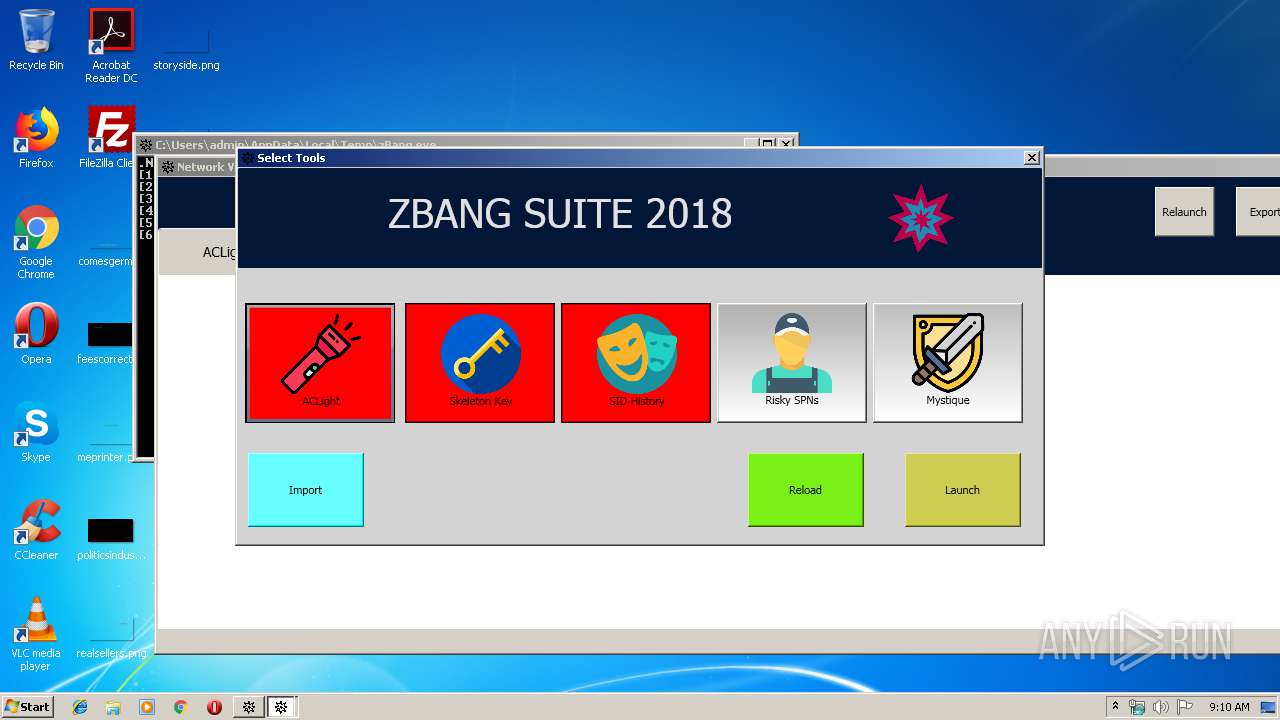
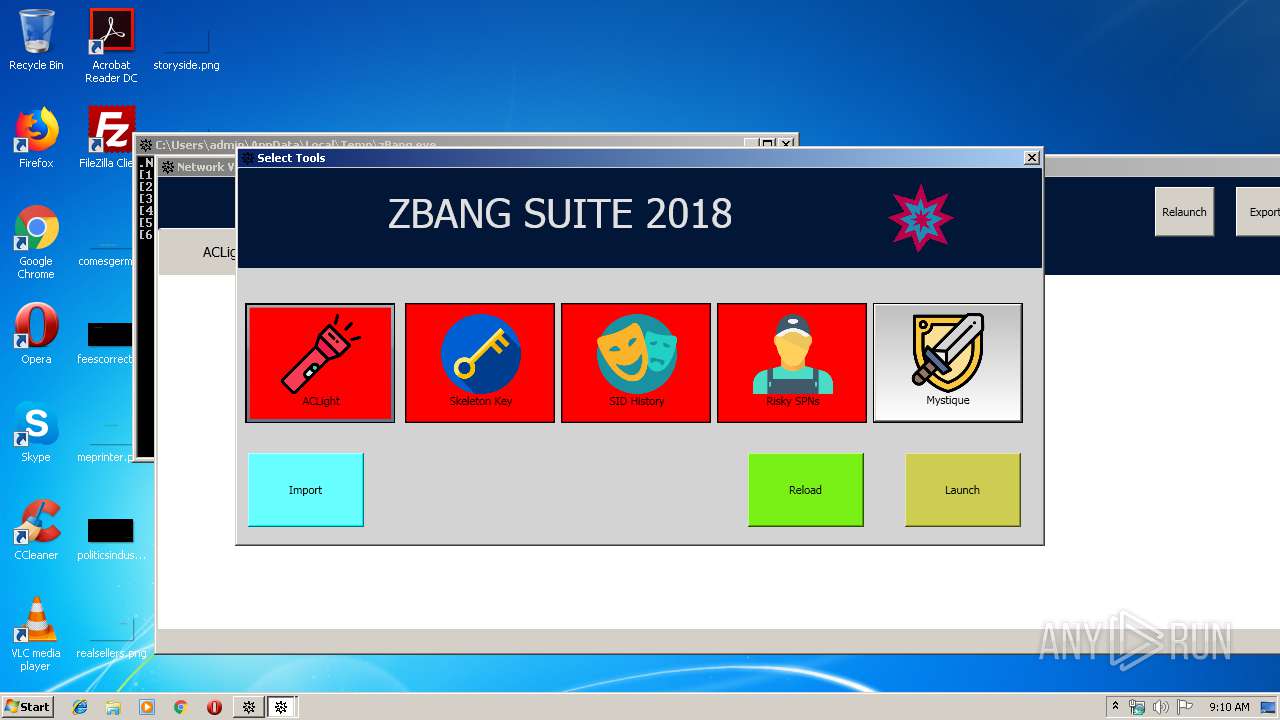
| File name: | zBang.exe |
| Full analysis: | https://app.any.run/tasks/9e8340bb-d5b3-4bbc-9d88-cbe0a3357551 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2019, 08:09:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4834485703E013286BF3489E10179839 |
| SHA1: | 906BF4C5DE97CB03D8F12D25E6C3494916918D57 |
| SHA256: | D47E989AE209685C51D05138FAF11CEFB97E32BF4E566807A1FFA9CBAB3EA37F |
| SSDEEP: | 196608:X+clAoz52j20mCRRvAV4cdOAlt+aXZ8lC0Lf:XDlAozi2bMvAqcdzltJZ8 |
MALICIOUS
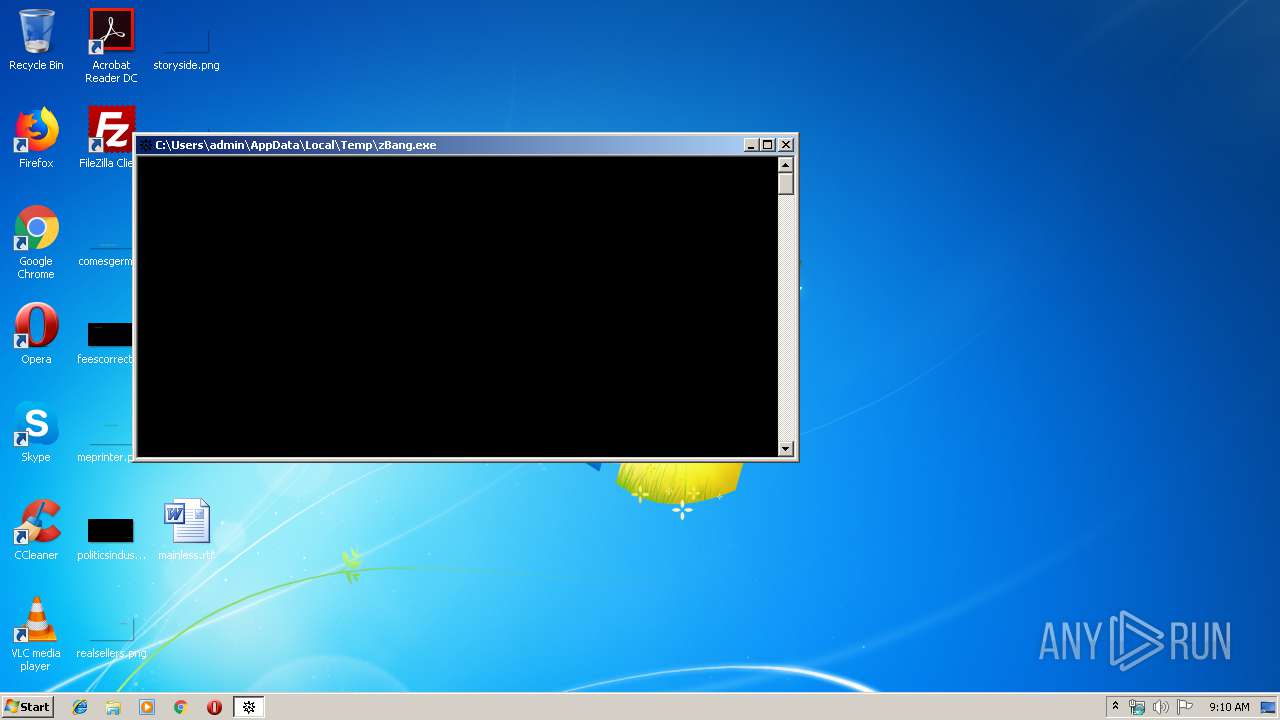
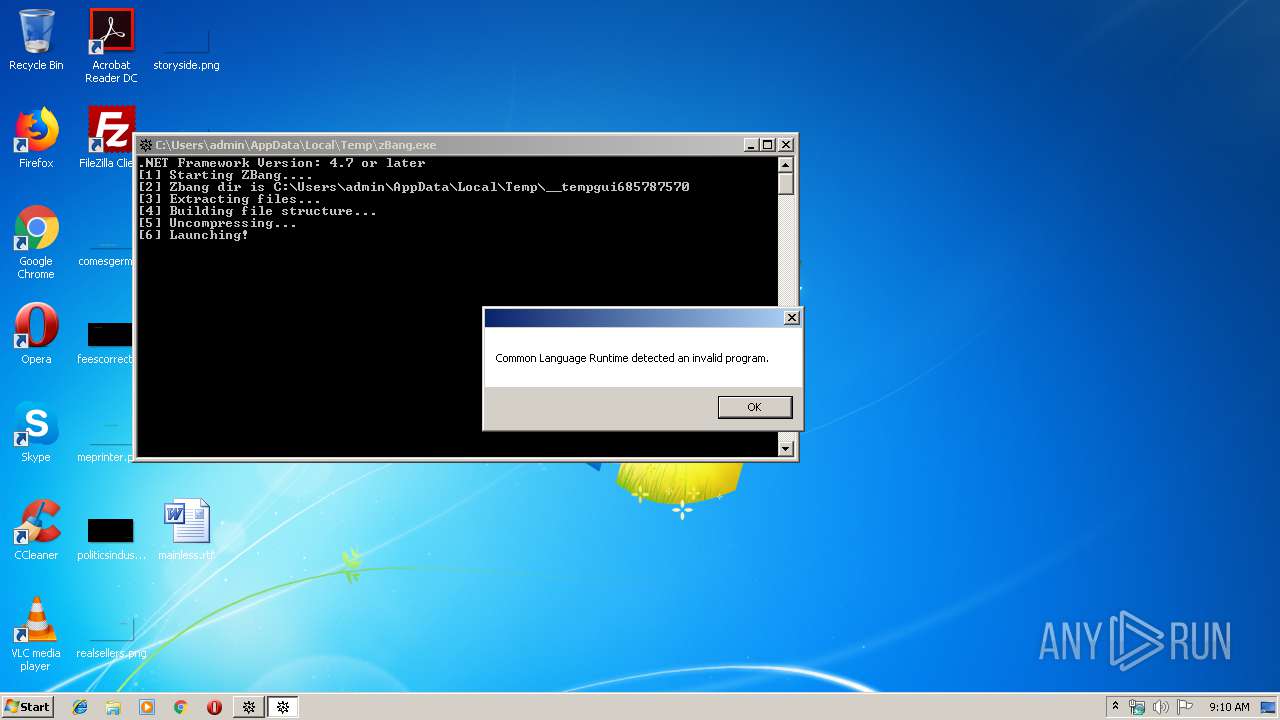
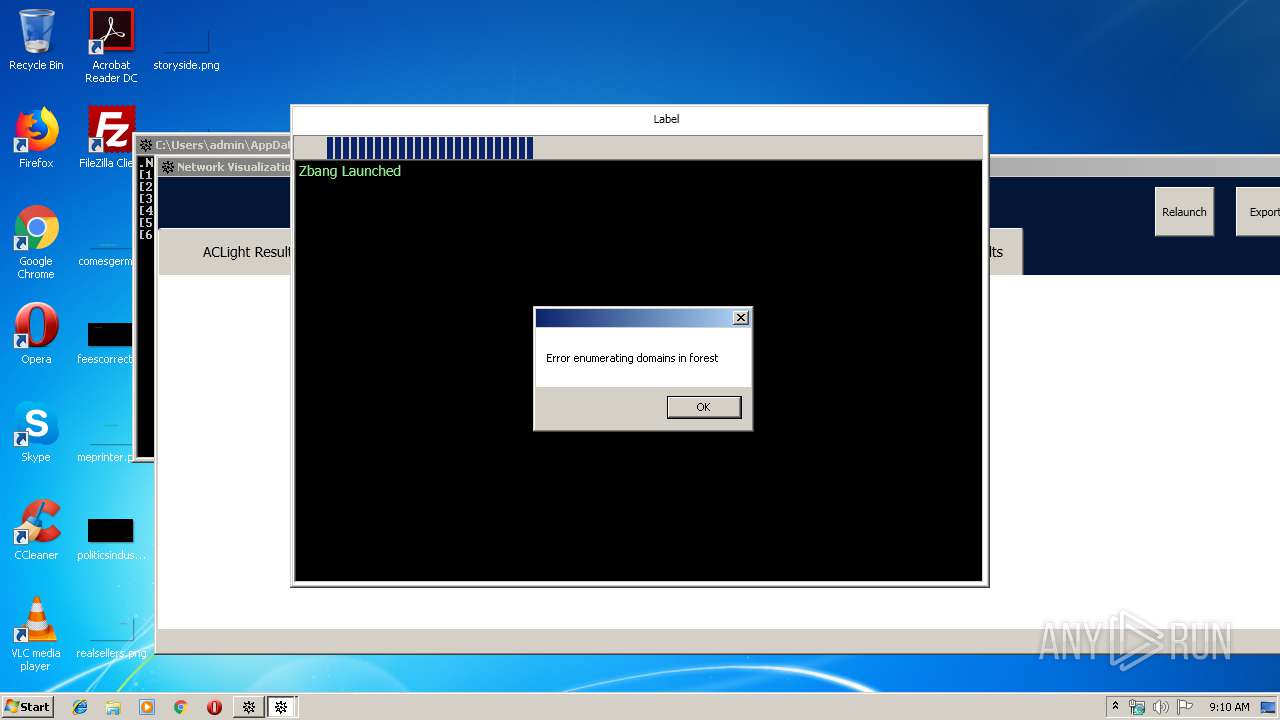
Application was dropped or rewritten from another process
- Graphviz4Net.WPF.Example.exe (PID: 3228)
Loads dropped or rewritten executable
- Graphviz4Net.WPF.Example.exe (PID: 3228)
SUSPICIOUS
Executable content was dropped or overwritten
- zBang.exe (PID: 3296)
Creates files in the user directory
- Powershell.exe (PID: 2676)
- powershell.exe (PID: 3196)
- Powershell.exe (PID: 3520)
- Powershell.exe (PID: 3960)
- Powershell.exe (PID: 2652)
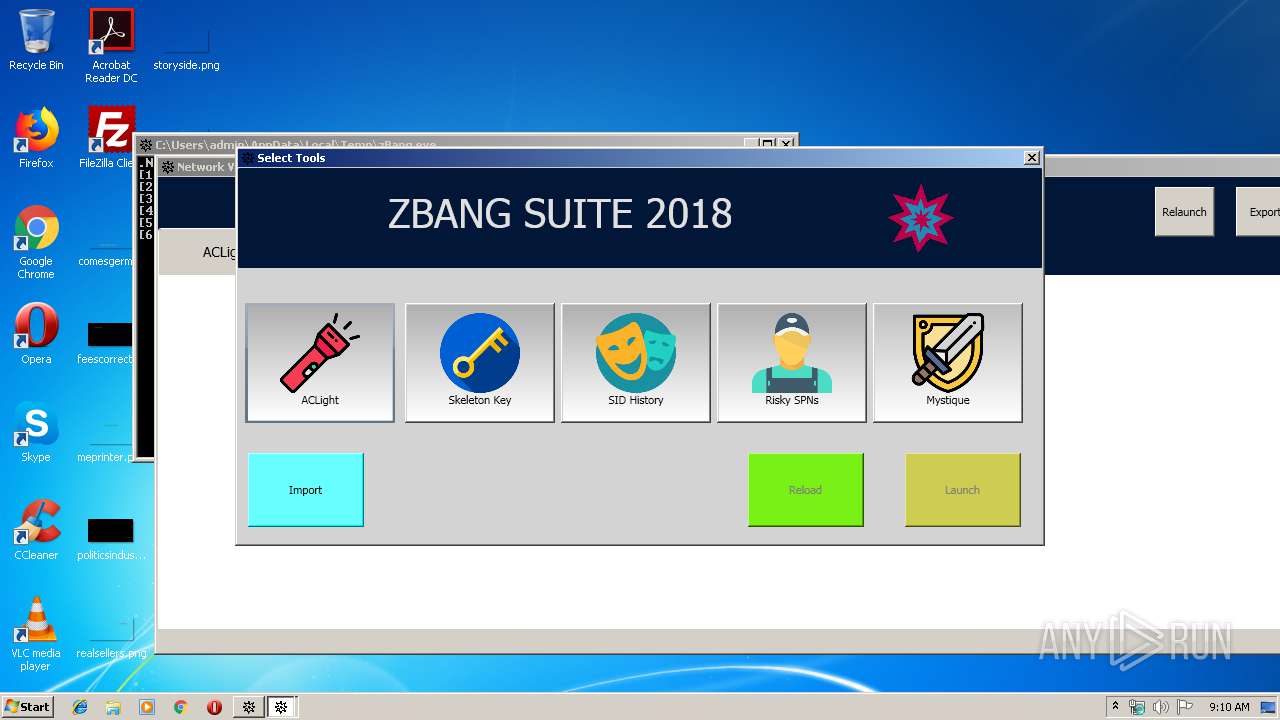
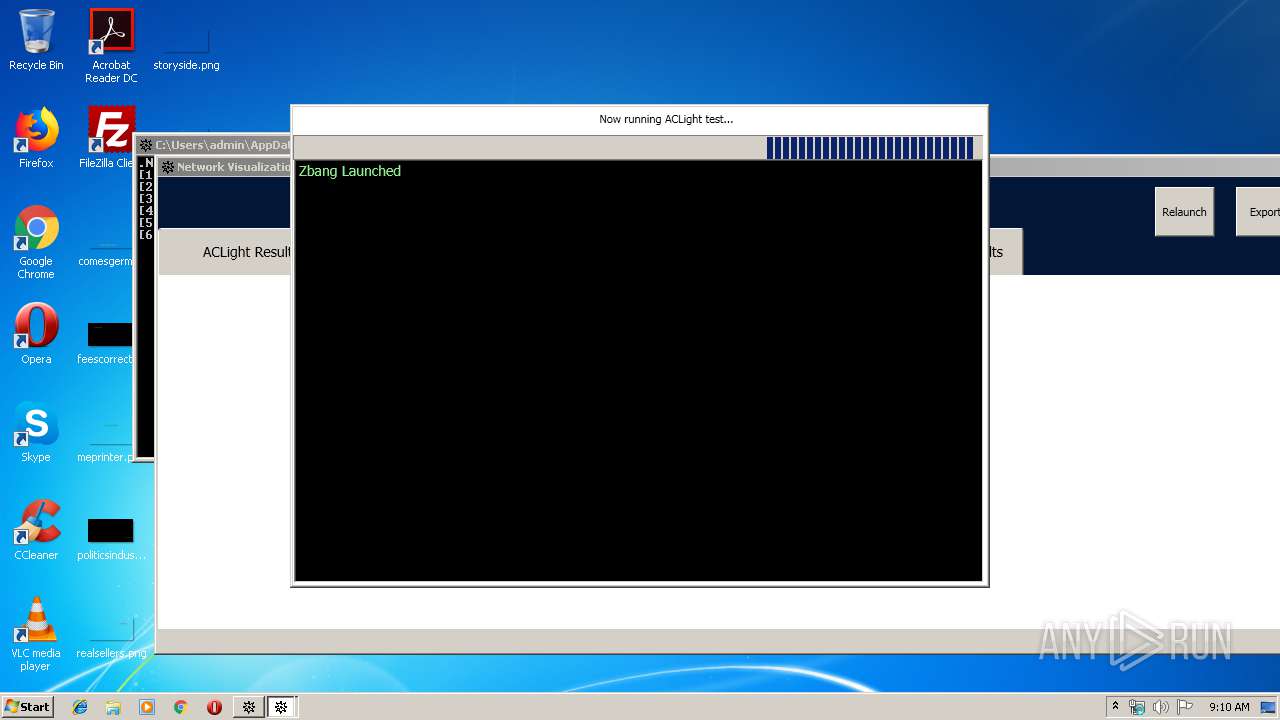
Executes PowerShell scripts
- Graphviz4Net.WPF.Example.exe (PID: 3228)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:22 17:24:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 8801792 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x866cba |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Aetos |
| FileDescription: | ZbangGui |
| FileVersion: | 1.0.0.0 |
| InternalName: | ZbangGui.exe |
| LegalCopyright: | Copyright © Aetos 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | ZbangGui.exe |
| ProductName: | ZbangGui |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 22-Nov-2018 16:24:38 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | Aetos |
| FileDescription: | ZbangGui |
| FileVersion: | 1.0.0.0 |
| InternalName: | ZbangGui.exe |
| LegalCopyright: | Copyright © Aetos 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | ZbangGui.exe |
| ProductName: | ZbangGui |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Nov-2018 16:24:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00864CC0 | 0x00864E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99876 |
.rsrc | 0x00868000 | 0x000019DC | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.42385 |
.reloc | 0x0086A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.51664 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2652 | "Powershell.exe" -noprofile -ExecutionPolicy Bypass -command "& { ./Mystique.ps1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | — | Graphviz4Net.WPF.Example.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
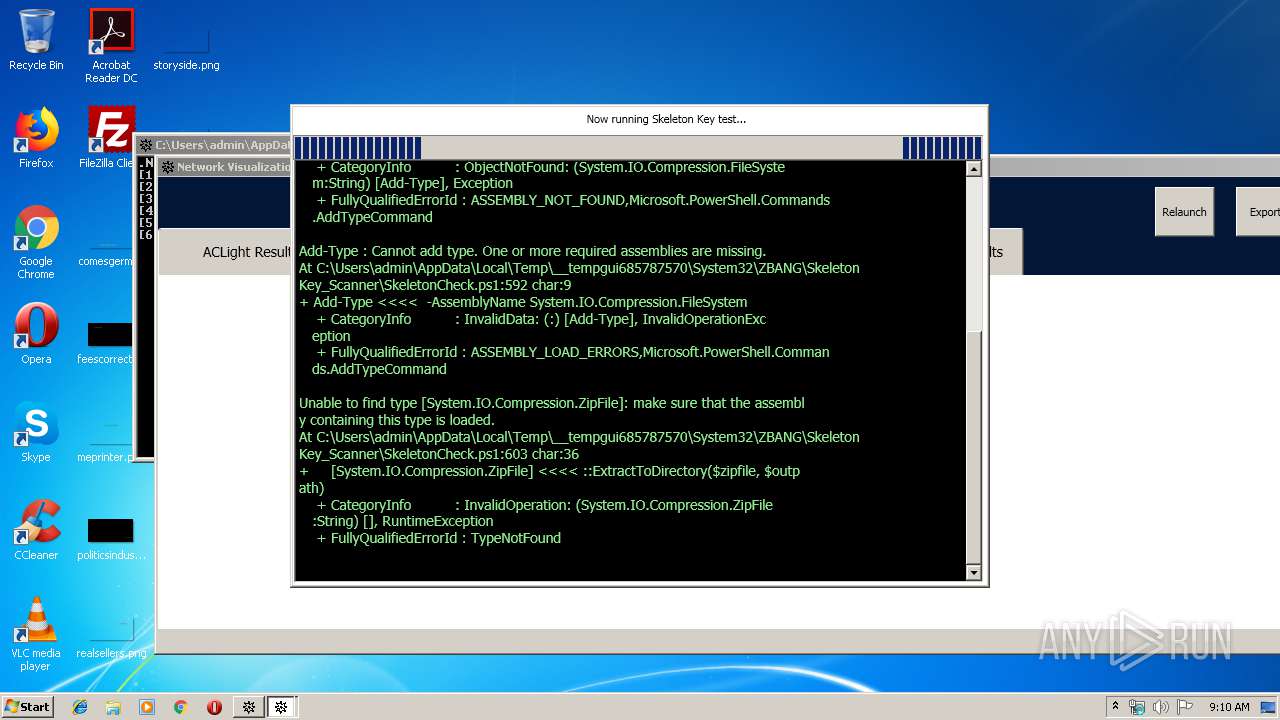
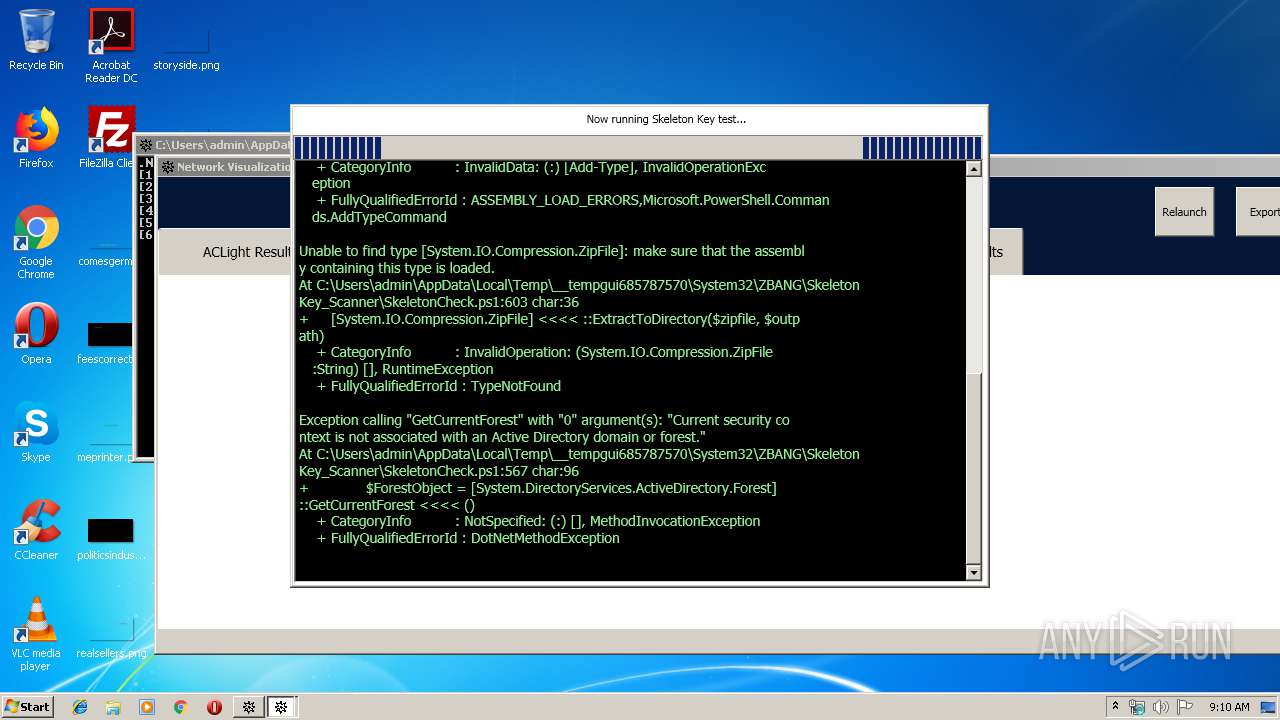
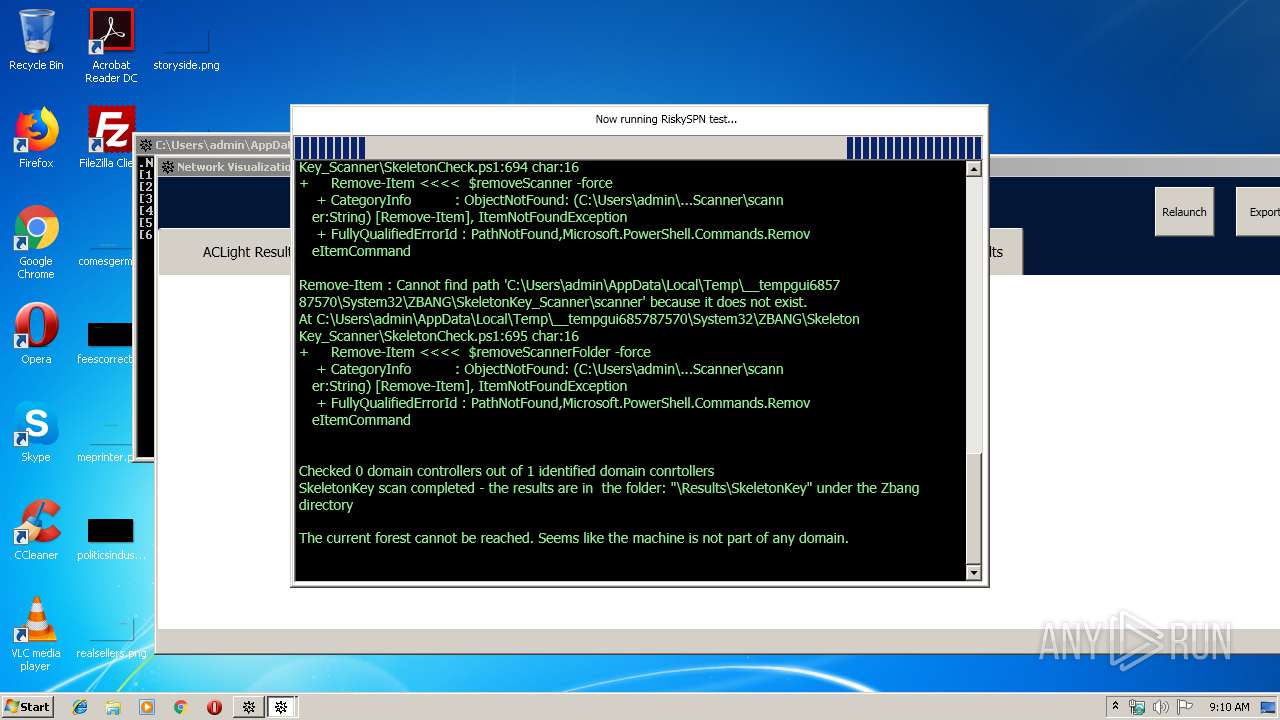
| 2676 | "Powershell.exe" -ExecutionPolicy bypass -noprofile -command "./SkeletonCheck.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | — | Graphviz4Net.WPF.Example.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | "powershell.exe" -ExecutionPolicy Bypass -noprofile -command "Import-Module './ACLight.ps1' -force ; Start-ACLsAnalysis" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Graphviz4Net.WPF.Example.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3228 | "Graphviz4Net.WPF.Example.exe" | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\Graphviz4Net.WPF.Example.exe | — | zBang.exe | |||||||||||
User: admin Company: CyberArk Integrity Level: MEDIUM Description: CyberArk Labs Zbang Tools Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\zBang.exe" | C:\Users\admin\AppData\Local\Temp\zBang.exe | explorer.exe | ||||||||||||
User: admin Company: Aetos Integrity Level: MEDIUM Description: ZbangGui Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
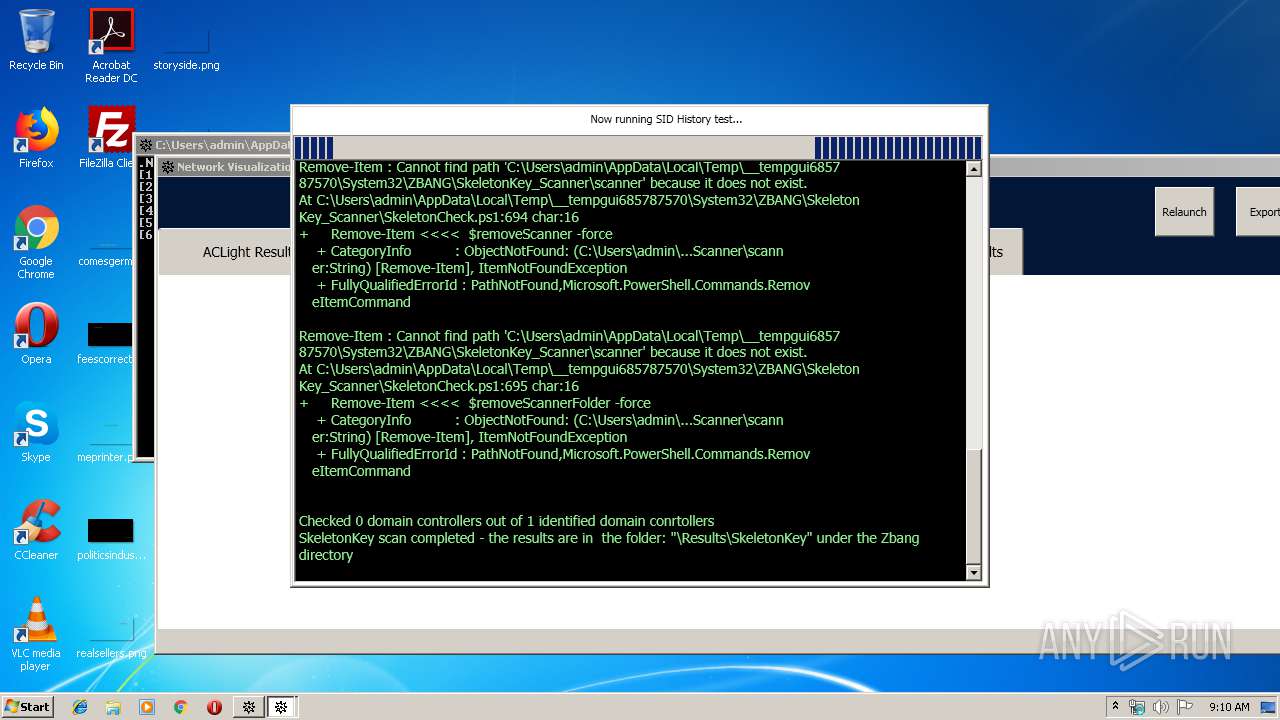
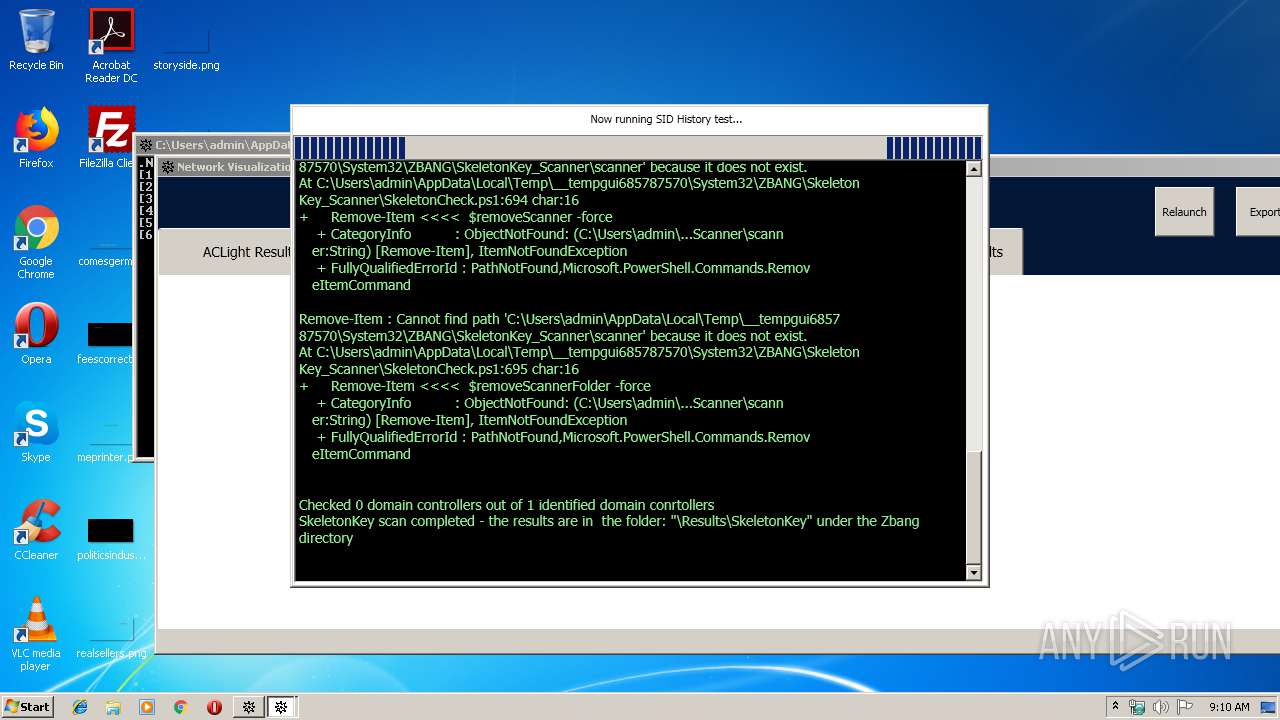
| 3520 | "Powershell.exe" -ExecutionPolicy Bypass -noprofile -Command "& { ./SIDHistory_Scanner.ps1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | — | Graphviz4Net.WPF.Example.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
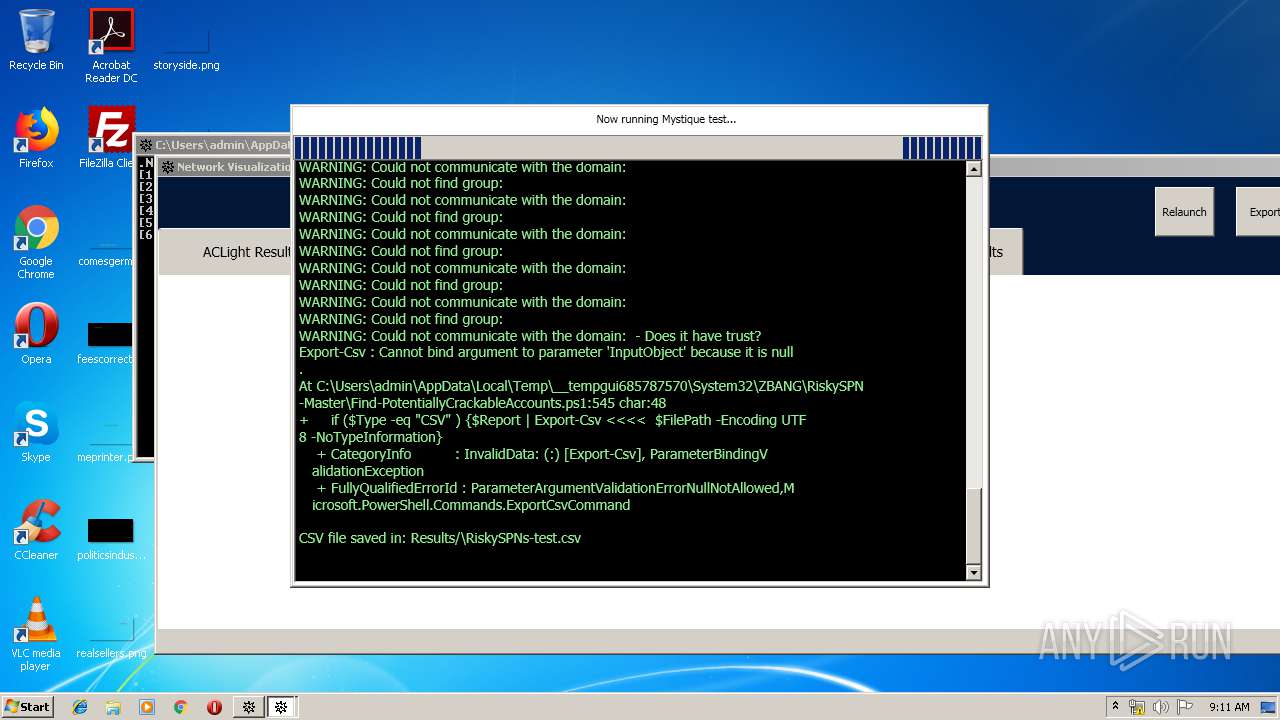
| 3960 | "Powershell.exe" -ExecutionPolicy Bypass -noprofile -command "& { ./Find-PotentiallyCrackableAccounts.ps1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | — | Graphviz4Net.WPF.Example.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 201
Read events
925
Write events
276
Delete events
0
Modification events
| (PID) Process: | (3228) Graphviz4Net.WPF.Example.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Graphviz4Net.WPF.Example.exe | |||
| (PID) Process: | (3196) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2676) Powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3520) Powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3960) Powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2652) Powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
19
Suspicious files
12
Text files
160
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\version.zip | compressed | |
MD5:— | SHA256:— | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\Graphviz4Net.WPF.Example.exe | executable | |
MD5:— | SHA256:— | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\gvc.dll | executable | |
MD5:3A152C05B0309FC8469C729E00C29EB0 | SHA256:7FD2257572E29C1B7B9234EFC1FFC6D32015B66BD92ADAD2853CDEB13D5F3986 | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\Graphviz4Net.dll | executable | |
MD5:C1E0D583ACEE09F2DD82F1C788194408 | SHA256:76EBFD25FAEF7609C3117F466002B7717958FB16B05E10C7E04413D6EE378223 | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\config6 | text | |
MD5:7CB0D8D801C1899D041CFC8FF26E9171 | SHA256:2DABDAAF36E4A9B8CD16542919E086D59CEE7A1739EED22E769193FB4258C896 | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\dot.exe | executable | |
MD5:1C95AC655DD413B3ECDED4159C1476F4 | SHA256:CFABED461F90A4CAB9DD545F2D0AD37FAB3DD220B546DBF4552F56ACA3193D75 | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\gvplugin_core.dll | executable | |
MD5:8A1EDD2FE54B8E3910FD7D990D46331A | SHA256:3450405A7CF66041A12EF1E508B23B0F4D89058D3543EA14E2B1FCFA41BA322D | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\cdt.dll | executable | |
MD5:6C146216C545E99453FD93D0C4D42D07 | SHA256:7DE4291A7D74353E2466EA819003F90D8C691B83BF733BAD46785BCEFA9C1CAC | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\release\bin\gvplugin_dot_layout.dll | executable | |
MD5:A889D031B9FCE089BD7215FC92276EB2 | SHA256:BF8FA329C5D2108EB3728208AFCCE34B760E1062064F86E636076693757081D4 | |||
| 3296 | zBang.exe | C:\Users\admin\AppData\Local\Temp\__tempgui685787570\System32\bin\release\Graphviz4Net.WPF.dll | executable | |
MD5:B43C6A72D5D46E01945A8957F15E109F | SHA256:1E044E8A1BC6093BE2A56B5A4F1C182A0BEE3B48A2B23598411A6D30FA425308 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report