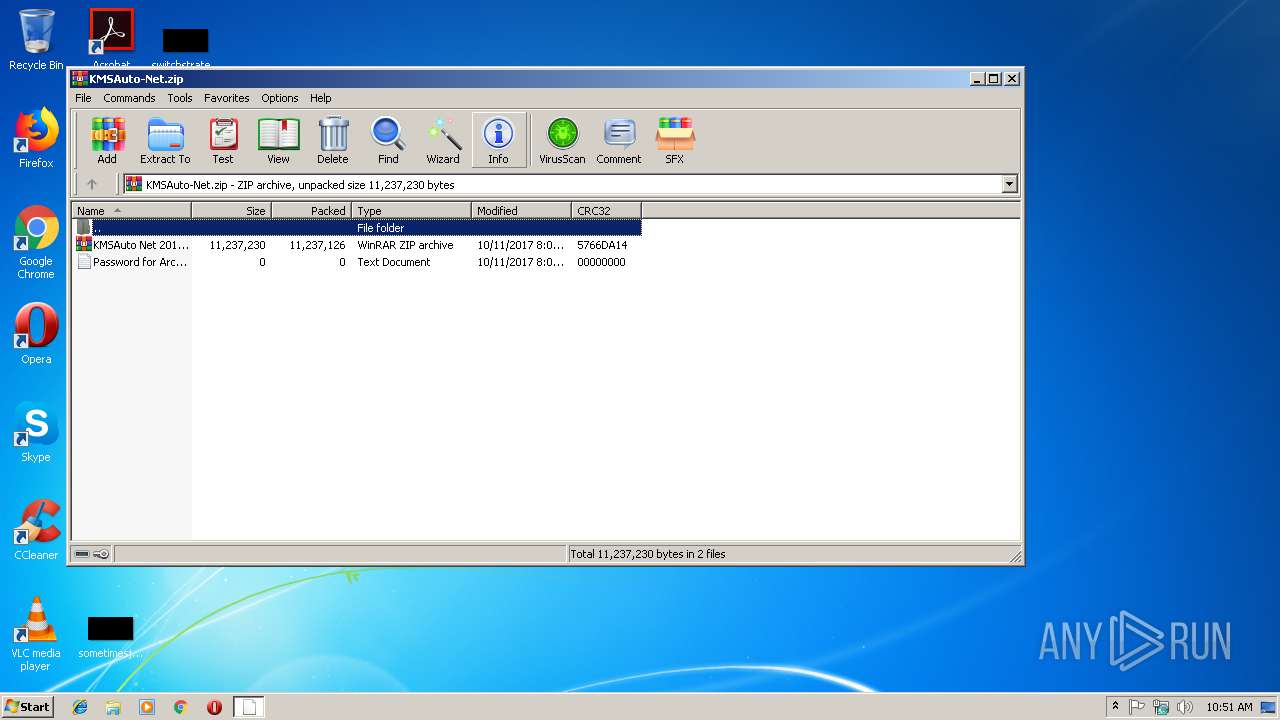
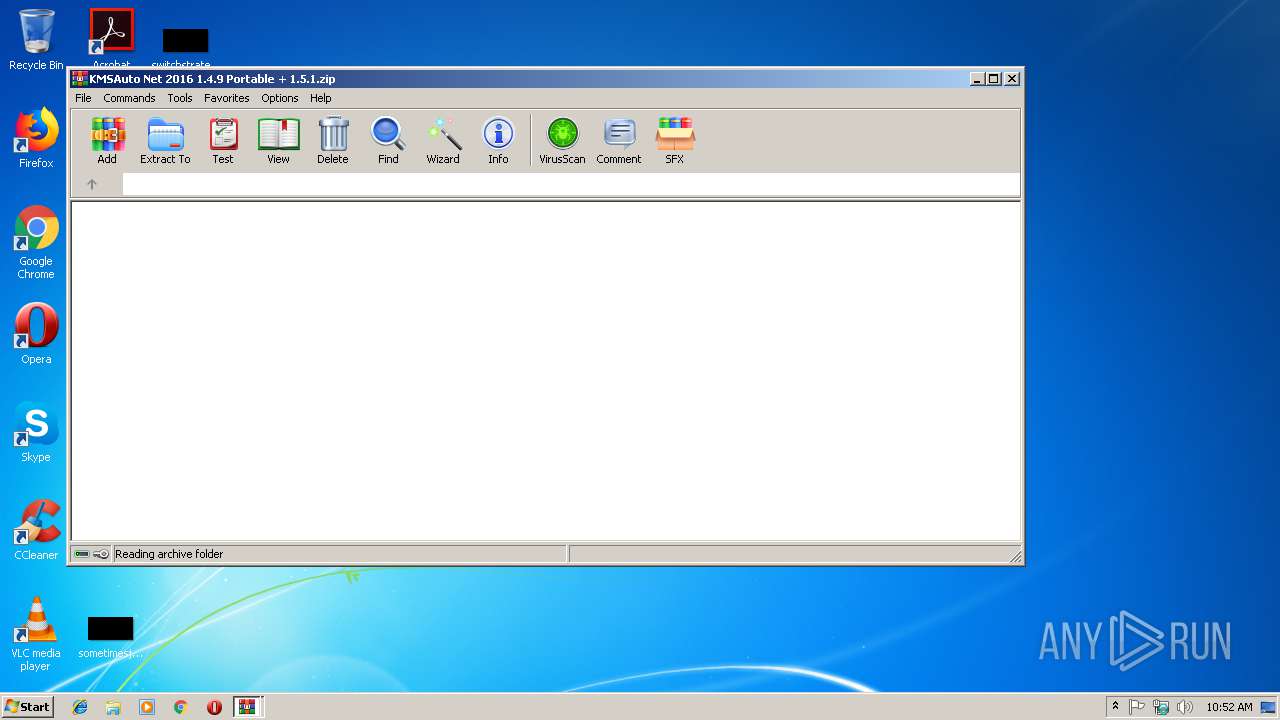
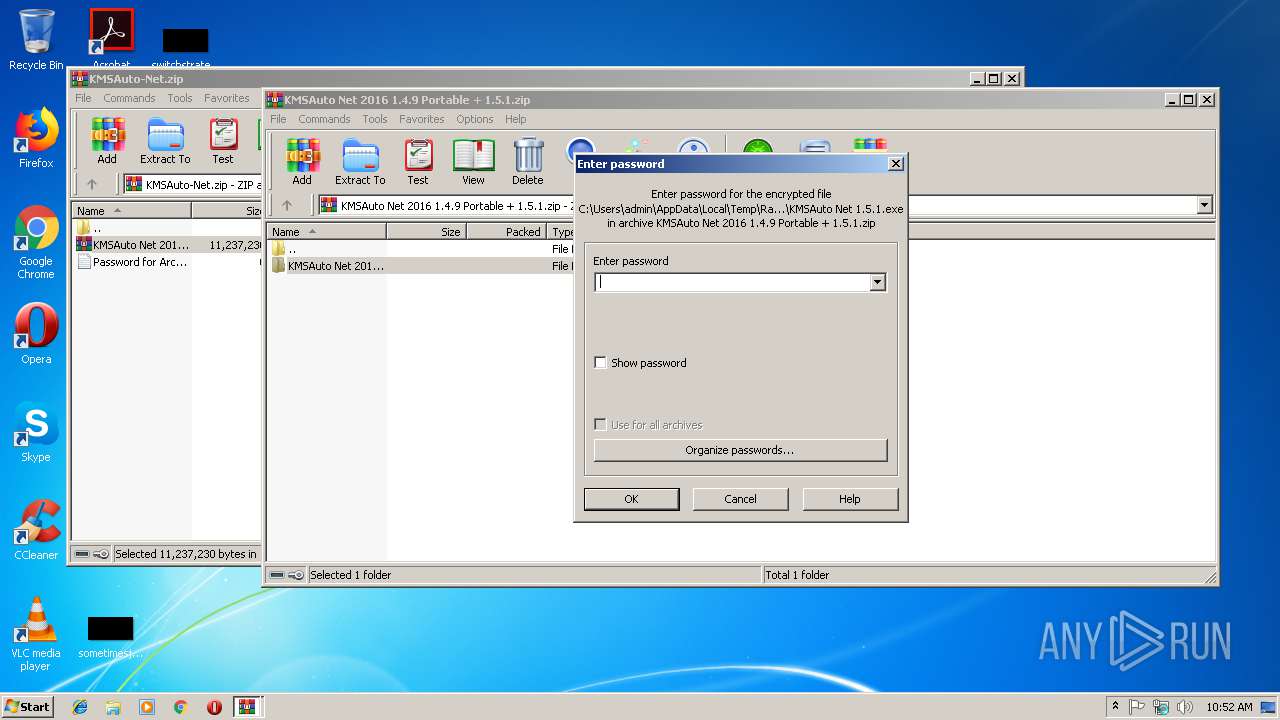
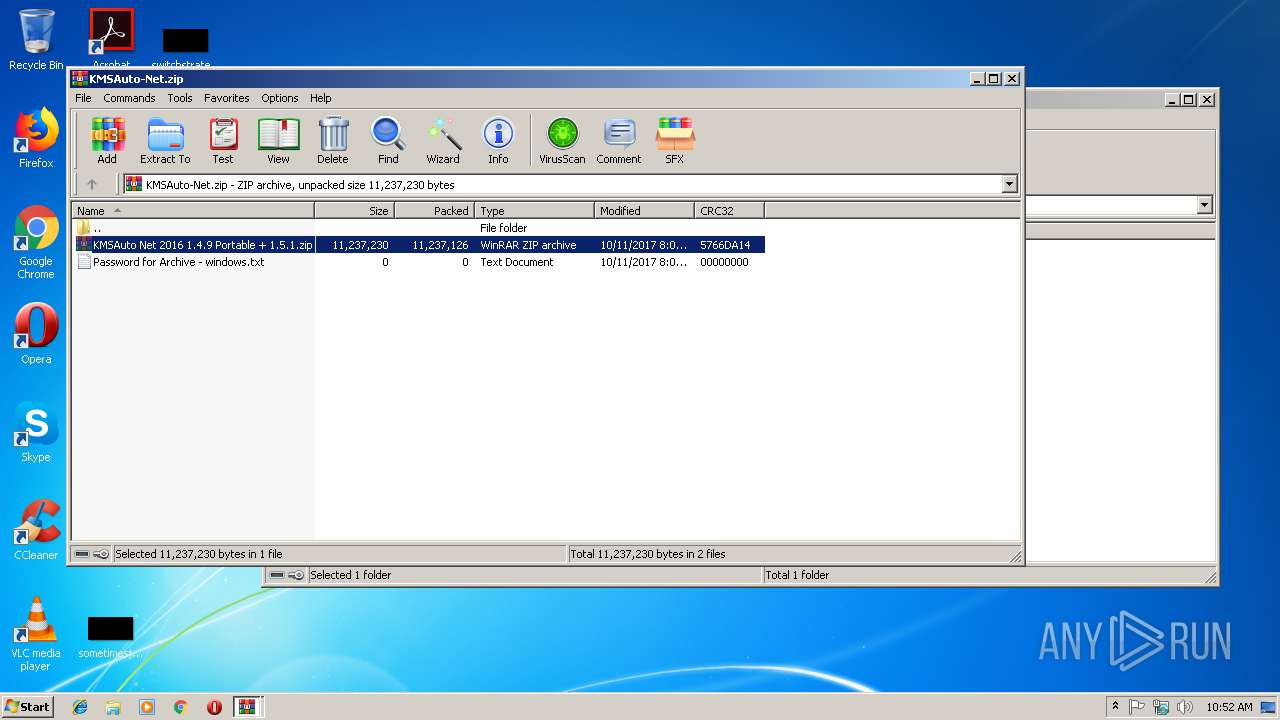
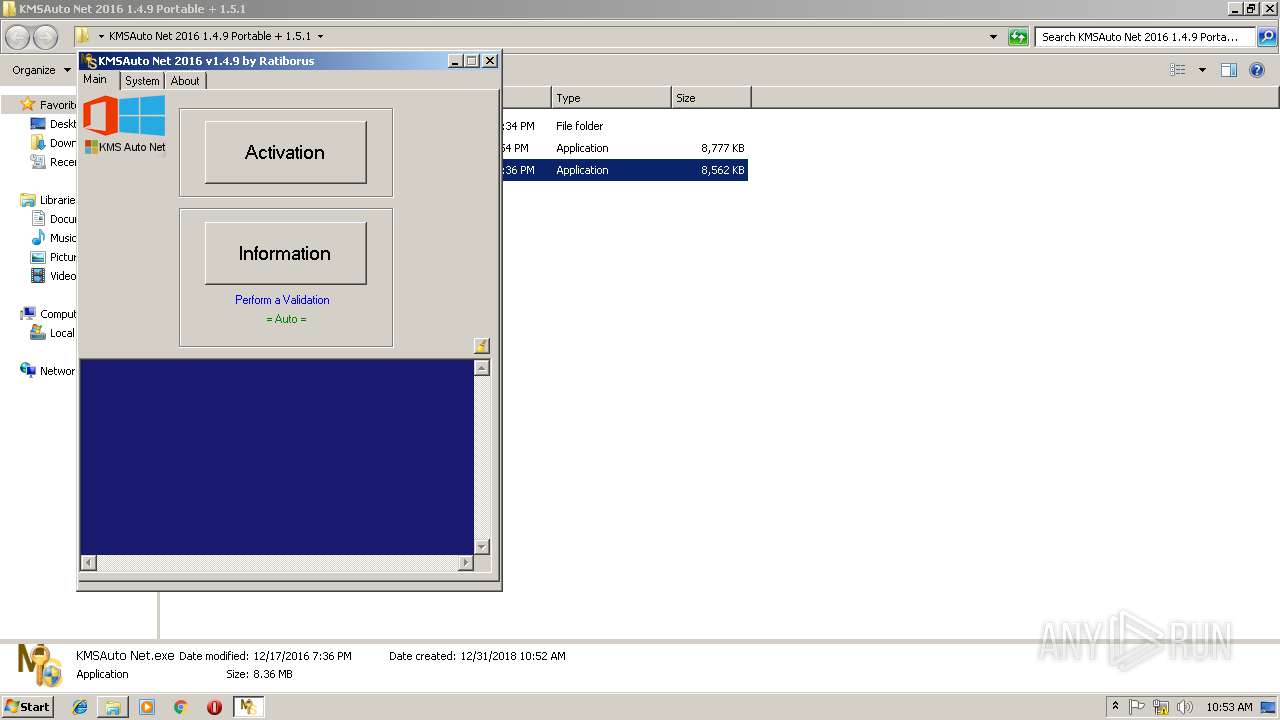
| download: | KMSAuto-Net.zip |
| Full analysis: | https://app.any.run/tasks/1a35c290-03dc-4dff-9a8d-fc0256d9a13e |
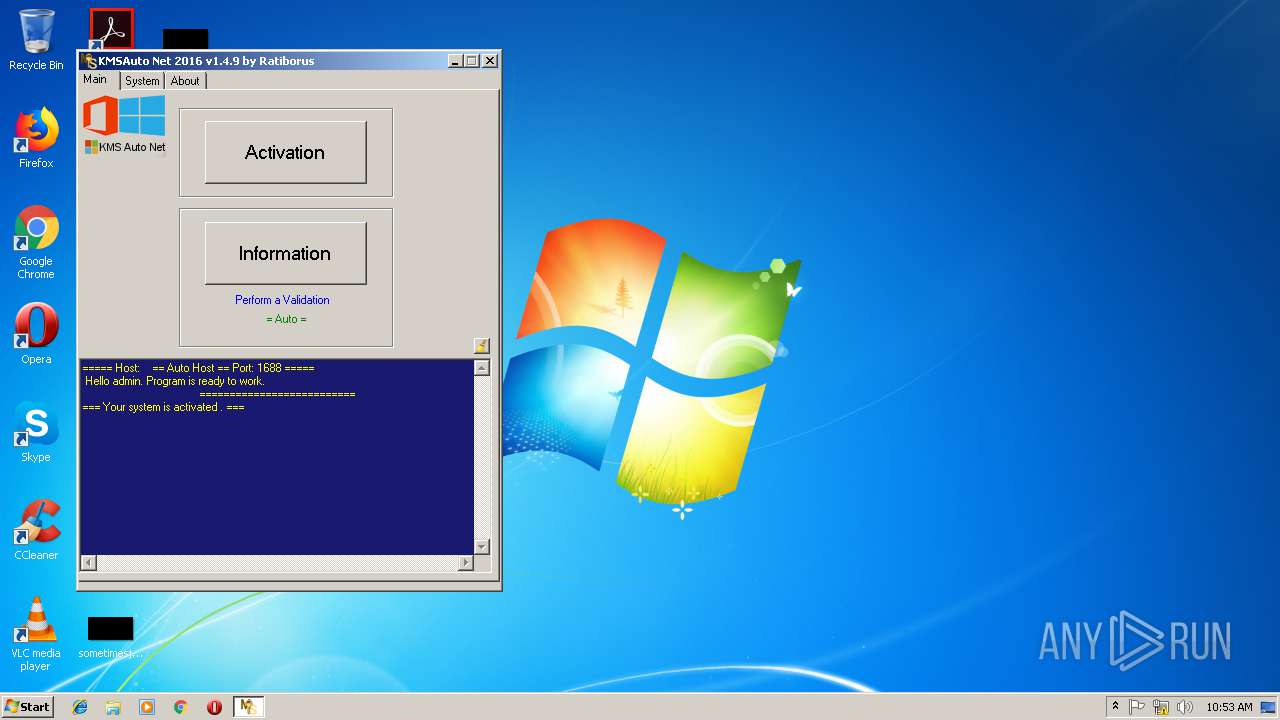
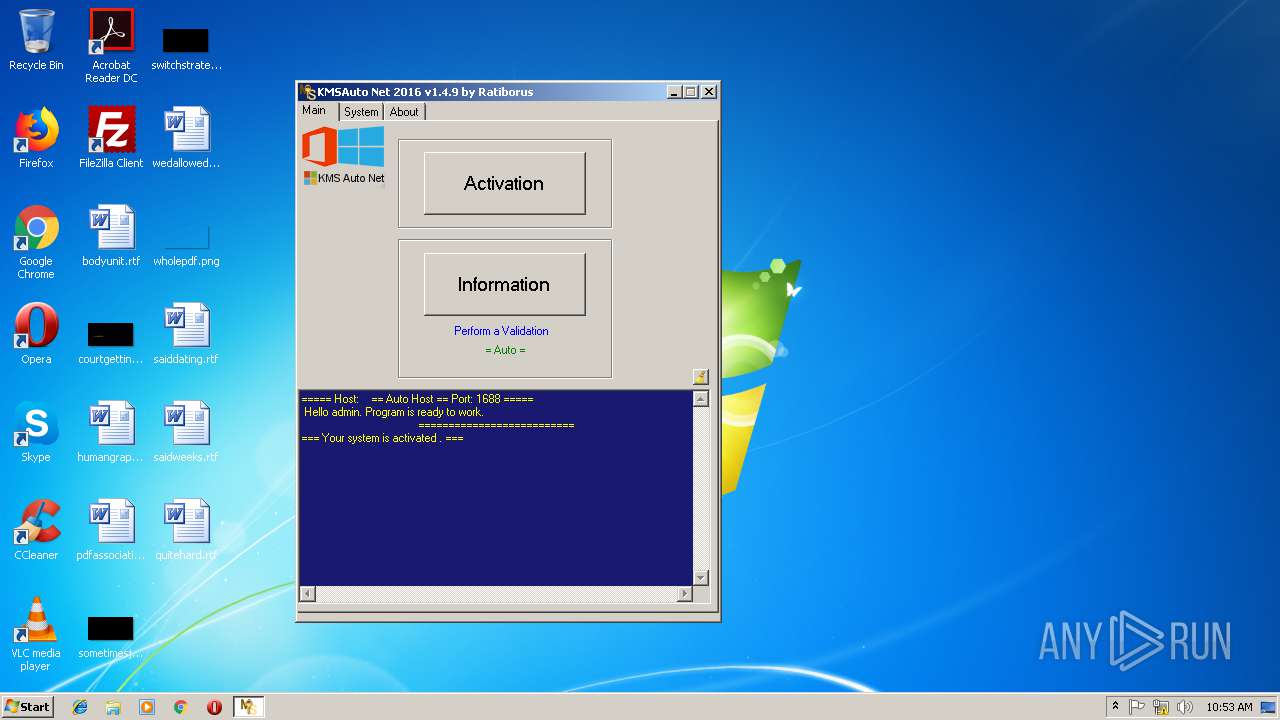
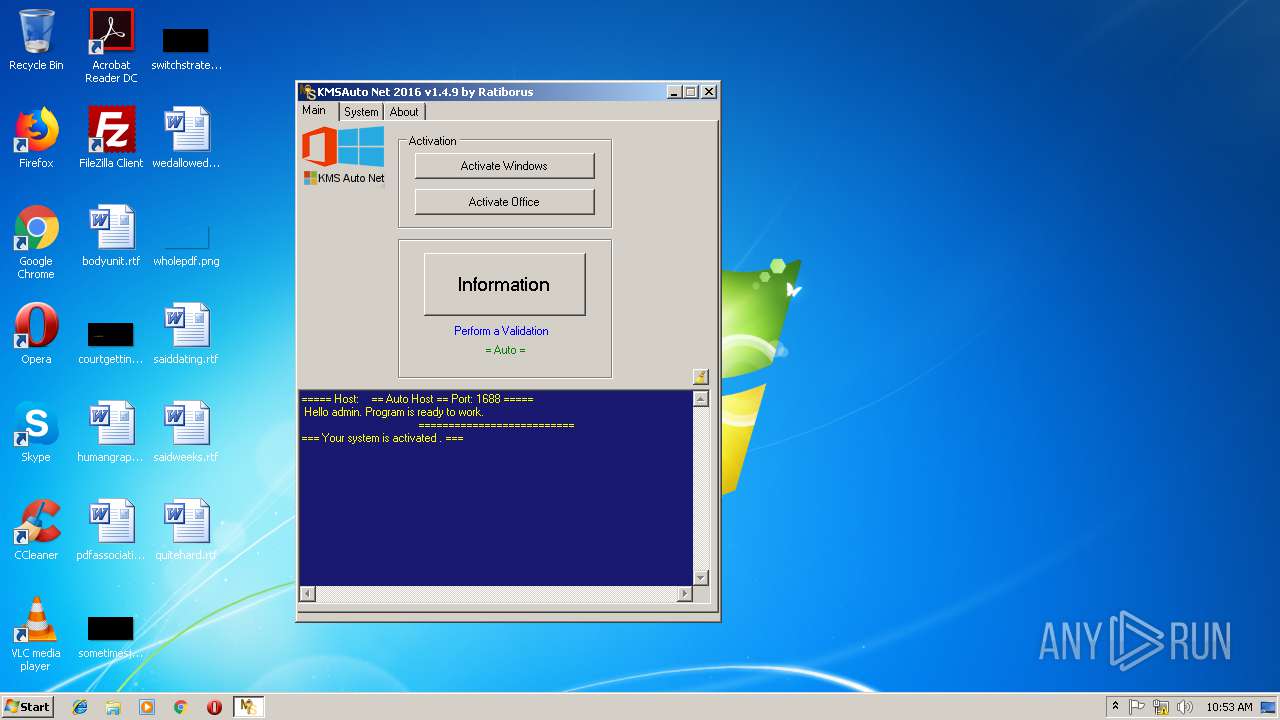
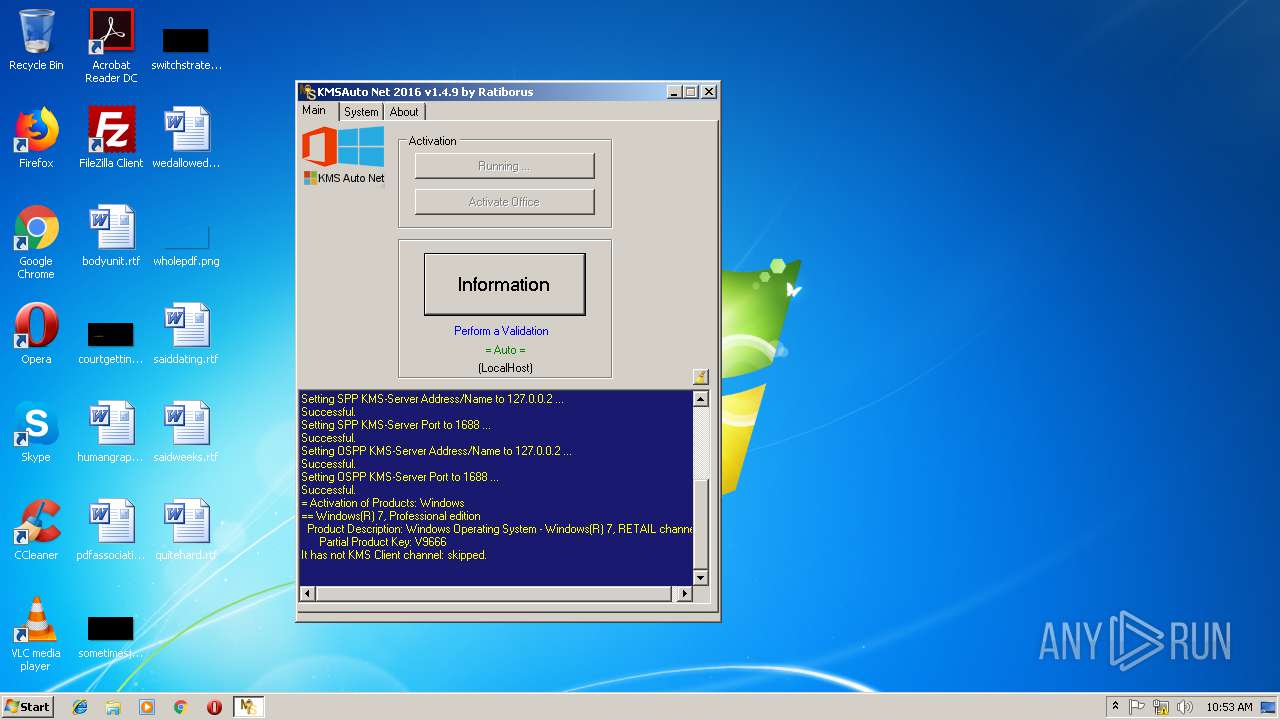
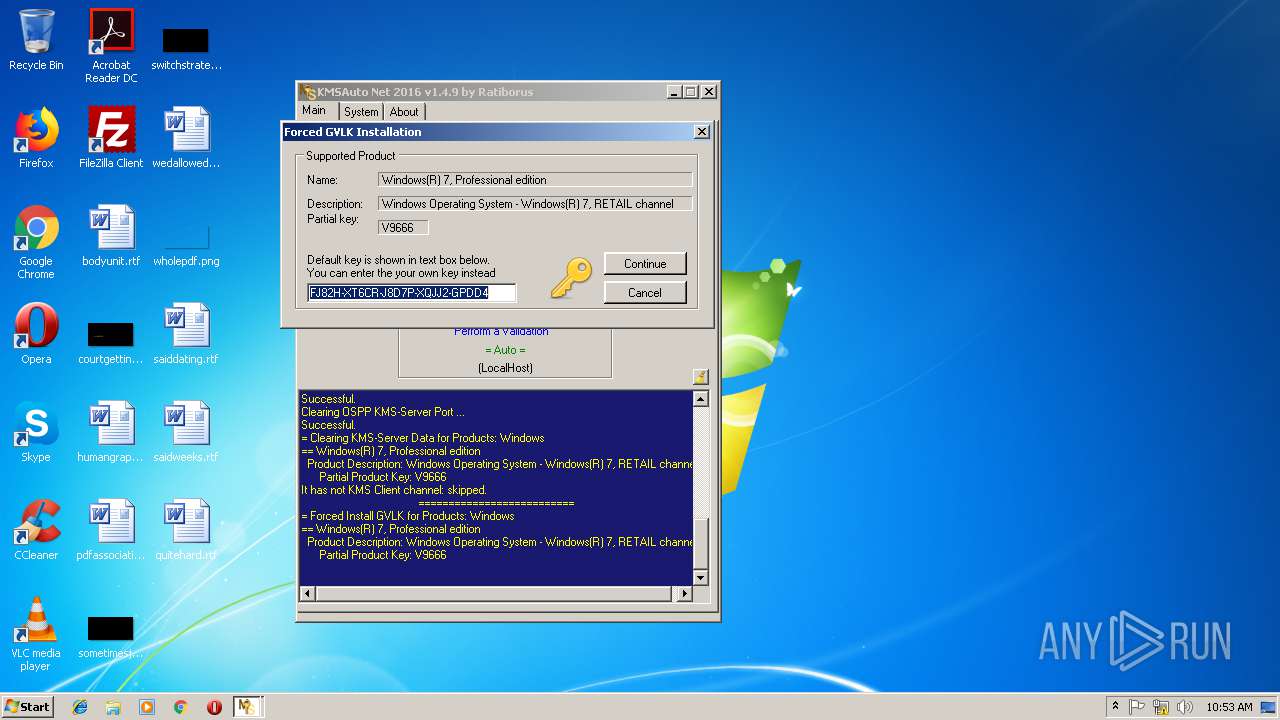
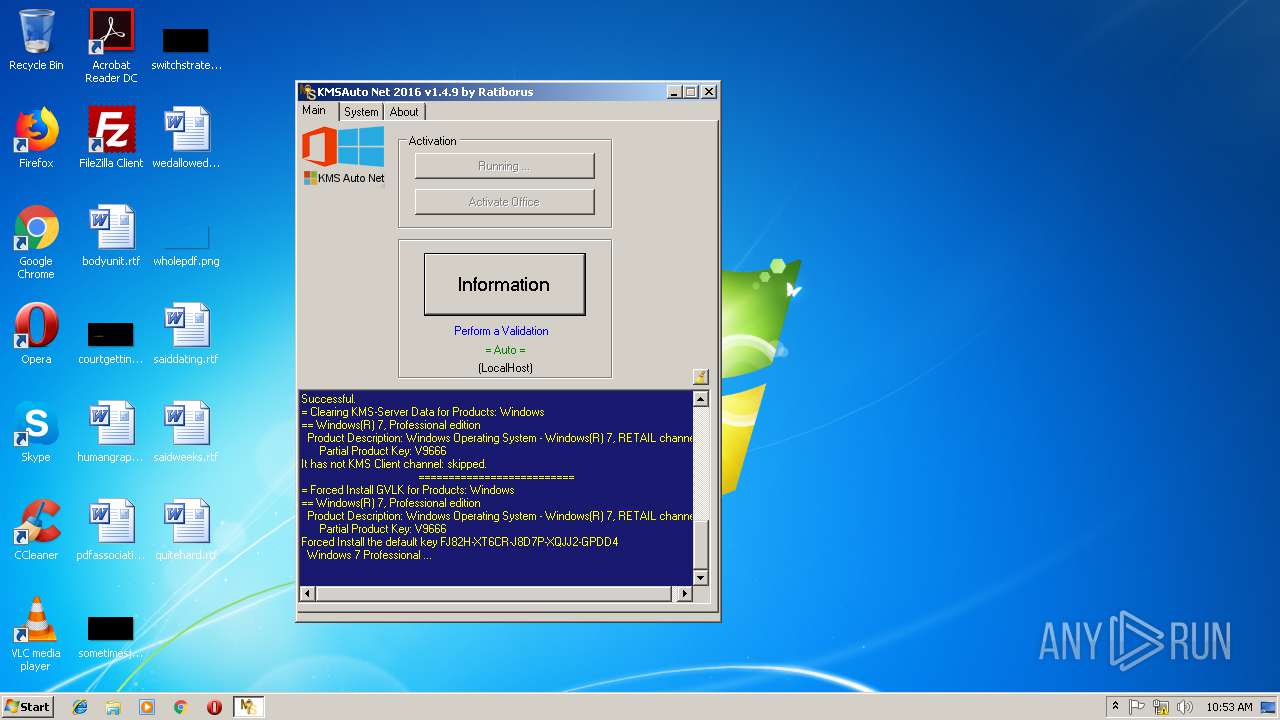
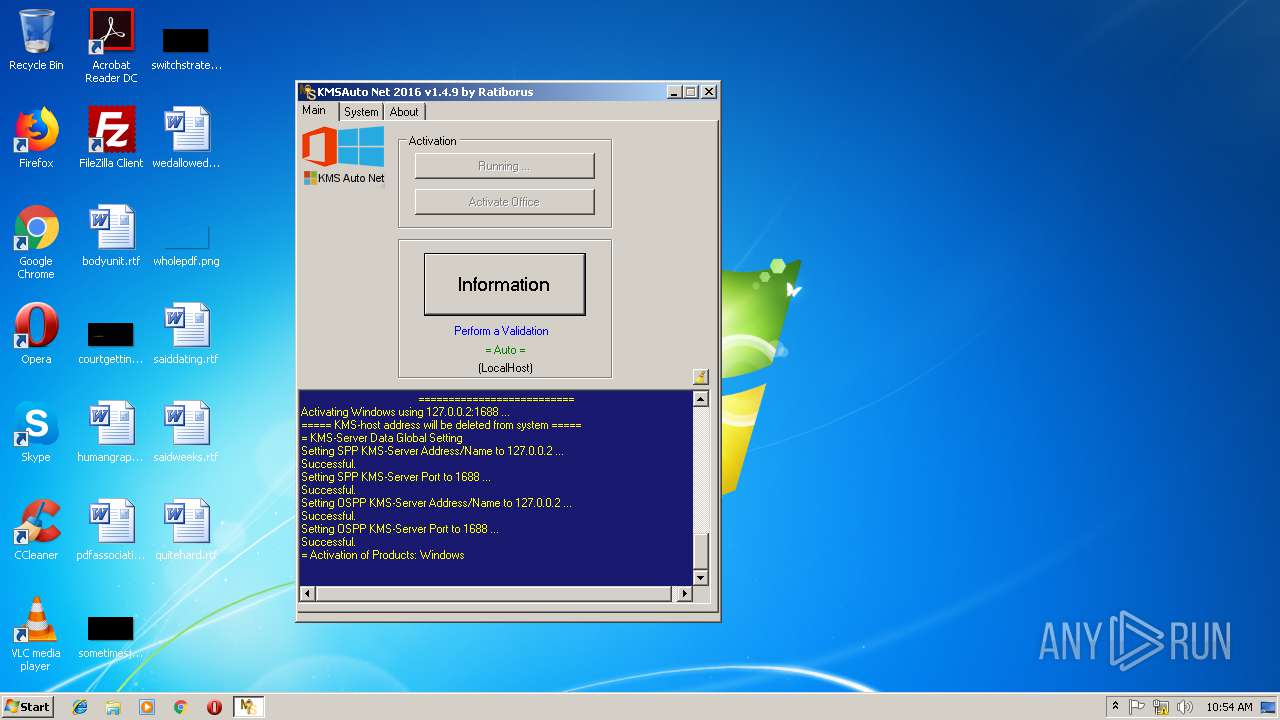
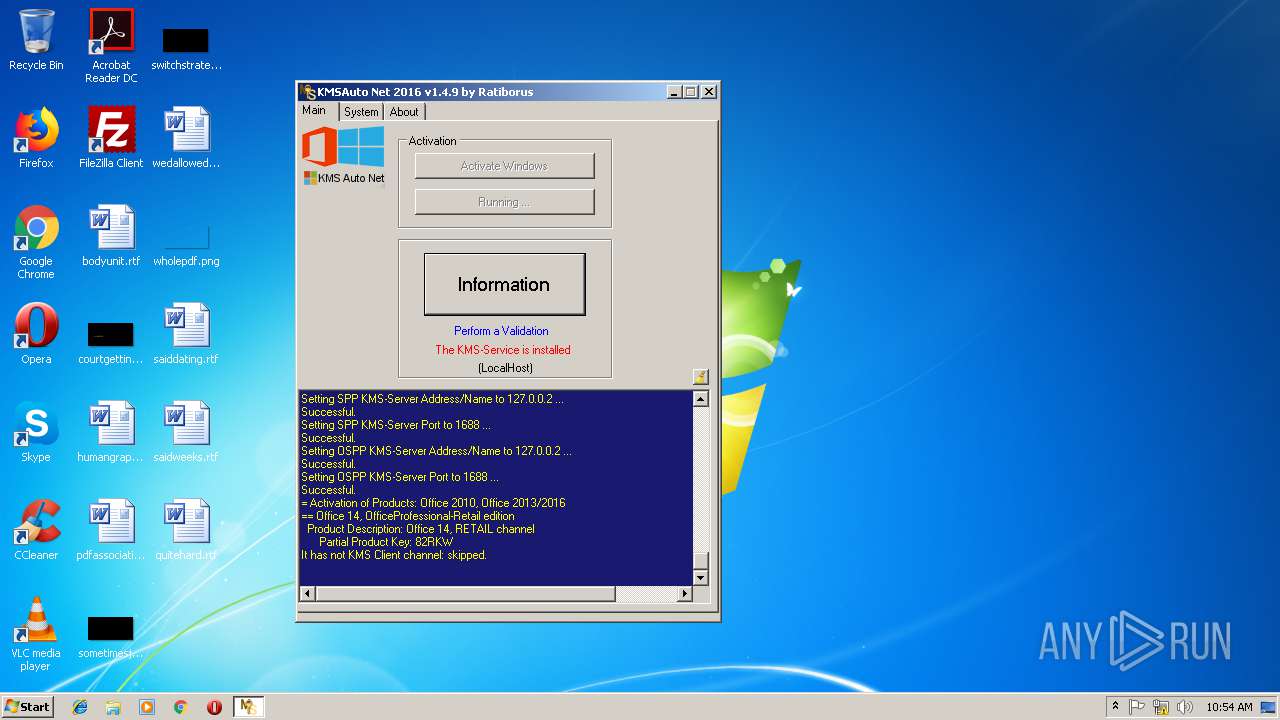
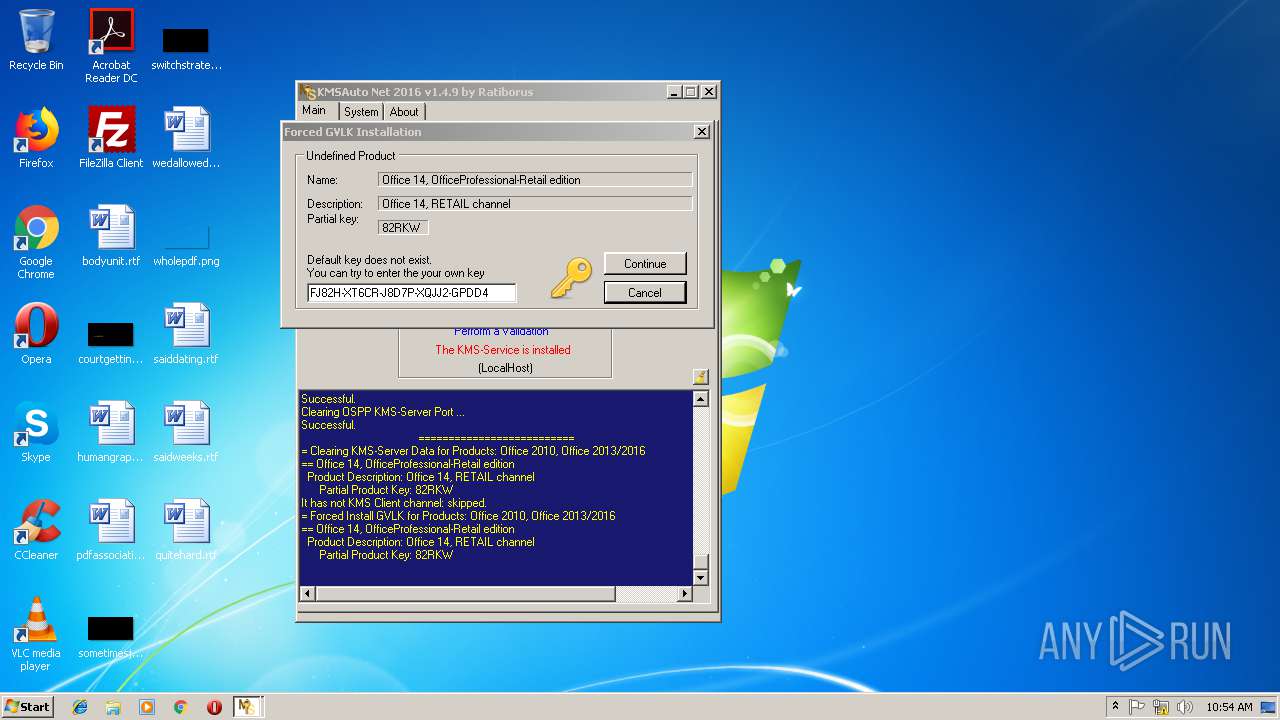
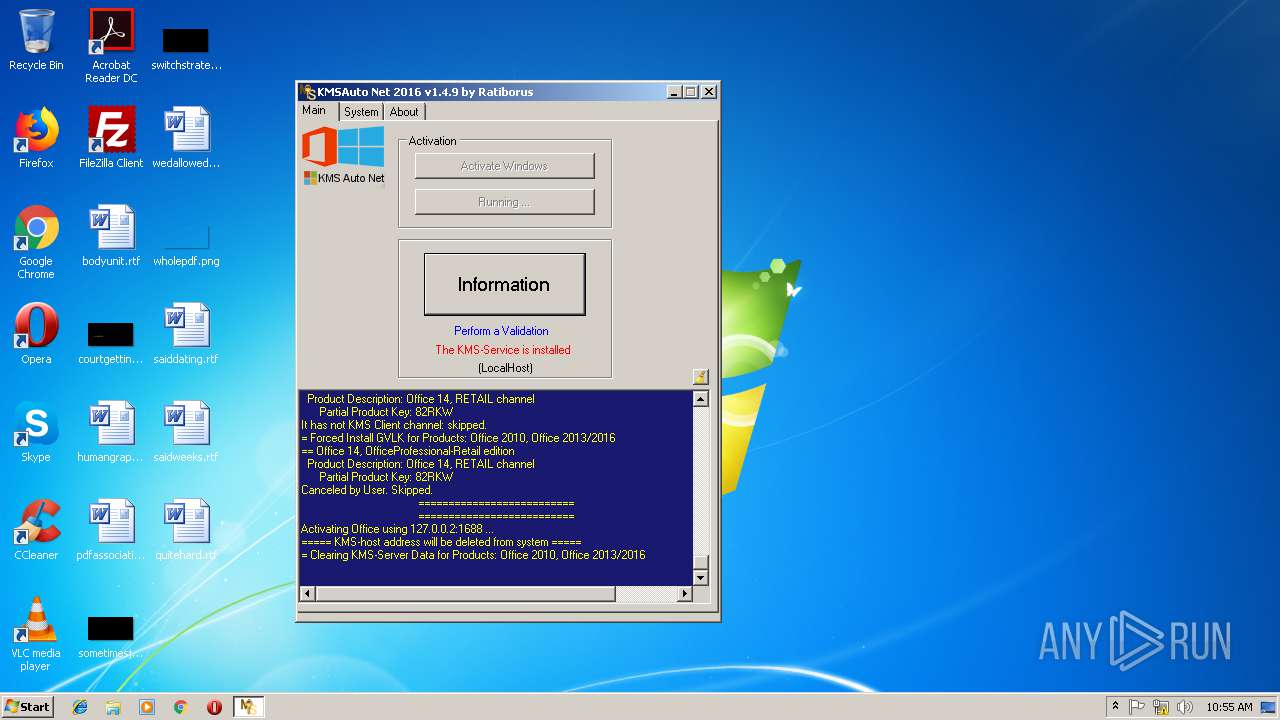
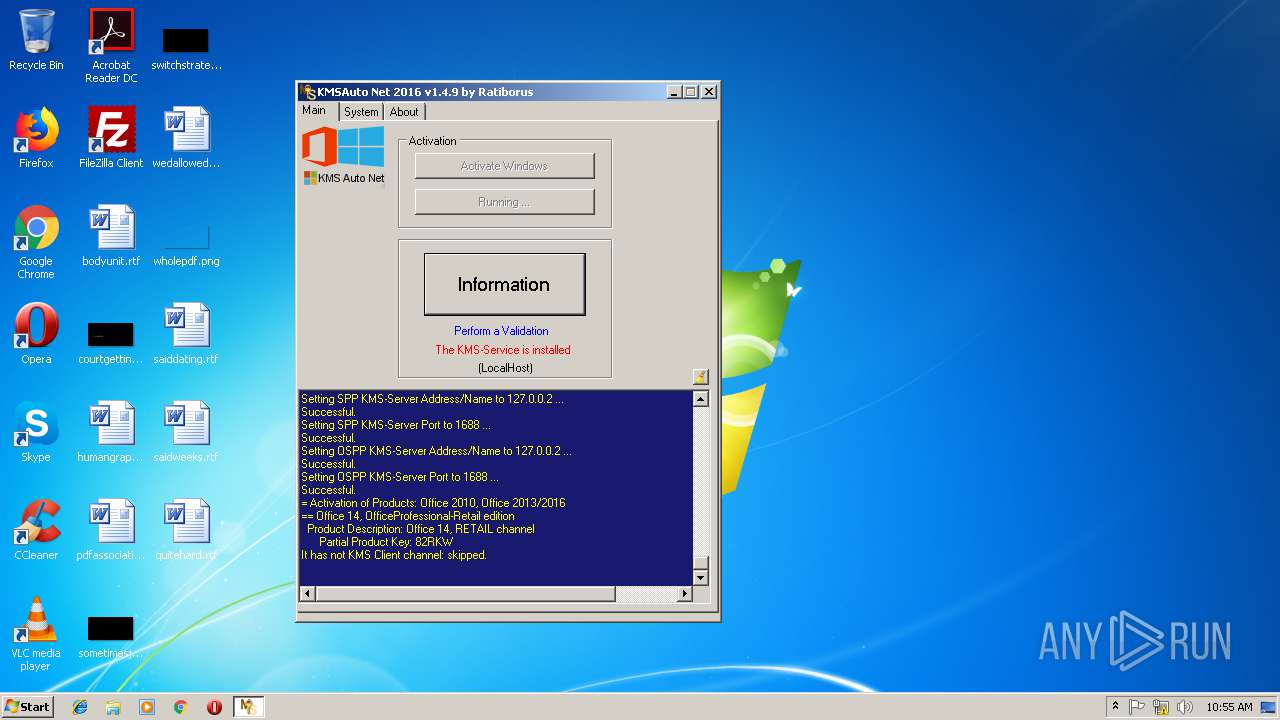
| Verdict: | Malicious activity |
| Analysis date: | December 31, 2018, 10:51:30 |
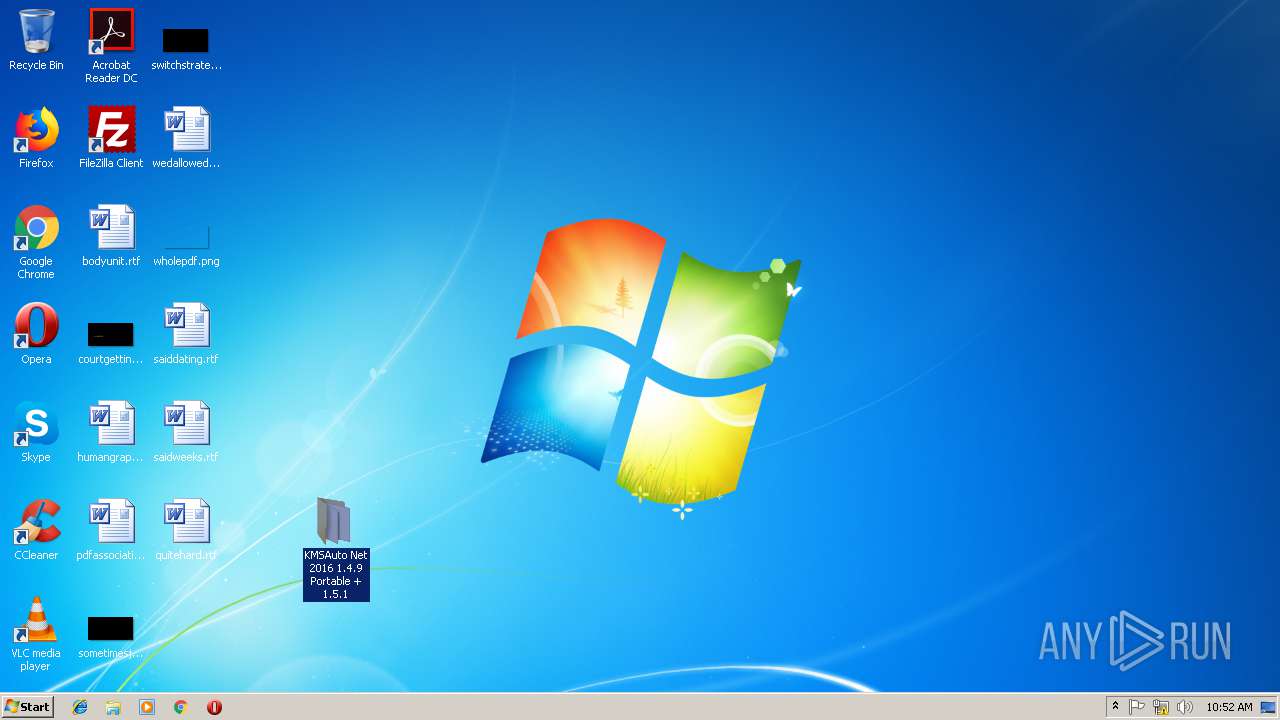
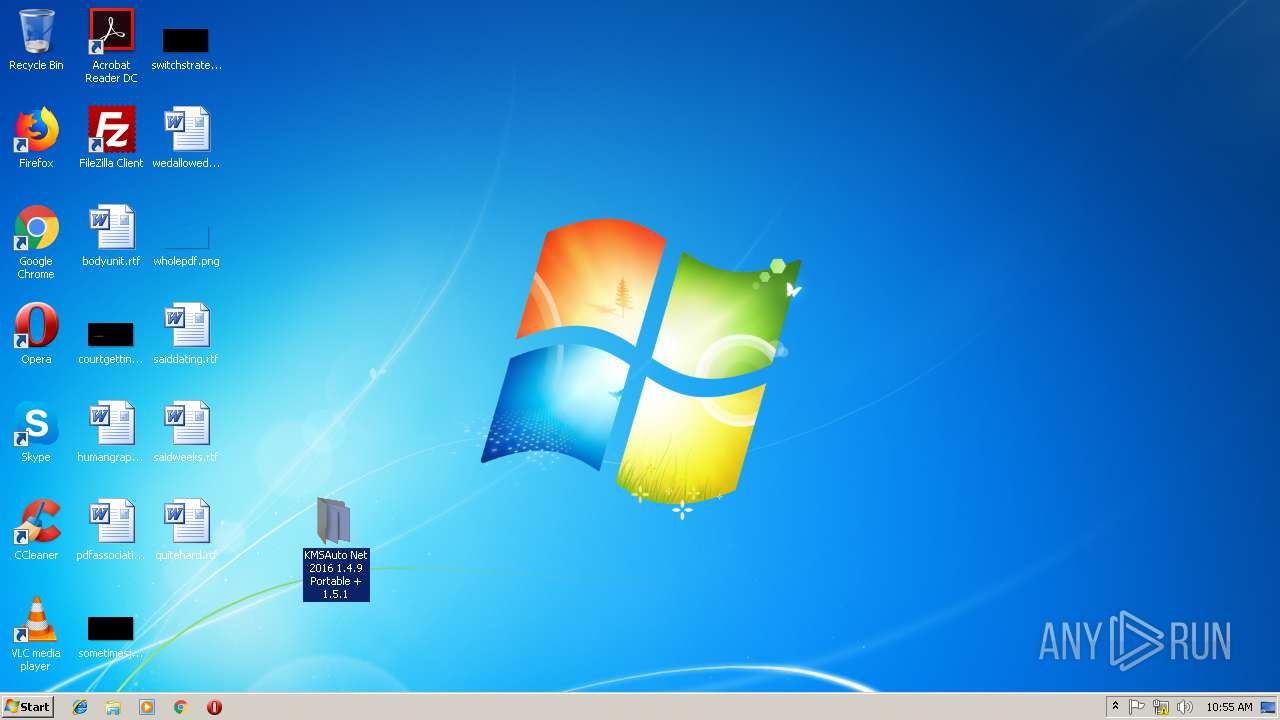
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 386CB87E6430D914820D793DB19D7D33 |
| SHA1: | 160A3788D24787FBF1C7579AC2A5DA2D0AE8E25B |
| SHA256: | D4230CAE5C3E1B11FCA61A711E7F3886088F6728858108A6811670AA3616A57B |
| SSDEEP: | 196608:qpAtZ+U7OeubvGx9Y9oFMmtcdV0wvnZDsuKYqCVtIlehIuoOCYgM2cXNAOQ8JWcC:qpesfvuw2FMmKwanBsuYLu8Yg/Pl8JWJ |
MALICIOUS
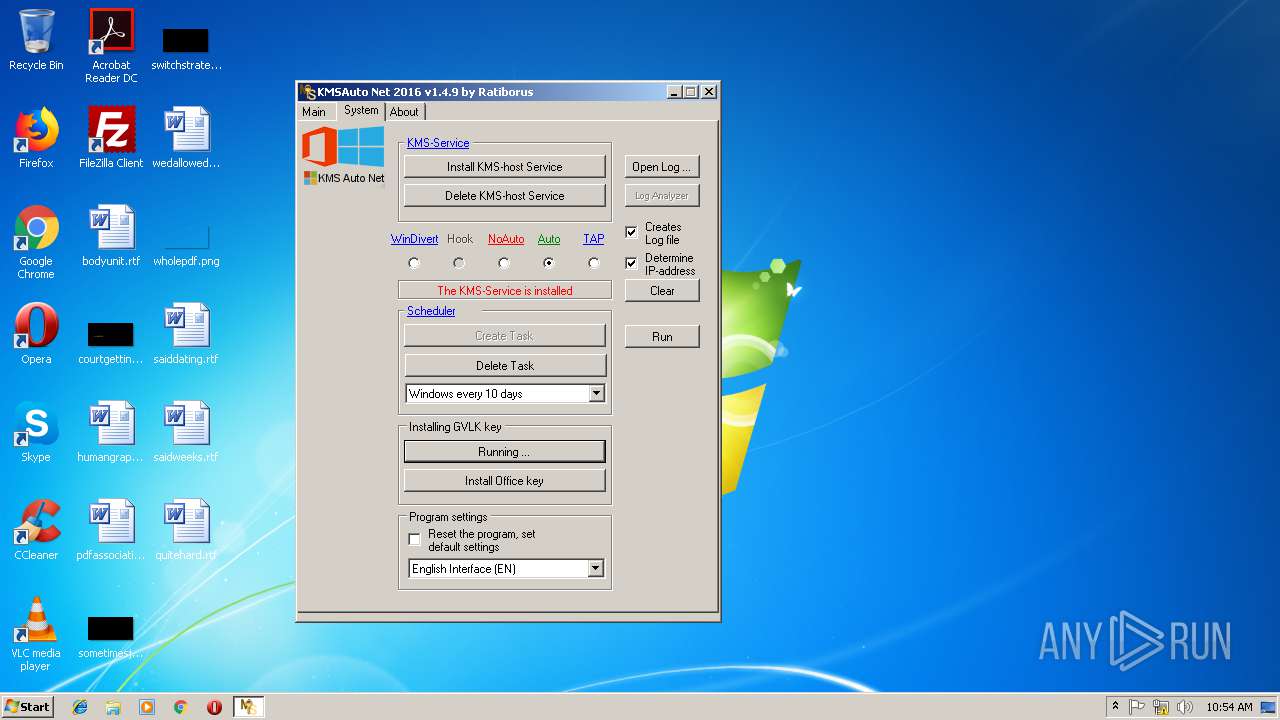
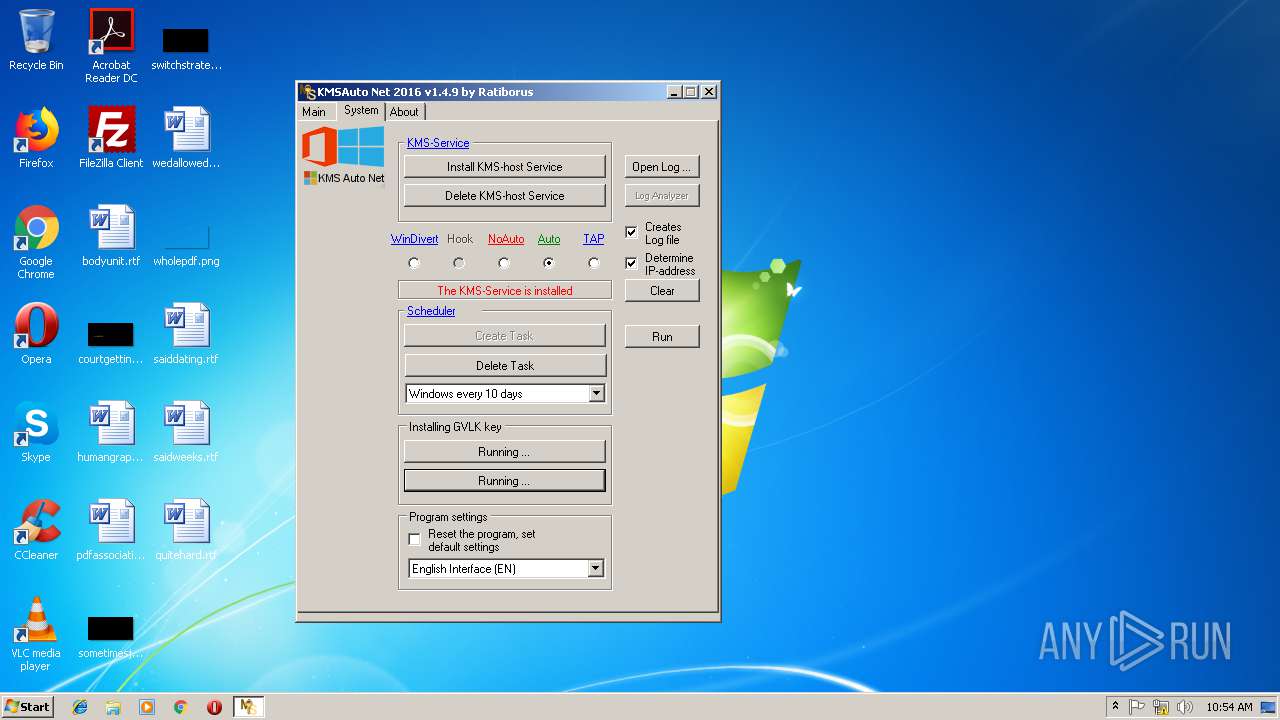
Application was dropped or rewritten from another process
- bin.dat (PID: 1908)
- KMSAuto Net.exe (PID: 2588)
- KMSAuto Net.exe (PID: 1352)
- bin.dat (PID: 180)
- bin_x86.dat (PID: 1820)
- bin_x86.dat (PID: 3360)
- bin.dat (PID: 2364)
- bin_x86.dat (PID: 2132)
- AESDecoder.exe (PID: 2500)
- AESDecoder.exe (PID: 292)
- KMSSS.exe (PID: 2616)
- AESDecoder.exe (PID: 3792)
- KMSAuto Net.exe (PID: 2100)
- bin_x86.dat (PID: 2940)
- KMSSS.exe (PID: 2604)
- FakeClient.exe (PID: 3004)
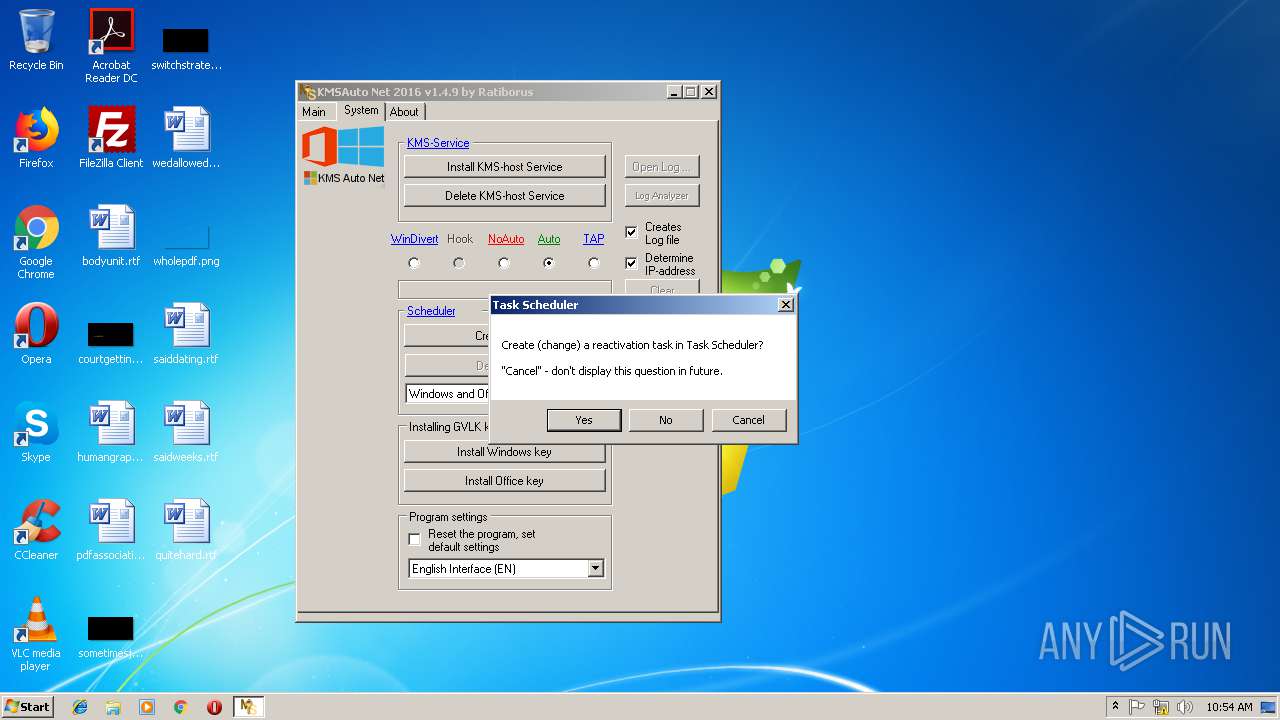
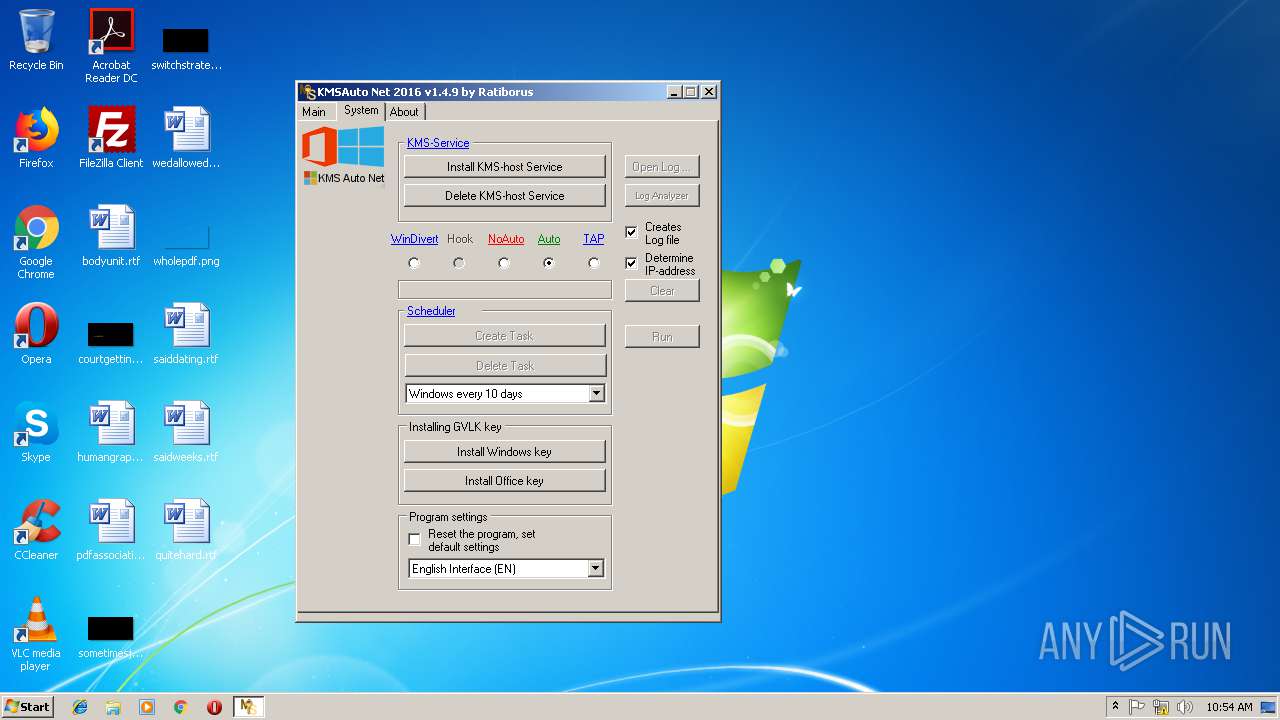
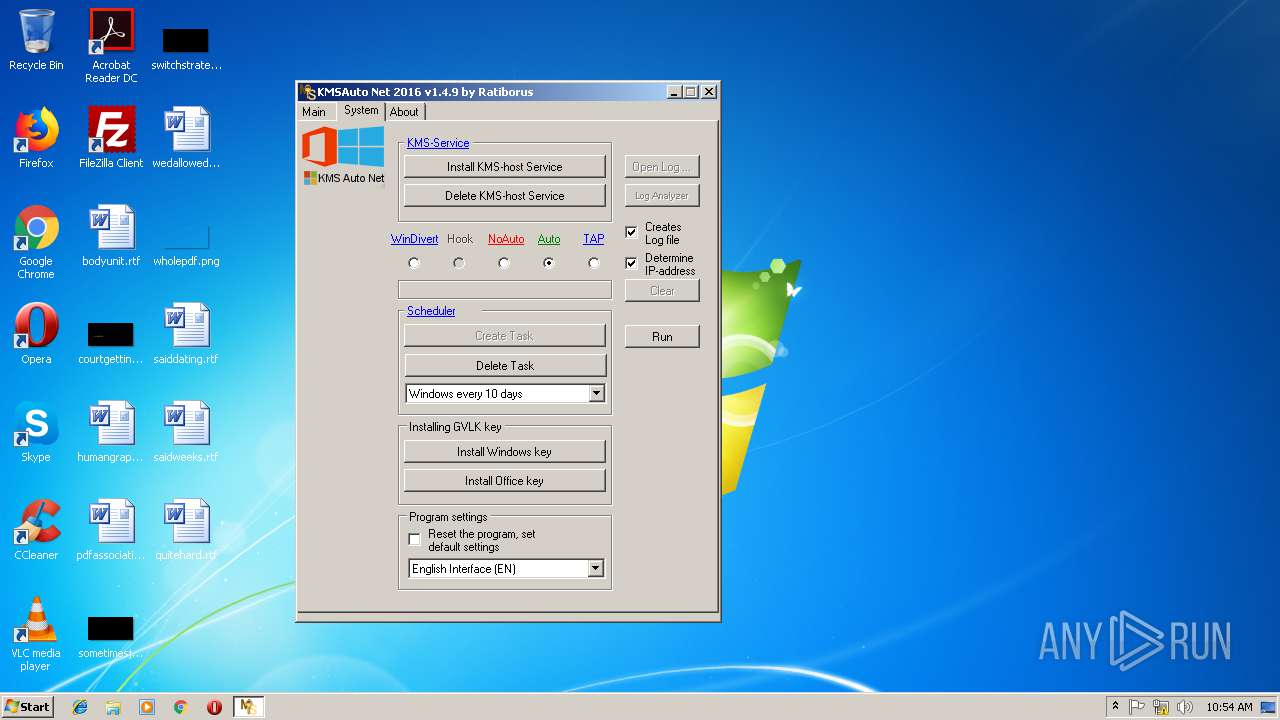
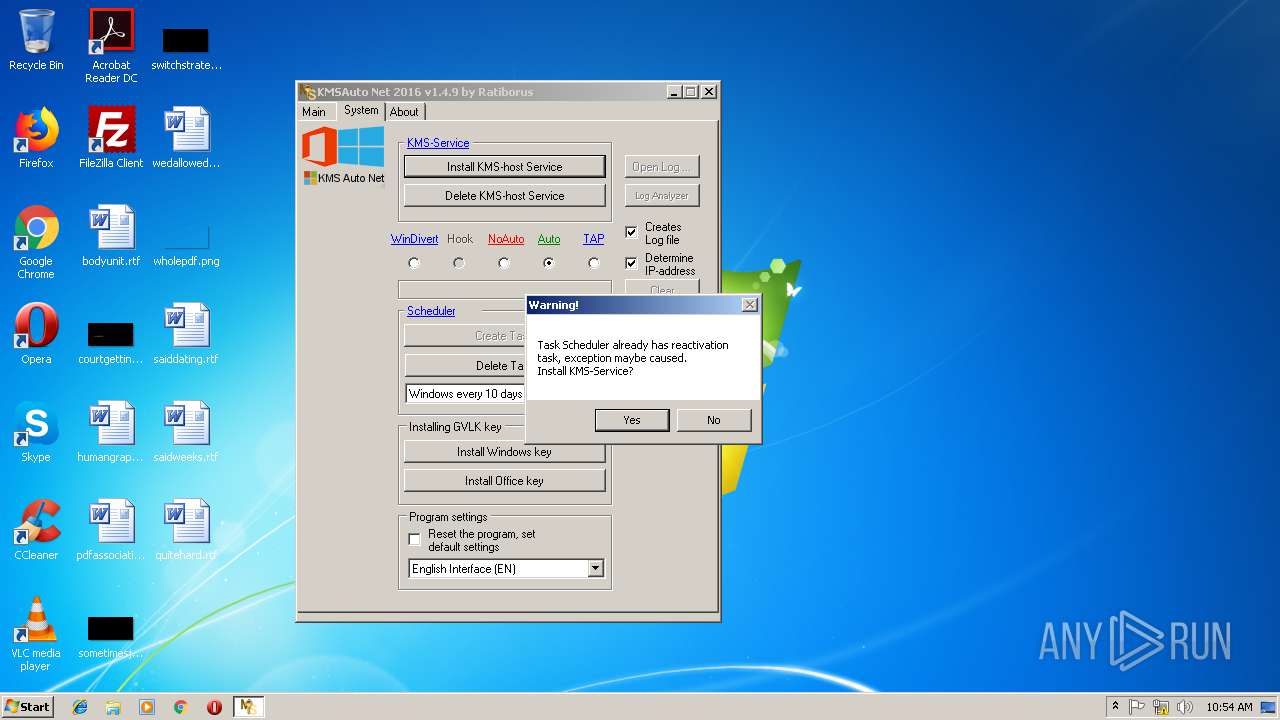
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1156)
- schtasks.exe (PID: 2884)
- schtasks.exe (PID: 3348)
- schtasks.exe (PID: 2340)
- schtasks.exe (PID: 3204)
- schtasks.exe (PID: 2176)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3772)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 3064)
- cmd.exe (PID: 3256)
Loads dropped or rewritten executable
- FakeClient.exe (PID: 3004)
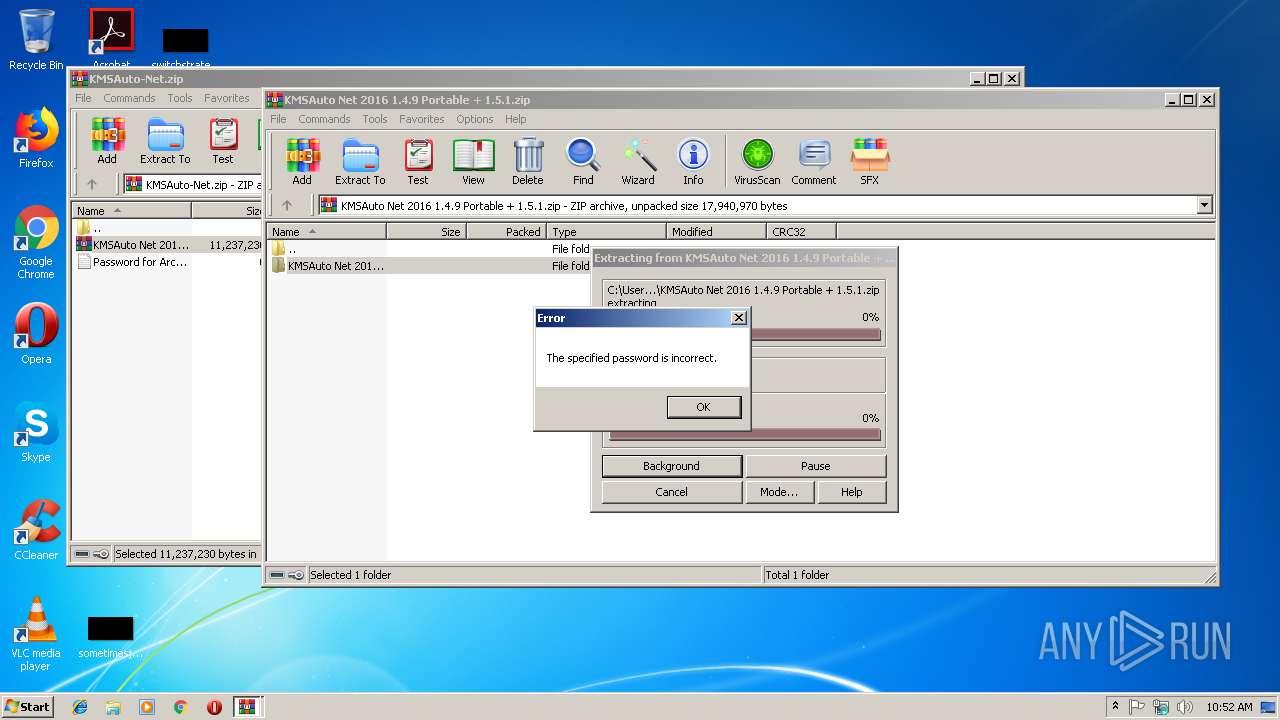
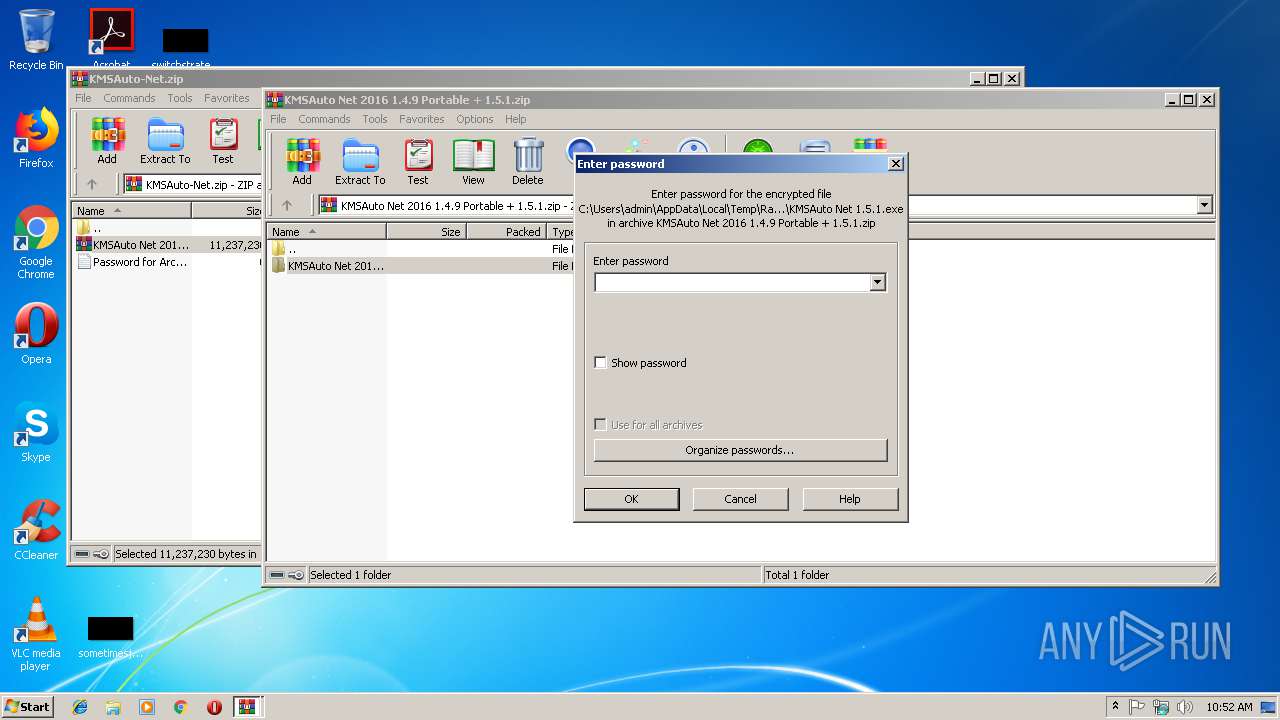
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 3236)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 1352)
Reads Environment values
- KMSAuto Net.exe (PID: 1352)
- KMSAuto Net.exe (PID: 2100)
Creates files in the program directory
- bin.dat (PID: 1908)
- AESDecoder.exe (PID: 2500)
- bin_x86.dat (PID: 1820)
- KMSAuto Net.exe (PID: 1352)
- KMSSS.exe (PID: 2604)
- AESDecoder.exe (PID: 3792)
- bin.dat (PID: 180)
- bin_x86.dat (PID: 3360)
- bin.dat (PID: 2364)
- bin_x86.dat (PID: 2132)
- AESDecoder.exe (PID: 292)
- cmd.exe (PID: 2468)
- KMSSS.exe (PID: 2616)
- KMSAuto Net.exe (PID: 2100)
- bin_x86.dat (PID: 2940)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 1352)
- AESDecoder.exe (PID: 2500)
- bin_x86.dat (PID: 1820)
- bin_x86.dat (PID: 3360)
- AESDecoder.exe (PID: 3792)
- AESDecoder.exe (PID: 292)
- bin.dat (PID: 2364)
- bin_x86.dat (PID: 2132)
- bin_x86.dat (PID: 2940)
Starts application with an unusual extension
- cmd.exe (PID: 1560)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 2352)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 3012)
- cmd.exe (PID: 2892)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4024)
- cmd.exe (PID: 3512)
- KMSAuto Net.exe (PID: 2100)
- KMSAuto Net.exe (PID: 1352)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 1728)
- cmd.exe (PID: 824)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 1352)
Creates or modifies windows services
- KMSAuto Net.exe (PID: 1352)
Uses REG.EXE to modify Windows registry
- KMSAuto Net.exe (PID: 1352)
- cmd.exe (PID: 1728)
- KMSAuto Net.exe (PID: 2100)
Executes scripts
- KMSAuto Net.exe (PID: 1352)
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 1352)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
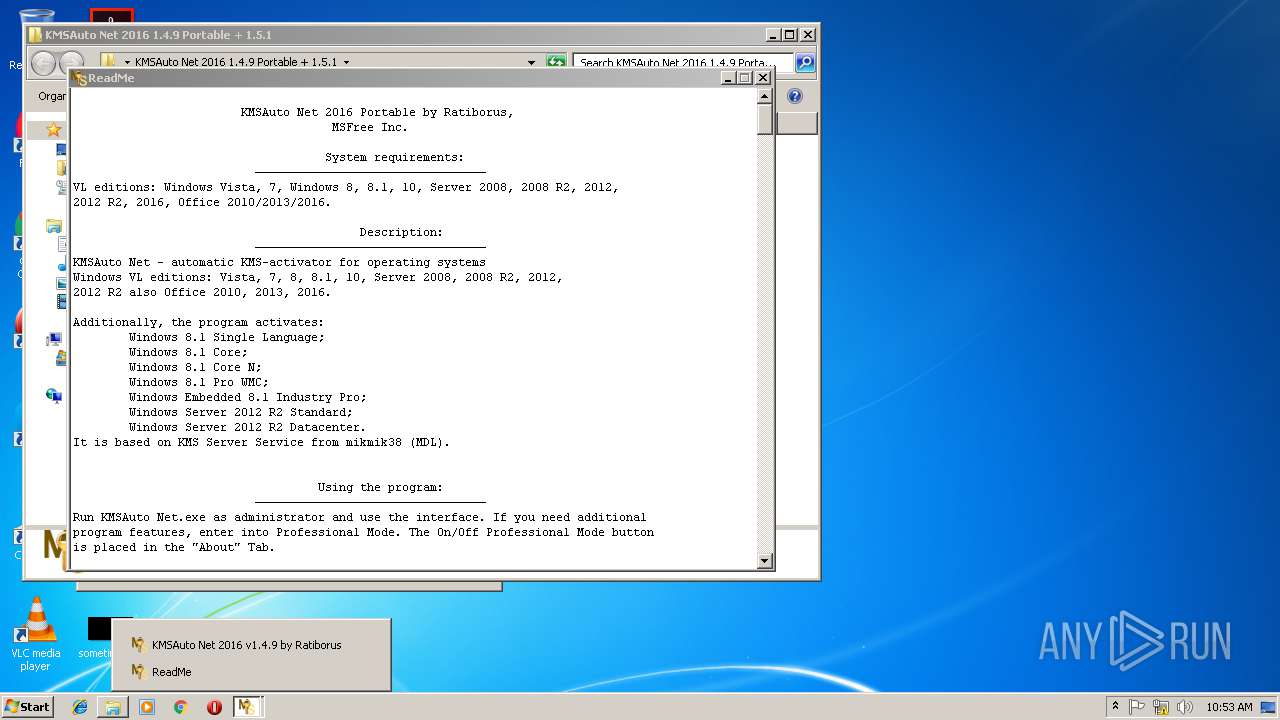
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
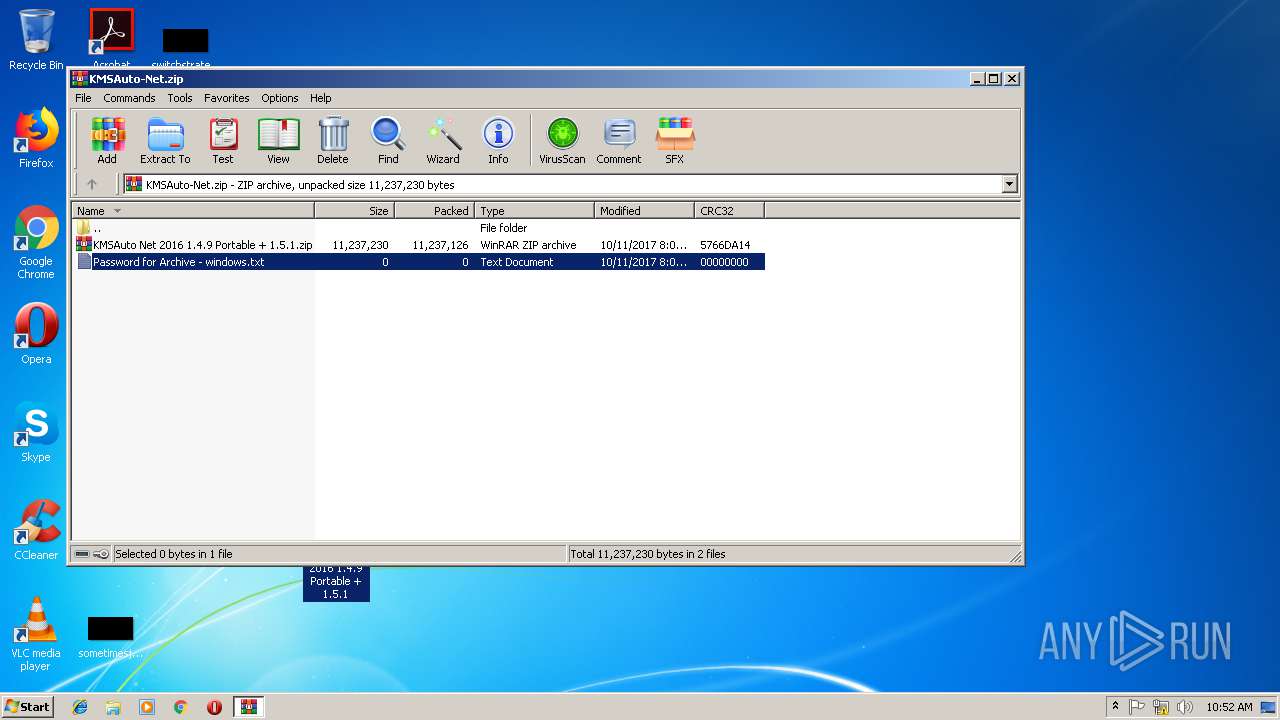
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:10:11 22:06:01 |
| ZipCRC: | 0x5766da14 |
| ZipCompressedSize: | 11237126 |
| ZipUncompressedSize: | 11237230 |
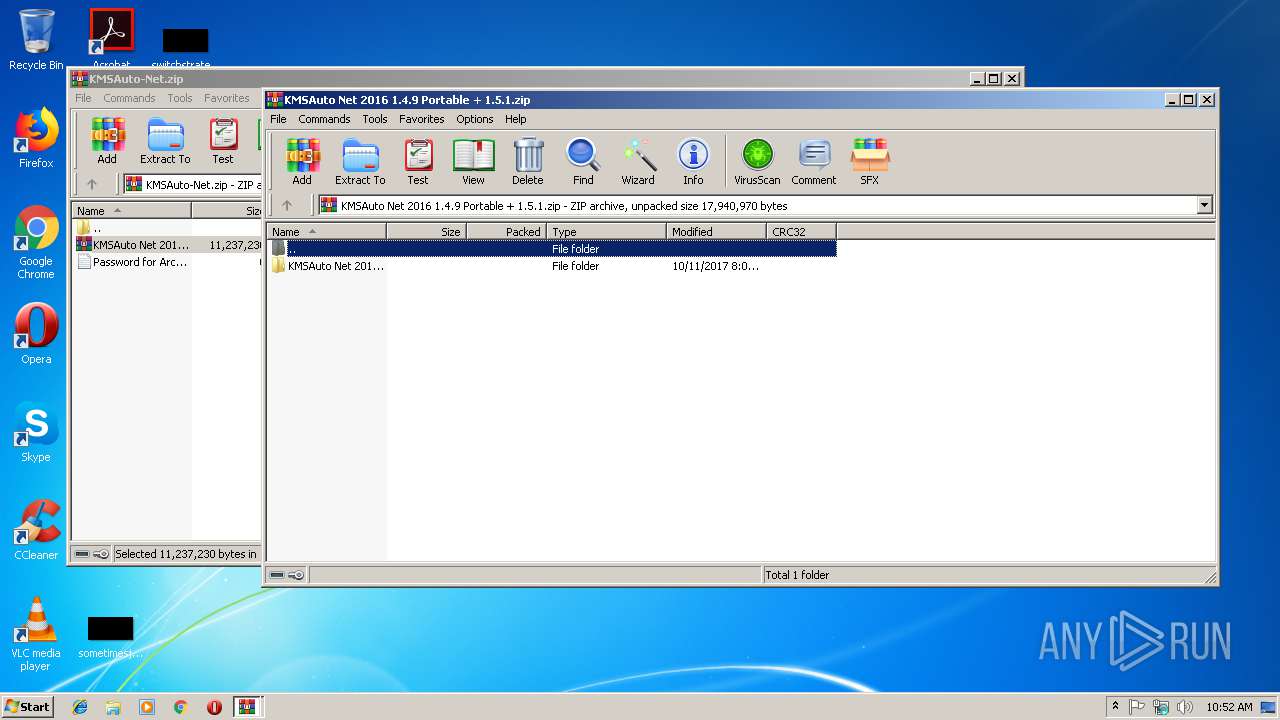
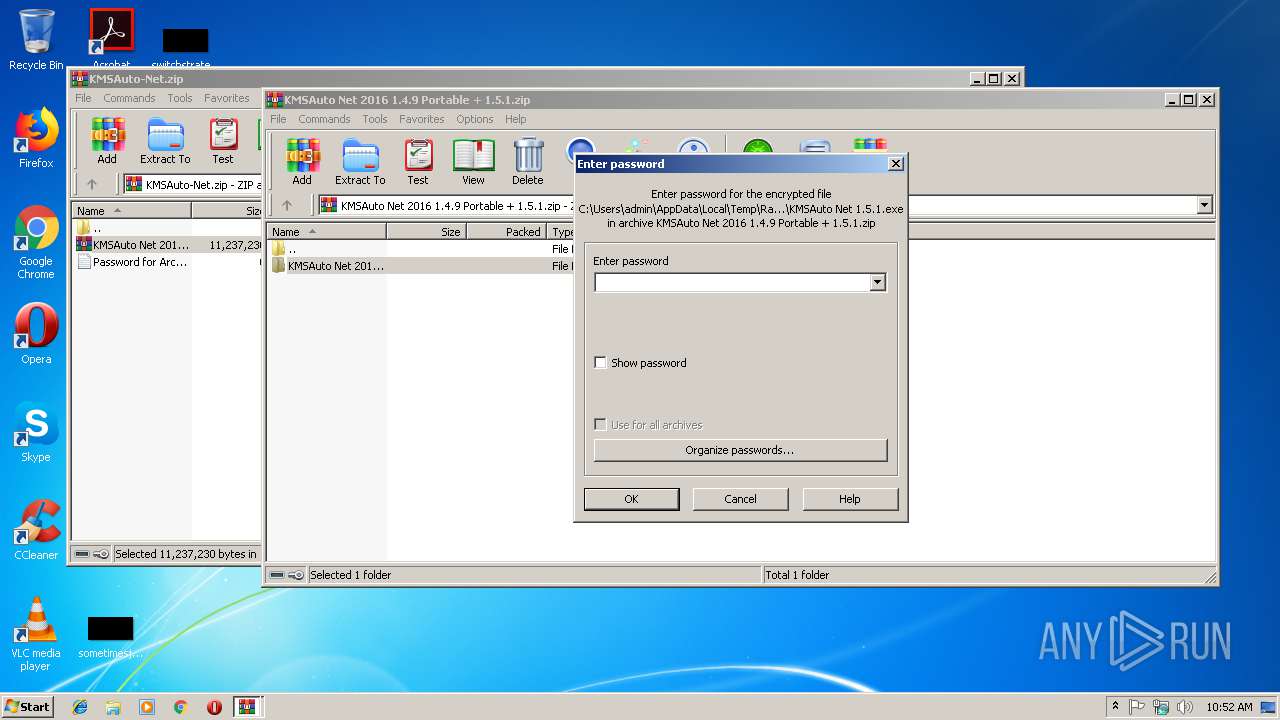
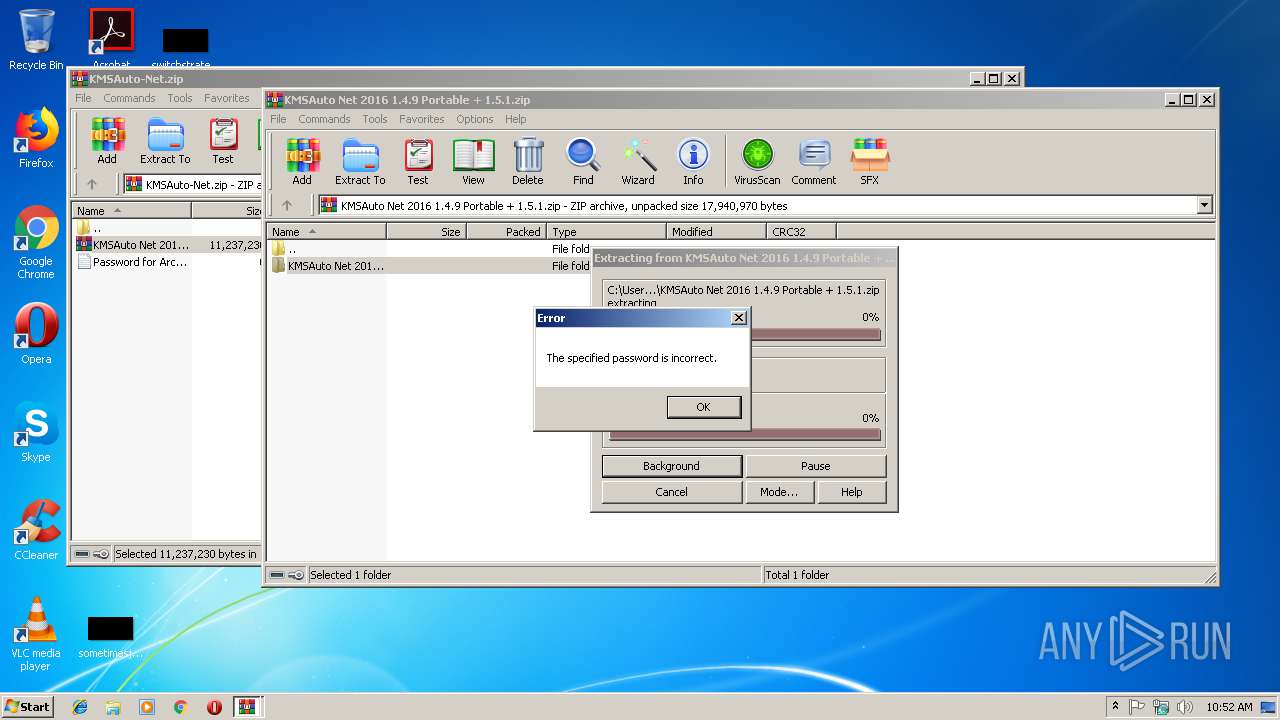
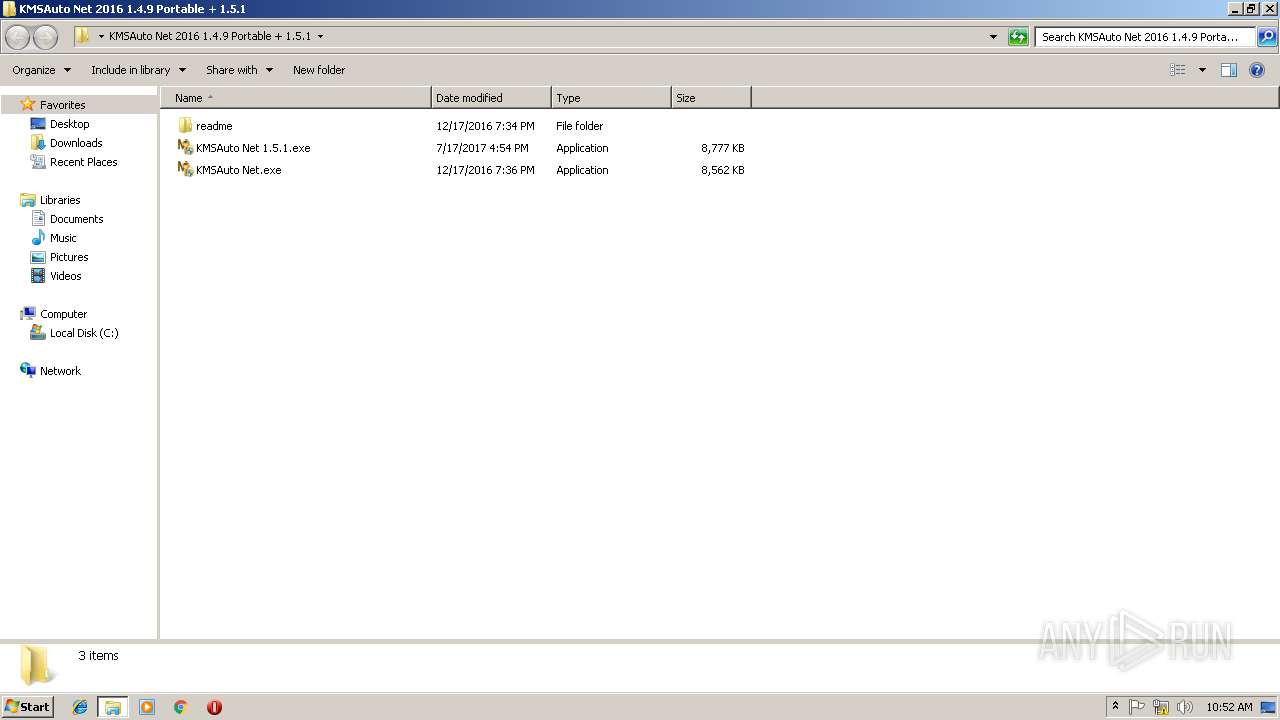
| ZipFileName: | KMSAuto Net 2016 1.4.9 Portable + 1.5.1.zip |
Total processes
283
Monitored processes
136
Malicious processes
6
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | bin.dat -y -pkmsauto | C:\ProgramData\KMSAutoS\bin.dat | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 236 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\AESDecoder.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 388 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55C92734-D682-4D71-983E-D6EC3F16059F" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
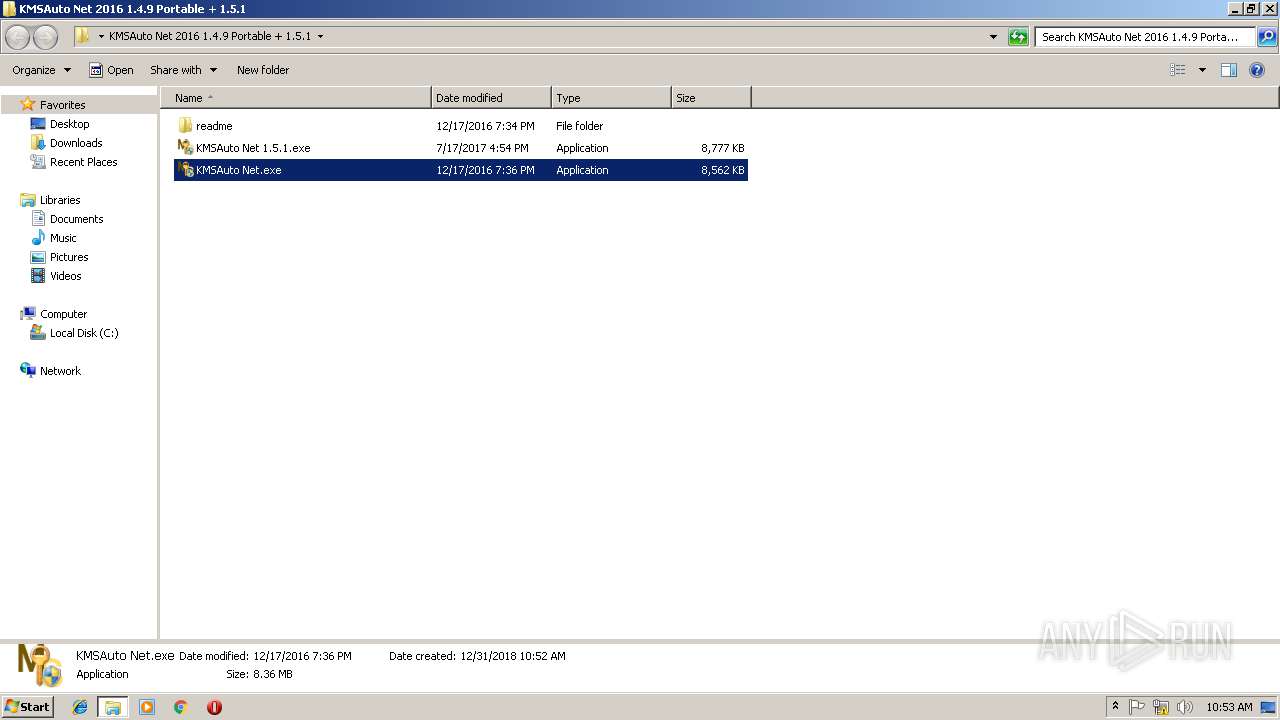
| 564 | "C:\Users\admin\Desktop\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\KMSAuto Net 1.5.1.exe" | C:\Users\admin\Desktop\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\KMSAuto Net 1.5.1.exe | explorer.exe | ||||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Exit code: 0 Version: 1.5.1 Modules
| |||||||||||||||
| 584 | C:\Windows\System32\cmd.exe /D /c del /F /Q "test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 624 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | C:\Windows\system32\cmd.exe /c netstat -ano | find ":1688 " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 916 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 741
Read events
1 373
Write events
348
Delete events
20
Modification events
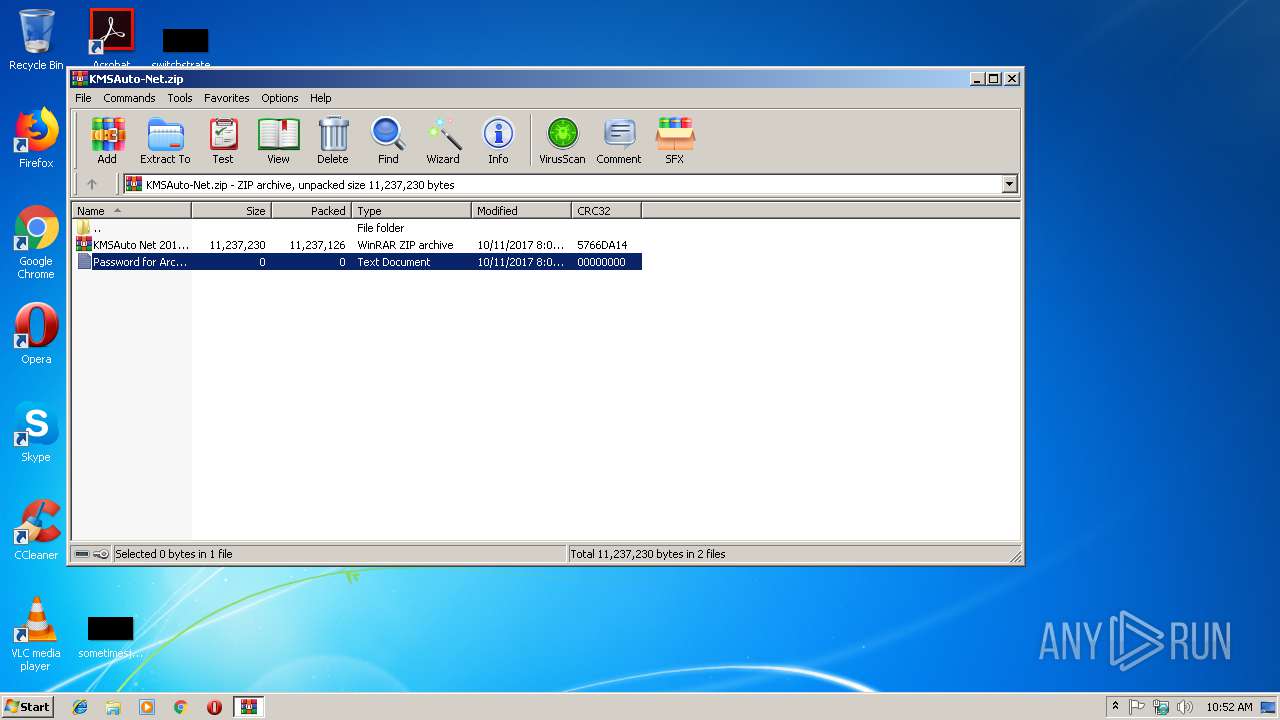
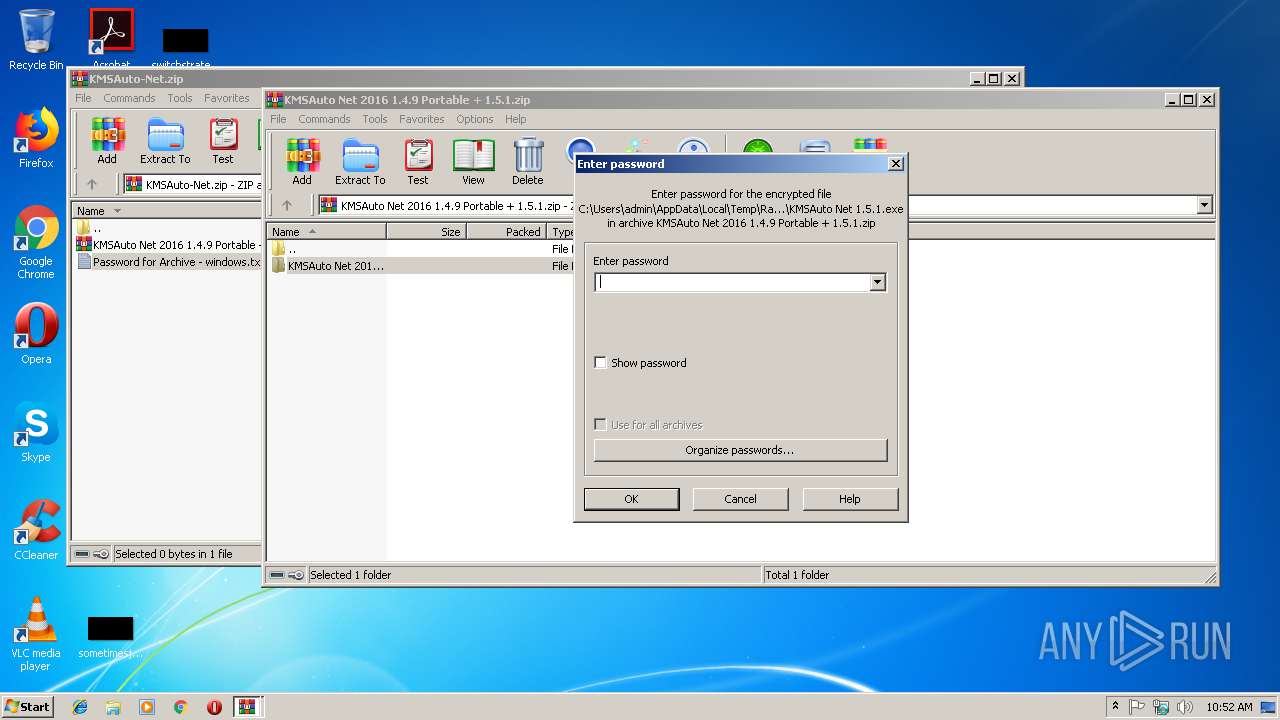
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSAuto-Net.zip | |||
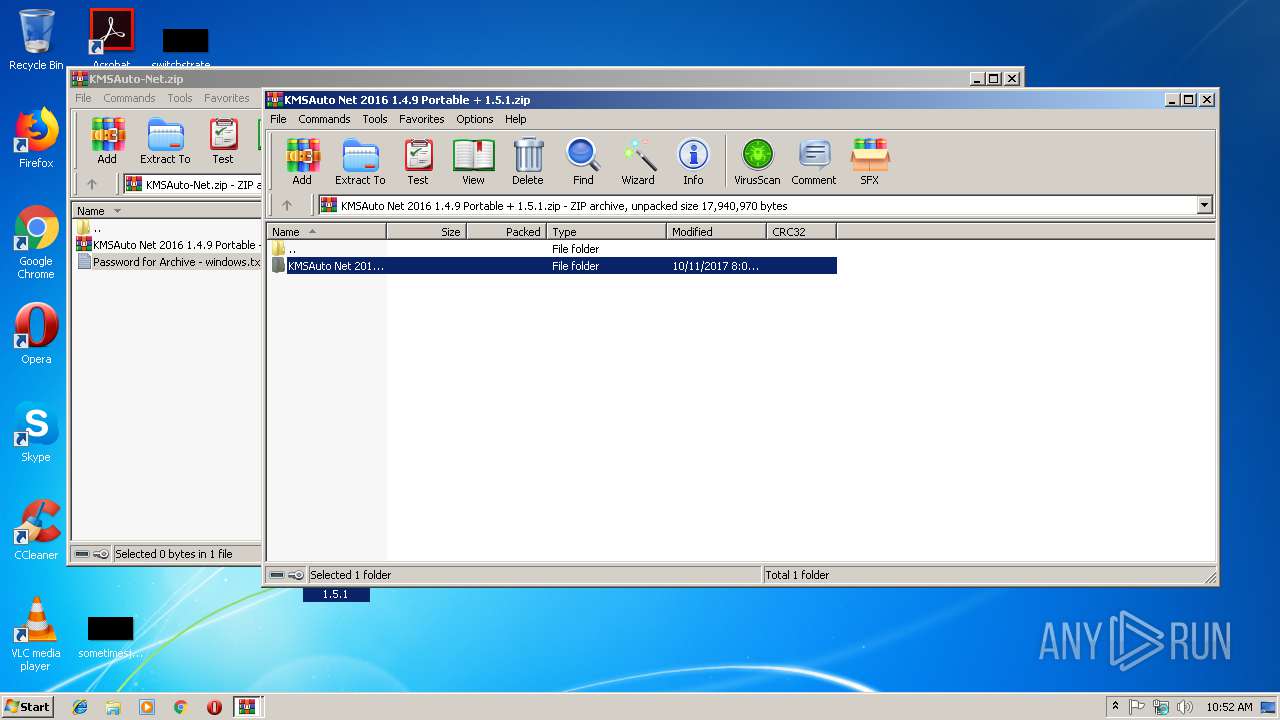
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
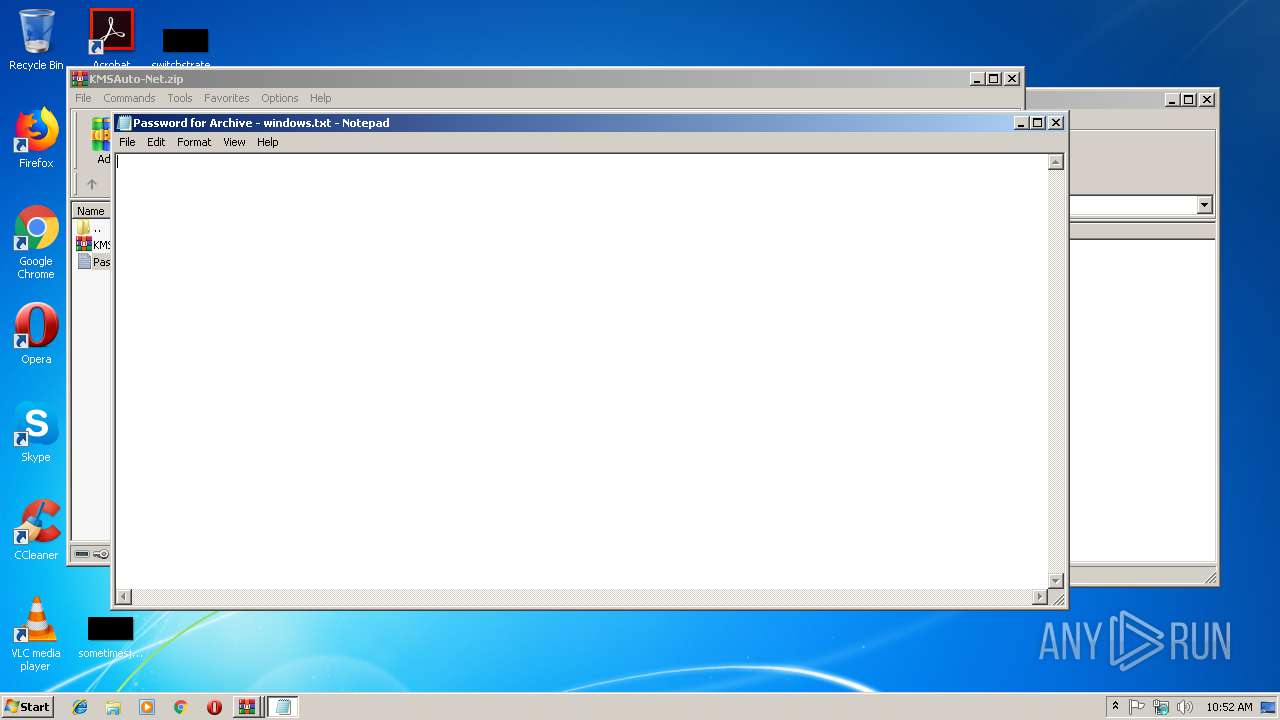
| (PID) Process: | (2620) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 110 | |||
| (PID) Process: | (2620) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 110 | |||
Executable files
48
Suspicious files
12
Text files
127
Unknown types
20
Dropped files
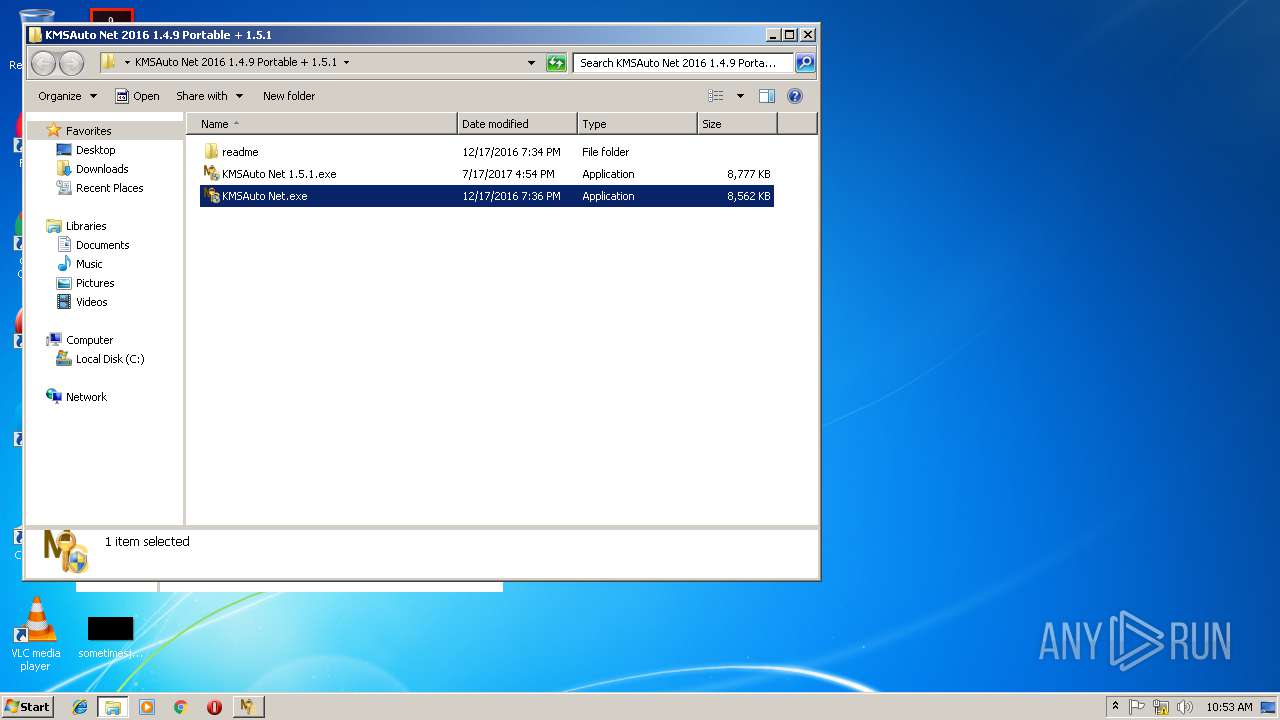
PID | Process | Filename | Type | |
|---|---|---|---|---|
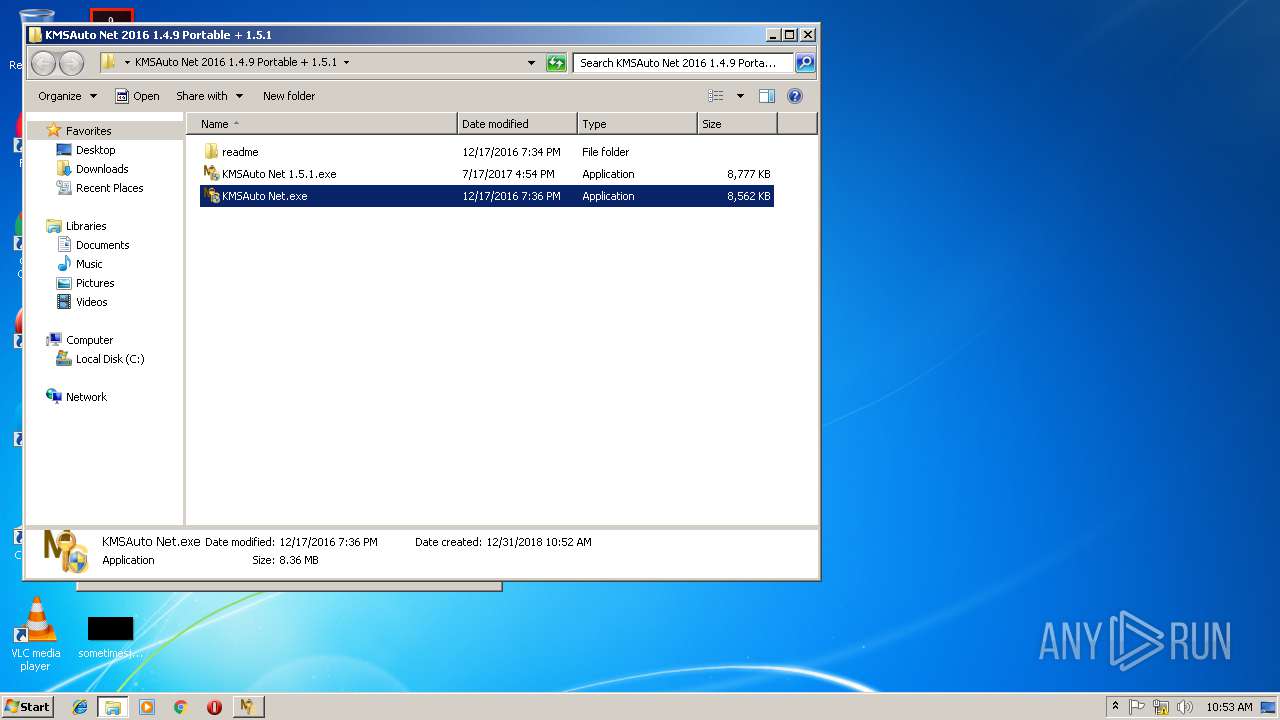
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\KMSAuto Net 1.5.1.exe | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\KMSAuto Net.exe | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_bg.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_cn.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_en.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_es.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_fr.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_kms.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_ru.txt | — | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3796.4058\KMSAuto Net 2016 1.4.9 Portable + 1.5.1\readme\readme_ua.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [12/31/2018 10:55.16.549] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [12/31/2018 10:55.16.564] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [12/31/2018 10:55.16.564] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|