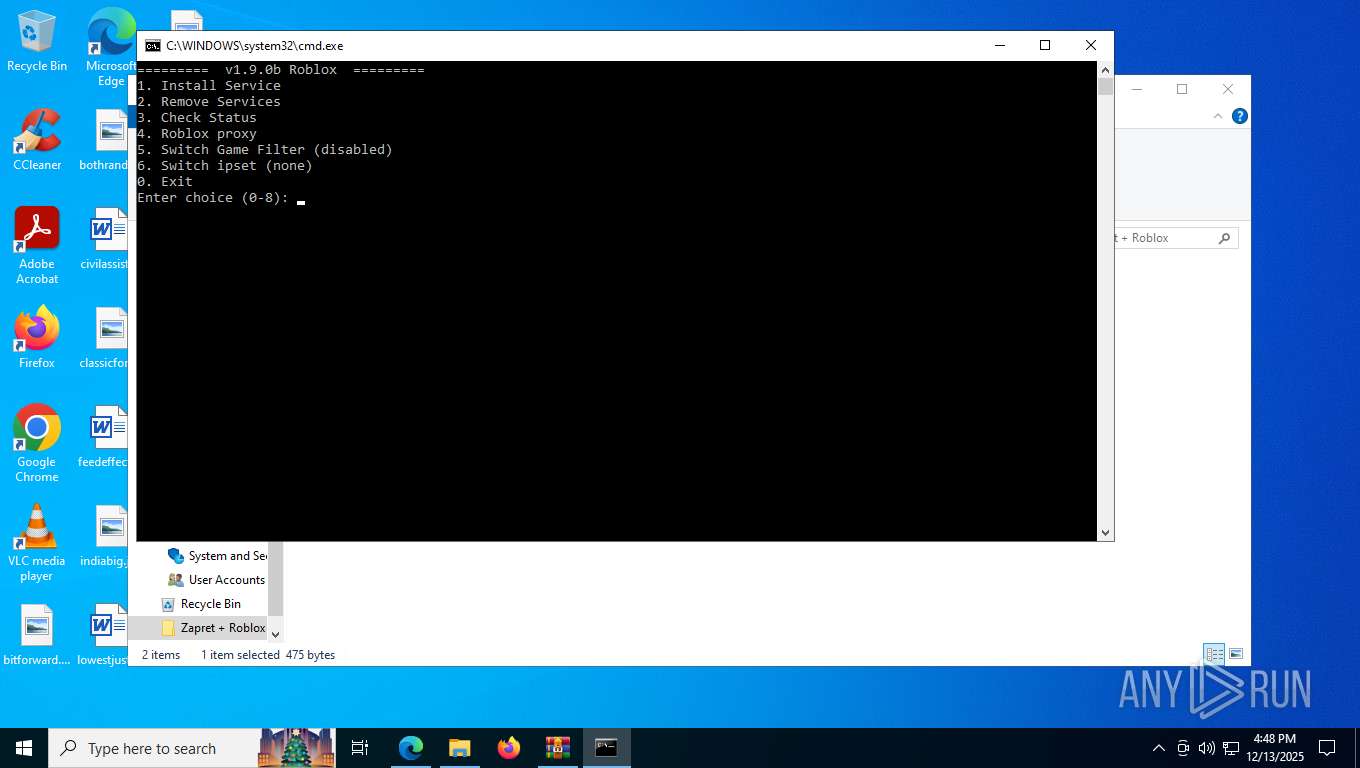
MALICIOUS
Detects Cygwin installation
- WinRAR.exe (PID: 5876)
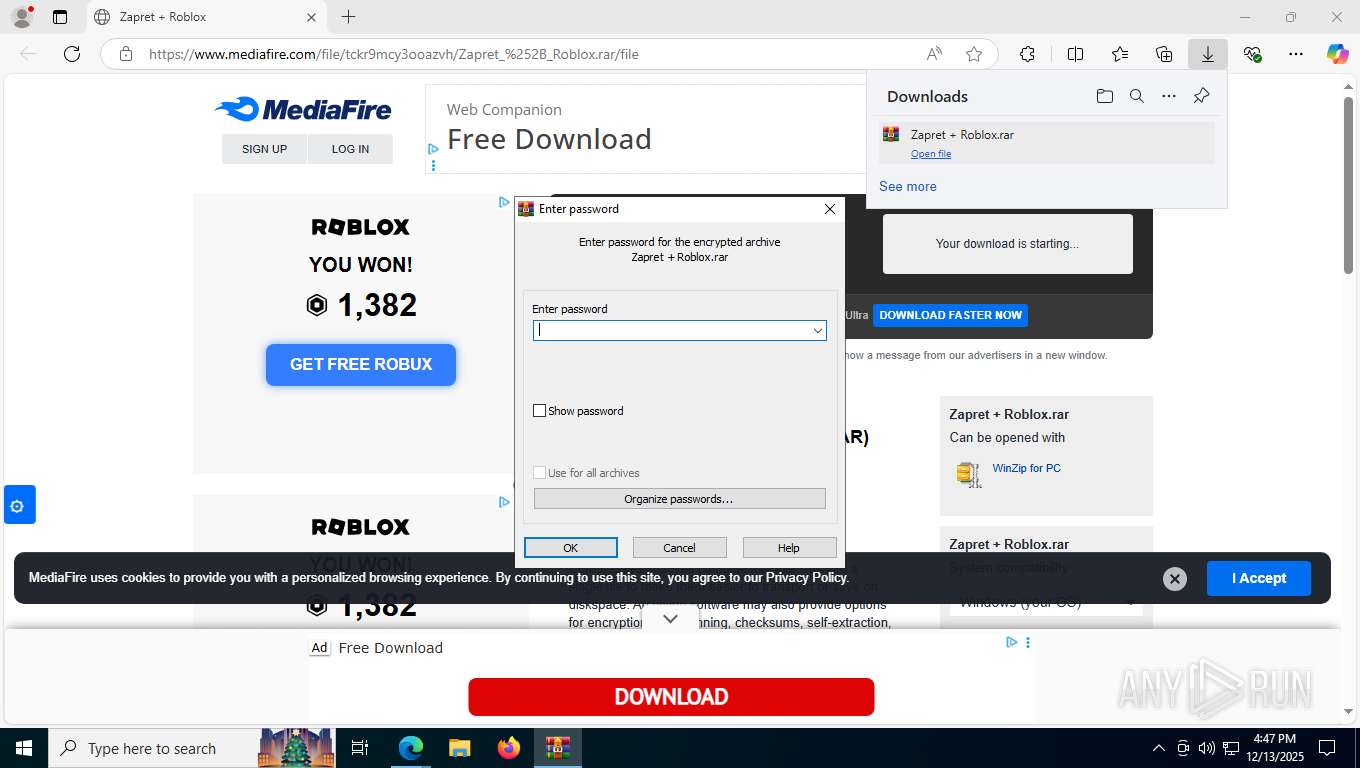
SALATSTEALER has been found (auto)
- WinRAR.exe (PID: 5876)
Malicious driver has been detected
- WinRAR.exe (PID: 5876)
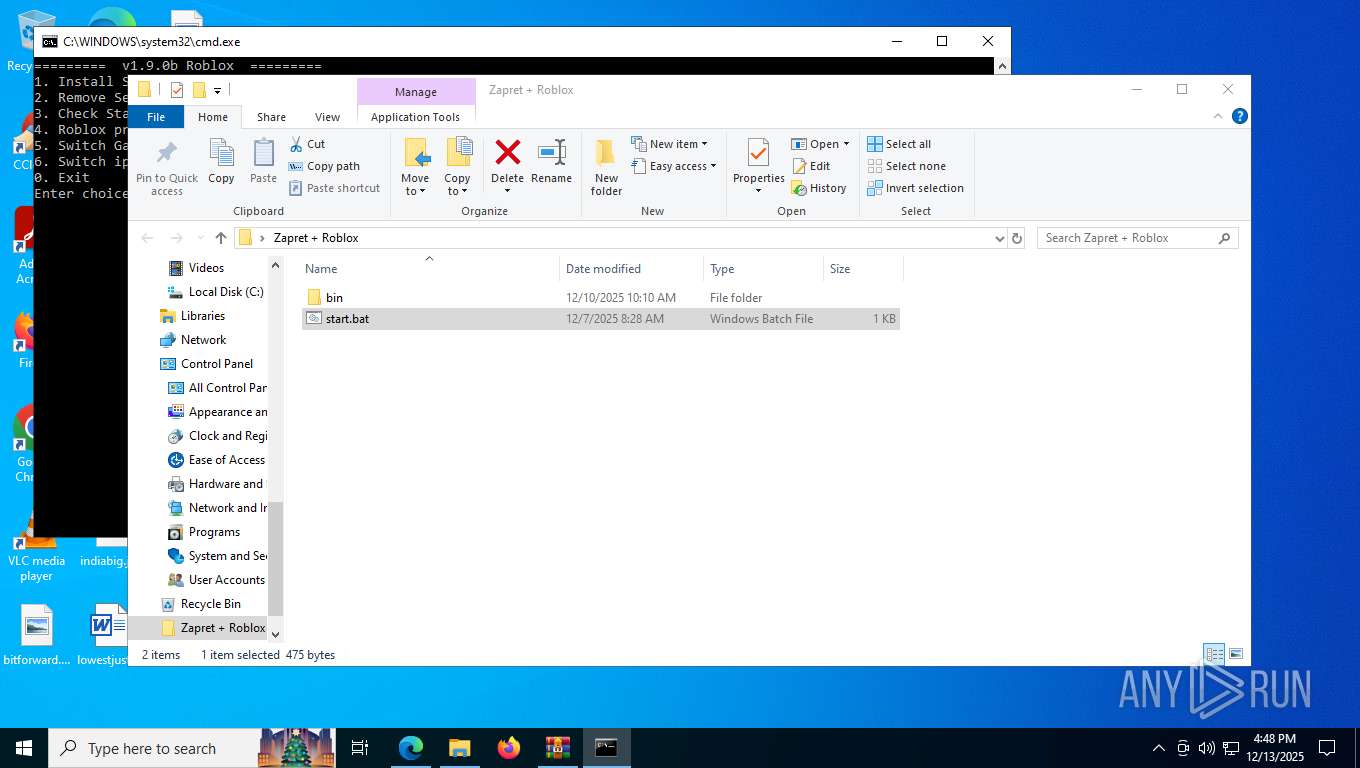
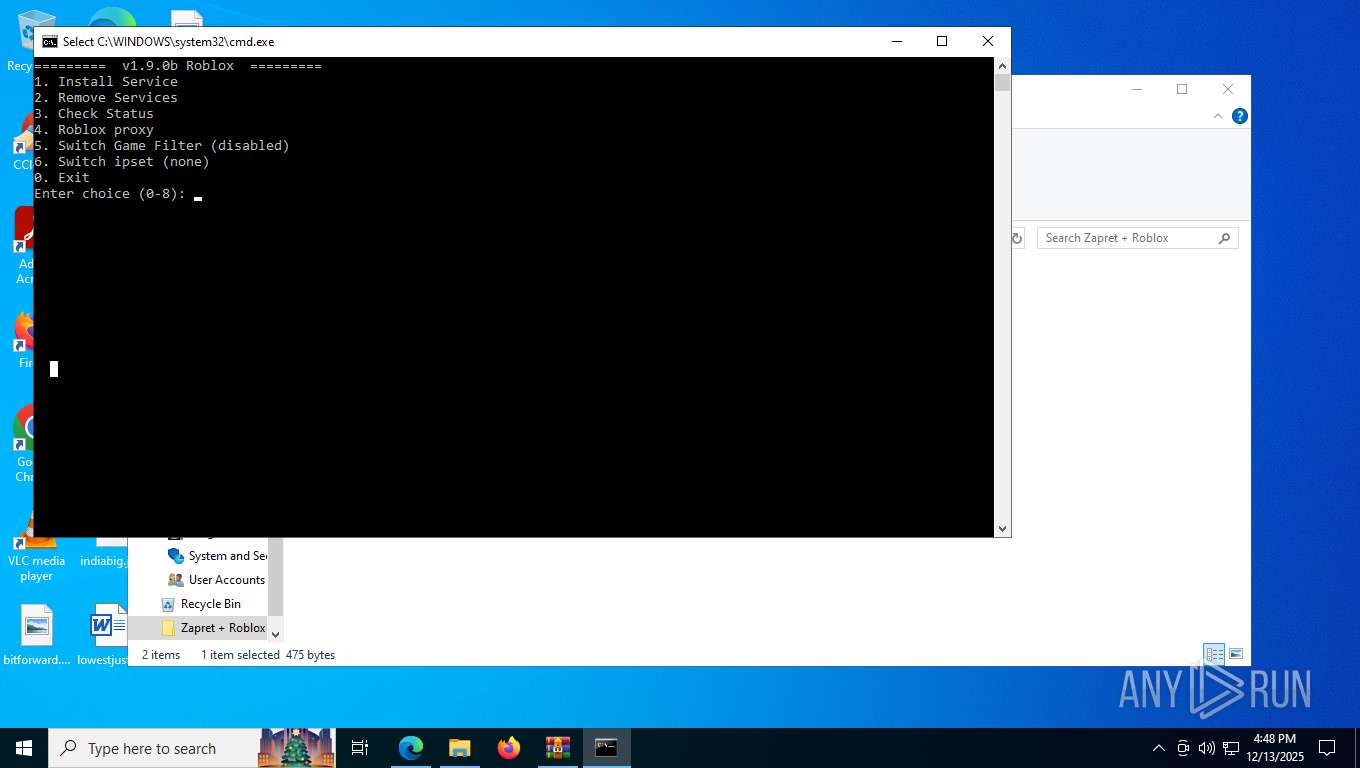
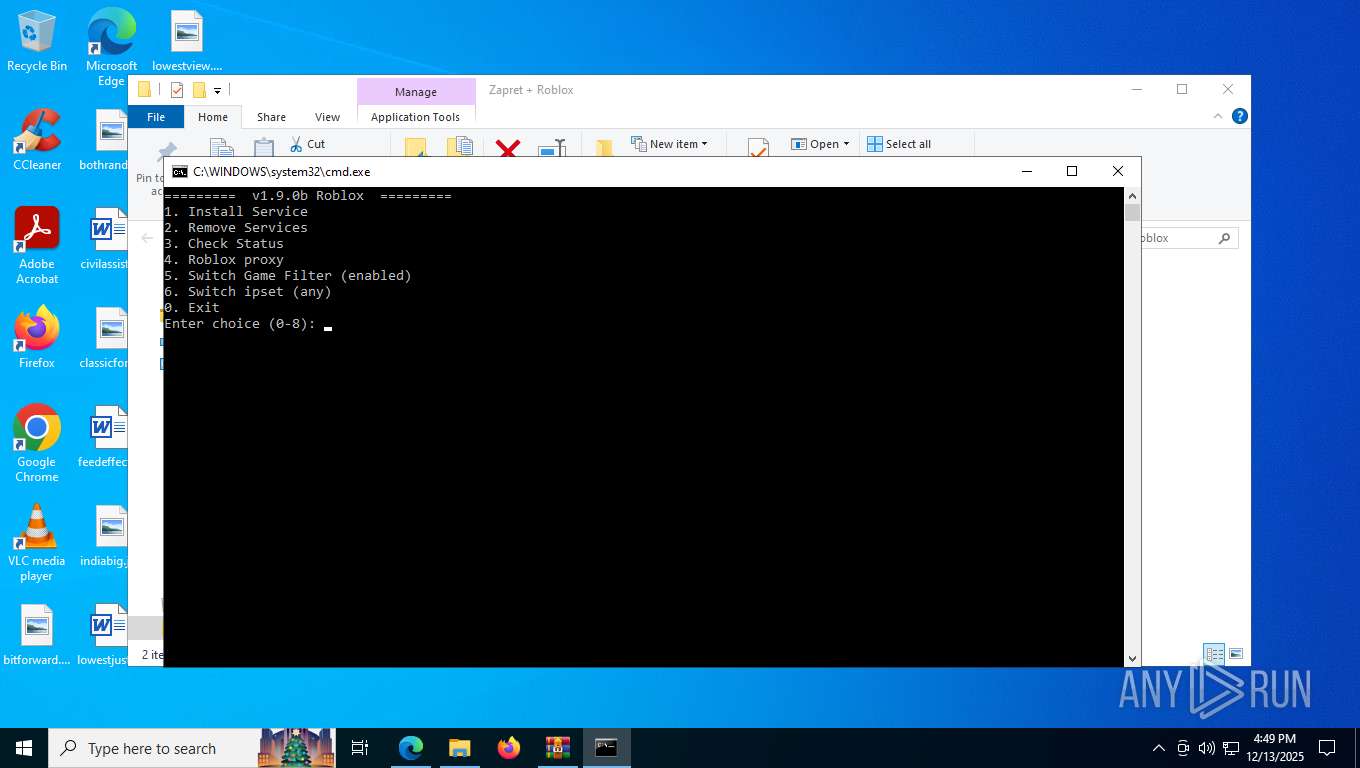
Starts NET.EXE for service management
- net.exe (PID: 3380)
- cmd.exe (PID: 3100)
Executing a file with an untrusted certificate
- robloxproxy.exe (PID: 9036)
- robloxproxy.exe (PID: 7276)
Bypass execution policy to execute commands
- powershell.exe (PID: 6096)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 5876)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6580)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 2360)
Starts process via Powershell
- powershell.exe (PID: 9064)
- powershell.exe (PID: 1756)
- powershell.exe (PID: 7468)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 9064)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 9104)
- robloxproxy.exe (PID: 7276)
- powershell.exe (PID: 7468)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 9104)
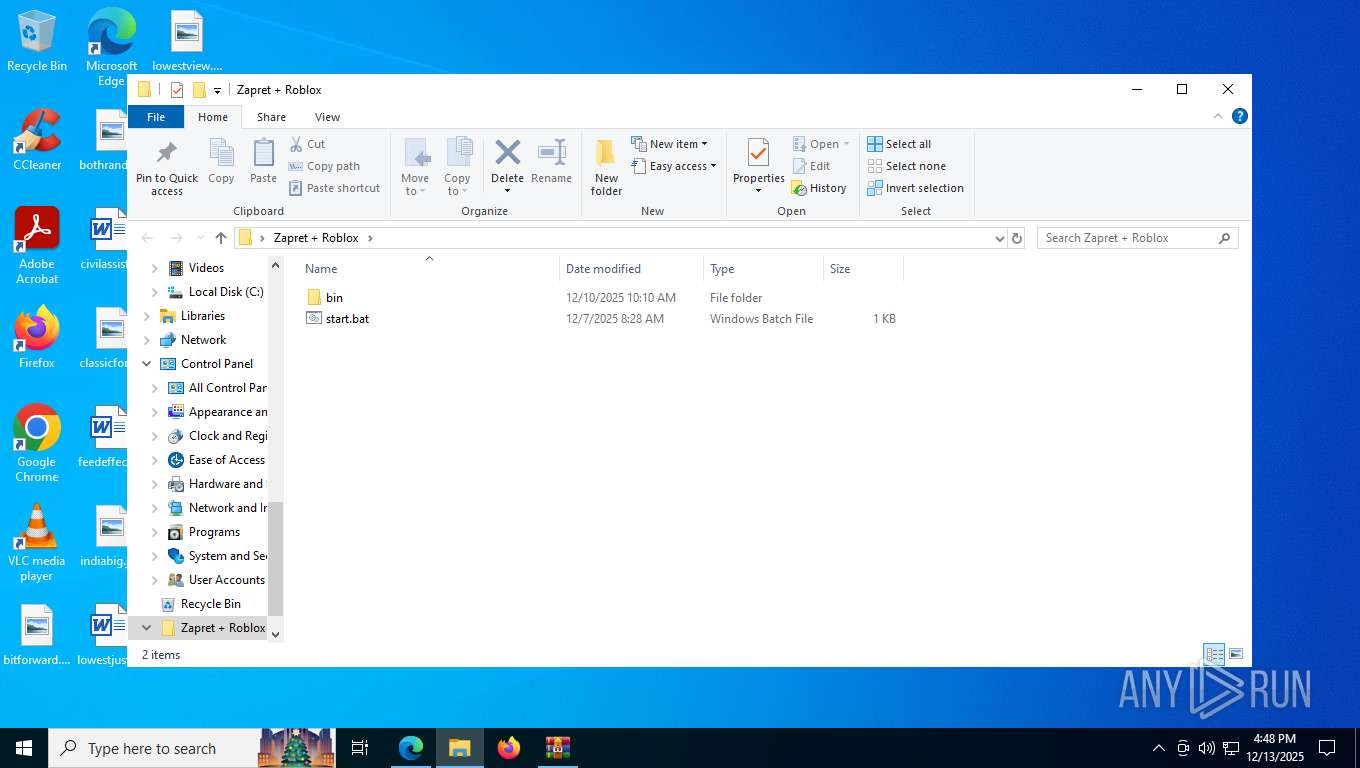
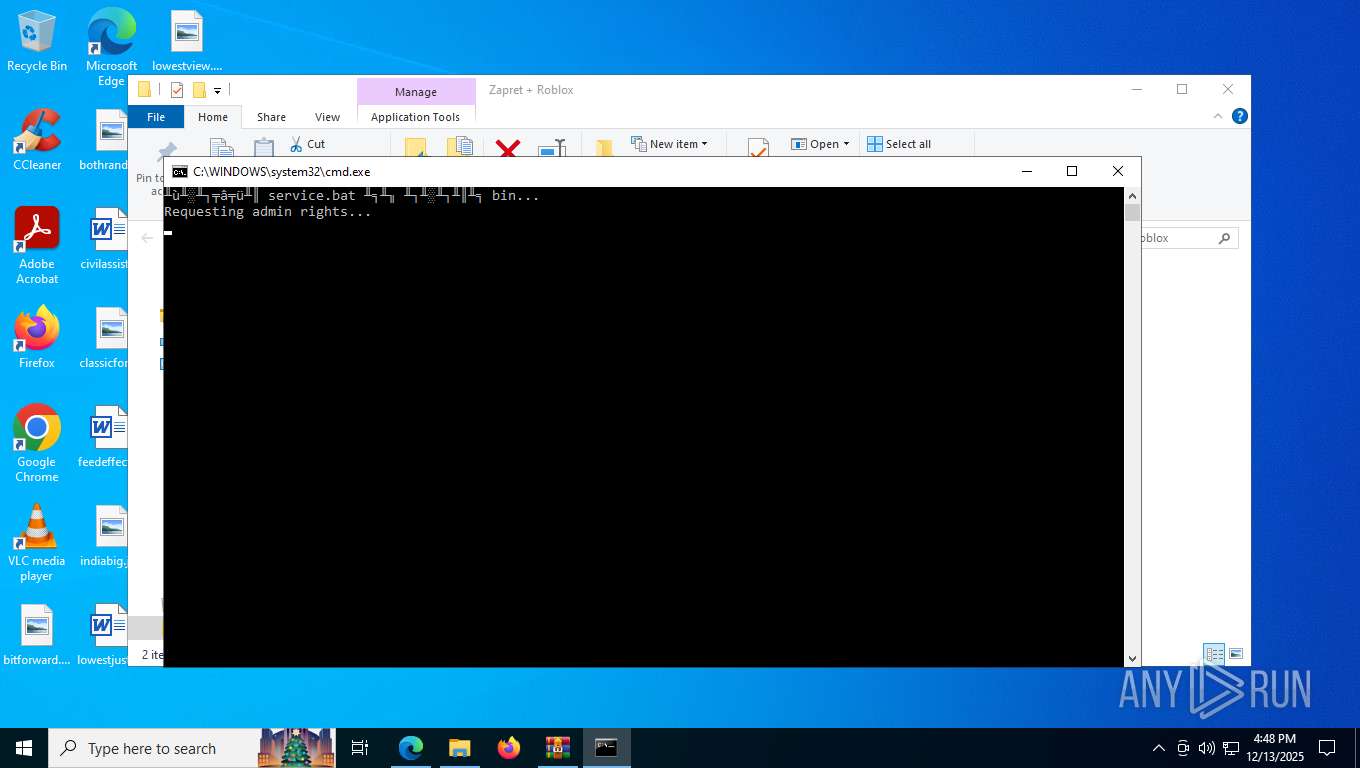
