| File name: | hmpalert.dll |
| Full analysis: | https://app.any.run/tasks/5ec54332-769a-4f88-9389-b8c38724d528 |
| Verdict: | No threats detected |
| Analysis date: | July 04, 2019, 03:04:19 |
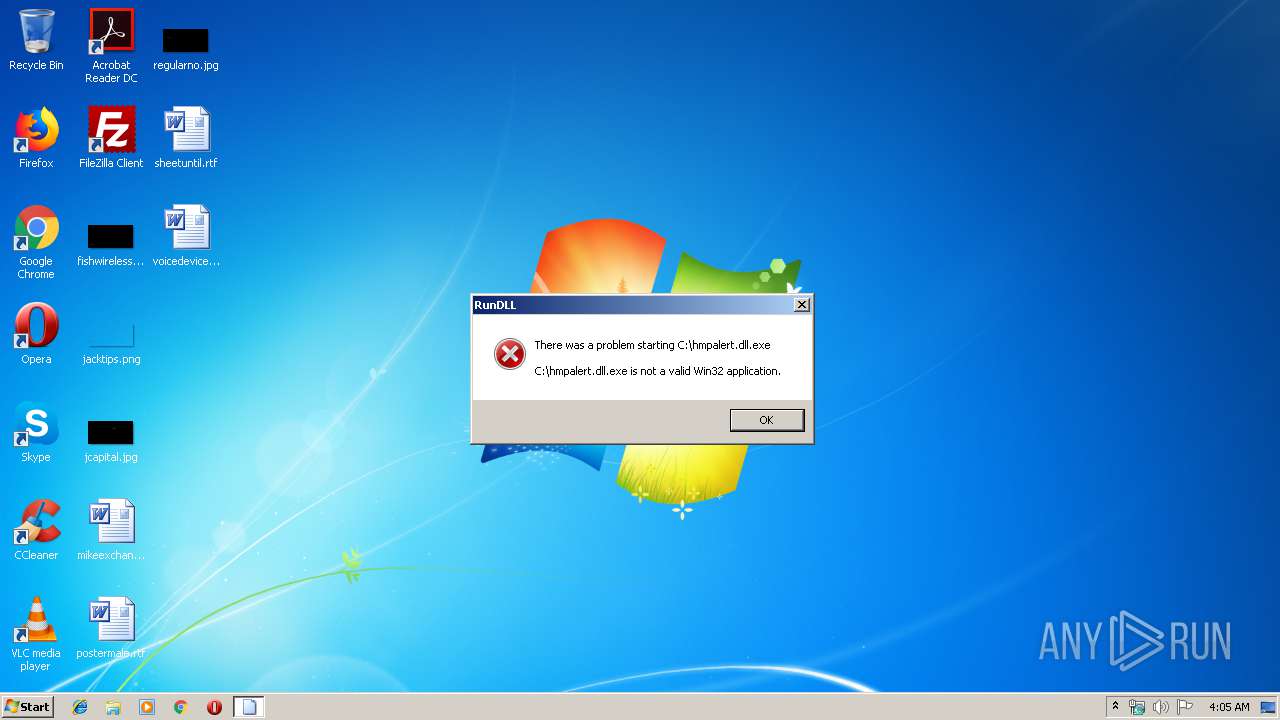
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (GUI) x86-64, for MS Windows |
| MD5: | EB4EA1ACBAE5EA4EF60B3CBB8BAF8EC8 |
| SHA1: | F8AD9ED45430E7E510E260CA7EF268EF995028C2 |
| SHA256: | D4391F86C86A3D0414956579743753666A603A7669565D1338A3561D1A831216 |
| SSDEEP: | 12288:5XuZwH6F3nkcPCX8h7VOI7JRd83wbLq+fkzAEngONqnXqYo5l/vvnpMGoKD9S/nZ:sHfX7URIYzAEngON+XjYpMQD9SvjdP |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:03:22 17:13:30+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 14.12 |
| CodeSize: | 670208 |
| InitializedDataSize: | 420352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b090 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.12.507 |
| ProductVersionNumber: | 3.7.12.507 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
| CompanyName: | SurfRight B.V. |
| FileVersion: | 3.7.12.507 |
| FileDescription: | HitmanPro.Alert 64-bit Support Library |
| OriginalFileName: | hmpalert_x64.dll |
| InternalName: | hmpalert.dll |
| LegalCopyright: | © 2013-2018 SurfRight, A Sophos Company |
| ProductName: | HitmanPro.Alert |
| ProductVersion: | 3.7.12.507 |
| Comments: | Incorporates Threatstar Exploit Mitigation Platform (EMP) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Mar-2019 16:13:30 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | SurfRight B.V. |
| FileVersion: | 3.7.12.507 |
| FileDescription: | HitmanPro.Alert 64-bit Support Library |
| OriginalFilename: | hmpalert_x64.dll |
| InternalName: | hmpalert.dll |
| LegalCopyright: | © 2013-2018 SurfRight, A Sophos Company |
| ProductName: | HitmanPro.Alert |
| ProductVersion: | 3.7.12.507 |
| Comments: | Incorporates Threatstar Exploit Mitigation Platform (EMP) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 7 |
| Time date stamp: | 22-Mar-2019 16:13:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A3875 | 0x000A3A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47434 |
.rdata | 0x000A5000 | 0x00038A20 | 0x00038C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.48766 |
.data | 0x000DE000 | 0x00015880 | 0x0000BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.45806 |
.pdata | 0x000F4000 | 0x00007C50 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.91802 |
.wo | 0x000FC000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000FD000 | 0x0000F770 | 0x0000F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97821 |
.reloc | 0x0010D000 | 0x00000B94 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.38014 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52877 | 976 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
300 | 7.99669 | 61740 | UNKNOWN | English - United States | RT_RCDATA |
Imports
KERNEL32.dll |
dbghelp.dll (delay-loaded) |
Exports
Title | Ordinal | Address |
|---|---|---|
A1 | 1 | 0x00038BC0 |
A2 | 2 | 0x00038BC0 |
A3 | 3 | 0x00038BC0 |
CVCCP | 4 | 0x000181C0 |
GetModuleHandleA | 5 | 0x00038B60 |
GetModuleHandleW | 6 | 0x00038B90 |
GetProcAddress | 7 | 0x00038B10 |
LoadLibraryA | 8 | 0x00038AB0 |
LoadLibraryW | 9 | 0x00038AE0 |
VirtualAlloc | 10 | 0x00038910 |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3232 | "C:\Windows\System32\rundll32.exe" "C:\hmpalert.dll.exe", A1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report