| File name: | b00def042414aa226b4abeace6039371 |
| Full analysis: | https://app.any.run/tasks/74daac27-34f3-419a-89fd-5e77b8b5a284 |
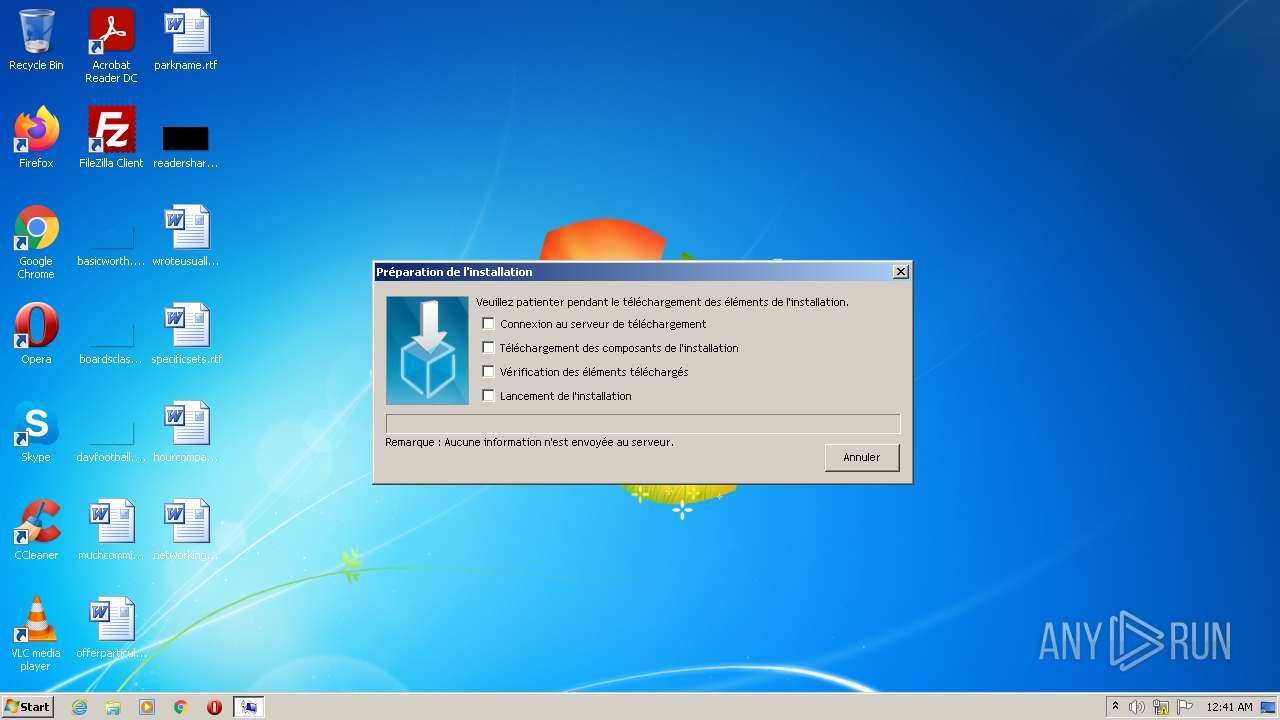
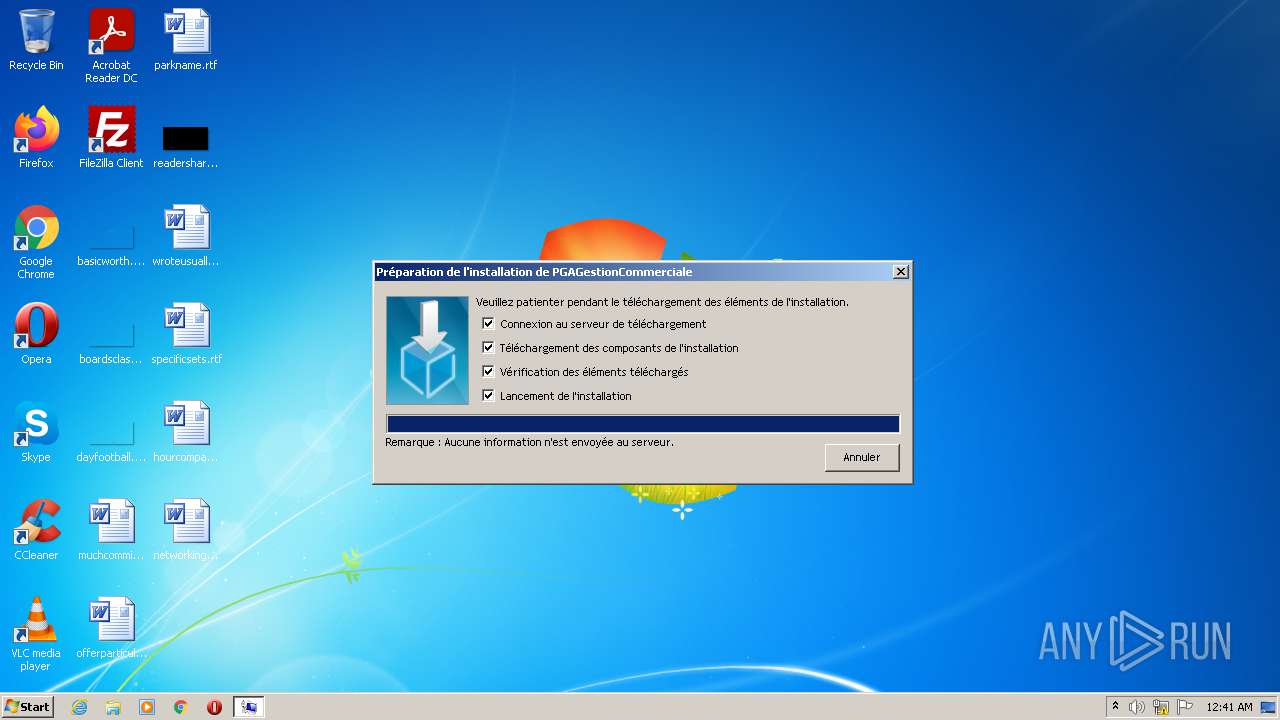
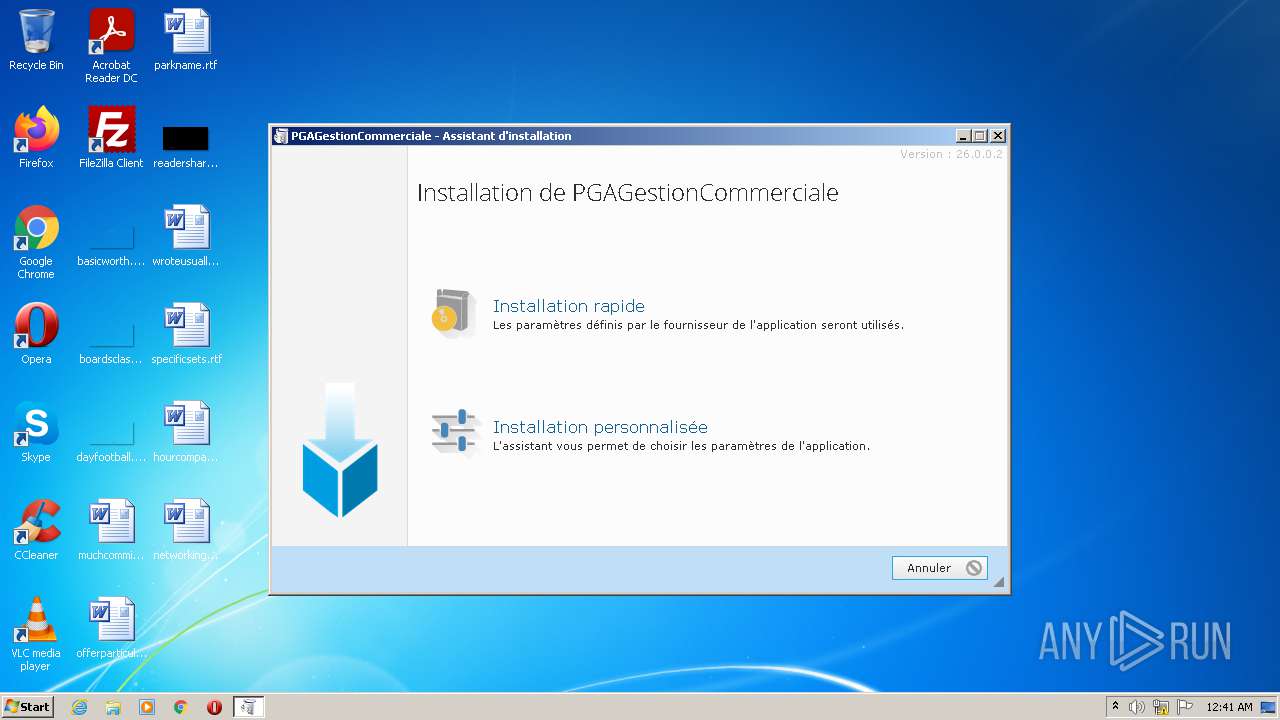
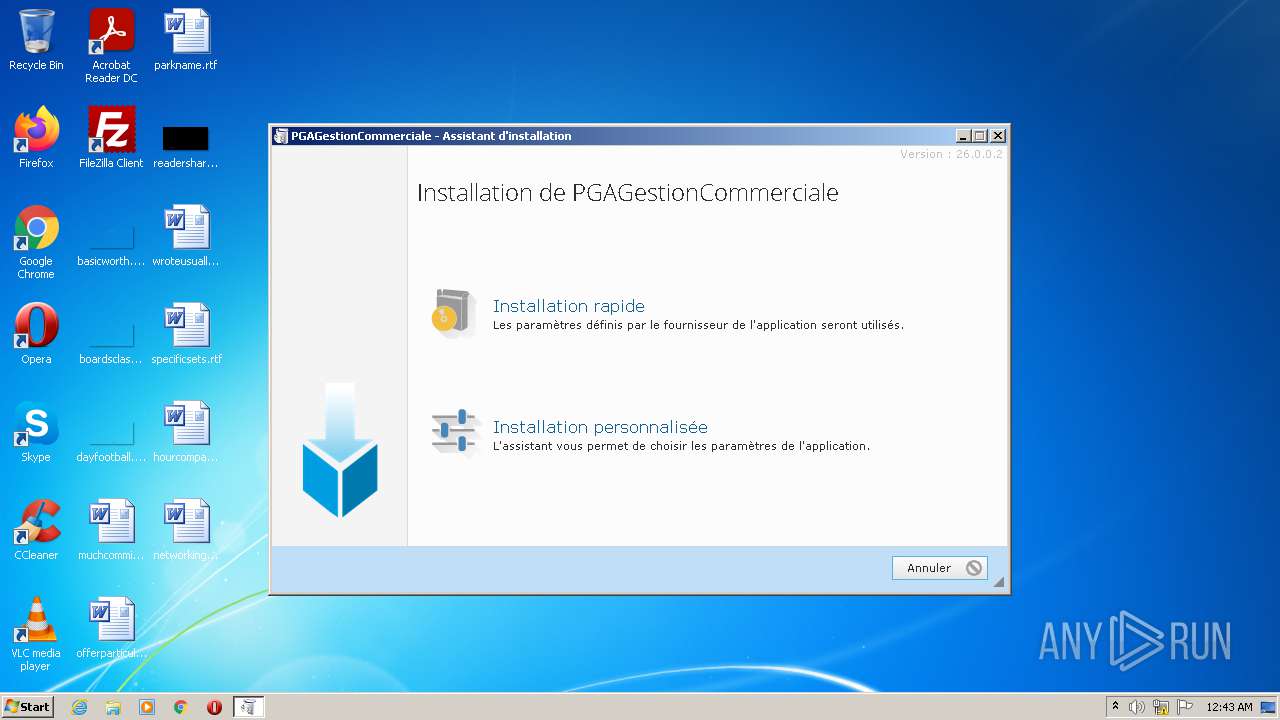
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2021, 23:41:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B00DEF042414AA226B4ABEACE6039371 |
| SHA1: | 91B55A4B55A02B89FA5616D5D2CB4086F2E38F45 |
| SHA256: | D3E7BFEF404BE4AF272C7C21A9F32C5A6FBBF1BC0C33CFA9C7A4988BC0C5E61D |
| SSDEEP: | 12288:smOSSPAWkQDl3+ND8hRTScTWYU3KMy/IkqpctmOASvoWKrTq6uRtRmPX:heY1QDlqD8hvT63hywkgctmO4WR6E2 |
MALICIOUS
Application was dropped or rewritten from another process
- INSTALL.EXE (PID: 3156)
- WDSetup.EXE (PID: 2136)
Loads dropped or rewritten executable
- WDSetup.EXE (PID: 2136)
Drops executable file immediately after starts
- b00def042414aa226b4abeace6039371.exe (PID: 1572)
SUSPICIOUS
Checks supported languages
- b00def042414aa226b4abeace6039371.exe (PID: 1572)
- INSTALL.EXE (PID: 3156)
- WDSetup.EXE (PID: 2136)
Reads the computer name
- WDSetup.EXE (PID: 2136)
- INSTALL.EXE (PID: 3156)
- b00def042414aa226b4abeace6039371.exe (PID: 1572)
Drops a file with a compile date too recent
- b00def042414aa226b4abeace6039371.exe (PID: 1572)
- INSTALL.EXE (PID: 3156)
Drops a file that was compiled in debug mode
- INSTALL.EXE (PID: 3156)
Executable content was dropped or overwritten
- INSTALL.EXE (PID: 3156)
- b00def042414aa226b4abeace6039371.exe (PID: 1572)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:05:07 12:19:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 179712 |
| InitializedDataSize: | 179712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1758d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 26.0.7.1 |
| ProductVersionNumber: | 26.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | French |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | PC SOFT |
| FileDescription: | WDAutoEx.EXE (Executable auto-extractible) - Win32 |
| FileVersion: | 26.0.7.1 |
| LegalCopyright: | Copyright © PC SOFT 1993-2020 |
| OriginalFileName: | WDAutoEx.EXE |
| Comments: | YV Francais |
| Plateforme: | Win32 UNICODE |
| FileDescriptionUS: | WDAutoEx.EXE (Self-extractible archive) - Win32 |
| ProductName: | WINDEV |
| ProductVersion: | 26.0 (26.0.7.1) VI xxxxxxxxxxxx |
| VersionVI: | xxxxxxxxxxxx |
| Version: | 26.0.7.1 |
| Checksum: | xx |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-May-2021 10:19:08 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | PC SOFT |
| FileDescription: | WDAutoEx.EXE (Executable auto-extractible) - Win32 |
| FileVersion: | 26.0.7.1 |
| LegalCopyright: | Copyright © PC SOFT 1993-2020 |
| OriginalFilename: | WDAutoEx.EXE |
| Comments: | YV Francais |
| Plateforme: | Win32 UNICODE |
| FileDescriptionUS: | WDAutoEx.EXE (Self-extractible archive) - Win32 |
| ProductName: | WINDEV |
| ProductVersion: | 26.0 (26.0.7.1) VI xxxxxxxxxxxx |
| VersionVI: | xxxxxxxxxxxx |
| Version: | 26.0.7.1 |
| Checksum: | xx |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-May-2021 10:19:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002BD67 | 0x0002BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70718 |
.rdata | 0x0002D000 | 0x00011DCE | 0x00011E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.01248 |
.data | 0x0003F000 | 0x0000203C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.80882 |
.rsrc | 0x00042000 | 0x00016BA8 | 0x00016C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0496 |
.reloc | 0x00059000 | 0x000021B4 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56368 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09846 | 759 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.04282 | 9640 | Latin 1 / Western European | French - France | RT_ICON |
3 | 5.14795 | 4264 | Latin 1 / Western European | French - France | RT_ICON |
4 | 4.89085 | 1128 | Latin 1 / Western European | French - France | RT_ICON |
20 | 2.87334 | 202 | Latin 1 / Western European | French - France | RT_STRING |
21 | 2.45463 | 108 | Latin 1 / Western European | French - France | RT_STRING |
102 | 3.80283 | 289 | Latin 1 / Western European | French - France | INFOWDZ |
103 | 3.97123 | 550 | Latin 1 / Western European | French - France | INFOWDZ |
104 | 3.44531 | 664 | Latin 1 / Western European | French - France | RT_DIALOG |
105 | 2.65982 | 62 | Latin 1 / Western European | French - France | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
SHELL32.dll |
USER32.dll |
UxTheme.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
CommandeComposante | 1 | 0x000017C4 |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
1
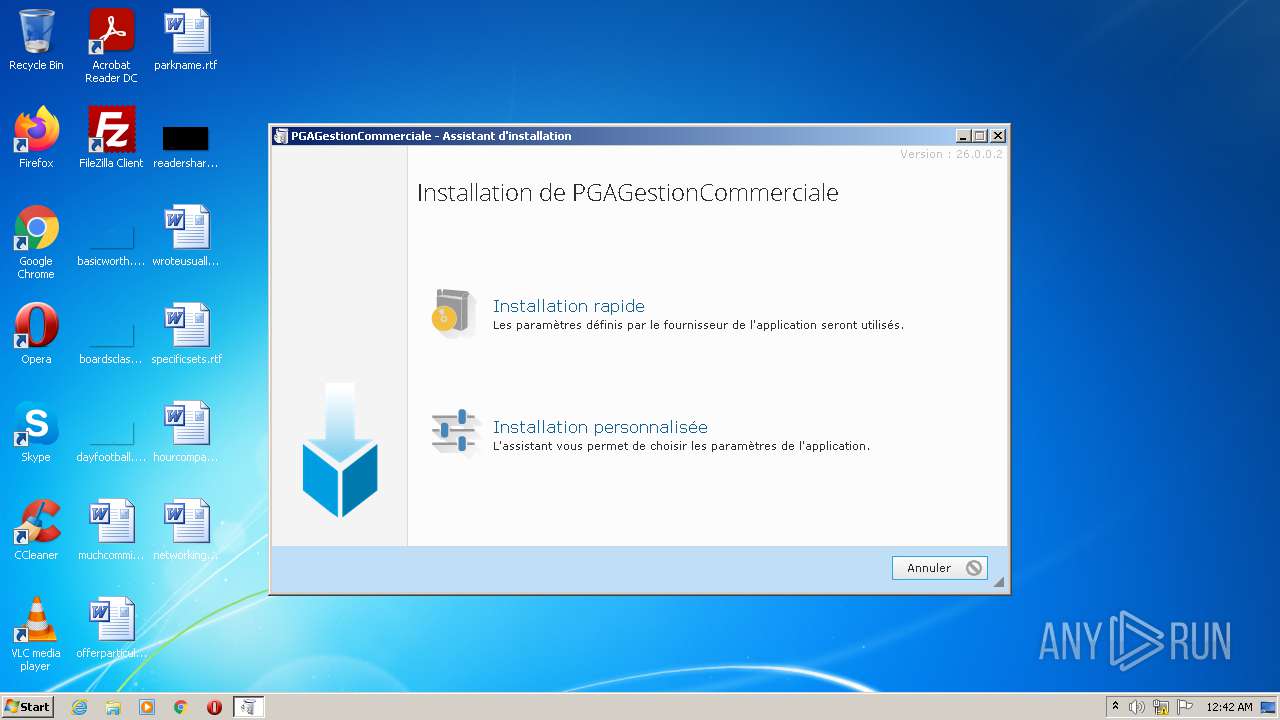
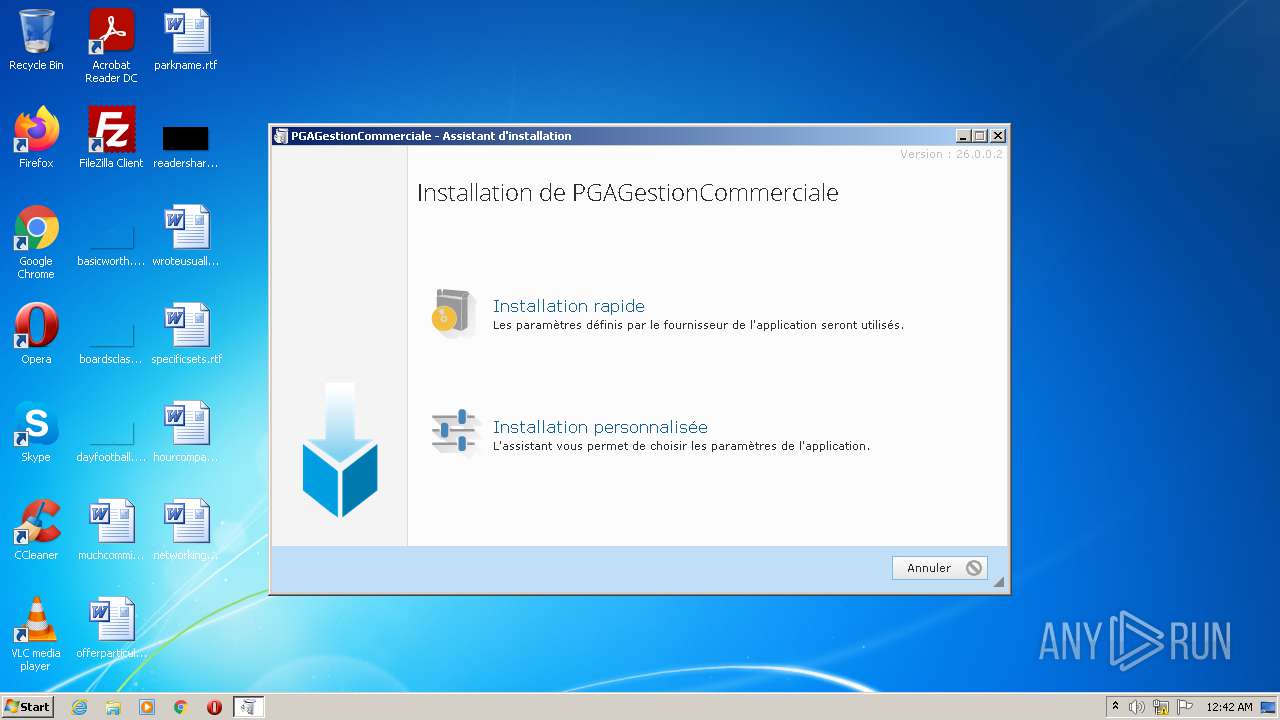
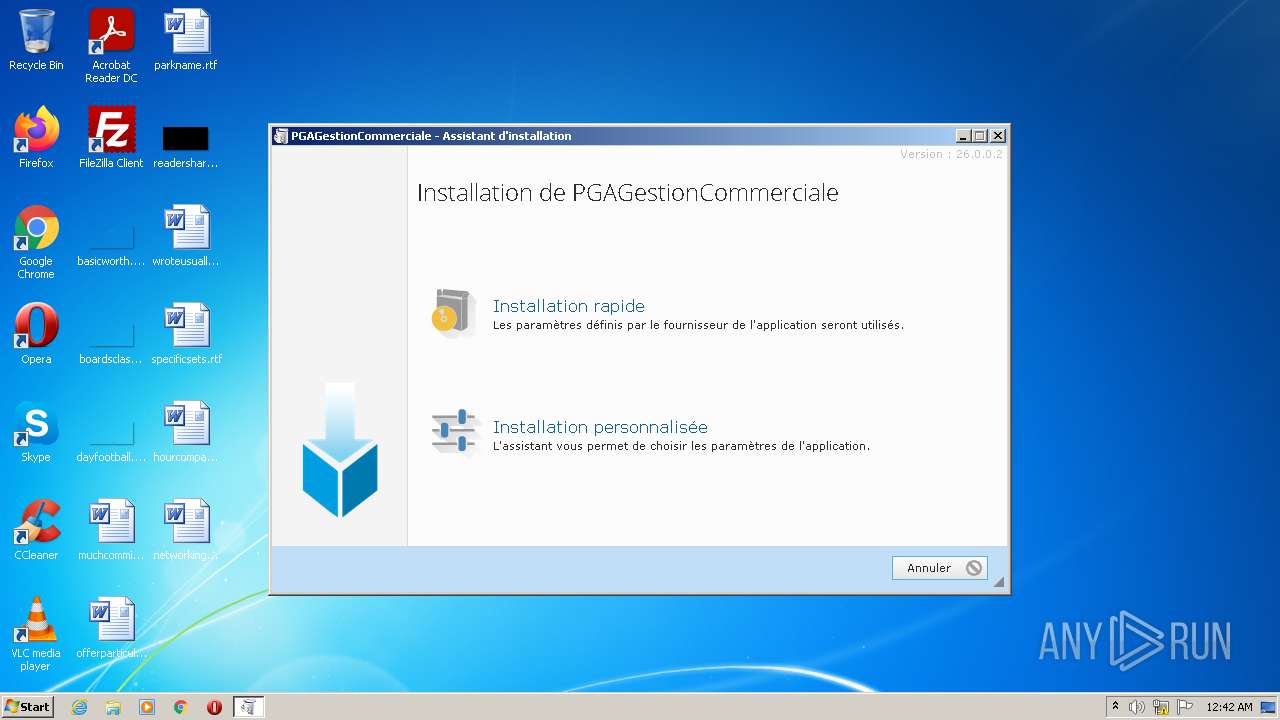
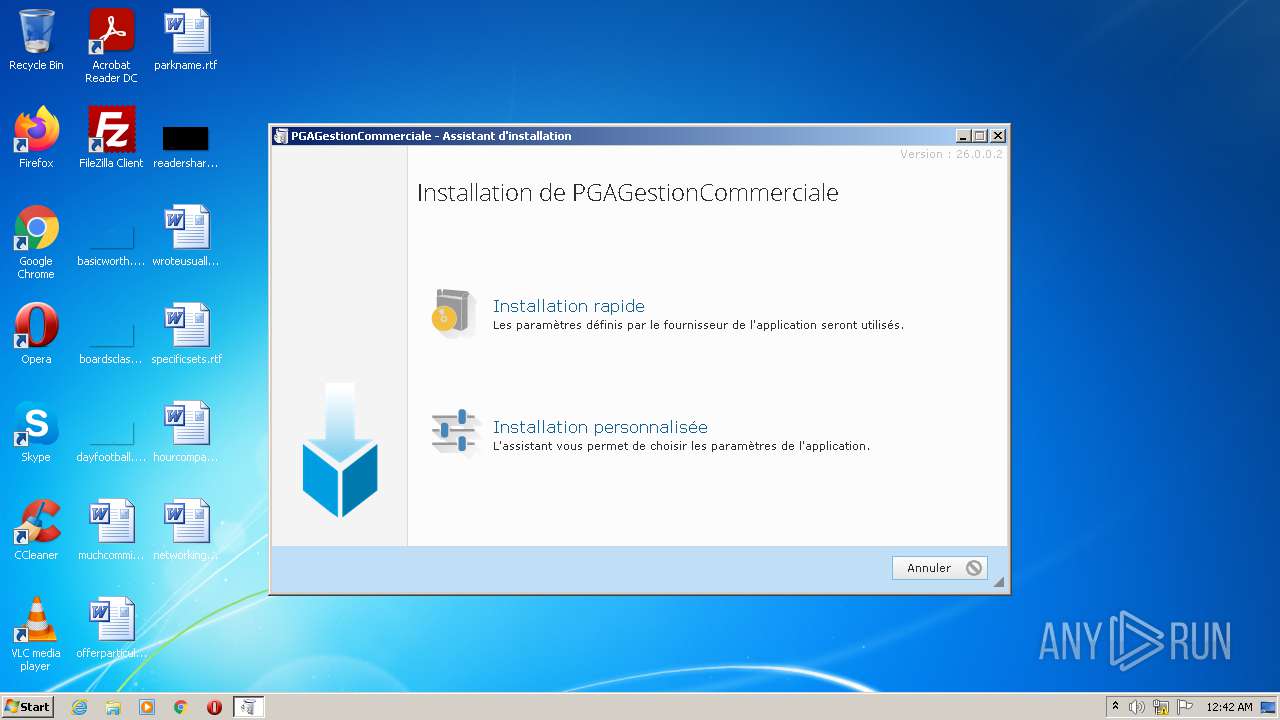
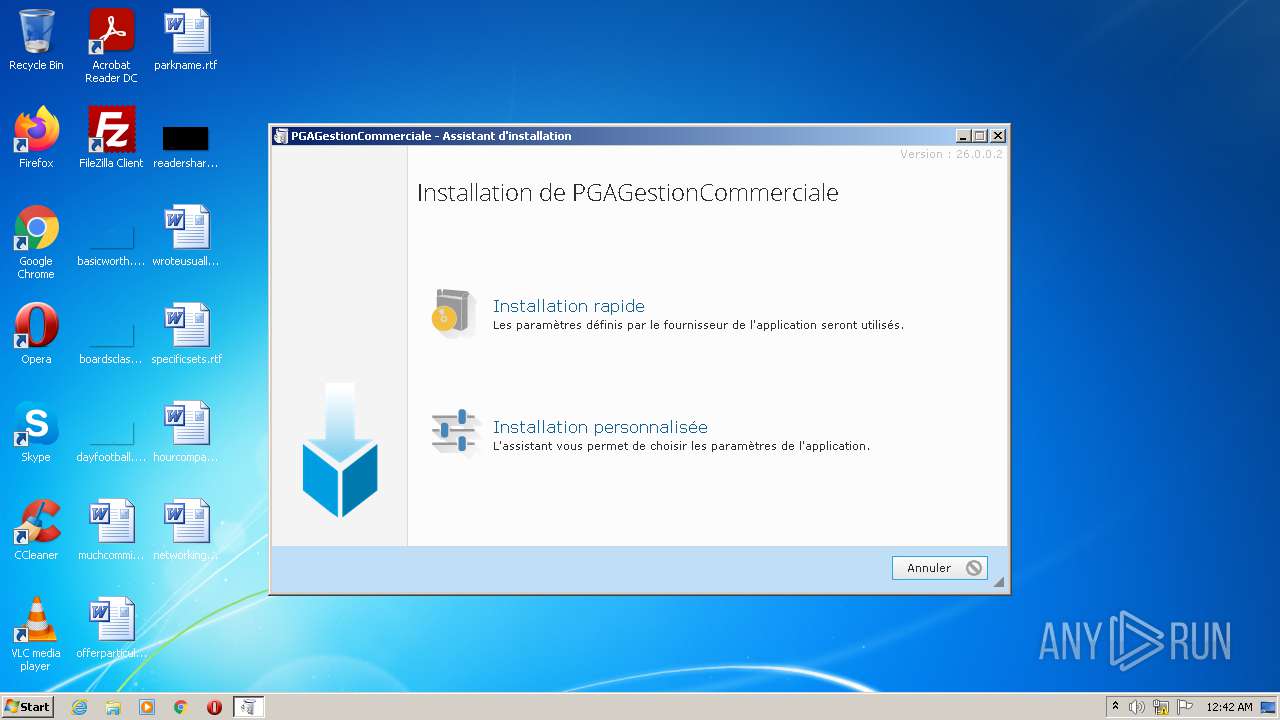
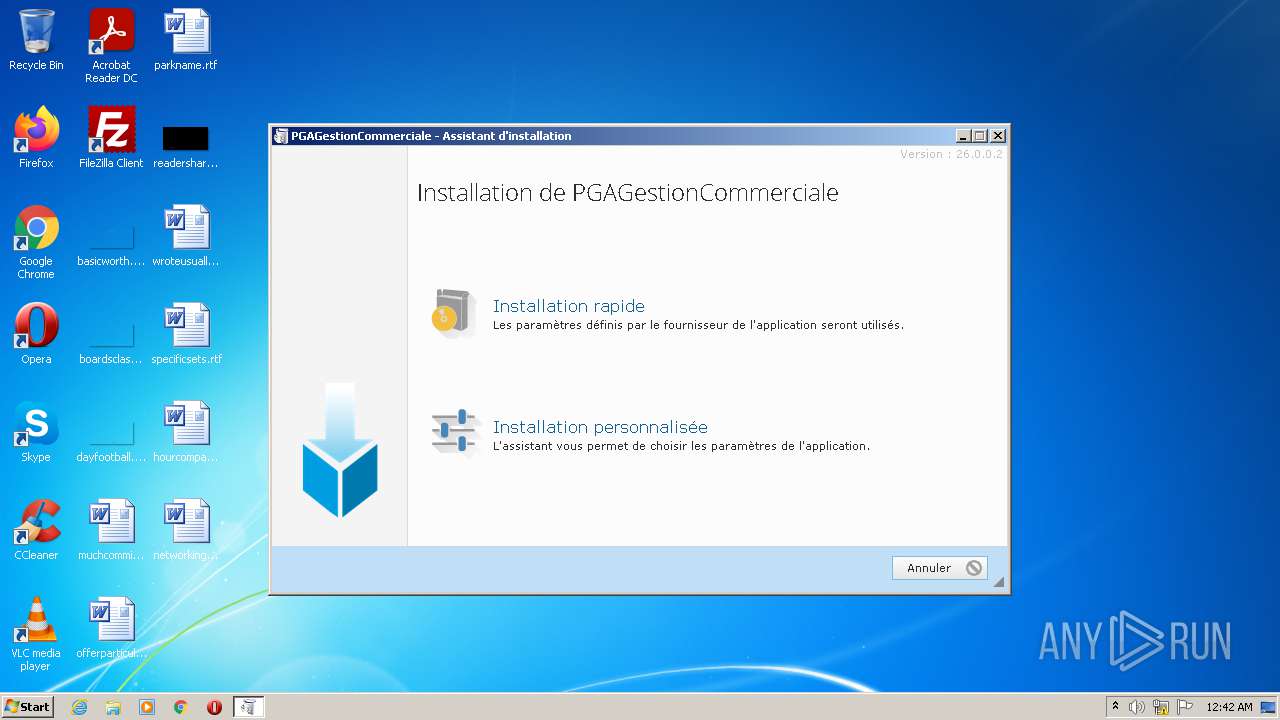
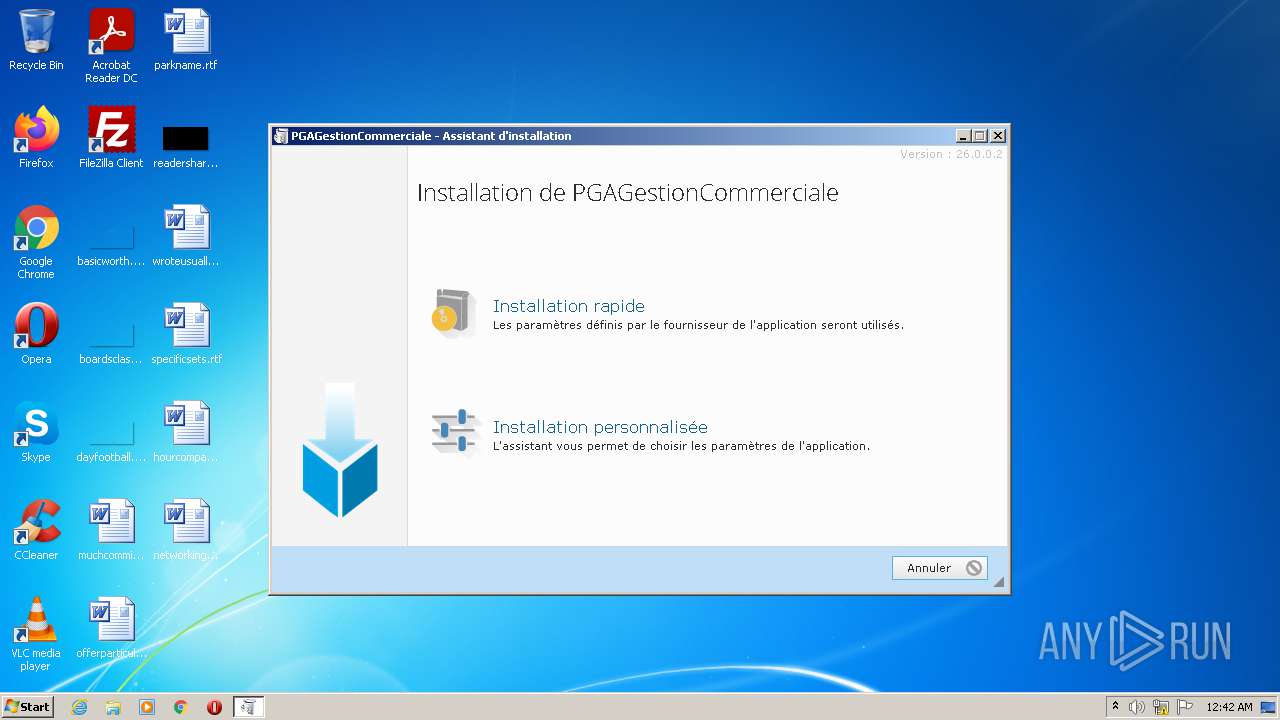
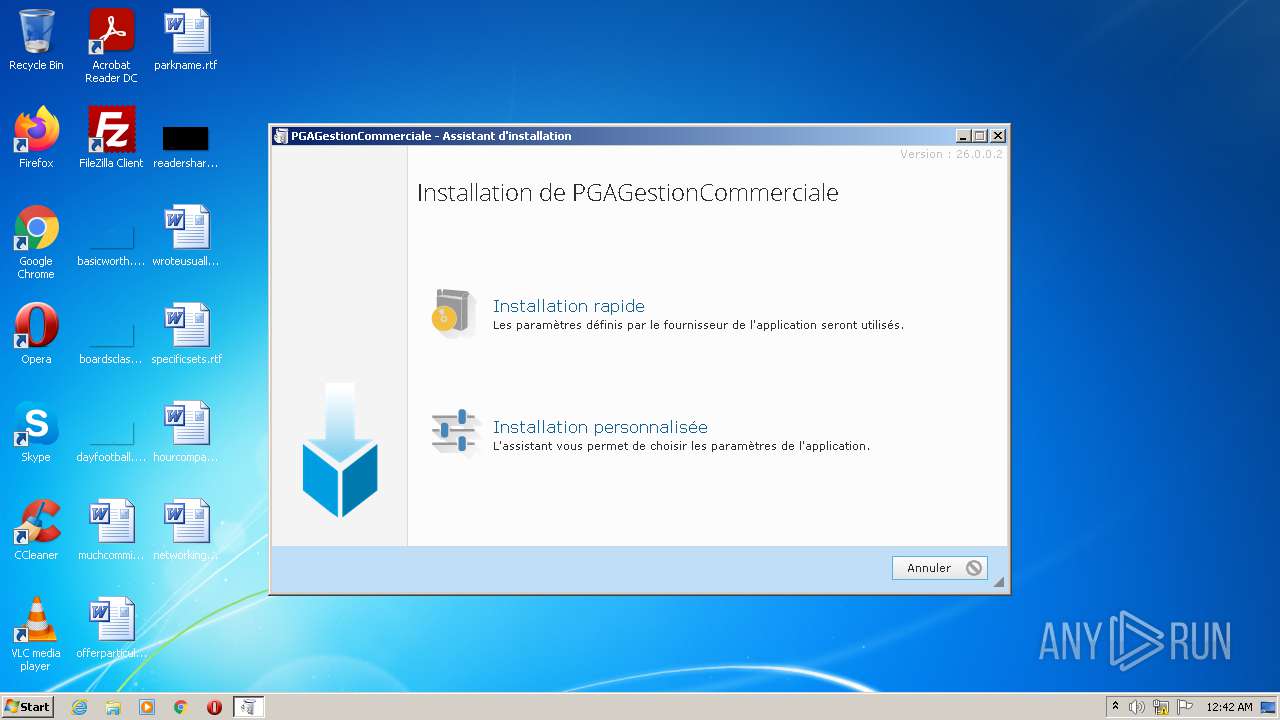
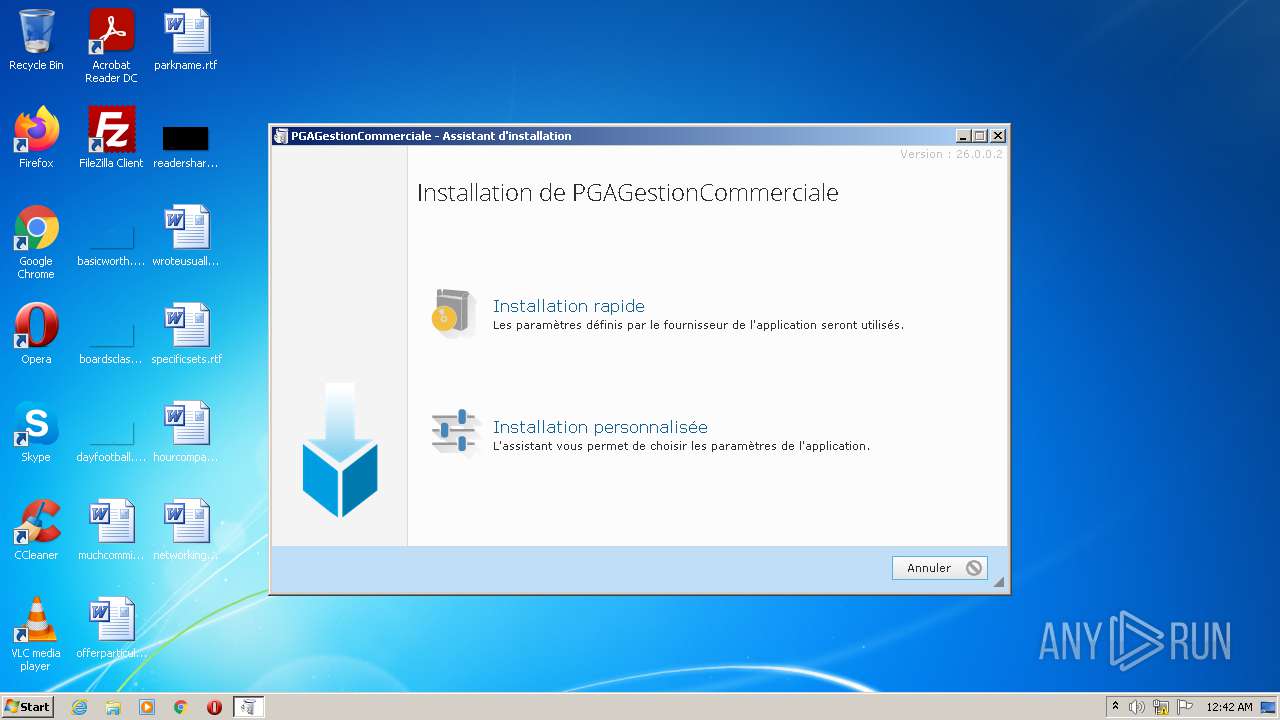
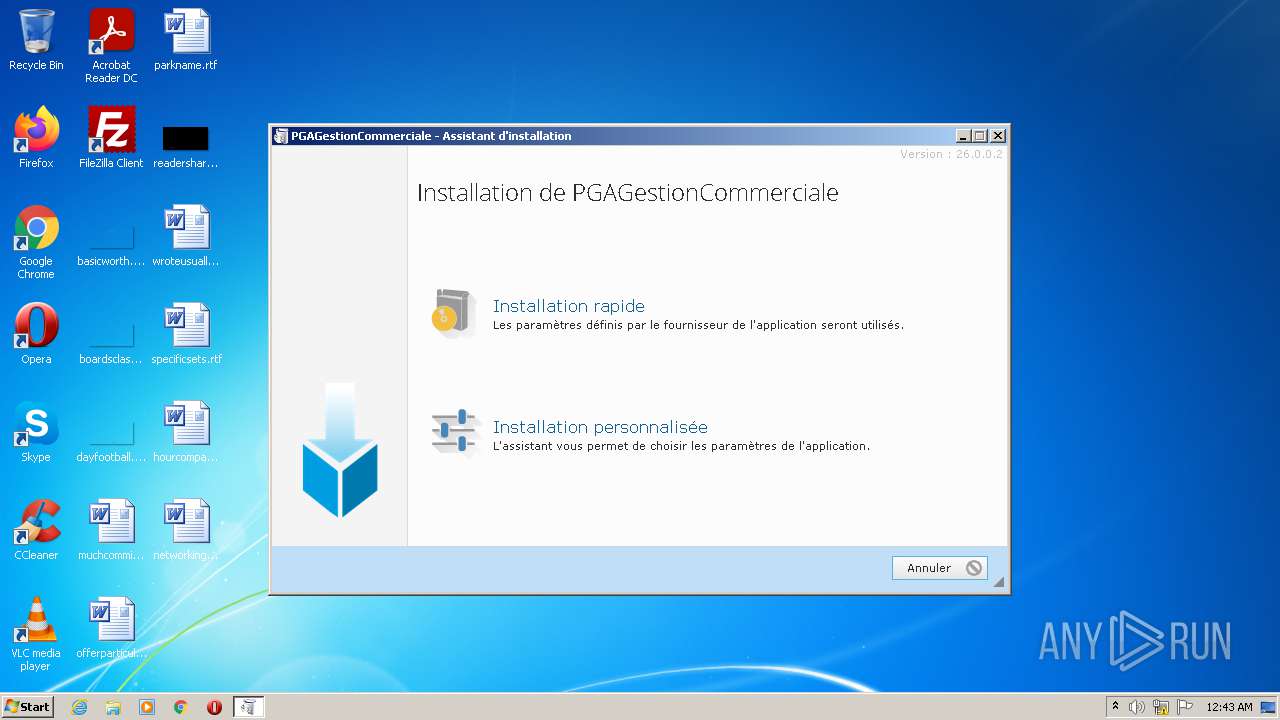
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1572 | "C:\Users\admin\AppData\Local\Temp\b00def042414aa226b4abeace6039371.exe" | C:\Users\admin\AppData\Local\Temp\b00def042414aa226b4abeace6039371.exe | Explorer.EXE | ||||||||||||
User: admin Company: PC SOFT Integrity Level: MEDIUM Description: WDAutoEx.EXE (Executable auto-extractible) - Win32 Exit code: 0 Version: 26.0.7.1 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\WDSetup.EXE" /REP="C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\" /PID_PARENT=3156 /VERSION_PARENT=26 /COMPOSITE=0 /WXF="C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\INST.WXF" "C:\Users\admin\AppData\Local\Temp\WD_3C1D.tmp\INSTALL.EXE" | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\WDSetup.EXE | — | INSTALL.EXE | |||||||||||
User: admin Company: PC SOFT Integrity Level: MEDIUM Description: Outil d'installation Exit code: 0 Version: 25.0.441.0 Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\AppData\Local\Temp\WD_3C1D.tmp\INSTALL.EXE" | C:\Users\admin\AppData\Local\Temp\WD_3C1D.tmp\INSTALL.EXE | b00def042414aa226b4abeace6039371.exe | ||||||||||||
User: admin Company: PC SOFT Integrity Level: MEDIUM Description: PreInstall.exe (Pr�-Installateur) - Win32 Exit code: 0 Version: 26.0.244.0 Modules
| |||||||||||||||
Total events
1 806
Read events
1 776
Write events
30
Delete events
0
Modification events
| (PID) Process: | (1572) b00def042414aa226b4abeace6039371.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1572) b00def042414aa226b4abeace6039371.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1572) b00def042414aa226b4abeace6039371.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1572) b00def042414aa226b4abeace6039371.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3156) INSTALL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
17
Suspicious files
3
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\wd260hf.dll | executable | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\wd260com.dll | executable | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\INST.WXF | txt | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\wd260mat.dll | executable | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\ServeursWeb.wdk | binary | |
MD5:— | SHA256:— | |||
| 1572 | b00def042414aa226b4abeace6039371.exe | C:\Users\admin\AppData\Local\Temp\WD_3C1D.tmp\INSTALL.INI | text | |
MD5:— | SHA256:— | |||
| 1572 | b00def042414aa226b4abeace6039371.exe | C:\Users\admin\AppData\Local\Temp\WD_3C1D.tmp\INSTALL.EXE | executable | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\wd260mdl.dll | executable | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\INSTALL[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 3156 | INSTALL.EXE | C:\Users\admin\AppData\Local\Temp\WD40E0.tmp\INSTALL.ZIP | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | INSTALL.EXE | GET | 200 | 185.43.44.65:80 | http://www.edonx.fr/PGAGestion/INSTALL/INSTALL.ZIP | FR | compressed | 28.9 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3156 | INSTALL.EXE | 185.43.44.65:80 | www.edonx.fr | Jaguar Network SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.edonx.fr |
| suspicious |
Threats
1 ETPRO signatures available at the full report