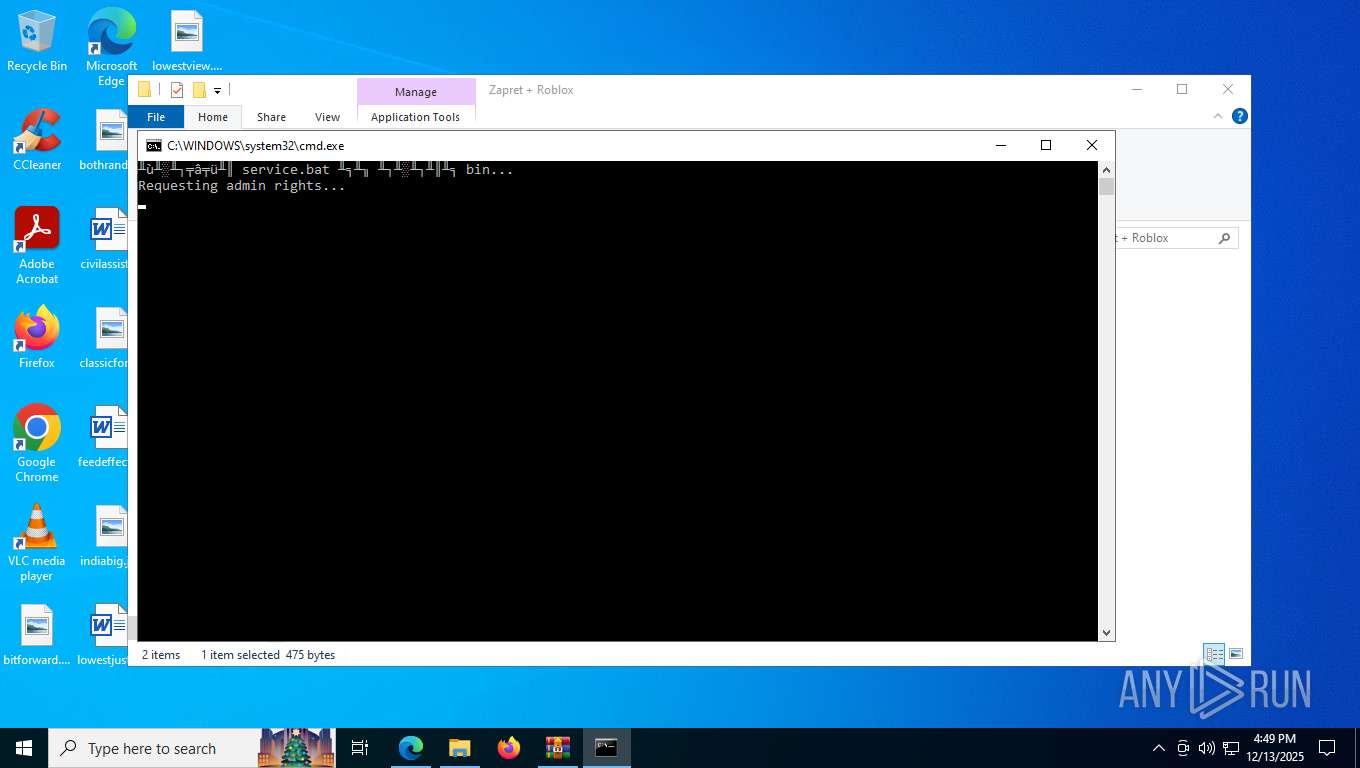
Executing commands from a ".bat" file
- powershell.exe (PID: 9064)
- cmd.exe (PID: 3100)
- powershell.exe (PID: 7468)
Hides command output
- cmd.exe (PID: 4804)
- cmd.exe (PID: 8064)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 7960)
Application launched itself
- cmd.exe (PID: 3100)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 9104)
- robloxproxy.exe (PID: 9036)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 9104)
Starts application with an unusual extension
- cmd.exe (PID: 3100)
- cmd.exe (PID: 5992)
- cmd.exe (PID: 2360)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3100)
- cmd.exe (PID: 4828)
- cmd.exe (PID: 6500)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 3100)
Starts SC.EXE for service management
- cmd.exe (PID: 3100)
- cmd.exe (PID: 2360)
- cmd.exe (PID: 4828)
- cmd.exe (PID: 6500)
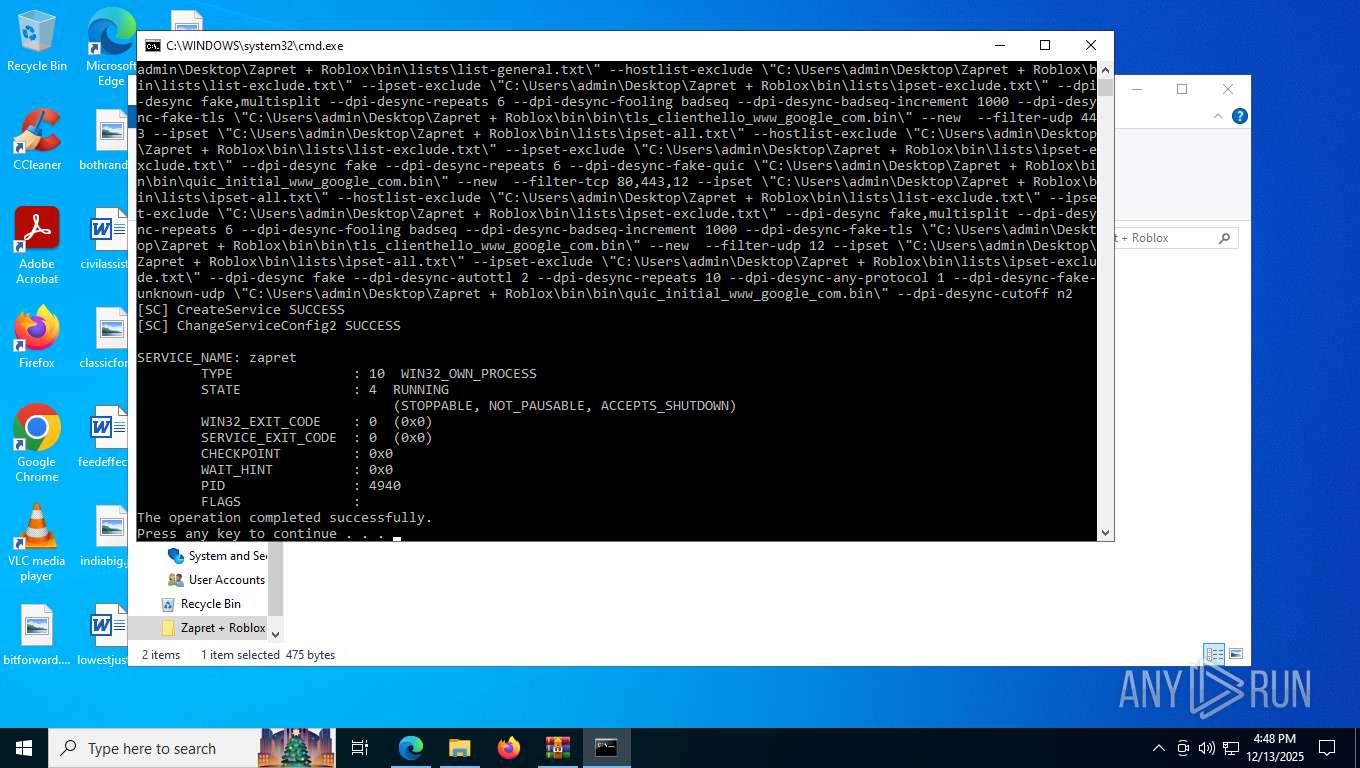
Creates a new Windows service
- sc.exe (PID: 6348)
Windows service management via SC.EXE
- sc.exe (PID: 272)
- sc.exe (PID: 4284)
- sc.exe (PID: 9008)
- sc.exe (PID: 3332)
- sc.exe (PID: 5168)
- sc.exe (PID: 6508)
Non windows owned service launched
- winws.exe (PID: 4940)
Executes as Windows Service
- winws.exe (PID: 4940)
Creates or modifies Windows services
- reg.exe (PID: 7072)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3100)
Executable content was dropped or overwritten
- robloxproxy.exe (PID: 9036)
- robloxproxy.exe (PID: 7276)
- temp_wrapper.py (PID: 8076)
Process drops legitimate windows executable
- robloxproxy.exe (PID: 9036)
Process drops python dynamic module
- robloxproxy.exe (PID: 9036)
The process drops C-runtime libraries
- robloxproxy.exe (PID: 9036)
Loads Python modules
- robloxproxy.exe (PID: 7276)
The executable file from the user directory is run by the CMD process
- temp_wrapper.py (PID: 8076)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3100)
There is functionality for taking screenshot (YARA)
- robloxproxy.exe (PID: 9036)
Get information on the list of running processes
- cmd.exe (PID: 2360)
The process creates files with name similar to system file names
- temp_wrapper.py (PID: 8076)
Starts itself from another location
- temp_wrapper.py (PID: 8076)
INFO
Reads Environment values
- identity_helper.exe (PID: 9000)
Checks supported languages
- identity_helper.exe (PID: 9000)
- chcp.com (PID: 5492)
- chcp.com (PID: 3180)
- chcp.com (PID: 7176)
- chcp.com (PID: 8732)
- chcp.com (PID: 9064)
- chcp.com (PID: 7696)
- robloxproxy.exe (PID: 9036)
- winws.exe (PID: 4940)
- robloxproxy.exe (PID: 7276)
- temp_wrapper.py (PID: 8076)
- chcp.com (PID: 8796)
- chcp.com (PID: 9040)
- chcp.com (PID: 8212)
- conhost.exe (PID: 5732)
Reads the computer name
- identity_helper.exe (PID: 9000)
- winws.exe (PID: 4940)
- robloxproxy.exe (PID: 9036)
- temp_wrapper.py (PID: 8076)
- conhost.exe (PID: 5732)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5876)
The sample compiled with english language support
- WinRAR.exe (PID: 5876)
- robloxproxy.exe (PID: 9036)
Application launched itself
- msedge.exe (PID: 7552)
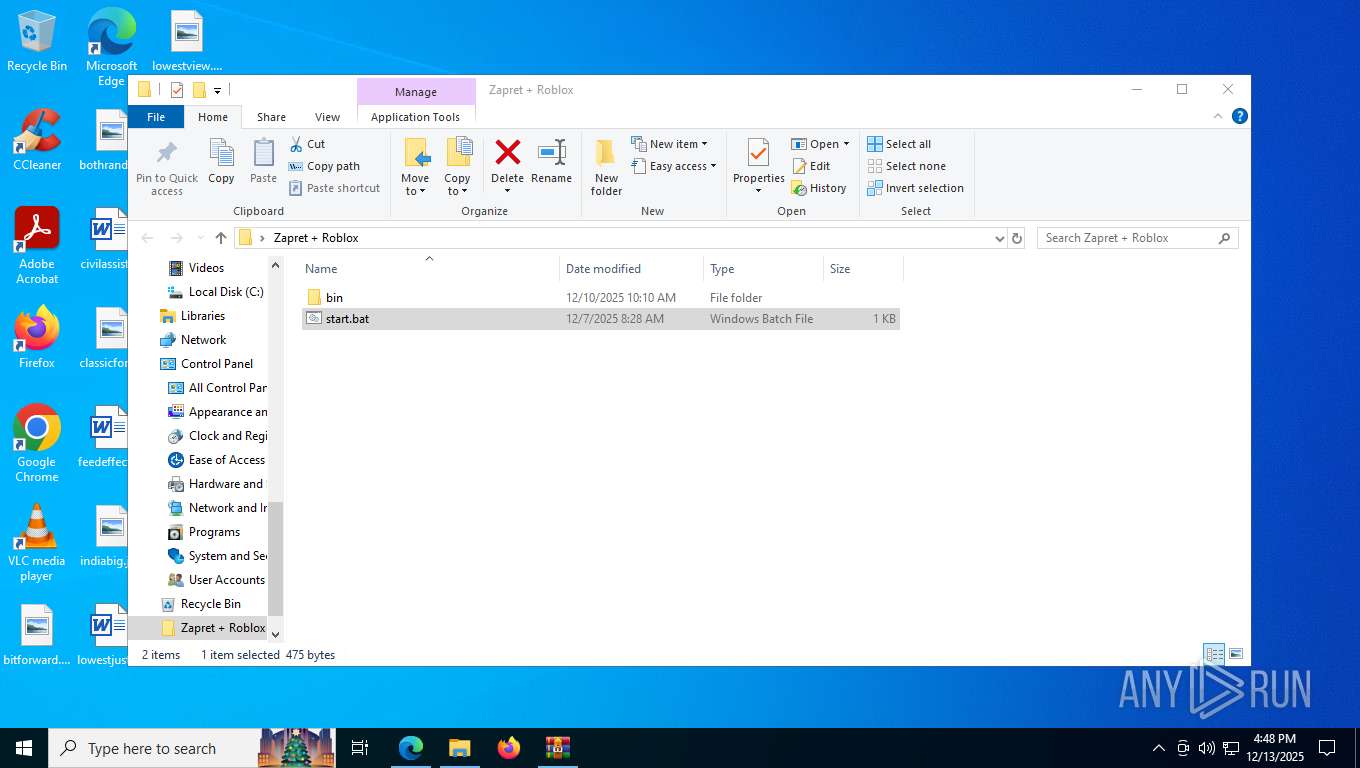
Manual execution by a user
- cmd.exe (PID: 6580)
- cmd.exe (PID: 7524)
Changes the display of characters in the console
- cmd.exe (PID: 3100)
- cmd.exe (PID: 2360)
Disables trace logs
- netsh.exe (PID: 4944)
- netsh.exe (PID: 8180)
Create files in a temporary directory
- robloxproxy.exe (PID: 9036)
- robloxproxy.exe (PID: 7276)
Reads the machine GUID from the registry
- robloxproxy.exe (PID: 7276)
- temp_wrapper.py (PID: 8076)
- conhost.exe (PID: 5732)
Checks operating system version
- robloxproxy.exe (PID: 7276)
PyInstaller has been detected (YARA)
- robloxproxy.exe (PID: 9036)
Checks proxy server information
- slui.exe (PID: 8752)
