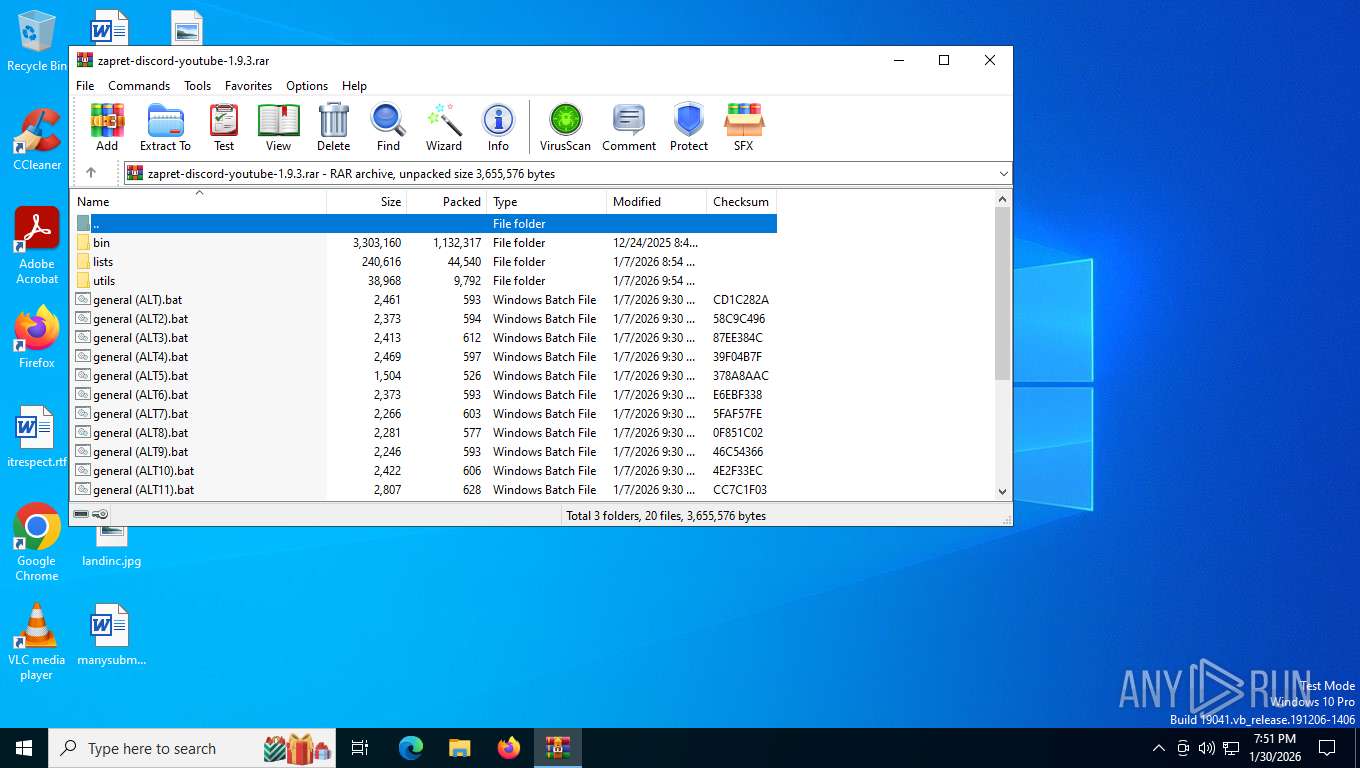
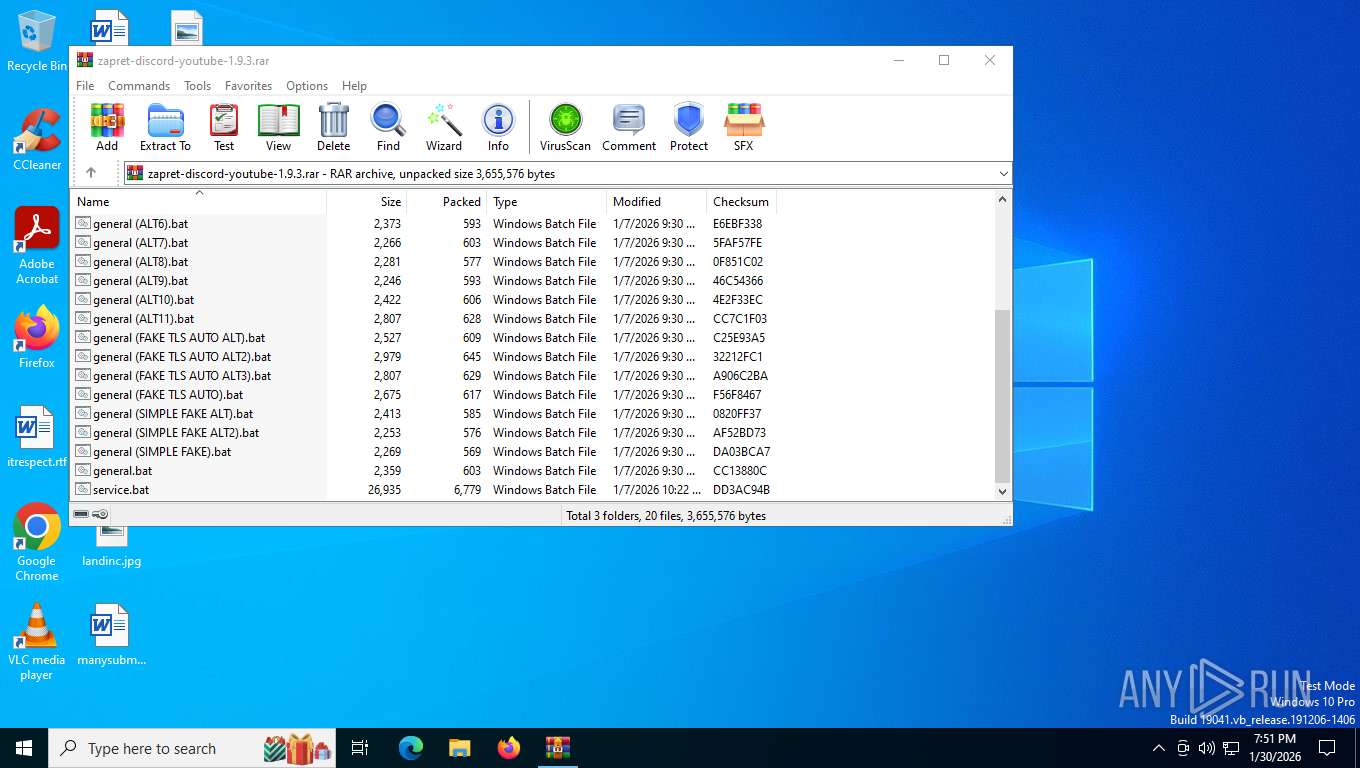
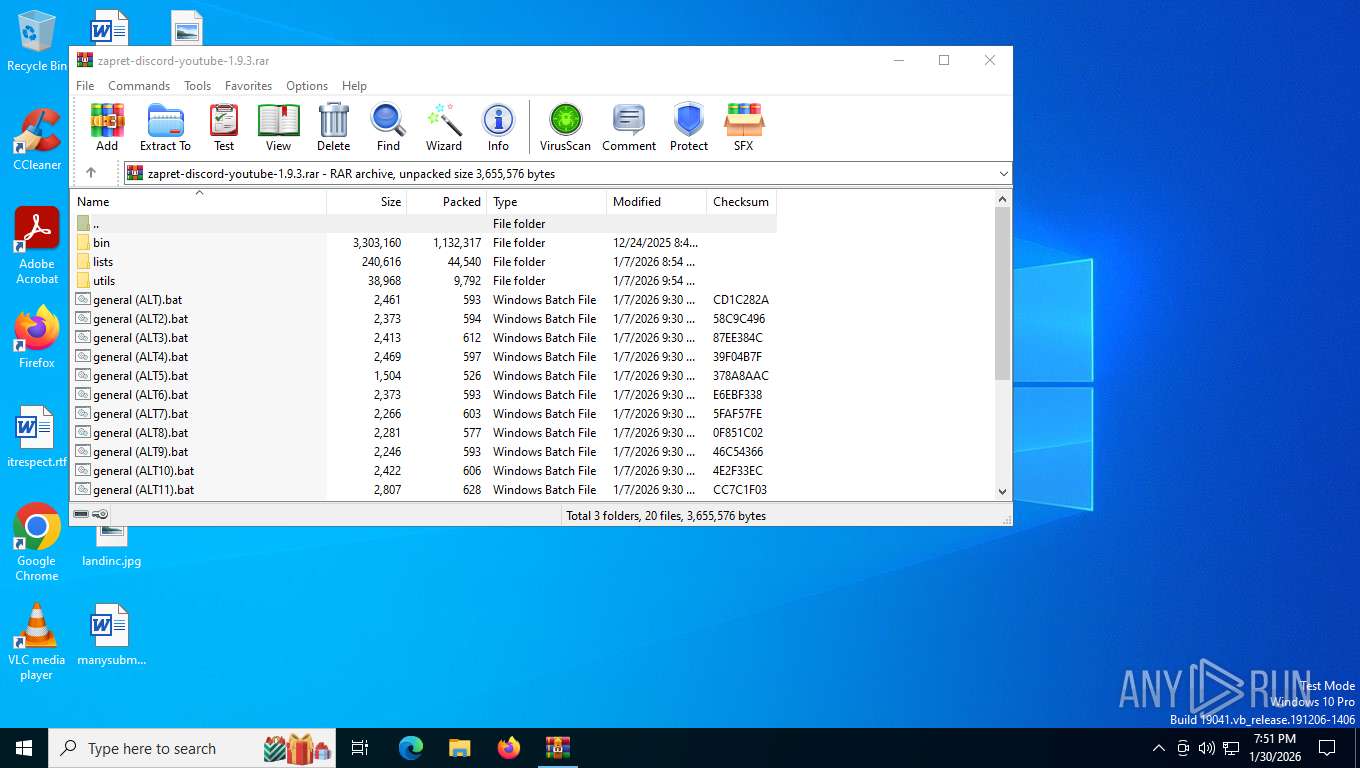
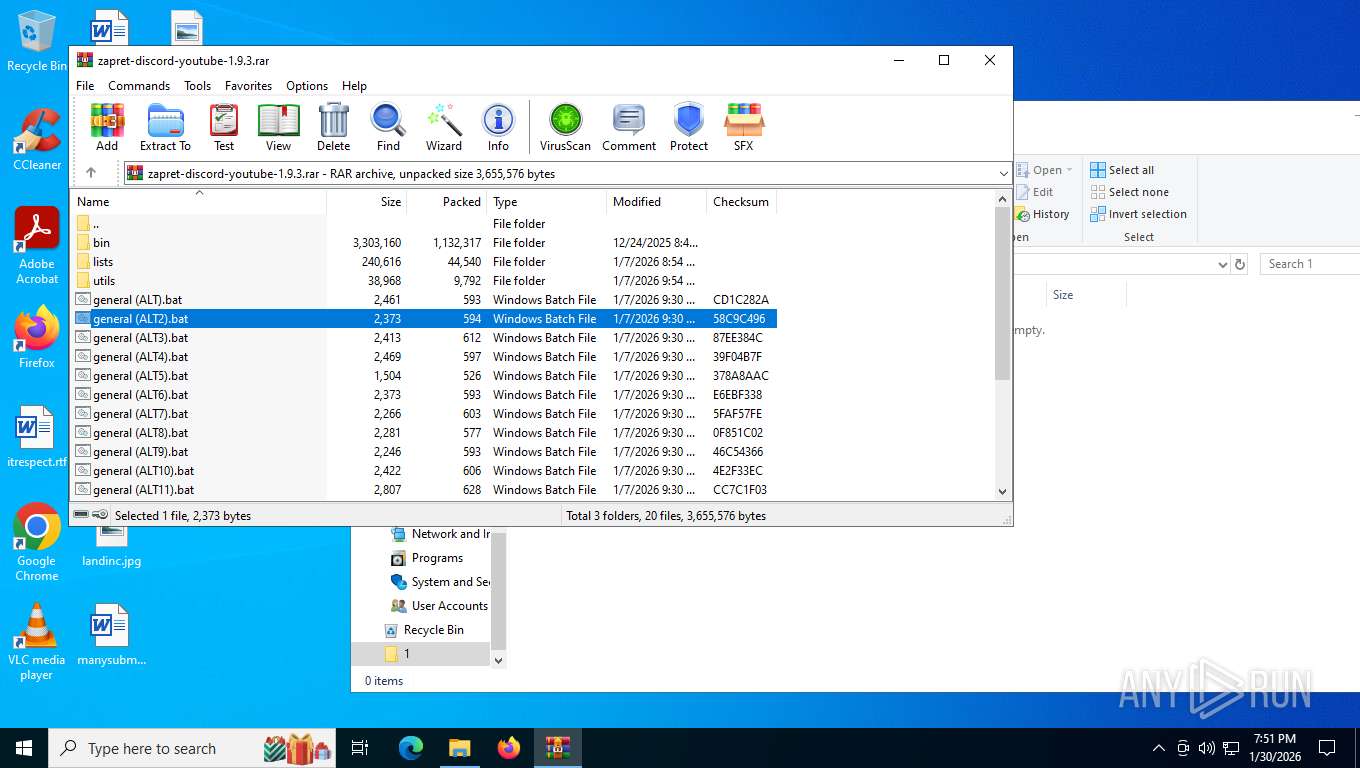
| File name: | zapret-discord-youtube-1.9.3.rar |
| Full analysis: | https://app.any.run/tasks/0031d023-7cb4-4684-8c32-2252dff45486 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2026, 00:51:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5073ECFCB0A1A33D4389D33B2ED6CFC3 |
| SHA1: | C36160FFEE4C0FA54D30BF9617613E0E44A5823C |
| SHA256: | D3C5A75D58729CD6E1A171E59A3D3DBB91D7DCBCBD024E025BCBF3DC39BB5CC3 |
| SSDEEP: | 49152:jb4FMyNCQMf5udb/DNj7Ze9rm45sDC69wDe1fwTCFvppsBS9VWIwQtkcTa8ZM1My:jb4utV58b/Jj789rv5D6uDefjFvppr9w |
MALICIOUS
Malicious driver has been detected
- WinRAR.exe (PID: 8248)
Detects Cygwin installation
- WinRAR.exe (PID: 8248)
Generic archive extractor
- WinRAR.exe (PID: 8248)
SUSPICIOUS
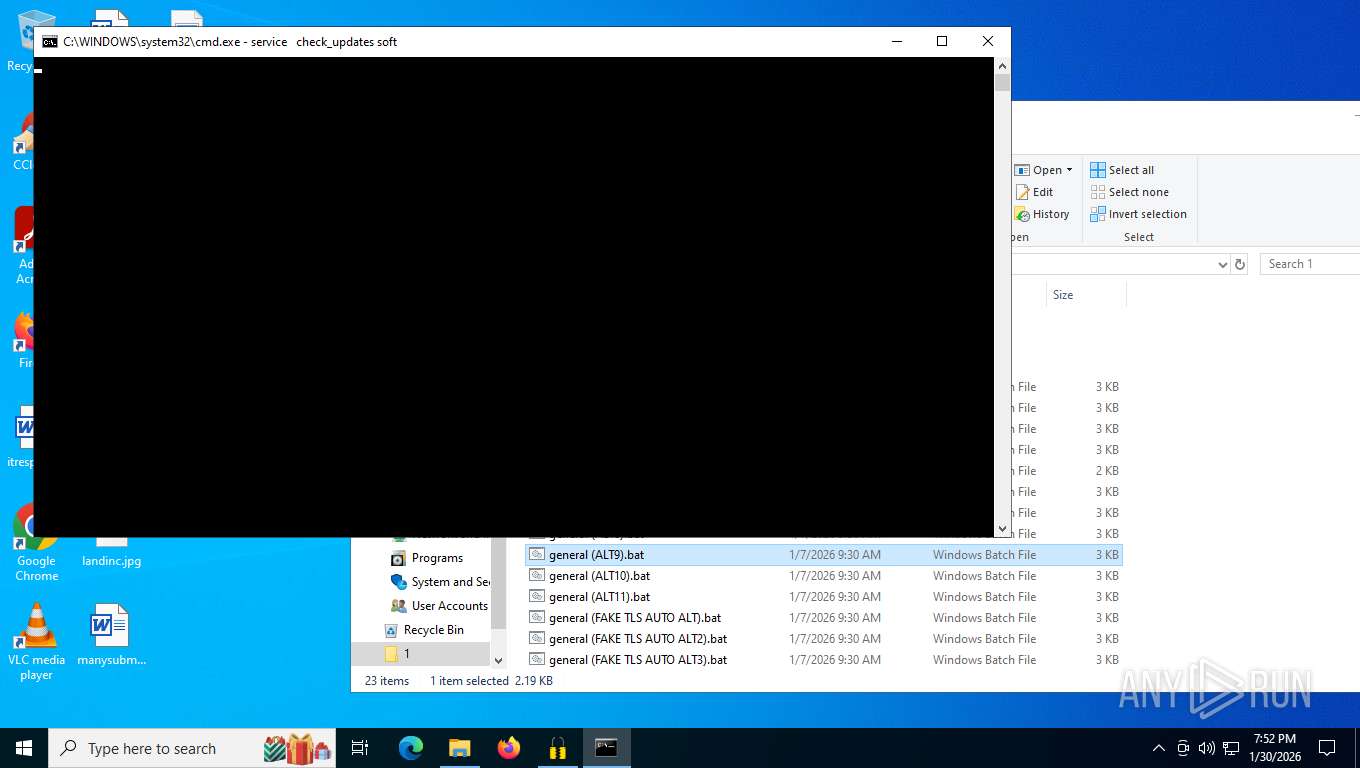
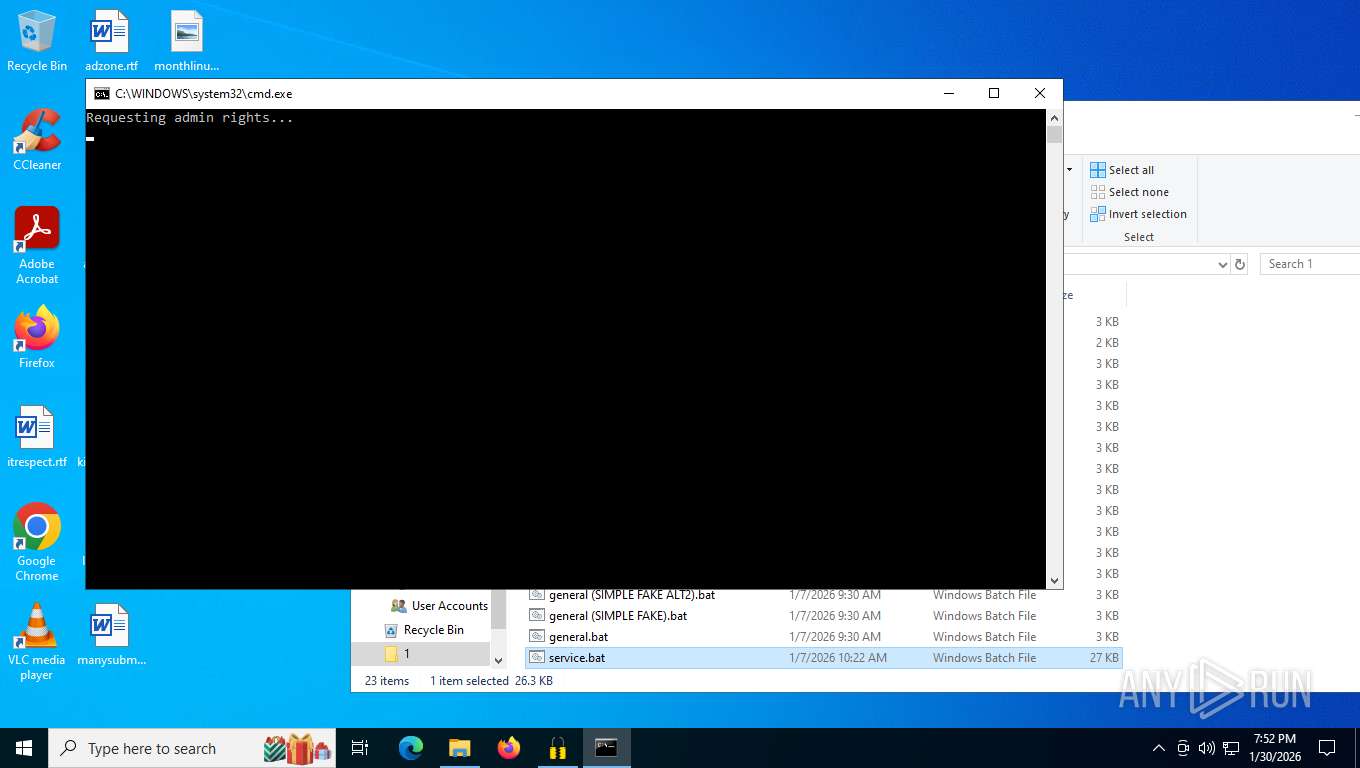
Application launched itself
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 8708)
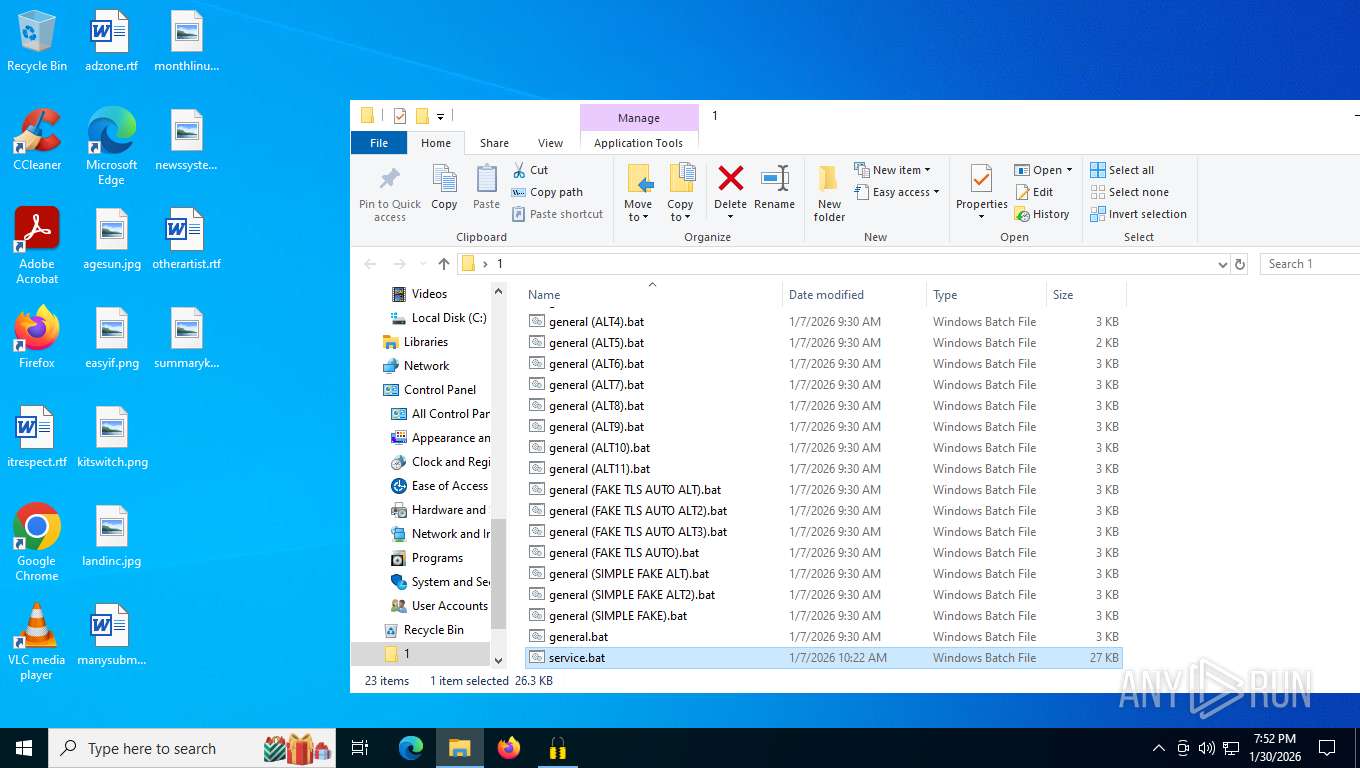
Starts SC.EXE for service management
- cmd.exe (PID: 5392)
- cmd.exe (PID: 5728)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5392)
- cmd.exe (PID: 7680)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 6056)
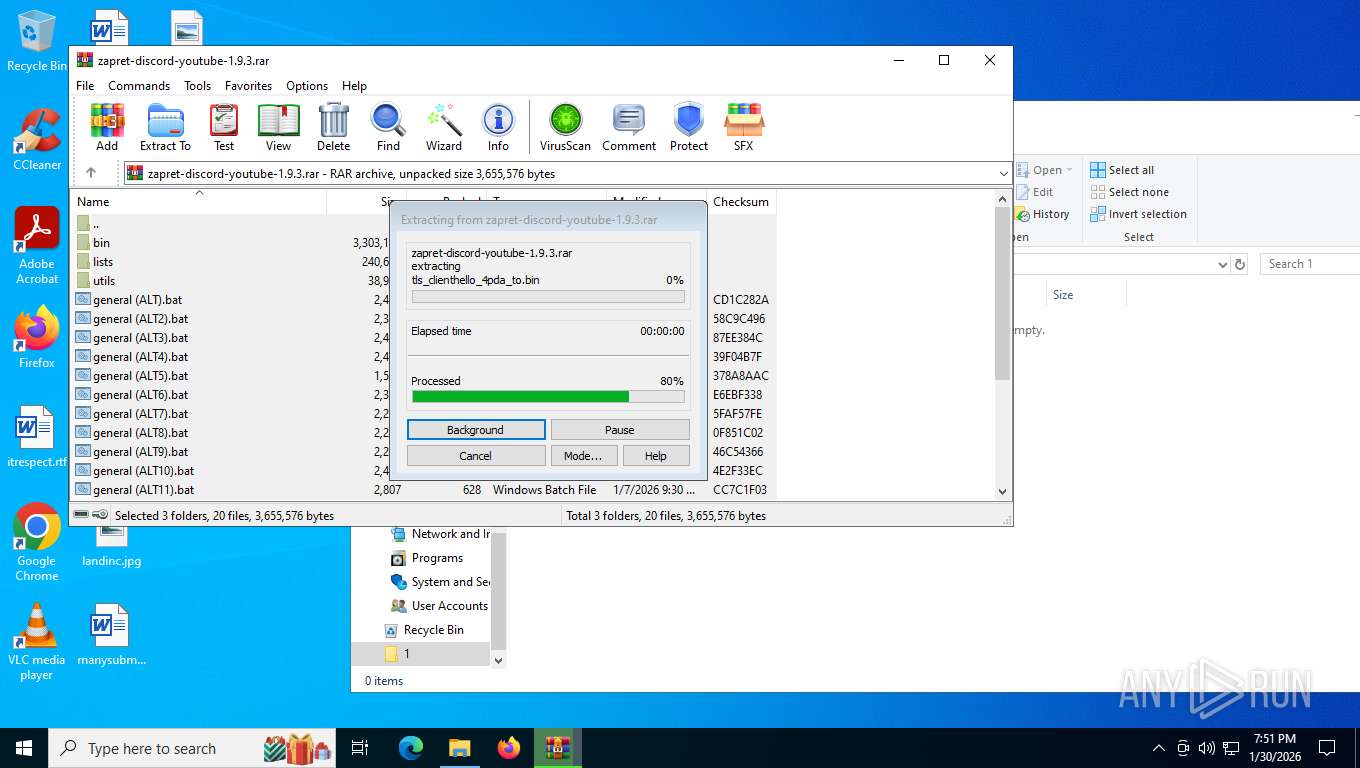
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8248)
Windows service management via SC.EXE
- sc.exe (PID: 1956)
- sc.exe (PID: 4104)
Starts application with an unusual extension
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 6056)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7680)
- cmd.exe (PID: 6172)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 1172)
- powershell.exe (PID: 2484)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 8708)
Hides command output
- cmd.exe (PID: 8608)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 8708)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8608)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 8772)
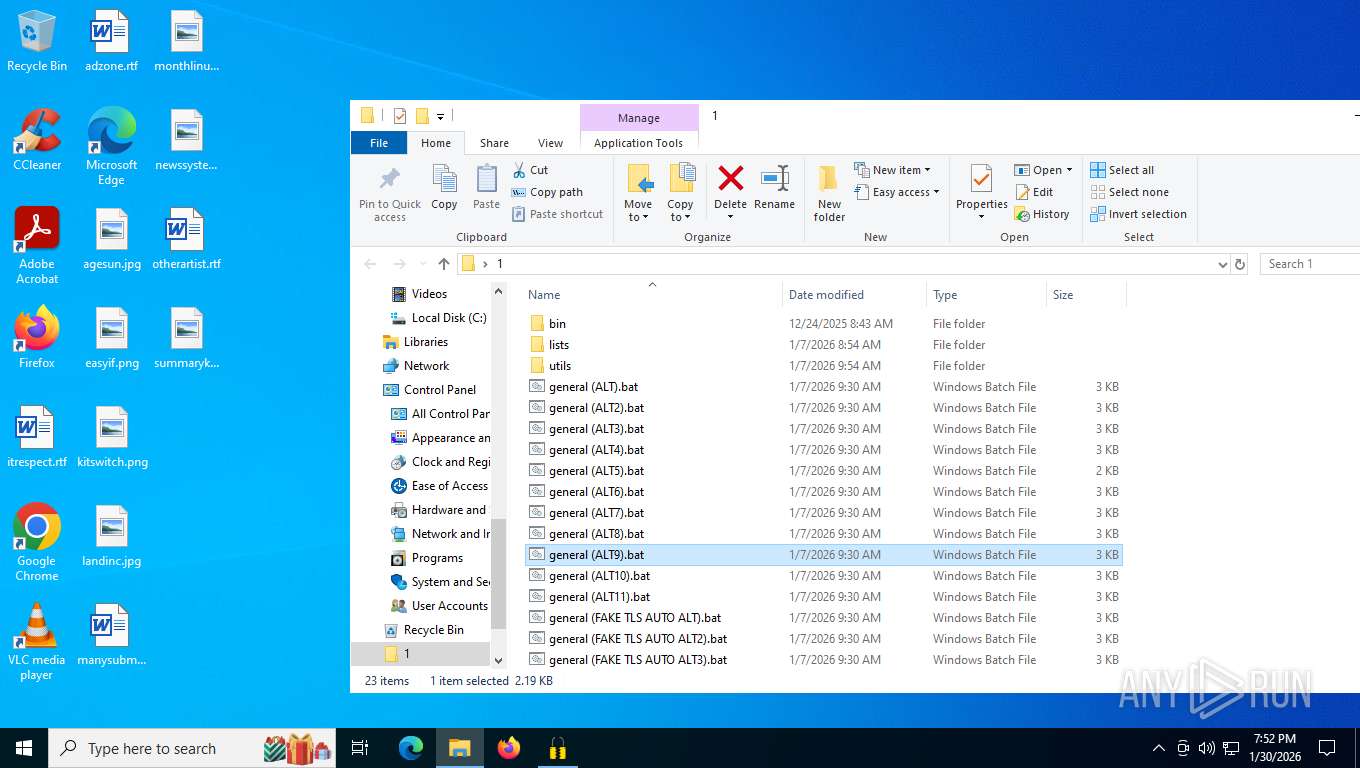
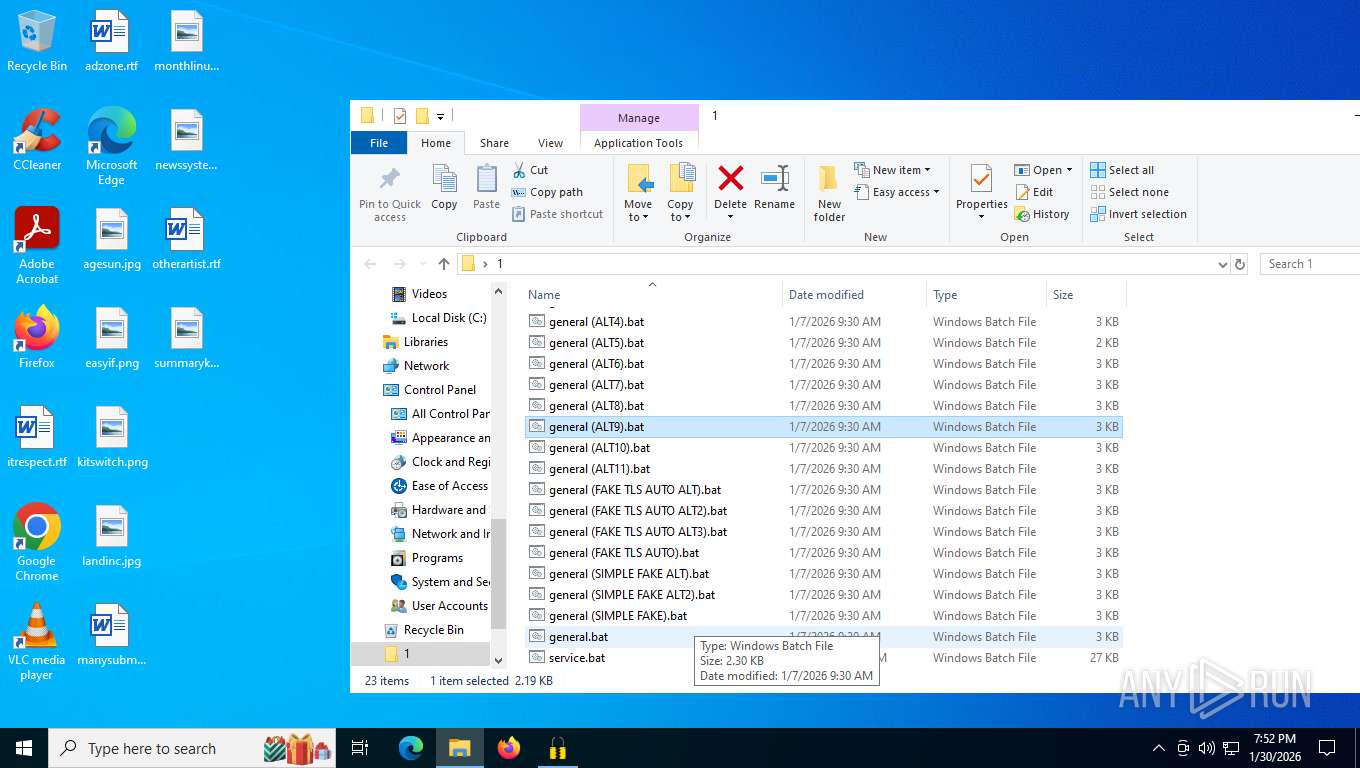
Executing commands from a ".bat" file
- powershell.exe (PID: 2484)
Starts process via Powershell
- powershell.exe (PID: 2484)
INFO
Drops script file
- WinRAR.exe (PID: 8248)
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7940)
- powershell.exe (PID: 9184)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 1172)
- powershell.exe (PID: 8696)
- cmd.exe (PID: 8772)
- powershell.exe (PID: 2484)
- cmd.exe (PID: 6056)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8248)
The sample compiled with english language support
- WinRAR.exe (PID: 8248)
Manual execution by a user
- cmd.exe (PID: 7680)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 8772)
Changes the display of characters in the console
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 6056)
Checks supported languages
- chcp.com (PID: 8788)
- chcp.com (PID: 1188)
- chcp.com (PID: 6300)
- winws.exe (PID: 3796)
- chcp.com (PID: 1084)
- chcp.com (PID: 5868)
- chcp.com (PID: 4072)
- winws.exe (PID: 7928)
- chcp.com (PID: 8132)
- chcp.com (PID: 6912)
- chcp.com (PID: 7824)
Disables trace logs
- netsh.exe (PID: 3276)
- netsh.exe (PID: 1600)
- powershell.exe (PID: 9184)
- netsh.exe (PID: 5804)
- netsh.exe (PID: 8916)
- powershell.exe (PID: 8696)
Reads the computer name
- winws.exe (PID: 3796)
- winws.exe (PID: 7928)
Checks proxy server information
- powershell.exe (PID: 9184)
- powershell.exe (PID: 8696)
The sample was built using Cygwin
- winws.exe (PID: 3796)
- winws.exe (PID: 7928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 972453 |
| UncompressedSize: | 2954293 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | bin/cygwin1.dll |
Total processes
205
Monitored processes
57
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | findstr /i "timestamps" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
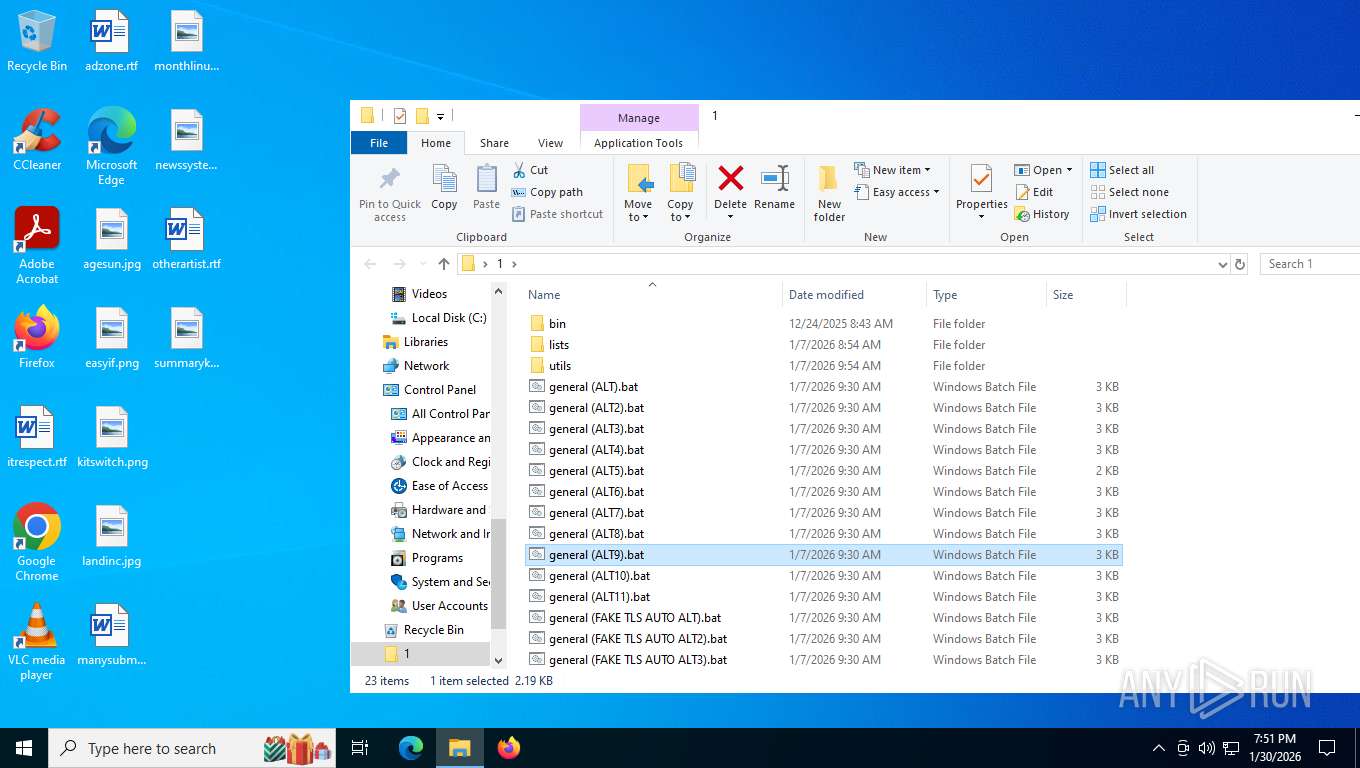
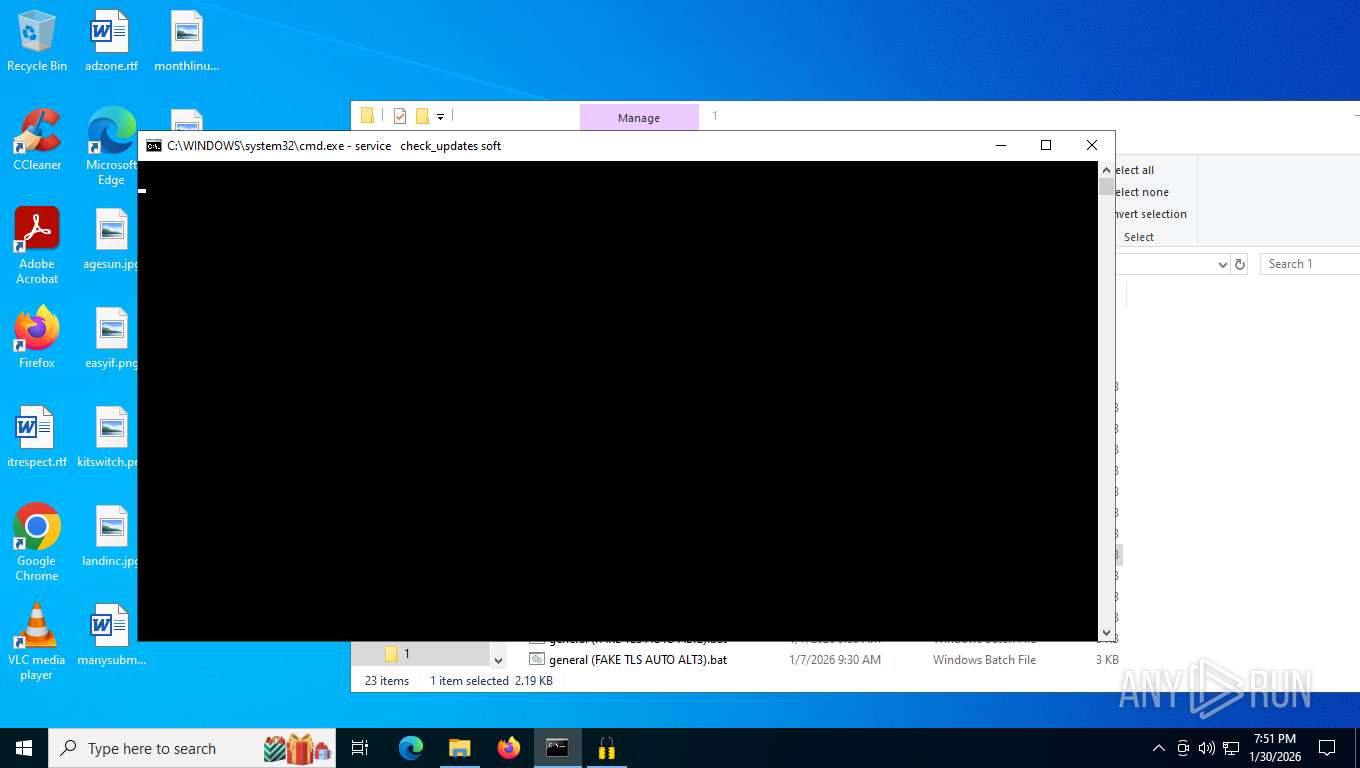
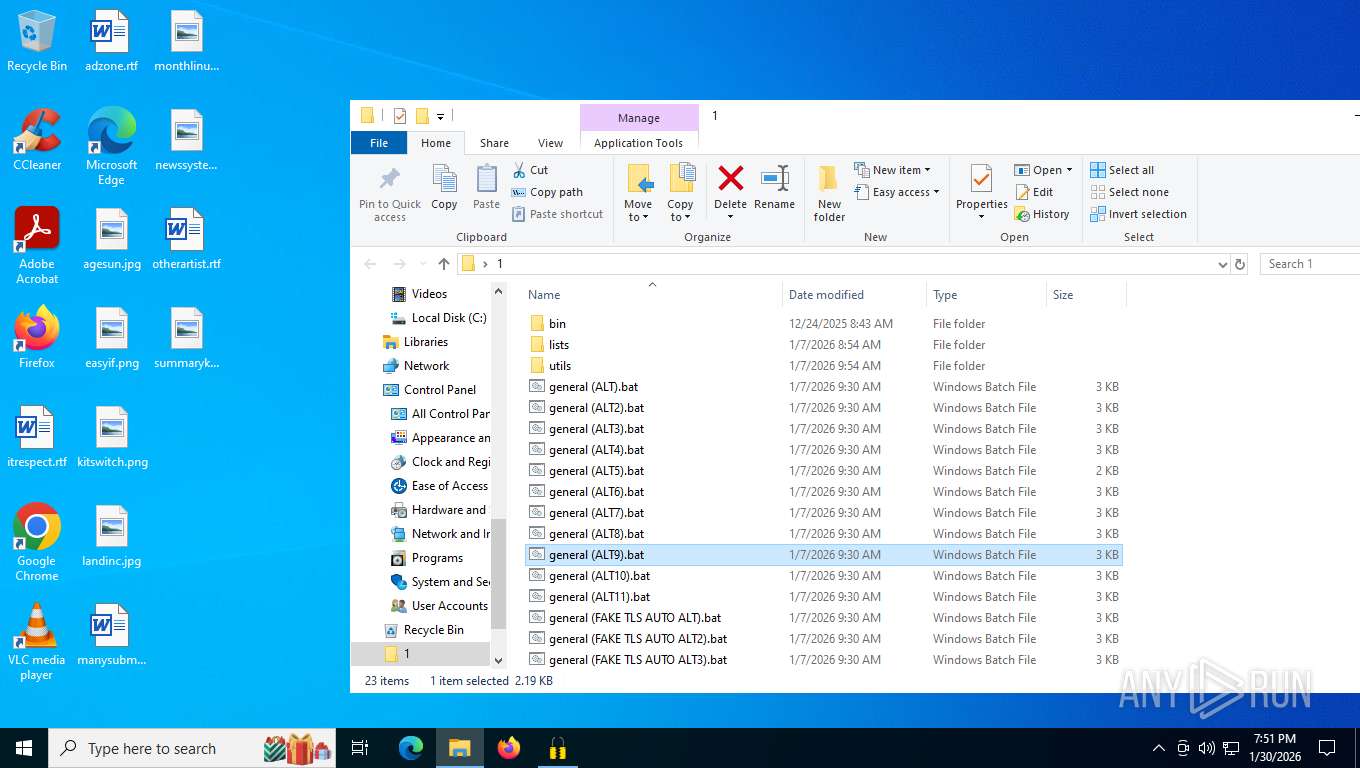
| 1172 | C:\WINDOWS\system32\cmd.exe /K service check_updates soft | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | findstr /i "enabled" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | netsh interface tcp set global timestamps=enabled | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\Desktop\1\bin\winws.exe" --wf-tcp=80,443,2053,2083,2087,2096,8443,12 --wf-udp=443,19294-19344,50000-50100,12 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\1\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\1\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\1\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\1\bin\quic_initial_www_google_com.bin" --new --filter-udp=19294-19344,50000-50100 --filter-l7=discord,stun --dpi-desync=fake --dpi-desync-repeats=6 --new --filter-tcp=2053,2083,2087,2096,8443 --hostlist-domains=discord.media --dpi-desync=hostfakesplit --dpi-desync-repeats=4 --dpi-desync-fooling=ts --dpi-desync-hostfakesplit-mod=host=www.google.com --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\1\lists\list-google.txt" --ip-id=zero --dpi-desync=hostfakesplit --dpi-desync-repeats=4 --dpi-desync-fooling=ts --dpi-desync-hostfakesplit-mod=host=www.google.com --new --filter-tcp=80,443 --hostlist="C:\Users\admin\Desktop\1\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\1\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\1\lists\ipset-exclude.txt" --dpi-desync=hostfakesplit --dpi-desync-repeats=4 --dpi-desync-fooling=ts,md5sig --dpi-desync-hostfakesplit-mod=host=ozon.ru --new --filter-udp=443 --ipset="C:\Users\admin\Desktop\1\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\1\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\1\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\1\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80,443,12 --ipset="C:\Users\admin\Desktop\1\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\1\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\1\lists\ipset-exclude.txt" --dpi-desync=hostfakesplit --dpi-desync-repeats=4 --dpi-desync-fooling=ts --dpi-desync-hostfakesplit-mod=host=ozon.ru --new --filter-udp=12 --ipset="C:\Users\admin\Desktop\1\lists\ipset-all.txt" --ipset-exclude="C:\Users\admin\Desktop\1\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=12 --dpi-desync-any-protocol=1 --dpi-desync-fake-unknown-udp="C:\Users\admin\Desktop\1\bin\quic_initial_www_google_com.bin" --dpi-desync-cutoff=n2 | C:\Users\admin\Desktop\1\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1956 | sc query "zapret" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 073
Read events
18 051
Write events
22
Delete events
0
Modification events
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube-1.9.3.rar | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (8248) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
5
Text files
35
Unknown types
0
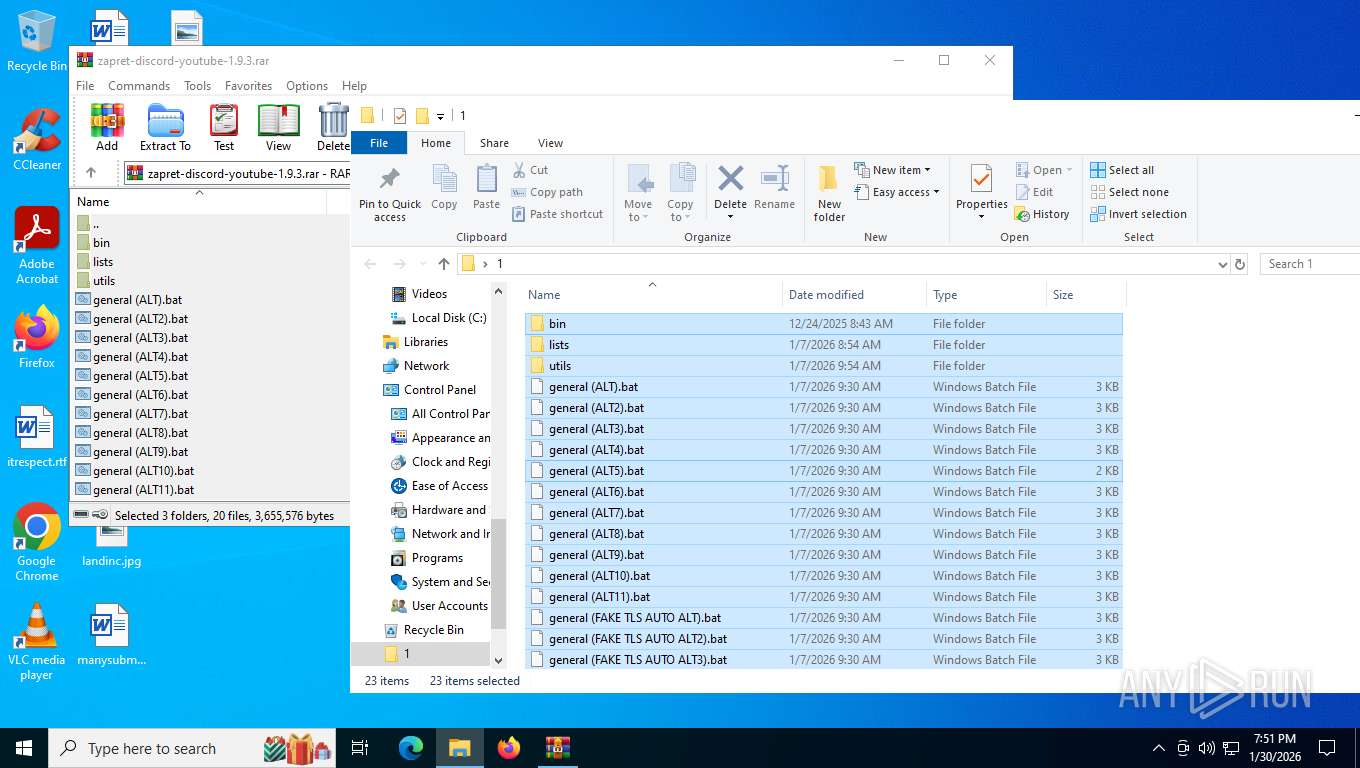
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\lists\list-google.txt | text | |
MD5:0C333BB65317588DC354B5C93E4203FF | SHA256:36EC86BBE19B9E5815D807D6B25DFFD01BDF69E9CF6C05D7CF60CD7C9BF036D8 | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\general (ALT3).bat | text | |
MD5:DA79047D434BEA1BC833E6346DCBF6F2 | SHA256:401001621590599251AE2623FA6C5FD19C9CE43269875F17126098B38557CD2C | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\bin\cygwin1.dll | executable | |
MD5:A1C82ED072DC079DD7851F82D9AA7678 | SHA256:103104A52E5293CE418944725DF19E2BF81AD9269B9A120D71D39028E821499B | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\utils\check_updates.enabled | text | |
MD5:9E57D6BDA4BEC067FF636FE400AF6EA5 | SHA256:02FA0E83883800772EC3462347E9A9F623FA3E13BE7D4DE7E0B2CB7E425AB212 | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\bin\tls_clienthello_www_google_com.bin | binary | |
MD5:41E47557F16690DF1781F67C8712714E | SHA256:F966351AE376963DFFBCB5B94256872649B9CDAAB8C5175025936FA50E07DC19 | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\bin\tls_clienthello_max_ru.bin | binary | |
MD5:2C2F962B7AB31E5A0760027E1F14AC46 | SHA256:E4A94CEC50B3C048EB988A513EE28191E4D7544DD5F98A9BF94F37EE02D2568E | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\lists\ipset-all.txt | text | |
MD5:42AD35639873F78E1B2DC5C1039499DF | SHA256:19123A22BF1108815C07BDA3CDA8DF282B30BD63E4939949928969C0FD195873 | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\bin\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\bin\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 8248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8248.34840\lists\list-general.txt | text | |
MD5:5ACBACD29F9CAD31F51D9B0FF7B0D9F9 | SHA256:3E6BFCE8E68832A24B80619D8635097B6F1AFD981C1A242E505365D0B6E792C9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
31
DNS requests
17
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
8400 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
2688 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
2688 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
2688 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
2688 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
356 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8400 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8400 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4256 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.63:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.241.218:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8400 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
9184 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
8696 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |