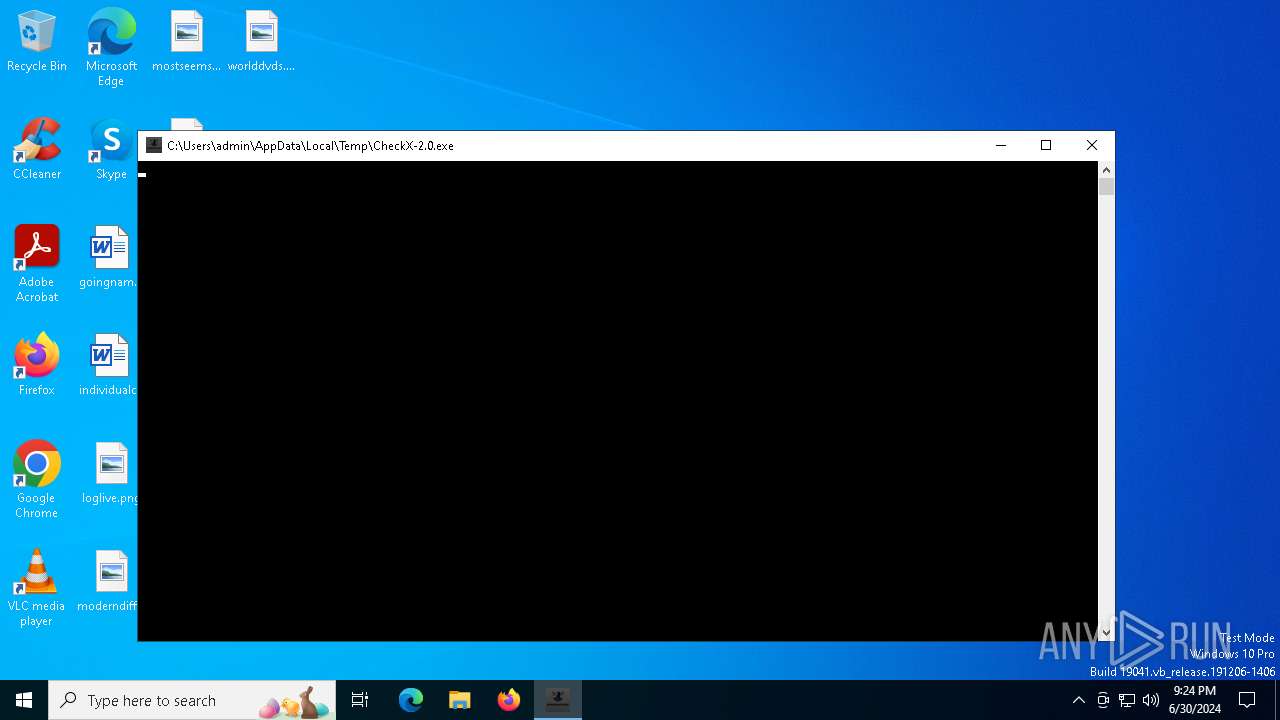
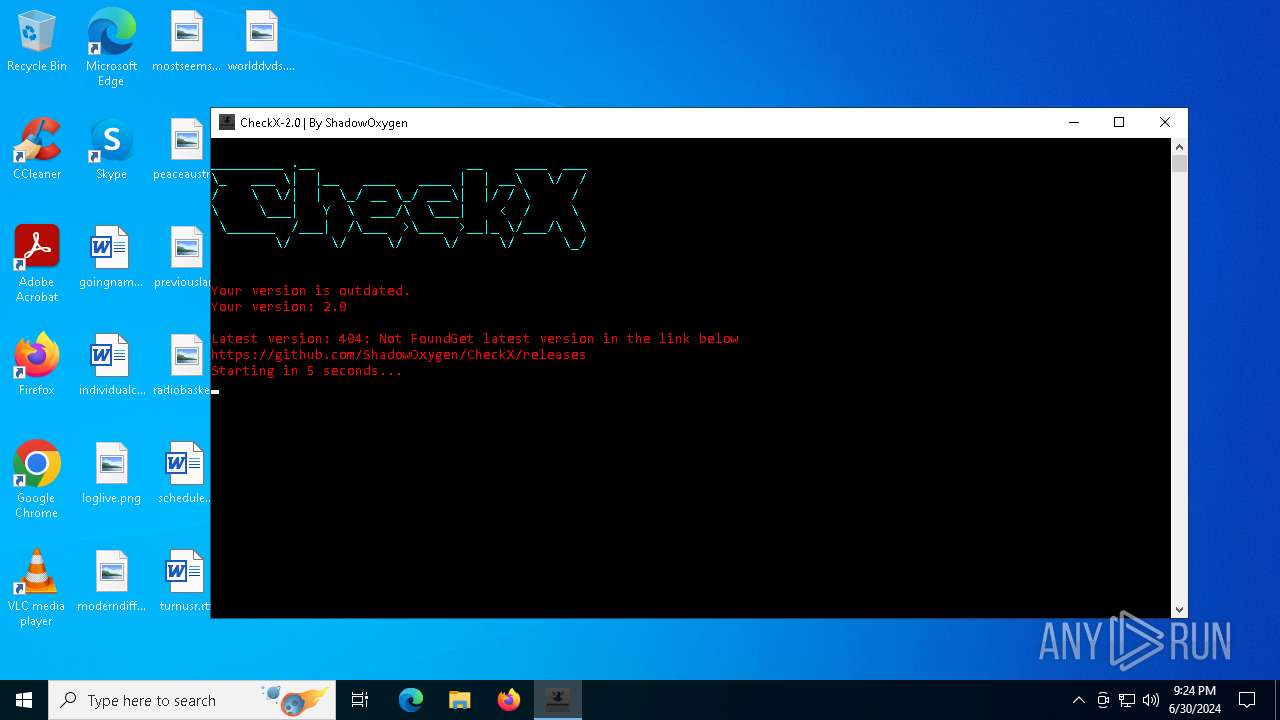
| File name: | CheckX-2.0.exe |
| Full analysis: | https://app.any.run/tasks/208a2cf1-fc43-49ca-afdc-f19b2ba23c71 |
| Verdict: | Malicious activity |
| Analysis date: | June 30, 2024, 21:24:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 85A9E00A5F25949CEF88DAA428822EE6 |
| SHA1: | 922C83F8B177BF5C8A348AA04DFAA2A4223A835D |
| SHA256: | D4B81CB86A71288707EB4182E8C754473E44A6A405A7E80450FBE9CEE7D48166 |
| SSDEEP: | 98304:cwMmw9aMoYB6LvlGqgOeszHh29qoVx+IZbFY8y8fPZ/nz/1pIOwcTViRwlv9Exw2:OUpKOx6mFh0KBcM2yqAc8 |
MALICIOUS
Drops the executable file immediately after the start
- CheckX-2.0.exe (PID: 5504)
SUSPICIOUS
Process drops legitimate windows executable
- CheckX-2.0.exe (PID: 5504)
Process drops python dynamic module
- CheckX-2.0.exe (PID: 5504)
Loads Python modules
- CheckX-2.0.exe (PID: 6228)
Potential Corporate Privacy Violation
- CheckX-2.0.exe (PID: 6228)
Checks for external IP
- CheckX-2.0.exe (PID: 6228)
Starts CMD.EXE for commands execution
- CheckX-2.0.exe (PID: 6228)
Application launched itself
- CheckX-2.0.exe (PID: 5504)
The process drops C-runtime libraries
- CheckX-2.0.exe (PID: 5504)
Executable content was dropped or overwritten
- CheckX-2.0.exe (PID: 5504)
INFO
Reads the computer name
- CheckX-2.0.exe (PID: 5504)
- CheckX-2.0.exe (PID: 6228)
Create files in a temporary directory
- CheckX-2.0.exe (PID: 5504)
- CheckX-2.0.exe (PID: 6228)
Checks supported languages
- CheckX-2.0.exe (PID: 6228)
- CheckX-2.0.exe (PID: 5504)
Reads the machine GUID from the registry
- CheckX-2.0.exe (PID: 6228)
Checks proxy server information
- CheckX-2.0.exe (PID: 6228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:08:08 12:28:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 135168 |
| InitializedDataSize: | 125440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8654 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
140
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CheckX-2.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5504 | "C:\Users\admin\AppData\Local\Temp\CheckX-2.0.exe" | C:\Users\admin\AppData\Local\Temp\CheckX-2.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 6228 | "C:\Users\admin\AppData\Local\Temp\CheckX-2.0.exe" | C:\Users\admin\AppData\Local\Temp\CheckX-2.0.exe | CheckX-2.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | CheckX-2.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
533
Read events
533
Write events
0
Delete events
0
Modification events
Executable files
24
Suspicious files
4
Text files
927
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_cffi_backend.cp37-win_amd64.pyd | executable | |
MD5:A9DF512BAE71F3618F77AEC6403B1D7C | SHA256:0087F25BEEED4D2CB0F9DA8E0D4F4DFA0E670C1CCE46E71738A67E990D991A8A | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\VCRUNTIME140.dll | executable | |
MD5:0C583614EB8FFB4C8C2D9E9880220F1D | SHA256:6CADB4FEF773C23B511ACC8B715A084815C6E41DD8C694BC70090A97B3B03FB9 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\CheckX-2.0.exe.manifest | xml | |
MD5:79958583AFB74E9DC6A328F33520C43D | SHA256:AF9F6DDBDC0DCC4DF3F5E05E3150FE508F60BBC79A921245A225300BD2B9219E | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_lzma.pyd | executable | |
MD5:2645AA11D8C4FFB04A8C5E04A440EC46 | SHA256:519F9E23D88AE387EA7D38BBC941A770A4B3ECC8C464A8ED0D977004344E4DE3 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_elementtree.pyd | executable | |
MD5:7E36B45AEEF3A9F0179933A4105829D6 | SHA256:F6D69EF4A7243EB3FEBED5FFAFD56A58596BBD886255D5D344893B98065449E3 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_yaml.cp37-win_amd64.pyd | executable | |
MD5:1CA3188F23ED58F3B2D624FC8D527754 | SHA256:D232B2AED474F93B1524EDAA5A5B0A742CEC1B39FD2B6F4FD4677538E2231302 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_socket.pyd | executable | |
MD5:35BBB04A44F81A1C95216A2DFDB82516 | SHA256:697E0A45EBE100DCE1DC4E11D11CD9E2B60D74EF4C7DF1CEFBE0E334D3997F7A | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_multiprocessing.pyd | executable | |
MD5:5D79454A1AF9EA1D19640C64F1ABD524 | SHA256:081420B369AC26AA08A9A9E66309274DFEE32C6D8DEAB277BF774A9A10494A32 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_testcapi.pyd | executable | |
MD5:578612F9622548C82BA76DEC76C4E937 | SHA256:841E820B74E5CB4F1F5DD387209C9E969E4BFBA76F259FA5F066735FE53D5375 | |||
| 5504 | CheckX-2.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI55042\_decimal.pyd | executable | |
MD5:1C9E794F2E7B289DE7E93FA7D75F44D1 | SHA256:C440319A641BD2B8E93D9B9264063D5AA8A89FC4465183A20781AAEE3C7257DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
82
DNS requests
28
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3872 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
3624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
420 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6228 | CheckX-2.0.exe | GET | 200 | 172.67.74.152:80 | http://api.ipify.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 92.123.104.17:443 | r.bing.com | Akamai International B.V. | DE | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4632 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5784 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3872 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3872 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3872 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3872 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3040 | OfficeClickToRun.exe | 104.208.16.89:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
mcr-ring-fallback.msedge.net |
| unknown |
t-ring-fdv2.msedge.net |
| unknown |
k-ring.msedge.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6228 | CheckX-2.0.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
6228 | CheckX-2.0.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup api.ipify.org |
2168 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6228 | CheckX-2.0.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
1 ETPRO signatures available at the full report