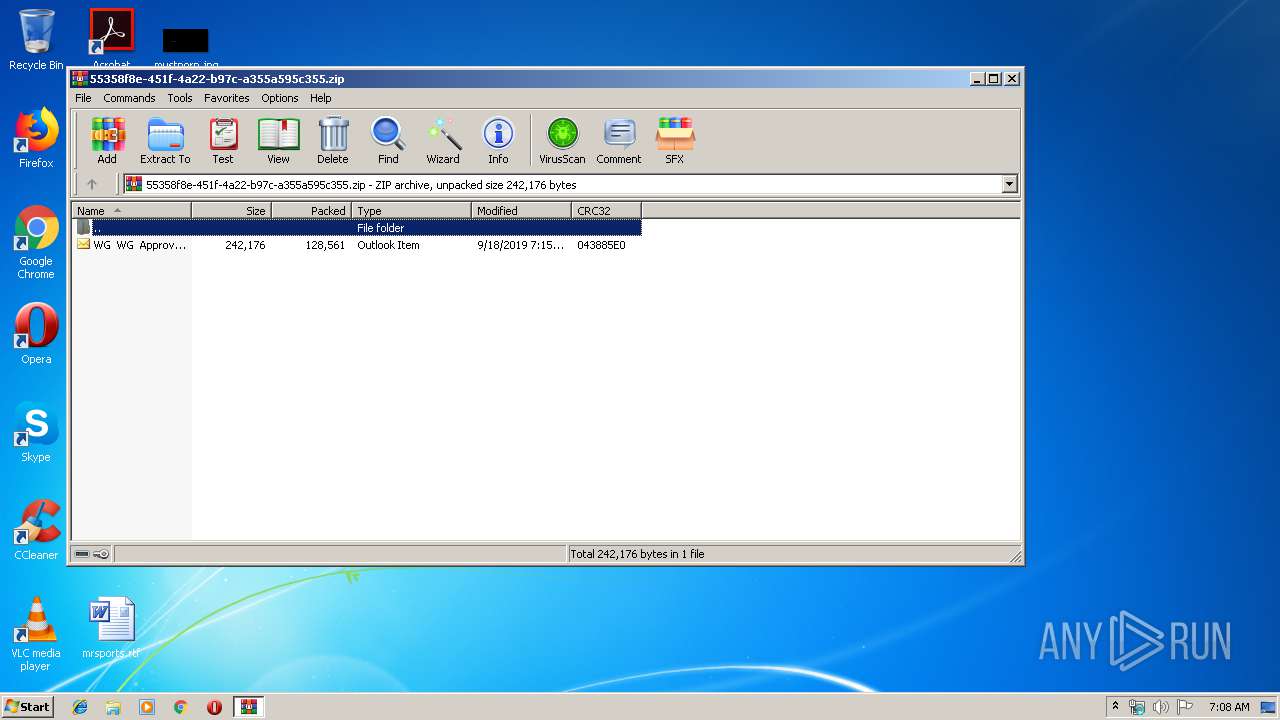
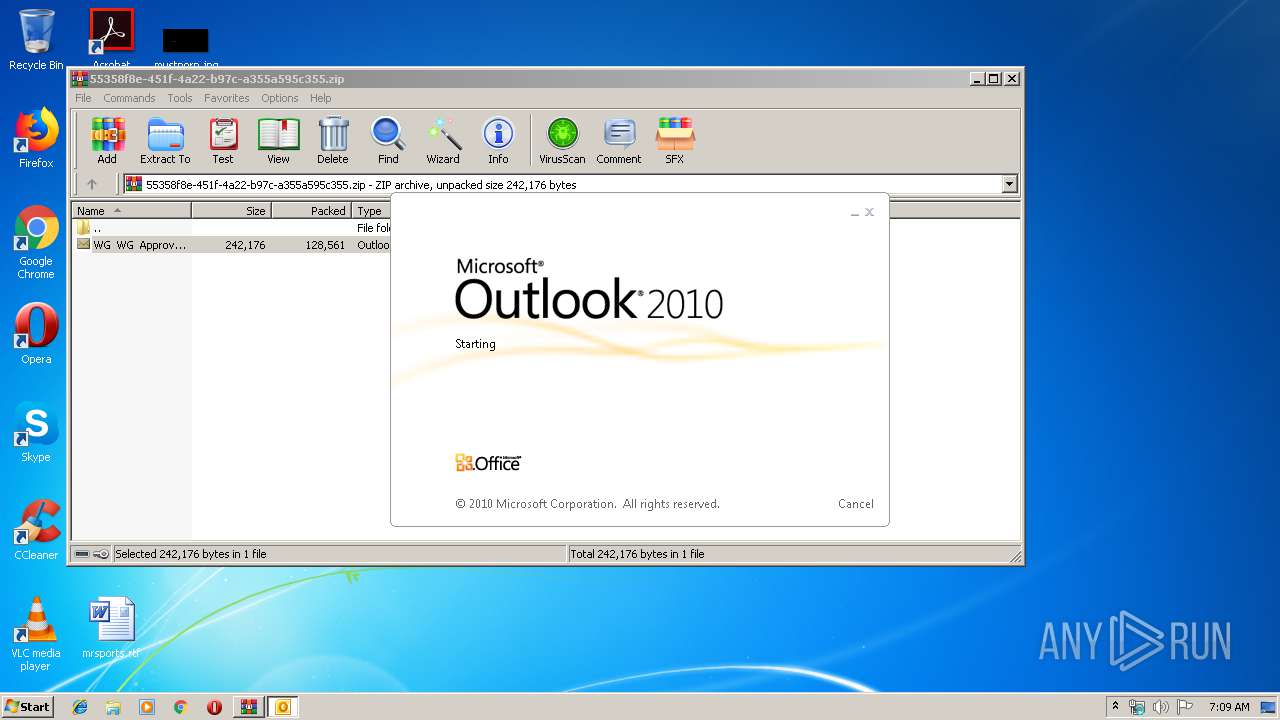
| File name: | WG WG Approval Question - DOA L1 Change - Germany Depts VIP & Belegschaftsgeschäft (New Approver Stephanie Reichelt) .zip |
| Full analysis: | https://app.any.run/tasks/281fb3f1-51c1-4ea0-a0a9-1c3c19358752 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 06:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B877B3333FFCE0B40B5F358AD8EB71B3 |
| SHA1: | F17C2AD6FF017A6A8CB675401CFB9237B415DC5A |
| SHA256: | D443A2322784A0681A884EB51CDC936D9549396C70CD8A65CB085922E0BFCDD7 |
| SSDEEP: | 3072:lkZcvsfiKZZQQ3wKyUyBbDTpasKkTHwZmmDxtKl:lkZDiuzwRU6fI7kz7D |
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3388)
- OUTLOOK.EXE (PID: 2700)
- WINWORD.EXE (PID: 3128)
Application was dropped or rewritten from another process
- 848.exe (PID: 3244)
- 848.exe (PID: 2728)
- 848.exe (PID: 2844)
- easywindow.exe (PID: 2416)
- 848.exe (PID: 3720)
- easywindow.exe (PID: 3328)
- easywindow.exe (PID: 3576)
- easywindow.exe (PID: 3420)
Emotet process was detected
- 848.exe (PID: 3720)
SUSPICIOUS
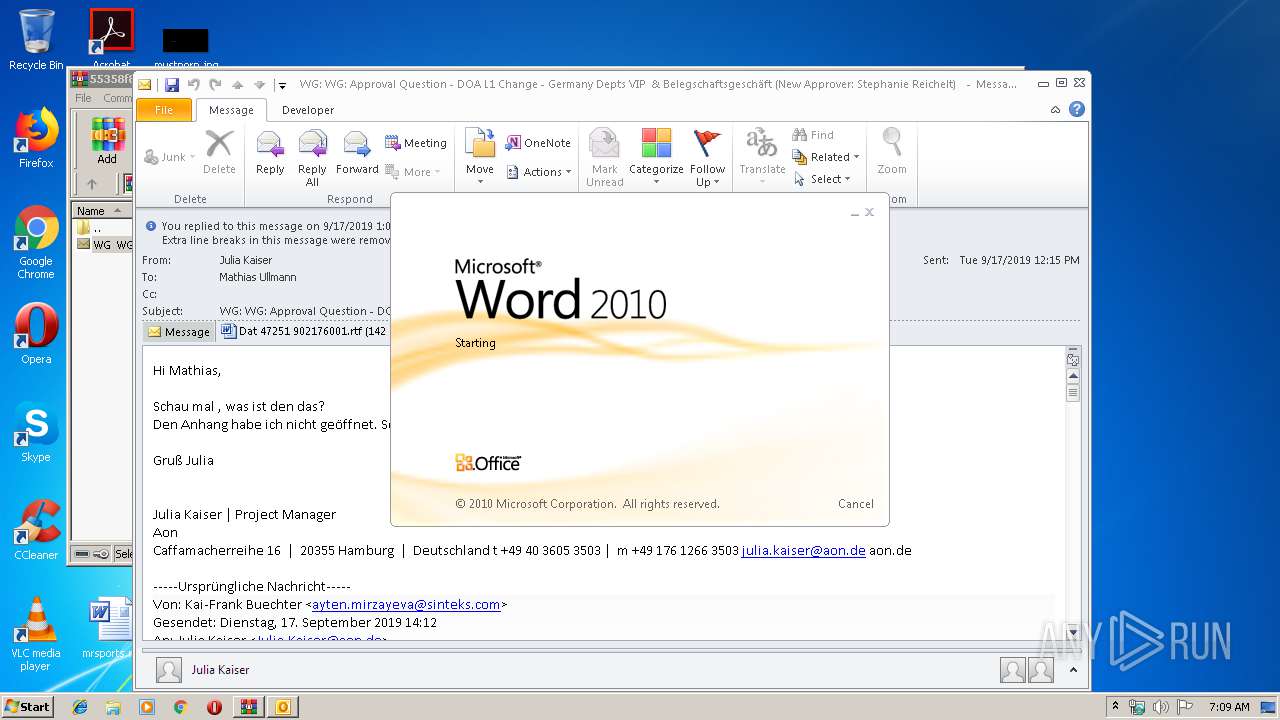
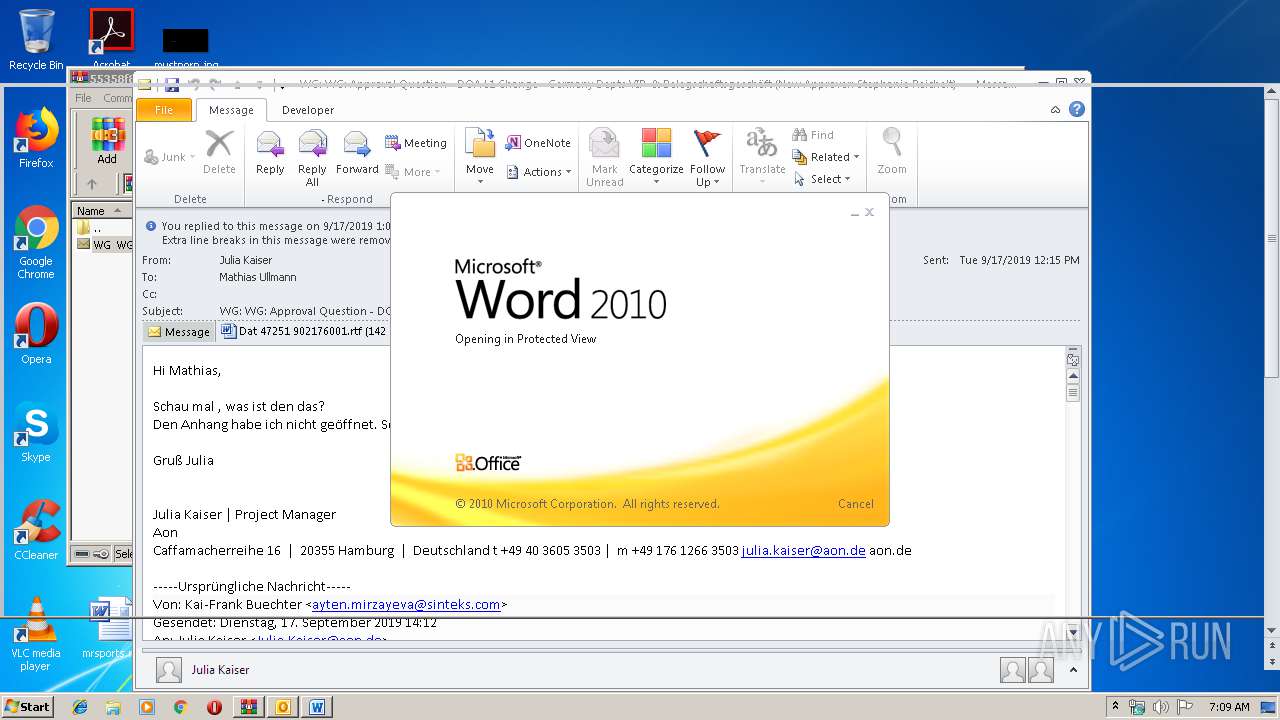
Starts Microsoft Office Application
- WinRAR.exe (PID: 3388)
- OUTLOOK.EXE (PID: 2700)
- WINWORD.EXE (PID: 3128)
Application launched itself
- WINWORD.EXE (PID: 3128)
- 848.exe (PID: 2844)
- easywindow.exe (PID: 3328)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2700)
- powershell.exe (PID: 3424)
Executed via WMI
- powershell.exe (PID: 3424)
PowerShell script executed
- powershell.exe (PID: 3424)
Executable content was dropped or overwritten
- powershell.exe (PID: 3424)
- 848.exe (PID: 3720)
Starts itself from another location
- 848.exe (PID: 3720)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3128)
- WINWORD.EXE (PID: 2736)
- OUTLOOK.EXE (PID: 2700)
Creates files in the user directory
- WINWORD.EXE (PID: 3128)
Reads settings of System Certificates
- powershell.exe (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
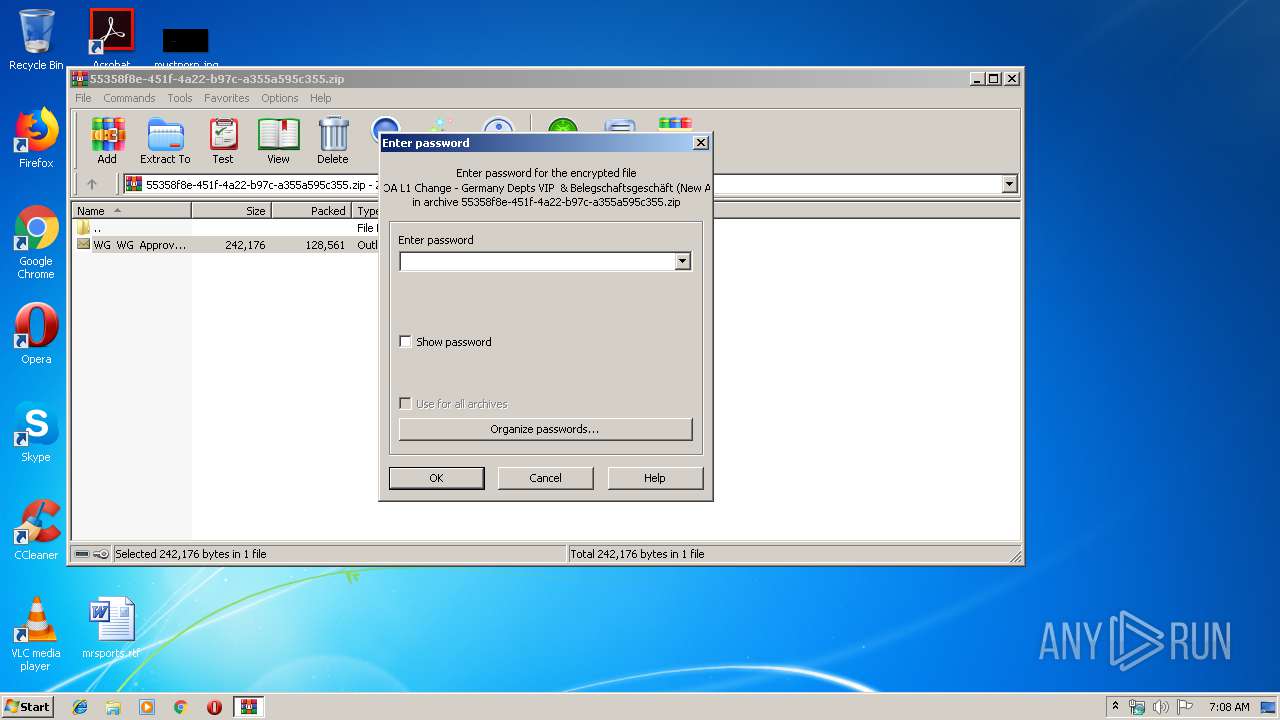
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:09:18 08:15:29 |
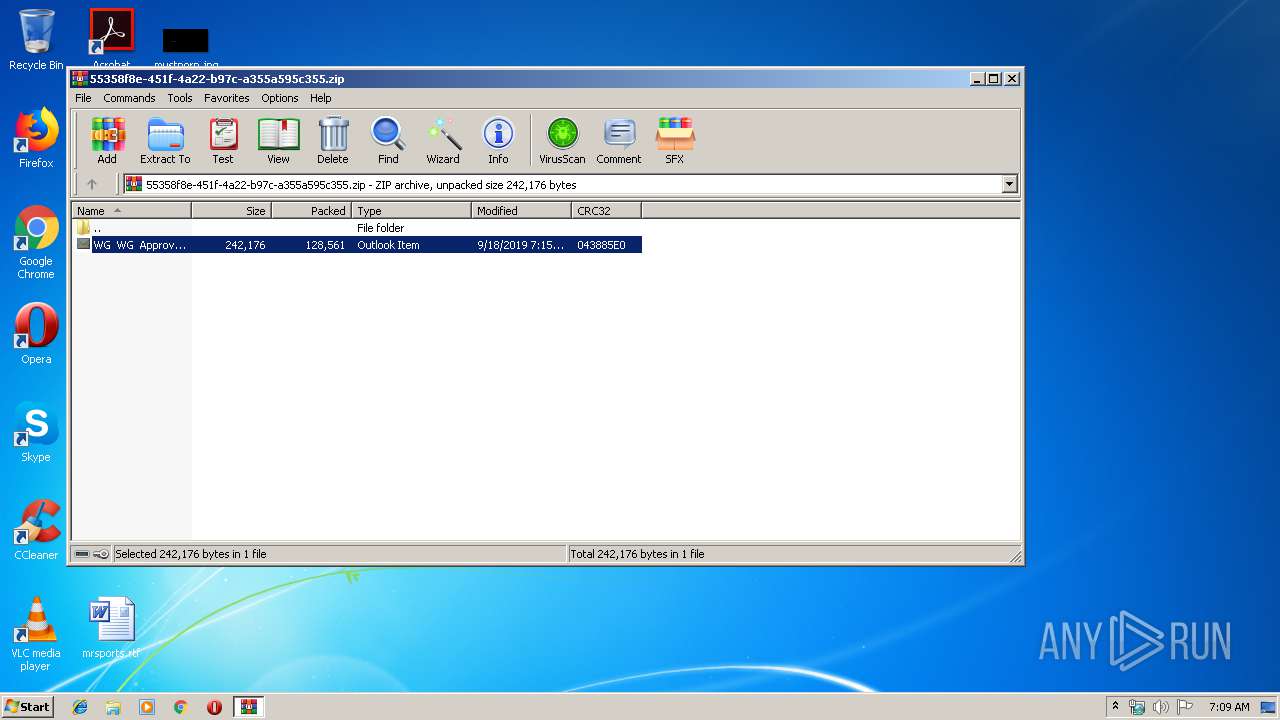
| ZipCRC: | 0x043885e0 |
| ZipCompressedSize: | 128561 |
| ZipUncompressedSize: | 242176 |
| ZipFileName: | WG WG Approval Question - DOA L1 Change - Germany Depts VIP & Belegschaftsgesch?ft (New Approver Stephanie Reichelt) .msg |
Total processes
48
Monitored processes
13
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2416 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
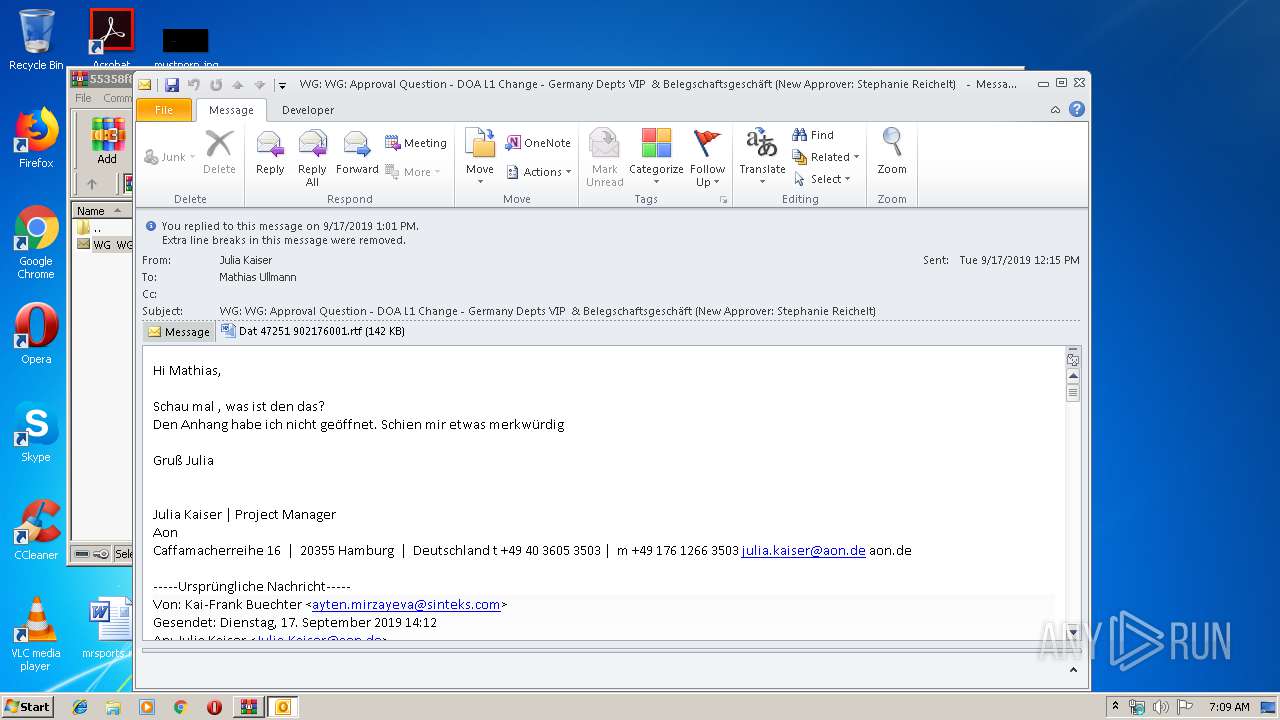
| 2700 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb3388.33231\WG WG Approval Question - DOA L1 Change - Germany Depts VIP & Belegschaftsgeschäft (New Approver Stephanie Reichelt) .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\848.exe" | C:\Users\admin\848.exe | — | 848.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2844 | --d2d5e0ba | C:\Users\admin\848.exe | — | 848.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
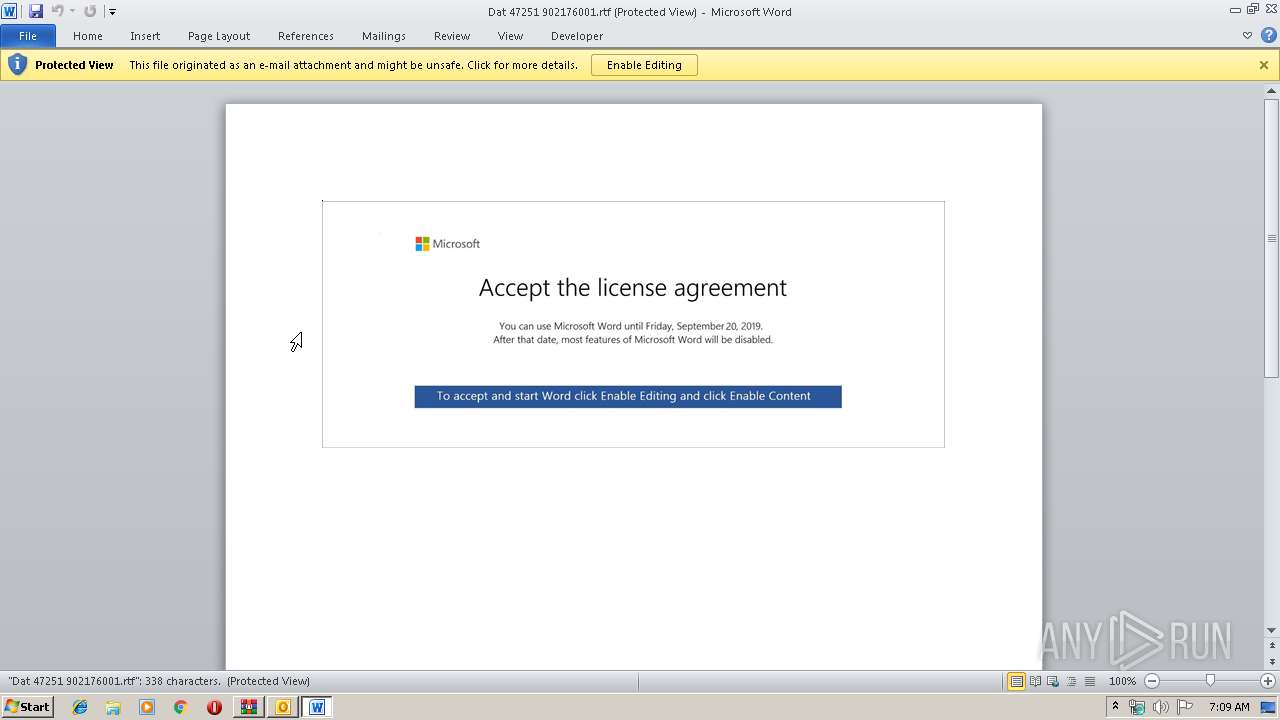
| 3128 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TZW9LR5T\Dat 47251 902176001.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\848.exe" | C:\Users\admin\848.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 848.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\55358f8e-451f-4a22-b97c-a355a595c355.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3420 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 816
Read events
3 632
Write events
1 157
Delete events
27
Modification events
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\55358f8e-451f-4a22-b97c-a355a595c355.zip | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000006273F8B3B06ED501 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000CAFC01B4B06ED501 | |||
Executable files
2
Suspicious files
14
Text files
24
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF66B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2700 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TZW9LR5T\Dat 47251 902176001 (2).rtf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3128 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\B56F9FBB.rtf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\D9B1BA51.wmf | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\9E1A8187.wmf | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\5CAD6C2D.wmf | — | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\364DFBC3.wmf | — | |
MD5:— | SHA256:— | |||
| 3388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3388.33231\WG WG Approval Question - DOA L1 Change - Germany Depts VIP & Belegschaftsgeschäft (New Approver Stephanie Reichelt) .msg | msg | |
MD5:— | SHA256:— | |||
| 2736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BB4EC058-BE40-467B-B824-EB5F0B06D208.0\77B6ADC9.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2700 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3424 | powershell.exe | 47.92.157.172:443 | www.59055.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.59055.cn |
| unknown |