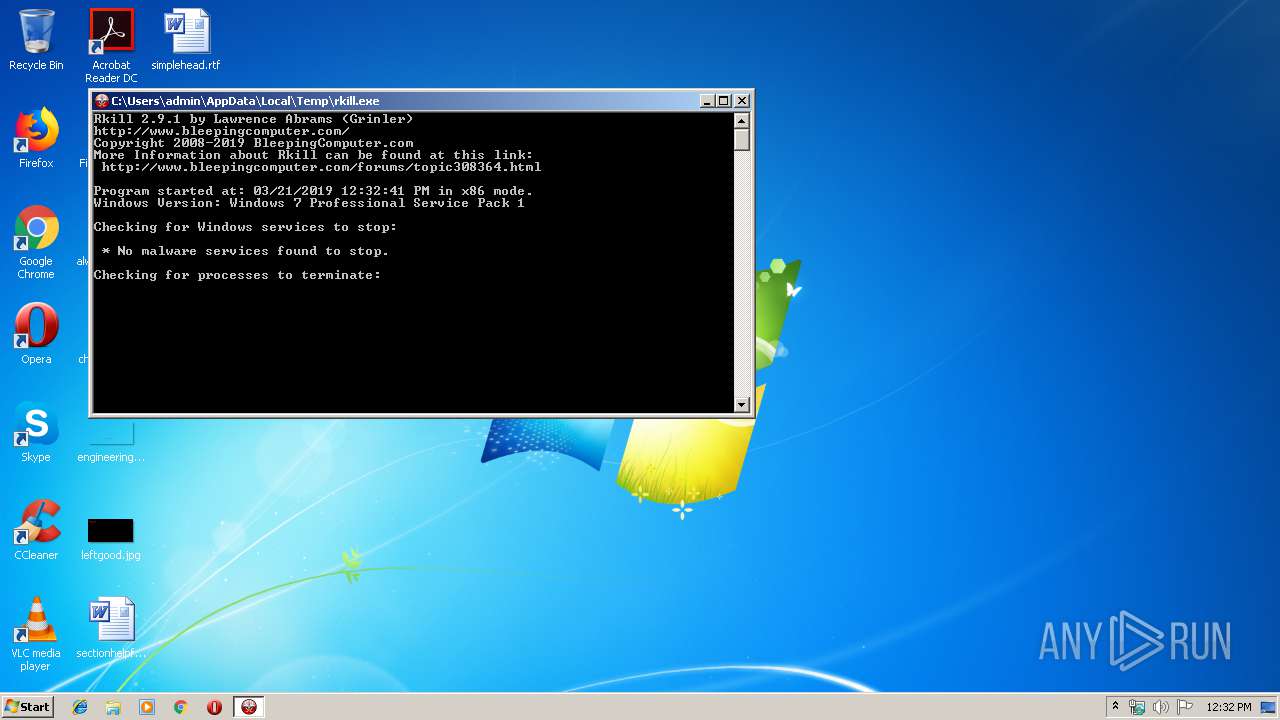
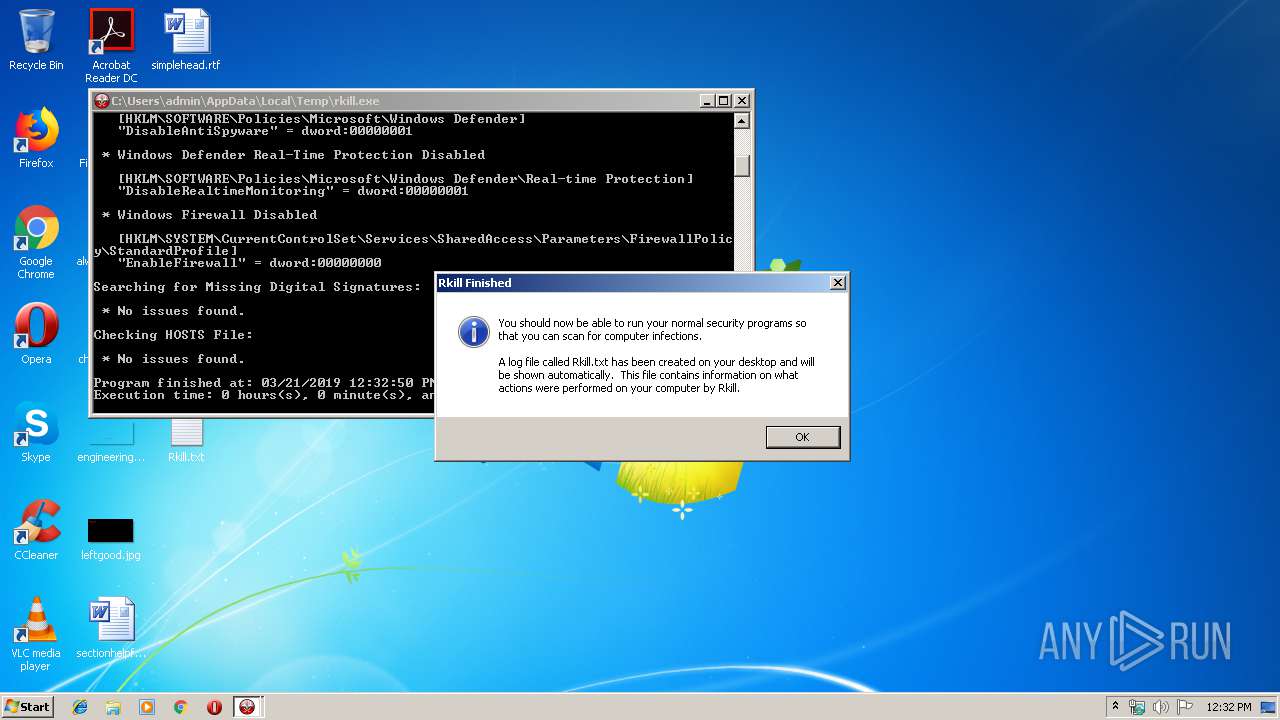
| File name: | rkill.exe |
| Full analysis: | https://app.any.run/tasks/af595b04-b071-4427-801b-b7995d52ff3b |
| Verdict: | No threats detected |
| Analysis date: | March 21, 2019, 12:32:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 6D622DCC87EDC9A7B10D35372ADE816B |
| SHA1: | 47D98825B03C507B85DEC02A2297E03EBC925F30 |
| SHA256: | D4AC5B3C525A5FD94019D80FF81B552E73B19B1BD0A554B9609CDD5E1B00955A |
| SSDEEP: | 49152:KpEsgw14kZV2HXsMnmjEREseBSsxHnfXsrHYi2Yijig:0wYJYW |
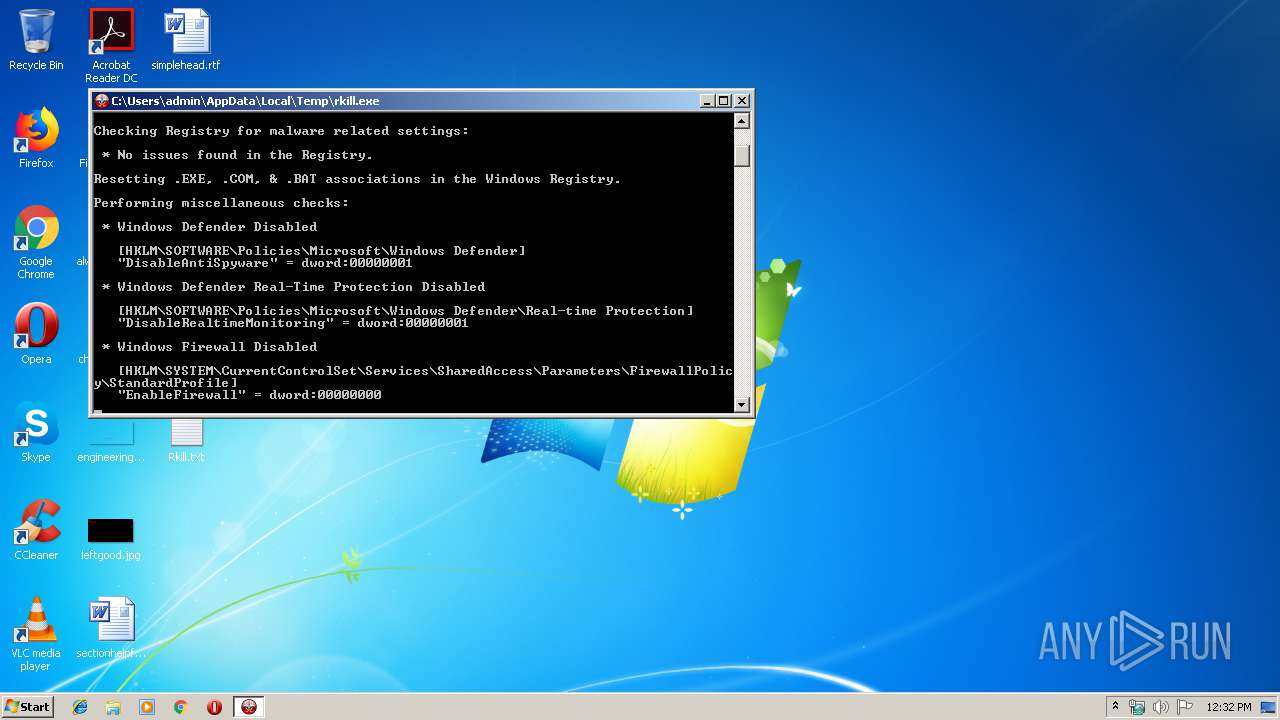
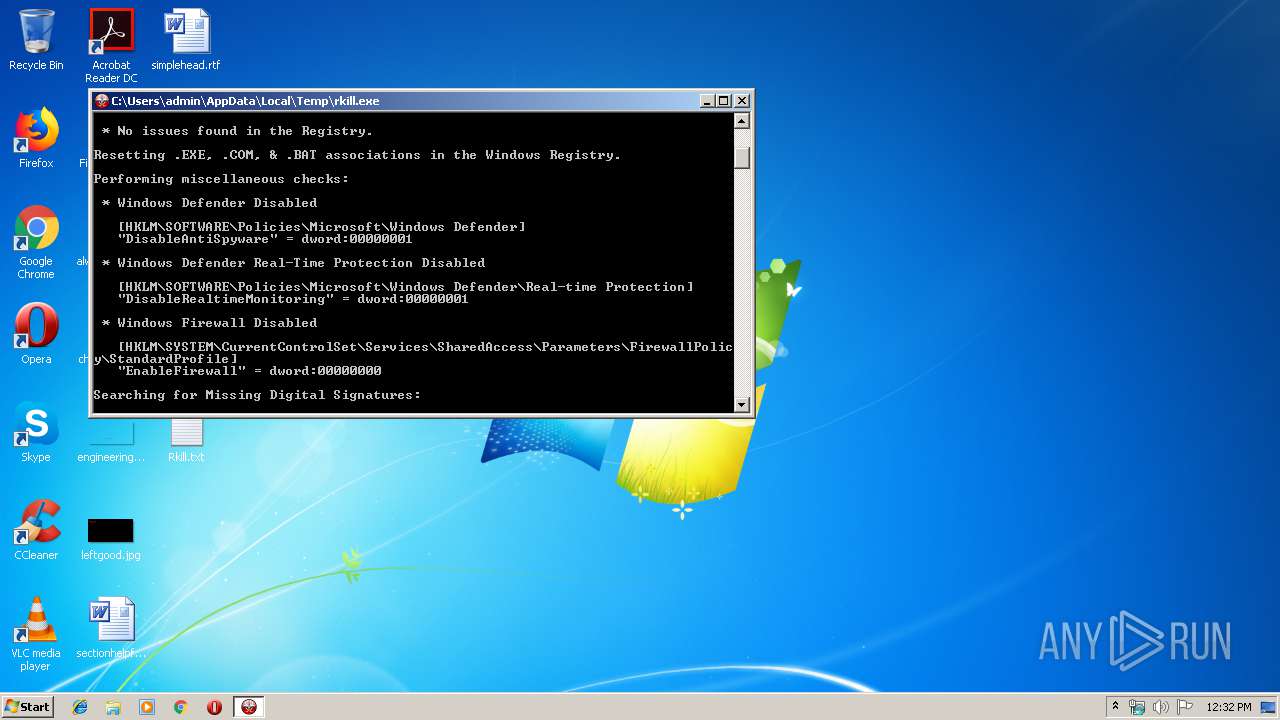
MALICIOUS
Changes settings of System certificates
- rkill.exe (PID: 2756)
SUSPICIOUS
Adds / modifies Windows certificates
- rkill.exe (PID: 2756)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:13 16:08:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 448512 |
| InitializedDataSize: | 1341952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x52cbb |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.9.1.0 |
| ProductVersionNumber: | 2.9.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Bleeping Computer, LLC |
| FileDescription: | Terminates malware processes so that you can run your normal security programs. |
| FileVersion: | 2.9.1 |
| InternalName: | rkill.exe |
| LegalCopyright: | © BleepingComputer.com. All rights reserved. |
| LegalTrademarks1: | - |
| LegalTrademarks2: | - |
| OriginalFileName: | rkill.exe |
| ProductName: | Rkill |
| ProductVersion: | 2.9.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 13-Mar-2018 15:08:50 |