Search a value from a registry key
- cmd.exe (PID: 7960)
- reg.exe (PID: 7268)
Creates files in the program directory
- temp_wrapper.py (PID: 8076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
349
Monitored processes
201
Malicious processes
10
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo --filter-udp=443 --hostlist="%LISTS%list-general.txt" --hostlist-exclude="%LISTS%list-exclude.txt" --ipset-exclude="%LISTS%ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="%BIN%quic_initial_www_google_com.bin" --new ^ " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 272 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | findstr /i "winws.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --subproc-heap-profiling --always-read-main-dll --field-trial-handle=8636,i,17280436667068669770,15160479399969863709,262144 --variations-seed-version --mojo-platform-channel-handle=6188 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1080 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo %LISTS%ipset-exclude.txt " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo --filter-udp=%GameFilter% --ipset="%LISTS%ipset-all.txt" --ipset-exclude="%LISTS%ipset-exclude.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=10 --dpi-desync-any-protocol=1 --dpi-desync-fake-unknown-udp="%BIN%quic_initial_www_google_com.bin" --dpi-desync-cutoff=n2 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo %LISTS%ipset-exclude.txt " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo %LISTS%list-general.txt " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1756 | powershell -Command "Start-Process 'C:\Users\admin\Desktop\Zapret + Roblox\bin\bin\robloxproxy.exe' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 157
Read events
49 128
Write events
16
Delete events
13
Modification events
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Zapret + Roblox.rar | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5876) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
50
Suspicious files
352
Text files
113
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf6d38.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFf6d38.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFf6d47.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFf6d38.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFf6d47.TMP | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7552 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
637
TCP/UDP connections
340
DNS requests
364
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7872 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:FxfYGkcfpmGUtKAbwHP0xzCXDnc0C02Hv65jbW5Lg8Q&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7872 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | binary | 768 b | whitelisted |
7872 | msedge.exe | GET | 200 | 104.17.147.83:443 | https://www.mediafire.com/file/tckr9mcy3ooazvh/Zapret_%252B_Roblox.rar/file | unknown | html | 128 Kb | whitelisted |
7872 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 658 b | whitelisted |
7872 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | binary | 25 b | whitelisted |
7872 | msedge.exe | GET | 200 | 104.21.42.32:443 | https://cmp.gatekeeperconsent.com/min.js | unknown | text | 1.03 Kb | whitelisted |
7872 | msedge.exe | GET | 200 | 172.67.199.186:443 | https://the.gatekeeperconsent.com/cmp.min.js | unknown | binary | 7.71 Kb | whitelisted |
7872 | msedge.exe | GET | 200 | 2.16.204.142:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | text | 128 Kb | whitelisted |
7872 | msedge.exe | GET | 200 | 172.67.199.186:443 | https://the.gatekeeperconsent.com/v2/cmp.js?v=445 | unknown | binary | 128 Kb | whitelisted |
7872 | msedge.exe | GET | 200 | 172.67.199.186:443 | https://privacy.gatekeeperconsent.com/tcf2_stub.js | unknown | binary | 1.32 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4292 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3060 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.142:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7872 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7872 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7872 | msedge.exe | 104.17.147.83:443 | www.mediafire.com | CLOUDFLARENET | US | whitelisted |
7872 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
cmp.gatekeeperconsent.com |
| whitelisted |
the.gatekeeperconsent.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
btloader.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7872 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7872 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7872 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7872 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7872 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7872 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7872 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7872 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7872 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |