| URL: | https://d.hodes.com/r/tp2?e=se&tv=pixel_tracker&p=web&aid=humanacrm&se_ca=email_unsub&se_ac=unsubscribe&se_la=12171&se_pr=5006&se_va=1923131&tr_id=&tr_af=9402&u=https://abael.com.br%2Fnew%2Fauth%2FwoB8%2F%2F%2F%2FY29rYWRhQGludHJlcGlkaWIuY29t |
| Full analysis: | https://app.any.run/tasks/01302e32-3544-4974-8ec5-744c4b337729 |
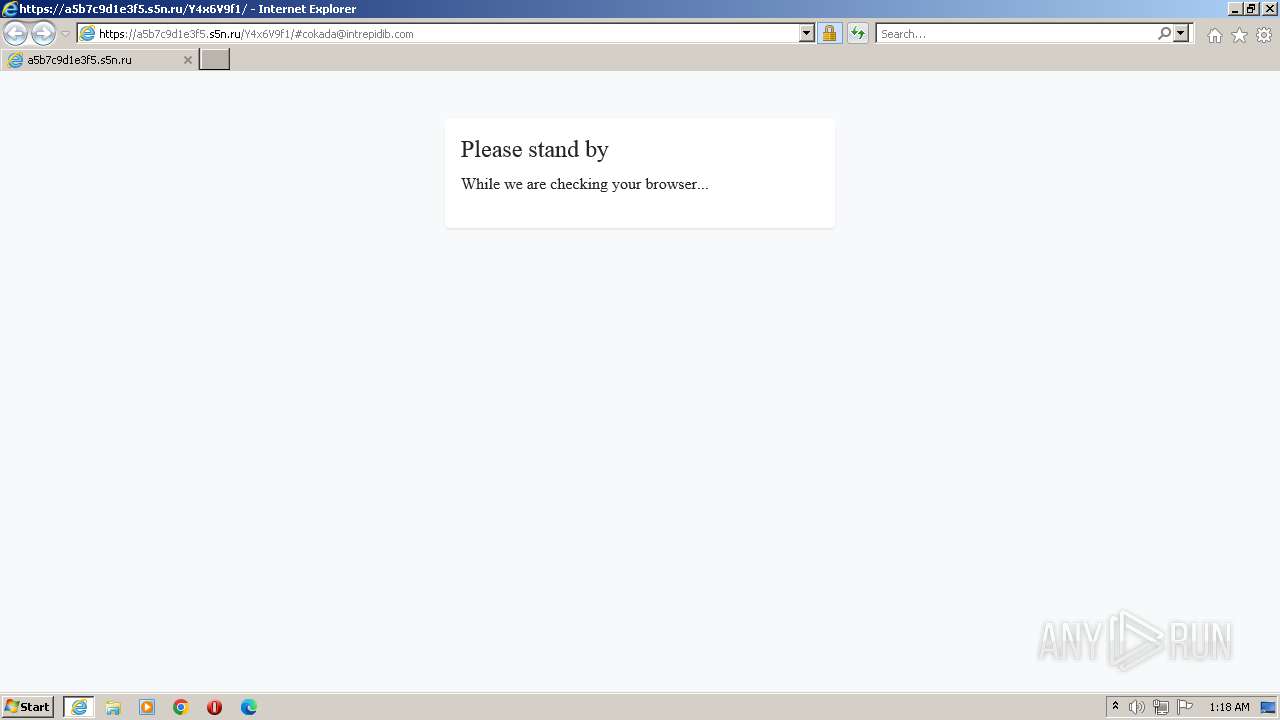
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2023, 00:16:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 914665395F4B07089B82A2F766E5C011 |
| SHA1: | 9B43B5B8F0545DD0D8068EFB8E2B7245FB866310 |
| SHA256: | D42804AB5767835DE8AAA27CD41063F37B2D627093E3EABC507F4997FB4F17CB |
| SSDEEP: | 6:2BrR4d+J6UZi56+pvSQZ01PRH5RVYWrw5rM0gBn:2fR656nQZ01PRHPVxrw1MRB |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://d.hodes.com/r/tp2?e=se&tv=pixel_tracker&p=web&aid=humanacrm&se_ca=email_unsub&se_ac=unsubscribe&se_la=12171&se_pr=5006&se_va=1923131&tr_id=&tr_af=9402&u=https://abael.com.br%2Fnew%2Fauth%2FwoB8%2F%2F%2F%2FY29rYWRhQGludHJlcGlkaWIuY29t" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1532 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
12 205
Read events
12 117
Write events
86
Delete events
2
Modification events
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:A01DBB5CB9A82176B019888582ED839A | SHA256:52697410FC0438EE08F8F2686ACD52209F176F32692322EFD8E961409283AB1E | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D03E46CD585BBE111C712E6577BC5F07_573A4DC5AFC6AAAF8BD5E9F5AAFA993F | binary | |
MD5:947D60359F44ECDB1BE590EC7E744689 | SHA256:1B57AD3CC9E7BA61F42B68BC2EA3DC0F788875A610F0E54F0BBDC79D171EEB5C | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:AE98B0483DCC80BA9D3D6A305A73B940 | SHA256:EDF42930F33A3C52F273B210AC806A03C6AFF71E6FCBD7FD298D26156DB10736 | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QR86KGF8.txt | text | |
MD5:4CCDA9847DF207B3B087A160C07227B3 | SHA256:B8C76B62FAEDF3530912528AC5CF3AAE73FAF1C2ACA0A83AE2DC478A9D2004CF | |||
| 1532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\KJXDC1HE\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:F5B895EED56FBD7CB088D013CEAE3E33 | SHA256:10AD97B1DA227C4A2FA24E9FF09F333CFF869E06F795D417530CCDCC3391E1E8 | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:63E48C526513DC5C383C1595E6ADD8E8 | SHA256:1DF7C1CB206B0203CC28F404DD071BC006B36D259B18793CA714BC8F01C0F1E5 | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:2D5E812CEA5941A47AEE8E420B98D4FF | SHA256:6E02359066814288566AF8C6BC3CCDB6DCFD259EC2410C82BBA16F35F9E26E2A | |||
| 2532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:3B38ED14F9347F62A98BE1F5989A1248 | SHA256:FF15A0565D6558C44710897ED83E0F0E6E9F1F2911B2D253FFA29D9306452290 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
65
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1532 | iexplore.exe | GET | — | 95.101.54.131:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQRfrjJTE5Sg1FOWWtIUDZzMQ%3D%3D | DE | — | — | shared |
1532 | iexplore.exe | GET | 304 | 67.26.75.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1d44ec3eb99ddbdc | US | — | — | whitelisted |
1532 | iexplore.exe | GET | 304 | 67.26.75.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?330fdf4551eea3d1 | US | — | — | whitelisted |
2532 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 67.26.75.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5a08c2ccd90008ba | US | compressed | 62.3 Kb | whitelisted |
1532 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 52.222.206.67:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | US | binary | 1.39 Kb | shared |
1532 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | binary | 1.47 Kb | whitelisted |
2532 | iexplore.exe | GET | 200 | 2.16.241.8:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQRfrjJTE5Sg1FOWWtIUDZzMQ%3D%3D | unknown | binary | 503 b | shared |
2532 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1084 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2532 | iexplore.exe | 67.26.75.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
1532 | iexplore.exe | 184.86.251.9:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2532 | iexplore.exe | 52.70.101.237:443 | d.hodes.com | AMAZON-AES | US | unknown |
2532 | iexplore.exe | 108.138.16.146:80 | ocsp.r2m01.amazontrust.com | AMAZON-02 | US | unknown |
2532 | iexplore.exe | 162.241.203.40:443 | abael.com.br | UNIFIEDLAYER-AS-1 | US | malicious |
2532 | iexplore.exe | 2.16.241.15:80 | r3.o.lencr.org | Akamai International B.V. | DE | suspicious |
2532 | iexplore.exe | 23.37.62.128:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
1532 | iexplore.exe | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
1532 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d.hodes.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m01.amazontrust.com |
| whitelisted |
abael.com.br |
| unknown |
iecvlist.microsoft.com |
| whitelisted |