| Detected languages: |
|
| CompanyName: | Bleeping Computer, LLC |
| FileDescription: | Terminates malware processes so that you can run your normal security programs. |
| FileVersion: | 2.9.1 |
| InternalName: | rkill.exe |
| LegalCopyright: | © BleepingComputer.com. All rights reserved. |
| LegalTrademarks1: | - |
| LegalTrademarks2: | - |
| OriginalFilename: | rkill.exe |
| ProductName: | Rkill |
| ProductVersion: | 2.9.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Mar-2018 15:08:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006D7C5 | 0x0006D800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62901 |
.rdata | 0x0006F000 | 0x00026C48 | 0x00026E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.99852 |
.data | 0x00096000 | 0x0000B064 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78589 |
.rsrc | 0x000A2000 | 0x00113490 | 0x00113600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.65951 |
.reloc | 0x001B6000 | 0x000087A4 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.59752 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09286 | 931 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.94092 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.36267 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.38323 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.57638 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.9791 | 59287 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.53099 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.54723 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.91709 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.71329 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINTRUST.dll |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
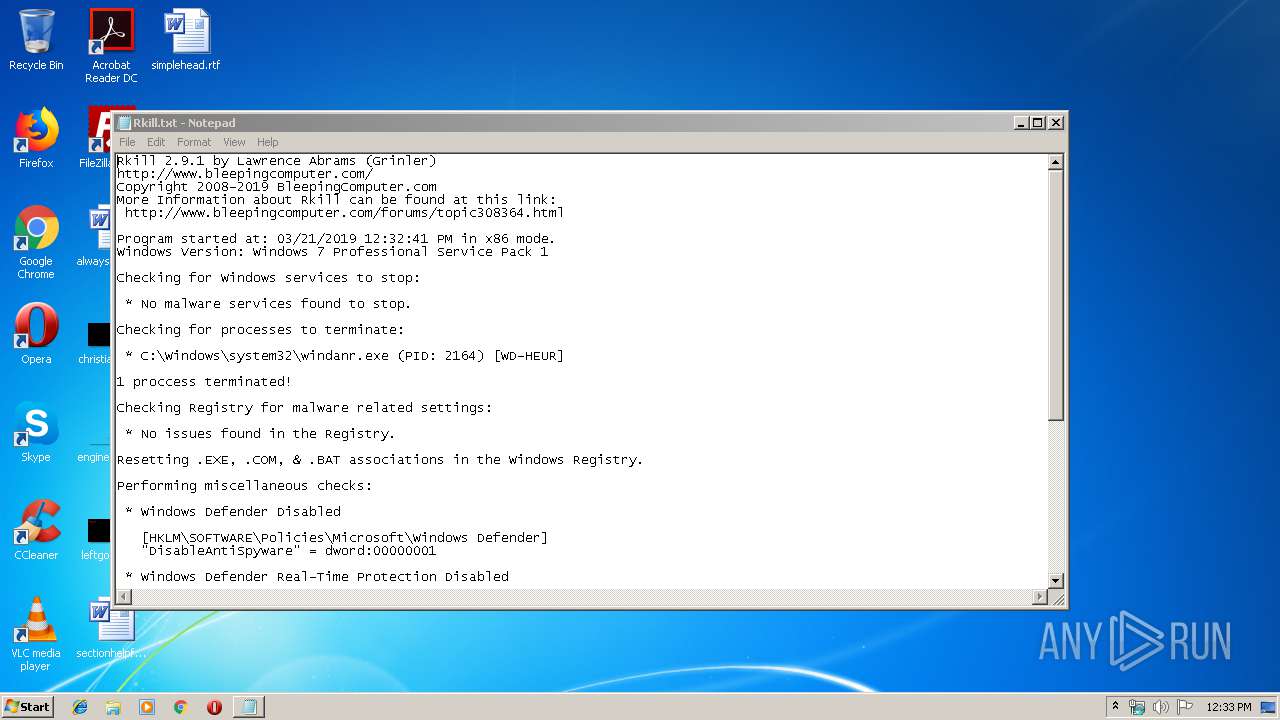
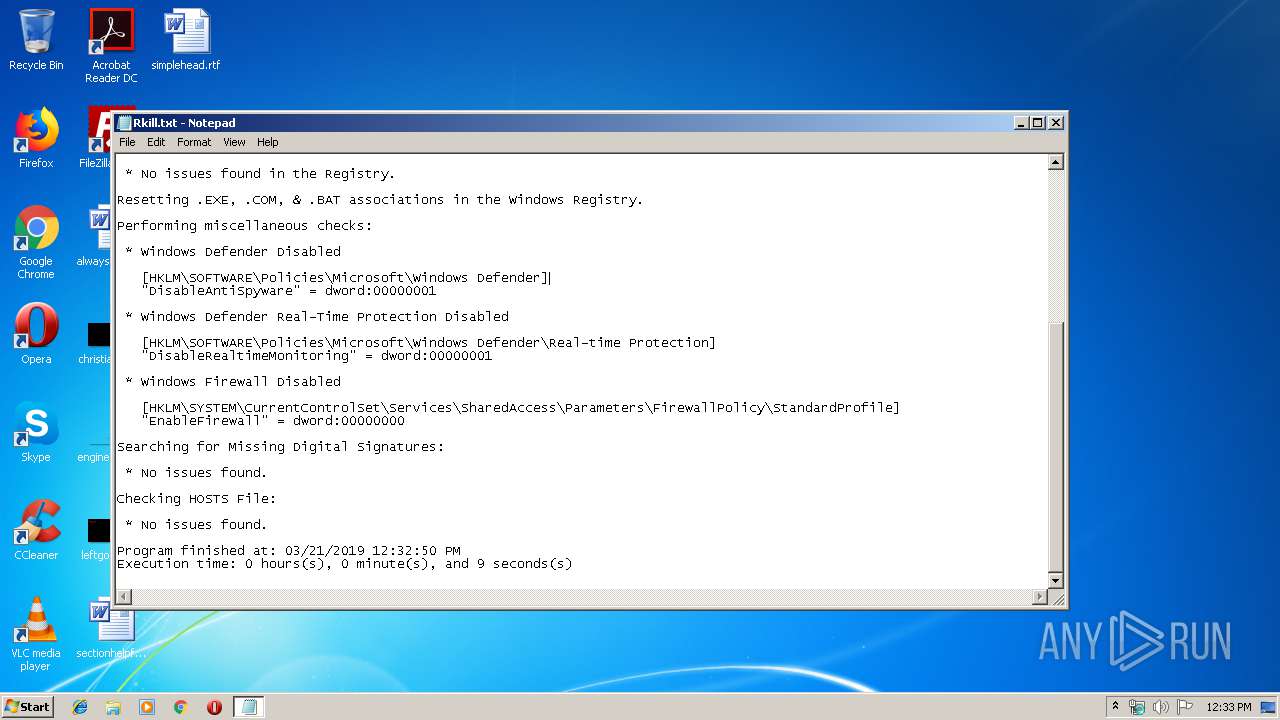
| 2624 | Notepad.exe C:\Users\admin\Desktop\Rkill.txt | C:\Windows\System32\Notepad.exe | — | rkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\Temp\rkill.exe" | C:\Users\admin\AppData\Local\Temp\rkill.exe | explorer.exe | ||||||||||||
User: admin Company: Bleeping Computer, LLC Integrity Level: HIGH Description: Terminates malware processes so that you can run your normal security programs. Exit code: 0 Version: 2.9.1 Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\AppData\Local\Temp\rkill.exe" | C:\Users\admin\AppData\Local\Temp\rkill.exe | — | explorer.exe | |||||||||||
User: admin Company: Bleeping Computer, LLC Integrity Level: MEDIUM Description: Terminates malware processes so that you can run your normal security programs. Exit code: 3221226540 Version: 2.9.1 Modules
| |||||||||||||||
Total events
91
Read events
38
Write events
53
Delete events
0
Modification events
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\E12DFB4B41D7D9C32B30514BAC1D81D8385E2D46 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000F45A0858C9CD920E647BAD539AB9F1CFC77F24CB090000000100000016000000301406082B0601050507030306082B06010505070308140000000100000014000000DAED6474149C143CABDD99A9BD5B284D8B3CC9D80B000000010000001400000055005300450052005400720075007300740000001D0000000100000010