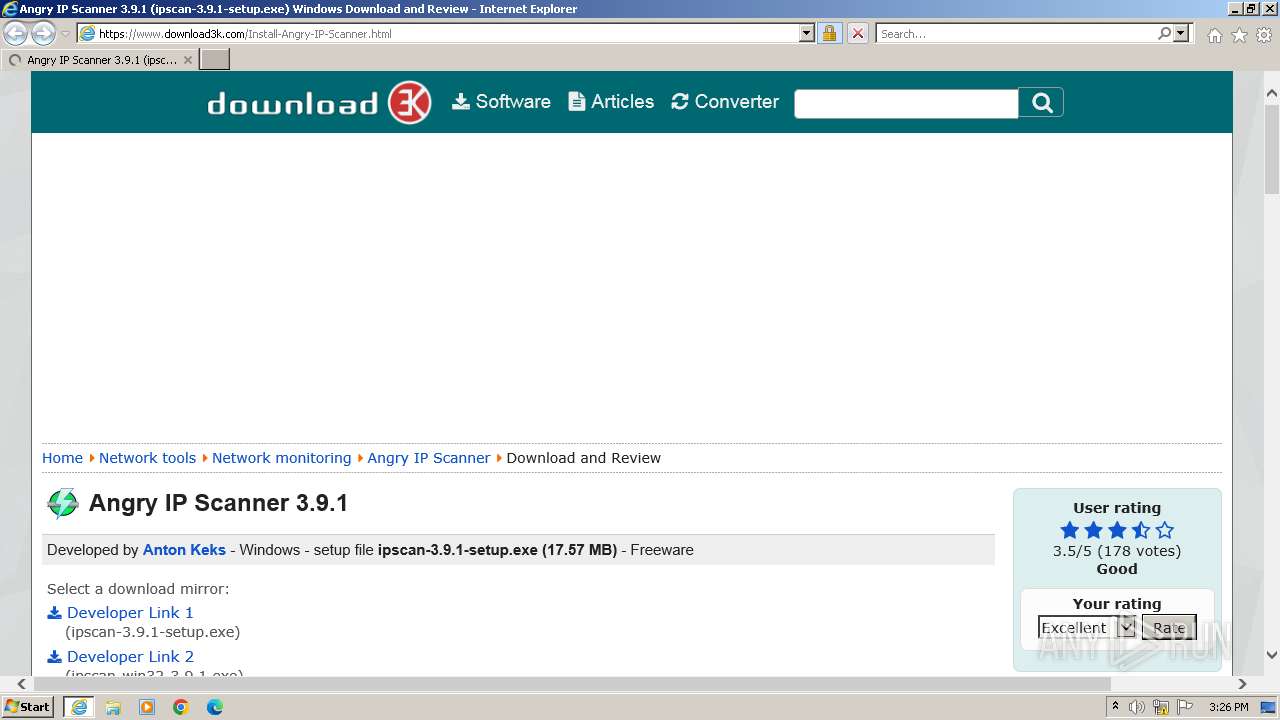
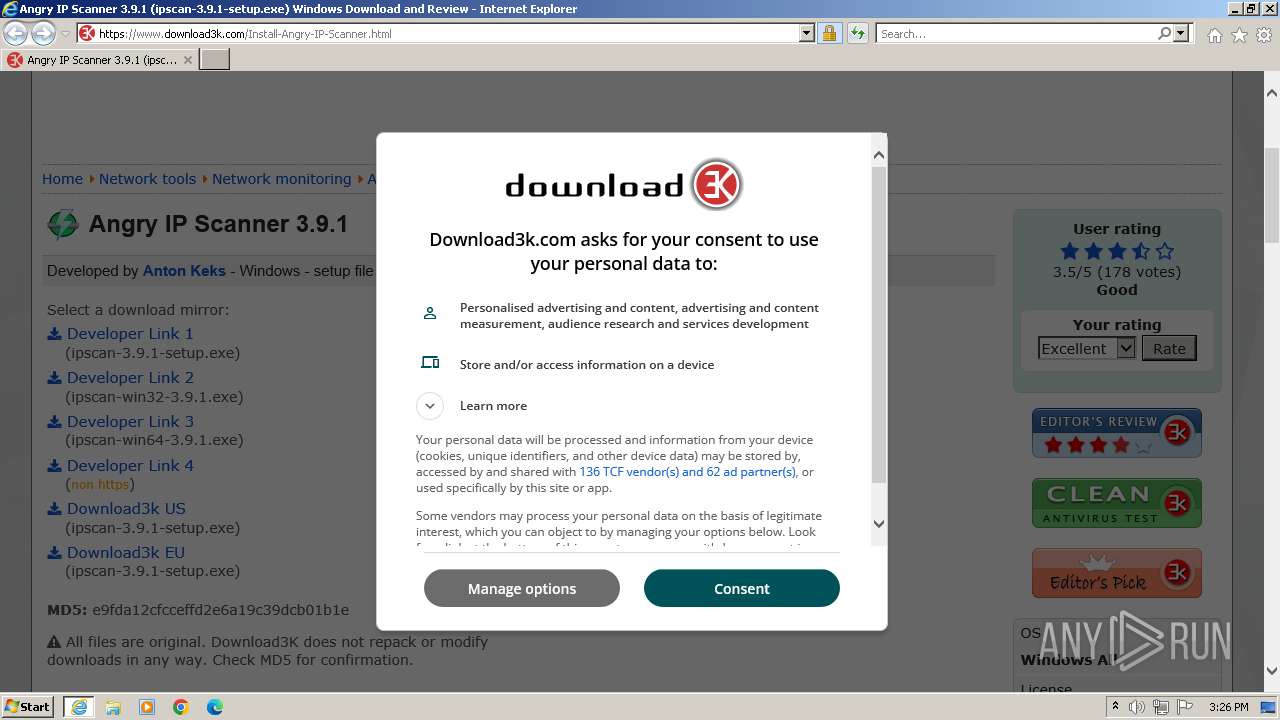
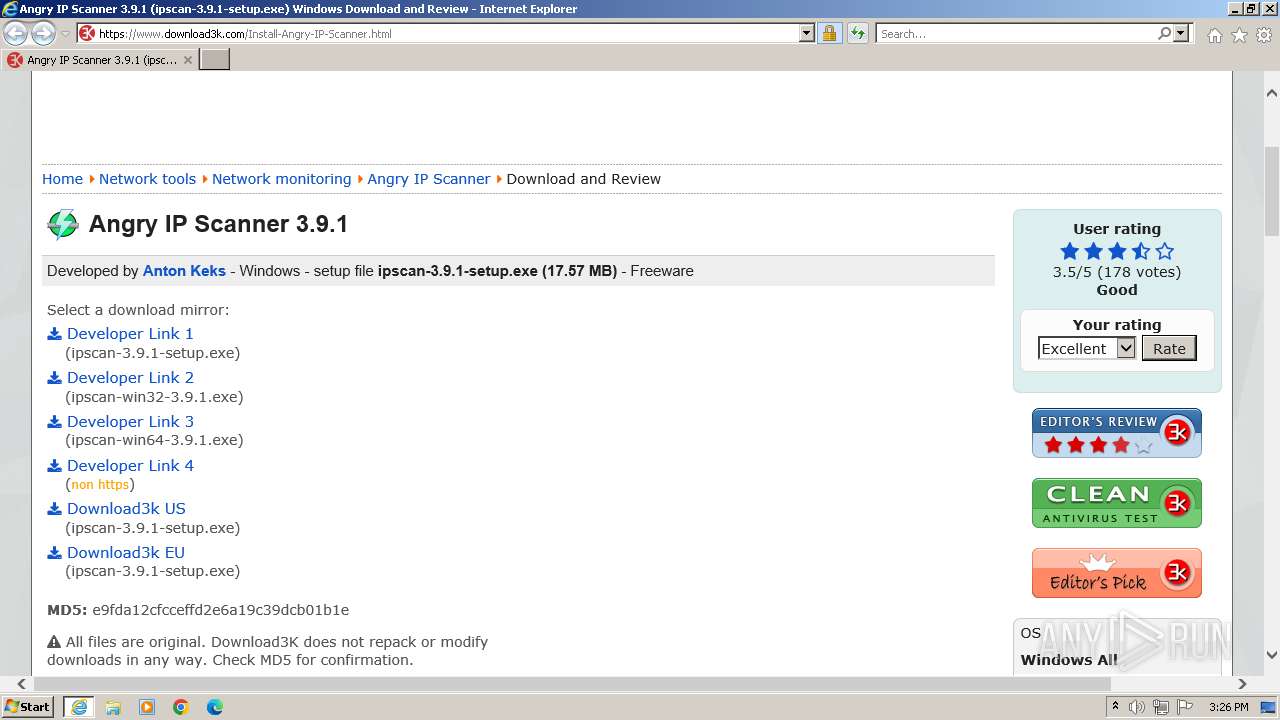
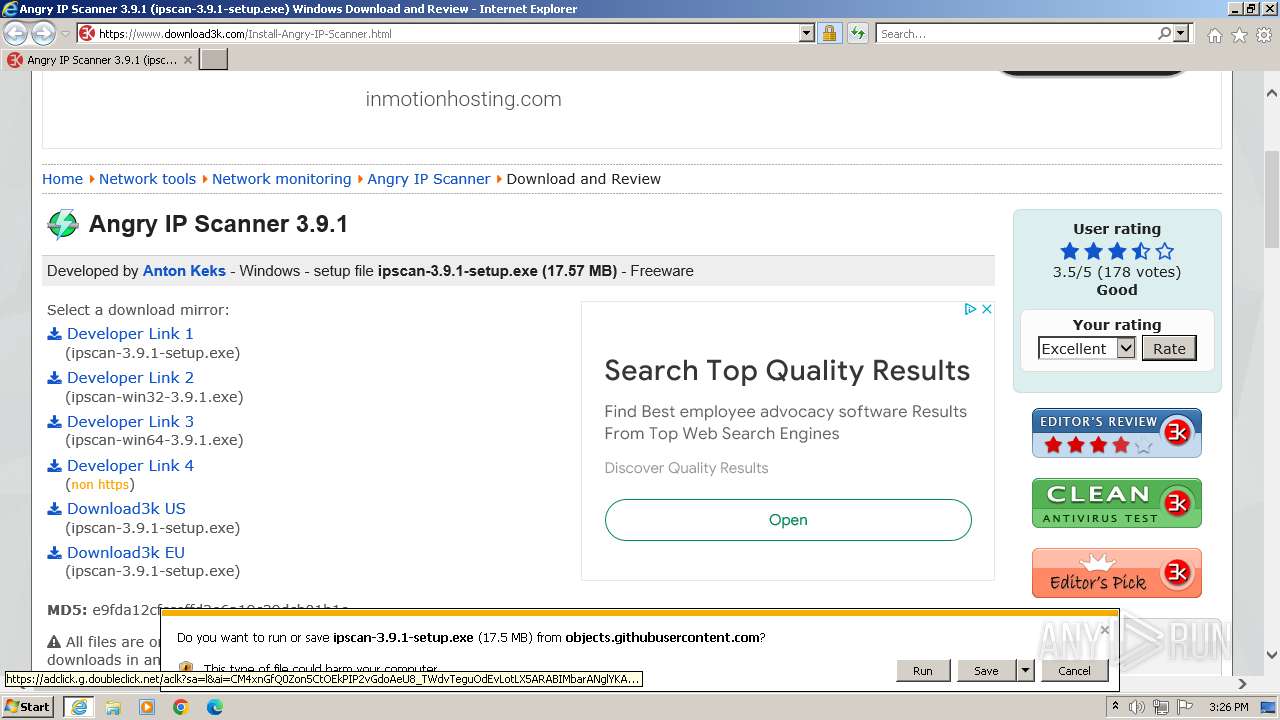
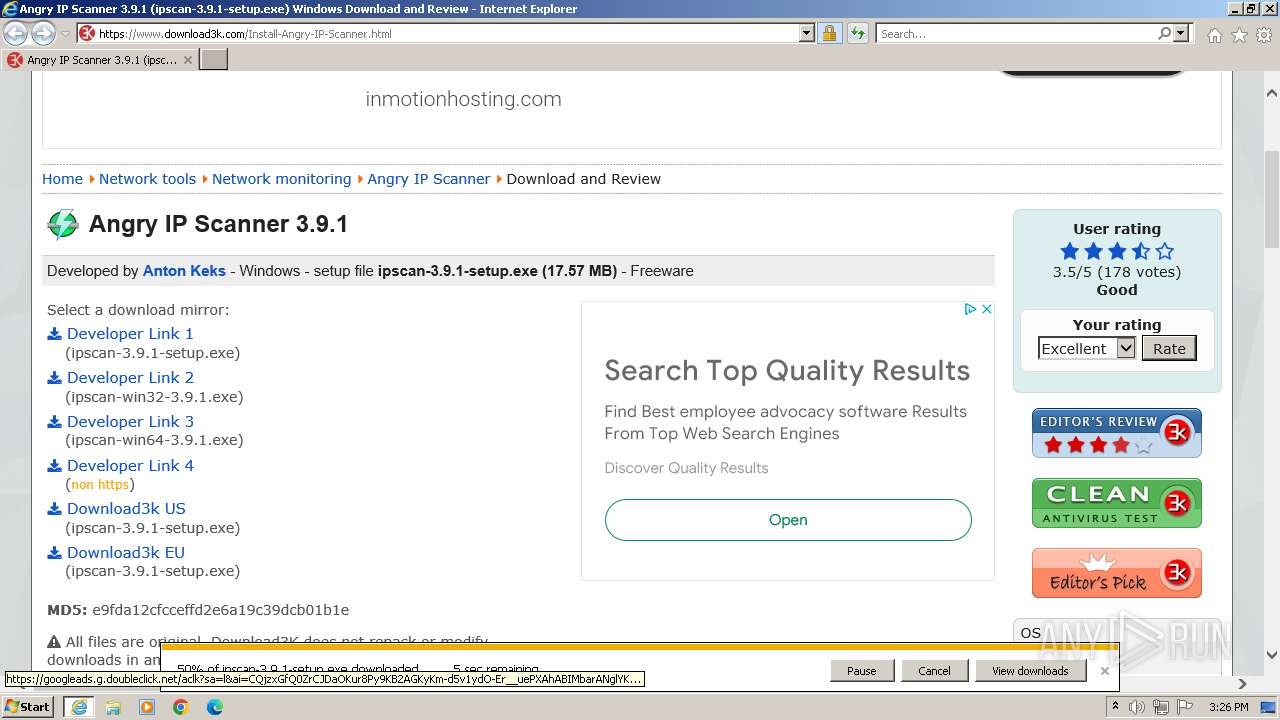
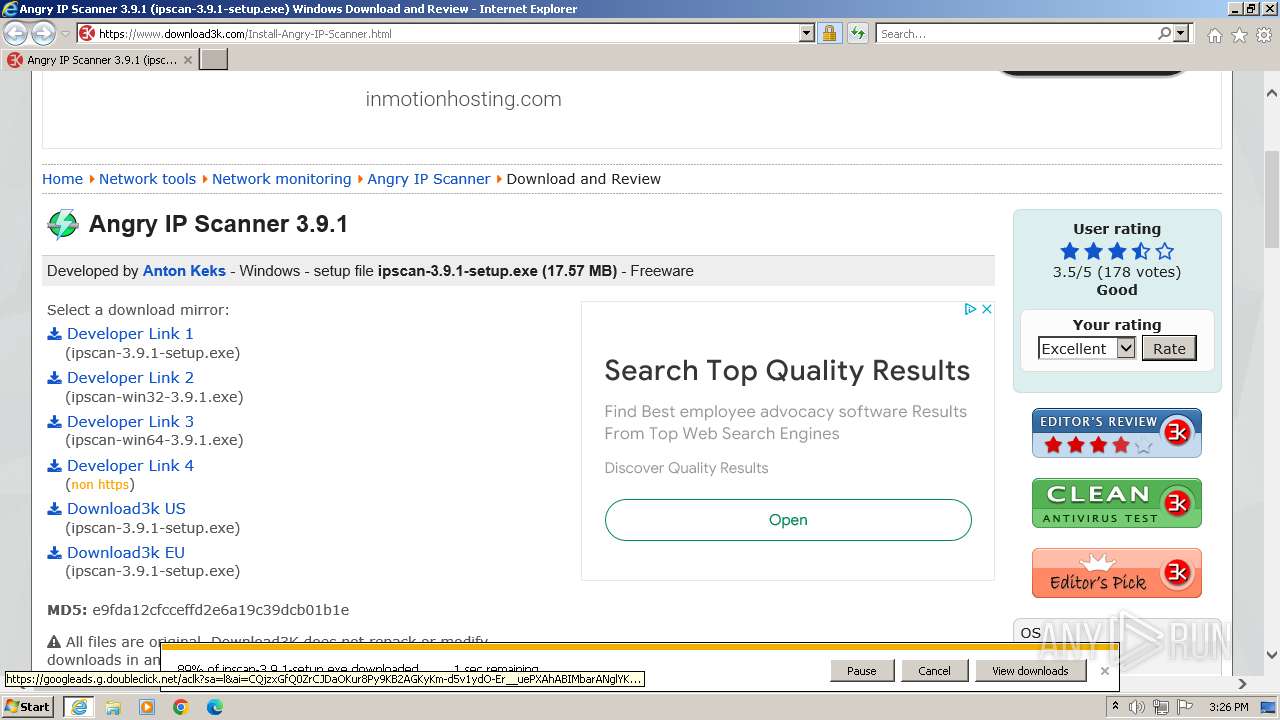
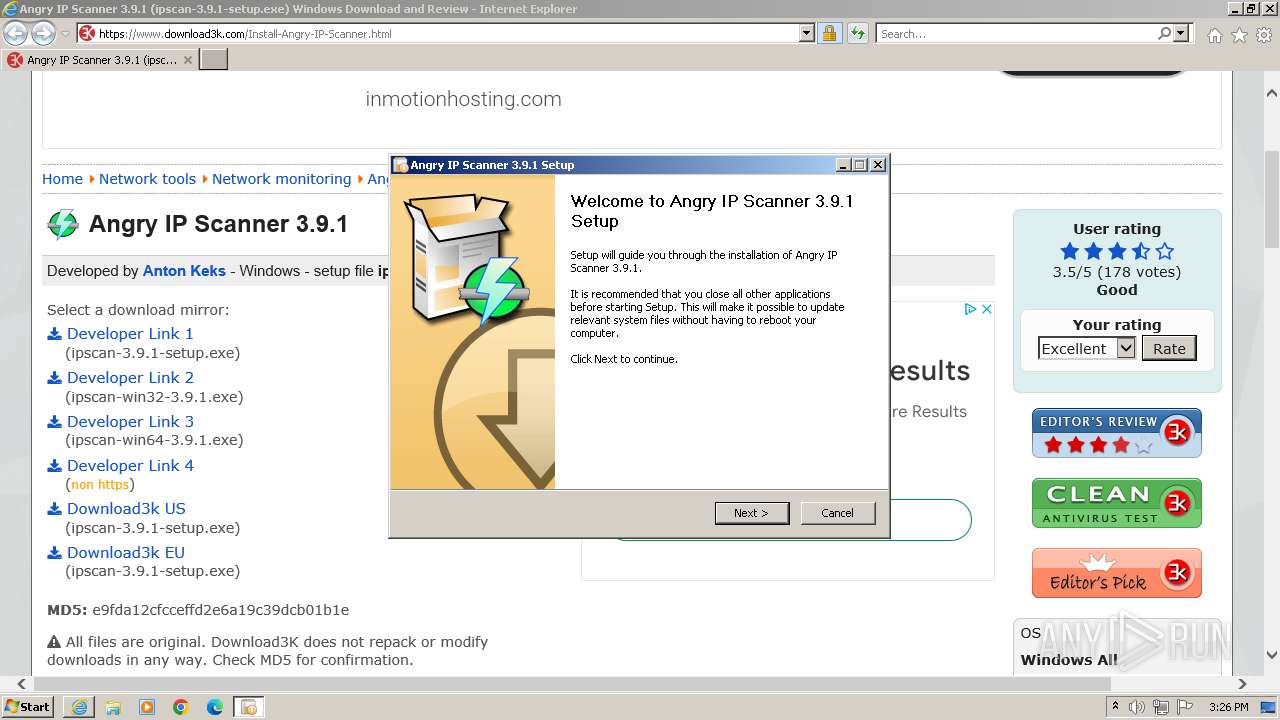
| URL: | https://www.download3k.com/Install-Angry-IP-Scanner.html |
| Full analysis: | https://app.any.run/tasks/1bc03d9f-d62c-4022-b0c5-4ac2dab56f11 |
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2024, 14:26:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FCC1BAB5F4AECC491F90FCFDC59D043C |
| SHA1: | 9225B86D44376BE992ACA31B13CAB53BB9037B9C |
| SHA256: | D4AAC9BDE7C4914B97CEA4E54C23C3594989F1CF4218A7E2545553B6DB9676B6 |
| SSDEEP: | 3:N8DSL0LjyJBX+GiLgG:2OL0yJfbG |
MALICIOUS
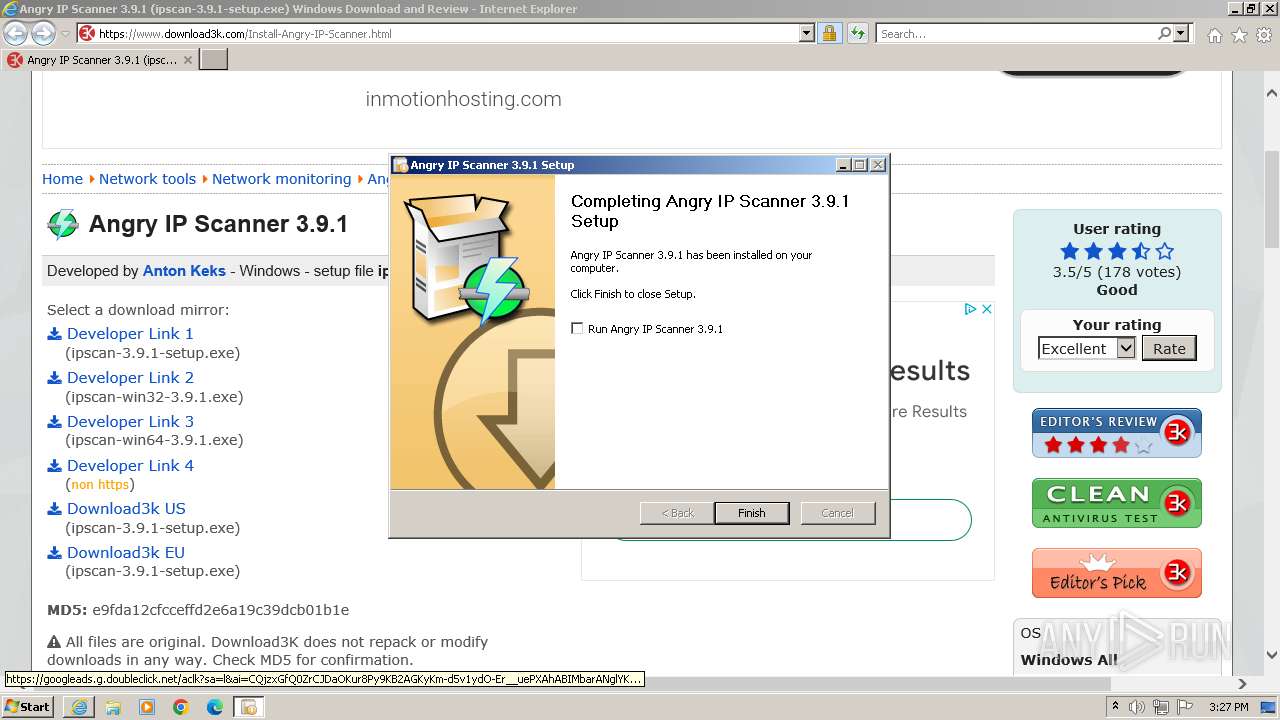
Drops the executable file immediately after the start
- ipscan-3.9.1-setup.exe (PID: 2528)
SUSPICIOUS
Executable content was dropped or overwritten
- ipscan-3.9.1-setup.exe (PID: 2528)
Process drops legitimate windows executable
- ipscan-3.9.1-setup.exe (PID: 2528)
The process drops C-runtime libraries
- ipscan-3.9.1-setup.exe (PID: 2528)
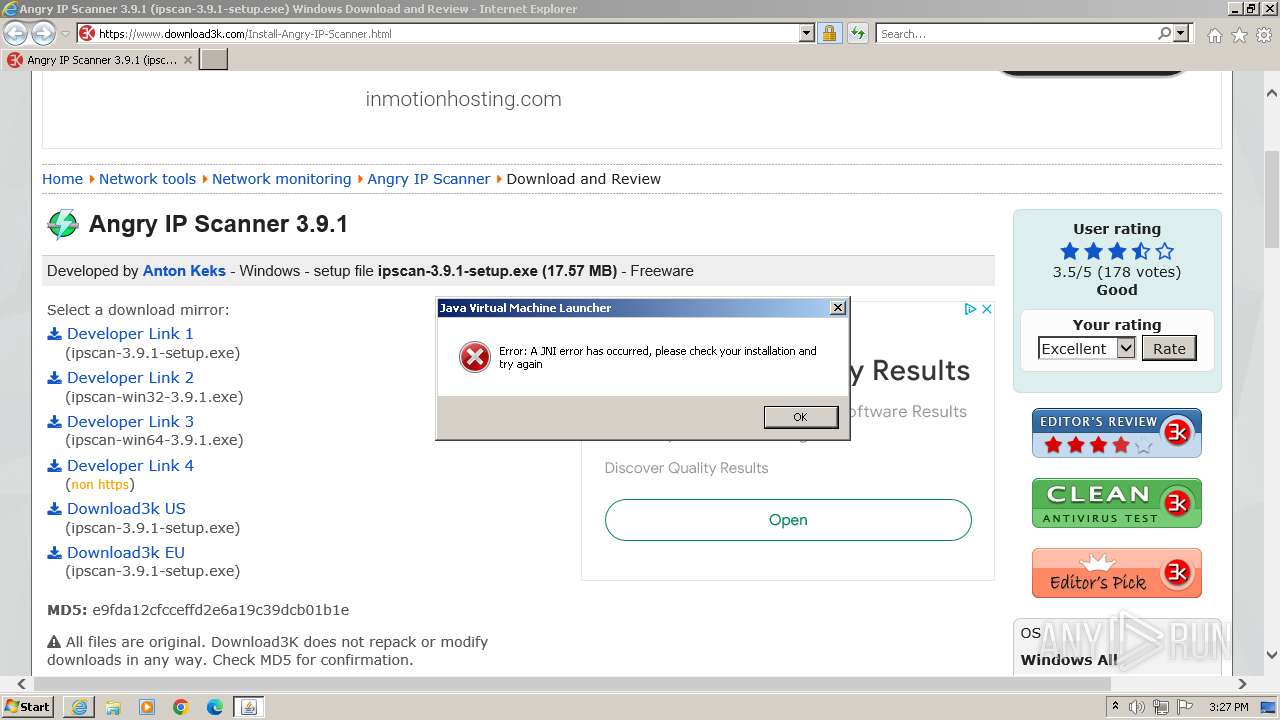
Checks for Java to be installed
- javaw.exe (PID: 992)
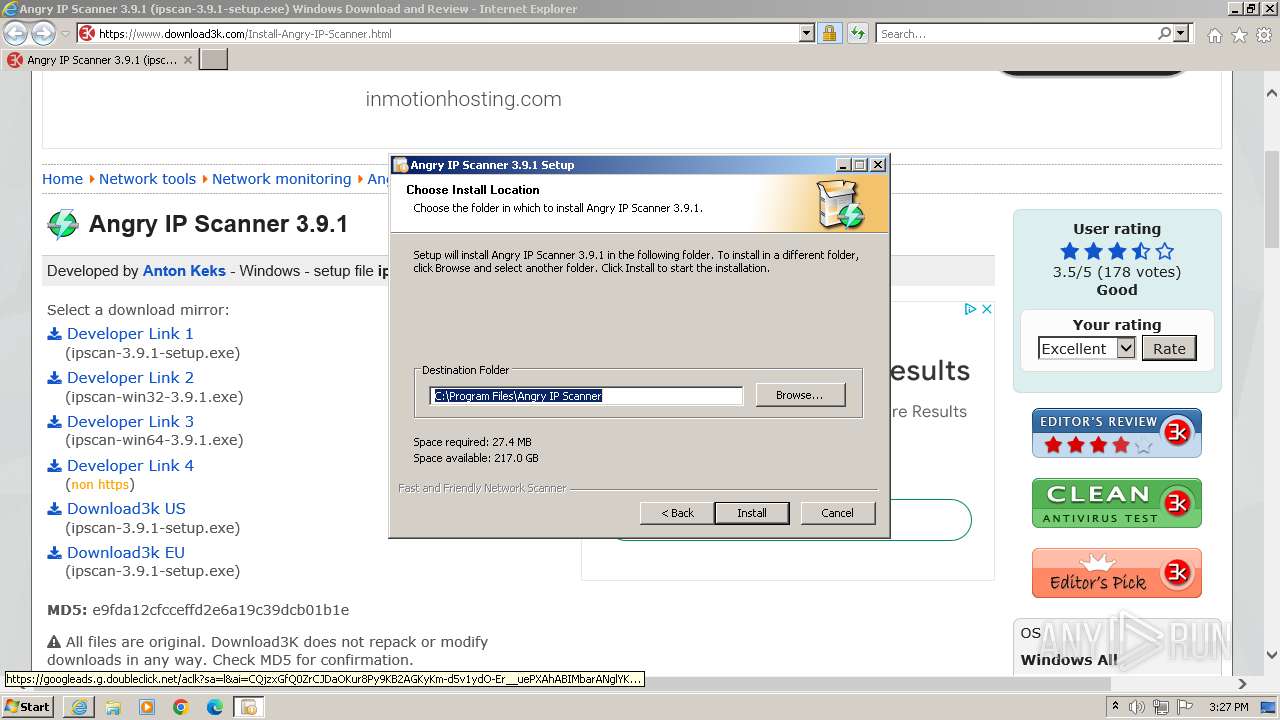
Creates a software uninstall entry
- ipscan-3.9.1-setup.exe (PID: 2528)
The process creates files with name similar to system file names
- ipscan-3.9.1-setup.exe (PID: 2528)
Malware-specific behavior (creating "System.dll" in Temp)
- ipscan-3.9.1-setup.exe (PID: 2528)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1080)
- ipscan-3.9.1-setup.exe (PID: 2528)
- javaw.exe (PID: 992)
- ipscan.exe (PID: 1980)
Manual execution by a user
- wmpnscfg.exe (PID: 1080)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3964)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2092)
- iexplore.exe (PID: 3964)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 2092)
Create files in a temporary directory
- ipscan-3.9.1-setup.exe (PID: 2528)
- javaw.exe (PID: 992)
Creates files in the program directory
- ipscan-3.9.1-setup.exe (PID: 2528)
- javaw.exe (PID: 992)
Reads the computer name
- ipscan-3.9.1-setup.exe (PID: 2528)
- wmpnscfg.exe (PID: 1080)
Application launched itself
- iexplore.exe (PID: 3964)
The process uses the downloaded file
- iexplore.exe (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | javaw -jar "C:\Program Files\Angry IP Scanner\ipscan.exe" | C:\Program Files\Common Files\Oracle\Java\javapath_target_52116515\javaw.exe | — | ipscan.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Angry IP Scanner\ipscan.exe" | C:\Program Files\Angry IP Scanner\ipscan.exe | — | ipscan-3.9.1-setup.exe | |||||||||||
User: admin Company: angryip.org Integrity Level: HIGH Description: Angry IP Scanner - fast and friendly network scanner Exit code: 1 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3964 CREDAT:2364702 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ipscan-3.9.1-setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ipscan-3.9.1-setup.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2456 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2528 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ipscan-3.9.1-setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ipscan-3.9.1-setup.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.download3k.com/Install-Angry-IP-Scanner.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3964 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
39 594
Read events
39 407
Write events
142
Delete events
45
Modification events
