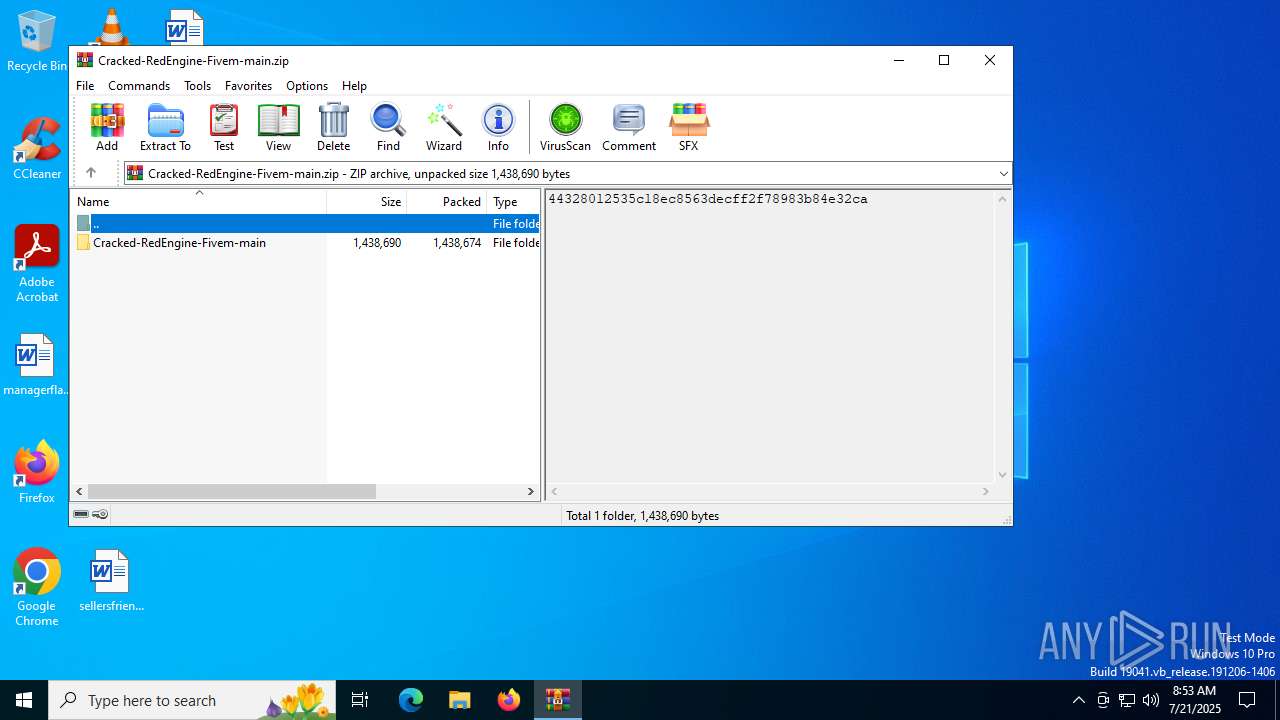
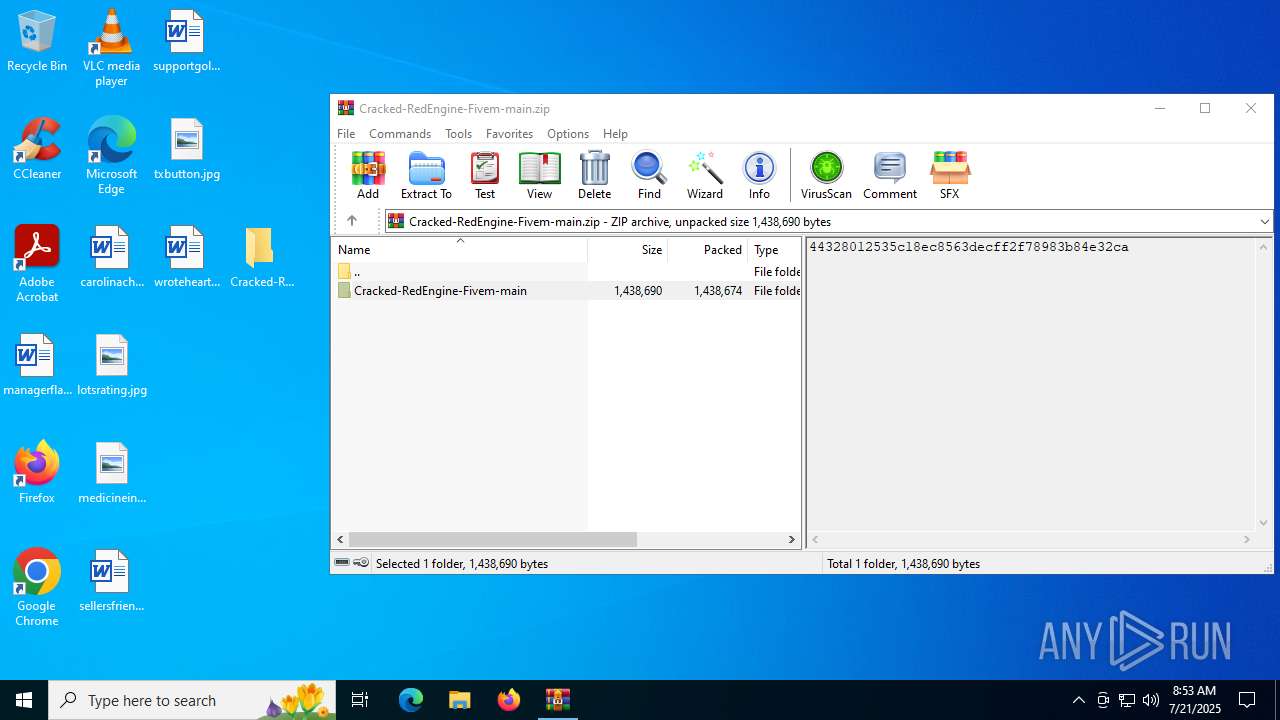
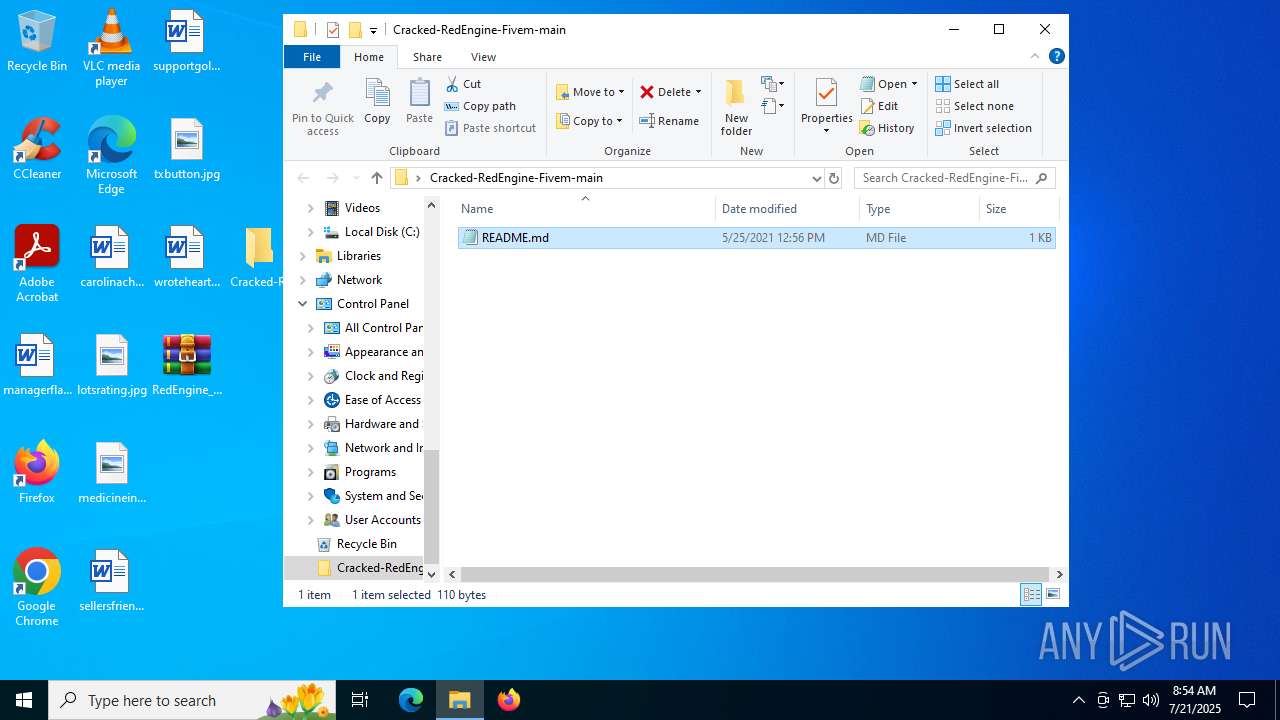
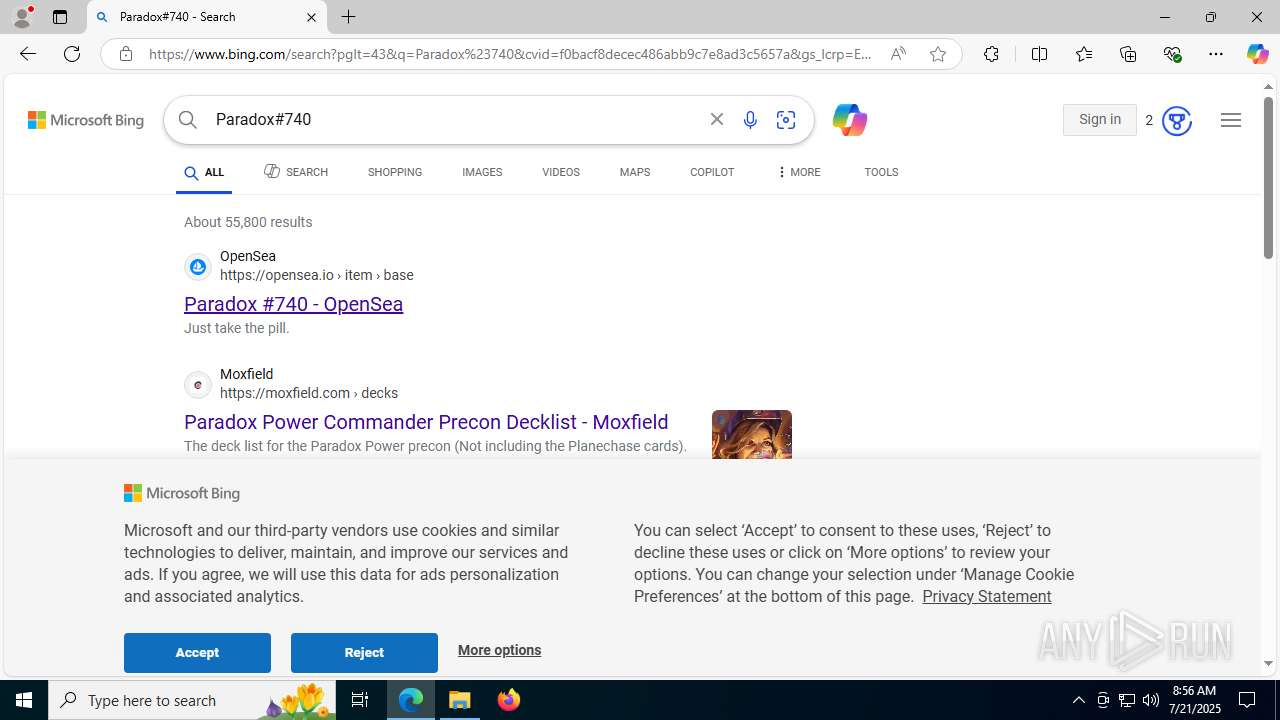
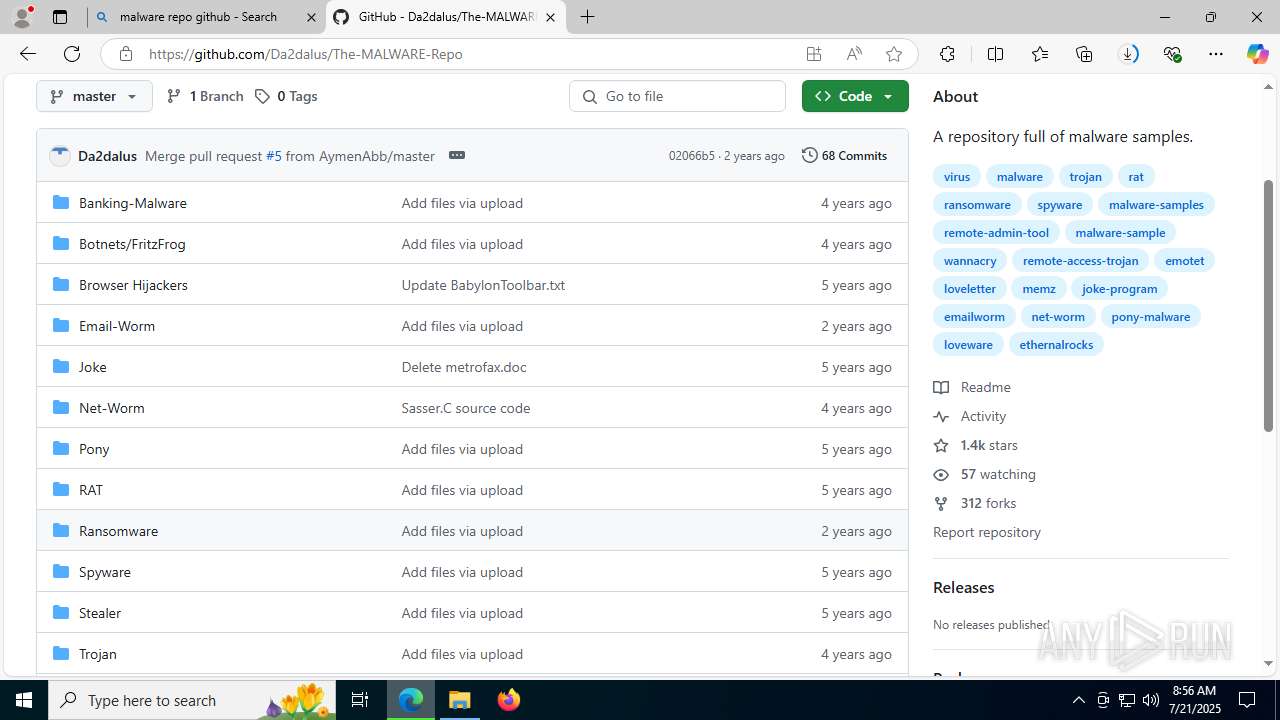
| File name: | Cracked-RedEngine-Fivem-main.zip |
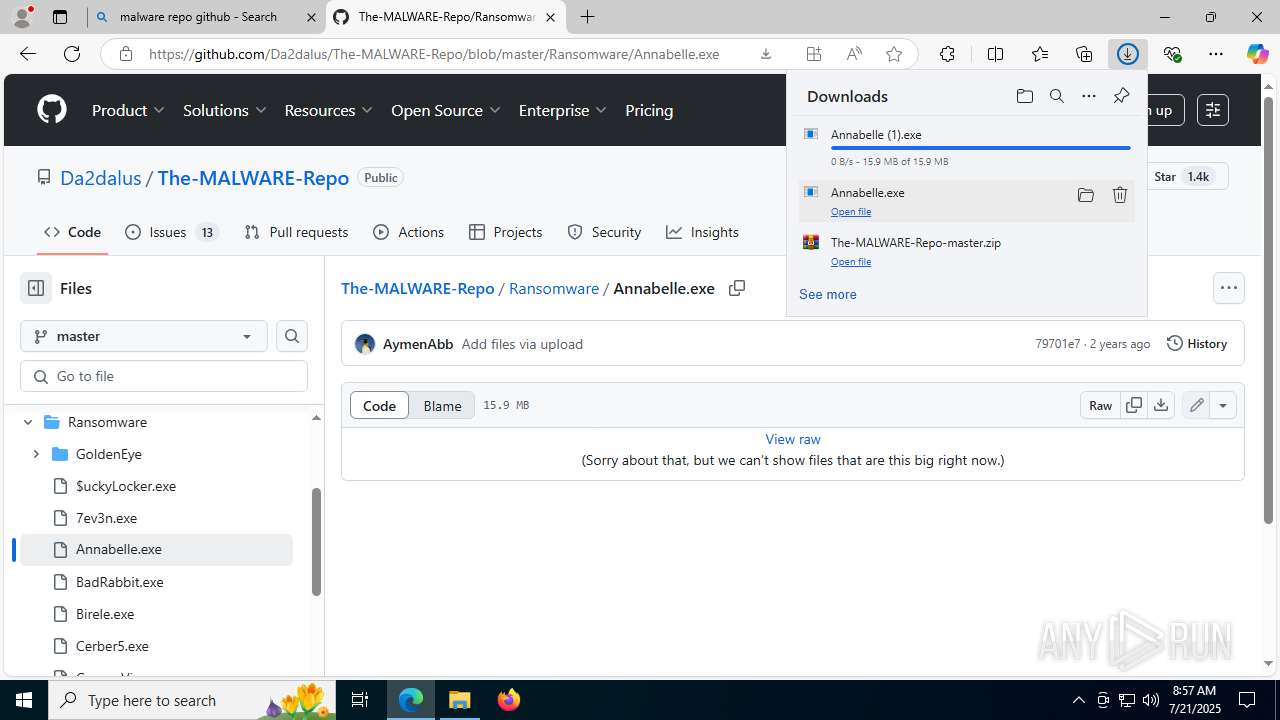
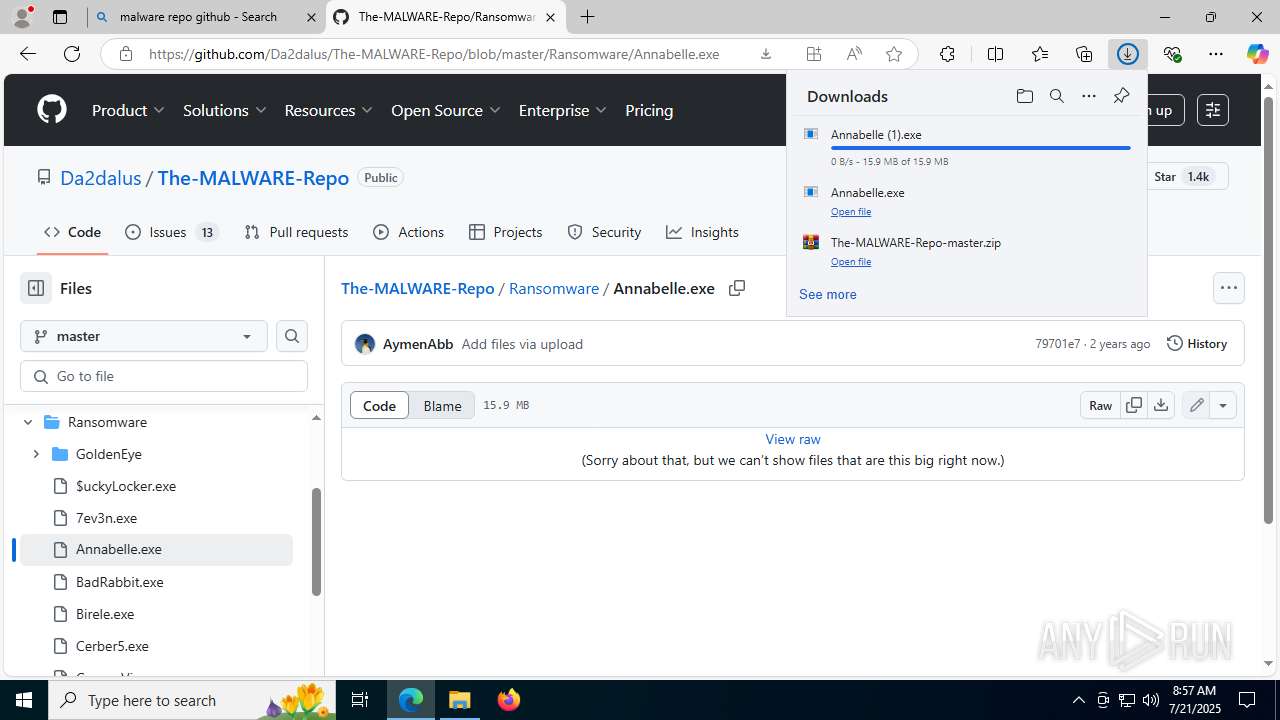
| Full analysis: | https://app.any.run/tasks/e90517e3-f30d-4487-afd6-26ca891e6be0 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2025, 08:52:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | E664A40454F21A1C906EA3F27726580B |
| SHA1: | C97F7E30782FB15F73798997D953252023309879 |
| SHA256: | D48FDAE8AD6D77A8966E05AD9B8B44D682AF1777E8A21D4499F7DB1A9C3DA33B |
| SSDEEP: | 49152:0t+ObLRSWsT+SCsRVsq76hInxm6PhOfkuxX1DOaAoHgWmL0zWE6nTqzAwwtOU2Mm:2+iLRSW1HhZ65OvxlDJH6IyqzA12tAfg |
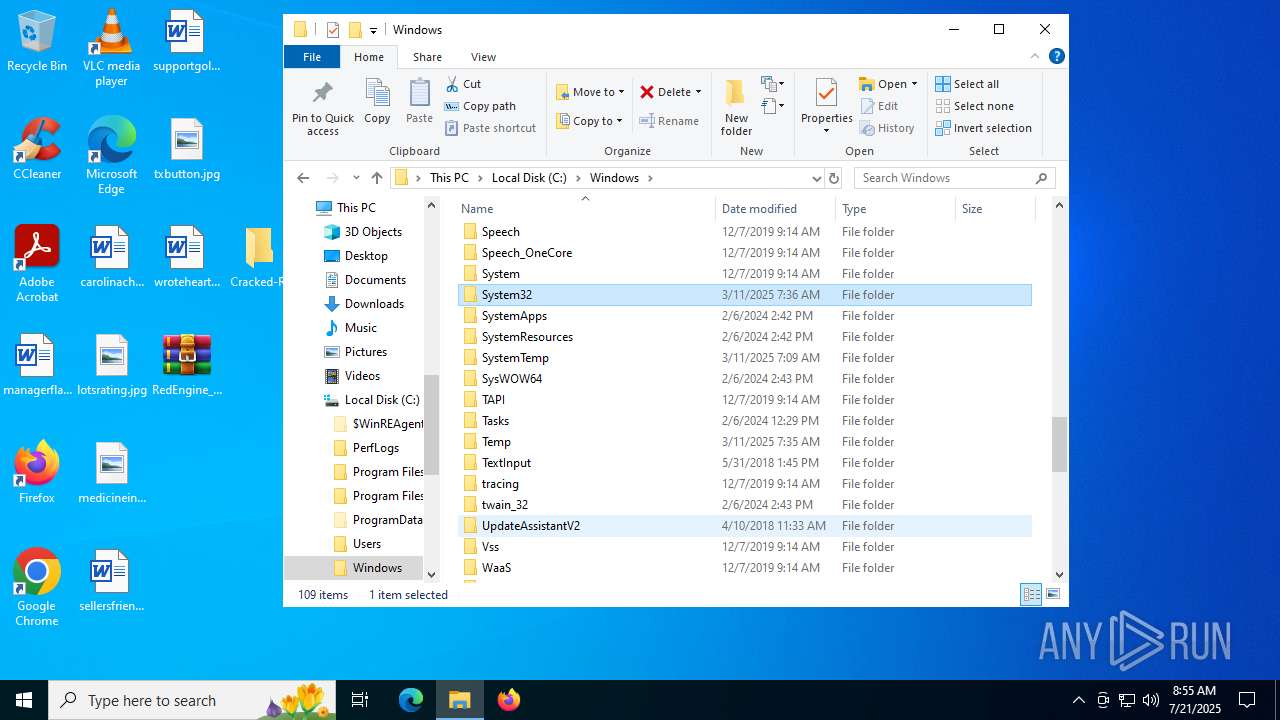
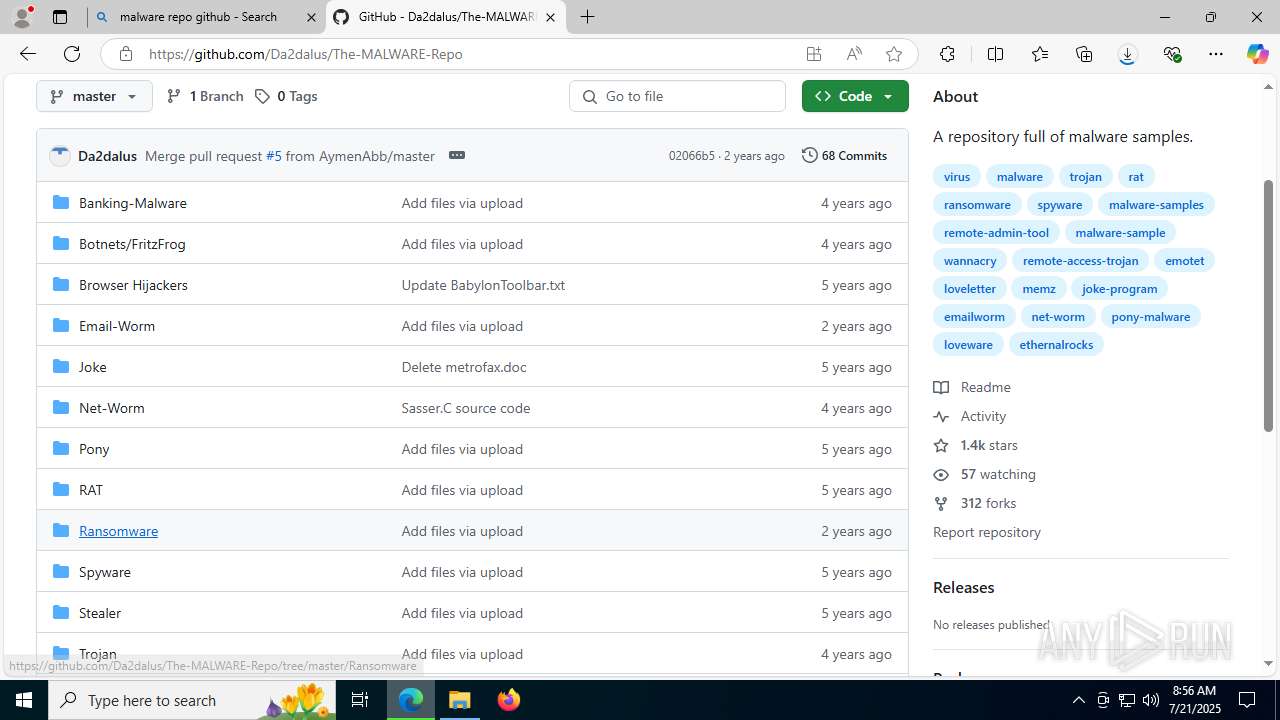
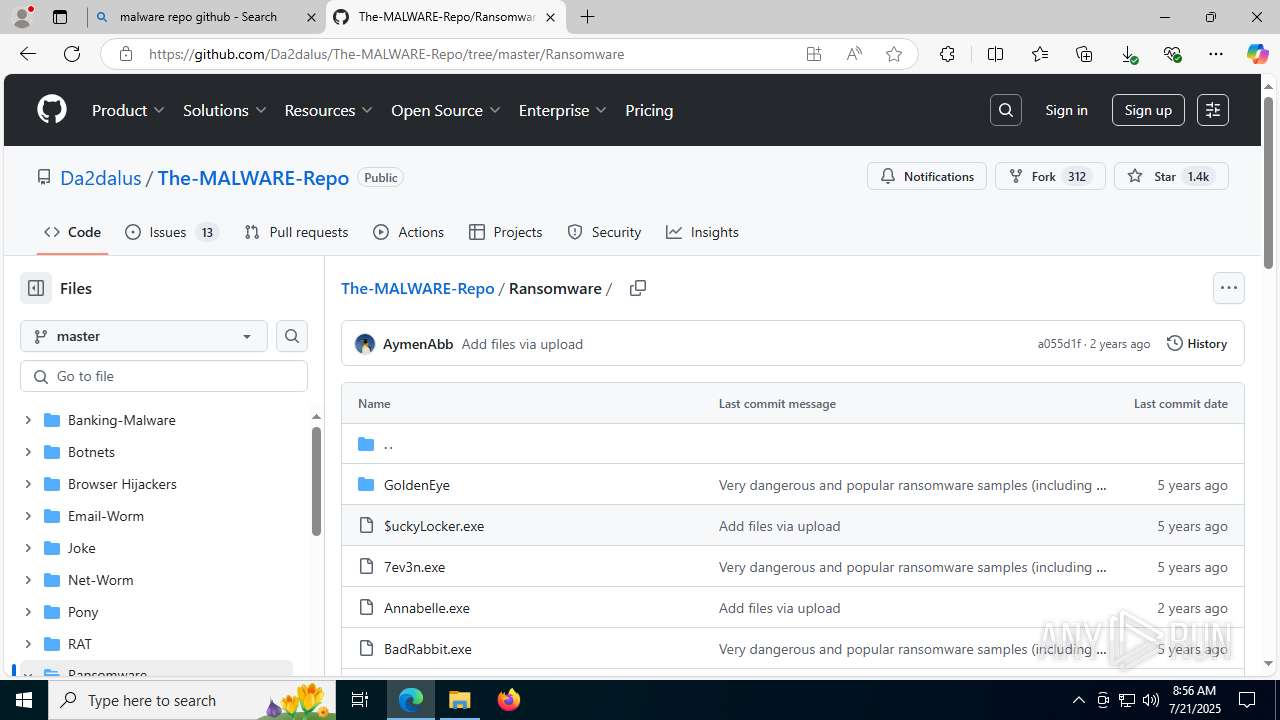
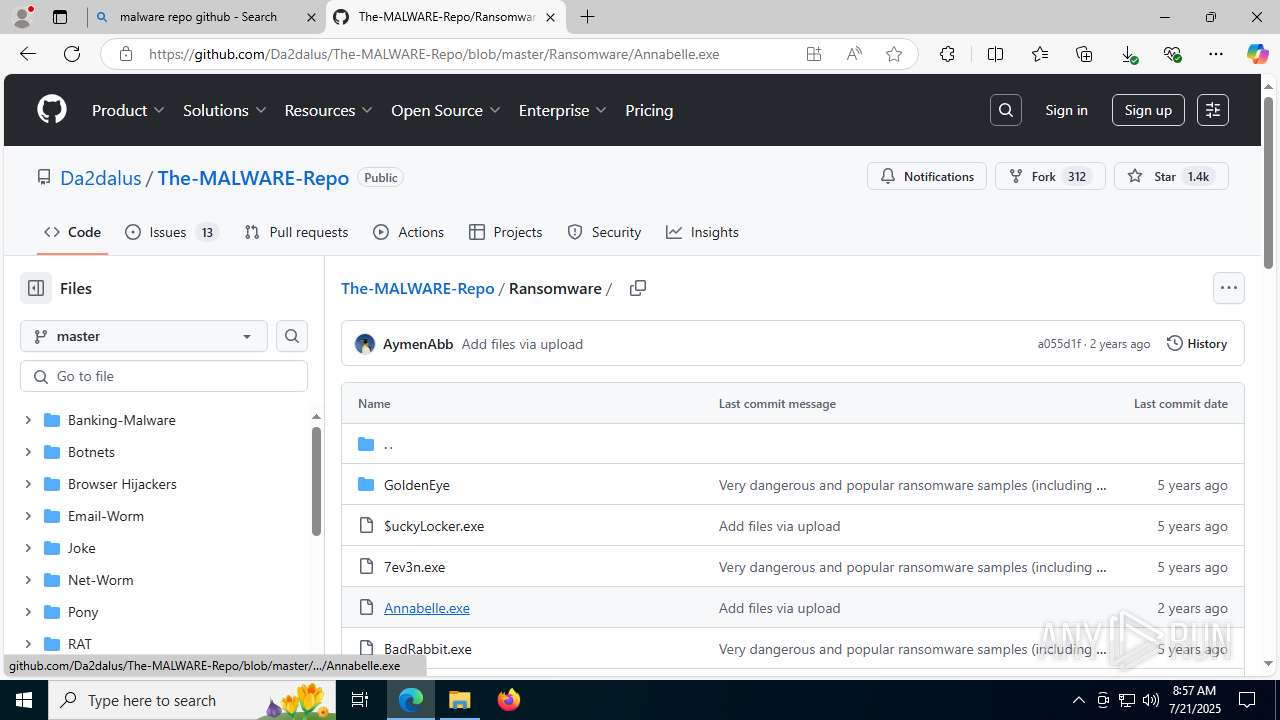
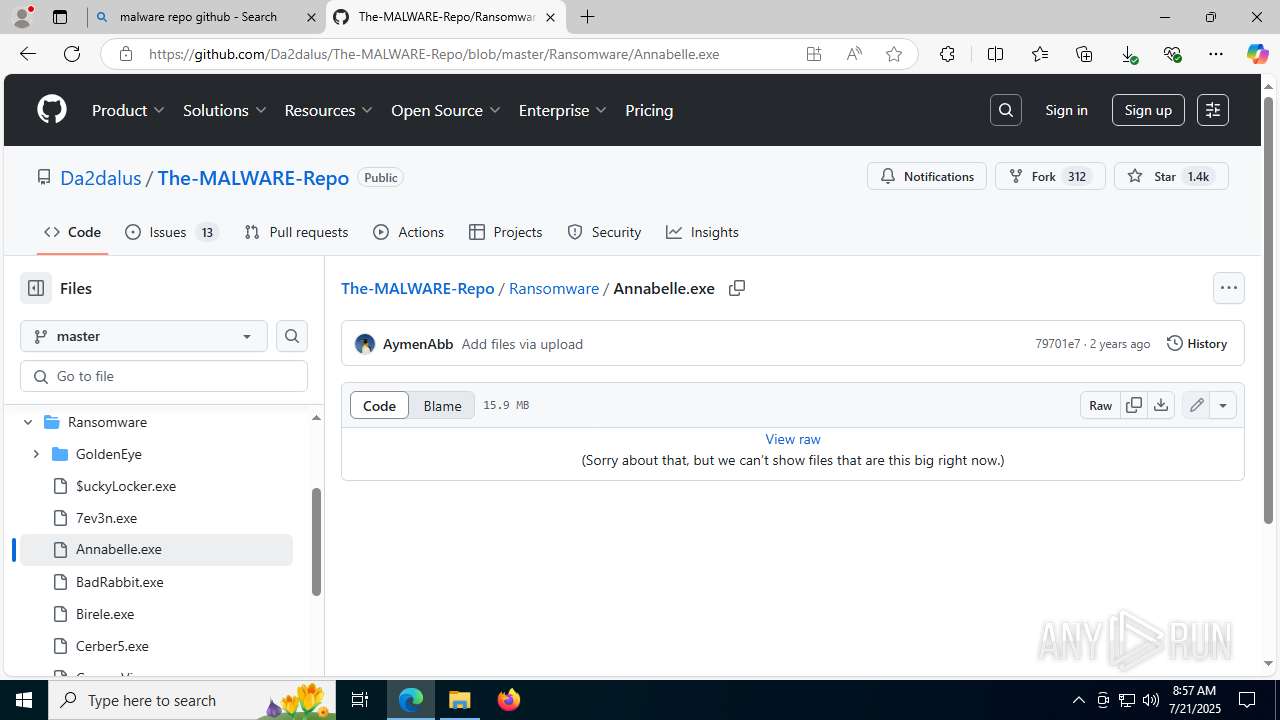
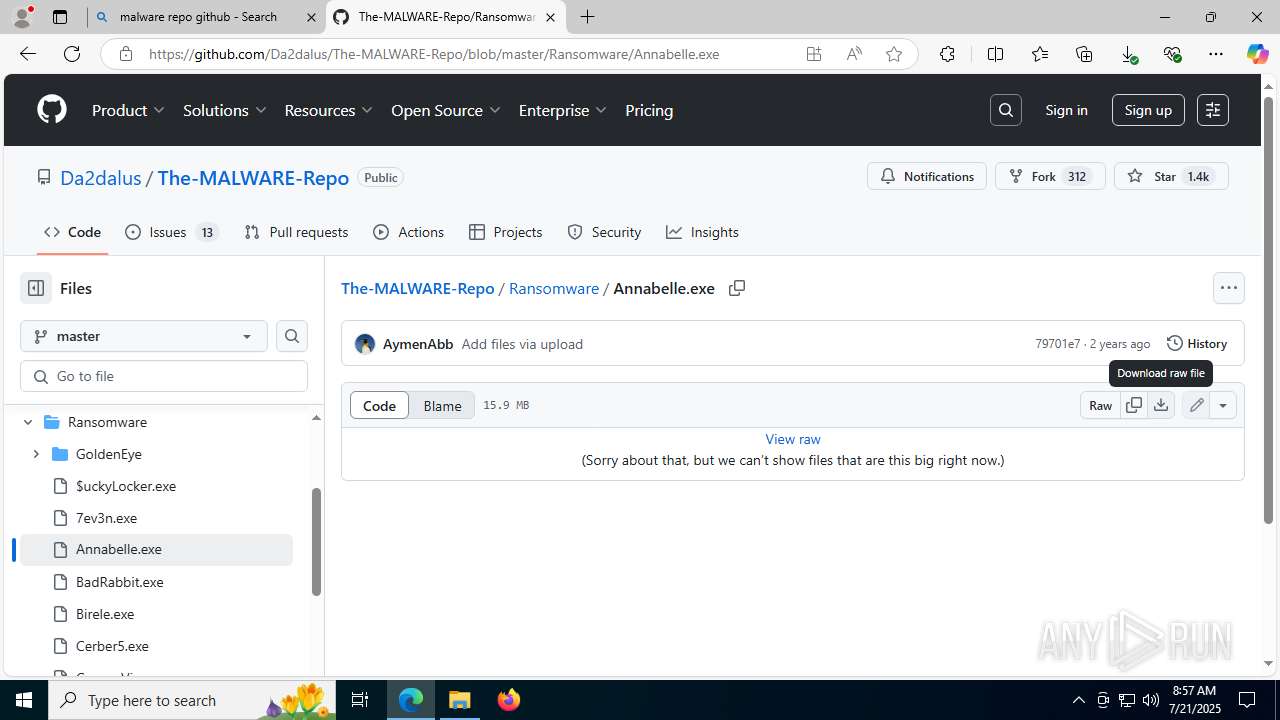
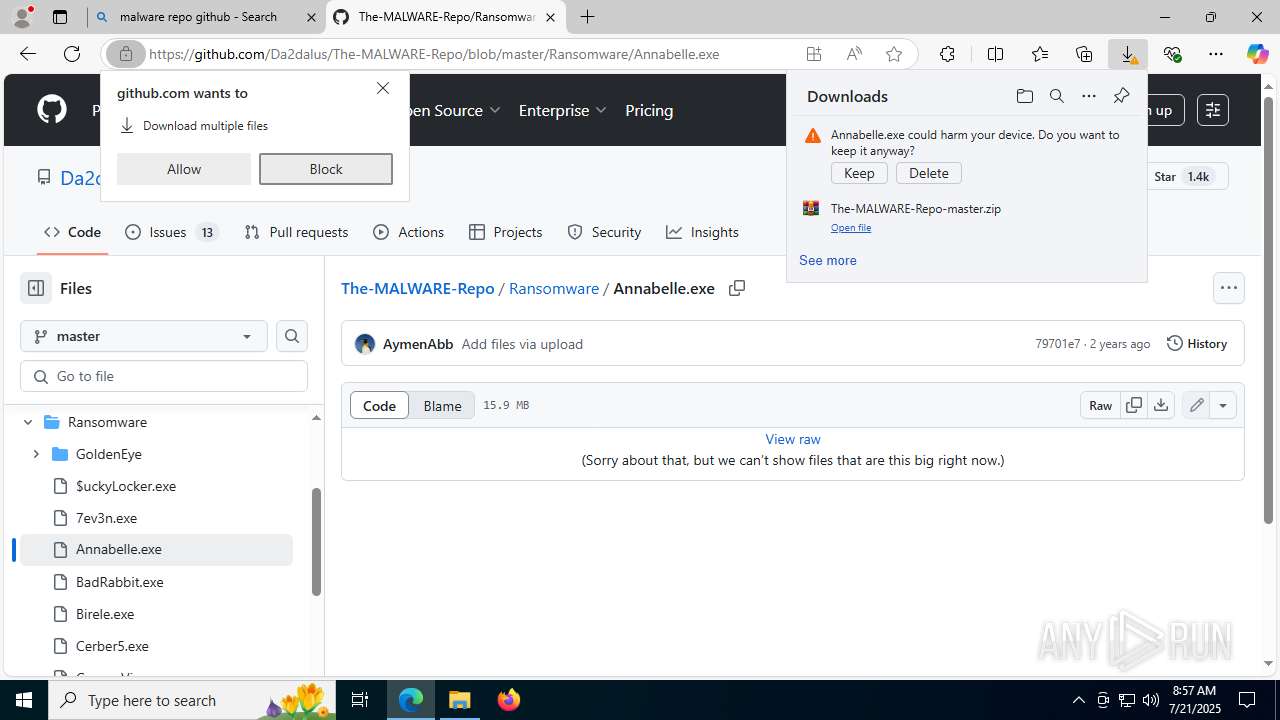
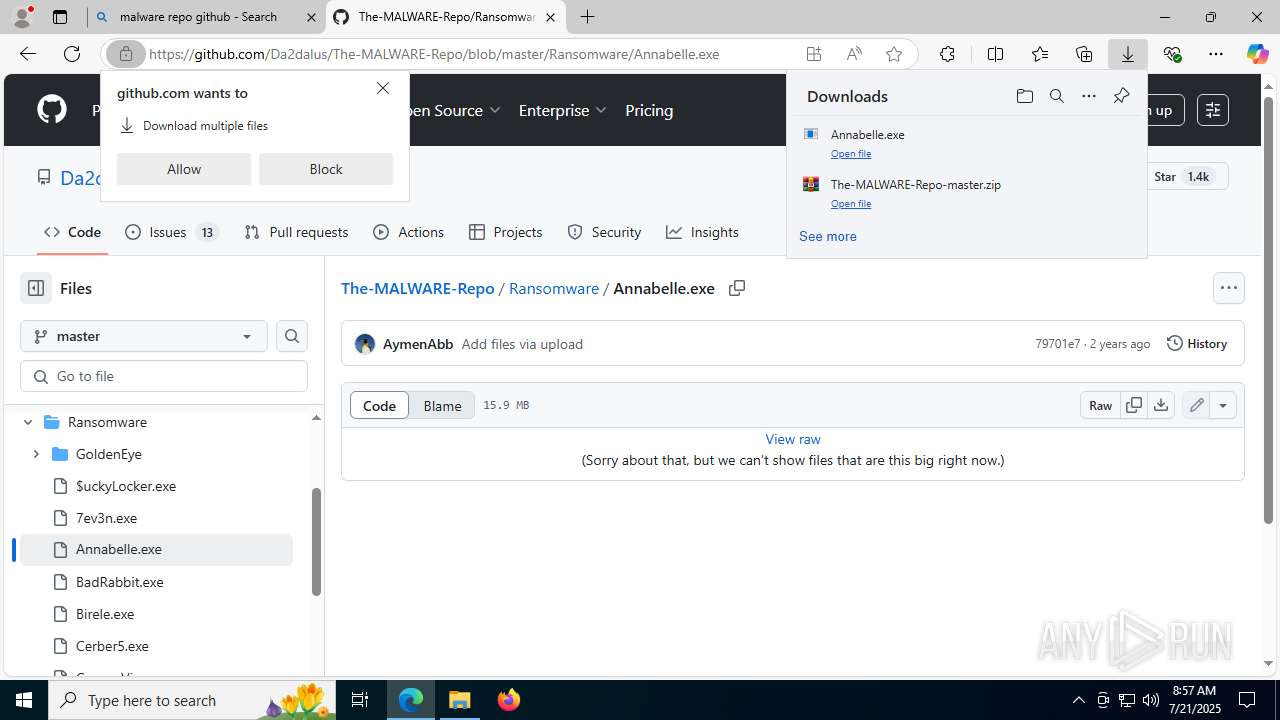
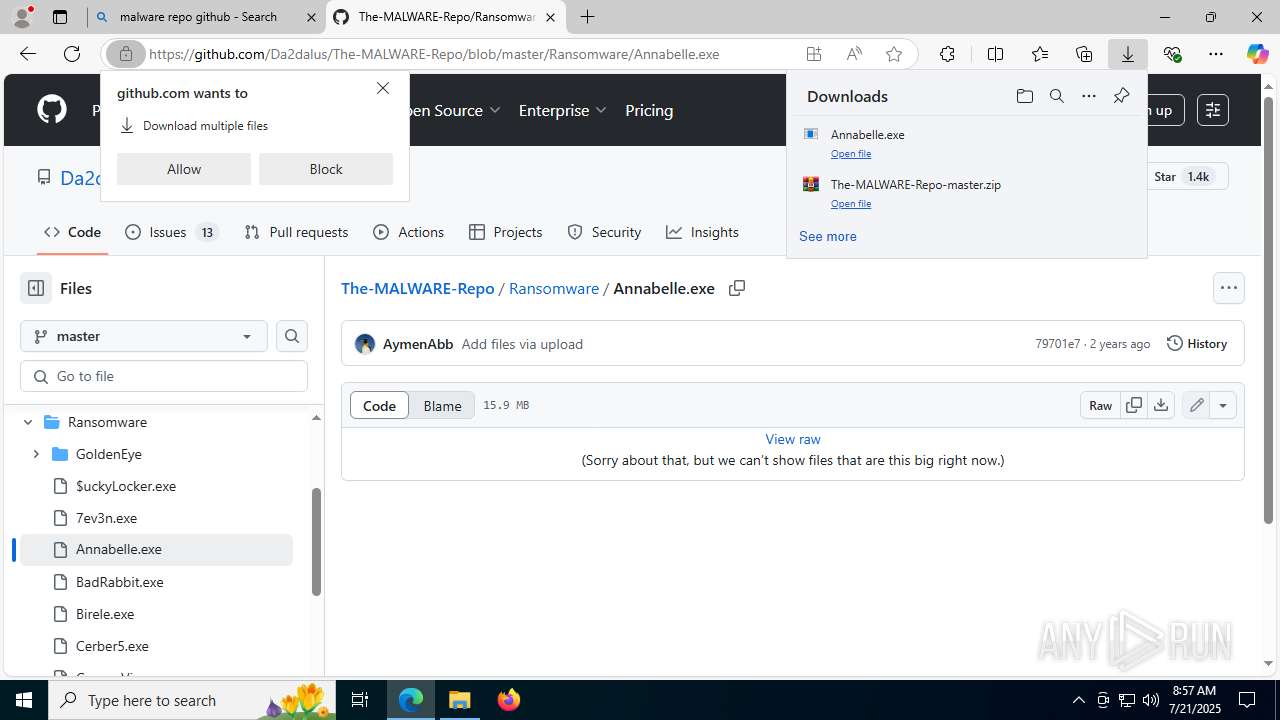
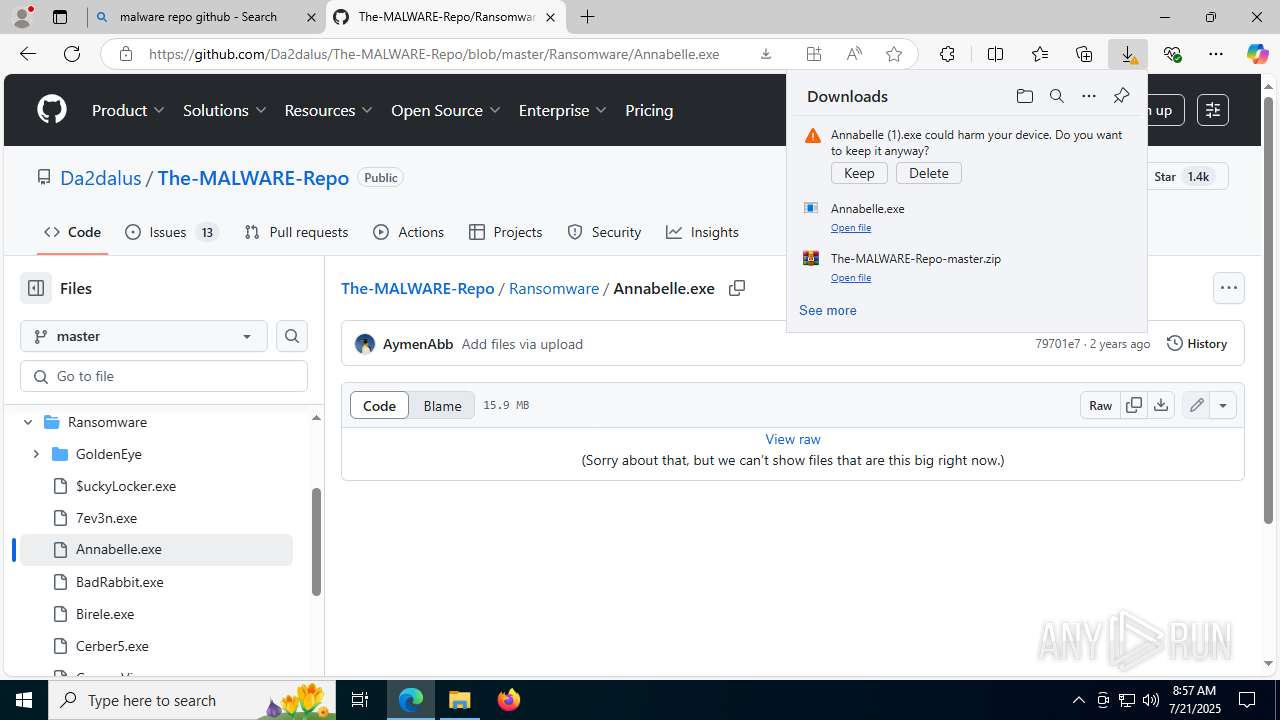
MALICIOUS
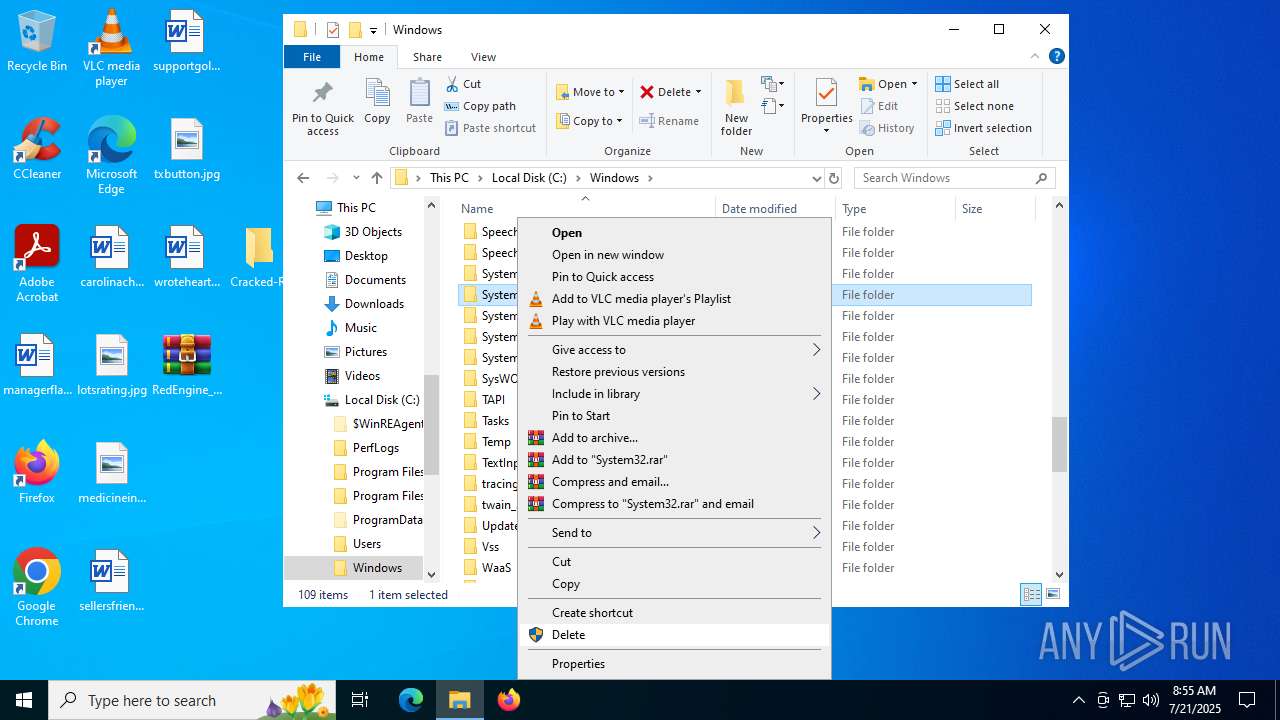
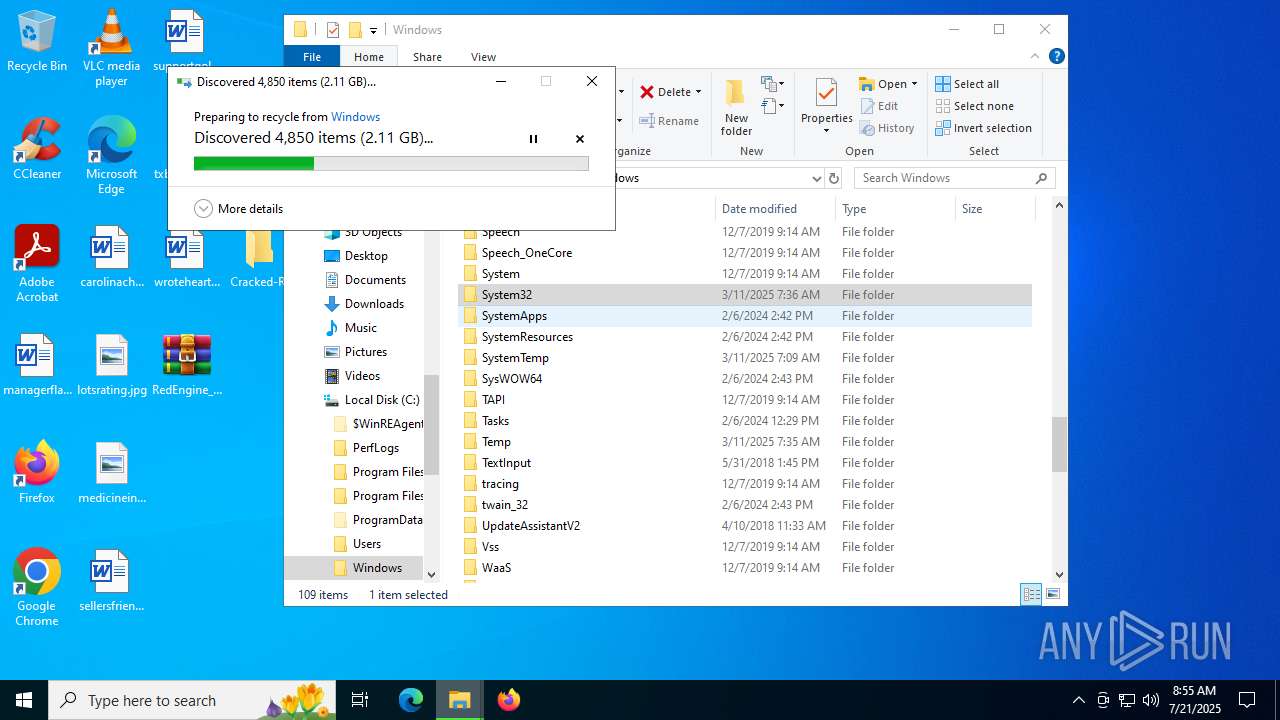
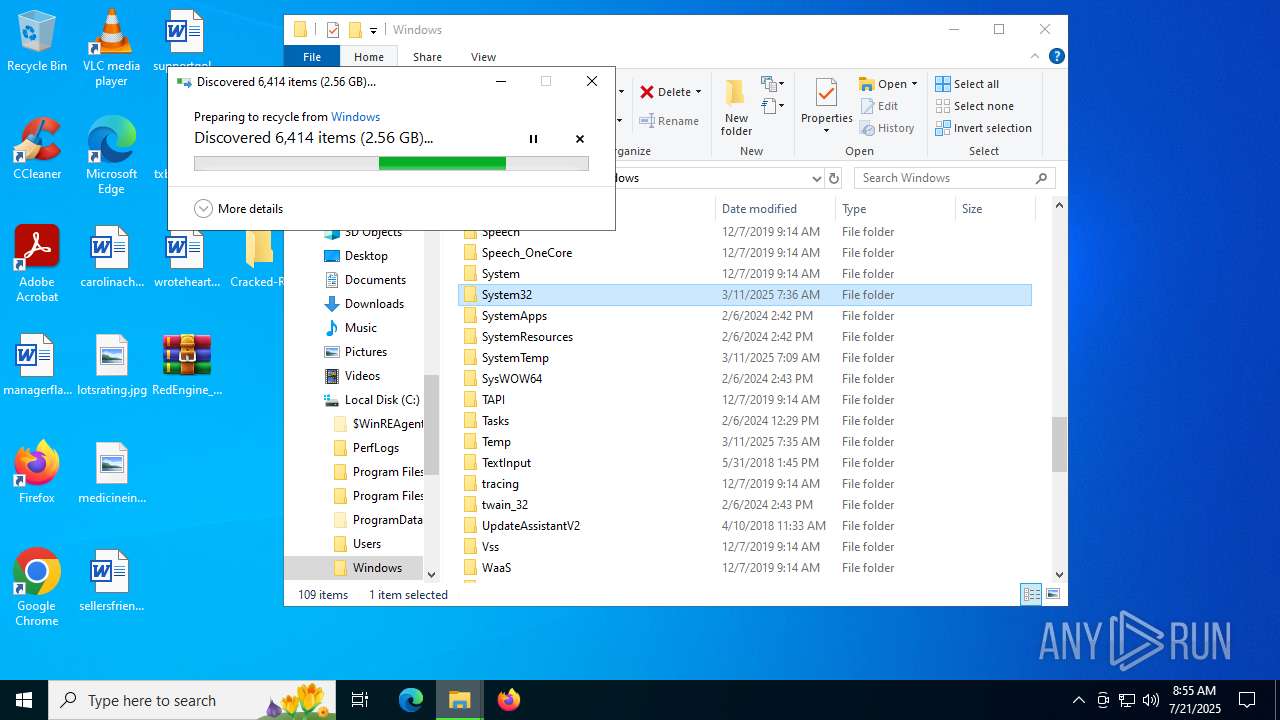
Deletes shadow copies
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Changes the autorun value in the registry
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 5960)
Disables Windows Defender
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
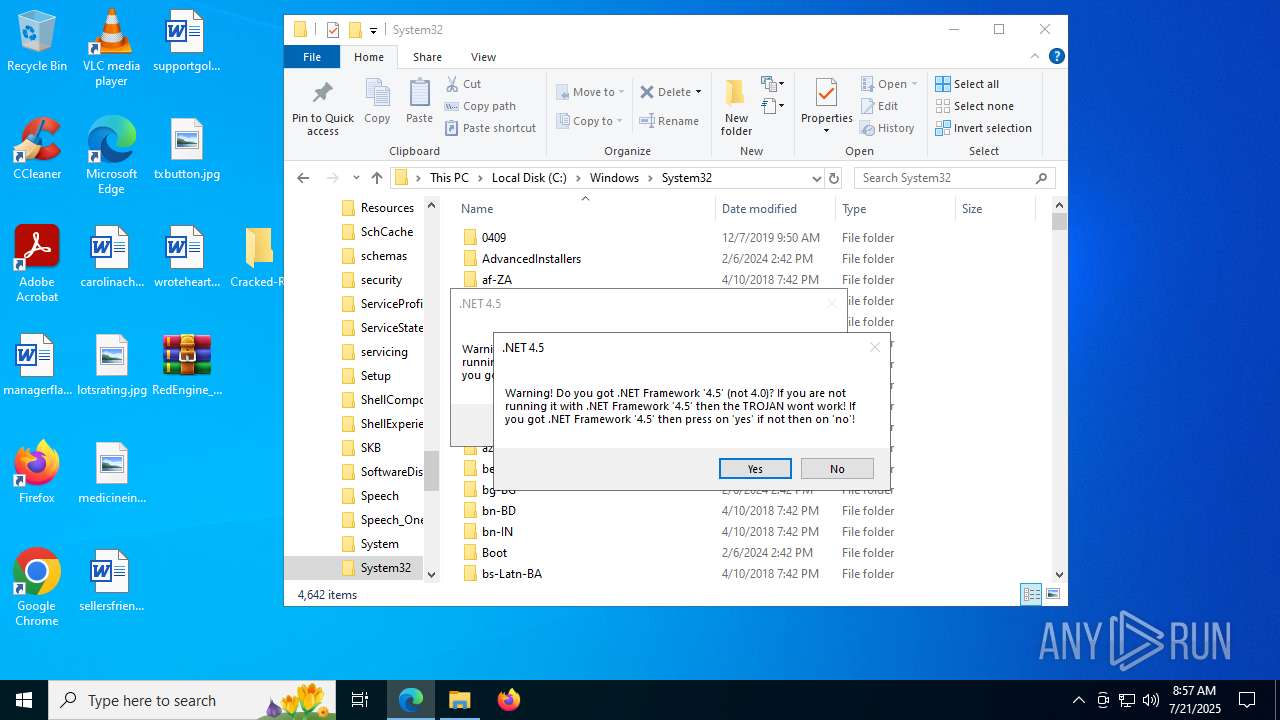
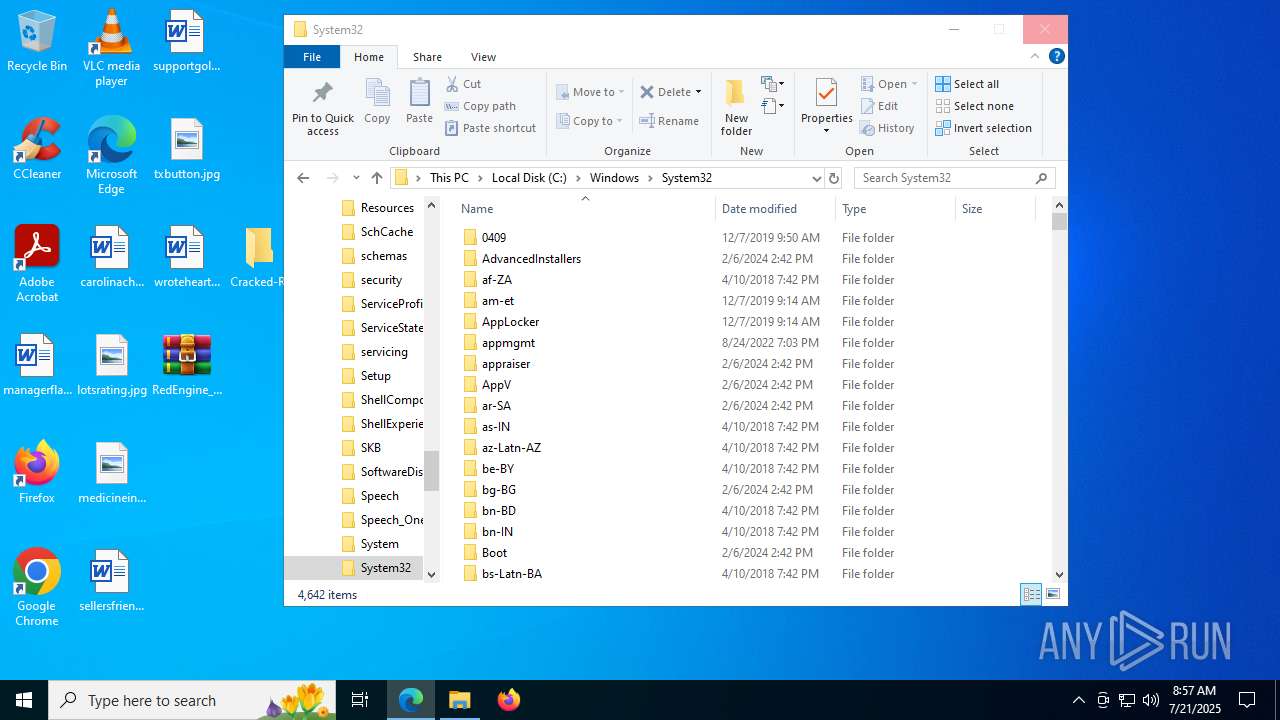
UAC/LUA settings modification
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Disables task manager
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Changes the login/logoff helper path in the registry
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Disables the Run the Start menu
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Changes image file execution options
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Task Manager has been disabled (taskmgr)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Modify registry editing tools (regedit)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
SUSPICIOUS
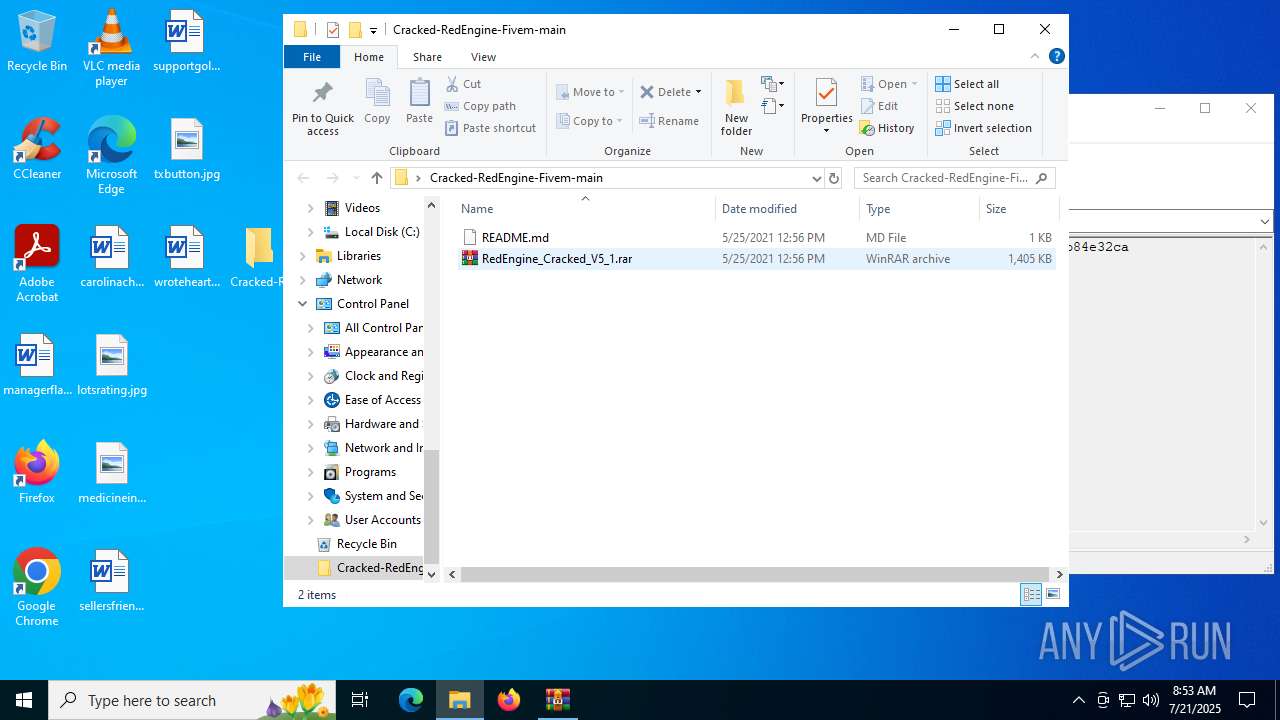
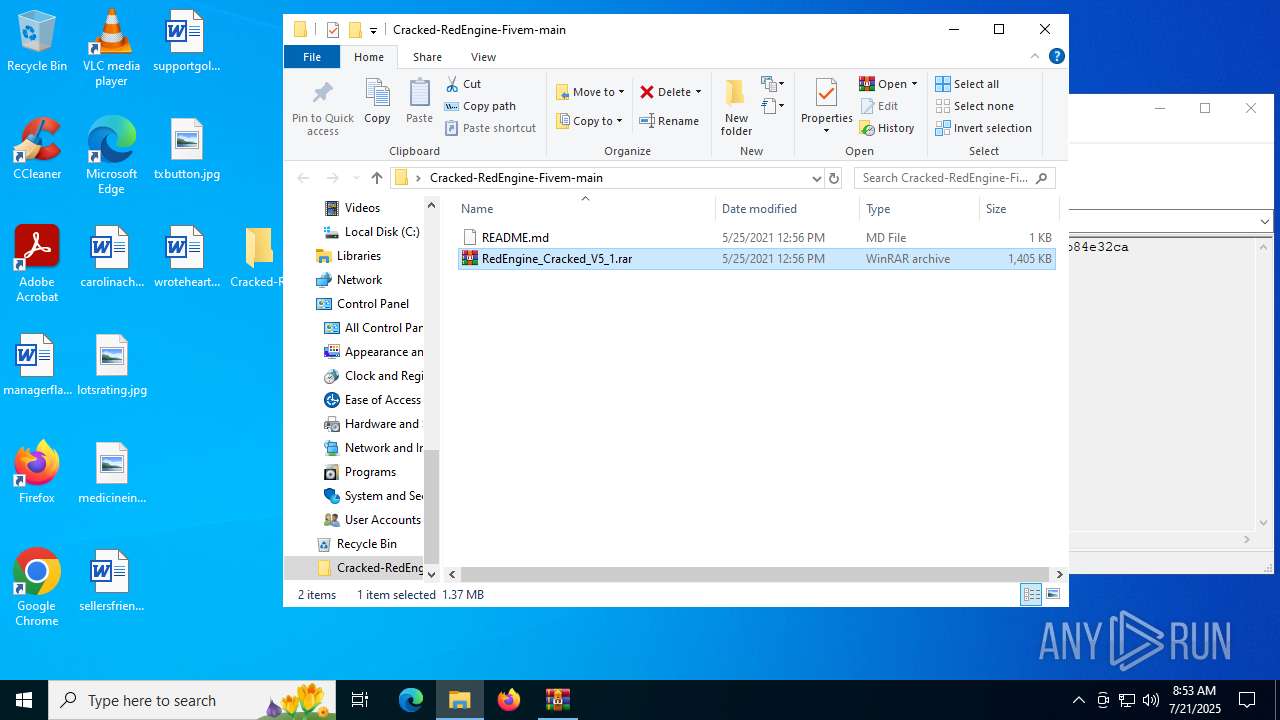
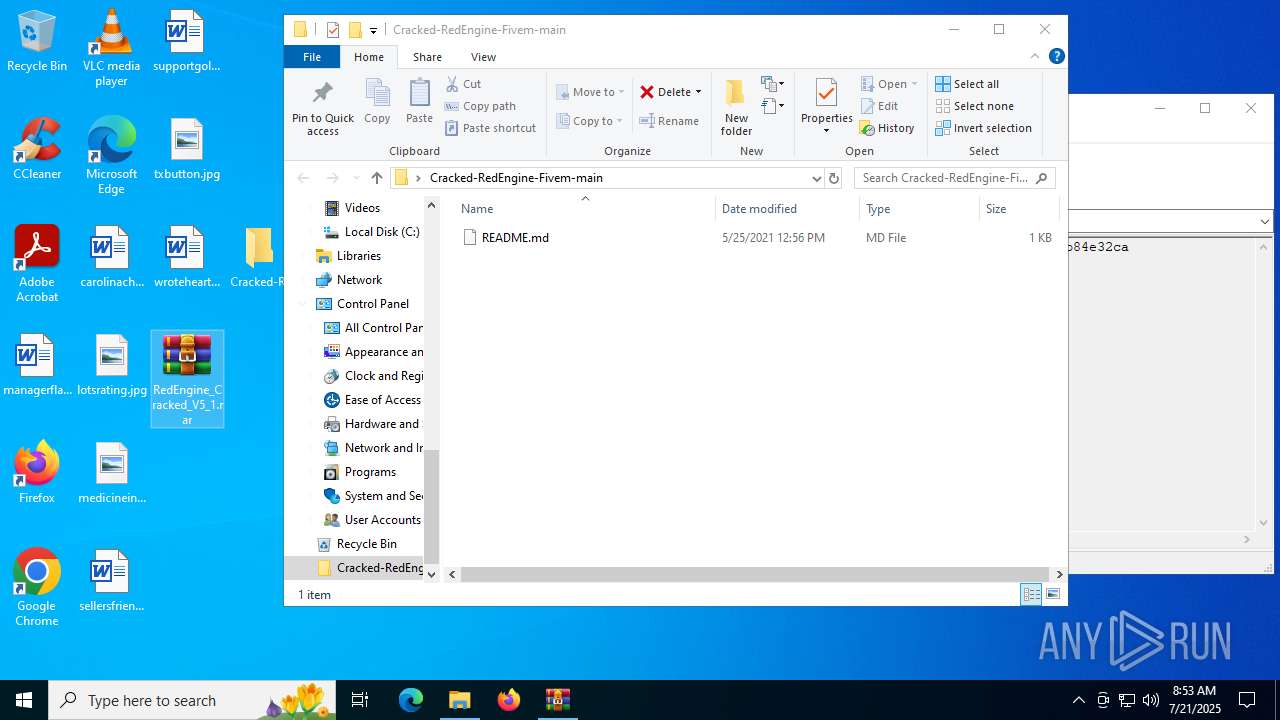
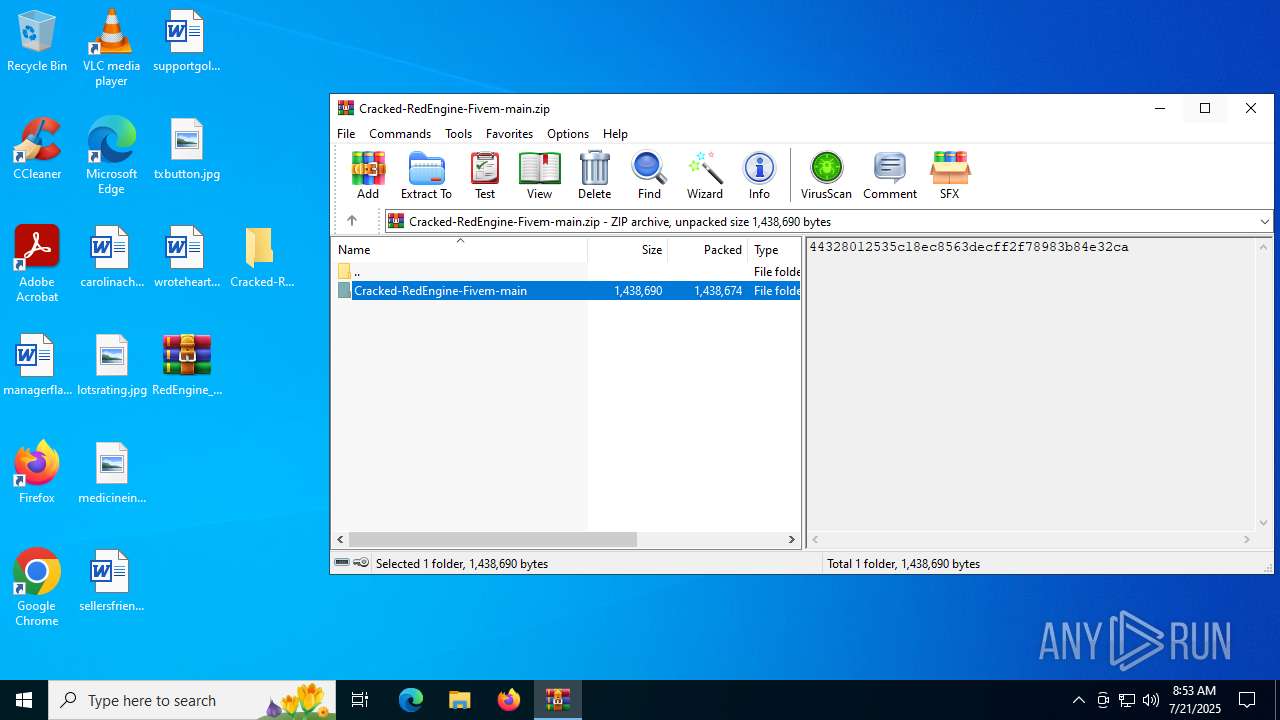
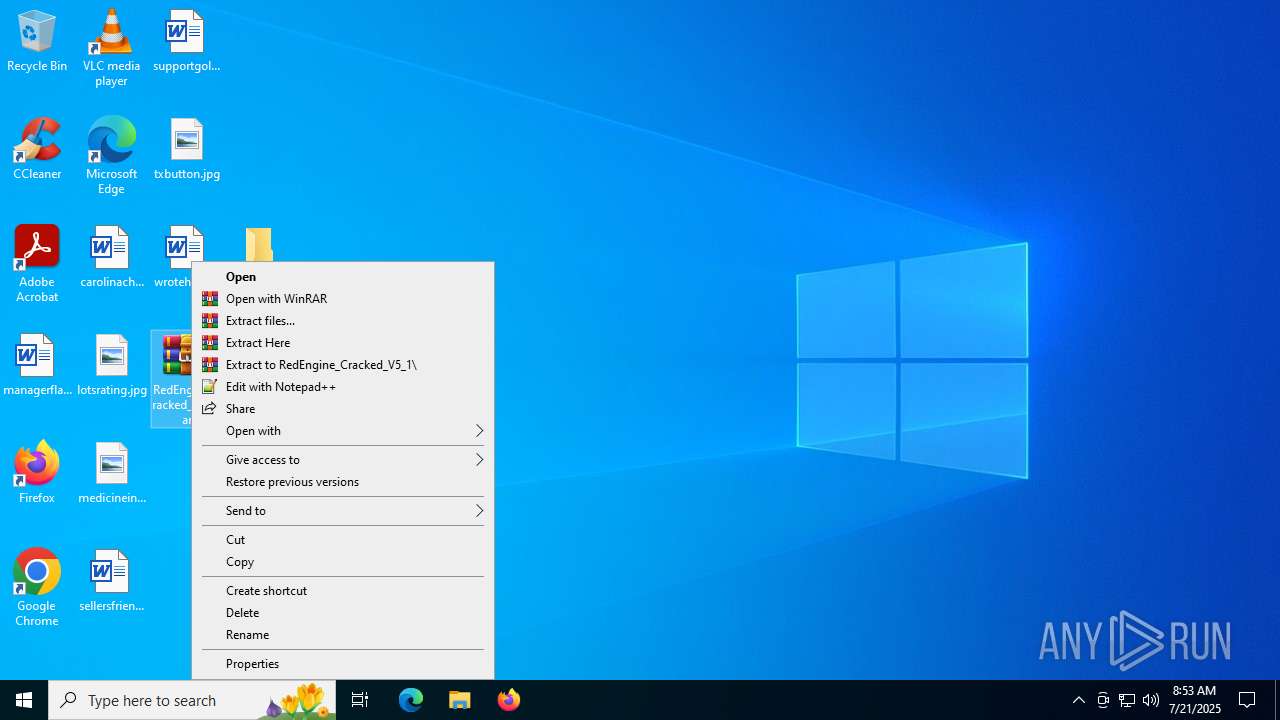
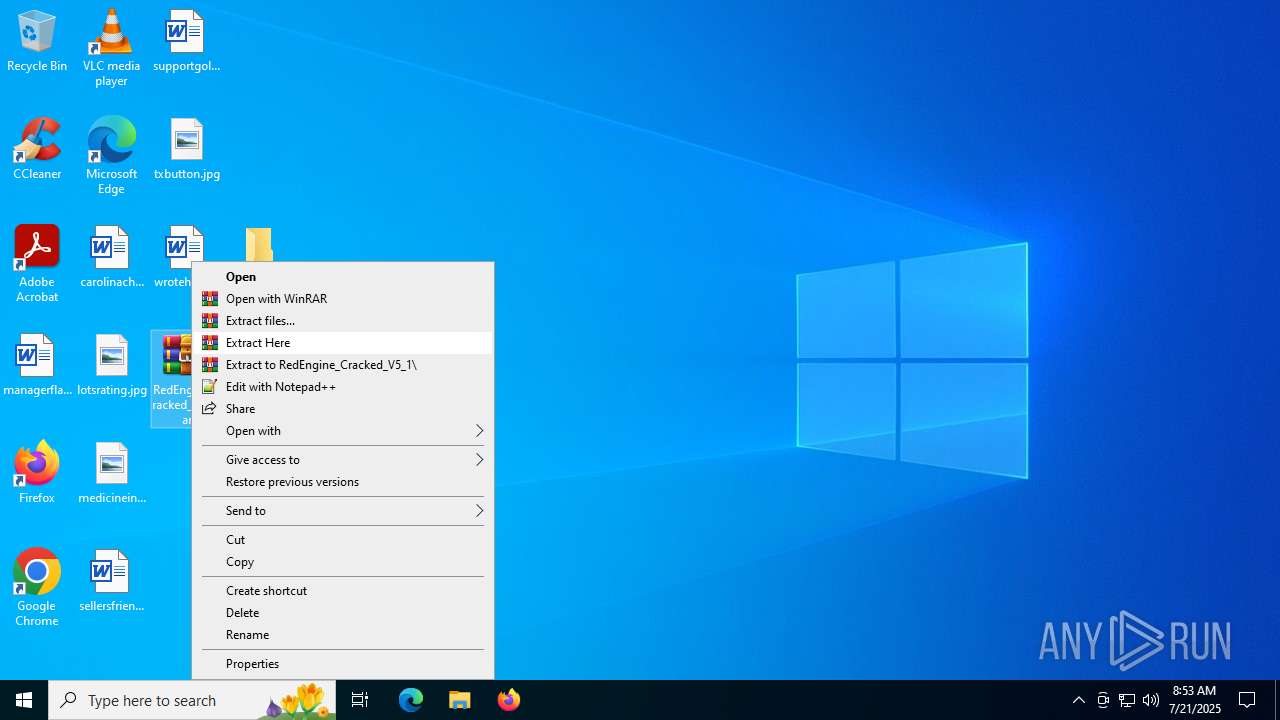
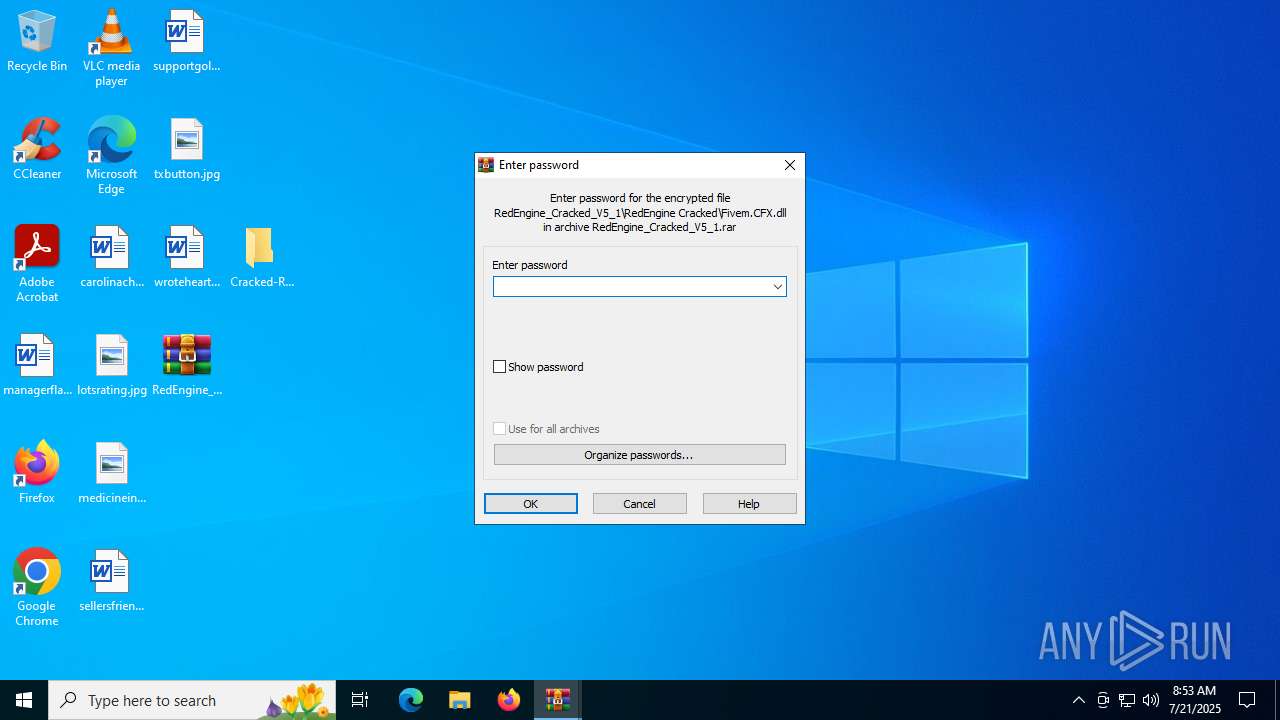
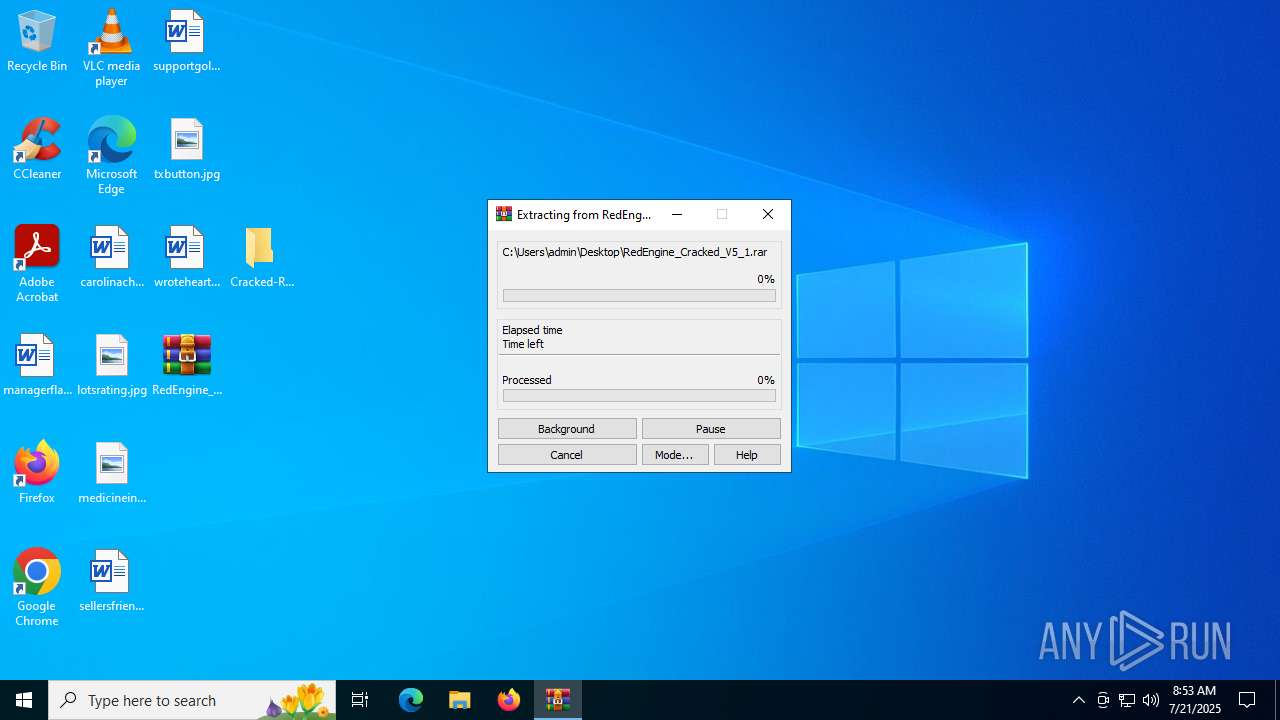
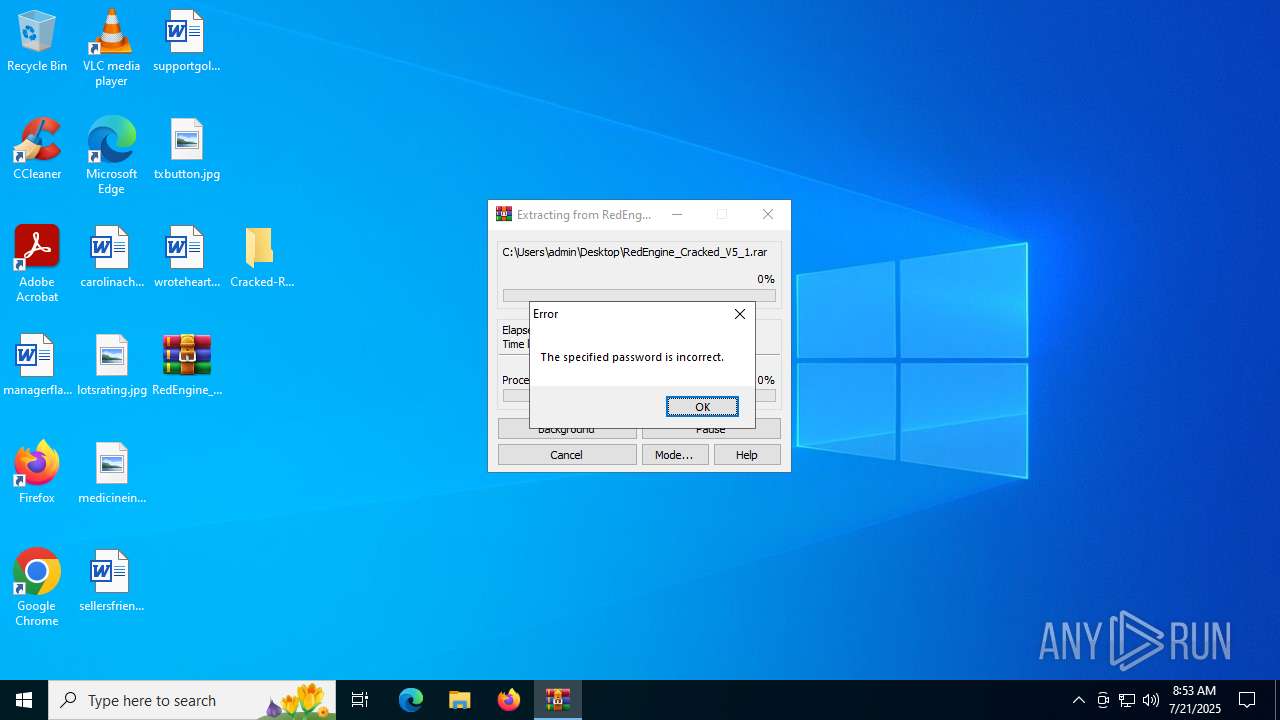
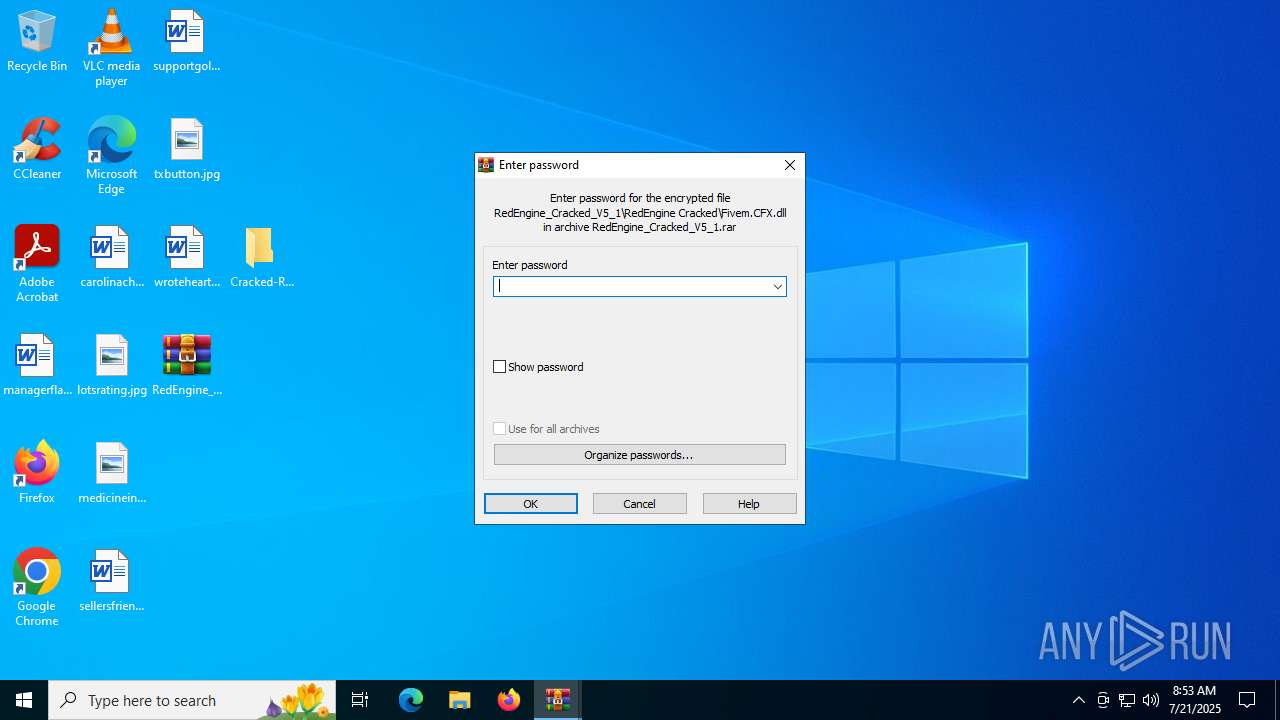
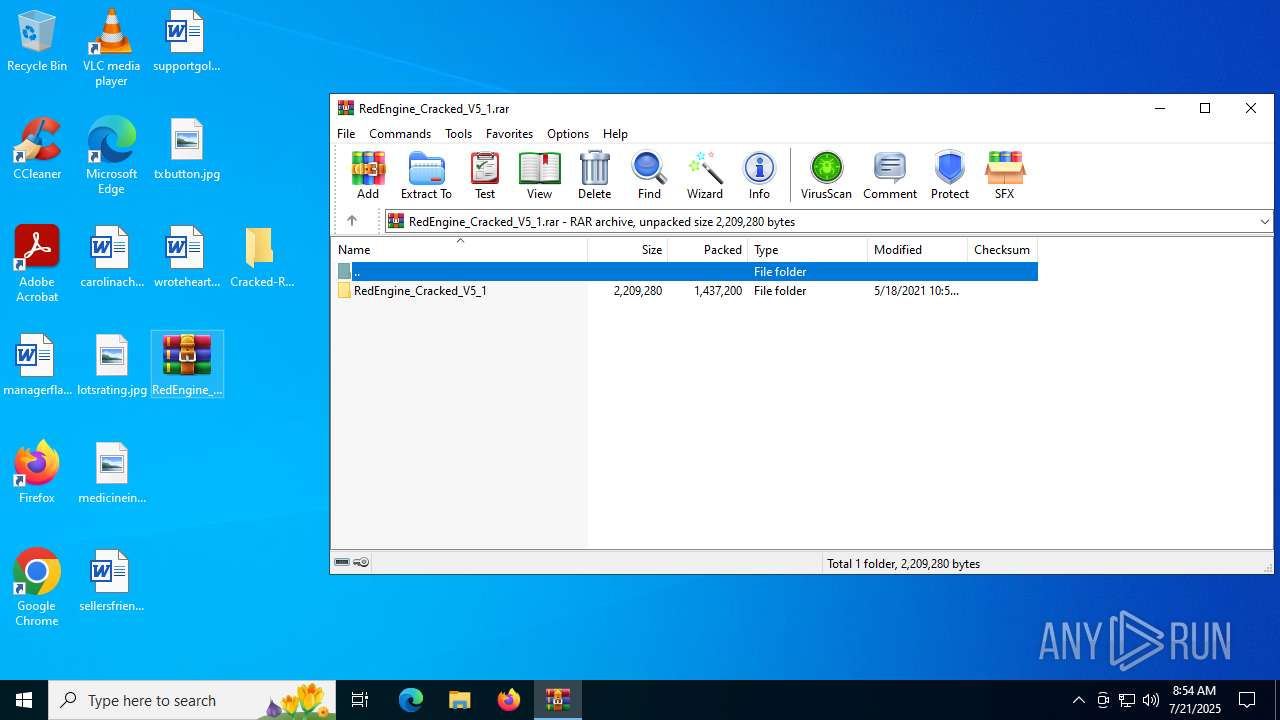
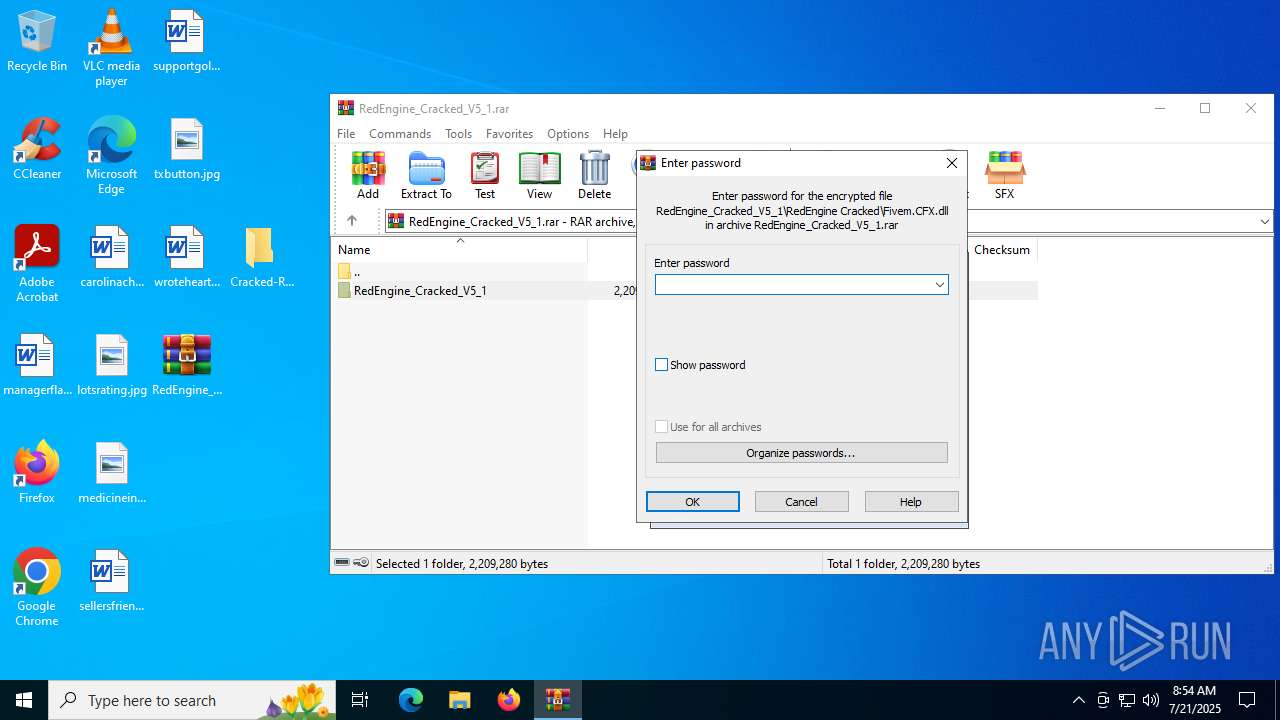
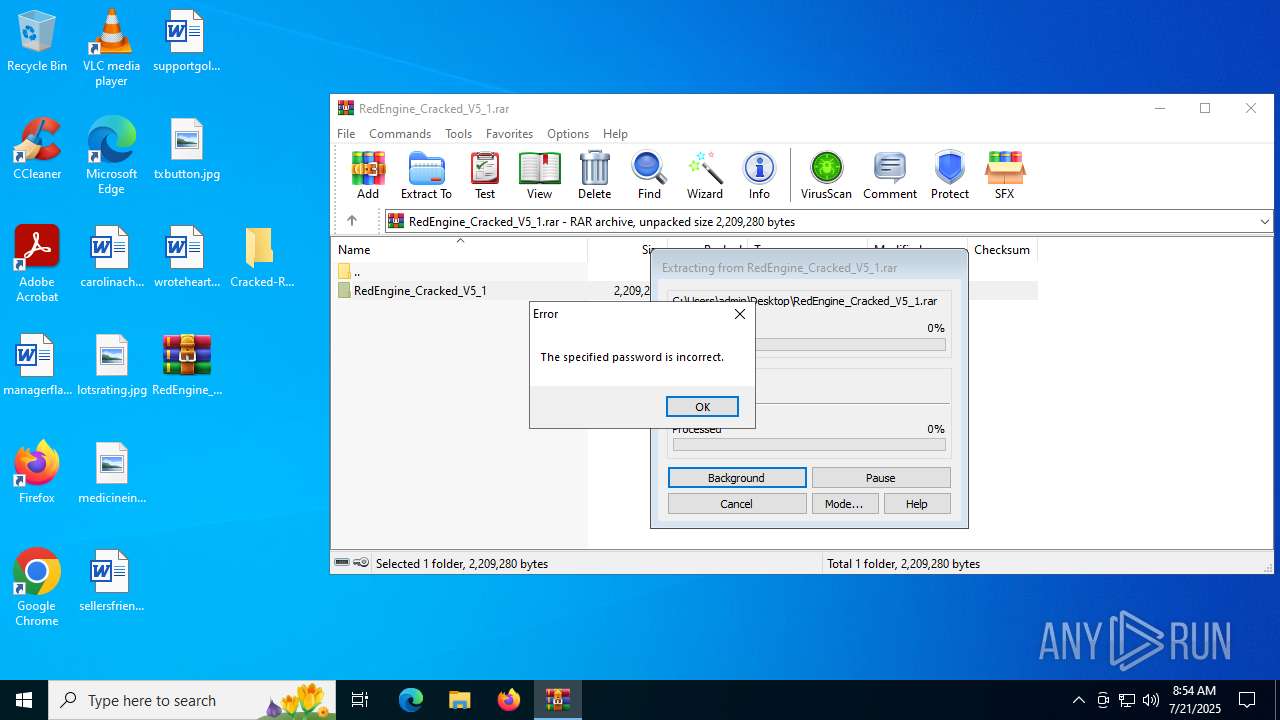
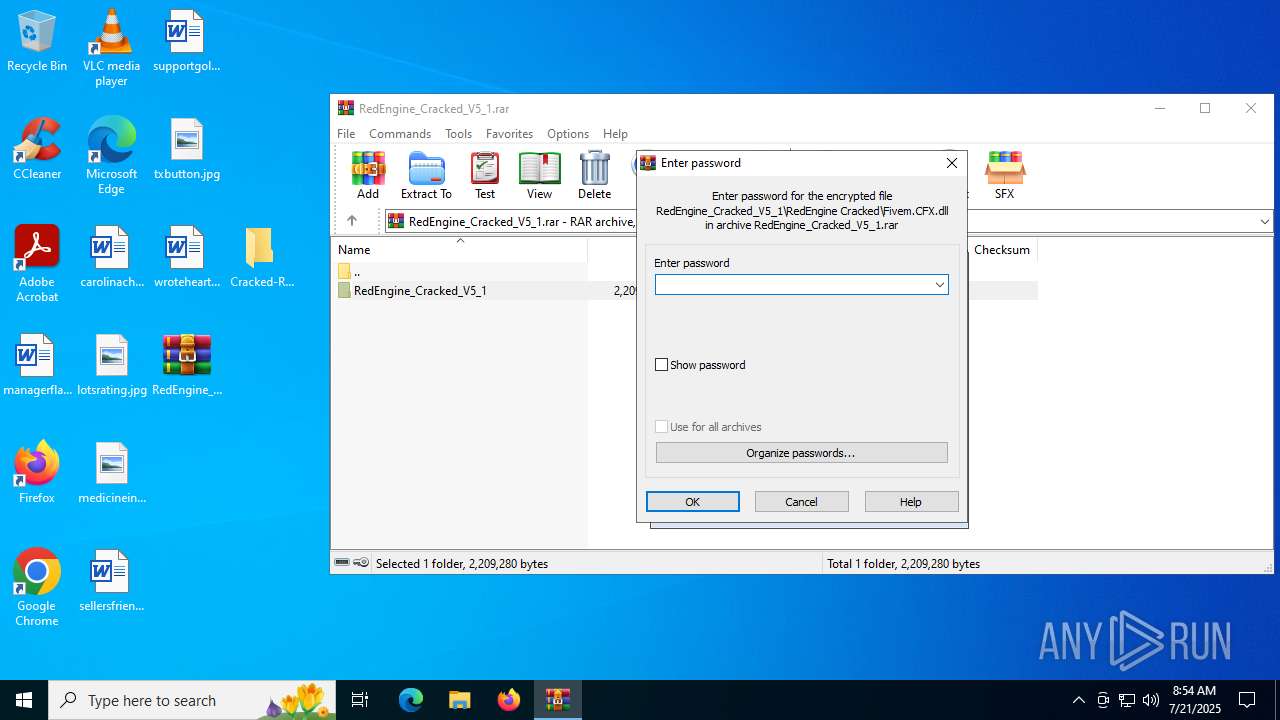
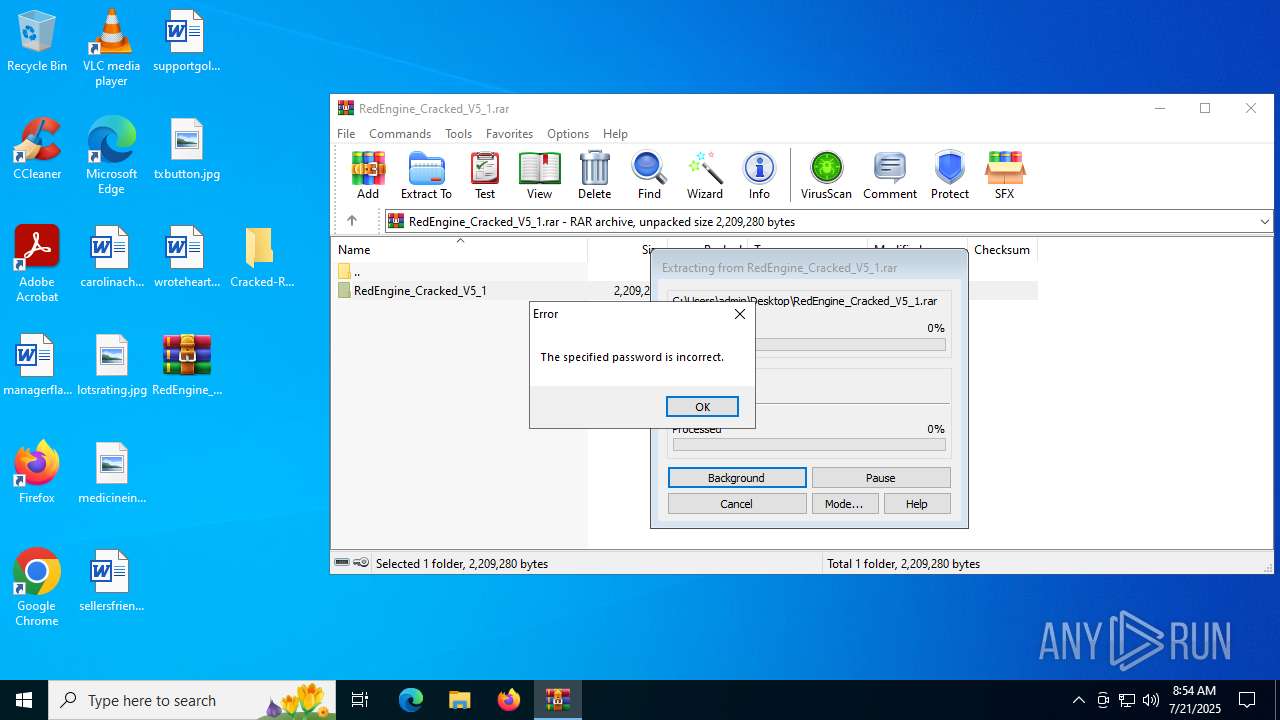
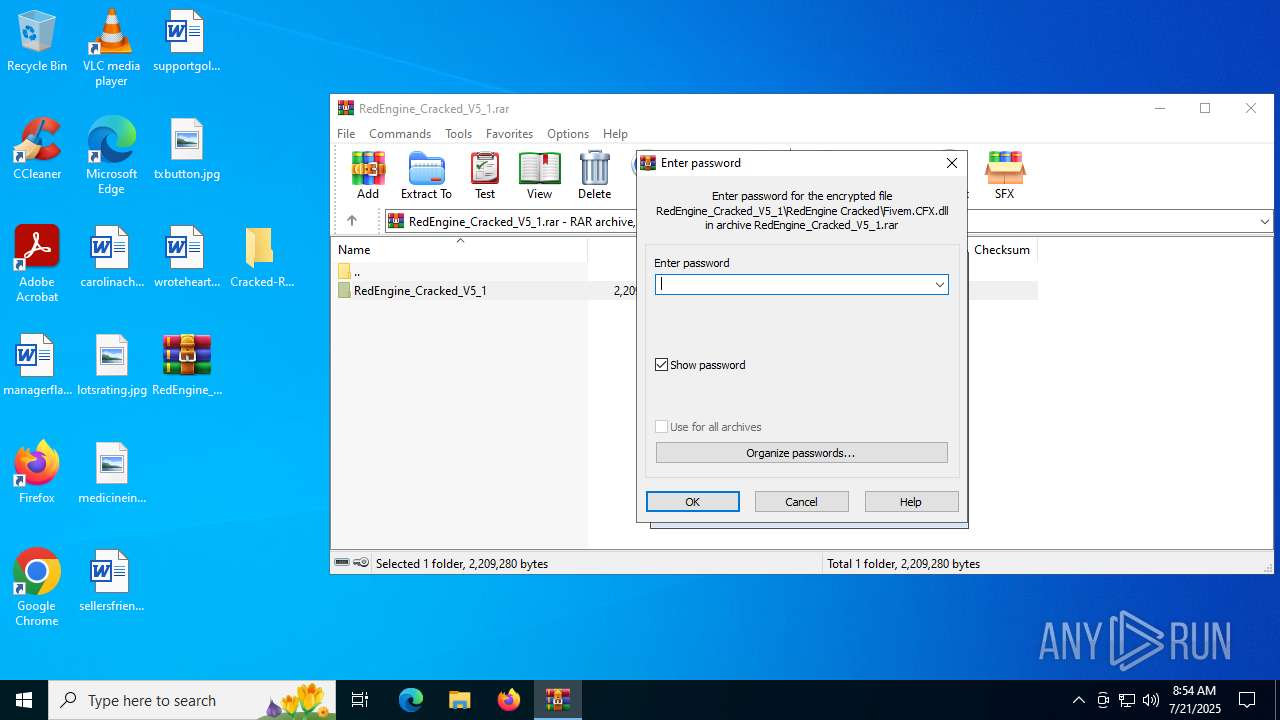
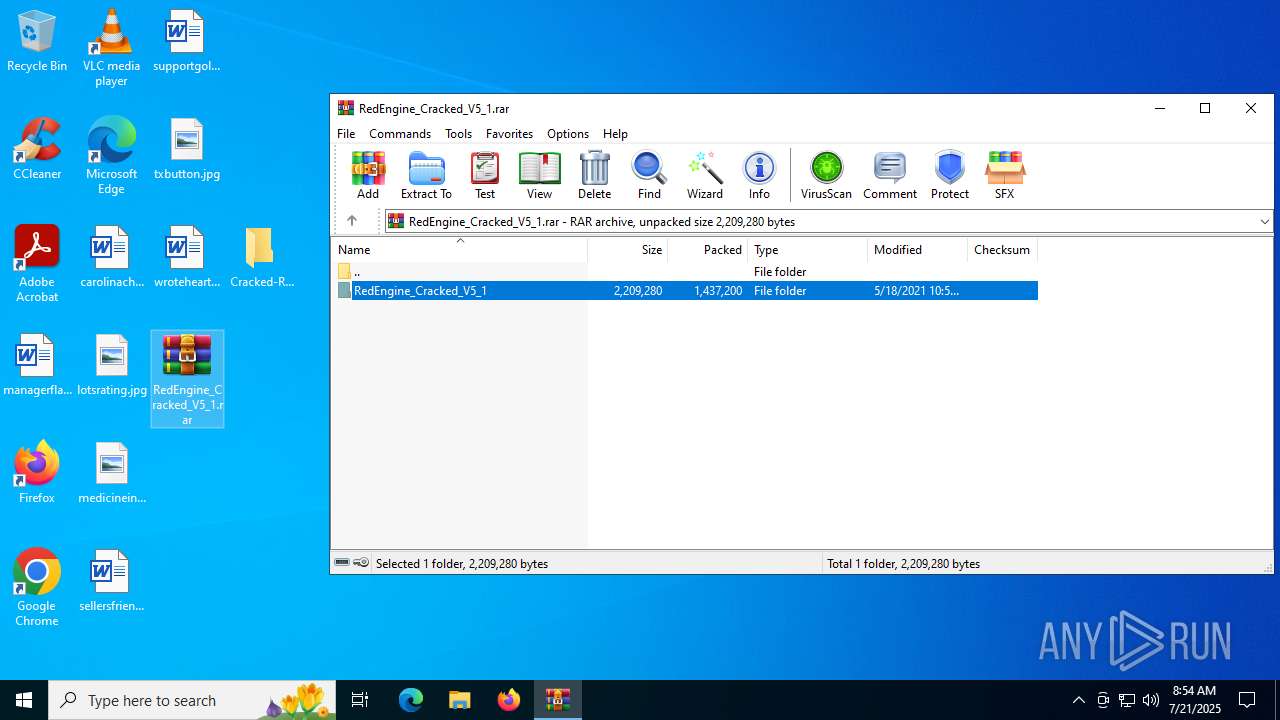
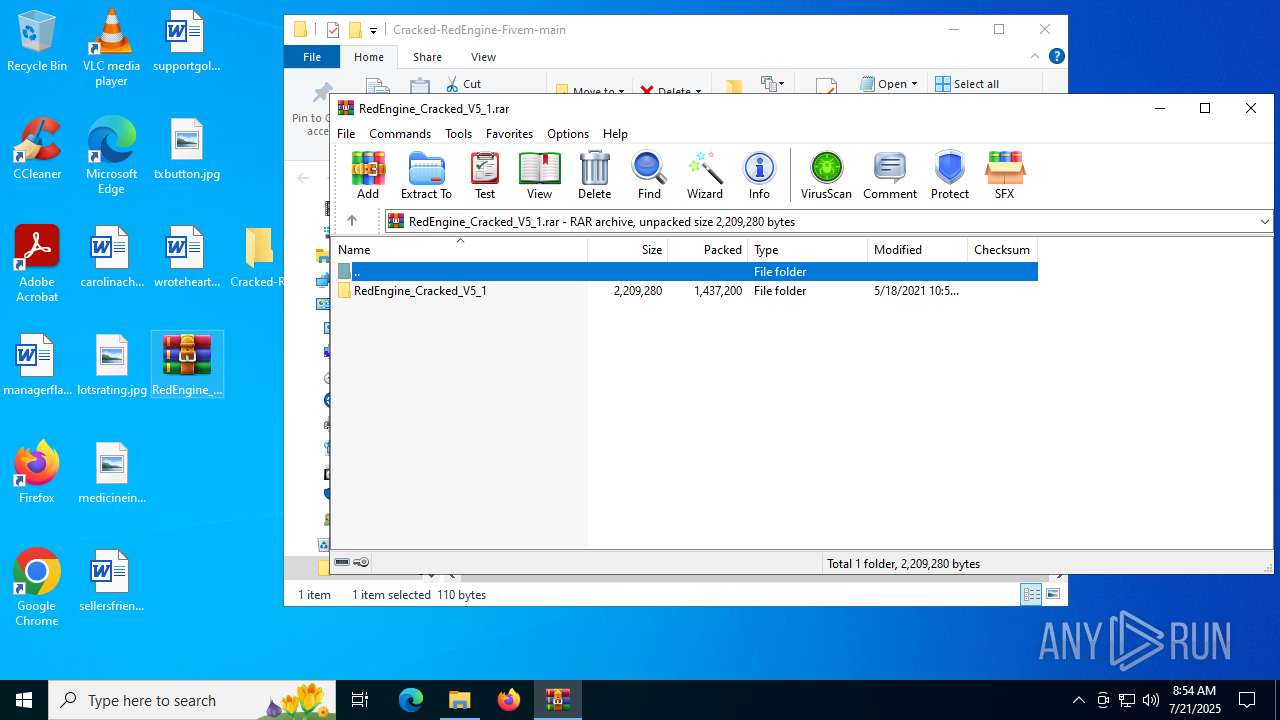
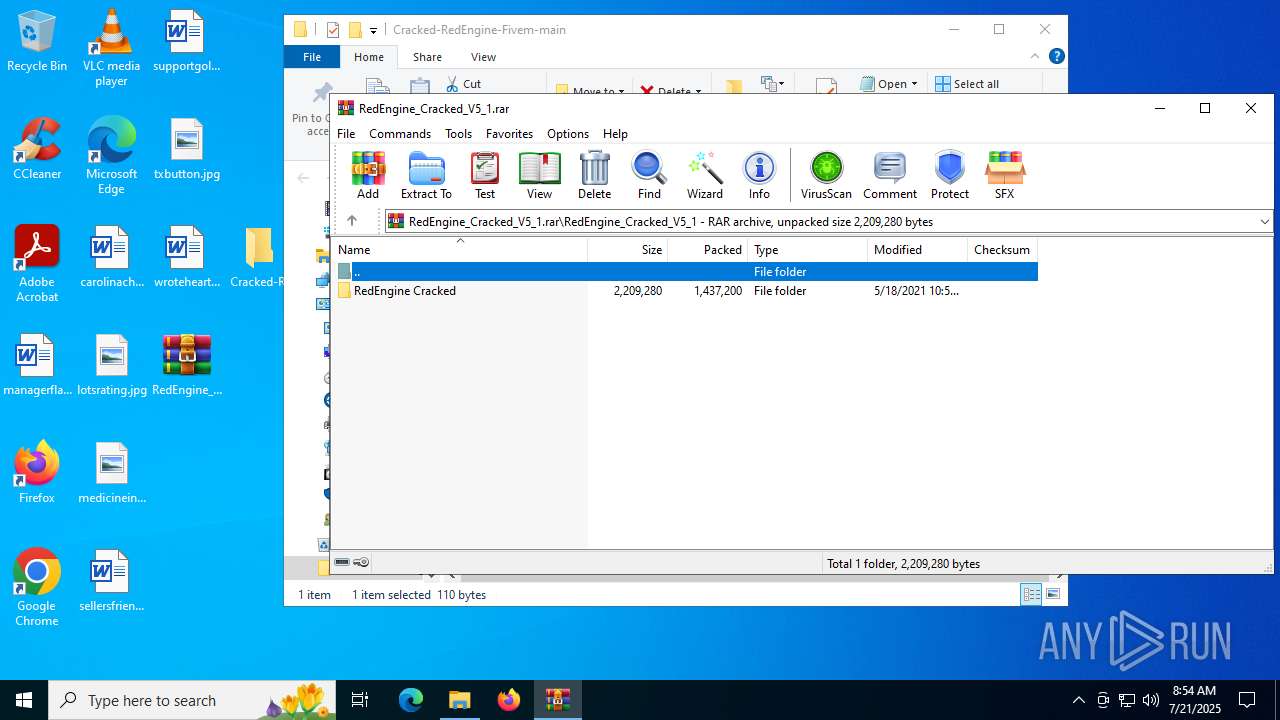
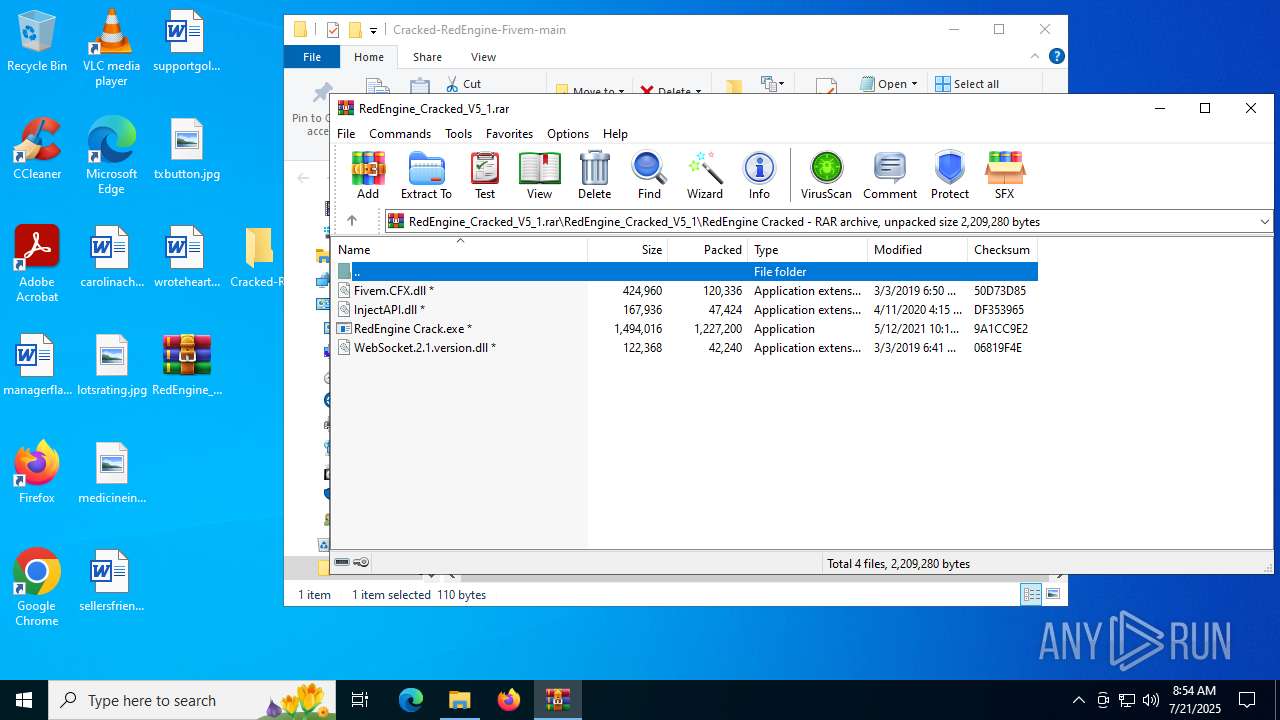
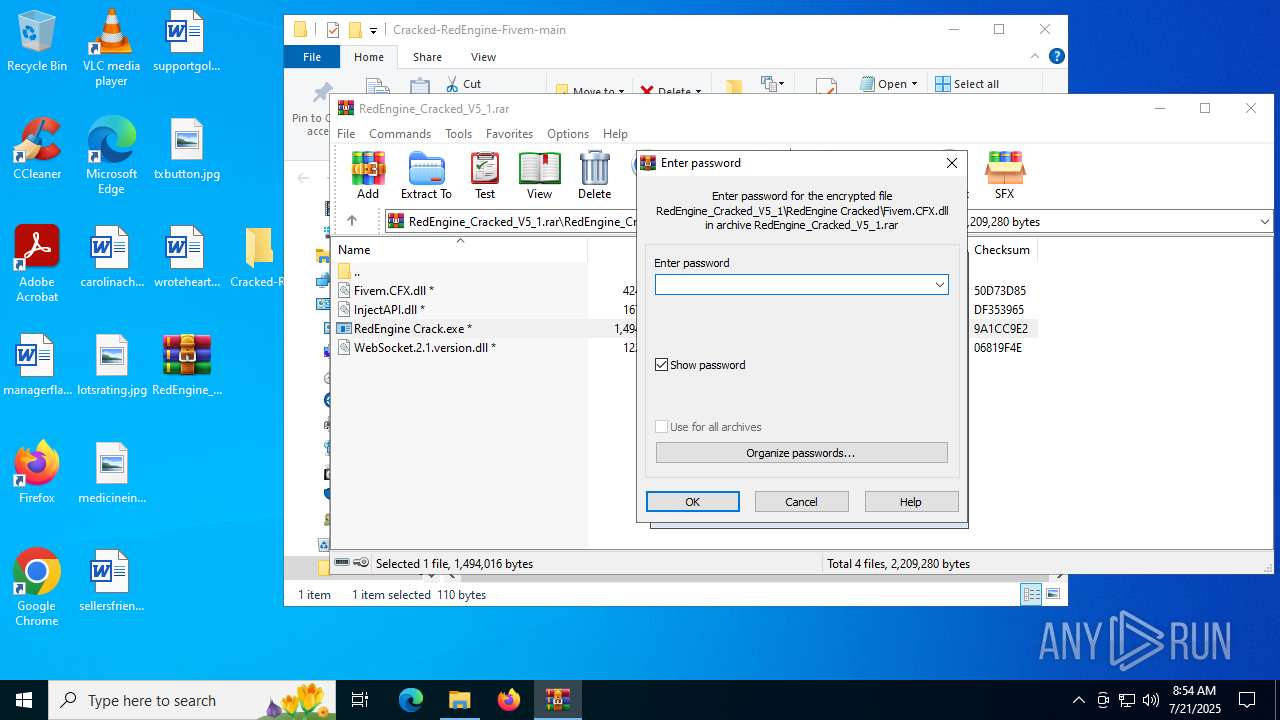
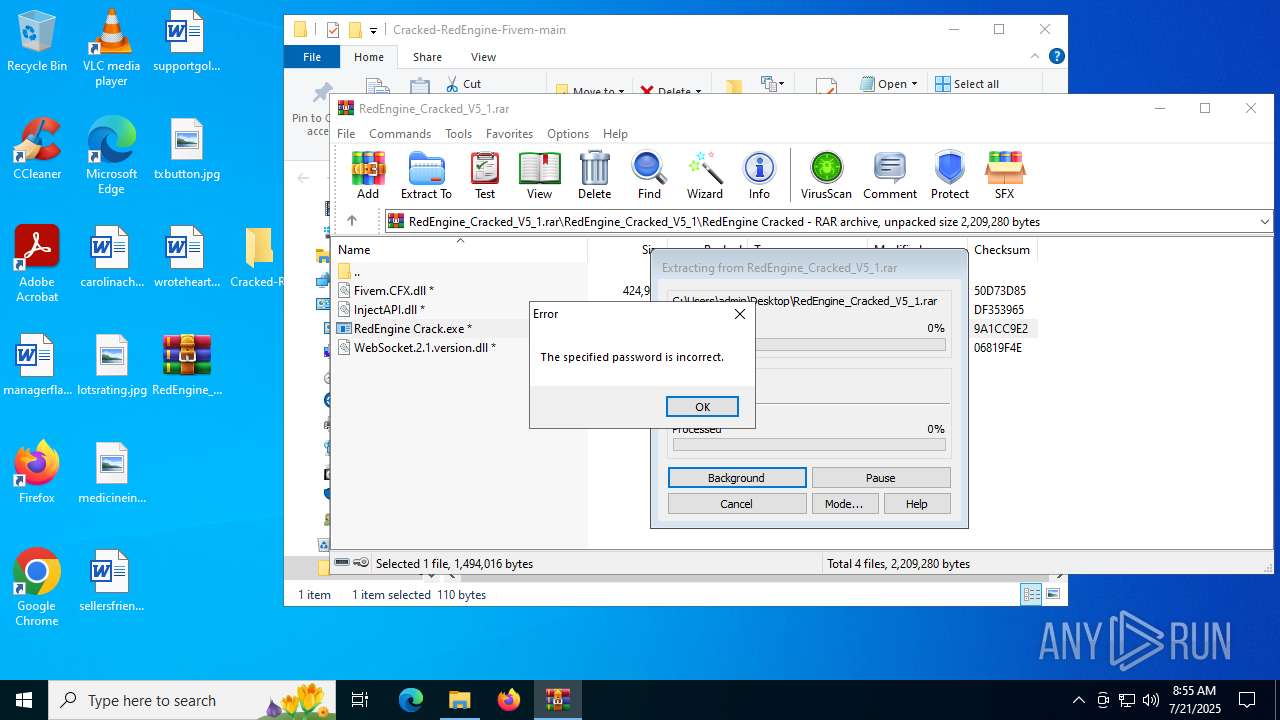
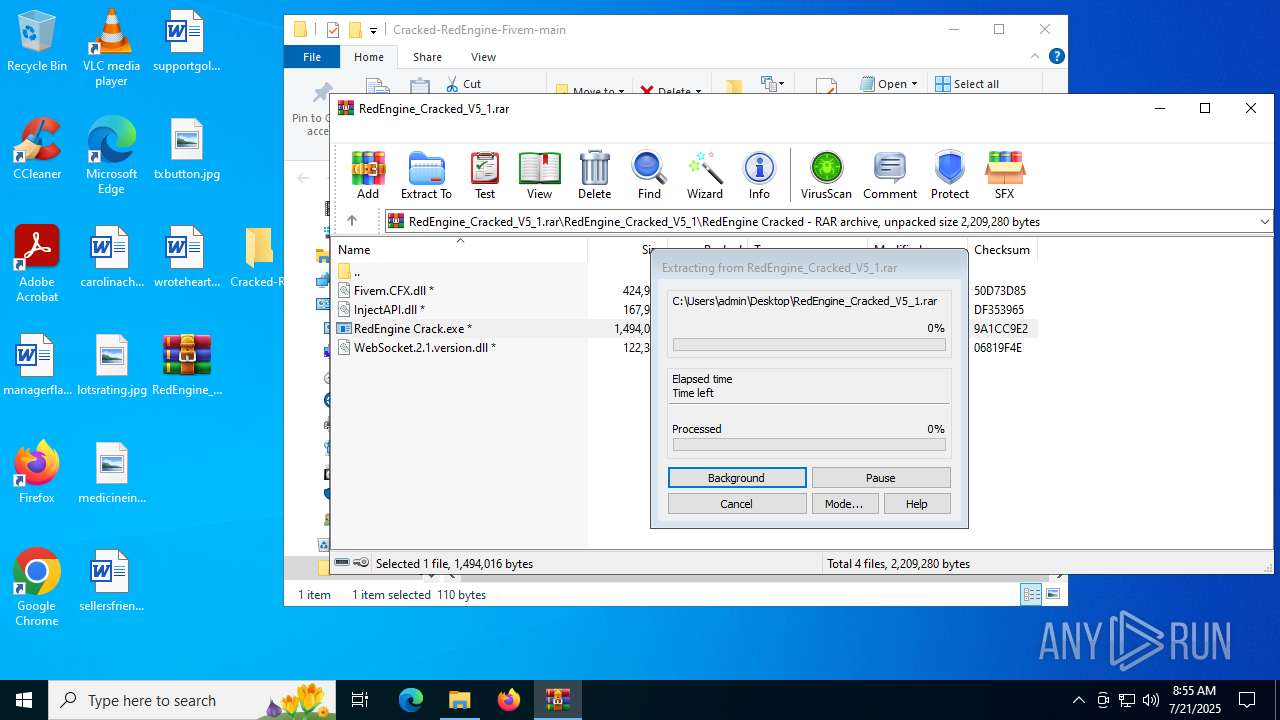
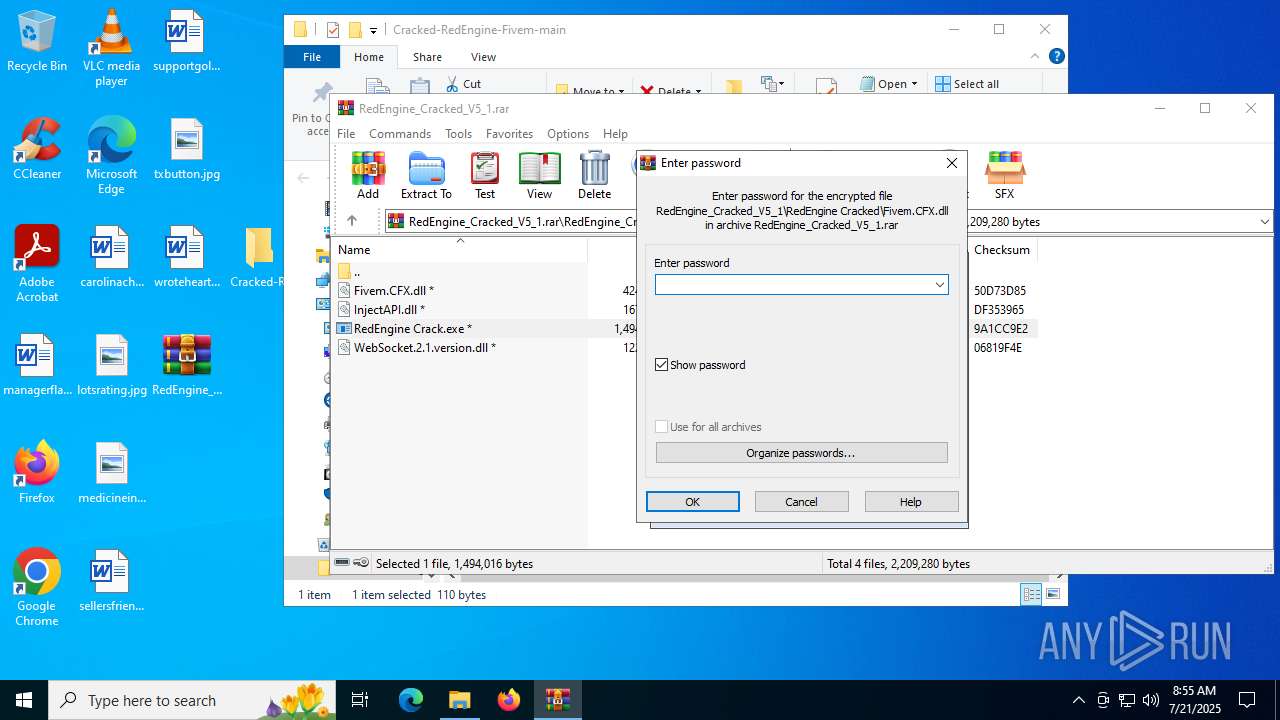
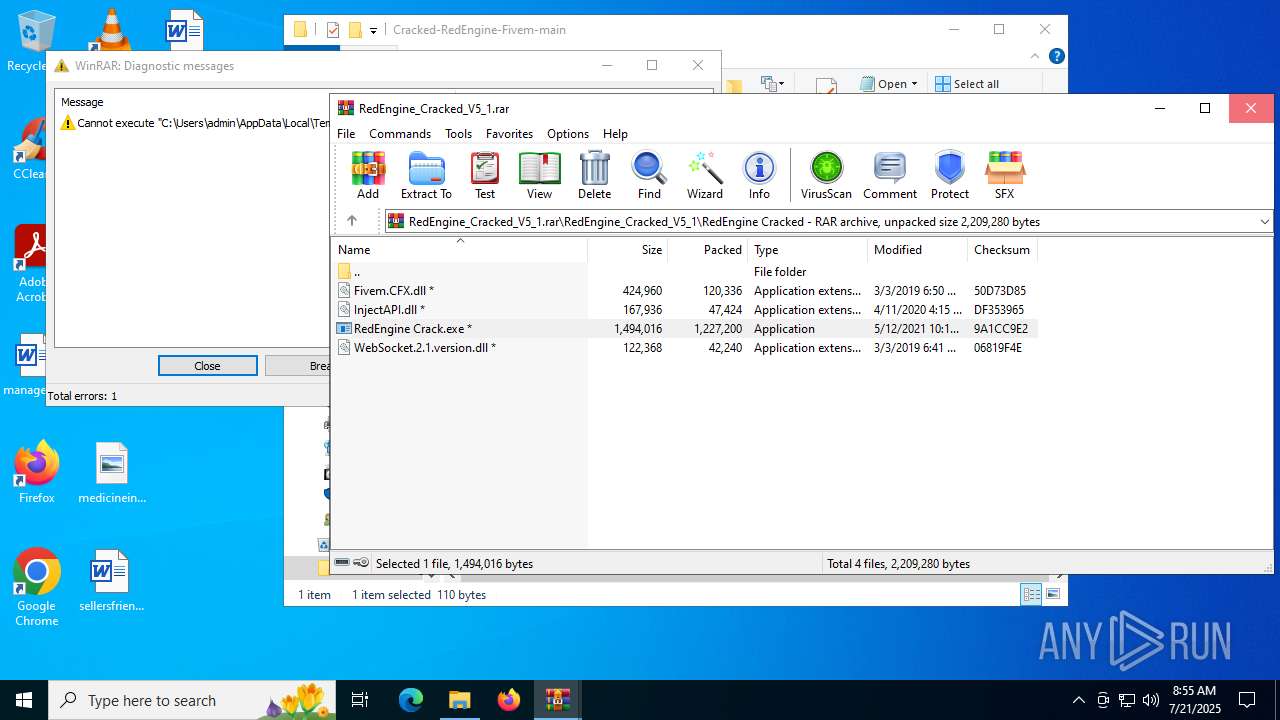
Generic archive extractor
- WinRAR.exe (PID: 6404)
The process checks if it is being run in the virtual environment
- dllhost.exe (PID: 3672)
Uses NETSH.EXE to change the status of the firewall
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Creates file in the systems drive root
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 4948)
- Annabelle.exe (PID: 7324)
- Annabelle.exe (PID: 7152)
- Annabelle.exe (PID: 7420)
Executes as Windows Service
- VSSVC.exe (PID: 8424)
Reads security settings of Internet Explorer
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 5960)
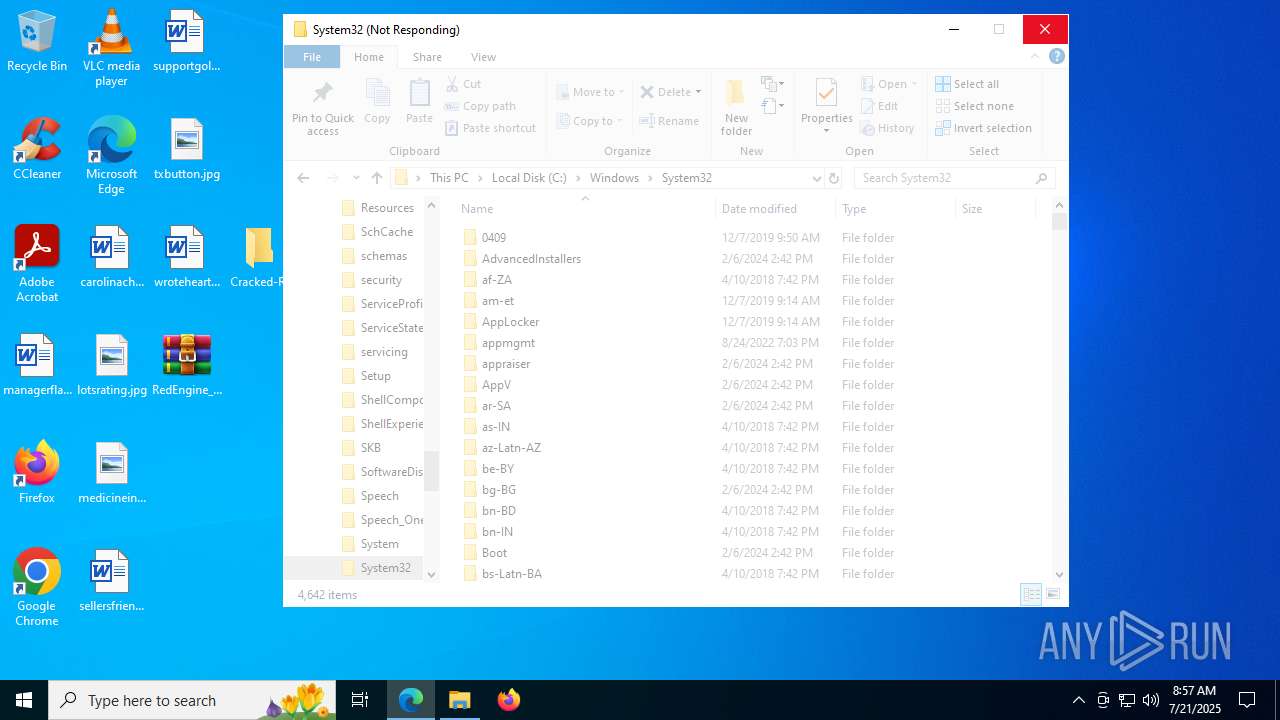
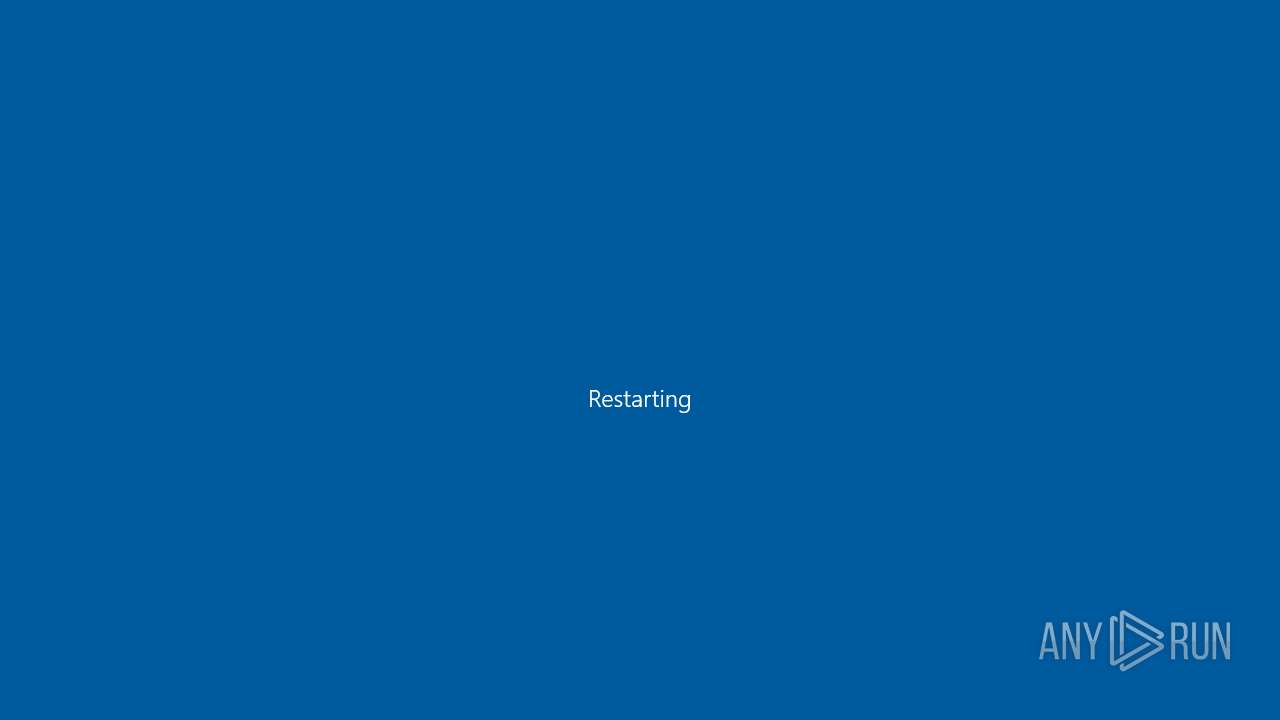
The system shut down or reboot
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Reads the date of Windows installation
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 5968)
- OpenWith.exe (PID: 3852)
- OpenWith.exe (PID: 5988)
- notepad.exe (PID: 1472)
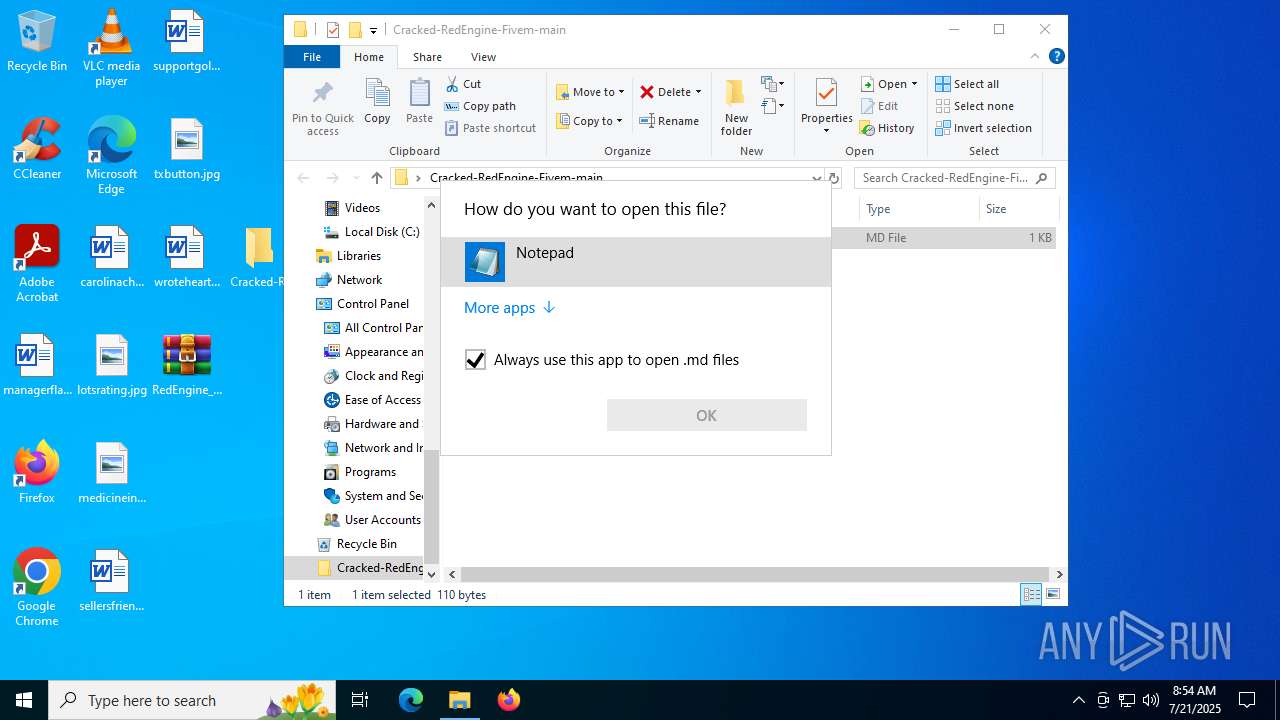
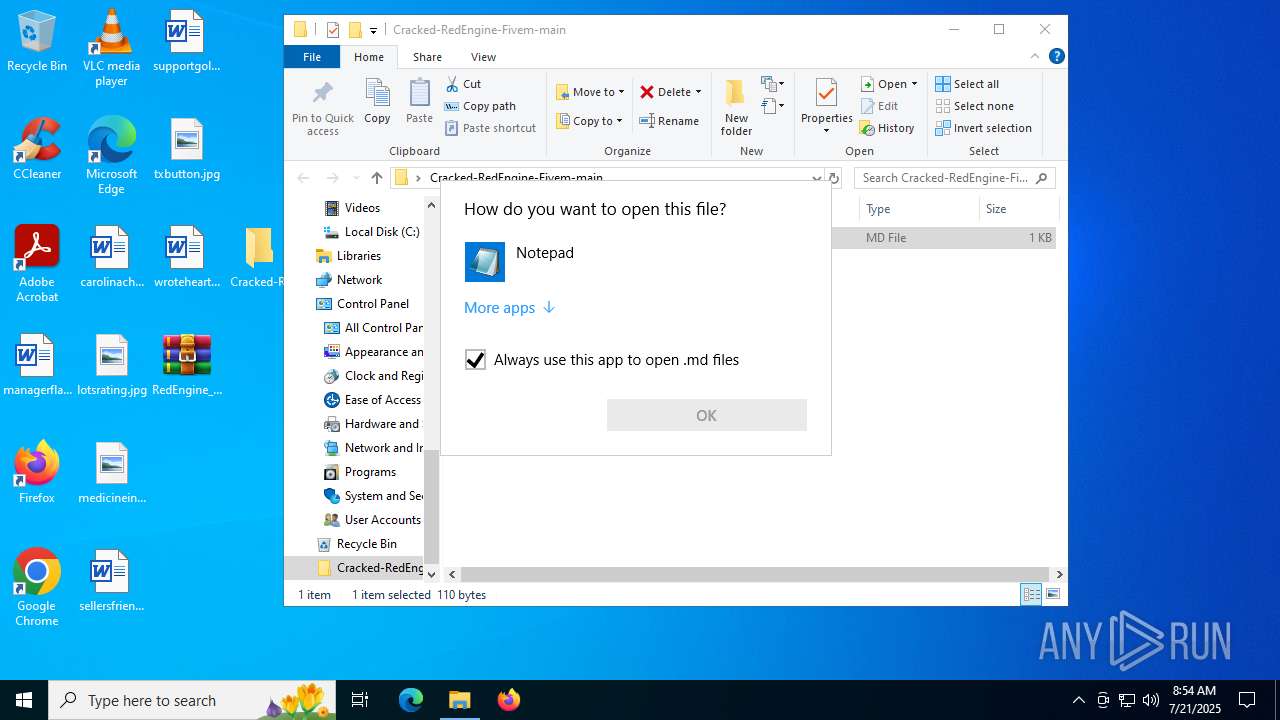
Manual execution by a user
- WinRAR.exe (PID: 3400)
- WinRAR.exe (PID: 1728)
- msedge.exe (PID: 6756)
- WinRAR.exe (PID: 6292)
Reads the software policy settings
- slui.exe (PID: 1352)
Reads the computer name
- identity_helper.exe (PID: 6508)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 7324)
- Annabelle.exe (PID: 4948)
- Annabelle.exe (PID: 7420)
- Annabelle.exe (PID: 7152)
- Annabelle.exe (PID: 7136)
- Annabelle.exe (PID: 1192)
- Annabelle.exe (PID: 2628)
- Annabelle.exe (PID: 1636)
- Annabelle.exe (PID: 5460)
- Annabelle.exe (PID: 7984)
- Annabelle.exe (PID: 6356)
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 8040)
Checks supported languages
- identity_helper.exe (PID: 6508)
- Annabelle.exe (PID: 7324)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 7420)
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 7152)
- Annabelle.exe (PID: 1192)
- Annabelle.exe (PID: 5460)
- Annabelle.exe (PID: 2628)
- Annabelle.exe (PID: 6356)
- Annabelle.exe (PID: 7984)
- Annabelle.exe (PID: 1636)
- Annabelle.exe (PID: 4948)
- Annabelle.exe (PID: 8040)
- Annabelle.exe (PID: 7136)
Application launched itself
- msedge.exe (PID: 6756)
Executable content was dropped or overwritten
- msedge.exe (PID: 3972)
- msedge.exe (PID: 6756)