000000F919B9CCCE1E59C2E785F7DC2CCF6708030000000100000014000000E12DFB4B41D7D9C32B30514BAC1D81D8385E2D4620000000010000006A040000308204663082034EA003020102021044BE0C8B500024B411D3362DE0B35F1B300D06092A864886F70D0101050500308195310B3009060355040613025553310B3009060355040813025554311730150603550407130E53616C74204C616B652043697479311E301C060355040A131554686520555345525452555354204E6574776F726B3121301F060355040B1318687474703A2F2F7777772E7573657274727573742E636F6D311D301B0603550403131455544E2D5553455246697273742D4F626A656374301E170D3939303730393138333132305A170D3139303730393138343033365A308195310B3009060355040613025553310B3009060355040813025554311730150603550407130E53616C74204C616B652043697479311E301C060355040A131554686520555345525452555354204E6574776F726B3121301F060355040B1318687474703A2F2F7777772E7573657274727573742E636F6D311D301B0603550403131455544E2D5553455246697273742D4F626A65637430820122300D06092A864886F70D01010105000382010F003082010A0282010100CEAA813FA3A36178AA31005595119E270F1F1CDF3A9B826830C04A611DF12F0EFABE79F7A523EF55519684CDDBE3B96E3E31D80A2067C7F4D9BF94EB47043E02CE2AA25D870409F6309D188A97B2AA1CFC41D2A136CBFB3D91BAE7D97035FAE4E790C39BA39BD33CF5129977B1B709E068E61CB8F39463886A6AFE0B76C9BEF422E467B9AB1A5E77C18507DD0D6CBFEE06C7776A419EA70FD7FBEE9417B7FC85BEA4ABC41C31DDD7B6D1E4F0EFDF168FB25293D7A1D489A1072EBFE10112421E1AE1D89534DB647928FFBA2E11C2E5E85B9248FB470BC26CDAAD328341F3A5E54170FD65906DFAFA51C4F9BD962B19042CD36DA7DCF07F6F8365E26AAB8786750203010001A381AF3081AC300B0603551D0F0404030201C6300F0603551D130101FF040530030101FF301D0603551D0E04160414DAED6474149C143CABDD99A9BD5B284D8B3CC9D830420603551D1F043B30393037A035A0338631687474703A2F2F63726C2E7573657274727573742E636F6D2F55544E2D5553455246697273742D4F626A6563742E63726C30290603551D250422302006082B0601050507030306082B06010505070308060A2B0601040182370A0304300D06092A864886F70D01010505000382010100081F52B1374478DBFDCEB9DA959698AA556480B55A40DD21A5C5C1F35F2C4CC8475A69EAE8F03535F4D025F3C8A6A4874ABD1BB17308BDD4C3CAB635BB59867731CDA78014AE13EFFCB148F96B25252D51B62C6D45C198C88A565D3EEE434E3E6B278ED03A4B850B5FD3ED6AA775CBD15A872F3975135A72B002819FBEF00F845420626C69D4E14DC60D9943010D12968C789DBF50A2B144AA6ACF177ACF6F0FD4F824555FF0341649663E5046C96371383162B862B9F353AD6CB52BA212AA194F09DA5EE793C68E1408FEF0308018A086854DC87DD78B03FE6ED5F79D16AC922CA023E59C91521F94DF179473C3B3C1C17105200078BD13521DA83ECD001FC8 | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\E12DFB4B41D7D9C32B30514BAC1D81D8385E2D46 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000E843AC3B52EC8C297FA948C9B1FB2819030000000100000014000000E12DFB4B41D7D9C32B30514BAC1D81D8385E2D461D0000000100000010000000F919B9CCCE1E59C2E785F7DC2CCF67080B00000001000000140000005500530045005200540072007500730074000000140000000100000014000000DAED6474149C143CABDD99A9BD5B284D8B3CC9D8090000000100000016000000301406082B0601050507030306082B060105050703080F0000000100000014000000F45A0858C9CD920E647BAD539AB9F1CFC77F24CB20000000010000006A040000308204663082034EA003020102021044BE0C8B500024B411D3362DE0B35F1B300D06092A864886F70D0101050500308195310B3009060355040613025553310B3009060355040813025554311730150603550407130E53616C74204C616B652043697479311E301C060355040A131554686520555345525452555354204E6574776F726B3121301F060355040B1318687474703A2F2F7777772E7573657274727573742E636F6D311D301B0603550403131455544E2D5553455246697273742D4F626A656374301E170D3939303730393138333132305A170D3139303730393138343033365A308195310B3009060355040613025553310B3009060355040813025554311730150603550407130E53616C74204C616B652043697479311E301C060355040A131554686520555345525452555354204E6574776F726B3121301F060355040B1318687474703A2F2F7777772E7573657274727573742E636F6D311D301B0603550403131455544E2D5553455246697273742D4F626A65637430820122300D06092A864886F70D01010105000382010F003082010A0282010100CEAA813FA3A36178AA31005595119E270F1F1CDF3A9B826830C04A611DF12F0EFABE79F7A523EF55519684CDDBE3B96E3E31D80A2067C7F4D9BF94EB47043E02CE2AA25D870409F6309D188A97B2AA1CFC41D2A136CBFB3D91BAE7D97035FAE4E790C39BA39BD33CF5129977B1B709E068E61CB8F39463886A6AFE0B76C9BEF422E467B9AB1A5E77C18507DD0D6CBFEE06C7776A419EA70FD7FBEE9417B7FC85BEA4ABC41C31DDD7B6D1E4F0EFDF168FB25293D7A1D489A1072EBFE10112421E1AE1D89534DB647928FFBA2E11C2E5E85B9248FB470BC26CDAAD328341F3A5E54170FD65906DFAFA51C4F9BD962B19042CD36DA7DCF07F6F8365E26AAB8786750203010001A381AF3081AC300B0603551D0F0404030201C6300F0603551D130101FF040530030101FF301D0603551D0E04160414DAED6474149C143CABDD99A9BD5B284D8B3CC9D830420603551D1F043B30393037A035A0338631687474703A2F2F63726C2E7573657274727573742E636F6D2F55544E2D5553455246697273742D4F626A6563742E63726C30290603551D250422302006082B0601050507030306082B06010505070308060A2B0601040182370A0304300D06092A864886F70D01010505000382010100081F52B1374478DBFDCEB9DA959698AA556480B55A40DD21A5C5C1F35F2C4CC8475A69EAE8F03535F4D025F3C8A6A4874ABD1BB17308BDD4C3CAB635BB59867731CDA78014AE13EFFCB148F96B25252D51B62C6D45C198C88A565D3EEE434E3E6B278ED03A4B850B5FD3ED6AA775CBD15A872F3975135A72B002819FBEF00F845420626C69D4E14DC60D9943010D12968C789DBF50A2B144AA6ACF177ACF6F0FD4F824555FF0341649663E5046C96371383162B862B9F353AD6CB52BA212AA194F09DA5EE793C68E1408FEF0308018A086854DC87DD78B03FE6ED5F79D16AC922CA023E59C91521F94DF179473C3B3C1C17105200078BD13521DA83ECD001FC8 | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe\PersistentHandler |
| Operation: | write | Name: | |
Value: {098f2470-bae0-11cd-b579-08002b30bfeb} | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe |
| Operation: | write | Name: | Content Type |
Value: application/x-msdownload | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile |
| Operation: | write | Name: | |
Value: Application | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile |
| Operation: | write | Name: | EditFlags |
Value: 38070000 | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\open |
| Operation: | write | Name: | EditFlags |
Value: 00000000 | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile |
| Operation: | write | Name: | FriendlyTypeName |
Value: @%SystemRoot%\System32\shell32.dll,-10156 | |||
| (PID) Process: | (2756) rkill.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\DefaultIcon |
| Operation: | write | Name: | |
Value: %1 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | rkill.exe | C:\Users\admin\Desktop\Rkill.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report