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31104357 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31104357 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
23
Suspicious files
70
Text files
237
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B365441F8A43FFD52D1D3D5D52D827D6 | SHA256:8549D71A2A1D601C07F752E176A9D77BEB63649256560424281533D4A2DD1F08 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D73576A2B1E2D4CB9B543CD01BDED20A | binary | |
MD5:92C893B81909166946EC1BCCACA335FD | SHA256:E9612EC7B065D67A310F24CBC730D668BC13D885A76CF3F6CC9E63E11D6AF67E | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:AFC7F9B5E273D2A8FE51E7A03A0F1F59 | SHA256:1B394D931ED323172698668FC0D316E101287B7E0F804E1BB1FFEFA5992F3382 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D73576A2B1E2D4CB9B543CD01BDED20A | der | |
MD5:94544FB12D98380AC00B46675BFA5FB5 | SHA256:B8145C922687B02113F051FCE1CC6DADA03E5F33EC6C2EA31CD781A5C2B25D6E | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\review8[1].gif | image | |
MD5:FD5899D27DD4D3C3ED1EBB647EF8AF8A | SHA256:7E0CD7EBA6748DD6A76CBFD9EC9C44433F5AA61ABDF276DEA9EB9B9EE2C8744B | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\SoftPerfect-Network-Scanner-163639[1].png | image | |
MD5:72BA6E676F2EEFCC65C91FEB0676656E | SHA256:867277F63083F55942FEC83FF03050F3DC64871C5C9C5533C5441512CE06A775 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\Ammyy-Admin-332696[1].png | image | |
MD5:DC9E14628C1603F423A7B56CF097DB41 | SHA256:DBC608A08AA7CA1B20E87776D2639BE6FAC3FAE9BBDC397537B59F67C988BFA5 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\free-IP-Scanner-197173[1].png | image | |
MD5:F4A7BE40930903E4DF6B3587353B7D9E | SHA256:6DDAB1076C1E44AA8907E644CE9CD67AC4362BA88A4A813135844929B4147883 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download3klogo-white[1].png | image | |
MD5:DA5093E1EB6DBE75F933D4CE8FB12F93 | SHA256:DB4B79B18B08884C6829ED4BC174C849BFE5B9A4C906AF7F45F6AD618F5B5BE8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
118
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4028 | iexplore.exe | GET | 304 | 23.65.124.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?30bfcba95dc85498 | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 304 | 23.65.124.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fdb53f965dd08005 | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 23.32.157.52:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEn9UPPGUtnUEjctHzGvXDE%3D | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 95.100.87.24:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRlgX41O7Q8HEWbEYb%2FnMt0zA%3D%3D | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAFWoeiRoD5nEA9wbC%2FqWOc%3D | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCTqdn9DPH4uxAjL7OzkKGU | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDzzS5Gqa0QJQniHZdCqy3p | unknown | — | — | unknown |
4028 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCTqdn9DPH4uxAjL7OzkKGU | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4028 | iexplore.exe | 37.48.94.74:443 | www.download3k.com | LeaseWeb Netherlands B.V. | NL | unknown |
4028 | iexplore.exe | 23.65.124.25:80 | ctldl.windowsupdate.com | Akamai International B.V. | IN | unknown |
4028 | iexplore.exe | 23.32.157.52:80 | x1.c.lencr.org | AKAMAI-AS | US | unknown |
4028 | iexplore.exe | 95.100.87.24:80 | r3.o.lencr.org | Akamai International B.V. | CO | unknown |
4028 | iexplore.exe | 142.250.74.196:443 | www.google.com | GOOGLE | US | whitelisted |
4028 | iexplore.exe | 142.250.184.226:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download3k.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
www.google.com |
| whitelisted |
www.statcounter.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |