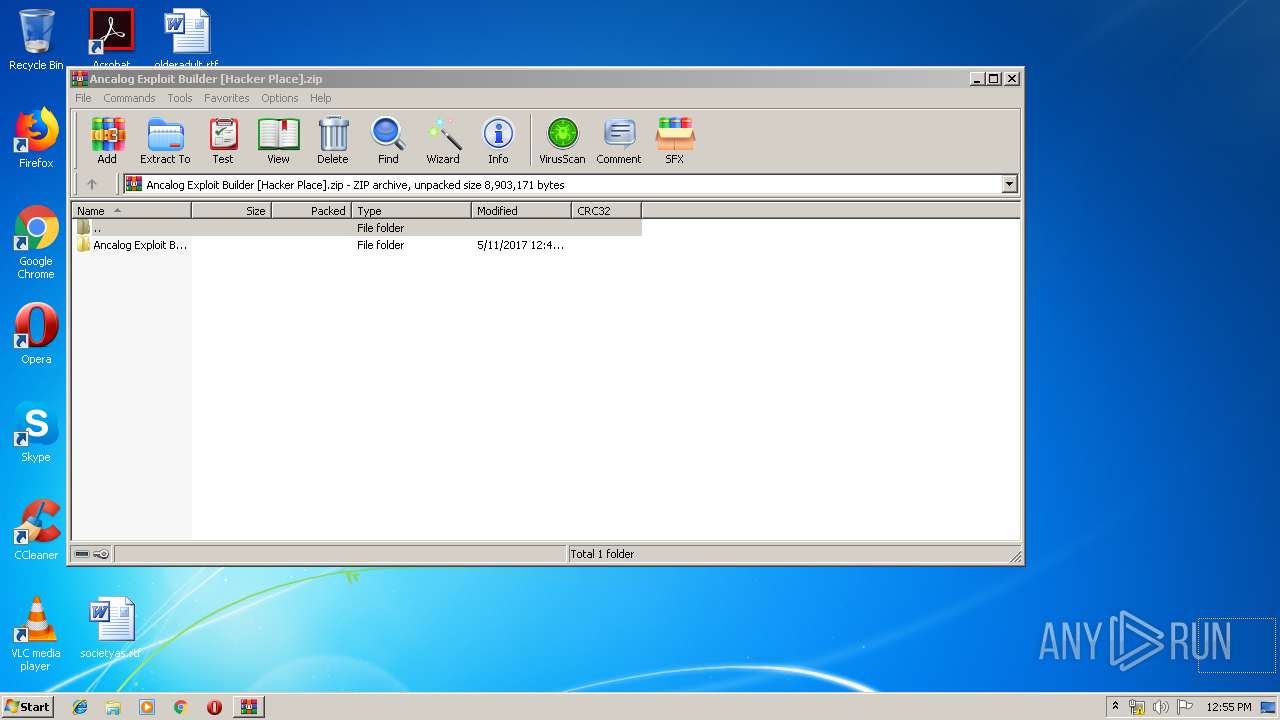
| File name: | Ancalog Exploit Builder [Hacker Place].zip |
| Full analysis: | https://app.any.run/tasks/9a108485-14a0-4839-840c-6621d4961783 |
| Verdict: | Suspicious activity |
| Analysis date: | June 22, 2019, 11:54:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CAFFC9501ECA369DA7F66D24C0650E36 |
| SHA1: | 619D054B8F0A346E7F3A7D51829A799B71C3515B |
| SHA256: | D4423CCC0780C2E5327F071EE45D97A338F4414D4C951DF883D66910C34D995D |
| SSDEEP: | 98304:dcZurFXRRbI+PoByZMWJPQONfbR1INaPWJA:dzrFXjHPSEHJPRZwNa+JA |
MALICIOUS
No malicious indicators.SUSPICIOUS
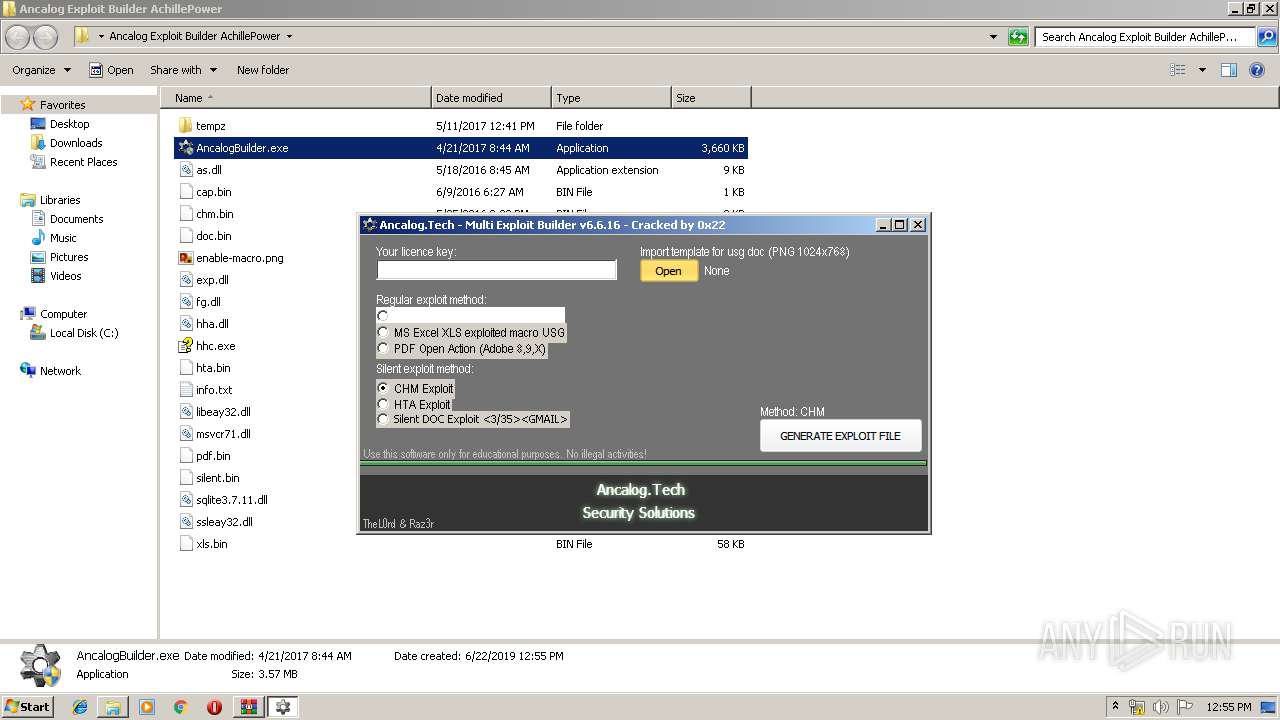
Reads Internet Cache Settings
- AncalogBuilder.exe (PID: 3728)
Executed via COM
- DllHost.exe (PID: 1720)
INFO
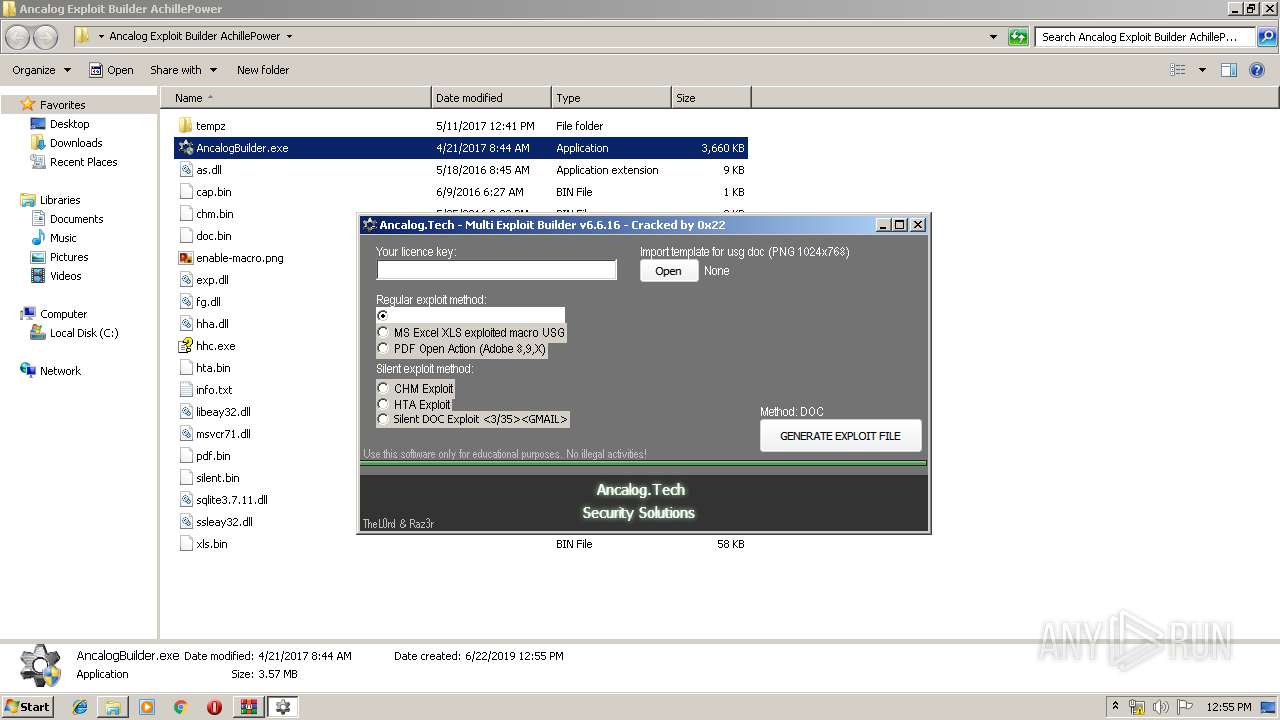
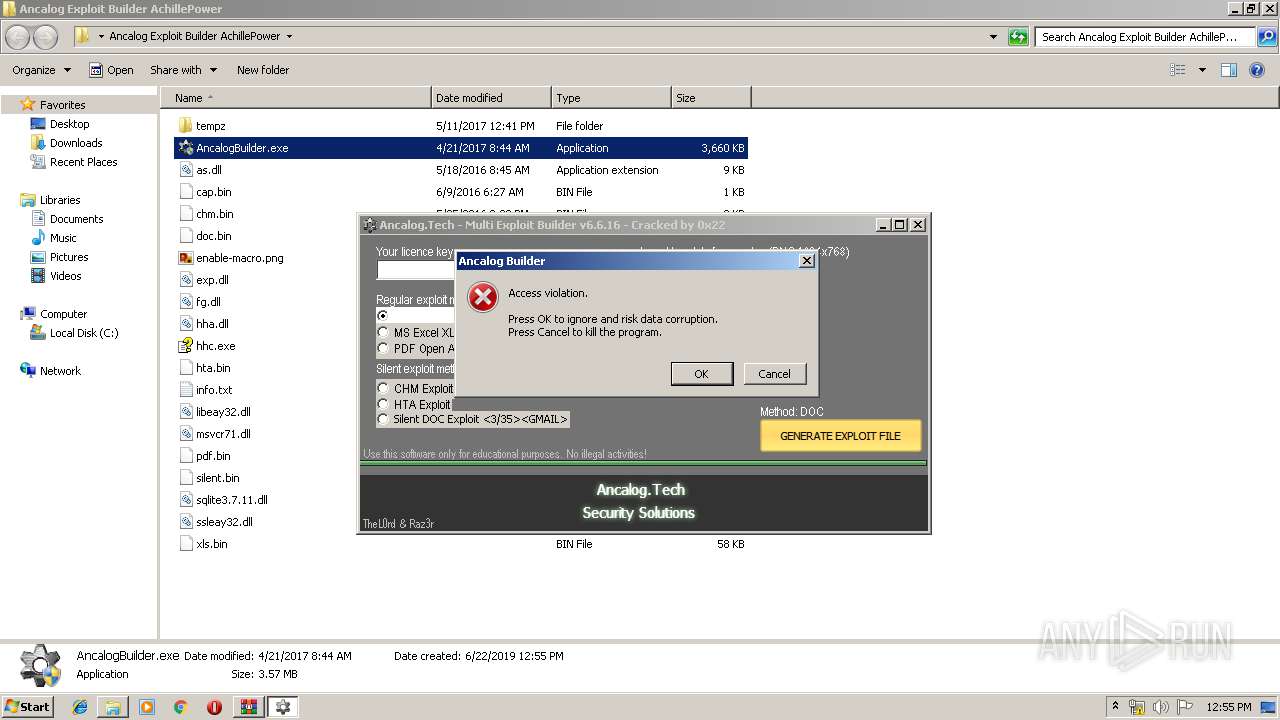
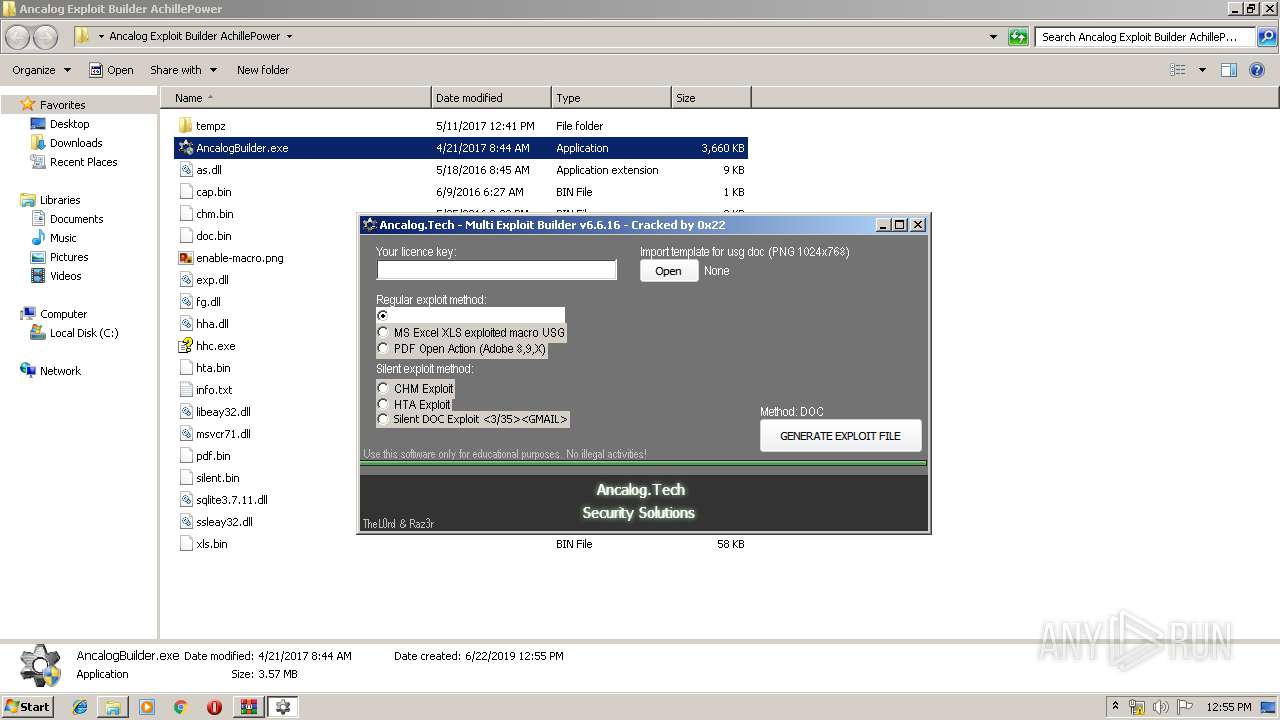
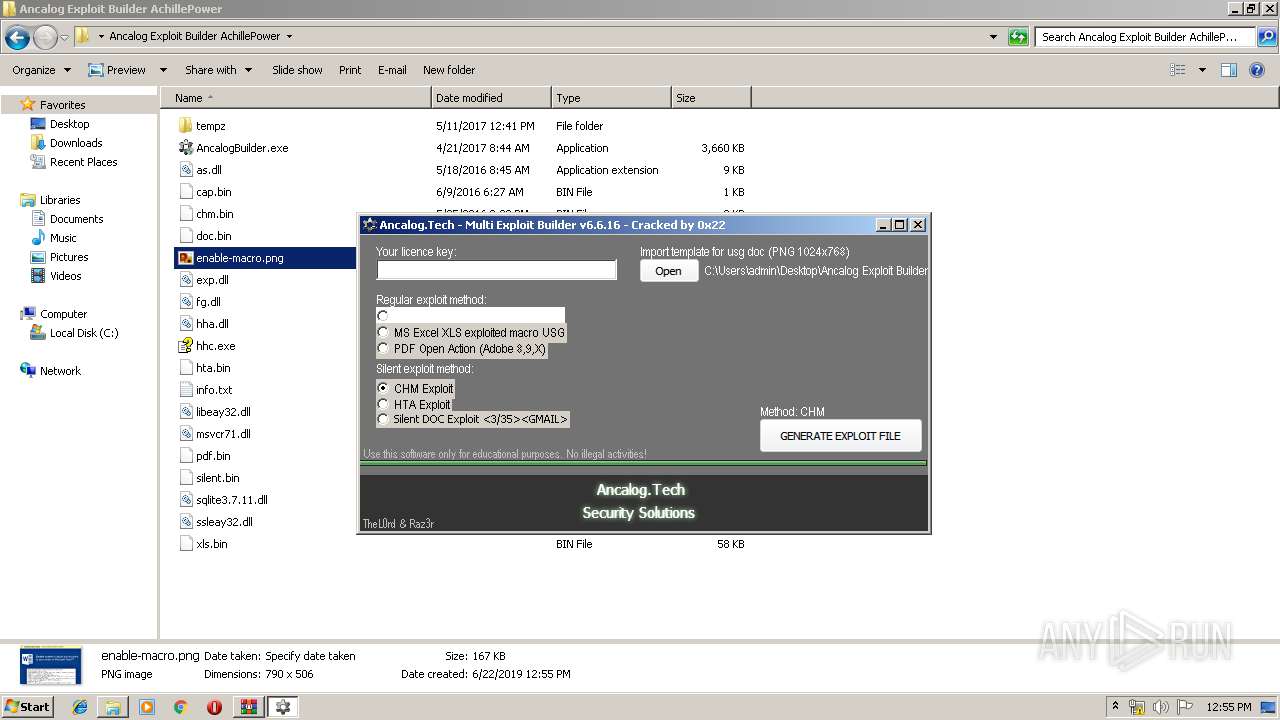
Manual execution by user
- AncalogBuilder.exe (PID: 3728)
- hhc.exe (PID: 920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
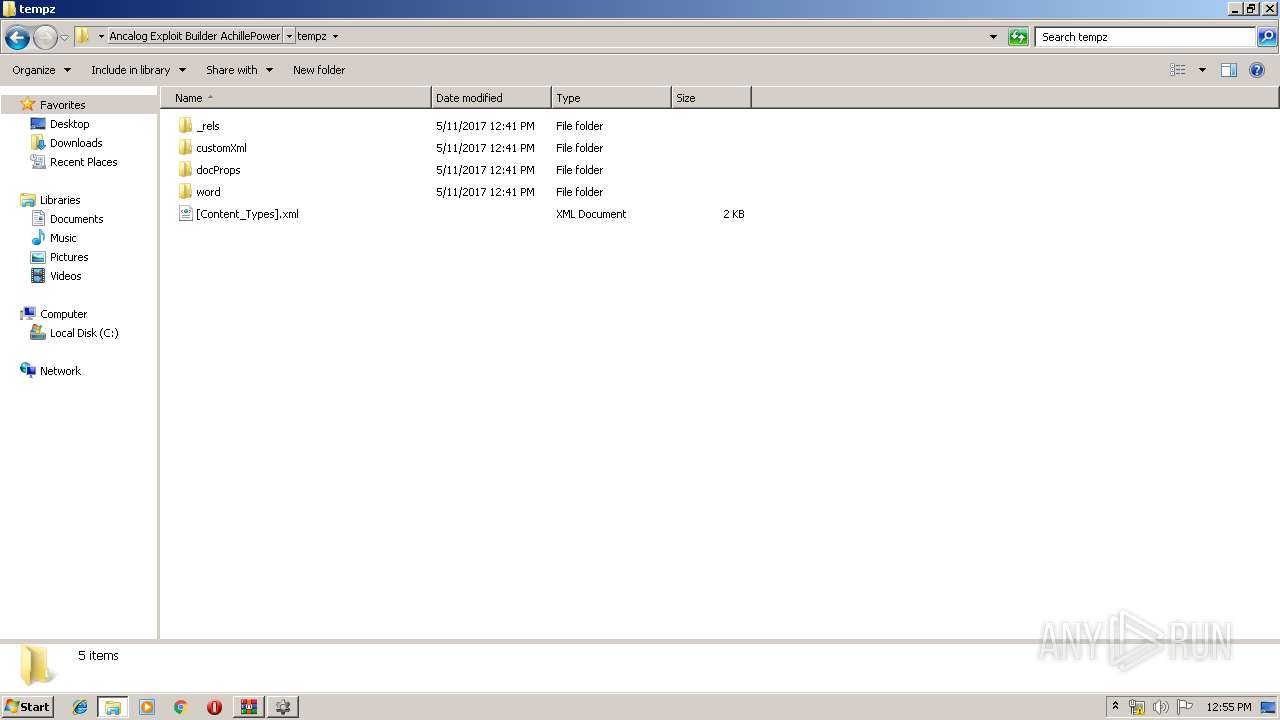
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2017:05:11 14:41:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
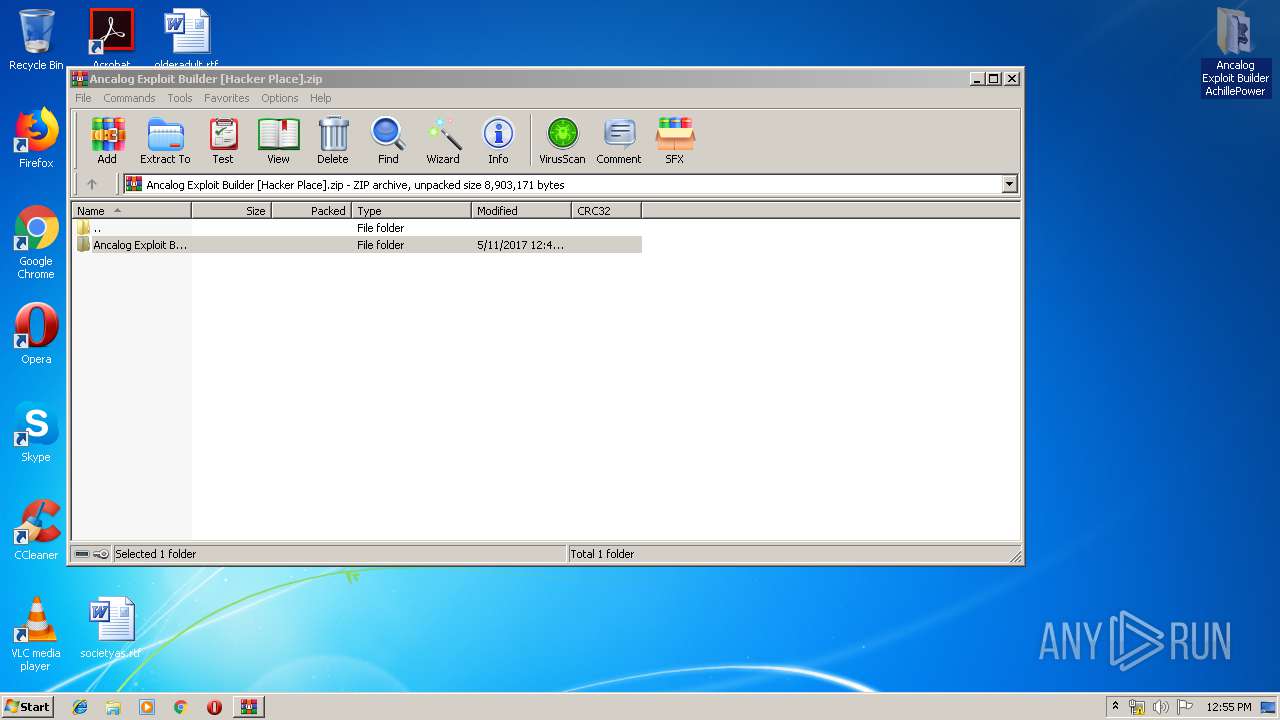
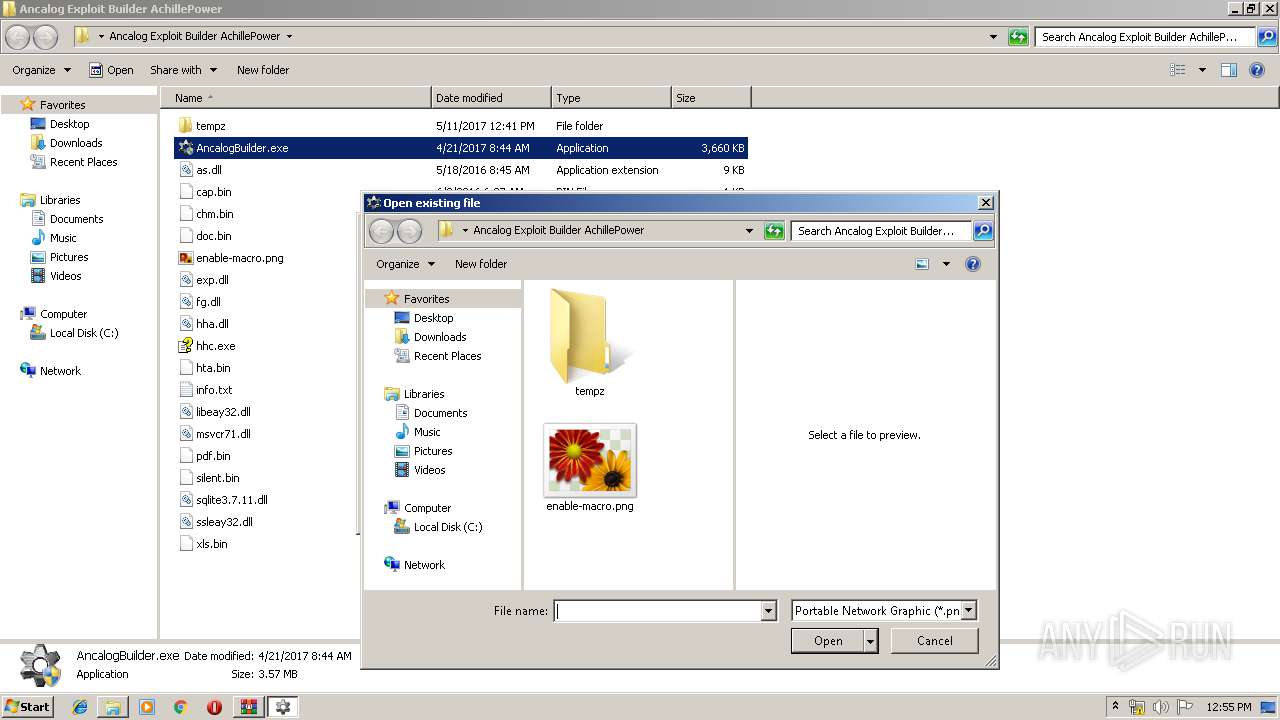
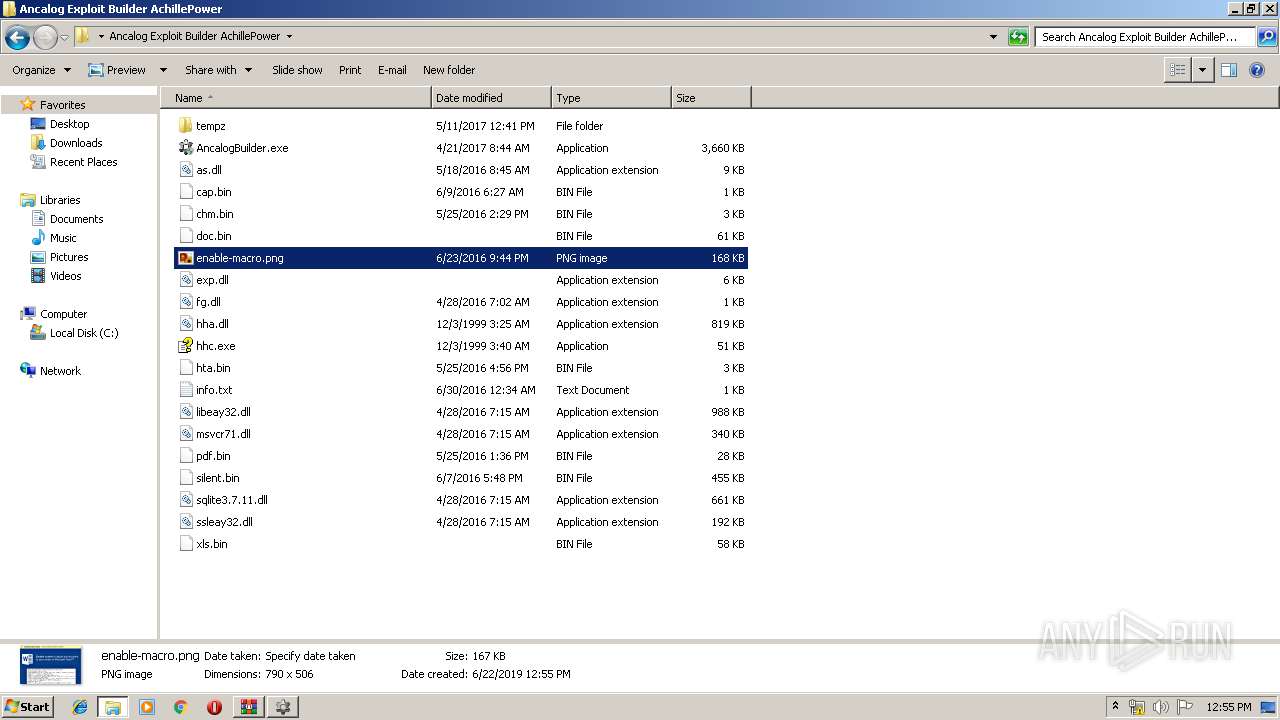
| ZipFileName: | Ancalog Exploit Builder AchillePower/ |
Total processes
42
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
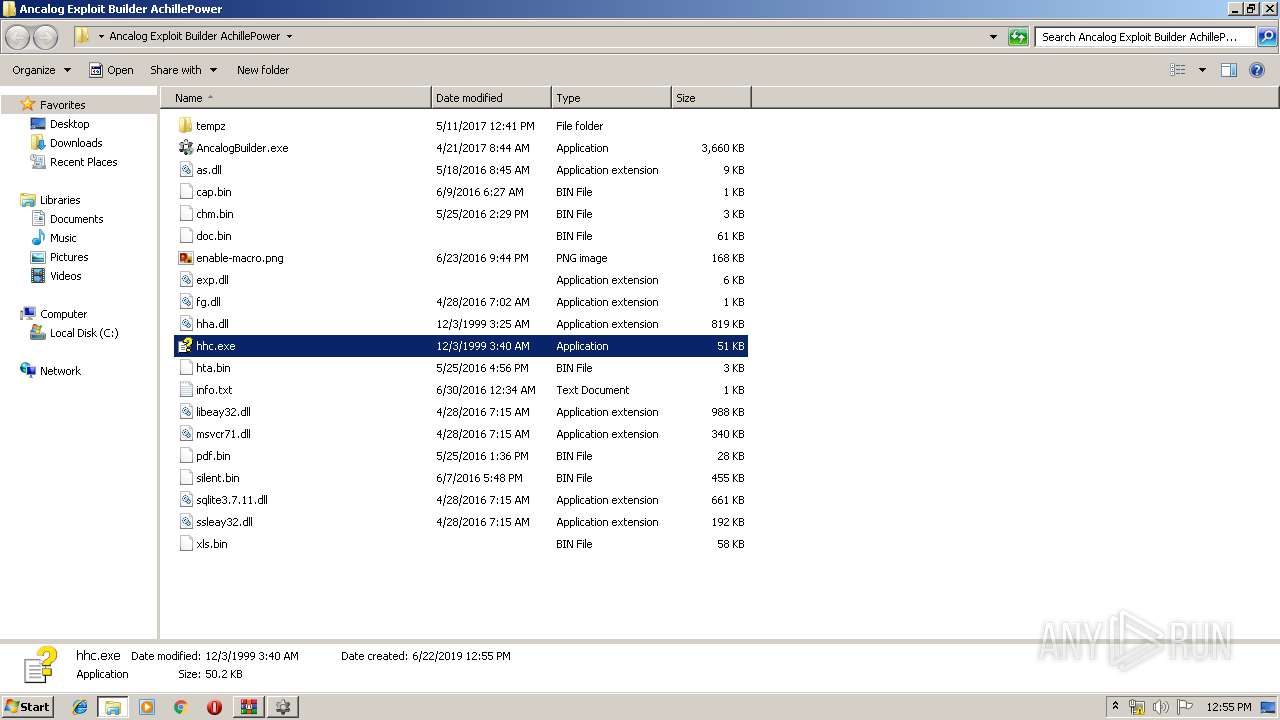
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Users\admin\Desktop\Ancalog Exploit Builder AchillePower\hhc.exe" | C:\Users\admin\Desktop\Ancalog Exploit Builder AchillePower\hhc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Compiler Exit code: 24 Version: 4.74.8702 Modules
| |||||||||||||||
| 1720 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
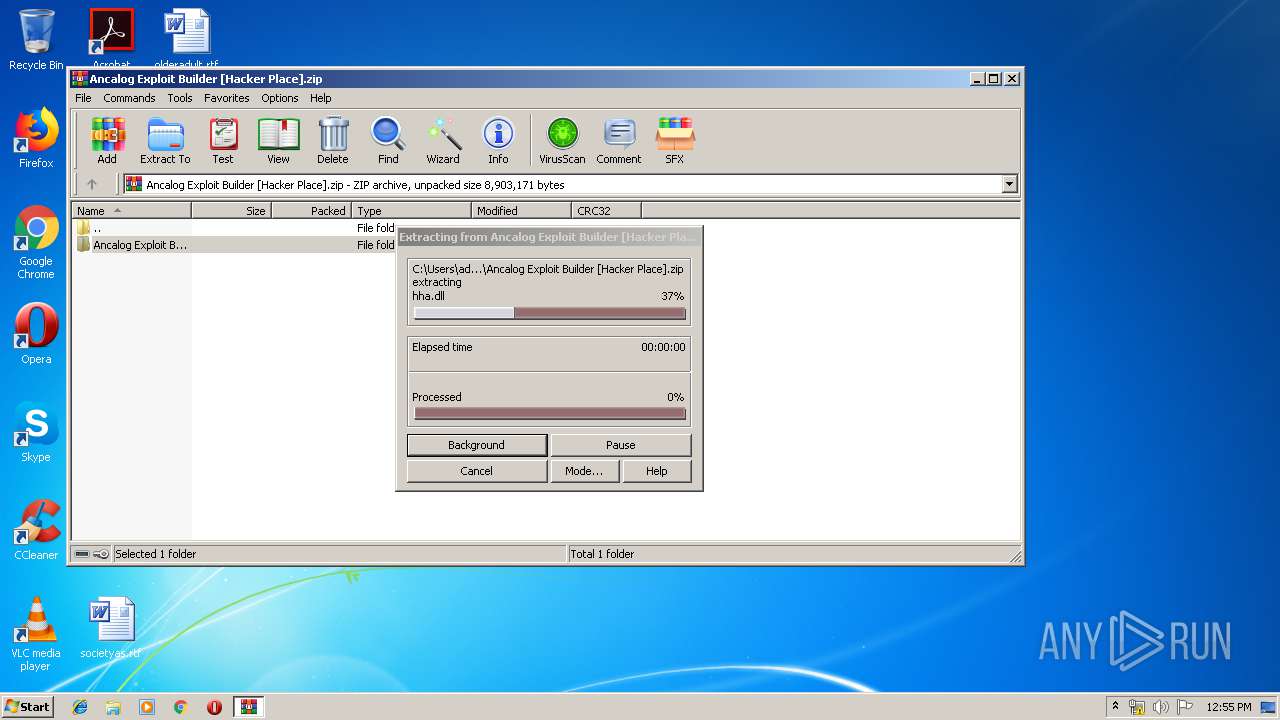
| 3136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ancalog Exploit Builder [Hacker Place].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
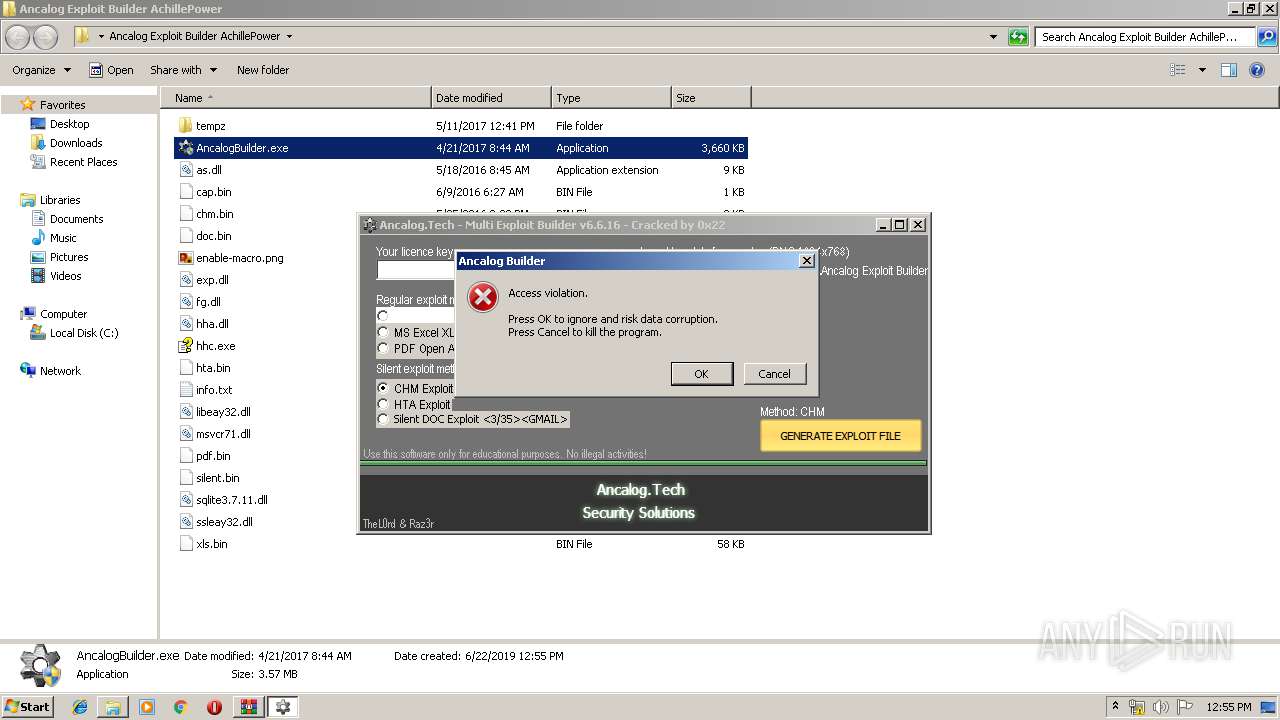
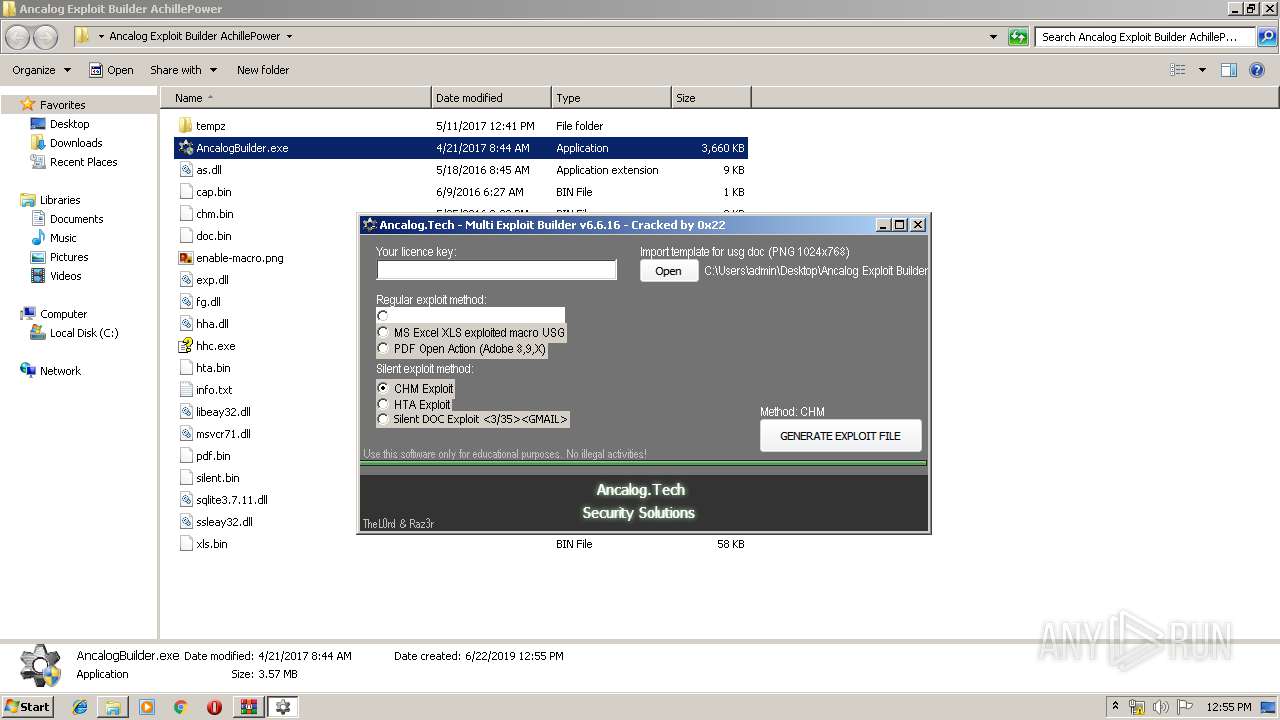
| 3728 | "C:\Users\admin\Desktop\Ancalog Exploit Builder AchillePower\AncalogBuilder.exe" | C:\Users\admin\Desktop\Ancalog Exploit Builder AchillePower\AncalogBuilder.exe | explorer.exe | ||||||||||||
User: admin Company: ancalog.tech Integrity Level: HIGH Description: Ancalog Multi Exploit Builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 065
Read events
995
Write events
69
Delete events
1
Modification events
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ancalog Exploit Builder [Hacker Place].zip | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3728) AncalogBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3728) AncalogBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 080000000100000000000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
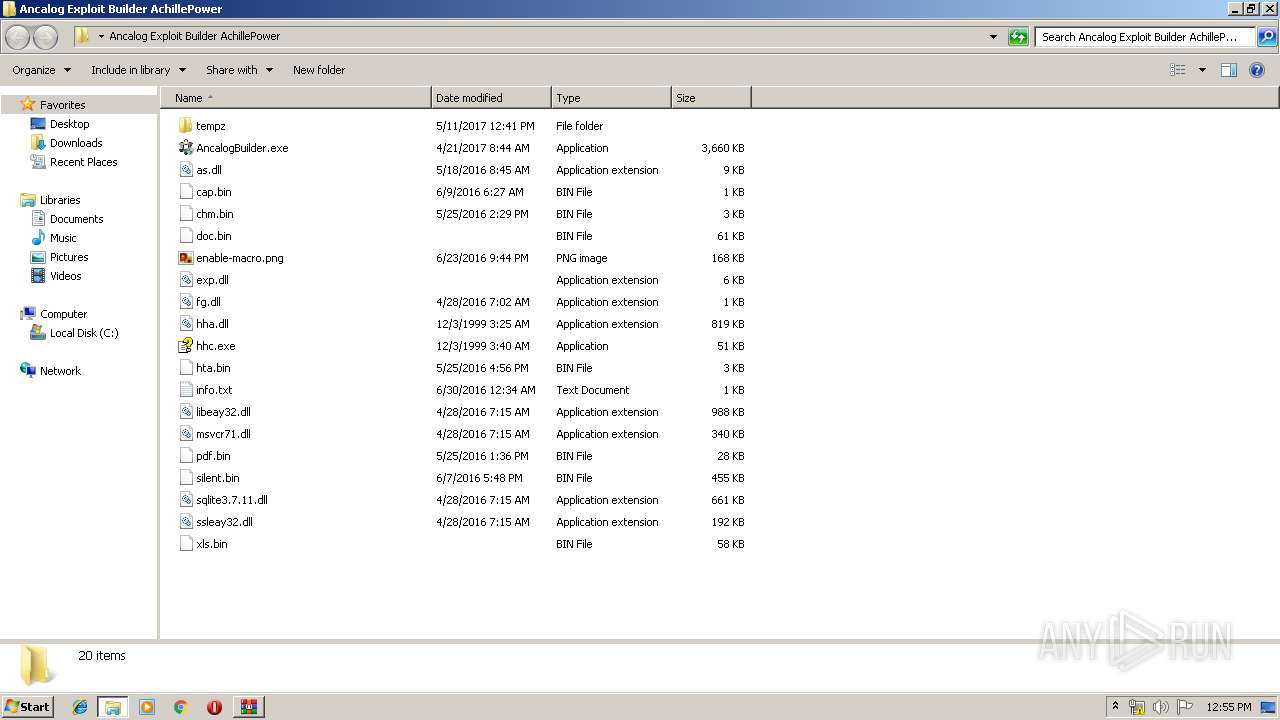
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\AncalogBuilder.exe | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\as.dll | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\cap.bin | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\chm.bin | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\doc.bin | — | |
MD5:— | SHA256:— | |||
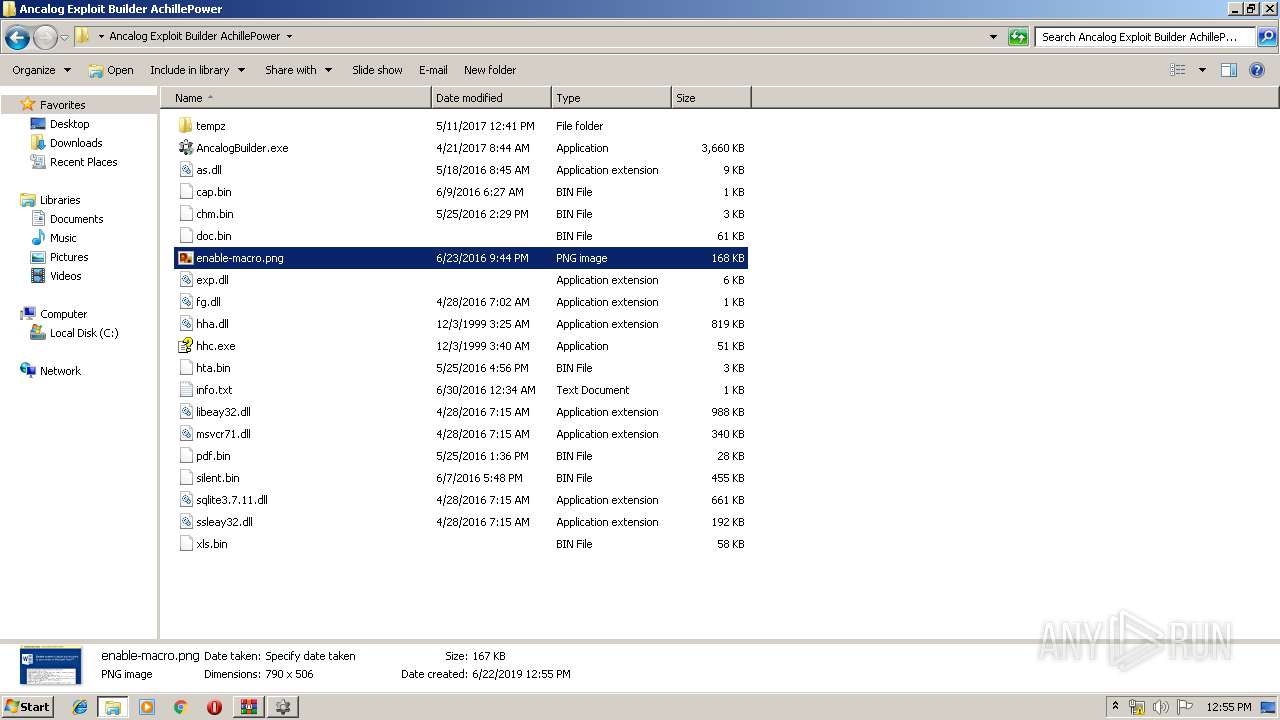
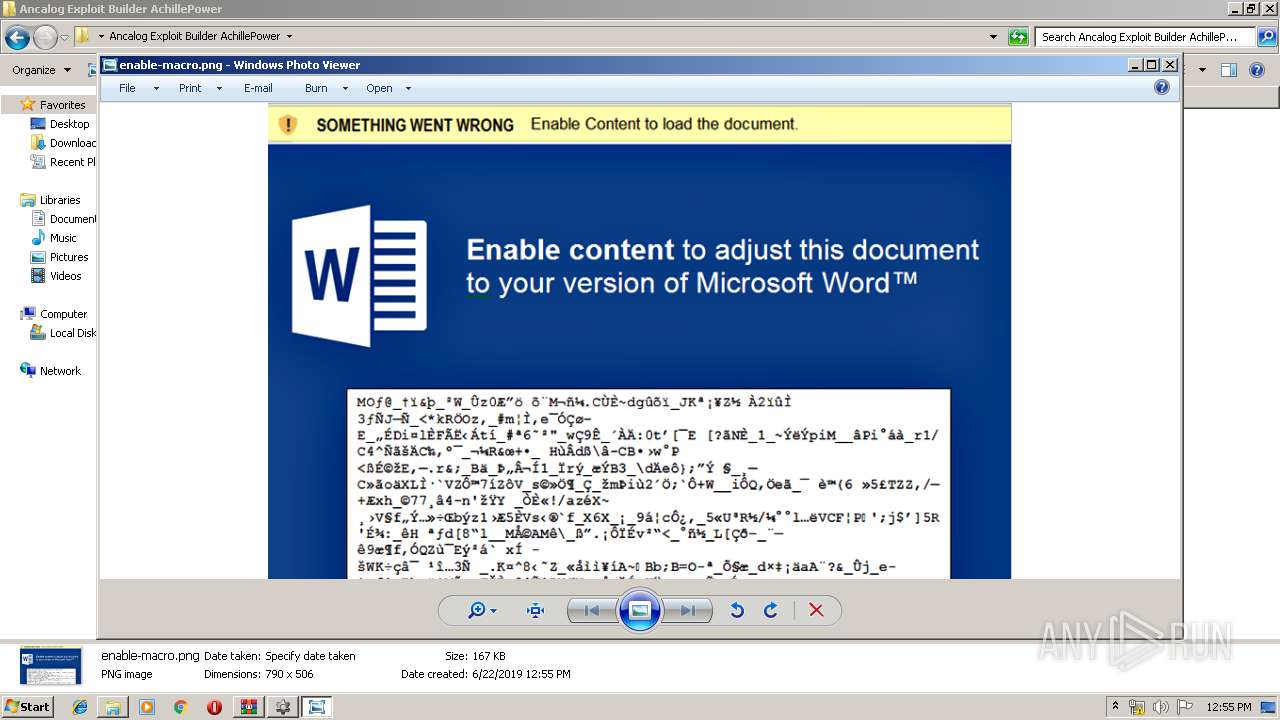
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\enable-macro.png | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\exp.dll | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\fg.dll | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\hha.dll | — | |
MD5:— | SHA256:— | |||
| 3136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3136.1685\Ancalog Exploit Builder AchillePower\hhc.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report