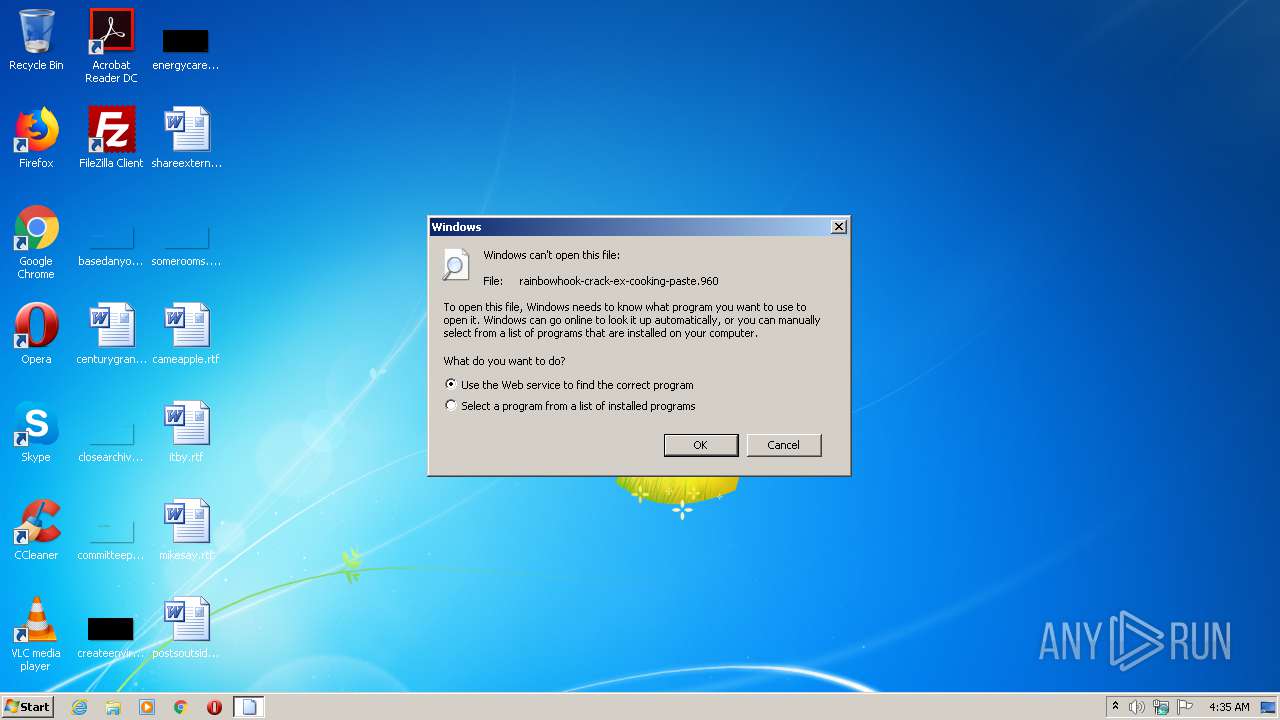
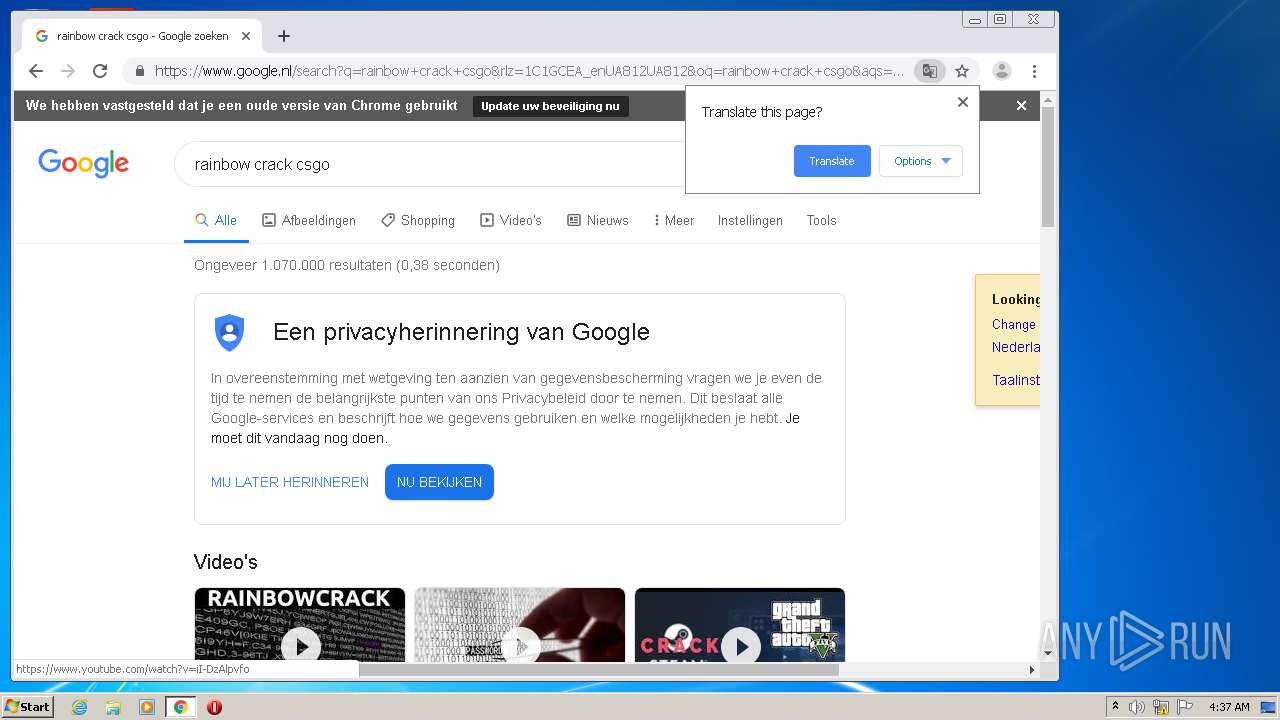
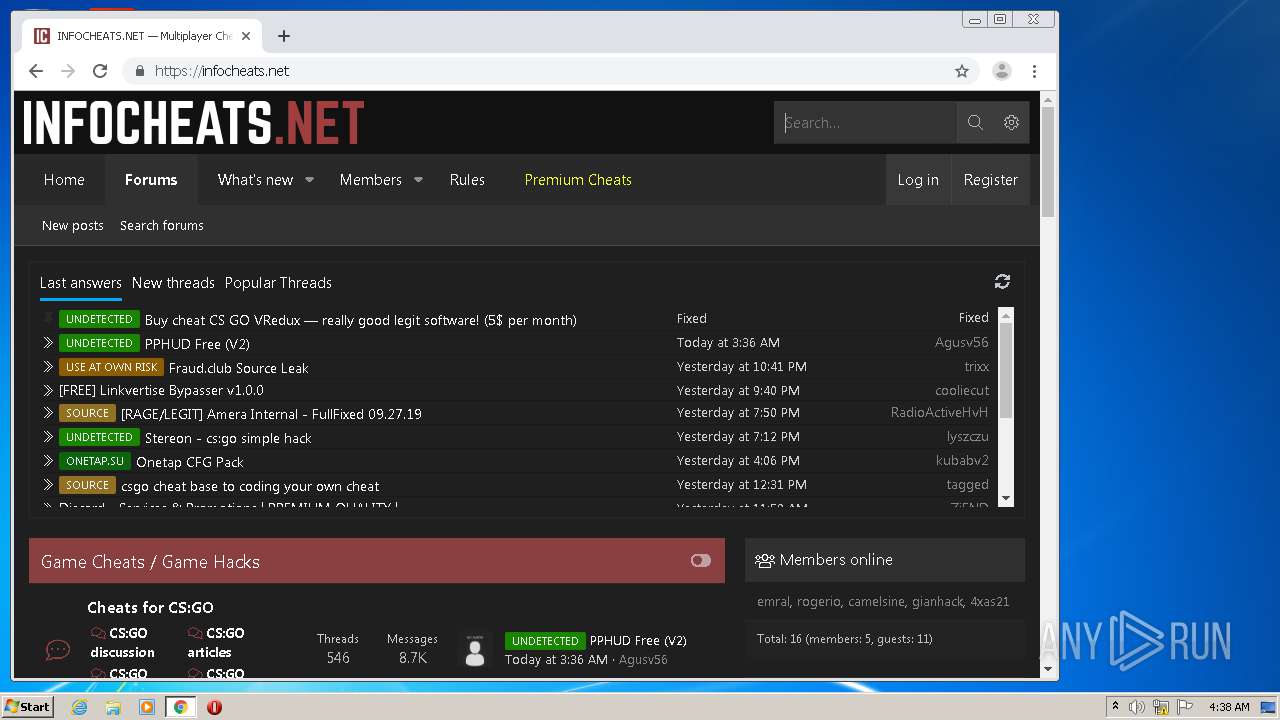
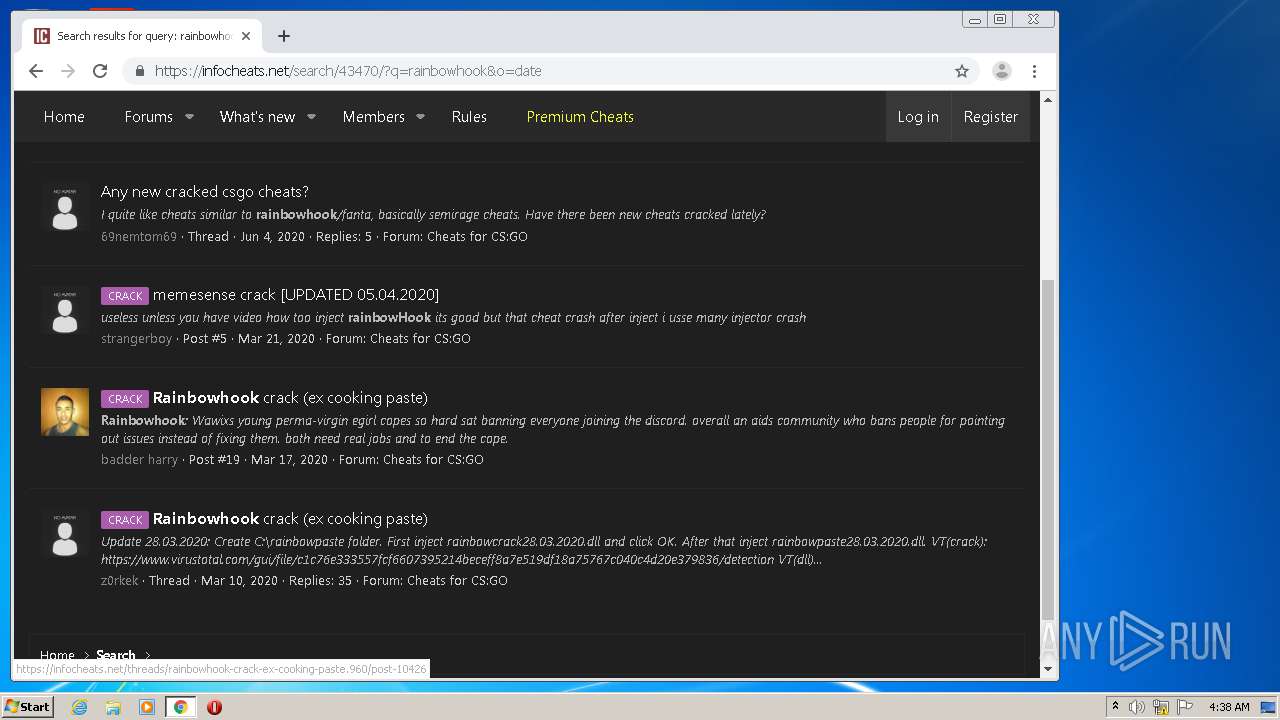
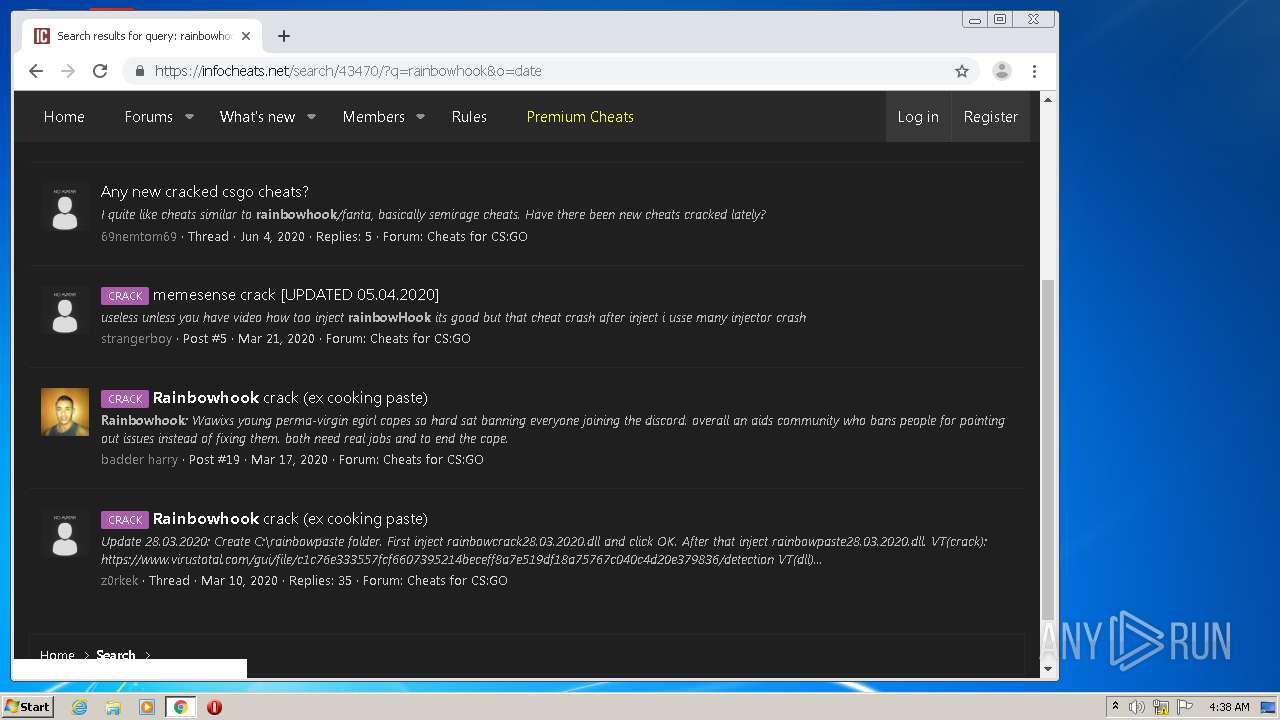
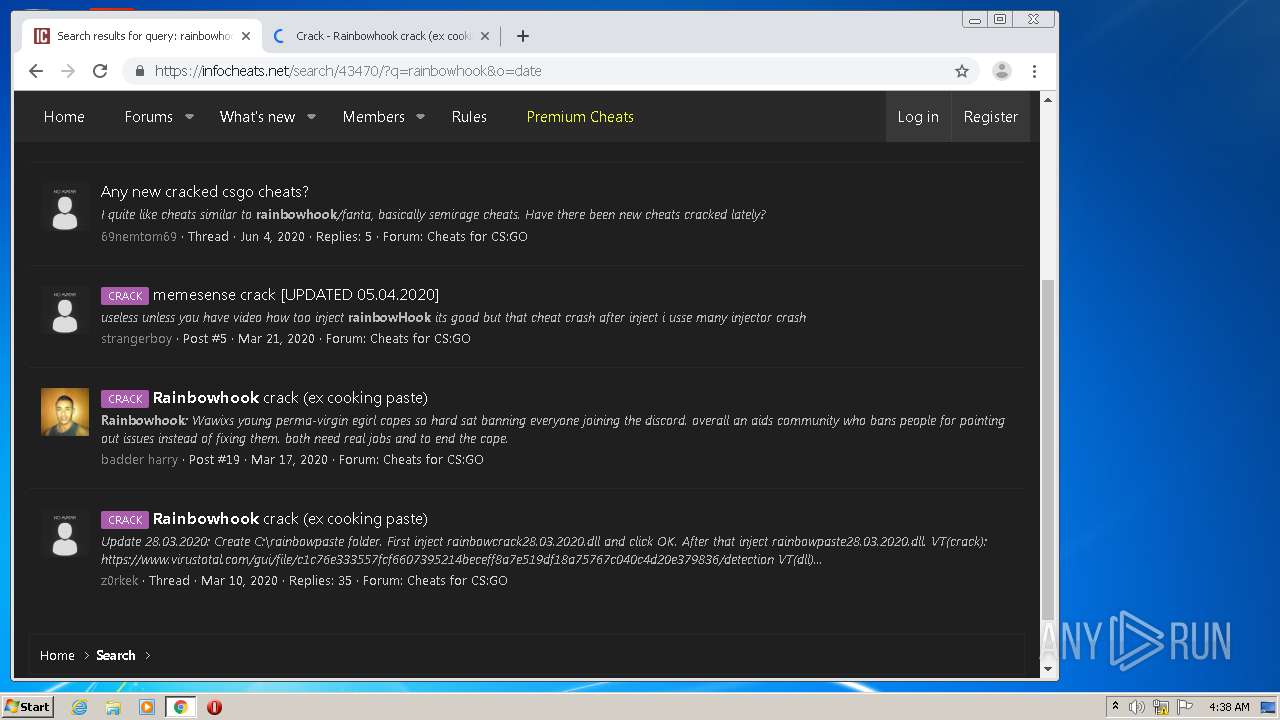
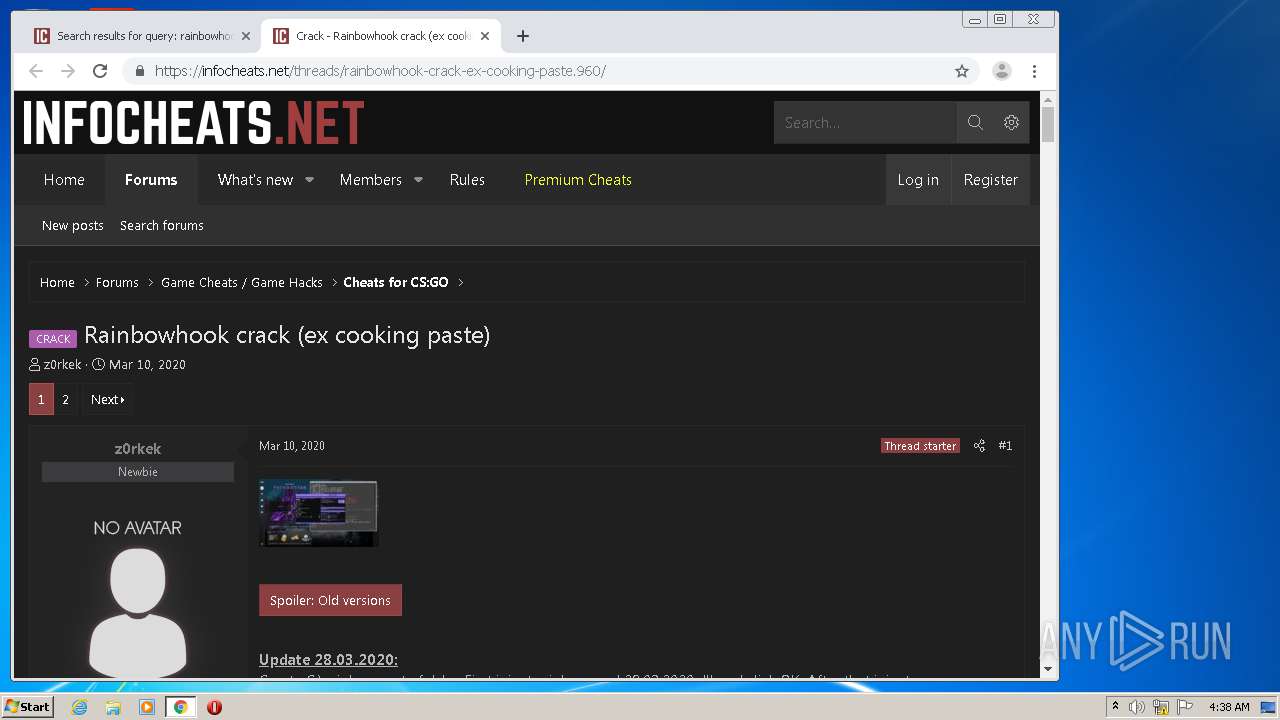
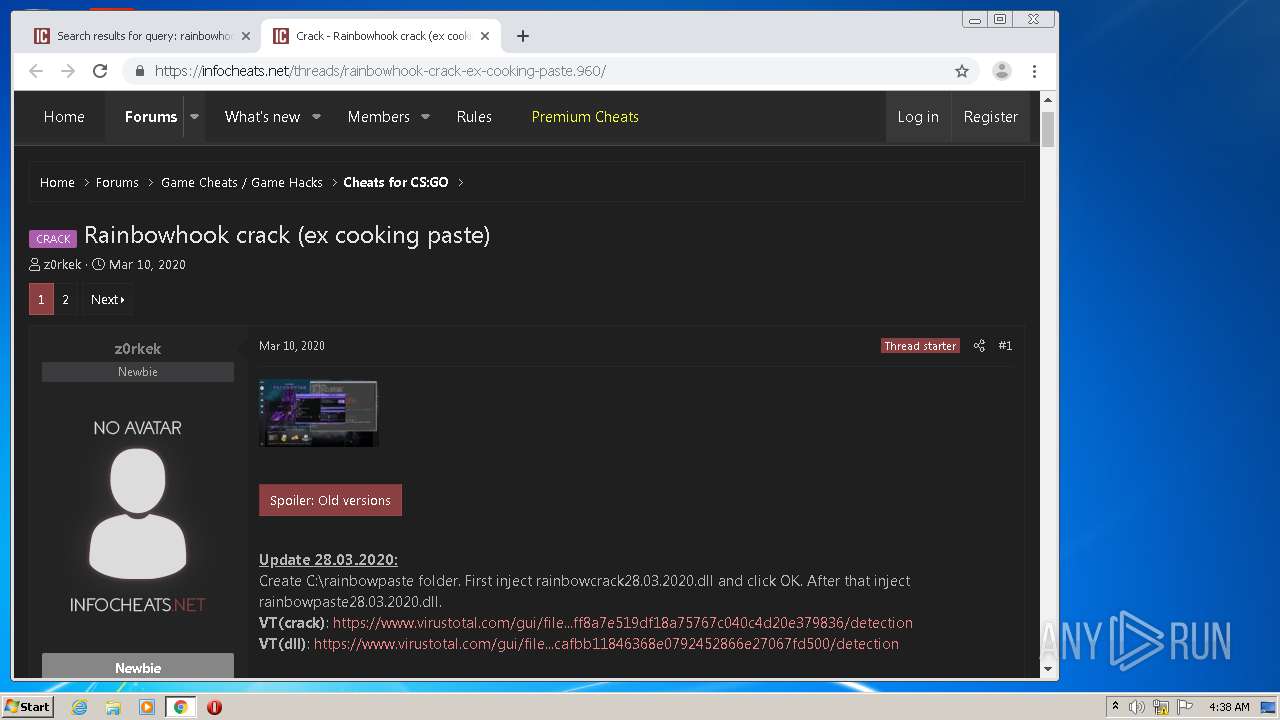
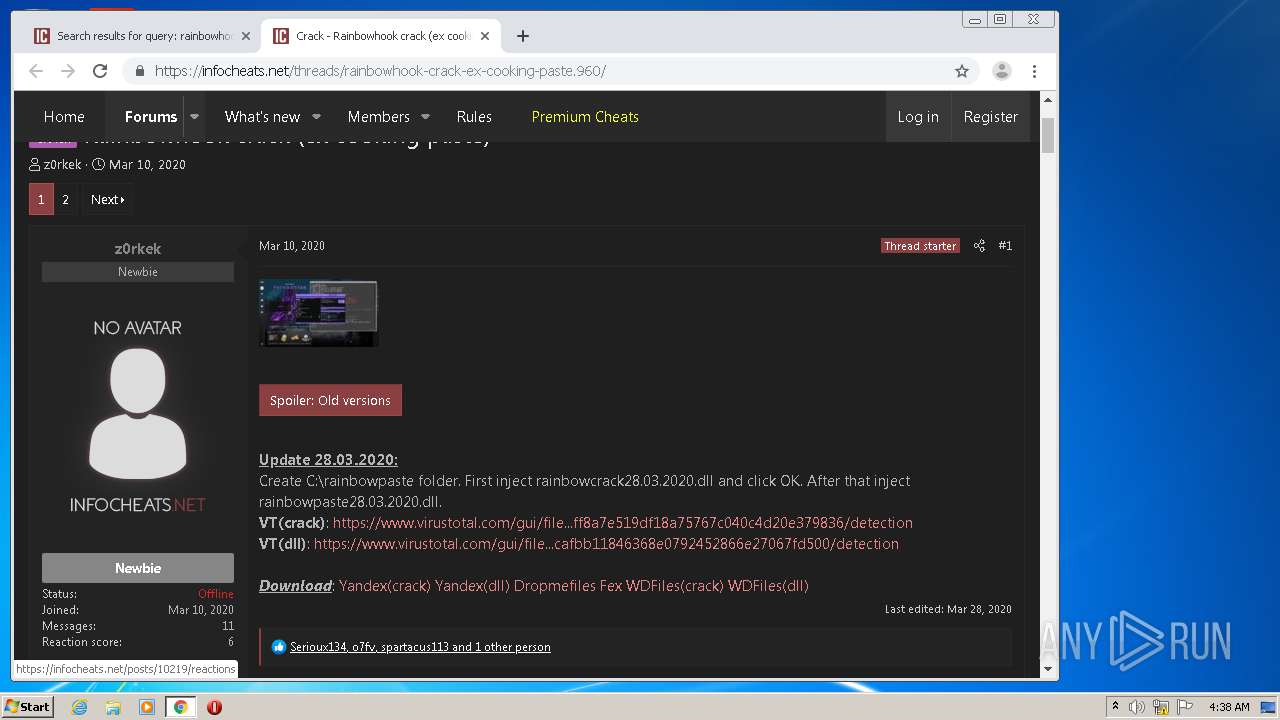
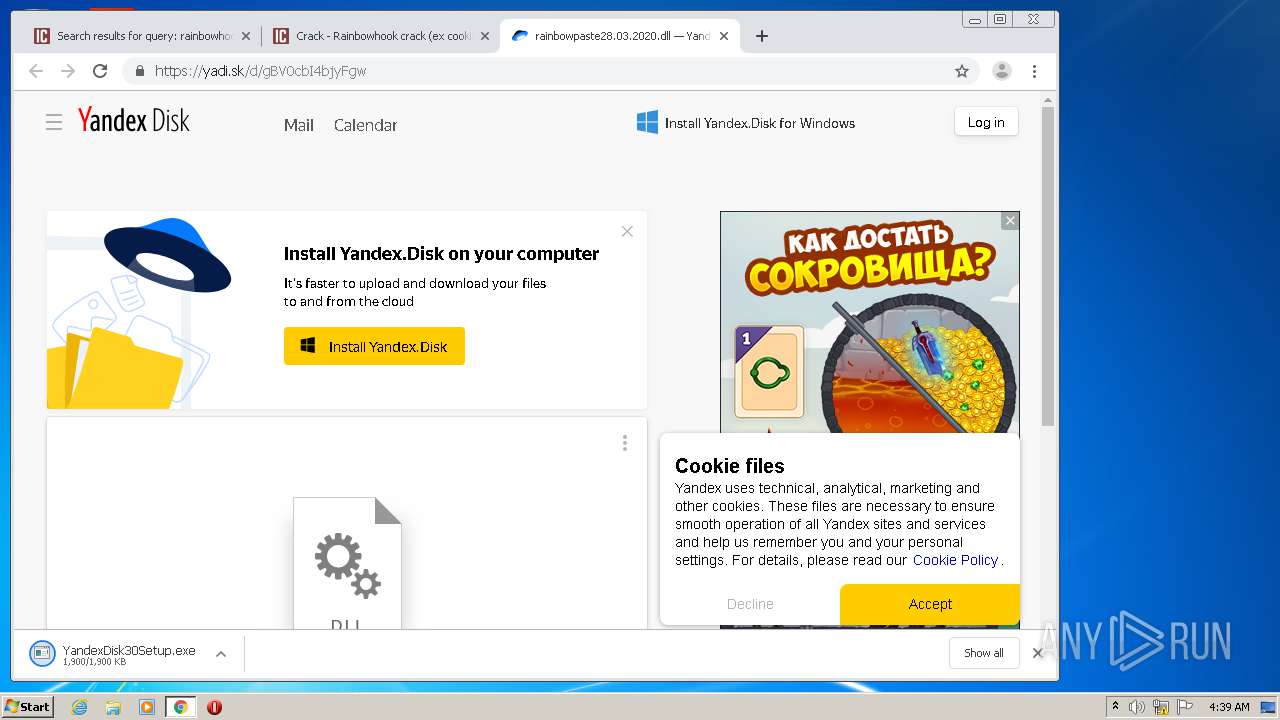
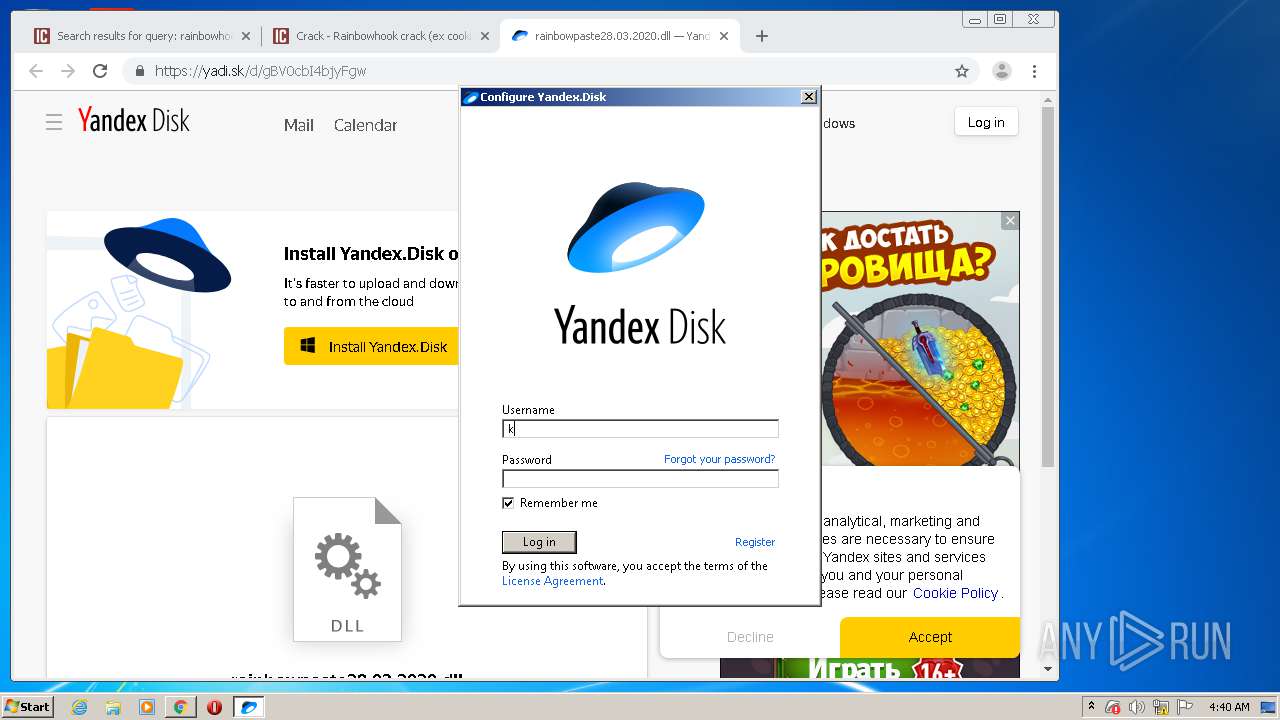
| download: | rainbowhook-crack-ex-cooking-paste.960 |
| Full analysis: | https://app.any.run/tasks/0dc4f715-f1df-43bb-8ce4-854611c8aa43 |
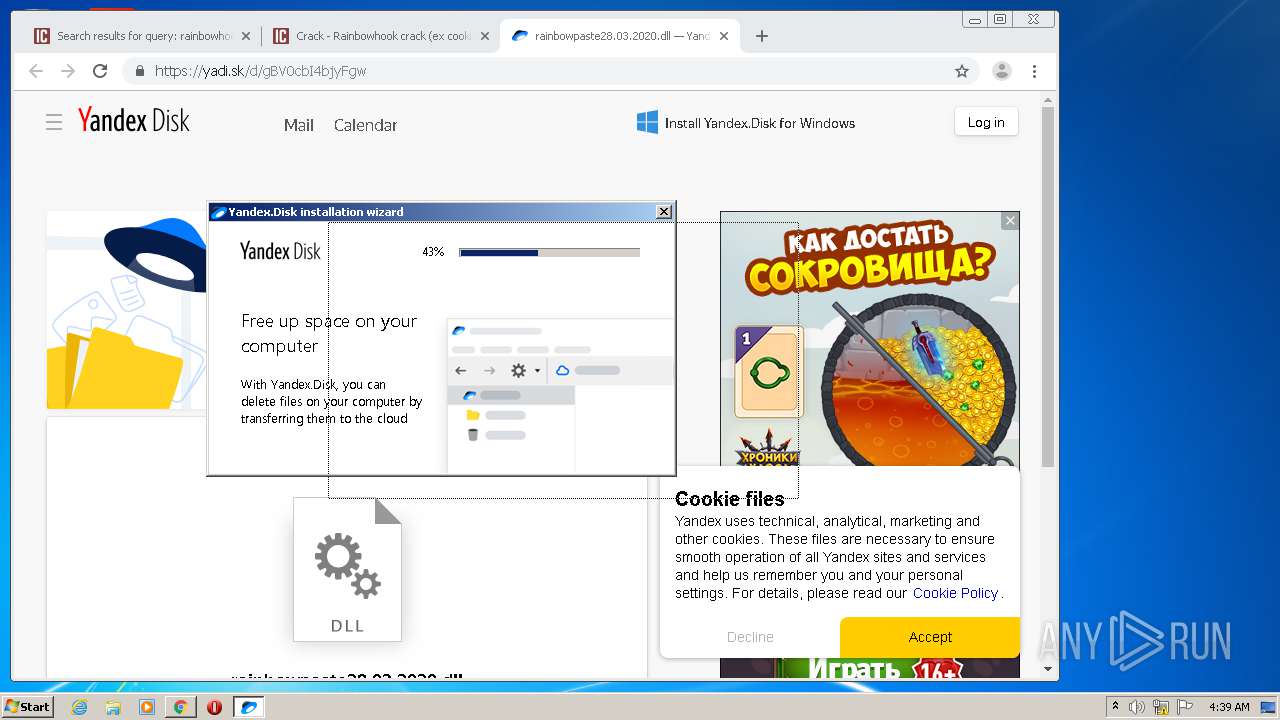
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 03:35:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with no line terminators |
| MD5: | 1577060D60DA44A89F98DC4B8A6001BD |
| SHA1: | E7C5FB83D81167A4416D9D74B8E7D97882D006F2 |
| SHA256: | D476F580504AADB4FEBD497DF94F9C145D18B7024A0C2E066C4422789903AF9E |
| SSDEEP: | 12:kIqJmWHov6mIDQYvdrWwXVZQ34l3zxv/3t03kX2egClTJBJLYLPZ5d9OI:k3ToymIsYv5WuVLFxjX2X09L0p9OI |
MALICIOUS
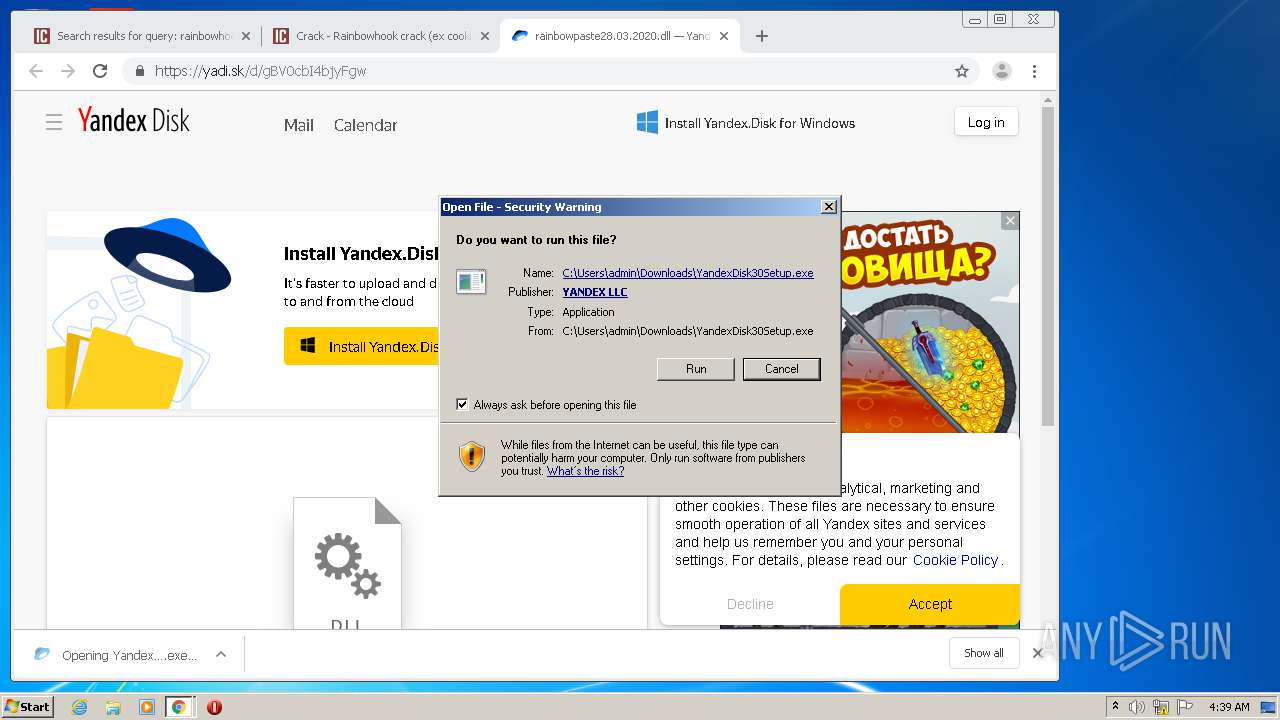
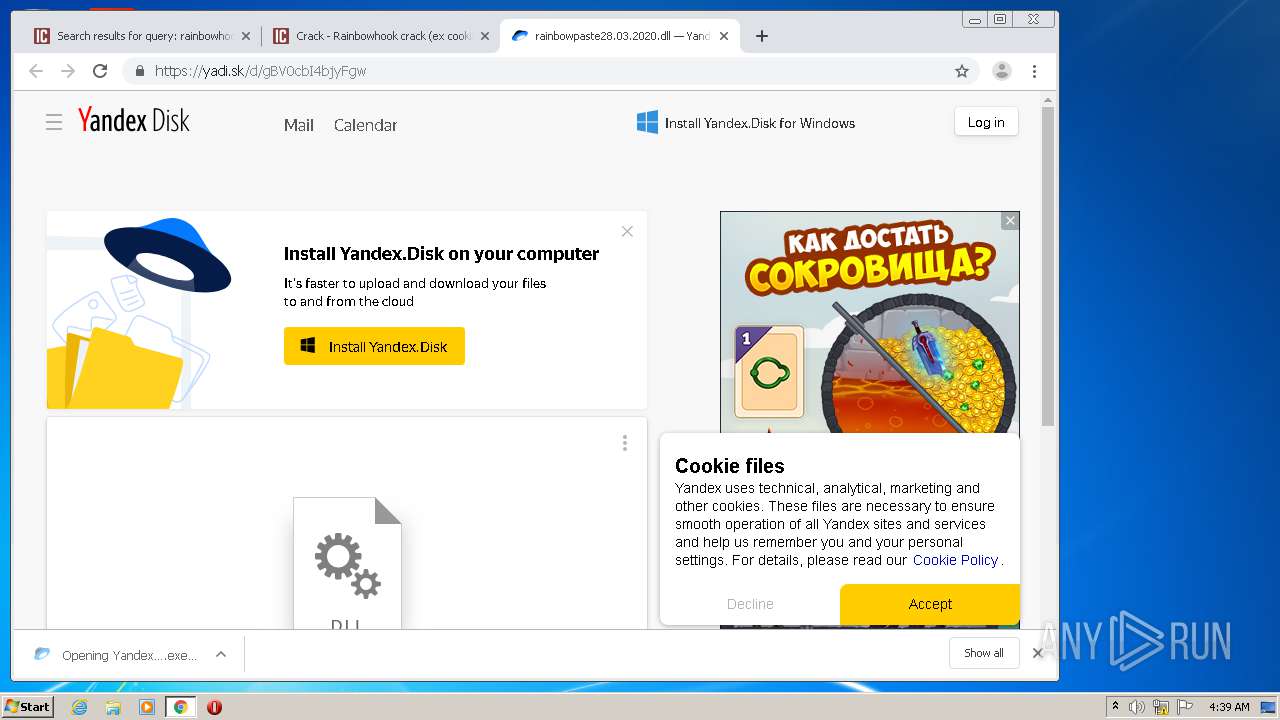
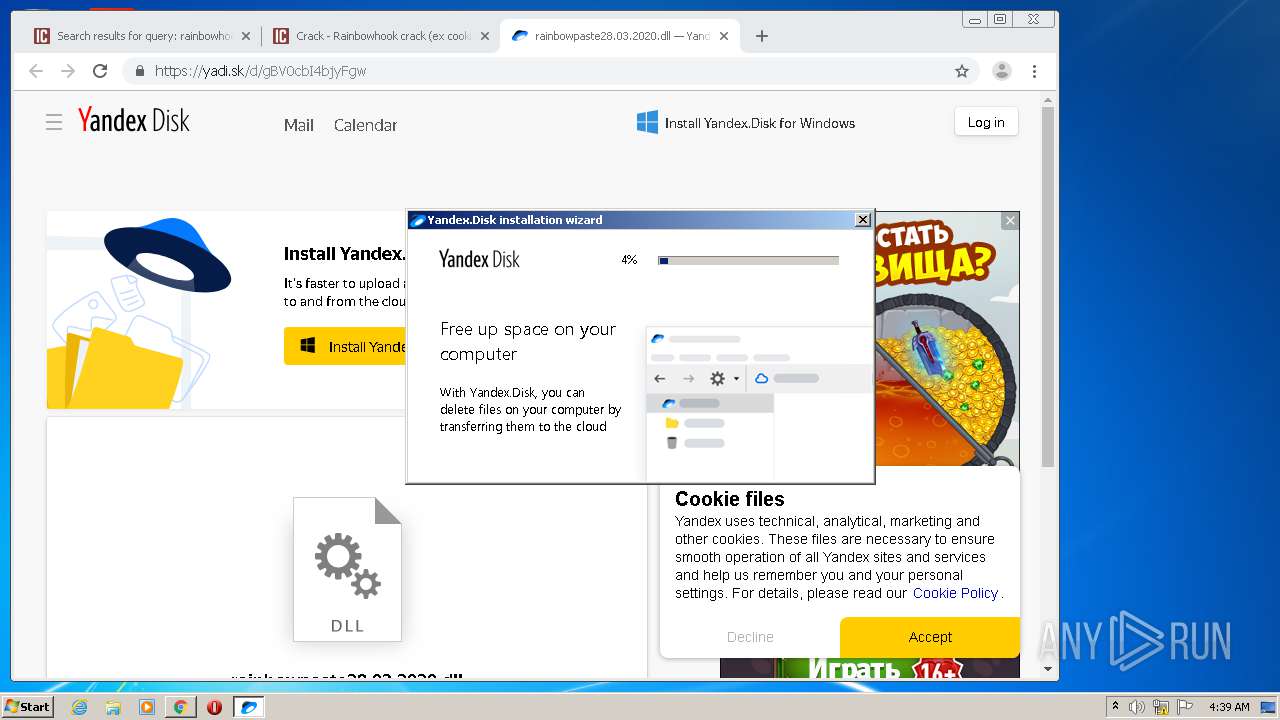
Application was dropped or rewritten from another process
- YandexDisk30Setup.exe (PID: 3240)
- 7za.exe (PID: 1508)
- 7za.exe (PID: 2528)
- 7za.exe (PID: 1004)
- 7za.exe (PID: 664)
- 7za.exe (PID: 2416)
- 7za.exe (PID: 2376)
- 7za.exe (PID: 1896)
- 7za.exe (PID: 1908)
- 7za.exe (PID: 2448)
- 7za.exe (PID: 2256)
- 7za.exe (PID: 3884)
- 7za.exe (PID: 3388)
- 7za.exe (PID: 1428)
- 7za.exe (PID: 3952)
- 7za.exe (PID: 3328)
- 7za.exe (PID: 1556)
- 7za.exe (PID: 2212)
- 7za.exe (PID: 2488)
- 7za.exe (PID: 1212)
- 7za.exe (PID: 2376)
- 7za.exe (PID: 2960)
- 7za.exe (PID: 1028)
- 7za.exe (PID: 900)
- 7za.exe (PID: 3204)
- 7za.exe (PID: 2868)
- 7za.exe (PID: 980)
- 7za.exe (PID: 3796)
- 7za.exe (PID: 2200)
- 7za.exe (PID: 2364)
- 7za.exe (PID: 2416)
- 7za.exe (PID: 2740)
- 7za.exe (PID: 3452)
- 7za.exe (PID: 2148)
- 7za.exe (PID: 3752)
- 7za.exe (PID: 3616)
- 7za.exe (PID: 3792)
- 7za.exe (PID: 3440)
- 7za.exe (PID: 3136)
- 7za.exe (PID: 3884)
- 7za.exe (PID: 2400)
- 7za.exe (PID: 2244)
- 7za.exe (PID: 3124)
- 7za.exe (PID: 2864)
- 7za.exe (PID: 3160)
- YandexDisk30Setup.exe (PID: 2868)
- YandexDisk2.exe (PID: 2972)
- YandexDisk2.exe (PID: 1936)
Changes the autorun value in the registry
- YandexDisk2.exe (PID: 2972)
- YandexDisk2.exe (PID: 1936)
Loads dropped or rewritten executable
- YandexDisk2.exe (PID: 2972)
- YandexDisk2.exe (PID: 1936)
SUSPICIOUS
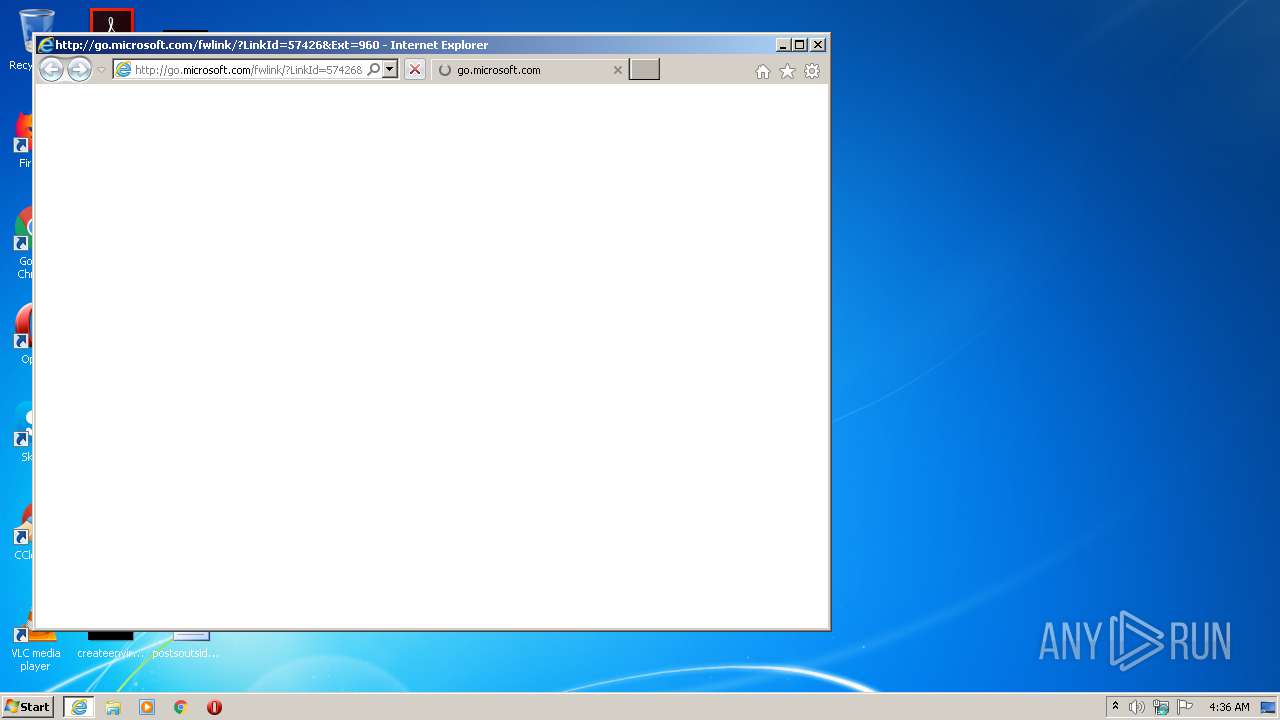
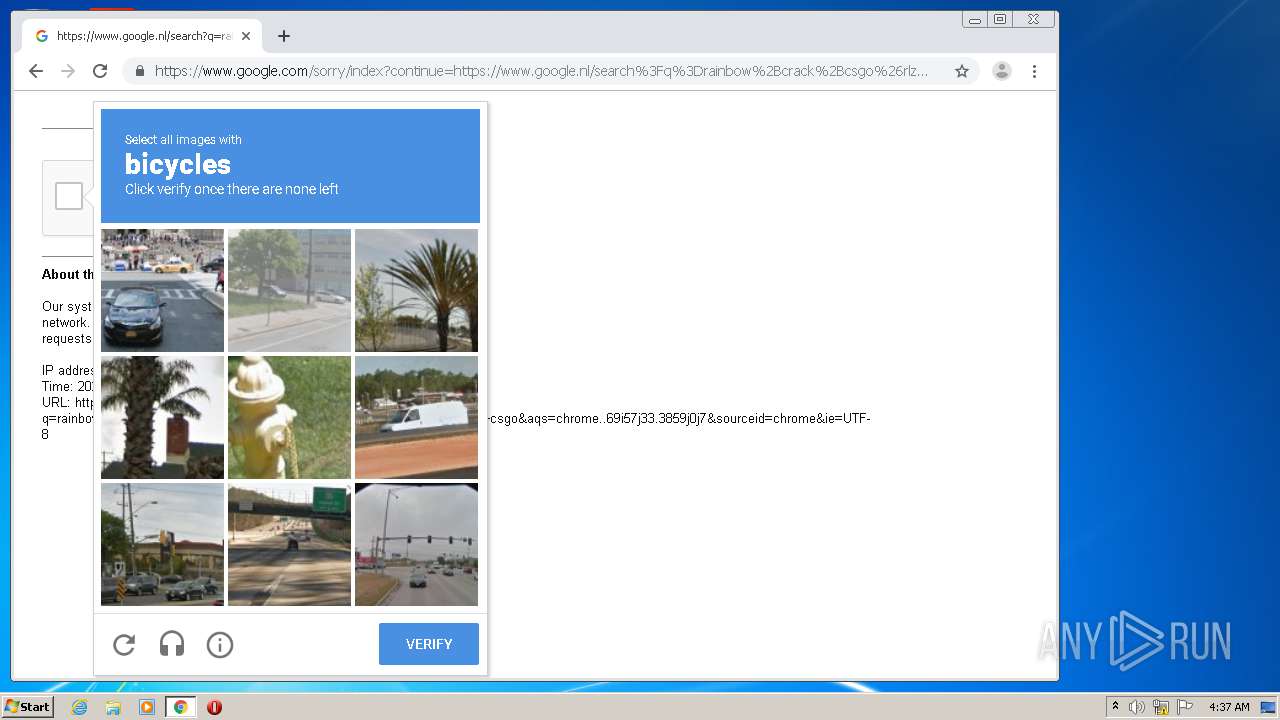
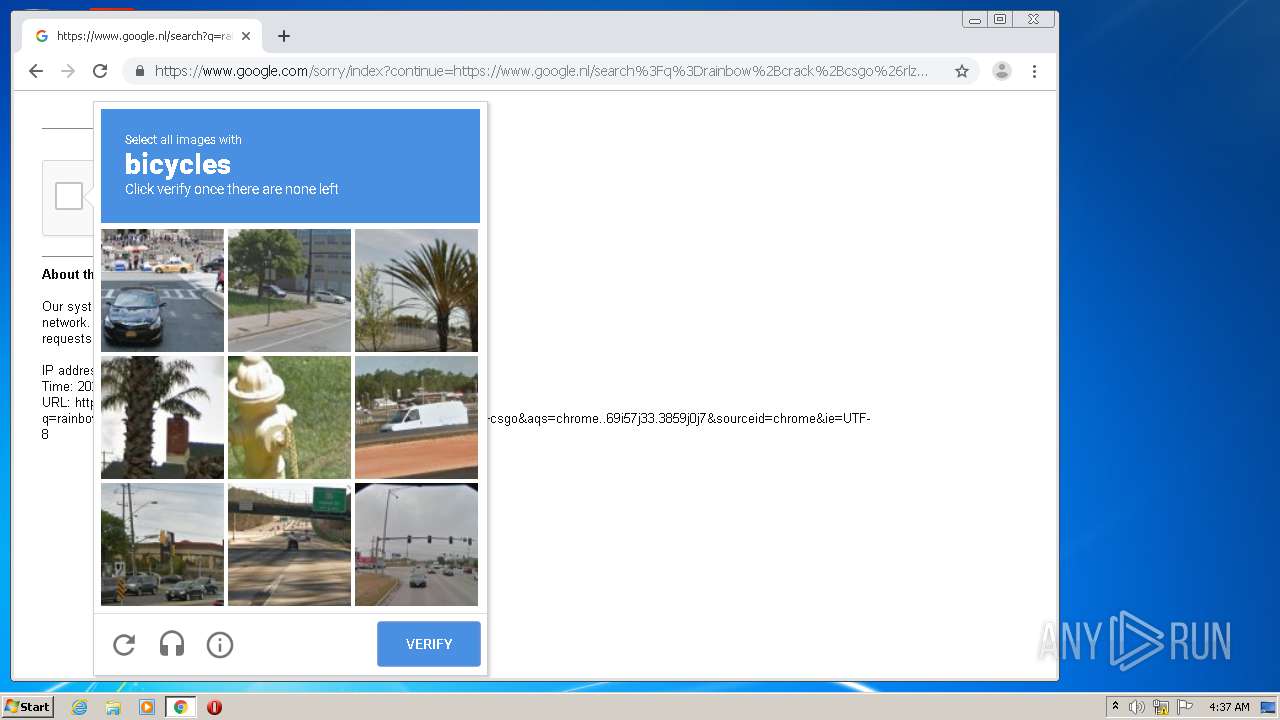
Starts Internet Explorer
- rundll32.exe (PID: 1796)
Executable content was dropped or overwritten
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2276)
- YandexDisk30Setup_x86.exe (PID: 2996)
- 7za.exe (PID: 1508)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2744)
Creates files in the program directory
- YandexDisk30Setup.exe (PID: 3240)
- 7za.exe (PID: 1508)
- YandexDisk30Setup_x86.exe (PID: 2996)
- 7za.exe (PID: 2528)
- 7za.exe (PID: 2376)
- 7za.exe (PID: 2416)
- 7za.exe (PID: 1896)
- 7za.exe (PID: 1004)
- 7za.exe (PID: 1908)
- 7za.exe (PID: 2448)
- 7za.exe (PID: 664)
- 7za.exe (PID: 2256)
- 7za.exe (PID: 3884)
- 7za.exe (PID: 3388)
- 7za.exe (PID: 1428)
- 7za.exe (PID: 3328)
- 7za.exe (PID: 3952)
- 7za.exe (PID: 2488)
- 7za.exe (PID: 2212)
- 7za.exe (PID: 1556)
- 7za.exe (PID: 2200)
- 7za.exe (PID: 1028)
- 7za.exe (PID: 2960)
- 7za.exe (PID: 1212)
- 7za.exe (PID: 2376)
- 7za.exe (PID: 900)
- 7za.exe (PID: 3204)
- 7za.exe (PID: 2868)
- 7za.exe (PID: 980)
- 7za.exe (PID: 3796)
- 7za.exe (PID: 2364)
- 7za.exe (PID: 2740)
- 7za.exe (PID: 2416)
- 7za.exe (PID: 3452)
- 7za.exe (PID: 3616)
- 7za.exe (PID: 3752)
- 7za.exe (PID: 2148)
- 7za.exe (PID: 3440)
- 7za.exe (PID: 3136)
- 7za.exe (PID: 3160)
- 7za.exe (PID: 2400)
- 7za.exe (PID: 3884)
- 7za.exe (PID: 3124)
- 7za.exe (PID: 2244)
- 7za.exe (PID: 2864)
- 7za.exe (PID: 3792)
Application launched itself
- YandexDisk30Setup_x86.exe (PID: 2996)
- YandexDisk30Setup.exe (PID: 3240)
Modifies the open verb of a shell class
- YandexDisk30Setup_x86.exe (PID: 2828)
- YandexDisk30Setup_x86.exe (PID: 2996)
Creates files in the user directory
- YandexDisk30Setup_x86.exe (PID: 2996)
- YandexDisk30Setup.exe (PID: 3240)
- YandexDisk2.exe (PID: 1936)
Creates a software uninstall entry
- YandexDisk30Setup_x86.exe (PID: 2996)
Creates COM task schedule object
- YandexDisk30Setup_x86.exe (PID: 2996)
Reads internet explorer settings
- YandexDisk2.exe (PID: 1936)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 3688)
- chrome.exe (PID: 2744)
Changes internet zones settings
- iexplore.exe (PID: 3896)
Manual execution by user
- chrome.exe (PID: 2744)
Reads the hosts file
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2744)
Creates files in the user directory
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 3896)
Reads internet explorer settings
- iexplore.exe (PID: 3688)
Application launched itself
- chrome.exe (PID: 2744)
Reads settings of System Certificates
- chrome.exe (PID: 2744)
- YandexDisk30Setup.exe (PID: 3240)
- chrome.exe (PID: 2276)
- iexplore.exe (PID: 3896)
- iexplore.exe (PID: 3688)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3896)
Changes settings of System certificates
- iexplore.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
185
Monitored processes
96
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17098181059432597393,6694492727282096866,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16306316294937217979 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe" x "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\zlib1.dll.zip" -aoa -o"C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}" | C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe | — | YandexDisk30Setup_x86.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17098181059432597393,6694492727282096866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17508809576942751628 --mojo-platform-channel-handle=3768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe" x "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\cef_200_percent.pak.zip" -aoa -o"C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}" | C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe | — | YandexDisk30Setup_x86.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 980 | "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe" x "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\app.asar.zip" -aoa -o"C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}" | C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe | — | YandexDisk30Setup_x86.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1004 | "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe" x "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\YandexDiskScreenshotEditor.exe.zip" -aoa -o"C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}" | C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe | — | YandexDisk30Setup_x86.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1028 | "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe" x "C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\cef_100_percent.pak.zip" -aoa -o"C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}" | C:\ProgramData\Yandex\Yandex.Disk.2\{D76D84C4-6CFA-441A-9C9A-79BD658F04CD}\7za.exe | — | YandexDisk30Setup_x86.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17098181059432597393,6694492727282096866,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8347702473583747510 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,17098181059432597393,6694492727282096866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17946315860656698522 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,17098181059432597393,6694492727282096866,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10563723265666679656 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 840
Read events
2 396
Write events
3 712
Delete events
1 732
Modification events
| (PID) Process: | (1796) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000EC335EBCC658D601 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3462165284 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824646 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
18
Suspicious files
143
Text files
353
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9136.tmp | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9137.tmp | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C668K1VR.txt | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BJZ3HIW7.txt | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PUGJTYZK.txt | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YEQ5I96K.txt | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabBD85.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarBD86.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver9C3.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
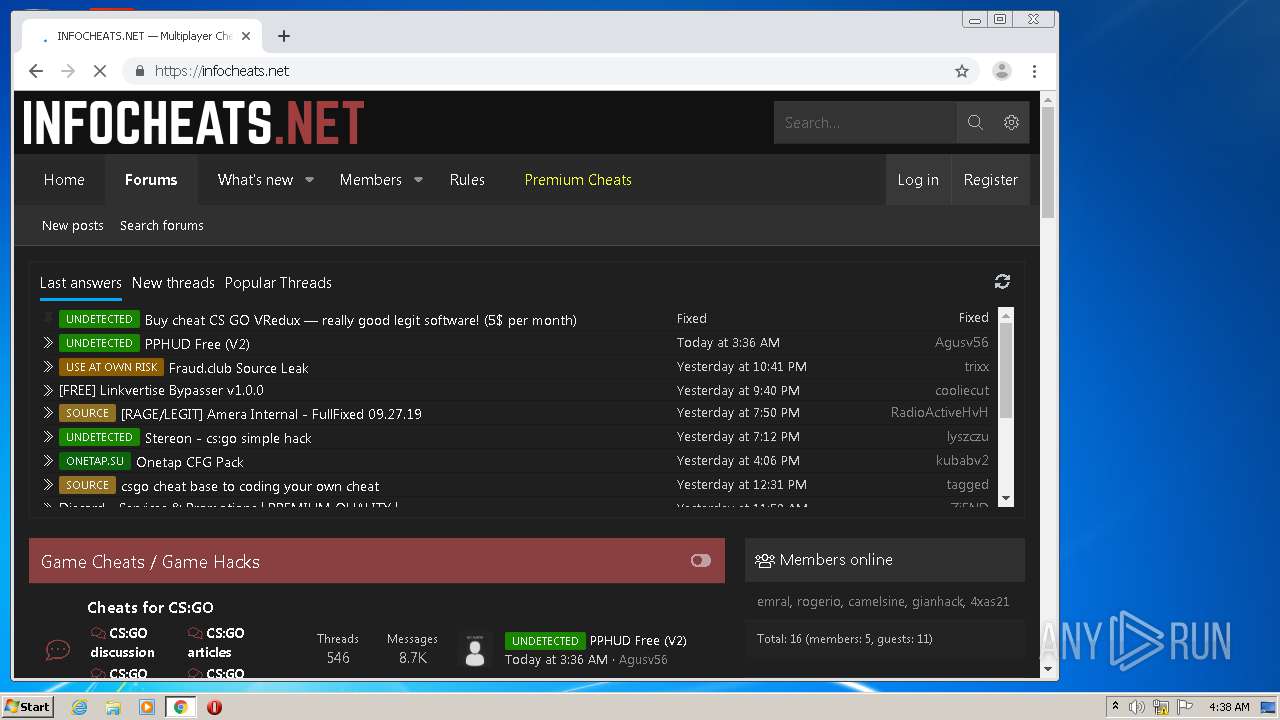
HTTP(S) requests
9
TCP/UDP connections
134
DNS requests
98
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3688 | iexplore.exe | GET | 302 | 88.221.62.148:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=960 | unknown | — | — | whitelisted |
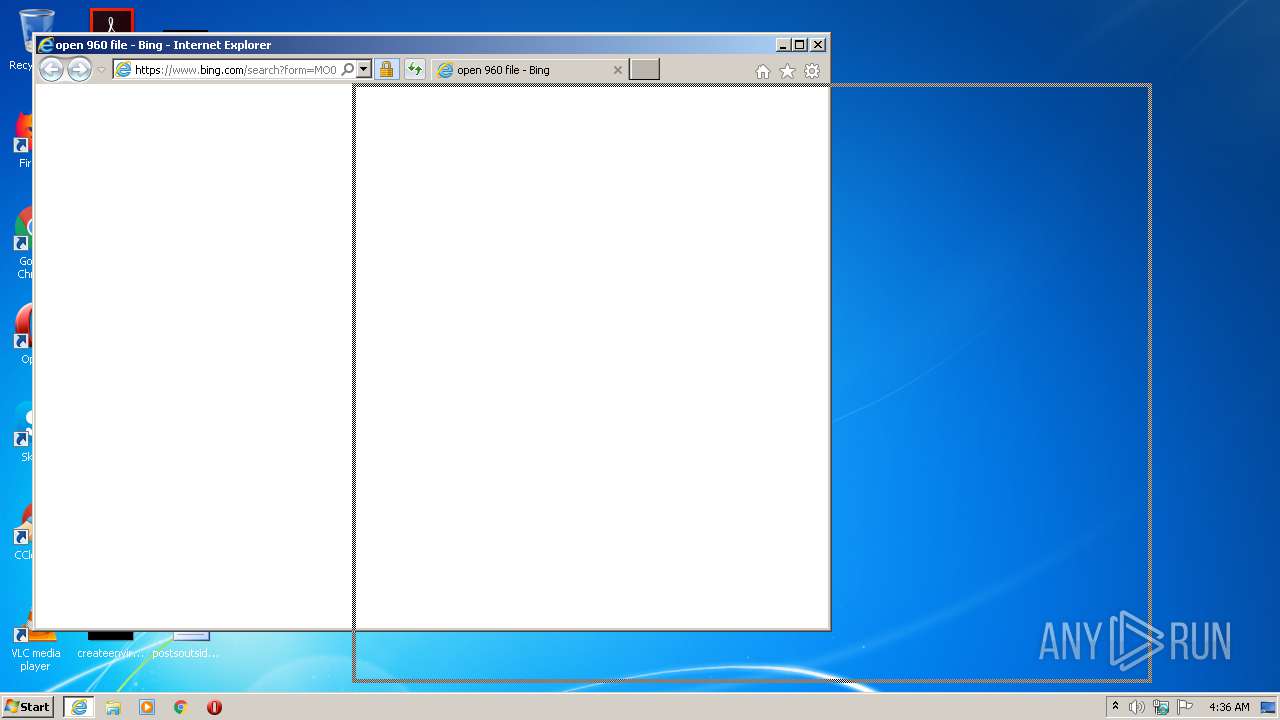
3688 | iexplore.exe | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=960 | unknown | — | — | whitelisted |
3688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2276 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
2276 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
3688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2276 | chrome.exe | GET | 200 | 74.125.8.140:80 | http://r6---sn-5hnednlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=45.86.201.12&mm=28&mn=sn-5hnednlk&ms=nvh&mt=1594611159&mv=u&mvi=6&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2276 | chrome.exe | GET | 200 | 74.125.100.73:80 | http://r4---sn-5hne6nsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=45.86.201.12&mm=28&mn=sn-5hne6nsz&ms=nvh&mt=1594611159&mv=u&mvi=4&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3896 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2276 | chrome.exe | 216.58.205.227:443 | www.google.nl | Google Inc. | US | whitelisted |
2276 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2276 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2276 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3688 | iexplore.exe | 88.221.62.148:80 | go.microsoft.com | Akamai Technologies, Inc. | — | malicious |
3688 | iexplore.exe | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
3688 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3688 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3896 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3688 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |