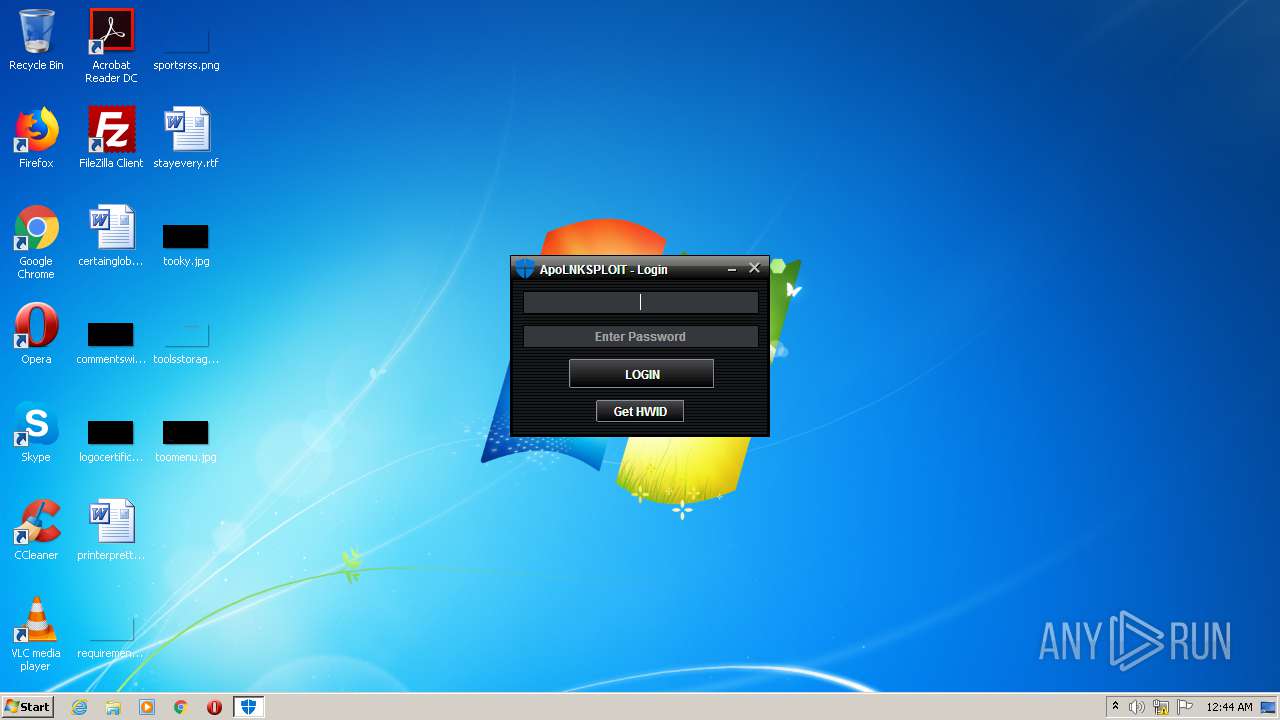
| File name: | ApoLNKSPLOIT.exe |
| Full analysis: | https://app.any.run/tasks/b9a2470b-5997-4d00-b8a9-93dfc9b9d8d4 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2021, 00:44:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | CAB4B3BF710436E742D39690EDCD45DB |
| SHA1: | CFFF184DC77DF81E9B2BF39D9099549F9F6A8733 |
| SHA256: | D40365E11ADCBB5278E5E5B968E1C6A411F2E12E352DBE94D3A6F89ADFF8FDF5 |
| SSDEEP: | 196608:zTdofr5OAIZMWDEllrbZB+BNJQUERXVOi6l:HqIZMq0tHYNSJRFd6l |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- ApoLNKSPLOIT.exe (PID: 2500)
Creates files in the user directory
- javaw.exe (PID: 2600)
Executes scripts
- javaw.exe (PID: 2600)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:29 23:47:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 19968 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Nov-2020 22:47:38 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 29-Nov-2020 22:47:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03278 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x00002888 | 0x00002A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.20111 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.01924 | 20 | UNKNOWN | Process Default Language | RT_GROUP_ICON |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
102 | 4.26779 | 115 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
53
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto6573521504309359449.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 856 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto2607223142947584537.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1724 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto4351751905495911090.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1960 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto9170201685451119248.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\Temp\ApoLNKSPLOIT.exe" | C:\Users\admin\AppData\Local\Temp\ApoLNKSPLOIT.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2556 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto1224524039518900727.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\ApoLNKSPLOIT.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | ApoLNKSPLOIT.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2684 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto2205723090074318226.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2928 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto8573567523204294589.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3672 | cscript //NoLogo C:\Users\admin\AppData\Local\Temp\realhowto1723273522773722454.vbs | C:\Windows\system32\cscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
153
Read events
152
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2600) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
0
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto963060423054769119.vbs | text | |
MD5:4C20CF9F87DC609F71E5A6D184D02BB0 | SHA256:2B327A612AF1361361211129F71022CE23A9ABE628E948C897316F2175A63496 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto6573521504309359449.vbs | text | |
MD5:7E489395E787BBC1F686CB0DA48E57EF | SHA256:E8A9F9C558304D66782332598C350EE351A9F8E7601576D5841B7DBF3A08EC30 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto8573567523204294589.vbs | text | |
MD5:7E489395E787BBC1F686CB0DA48E57EF | SHA256:E8A9F9C558304D66782332598C350EE351A9F8E7601576D5841B7DBF3A08EC30 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto9170201685451119248.vbs | text | |
MD5:7E489395E787BBC1F686CB0DA48E57EF | SHA256:E8A9F9C558304D66782332598C350EE351A9F8E7601576D5841B7DBF3A08EC30 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto2607223142947584537.vbs | text | |
MD5:4C20CF9F87DC609F71E5A6D184D02BB0 | SHA256:2B327A612AF1361361211129F71022CE23A9ABE628E948C897316F2175A63496 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto2205723090074318226.vbs | text | |
MD5:7E489395E787BBC1F686CB0DA48E57EF | SHA256:E8A9F9C558304D66782332598C350EE351A9F8E7601576D5841B7DBF3A08EC30 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto1224524039518900727.vbs | text | |
MD5:4C20CF9F87DC609F71E5A6D184D02BB0 | SHA256:2B327A612AF1361361211129F71022CE23A9ABE628E948C897316F2175A63496 | |||
| 2600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\realhowto4351751905495911090.vbs | text | |
MD5:7E489395E787BBC1F686CB0DA48E57EF | SHA256:E8A9F9C558304D66782332598C350EE351A9F8E7601576D5841B7DBF3A08EC30 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
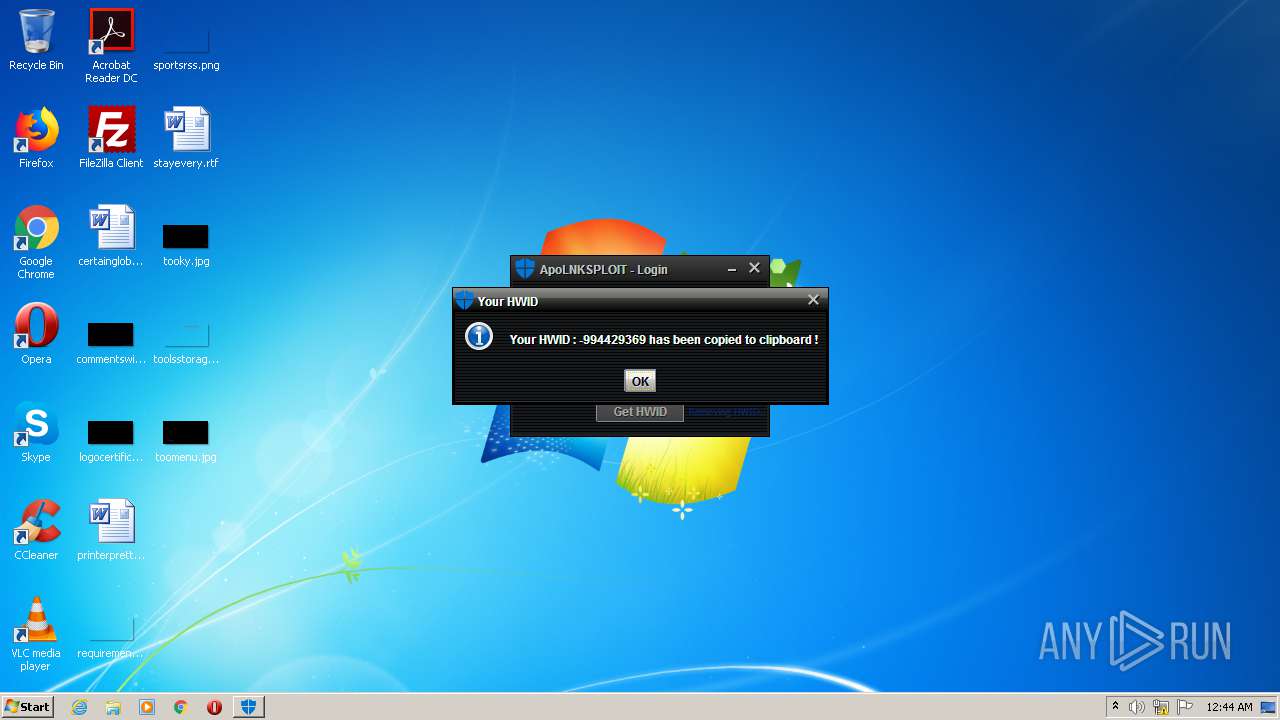
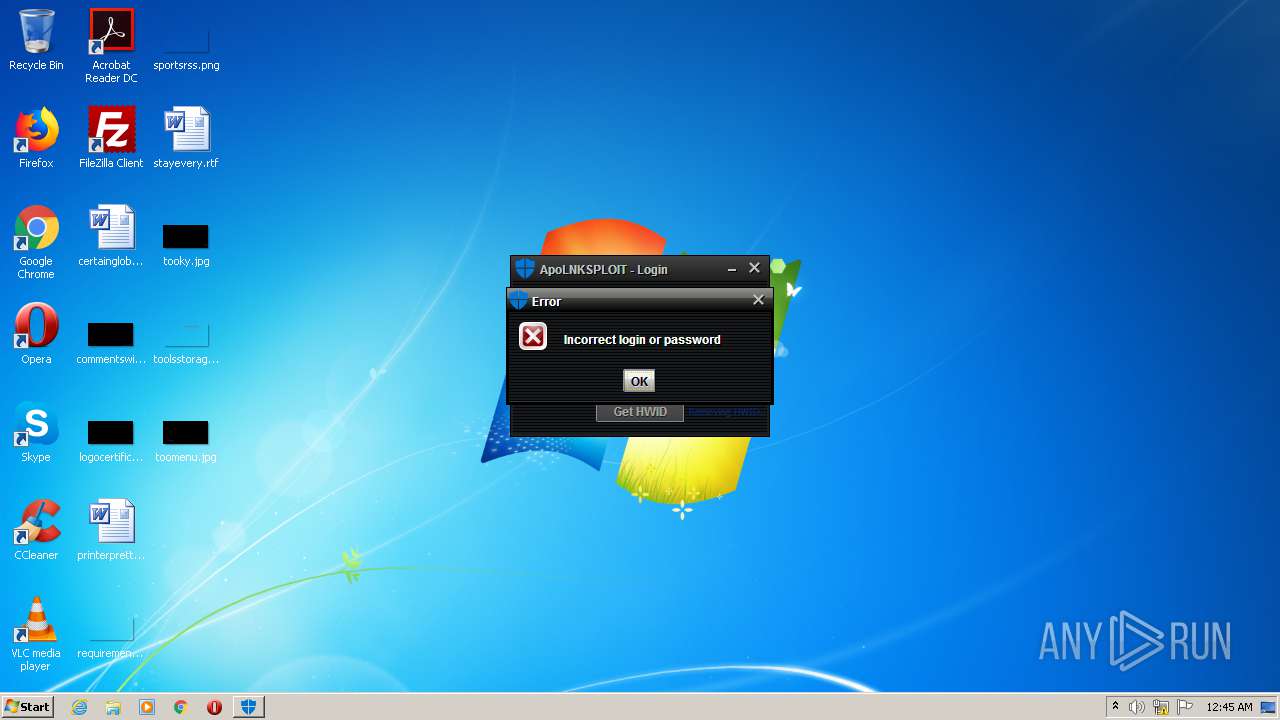
2600 | javaw.exe | GET | 200 | 75.119.205.210:80 | http://antuza.dreamhosters.com/versionlnk.html | US | ini | 20 b | unknown |
2600 | javaw.exe | GET | 200 | 75.119.205.210:80 | http://antuza.dreamhosters.com/loginapp.php?name=yeet&password=yeet&hwid=-994429369 | US | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2600 | javaw.exe | 75.119.205.210:80 | antuza.dreamhosters.com | New Dream Network, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
antuza.dreamhosters.com |
| unknown |