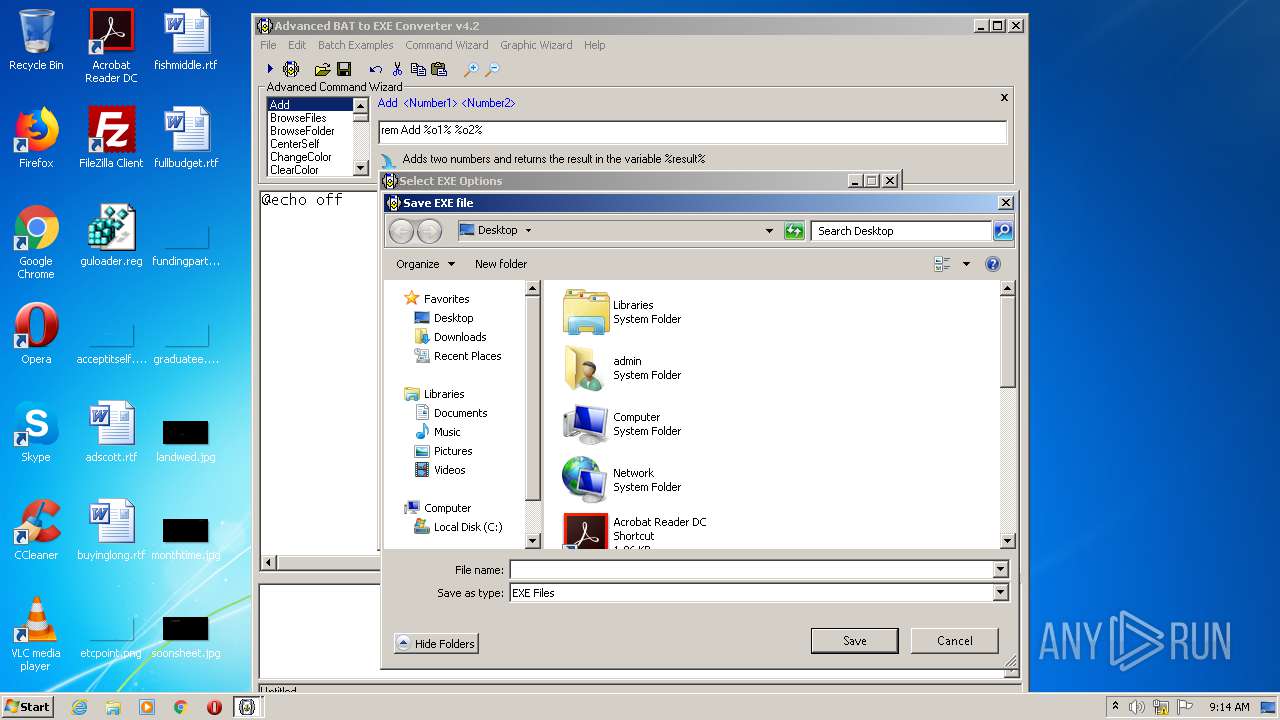
| File name: | advbattoexeconverter.exe |
| Full analysis: | https://app.any.run/tasks/db562fb6-99f7-4ab9-b807-f15dcffd0d0b |
| Verdict: | Malicious activity |
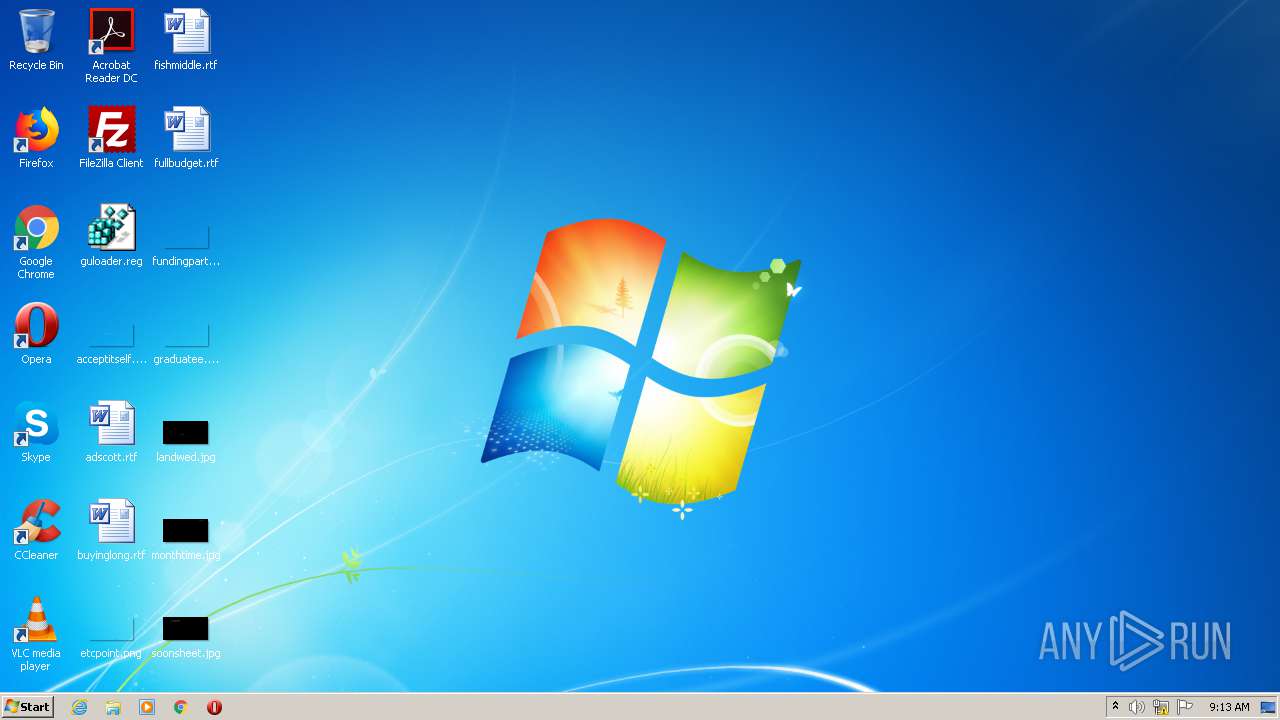
| Analysis date: | November 29, 2020, 09:13:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 491186EEC5227E7F48A6D832385B2189 |
| SHA1: | DDE9F762D7988A5633AB0A29D017C5F9768E4C1F |
| SHA256: | D494391D7EAE3860A04A45B7DDAC62F1369CF7E61AD12B8A8930AA91E4F34AAD |
| SSDEEP: | 12288:dSGxFfeSZ0si/IWV1Z8AGJ/zhpQJOjzUqbcQXiN18tn2t2PKjLRjNnooj6:9xFVSsAIWzZSNpQkFbg+p29Z9oF |
MALICIOUS
Loads dropped or rewritten executable
- advbattoexeconverter.exe (PID: 3936)
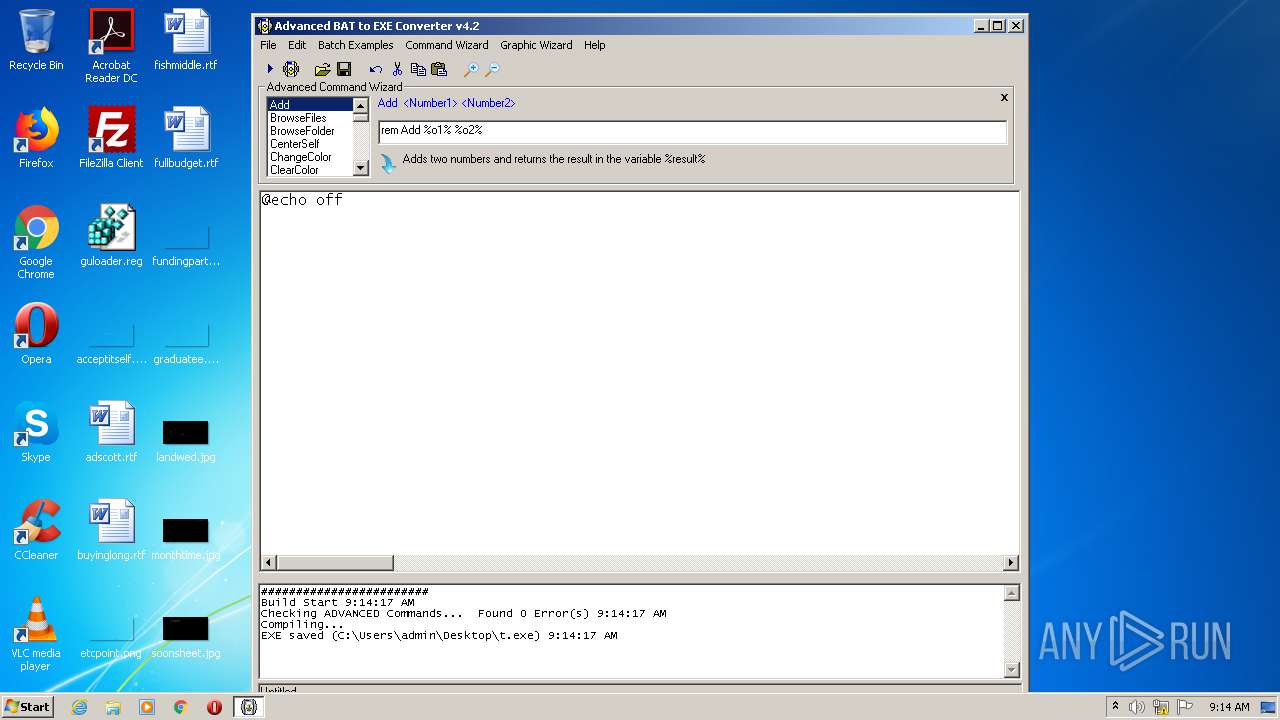
Drops executable file immediately after starts
- advbattoexeconverter.exe (PID: 3936)
Application was dropped or rewritten from another process
- setupinf.exe (PID: 2700)
- aB2Econv.exe (PID: 2488)
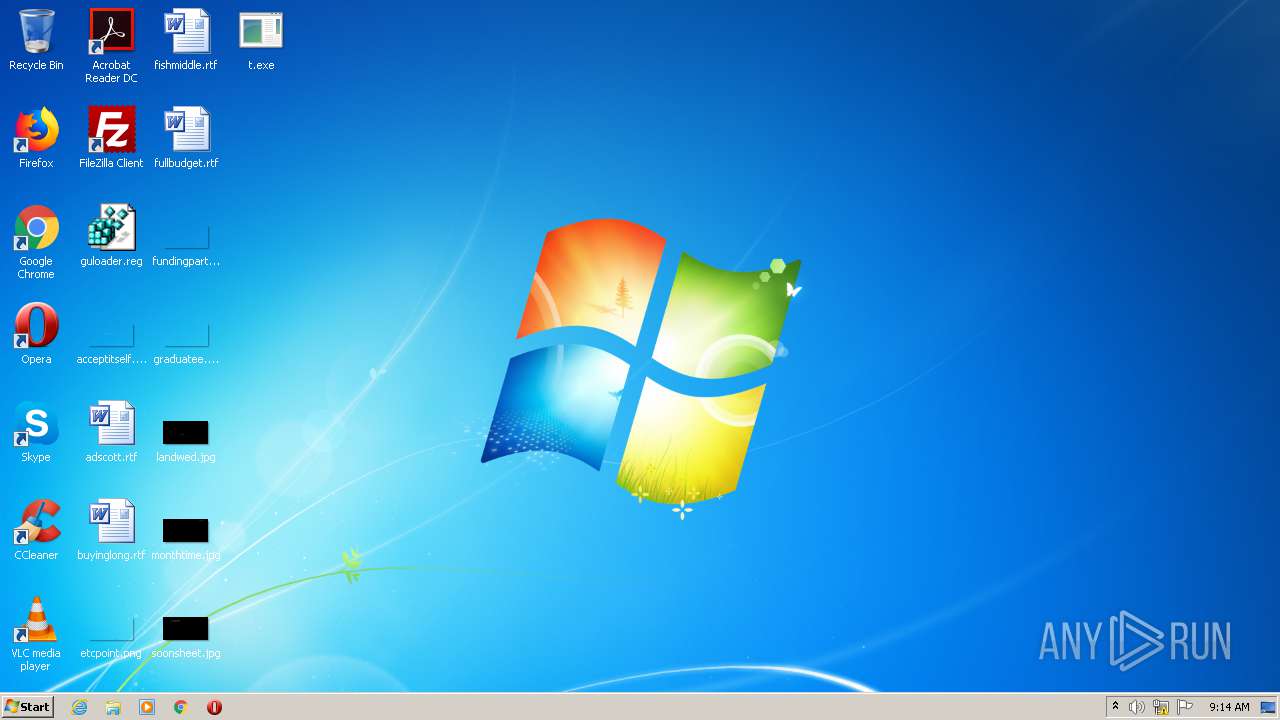
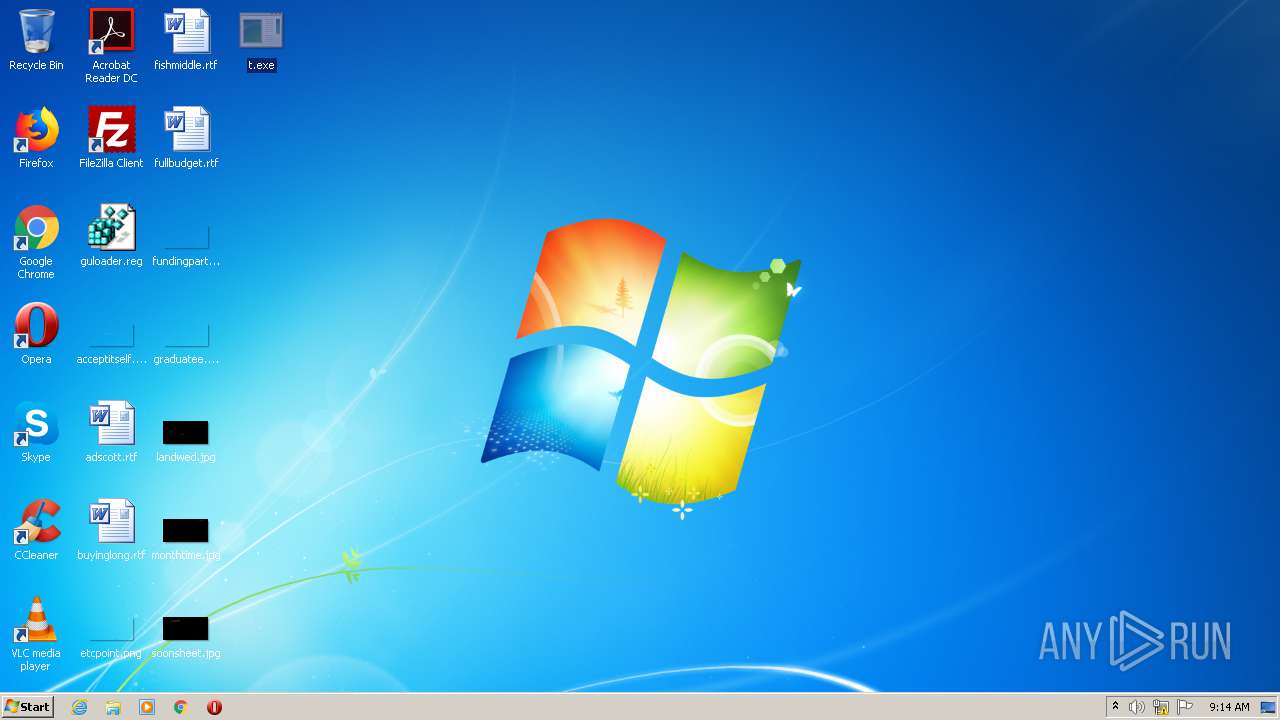
- t.exe (PID: 3024)
SUSPICIOUS
Executable content was dropped or overwritten
- advbattoexeconverter.exe (PID: 3936)
- aB2Econv.exe (PID: 2488)
Drops a file with too old compile date
- advbattoexeconverter.exe (PID: 3936)
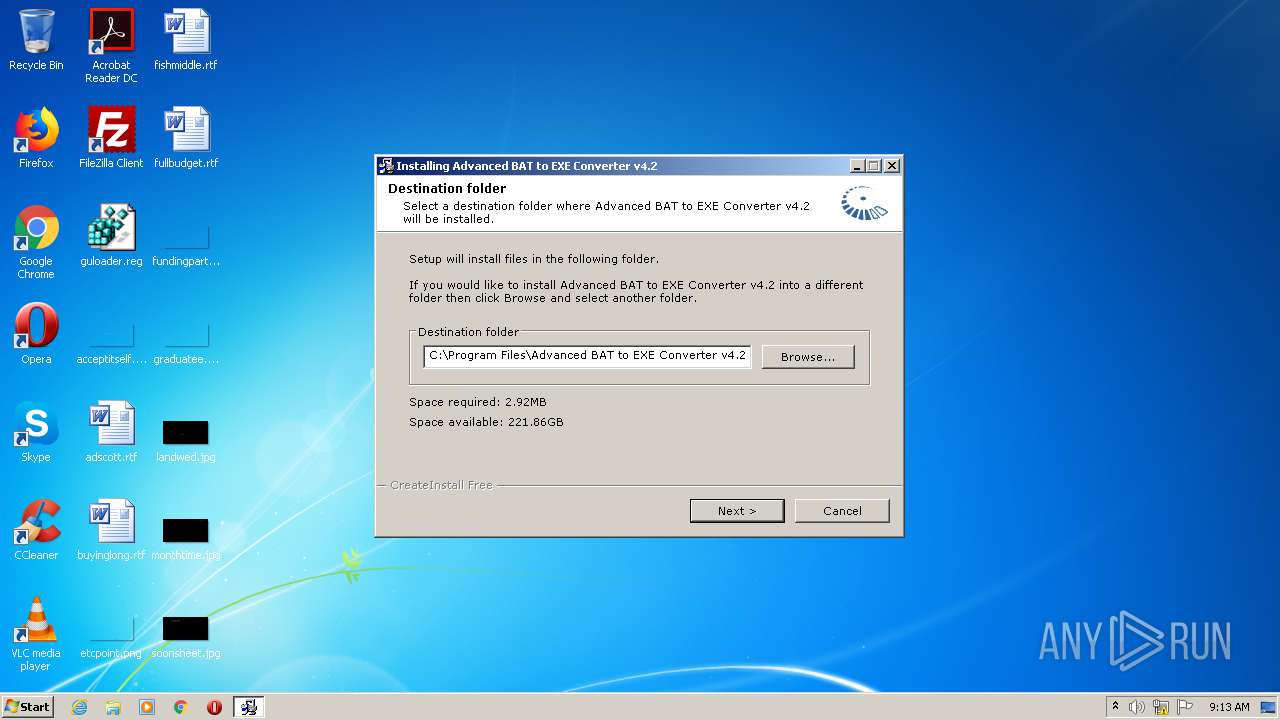
Creates a directory in Program Files
- advbattoexeconverter.exe (PID: 3936)
Drops a file that was compiled in debug mode
- advbattoexeconverter.exe (PID: 3936)
Drops a file with a compile date too recent
- advbattoexeconverter.exe (PID: 3936)
- aB2Econv.exe (PID: 2488)
Creates files in the Windows directory
- advbattoexeconverter.exe (PID: 3936)
Creates files in the program directory
- advbattoexeconverter.exe (PID: 3936)
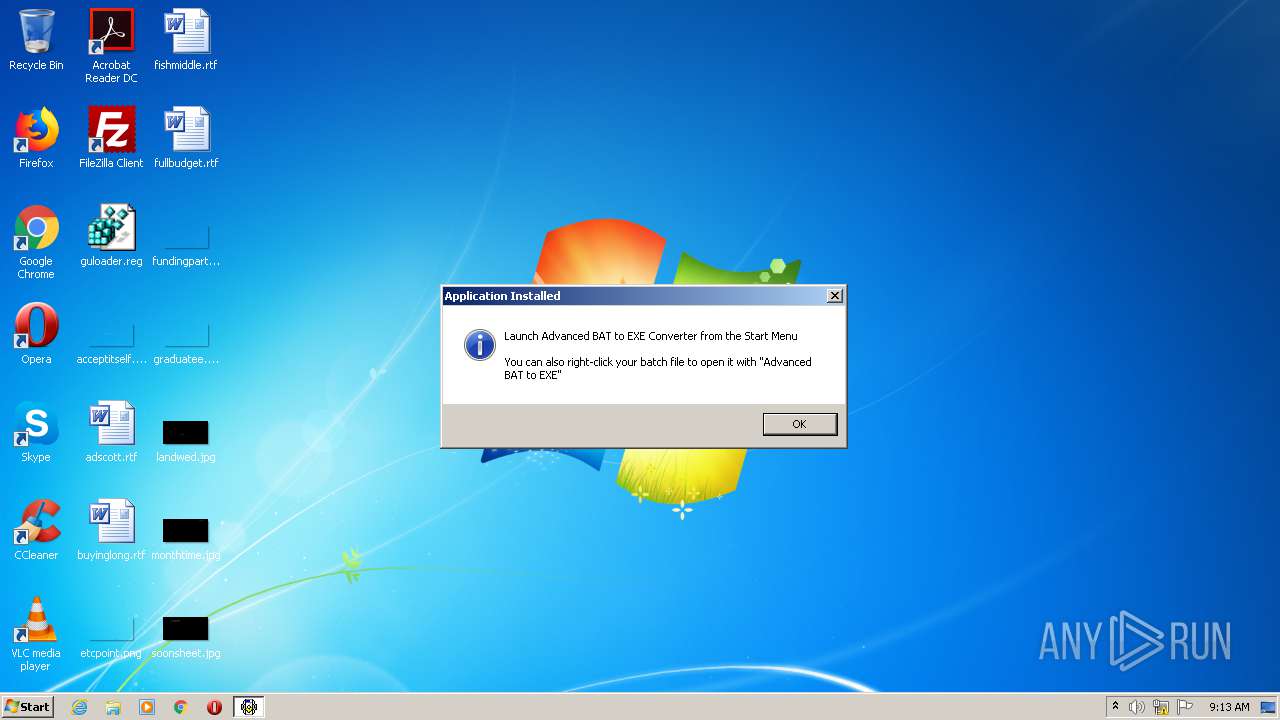
Creates a software uninstall entry
- advbattoexeconverter.exe (PID: 3936)
Creates files in the user directory
- advbattoexeconverter.exe (PID: 3936)
Starts CMD.EXE for commands execution
- t.exe (PID: 3024)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2472)
INFO
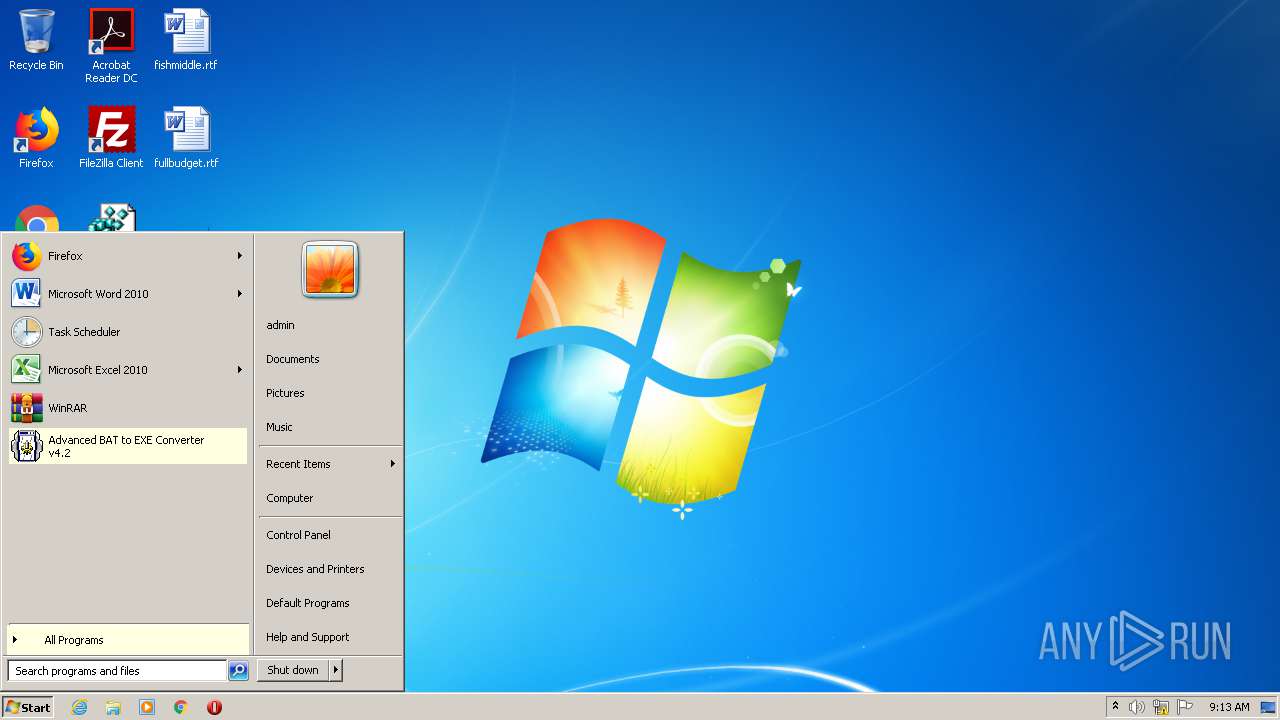
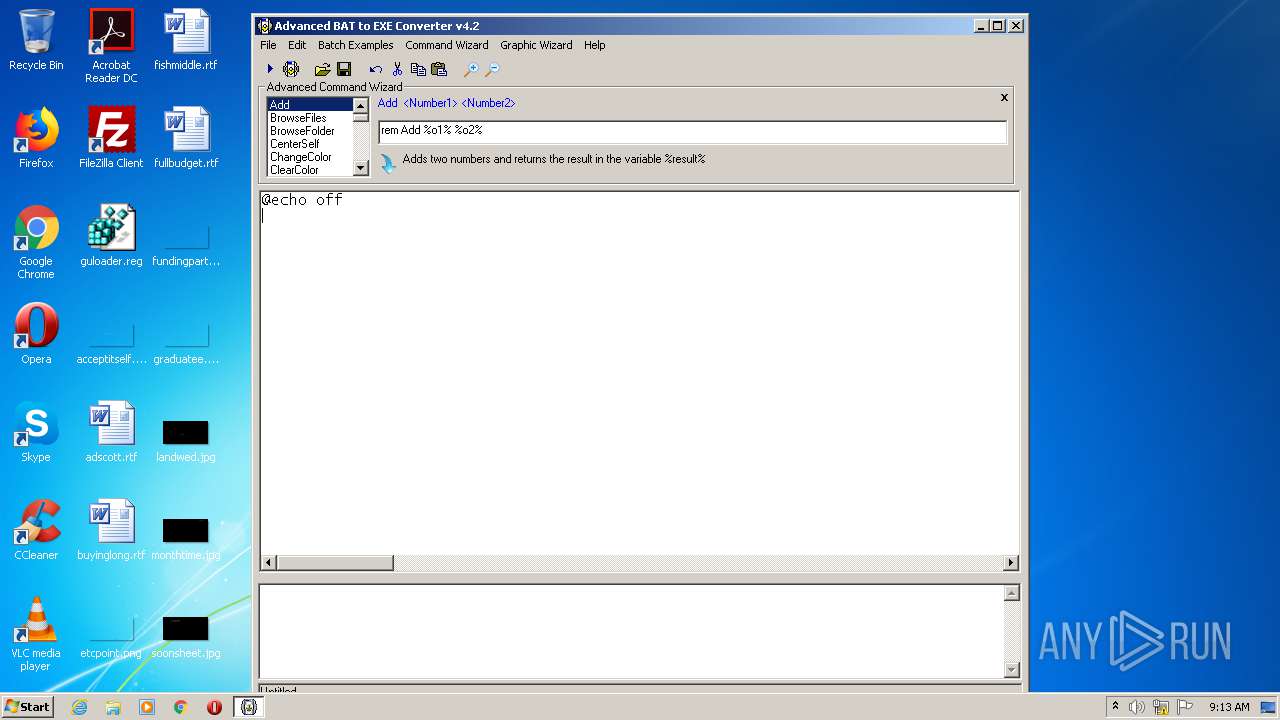
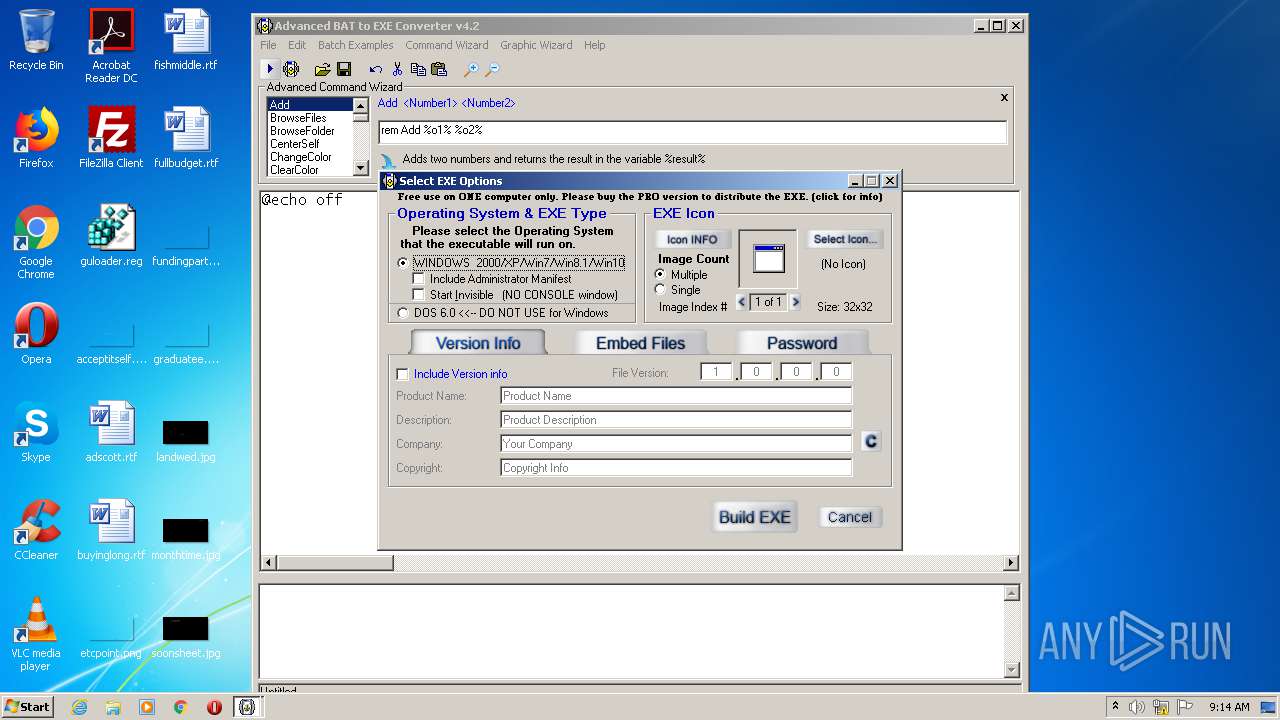
Manual execution by user
- aB2Econv.exe (PID: 2488)
- t.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:04:05 10:55:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 3584 |
| InitializedDataSize: | 94208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1226 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Apr-2006 08:55:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Apr-2006 08:55:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C91 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.93214 |
.rdata | 0x00002000 | 0x00000078 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.723443 |
.data | 0x00003000 | 0x00000504 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12782 |
.idata | 0x00004000 | 0x000002B0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.45462 |
.reloc | 0x00005000 | 0x0000012C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.28756 |
.gentee | 0x00006000 | 0x00013AC9 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99549 |
.rsrc | 0x0001A000 | 0x00002758 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.03453 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99128 | 784 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
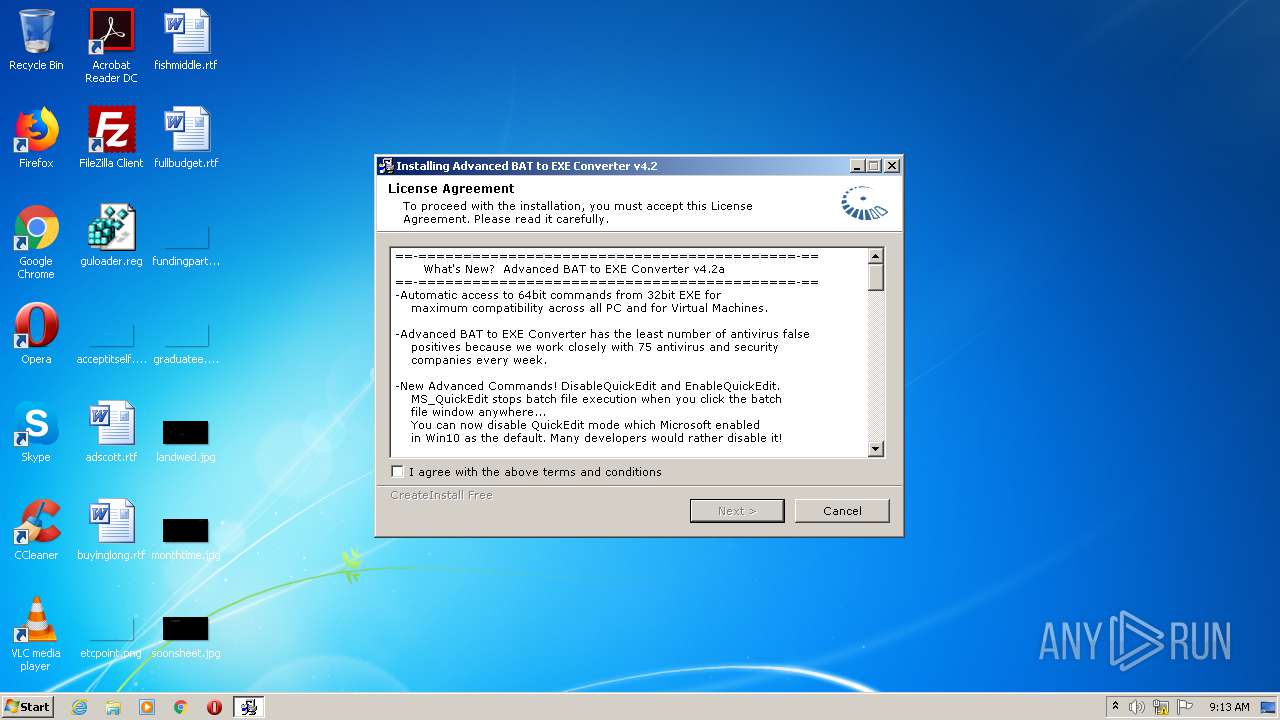
IDD_DLGLIC | 2.66912 | 440 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGPATH | 2.69399 | 640 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPROG | 2.70702 | 568 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUCONF | 2.54565 | 376 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUFIN | 2.60408 | 440 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUNDEL | 2.6827 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUPROG | 2.71234 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
SETUP_TEMP | 7.91625 | 4067 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
54
Monitored processes
16
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\wxy\tmp41149.bat "C:\Users\admin\Desktop\t.exe" | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\AppData\Local\Temp\advbattoexeconverter.exe" | C:\Users\admin\AppData\Local\Temp\advbattoexeconverter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 1532 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\myfiles" mkdir "C:\Users\admin\AppData\Local\Temp\myfiles" | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1812 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\wxy\tmp41639.exe" del "C:\Users\admin\AppData\Local\Temp\wxy\tmp41639.exe" | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\wxy" mkdir "C:\Users\admin\AppData\Local\Temp\wxy" | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2456 | attrib +h C:\Users\admin\AppData\Local\Temp\wxy | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | C:\Windows\system32\cmd.exe /c attrib +h C:\Users\admin\AppData\Local\Temp\wxy | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\aB2Econv.exe" | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\aB2Econv.exe | explorer.exe | ||||||||||||
User: admin Company: Brandon Dargo Integrity Level: MEDIUM Description: Advanced BAT to EXE Converter Exit code: 0 Version: 4.02 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\setupinf.exe" | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\setupinf.exe | — | advbattoexeconverter.exe | |||||||||||
User: admin Company: Brandon Dargo Integrity Level: HIGH Exit code: 0 Version: 1.02.0003 Modules
| |||||||||||||||
| 2716 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\wxy\tmp41149.bat" del "C:\Users\admin\AppData\Local\Temp\wxy\tmp41149.bat" | C:\Windows\system32\cmd.exe | — | t.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
837
Read events
732
Write events
99
Delete events
6
Modification events
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.2 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.2\uninstall.exe | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.2 |
| Operation: | write | Name: | DisplayName |
Value: Advanced BAT to EXE Converter v4.2 | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.2 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.2\uninstall.exe | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | write | Name: | (default) |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Windows\system32\richtx32.ocx | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl |
| Operation: | write | Name: | (default) |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CLSID |
| Operation: | write | Name: | (default) |
Value: {3B7C8860-D78F-101B-B9B5-04021C009402} | |||
| (PID) Process: | (3936) advbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CurVer |
| Operation: | write | Name: | (default) |
Value: RICHTEXT.RichtextCtrl.1 | |||
Executable files
22
Suspicious files
1
Text files
46
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | advbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\setup_temp.gea | bs | |
MD5:— | SHA256:— | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\aB2Econv.exe | executable | |
MD5:— | SHA256:— | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\advex1.bat | text | |
MD5:— | SHA256:— | |||
| 3936 | advbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\guig.dll | executable | |
MD5:F78EE6369ADA1FB02B776498146CC903 | SHA256:F1073319D4868D38E0AE983AD42A00CDC53BE93B31275B4B55AF676976C1AA3F | |||
| 3936 | advbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\gentee.dll | executable | |
MD5:30439E079A3D603C461D2C2F4F8CB064 | SHA256:D6D0535175FB2302E5B5A498119823C37F6BDDFF4AB24F551AA7E038C343077A | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\advex10.bat | text | |
MD5:968E898D05ACAF33A5008BE202F5DE7F | SHA256:86785CFD394E139A5325DCA33E4C3D1B69FE3F5F4229F00445AE86C592DF6BCC | |||
| 3936 | advbattoexeconverter.exe | C:\Users\admin\AppData\Local\Temp\gentee00\1Default.bmp | image | |
MD5:0895D223FA59A94BED73D25D1CB5AF70 | SHA256:53228A7C924889D300C7FFE9BAA1879EE94BD9B4286E84B7B29F870E9567B82D | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\advex4.bat | text | |
MD5:— | SHA256:— | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\advex17.bat | text | |
MD5:1FD8C3EC584D29ACB9428925D803BBAE | SHA256:47D5D77316B3E4D5861B21A2BA8DC4C74C5EC686C7F5720DB3C6CE408A39C650 | |||
| 3936 | advbattoexeconverter.exe | C:\Program Files\Advanced BAT to EXE Converter v4.2\ab2econv42\advex5.bat | text | |
MD5:0B17712F708EC60A62716D1EAC91AA90 | SHA256:8A329A671D7C9B3E8EC5B7FFE313CF48529E1A8F6AFF144DE46F86E19107CE96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report