Reads Environment values
- identity_helper.exe (PID: 6508)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5988)
- OpenWith.exe (PID: 3852)
Checks proxy server information
- slui.exe (PID: 1352)
Launching a file from a Registry key
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Reads the machine GUID from the registry
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 8108)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 4948)
- Annabelle.exe (PID: 7324)
- Annabelle.exe (PID: 7152)
- Annabelle.exe (PID: 7420)
Process checks computer location settings
- Annabelle.exe (PID: 5296)
- Annabelle.exe (PID: 5960)
- Annabelle.exe (PID: 8108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:05:25 05:56:38 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Cracked-RedEngine-Fivem-main/ |
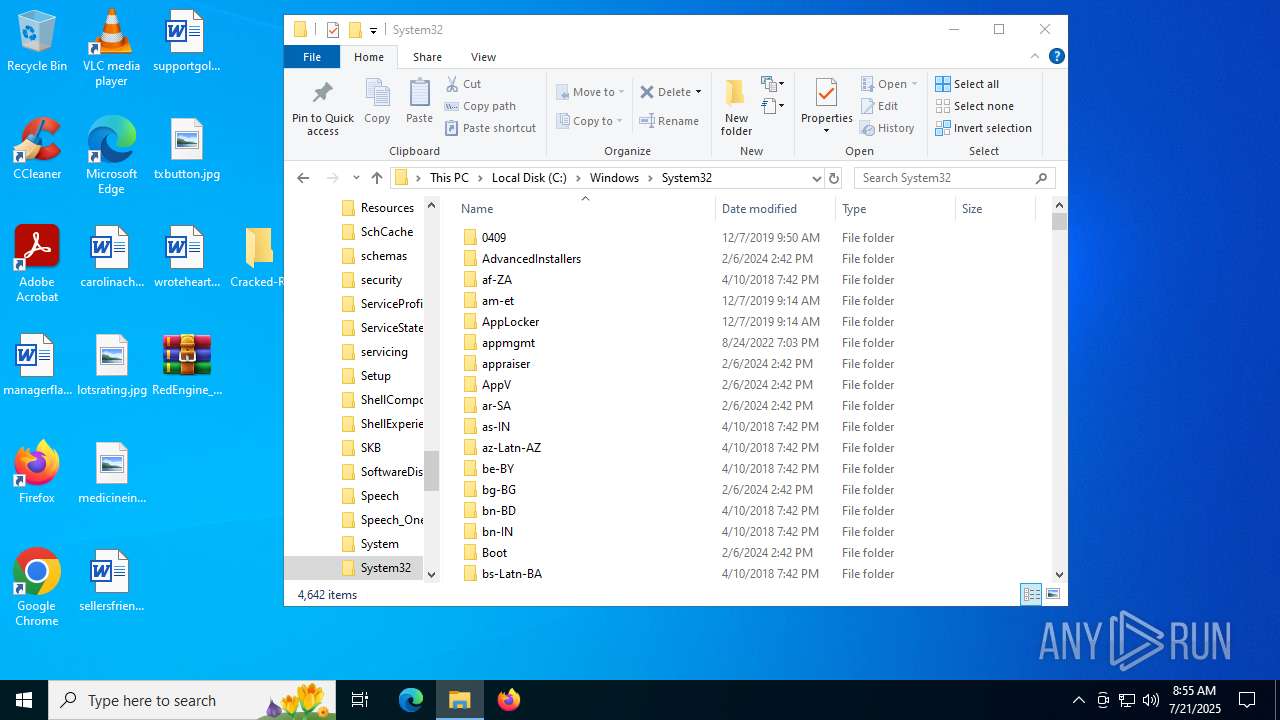
Total processes
273
Monitored processes
106
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Users\admin\Downloads\Annabelle.exe" | C:\Users\admin\Downloads\Annabelle.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Annabelle Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7160,i,18421373573152859239,10226452354987679862,262144 --variations-seed-version --mojo-platform-channel-handle=6996 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc44cdf208,0x7ffc44cdf214,0x7ffc44cdf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5540,i,18421373573152859239,10226452354987679862,262144 --variations-seed-version --mojo-platform-channel-handle=5516 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\Downloads\Annabelle.exe" | C:\Users\admin\Downloads\Annabelle.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Annabelle Version: 2.1.0.0 Modules
| |||||||||||||||
| 1352 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1512,i,18421373573152859239,10226452354987679862,262144 --variations-seed-version --mojo-platform-channel-handle=7064 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4272,i,18421373573152859239,10226452354987679862,262144 --variations-seed-version --mojo-platform-channel-handle=4296 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
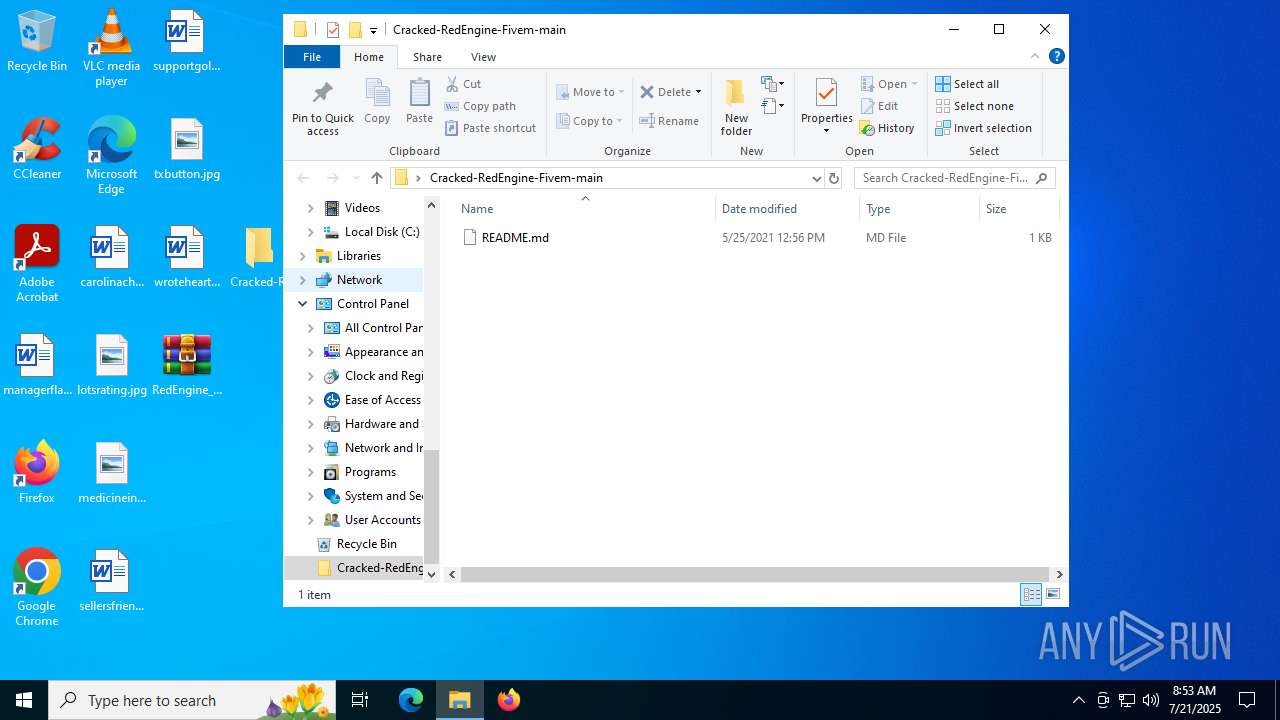
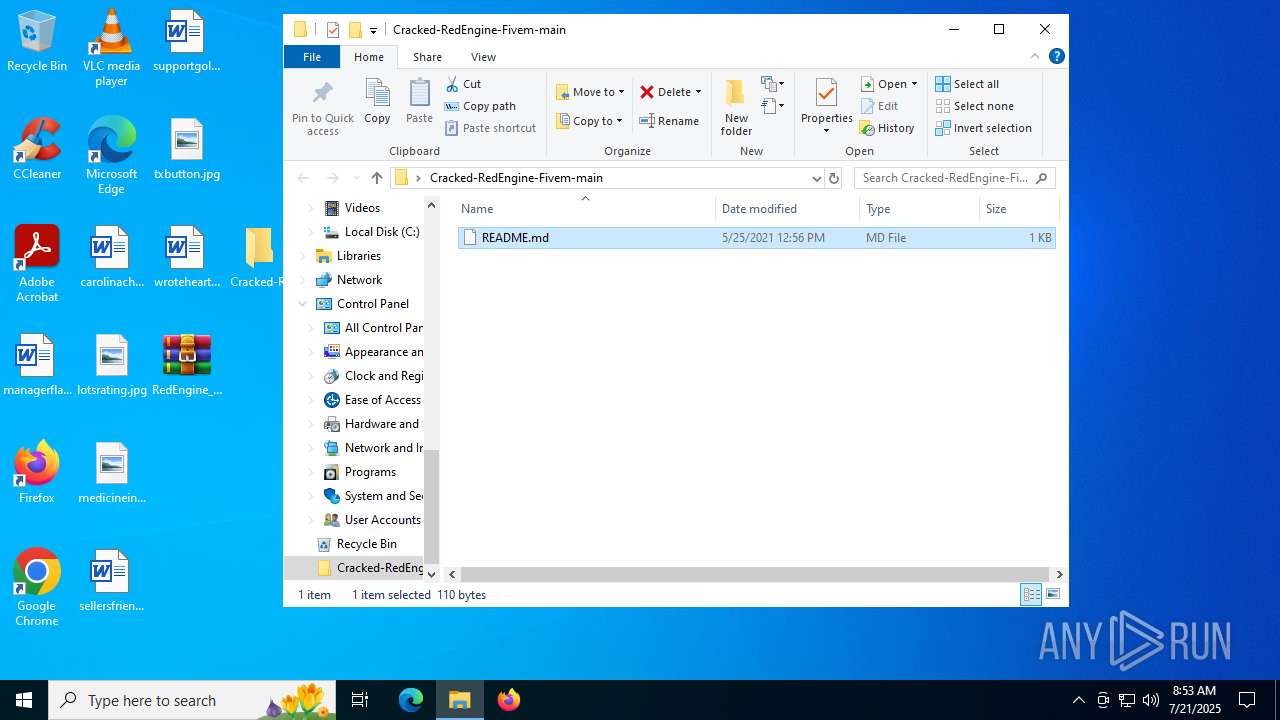
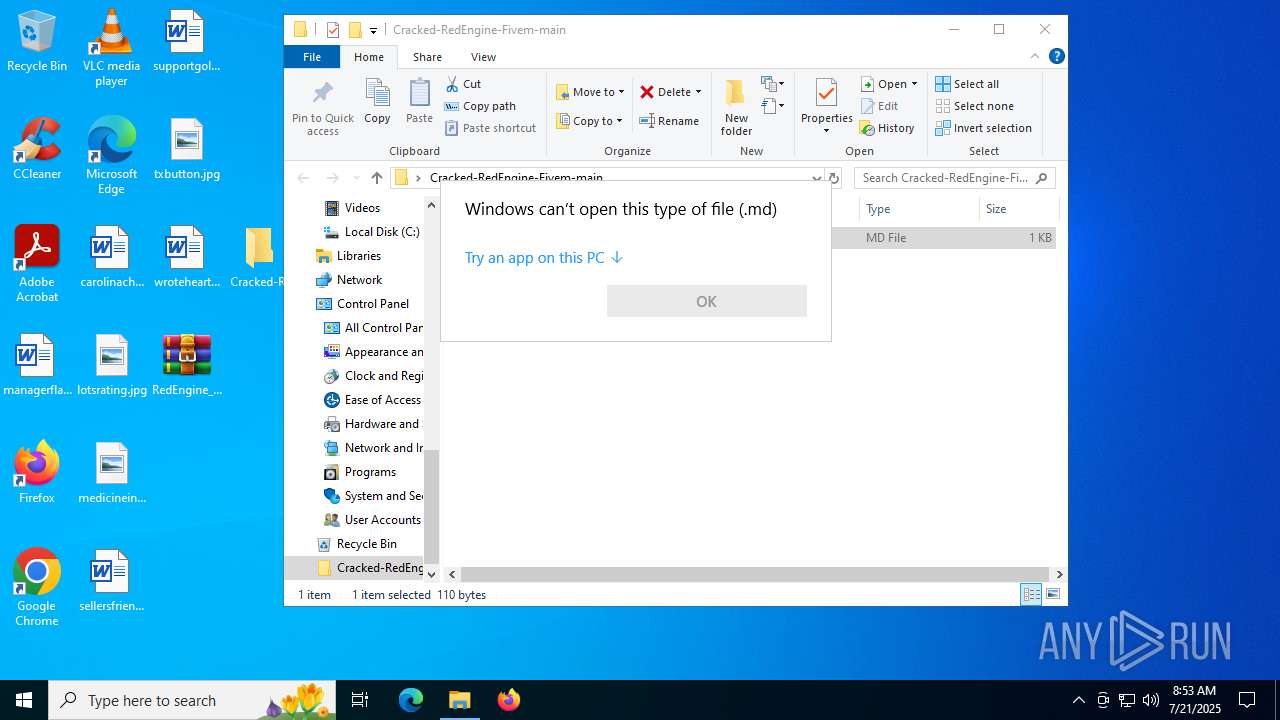
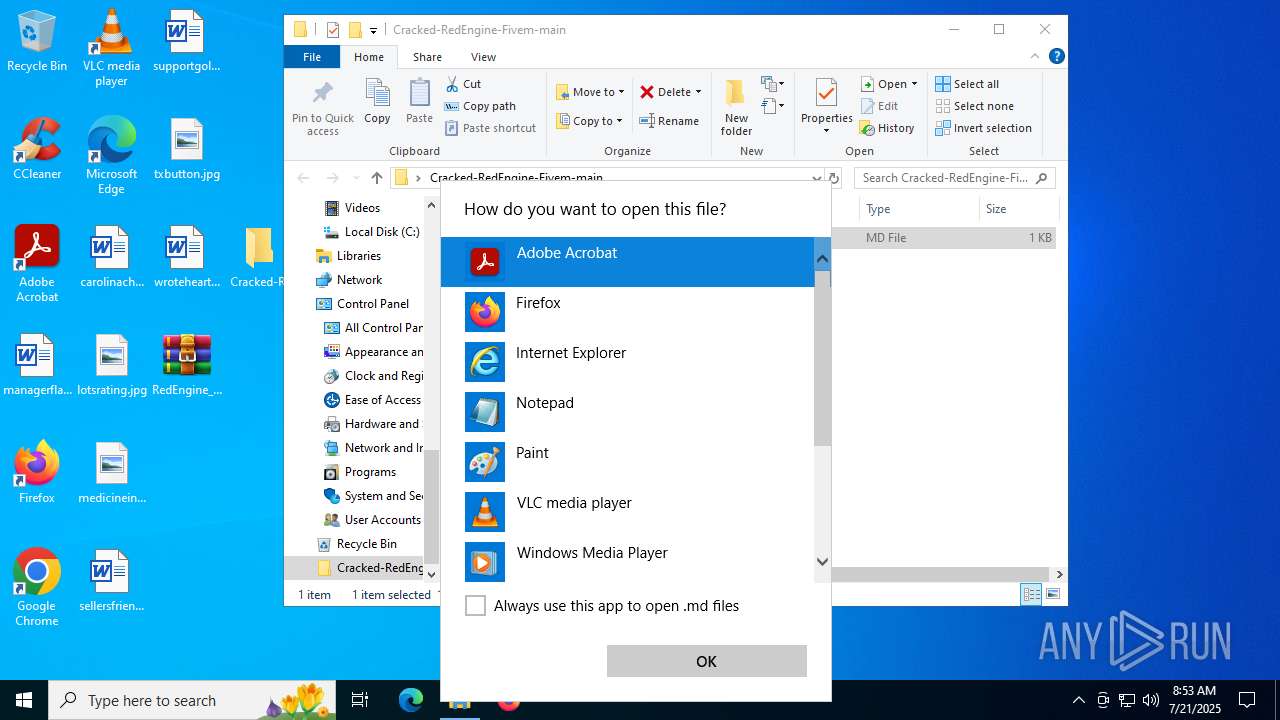
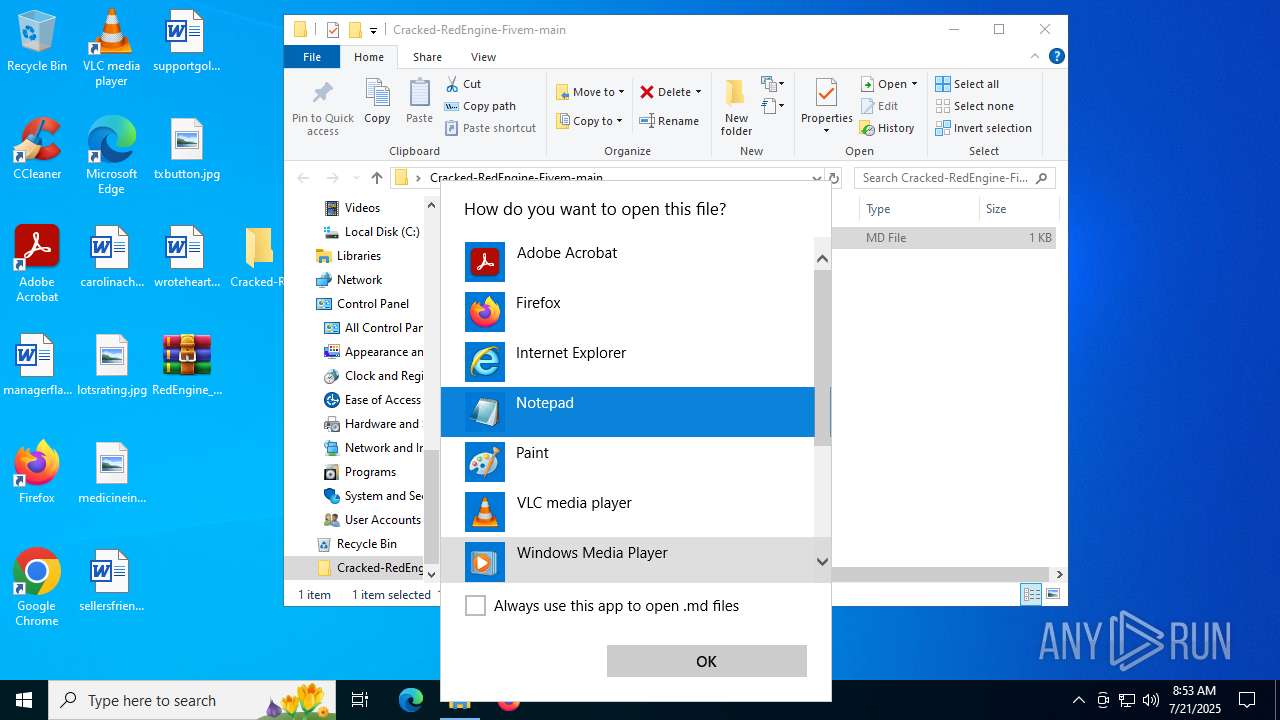
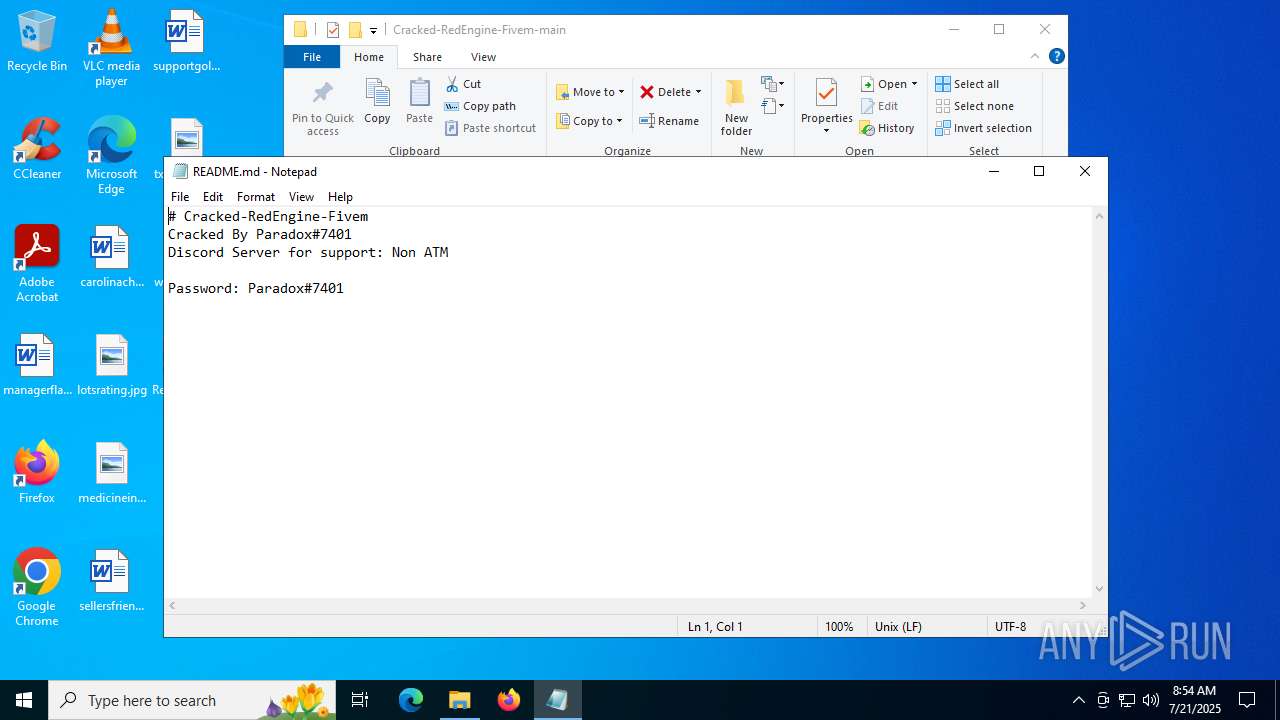
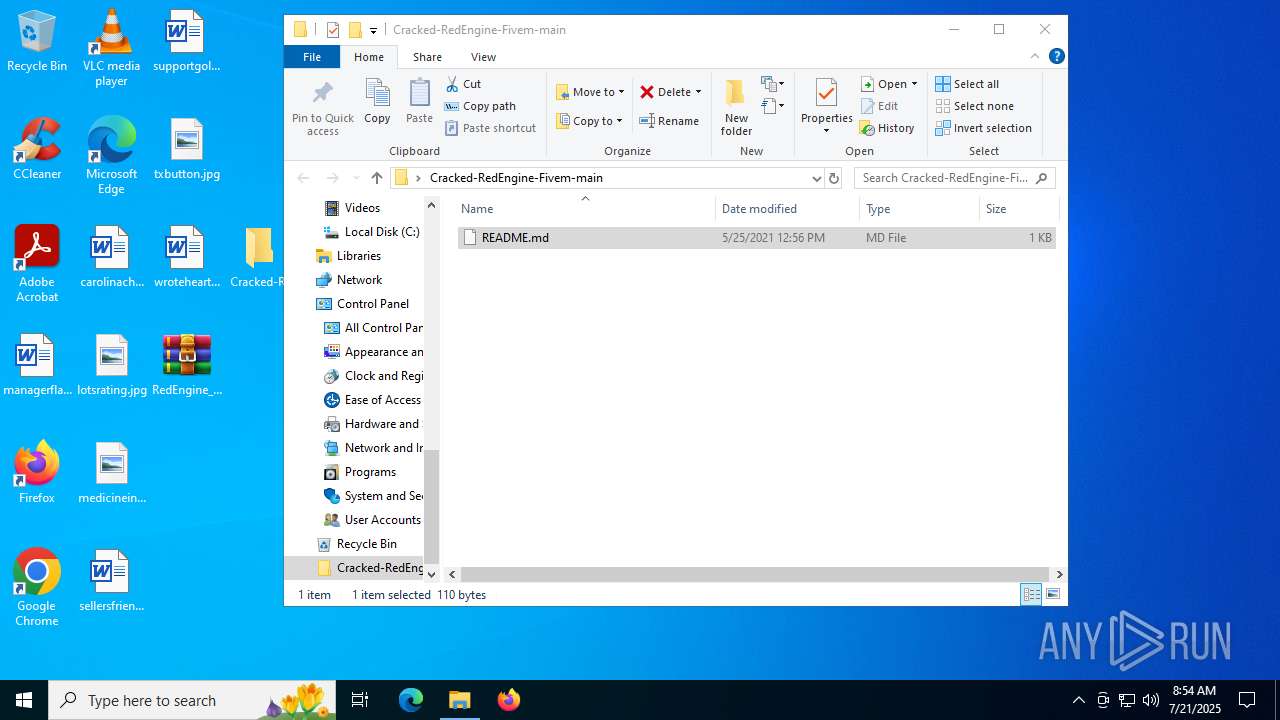
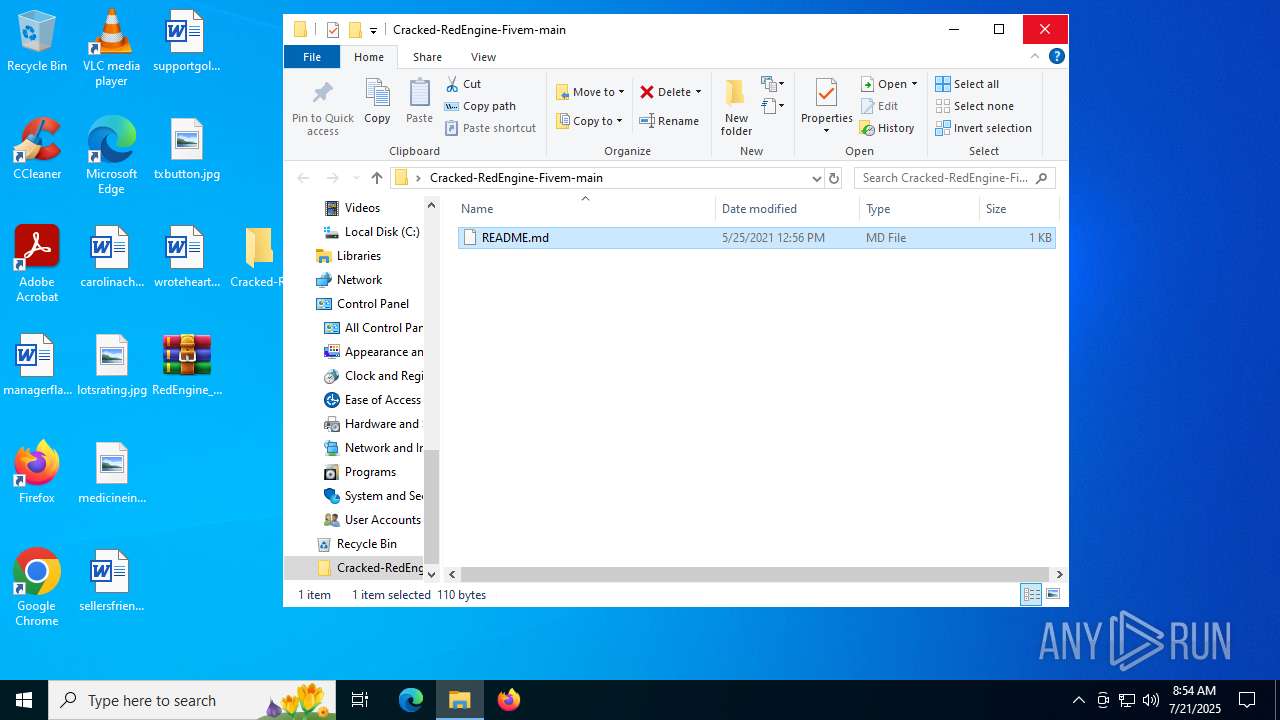
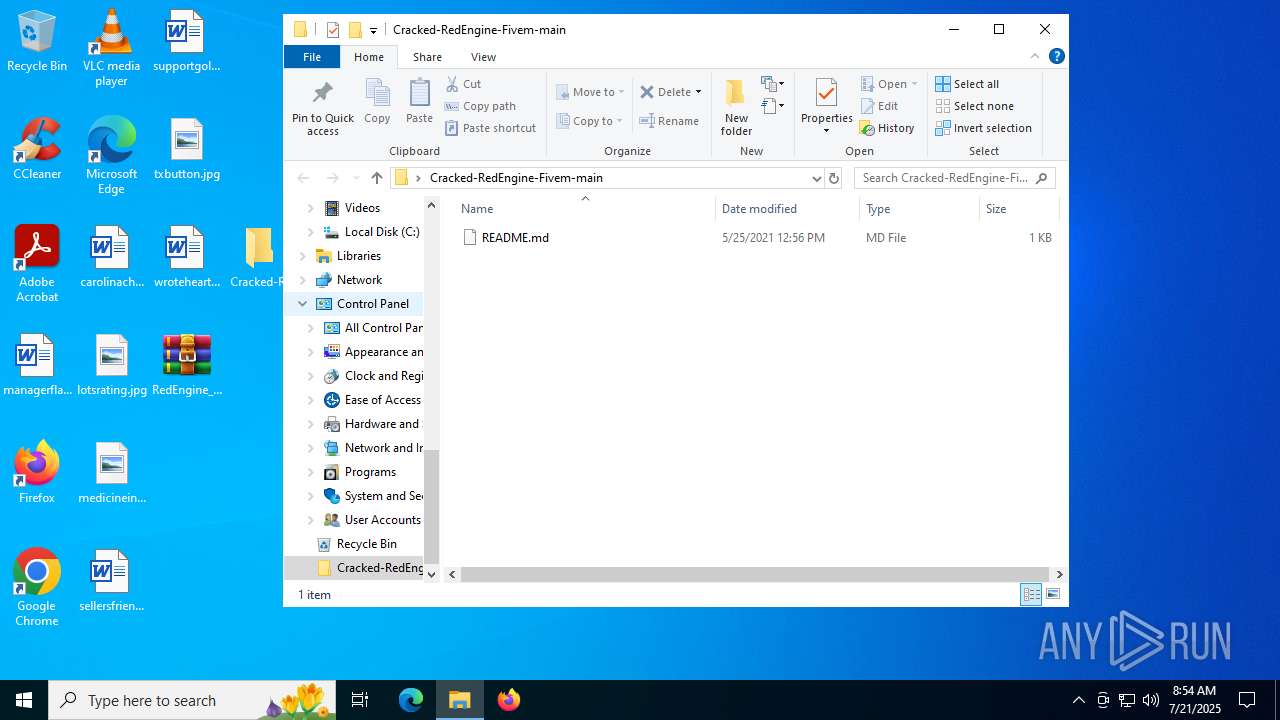
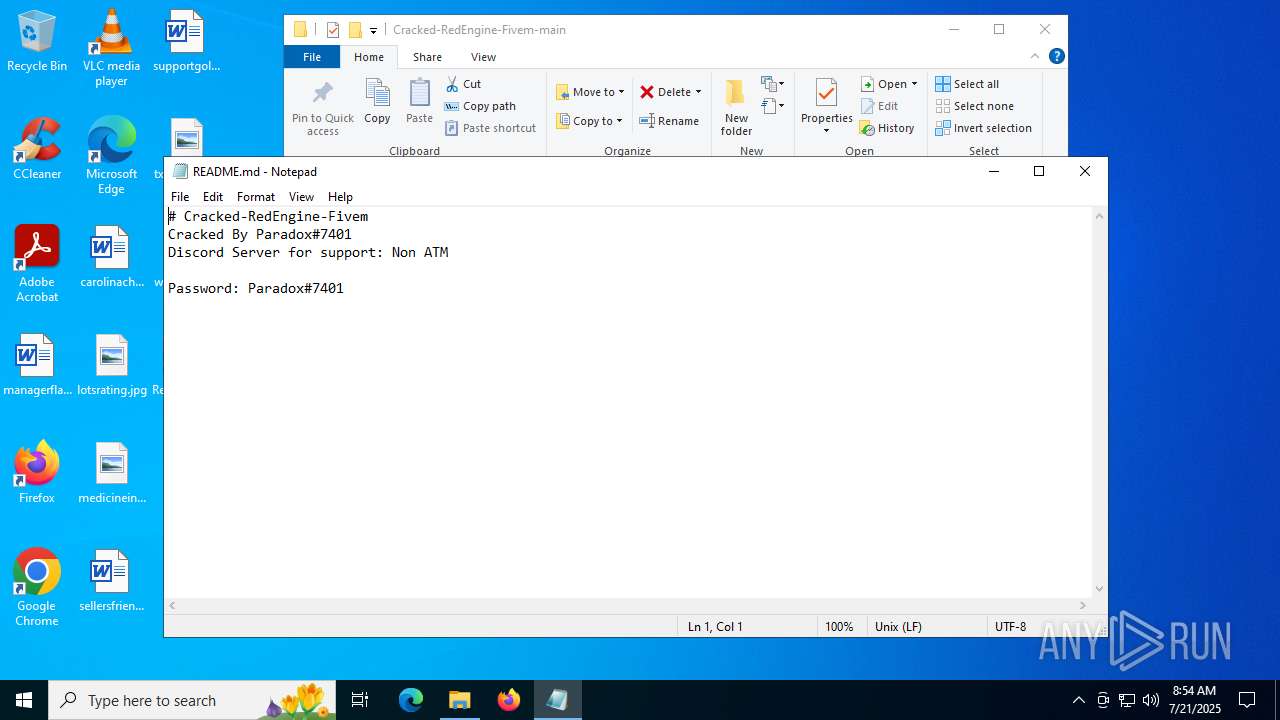
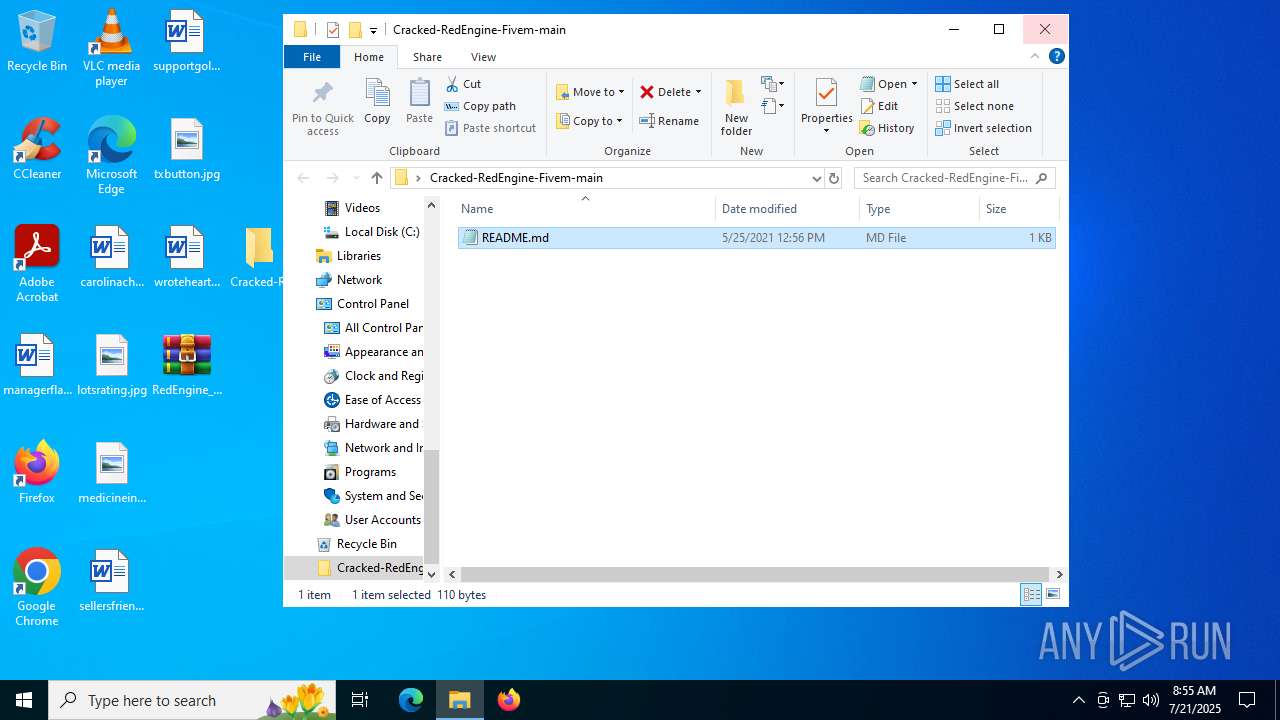
| 1472 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Cracked-RedEngine-Fivem-main\README.md | C:\Windows\System32\notepad.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Users\admin\Downloads\Annabelle.exe" | C:\Users\admin\Downloads\Annabelle.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Annabelle Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
20 533
Read events
20 159
Write events
374
Delete events
0
Modification events
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cracked-RedEngine-Fivem-main.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF420100005D0000000205000046020000 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
7
Suspicious files
692
Text files
142
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b6a11.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1b6a20.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b6a30.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1b6a3f.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1b6a4f.TMP | — | |
MD5:— | SHA256:— | |||
| 6756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1b6a5f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
159
DNS requests
130
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6452 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2192 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4912 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753563210&P2=404&P3=2&P4=Uf7ETo%2bq%2b4kaswAPeFY4qA%2fJVpXiY7EC1JVNirAUSFF%2bmqJ9b11CS%2bzUWqQkjqC2AxwrLcmxFoJo2cGo8W7X0A%3d%3d | unknown | — | — | whitelisted |
6452 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1753563210&P2=404&P3=2&P4=IphSm9hi5I3cDhTRSXyFfcJDJlQ3rLRYqY2CHRaVnJgWWi6Y1mUTs9trsaN8di%2bMDC3iN07p95kU%2bbNsqbdQPg%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7412 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753563210&P2=404&P3=2&P4=Uf7ETo%2bq%2b4kaswAPeFY4qA%2fJVpXiY7EC1JVNirAUSFF%2bmqJ9b11CS%2bzUWqQkjqC2AxwrLcmxFoJo2cGo8W7X0A%3d%3d | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753563210&P2=404&P3=2&P4=Uf7ETo%2bq%2b4kaswAPeFY4qA%2fJVpXiY7EC1JVNirAUSFF%2bmqJ9b11CS%2bzUWqQkjqC2AxwrLcmxFoJo2cGo8W7X0A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7032 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4912 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4912 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
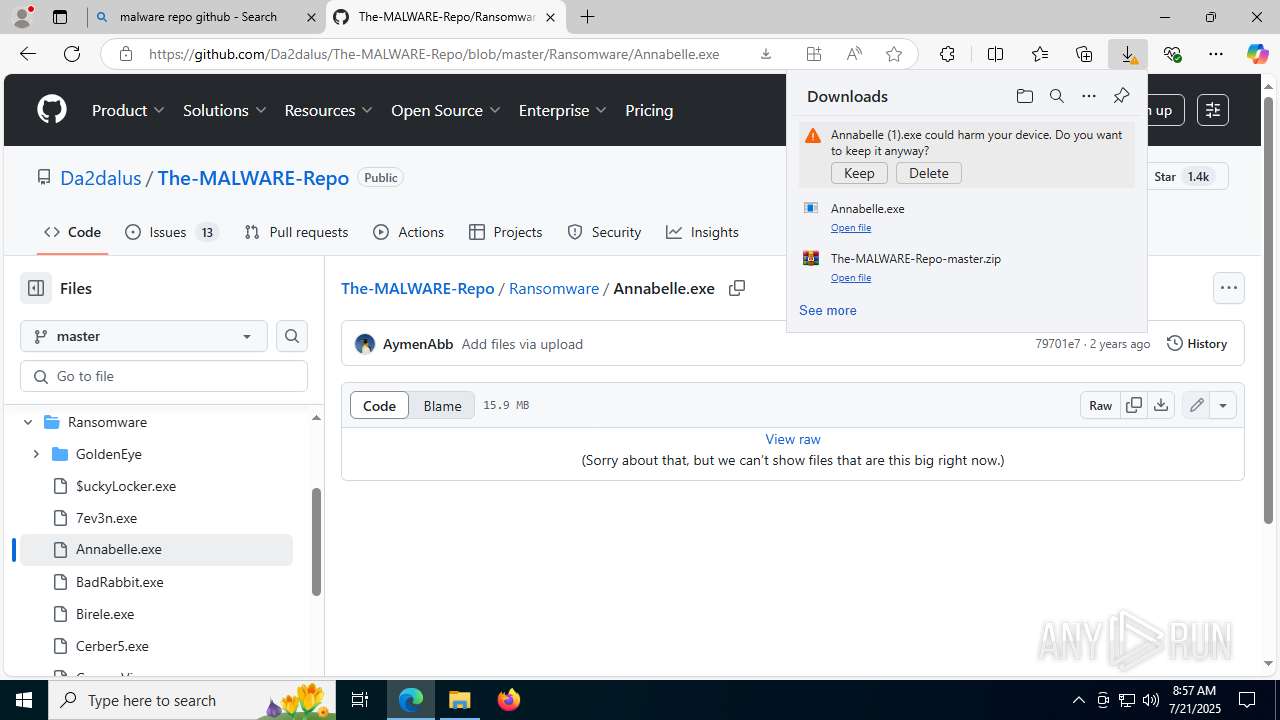
Threats
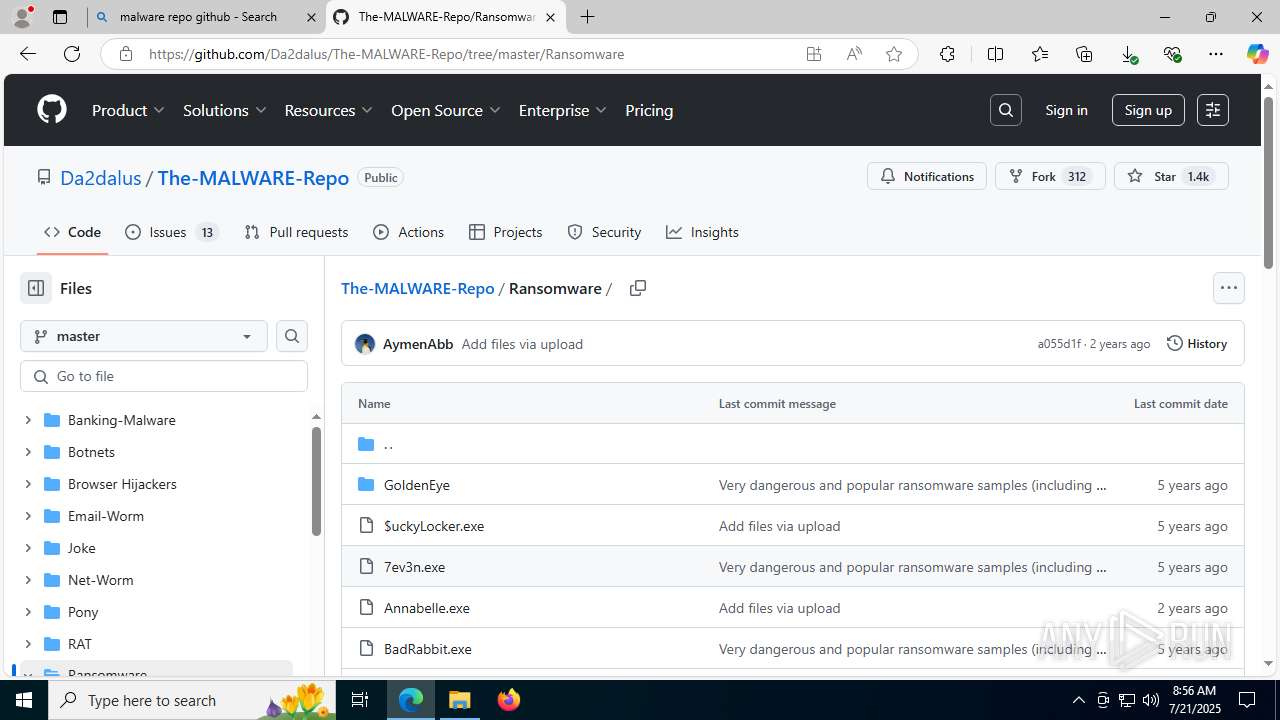
PID | Process | Class | Message |
|---|---|---|---|
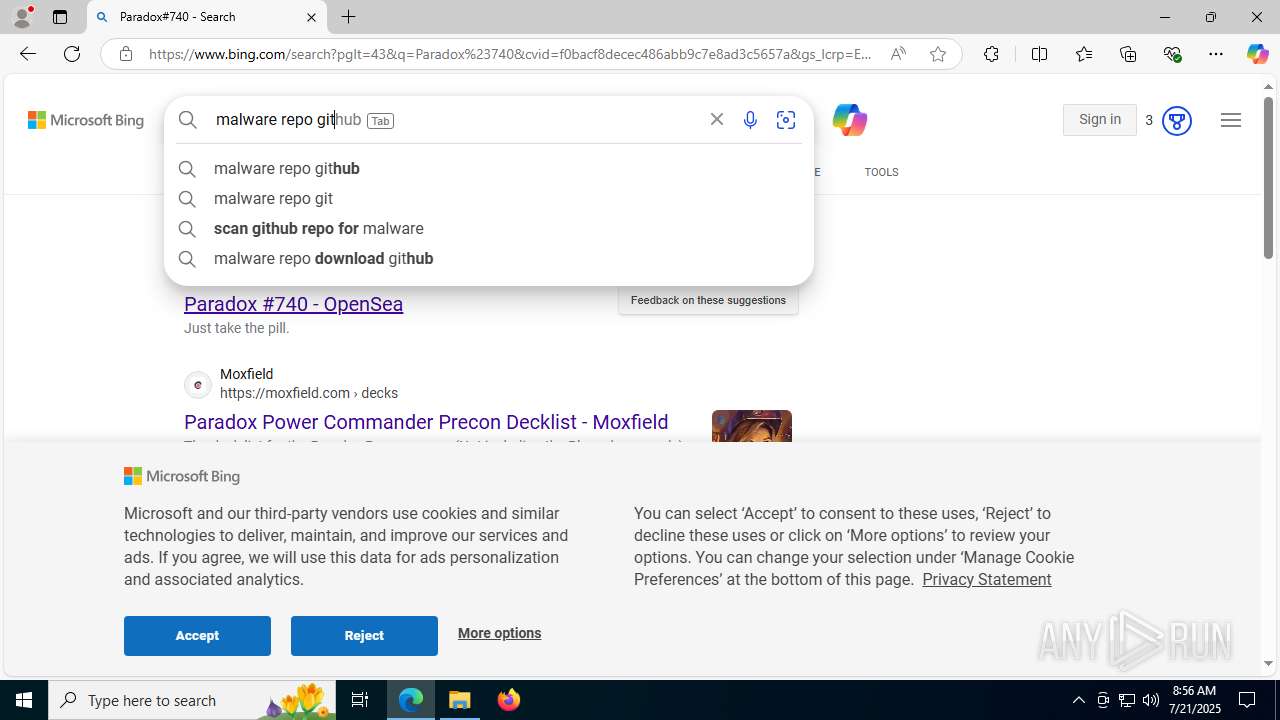
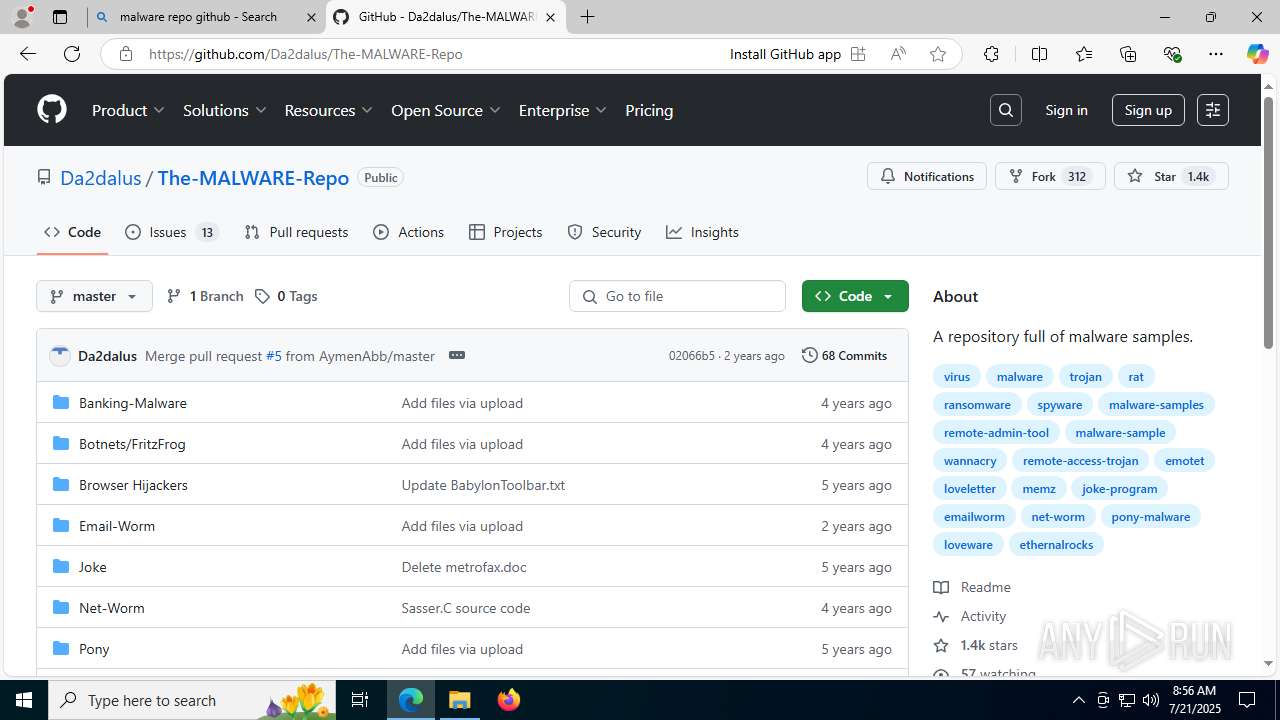
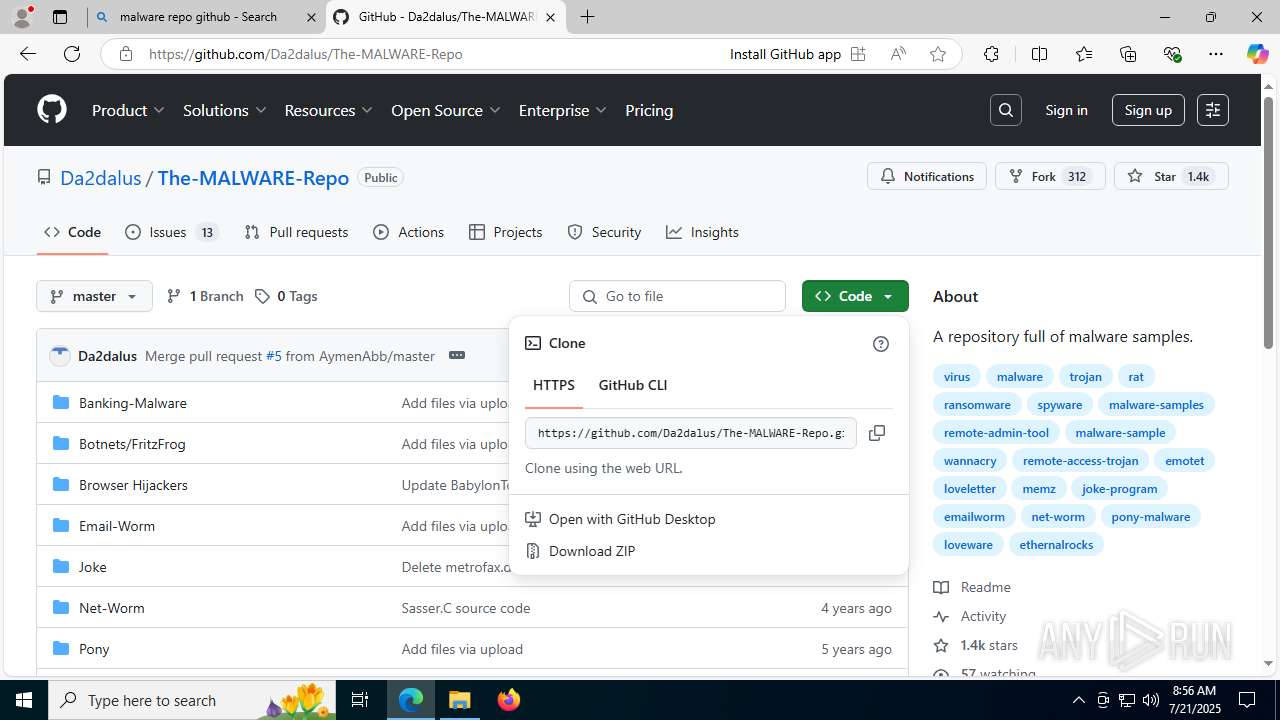
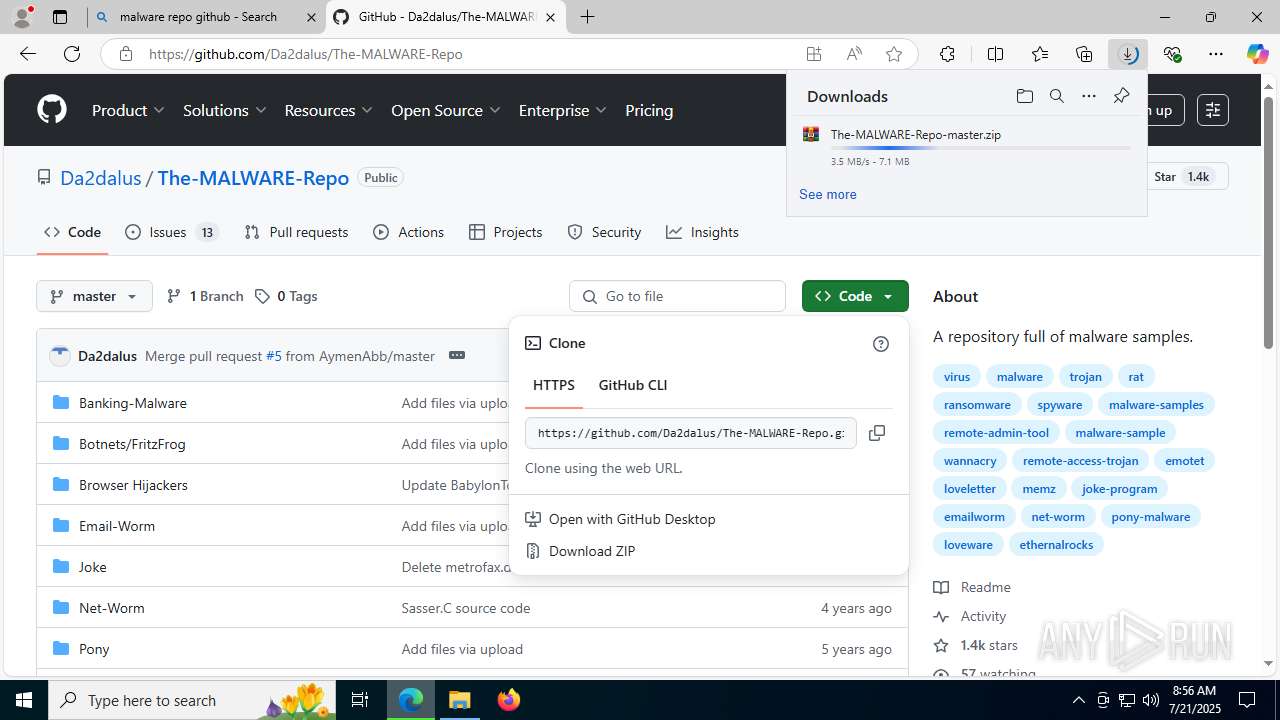
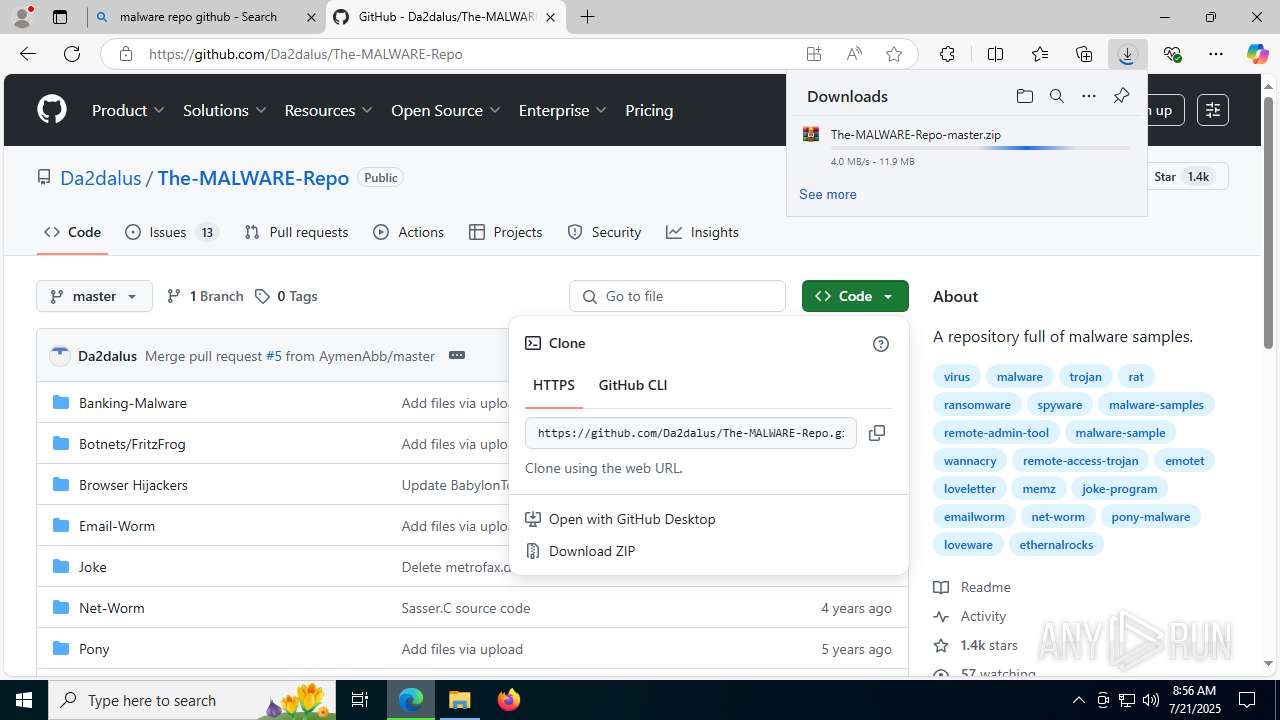
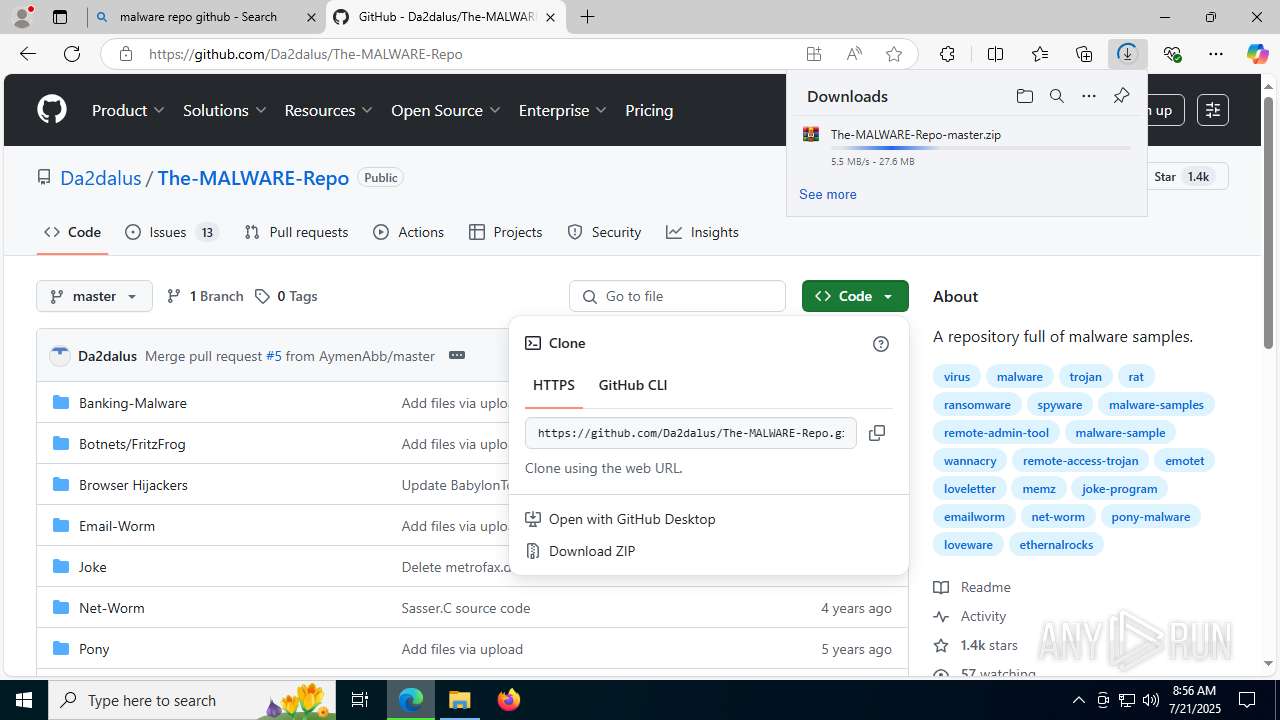
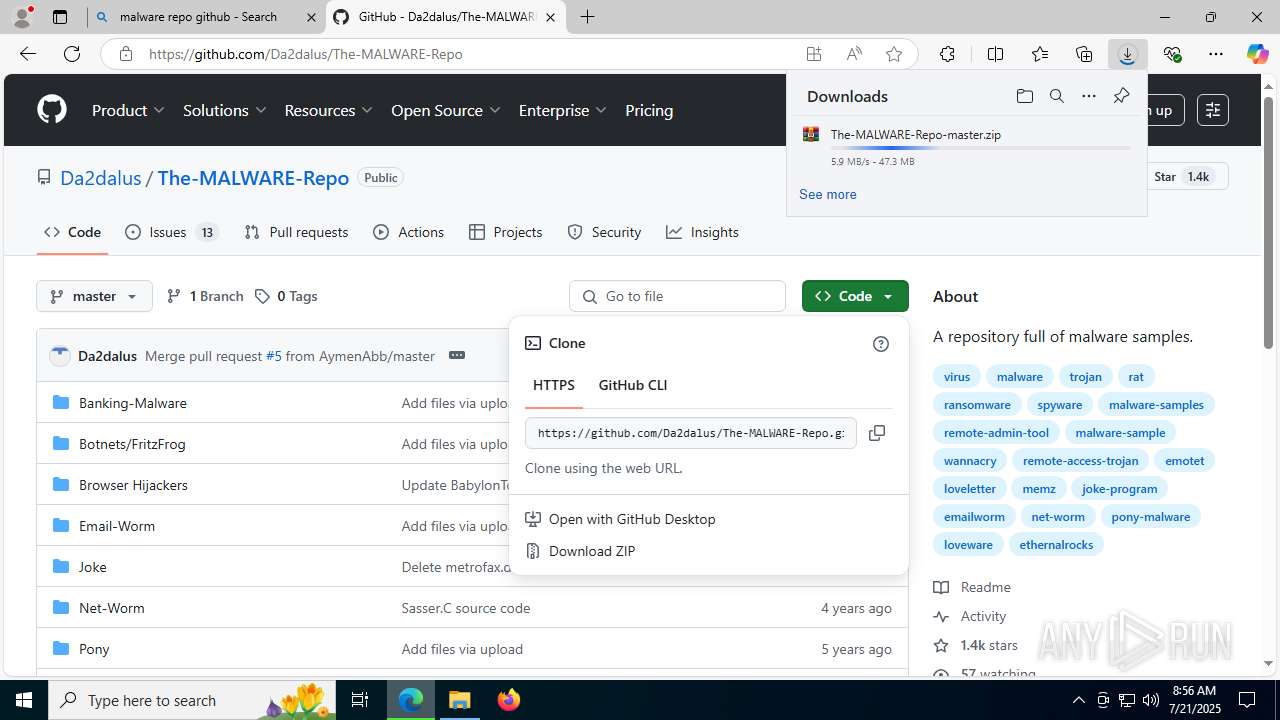
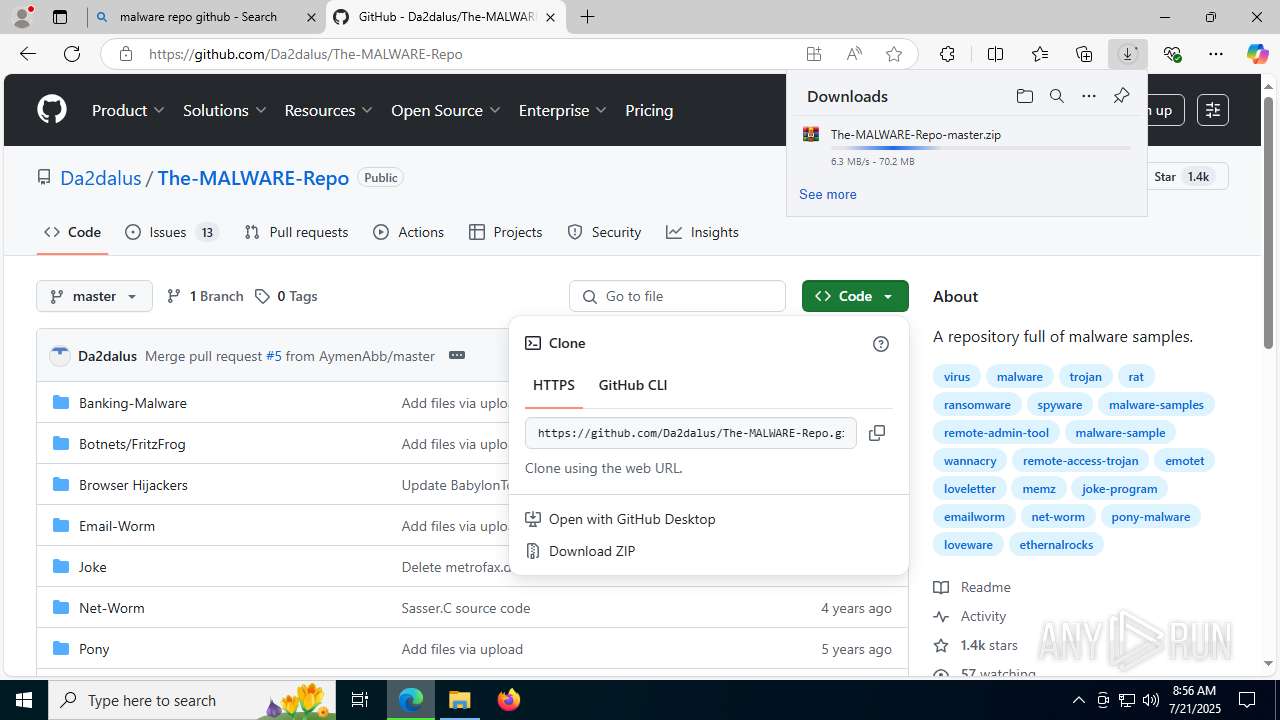
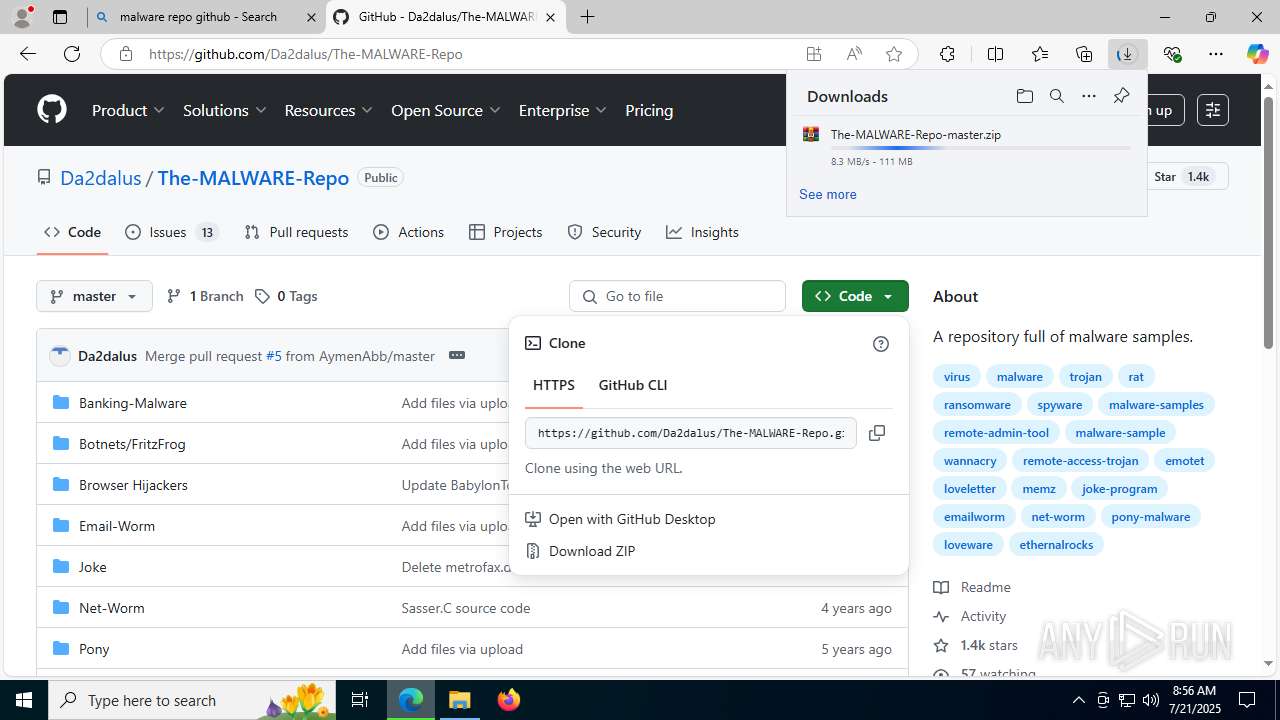
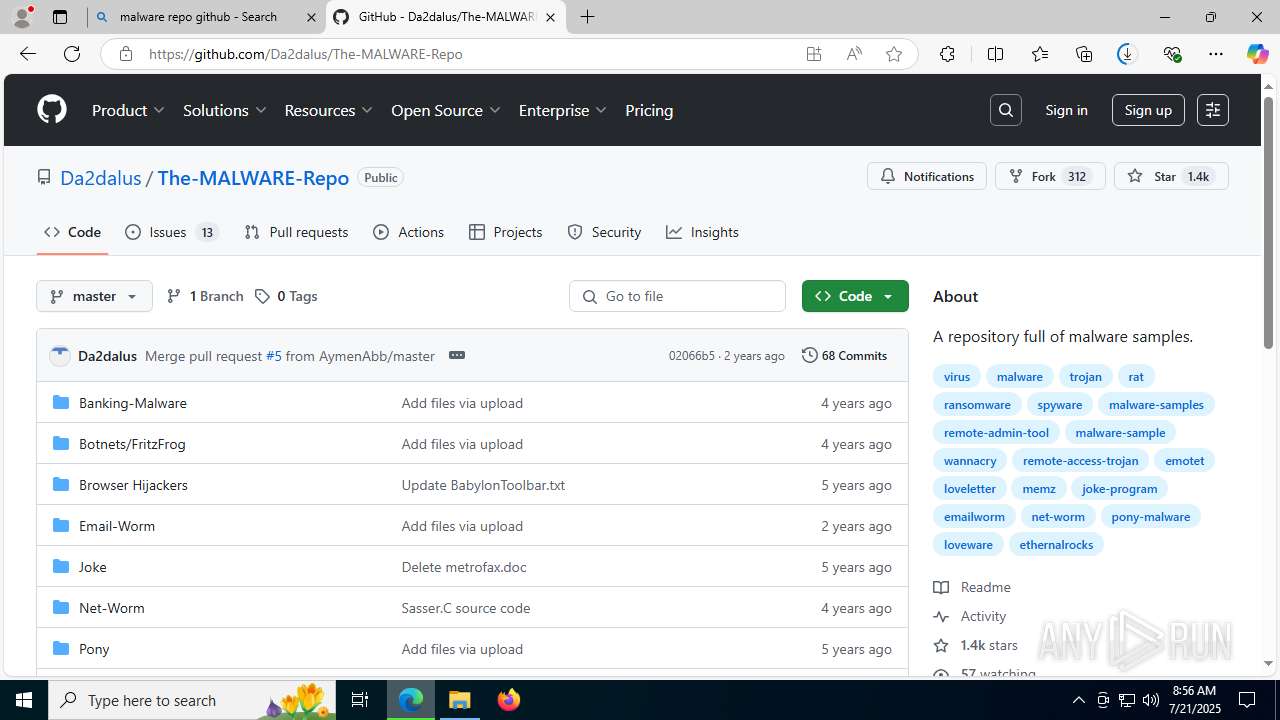
3972 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3972 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |