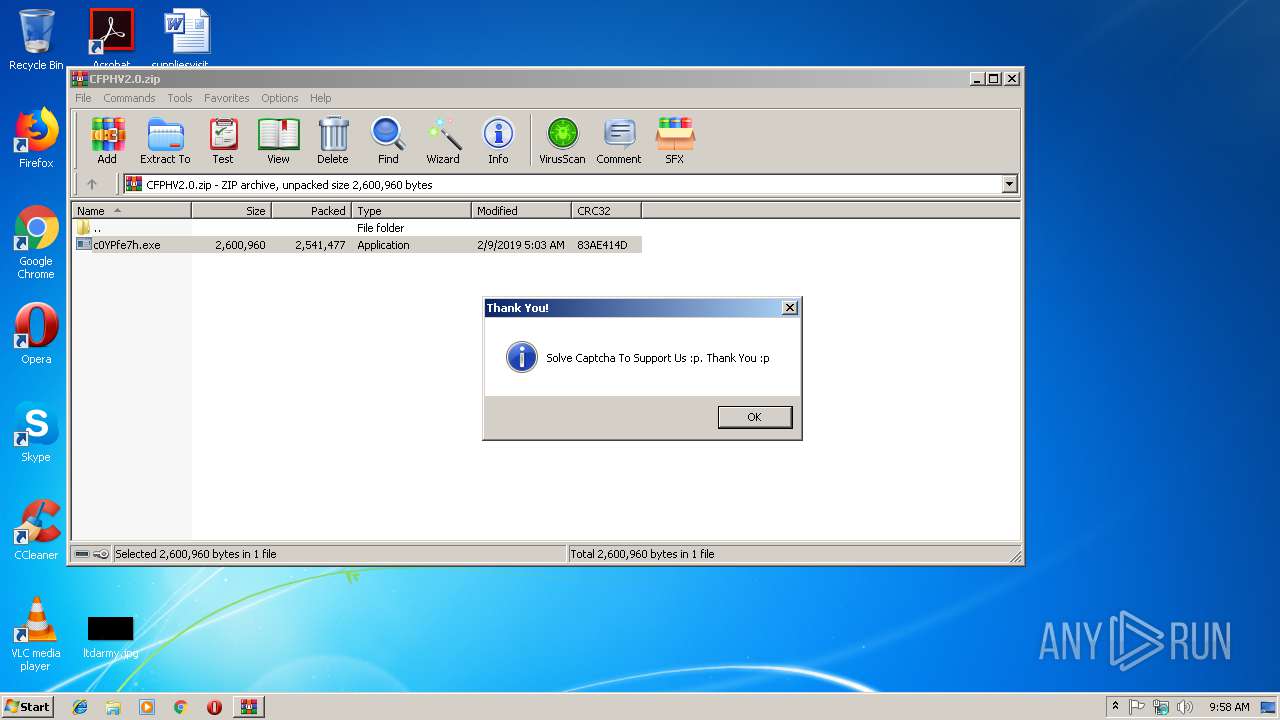
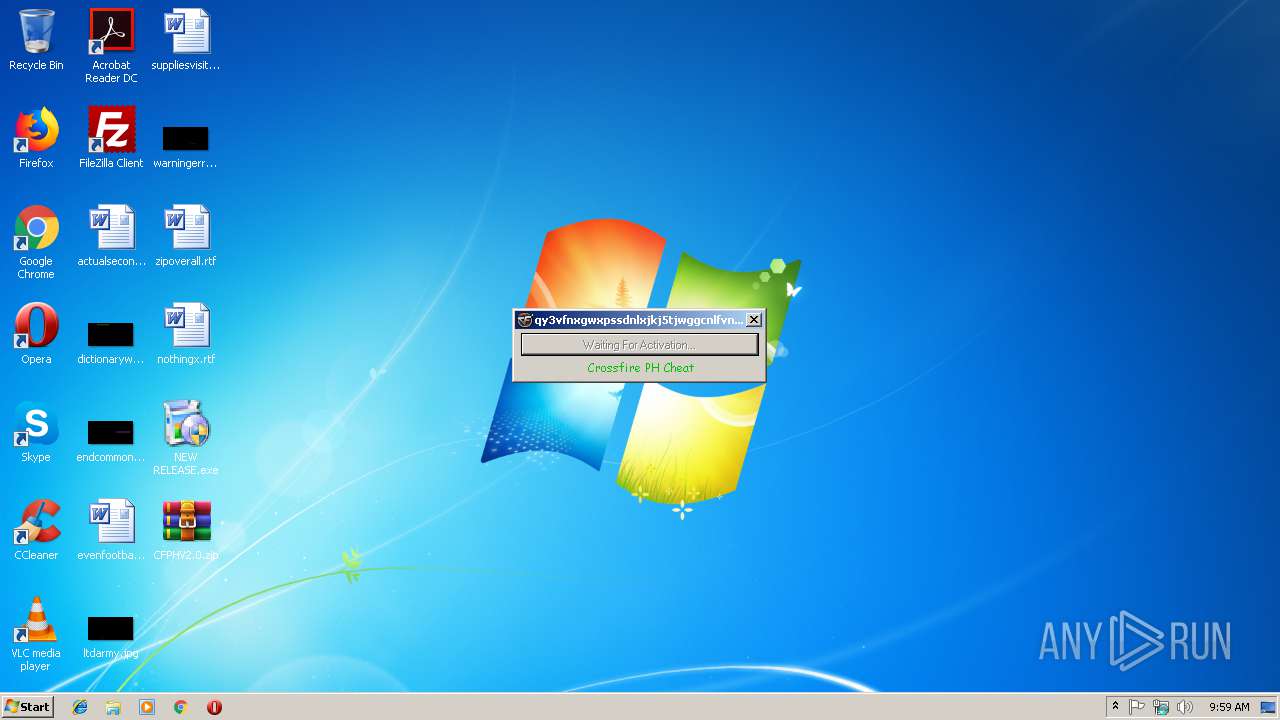
| File name: | NEW RELEASE.exe |
| Full analysis: | https://app.any.run/tasks/5ef98c54-e898-4587-8c39-89a595ecc3f2 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 09:58:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FD795AA8E5FB45F117EE4FEAF5A4E2FA |
| SHA1: | D196A77195290EF214E0A345BDC9B1BFDA5E57E4 |
| SHA256: | D3BCCC5F6F85F2B6D18B3BD961463583ACC2183E8A18516258F64A9F1741CC56 |
| SSDEEP: | 98304:vyurVX64DikVYc3ZuLb0lWZ7CS9iMqrn0+XYOFKl:6rIV5EL4lWZijIn |
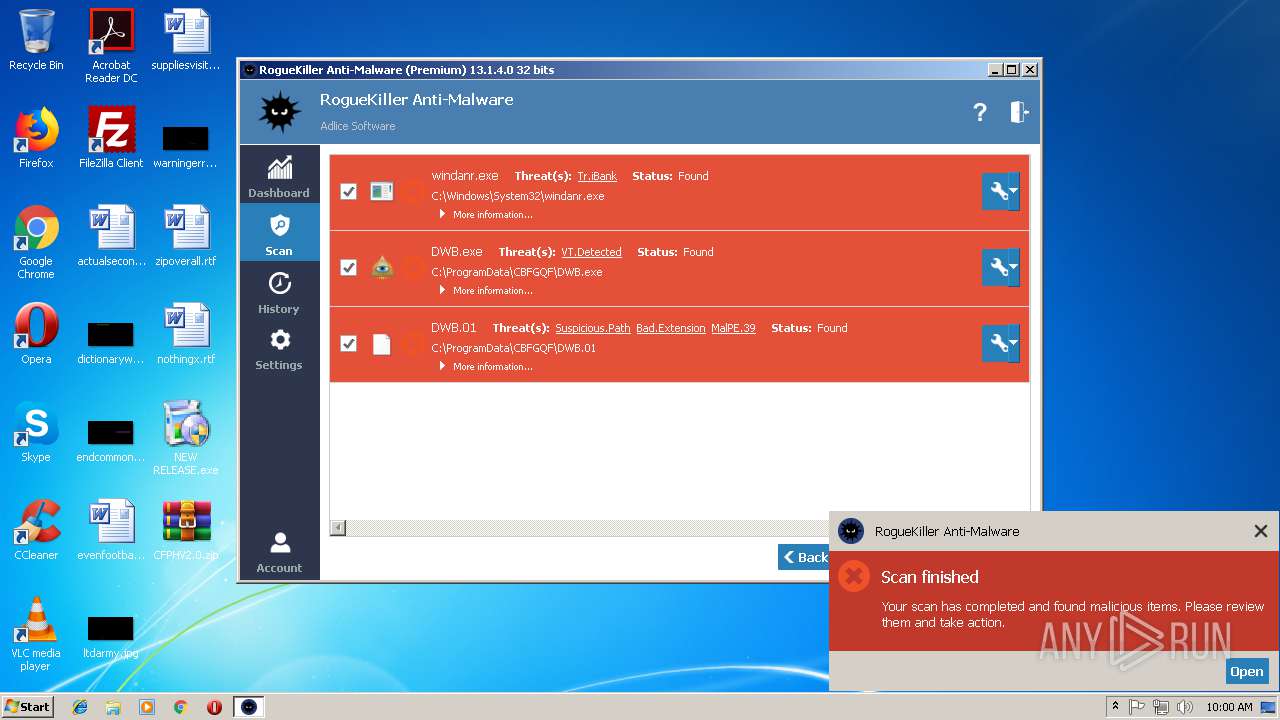
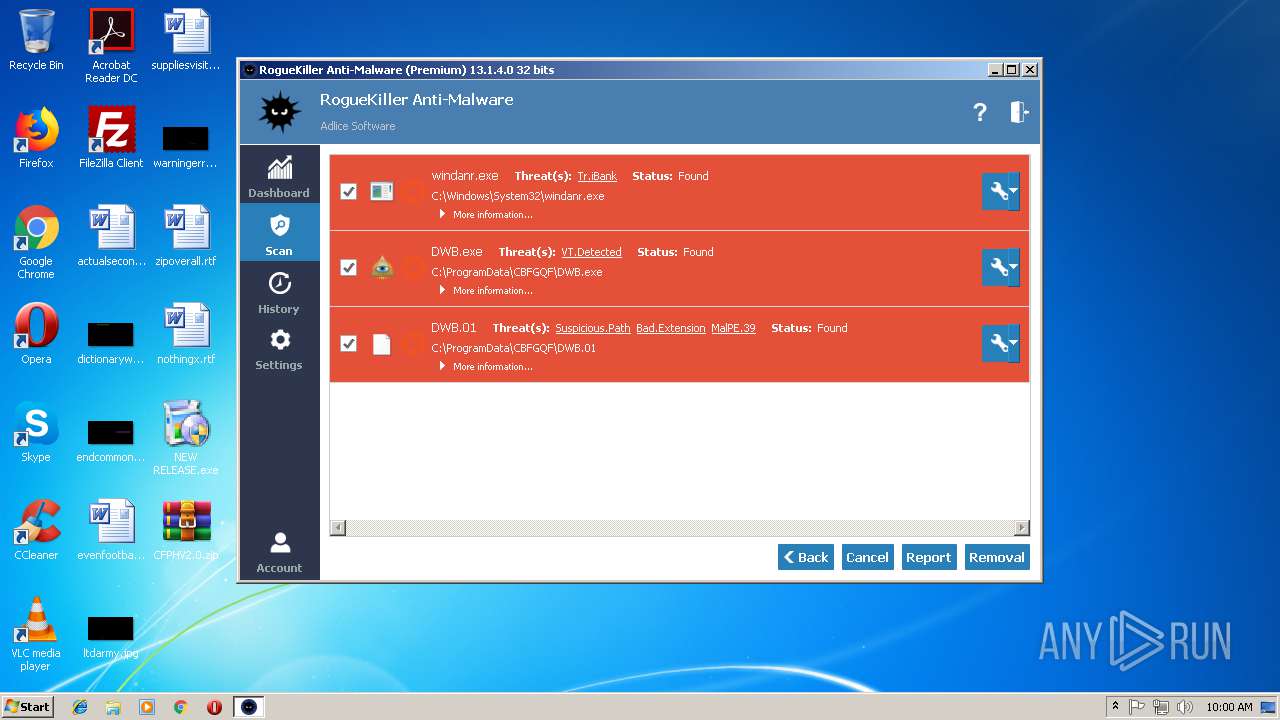
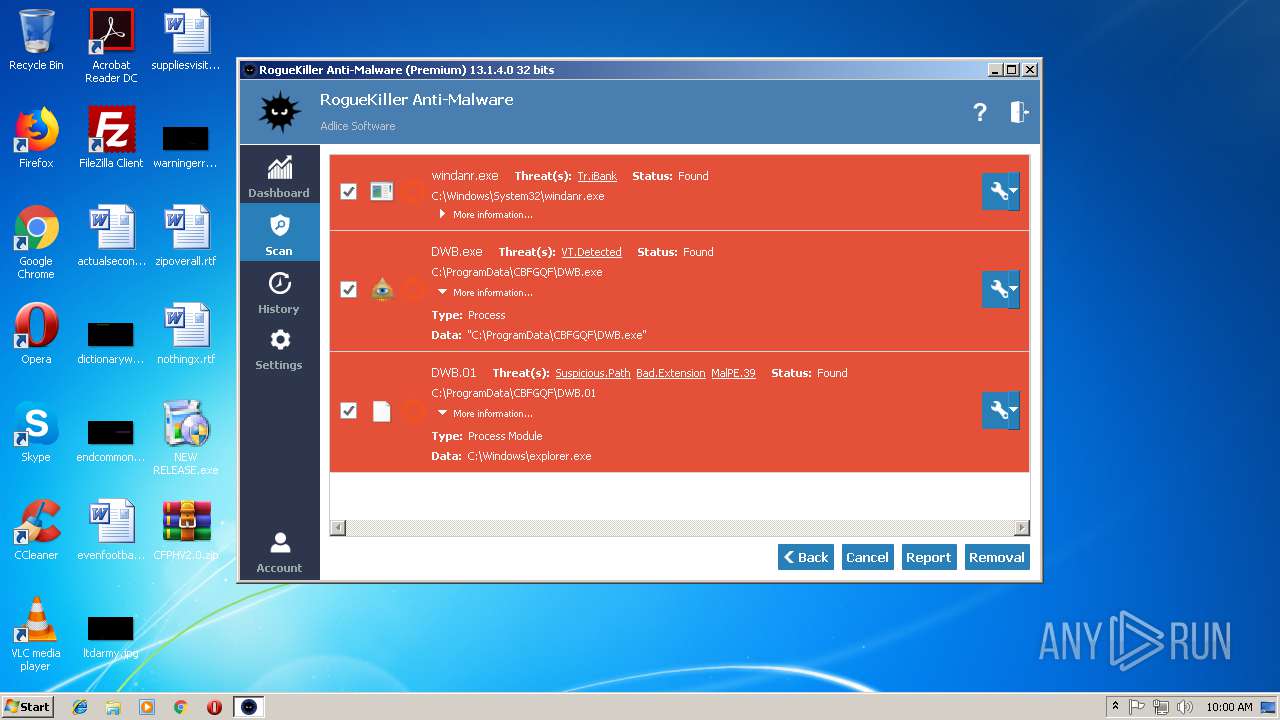
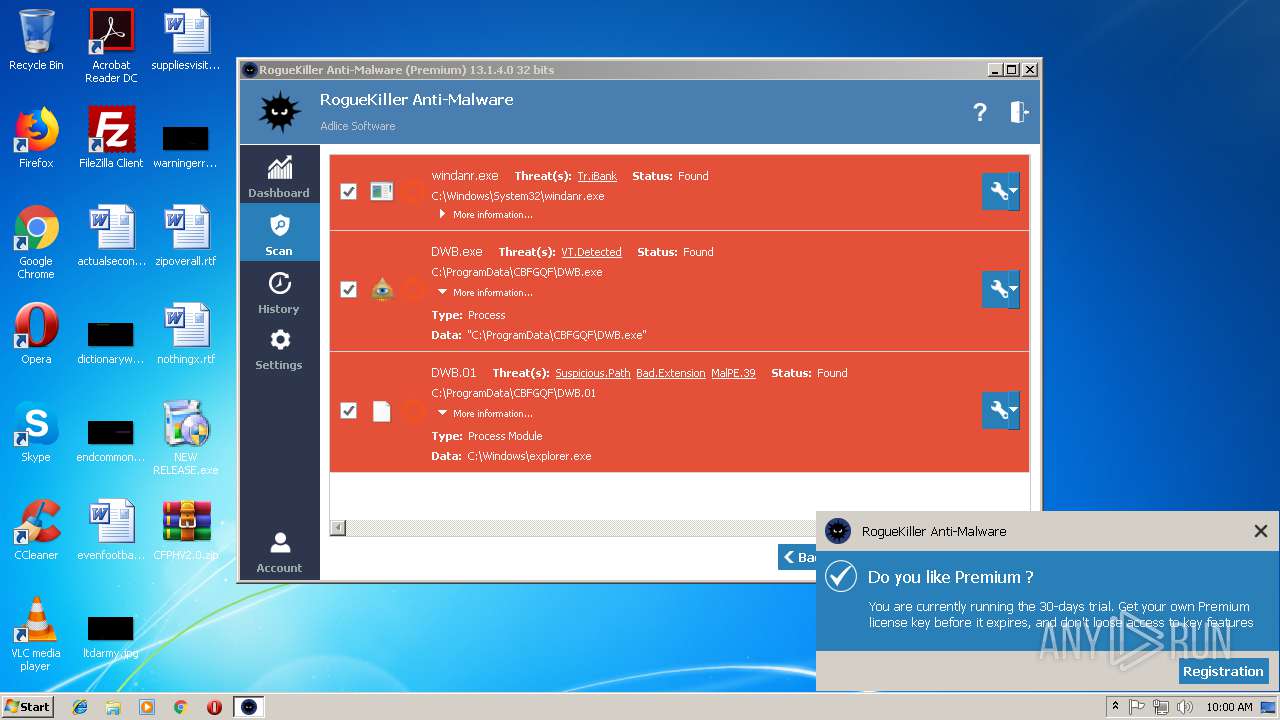
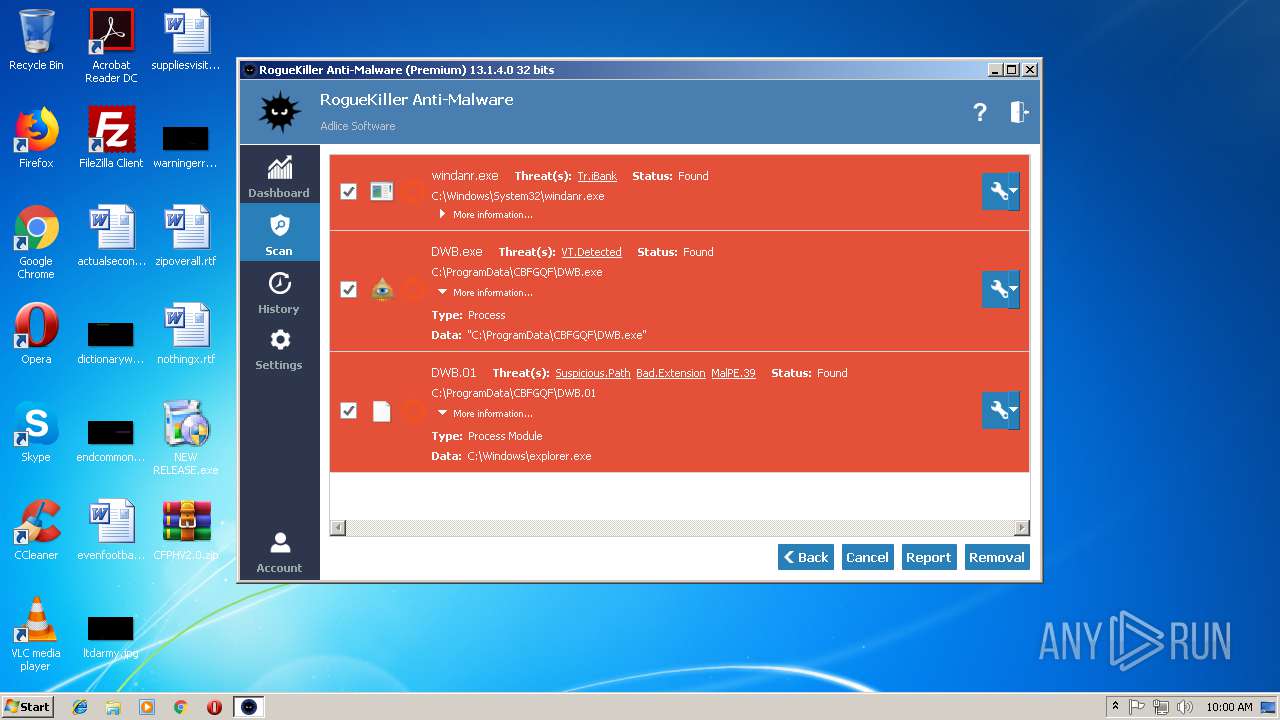
MALICIOUS
Loads dropped or rewritten executable
- WinRAR.exe (PID: 3632)
- DllHost.exe (PID: 3700)
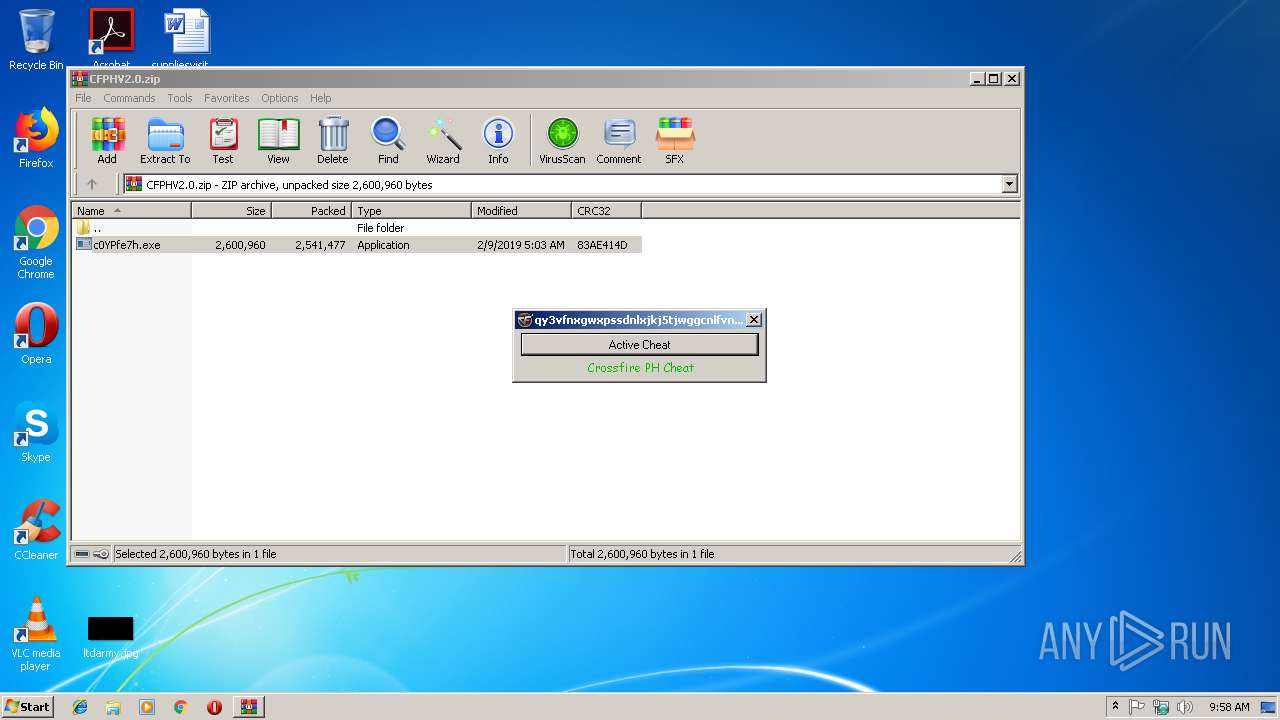
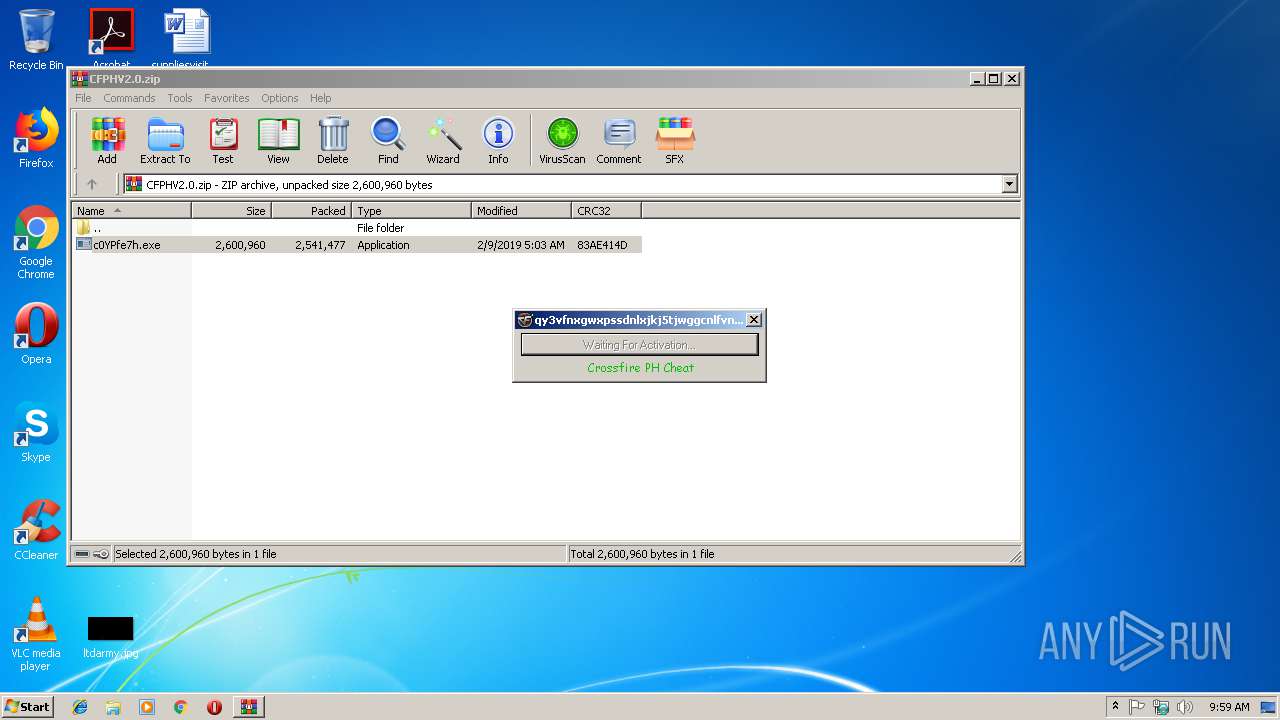
- c0YPfe7h.exe (PID: 3968)
- dwm.exe (PID: 1988)
- iexplore.exe (PID: 3084)
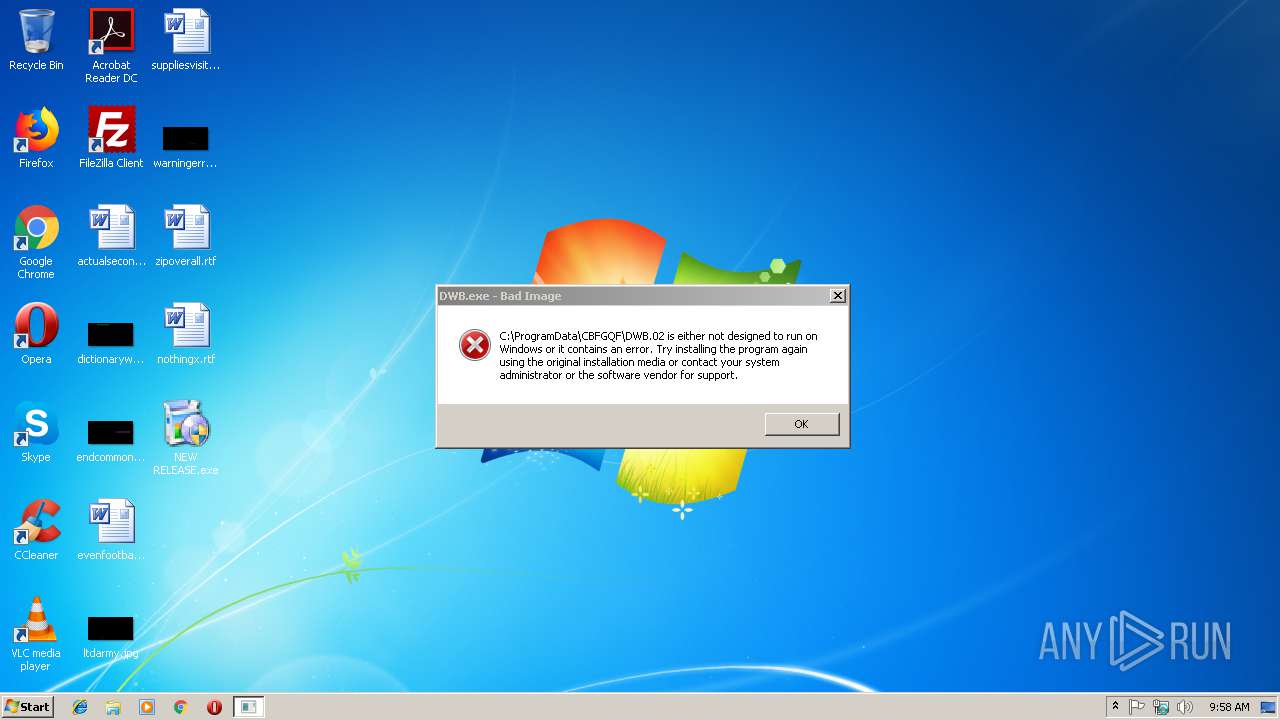
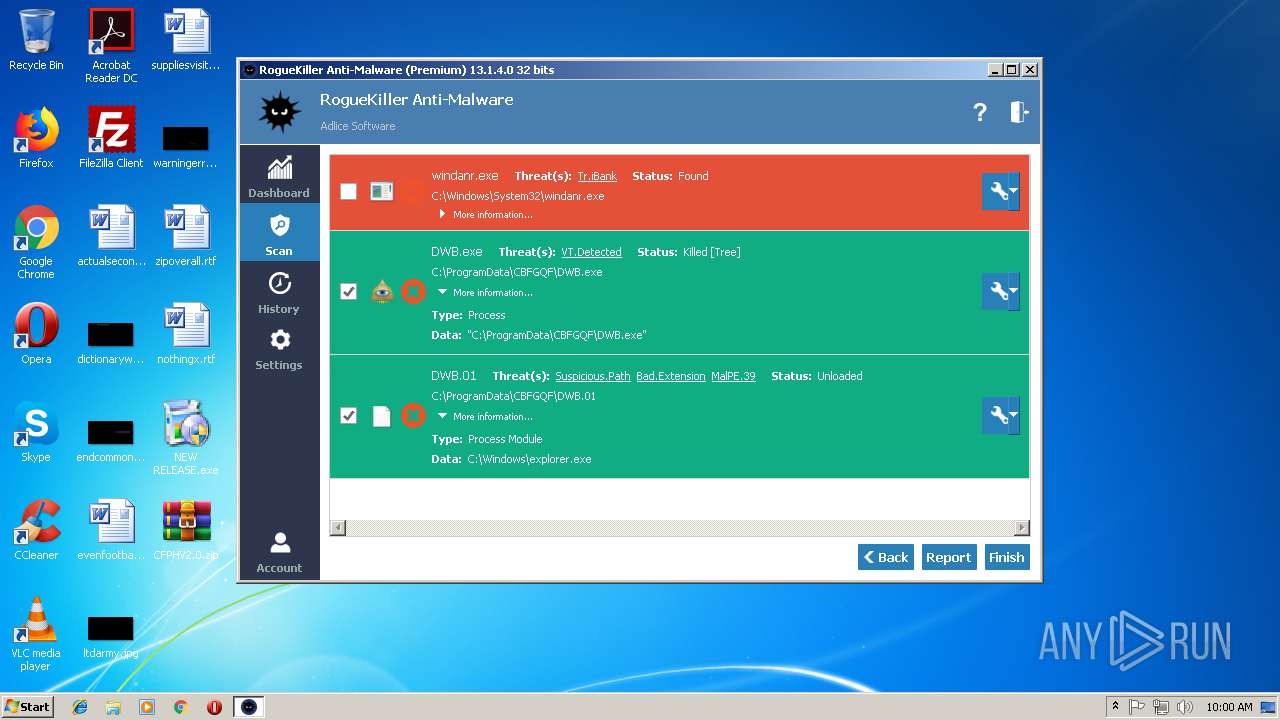
- DWB.exe (PID: 3312)
- iexplore.exe (PID: 3824)
- explorer.exe (PID: 284)
- chrome.exe (PID: 3036)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 2428)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3608)
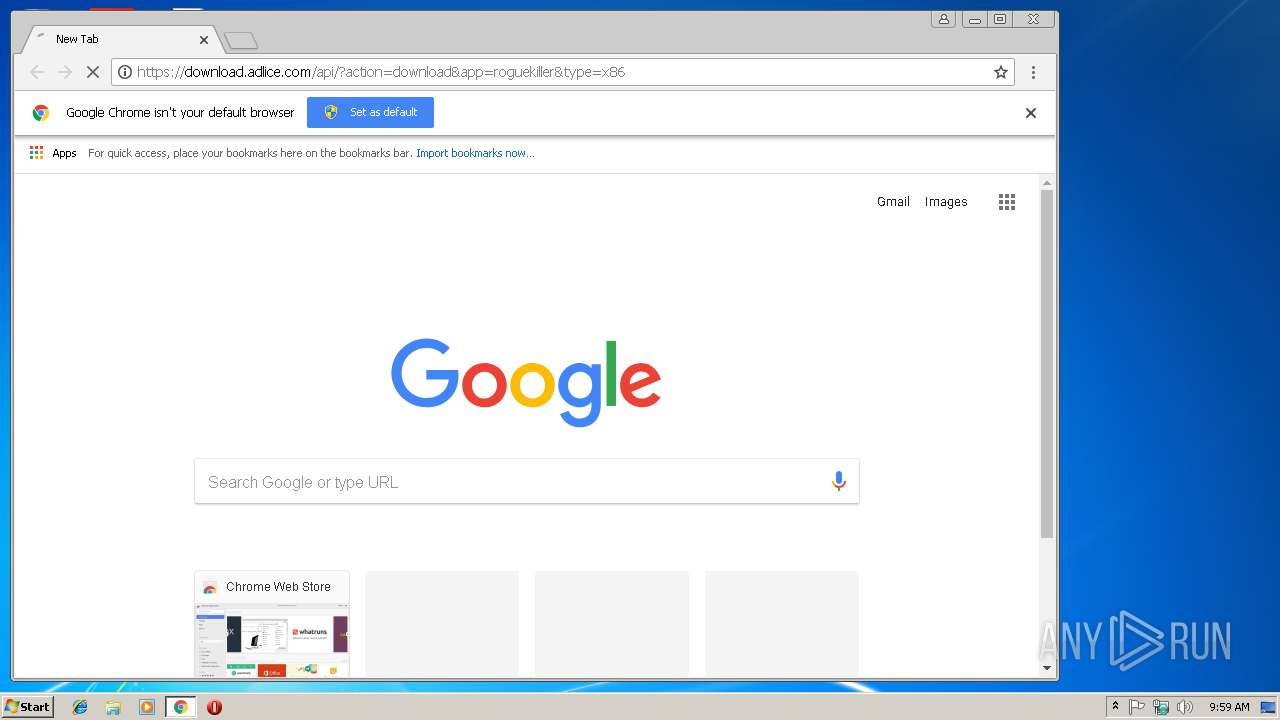
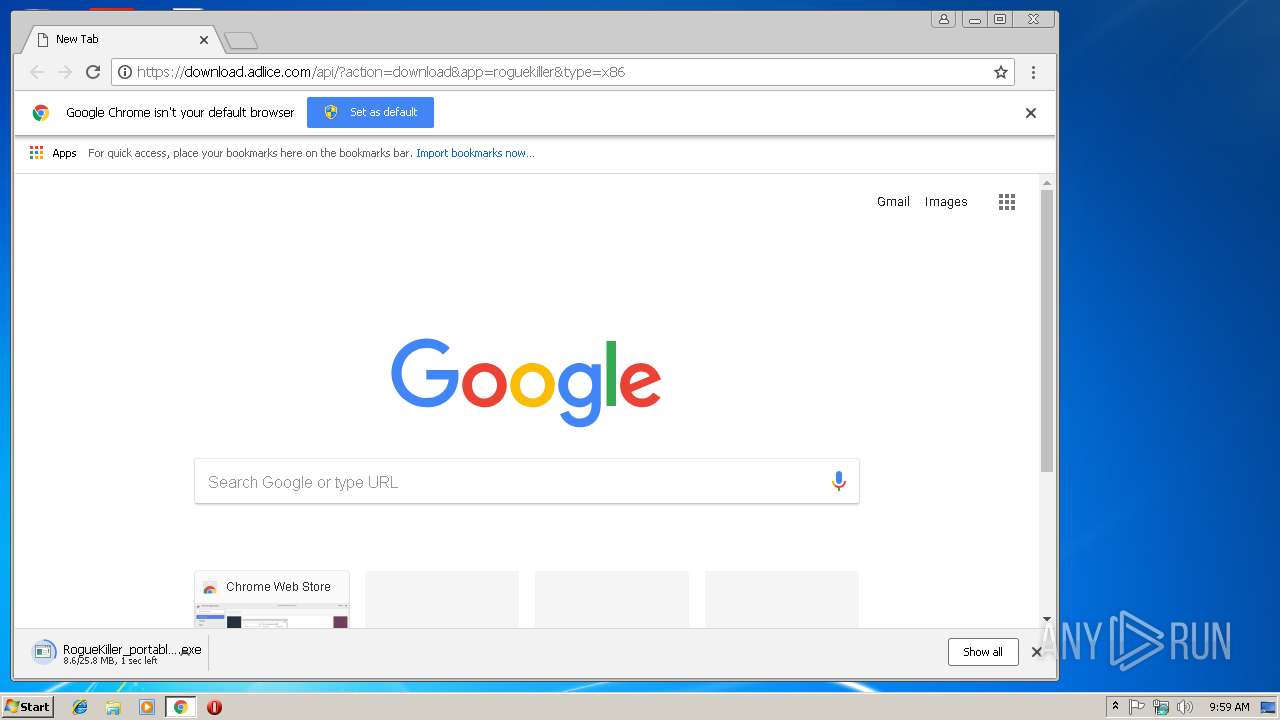
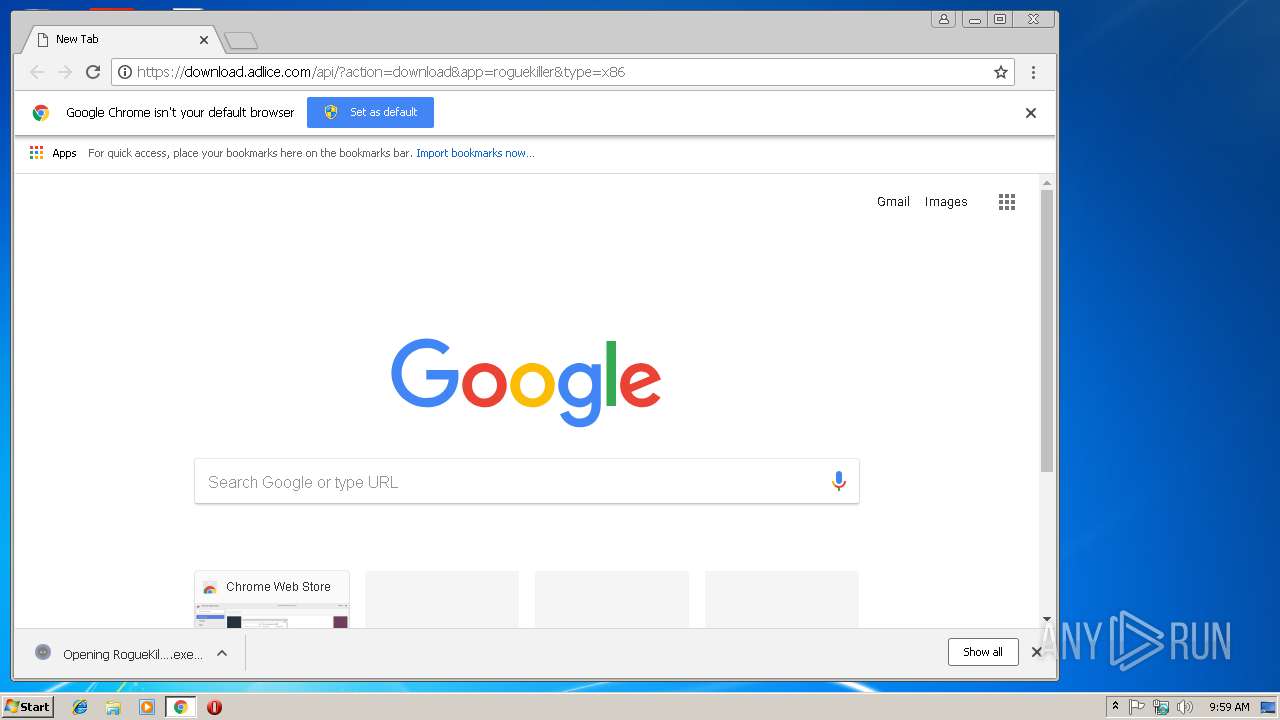
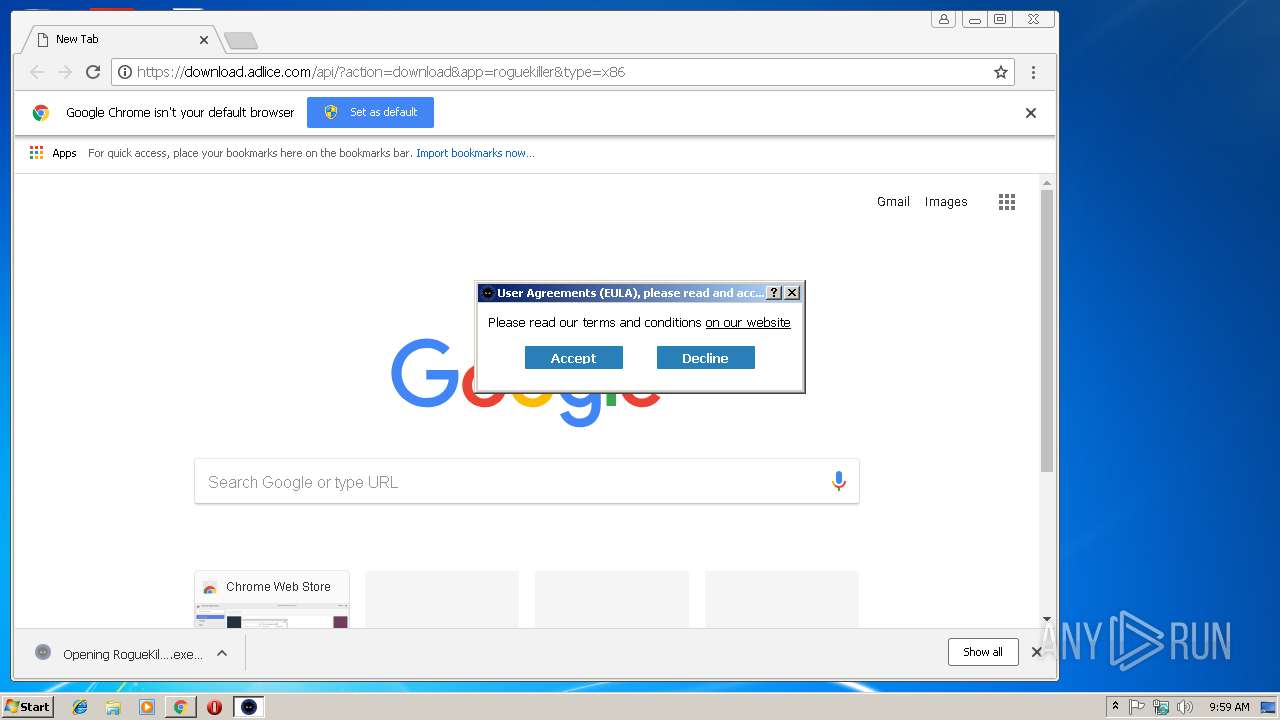
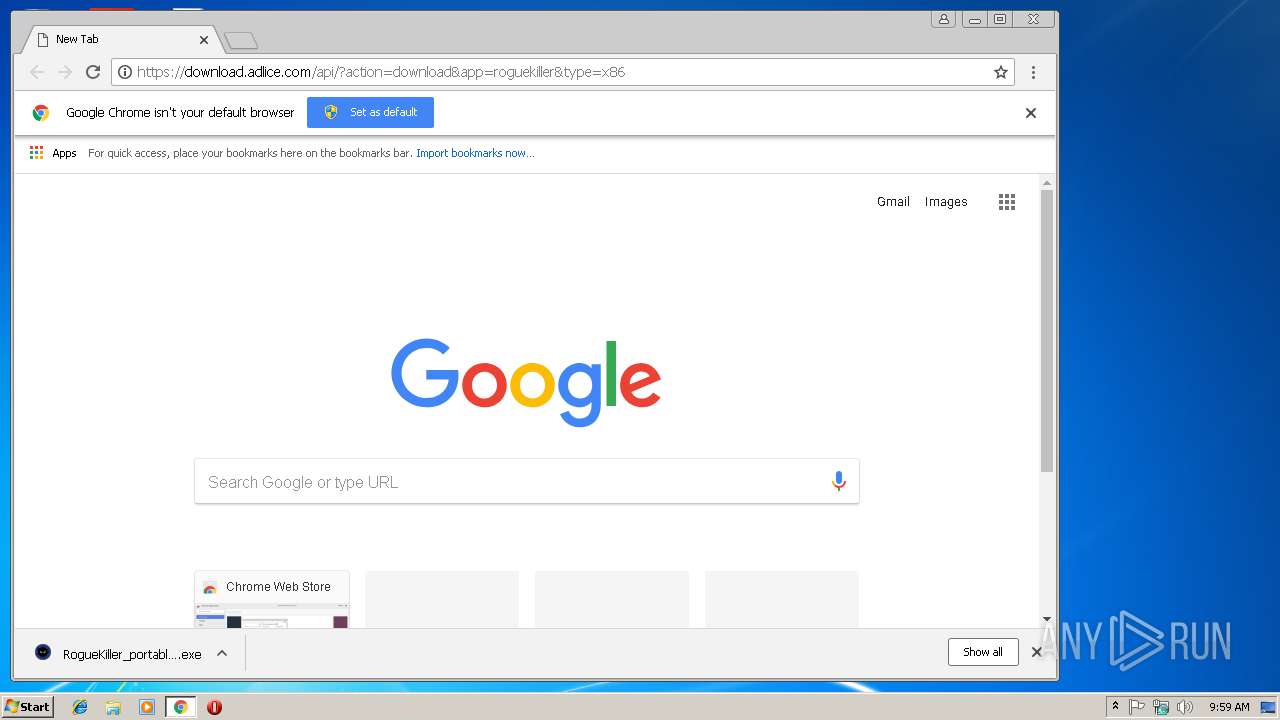
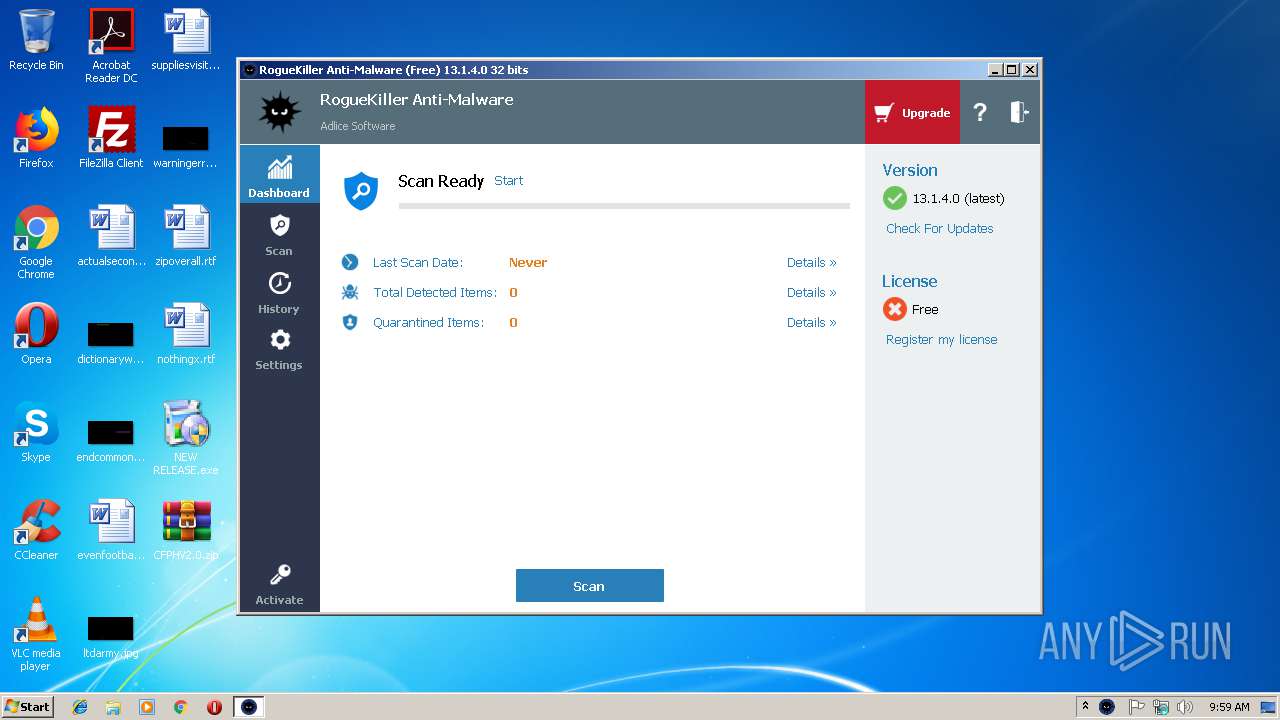
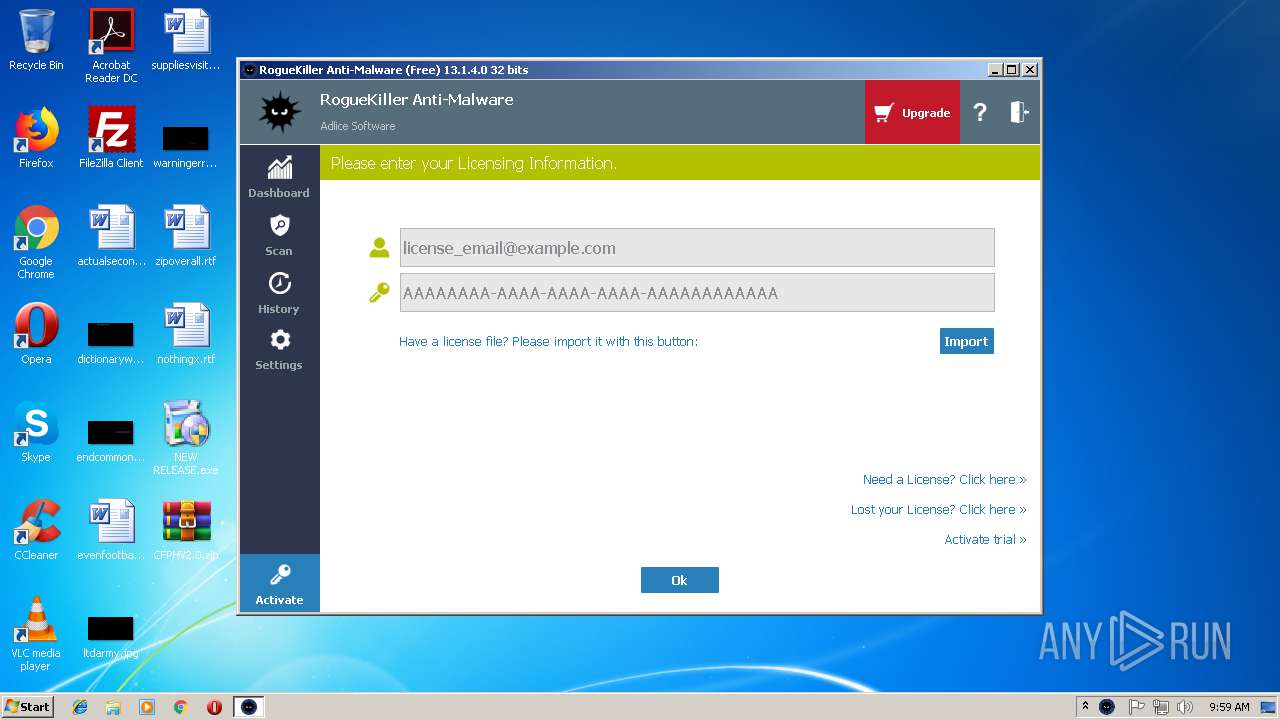
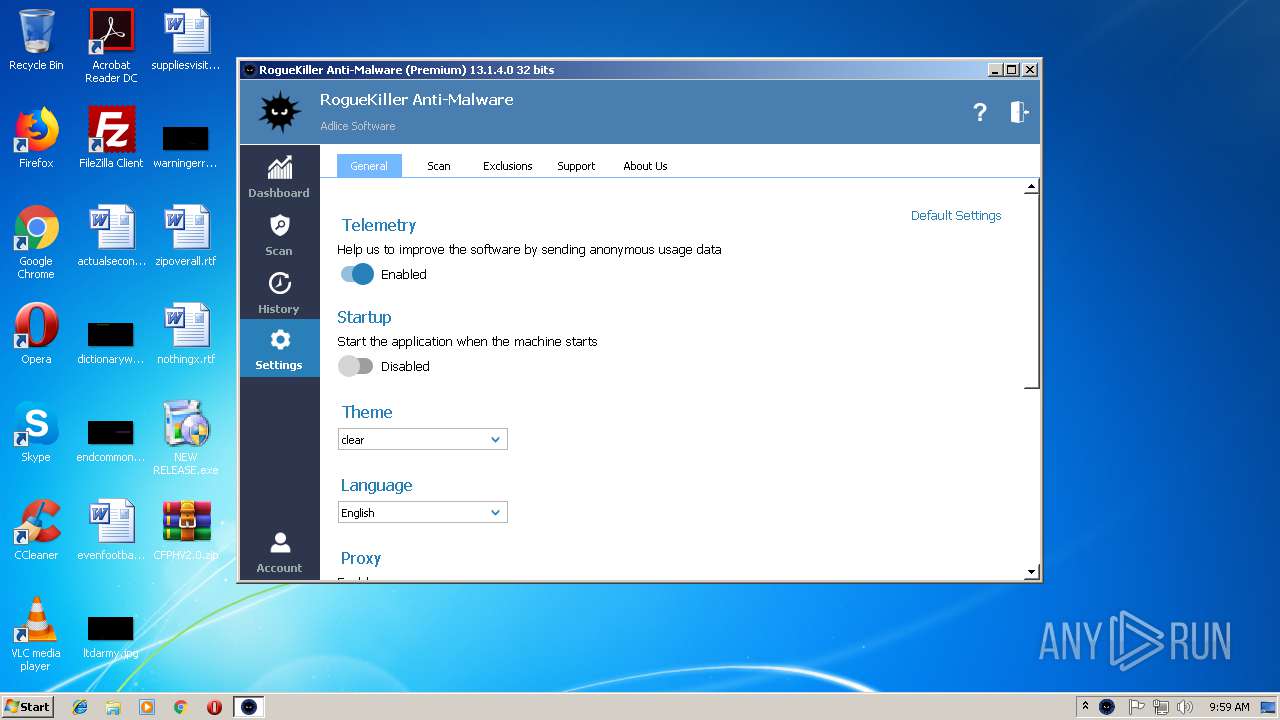
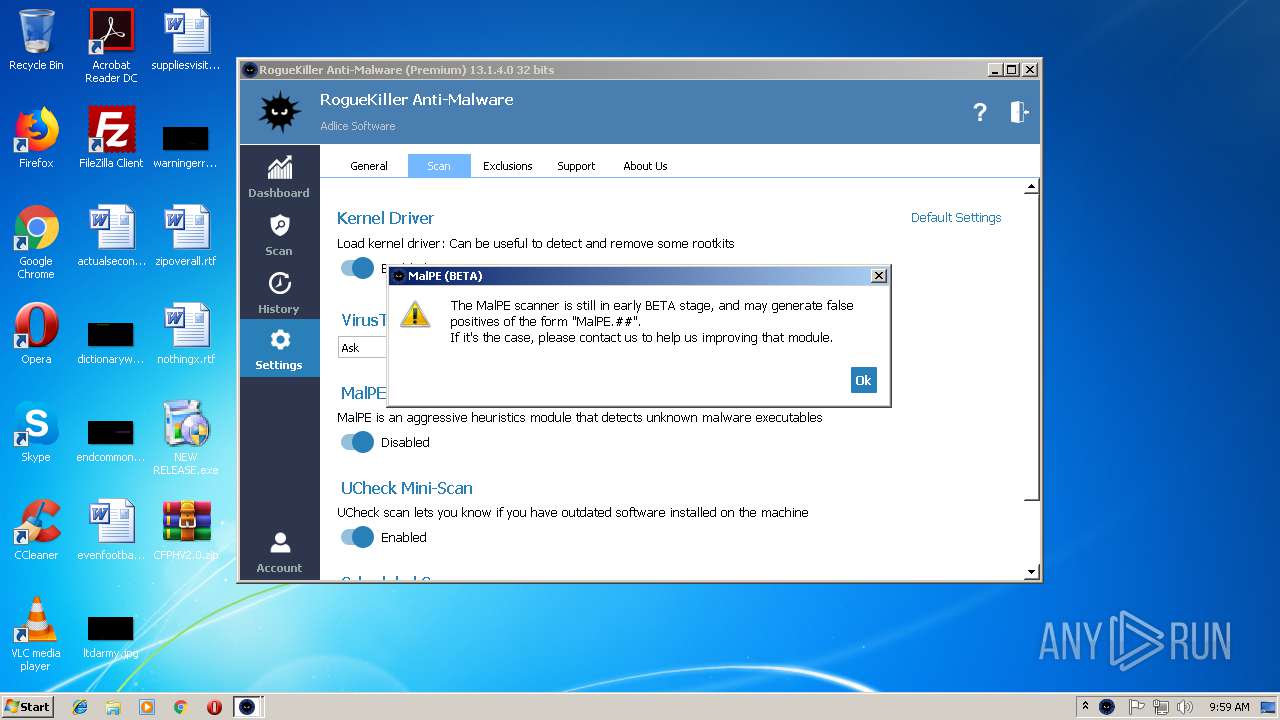
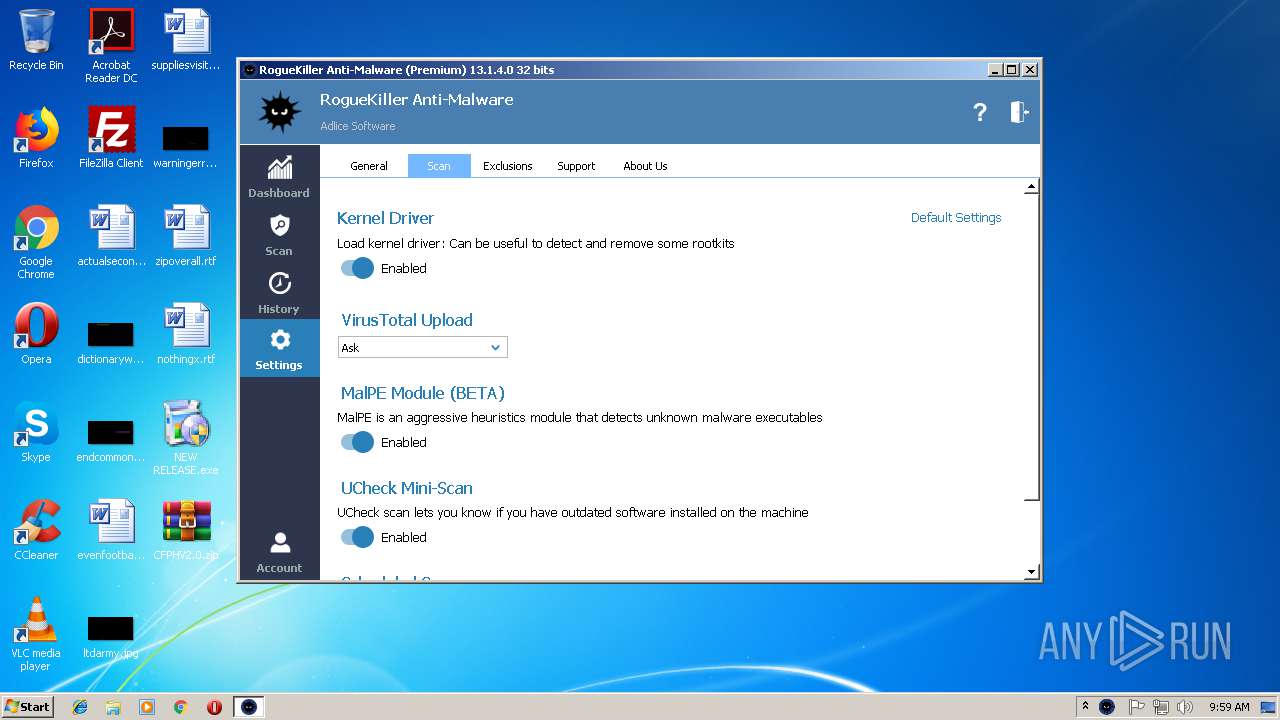
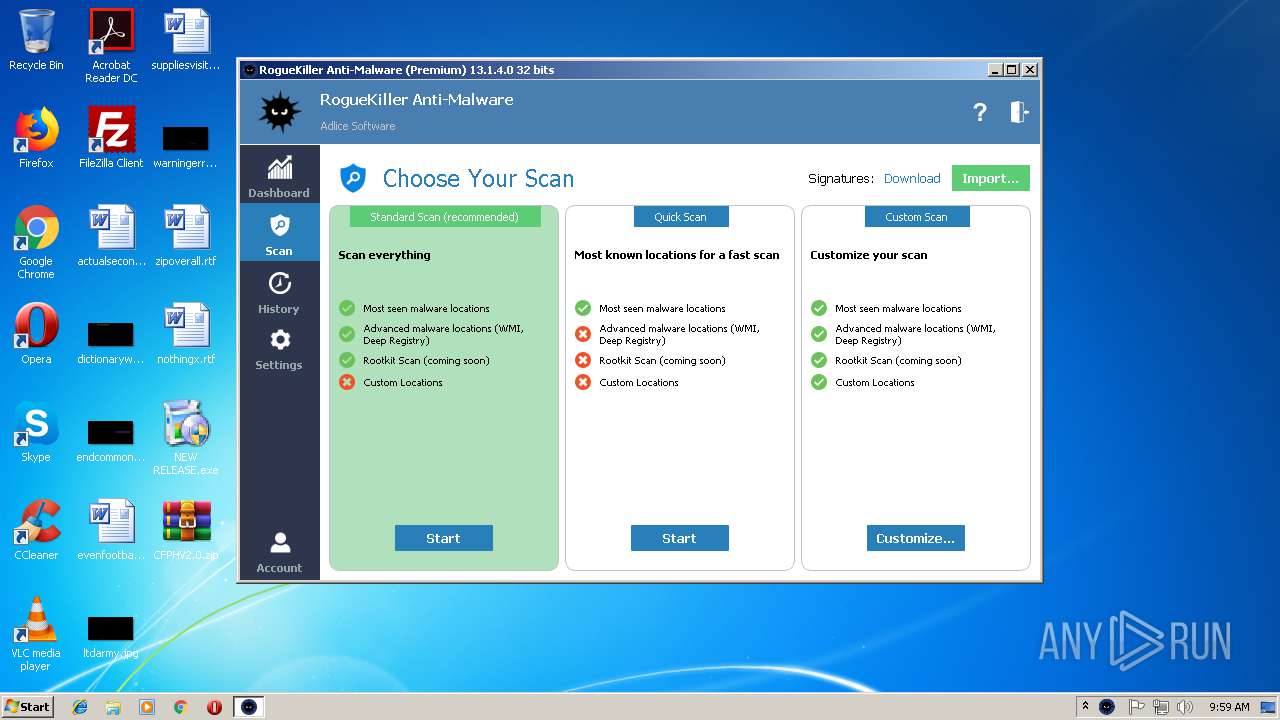
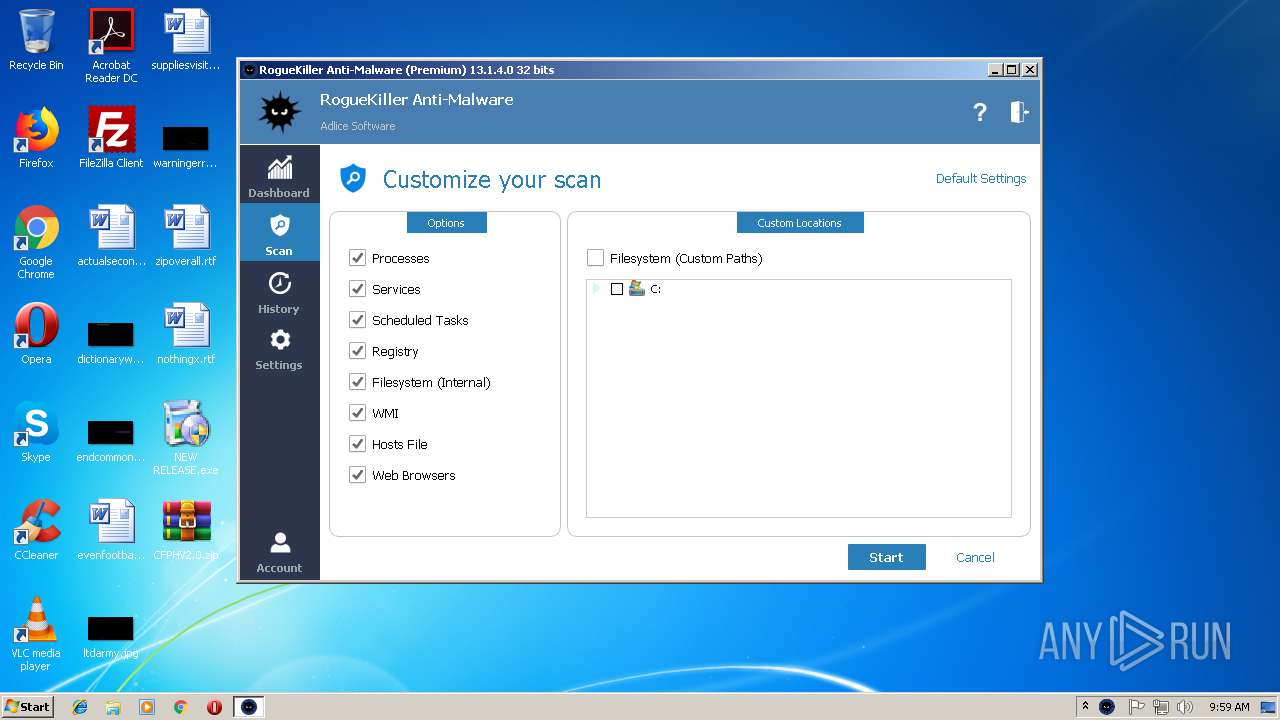
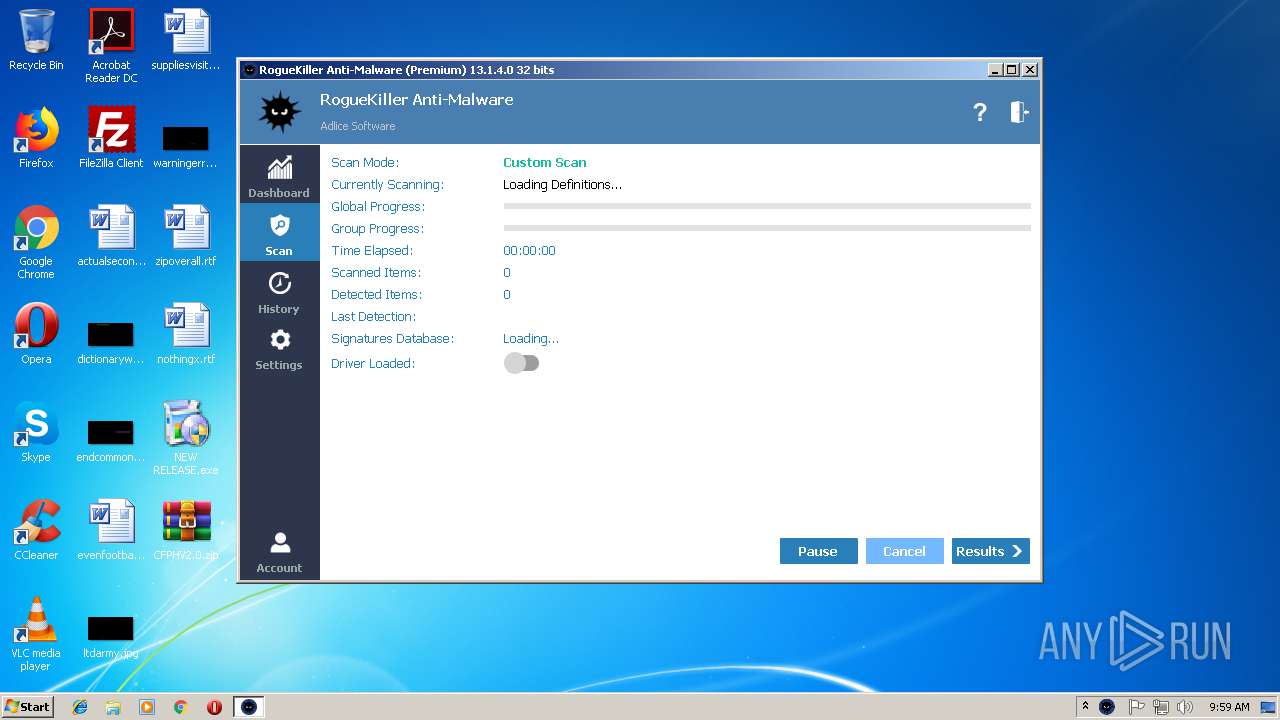
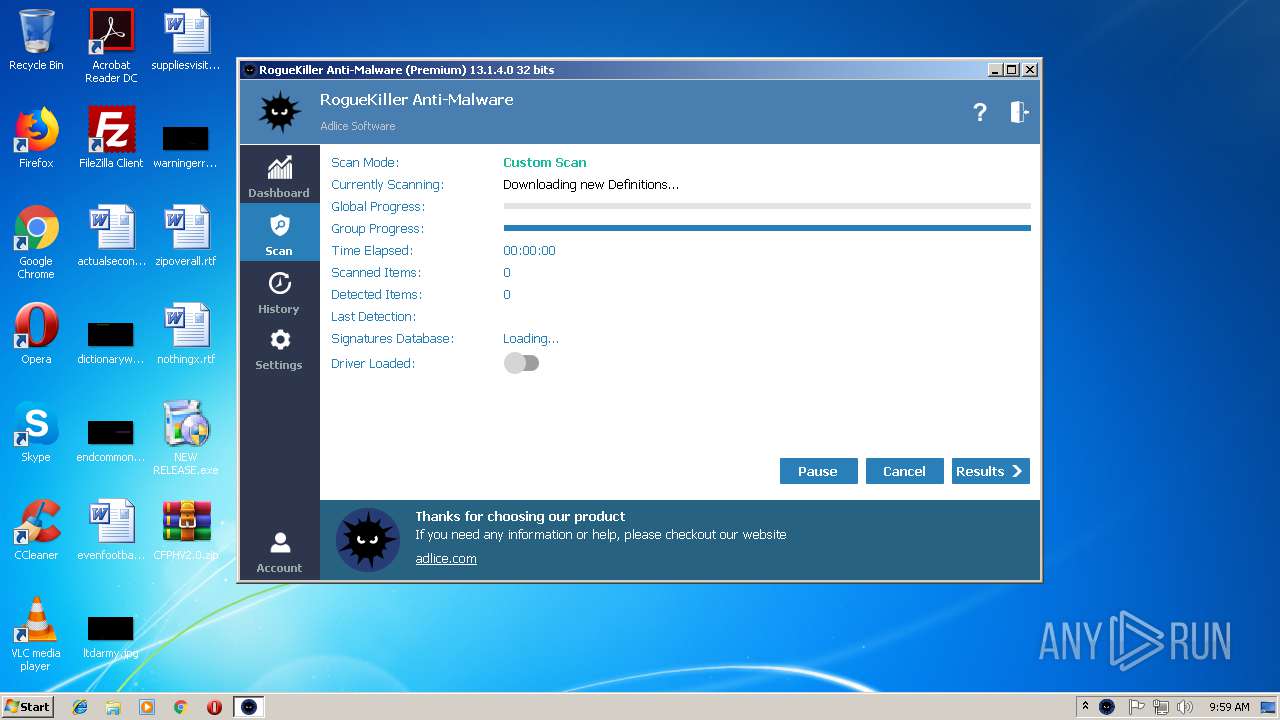
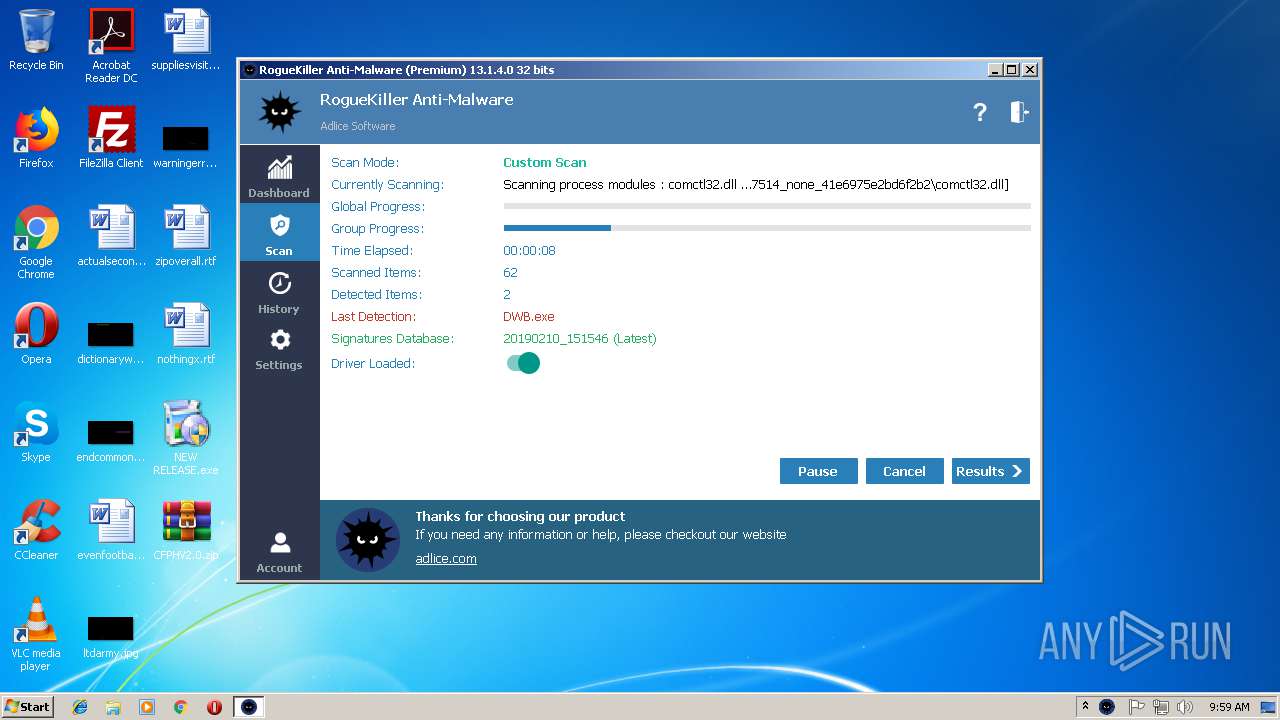
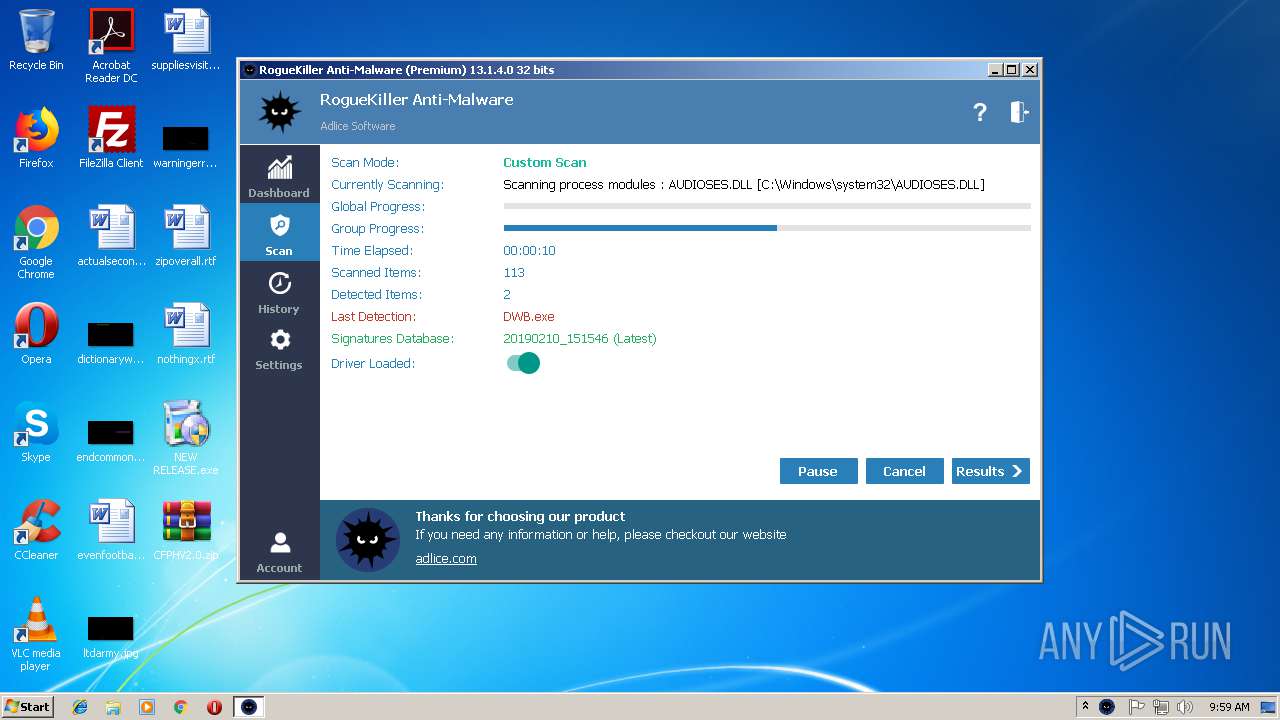
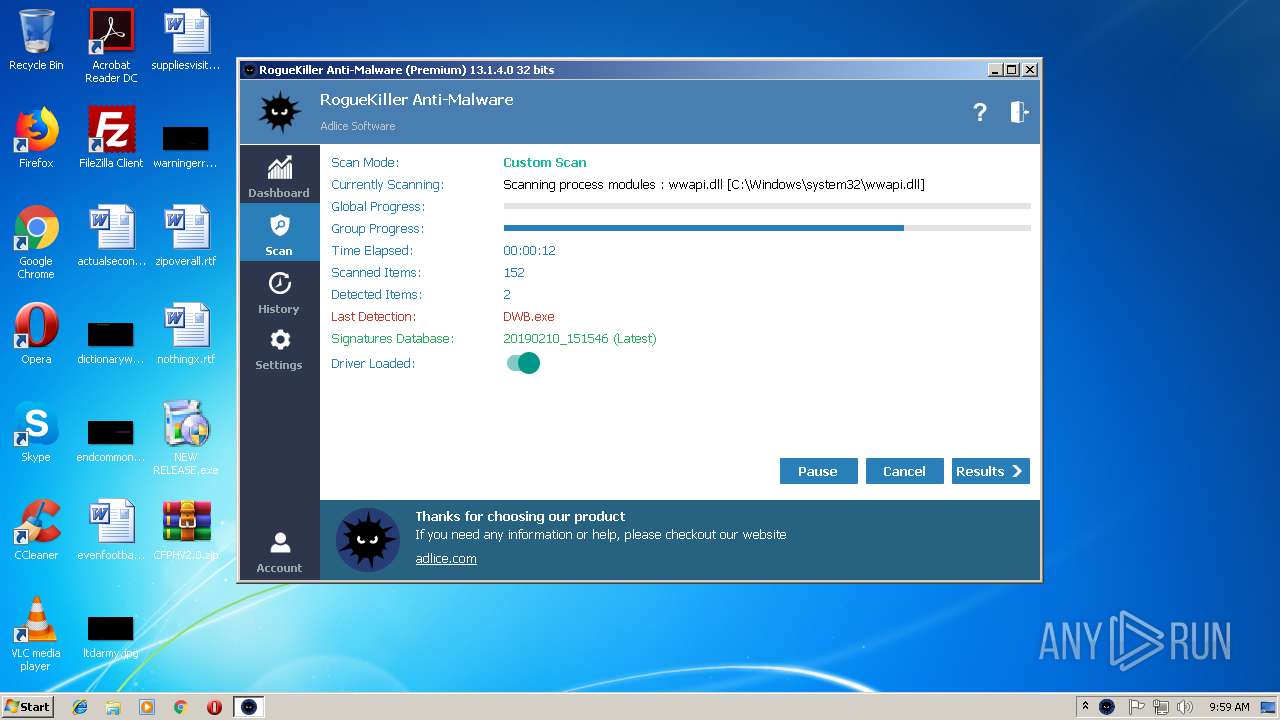
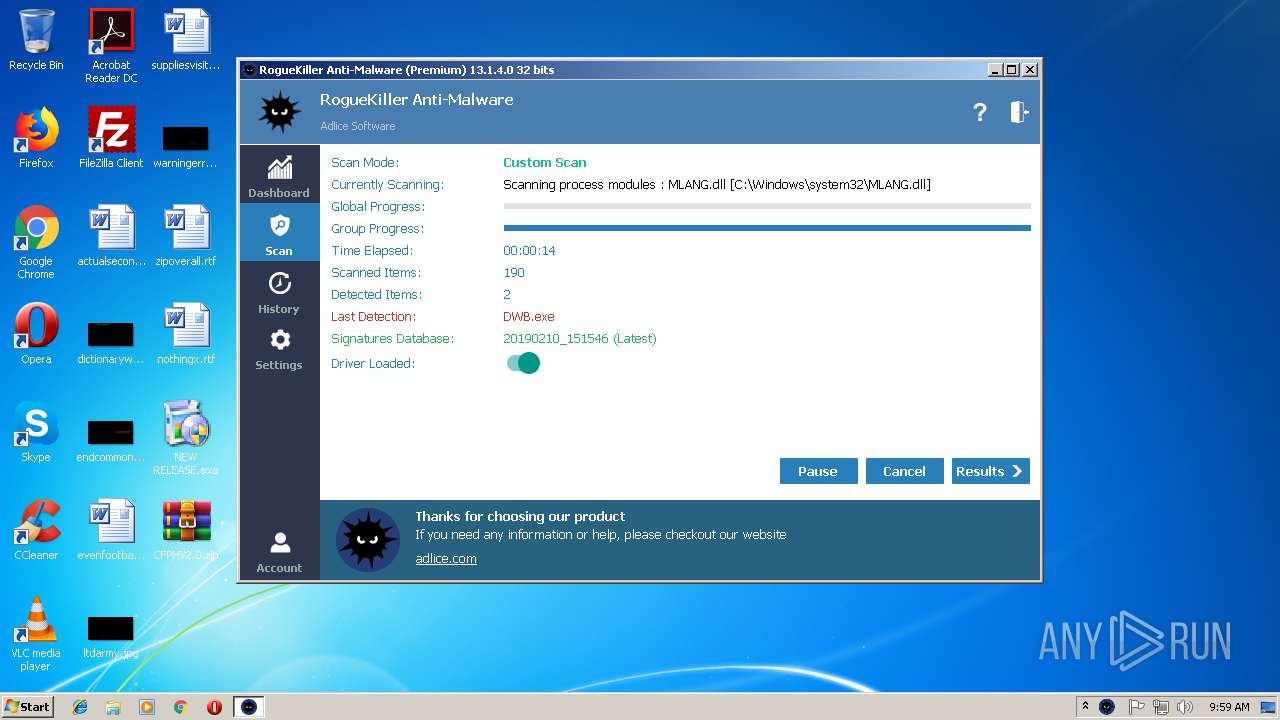
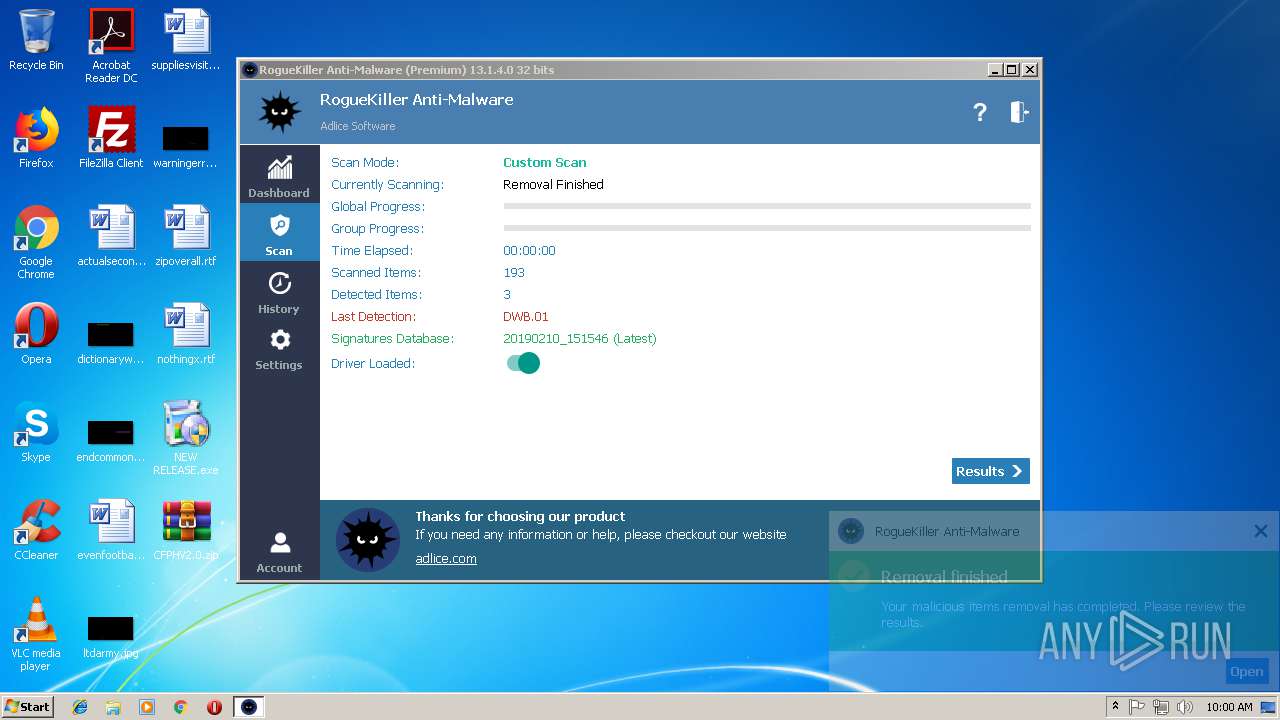
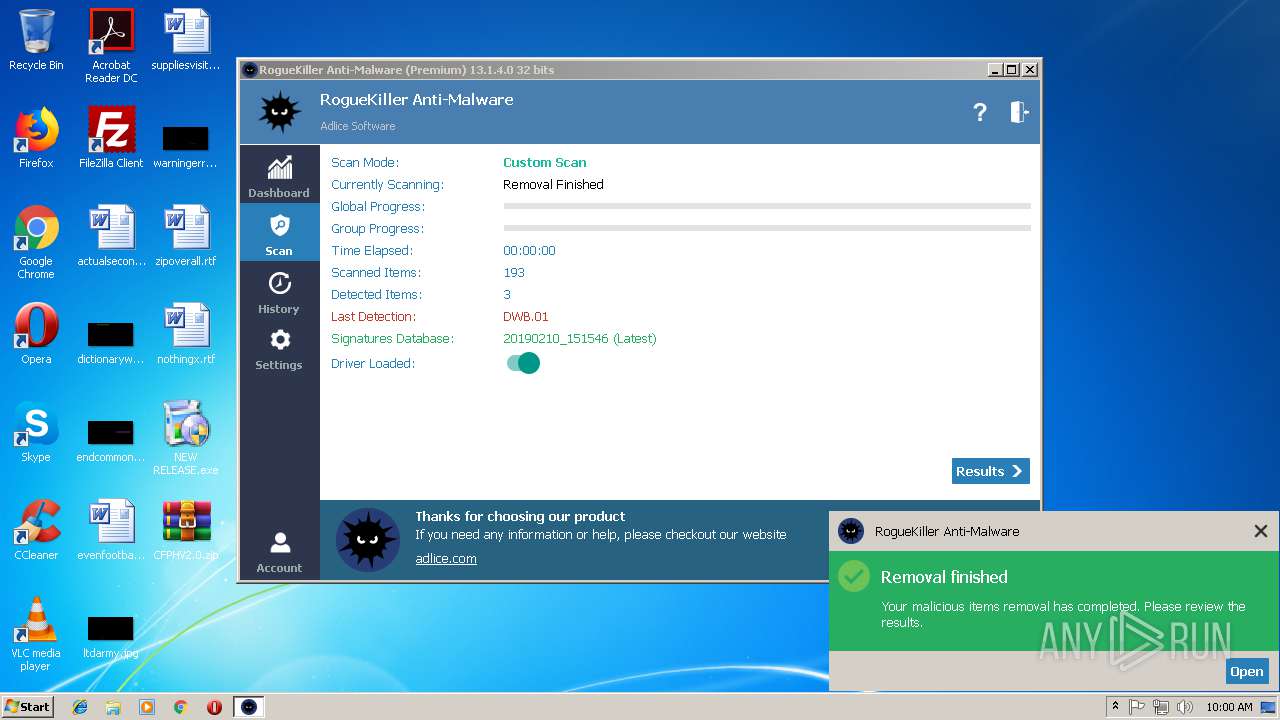
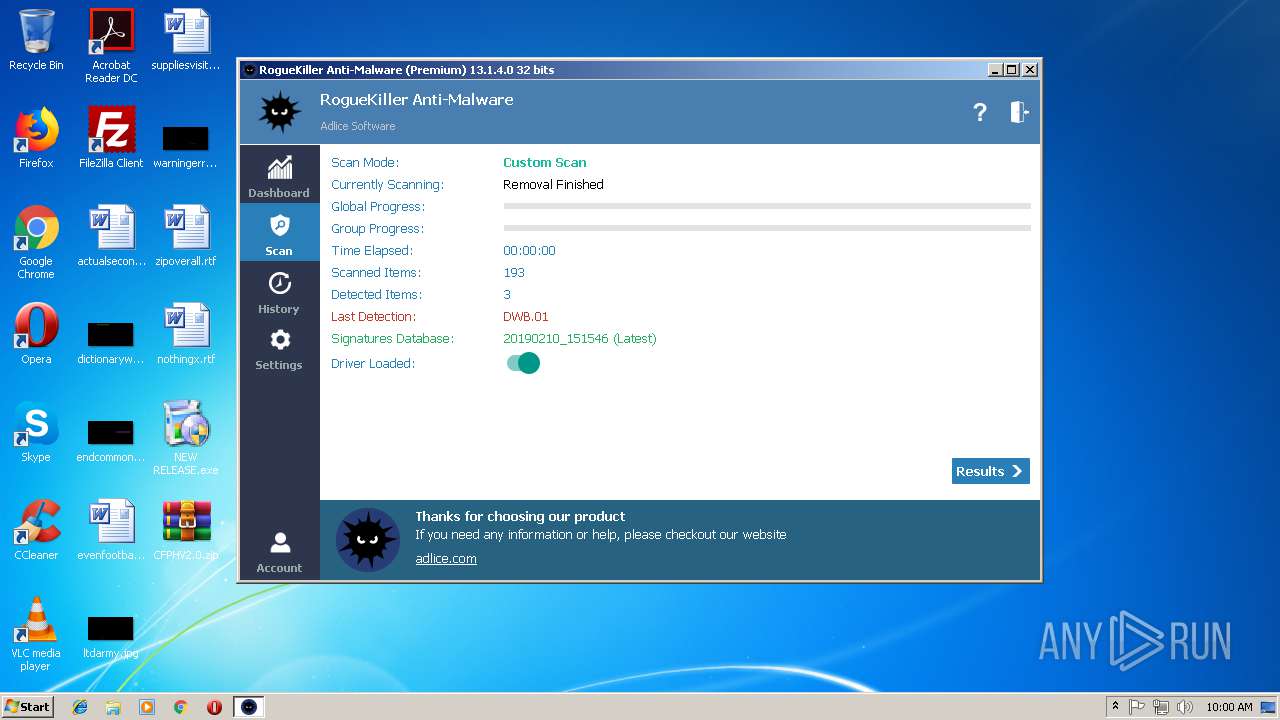
- RogueKiller_portable32.exe (PID: 1060)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 2792)
- chrome.exe (PID: 2968)
Application was dropped or rewritten from another process
- DWB.exe (PID: 3312)
- RogueKiller_portable32.exe (PID: 1060)
- RogueKiller_portable32.exe (PID: 3360)
- c0YPfe7h.exe (PID: 3968)
Changes the autorun value in the registry
- DWB.exe (PID: 3312)
Loads the Task Scheduler DLL interface
- RogueKiller_portable32.exe (PID: 1060)
Loads the Task Scheduler COM API
- RogueKiller_portable32.exe (PID: 1060)
SUSPICIOUS
Creates files in the program directory
- NEW RELEASE.exe (PID: 2308)
- DWB.exe (PID: 3312)
- RogueKiller_portable32.exe (PID: 1060)
Executable content was dropped or overwritten
- NEW RELEASE.exe (PID: 2308)
- WinRAR.exe (PID: 3632)
- chrome.exe (PID: 1244)
- RogueKiller_portable32.exe (PID: 1060)
Creates files in the user directory
- explorer.exe (PID: 284)
Reads Internet Cache Settings
- explorer.exe (PID: 284)
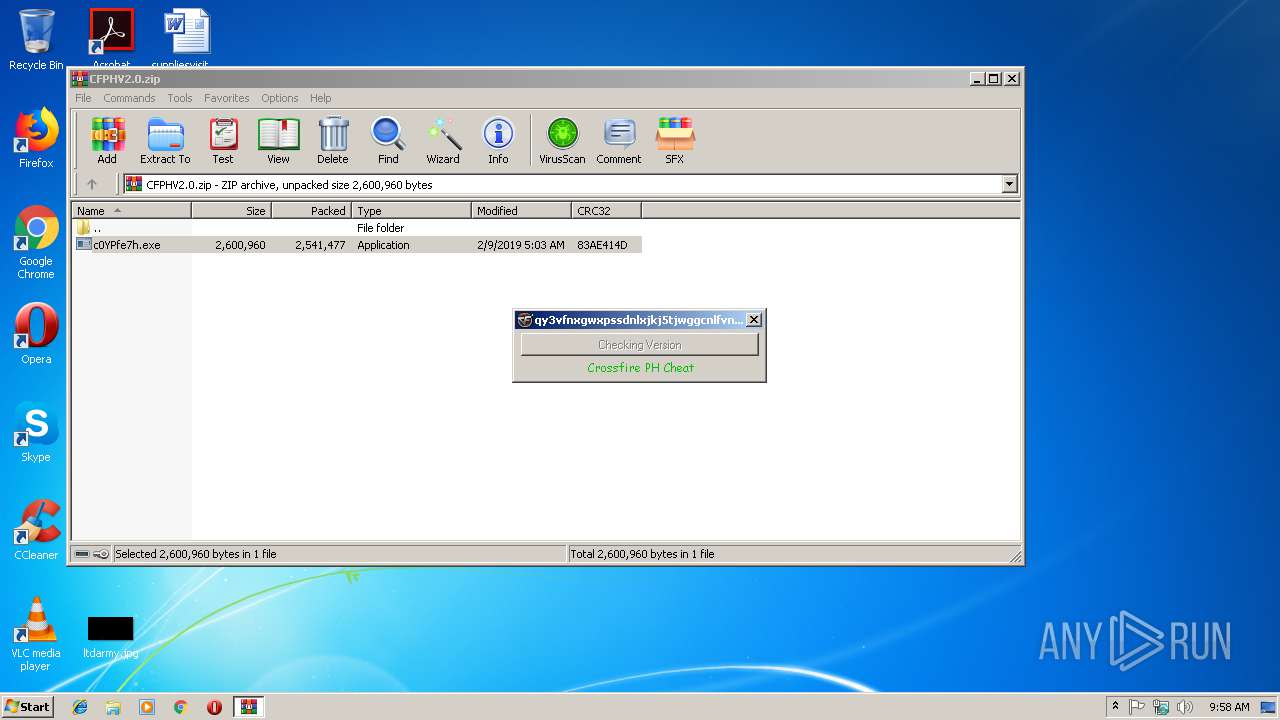
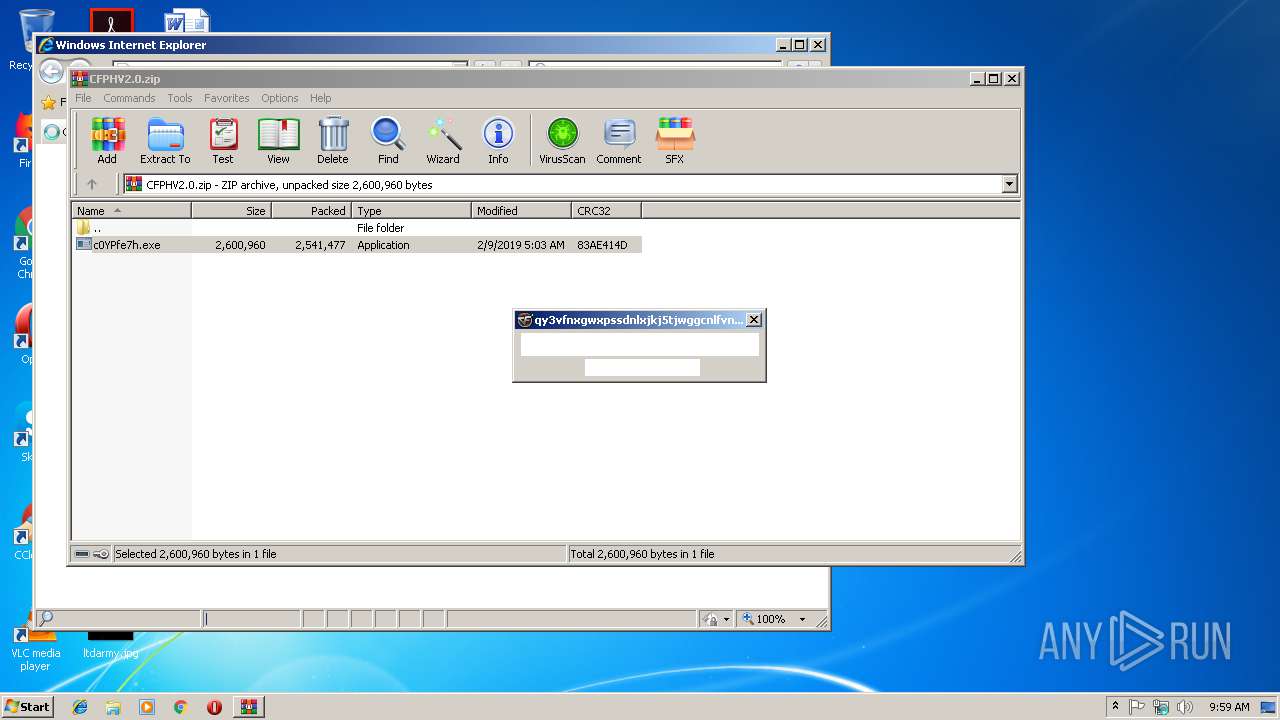
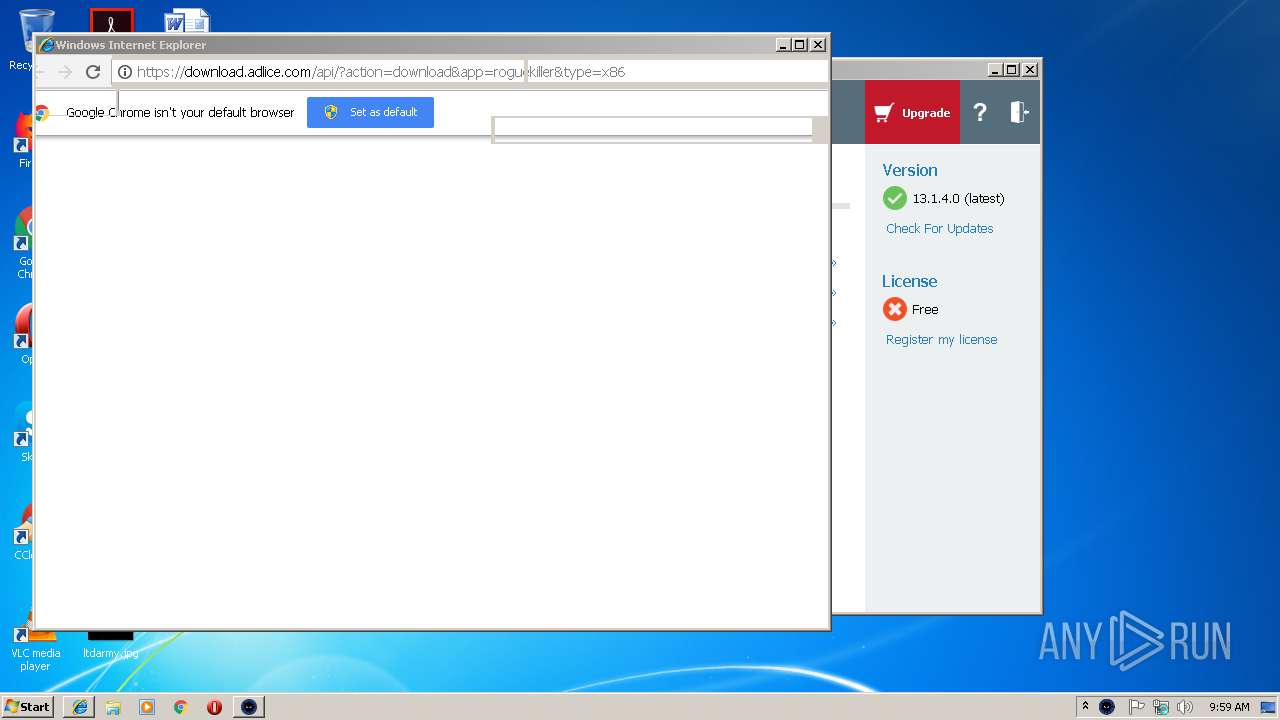
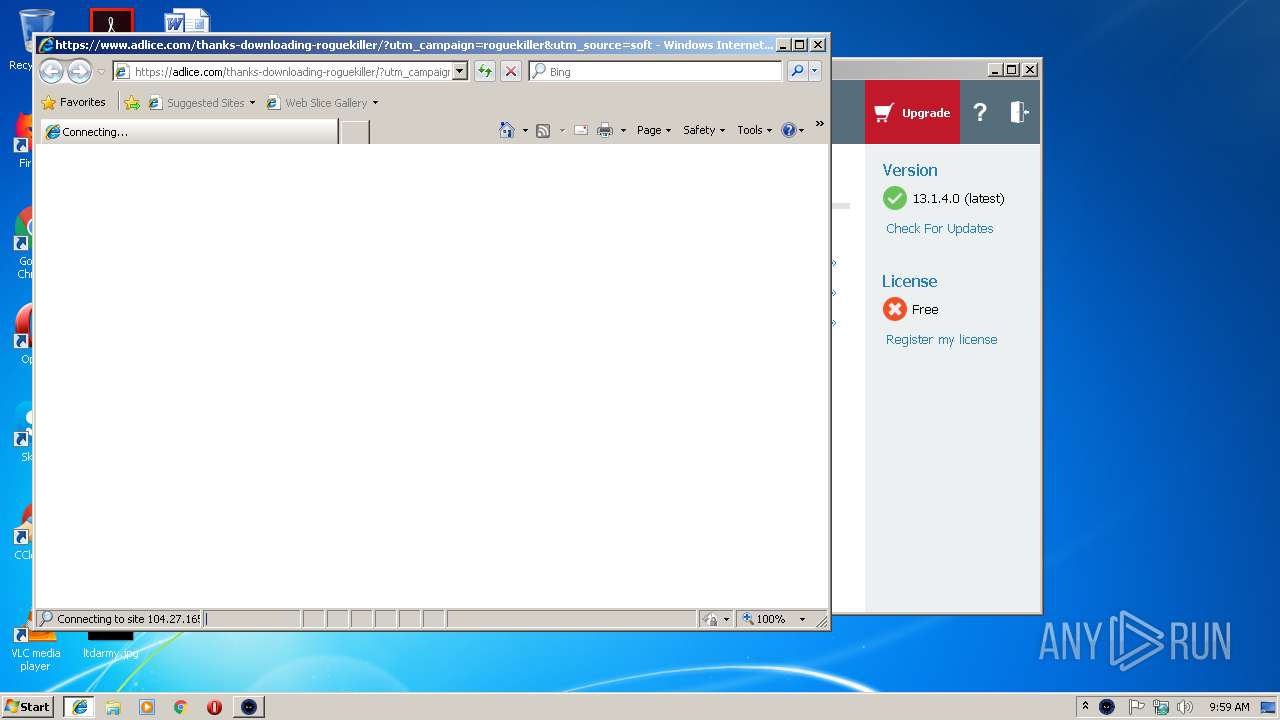
Starts Internet Explorer
- c0YPfe7h.exe (PID: 3968)
- RogueKiller_portable32.exe (PID: 1060)
Low-level read access rights to disk partition
- RogueKiller_portable32.exe (PID: 1060)
Creates files in the Windows directory
- RogueKiller_portable32.exe (PID: 1060)
Creates files in the driver directory
- RogueKiller_portable32.exe (PID: 1060)
Creates or modifies windows services
- RogueKiller_portable32.exe (PID: 1060)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3112)
Reads internet explorer settings
- iexplore.exe (PID: 3824)
Changes settings of System certificates
- iexplore.exe (PID: 3824)
Creates files in the user directory
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 2792)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3824)
Application launched itself
- chrome.exe (PID: 1244)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3112)
Reads Internet Cache Settings
- iexplore.exe (PID: 3824)
- chrome.exe (PID: 1244)
Reads settings of System Certificates
- chrome.exe (PID: 1244)
- RogueKiller_portable32.exe (PID: 1060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:05 14:55:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 39936 |
| InitializedDataSize: | 5122560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x54c2 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2016 13:55:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2016 13:55:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00009B64 | 0x00009C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.3934 |
.rdata | 0x0000B000 | 0x00002340 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.48747 |
.data | 0x0000E000 | 0x00001F60 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29264 |
.rsrc | 0x00010000 | 0x004DE3C0 | 0x004DE400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.76021 |
.reloc | 0x004EF000 | 0x0000127E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.61866 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19546 | 660 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.26359 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 6.11058 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.29176 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 3.45943 | 11 | Latin 1 / Western European | UNKNOWN | RT_STRING |
102 | 3.93633 | 1464 | Latin 1 / Western European | UNKNOWN | RT_STRING |
103 | 7.30892 | 486 | Latin 1 / Western European | UNKNOWN | RT_STRING |
104 | 7.47736 | 472 | Latin 1 / Western European | UNKNOWN | RT_STRING |
105 | 7.47931 | 441 | Latin 1 / Western European | UNKNOWN | RT_STRING |
106 | 7.28909 | 398 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
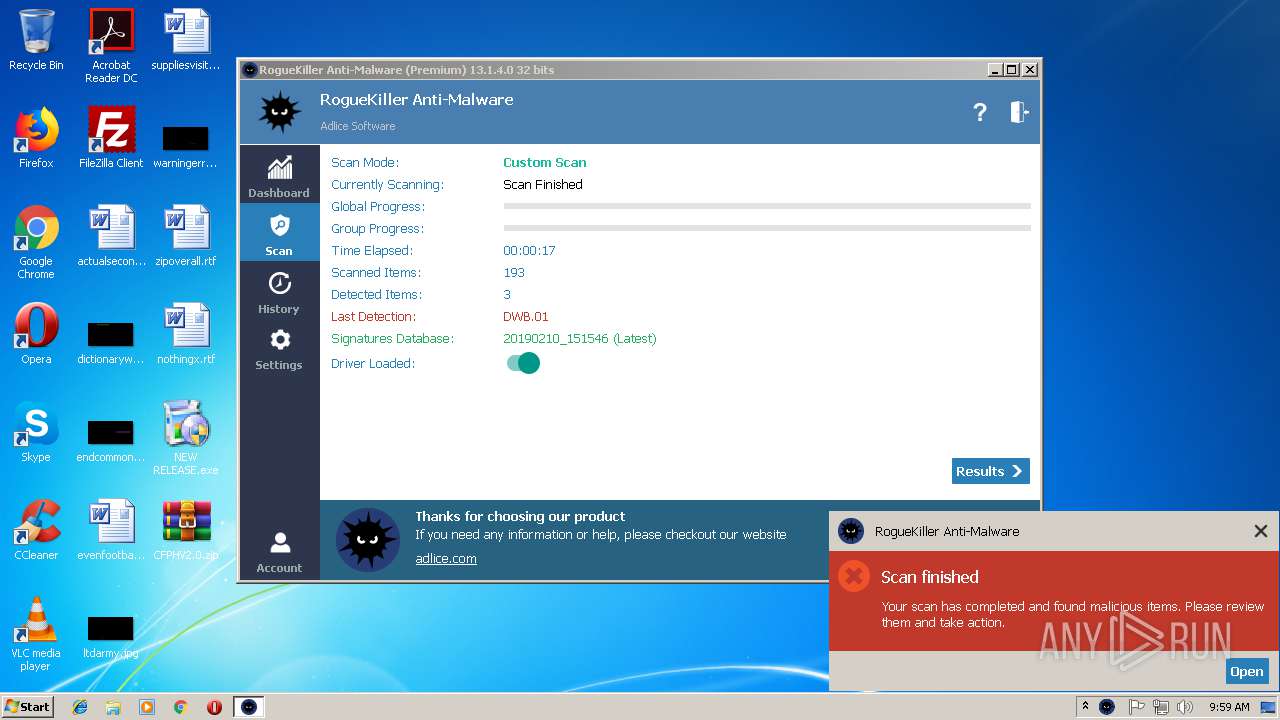
Total processes
62
Monitored processes
26
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\Downloads\RogueKiller_portable32.exe" | C:\Users\admin\Downloads\RogueKiller_portable32.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1988 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,15617248576162430067,13383672693656805594,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=293D02D81442FFA9D3973630CF634A88 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=293D02D81442FFA9D3973630CF634A88 --renderer-client-id=8 --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\Desktop\NEW RELEASE.exe" | C:\Users\admin\Desktop\NEW RELEASE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3804 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,15617248576162430067,13383672693656805594,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B8C974B3524AB8C2A90951A6B68DE94E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B8C974B3524AB8C2A90951A6B68DE94E --renderer-client-id=6 --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3112 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6fef00b0,0x6fef00c0,0x6fef00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
4 494
Read events
4 143
Write events
343
Delete events
8
Modification events
| (PID) Process: | (2308) NEW RELEASE.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2308) NEW RELEASE.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) DWB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | DWB Start |
Value: C:\ProgramData\CBFGQF\DWB.exe | |||
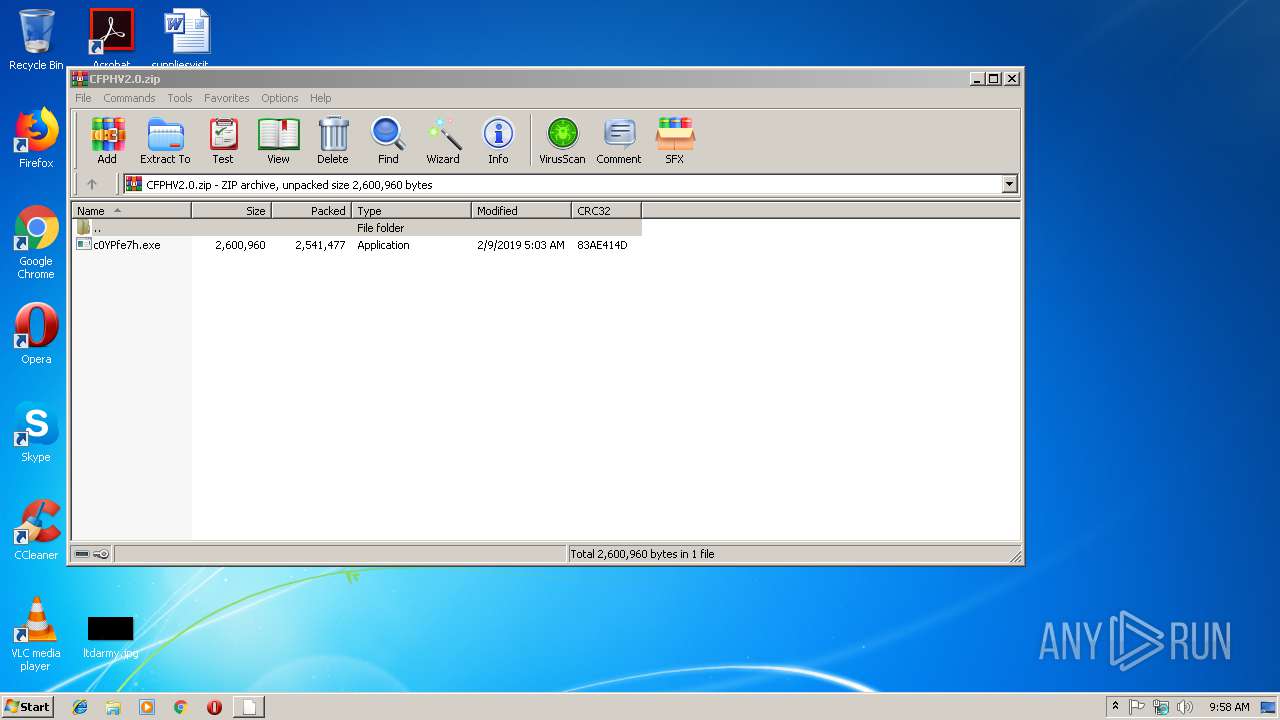
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
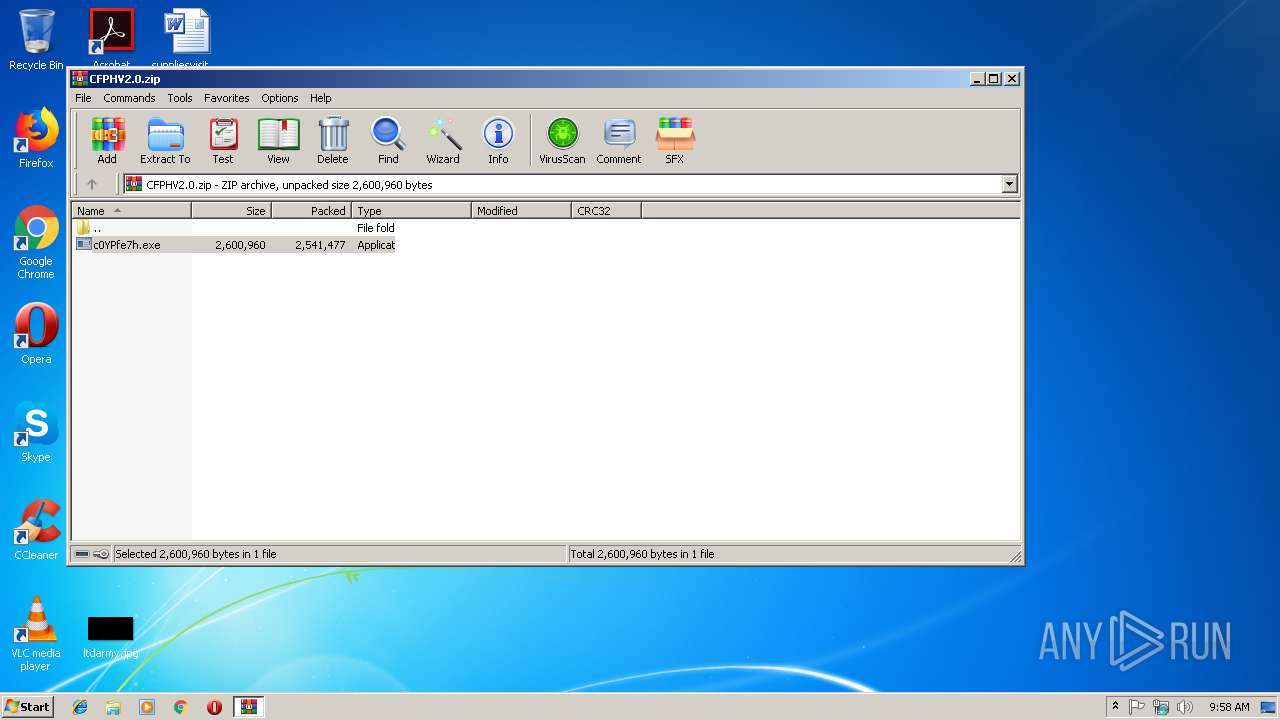
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\CFPHV2.0.zip | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
6
Suspicious files
143
Text files
125
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | NEW RELEASE.exe | C:\ProgramData\CBFGQF\DWB.02 | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8B84FFFD16108643.TMP | — | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CFPHV2.0.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEC6DB8C213AA597E.TMP | — | |
MD5:— | SHA256:— | |||
| 3312 | DWB.exe | C:\ProgramData\PEZ\DWB.004 | binary | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019021120190212\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1724942A966E1C29.TMP | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{A4ADA3E4-2DE3-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
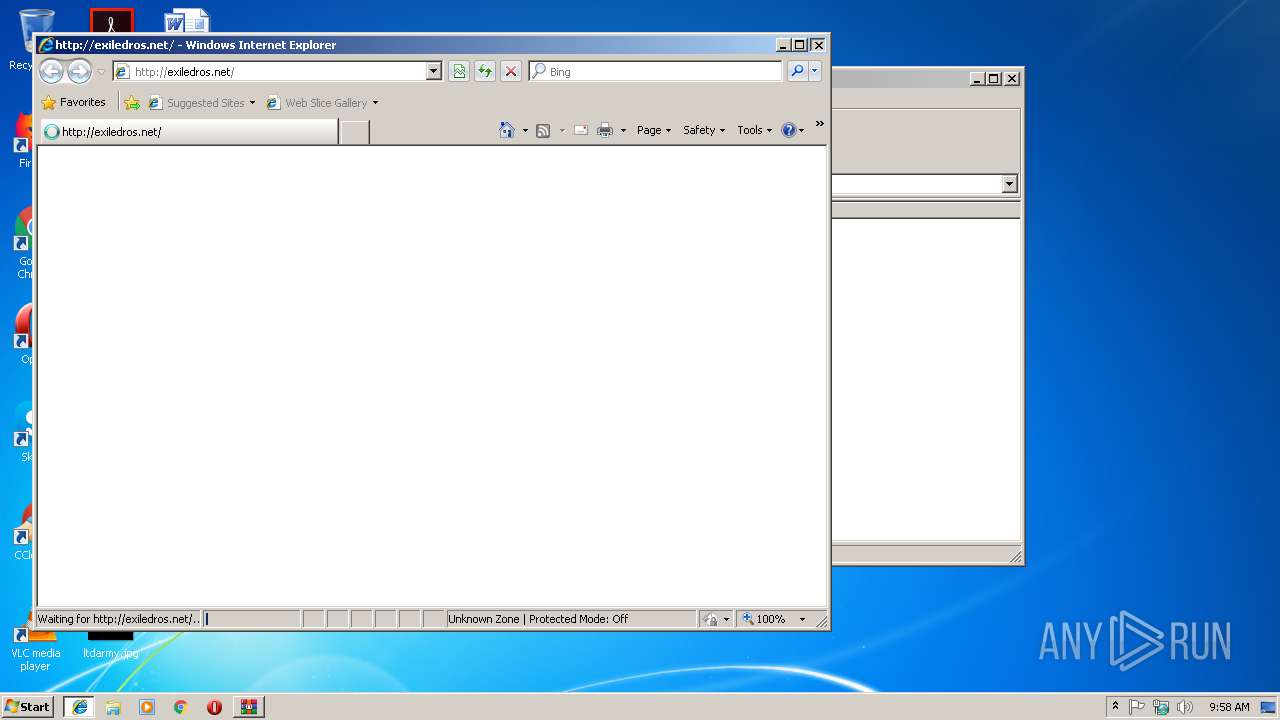
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\exiledros_net[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
45
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | iexplore.exe | GET | — | 103.255.237.236:80 | http://exiledros.net/file/introboxes.js | VN | — | — | malicious |
3824 | iexplore.exe | GET | — | 103.255.237.236:80 | http://exiledros.net/file/jquery-latest.js | VN | — | — | malicious |
3968 | c0YPfe7h.exe | GET | 200 | 103.255.237.236:80 | http://exiledros.net/webcheck.php | VN | text | 20 b | malicious |
3824 | iexplore.exe | GET | 200 | 103.255.237.236:80 | http://exiledros.net/ | VN | html | 3.79 Kb | malicious |
3968 | c0YPfe7h.exe | GET | 200 | 103.255.237.236:80 | http://exiledros.net/downloadlink.php | VN | text | 24 b | malicious |
3824 | iexplore.exe | GET | 200 | 172.217.18.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 29.4 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 103.255.237.236:80 | http://exiledros.net/file/css1.css | VN | text | 1.47 Kb | malicious |
3824 | iexplore.exe | GET | 200 | 172.217.22.106:80 | http://ajax.googleapis.com/ajax/libs/jquery/1/jquery.min.js | US | text | 32.6 Kb | whitelisted |
3804 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3968 | c0YPfe7h.exe | GET | 200 | 103.255.237.236:80 | http://exiledros.net/GpRk9lnkYDU7ROyE.php | VN | text | 9 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | c0YPfe7h.exe | 103.255.237.236:80 | exiledros.net | VNPT Corp | VN | unknown |
3084 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3824 | iexplore.exe | 103.255.237.236:80 | exiledros.net | VNPT Corp | VN | unknown |
3824 | iexplore.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3824 | iexplore.exe | 172.217.22.106:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3824 | iexplore.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3804 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3824 | iexplore.exe | 172.217.18.98:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2428 | iexplore.exe | 104.28.13.33:443 | clk.ink | Cloudflare Inc | US | shared |
1244 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exiledros.net |
| malicious |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
clk.ink |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
c0YPfe7h.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|