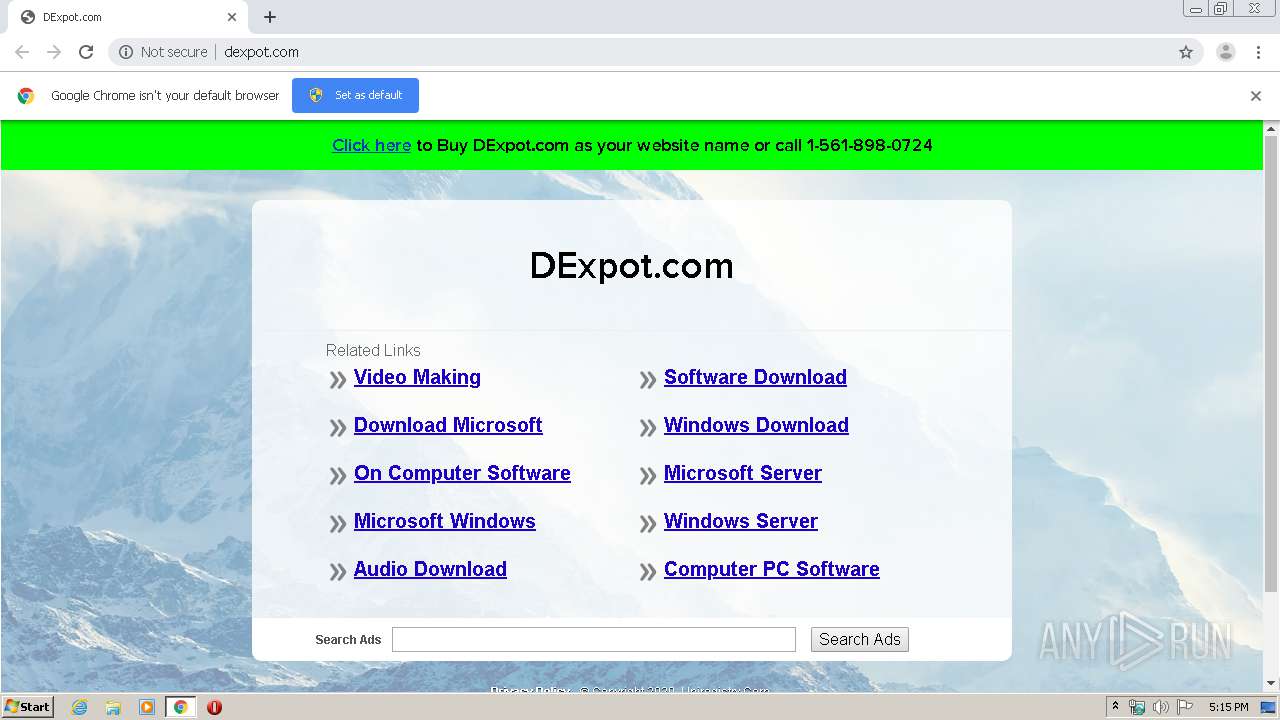
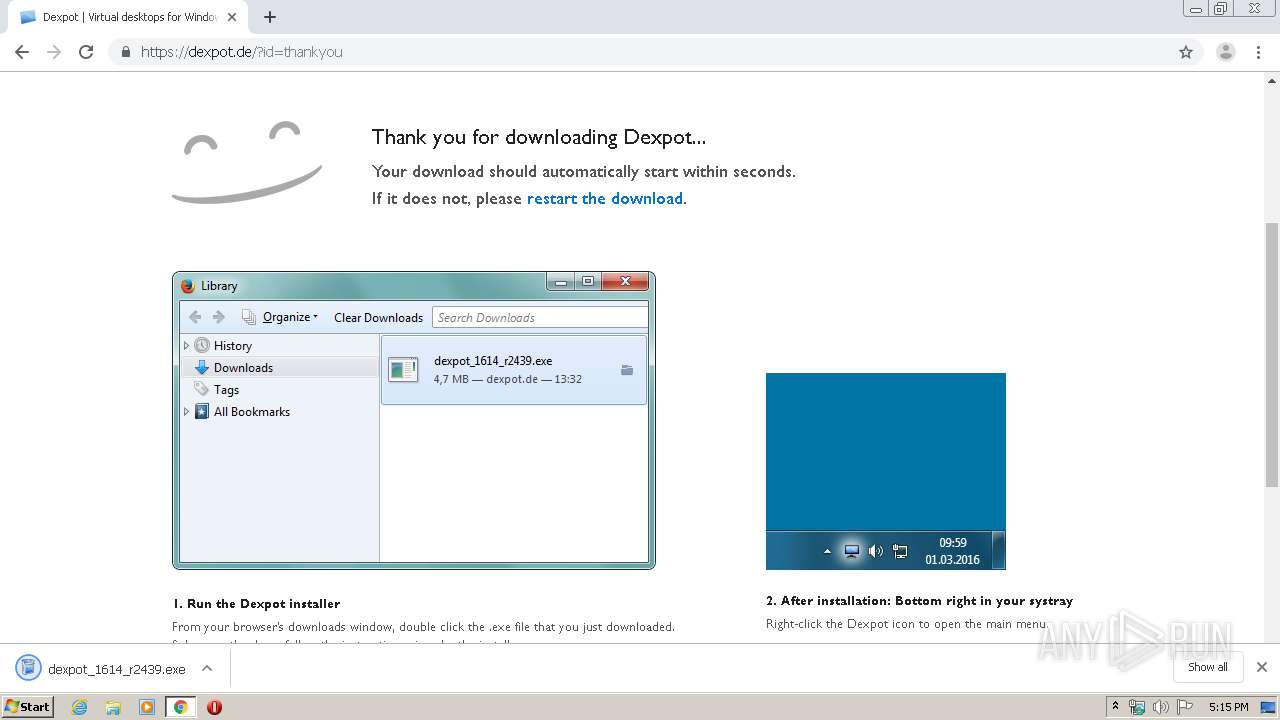
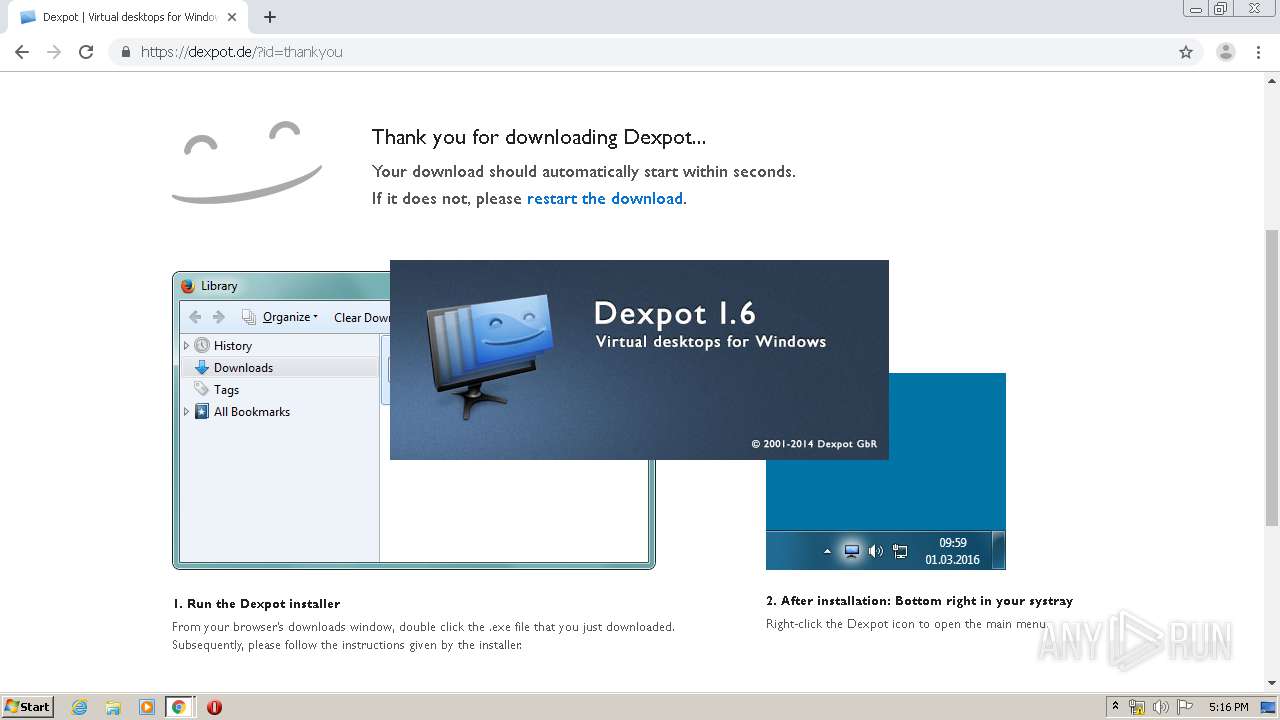
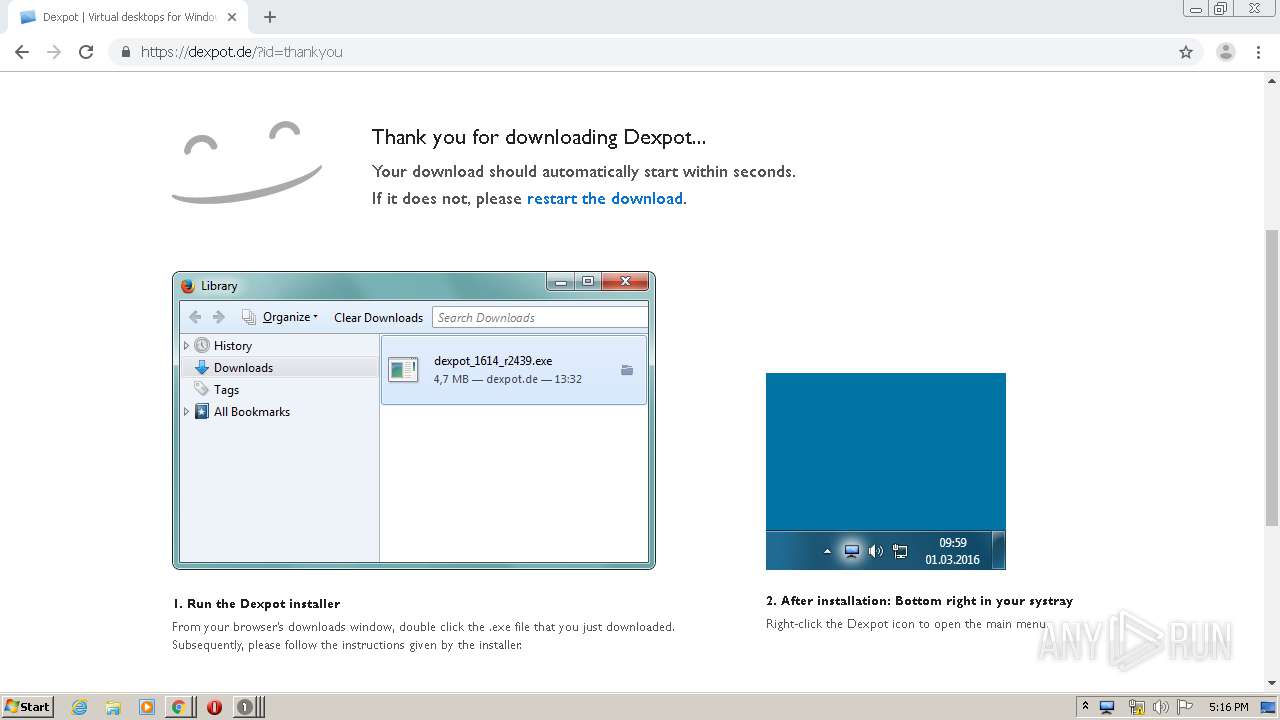
| URL: | http://dexpot.com |
| Full analysis: | https://app.any.run/tasks/5a62a457-fa62-472a-8fef-f6a7c2c7d3b9 |
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2020, 17:14:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E3E9A4A11EE7A52D3356AB93BB03B36D |
| SHA1: | 23BDDE8CA656BB76947390D03C9D2B6F7C9A1F9A |
| SHA256: | D4285CB9FE8300F1AD012A77A4F950DD5662F710CC7E7EA77C191C76F42F38A1 |
| SSDEEP: | 3:N1KaAd1Tn:Cakn |
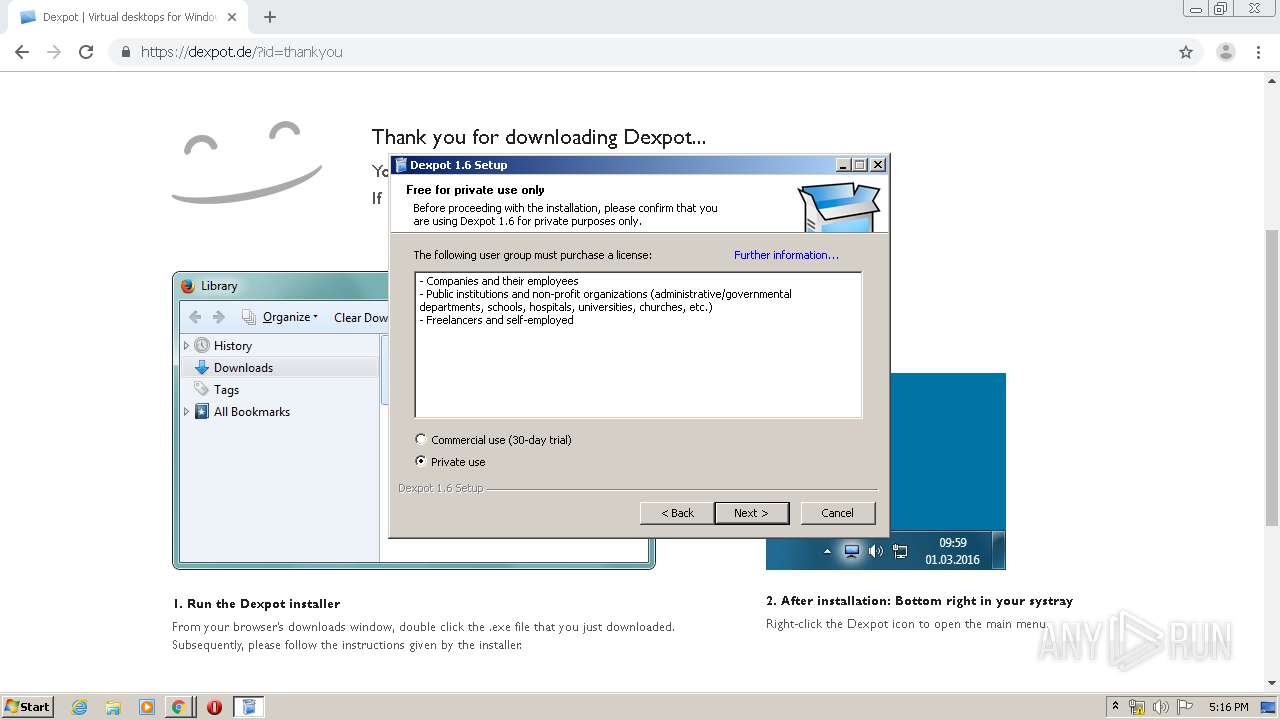
MALICIOUS
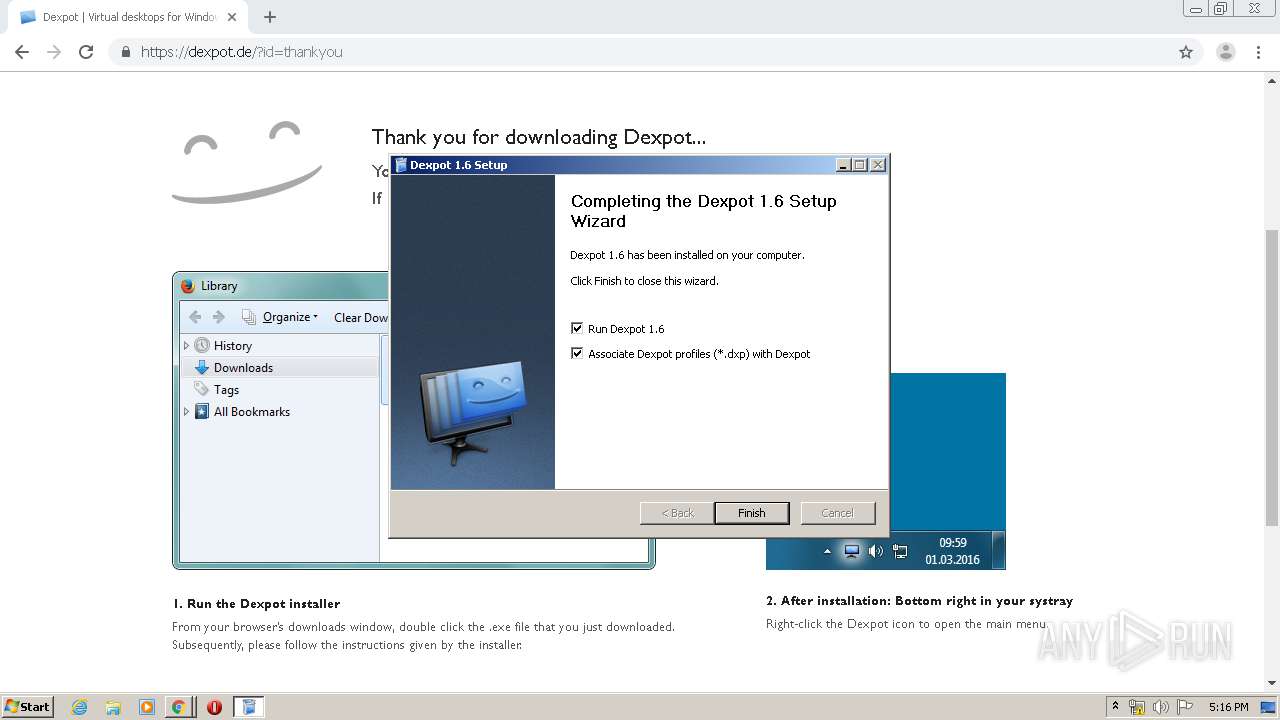
Application was dropped or rewritten from another process
- dexpot_1614_r2439.exe (PID: 680)
- dexpot_1614_r2439.exe (PID: 340)
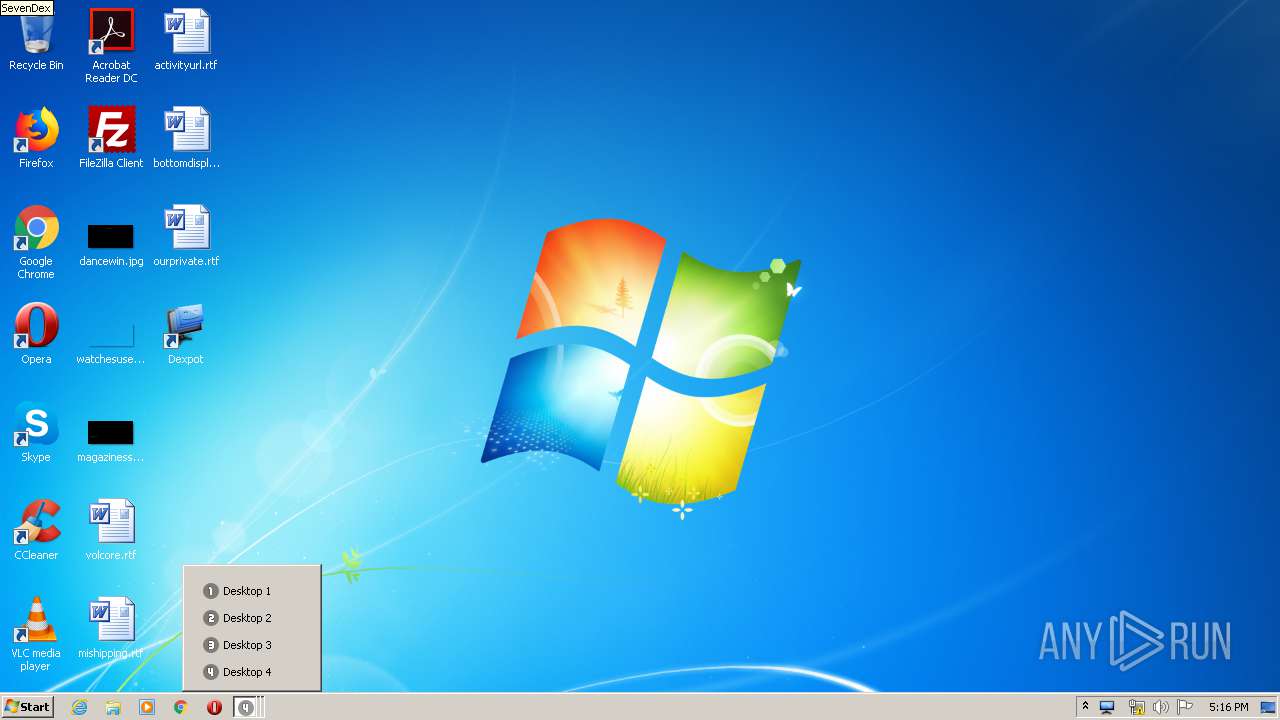
- dexpot.exe (PID: 2336)
- SevenDex.exe (PID: 2376)
Loads dropped or rewritten executable
- dexpot_1614_r2439.exe (PID: 340)
- dexpot_1614_r2439.exe (PID: 680)
- dexpot.exe (PID: 2336)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 1524)
- taskhost.exe (PID: 1968)
- taskeng.exe (PID: 1984)
- ctfmon.exe (PID: 652)
- SevenDex.exe (PID: 2376)
- explorer.exe (PID: 372)
- dwm.exe (PID: 2044)
- DllHost.exe (PID: 2712)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3956)
- dexpot_1614_r2439.exe (PID: 680)
- chrome.exe (PID: 1524)
- dexpot_1614_r2439.exe (PID: 340)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1524)
Application launched itself
- dexpot_1614_r2439.exe (PID: 680)
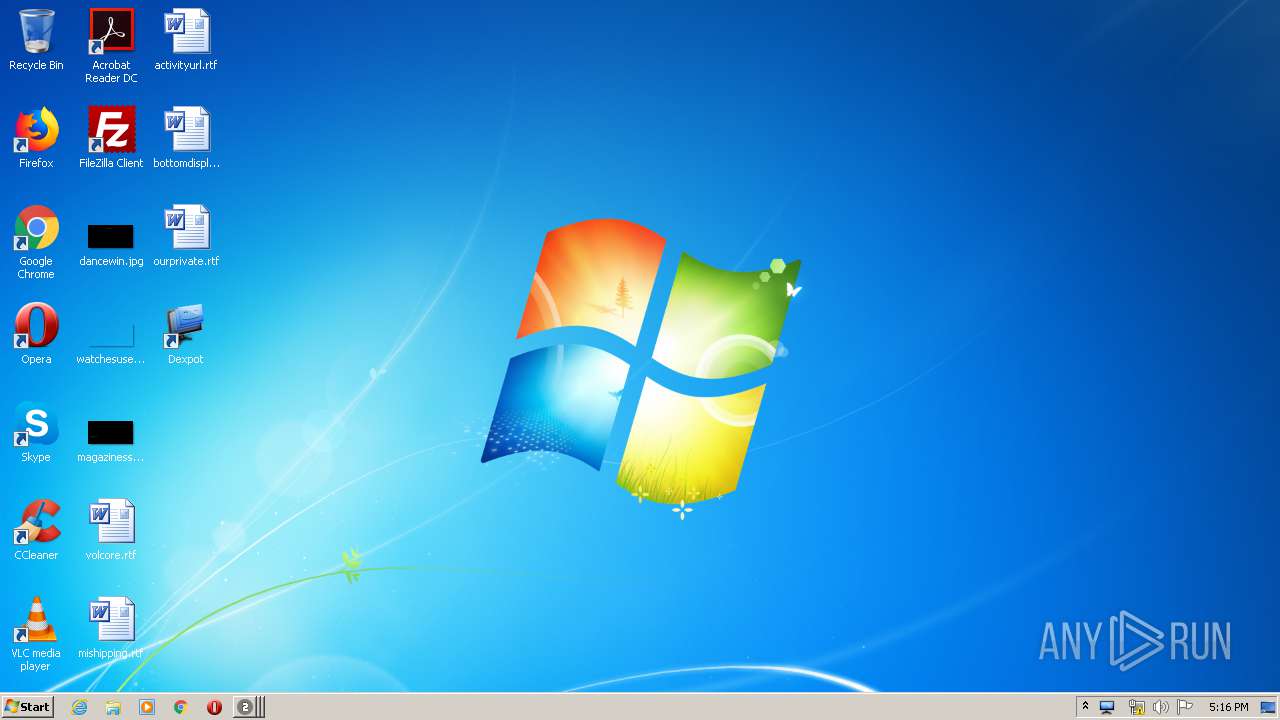
Creates files in the user directory
- dexpot_1614_r2439.exe (PID: 680)
- dexpot.exe (PID: 2336)
- SevenDex.exe (PID: 2376)
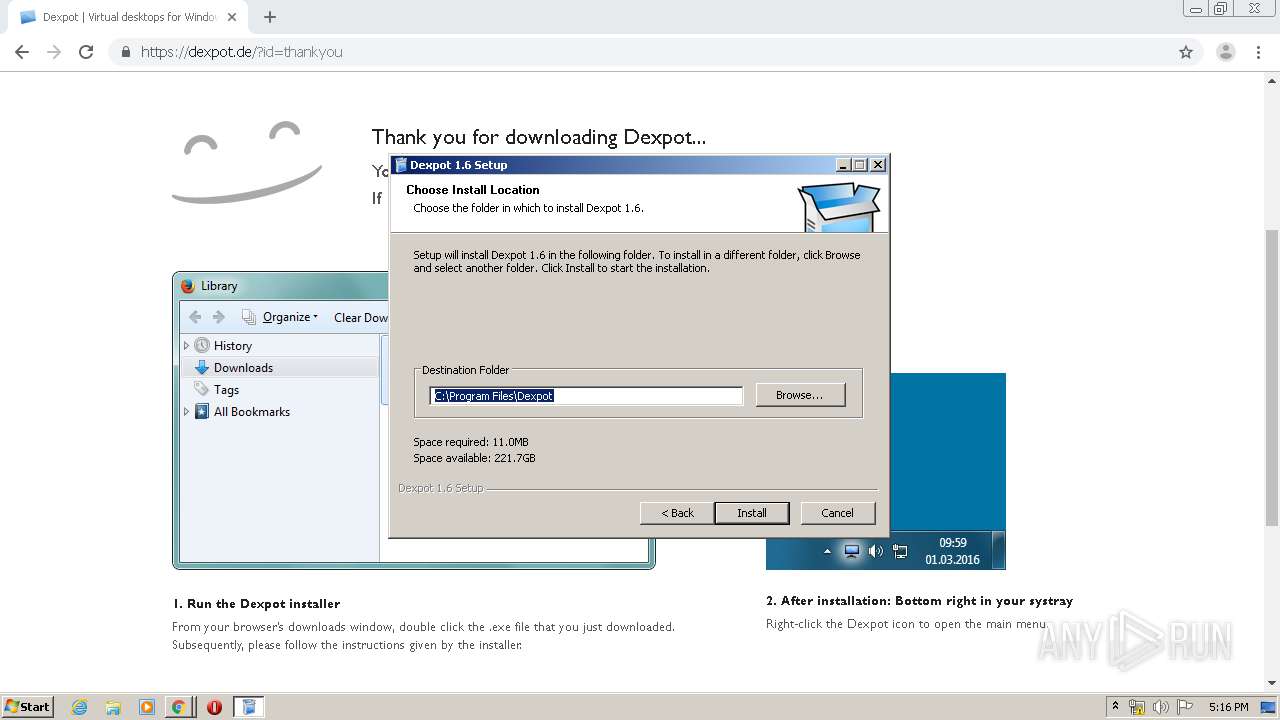
Creates a software uninstall entry
- dexpot_1614_r2439.exe (PID: 680)
Modifies the open verb of a shell class
- dexpot_1614_r2439.exe (PID: 340)
Executed via COM
- explorer.exe (PID: 3056)
Creates files in the program directory
- dexpot_1614_r2439.exe (PID: 340)
INFO
Reads the hosts file
- chrome.exe (PID: 1524)
- chrome.exe (PID: 3956)
Reads settings of System Certificates
- chrome.exe (PID: 1524)
Reads Internet Cache Settings
- chrome.exe (PID: 1524)
Application launched itself
- chrome.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
41
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
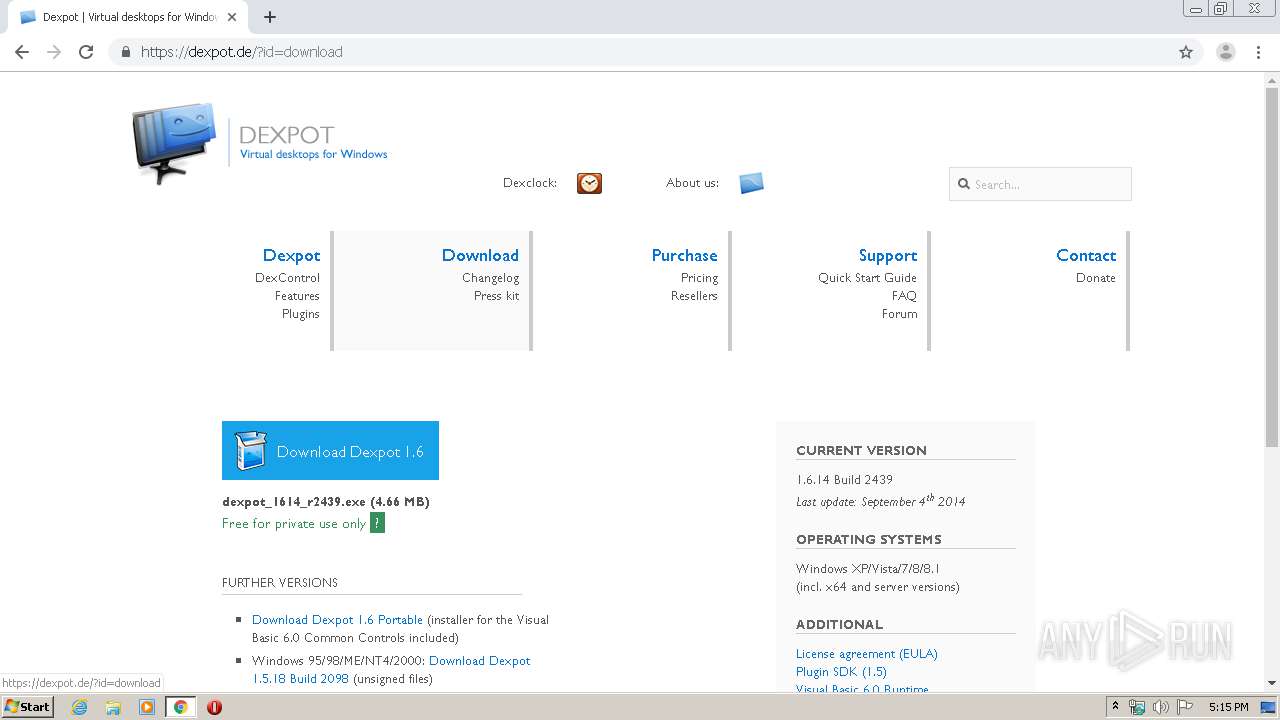
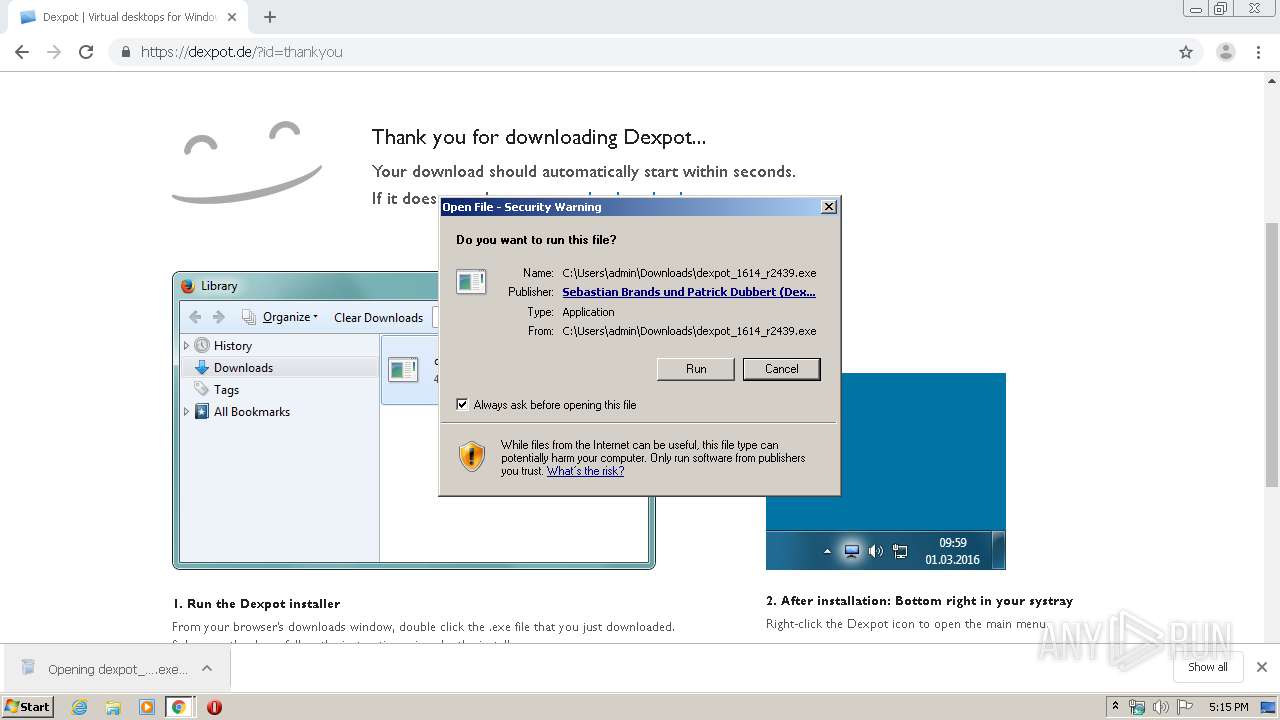
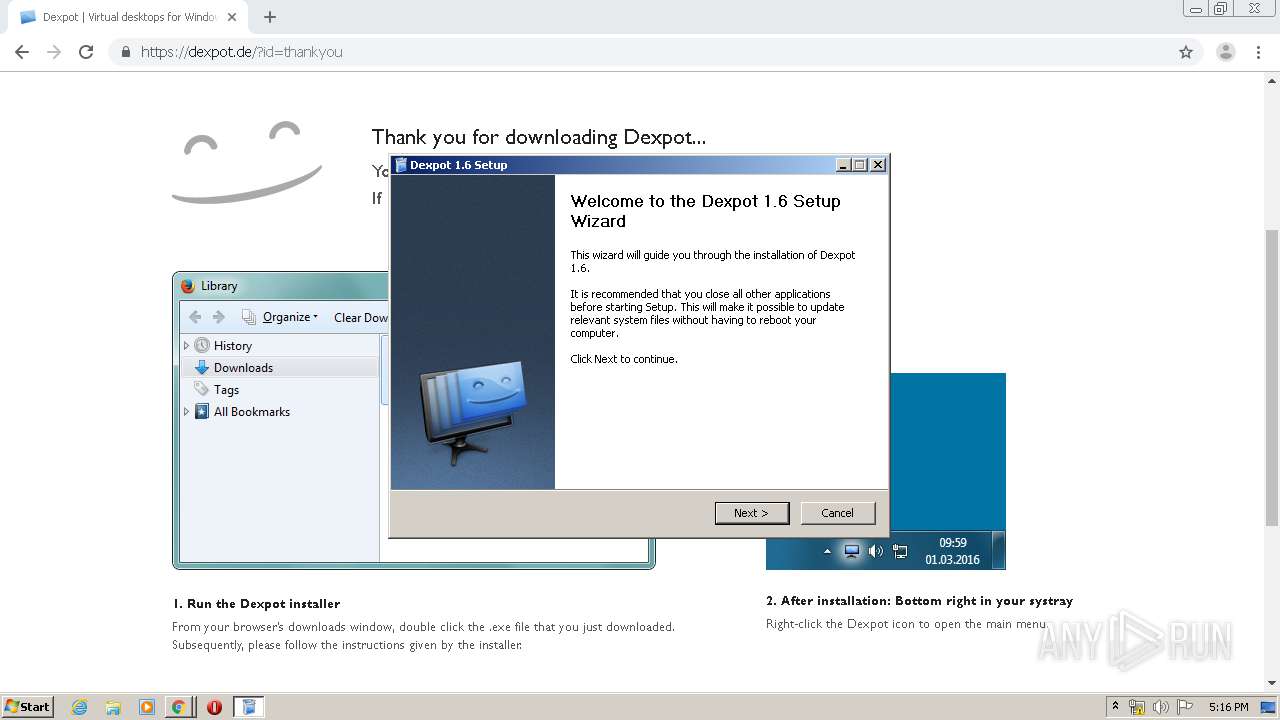
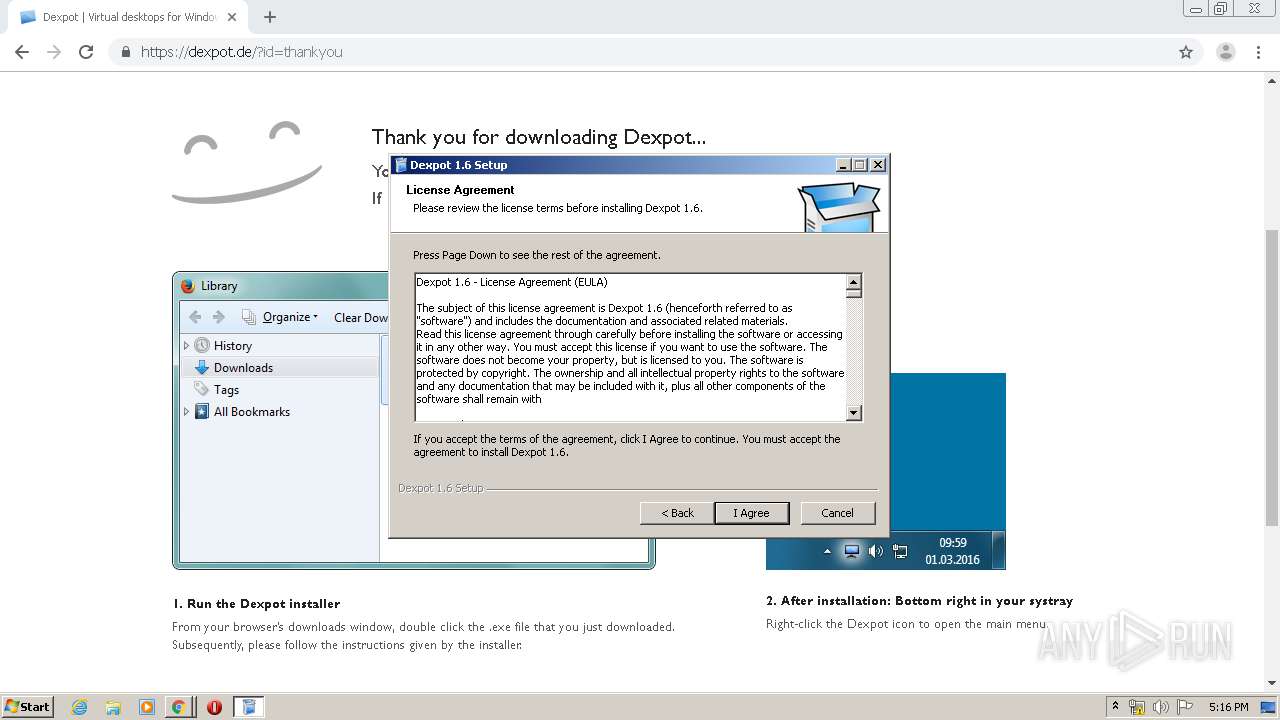
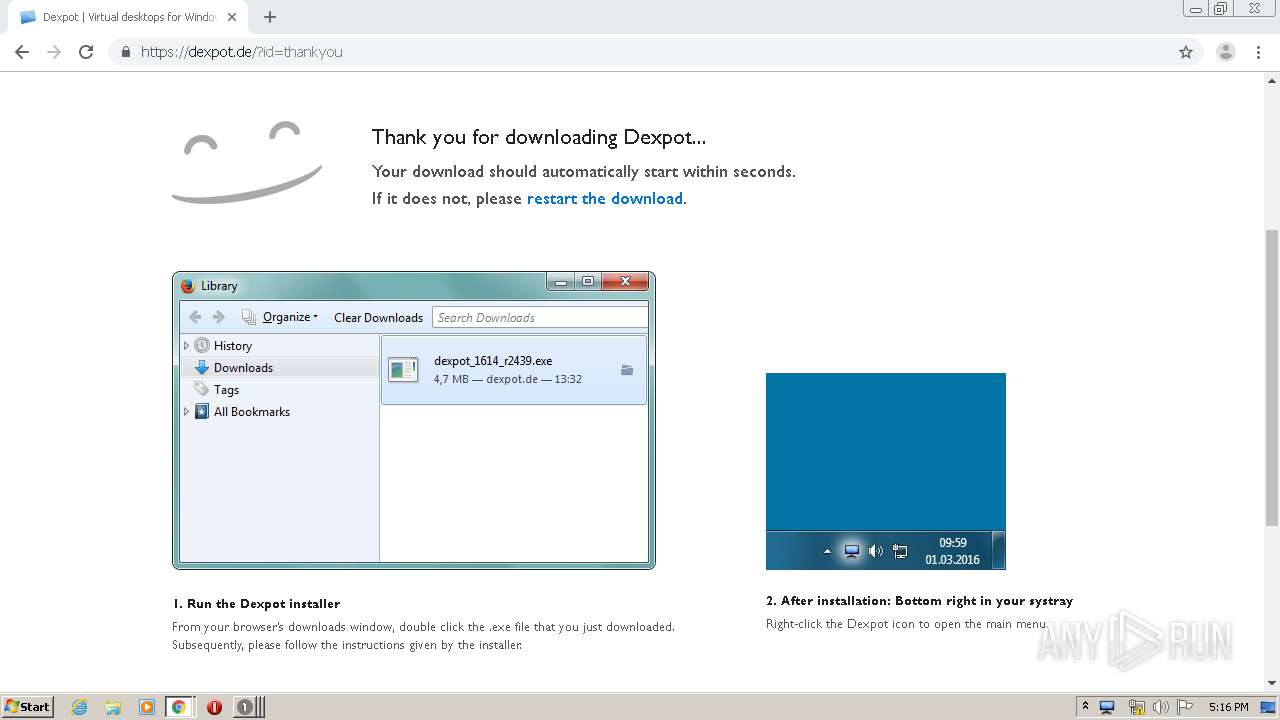
| 340 | "C:\Users\admin\Downloads\dexpot_1614_r2439.exe" /UAC:5021E /NCRC | C:\Users\admin\Downloads\dexpot_1614_r2439.exe | dexpot_1614_r2439.exe | ||||||||||||
User: admin Company: Dexpot GbR Integrity Level: HIGH Description: Installer for Dexpot 1.6 Exit code: 0 Version: 1.6.14 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 652 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
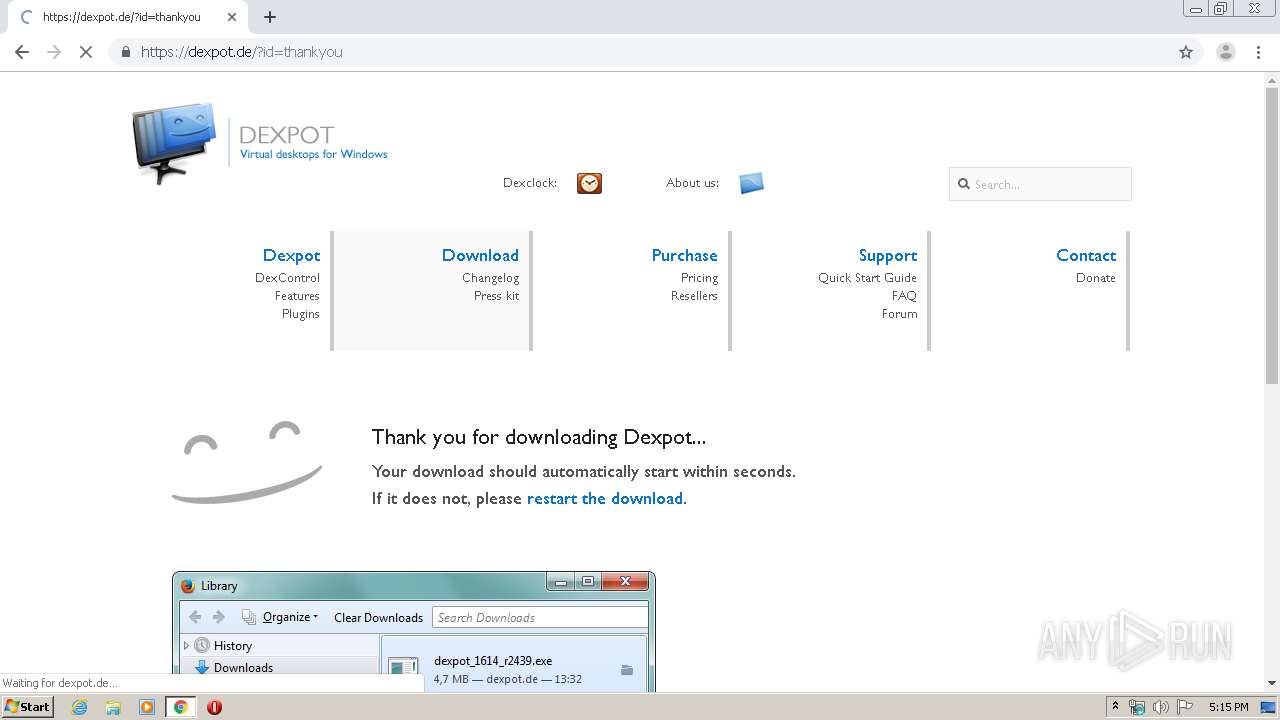
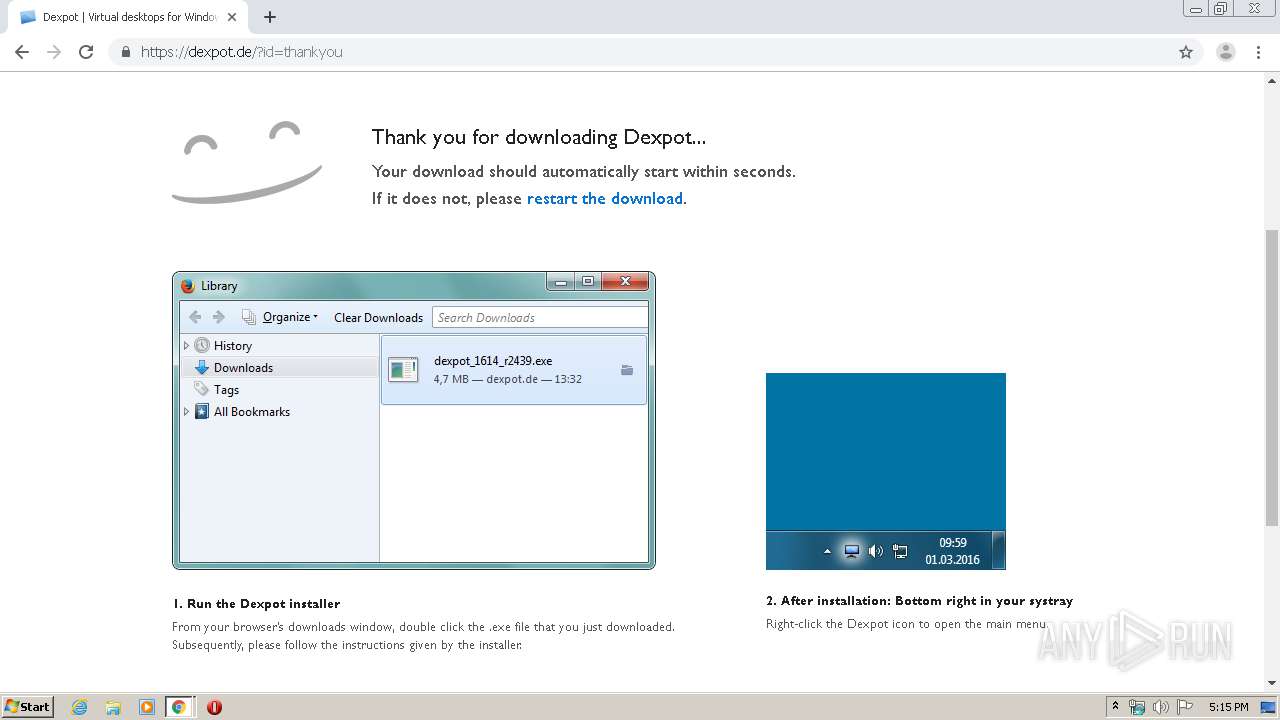
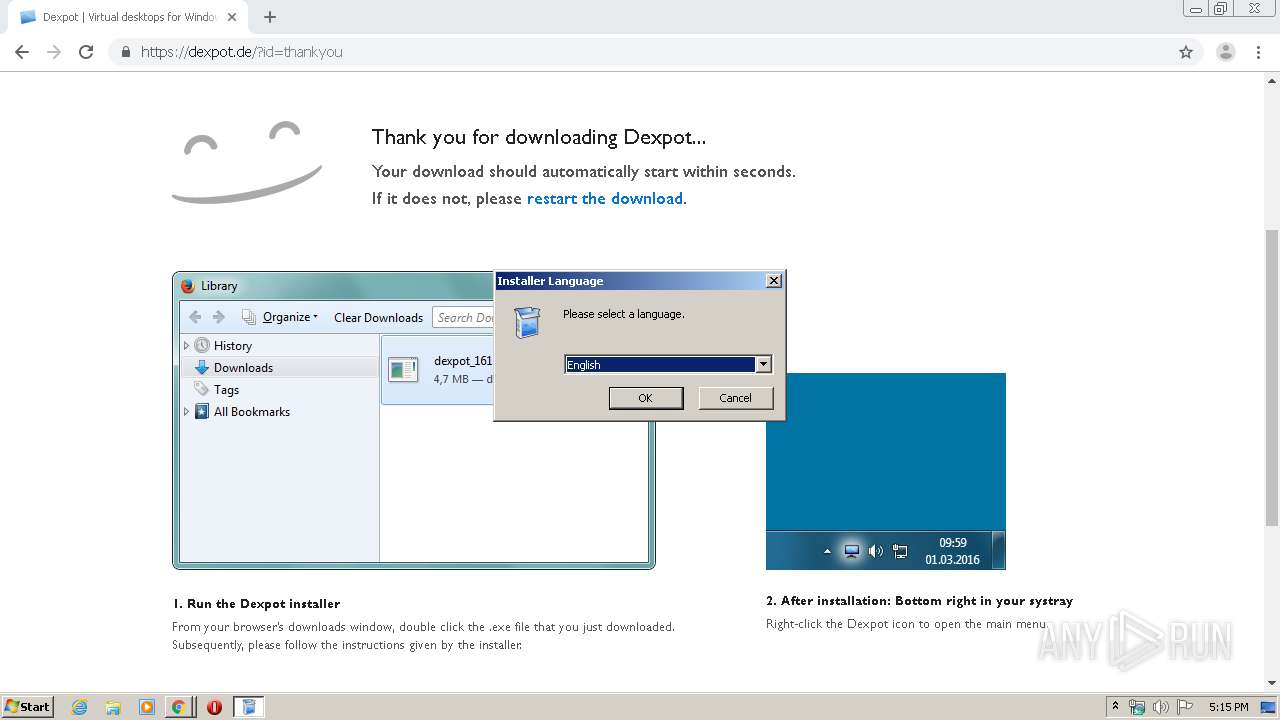
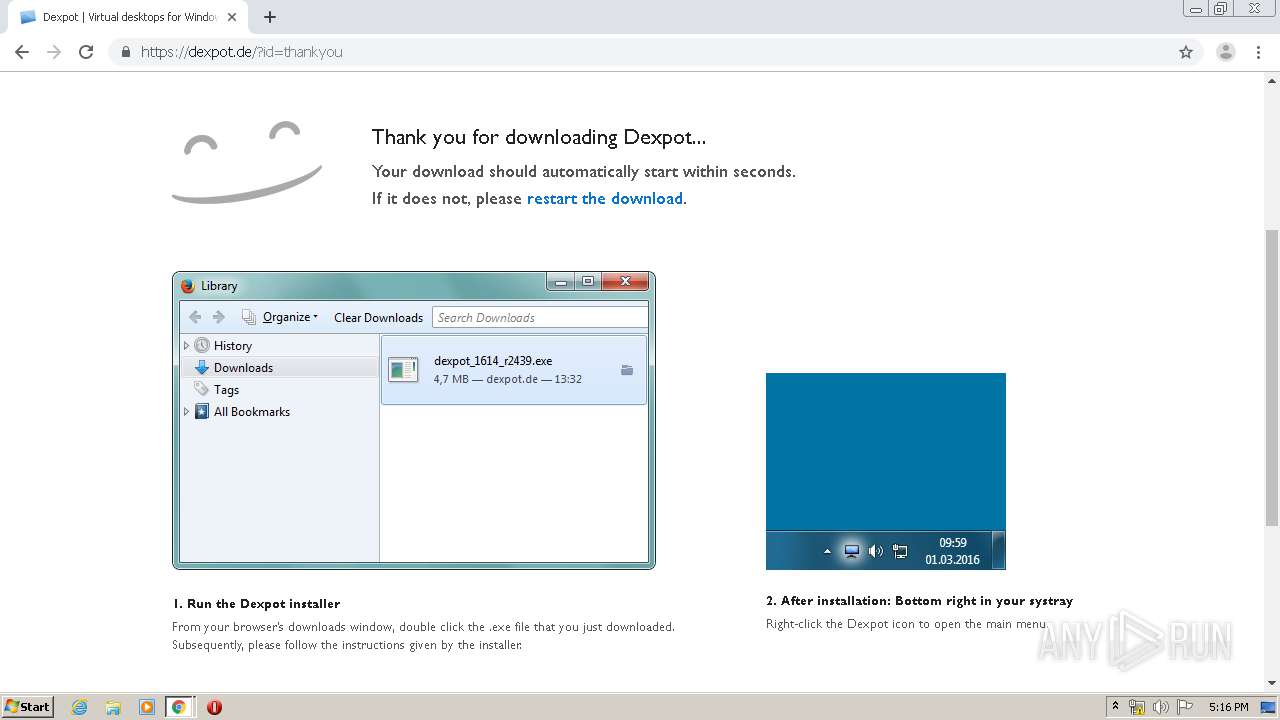
| 680 | "C:\Users\admin\Downloads\dexpot_1614_r2439.exe" | C:\Users\admin\Downloads\dexpot_1614_r2439.exe | chrome.exe | ||||||||||||
User: admin Company: Dexpot GbR Integrity Level: MEDIUM Description: Installer for Dexpot 1.6 Exit code: 0 Version: 1.6.14 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18336286758178776820 --mojo-platform-channel-handle=4164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5008386889038301735 --mojo-platform-channel-handle=4300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16065345979672850447 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://dexpot.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16003375879126165537 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=780 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 569
Read events
3 805
Write events
681
Delete events
83
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1524-13227297302214125 |
Value: 259 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
36
Suspicious files
40
Text files
496
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E57F916-5F4.pma | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1e3e0645-4f1c-40cc-954e-4526157afb93.tmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c10.TMP | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c4f.TMP | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e43.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
41
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | chrome.exe | GET | 200 | 69.172.201.153:80 | http://dexpot.com/ | US | html | 776 b | malicious |
3956 | chrome.exe | GET | 200 | 69.172.201.153:80 | http://dexpot.com/tg.php?uid=dexpot5e57f918a408a9.15420470 | US | html | 265 b | malicious |
3956 | chrome.exe | GET | 200 | 69.172.201.153:80 | http://dexpot.com/ | US | html | 963 b | malicious |
3956 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3956 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
3956 | chrome.exe | GET | 200 | 69.172.201.153:80 | http://dexpot.com/page.php?dexpot5e57f918a408a9.15420470 | US | html | 161 b | malicious |
3956 | chrome.exe | GET | 301 | 81.169.145.77:80 | http://dexpot.de/ | DE | html | 226 b | whitelisted |
3956 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
3956 | chrome.exe | GET | 200 | 69.172.201.153:80 | http://dexpot.com/ads.js | US | text | 128 b | malicious |
3956 | chrome.exe | GET | 200 | 216.58.208.42:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.5.2/jquery.min.js | US | text | 29.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | chrome.exe | 69.172.201.153:80 | dexpot.com | Dosarrest Internet Security LTD | US | malicious |
3956 | chrome.exe | 216.58.208.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3956 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3956 | chrome.exe | 176.74.176.178:80 | return.uk.uniregistry.com | Peer 1 Network (USA) Inc. | GB | suspicious |
3956 | chrome.exe | 13.225.73.11:443 | static.uniregistry.com | — | US | suspicious |
3956 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
3956 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.195:80 | www.gstatic.com | Google Inc. | US | whitelisted |
3956 | chrome.exe | 172.217.21.195:80 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dexpot.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
return.uk.uniregistry.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
static.uniregistry.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
uniregistry.com |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3956 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |