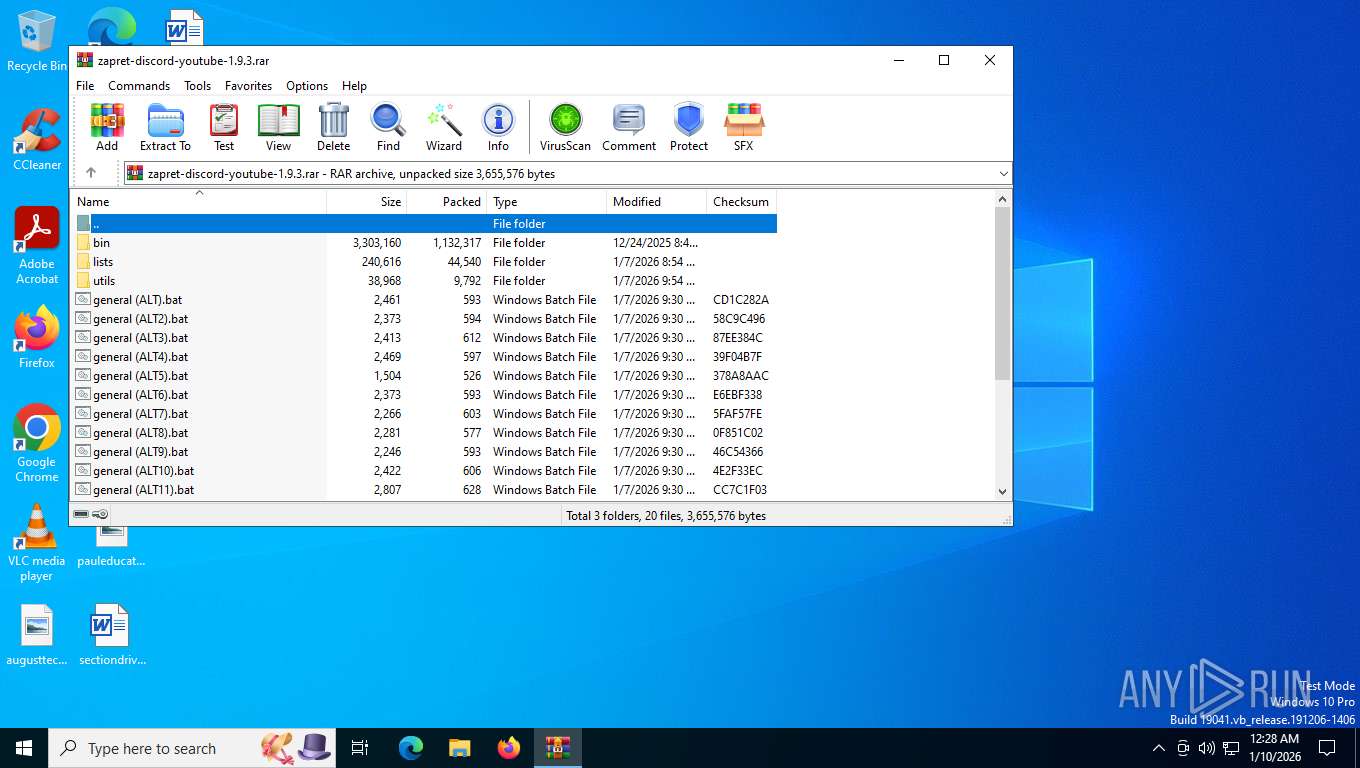
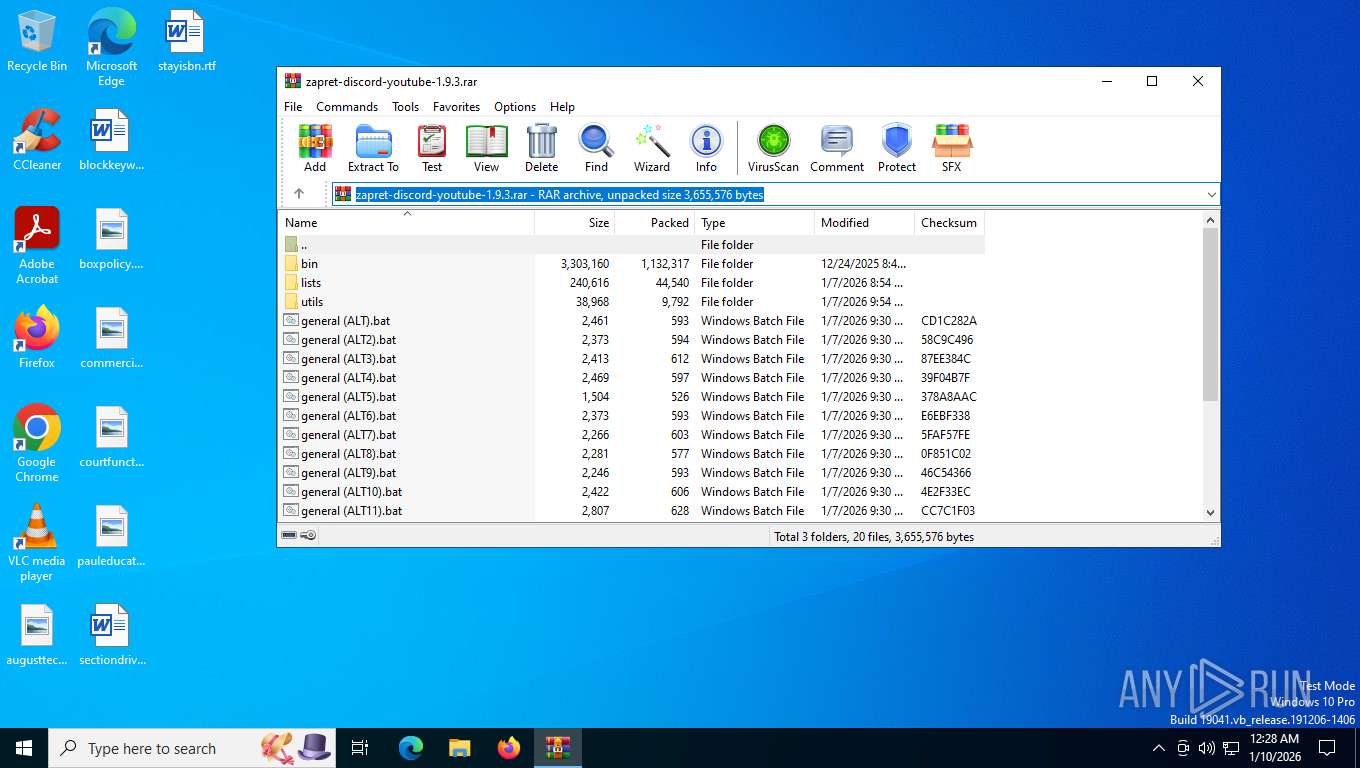
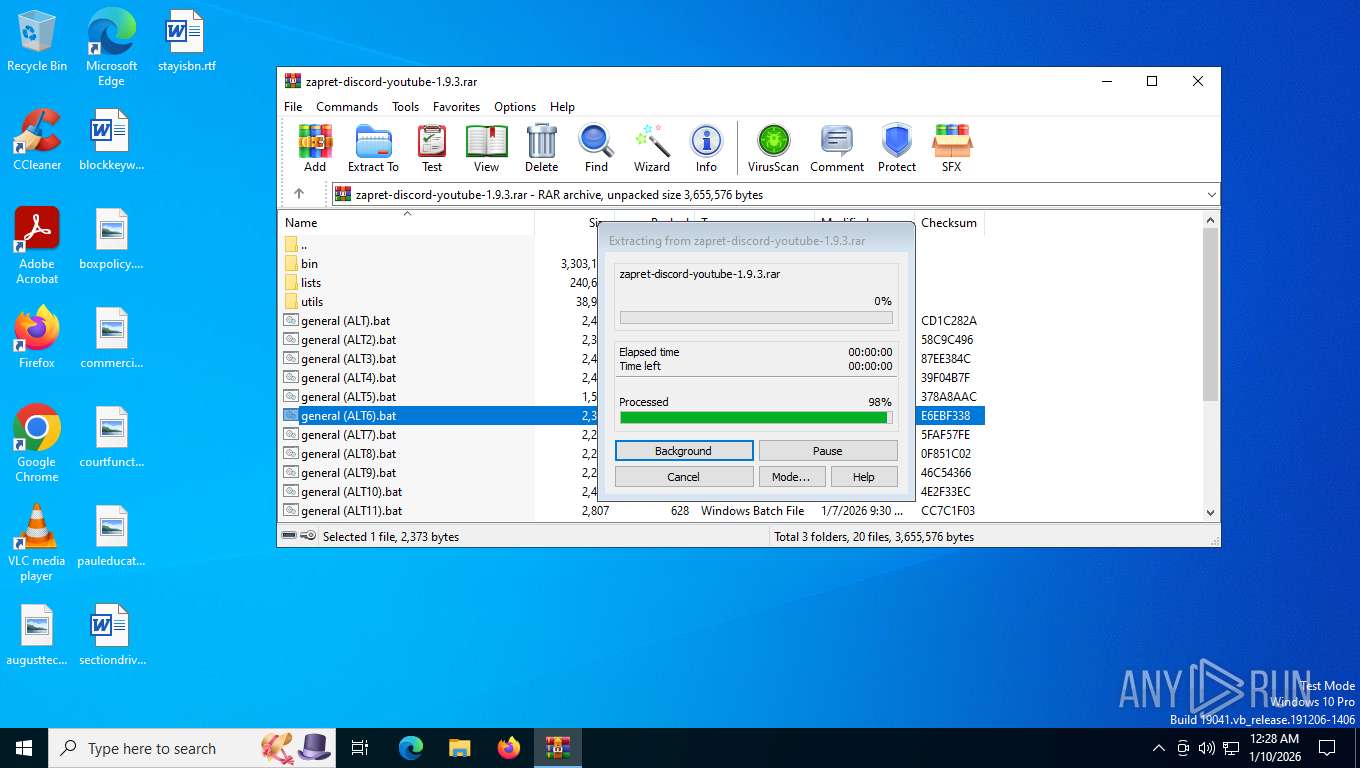
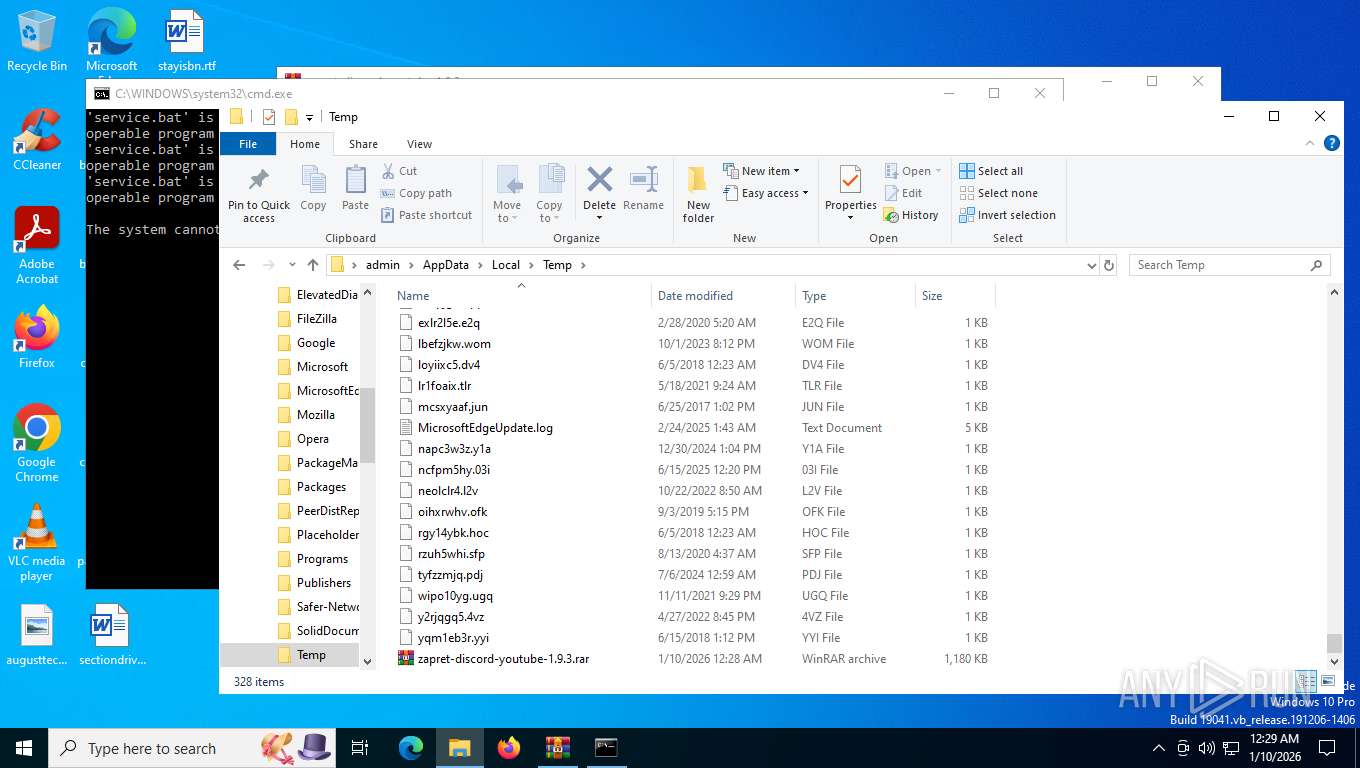
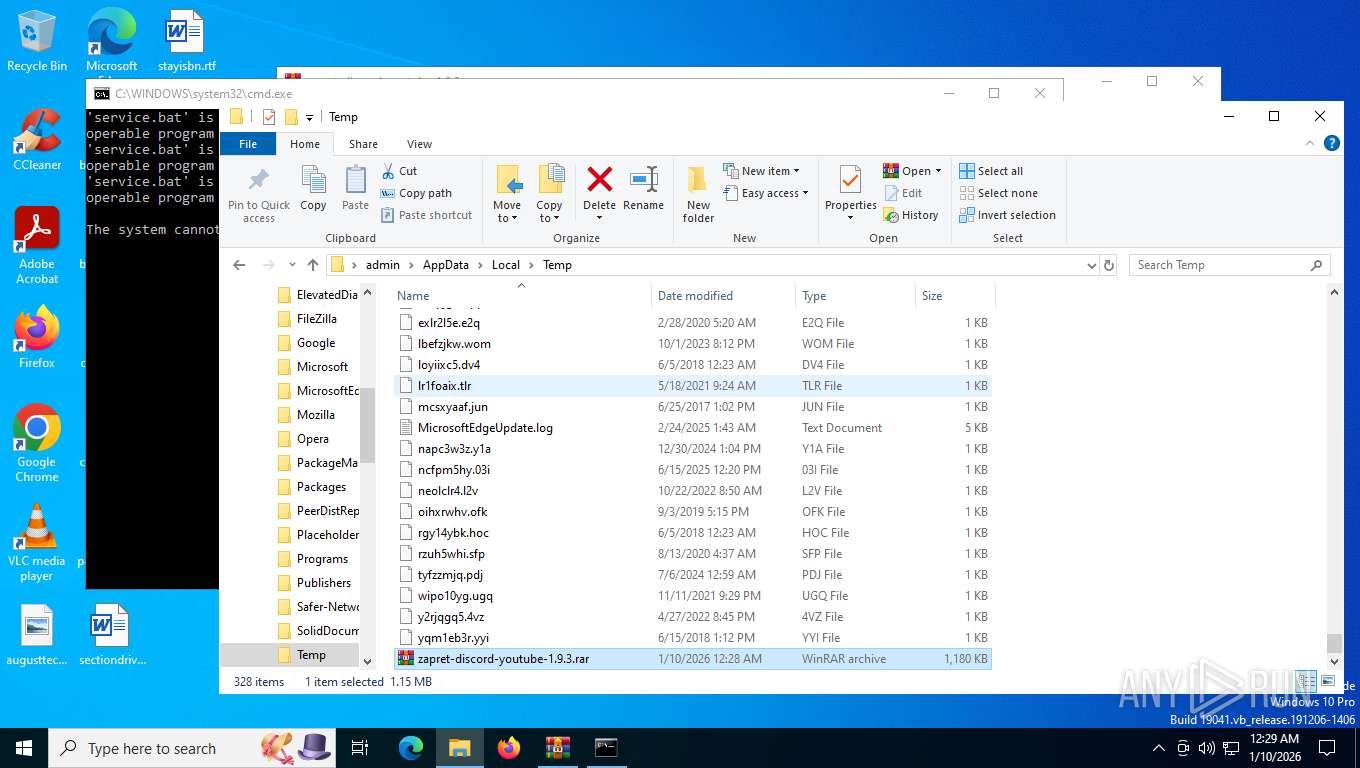
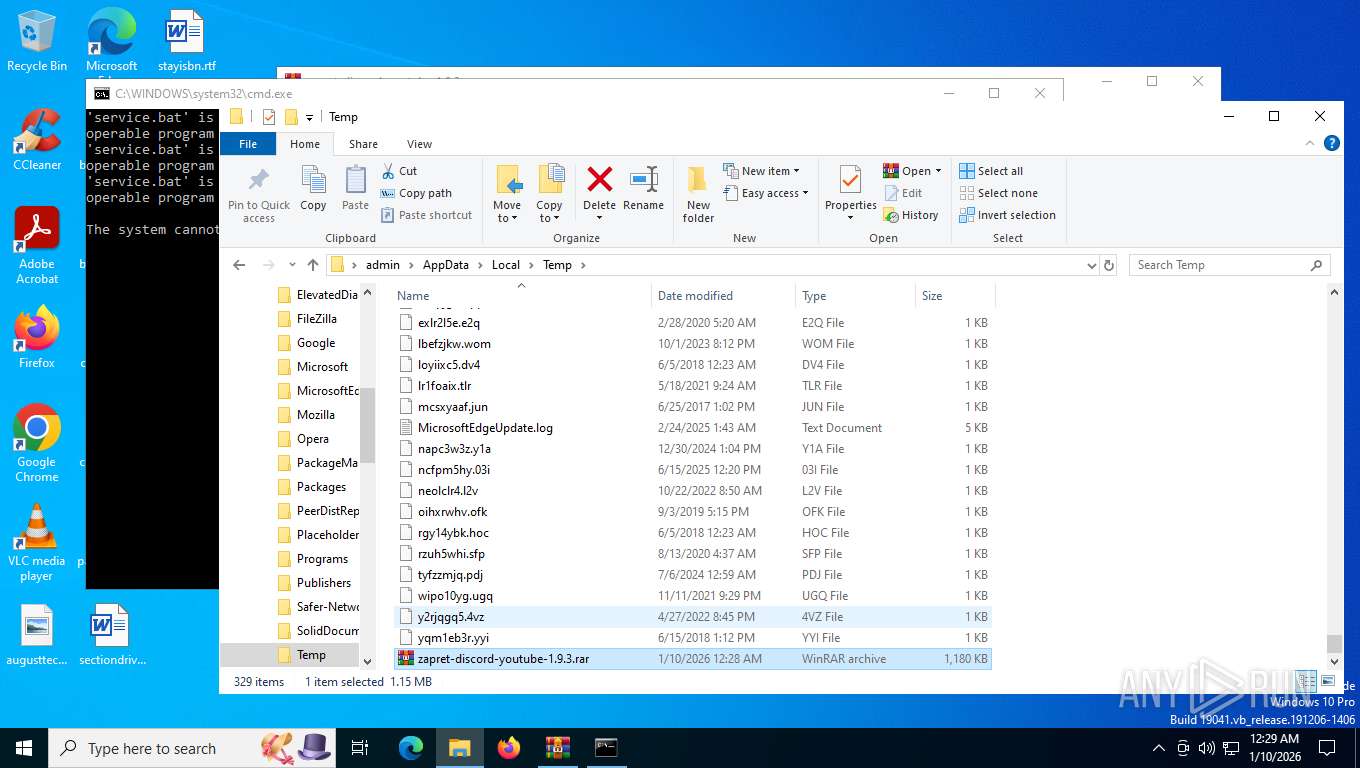
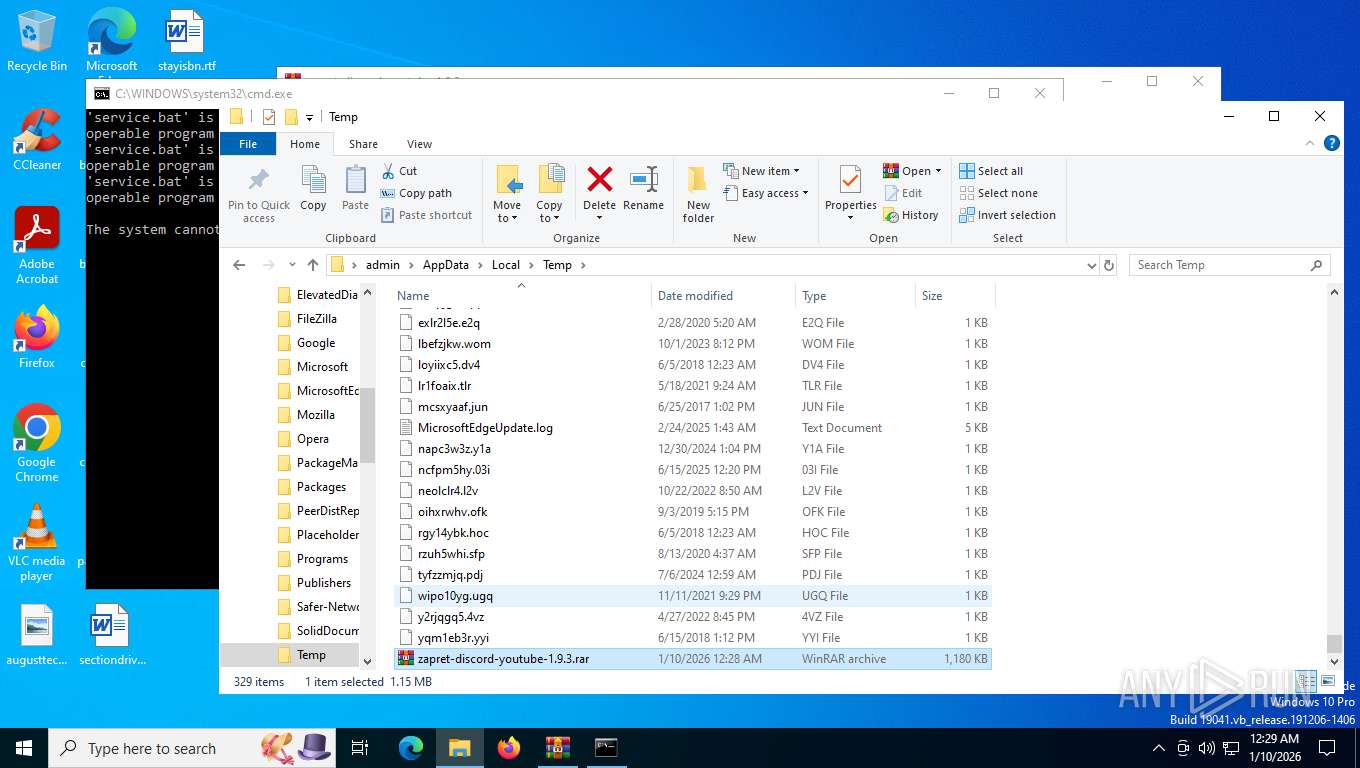
| File name: | zapret-discord-youtube-1.9.3.rar |
| Full analysis: | https://app.any.run/tasks/2ac60f59-ee7f-459b-bb63-fd7180ff68f2 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2026, 05:28:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5073ECFCB0A1A33D4389D33B2ED6CFC3 |
| SHA1: | C36160FFEE4C0FA54D30BF9617613E0E44A5823C |
| SHA256: | D3C5A75D58729CD6E1A171E59A3D3DBB91D7DCBCBD024E025BCBF3DC39BB5CC3 |
| SSDEEP: | 49152:jb4FMyNCQMf5udb/DNj7Ze9rm45sDC69wDe1fwTCFvppsBS9VWIwQtkcTa8ZM1My:jb4utV58b/Jj789rv5D6uDefjFvppr9w |
MALICIOUS
Malicious driver has been detected
- WinRAR.exe (PID: 7540)
- WinRAR.exe (PID: 7292)
Detects Cygwin installation
- WinRAR.exe (PID: 7292)
SUSPICIOUS
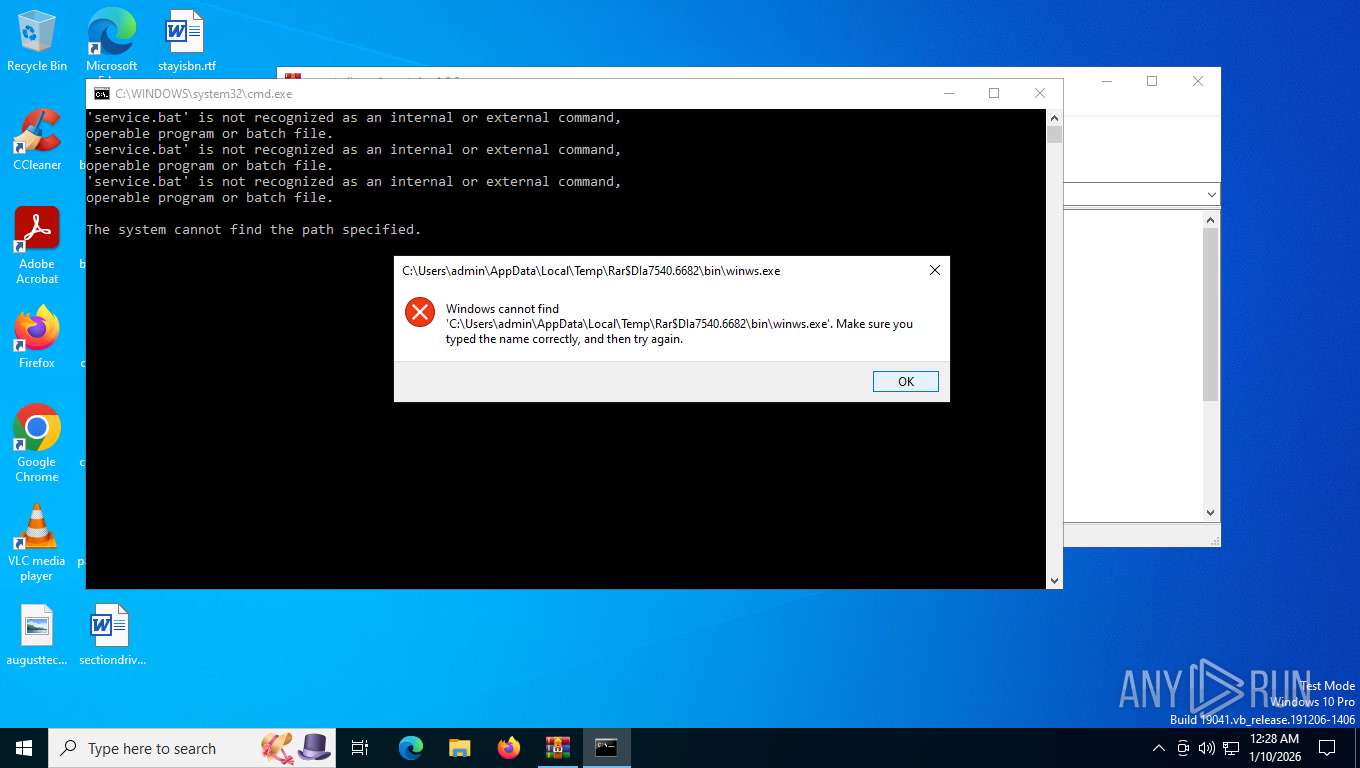
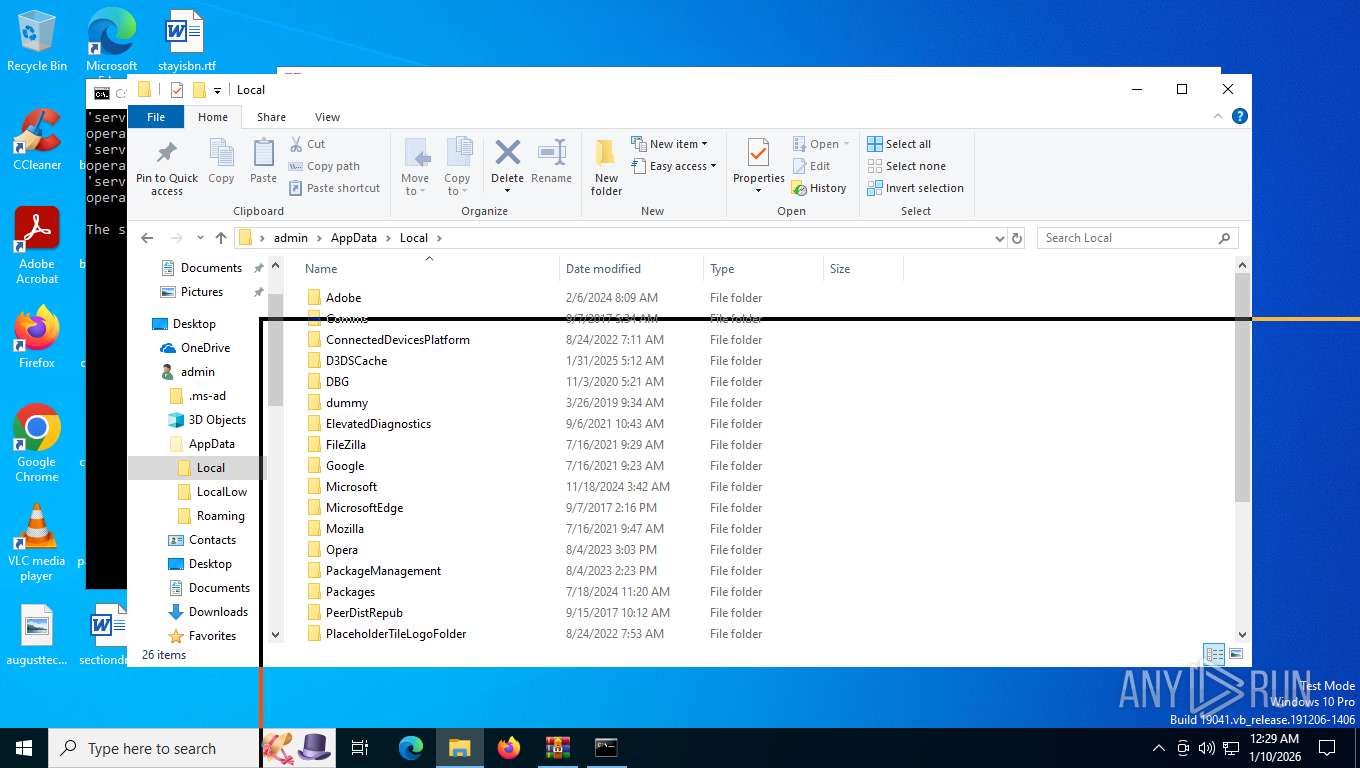
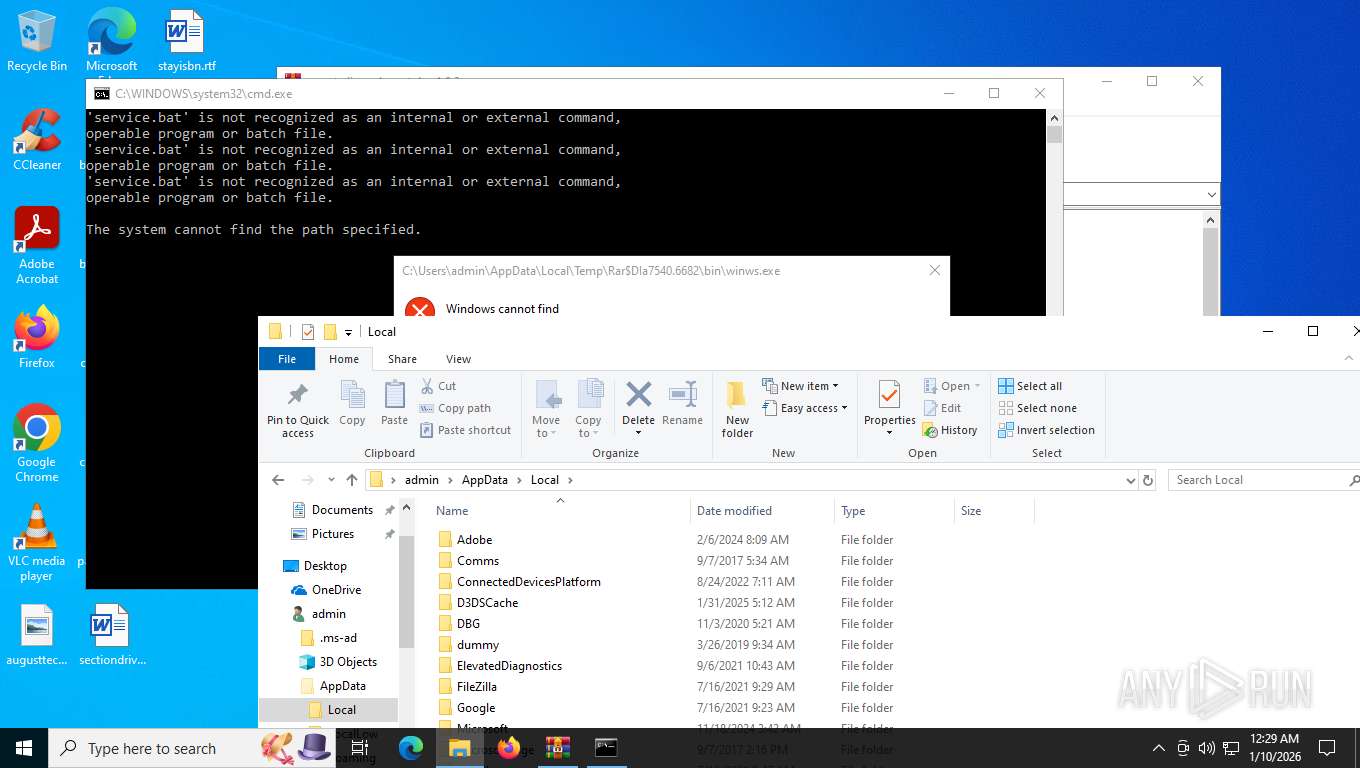
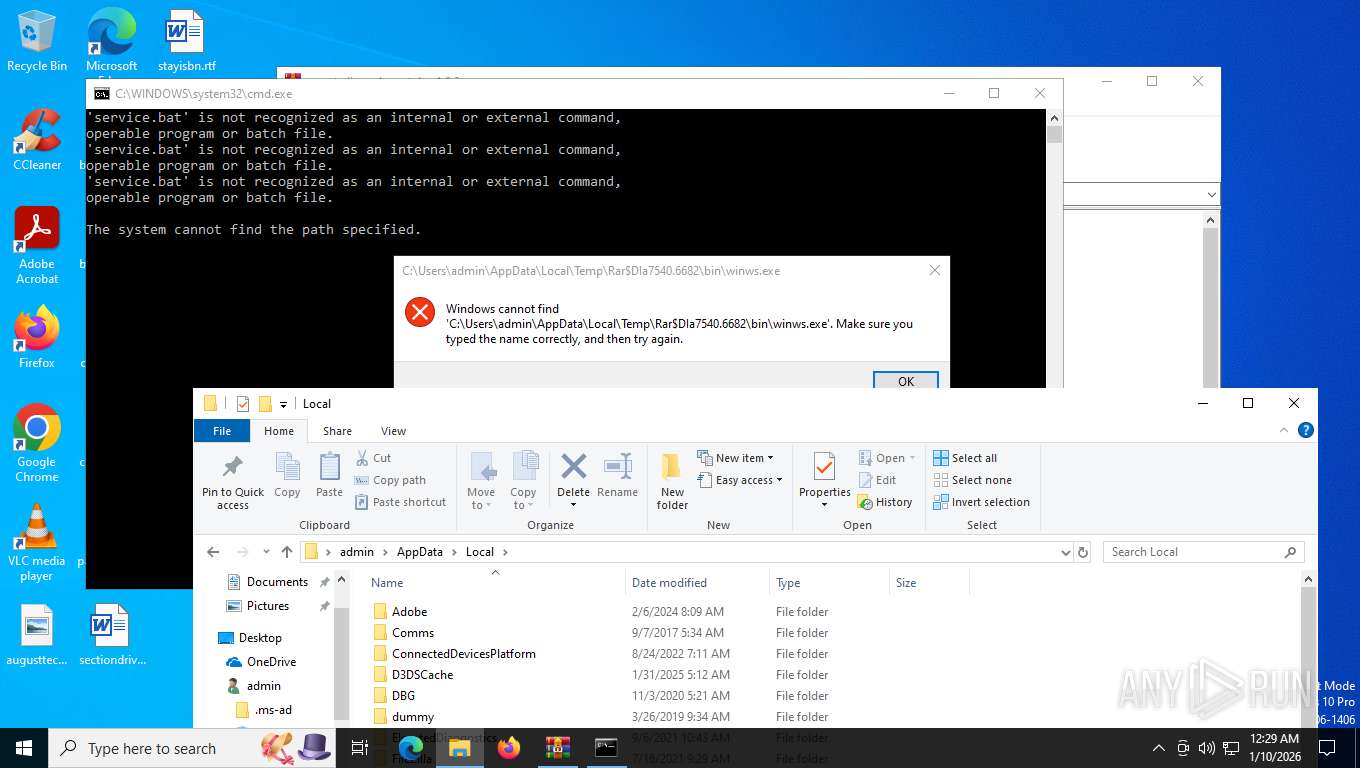
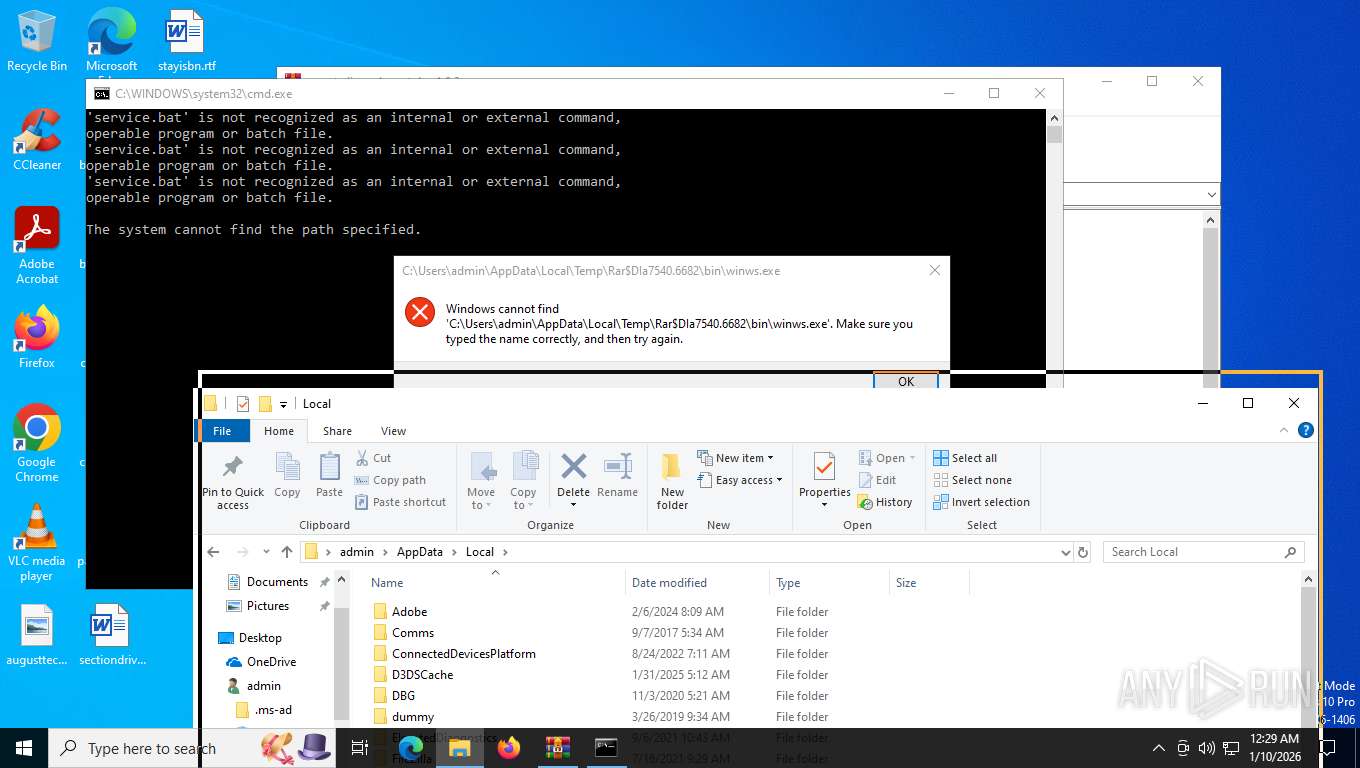
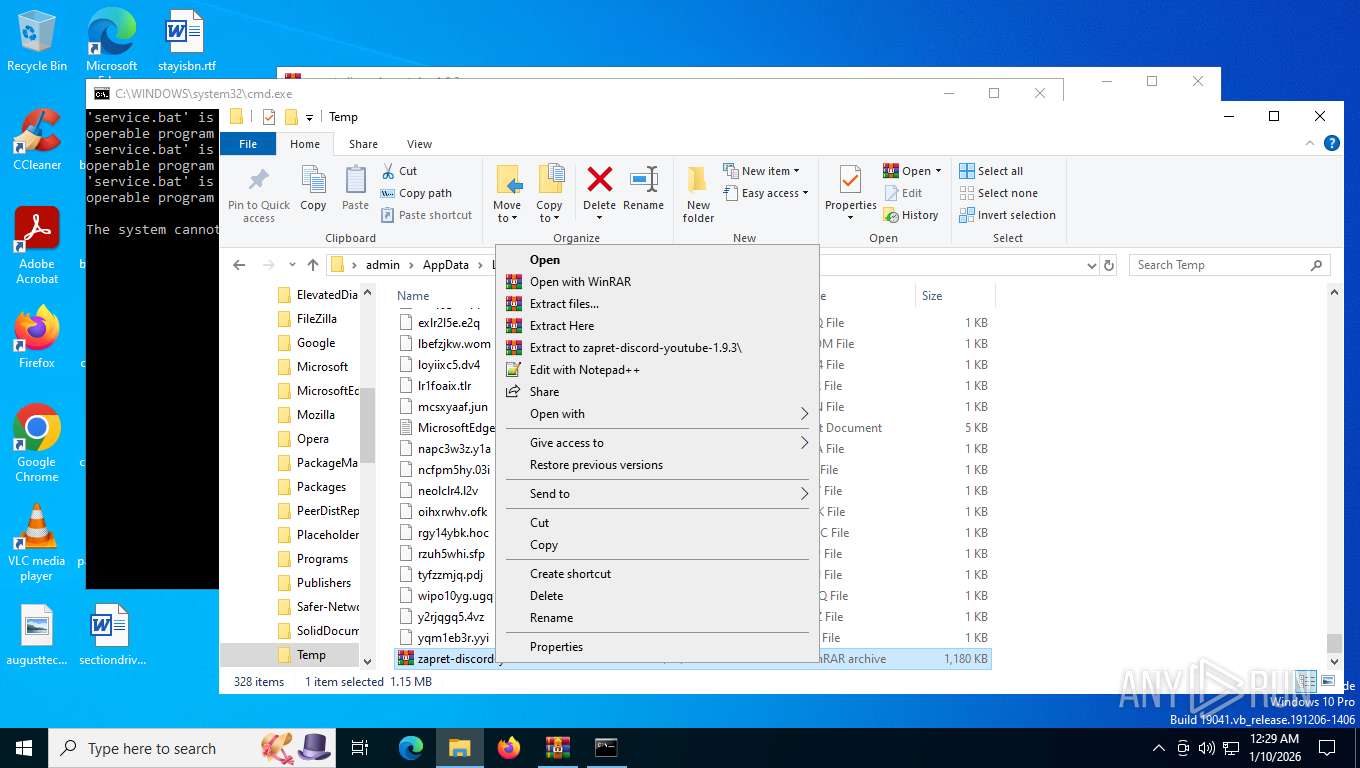
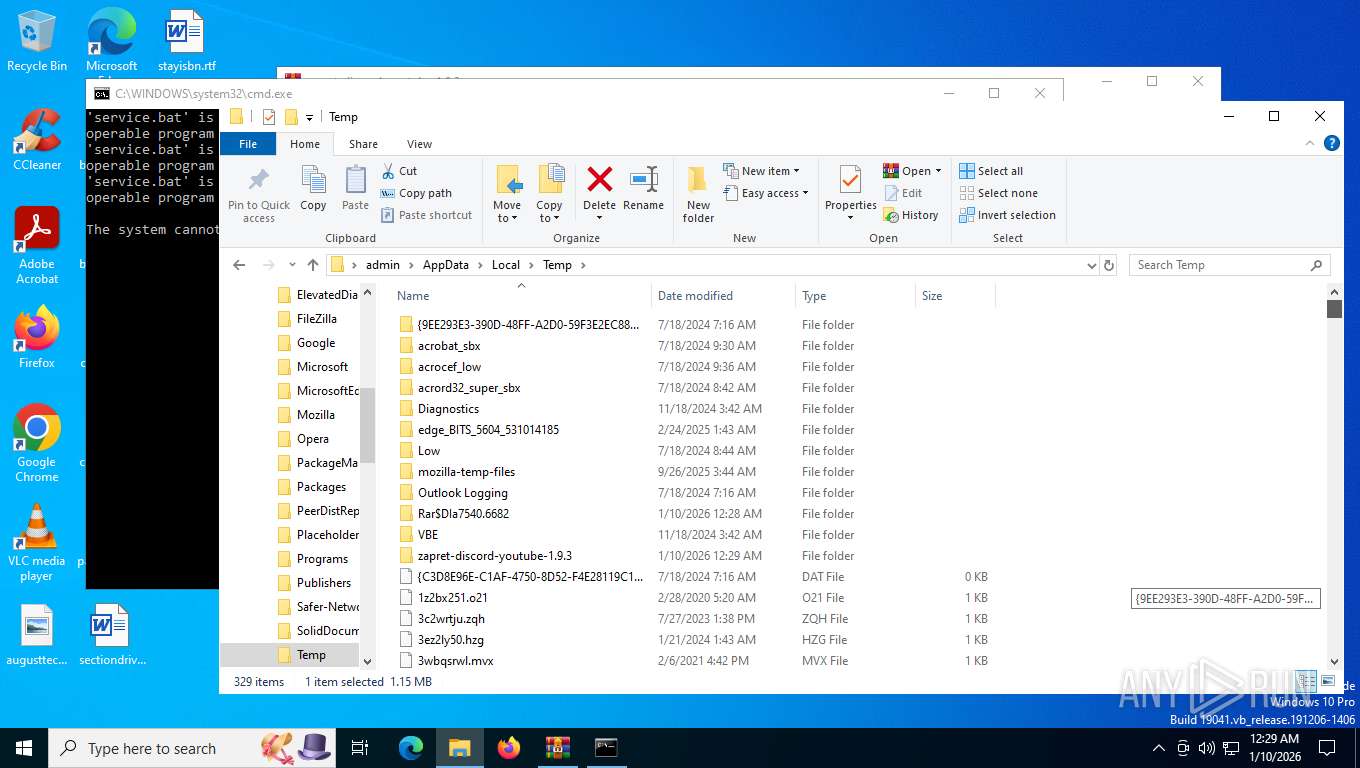
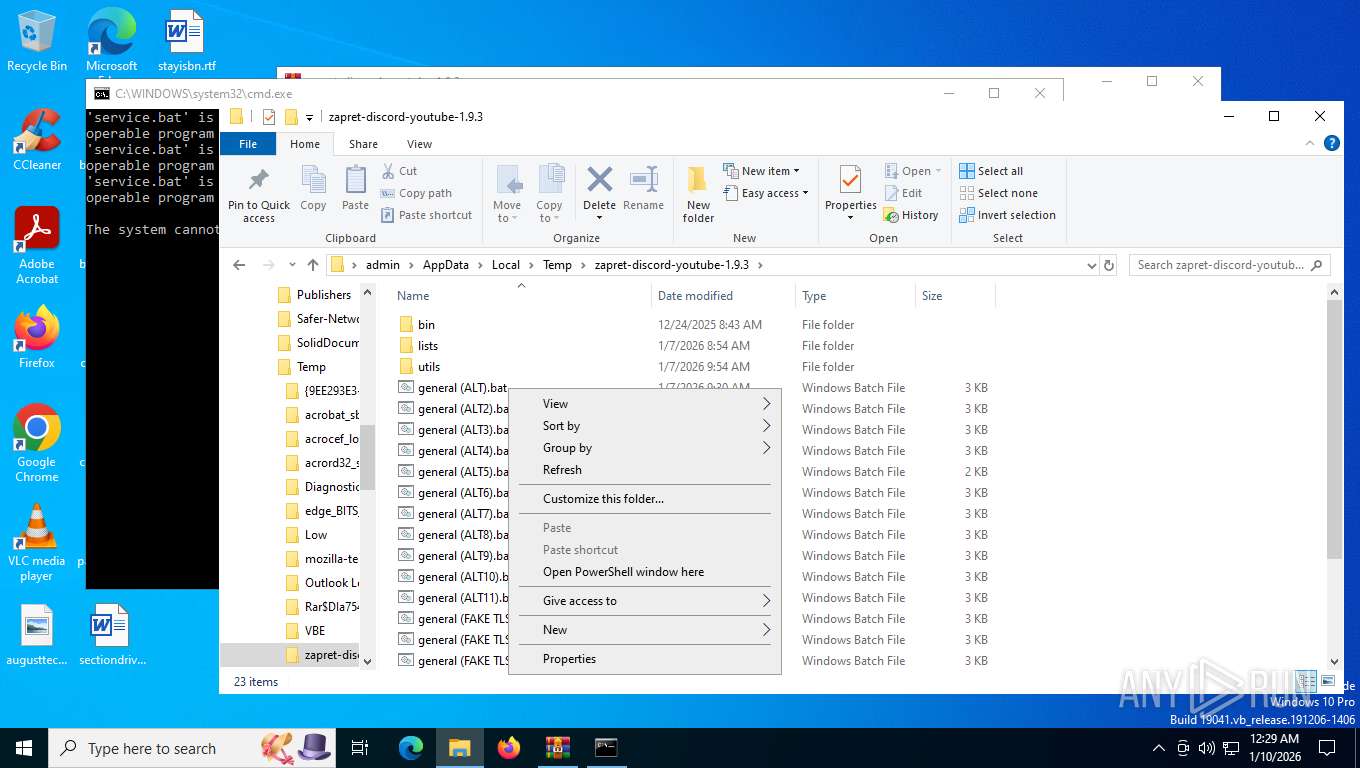
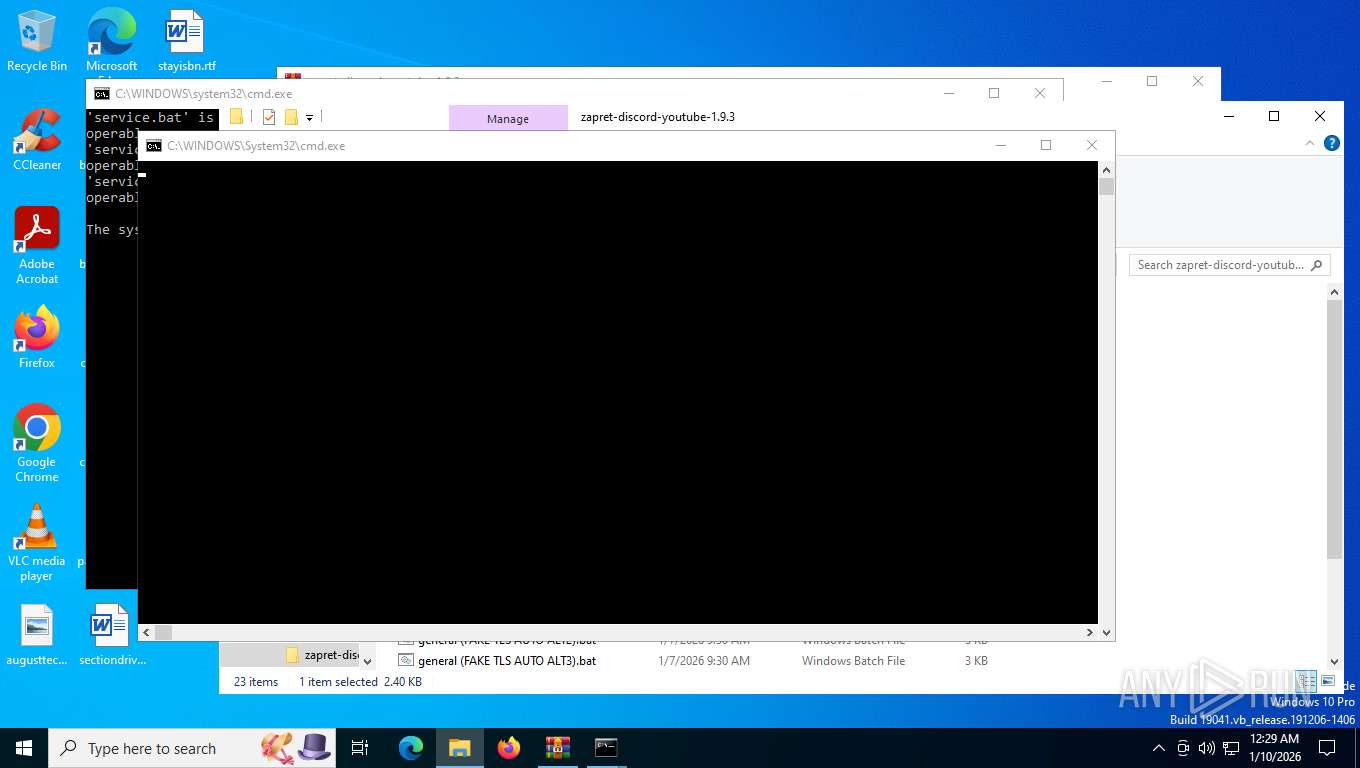
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7540)
- cmd.exe (PID: 5168)
- cmd.exe (PID: 8064)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7540)
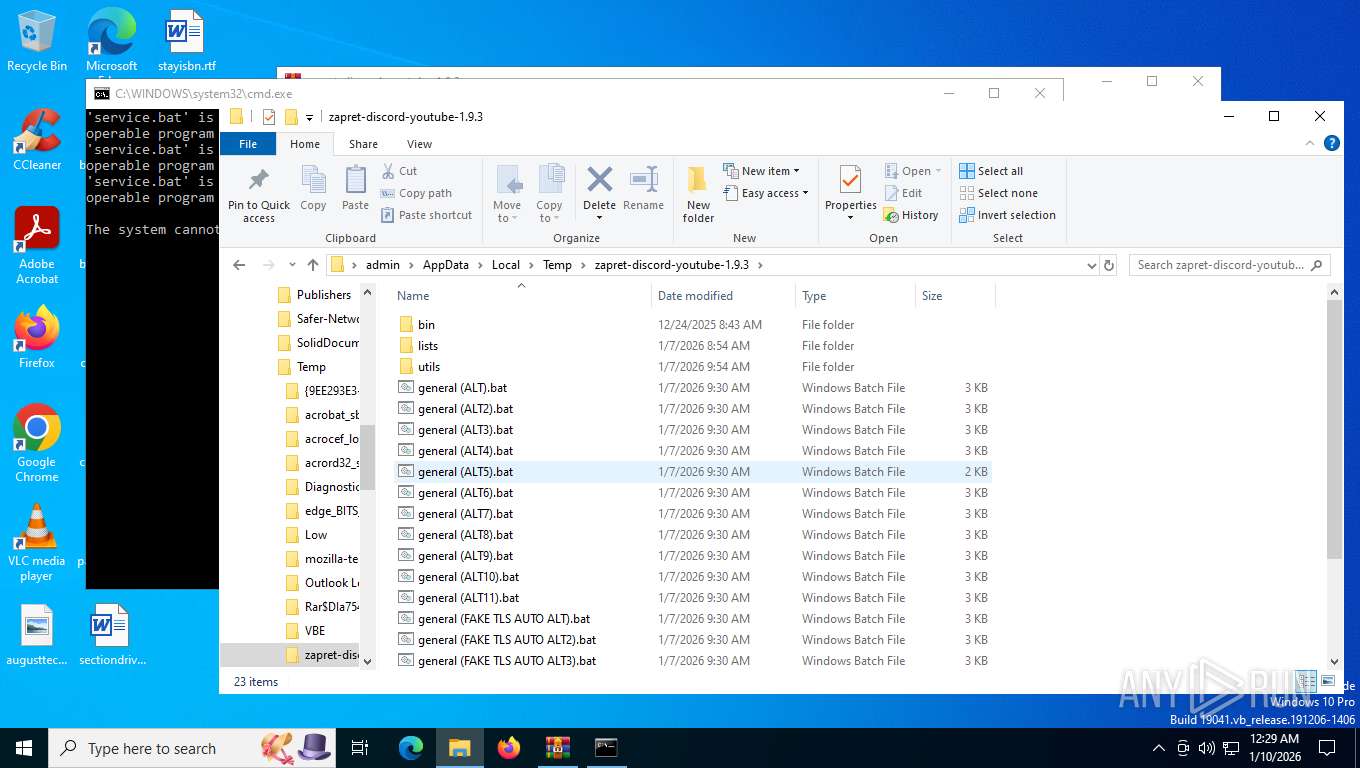
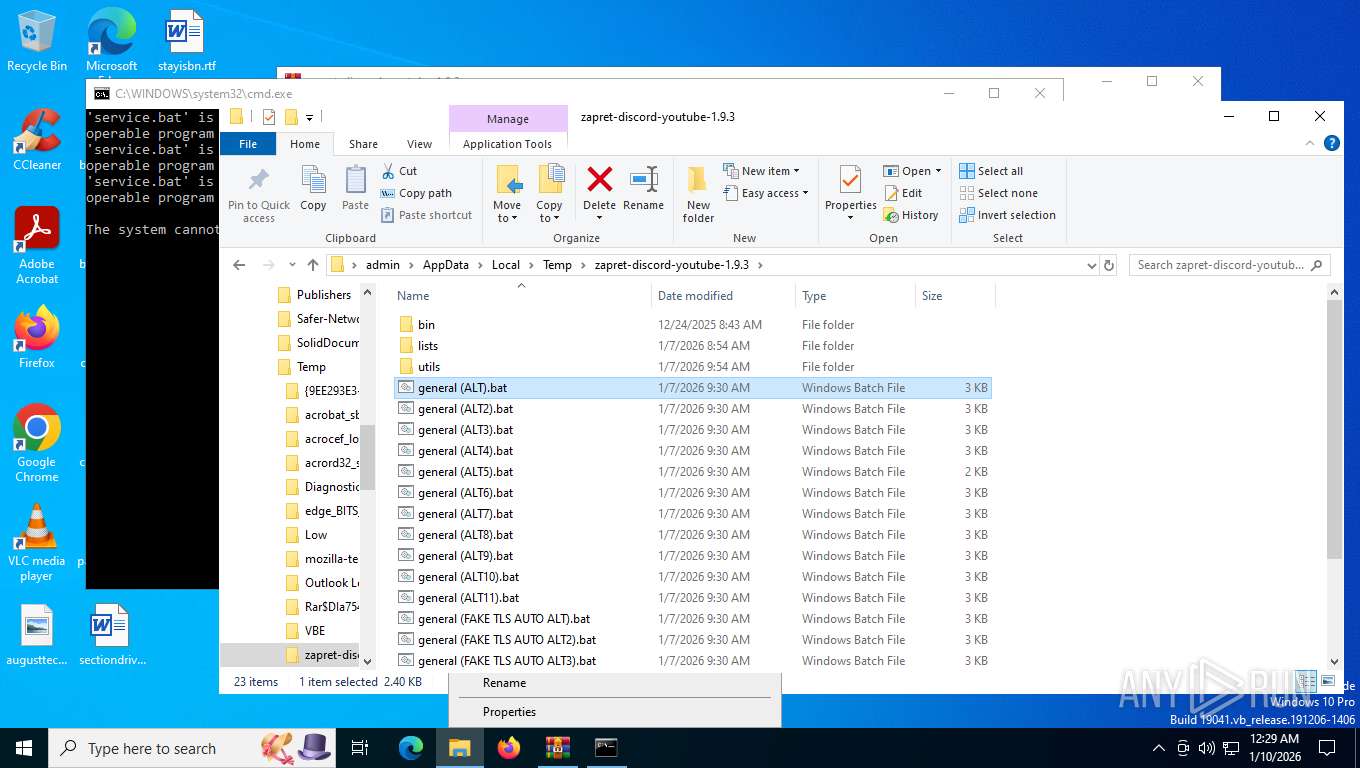
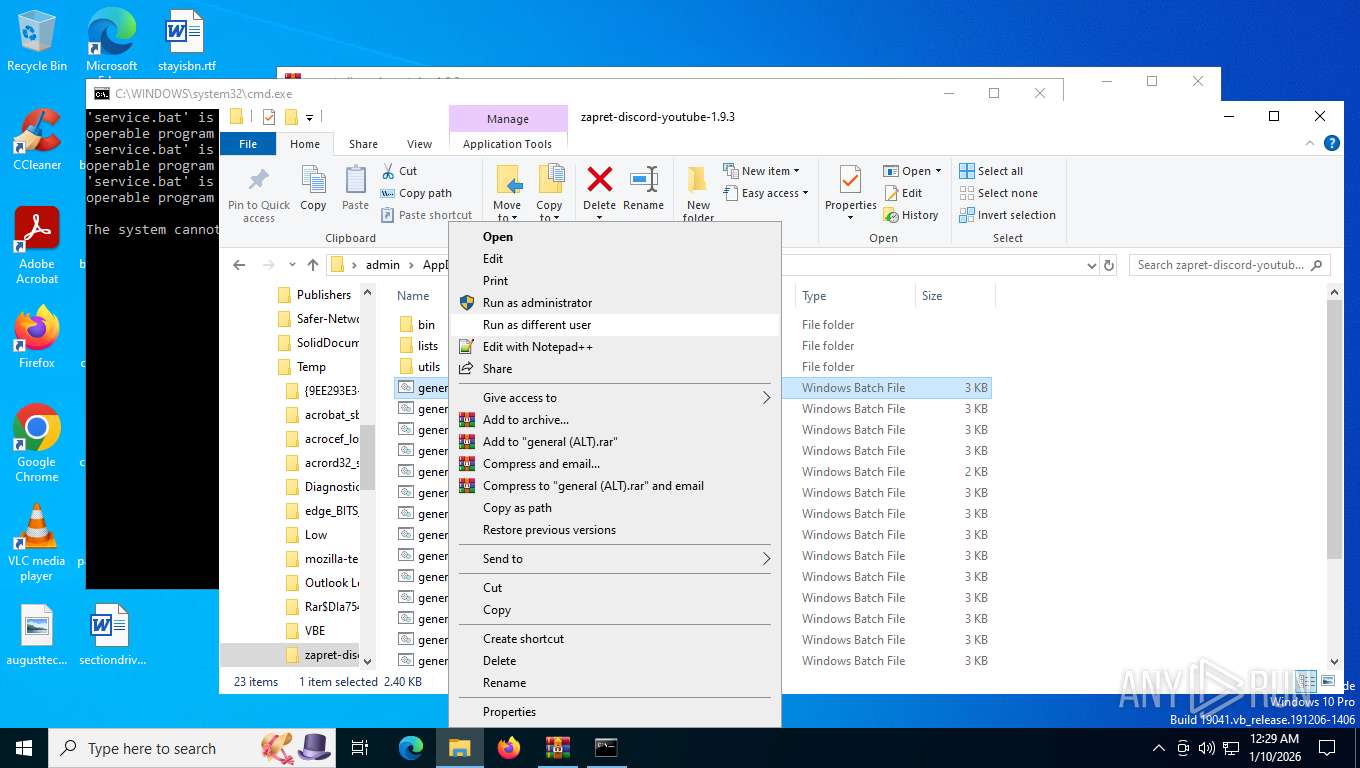
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7540)
Starts application with an unusual extension
- cmd.exe (PID: 7904)
- cmd.exe (PID: 5168)
- cmd.exe (PID: 8064)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7292)
Starts SC.EXE for service management
- cmd.exe (PID: 7852)
Application launched itself
- cmd.exe (PID: 5168)
- cmd.exe (PID: 8064)
Windows service management via SC.EXE
- sc.exe (PID: 7844)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7852)
- cmd.exe (PID: 5168)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5168)
Hides command output
- cmd.exe (PID: 8092)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8092)
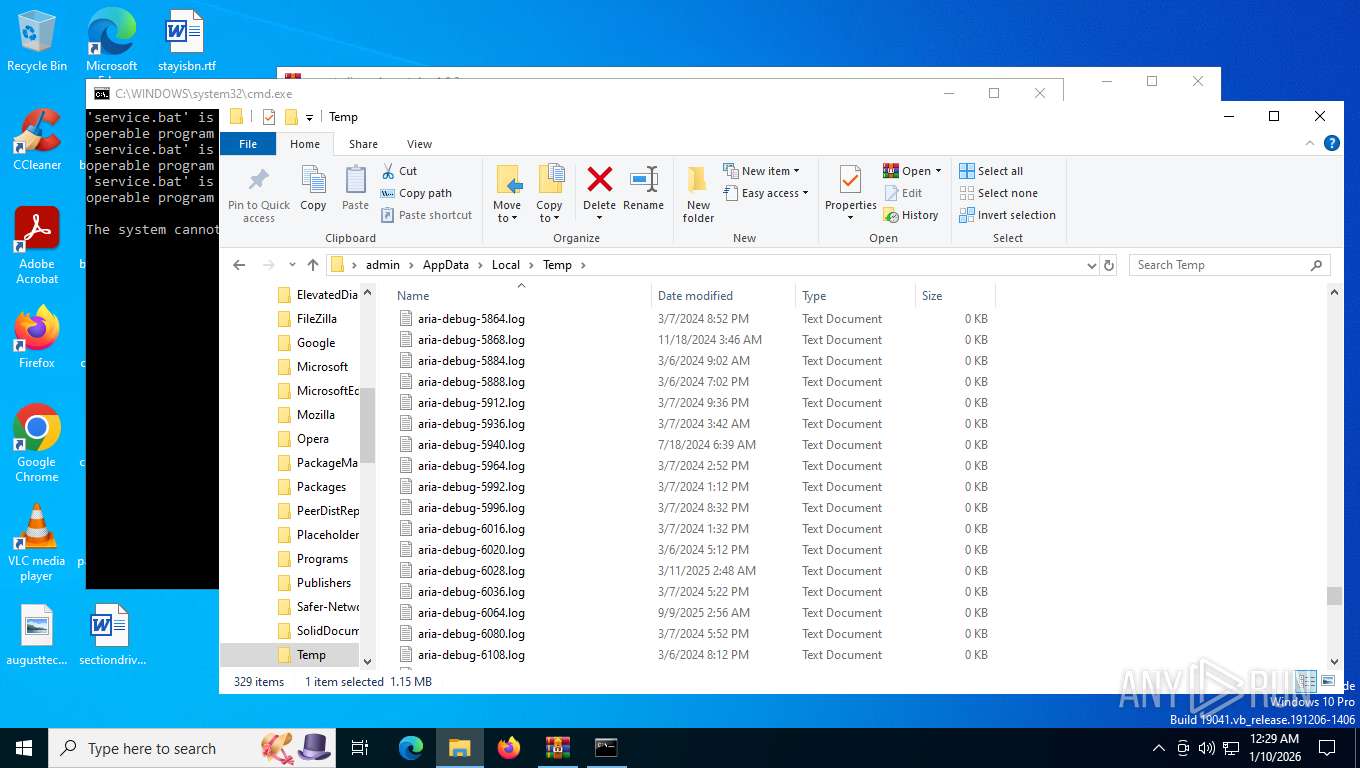
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7540)
- WinRAR.exe (PID: 7292)
Changes the display of characters in the console
- cmd.exe (PID: 7904)
- cmd.exe (PID: 5168)
- cmd.exe (PID: 8064)
Reads the computer name
- TextInputHost.exe (PID: 7728)
- winws.exe (PID: 8004)
Manual execution by a user
- WinRAR.exe (PID: 7292)
- cmd.exe (PID: 5168)
Checks supported languages
- TextInputHost.exe (PID: 7728)
- chcp.com (PID: 7968)
- chcp.com (PID: 4912)
- chcp.com (PID: 8060)
- chcp.com (PID: 8080)
- winws.exe (PID: 8004)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7292)
Disables trace logs
- netsh.exe (PID: 7976)
- netsh.exe (PID: 7828)
- powershell.exe (PID: 8100)
Checks proxy server information
- powershell.exe (PID: 8100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 972453 |
| UncompressedSize: | 2954293 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | bin/cygwin1.dll |
Total processes
166
Monitored processes
24
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | findstr /i "enabled" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | findstr /i "STATE" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4912 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
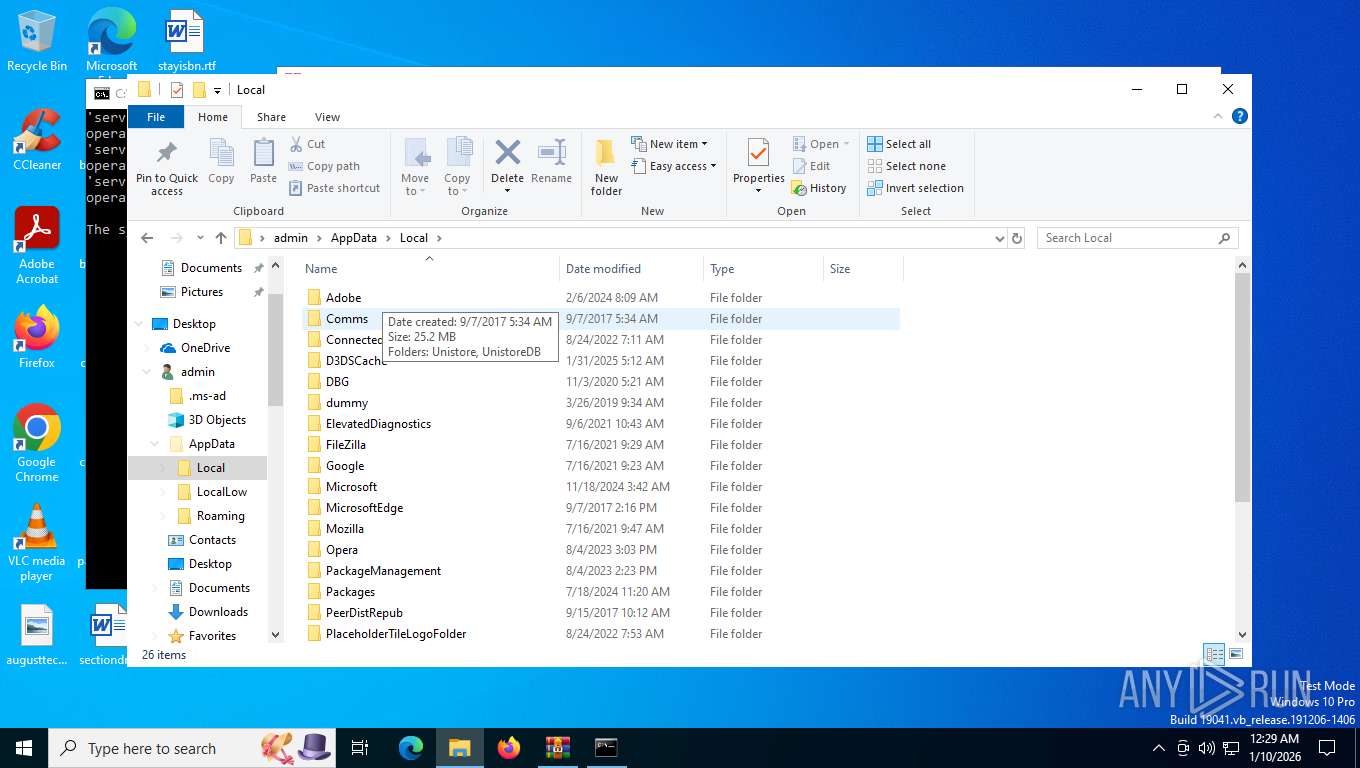
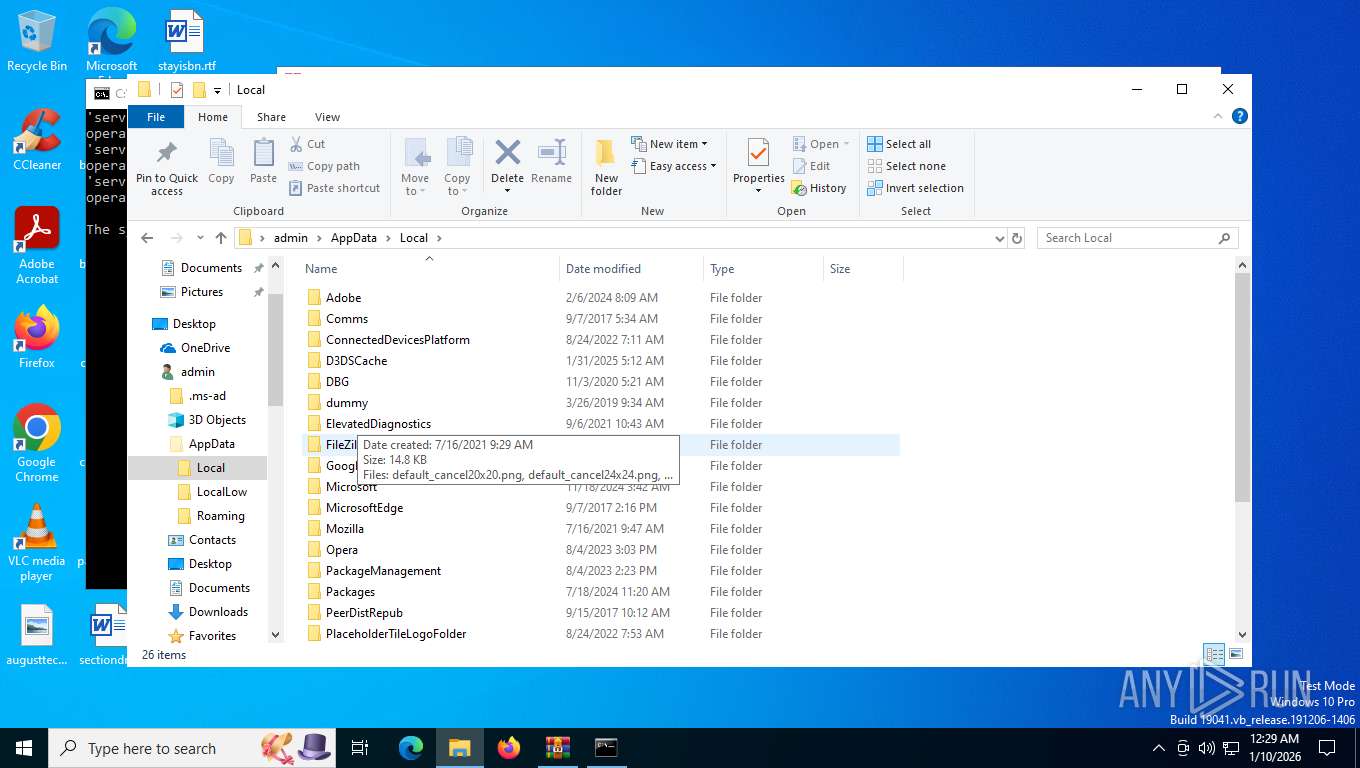
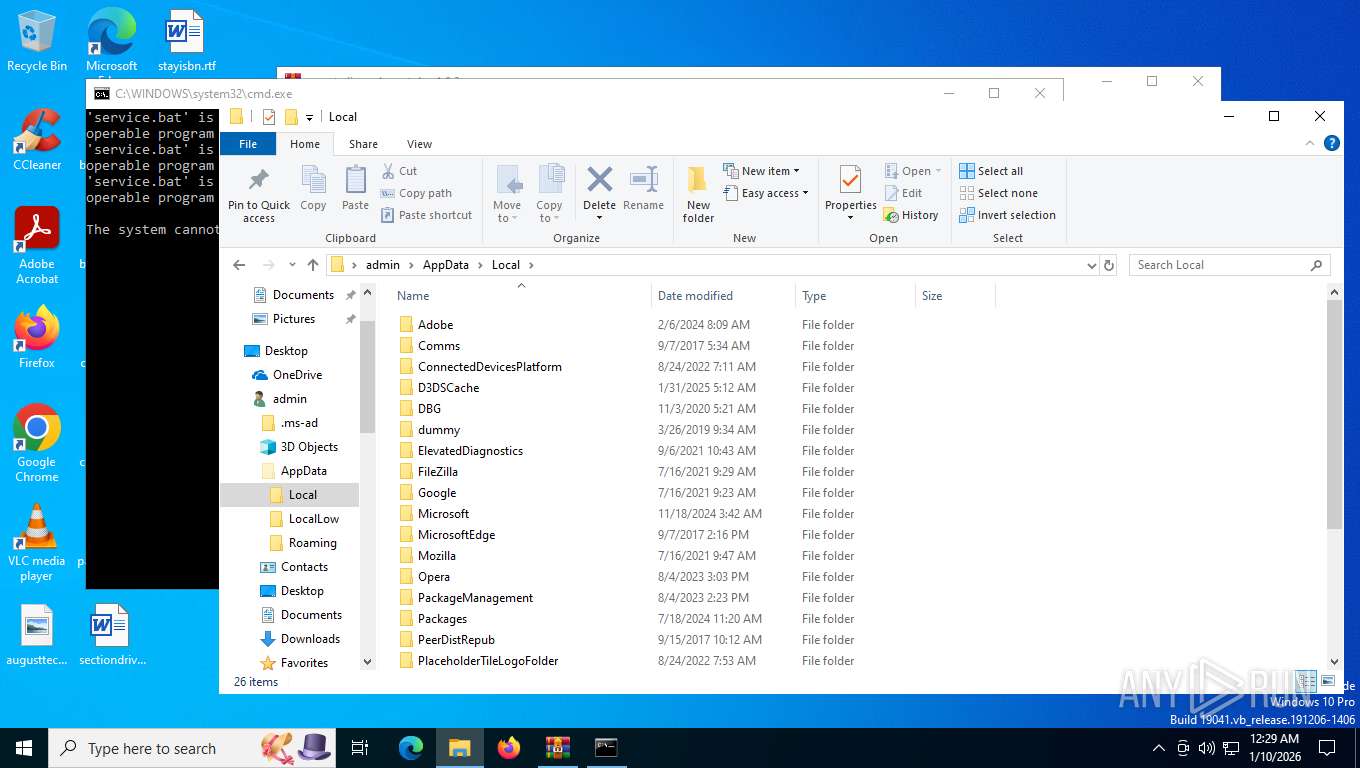
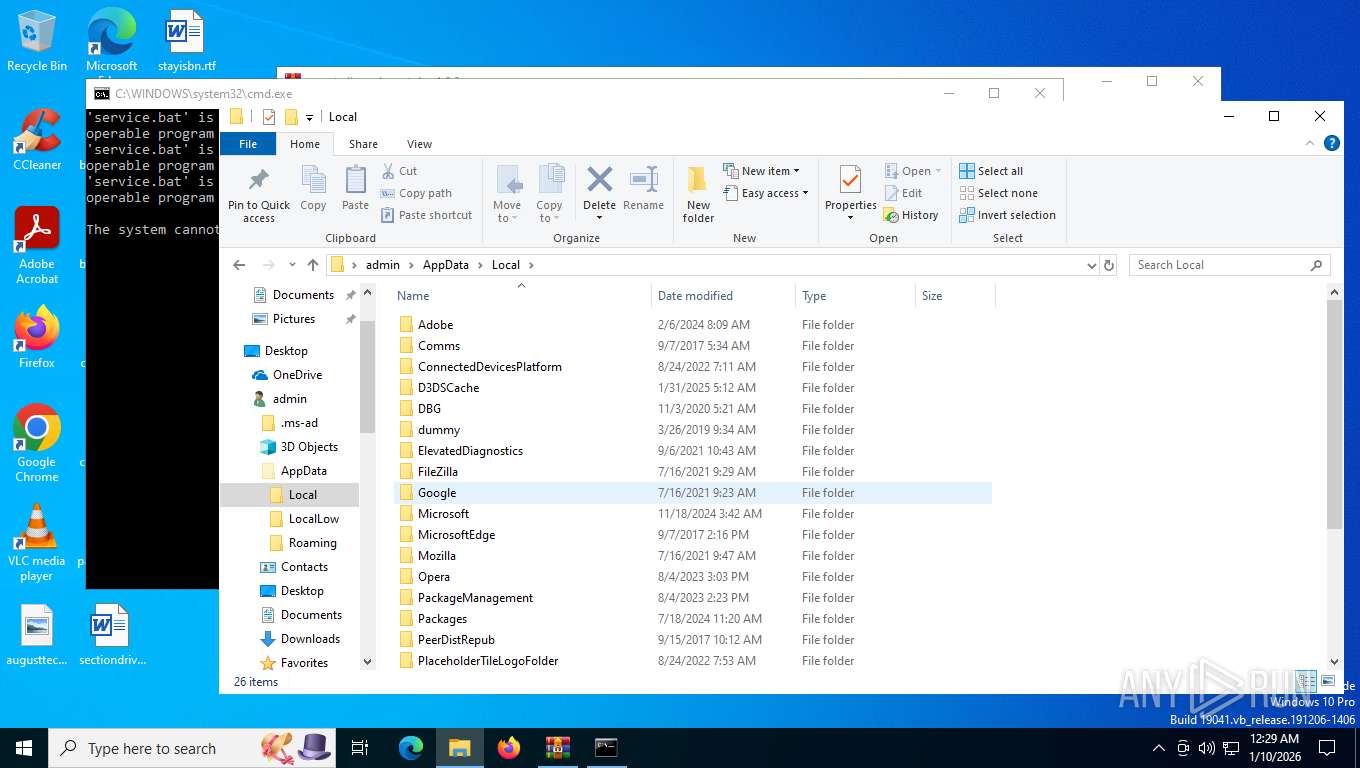
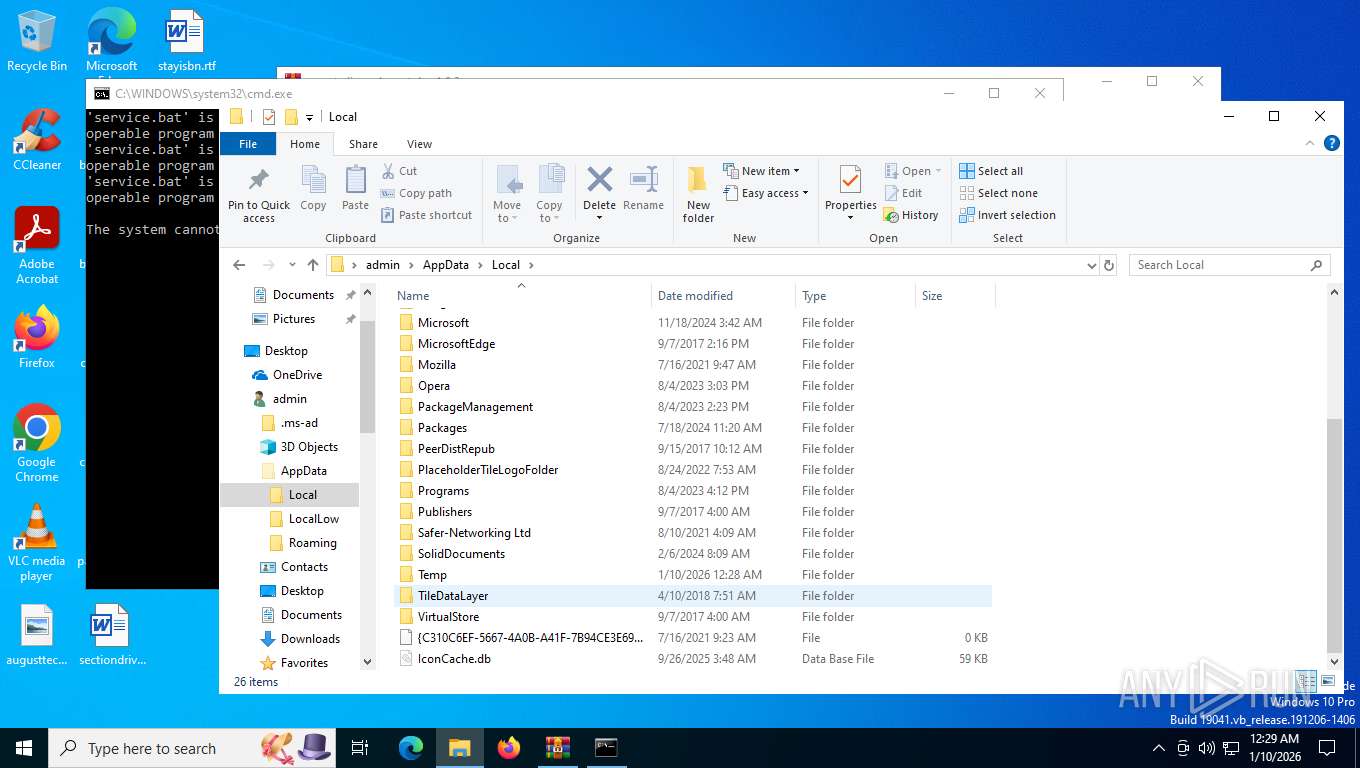
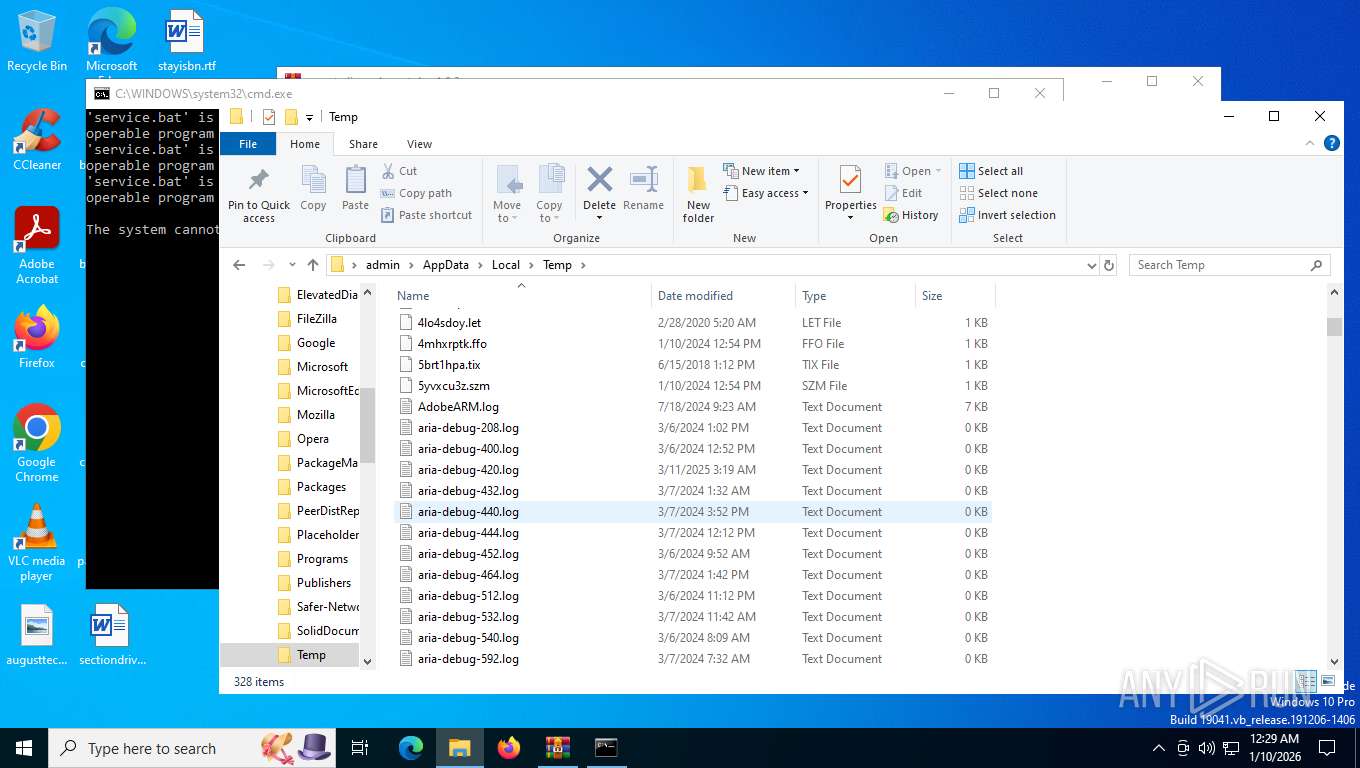
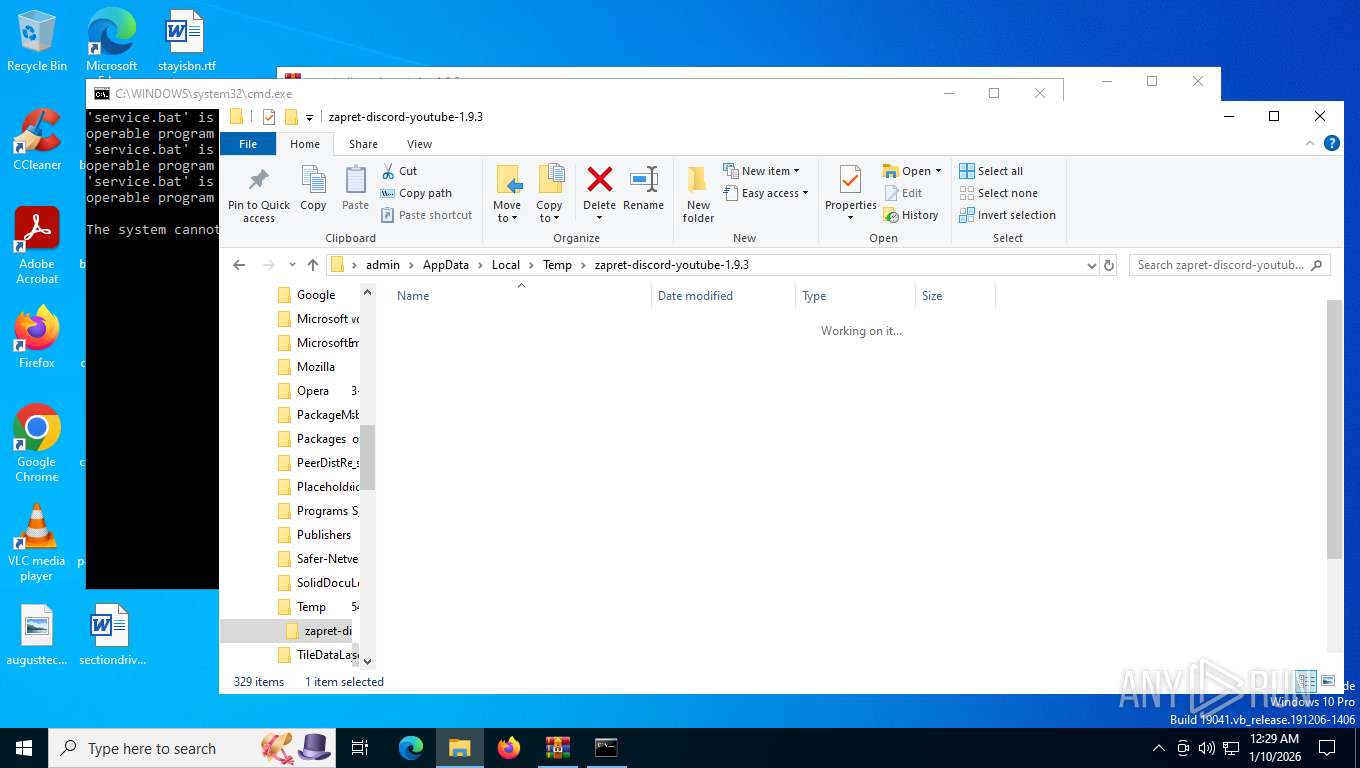
| 5168 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\general (ALT).bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7292 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3.rar" C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7432 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7540 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7728 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 7764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 410
Read events
8 395
Write events
15
Delete events
0
Modification events
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3.rar | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7292) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7292) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
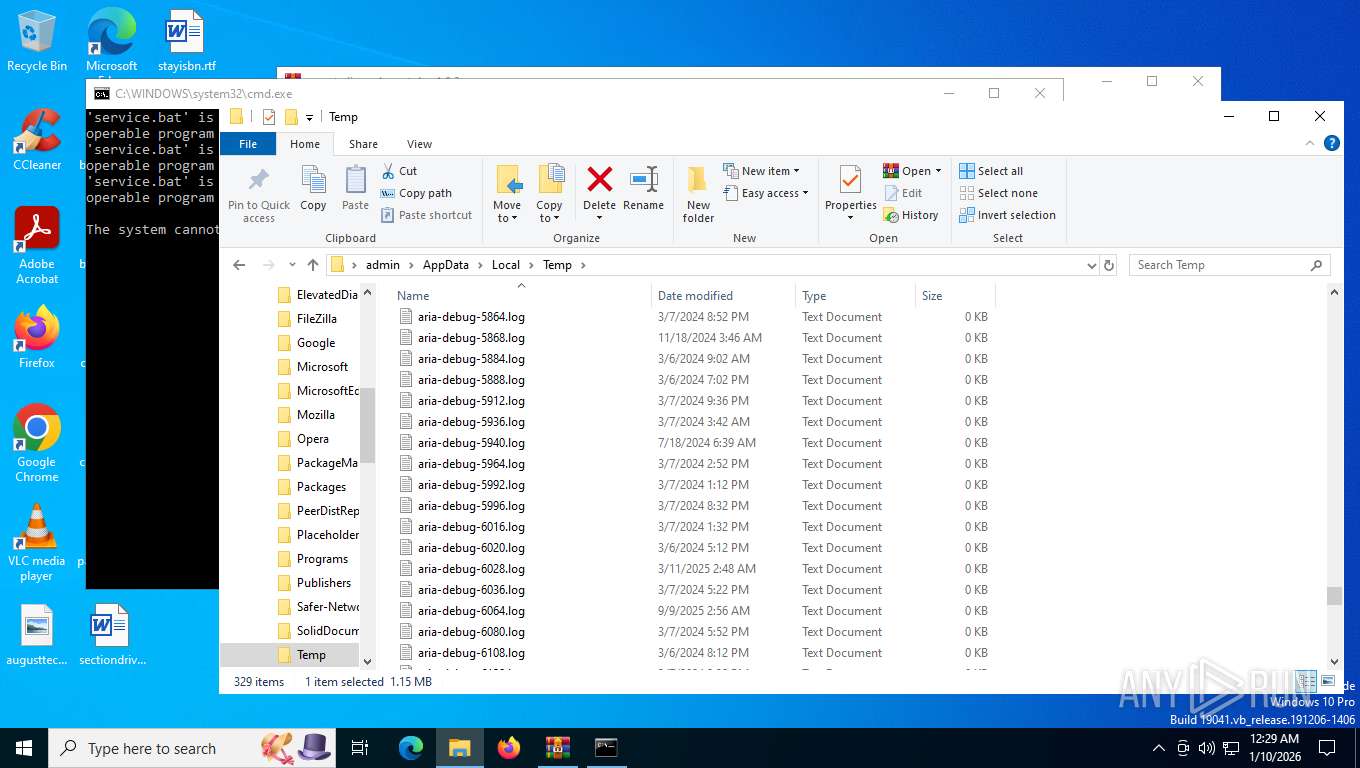
Executable files
4
Suspicious files
5
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
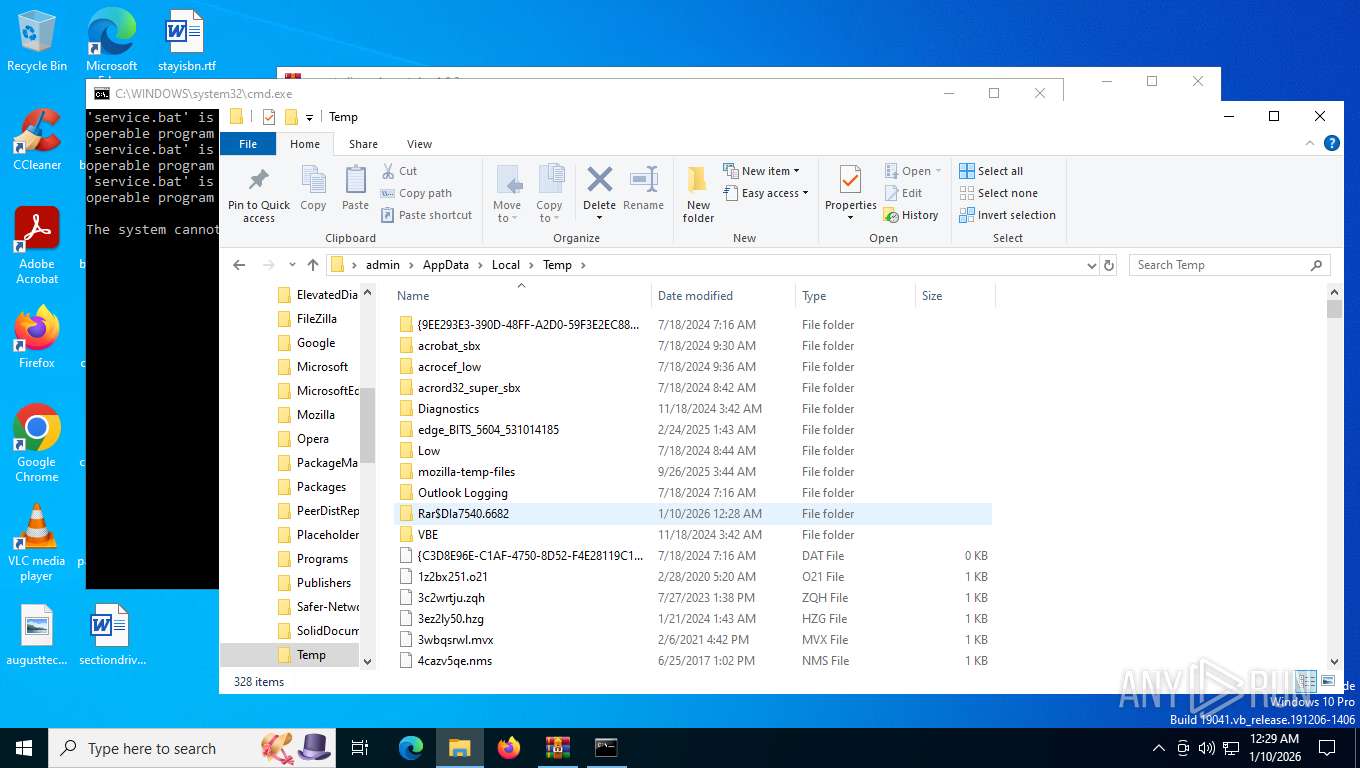
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\tls_clienthello_www_google_com.bin | binary | |
MD5:41E47557F16690DF1781F67C8712714E | SHA256:F966351AE376963DFFBCB5B94256872649B9CDAAB8C5175025936FA50E07DC19 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\WinDivert.dll | executable | |
MD5:B2014D33EE645112D5DC16FE9D9FCBFF | SHA256:C1E060EE19444A259B2162F8AF0F3FE8C4428A1C6F694DCE20DE194AC8D7D9A2 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\tls_clienthello_max_ru.bin | binary | |
MD5:2C2F962B7AB31E5A0760027E1F14AC46 | SHA256:E4A94CEC50B3C048EB988A513EE28191E4D7544DD5F98A9BF94F37EE02D2568E | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\lists\ipset-all.txt | text | |
MD5:42AD35639873F78E1B2DC5C1039499DF | SHA256:19123A22BF1108815C07BDA3CDA8DF282B30BD63E4939949928969C0FD195873 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\lists\list-exclude.txt | text | |
MD5:5532C51FE45FD3E63075D9BF0573649D | SHA256:720F8594E5C2B0F9ACB2437408895A6CE2A443E9A08F597B251663005CB008C8 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\tls_clienthello_4pda_to.bin | binary | |
MD5:E6D649DE132C3C10CB62531EF74F5B73 | SHA256:EEFEAF09DDE8D69B1F176212541F63C68B314A33A335ECED99A8A29F17254DA8 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\cygwin1.dll | executable | |
MD5:A1C82ED072DC079DD7851F82D9AA7678 | SHA256:103104A52E5293CE418944725DF19E2BF81AD9269B9A120D71D39028E821499B | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\bin\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 7292 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3\lists\ipset-all.txt.backup | text | |
MD5:4DC21738D0A6CB7625FF33B071113FEF | SHA256:47BDDD7CEB076F3434552D9CCC5A1288A4B638C1D0A9227F3E257DF7CA276C96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
27
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
7436 | SIHClient.exe | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
7436 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7436 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5628 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5628 | svchost.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 5.51 Kb | whitelisted |
4744 | svchost.exe | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
7436 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | unknown | text | 87.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5628 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5148 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5628 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5628 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5628 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4744 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |