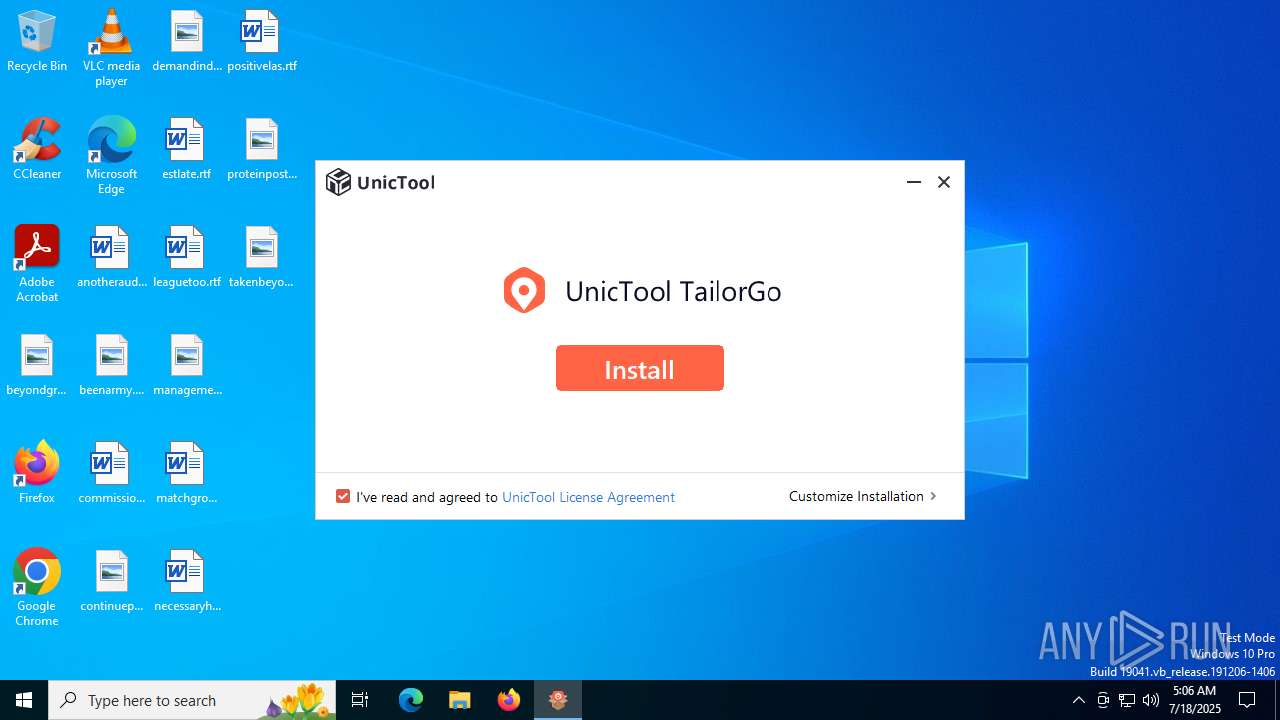
| File name: | unictool-tailorgo_setup.exe |
| Full analysis: | https://app.any.run/tasks/1d59d250-a9fb-4101-b3f2-9e5842463cf3 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 05:06:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 25ECCF99A8E220C3F2437B6557A921D4 |
| SHA1: | 11B30C1D06B61D65213C8019656C6A5EAA778977 |
| SHA256: | D47AD163A5DD8E7A44D3C7F6A32300964214E9819D8FA8FDDACA073CB308A916 |
| SSDEEP: | 98304:2LSdRMQm6oUK3CkTjYkInuBcGh7lRxRNeCdeDPgZg/Yjqqk6hsNO8liVT9NoDep5:g48 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- imyfone-download.exe (PID: 2120)
- imyfone-download.tmp (PID: 4552)
Reads the Windows owner or organization settings
- imyfone-download.tmp (PID: 4552)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6256)
- cmd.exe (PID: 1604)
- cmd.exe (PID: 5240)
- cmd.exe (PID: 3556)
Starts CMD.EXE for commands execution
- imyfone-download.tmp (PID: 4552)
Drops 7-zip archiver for unpacking
- imyfone-download.tmp (PID: 4552)
There is functionality for VM detection VMWare (YARA)
- imyfone-download.tmp (PID: 4552)
Drops a system driver (possible attempt to evade defenses)
- imyfone-download.tmp (PID: 4552)
The process drops C-runtime libraries
- imyfone-download.tmp (PID: 4552)
Reads security settings of Internet Explorer
- unictool-tailorgo_setup.exe (PID: 4544)
Process drops legitimate windows executable
- imyfone-download.tmp (PID: 4552)
INFO
Creates files in the program directory
- unictool-tailorgo_setup.exe (PID: 4544)
- imyfone-download.tmp (PID: 4552)
Reads the computer name
- unictool-tailorgo_setup.exe (PID: 4544)
- imyfone-download.tmp (PID: 4552)
- identity_helper.exe (PID: 2064)
- identity_helper.exe (PID: 6832)
Checks supported languages
- SearchApp.exe (PID: 5328)
- unictool-tailorgo_setup.exe (PID: 4544)
- imyfone-download.tmp (PID: 4552)
- imyfone-download.exe (PID: 2120)
- identity_helper.exe (PID: 2064)
- identity_helper.exe (PID: 6832)
Create files in a temporary directory
- imyfone-download.exe (PID: 2120)
- imyfone-download.tmp (PID: 4552)
The sample compiled with english language support
- unictool-tailorgo_setup.exe (PID: 4544)
- imyfone-download.tmp (PID: 4552)
Checks proxy server information
- unictool-tailorgo_setup.exe (PID: 4544)
- slui.exe (PID: 4172)
Reads product name
- unictool-tailorgo_setup.exe (PID: 4544)
Reads Environment values
- unictool-tailorgo_setup.exe (PID: 4544)
- identity_helper.exe (PID: 2064)
- identity_helper.exe (PID: 6832)
Reads the machine GUID from the registry
- unictool-tailorgo_setup.exe (PID: 4544)
- SearchApp.exe (PID: 5328)
Reads the software policy settings
- unictool-tailorgo_setup.exe (PID: 4544)
- SearchApp.exe (PID: 5328)
- slui.exe (PID: 4172)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
The sample compiled with arabic language support
- imyfone-download.tmp (PID: 4552)
Compiled with Borland Delphi (YARA)
- imyfone-download.exe (PID: 2120)
- imyfone-download.tmp (PID: 4552)
The sample compiled with chinese language support
- imyfone-download.tmp (PID: 4552)
Detects InnoSetup installer (YARA)
- imyfone-download.tmp (PID: 4552)
- imyfone-download.exe (PID: 2120)
Manual execution by a user
- msedge.exe (PID: 4948)
Application launched itself
- msedge.exe (PID: 4948)
- msedge.exe (PID: 3832)
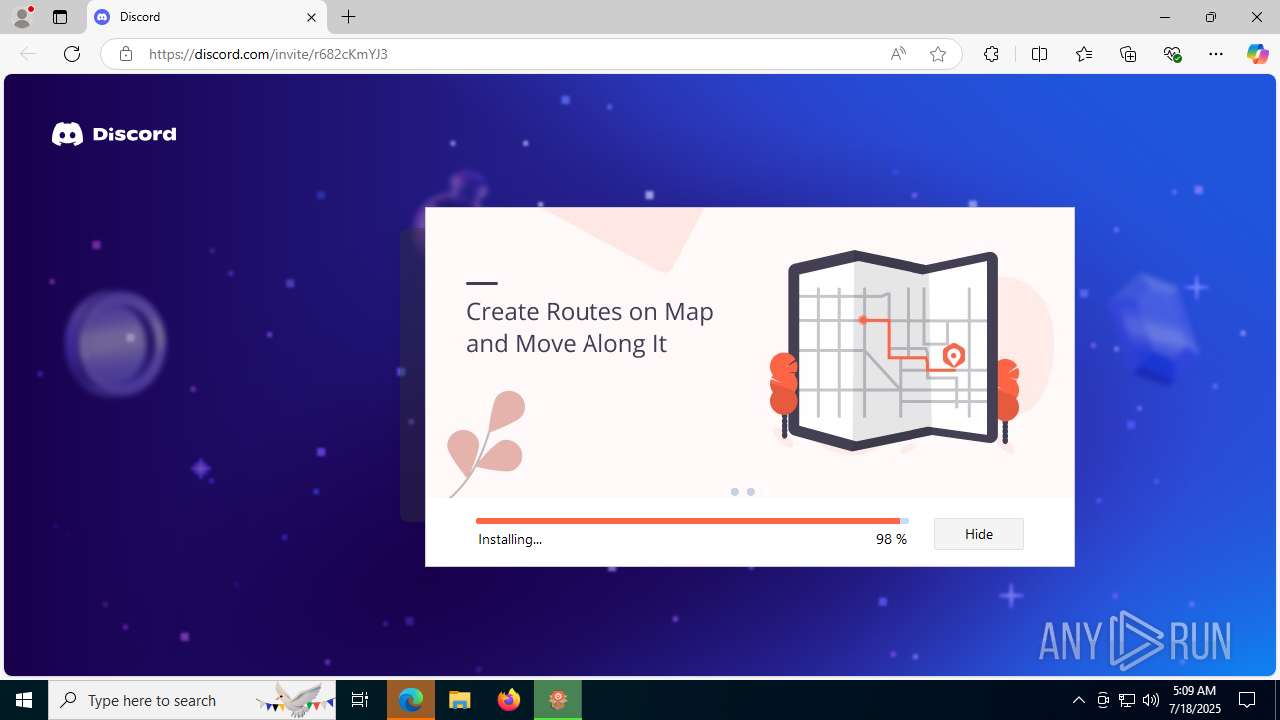
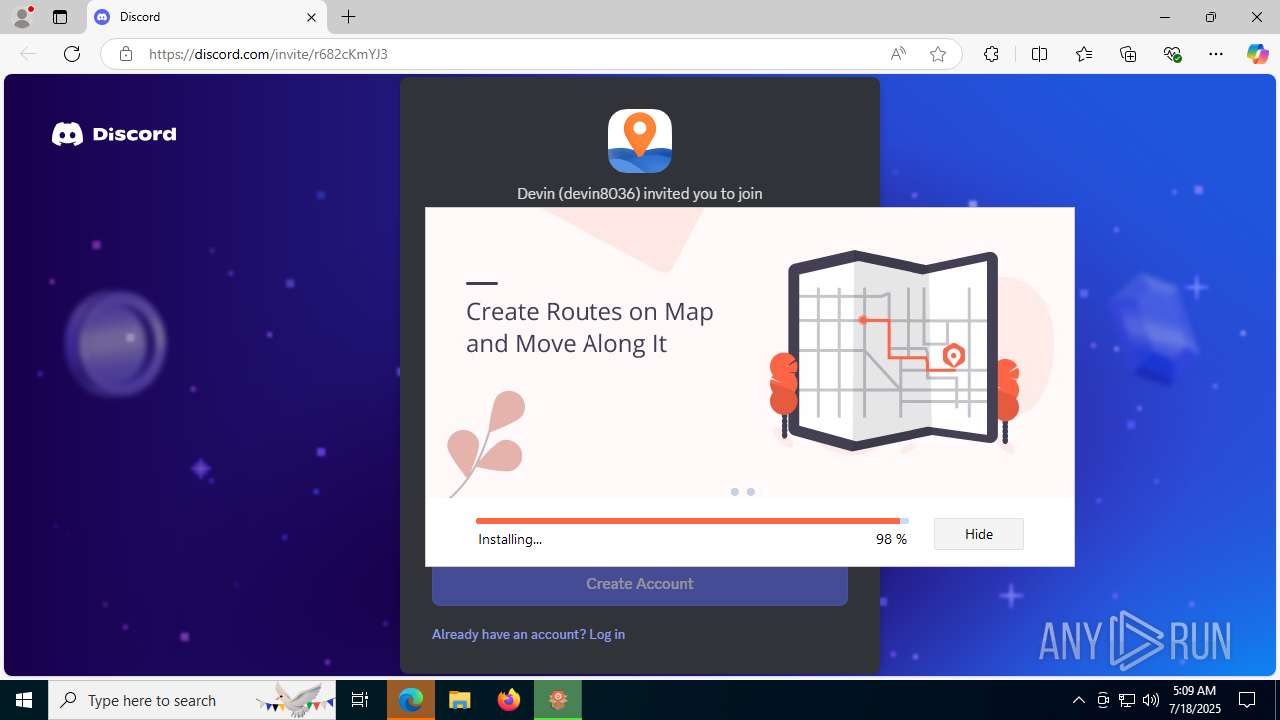
Attempting to use instant messaging service
- msedge.exe (PID: 6212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:30 01:40:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 2128384 |
| InitializedDataSize: | 829952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bdd14 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.0.1 |
| ProductVersionNumber: | 4.4.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | unictool-tailorgo_setup.exe |
| FileVersion: | 4.4.0.1 |
| LegalCopyright: | Copyright (C) 2025 UnicTool. All rights reserved. |
| ProductName: | UnicTool TailorGo |
| ProductVersion: | 4.4.0.1 |
Total processes
200
Monitored processes
50
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4192,i,17985483922820357578,11748880477864276068,262144 --variations-seed-version --mojo-platform-channel-handle=4200 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 512 | "C:\Users\admin\AppData\Local\Temp\unictool-tailorgo_setup.exe" | C:\Users\admin\AppData\Local\Temp\unictool-tailorgo_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: unictool-tailorgo_setup.exe Exit code: 3221226540 Version: 4.4.0.1 Modules
| |||||||||||||||
| 788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5164,i,3422756308171947490,12232181131001686662,262144 --variations-seed-version --mojo-platform-channel-handle=5100 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1604 | "cmd.exe" /c taskkill /f /t /im Feedback.exe | C:\Windows\SysWOW64\cmd.exe | — | imyfone-download.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5828,i,17985483922820357578,11748880477864276068,262144 --variations-seed-version --mojo-platform-channel-handle=5836 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2064 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6568,i,17985483922820357578,11748880477864276068,262144 --variations-seed-version --mojo-platform-channel-handle=6548 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2120 | /verysilent /imyfone_down /wait_run /path="C:\Program Files (x86)\" /progress="C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\temp.progress" | C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\imyfone-download.exe | unictool-tailorgo_setup.exe | ||||||||||||
User: admin Company: Wheatfield Guard Technology Co. Ltd Integrity Level: HIGH Description: UnicTool TailorGo Version: 8.0.0.1 Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4188,i,3422756308171947490,12232181131001686662,262144 --variations-seed-version --mojo-platform-channel-handle=4256 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4196,i,17985483922820357578,11748880477864276068,262144 --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4120,i,3422756308171947490,12232181131001686662,262144 --variations-seed-version --mojo-platform-channel-handle=3176 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
13 211
Read events
13 104
Write events
105
Delete events
2
Modification events
| (PID) Process: | (4544) unictool-tailorgo_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\iMyfone\iMyfoneDown |
| Operation: | write | Name: | GUID |
Value: 27FCC6B8-7B4F-4b39-BF70-D38071BB8885 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsMSACloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsAADCloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | CortanaStateLastRun |
Value: 69D6796800000000 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | delete value | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | write | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 151357 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 157467 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Recognizers |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Recognizers\Tokens\MS-1033-110-WINMO-DNN | |||
Executable files
322
Suspicious files
816
Text files
3 521
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4544 | unictool-tailorgo_setup.exe | C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\language\text.ini | text | |
MD5:8C04D1926EA945DD37666895553B793F | SHA256:A30AC2A9A22086FB00B017A82850071495360FD76CD6321D97E0909776583681 | |||
| 4544 | unictool-tailorgo_setup.exe | C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\language\English\pr_1.png | image | |
MD5:4983C07334E738F02C6C93EE10F1E065 | SHA256:9E4F4DEB0CE4892DDDD06B64B28B3E8BB7689087908417A705D84AA987D523B8 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\AptopUBu7_oVDubJxwvaIprW-lI[1].css | text | |
MD5:29DE55D0A7A581B230CC2D70686CD03A | SHA256:D9F161C1FE8751953E4F3819993C16C2A61A0121B527E09862C34C89E7B6C677 | |||
| 4544 | unictool-tailorgo_setup.exe | C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\language\language.ini | text | |
MD5:EDDEDFFE2418656AD2CB85705932AC5F | SHA256:734F4DDA01A12AFEF3E9A21B656F6717DBD0AC27D1E89C318F0DFF49CD473DCD | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\2zG9LNLNE5v-jAEMg-AweJz2aRE.br[1].js | binary | |
MD5:B16E3B0F4F46CA8C2B09A6FD3166FD5E | SHA256:5EED0FEF0810F9F79A02E6D08EA87C17B9085B50619793A46F576AC2AA3CF148 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\-iNIzuEypRdgRJ6xnyVHizZ3bpM.br[1].js | binary | |
MD5:E86ABEFE45E62F7E2F865D8A344D0B6F | SHA256:5D54790C856CE13811590E18AC3B0ACEEFEFB61258852490F4C5C60748365E89 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:E68E1623702AB21F5FC12C81F7A00F8D | SHA256:A5AE6E2990AFA9B1048E5ACBDA62FA5DB5C96600F85C7C82D9089F42EF77384C | |||
| 4544 | unictool-tailorgo_setup.exe | C:\Program Files (x86)\imyfone_down\unictool-tailorgo_setup\language\productInfo.ini | text | |
MD5:A00C1551C244D11CEC3D11E14826D952 | SHA256:58677CD72E604646876128FB8609AFE29D73AAAAE0C7C4E20114DF4D66284F82 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\4BpQ1bD8vX1mXuJObN-gg9RqkyQ.br[1].js | binary | |
MD5:8465A334065673EB6A6487C8D87539DB | SHA256:84ED6C495B322B0F2213CC33EC6C652D84D82E010C928B1141DB2290D4365F3D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
112
DNS requests
80
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3688 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3732 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3688 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6664 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6212 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Ar8sSYlkNLFJOXEpZez4aAEUZ38sMZ-Smt82qfRvuk8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4544 | unictool-tailorgo_setup.exe | 142.250.185.78:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
4544 | unictool-tailorgo_setup.exe | 163.181.58.173:443 | apipdm.imyfone.club | — | MY | suspicious |
4544 | unictool-tailorgo_setup.exe | 13.32.99.14:443 | download.unictool.com | AMAZON-02 | US | unknown |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
download.unictool.com |
| unknown |
apipdm.imyfone.club |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
6212 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
6212 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6212 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |